| File name: | saml.exe.0ae0_00021000.exe.00_00021000.exe |
| Full analysis: | https://app.any.run/tasks/5574b221-c8bf-4989-a557-f807eebbbbac |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | April 01, 2023, 16:38:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EB8EF174447C940754AD6B15184ED02D |
| SHA1: | 27700155DE246C99CEF9B3C8AEFF8905F693B5B2 |
| SHA256: | CF7C08445C3F52912C7713387351DDEC98B9D3F1985F0FC900EBAE70AF505E4E |
| SSDEEP: | 3072:K7W9jps0Tx4azG6GweOTir5axbjNCz45LT7a:KwpsERzGKurEXCzeLT7a |
MALICIOUS
Create files in the Startup directory
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
The process bypass UAC
- Dism.exe (PID: 3028)
- Dism.exe (PID: 2400)
Avemaria is detected
- images.exe (PID: 3068)
Application was injected by another process
- explorer.exe (PID: 1160)
Runs injected code in another process
- images.exe (PID: 3068)
- images.exe (PID: 2996)
Adds path to the Windows Defender exclusion list
- images.exe (PID: 2996)
WARZONE detected by memory dumps
- images.exe (PID: 2996)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
Executable content was dropped or overwritten
- dllhost.exe (PID: 3912)
- cmd.exe (PID: 3480)
- cmd.exe (PID: 3196)
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
Reads the Internet Settings
- cmd.exe (PID: 3196)
- cmd.exe (PID: 3480)
- powershell.exe (PID: 3332)
Starts CMD.EXE for commands execution
- images.exe (PID: 3068)
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
Starts POWERSHELL.EXE for commands execution
- images.exe (PID: 2996)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3332)
Connects to unusual port
- images.exe (PID: 3068)
- images.exe (PID: 2996)
Starts itself from another location
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
INFO
Reads the computer name
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
- images.exe (PID: 3068)
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2936)
- wmpnscfg.exe (PID: 1468)
- images.exe (PID: 2996)
- images.exe (PID: 2884)
- images.exe (PID: 2908)
The process checks LSA protection
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
- images.exe (PID: 3068)
- cmd.exe (PID: 3196)
- dllhost.exe (PID: 3912)
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2936)
- cmd.exe (PID: 3480)
- powershell.exe (PID: 3332)
- images.exe (PID: 2996)
- wmpnscfg.exe (PID: 1468)
- images.exe (PID: 2884)
- images.exe (PID: 2908)
Checks supported languages
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
- images.exe (PID: 3068)
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2936)
- images.exe (PID: 2996)
- wmpnscfg.exe (PID: 1468)
- images.exe (PID: 2884)
- images.exe (PID: 2908)
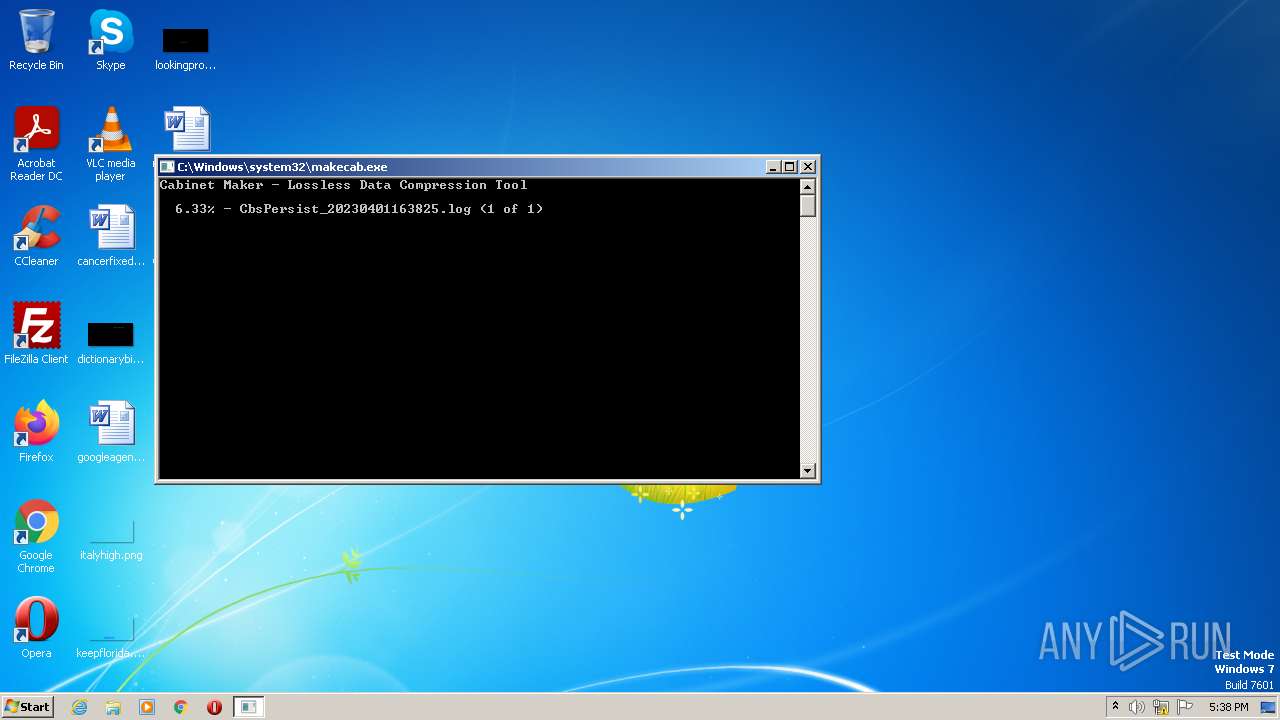
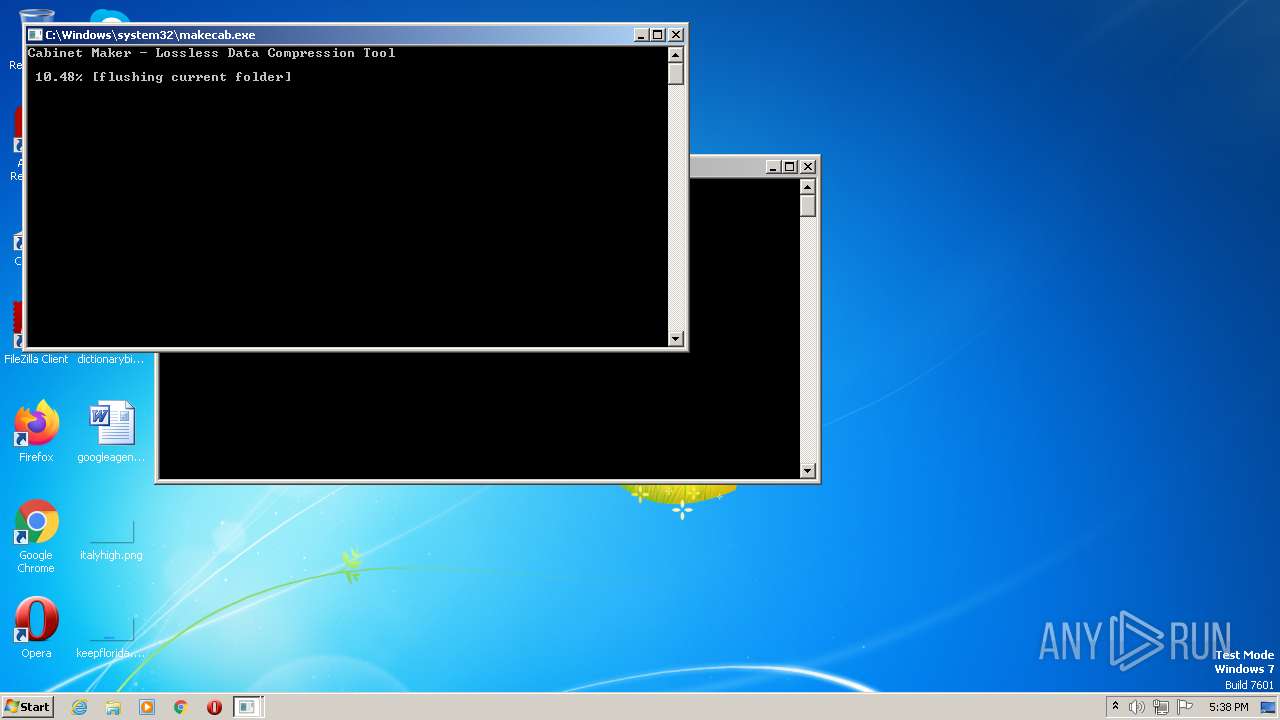
Create files in a temporary directory
- cmd.exe (PID: 3196)
- makecab.exe (PID: 3036)
- cmd.exe (PID: 3480)
