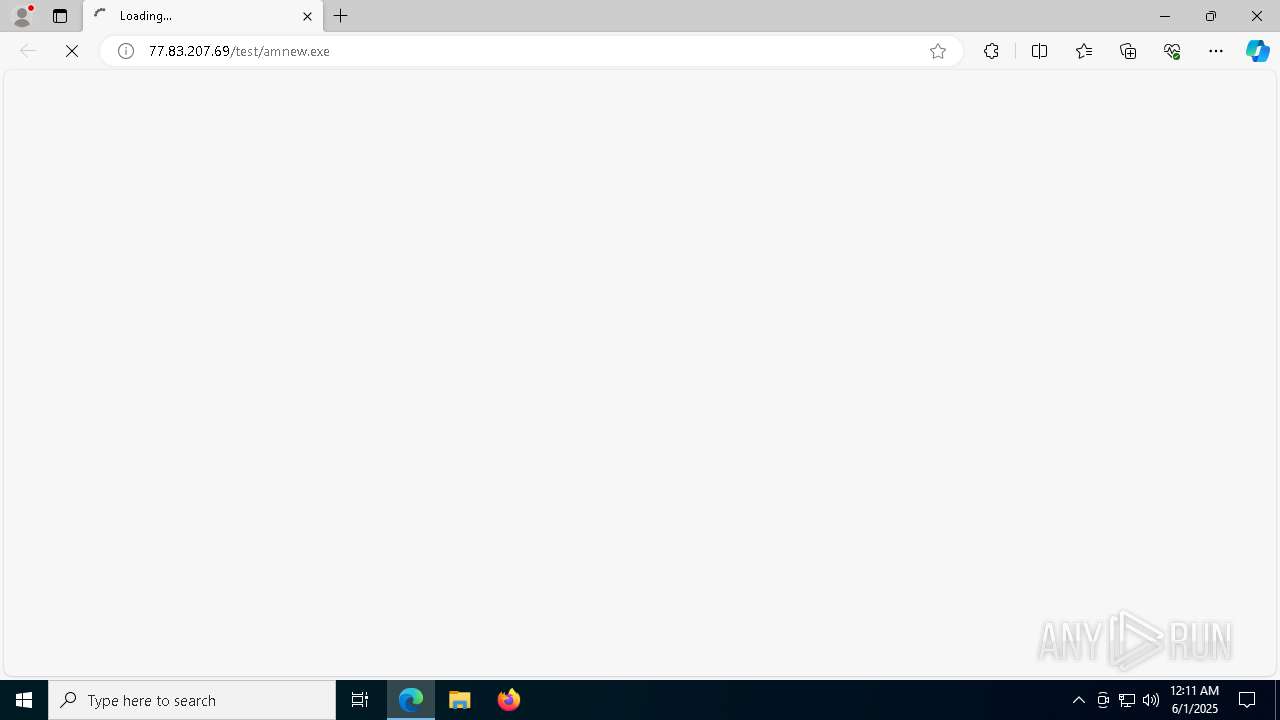
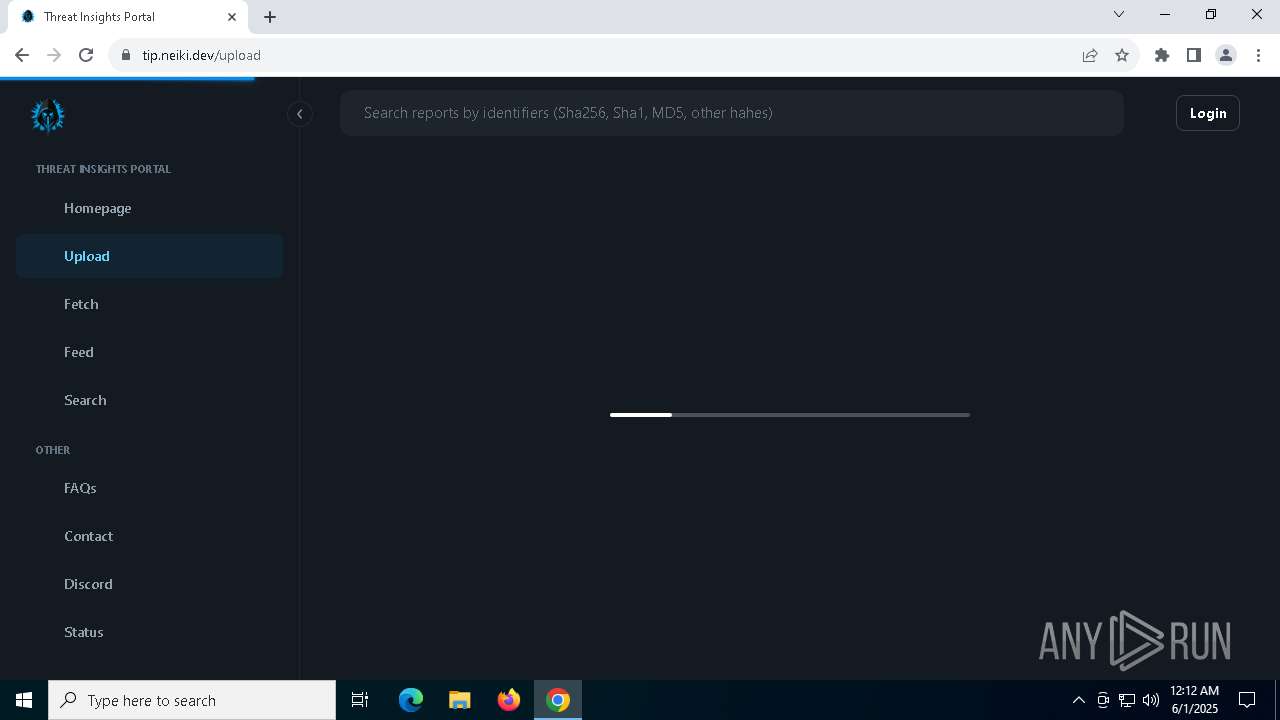
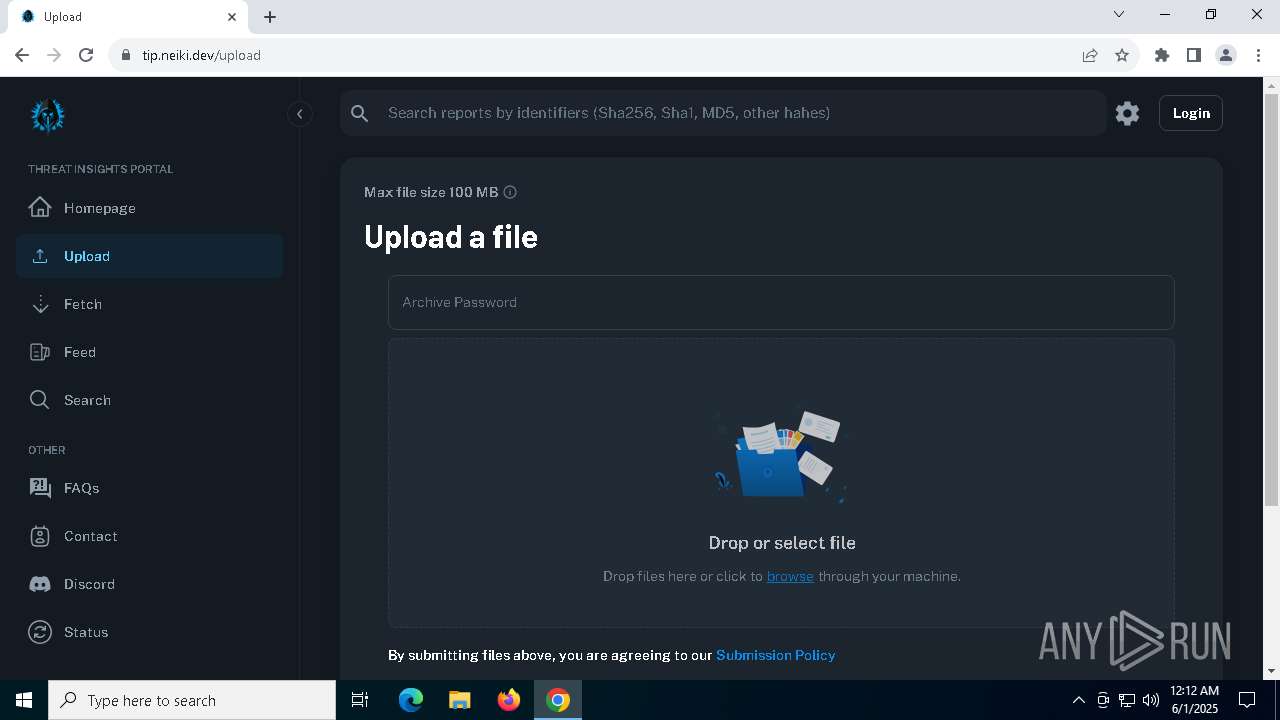
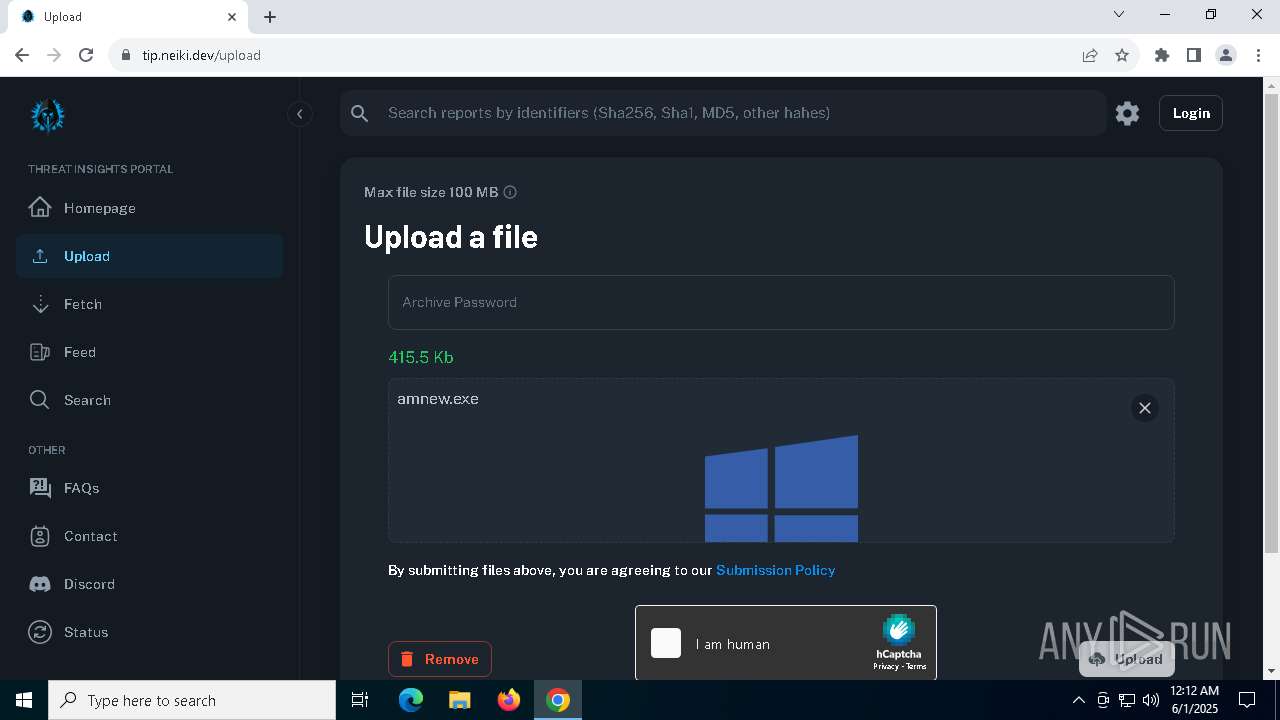
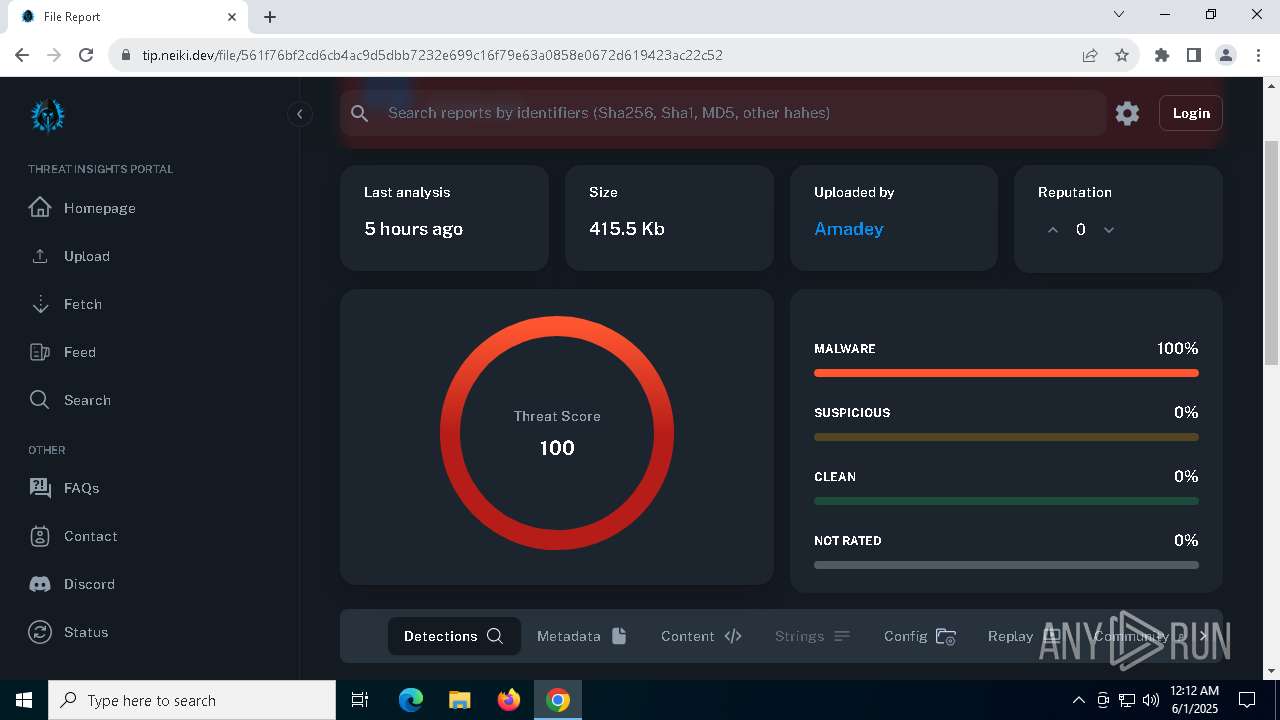
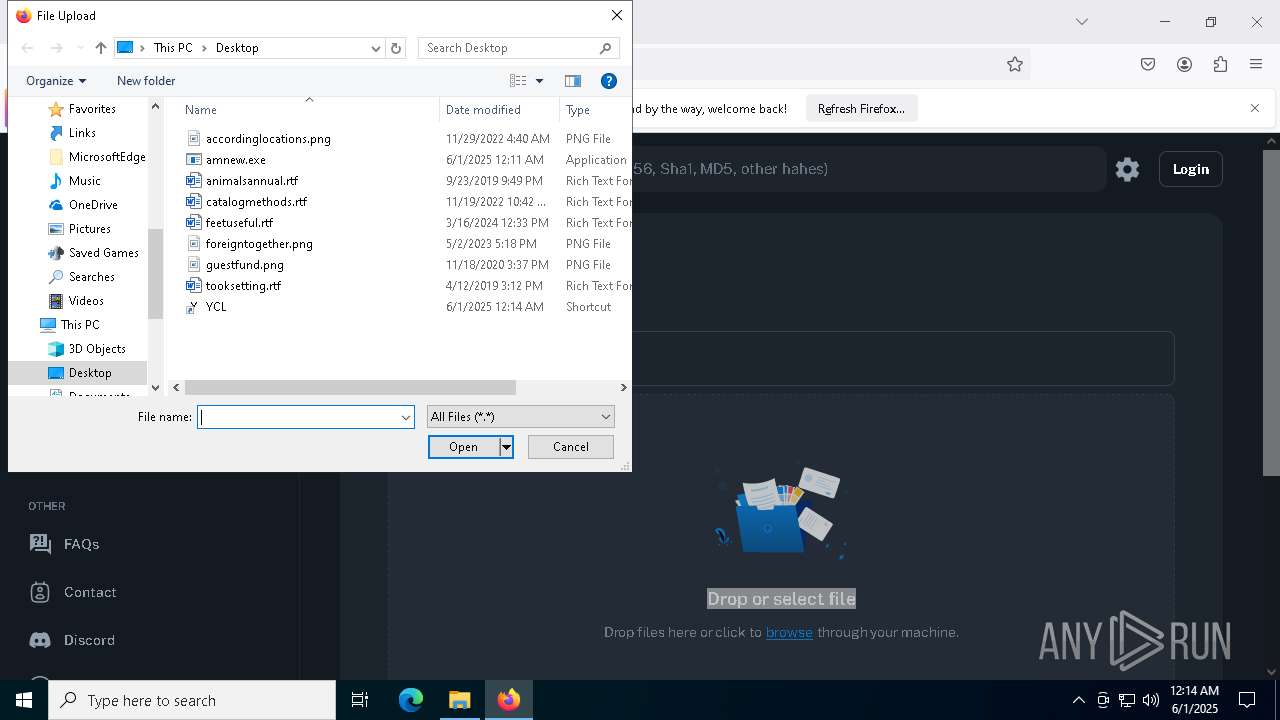
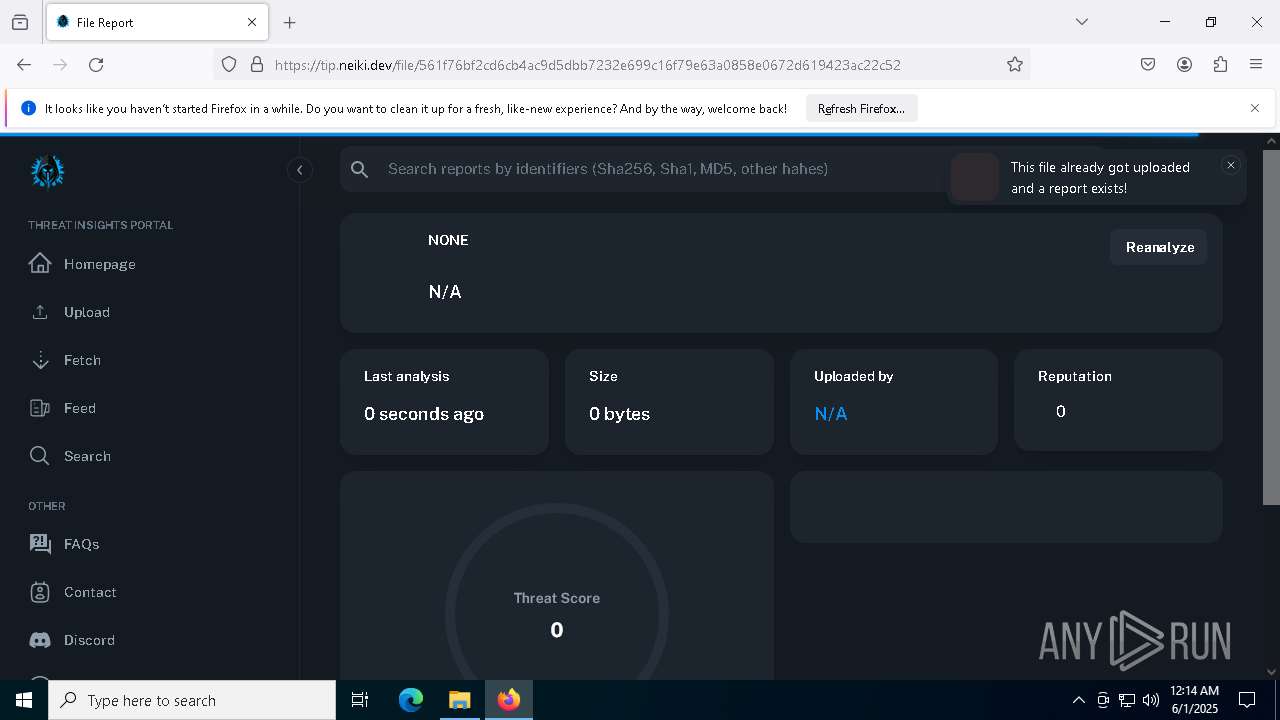
| URL: | http://77.83.207.69/test/amnew.exe |
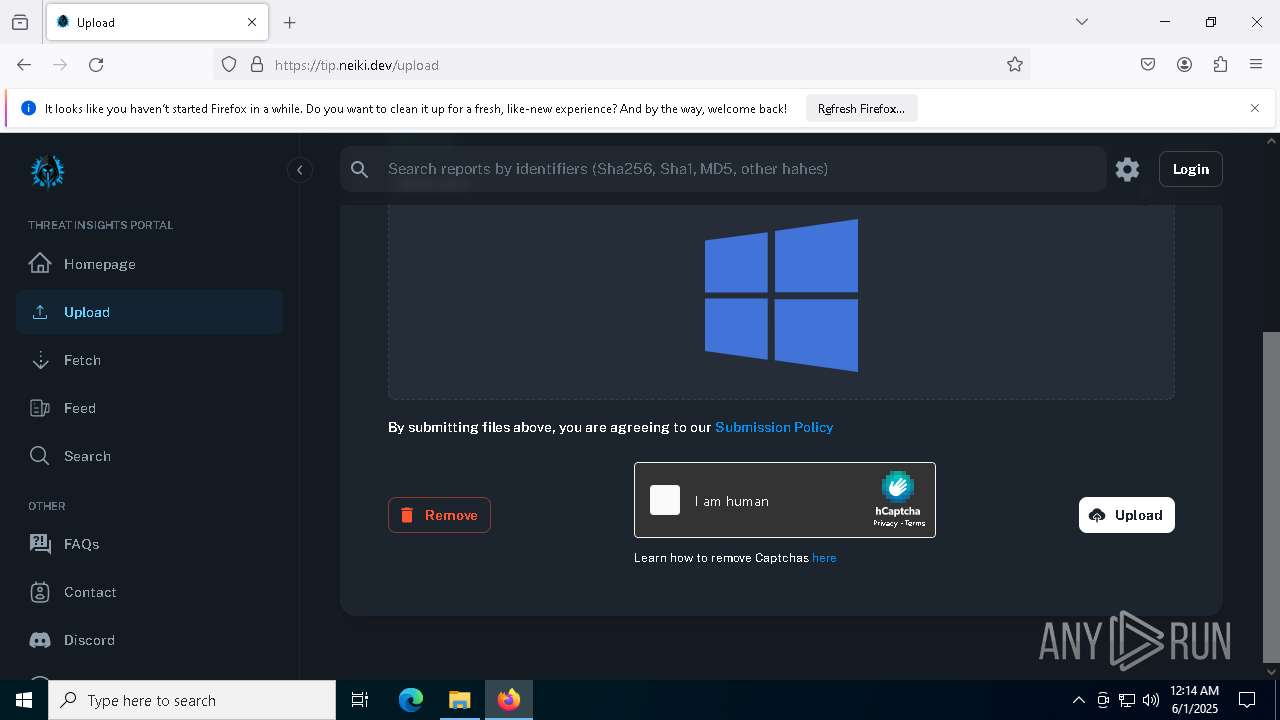
| Full analysis: | https://app.any.run/tasks/76c8ed0b-b539-4efa-a10d-e20c62a8050c |
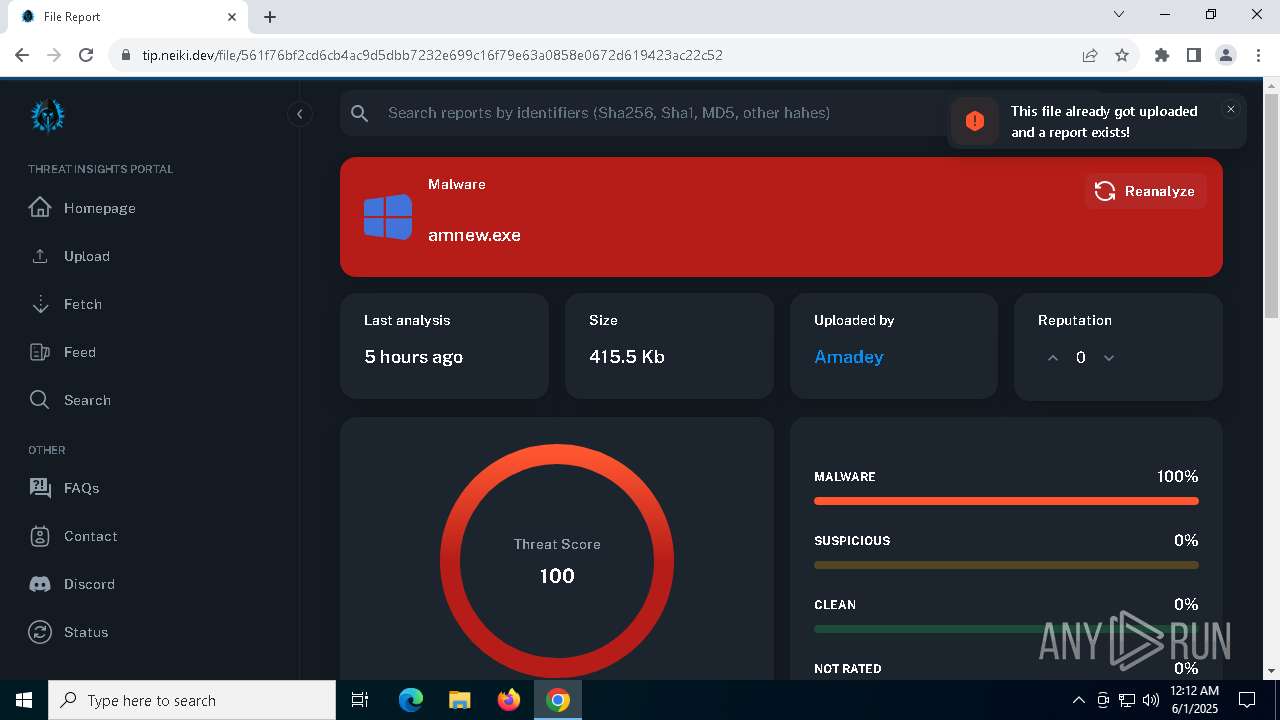
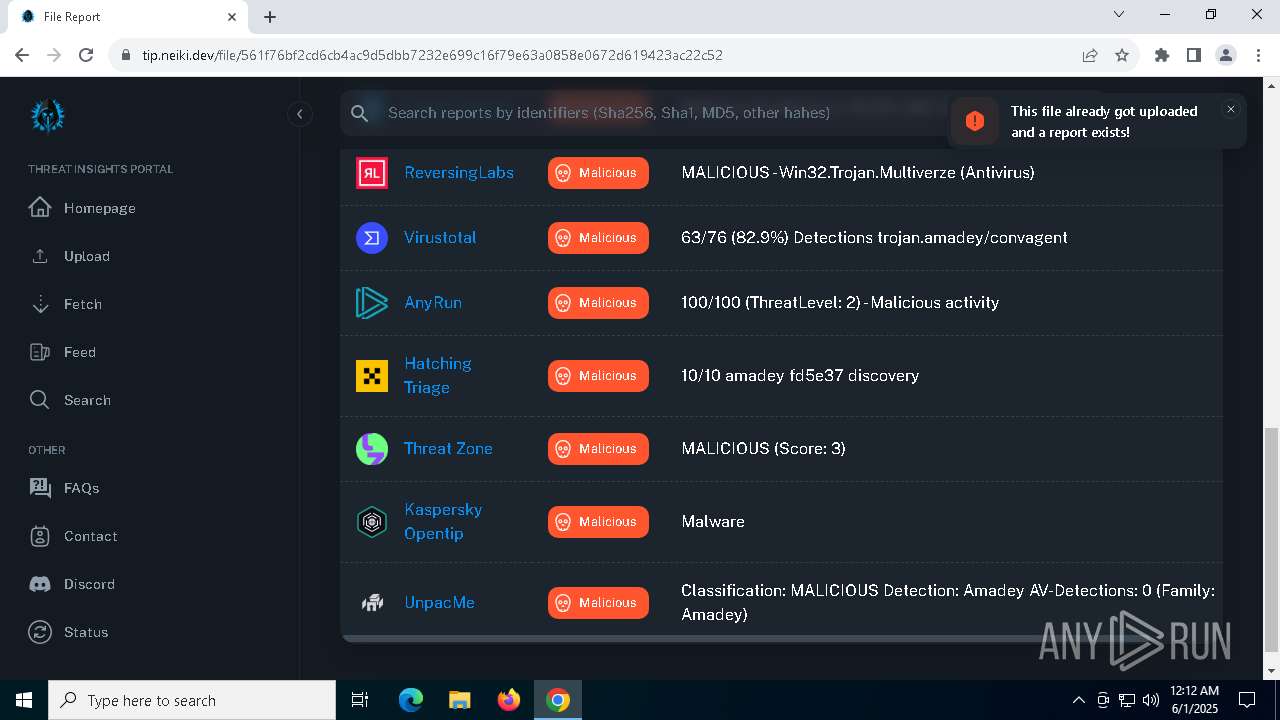
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 01, 2025, 00:11:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5C35DCB445362AF294AFE46288DD78C1 |
| SHA1: | 46B5F1408C7AFD24BF34A11E3958BA67A000EB97 |
| SHA256: | CFDA539CBD88FACA3C5ECE429424ED34F44D5FAB7448B96D3987120AEF7D3BB1 |
| SSDEEP: | 3:N1KcLdMYAkA:Ccta |
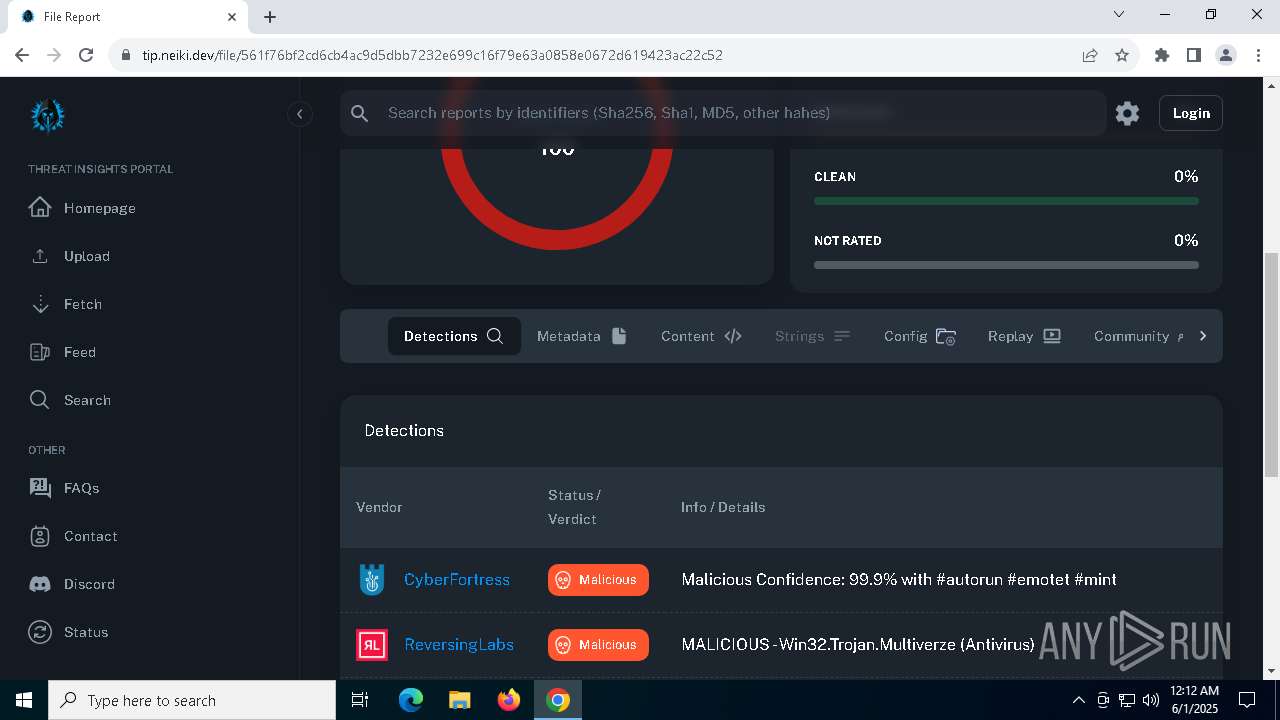
MALICIOUS
AMADEY has been detected (SURICATA)
- saren.exe (PID: 3896)
Connects to the CnC server
- saren.exe (PID: 3896)
AMADEY has been detected (YARA)
- saren.exe (PID: 3896)
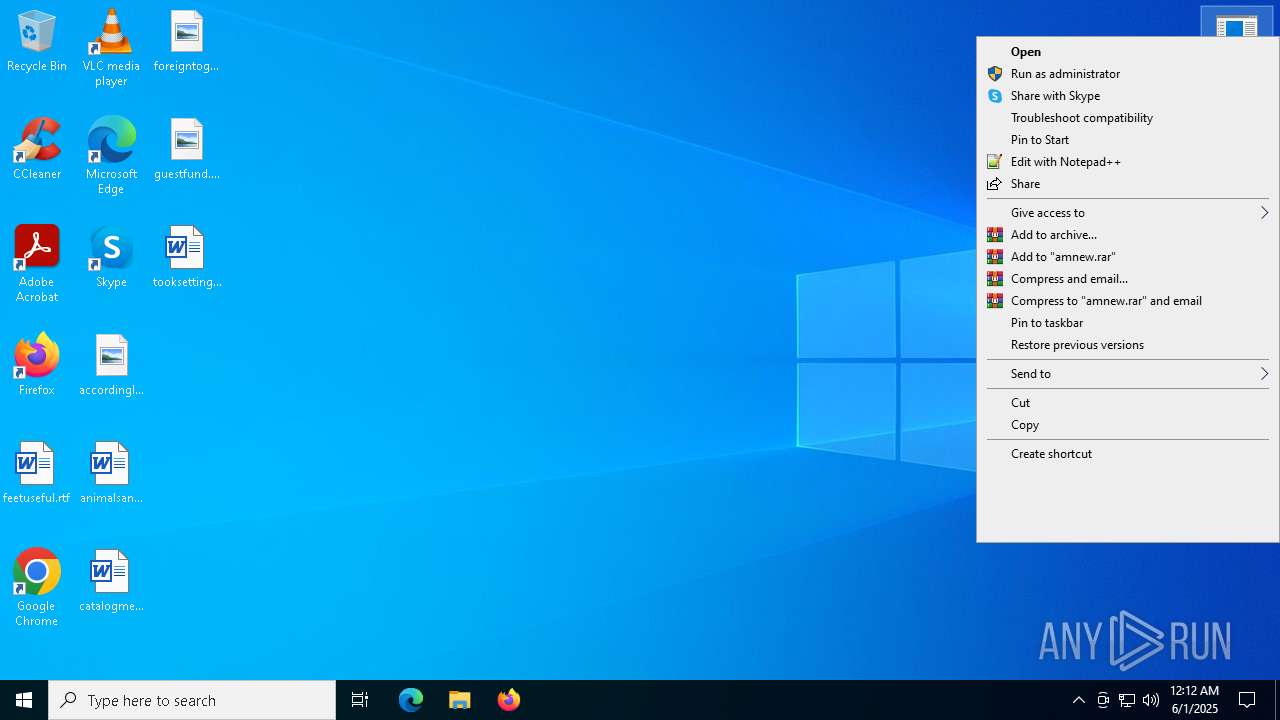
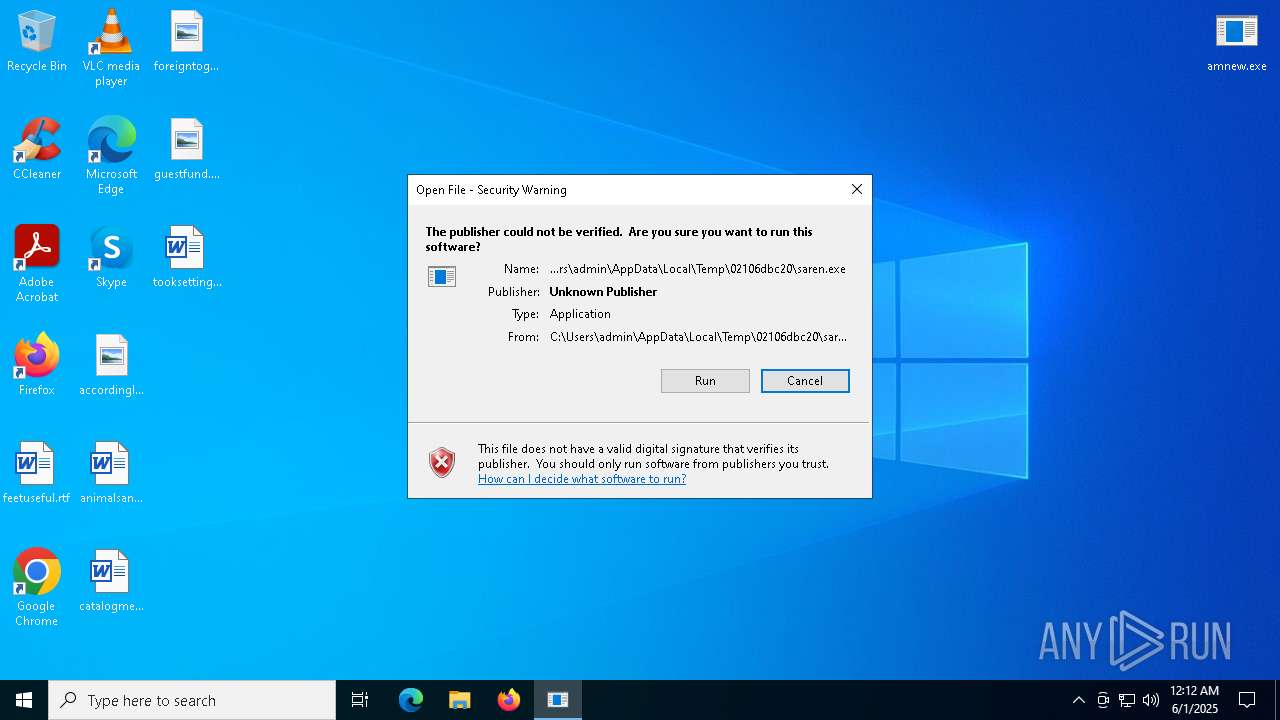
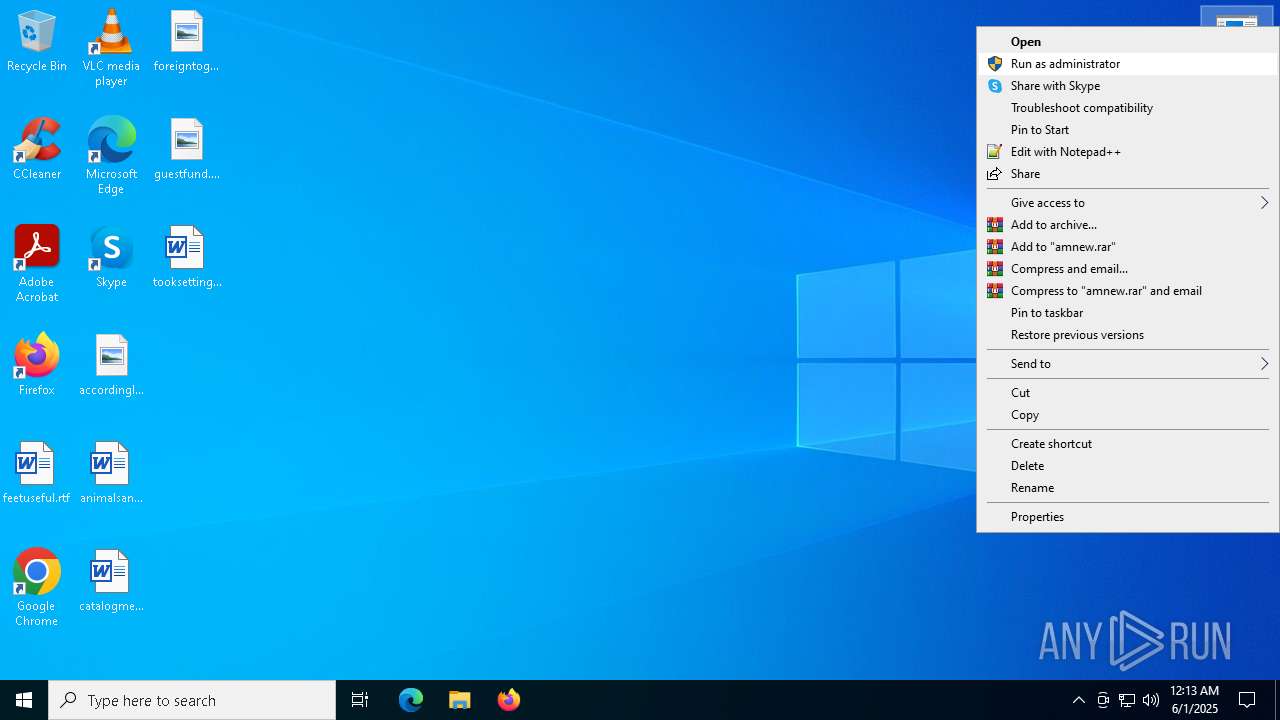
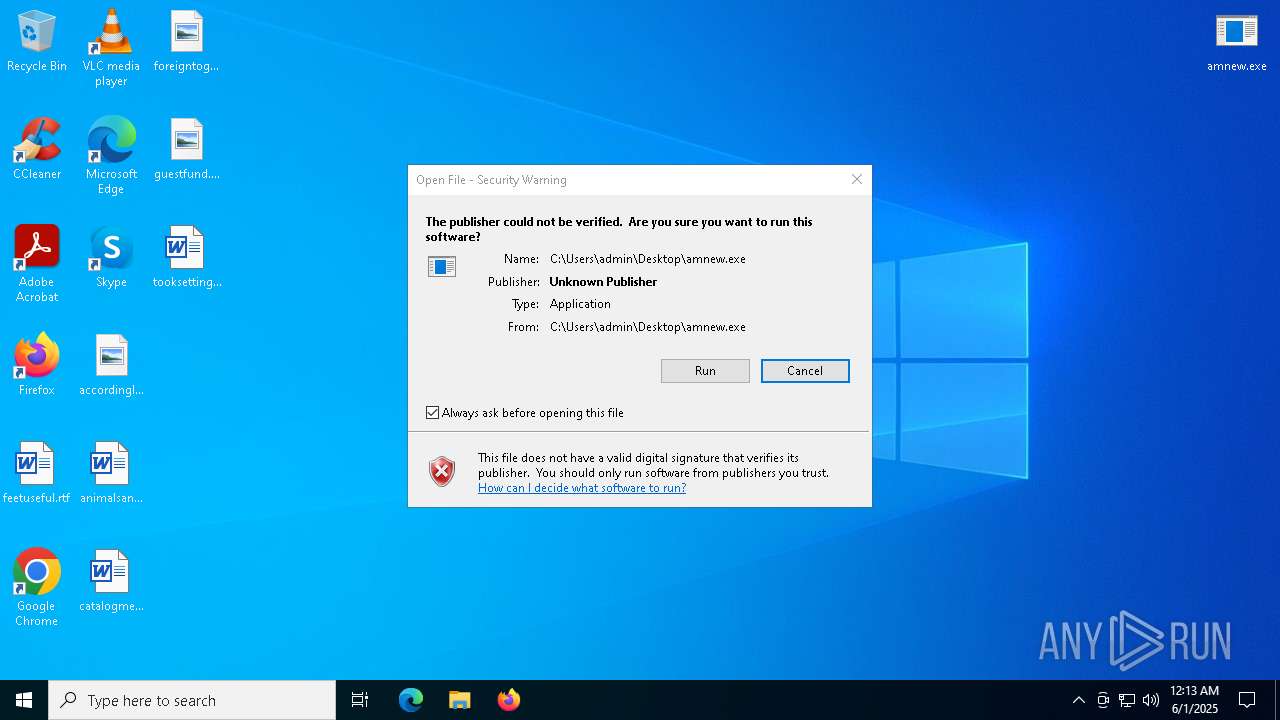
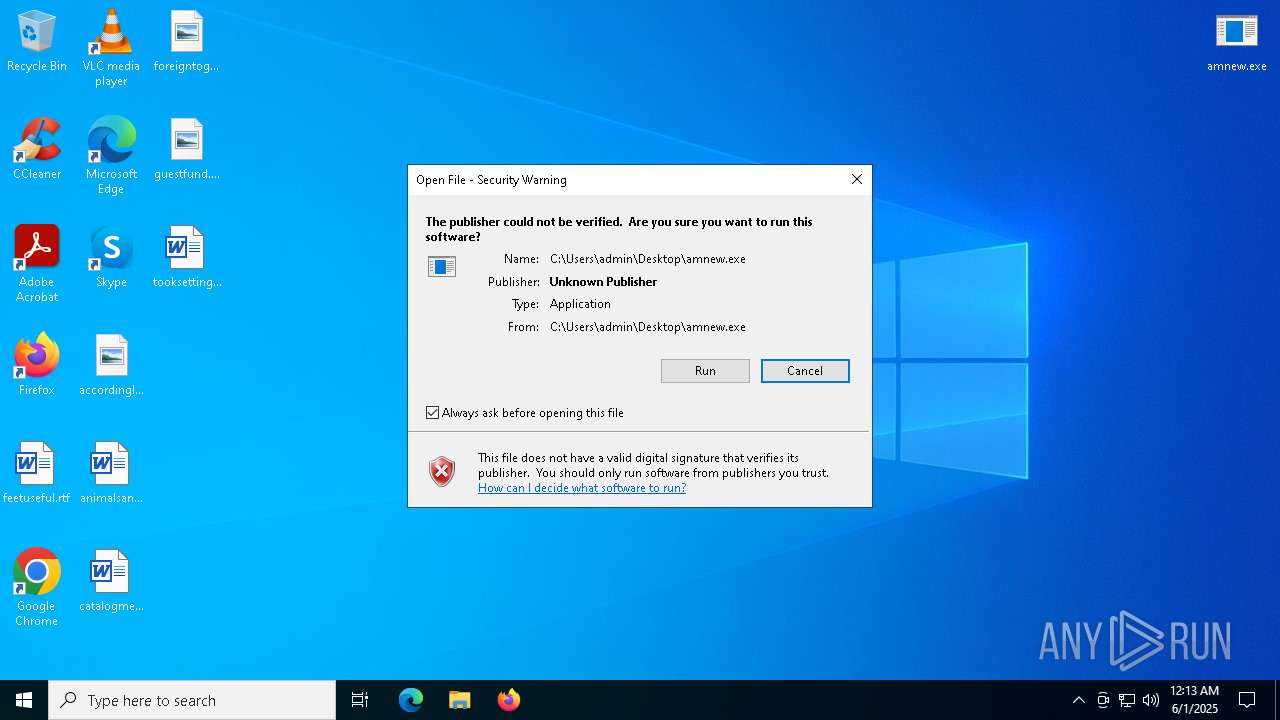
Executing a file with an untrusted certificate
- 6045c1e532.exe (PID: 7684)
GCLEANER has been detected (SURICATA)
- 6045c1e532.exe (PID: 7684)
GENERIC has been found (auto)
- 6045c1e532.exe (PID: 7684)
SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 3968)
- saren.exe (PID: 3896)
- 6045c1e532.exe (PID: 7684)
Contacting a server suspected of hosting an CnC
- saren.exe (PID: 3896)
Process requests binary or script from the Internet
- saren.exe (PID: 3896)
Connects to the server without a host name
- saren.exe (PID: 3896)
- 6045c1e532.exe (PID: 7684)
There is functionality for taking screenshot (YARA)
- saren.exe (PID: 3896)
- 6045c1e532.exe (PID: 7684)
There is functionality for enable RDP (YARA)
- saren.exe (PID: 3896)
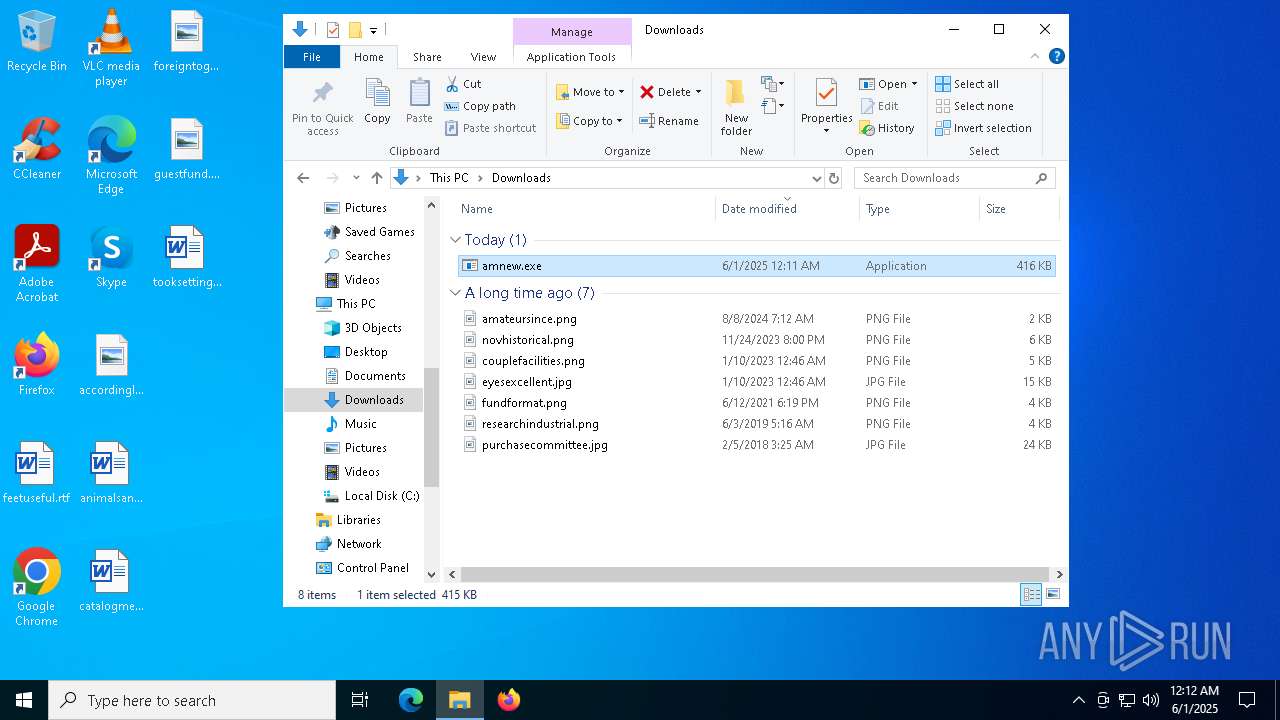
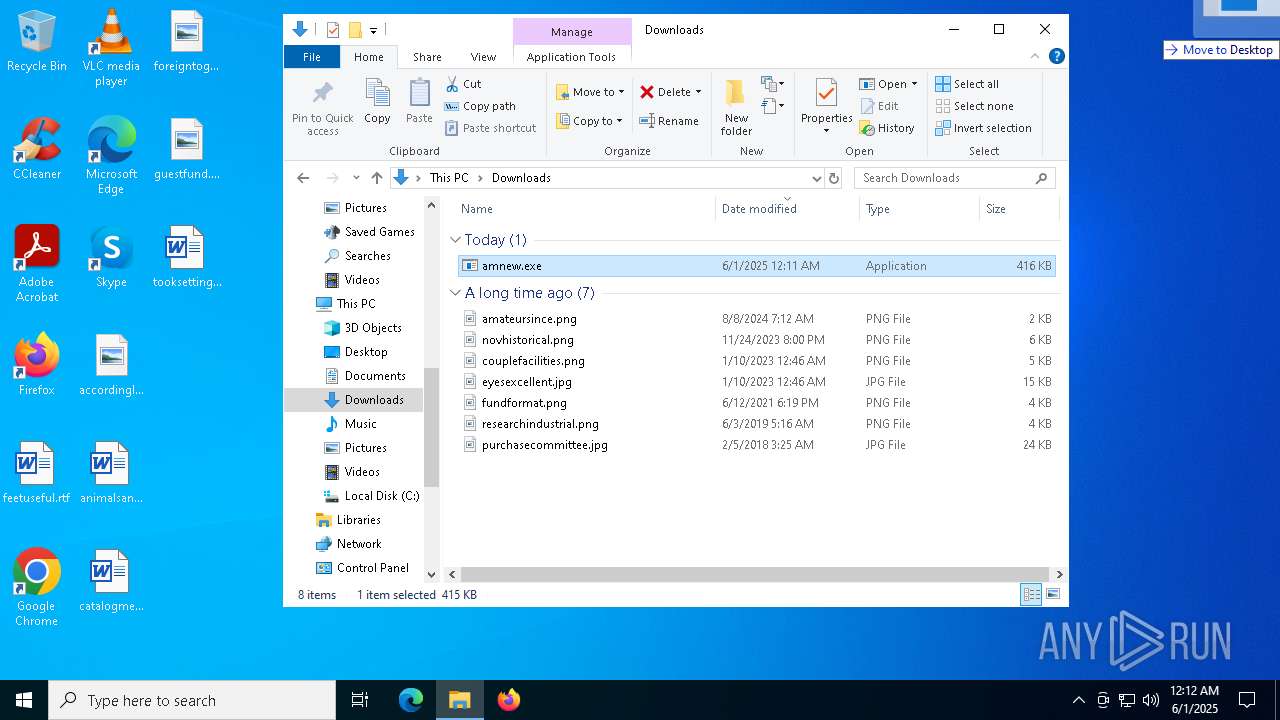
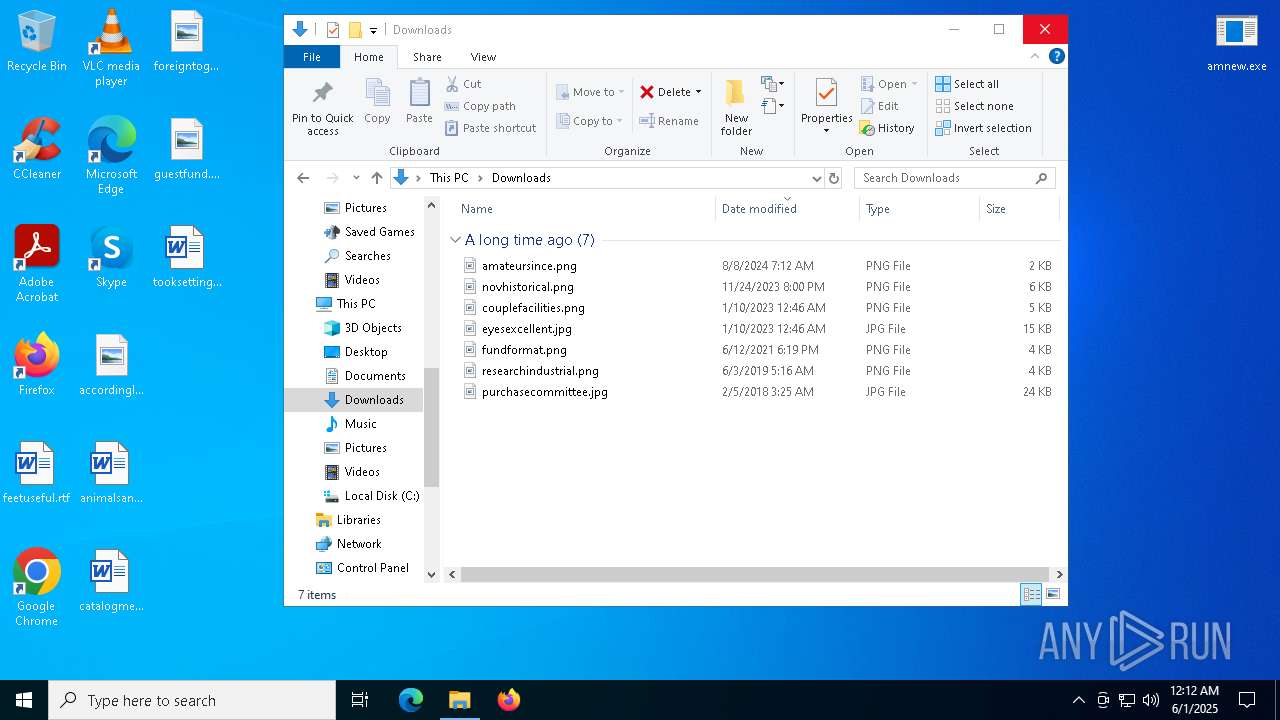
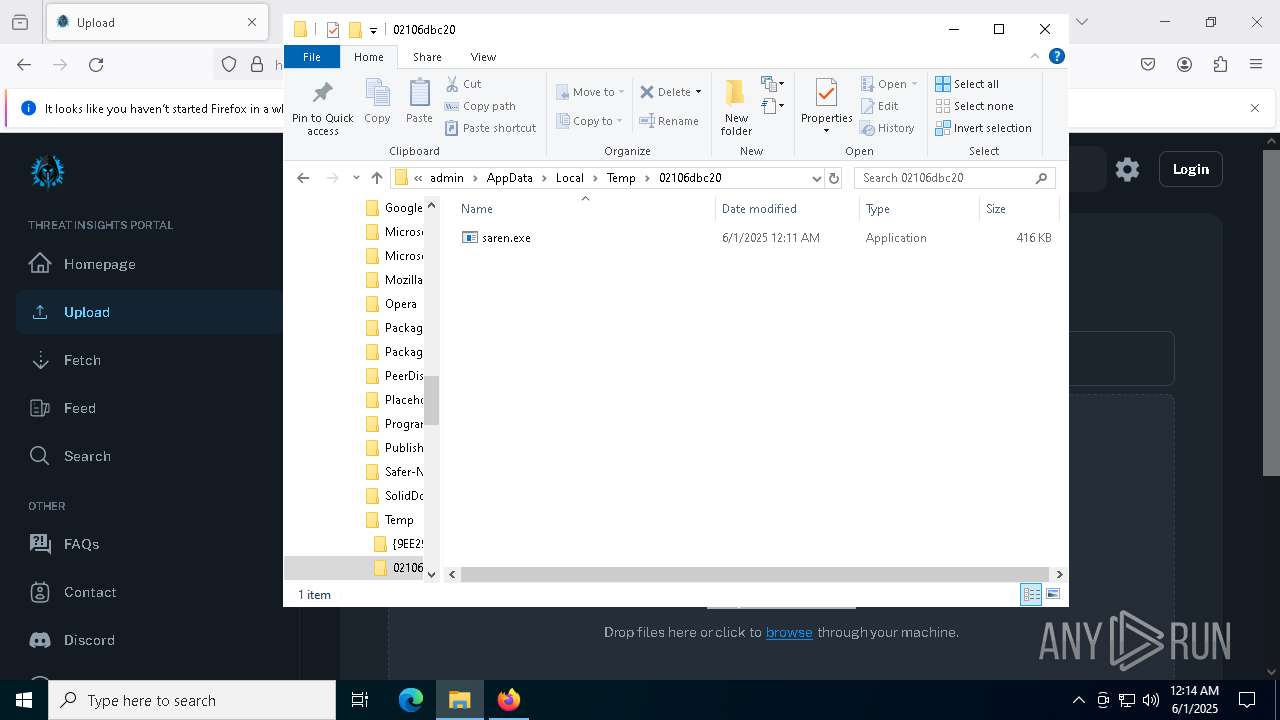
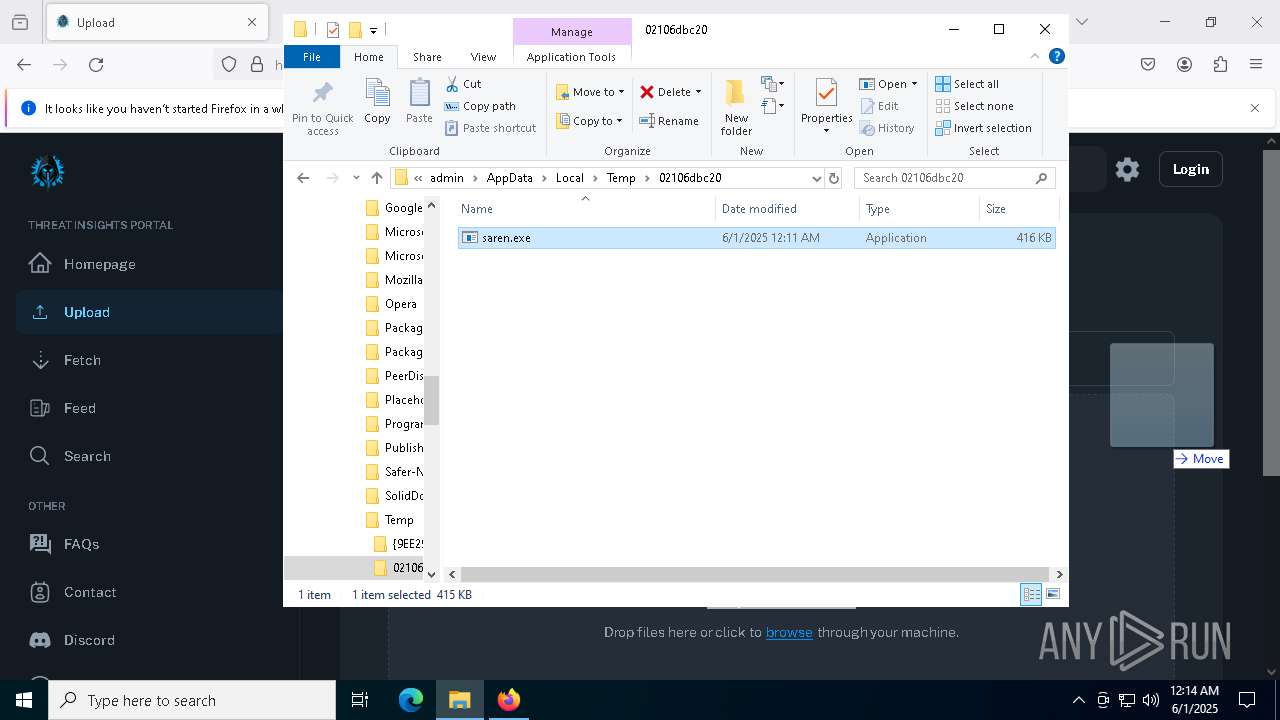
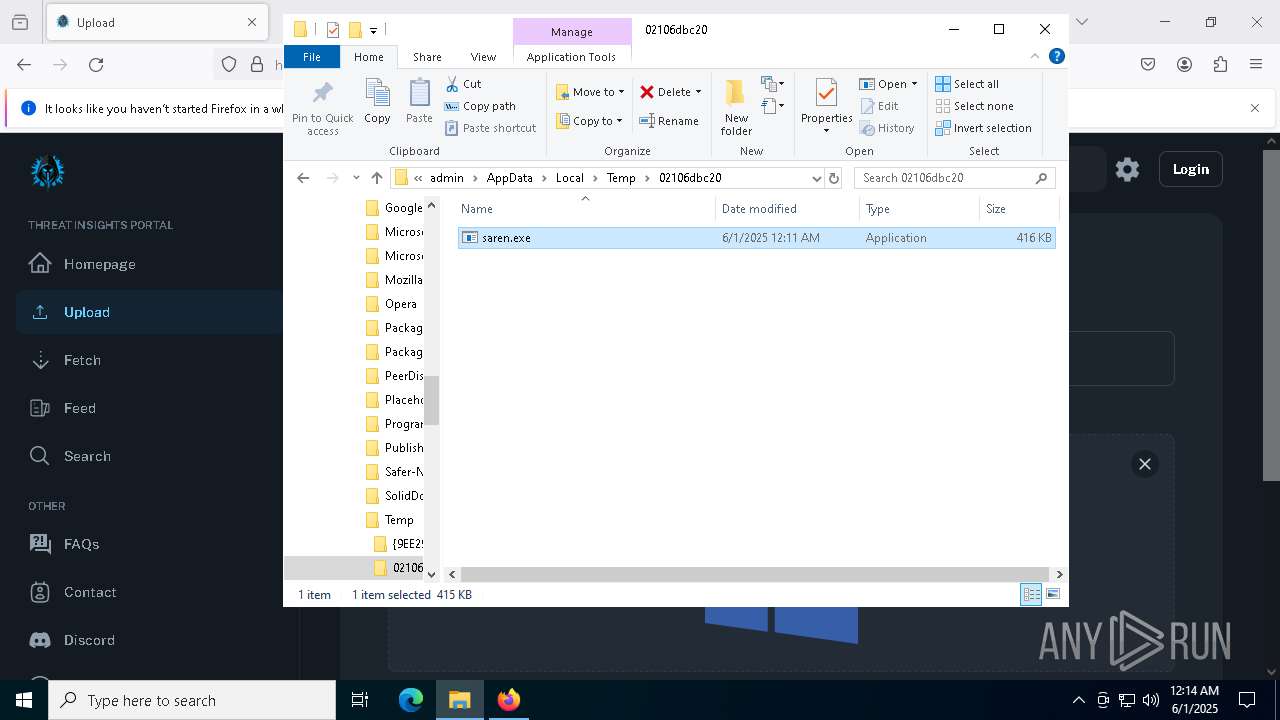
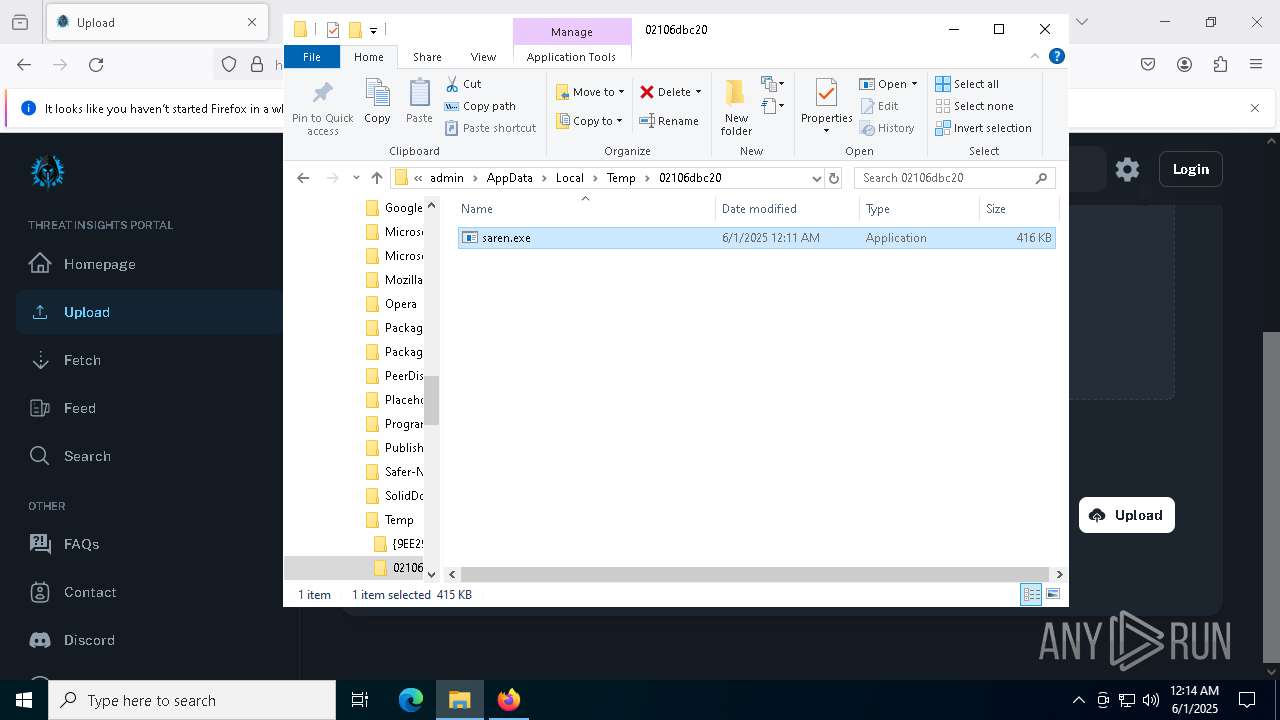
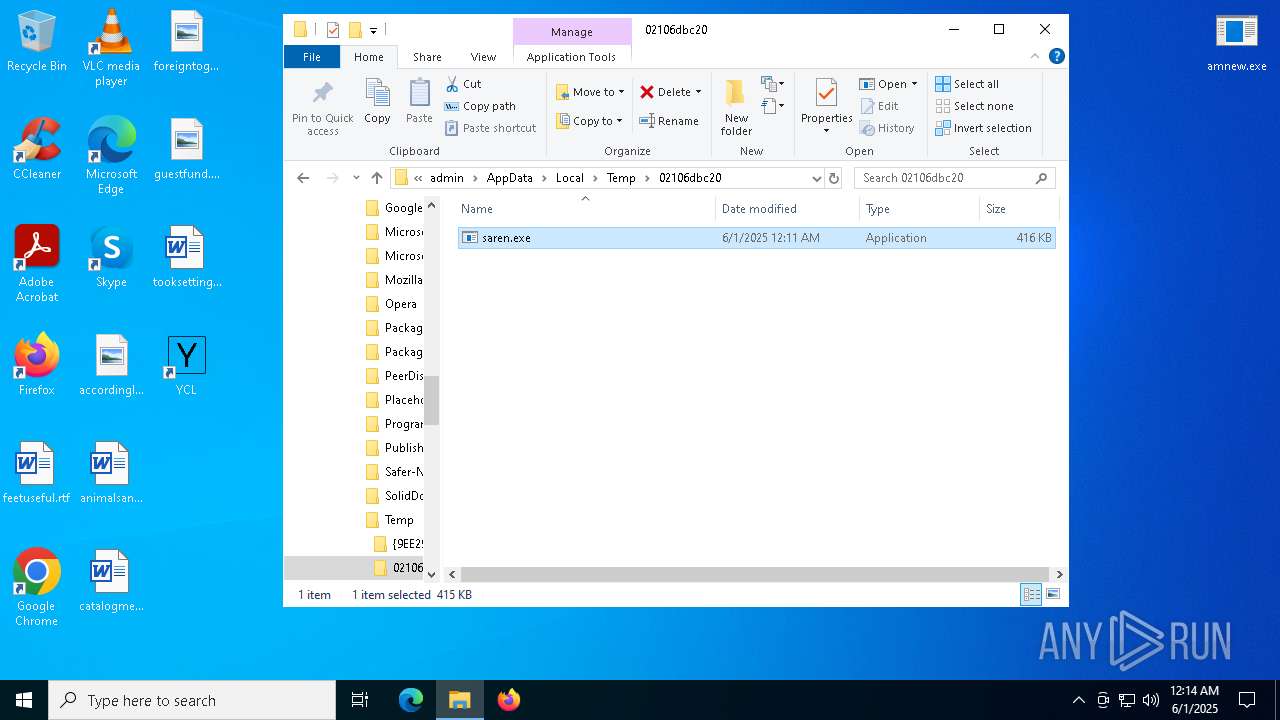
Executable content was dropped or overwritten
- amnew.exe (PID: 2392)
- saren.exe (PID: 3896)
- 6045c1e532.exe (PID: 7684)
Starts itself from another location
- amnew.exe (PID: 2392)
INFO
Application launched itself
- msedge.exe (PID: 4224)
- msedge.exe (PID: 3304)
- chrome.exe (PID: 5988)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 660)
- firefox.exe (PID: 5072)
- firefox.exe (PID: 8020)
Checks supported languages
- identity_helper.exe (PID: 7612)
- identity_helper.exe (PID: 5596)
Reads the computer name
- identity_helper.exe (PID: 7612)
- identity_helper.exe (PID: 5596)
Executable content was dropped or overwritten
- msedge.exe (PID: 4224)
- msedge.exe (PID: 3968)
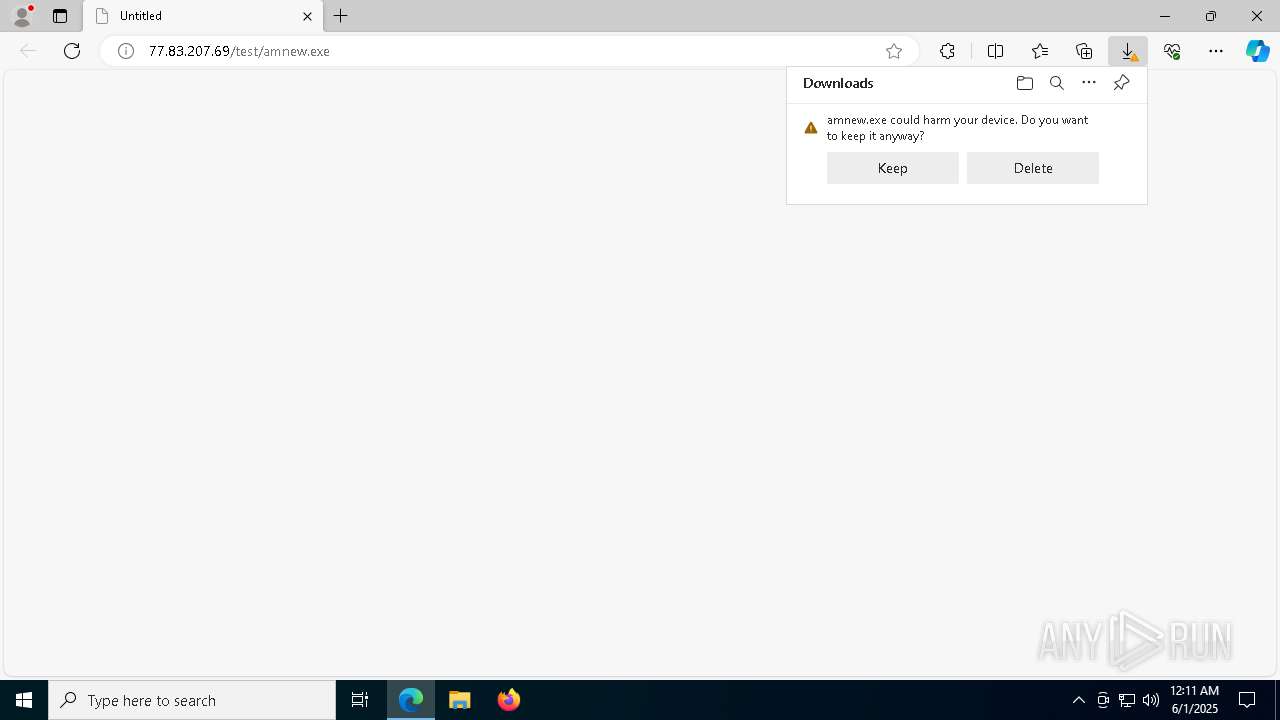
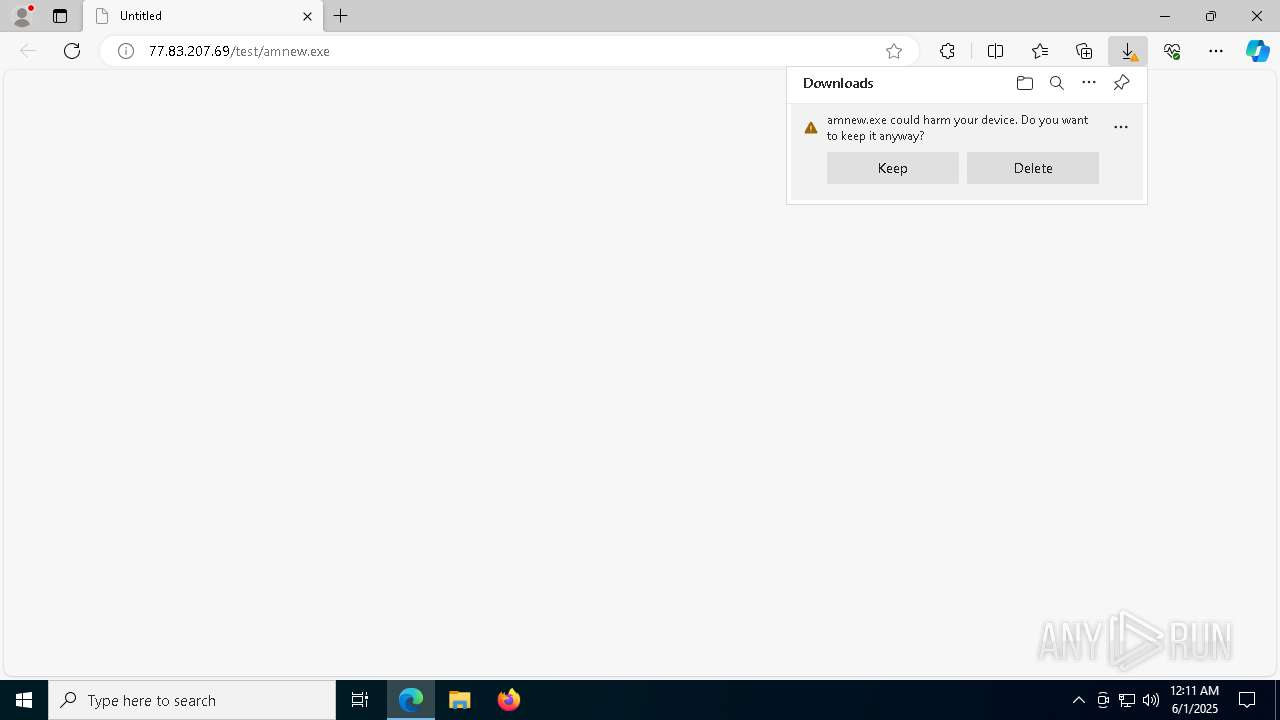
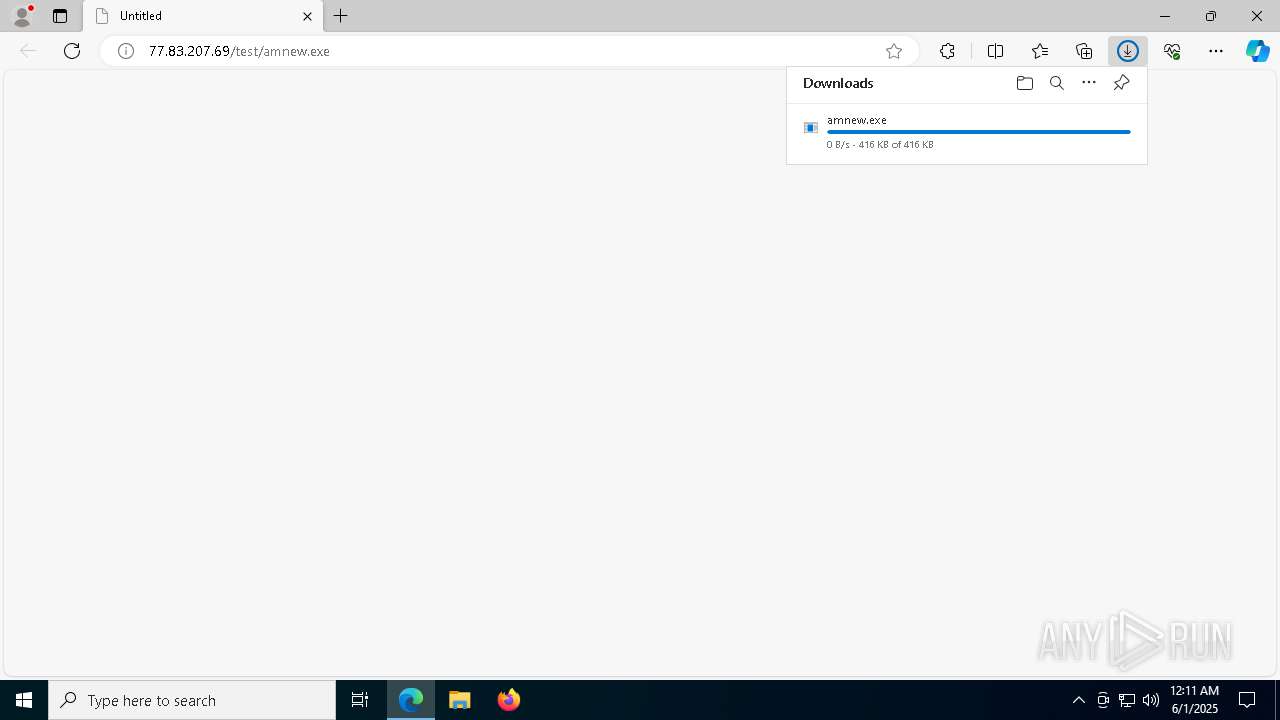
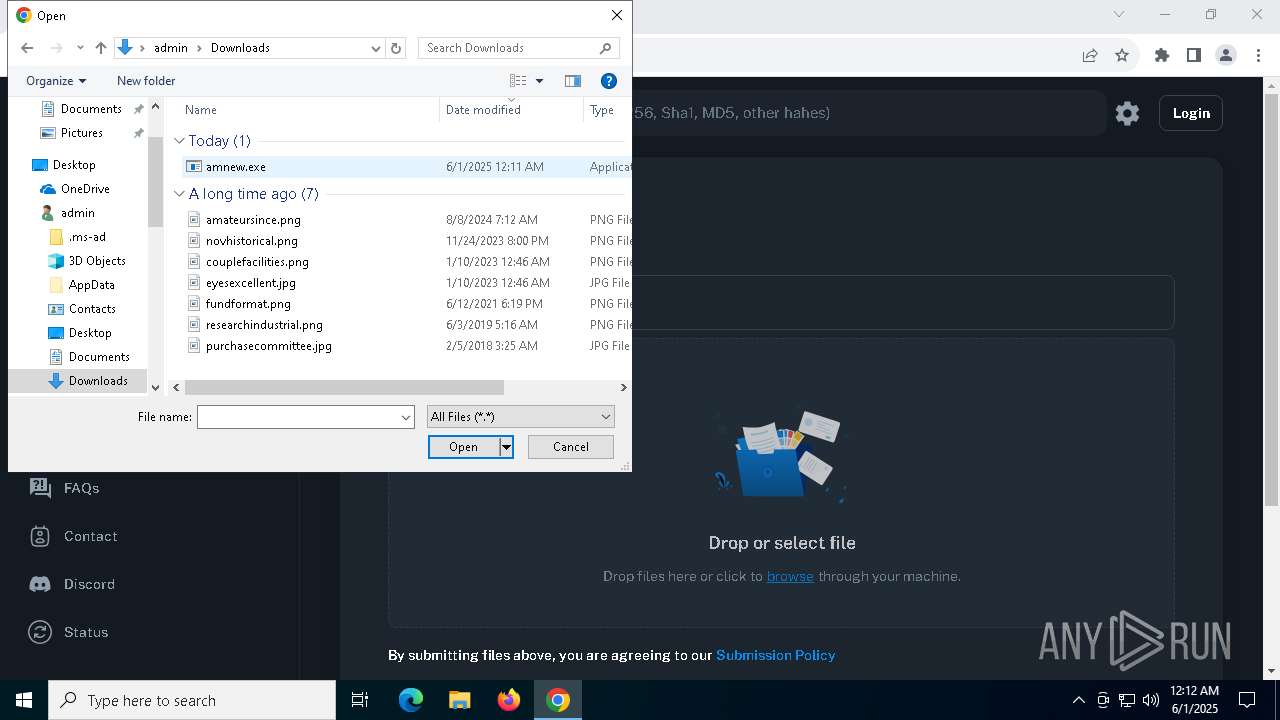
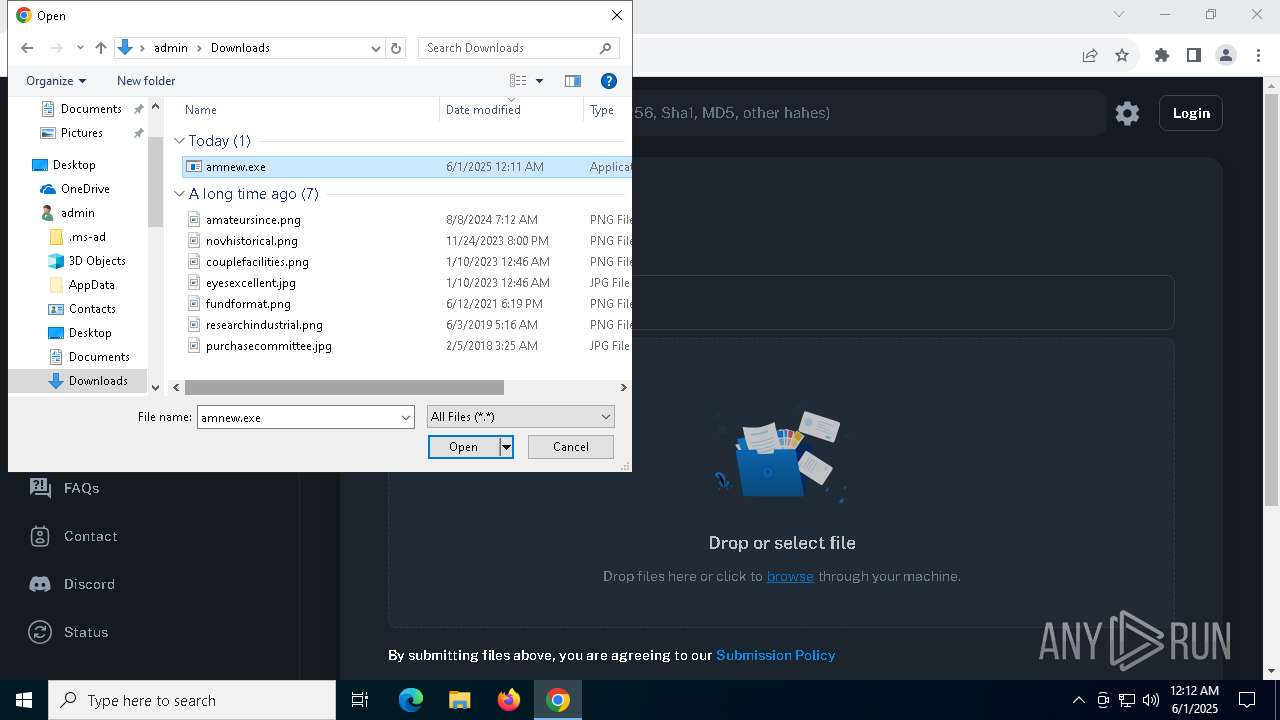
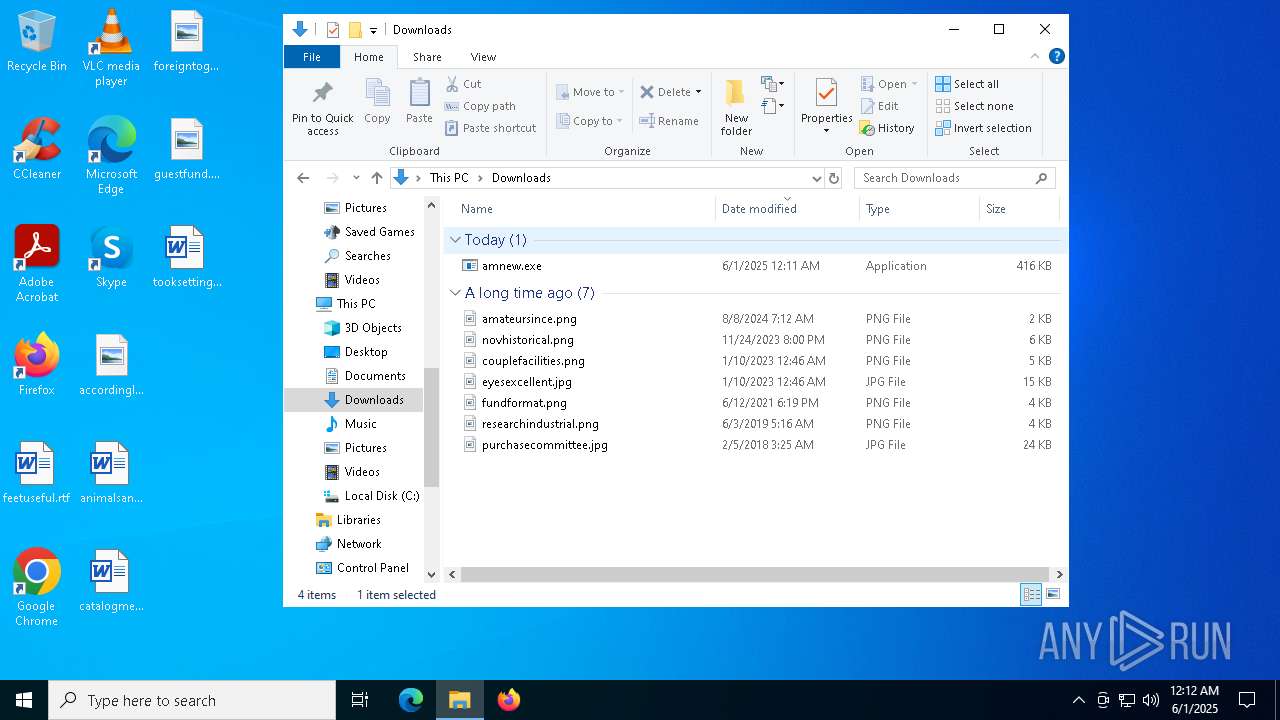
Launch of the file from Downloads directory
- msedge.exe (PID: 4224)
Reads Environment values
- identity_helper.exe (PID: 5596)
- identity_helper.exe (PID: 7612)
Manual execution by a user
- chrome.exe (PID: 660)
- chrome.exe (PID: 5988)
- chrome.exe (PID: 3132)
- amnew.exe (PID: 7688)
- amnew.exe (PID: 760)
- amnew.exe (PID: 2392)
- amnew.exe (PID: 5972)
- amnew.exe (PID: 4724)
- amnew.exe (PID: 7968)
- amnew.exe (PID: 4892)
- amnew.exe (PID: 7984)
- amnew.exe (PID: 1324)
- amnew.exe (PID: 8072)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 7912)
- amnew.exe (PID: 5968)
- amnew.exe (PID: 6240)
- amnew.exe (PID: 4700)
- amnew.exe (PID: 5452)
- amnew.exe (PID: 1072)
- amnew.exe (PID: 3192)
- amnew.exe (PID: 8032)
