| File name: | Rfiles.exe |
| Full analysis: | https://app.any.run/tasks/ac8b90ad-c607-490a-bf07-137286d99339 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | December 06, 2019, 13:31:55 |
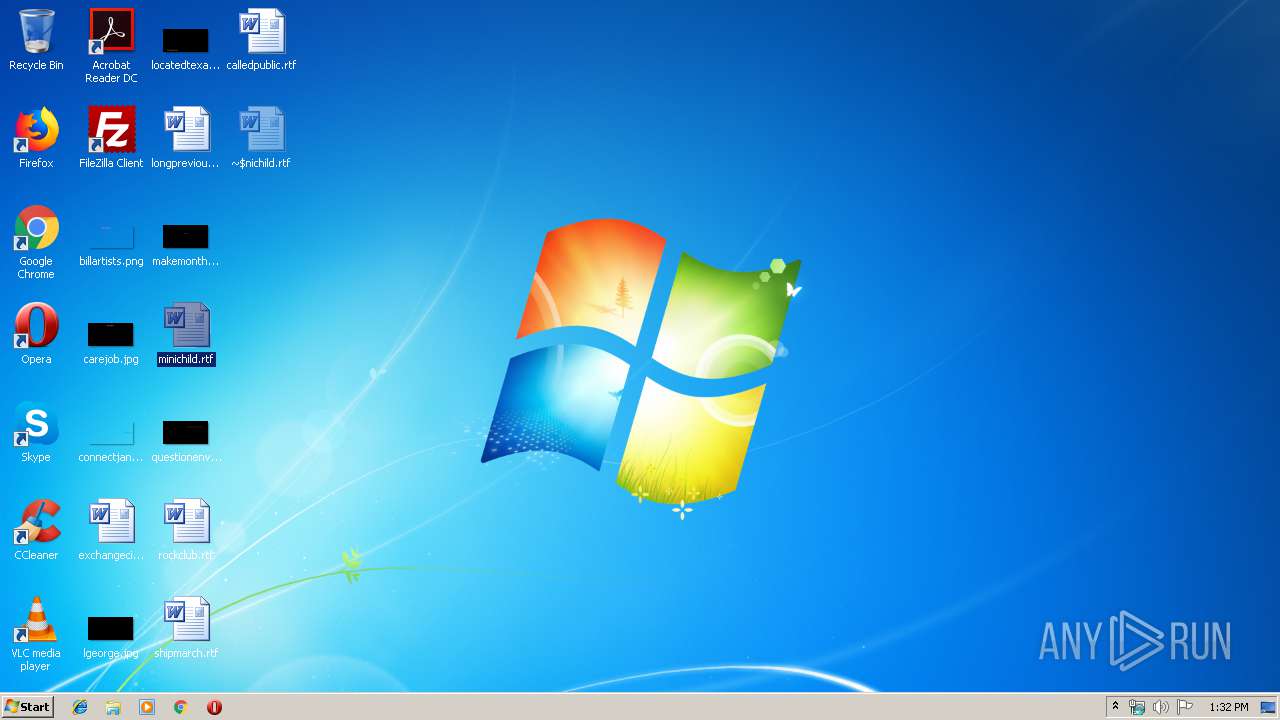
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 051A8B59C59C09A0DF060EEE484C2056 |
| SHA1: | DD0C9FD23F8318641820E2A00650824BD1117698 |
| SHA256: | CEAEA9EED45ABC277139C408FE954D5A1699B7AE9C18BCB7692419FD92C00D72 |
| SSDEEP: | 24576:LZMbkcIsW7wDaIHFhlry+NpgUSvbdew3YJ4Sr:ikD8a6FZNyvbSJ |
MALICIOUS
LOKIBOT was detected
- Rfiles.exe (PID: 2700)
Connects to CnC server
- Rfiles.exe (PID: 2700)
Actions looks like stealing of personal data
- Rfiles.exe (PID: 2700)
SUSPICIOUS
Application launched itself
- Rfiles.exe (PID: 2620)
Loads DLL from Mozilla Firefox
- Rfiles.exe (PID: 2700)
Creates files in the user directory
- Rfiles.exe (PID: 2700)
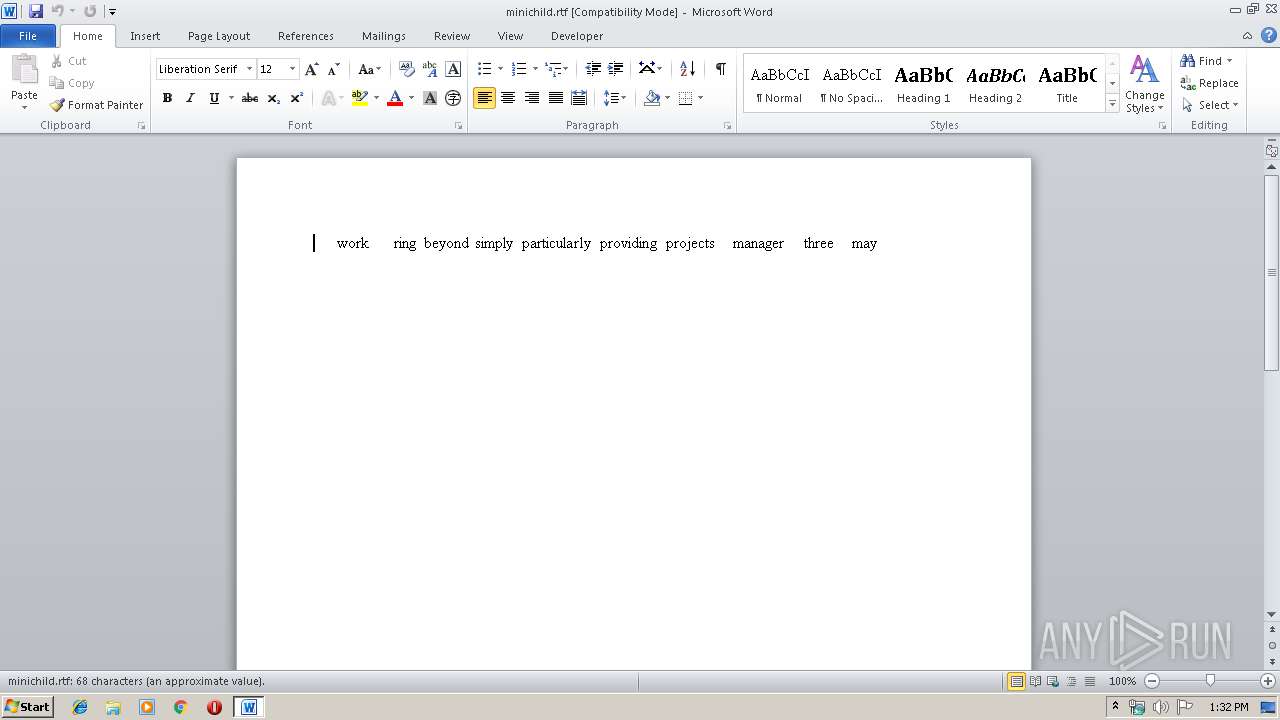
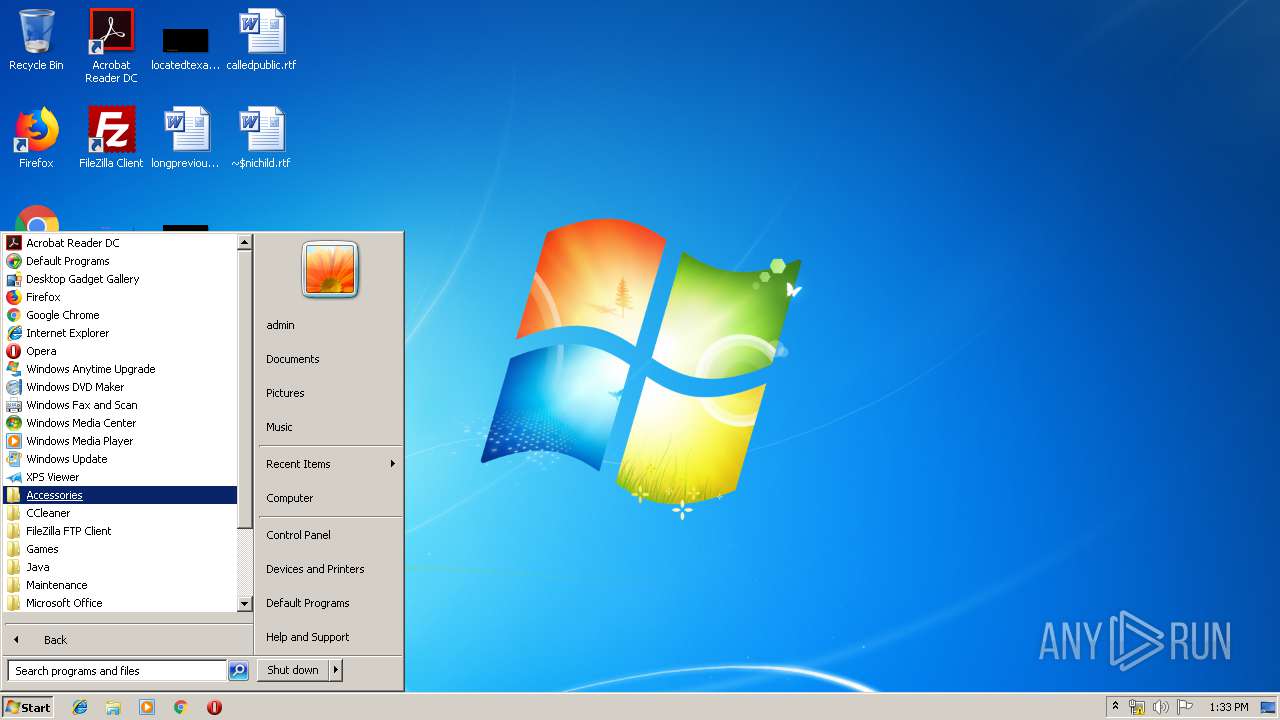
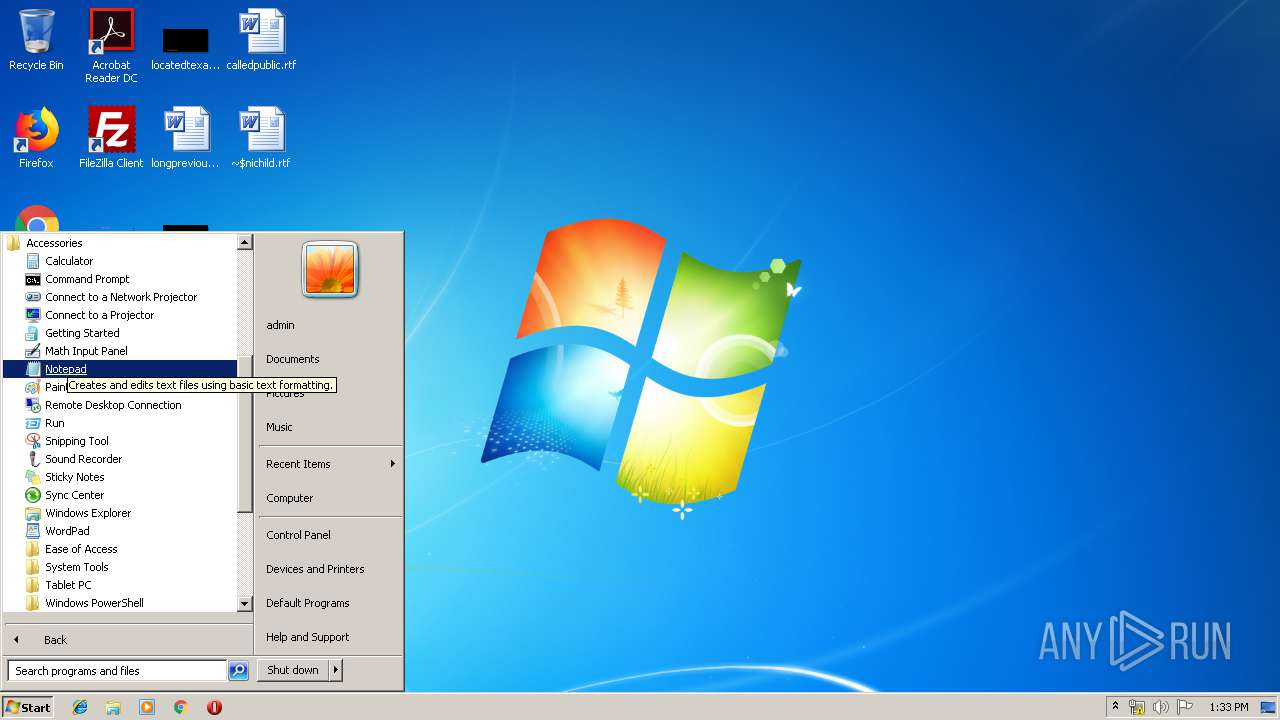
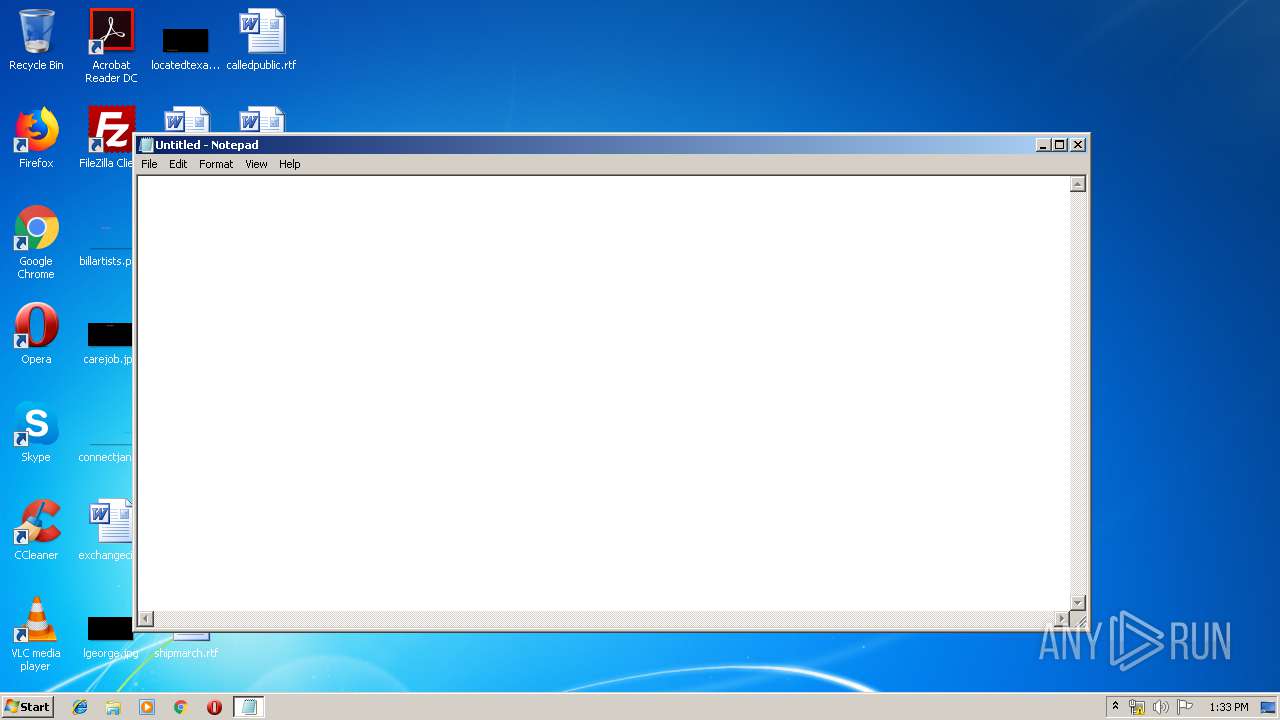
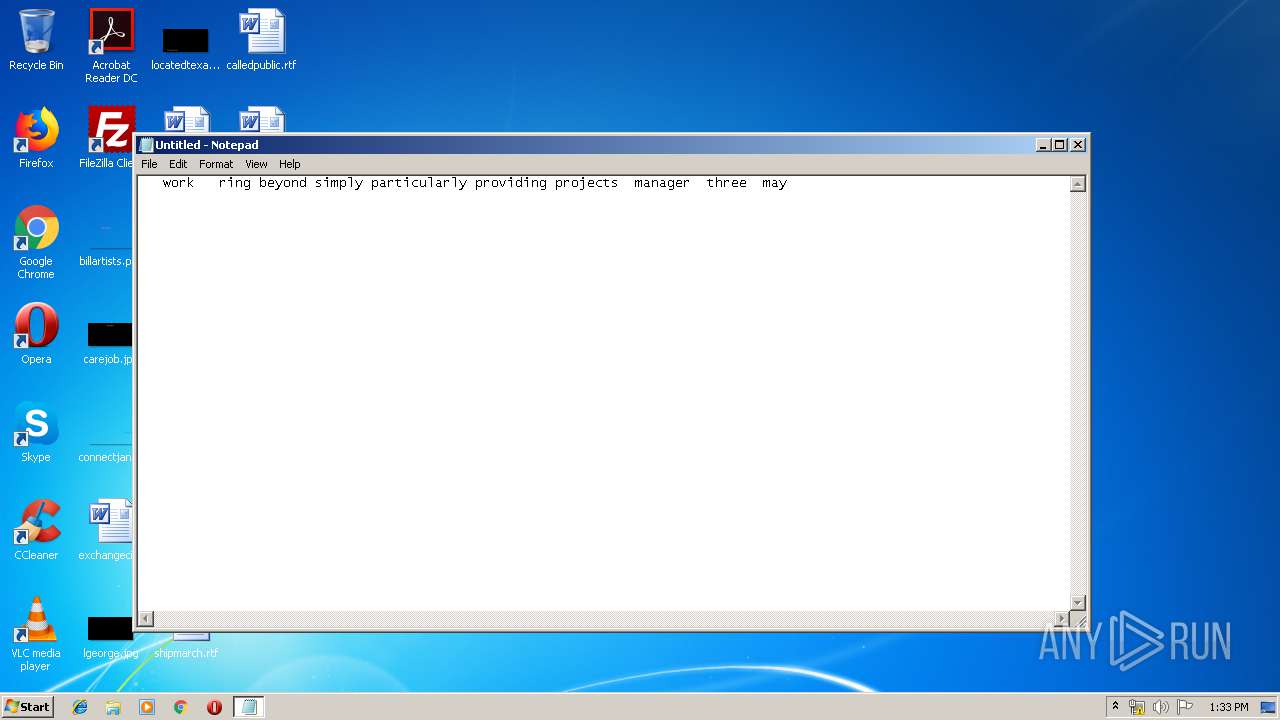
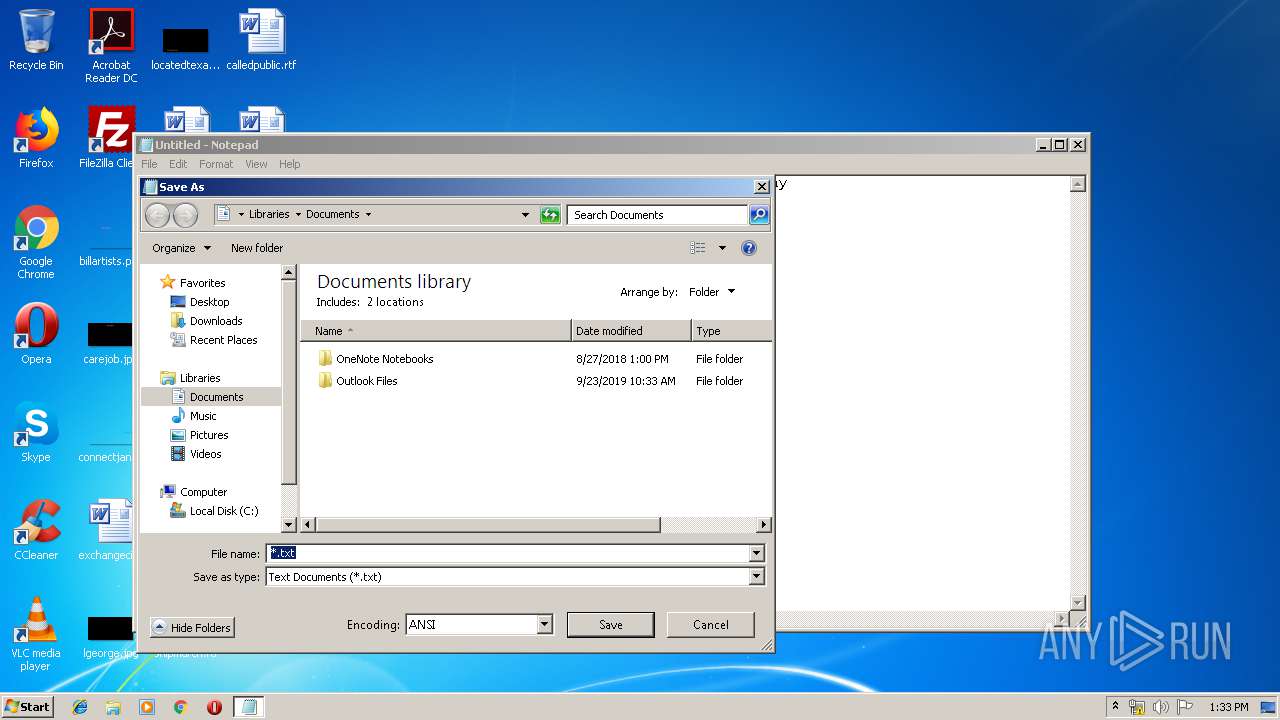
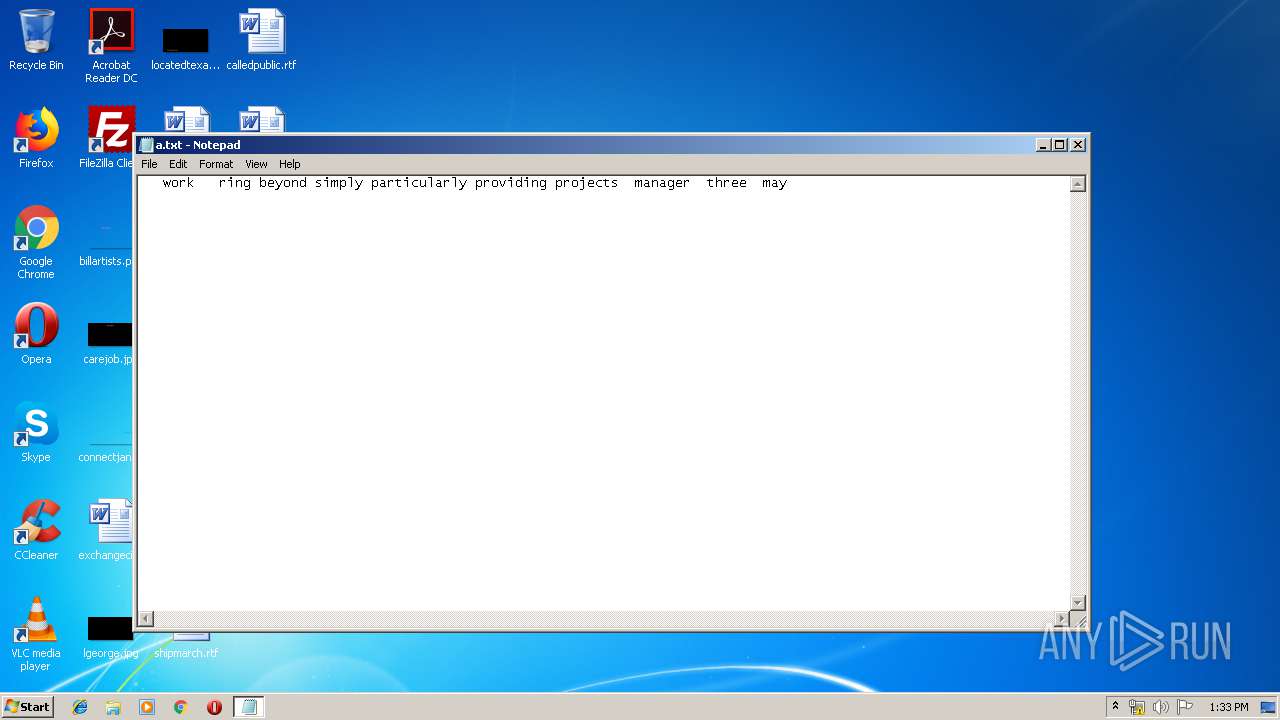
INFO
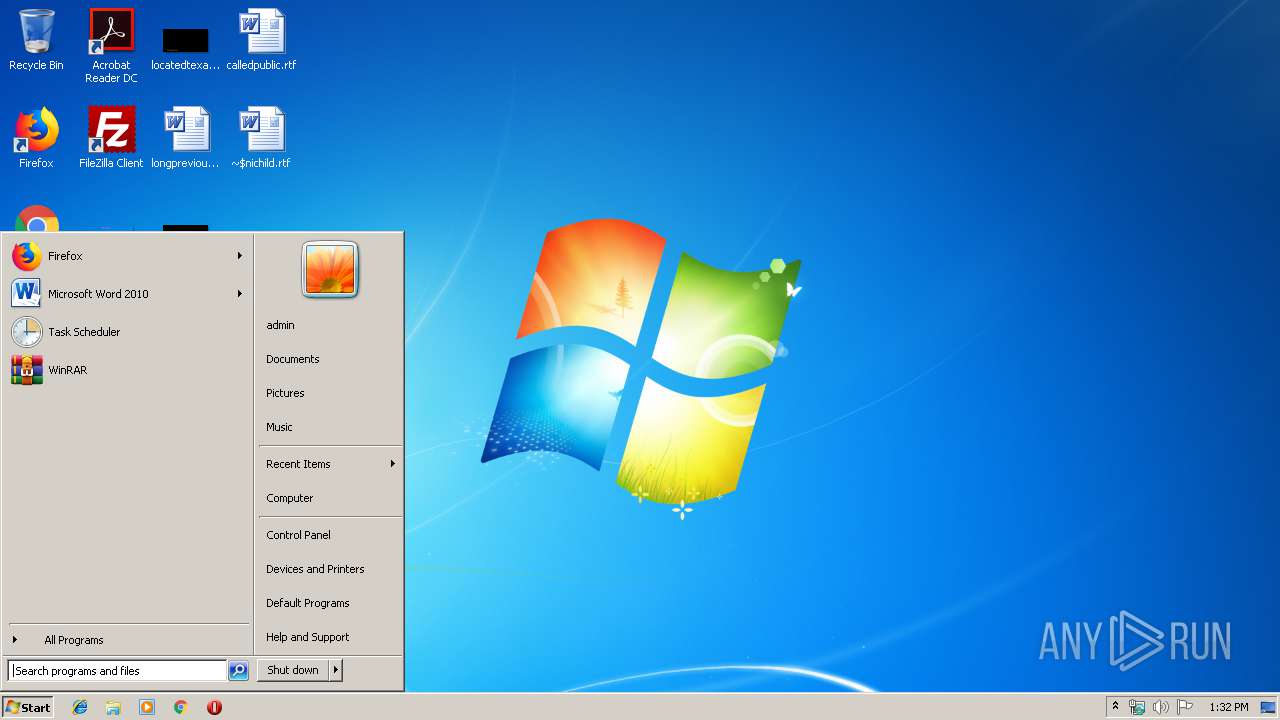
Manual execution by user
- notepad.exe (PID: 324)
- WINWORD.EXE (PID: 3792)
Creates files in the user directory
