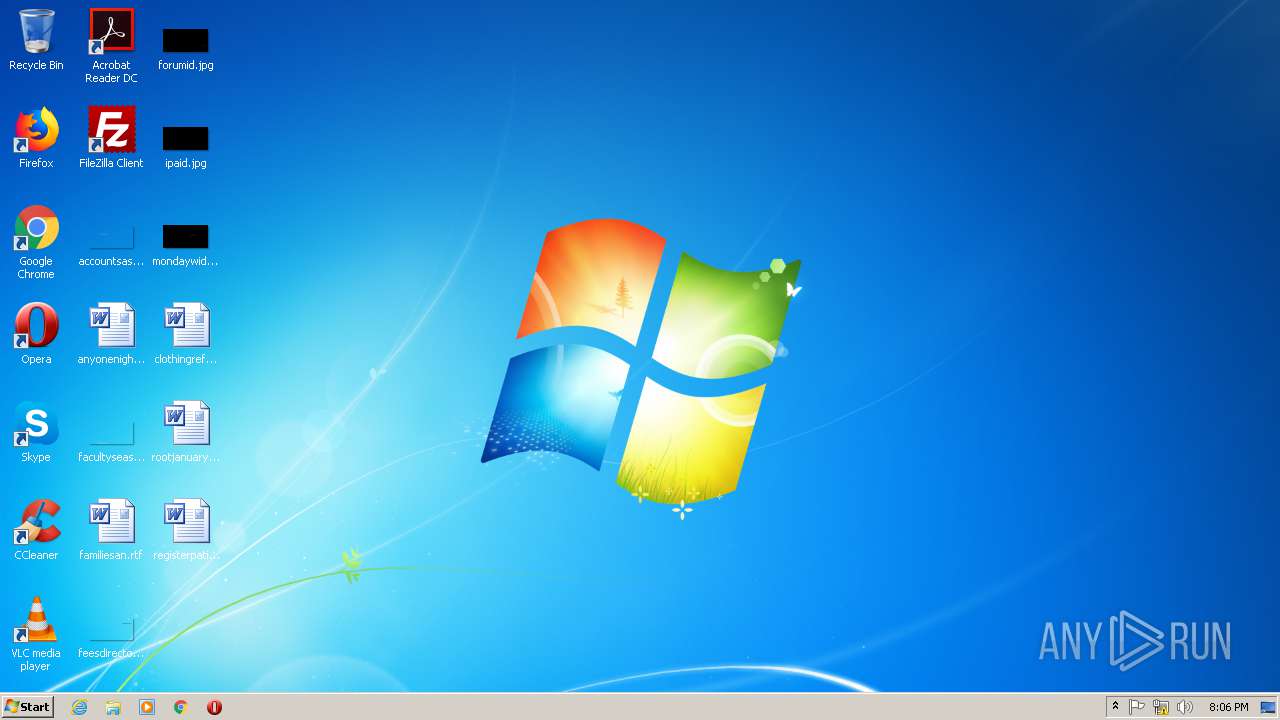
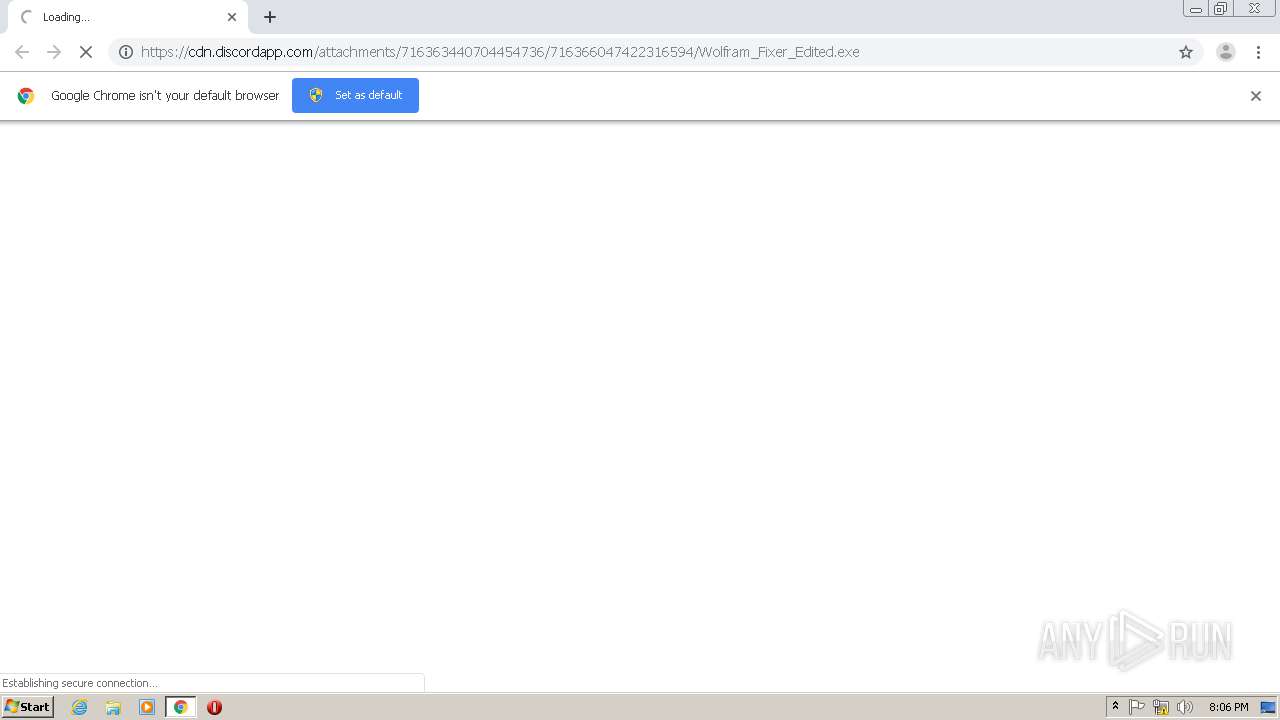
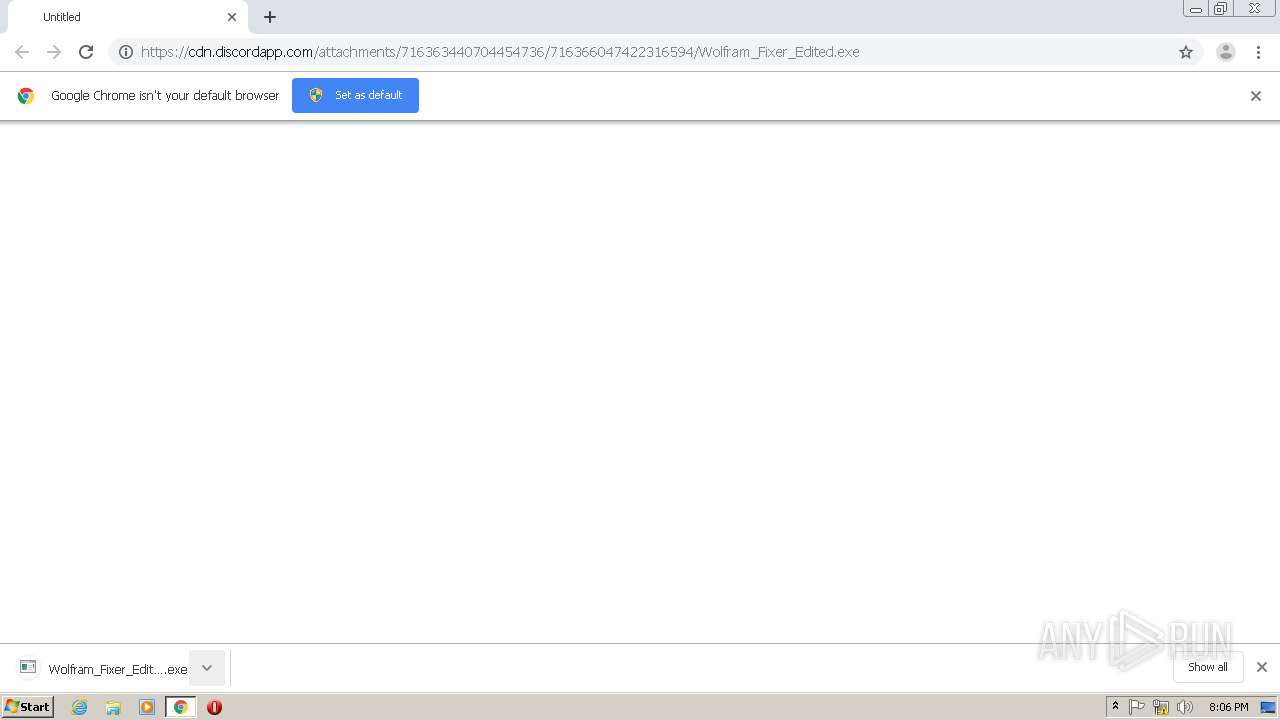
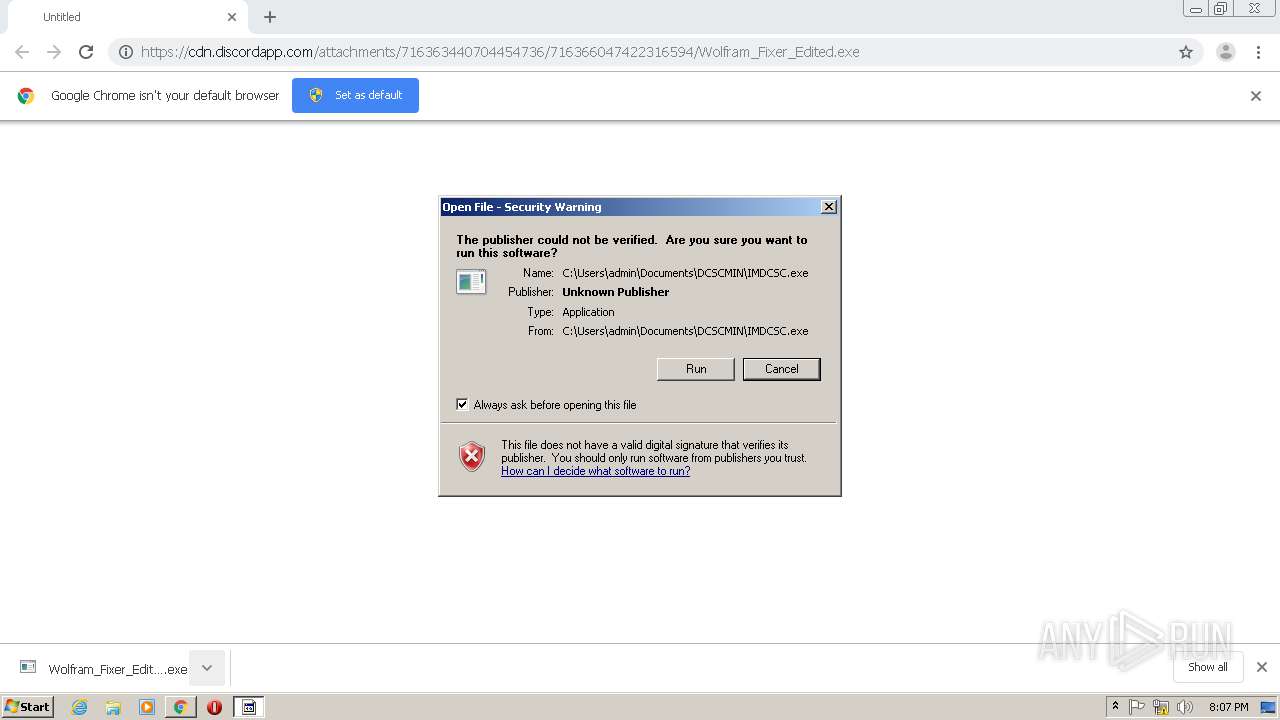
| URL: | https://cdn.discordapp.com/attachments/716363440704454736/716366047422316594/Wolfram_Fixer_Edited.exe |
| Full analysis: | https://app.any.run/tasks/31450f84-bc9c-4e80-9983-894e31a99214 |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | May 30, 2020, 19:06:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A1CEB25F27CAB8FEE55D177643B0C269 |
| SHA1: | 4ED7A386C296AA637DD20E7F8378736A43382EFD |
| SHA256: | CEB0F89FC59AB99C9EA1F21B12BD982C197D476CBBBA673D13B8EAB824C8093F |
| SSDEEP: | 3:N8cCWdy6//nTUWFlTKaz0XWUTQRFh6jMjEodAn:2cry6XnYWLTK/WUTs3lEodA |
MALICIOUS
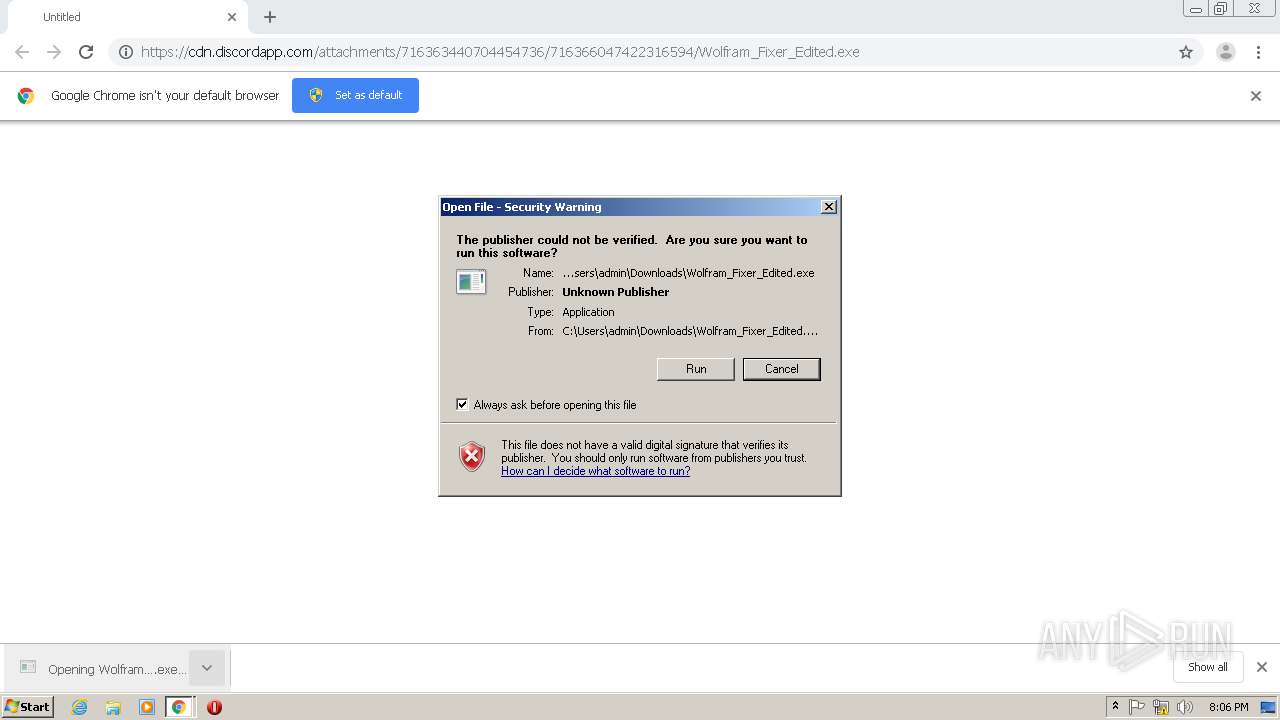
Application was dropped or rewritten from another process
- Wolfram_Fixer_Edited.exe (PID: 2512)
- IMDCSC.exe (PID: 3664)
Changes the autorun value in the registry
- Wolfram_Fixer_Edited.exe (PID: 2512)
DARKCOMET was detected
- IMDCSC.exe (PID: 3664)
Changes the login/logoff helper path in the registry
- Wolfram_Fixer_Edited.exe (PID: 2512)
SUSPICIOUS
Starts itself from another location
- Wolfram_Fixer_Edited.exe (PID: 2512)
Executable content was dropped or overwritten