- amnew.exe (PID: 6800)
- amnew.exe (PID: 3140)
- amnew.exe (PID: 6156)
- amnew.exe (PID: 5304)
- amnew.exe (PID: 5776)
- amnew.exe (PID: 6920)
- firefox.exe (PID: 8020)
- amnew.exe (PID: 3248)
- amnew.exe (PID: 5772)
- amnew.exe (PID: 672)
- amnew.exe (PID: 7432)
- amnew.exe (PID: 7572)
- amnew.exe (PID: 5156)
- amnew.exe (PID: 7328)
- amnew.exe (PID: 2316)
- amnew.exe (PID: 2504)
- amnew.exe (PID: 5304)
- amnew.exe (PID: 7464)
- amnew.exe (PID: 1348)
- amnew.exe (PID: 8116)
- amnew.exe (PID: 780)
- amnew.exe (PID: 3276)
- amnew.exe (PID: 3436)
- amnew.exe (PID: 7124)
- amnew.exe (PID: 2476)
- amnew.exe (PID: 8076)
- amnew.exe (PID: 5996)
- amnew.exe (PID: 3996)
- amnew.exe (PID: 3180)
- amnew.exe (PID: 6068)
- amnew.exe (PID: 7720)
- amnew.exe (PID: 716)
- amnew.exe (PID: 7552)
- amnew.exe (PID: 5720)
- amnew.exe (PID: 5024)
- amnew.exe (PID: 6032)
- amnew.exe (PID: 536)
- amnew.exe (PID: 1812)
- amnew.exe (PID: 7712)
- amnew.exe (PID: 7624)
- amnew.exe (PID: 6712)
- amnew.exe (PID: 7184)
- amnew.exe (PID: 7976)
- amnew.exe (PID: 516)
- amnew.exe (PID: 5216)
- amnew.exe (PID: 800)
- amnew.exe (PID: 7148)
- amnew.exe (PID: 7200)
- amnew.exe (PID: 644)
- amnew.exe (PID: 5592)
- amnew.exe (PID: 7480)
- amnew.exe (PID: 1240)
- amnew.exe (PID: 2644)
- amnew.exe (PID: 5332)
- amnew.exe (PID: 2092)
- amnew.exe (PID: 4724)
- amnew.exe (PID: 5744)
- amnew.exe (PID: 5480)
- amnew.exe (PID: 5936)
- amnew.exe (PID: 8148)
- amnew.exe (PID: 7084)
- amnew.exe (PID: 6028)
- amnew.exe (PID: 1056)
- amnew.exe (PID: 8108)
- amnew.exe (PID: 6180)
- amnew.exe (PID: 4452)
- amnew.exe (PID: 7820)
- amnew.exe (PID: 2840)
- amnew.exe (PID: 2596)
- amnew.exe (PID: 1696)
- amnew.exe (PID: 2420)
- amnew.exe (PID: 2780)
- amnew.exe (PID: 3264)
- amnew.exe (PID: 8100)
- amnew.exe (PID: 5008)
- amnew.exe (PID: 2244)
- amnew.exe (PID: 6592)
- amnew.exe (PID: 6576)
- amnew.exe (PID: 7308)
- amnew.exe (PID: 6584)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 7324)
- amnew.exe (PID: 1196)
- amnew.exe (PID: 6712)
- amnew.exe (PID: 2656)
- amnew.exe (PID: 3100)
- amnew.exe (PID: 6068)
- amnew.exe (PID: 5608)
- amnew.exe (PID: 6392)
- amnew.exe (PID: 4040)
- amnew.exe (PID: 4672)
- amnew.exe (PID: 4920)
- amnew.exe (PID: 1072)
- amnew.exe (PID: 4448)
- amnew.exe (PID: 7036)
- amnew.exe (PID: 7588)
- amnew.exe (PID: 6744)
- amnew.exe (PID: 5408)
- amnew.exe (PID: 7184)
- amnew.exe (PID: 2600)
- amnew.exe (PID: 7976)
- amnew.exe (PID: 5216)
- amnew.exe (PID: 7944)
- amnew.exe (PID: 8068)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 8064)
- amnew.exe (PID: 3192)
- amnew.exe (PID: 5124)
- amnew.exe (PID: 7640)
- amnew.exe (PID: 8176)
- amnew.exe (PID: 2644)
- amnew.exe (PID: 6656)
- amnew.exe (PID: 6248)
- amnew.exe (PID: 6032)
- amnew.exe (PID: 7220)
- amnew.exe (PID: 7988)
- amnew.exe (PID: 4404)
- amnew.exe (PID: 808)
- amnew.exe (PID: 7404)
- amnew.exe (PID: 1852)
- amnew.exe (PID: 1312)
- amnew.exe (PID: 3140)
- amnew.exe (PID: 4732)
- amnew.exe (PID: 4452)
- amnew.exe (PID: 1600)
- amnew.exe (PID: 7880)
- amnew.exe (PID: 7476)
- amnew.exe (PID: 5484)
- amnew.exe (PID: 4324)
- amnew.exe (PID: 3036)
- amnew.exe (PID: 3416)
- amnew.exe (PID: 7432)
- amnew.exe (PID: 8048)
- amnew.exe (PID: 7464)
- amnew.exe (PID: 6156)
- amnew.exe (PID: 7048)
- amnew.exe (PID: 1520)
- amnew.exe (PID: 6592)
- amnew.exe (PID: 1672)
- amnew.exe (PID: 7348)
- amnew.exe (PID: 1196)
- amnew.exe (PID: 7248)
- amnew.exe (PID: 6044)
- amnew.exe (PID: 2244)
- amnew.exe (PID: 5556)
- amnew.exe (PID: 6940)
- amnew.exe (PID: 6248)
- amnew.exe (PID: 7460)
- amnew.exe (PID: 300)
- amnew.exe (PID: 856)
- amnew.exe (PID: 4040)
- amnew.exe (PID: 7324)
- amnew.exe (PID: 7712)
- amnew.exe (PID: 7864)
- amnew.exe (PID: 7756)
- amnew.exe (PID: 7944)
- amnew.exe (PID: 7148)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 7752)
- amnew.exe (PID: 8176)
- amnew.exe (PID: 2236)
- amnew.exe (PID: 6132)
- amnew.exe (PID: 3272)
- amnew.exe (PID: 808)
- amnew.exe (PID: 1852)
- amnew.exe (PID: 6268)