- powershell.exe (PID: 3332)
- makecab.exe (PID: 1592)
Checks transactions between databases Windows and Oracle
- cmd.exe (PID: 3196)
- cmd.exe (PID: 3480)
Creates files in the program directory
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2936)
Reads settings of System Certificates
- powershell.exe (PID: 3332)
Manual execution by a user
- wmpnscfg.exe (PID: 1468)
- images.exe (PID: 2884)
- images.exe (PID: 2908)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3332)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1468)
Creates files or folders in the user directory
- saml.exe.0ae0_00021000.exe.00_00021000.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x6da4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1303552 |
| CodeSize: | 94720 |
| LinkerVersion: | 14.31 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:07:21 07:34:06+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jul-2022 07:34:06 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 21-Jul-2022 07:34:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001718E | 0x00017200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53879 |
.rdata | 0x00019000 | 0x00004F9A | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25324 |
.data | 0x0001E000 | 0x00135108 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98102 |
.rsrc | 0x00154000 | 0x00002C70 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.95827 |
.reloc | 0x00157000 | 0x000012C4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60071 |
.bss | 0x00159000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.26705 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
102 | 4.08279 | 11264 | UNKNOWN | UNKNOWN | WM_DSP |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
WS2_32.dll |
Total processes
63
Monitored processes
20
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\System32\PkgMgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1160 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "C:\Windows\system32\makecab.exe" C:\Windows\Logs\CBS\CbsPersist_20230401163825.log C:\Windows\Logs\CBS\CbsPersist_20230401163825.cab | C:\Windows\System32\makecab.exe | — | PkgMgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\System32\PkgMgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2400 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\System32\Dism.exe | — | PkgMgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\System32\PkgMgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\saml.exe.0ae0_00021000.exe.00_00021000.exe" | C:\Users\admin\AppData\Local\Temp\saml.exe.0ae0_00021000.exe.00_00021000.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2804 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\System32\PkgMgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2884 | "C:\Users\admin\Documents\images.exe" | C:\Users\admin\Documents\images.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
13 686
Read events
13 568
Write events
112
Delete events
6
Modification events
| (PID) Process: | (1160) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000008DAEBB14DAA9454A8FA3FE6EA57884410000000002000000000010660000000100002000000037A62E18291936BDF3FBEBDB1A0A05433342B6D9B290AD8CEABF12D32448C0A3000000000E8000000002000020000000954DA1B1A7562B56EDBF87C28062B3DE9D7587FA69240B989521EB0518F99C1A300000006CD6BD155F8CDB4C0E45BFE953EF2BF0801B46B7D553C27BE936C4785D282BDBD43D51783B2CA2538599ECDC56538EB2400000004DFEC9A0500C0A71F40F35A49D6AB58C3FEB6D2765EA33FC427EB7A0644A0631763C4C5CF68E8CAF056ED3981A508CD14B8DAC98FB242636B8582A19122ABBE1 | |||
| (PID) Process: | (3196) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3196) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3196) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3196) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3068) images.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3068) images.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (3068) images.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\AppData\Local\Temp\saml.exe.0ae0_00021000.exe.00_00021000.exe | |||
| (PID) Process: | (3480) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3480) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
10
Suspicious files
26
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | PkgMgr.exe | C:\Windows\Logs\CBS\CbsPersist_20230401163825.log | — | |
MD5:— | SHA256:— | |||
| 2660 | PkgMgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 2668 | saml.exe.0ae0_00021000.exe.00_00021000.exe | C:\Users\admin\Documents\images.exe | executable | |
MD5:EB8EF174447C940754AD6B15184ED02D | SHA256:CF7C08445C3F52912C7713387351DDEC98B9D3F1985F0FC900EBAE70AF505E4E | |||
| 3196 | cmd.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 2668 | saml.exe.0ae0_00021000.exe.00_00021000.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\programs.bat | text | |
MD5:08723FDD18DA4274C4B0A3D71EA6BF20 | SHA256:27BE5CFBAAB7E724BCBB0703A72DD6B7397EF6E03139C349872D78C0ADAD3EF0 | |||
| 3912 | dllhost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 3480 | cmd.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 3036 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3036_5 | binary | |
MD5:— | SHA256:— | |||
| 1592 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_1592_3 | binary | |
MD5:— | SHA256:— | |||
| 3036 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3036_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3068 | images.exe | 18.228.115.60:20934 | 1.tcp.sa.ngrok.io | AMAZON-02 | BR | malicious |
2996 | images.exe | 18.228.115.60:20934 | 1.tcp.sa.ngrok.io | AMAZON-02 | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
1.tcp.sa.ngrok.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |