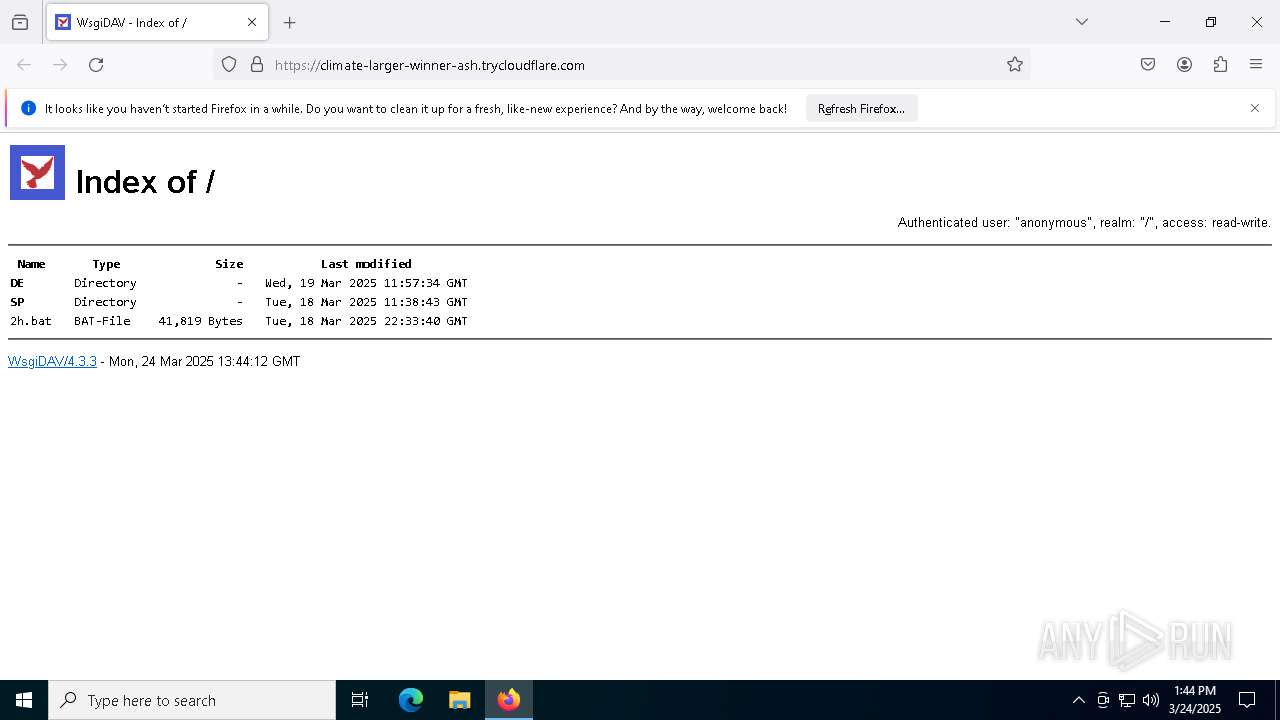
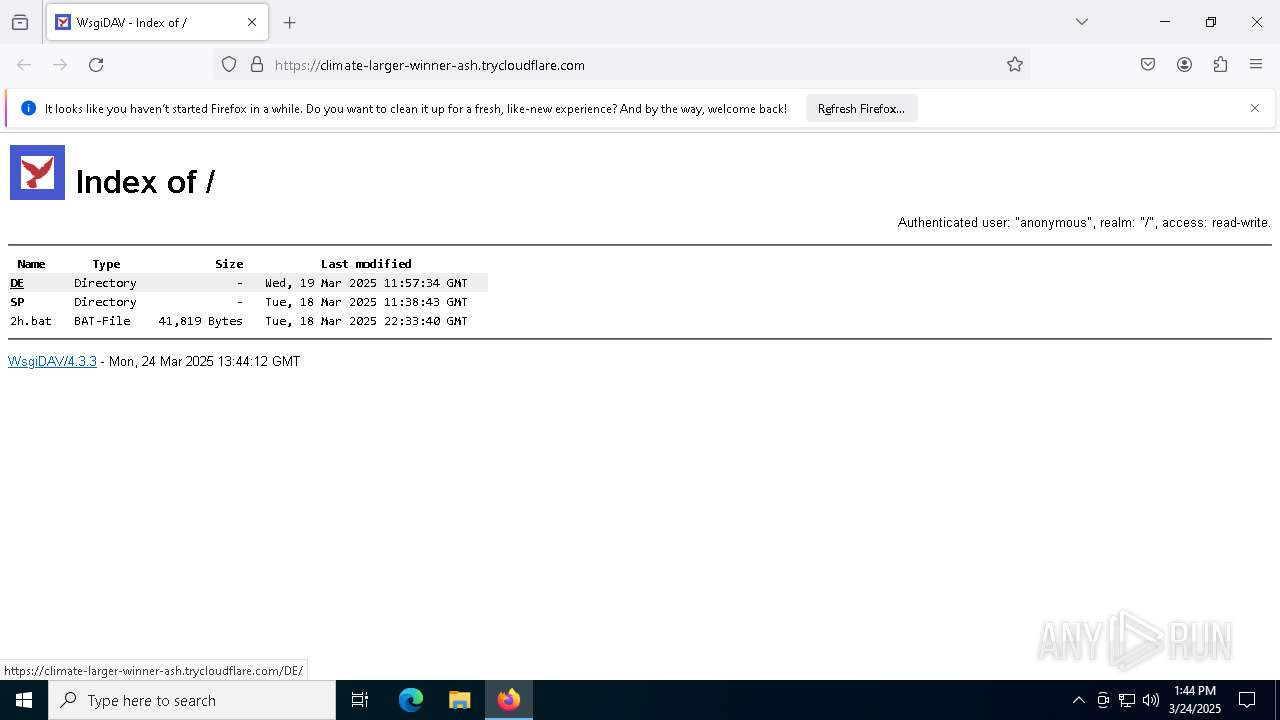
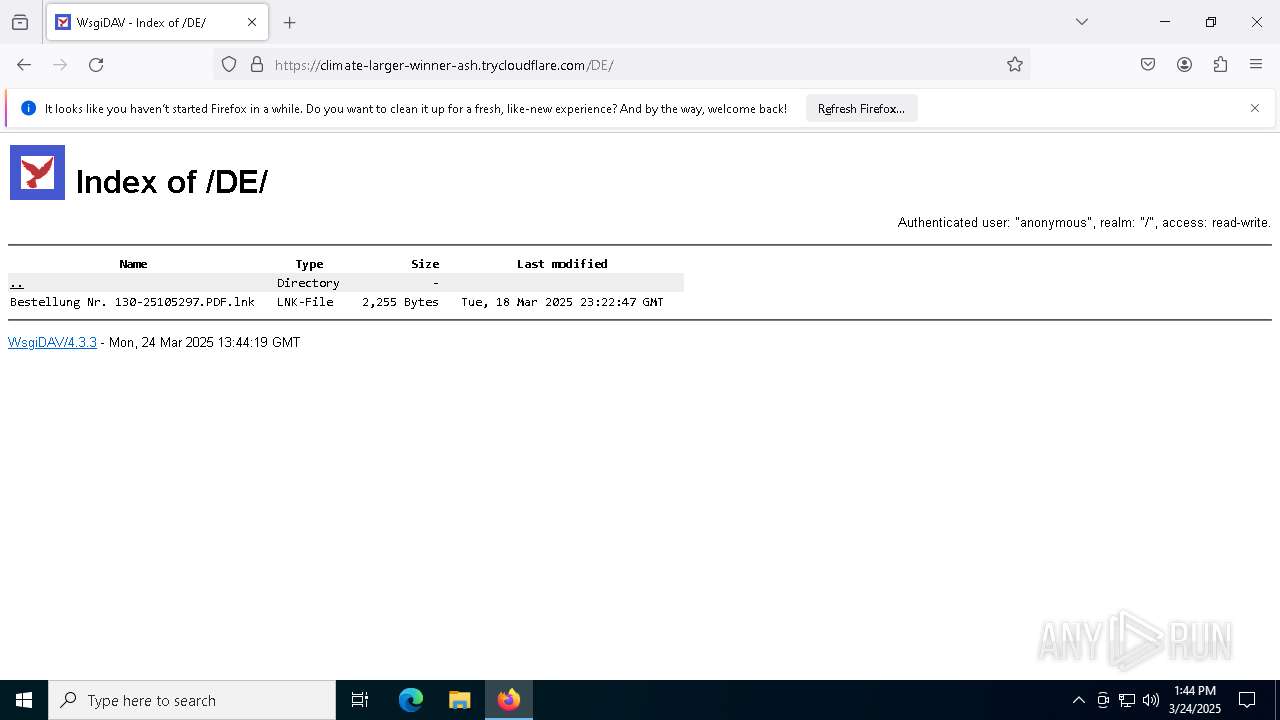
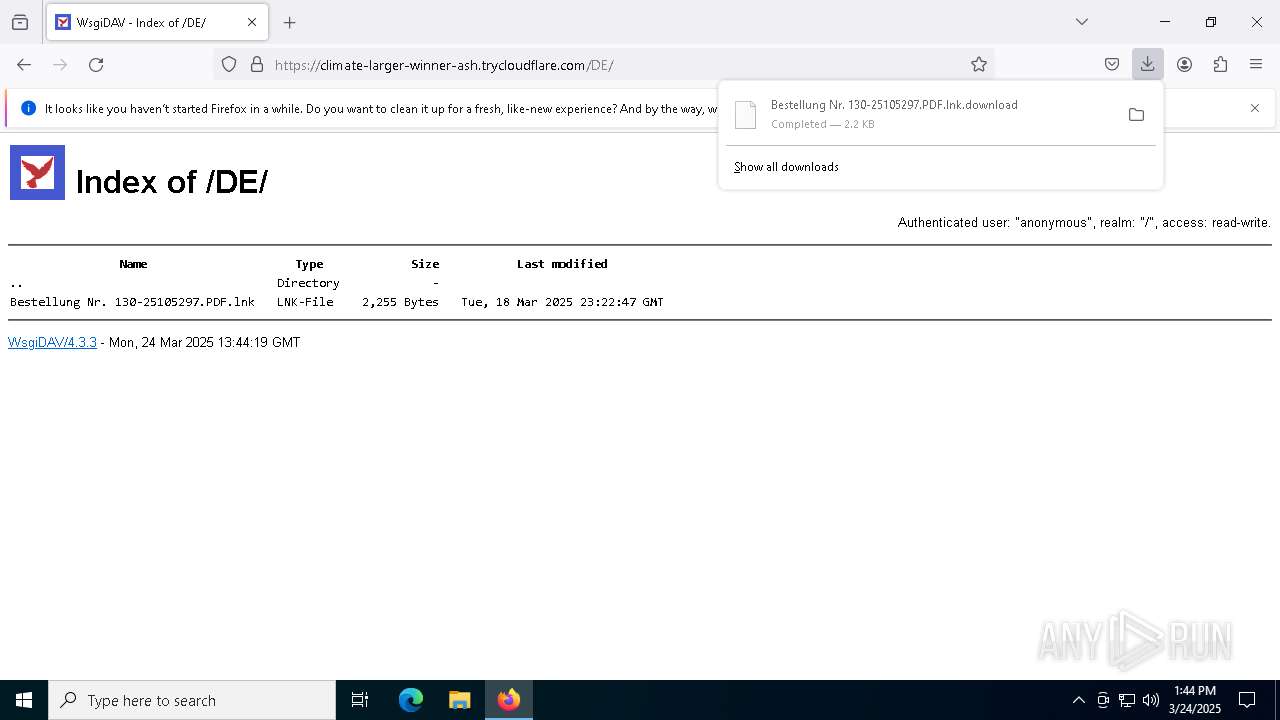
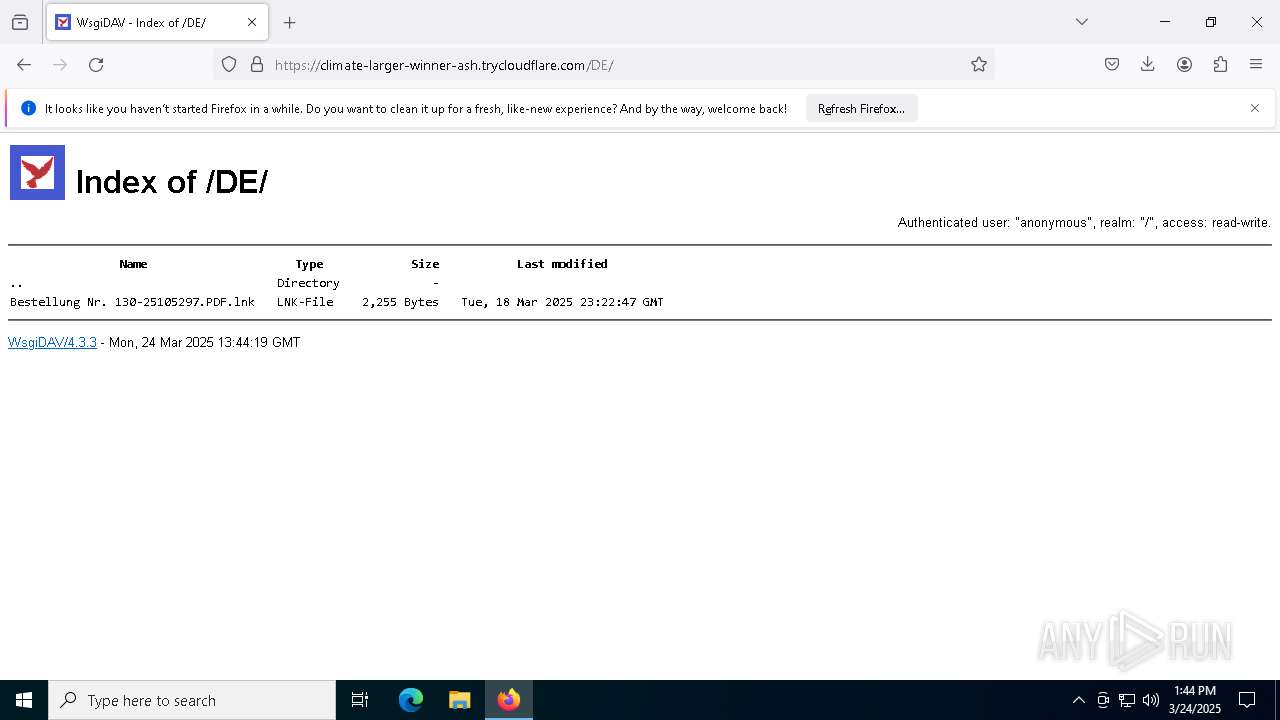
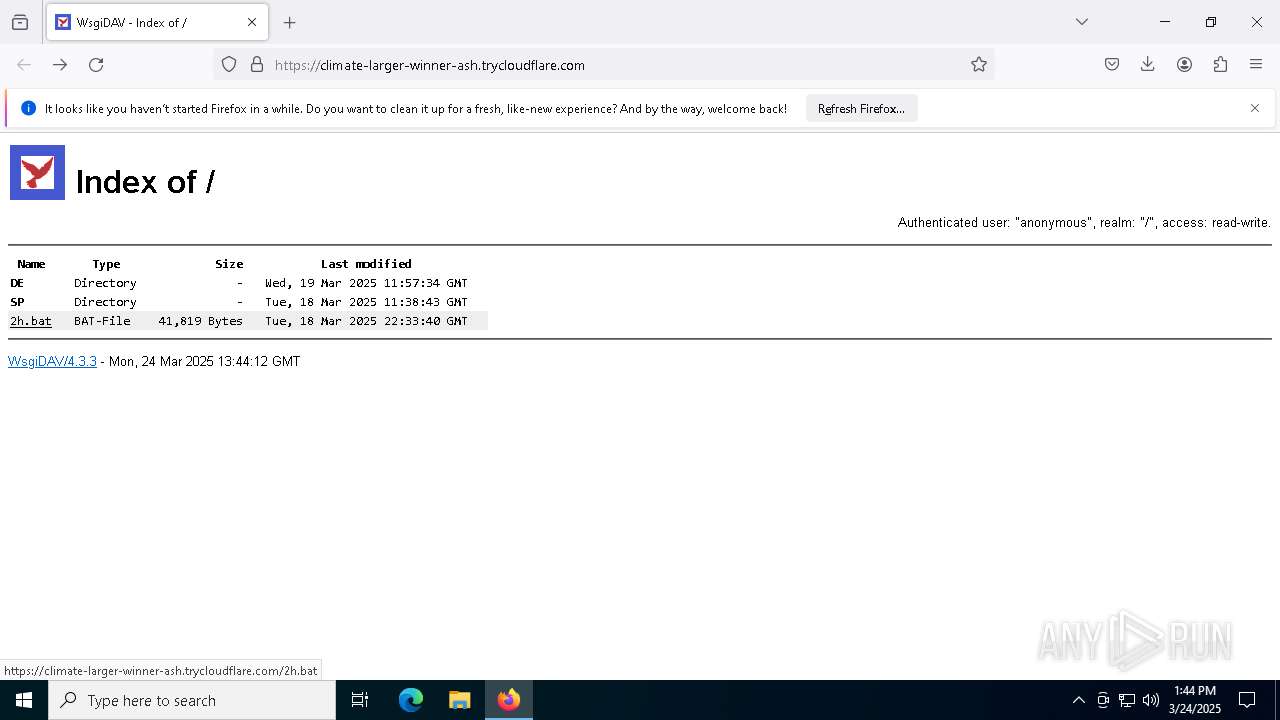
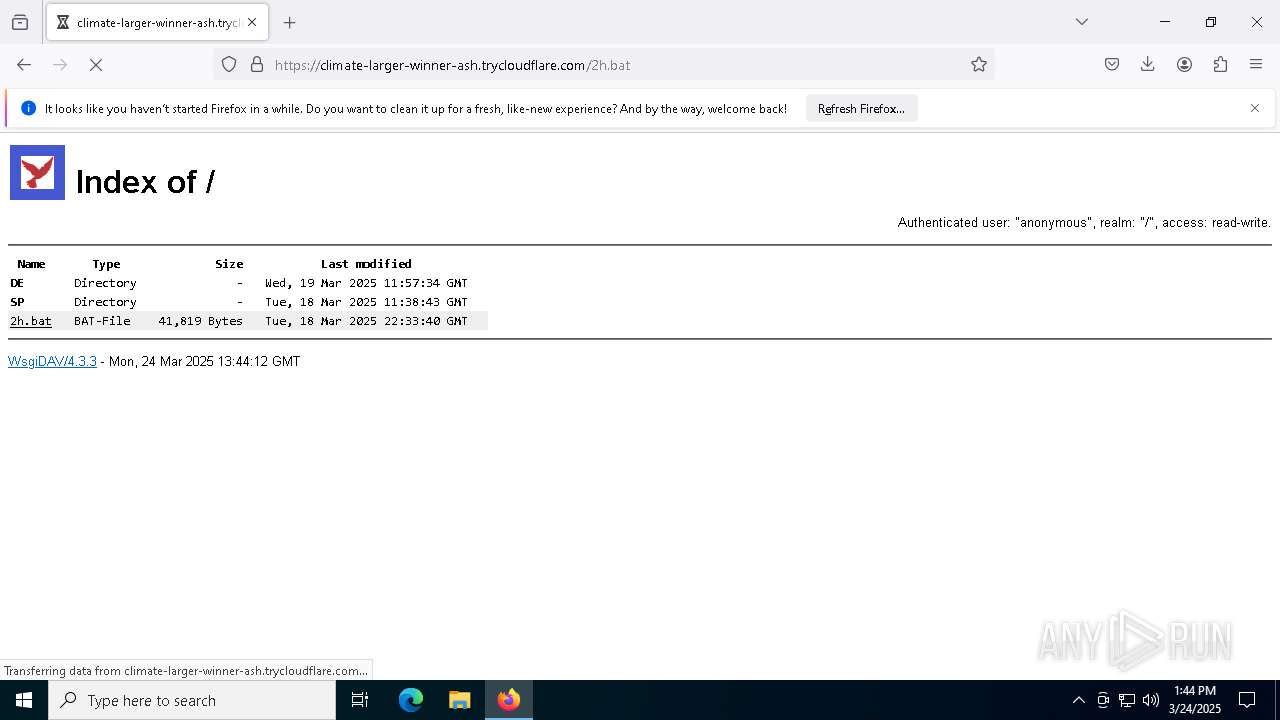
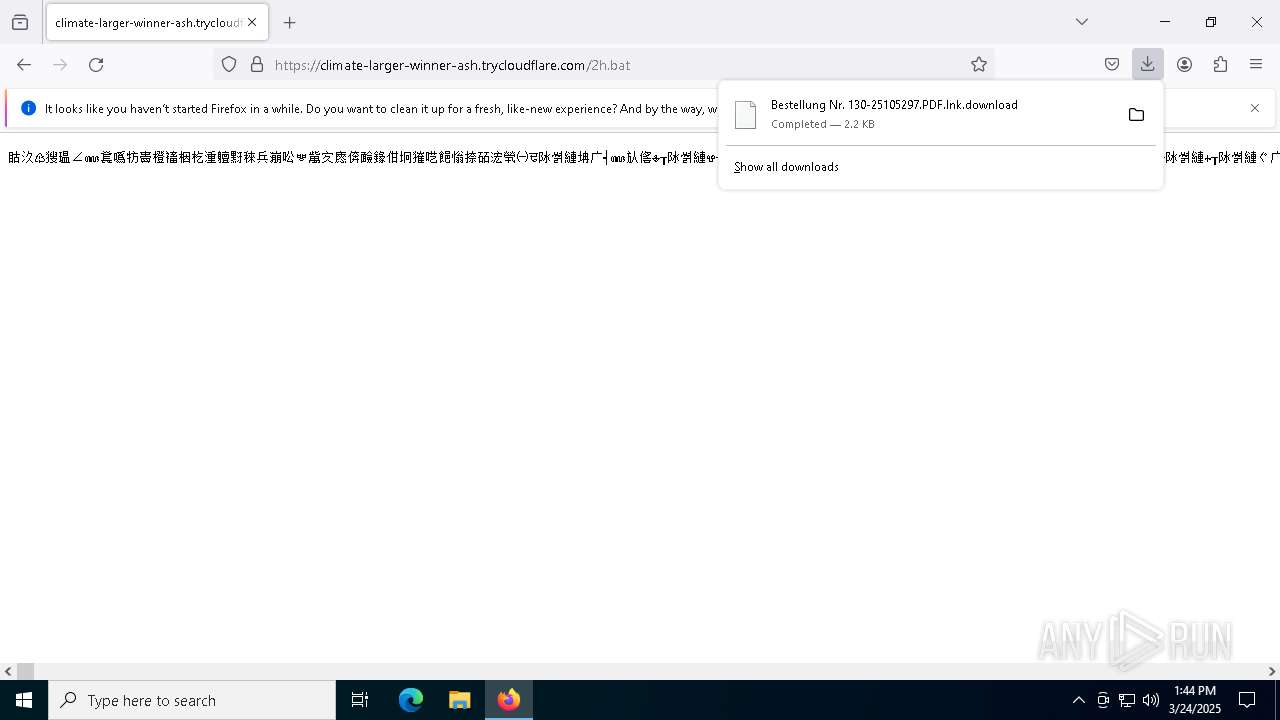
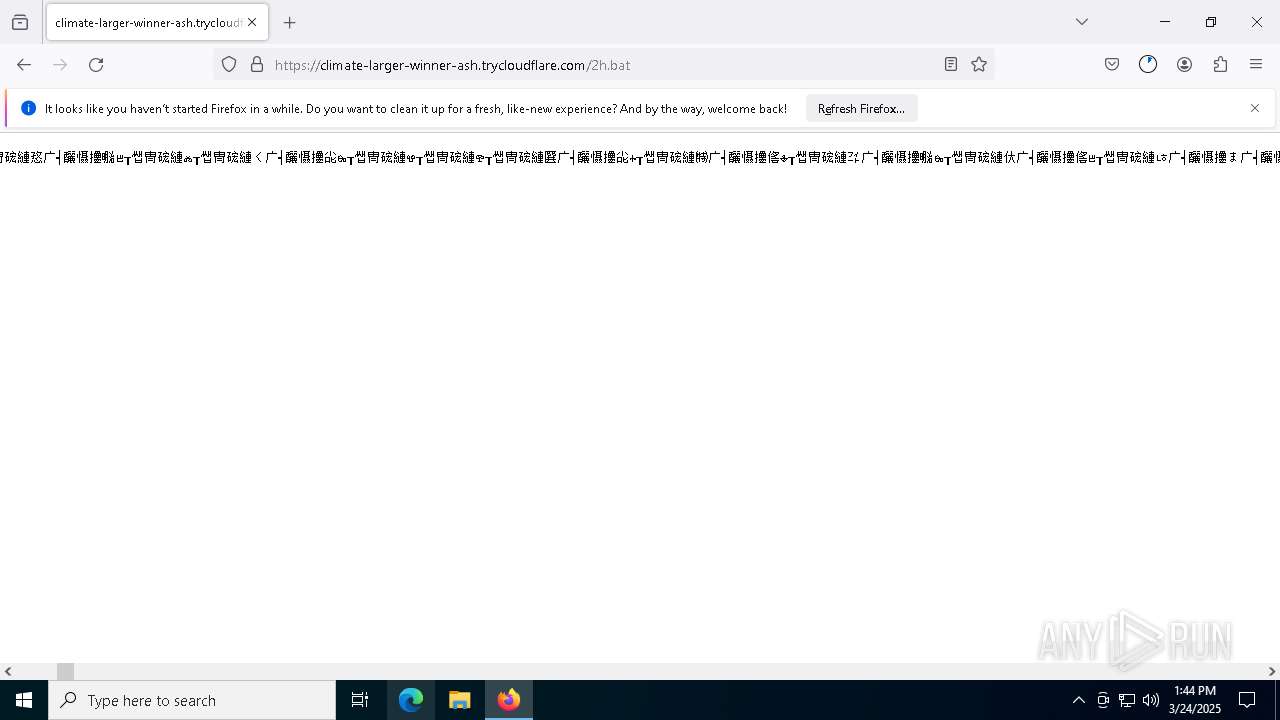
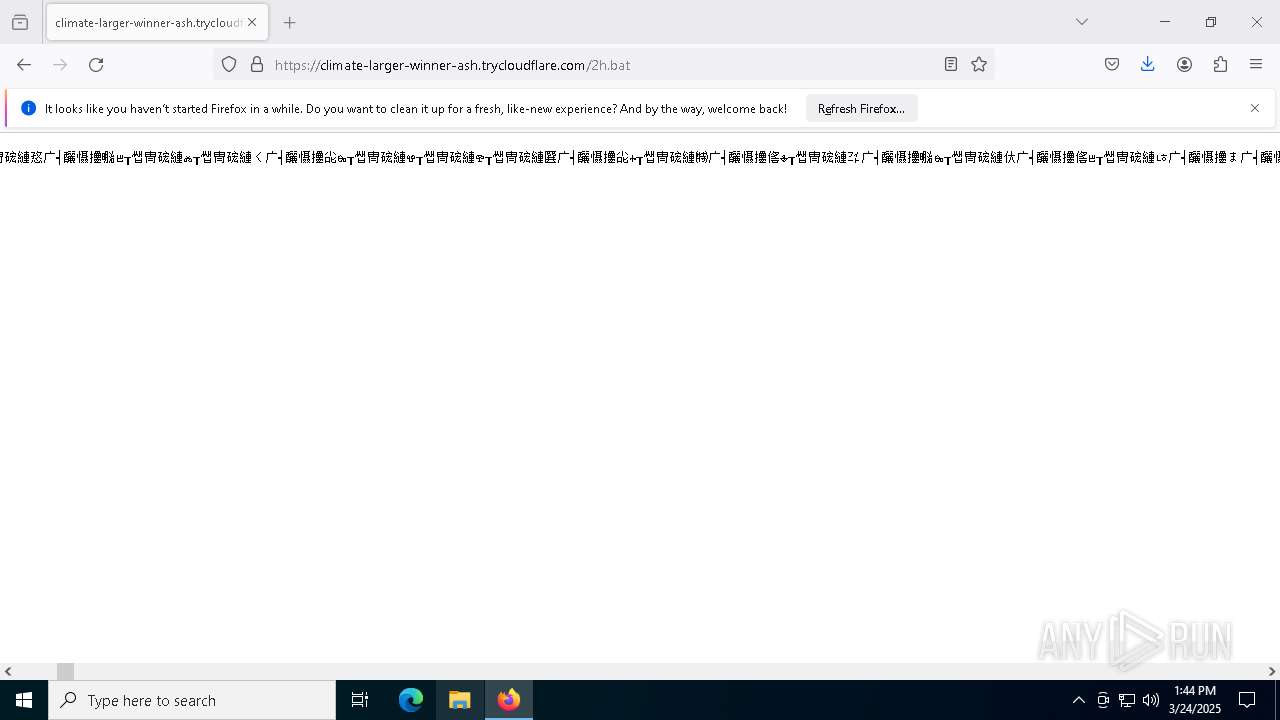
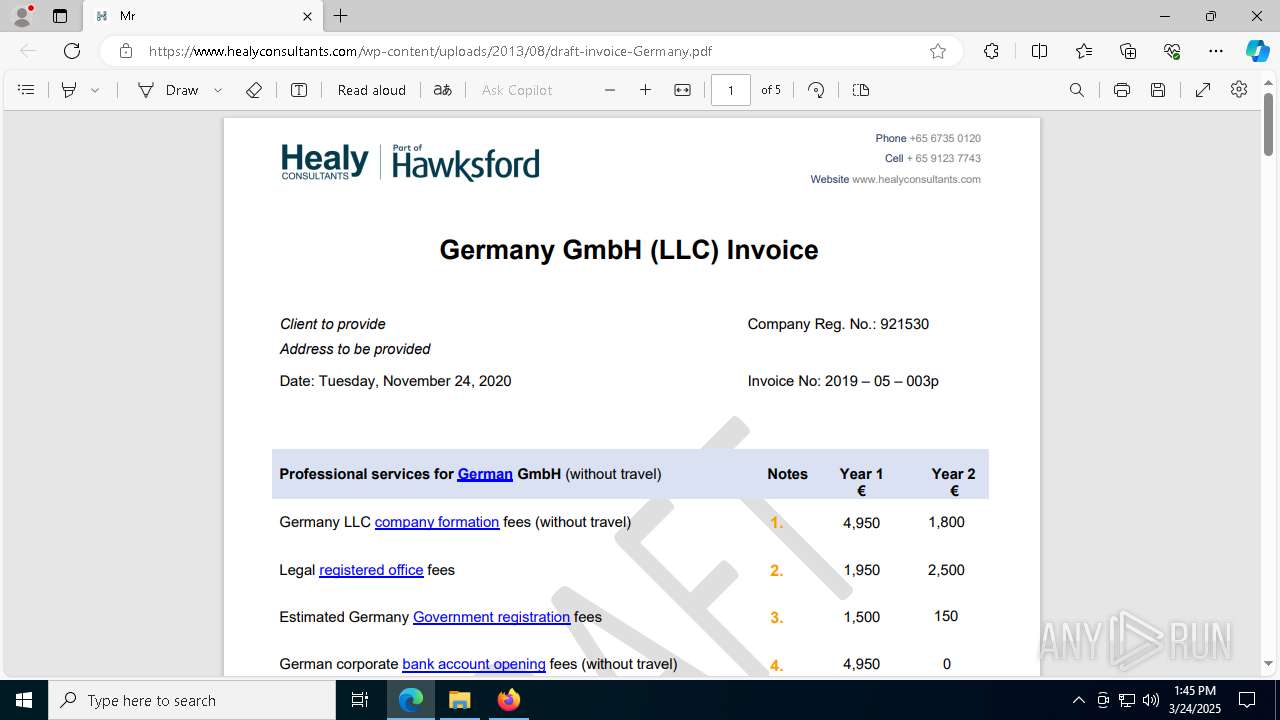
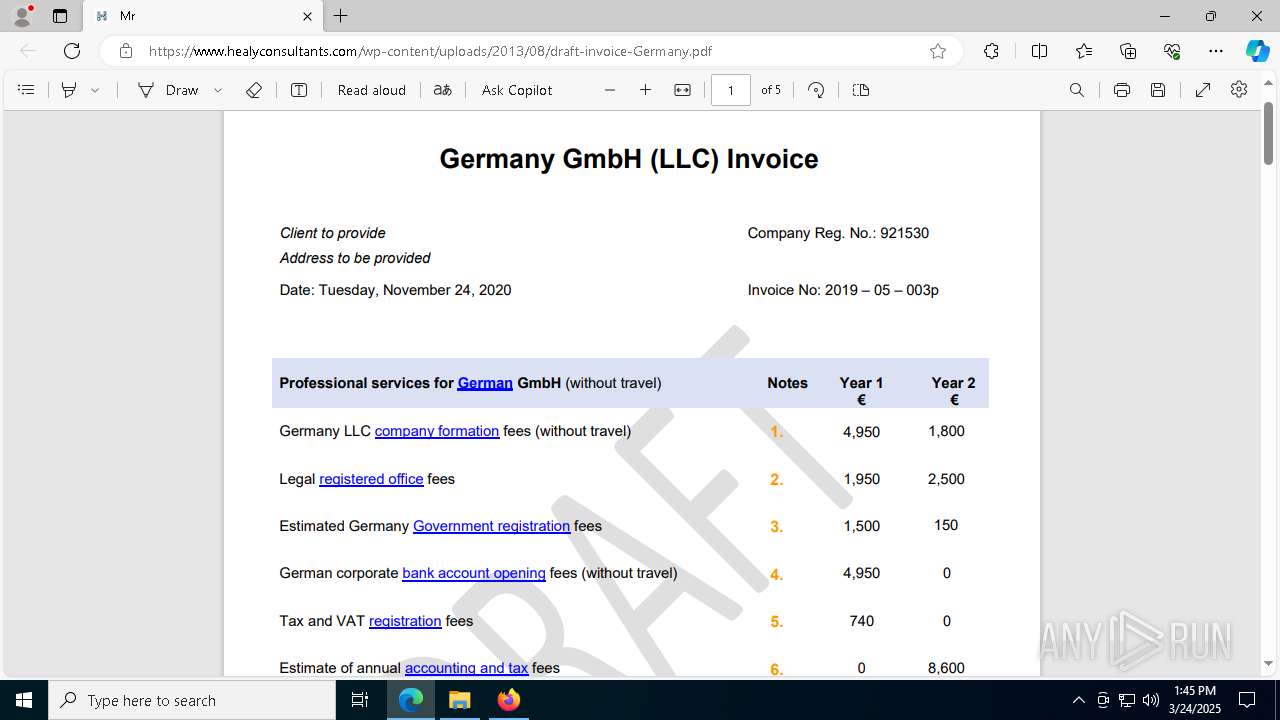
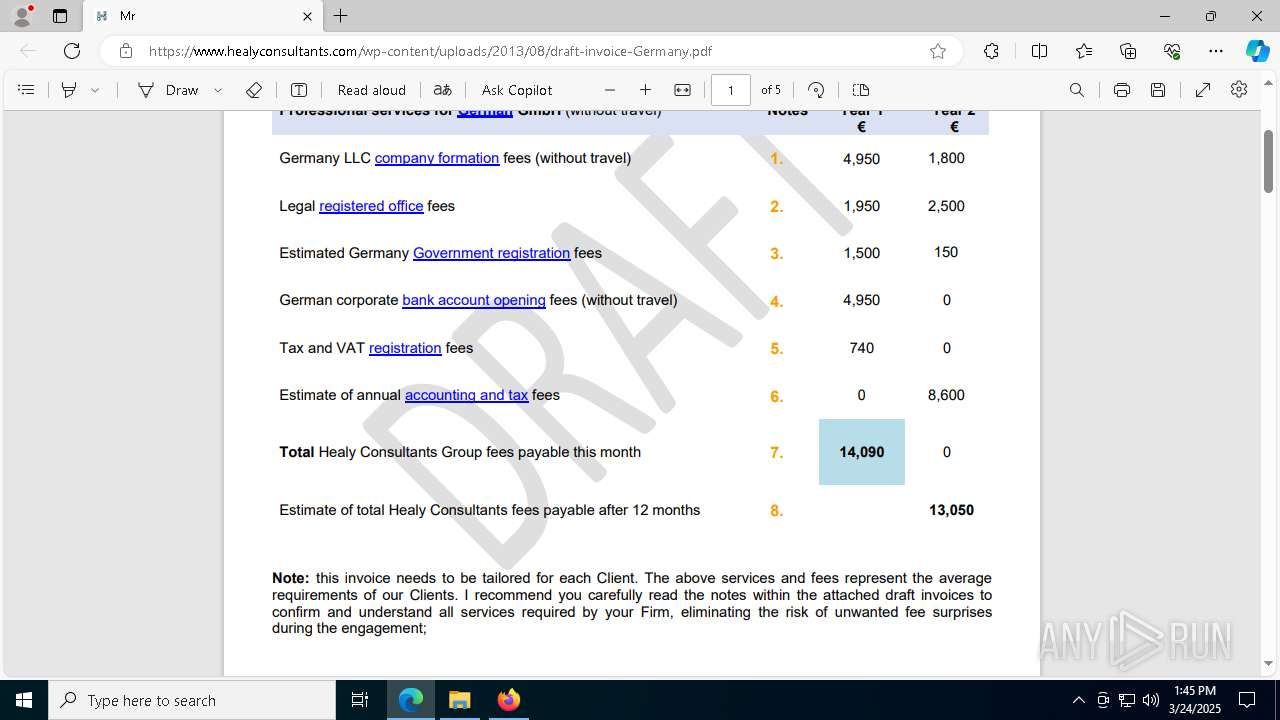
| URL: | https://climate-larger-winner-ash.trycloudflare.com/ |
| Full analysis: | https://app.any.run/tasks/a59f0a93-53c2-4ee0-85bf-752445d229e5 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 24, 2025, 13:44:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BE7A334036386B63F5B02ED1A9F53137 |
| SHA1: | 3D8C2F042C85D12AD30A29424E44AD467FDE55C0 |
| SHA256: | CF4D092F74F05AF4685F241E8EEC3FA60E4CA0629557ABE8C9D42F9723BEAEAD |
| SSDEEP: | 3:N8UZXCfL9RpL1T:2UZuL9bLZ |
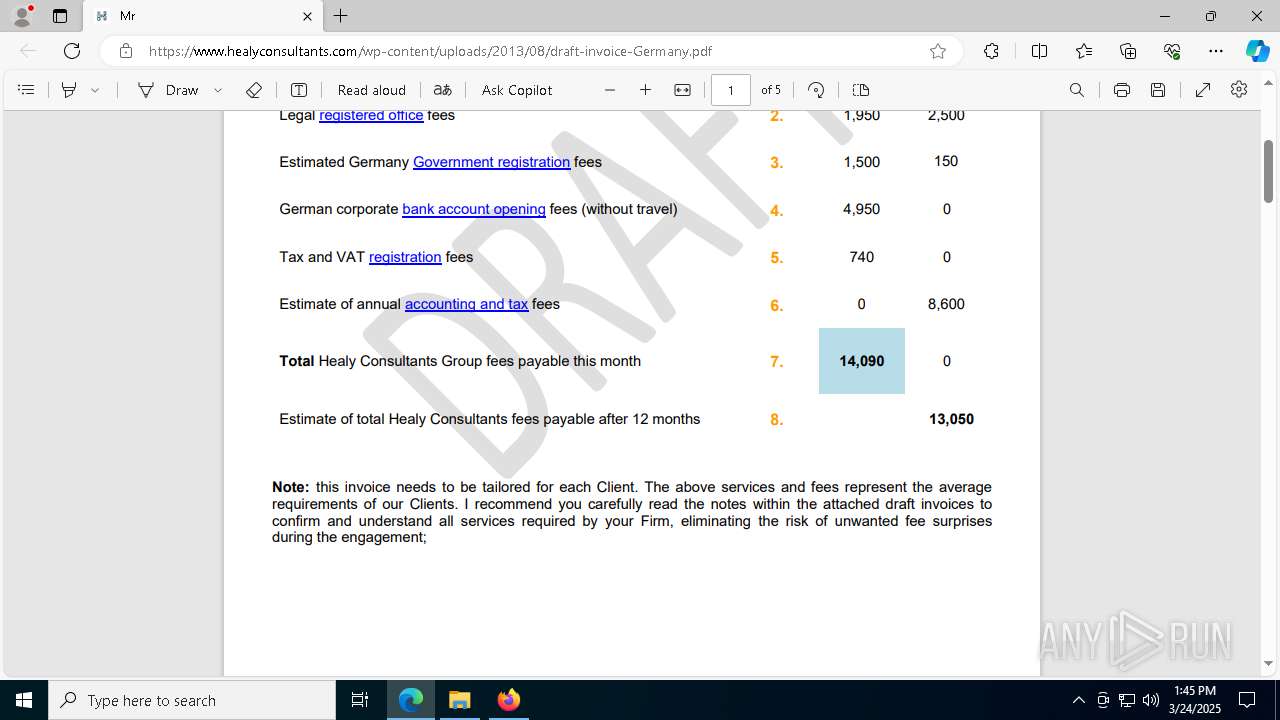
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 8280)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 8516)
ASYNCRAT has been detected (SURICATA)
- notepad.exe (PID: 6584)
- notepad.exe (PID: 900)
- notepad.exe (PID: 5112)
XWORM has been detected (SURICATA)
- notepad.exe (PID: 5020)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8516)
Starts process via Powershell
- powershell.exe (PID: 8280)
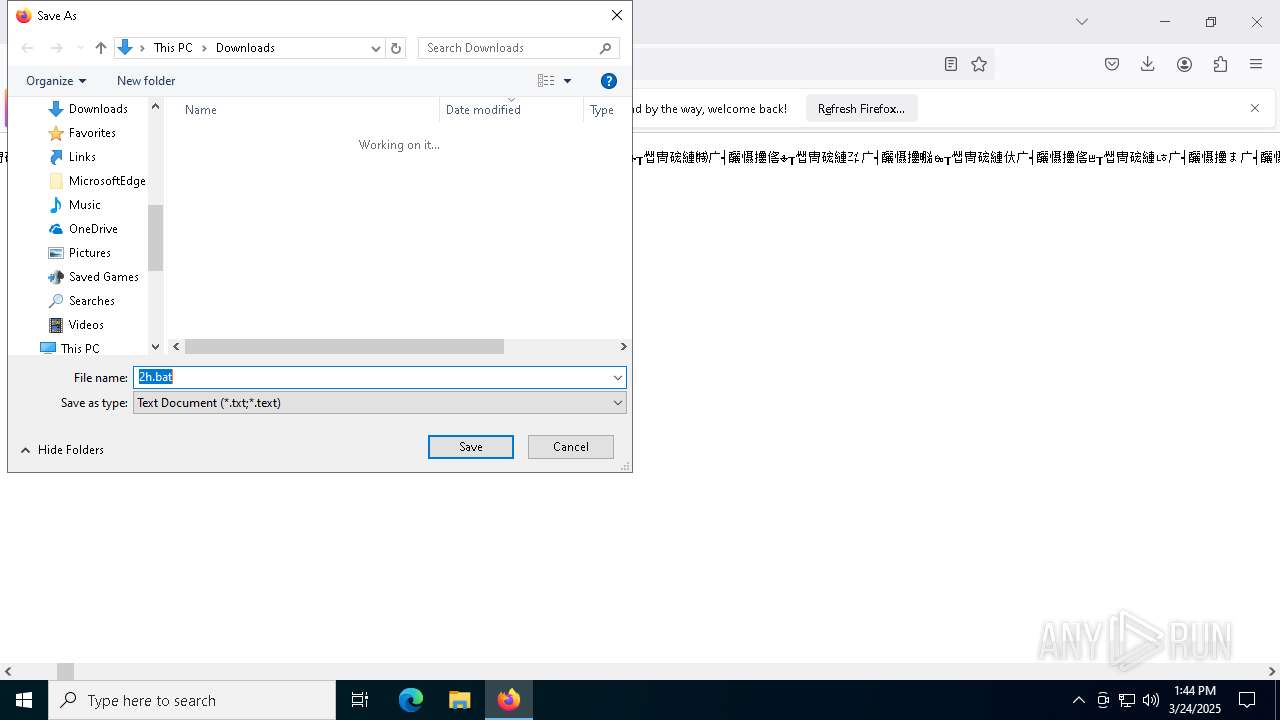
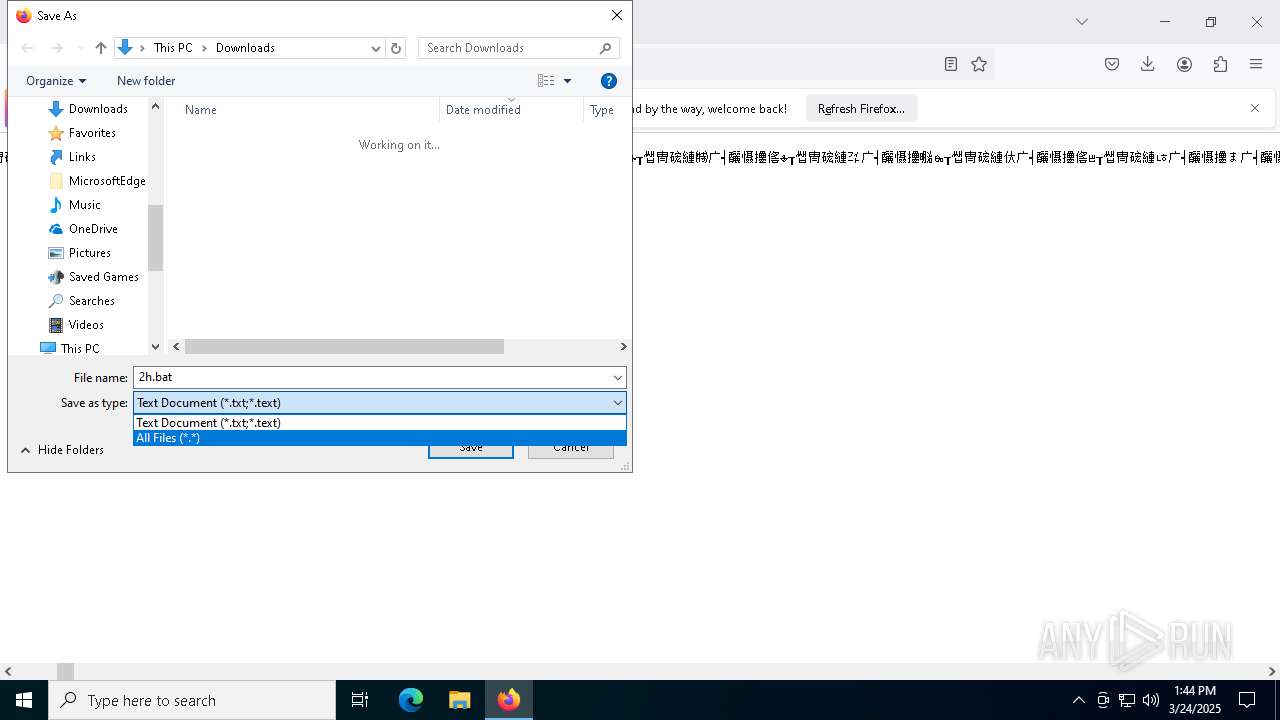
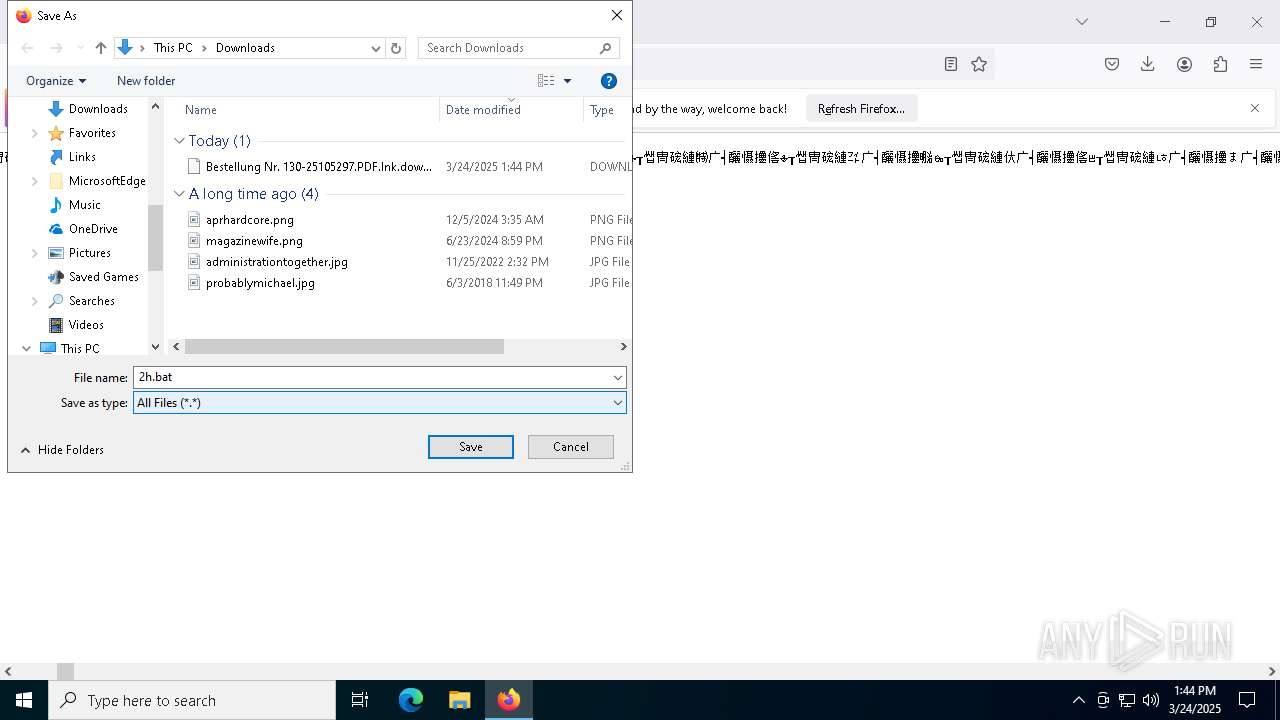
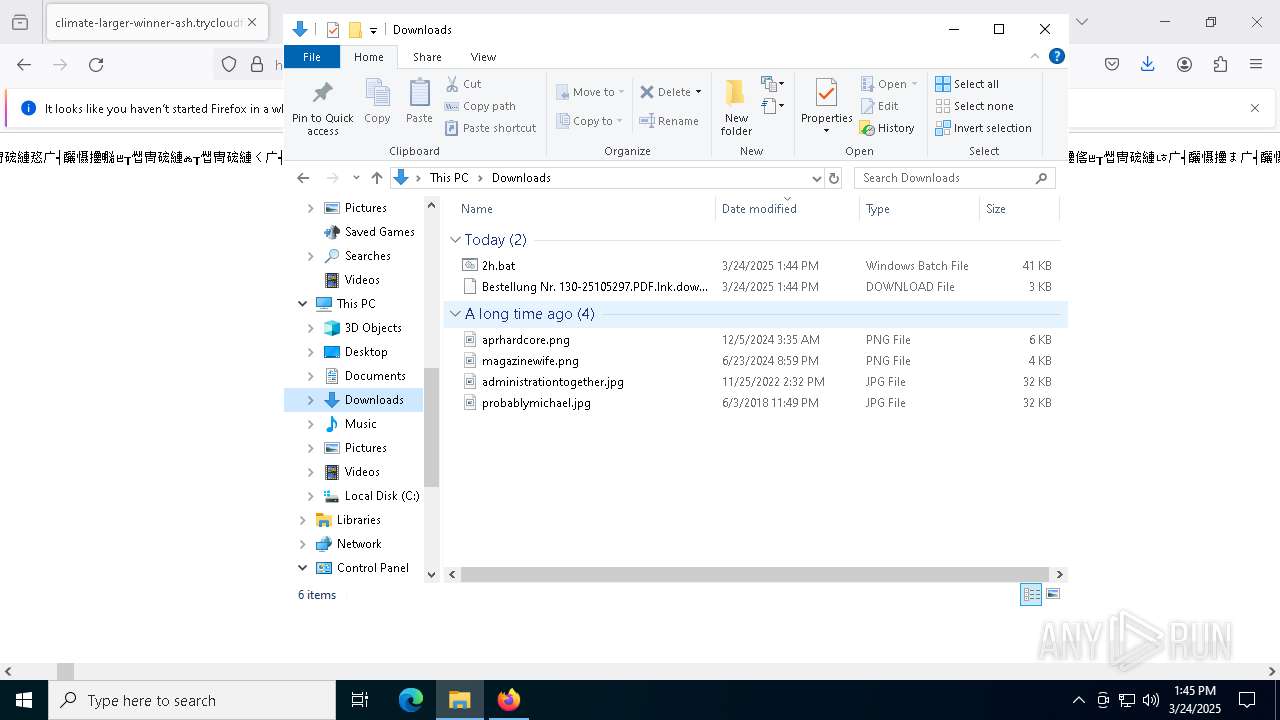
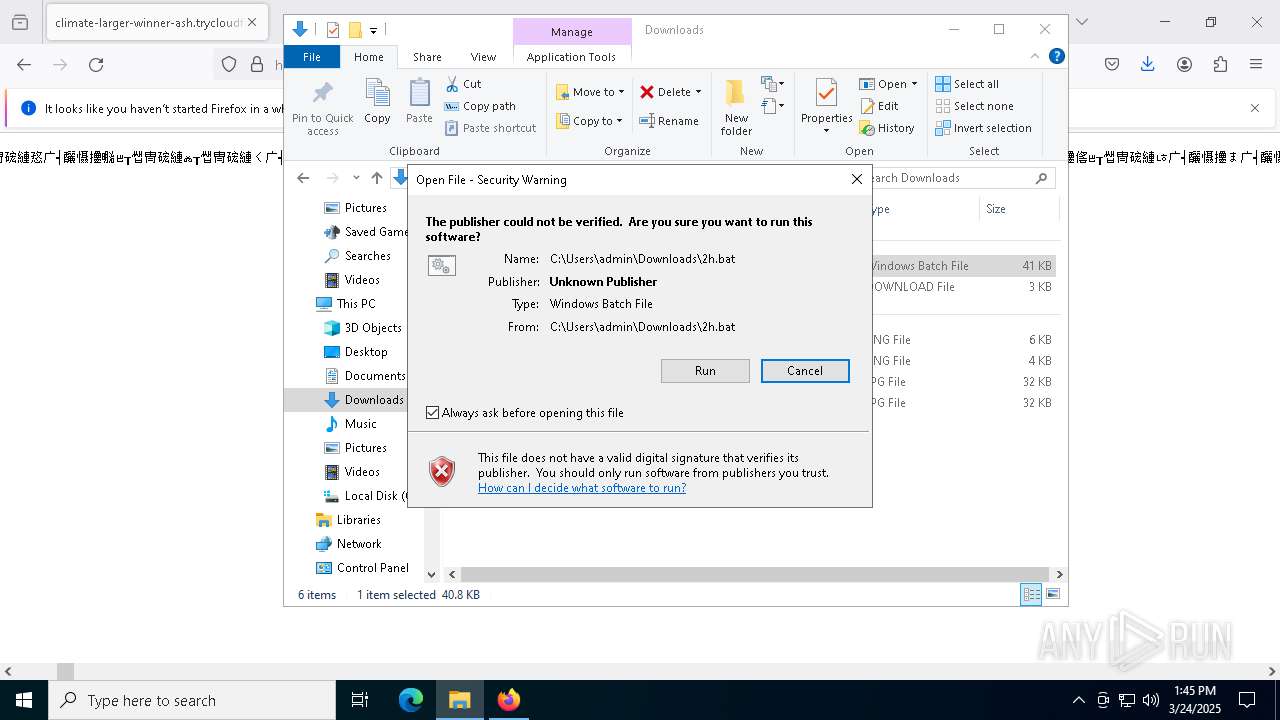
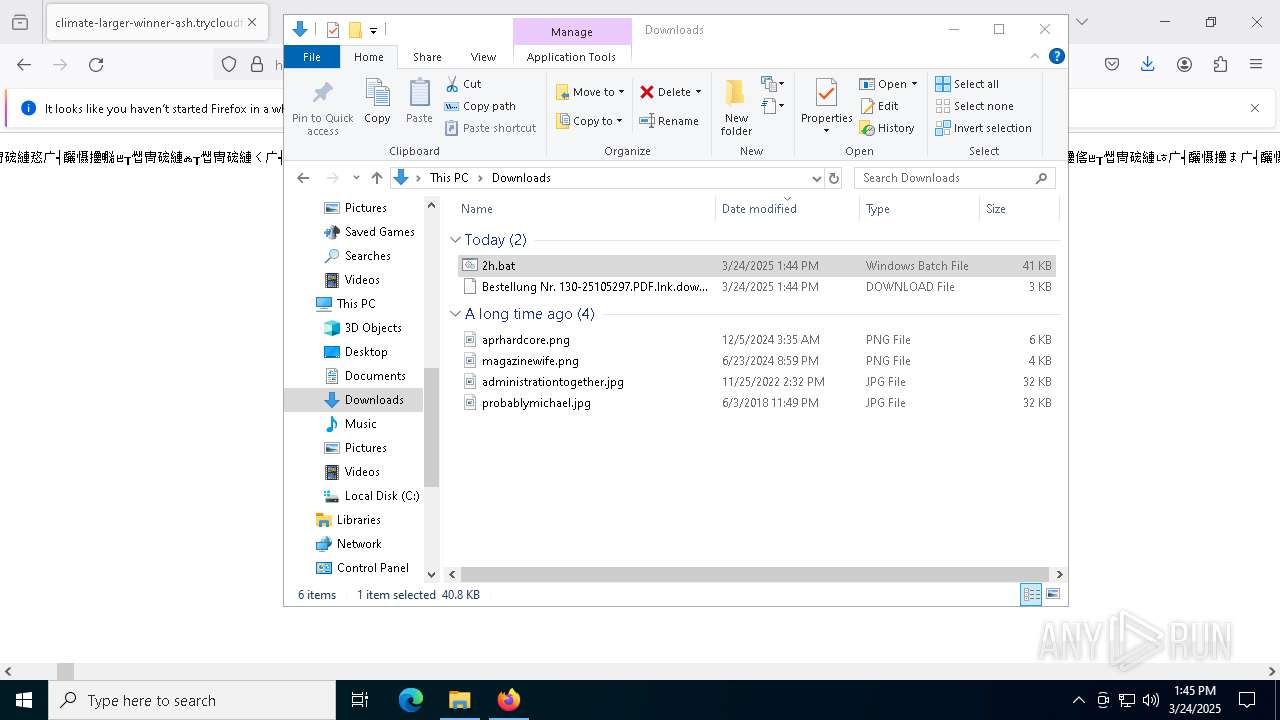
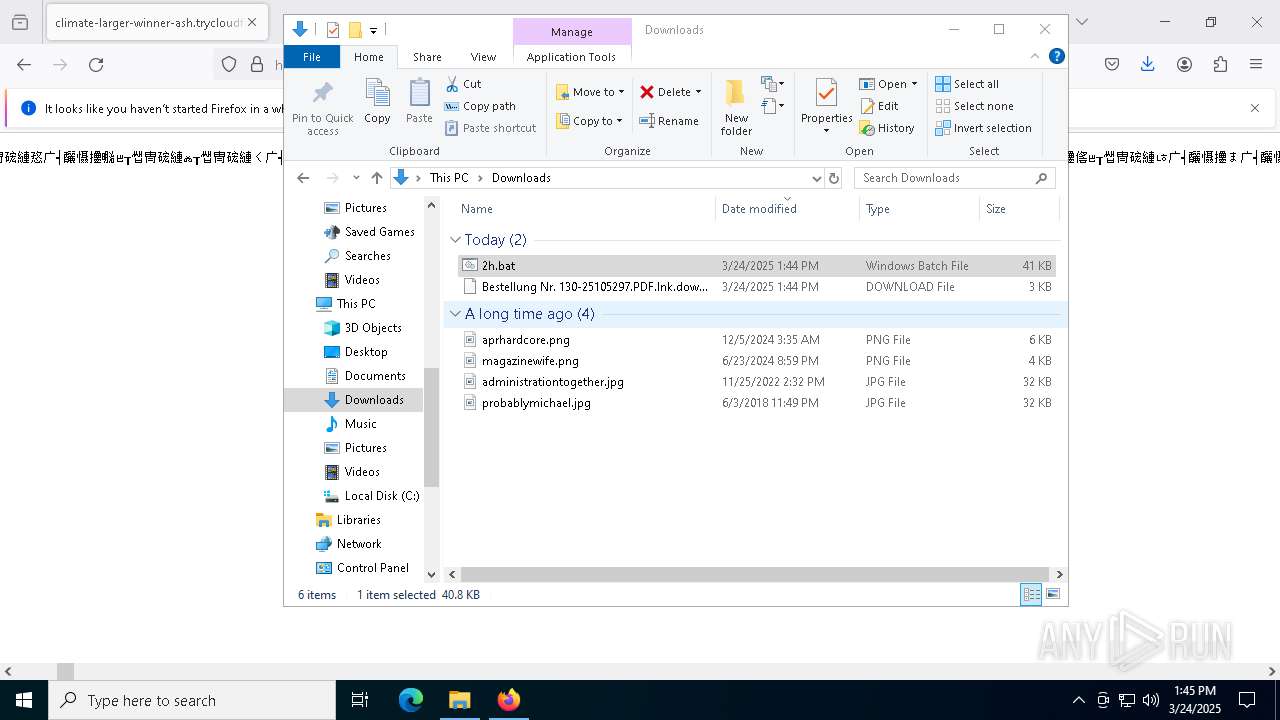
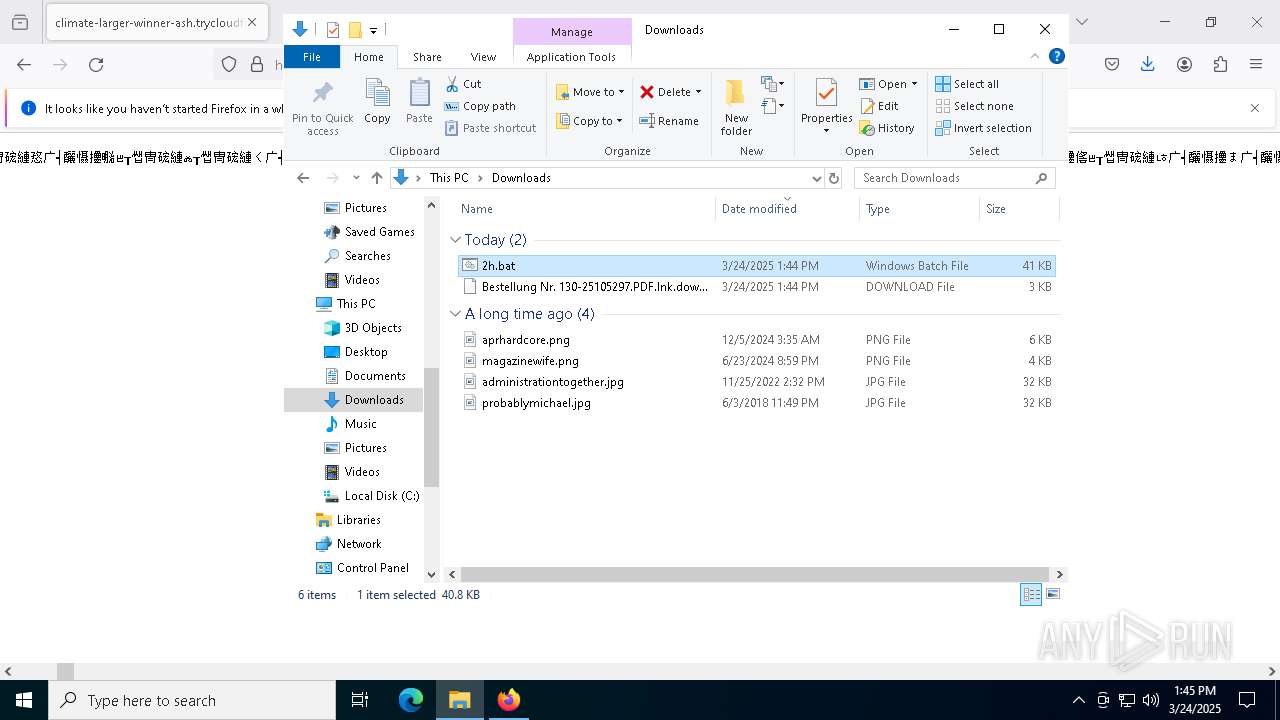
Executing commands from a ".bat" file
- powershell.exe (PID: 8280)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 8280)
Starts NET.EXE to map network drives
- cmd.exe (PID: 8516)
Remote file execution via WebDAV
- net.exe (PID: 8536)