- amnew.exe (PID: 1040)
- amnew.exe (PID: 7708)
- amnew.exe (PID: 3248)
- amnew.exe (PID: 5624)
- amnew.exe (PID: 8128)
- amnew.exe (PID: 1168)
- amnew.exe (PID: 7124)
- amnew.exe (PID: 5960)
- amnew.exe (PID: 5132)
- amnew.exe (PID: 1616)
- amnew.exe (PID: 4020)
- amnew.exe (PID: 2316)
- amnew.exe (PID: 4028)
- amnew.exe (PID: 5996)
- amnew.exe (PID: 1348)
- amnew.exe (PID: 4424)
- amnew.exe (PID: 6252)
- amnew.exe (PID: 2368)
- amnew.exe (PID: 6584)
- amnew.exe (PID: 2656)
- amnew.exe (PID: 6180)
- amnew.exe (PID: 4184)
- amnew.exe (PID: 5452)
- amnew.exe (PID: 1764)
- amnew.exe (PID: 3268)
- amnew.exe (PID: 5164)
- amnew.exe (PID: 5116)
- amnew.exe (PID: 5344)
- amnew.exe (PID: 7712)
- amnew.exe (PID: 6904)
- amnew.exe (PID: 6908)
- amnew.exe (PID: 7868)
- amnew.exe (PID: 7608)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 8000)
- amnew.exe (PID: 7944)
- amnew.exe (PID: 5640)
- amnew.exe (PID: 6656)
- amnew.exe (PID: 7496)
- amnew.exe (PID: 2192)
- amnew.exe (PID: 2392)
- amnew.exe (PID: 2980)
- amnew.exe (PID: 6324)
- amnew.exe (PID: 5480)
- amnew.exe (PID: 1324)
- amnew.exe (PID: 6132)
- amnew.exe (PID: 3272)
- amnew.exe (PID: 808)
- amnew.exe (PID: 1852)
- amnew.exe (PID: 668)
- amnew.exe (PID: 4276)
- amnew.exe (PID: 7716)
- amnew.exe (PID: 7724)
- amnew.exe (PID: 3080)
- amnew.exe (PID: 4920)
- amnew.exe (PID: 4324)
- amnew.exe (PID: 6180)
- amnew.exe (PID: 7752)
- amnew.exe (PID: 2664)
- amnew.exe (PID: 7288)
- amnew.exe (PID: 5280)
- amnew.exe (PID: 2504)
- amnew.exe (PID: 4028)
- amnew.exe (PID: 1176)
- amnew.exe (PID: 4020)
- amnew.exe (PID: 3012)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 6252)
- amnew.exe (PID: 8168)
- amnew.exe (PID: 5176)
- amnew.exe (PID: 3996)
- amnew.exe (PID: 472)
- amnew.exe (PID: 4652)
- amnew.exe (PID: 1764)
- amnew.exe (PID: 6904)
- amnew.exe (PID: 7928)
- amnew.exe (PID: 5452)
- amnew.exe (PID: 6892)
- amnew.exe (PID: 7796)
- amnew.exe (PID: 2852)
- amnew.exe (PID: 5344)
- amnew.exe (PID: 5936)
- amnew.exe (PID: 6368)
- amnew.exe (PID: 1188)
- amnew.exe (PID: 7352)
- amnew.exe (PID: 1168)
- amnew.exe (PID: 4068)
- amnew.exe (PID: 2612)
- amnew.exe (PID: 6132)
- amnew.exe (PID: 1324)
- amnew.exe (PID: 2664)
- amnew.exe (PID: 5640)
- amnew.exe (PID: 7496)
- amnew.exe (PID: 6072)
- amnew.exe (PID: 7744)
- amnew.exe (PID: 2192)
- amnew.exe (PID: 7648)
- amnew.exe (PID: 3032)
- amnew.exe (PID: 3744)
- amnew.exe (PID: 3784)
- amnew.exe (PID: 4184)
- amnew.exe (PID: 3436)
- amnew.exe (PID: 644)
- amnew.exe (PID: 672)
- amnew.exe (PID: 1568)
- amnew.exe (PID: 7484)
- amnew.exe (PID: 5996)
- amnew.exe (PID: 2868)
- amnew.exe (PID: 7284)
- amnew.exe (PID: 1056)
- amnew.exe (PID: 1704)
- amnew.exe (PID: 2848)
- amnew.exe (PID: 7888)
- amnew.exe (PID: 1600)
- amnew.exe (PID: 5740)
- amnew.exe (PID: 5528)
- amnew.exe (PID: 6712)
- amnew.exe (PID: 704)
- amnew.exe (PID: 2140)
- amnew.exe (PID: 2192)
- amnew.exe (PID: 6048)
- amnew.exe (PID: 7892)
- amnew.exe (PID: 5364)
- amnew.exe (PID: 7460)
- amnew.exe (PID: 976)
- amnew.exe (PID: 2152)
- amnew.exe (PID: 4844)
- amnew.exe (PID: 7148)
- amnew.exe (PID: 5344)
- amnew.exe (PID: 7572)
- amnew.exe (PID: 2088)
- amnew.exe (PID: 7048)
- amnew.exe (PID: 7132)
- amnew.exe (PID: 3308)
- amnew.exe (PID: 5972)
- amnew.exe (PID: 8152)
- amnew.exe (PID: 736)
- amnew.exe (PID: 7188)
- amnew.exe (PID: 6324)
- amnew.exe (PID: 8172)
- amnew.exe (PID: 3248)
- amnew.exe (PID: 5480)
- amnew.exe (PID: 5600)
- amnew.exe (PID: 7816)
- amnew.exe (PID: 6028)
- amnew.exe (PID: 760)
- amnew.exe (PID: 7104)
- amnew.exe (PID: 1600)
- amnew.exe (PID: 6740)
- amnew.exe (PID: 4948)
- amnew.exe (PID: 6920)
- amnew.exe (PID: 2772)
- amnew.exe (PID: 1616)
- amnew.exe (PID: 4920)
- amnew.exe (PID: 5988)
- amnew.exe (PID: 6252)
- amnew.exe (PID: 2316)
- amnew.exe (PID: 1760)
- amnew.exe (PID: 6592)
- amnew.exe (PID: 4424)
- amnew.exe (PID: 6576)
- amnew.exe (PID: 3028)
- amnew.exe (PID: 744)
- amnew.exe (PID: 7284)
- amnew.exe (PID: 8116)
- amnew.exe (PID: 7820)
- amnew.exe (PID: 7588)
- amnew.exe (PID: 1196)
- amnew.exe (PID: 2980)
- amnew.exe (PID: 6032)
- amnew.exe (PID: 3748)
- amnew.exe (PID: 5156)
- amnew.exe (PID: 7504)
- amnew.exe (PID: 7744)
- amnew.exe (PID: 5364)
- amnew.exe (PID: 7712)
- amnew.exe (PID: 736)
- amnew.exe (PID: 7940)
- amnew.exe (PID: 1560)
- amnew.exe (PID: 516)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 7636)
- amnew.exe (PID: 7620)
- amnew.exe (PID: 1388)
- amnew.exe (PID: 7188)
- amnew.exe (PID: 3180)
- amnew.exe (PID: 6180)
- amnew.exe (PID: 4452)
- amnew.exe (PID: 7104)
- amnew.exe (PID: 3968)
- amnew.exe (PID: 7488)
- amnew.exe (PID: 5408)
- amnew.exe (PID: 6880)
- amnew.exe (PID: 7780)
- amnew.exe (PID: 3960)
- amnew.exe (PID: 7288)
- amnew.exe (PID: 4988)
- amnew.exe (PID: 6392)
- amnew.exe (PID: 3416)
- amnew.exe (PID: 2644)
- amnew.exe (PID: 8128)
- amnew.exe (PID: 1472)
- amnew.exe (PID: 7248)
- amnew.exe (PID: 6368)
- amnew.exe (PID: 6240)
- amnew.exe (PID: 1568)
- amnew.exe (PID: 3192)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 3160)
- amnew.exe (PID: 5588)
- amnew.exe (PID: 7692)
- amnew.exe (PID: 7376)
- amnew.exe (PID: 5740)
- amnew.exe (PID: 6464)
- amnew.exe (PID: 7324)
- amnew.exe (PID: 1696)
- amnew.exe (PID: 3264)
- amnew.exe (PID: 7036)
- amnew.exe (PID: 6032)
- amnew.exe (PID: 1660)
- amnew.exe (PID: 7832)
- amnew.exe (PID: 7744)
- amnew.exe (PID: 5988)
- amnew.exe (PID: 8168)
- amnew.exe (PID: 5164)
- amnew.exe (PID: 2800)
- amnew.exe (PID: 7488)
- amnew.exe (PID: 6028)
- amnew.exe (PID: 5624)
- amnew.exe (PID: 5936)
- amnew.exe (PID: 1228)
- amnew.exe (PID: 1324)
- amnew.exe (PID: 7156)
- amnew.exe (PID: 8072)
- amnew.exe (PID: 2644)
- amnew.exe (PID: 808)
- amnew.exe (PID: 7696)
- amnew.exe (PID: 1128)
- amnew.exe (PID: 632)
- amnew.exe (PID: 7728)
- amnew.exe (PID: 704)
- amnew.exe (PID: 660)
- amnew.exe (PID: 5736)
- amnew.exe (PID: 4896)
- amnew.exe (PID: 3272)
- amnew.exe (PID: 960)
- amnew.exe (PID: 7020)
- amnew.exe (PID: 4924)
- amnew.exe (PID: 2268)
- amnew.exe (PID: 2432)
- amnew.exe (PID: 6828)
- amnew.exe (PID: 2316)
- amnew.exe (PID: 2776)
- amnew.exe (PID: 3016)
- amnew.exe (PID: 7268)
- amnew.exe (PID: 4020)
- amnew.exe (PID: 3192)
- amnew.exe (PID: 2088)
- amnew.exe (PID: 3676)
- amnew.exe (PID: 7580)
- amnew.exe (PID: 5304)
- amnew.exe (PID: 1196)
- amnew.exe (PID: 6248)
- amnew.exe (PID: 4244)
- amnew.exe (PID: 5980)
- amnew.exe (PID: 3264)
- amnew.exe (PID: 4844)
- amnew.exe (PID: 7812)
- amnew.exe (PID: 7868)
- amnew.exe (PID: 1516)
- amnew.exe (PID: 6072)
- amnew.exe (PID: 4100)
- amnew.exe (PID: 4040)
- amnew.exe (PID: 7012)
- amnew.exe (PID: 7692)
- amnew.exe (PID: 5528)
- amnew.exe (PID: 6252)
- amnew.exe (PID: 3036)
- amnew.exe (PID: 7308)
- amnew.exe (PID: 448)
- amnew.exe (PID: 4188)
- amnew.exe (PID: 5624)
- amnew.exe (PID: 3180)
- amnew.exe (PID: 7156)
- amnew.exe (PID: 2392)
- amnew.exe (PID: 2644)
- amnew.exe (PID: 5776)
- amnew.exe (PID: 5480)
- amnew.exe (PID: 5484)
- amnew.exe (PID: 1704)
- amnew.exe (PID: 3828)
- amnew.exe (PID: 1228)
- amnew.exe (PID: 3884)
- amnew.exe (PID: 3960)
- amnew.exe (PID: 4184)
- amnew.exe (PID: 5772)
- amnew.exe (PID: 6816)
- amnew.exe (PID: 7284)
- amnew.exe (PID: 3160)
- amnew.exe (PID: 7628)
- amnew.exe (PID: 3016)
- amnew.exe (PID: 1276)
- amnew.exe (PID: 7220)
- amnew.exe (PID: 2596)
- amnew.exe (PID: 7340)
- amnew.exe (PID: 7288)
- amnew.exe (PID: 6180)
- amnew.exe (PID: 7684)
- amnew.exe (PID: 7956)
- amnew.exe (PID: 7172)
- amnew.exe (PID: 896)
- amnew.exe (PID: 6892)
- amnew.exe (PID: 1196)
- amnew.exe (PID: 7604)
- amnew.exe (PID: 3264)
- amnew.exe (PID: 5960)
- amnew.exe (PID: 8068)
- amnew.exe (PID: 7328)
- amnew.exe (PID: 7868)
- amnew.exe (PID: 5400)
- amnew.exe (PID: 4100)
- amnew.exe (PID: 2612)
- amnew.exe (PID: 1516)
- amnew.exe (PID: 7620)
- amnew.exe (PID: 3828)
- amnew.exe (PID: 5528)
- amnew.exe (PID: 8116)
- amnew.exe (PID: 2244)
- amnew.exe (PID: 5624)
- amnew.exe (PID: 5048)
- amnew.exe (PID: 5756)
- amnew.exe (PID: 2692)
- amnew.exe (PID: 8128)
- amnew.exe (PID: 2392)
- amnew.exe (PID: 7608)
- amnew.exe (PID: 6300)
- amnew.exe (PID: 6640)
- amnew.exe (PID: 3884)
- amnew.exe (PID: 872)
- amnew.exe (PID: 2108)
- amnew.exe (PID: 3708)
- amnew.exe (PID: 5936)
- amnew.exe (PID: 1244)
- amnew.exe (PID: 6880)
- amnew.exe (PID: 7612)
- amnew.exe (PID: 5588)
- amnew.exe (PID: 3140)
- amnew.exe (PID: 7012)
- amnew.exe (PID: 3996)
- amnew.exe (PID: 7808)
- amnew.exe (PID: 8116)
- amnew.exe (PID: 7376)
- amnew.exe (PID: 2852)
- amnew.exe (PID: 7200)
- amnew.exe (PID: 4184)
- amnew.exe (PID: 3796)
- amnew.exe (PID: 8152)
- amnew.exe (PID: 908)
- amnew.exe (PID: 1184)
- amnew.exe (PID: 472)
- amnew.exe (PID: 7292)
- amnew.exe (PID: 5072)
- amnew.exe (PID: 7812)
- amnew.exe (PID: 2772)
- amnew.exe (PID: 2092)
- amnew.exe (PID: 7940)
- amnew.exe (PID: 672)
- amnew.exe (PID: 5600)
- amnew.exe (PID: 6744)
- amnew.exe (PID: 7248)
- amnew.exe (PID: 8176)
- amnew.exe (PID: 2612)
- amnew.exe (PID: 7596)
- amnew.exe (PID: 1324)
- amnew.exe (PID: 7924)
- amnew.exe (PID: 1696)
- amnew.exe (PID: 7324)
- amnew.exe (PID: 7552)
- amnew.exe (PID: 5868)
- amnew.exe (PID: 3804)
- amnew.exe (PID: 4924)
- amnew.exe (PID: 6028)
- amnew.exe (PID: 7708)
- amnew.exe (PID: 5776)
- amnew.exe (PID: 4188)
- amnew.exe (PID: 3248)
- amnew.exe (PID: 8180)
- amnew.exe (PID: 3884)
- amnew.exe (PID: 7580)
- amnew.exe (PID: 7756)
- amnew.exe (PID: 2524)
- amnew.exe (PID: 6988)
- amnew.exe (PID: 4732)
- amnew.exe (PID: 7988)
- amnew.exe (PID: 8152)
- amnew.exe (PID: 5552)
- amnew.exe (PID: 2776)
- amnew.exe (PID: 4452)
- amnew.exe (PID: 6584)
- amnew.exe (PID: 8168)
- amnew.exe (PID: 3276)
- amnew.exe (PID: 7508)
- amnew.exe (PID: 512)
- amnew.exe (PID: 2660)
- amnew.exe (PID: 7376)
- amnew.exe (PID: 5592)
- amnew.exe (PID: 6392)
- amnew.exe (PID: 7264)
- amnew.exe (PID: 4700)
- amnew.exe (PID: 4020)
- amnew.exe (PID: 1676)
- amnew.exe (PID: 5248)
- amnew.exe (PID: 7272)
- amnew.exe (PID: 3992)
- amnew.exe (PID: 4844)
- amnew.exe (PID: 2152)
- amnew.exe (PID: 3264)
- amnew.exe (PID: 1348)
- amnew.exe (PID: 5980)
- amnew.exe (PID: 8032)
- amnew.exe (PID: 6156)
- amnew.exe (PID: 2980)
- amnew.exe (PID: 4100)
- amnew.exe (PID: 3748)
- amnew.exe (PID: 4628)
- amnew.exe (PID: 7256)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 1660)
- amnew.exe (PID: 7184)
- amnew.exe (PID: 1228)
- amnew.exe (PID: 5048)
- amnew.exe (PID: 2692)
- amnew.exe (PID: 6880)
- amnew.exe (PID: 3396)
- amnew.exe (PID: 8144)
- amnew.exe (PID: 3436)
- amnew.exe (PID: 8076)
- amnew.exe (PID: 7188)
- amnew.exe (PID: 7752)
- amnew.exe (PID: 872)
- amnew.exe (PID: 716)
- amnew.exe (PID: 5216)
- amnew.exe (PID: 4028)
- amnew.exe (PID: 7284)
- amnew.exe (PID: 5008)
- amnew.exe (PID: 6040)
- amnew.exe (PID: 1244)
- amnew.exe (PID: 4920)
- amnew.exe (PID: 5984)
- amnew.exe (PID: 8064)
- amnew.exe (PID: 8148)
- amnew.exe (PID: 7104)
- amnew.exe (PID: 4728)
- amnew.exe (PID: 6456)
- amnew.exe (PID: 1760)
- amnew.exe (PID: 7456)
- amnew.exe (PID: 1812)
- amnew.exe (PID: 7792)
- amnew.exe (PID: 7820)
- amnew.exe (PID: 6344)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 3416)
- amnew.exe (PID: 3968)
- amnew.exe (PID: 4932)
- amnew.exe (PID: 5624)
- amnew.exe (PID: 4272)
- amnew.exe (PID: 1348)
- amnew.exe (PID: 3164)
- amnew.exe (PID: 7640)
- amnew.exe (PID: 7248)
- amnew.exe (PID: 6156)
- amnew.exe (PID: 1128)
- amnew.exe (PID: 7008)
- amnew.exe (PID: 3008)
- amnew.exe (PID: 6892)
- amnew.exe (PID: 208)
- amnew.exe (PID: 5096)
- amnew.exe (PID: 6044)
- amnew.exe (PID: 3876)
- amnew.exe (PID: 6240)
- amnew.exe (PID: 7636)
- amnew.exe (PID: 6340)
- amnew.exe (PID: 7968)
- amnew.exe (PID: 5556)
- amnew.exe (PID: 7348)
- amnew.exe (PID: 856)
- amnew.exe (PID: 4380)
- amnew.exe (PID: 1152)
- amnew.exe (PID: 7084)
- amnew.exe (PID: 1240)
- amnew.exe (PID: 2812)
- amnew.exe (PID: 2852)
- amnew.exe (PID: 5744)
- amnew.exe (PID: 7648)
- amnew.exe (PID: 6988)
- amnew.exe (PID: 5048)
- amnew.exe (PID: 1228)
- amnew.exe (PID: 808)
- amnew.exe (PID: 5892)
- amnew.exe (PID: 1176)
- amnew.exe (PID: 7268)
- amnew.exe (PID: 8148)
- amnew.exe (PID: 5740)
- amnew.exe (PID: 7012)
- amnew.exe (PID: 7628)
- amnew.exe (PID: 4892)
- amnew.exe (PID: 908)
- amnew.exe (PID: 5596)
- amnew.exe (PID: 3784)
- amnew.exe (PID: 5132)
- amnew.exe (PID: 6168)
- amnew.exe (PID: 6744)
- amnew.exe (PID: 7900)
- amnew.exe (PID: 4932)
- amnew.exe (PID: 7456)
- amnew.exe (PID: 7928)
- amnew.exe (PID: 2660)
- amnew.exe (PID: 7820)
- amnew.exe (PID: 1268)
- amnew.exe (PID: 8028)
- amnew.exe (PID: 5024)
- amnew.exe (PID: 1852)
- amnew.exe (PID: 672)
- amnew.exe (PID: 5960)
- amnew.exe (PID: 3008)
- amnew.exe (PID: 7712)
- amnew.exe (PID: 2192)
- amnew.exe (PID: 7728)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 3096)
- amnew.exe (PID: 1348)
- amnew.exe (PID: 2980)
- amnew.exe (PID: 7608)
- amnew.exe (PID: 1240)
- amnew.exe (PID: 7084)
- amnew.exe (PID: 5484)
- amnew.exe (PID: 7156)
- amnew.exe (PID: 3396)
- amnew.exe (PID: 4924)
- amnew.exe (PID: 7008)
- amnew.exe (PID: 4220)
- amnew.exe (PID: 1560)
- amnew.exe (PID: 6048)
- amnew.exe (PID: 7988)
- amnew.exe (PID: 7188)
- amnew.exe (PID: 6880)
- amnew.exe (PID: 6240)
- amnew.exe (PID: 1064)
- amnew.exe (PID: 7908)
- amnew.exe (PID: 2780)
- amnew.exe (PID: 4020)
- amnew.exe (PID: 4940)
- amnew.exe (PID: 6592)
- amnew.exe (PID: 3968)
- amnew.exe (PID: 5740)
- amnew.exe (PID: 7628)
- amnew.exe (PID: 3028)
- amnew.exe (PID: 776)
- amnew.exe (PID: 2852)
- amnew.exe (PID: 3032)
- amnew.exe (PID: 5956)
- amnew.exe (PID: 7020)
- amnew.exe (PID: 4892)
- amnew.exe (PID: 6656)
- amnew.exe (PID: 1696)
- amnew.exe (PID: 1852)
- amnew.exe (PID: 3876)
- amnew.exe (PID: 3308)
- amnew.exe (PID: 5400)
- amnew.exe (PID: 7328)
- amnew.exe (PID: 7148)
- amnew.exe (PID: 4272)
- amnew.exe (PID: 6324)
- amnew.exe (PID: 3996)
- amnew.exe (PID: 4728)
- amnew.exe (PID: 1660)
- amnew.exe (PID: 7172)
- amnew.exe (PID: 6344)
- amnew.exe (PID: 5156)
- amnew.exe (PID: 472)
- amnew.exe (PID: 7432)
- amnew.exe (PID: 7712)
- amnew.exe (PID: 5608)
- amnew.exe (PID: 8100)
- amnew.exe (PID: 3396)
- amnew.exe (PID: 2140)
- amnew.exe (PID: 7696)
- amnew.exe (PID: 7188)
- amnew.exe (PID: 2600)
- amnew.exe (PID: 1704)
- amnew.exe (PID: 7968)
- amnew.exe (PID: 7716)
- amnew.exe (PID: 716)
- amnew.exe (PID: 6240)
- amnew.exe (PID: 5988)
- amnew.exe (PID: 3124)
- amnew.exe (PID: 1516)
- amnew.exe (PID: 6988)
- amnew.exe (PID: 2104)
- amnew.exe (PID: 1276)
- amnew.exe (PID: 6132)
- amnew.exe (PID: 5552)
- amnew.exe (PID: 1176)
- amnew.exe (PID: 724)
- amnew.exe (PID: 4948)
- amnew.exe (PID: 960)
- amnew.exe (PID: 7892)
- amnew.exe (PID: 8064)
- amnew.exe (PID: 1616)
- amnew.exe (PID: 3080)
- amnew.exe (PID: 6456)
- amnew.exe (PID: 8116)
- amnew.exe (PID: 3028)
- amnew.exe (PID: 7808)
- amnew.exe (PID: 1496)
- amnew.exe (PID: 4068)
- amnew.exe (PID: 6840)
- amnew.exe (PID: 7704)
- amnew.exe (PID: 7260)
- amnew.exe (PID: 7464)
- amnew.exe (PID: 7476)
- amnew.exe (PID: 2244)
- amnew.exe (PID: 1052)
- amnew.exe (PID: 7900)
- amnew.exe (PID: 5736)
- amnew.exe (PID: 6744)
- amnew.exe (PID: 5600)
- amnew.exe (PID: 6324)
- amnew.exe (PID: 2092)
- amnew.exe (PID: 2524)
- amnew.exe (PID: 7688)
- amnew.exe (PID: 3744)
- amnew.exe (PID: 472)
- amnew.exe (PID: 4728)
- amnew.exe (PID: 7188)
- amnew.exe (PID: 6268)
- amnew.exe (PID: 7988)
- amnew.exe (PID: 3884)
- amnew.exe (PID: 4380)
- amnew.exe (PID: 6300)
- amnew.exe (PID: 5640)
- amnew.exe (PID: 7716)
- amnew.exe (PID: 5972)
- amnew.exe (PID: 2028)
- amnew.exe (PID: 7420)
- amnew.exe (PID: 4336)
- amnew.exe (PID: 2800)
- amnew.exe (PID: 516)
- amnew.exe (PID: 7728)
- amnew.exe (PID: 6216)
- amnew.exe (PID: 7960)
- amnew.exe (PID: 7580)
- amnew.exe (PID: 7020)
- amnew.exe (PID: 4948)
- amnew.exe (PID: 3012)
- amnew.exe (PID: 7312)
- amnew.exe (PID: 1676)
- amnew.exe (PID: 7724)
- amnew.exe (PID: 6456)
- amnew.exe (PID: 3080)
- amnew.exe (PID: 7104)
- amnew.exe (PID: 2664)
- amnew.exe (PID: 4068)
- amnew.exe (PID: 900)
- amnew.exe (PID: 5408)
- amnew.exe (PID: 7588)
- amnew.exe (PID: 4452)
- amnew.exe (PID: 5072)
- amnew.exe (PID: 7928)
- amnew.exe (PID: 7260)
- amnew.exe (PID: 7940)
- amnew.exe (PID: 512)
- amnew.exe (PID: 6656)
- amnew.exe (PID: 7496)
- amnew.exe (PID: 6156)
- amnew.exe (PID: 8108)
- amnew.exe (PID: 1312)
- amnew.exe (PID: 3096)
- amnew.exe (PID: 4244)
- amnew.exe (PID: 7824)
- amnew.exe (PID: 7572)
- amnew.exe (PID: 6668)
- amnew.exe (PID: 6632)
- amnew.exe (PID: 516)
- amnew.exe (PID: 7308)
- amnew.exe (PID: 5608)
- amnew.exe (PID: 7832)
- amnew.exe (PID: 760)
- amnew.exe (PID: 7988)
- amnew.exe (PID: 5556)
- amnew.exe (PID: 7648)
- amnew.exe (PID: 872)
- amnew.exe (PID: 856)
- amnew.exe (PID: 7348)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 8032)
- amnew.exe (PID: 3872)
- amnew.exe (PID: 6324)
- amnew.exe (PID: 1136)
- amnew.exe (PID: 2840)
- amnew.exe (PID: 2812)
- amnew.exe (PID: 8020)
- amnew.exe (PID: 744)
- amnew.exe (PID: 7584)
- amnew.exe (PID: 900)
- amnew.exe (PID: 5744)
- amnew.exe (PID: 6816)
- amnew.exe (PID: 4724)
- amnew.exe (PID: 7020)
- amnew.exe (PID: 3968)
- amnew.exe (PID: 1056)
- amnew.exe (PID: 6240)
- amnew.exe (PID: 1504)
- amnew.exe (PID: 4352)
- amnew.exe (PID: 2028)
- amnew.exe (PID: 5480)
- amnew.exe (PID: 6740)
- amnew.exe (PID: 7624)
- amnew.exe (PID: 5024)
- amnew.exe (PID: 4728)
- amnew.exe (PID: 7984)
- amnew.exe (PID: 832)
- amnew.exe (PID: 1812)
- amnew.exe (PID: 672)
- amnew.exe (PID: 4212)
- amnew.exe (PID: 4652)
- amnew.exe (PID: 3164)
- amnew.exe (PID: 8176)
- amnew.exe (PID: 7432)
- amnew.exe (PID: 4184)
- amnew.exe (PID: 5592)
- amnew.exe (PID: 7320)
- amnew.exe (PID: 5380)
- amnew.exe (PID: 6272)
- amnew.exe (PID: 1516)
- amnew.exe (PID: 704)
- amnew.exe (PID: 5304)
- amnew.exe (PID: 8012)
- amnew.exe (PID: 7184)
- amnew.exe (PID: 7008)
- amnew.exe (PID: 7448)
- amnew.exe (PID: 5936)
- amnew.exe (PID: 3488)
- amnew.exe (PID: 1472)
- amnew.exe (PID: 1228)
- amnew.exe (PID: 7832)
- amnew.exe (PID: 7888)
- amnew.exe (PID: 2656)
- amnew.exe (PID: 300)
- amnew.exe (PID: 3308)
- amnew.exe (PID: 6416)
- amnew.exe (PID: 780)
- amnew.exe (PID: 3800)
- amnew.exe (PID: 6828)
- amnew.exe (PID: 7620)
- amnew.exe (PID: 1168)
- amnew.exe (PID: 5868)
- amnew.exe (PID: 4352)
- amnew.exe (PID: 5480)
- amnew.exe (PID: 7776)
- amnew.exe (PID: 8020)
- amnew.exe (PID: 6908)
- amnew.exe (PID: 5180)
- amnew.exe (PID: 6068)
- amnew.exe (PID: 7736)
- amnew.exe (PID: 7608)
- amnew.exe (PID: 5124)
- amnew.exe (PID: 6472)
- amnew.exe (PID: 3248)
- amnew.exe (PID: 6612)
- amnew.exe (PID: 2216)
- amnew.exe (PID: 1660)
- amnew.exe (PID: 2776)
- amnew.exe (PID: 6740)
- amnew.exe (PID: 3996)
- amnew.exe (PID: 7924)
- amnew.exe (PID: 7720)
- amnew.exe (PID: 5024)
- amnew.exe (PID: 4732)
- amnew.exe (PID: 4448)
- amnew.exe (PID: 7476)
- amnew.exe (PID: 512)
- amnew.exe (PID: 6168)
- amnew.exe (PID: 3768)
- amnew.exe (PID: 6192)
- amnew.exe (PID: 7612)
- amnew.exe (PID: 7892)
- amnew.exe (PID: 5596)
- amnew.exe (PID: 2612)
- amnew.exe (PID: 7296)
- amnew.exe (PID: 1388)
- amnew.exe (PID: 2092)
- amnew.exe (PID: 5452)
- amnew.exe (PID: 5936)
- amnew.exe (PID: 7944)
- amnew.exe (PID: 808)
- amnew.exe (PID: 7832)
- amnew.exe (PID: 736)
- amnew.exe (PID: 3828)
- amnew.exe (PID: 7908)
- amnew.exe (PID: 2656)
- amnew.exe (PID: 1300)
- amnew.exe (PID: 8100)
- amnew.exe (PID: 5720)
- amnew.exe (PID: 3904)
- amnew.exe (PID: 1072)
- amnew.exe (PID: 2812)
- amnew.exe (PID: 8020)
- amnew.exe (PID: 7468)
- amnew.exe (PID: 6472)
- amnew.exe (PID: 7200)
- amnew.exe (PID: 6828)
- amnew.exe (PID: 744)
- amnew.exe (PID: 6180)
- amnew.exe (PID: 7580)
- amnew.exe (PID: 4736)
- amnew.exe (PID: 1760)
- amnew.exe (PID: 856)
- amnew.exe (PID: 2600)
- amnew.exe (PID: 7084)
- amnew.exe (PID: 1696)
- amnew.exe (PID: 7012)
- amnew.exe (PID: 7508)
- amnew.exe (PID: 7892)
- amnew.exe (PID: 3012)
- amnew.exe (PID: 5380)
- amnew.exe (PID: 1496)
- amnew.exe (PID: 6916)
- amnew.exe (PID: 6248)
- amnew.exe (PID: 2368)
The sample compiled with english language support
- saren.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
1 255
Monitored processes
1 120
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 300 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 300 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 448 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 512 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 512 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
40 576
Read events
40 417
Write events
153
Delete events
6
Modification events
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 469BF1C60D952F00 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FCC5F8C60D952F00 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1245918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {350D7555-4D08-4AA7-B5C1-B5200D1EF1C0} | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E36524C70D952F00 | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (4224) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1245918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {71C0A40D-56A3-4A5B-B049-B7A0B85089F3} | |||
Executable files
23
Suspicious files
431
Text files
70
Unknown types
3
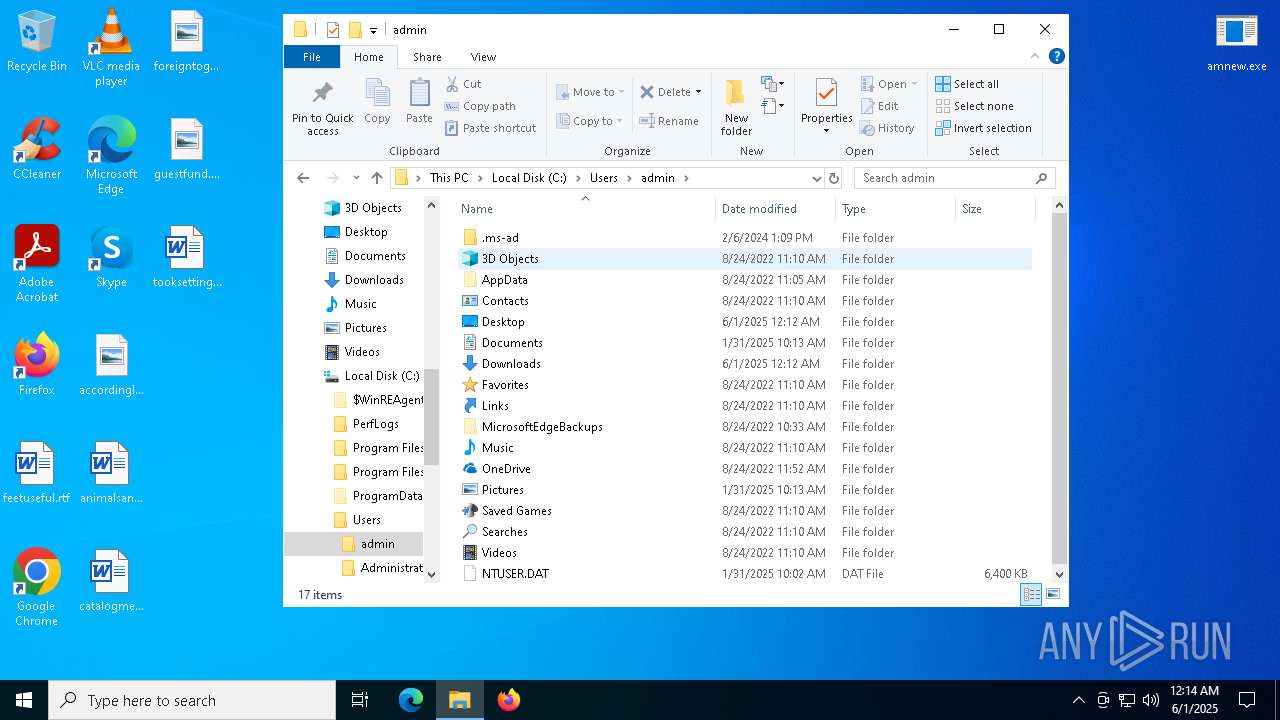
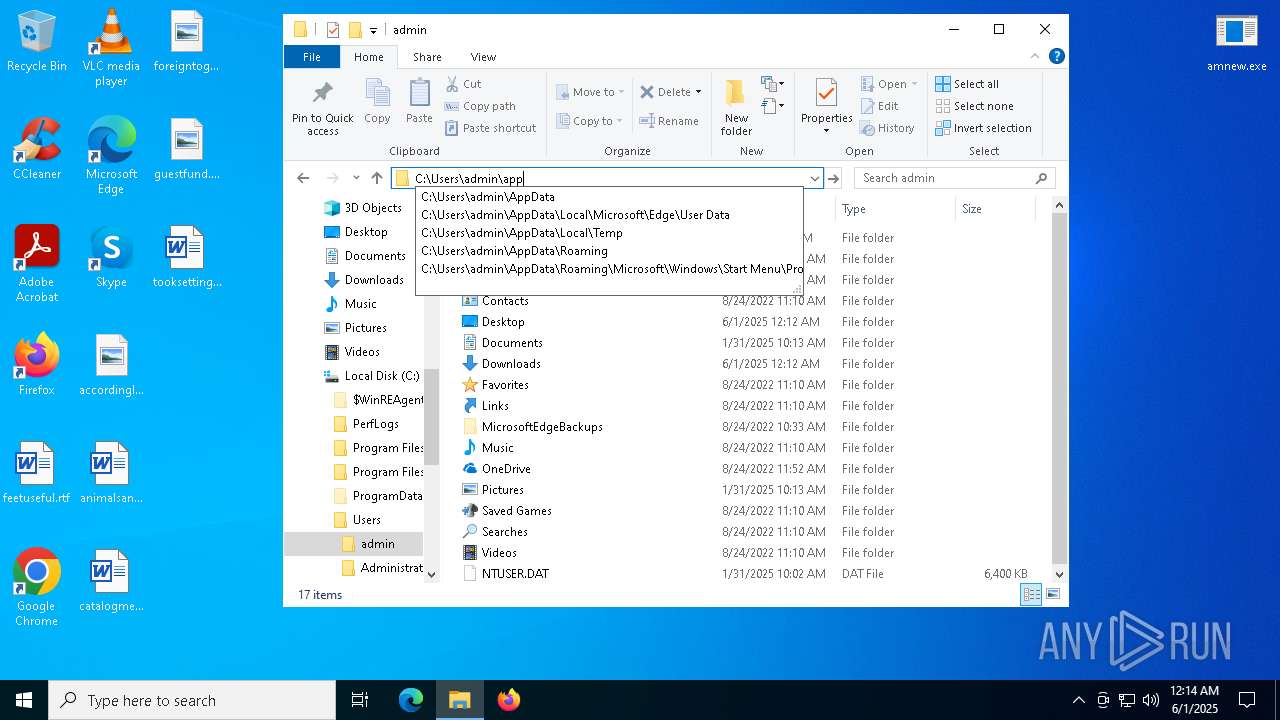
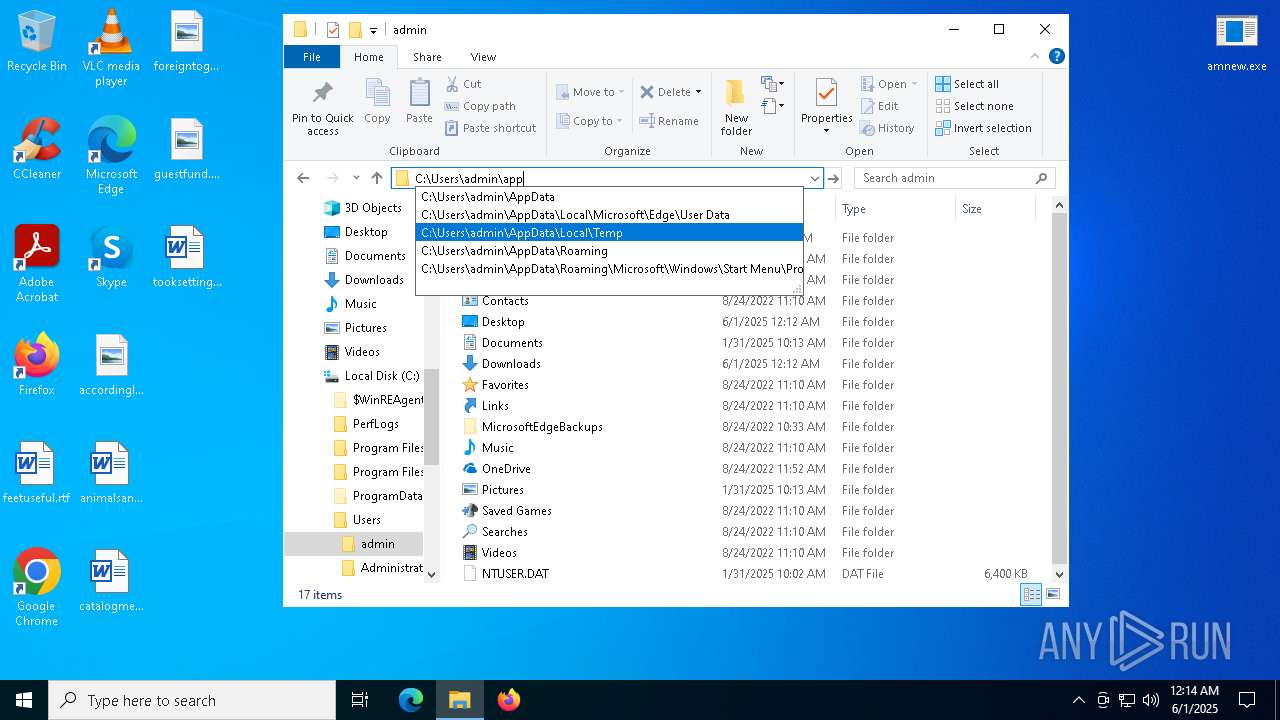
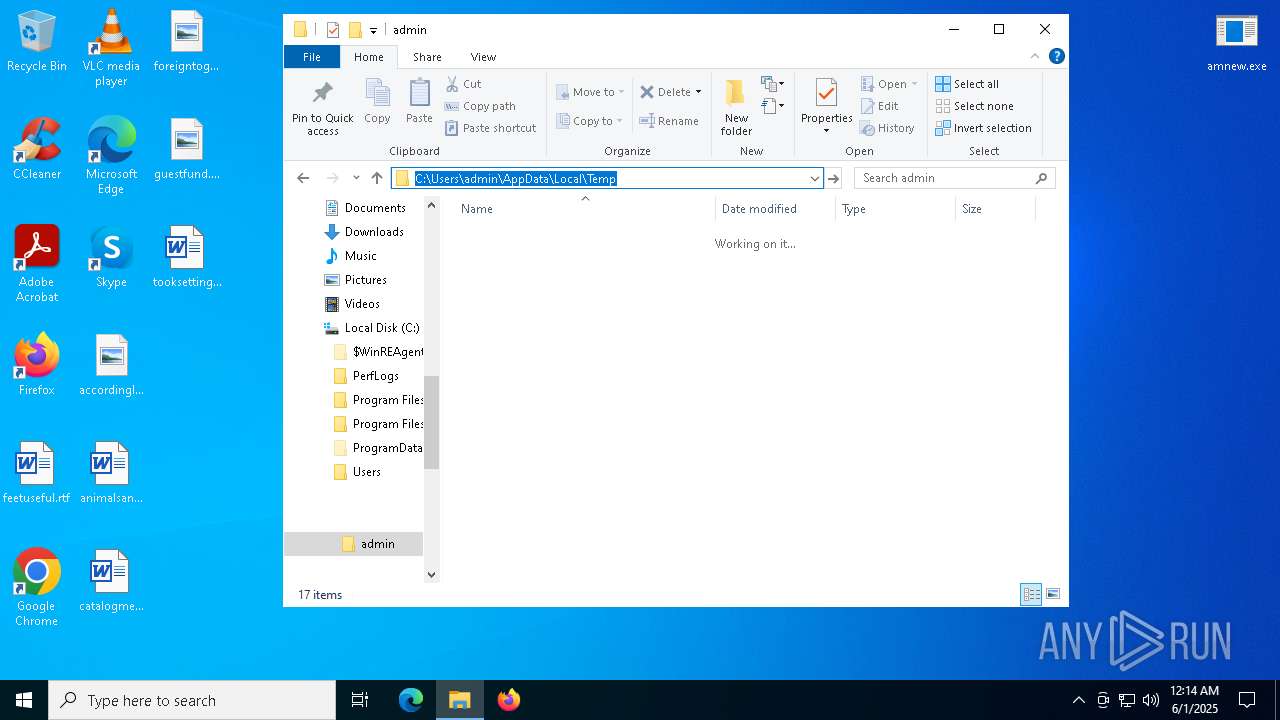
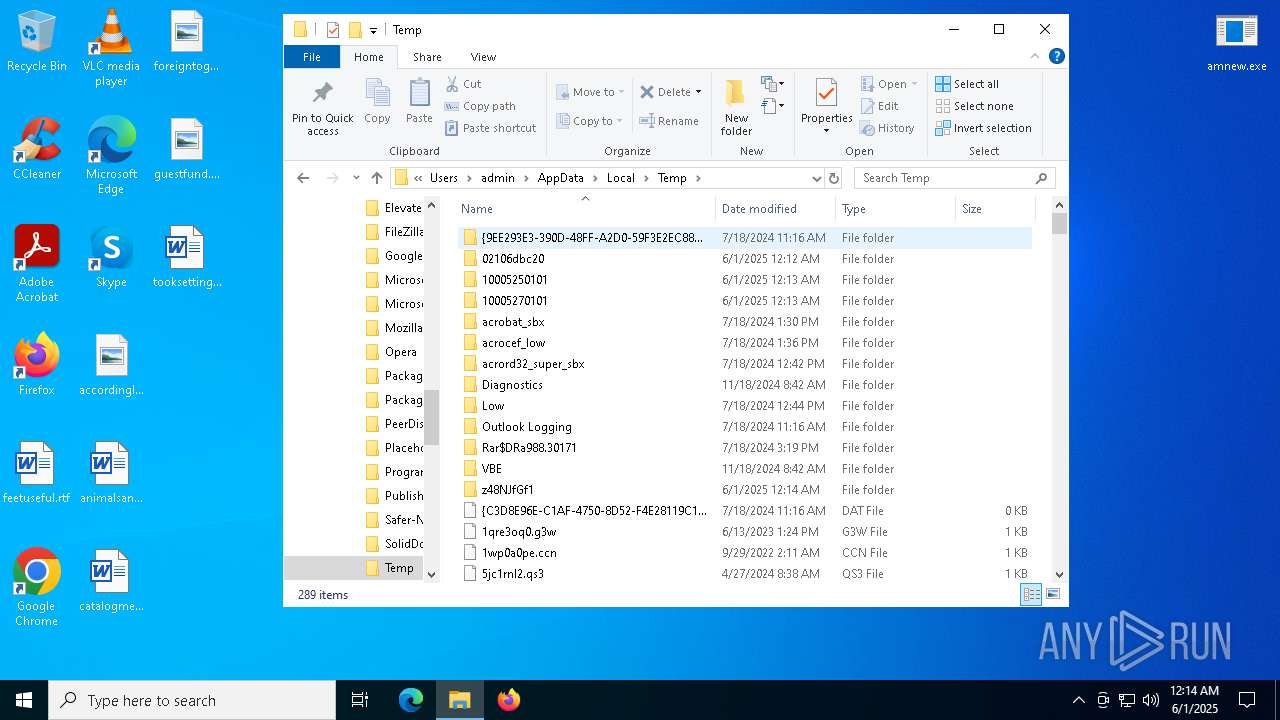
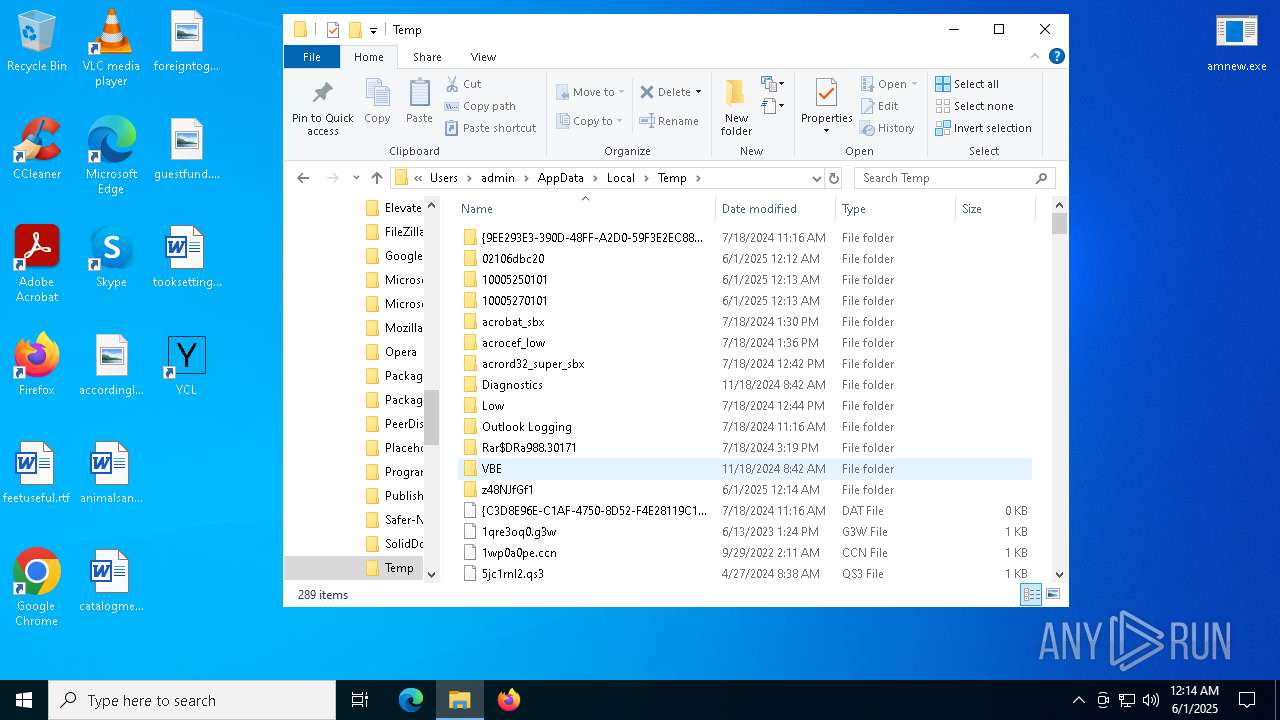
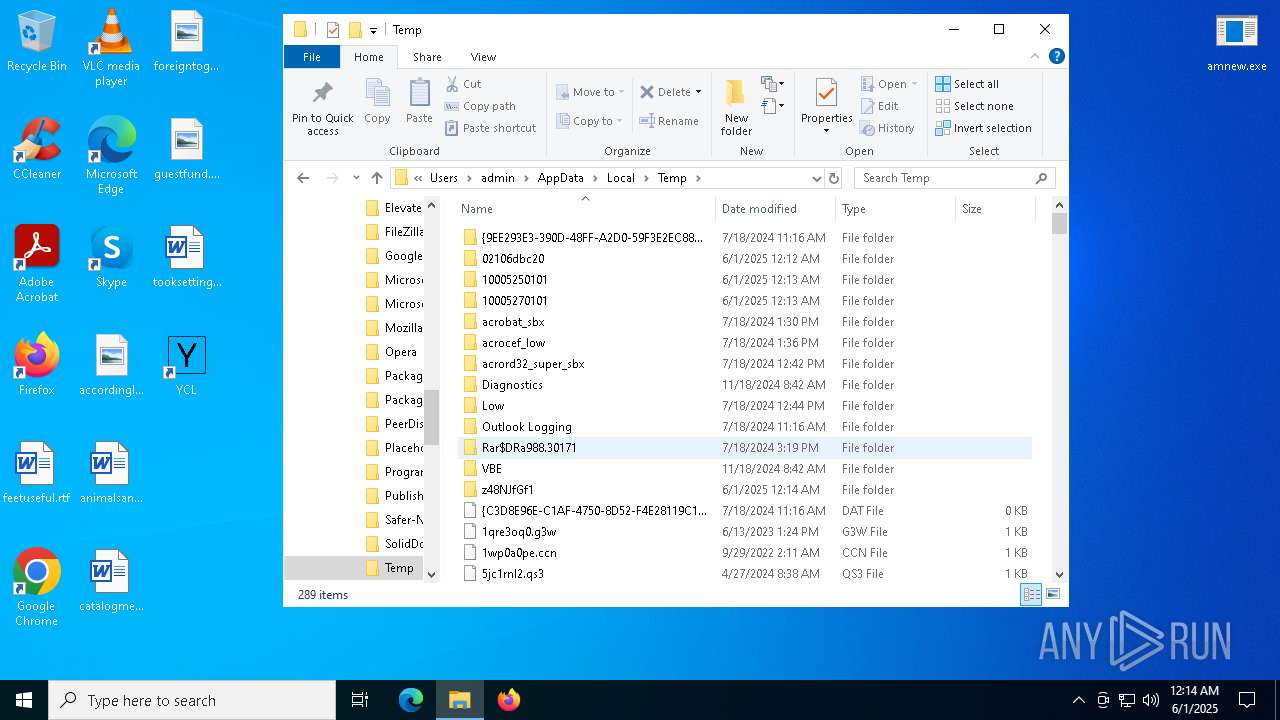
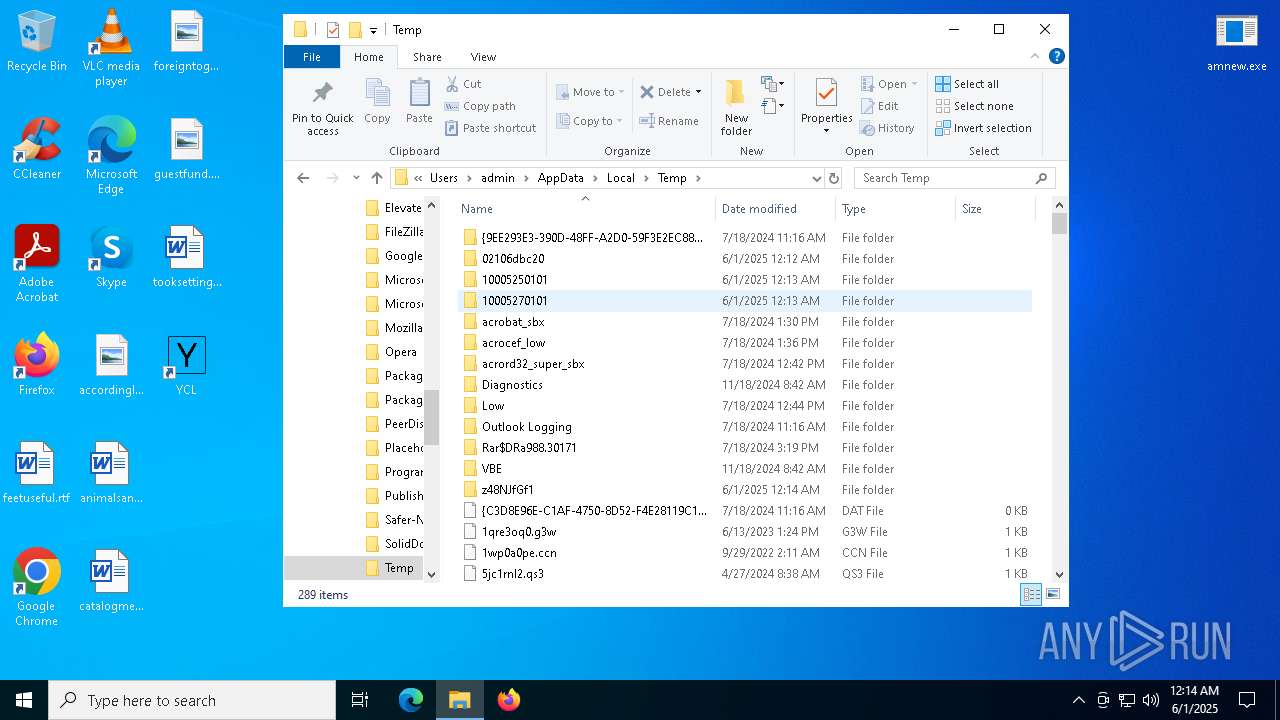
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f411.TMP | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f431.TMP | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f431.TMP | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11f440.TMP | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f440.TMP | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4224 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f440.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
188
DNS requests
209
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3968 | msedge.exe | GET | 200 | 77.83.207.69:80 | http://77.83.207.69/test/amnew.exe | unknown | — | — | malicious |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5988 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3896 | saren.exe | POST | 200 | 77.83.207.69:80 | http://77.83.207.69/rob75u9v/index.php | unknown | — | — | malicious |
5988 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8136 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748975268&P2=404&P3=2&P4=UojifVhHi6vXWyjVbOU1vx6DxN19CjBAXHnGcbsNdkN6Cwznqtopkt235zY%2fpC0%2fPzh6LjpeXSd7N5%2fI5gW%2bHg%3d%3d | unknown | — | — | whitelisted |
3896 | saren.exe | GET | 200 | 77.83.207.69:80 | http://77.83.207.69/inc/build111.exe | unknown | — | — | malicious |
8136 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748975268&P2=404&P3=2&P4=UojifVhHi6vXWyjVbOU1vx6DxN19CjBAXHnGcbsNdkN6Cwznqtopkt235zY%2fpC0%2fPzh6LjpeXSd7N5%2fI5gW%2bHg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4224 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3968 | msedge.exe | 77.83.207.69:80 | — | Internet Technologies LLC | UA | malicious |
3968 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3968 | msedge.exe | 77.83.207.69:443 | — | Internet Technologies LLC | UA | malicious |
3968 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3968 | msedge.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
3968 | msedge.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
3968 | msedge.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
3968 | msedge.exe | Misc activity | ET INFO Packed Executable Download |
6060 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
6060 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
3896 | saren.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
3896 | saren.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
3896 | saren.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
3896 | saren.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |