| File name: | bad.exe |
| Full analysis: | https://app.any.run/tasks/c3fb3a75-3ddc-47f2-8503-7b18c80582a5 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | October 09, 2019, 13:20:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AA56E56400BB0CA44EE988A123B90304 |
| SHA1: | 566DFD8EF930F33356E139FC2E43A73175598909 |
| SHA256: | CEBDFA6A87582737ABD424D4DBCDAAC1C26004822CEFD2E3CFE2B297EA76E701 |
| SSDEEP: | 6144:j5lz/+kkPnAEfOskkXrkayMNz0Tu9wkV46Yi:dUkkP97bkqx2CX46Yi |
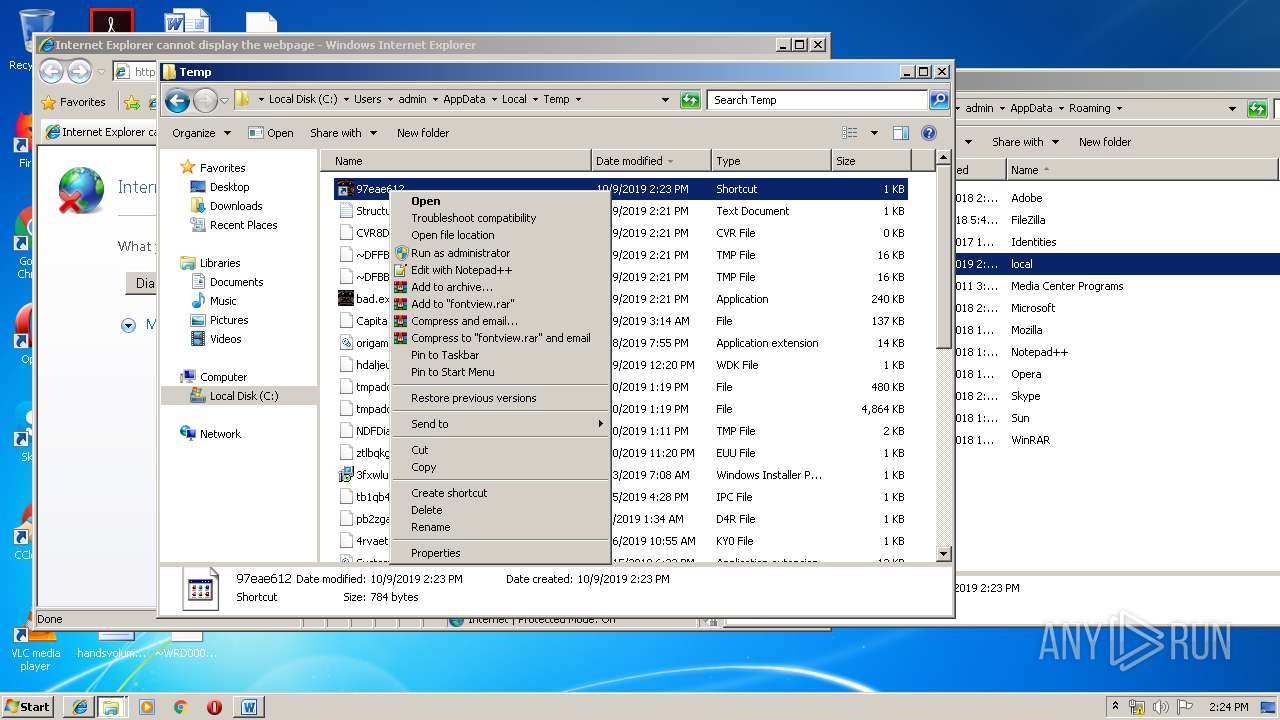
MALICIOUS
Loads dropped or rewritten executable
- bad.exe (PID: 3148)
SUSPICIOUS
Creates files in the user directory
- bad.exe (PID: 3148)
Executable content was dropped or overwritten
- bad.exe (PID: 3148)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3359 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000062A5 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43142 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15971 |
.data | 0x0000A000 | 0x00020318 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.90464 |
.ndata | 0x0002B000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00001CB0 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.44441 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2992 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.22353 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.1185 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 3.49005 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.21733 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
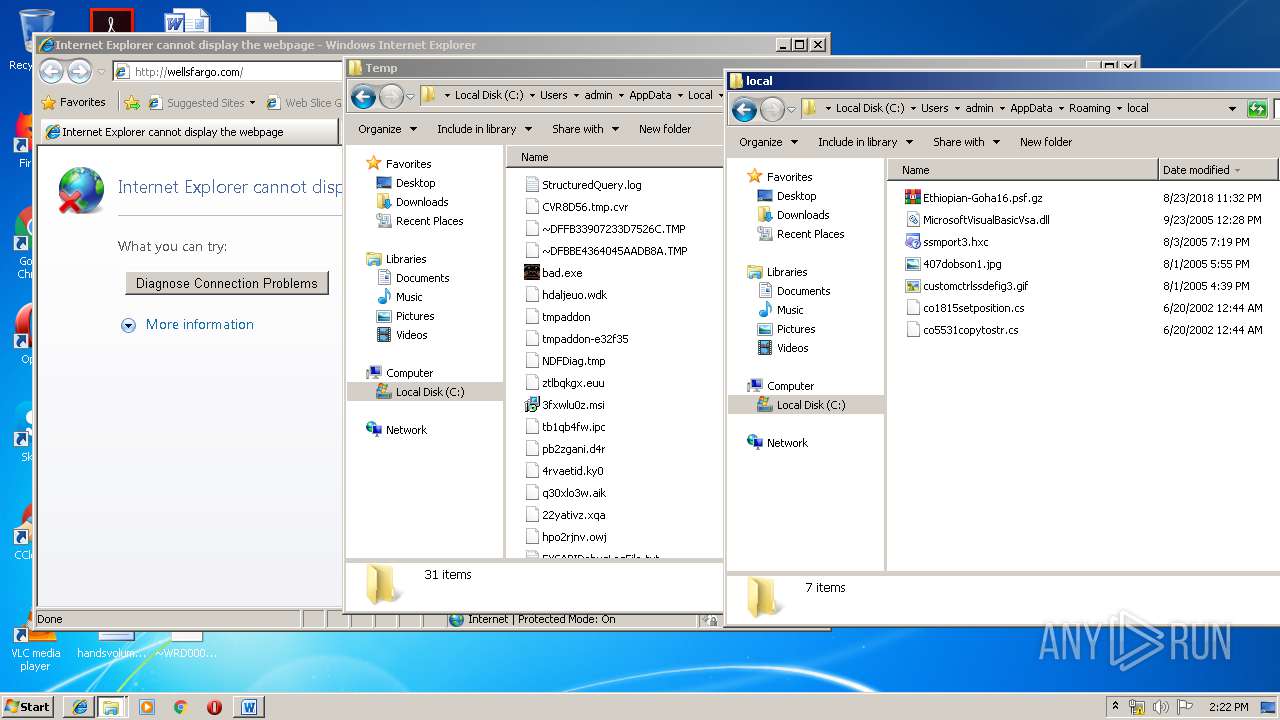
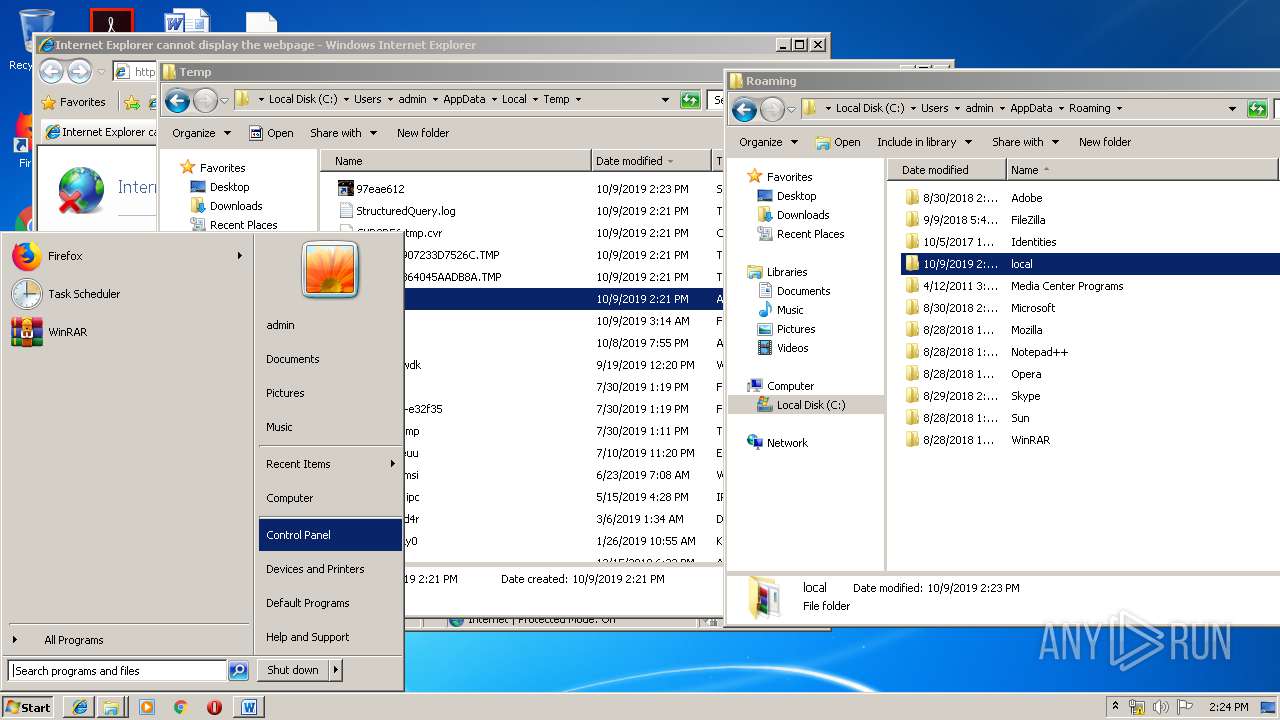
Total processes
32
Monitored processes
1
Malicious processes
1
Suspicious processes
0
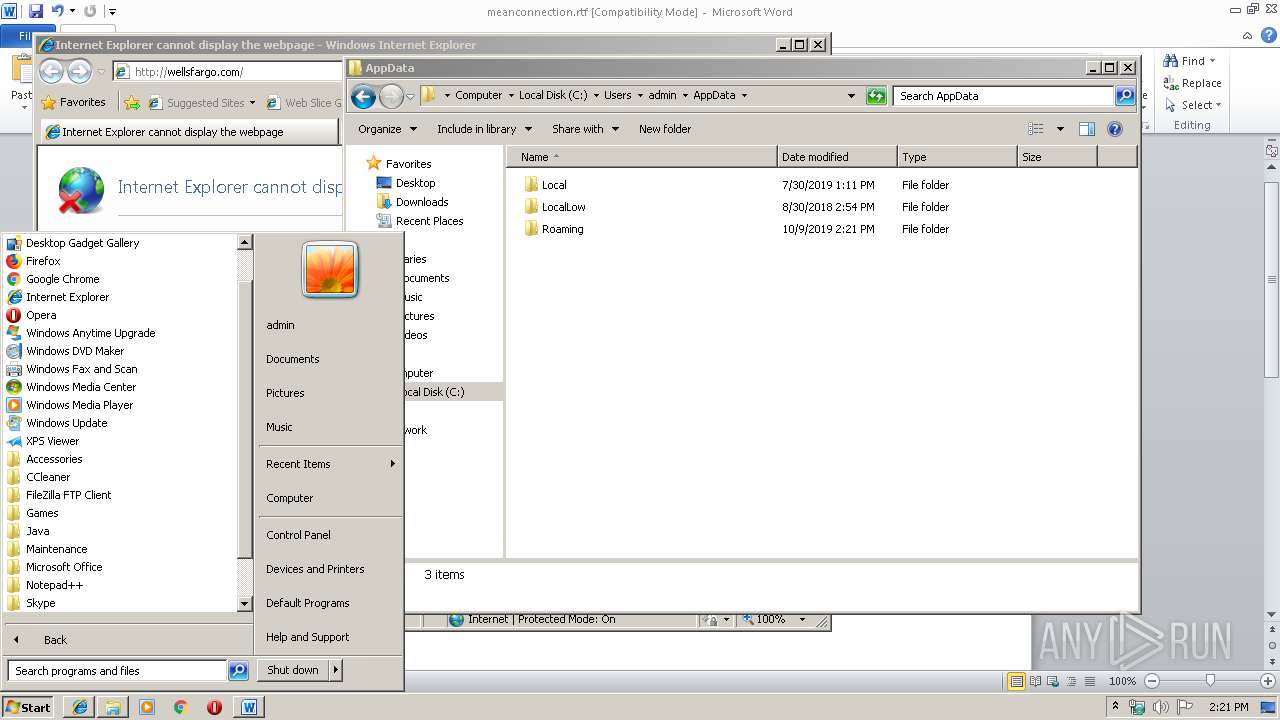
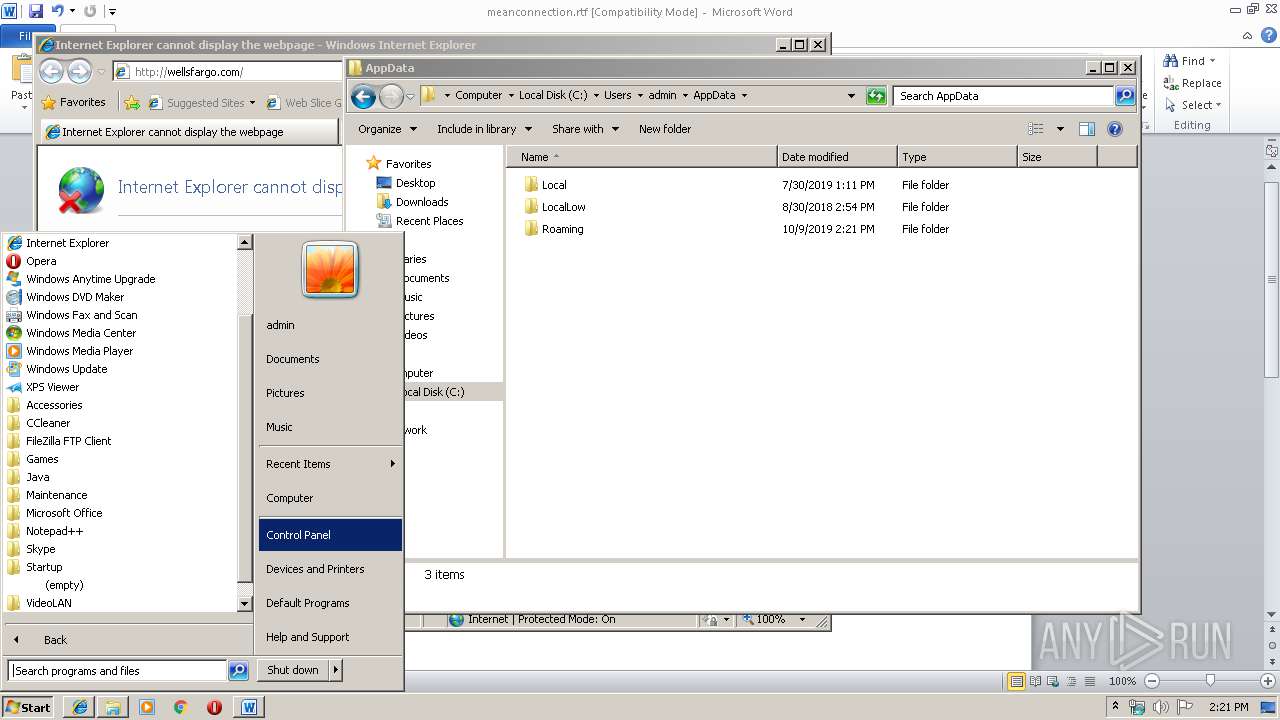
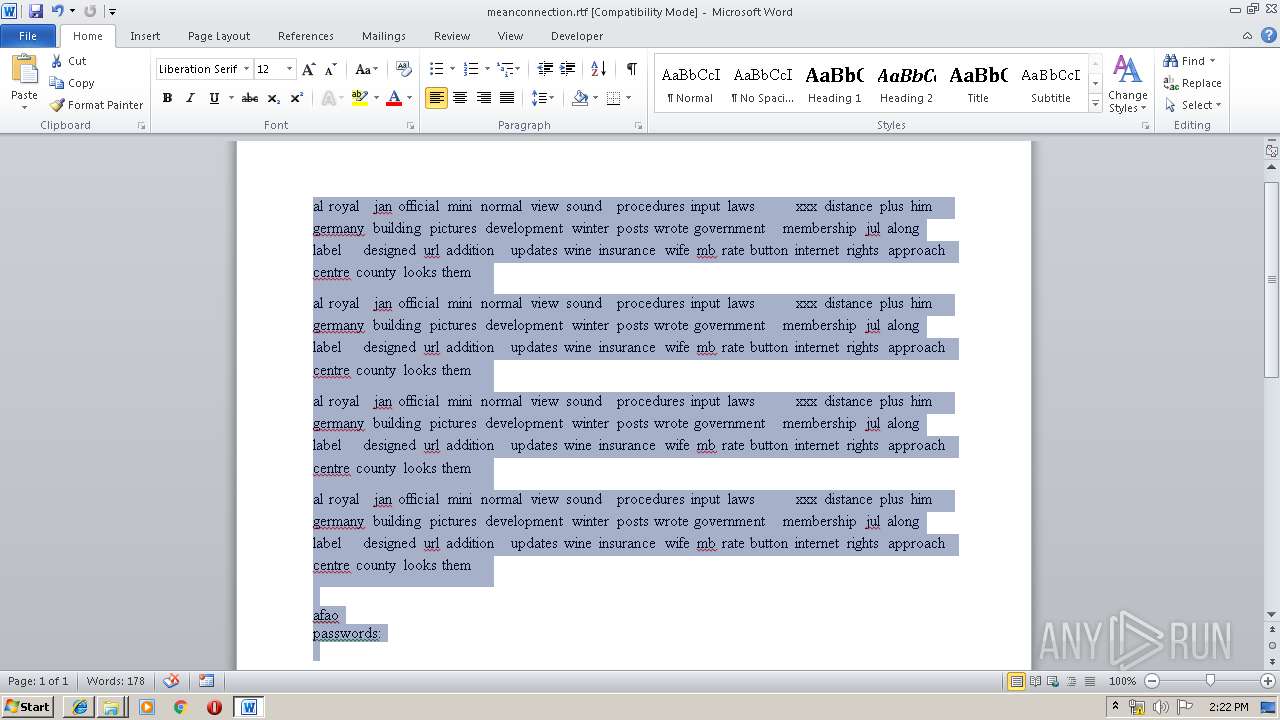
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
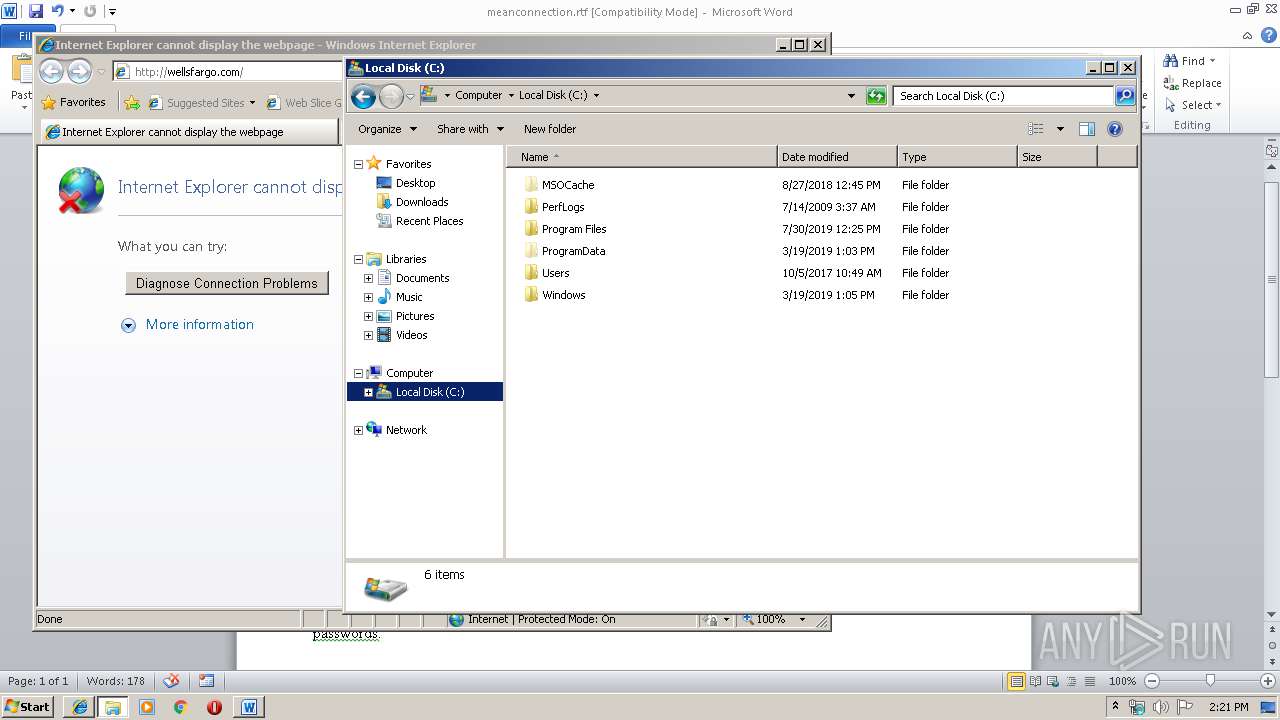
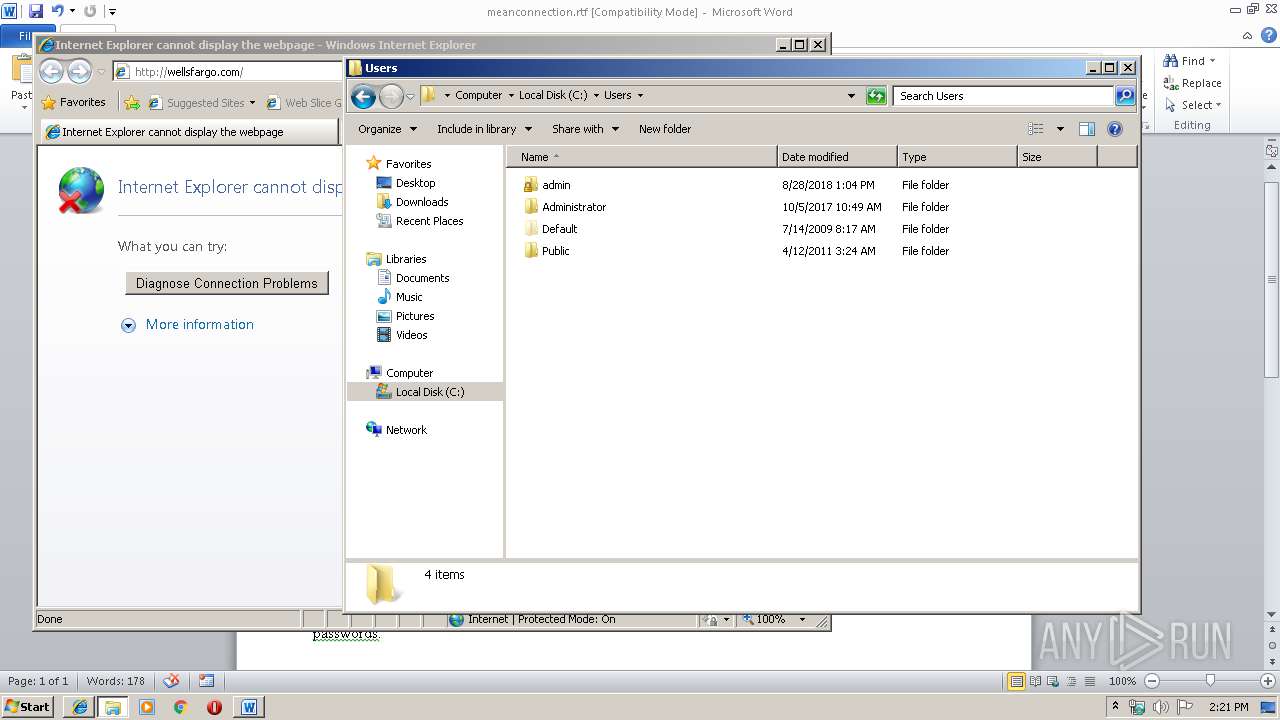
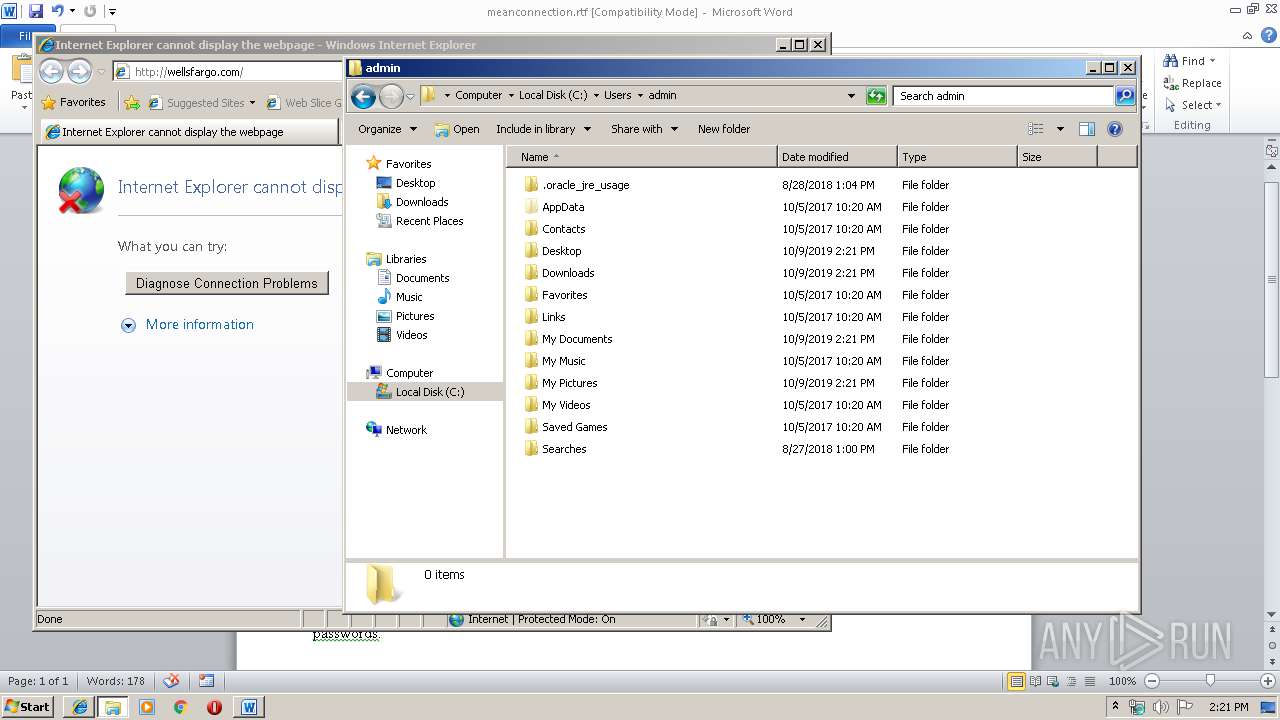
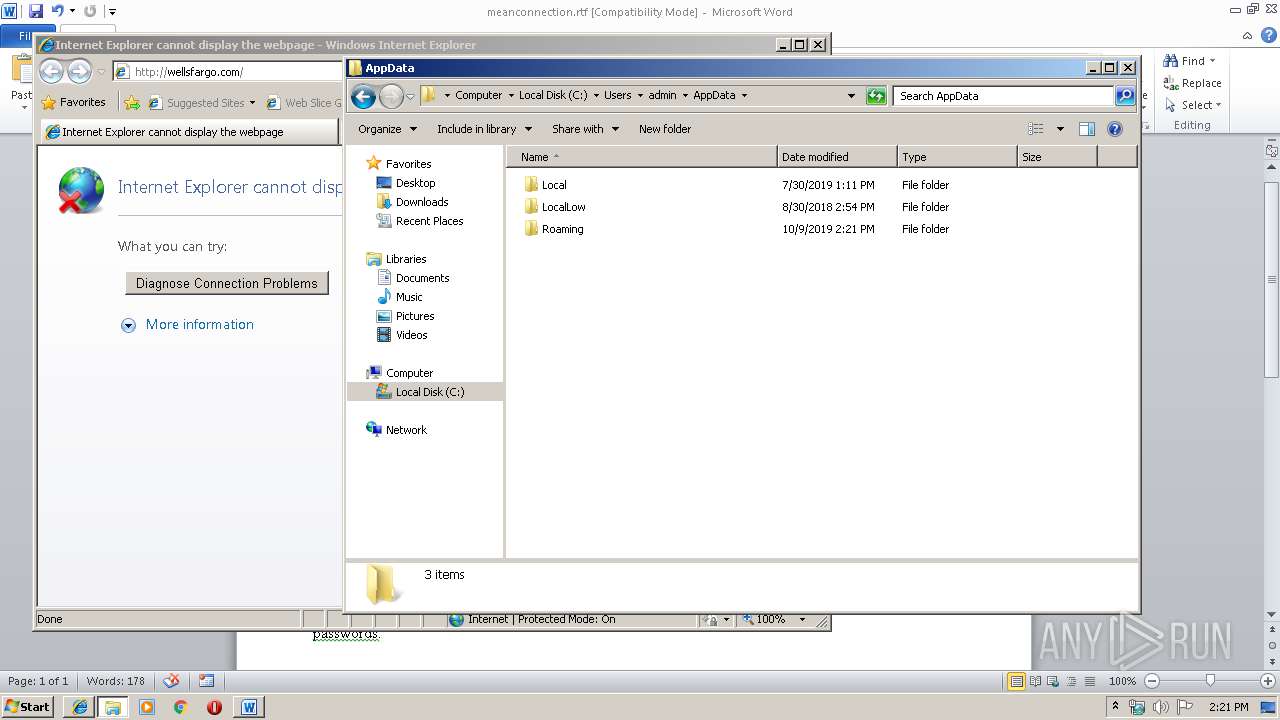
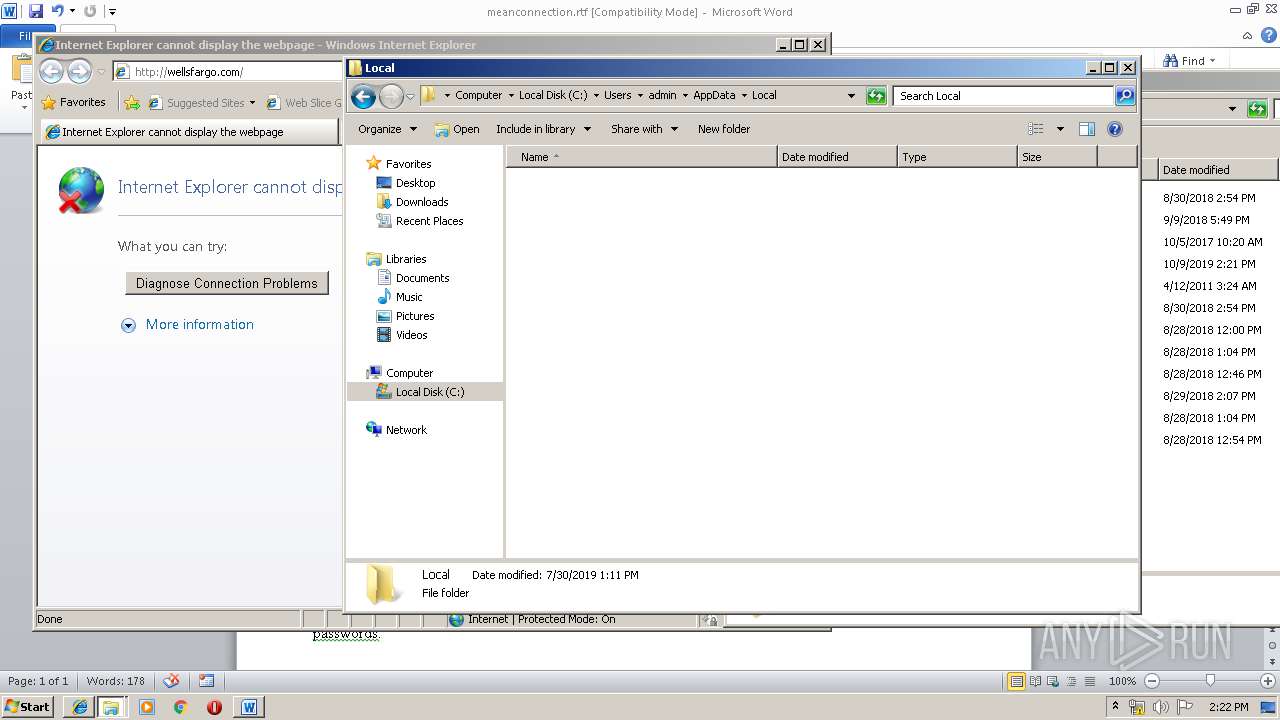
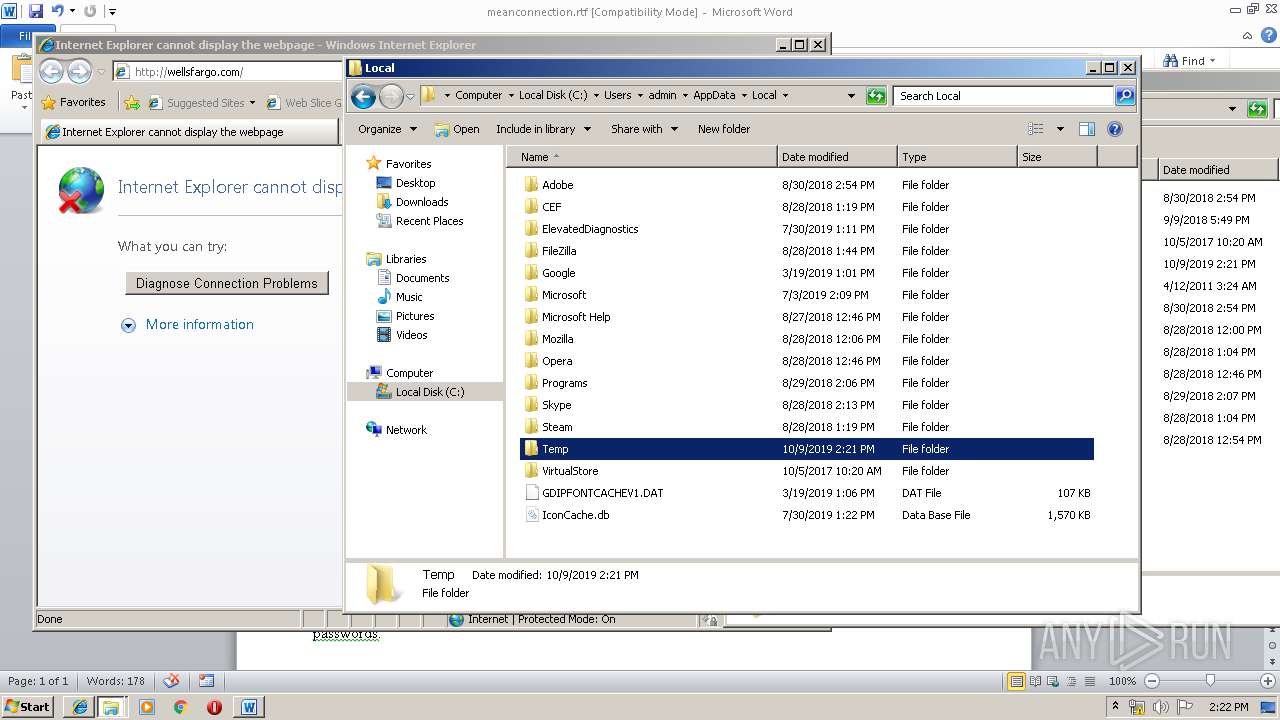
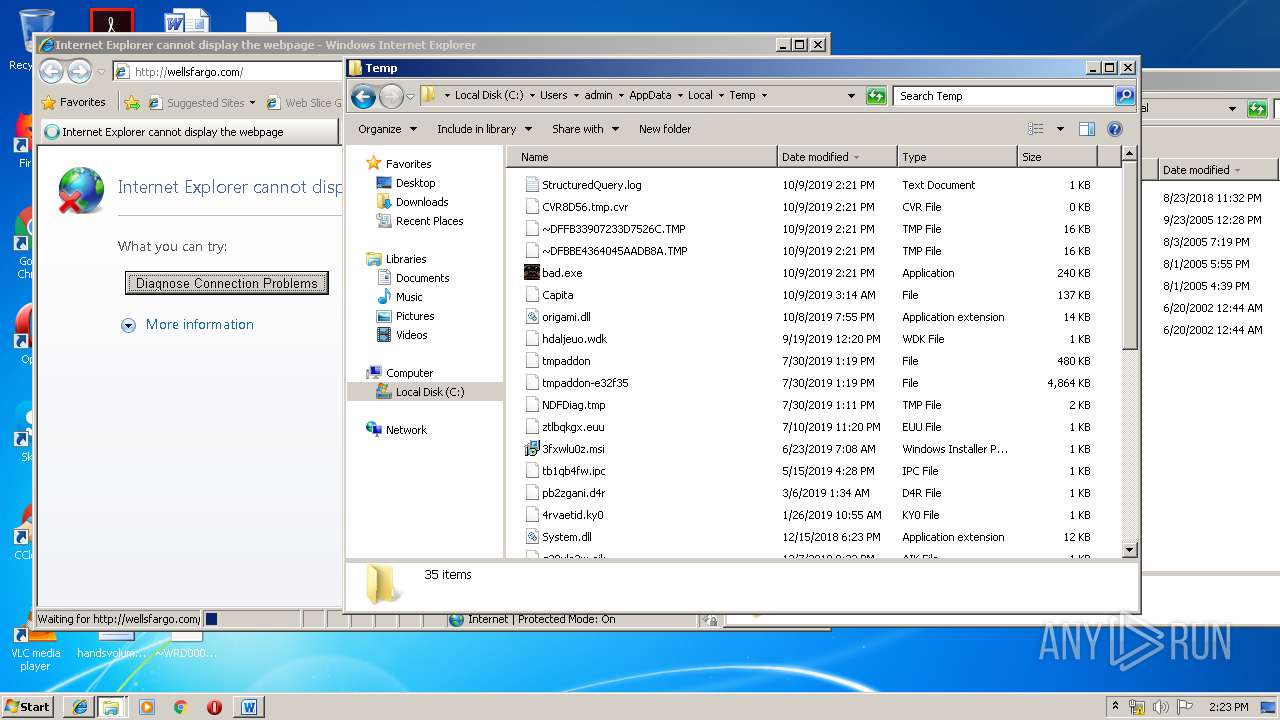
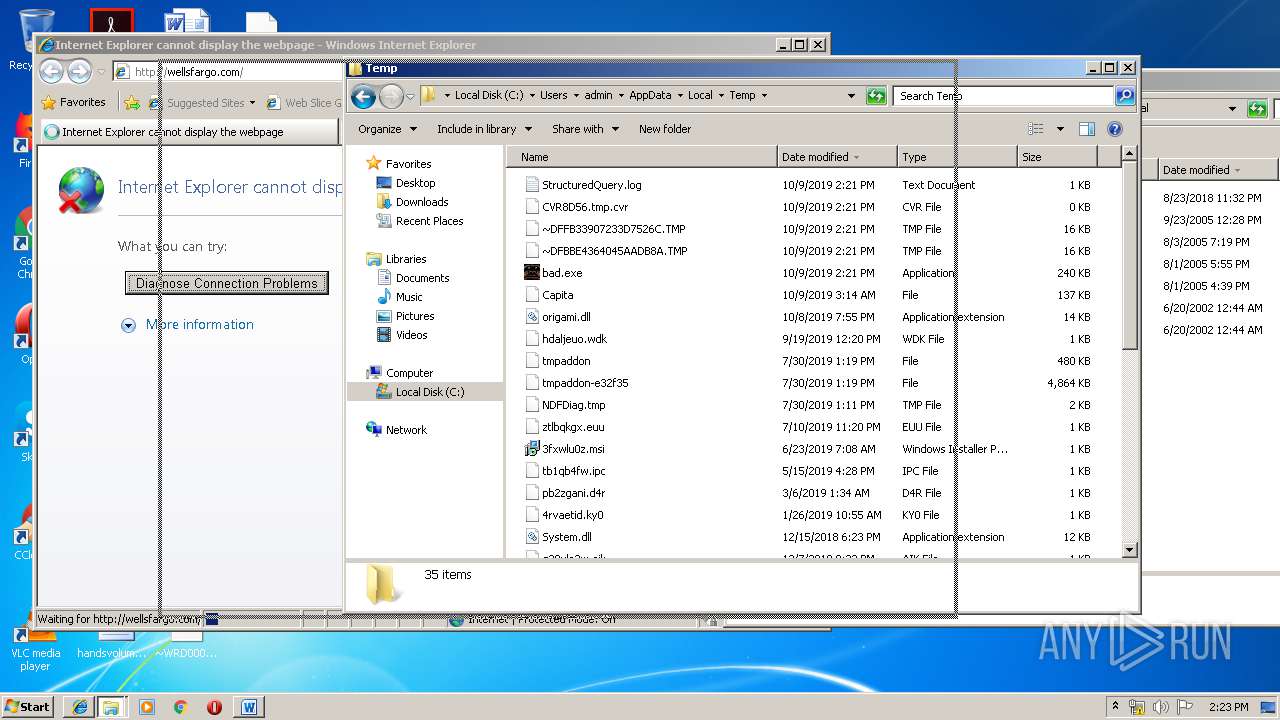
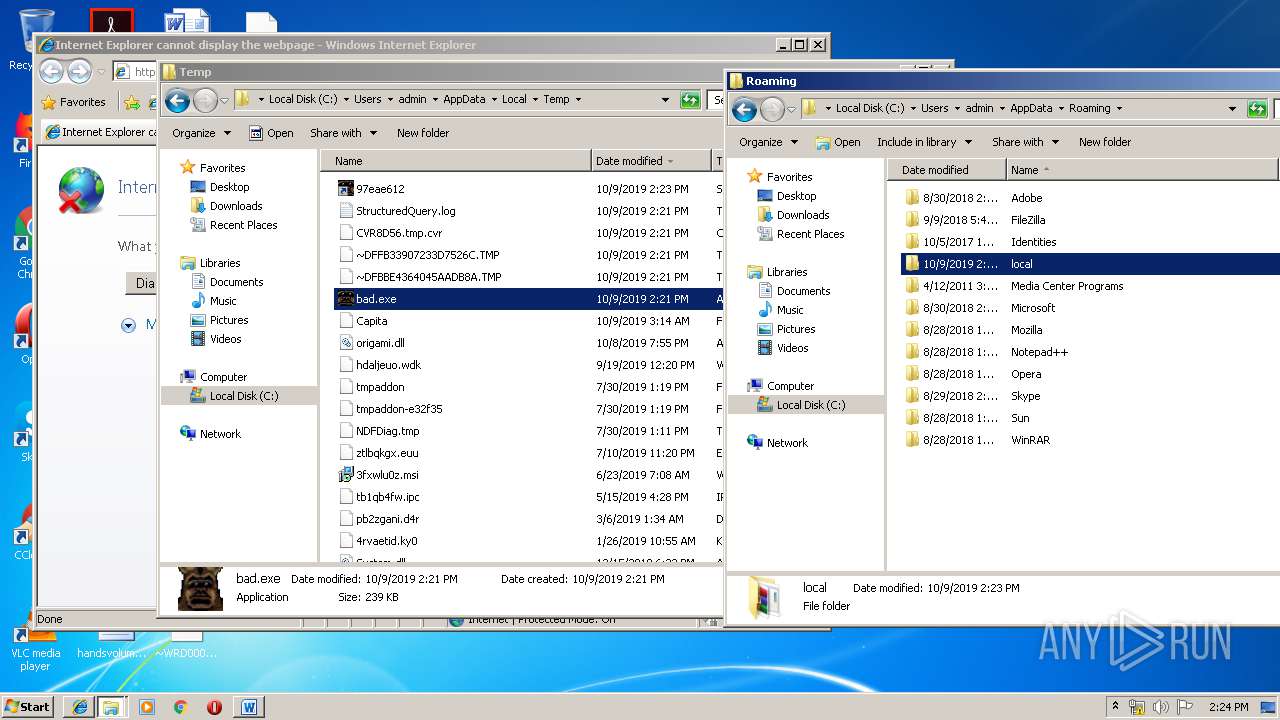
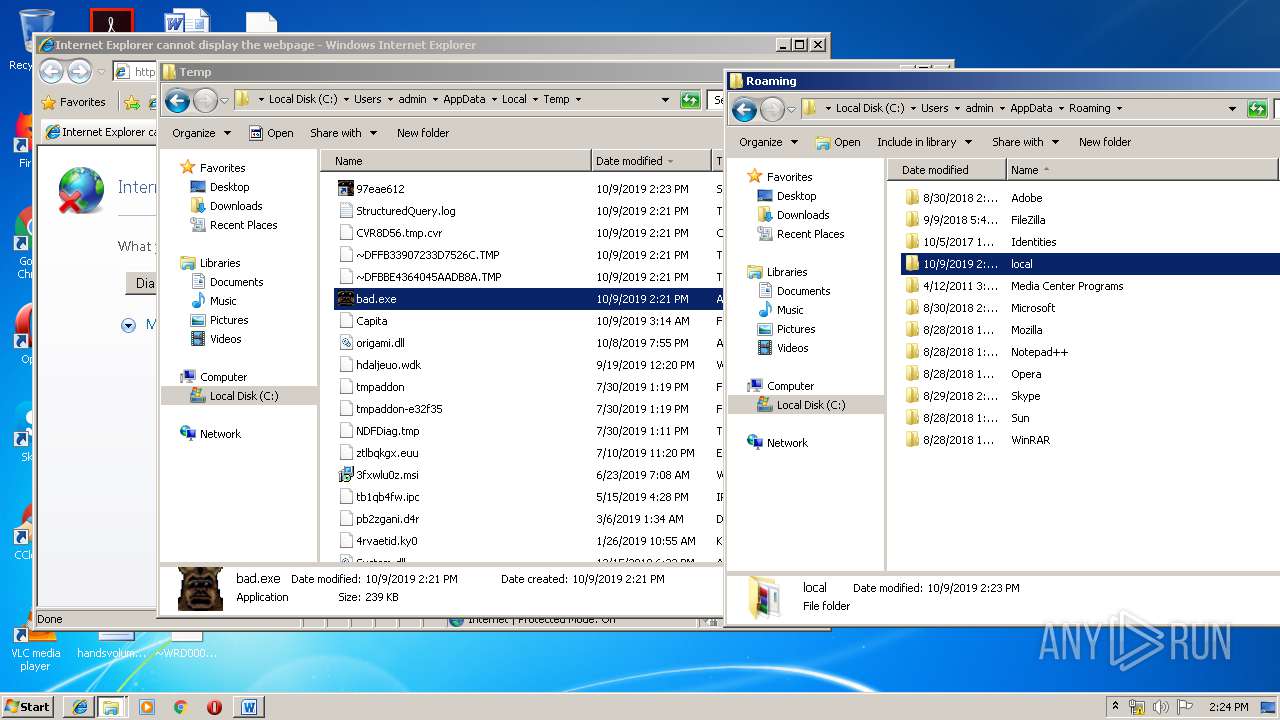
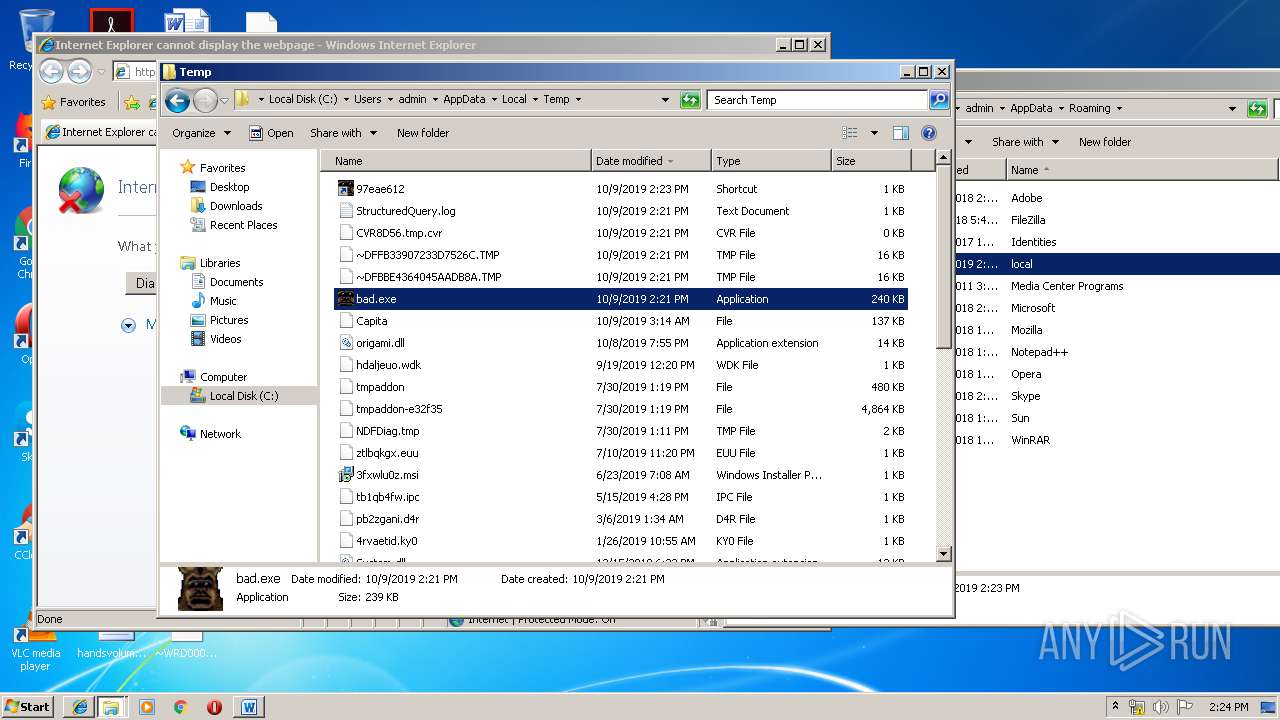
| 3148 | "C:\Users\admin\AppData\Local\Temp\bad.exe" | C:\Users\admin\AppData\Local\Temp\bad.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
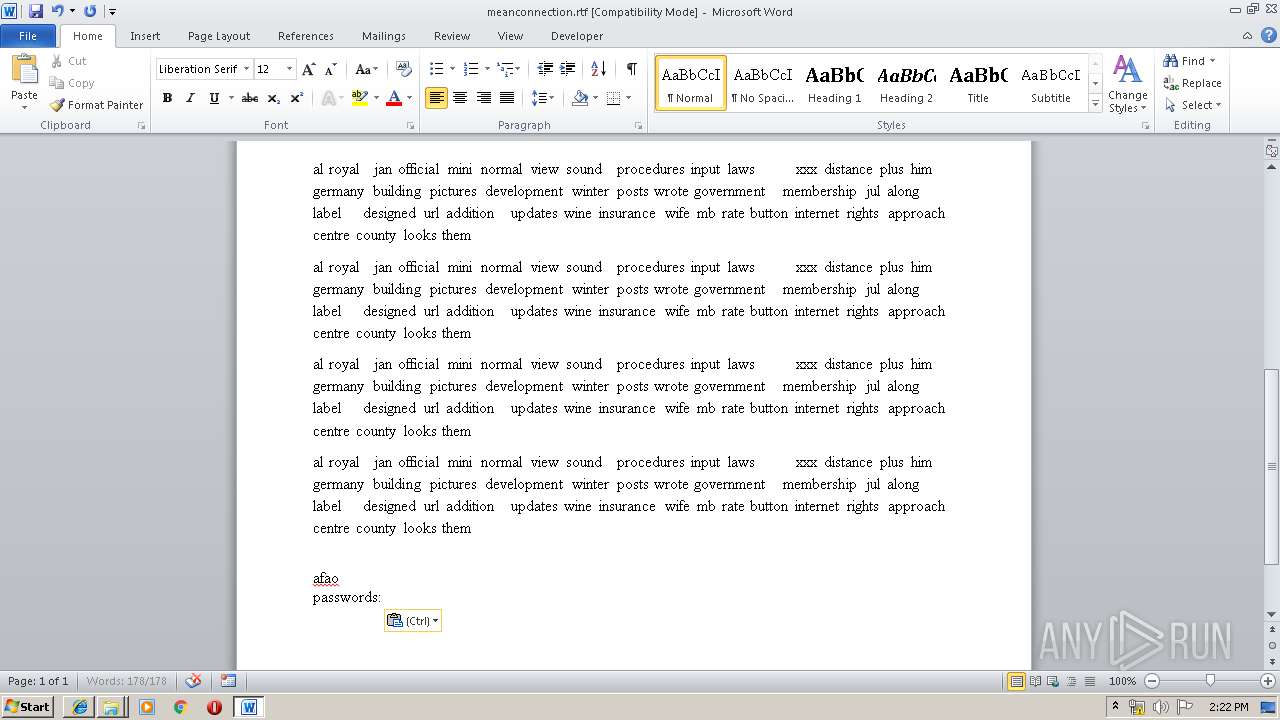
Total events
366
Read events
366
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
1
Text files
6
Unknown types
0
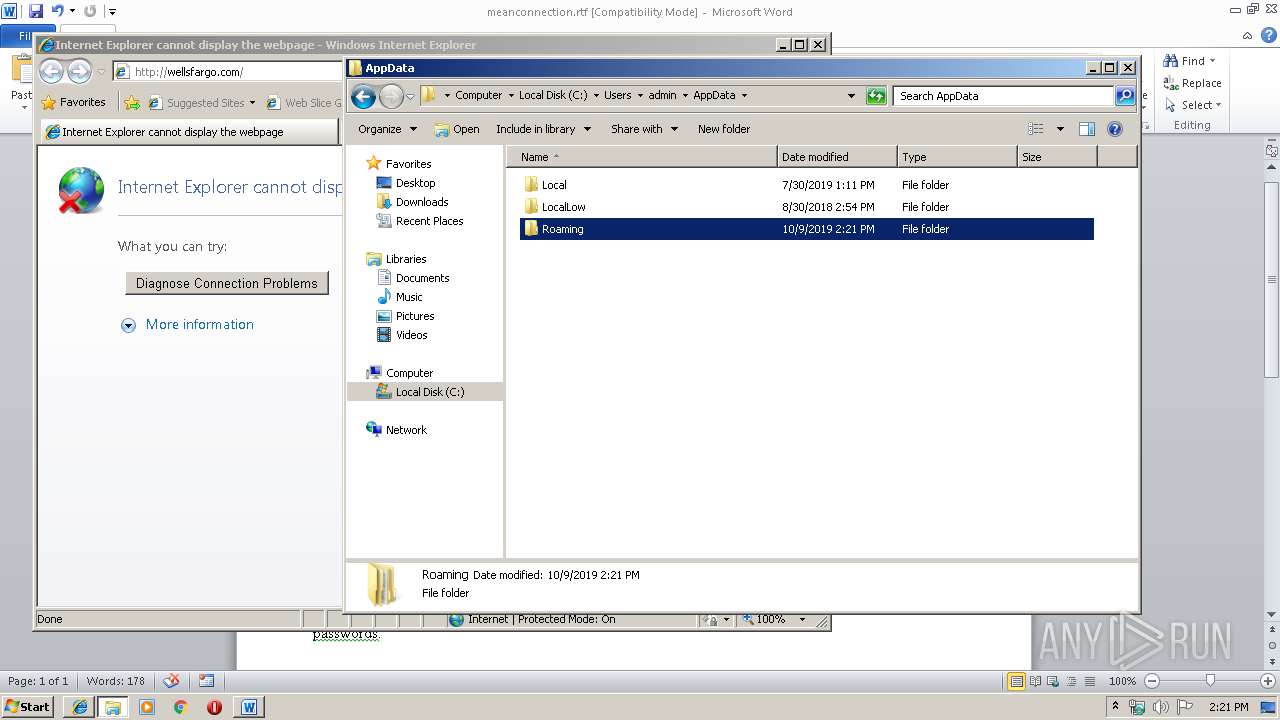
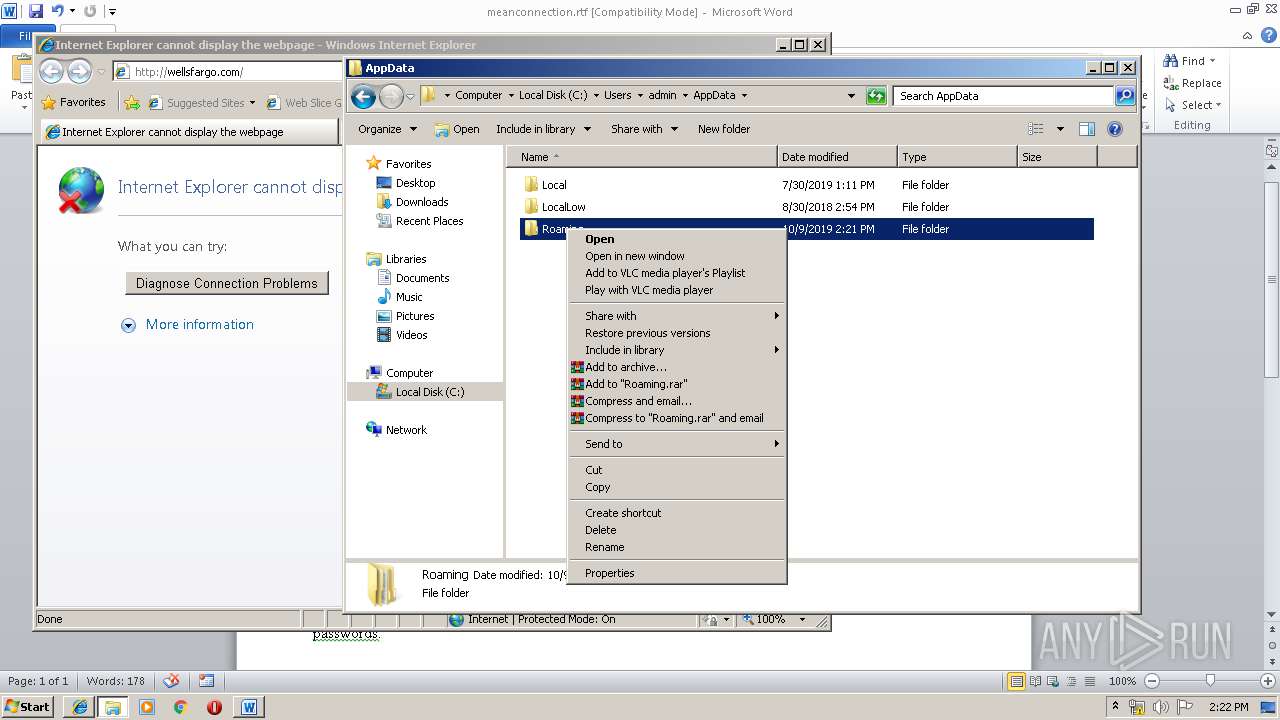
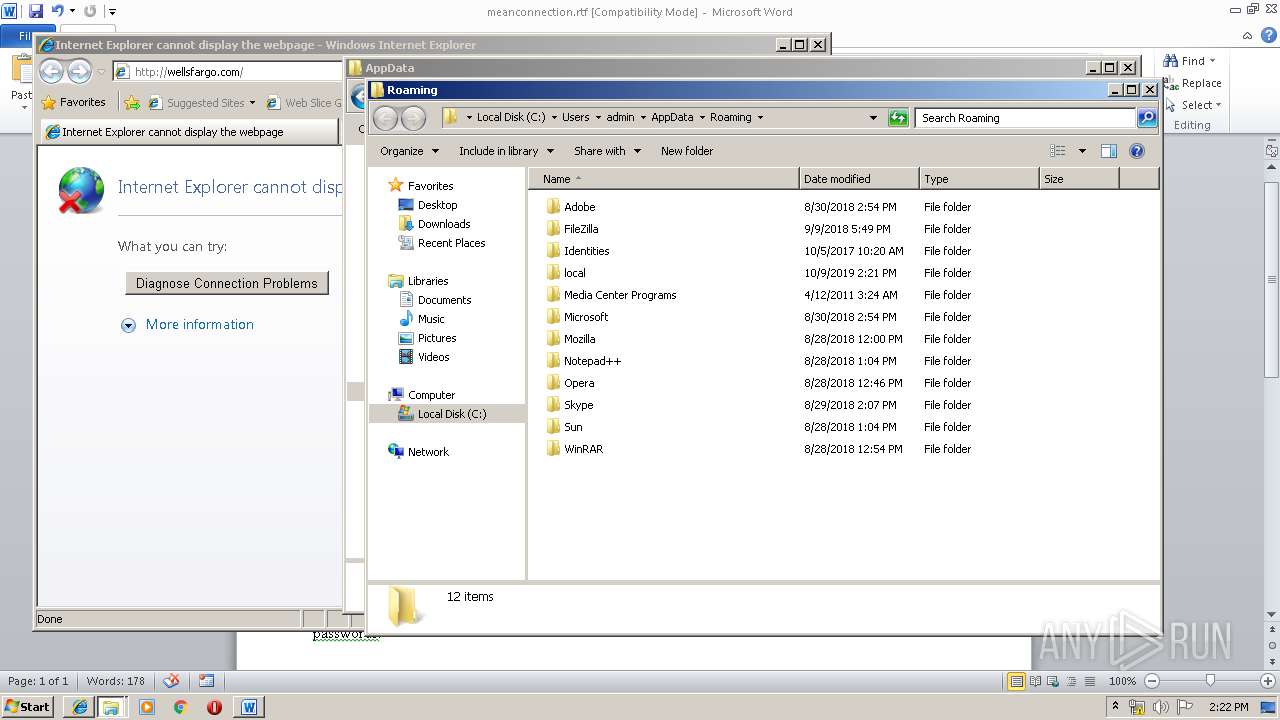
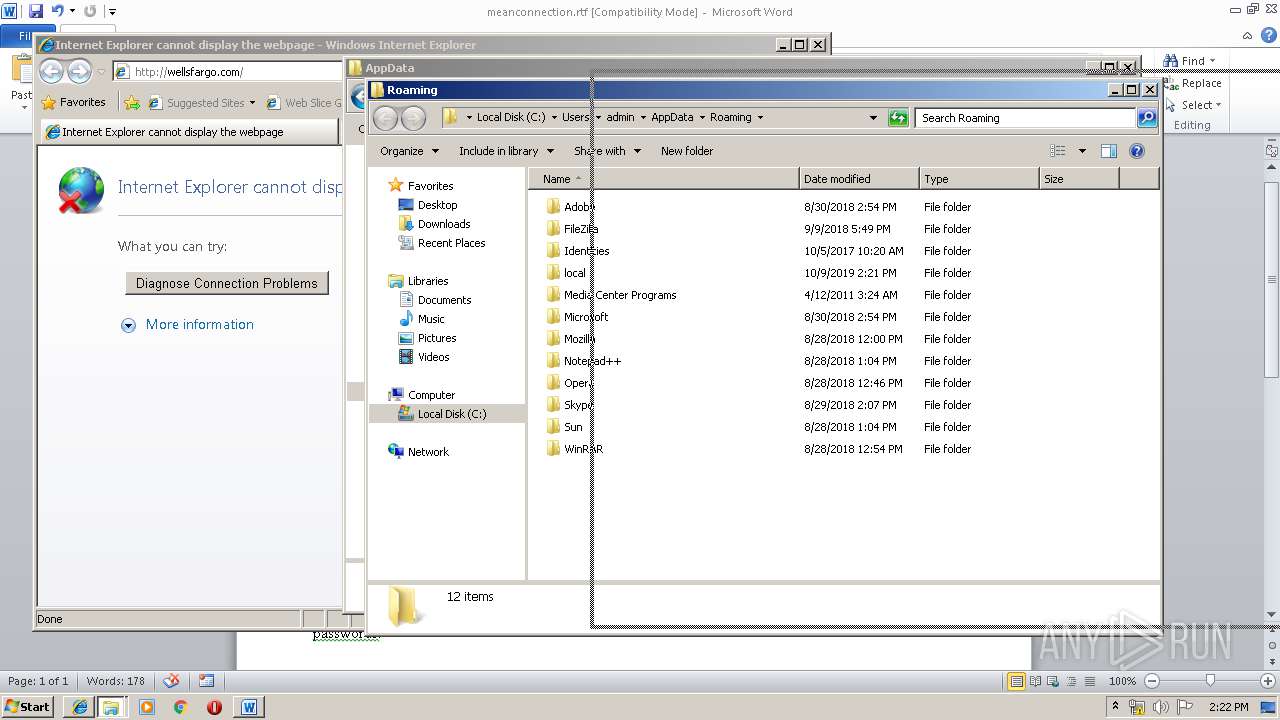
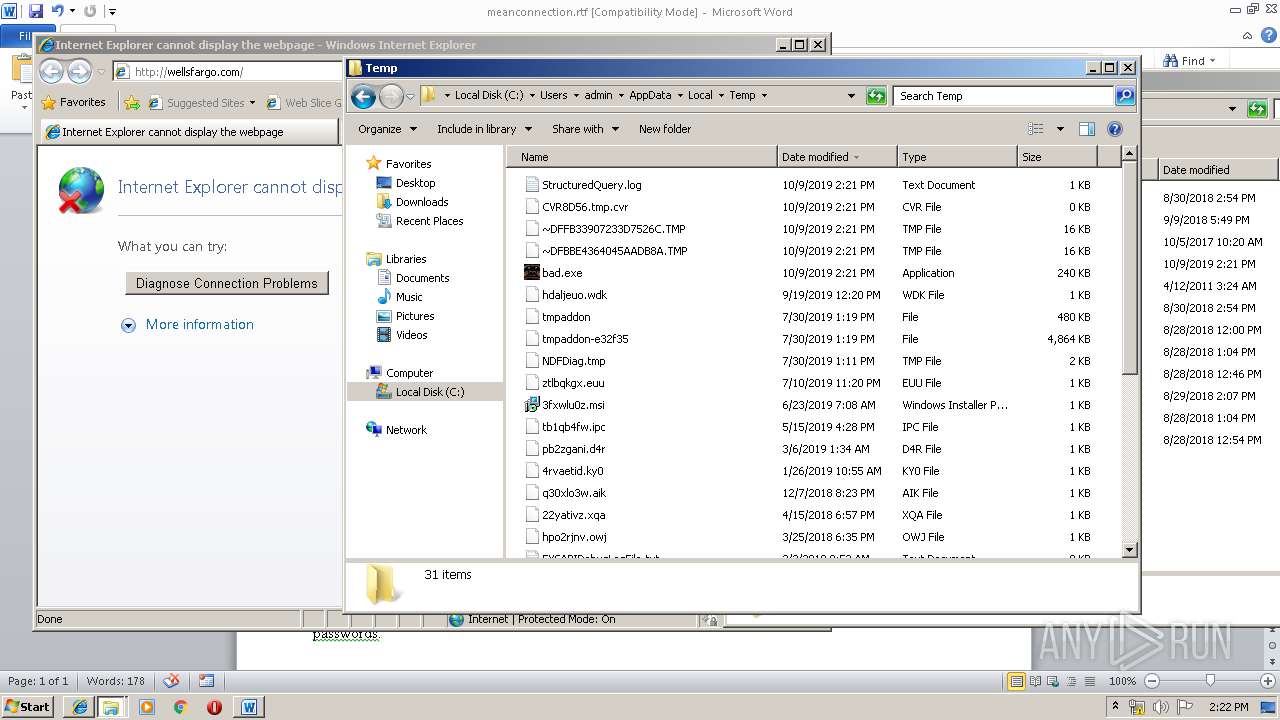
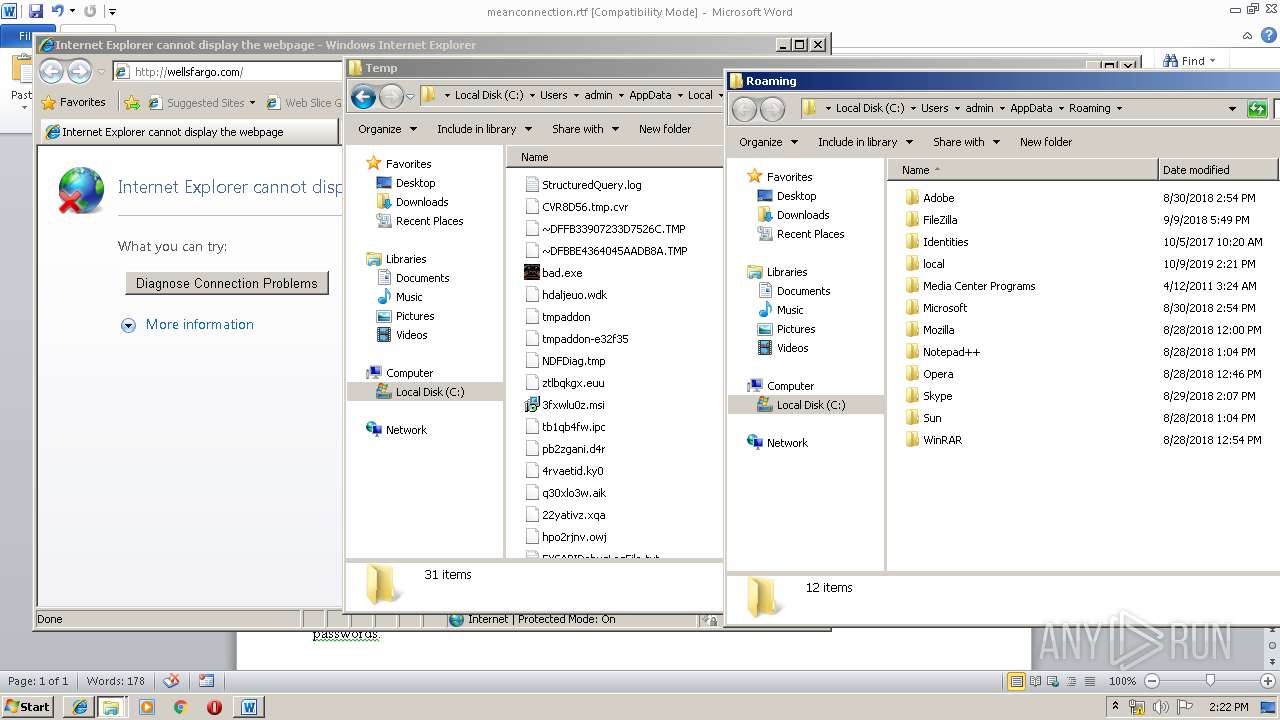
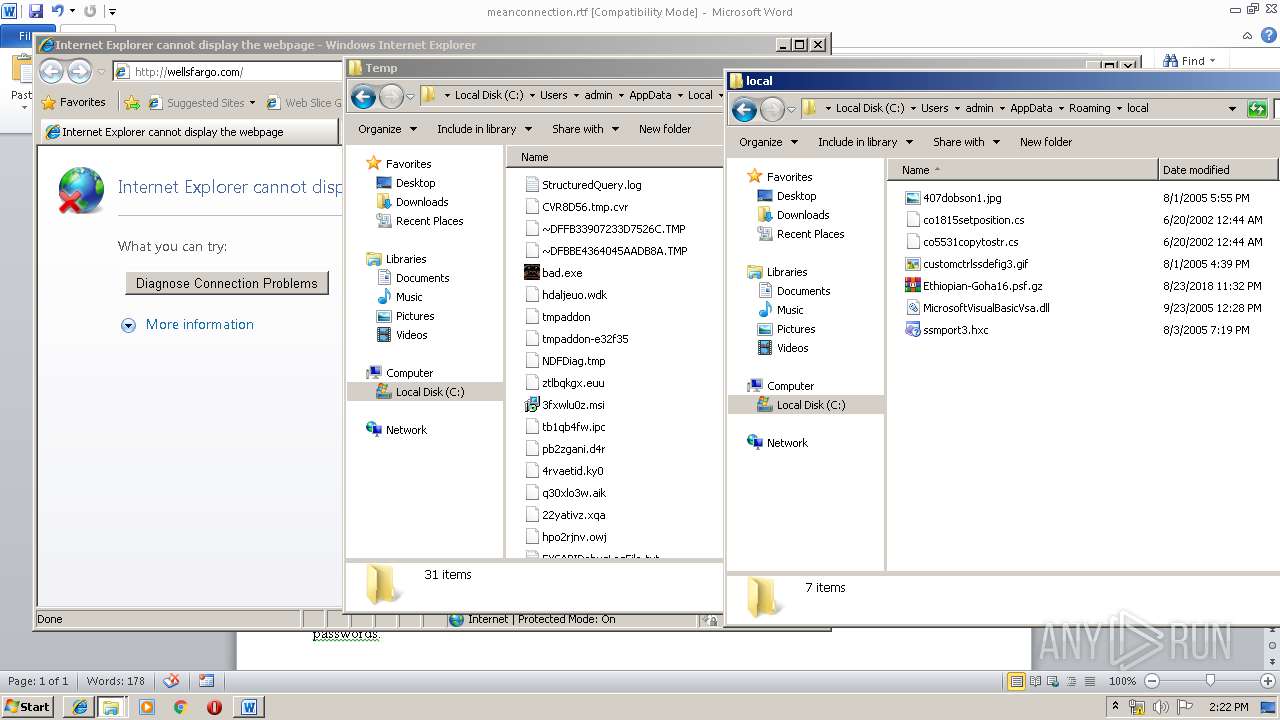
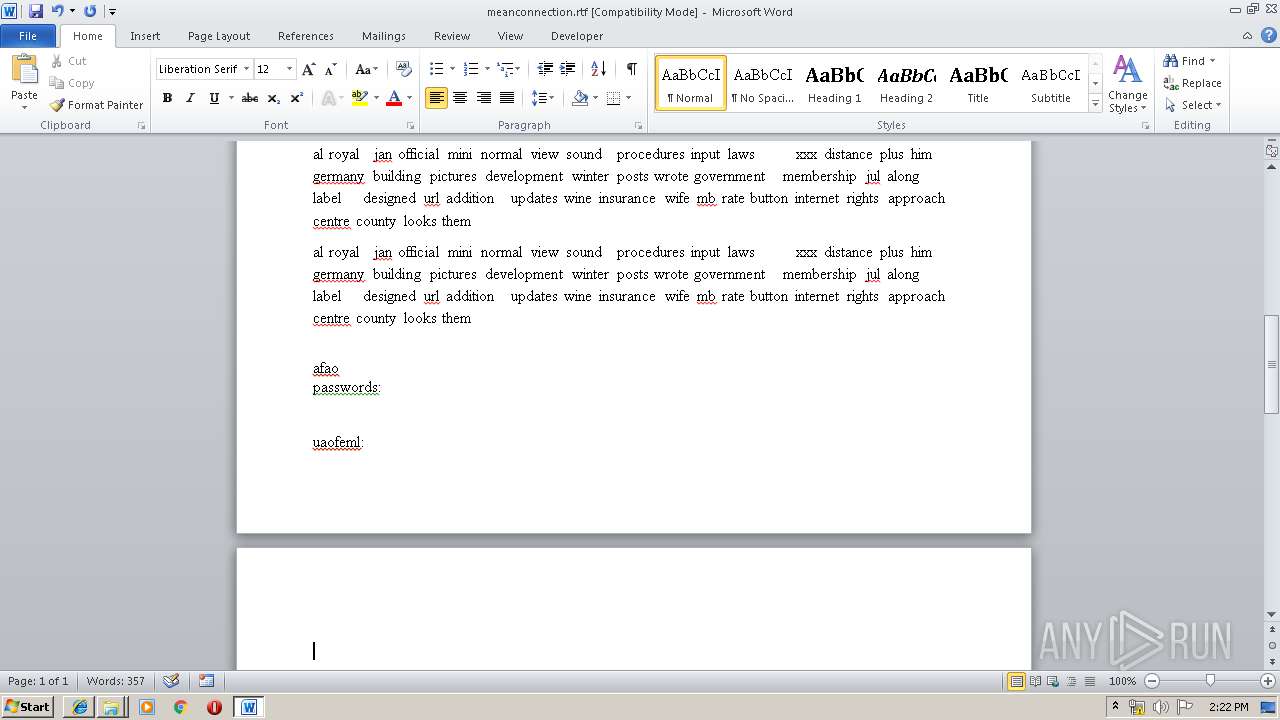
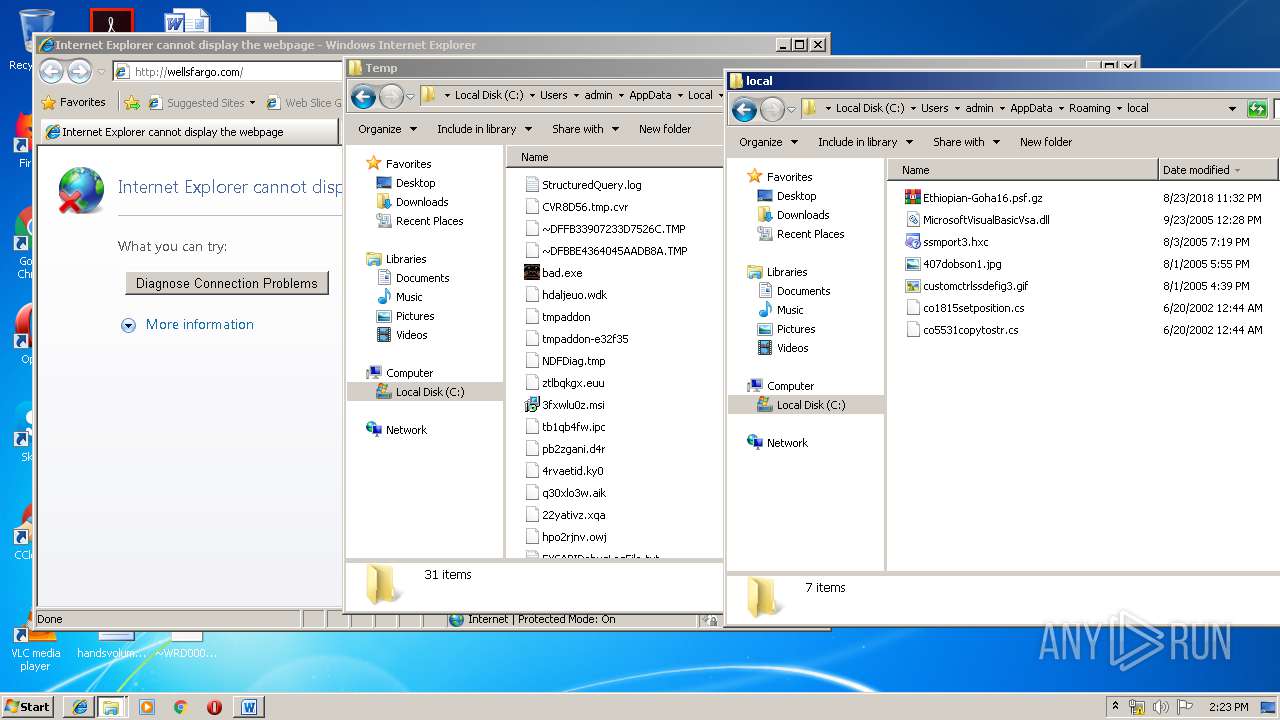
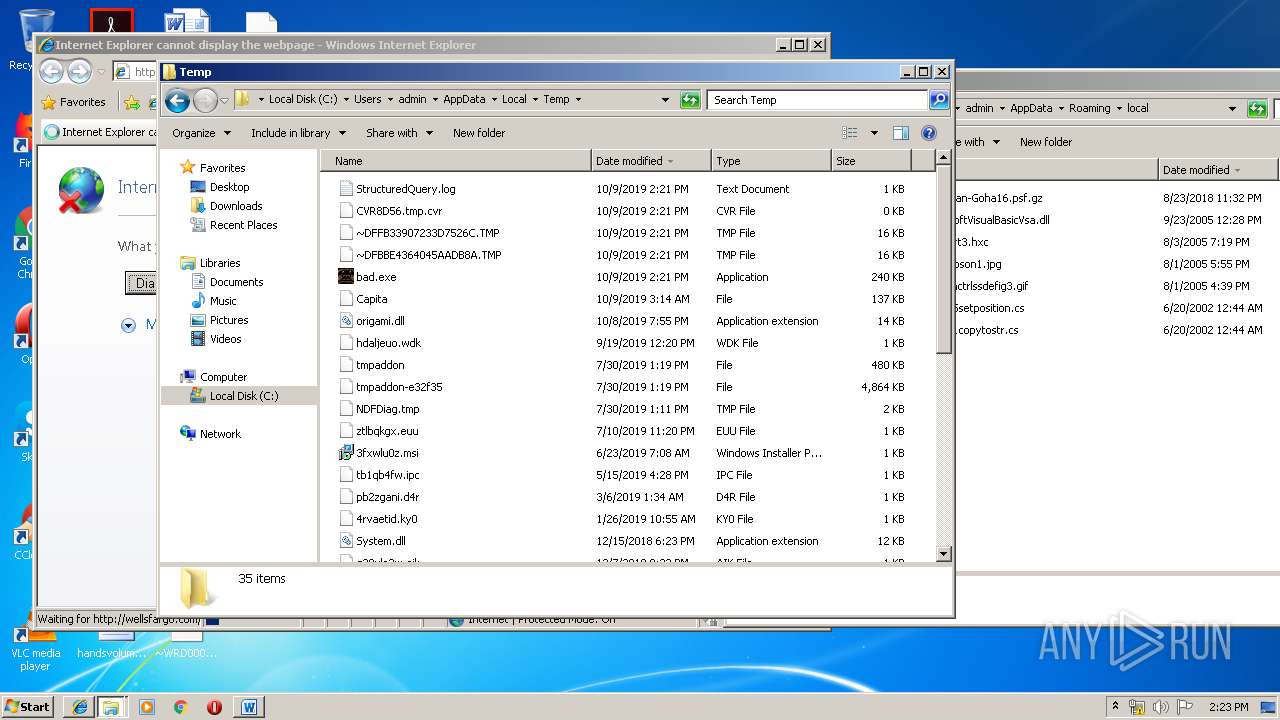
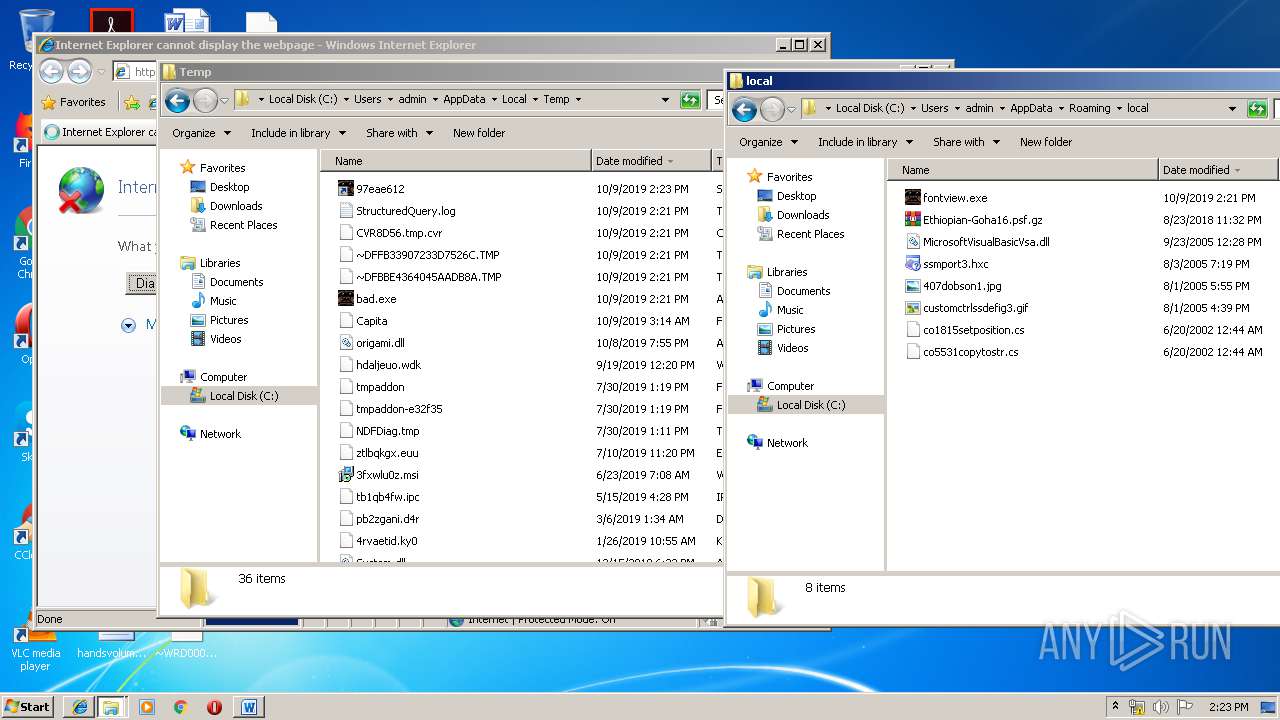
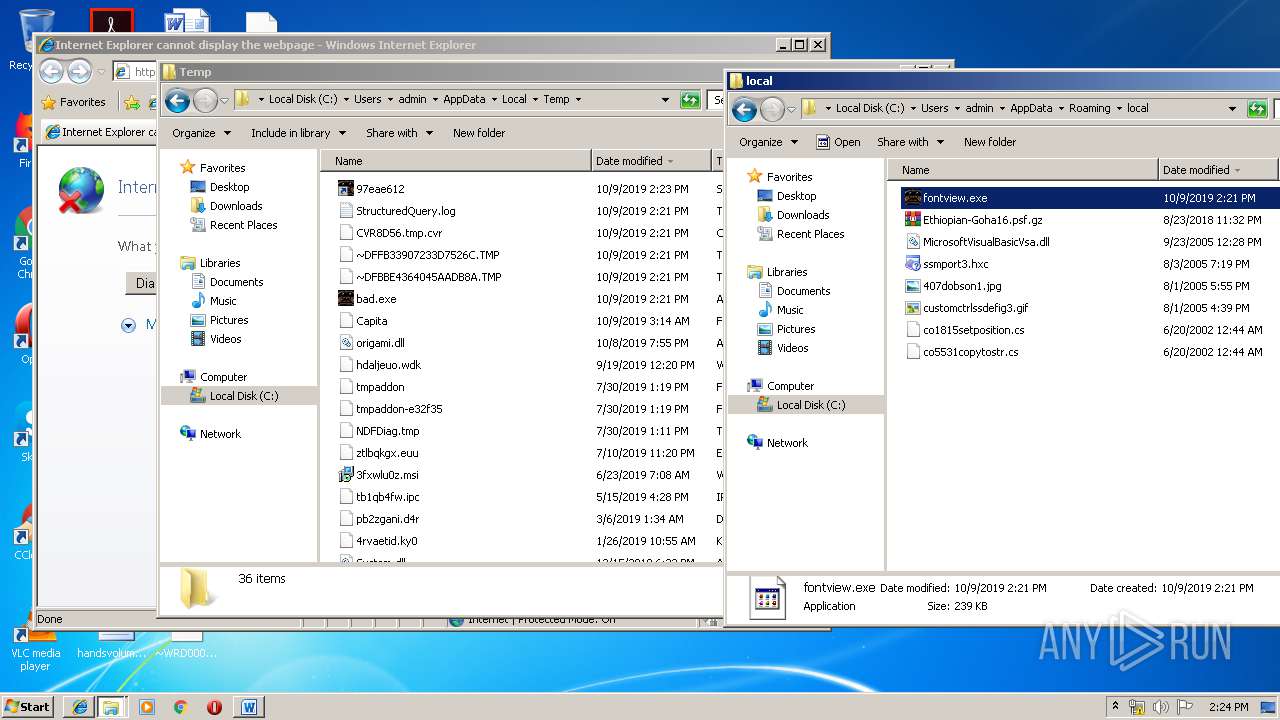
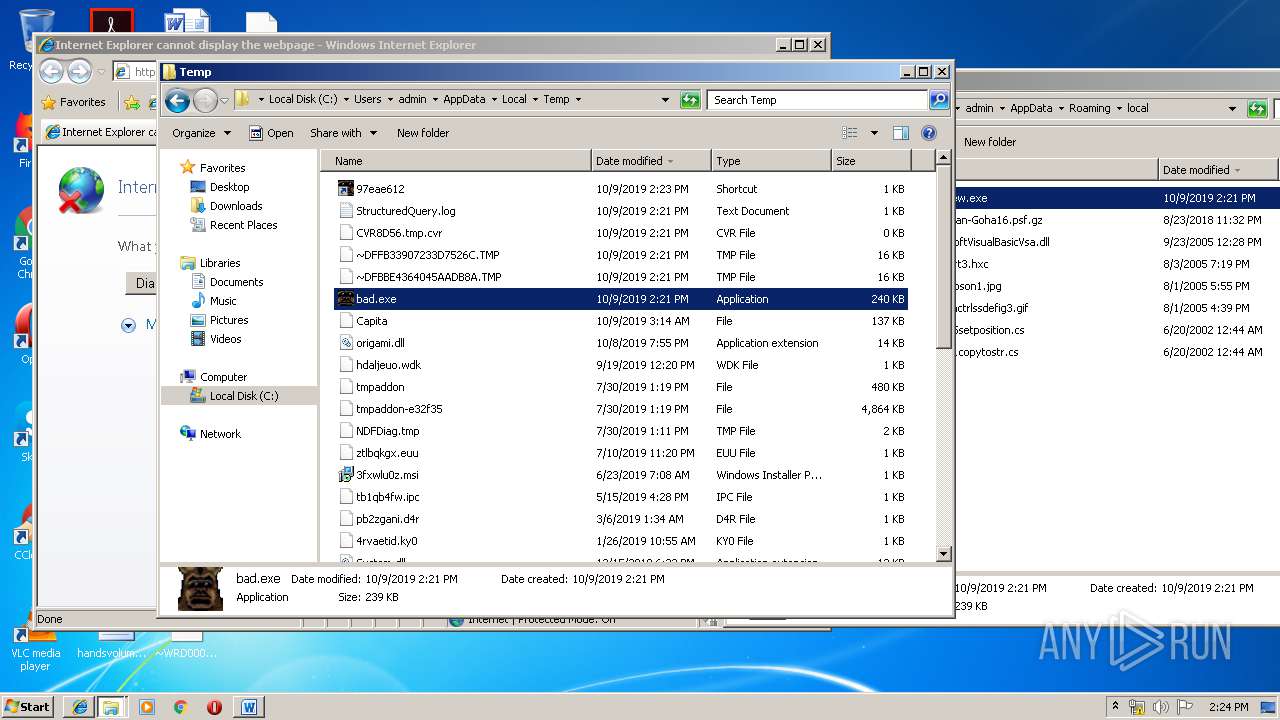
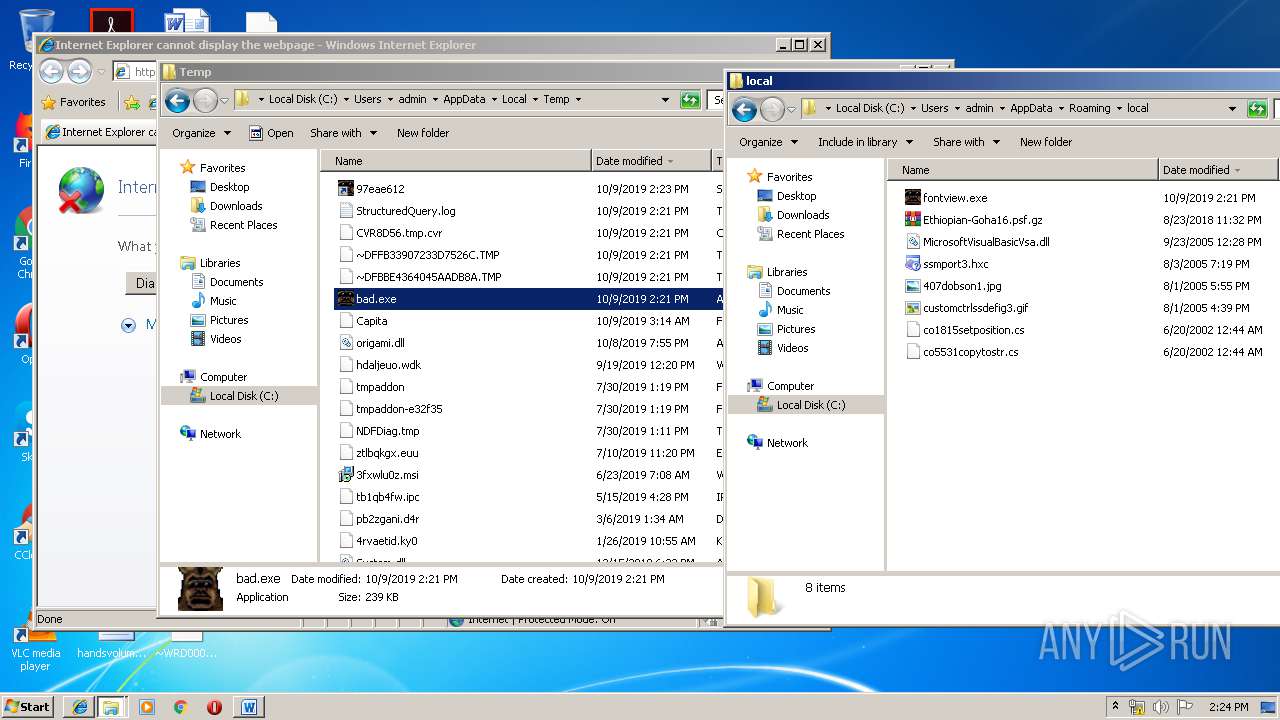
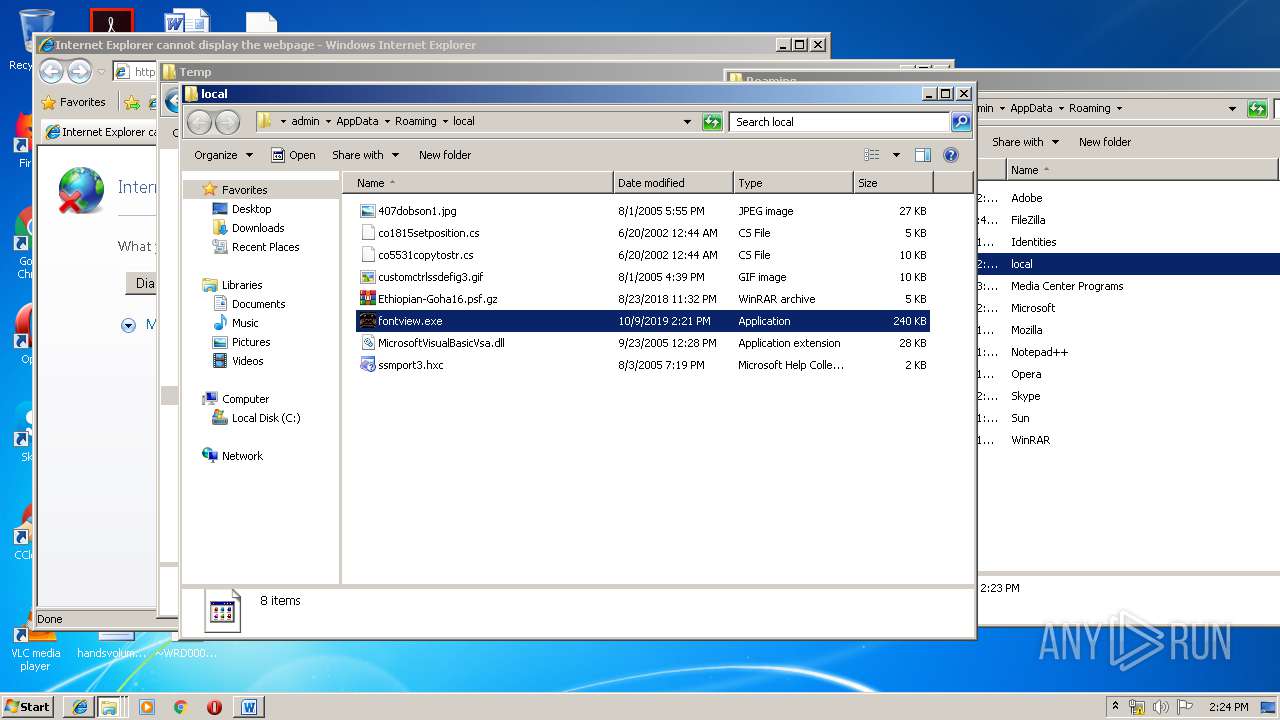
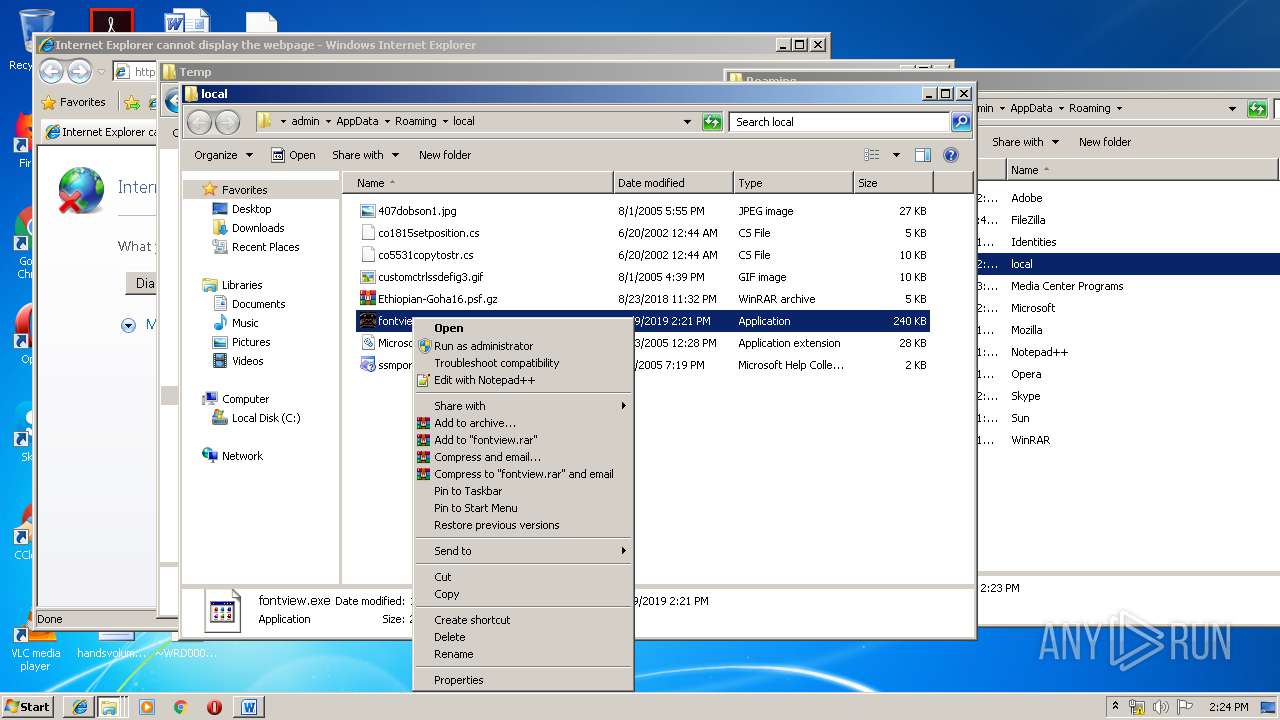
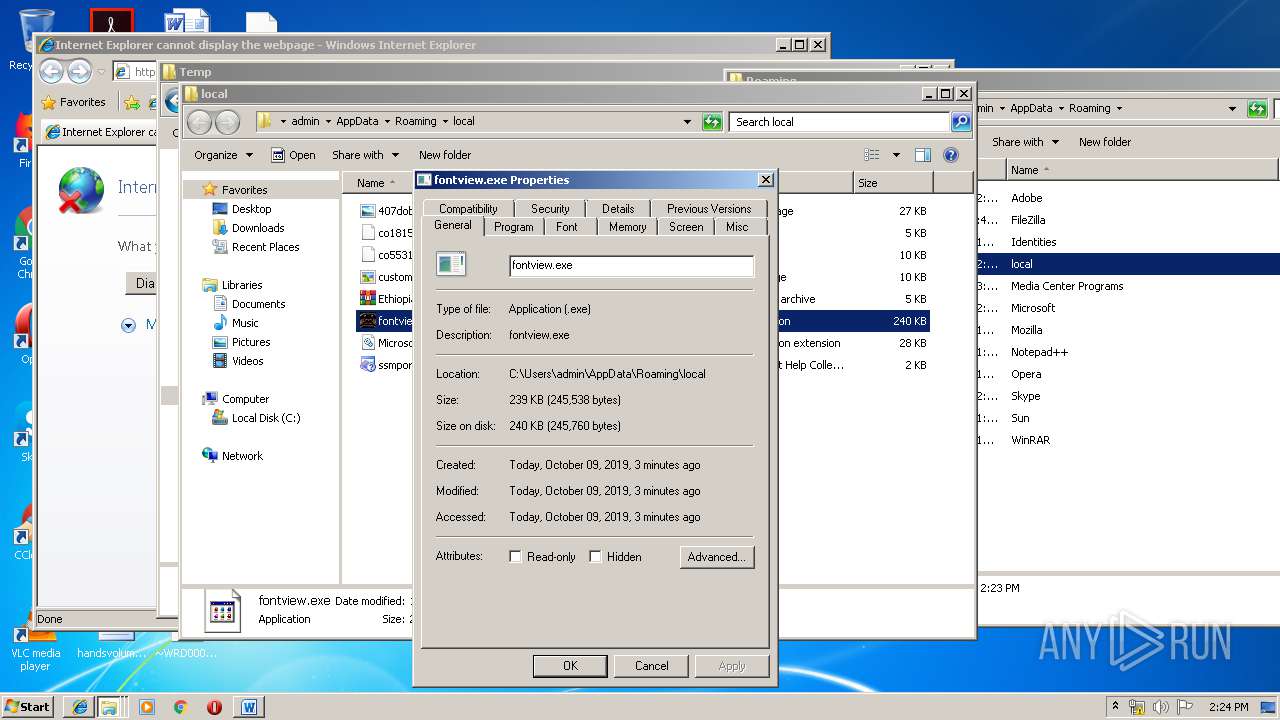
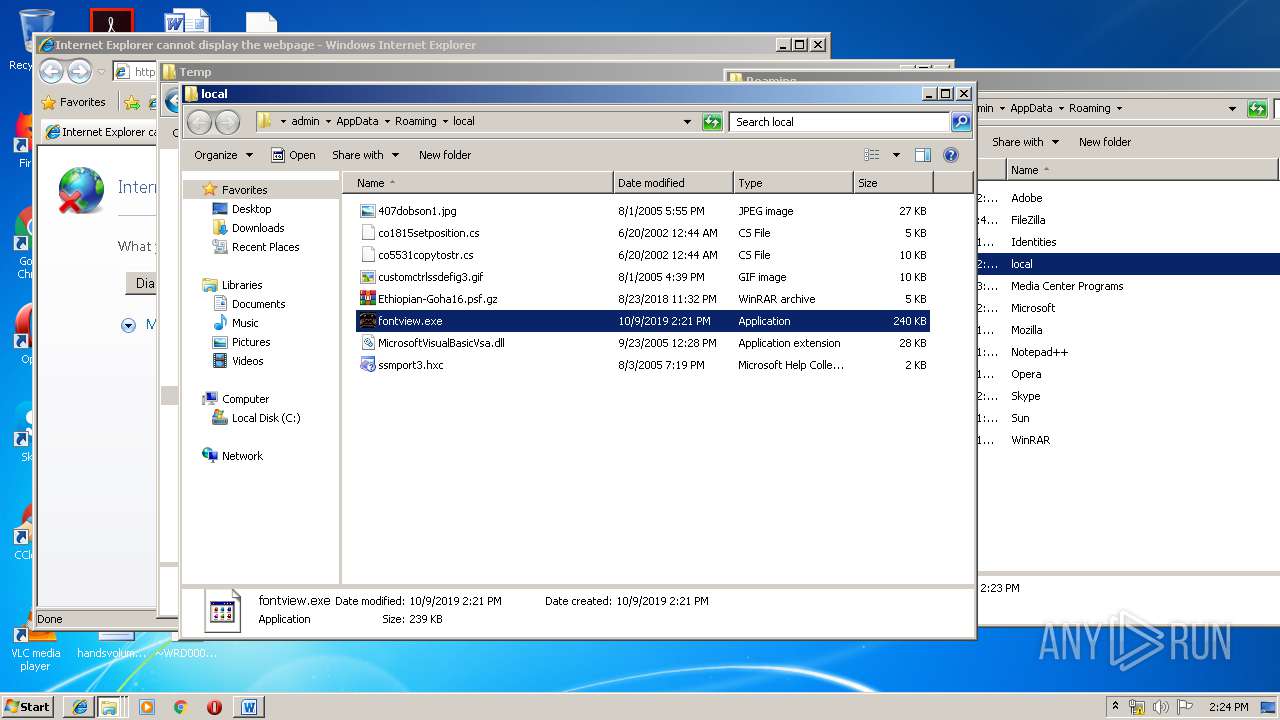
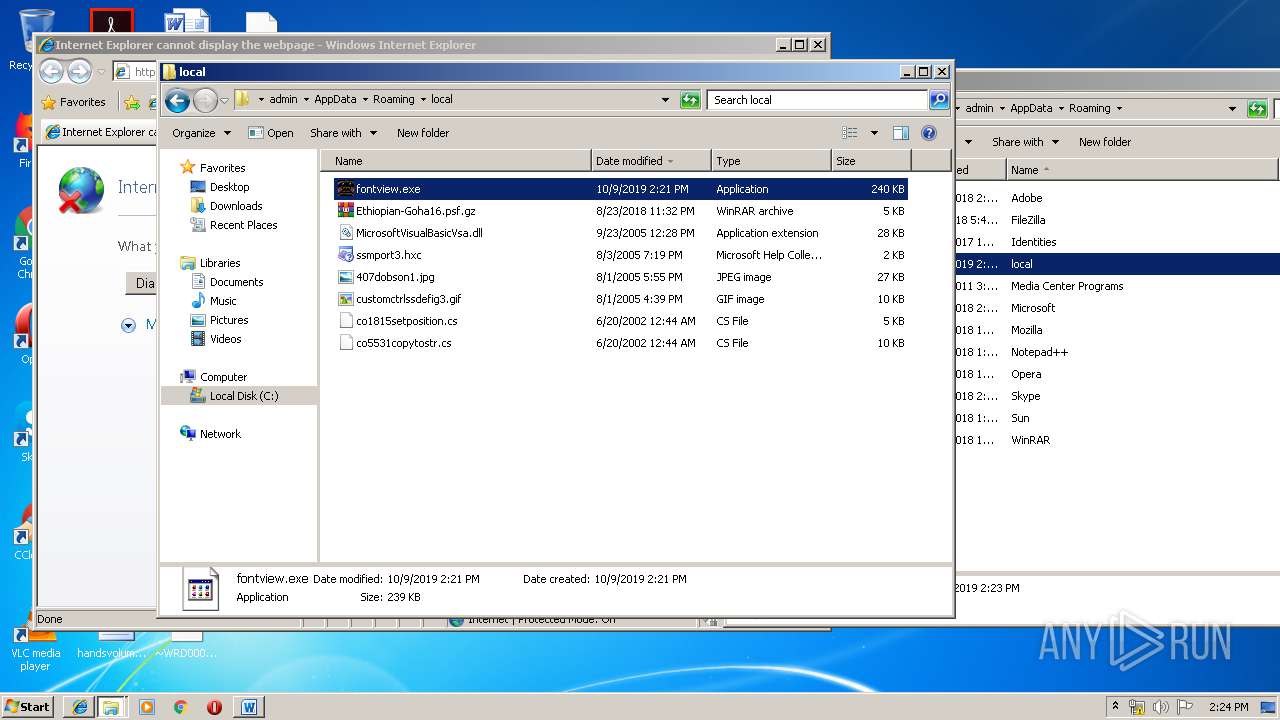
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
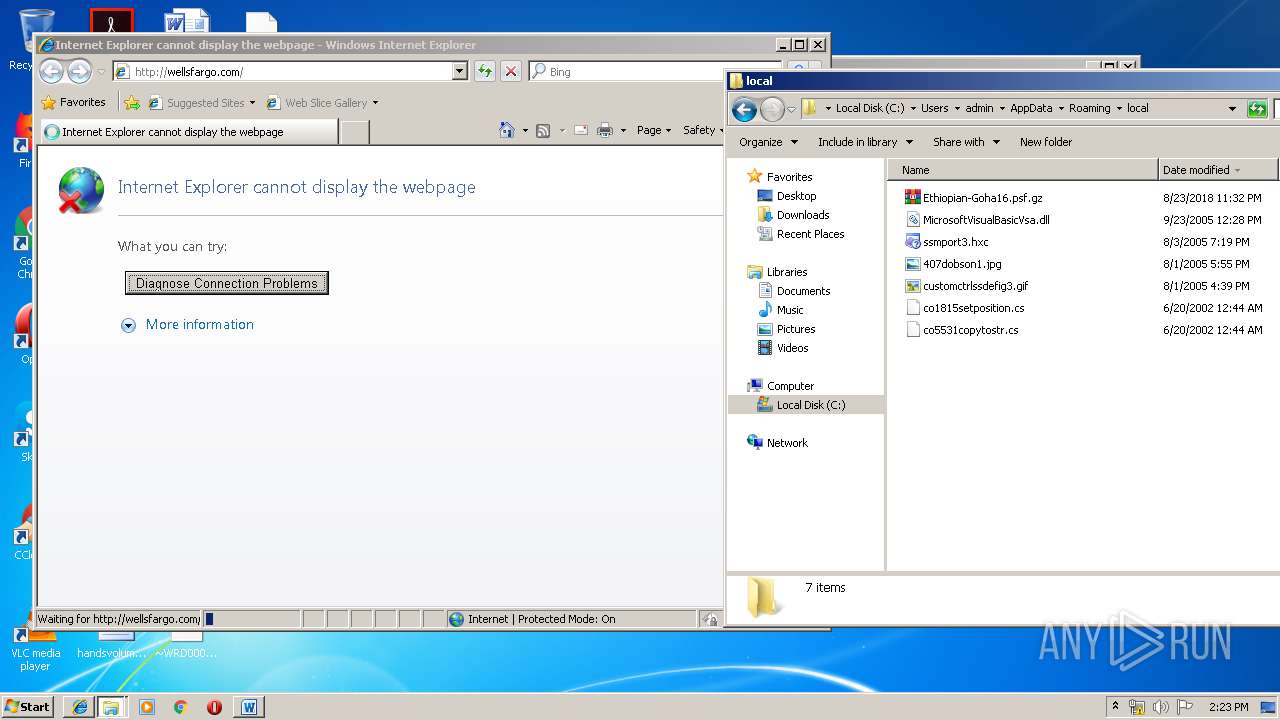
| 3148 | bad.exe | C:\Users\admin\AppData\Local\Temp\nsj63E6.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
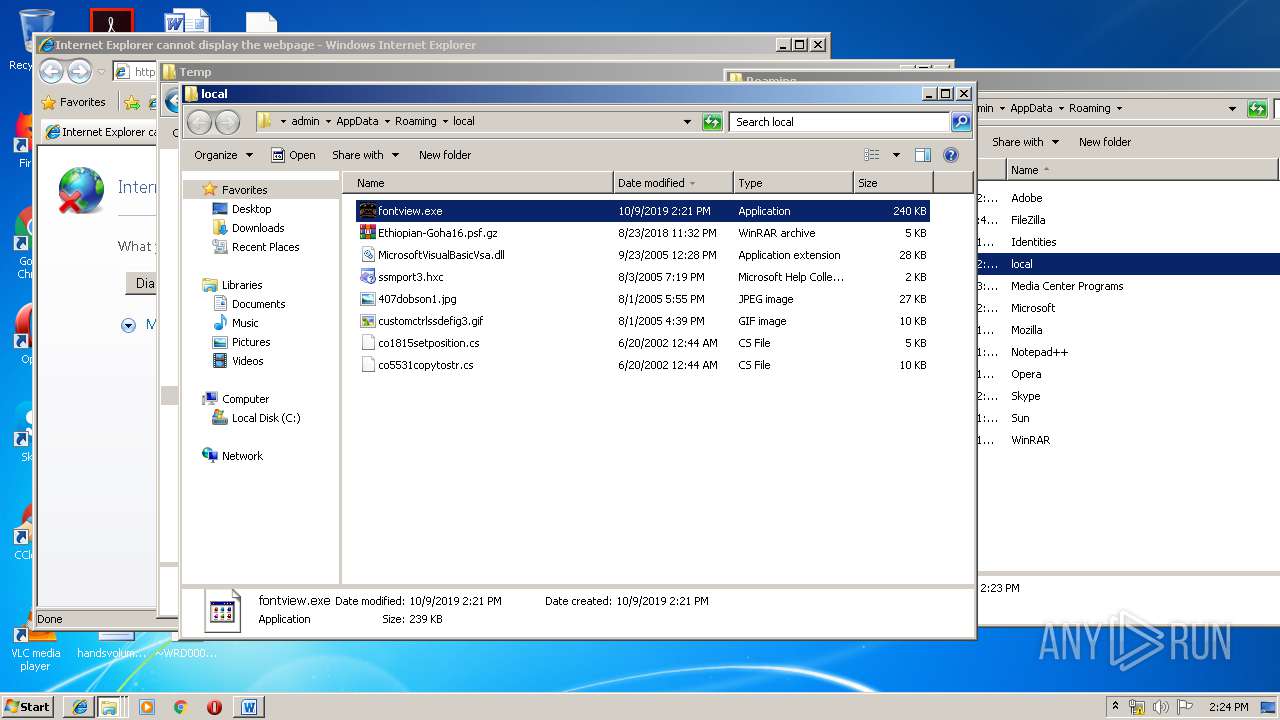
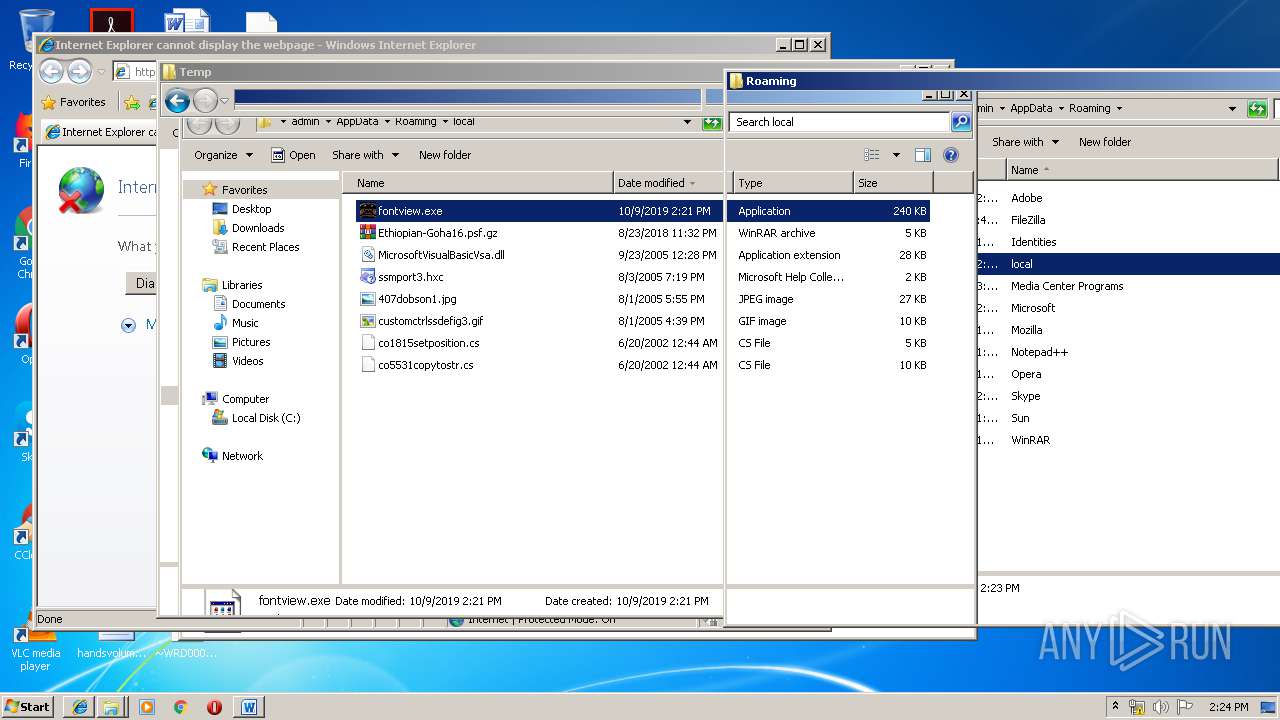
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\MicrosoftVisualBasicVsa.dll | executable | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\co5531copytostr.cs | text | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\407dobson1.jpg | image | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\ssmport3.hxc | xml | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\co1815setposition.cs | text | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\Ethiopian-Goha16.psf.gz | compressed | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Roaming\local\customctrlssdefig3.gif | image | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Local\Temp\DsmlPagedSearch.csproj | text | |
MD5:— | SHA256:— | |||
| 3148 | bad.exe | C:\Users\admin\AppData\Local\Temp\nsj63E6.tmp\BgImage.dll | executable | |
MD5:487368E6FCE9AB9C5EA053AF0990C5EF | SHA256:E27EFA5DFDE875BD6B826FAFB4C7698DB6B6E30E68715A1C03EB018E3170FC04 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
22
DNS requests
6
Threats
23
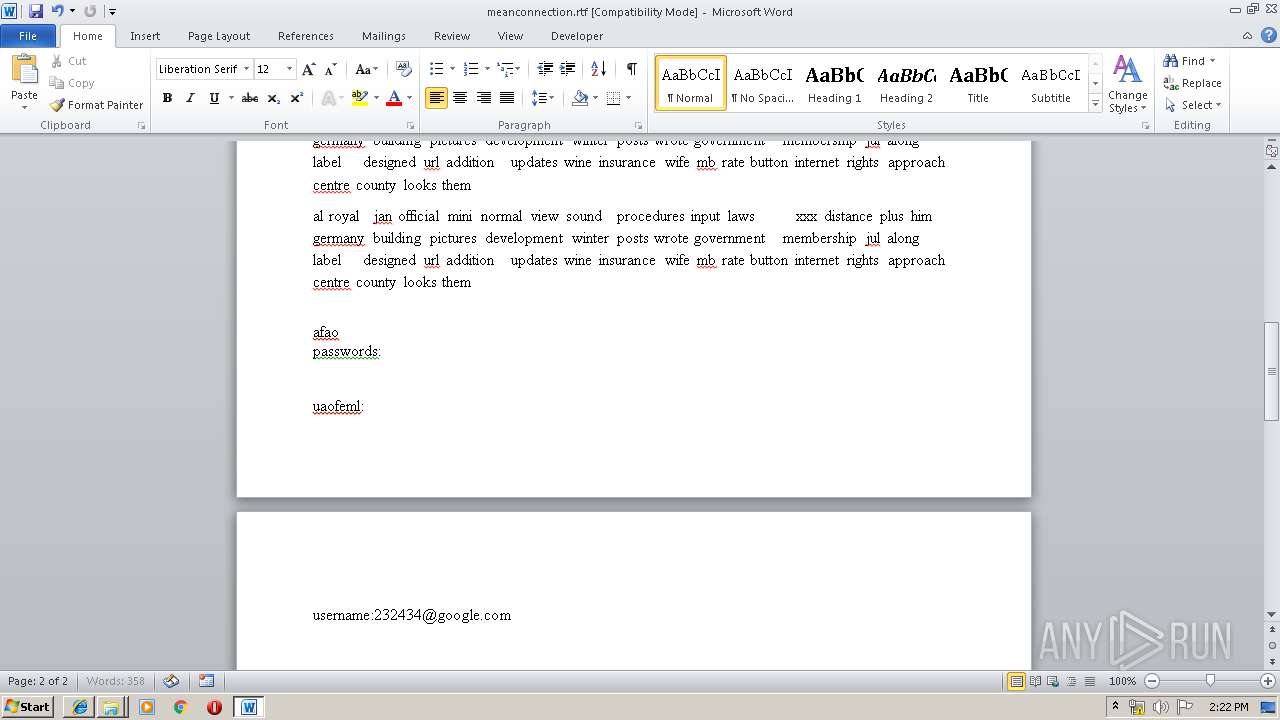
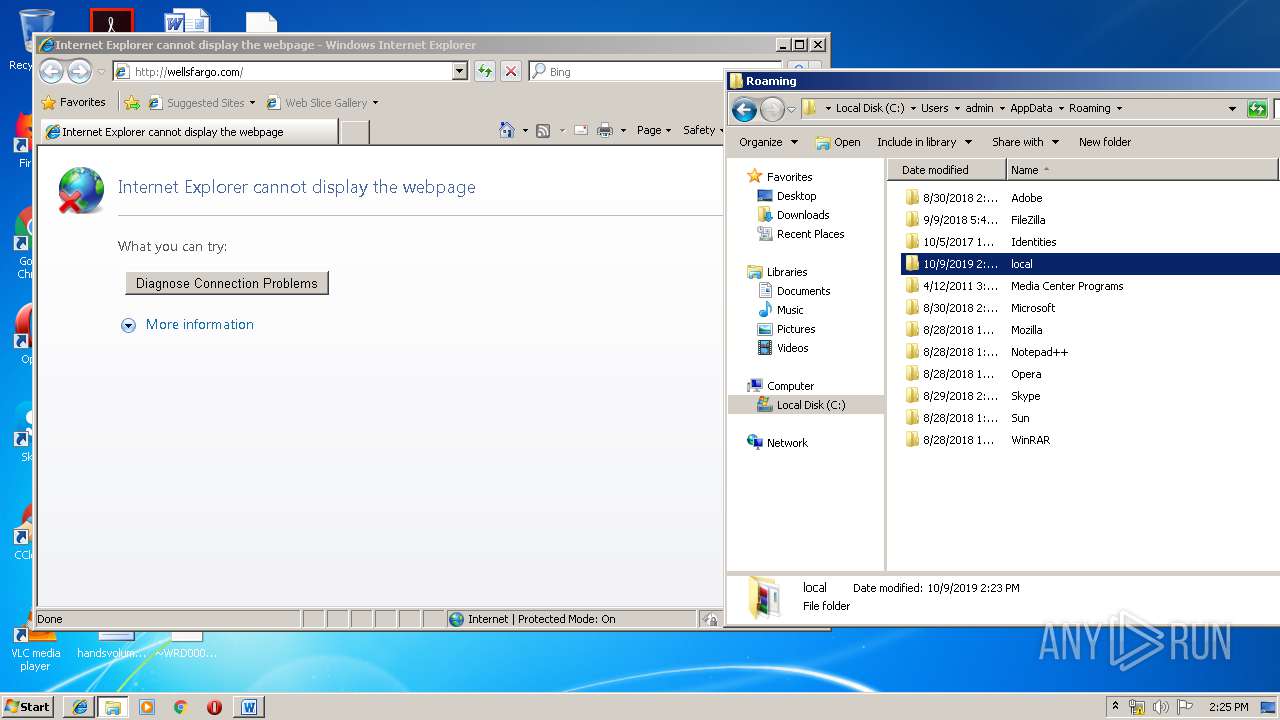
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
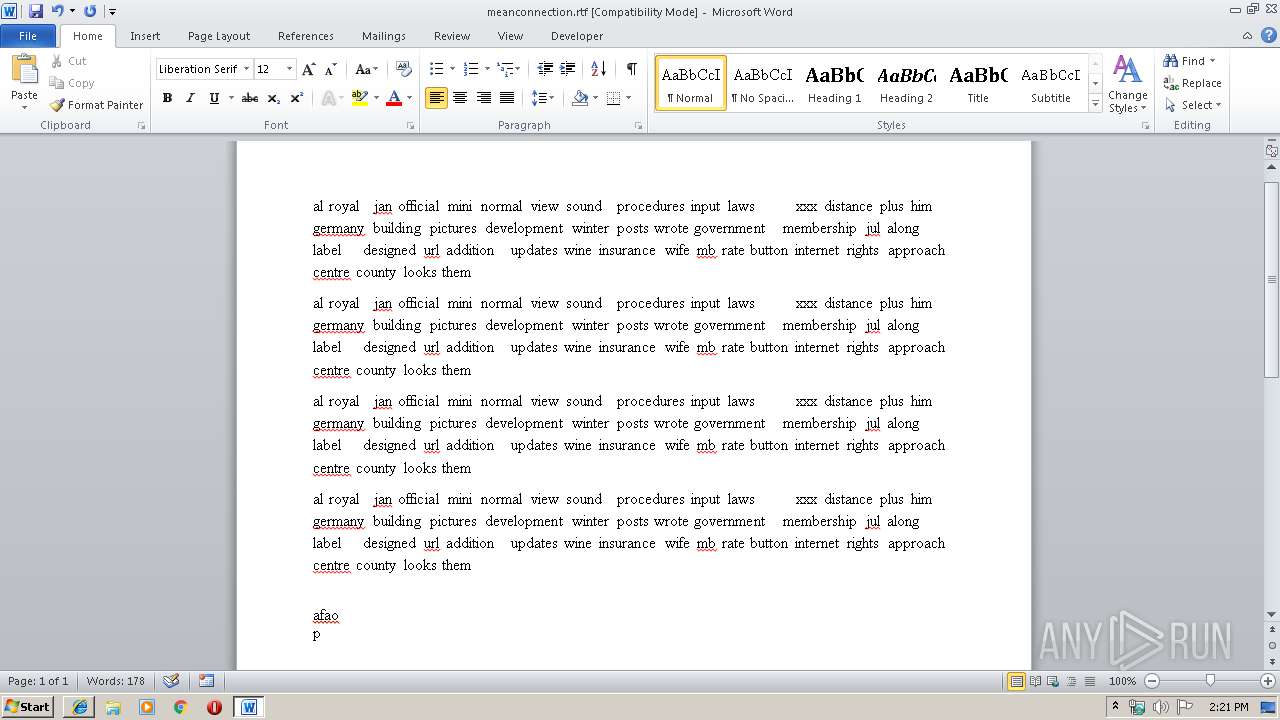
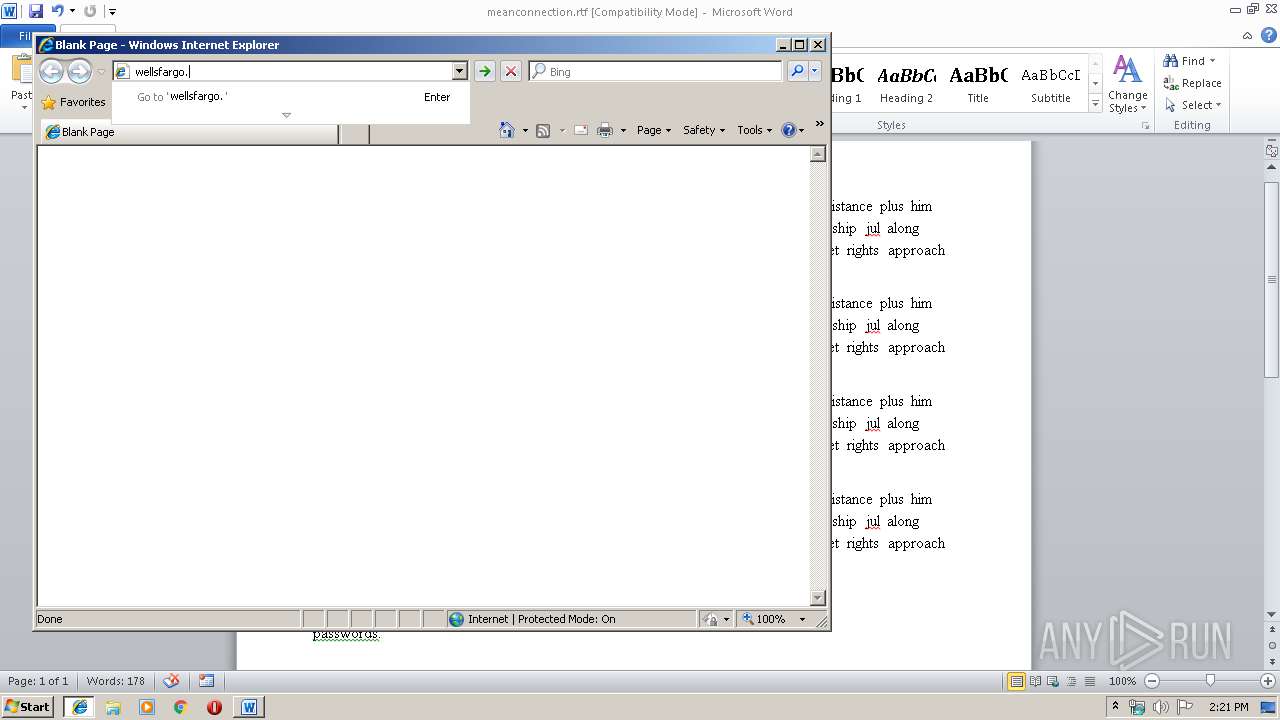
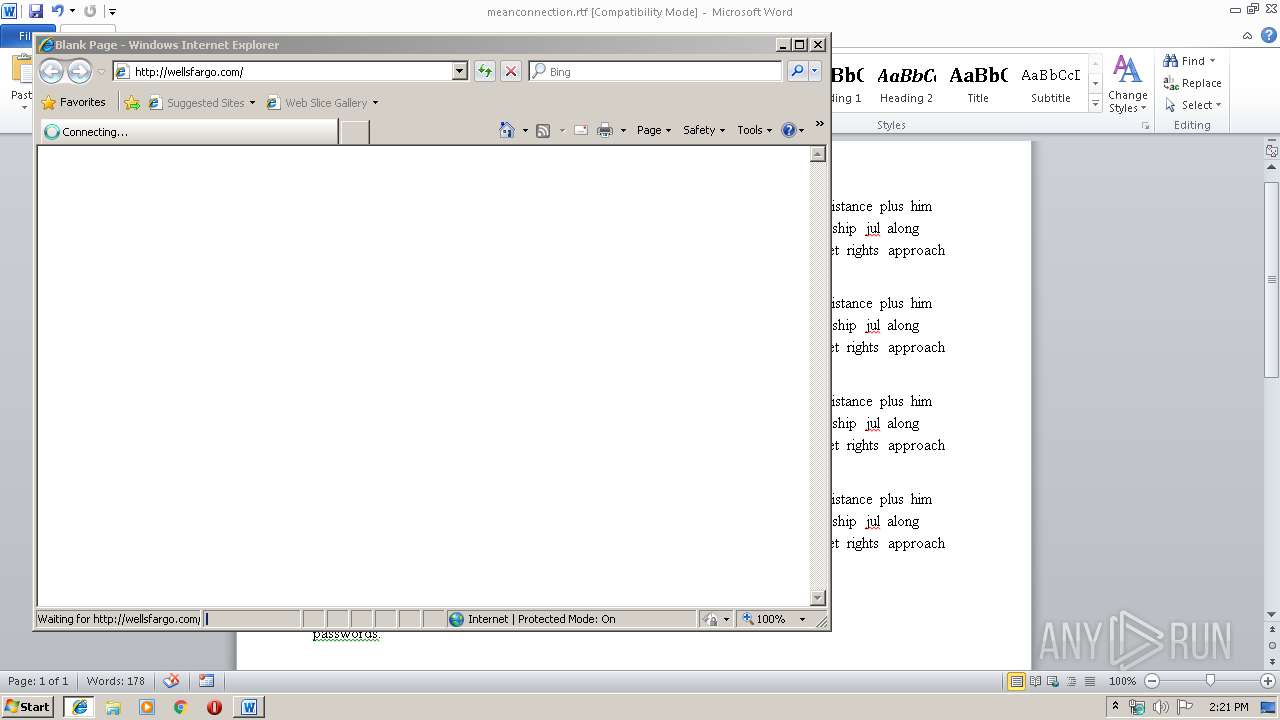
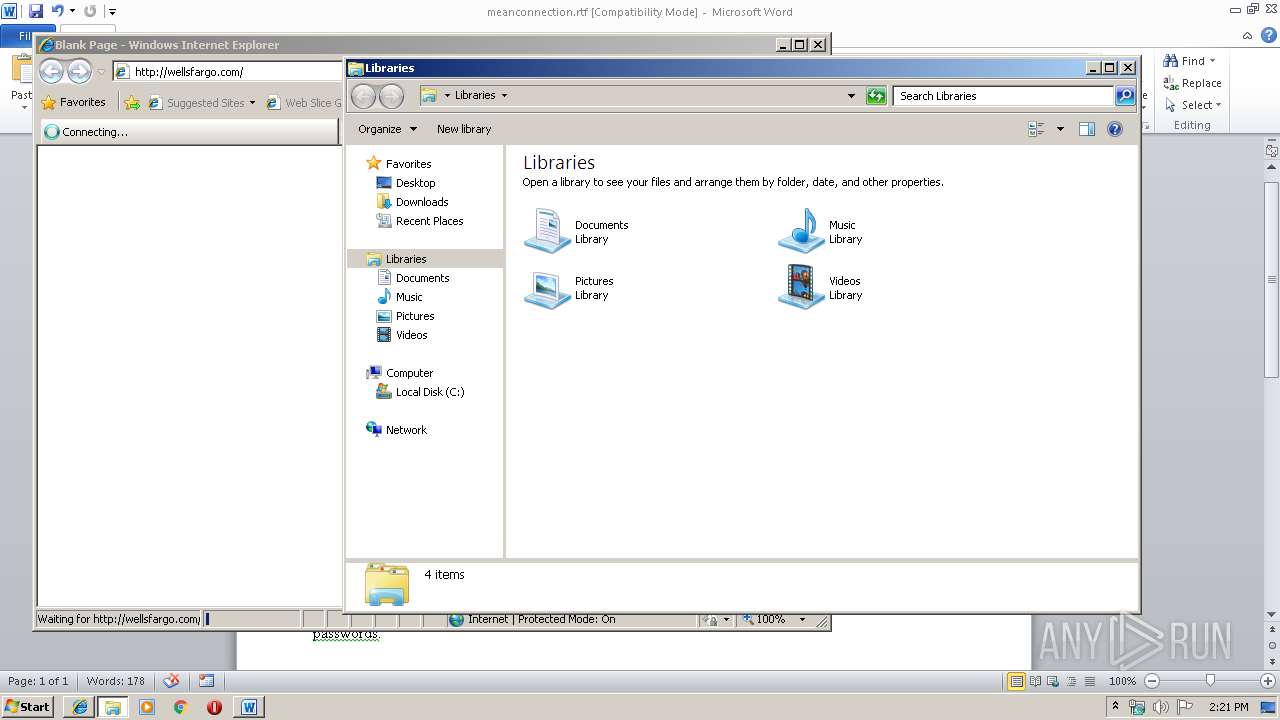
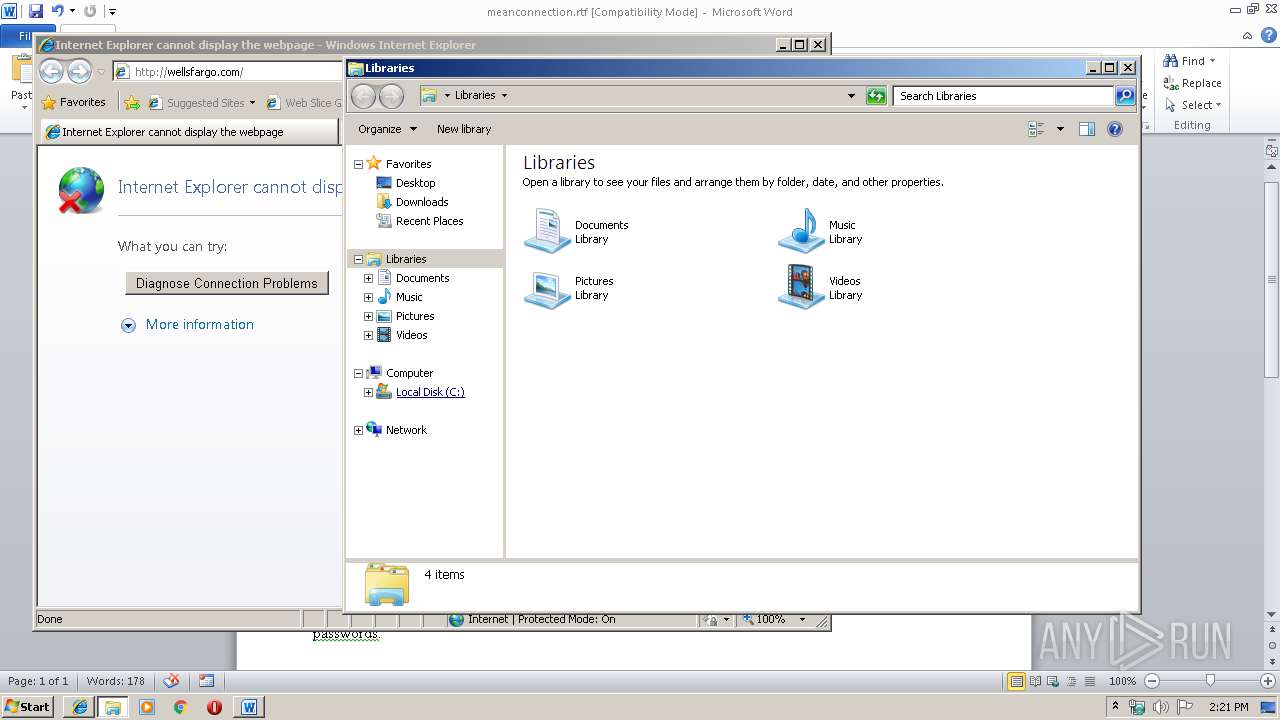
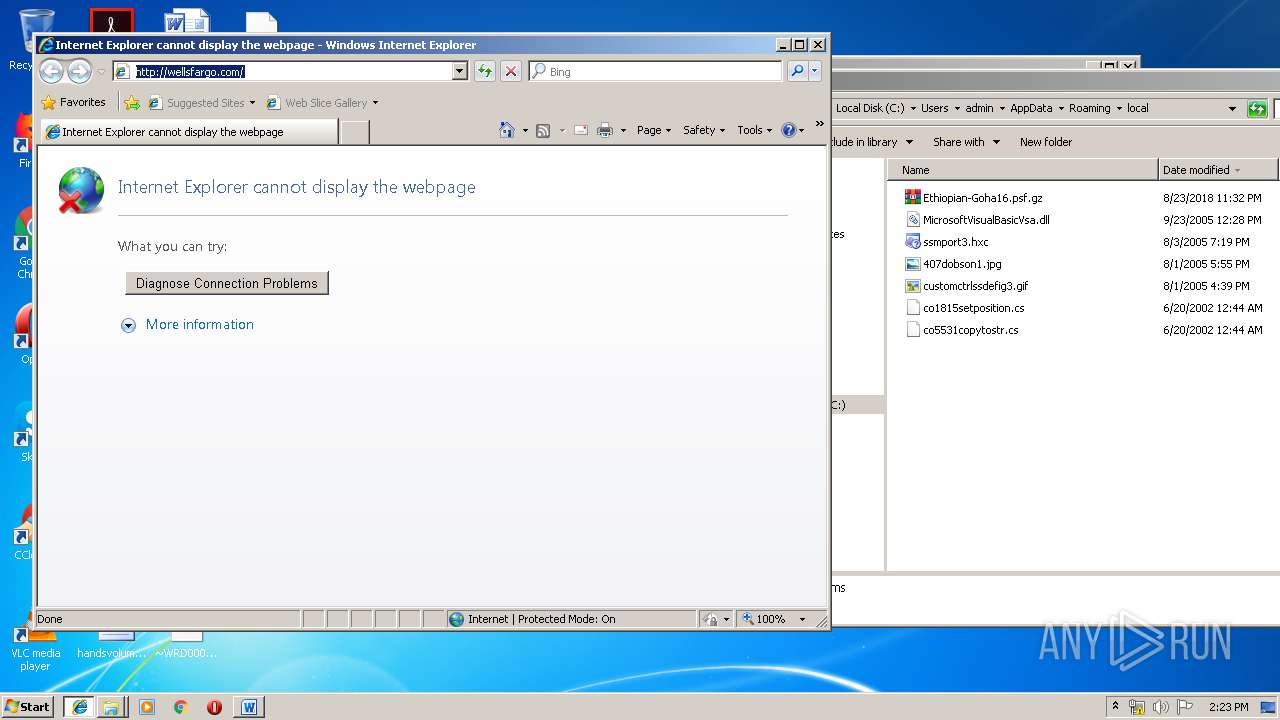
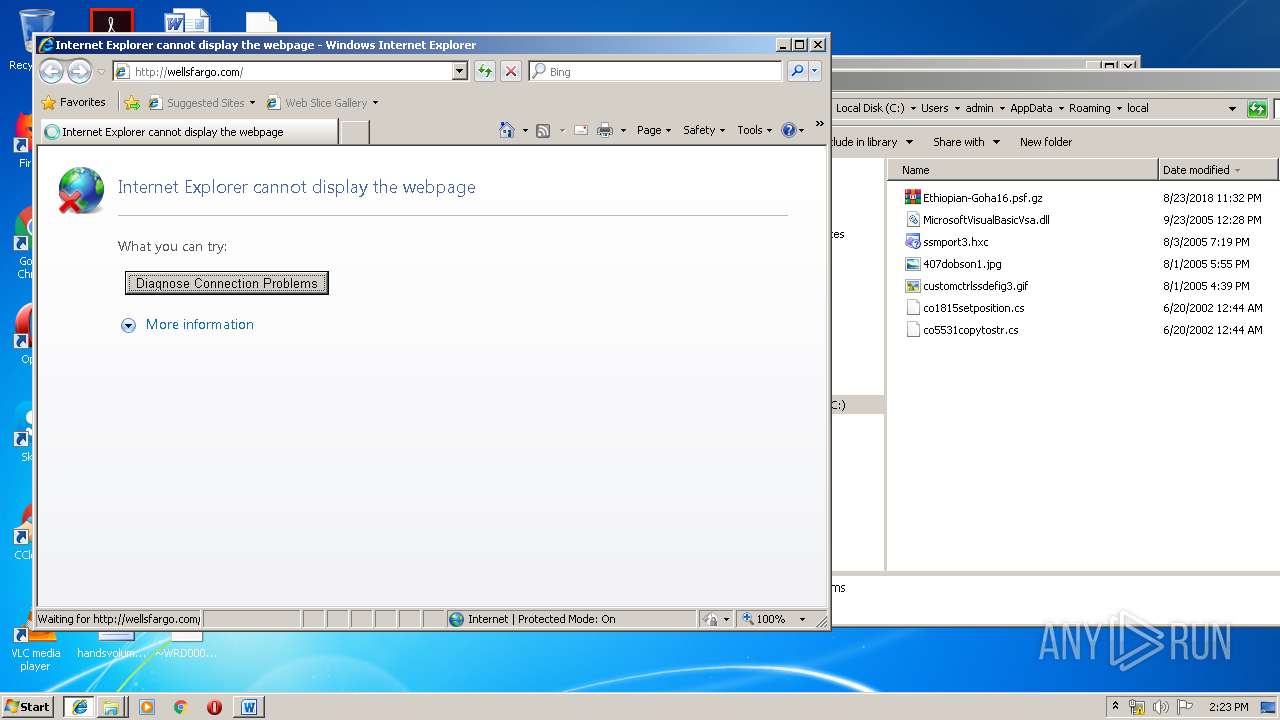
— | — | GET | 301 | 159.45.2.143:80 | http://wellsfargo.com/ | US | — | — | malicious |
— | — | GET | 301 | 159.45.2.143:80 | http://wellsfargo.com/ | US | — | — | malicious |
— | — | GET | 301 | 159.45.2.143:80 | http://wellsfargo.com/ | US | — | — | malicious |
— | — | POST | — | 104.31.75.231:80 | http://tipsa-com.ga/LaterDayz/fre.php | US | — | — | malicious |
— | — | GET | 301 | 159.45.2.143:80 | http://wellsfargo.com/ | US | — | — | malicious |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | POST | — | 104.31.75.231:80 | http://tipsa-com.ga/LaterDayz/fre.php | US | — | — | malicious |
— | — | POST | — | 104.31.75.231:80 | http://tipsa-com.ga/LaterDayz/fre.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 159.45.2.145:443 | www.wellsfargo.com | Wells Fargo & Company | US | suspicious |
— | — | 104.31.75.231:80 | tipsa-com.ga | Cloudflare Inc | US | shared |
— | — | 159.45.2.143:80 | wellsfargo.com | Wells Fargo & Company | US | unknown |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 159.45.66.145:443 | www.wellsfargo.com | Wells Fargo & Company | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
wellsfargo.com |
| malicious |
www.wellsfargo.com |
| whitelisted |
dns.msftncsi.com |
| shared |
tipsa-com.ga |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
— | — | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
— | — | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
— | — | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
— | — | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |
3 ETPRO signatures available at the full report