The process drops C-runtime libraries
- powershell.exe (PID: 7460)
- svchost.exe (PID: 8048)
- cmd.exe (PID: 8516)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7460)
Executable content was dropped or overwritten
- powershell.exe (PID: 7460)
Process drops python dynamic module
- powershell.exe (PID: 7460)
The executable file from the user directory is run by the CMD process
- python.exe (PID: 2104)
- python.exe (PID: 7856)
- python.exe (PID: 6044)
- python.exe (PID: 8540)
Process drops legitimate windows executable
- powershell.exe (PID: 7460)
- cmd.exe (PID: 8516)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 8048)
Abuses WebDav for code execution
- svchost.exe (PID: 8048)
Loads Python modules
- python.exe (PID: 6044)
- python.exe (PID: 7856)
- python.exe (PID: 8540)
- python.exe (PID: 2104)
Connects to unusual port
- notepad.exe (PID: 6584)
- notepad.exe (PID: 5020)
- notepad.exe (PID: 5112)
- notepad.exe (PID: 900)
Contacting a server suspected of hosting an CnC
- notepad.exe (PID: 6584)
- notepad.exe (PID: 900)
- notepad.exe (PID: 5112)
- notepad.exe (PID: 5020)
INFO
Application launched itself
- firefox.exe (PID: 6620)
- firefox.exe (PID: 496)
- msedge.exe (PID: 4892)
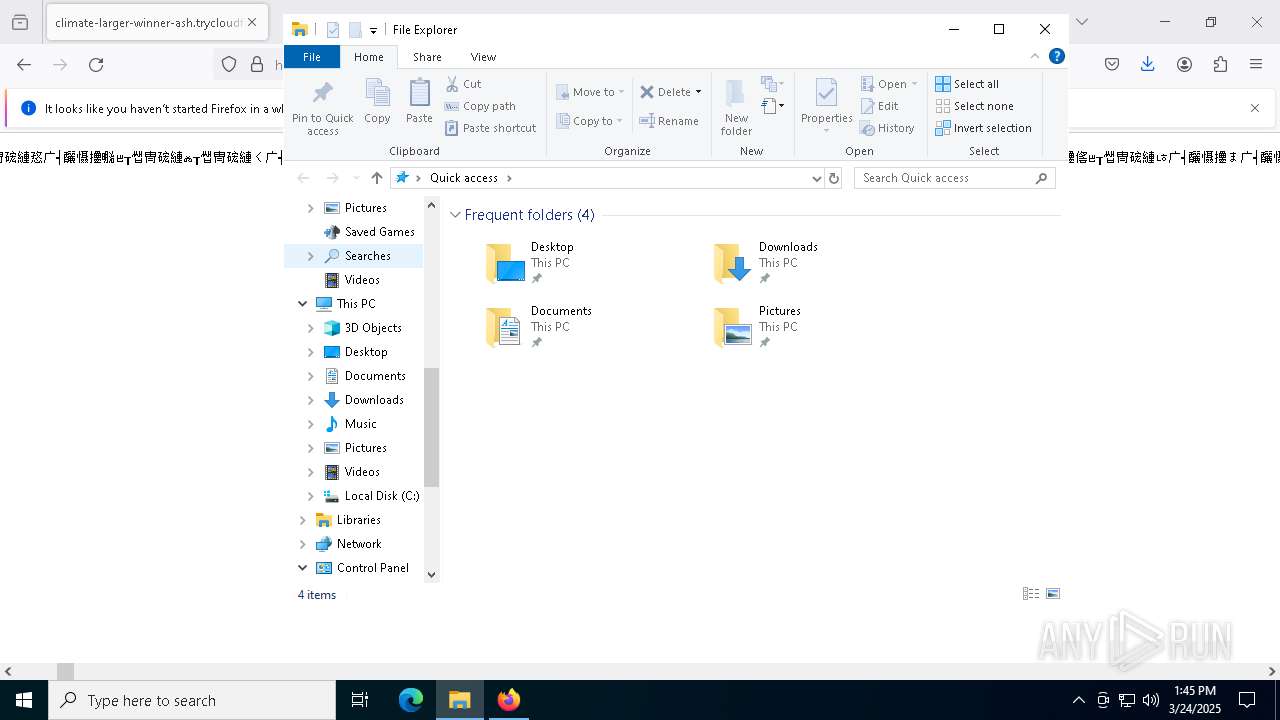
Autorun file from Downloads
- firefox.exe (PID: 6620)
Manual execution by a user
- cmd.exe (PID: 8392)
- notepad.exe (PID: 6584)
- notepad.exe (PID: 5112)
- notepad.exe (PID: 900)
- notepad.exe (PID: 5020)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7460)
Python executable
- python.exe (PID: 2104)
- python.exe (PID: 6044)
- python.exe (PID: 8540)
- python.exe (PID: 7856)
The sample compiled with english language support
- svchost.exe (PID: 8048)
- cmd.exe (PID: 8516)
- powershell.exe (PID: 7460)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7460)
Checks supported languages
- python.exe (PID: 8540)
Creates files or folders in the user directory
- notepad.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
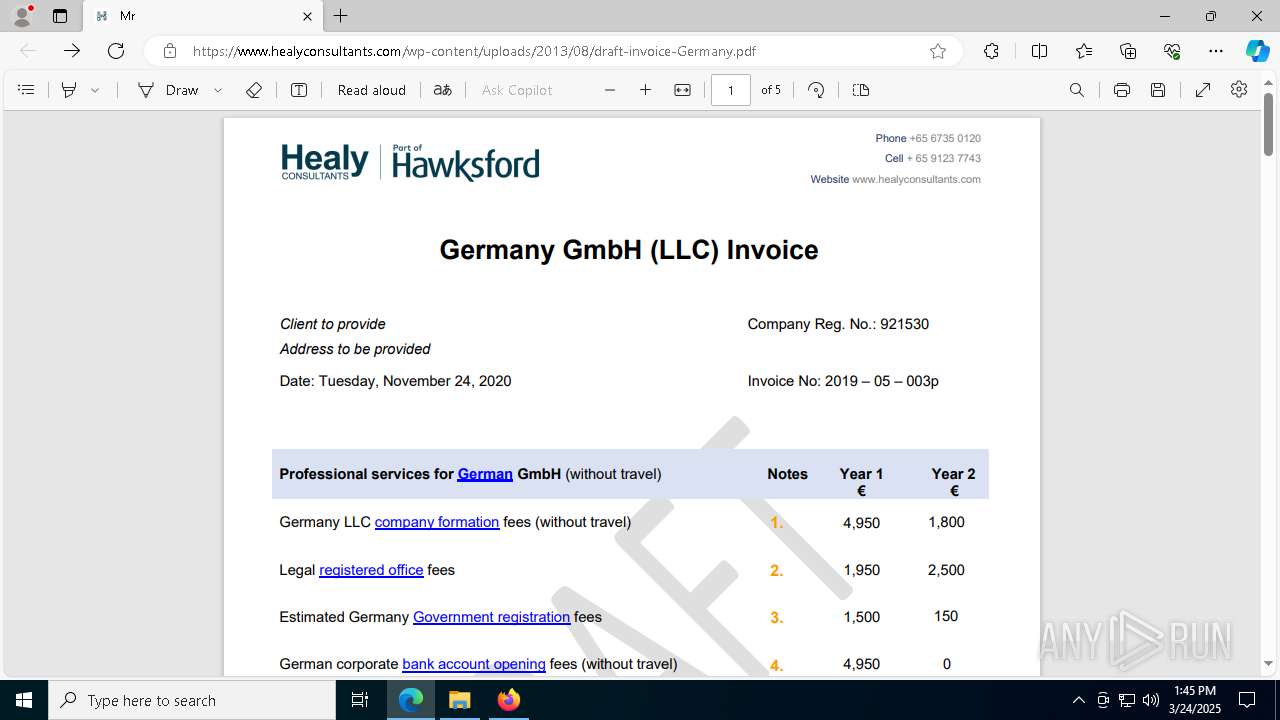
Total processes
210
Monitored processes
71
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
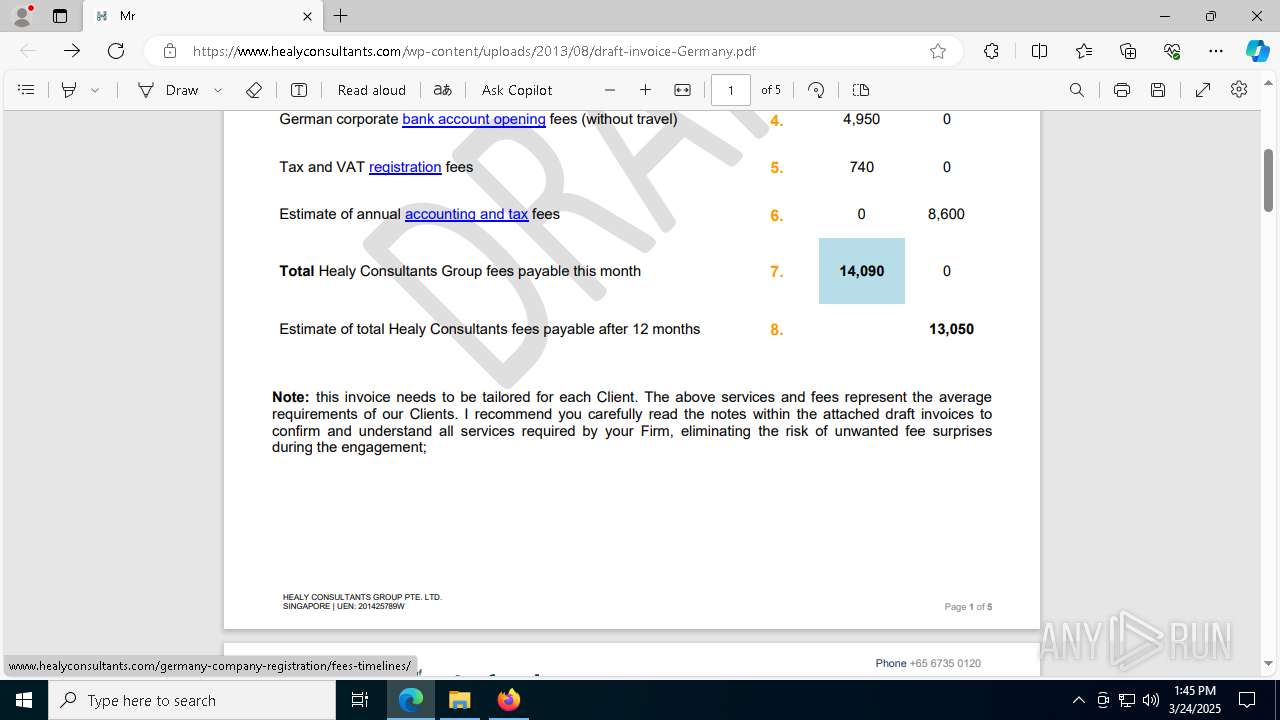
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://climate-larger-winner-ash.trycloudflare.com/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc871c5fd8,0x7ffc871c5fe4,0x7ffc871c5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
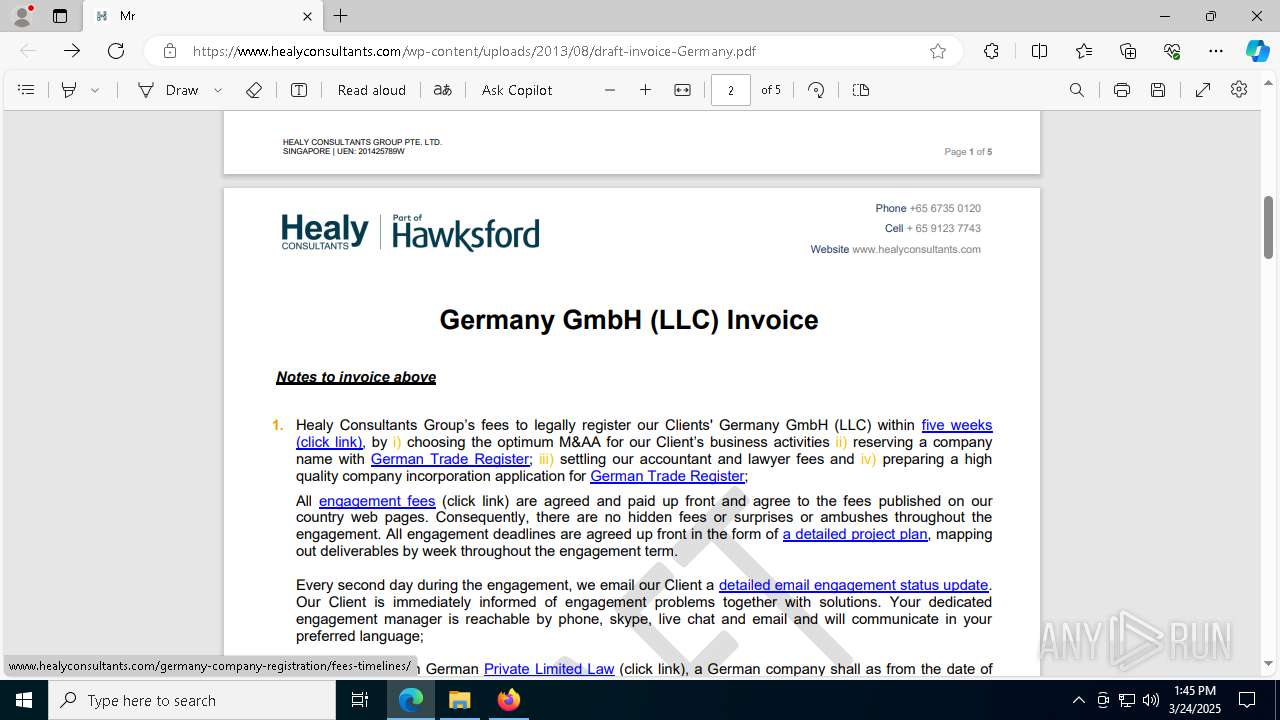
| 644 | net use Z: /delete /yes | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | C:\Windows\System32\notepad.exe | C:\Windows\System32\notepad.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3456 --field-trial-handle=2412,i,1892078677101372044,12649935052016730555,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=6220 --field-trial-handle=2412,i,1892078677101372044,12649935052016730555,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2104 | python "1.py" | C:\Users\admin\Contacts\python\python.exe | — | cmd.