- chrome.exe (PID: 2396)
- chrome.exe (PID: 2840)
- Wolfram_Fixer_Edited.exe (PID: 2512)
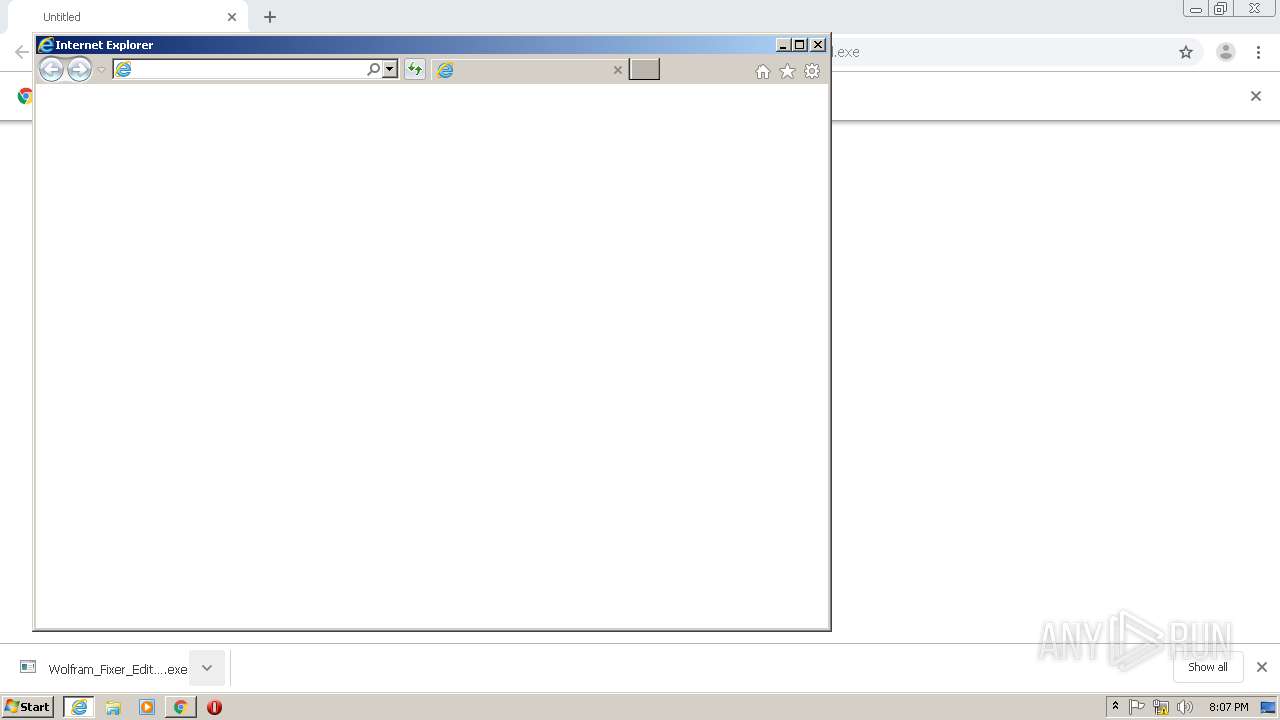
Starts Internet Explorer
- IMDCSC.exe (PID: 3664)
INFO
Application launched itself
- chrome.exe (PID: 2840)
- iexplore.exe (PID: 2456)
Reads Internet Cache Settings
- chrome.exe (PID: 2840)
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 3244)
Reads the hosts file
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2396)
Changes internet zones settings
- iexplore.exe (PID: 2456)
Creates files in the user directory
- iexplore.exe (PID: 3244)
Reads internet explorer settings
- iexplore.exe (PID: 3244)
Reads settings of System Certificates
- chrome.exe (PID: 2396)
- iexplore.exe (PID: 2456)
Changes settings of System certificates
- iexplore.exe (PID: 2456)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,8812408803971929120,532173938783045888,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14505733645712651993 --mojo-platform-channel-handle=3772 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,8812408803971929120,532173938783045888,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7723939115204994202 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,8812408803971929120,532173938783045888,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12162660044882490501 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8812408803971929120,532173938783045888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2250046009741186279 --mojo-platform-channel-handle=1576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.google.com/ | C:\Program Files\Internet Explorer\iexplore.exe | IMDCSC.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\Downloads\Wolfram_Fixer_Edited.exe" | C:\Users\admin\Downloads\Wolfram_Fixer_Edited.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,8812408803971929120,532173938783045888,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1167530027464593204 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://cdn.discordapp.com/attachments/716363440704454736/716366047422316594/Wolfram_Fixer_Edited.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2844 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2456 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 309
Read events
2 063
Write events
2 189
Delete events
1 057
Modification events
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2840-13235339209797625 |
Value: 259 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
6
Suspicious files
37
Text files
89
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED2AECA-B18.pma | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\aff9e7a3-ee75-4db1-9412-af52596636f9.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF7cb4c.TMP | text | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF7cd31.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
25
DNS requests
15
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3244 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBqGiw2vm8c0CAAAAAA%2BvZc%3D | US | der | 471 b | whitelisted |
3244 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDEKiK1zGWeAwgAAAAAPr4Q | US | der | 472 b | whitelisted |
3244 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDvkDzv2QYa2AgAAAABnMwk%3D | US | der | 471 b | whitelisted |
3244 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDEKiK1zGWeAwgAAAAAPr4Q | US | der | 472 b | whitelisted |
3244 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBqGiw2vm8c0CAAAAAA%2BvZc%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3244 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3244 | iexplore.exe | GET | 302 | 172.217.18.100:80 | http://www.google.com/ | US | html | 231 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2396 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2396 | chrome.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2396 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3244 | iexplore.exe | 172.217.22.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2396 | chrome.exe | 172.217.22.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3244 | iexplore.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2456 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2456 | iexplore.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2396 | chrome.exe | 216.58.212.142:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2396 | chrome.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
safebrowsing.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
0.tcp.ngrok.io |
| malicious |
ocsp.pki.goog |
| whitelisted |
consent.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
3664 | IMDCSC.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
3664 | IMDCSC.exe | A Network Trojan was detected | REMOTE [PTsecurity] DarkComet |
3664 | IMDCSC.exe | A Network Trojan was detected | REMOTE [PTsecurity] Possible DarkComet-RAT activity |
2 ETPRO signatures available at the full report