- WINWORD.EXE (PID: 3792)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (90.6) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:07:06 10:47:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1081344 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11f0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Norwegian (Bokml) |
| CharacterSet: | Unicode |
| CompanyName: | asus |
| ProductName: | KIroeffect8 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | GRuciolata |
| OriginalFileName: | GRuciolata.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jul-2004 08:47:40 |
| Detected languages: |
|
| CompanyName: | asus |
| ProductName: | KIroeffect8 |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | GRuciolata |
| OriginalFilename: | GRuciolata.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Jul-2004 08:47:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001072B8 | 0x00108000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6185 |
.data | 0x00109000 | 0x00000A0C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0010A000 | 0x0000C61A | 0x0000D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.79158 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.15456 | 540 | Unicode (UTF 16LE) | Norwegian - Norway (Bokmal) | RT_VERSION |
30001 | 6.00973 | 22216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 5.12338 | 7336 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 5.92247 | 3240 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30004 | 6.15417 | 16936 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Windows\system32\notepad.exe" | C:\Windows\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\AppData\Local\Temp\Rfiles.exe" | C:\Users\admin\AppData\Local\Temp\Rfiles.exe | — | explorer.exe | |||||||||||
User: admin Company: asus Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\Rfiles.exe" | C:\Users\admin\AppData\Local\Temp\Rfiles.exe | Rfiles.exe | ||||||||||||
User: admin Company: asus Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\minichild.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 667
Read events
1 298
Write events
214
Delete events
155
Modification events
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a2i |
Value: 61326900D00E0000010000000000000000000000 | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3792) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181951 | |||
Executable files
0
Suspicious files
1
Text files
5
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2A61.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0001.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0000.docx | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~$RD0000.docx | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0003.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0002.docx | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~$RD0002.docx | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{1602446C-8737-458A-B8EC-BA052C832F34}.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6B5D74BC-158E-4332-B9BA-DC162FF618C4}.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{90504117-8782-47C0-8A28-F7137E7E639B}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2700 | Rfiles.exe | POST | — | 185.189.12.85:80 | http://baiksan-kr.com/cool/rok4/fre.php | RU | — | — | malicious |
2700 | Rfiles.exe | POST | — | 185.189.12.85:80 | http://baiksan-kr.com/cool/rok4/fre.php | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2700 | Rfiles.exe | 185.189.12.85:80 | baiksan-kr.com | MediaServicePlus LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
baiksan-kr.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2700 | Rfiles.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2700 | Rfiles.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2700 | Rfiles.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2700 | Rfiles.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2700 | Rfiles.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2700 | Rfiles.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2700 | Rfiles.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
1 ETPRO signatures available at the full report