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.11.9 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6416 --field-trial-handle=2412,i,1892078677101372044,12649935052016730555,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
44 815
Read events
44 749
Write events
64
Delete events
2
Modification events
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000000000004000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Downloads | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: D361E16700000000 | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\bat |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\bat |
| Operation: | write | Name: | 0 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D3A002E8005398E082303024B98265D99428E115F260001002600EFBE11000000FCD61862AF27D3013908FFDAC29CDB013D6004DBC29CDB011400540032000000000000000000800032682E62617400003E0009000400EFBE00000000000000002E0000000000000000000000000000000000000000000000000000000000320068002E00620061007400000016000000 | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\bat |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
37
Suspicious files
279
Text files
65
Unknown types
7
Dropped files
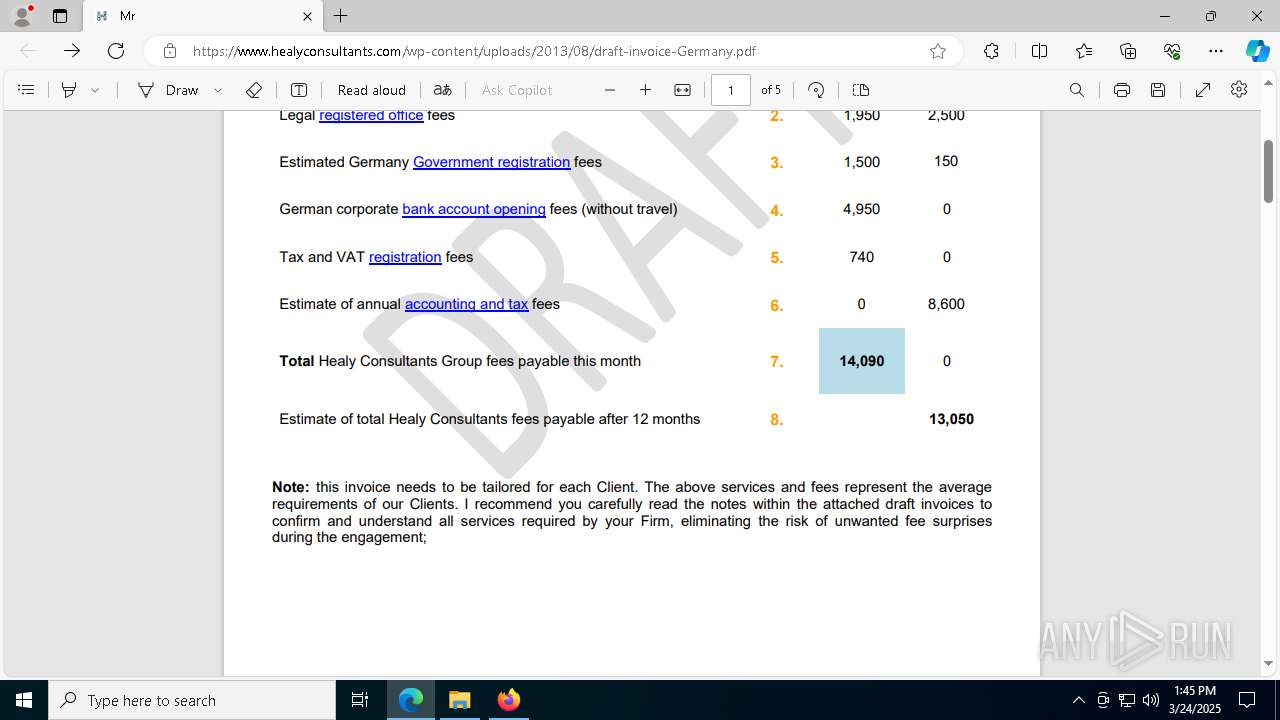
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:18DEC106E8E1B60CCA33C519C7F5ADFD | SHA256:95117877A4C47047E9659E41BBF20CC615BD2C6B53C68E5BBB9233A429B3D7AC | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:F759EB25271E6A6F0A3500520813E5FE | SHA256:015E515D432DD64FDC9502ABE9C723EEF544E7AF11C36BDFE8B38412597CA1EC | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:63CAE799FDE4579934AAD52309A53E3B | SHA256:30F793EBE46966E685F98B0ADB4DC0FCED0279ED615A6A5D4619186E65AF9E86 | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:82D9E5335481A0F7E2D4F3AA11251187 | SHA256:DF06D0F36FD13E70E4475F3E36BD8FB46B05A9E0528448019BE0478BE1C5E136 | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:D4E29A0670C750467F946A368FF3356F | SHA256:2B4CE418936F2E03686057779398263EECD55D4DCD34A1B38751100344D46842 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
147
DNS requests
212
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 2.22.242.122:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 2.22.242.122:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6620 | firefox.exe | 104.16.231.132:443 | climate-larger-winner-ash.trycloudflare.com | CLOUDFLARENET | — | whitelisted |
6620 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
6620 | firefox.exe | 216.58.206.74:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6620 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6620 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
6620 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
climate-larger-winner-ash.trycloudflare.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
6620 | firefox.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
6620 | firefox.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
6620 | firefox.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
6620 | firefox.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |