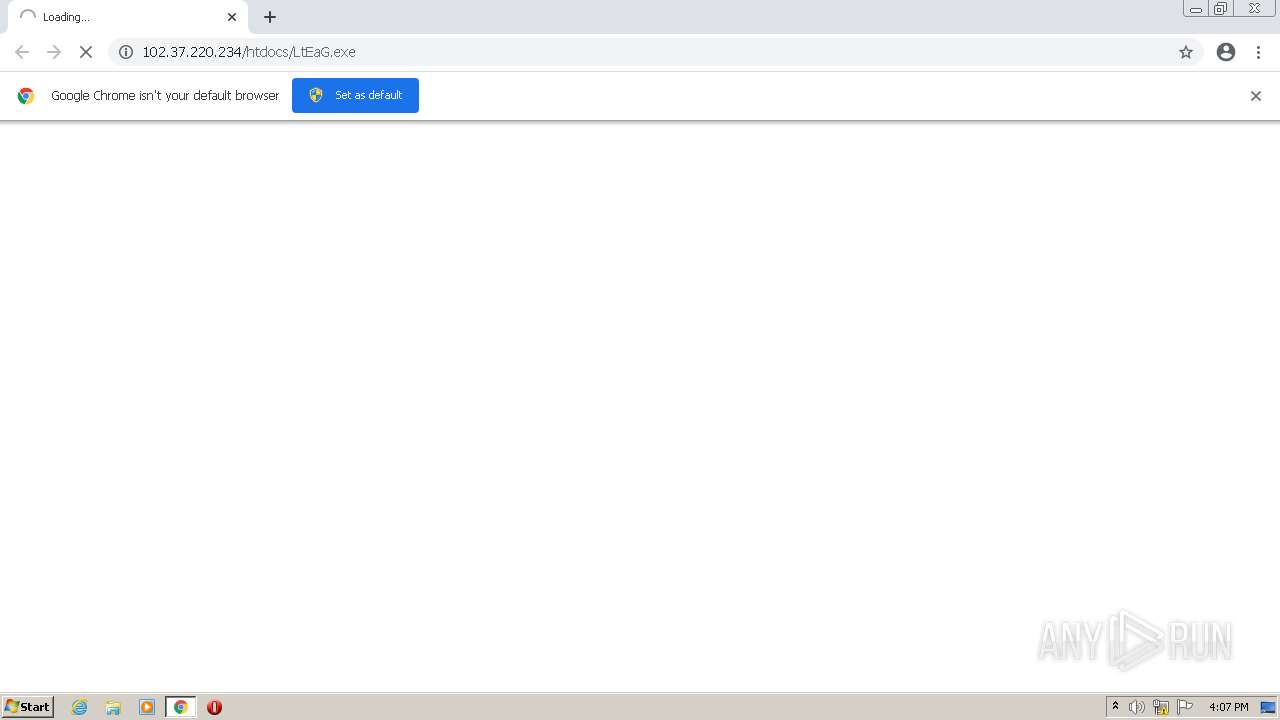
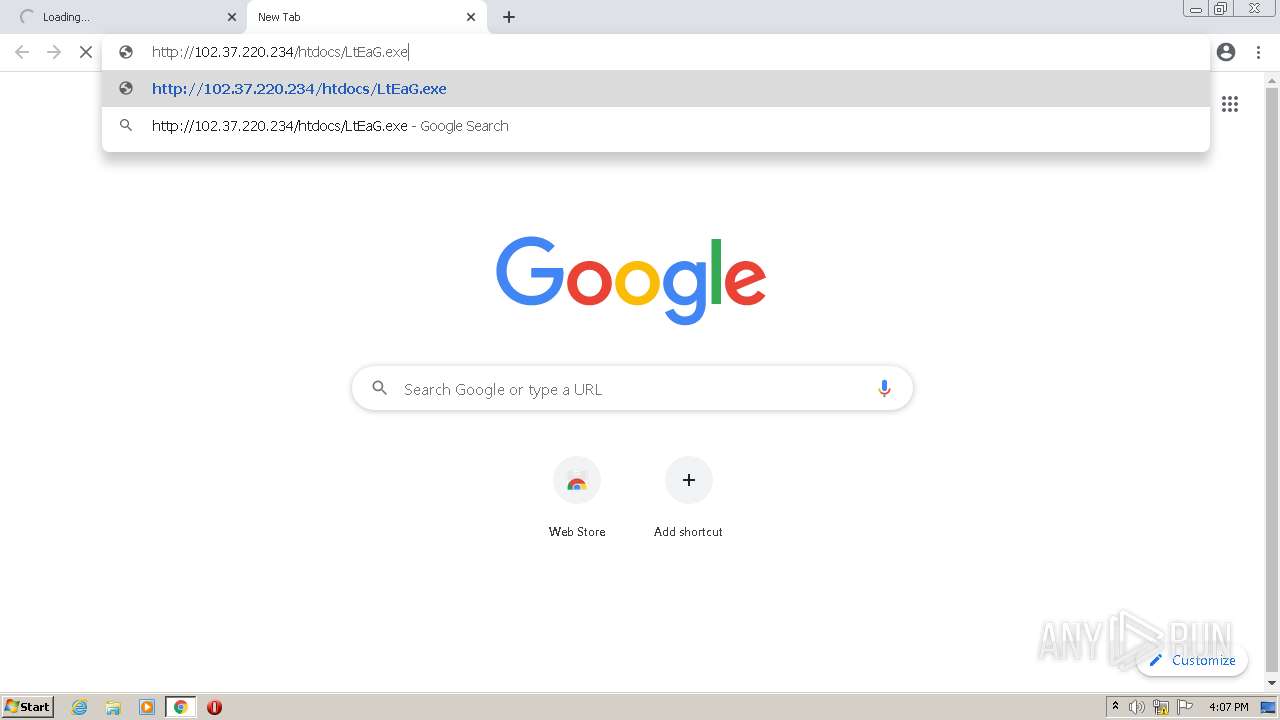
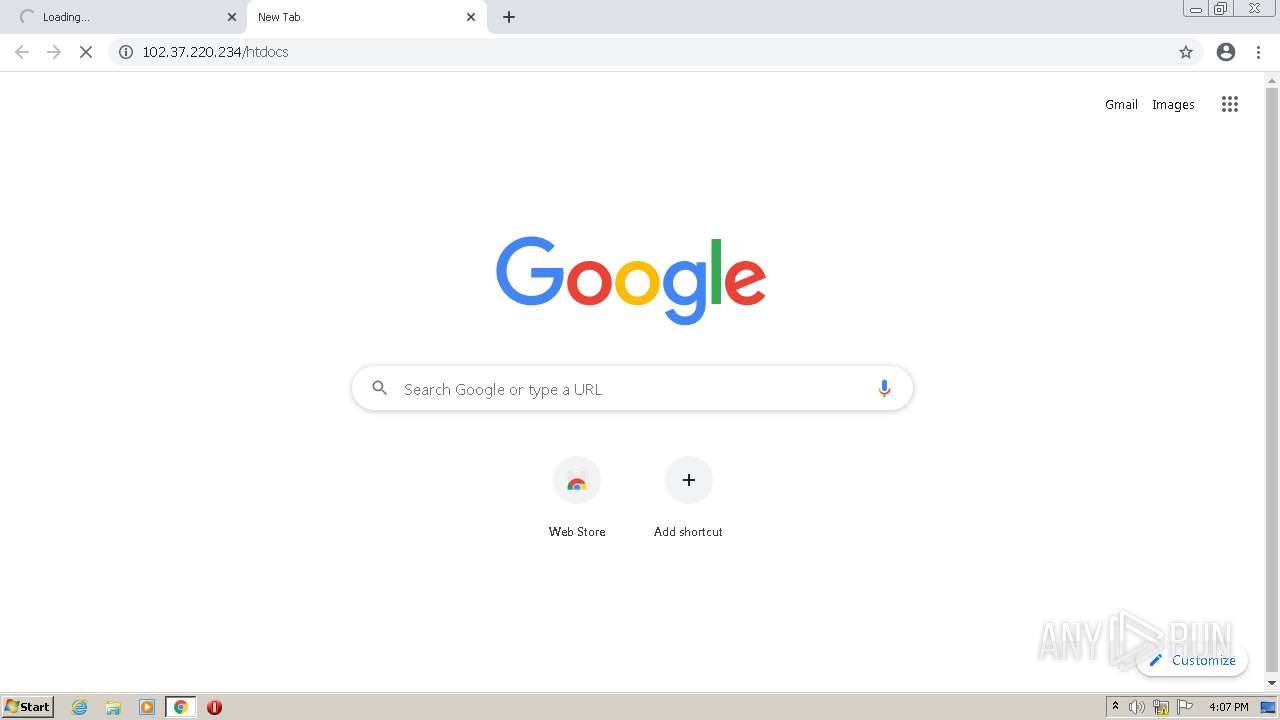
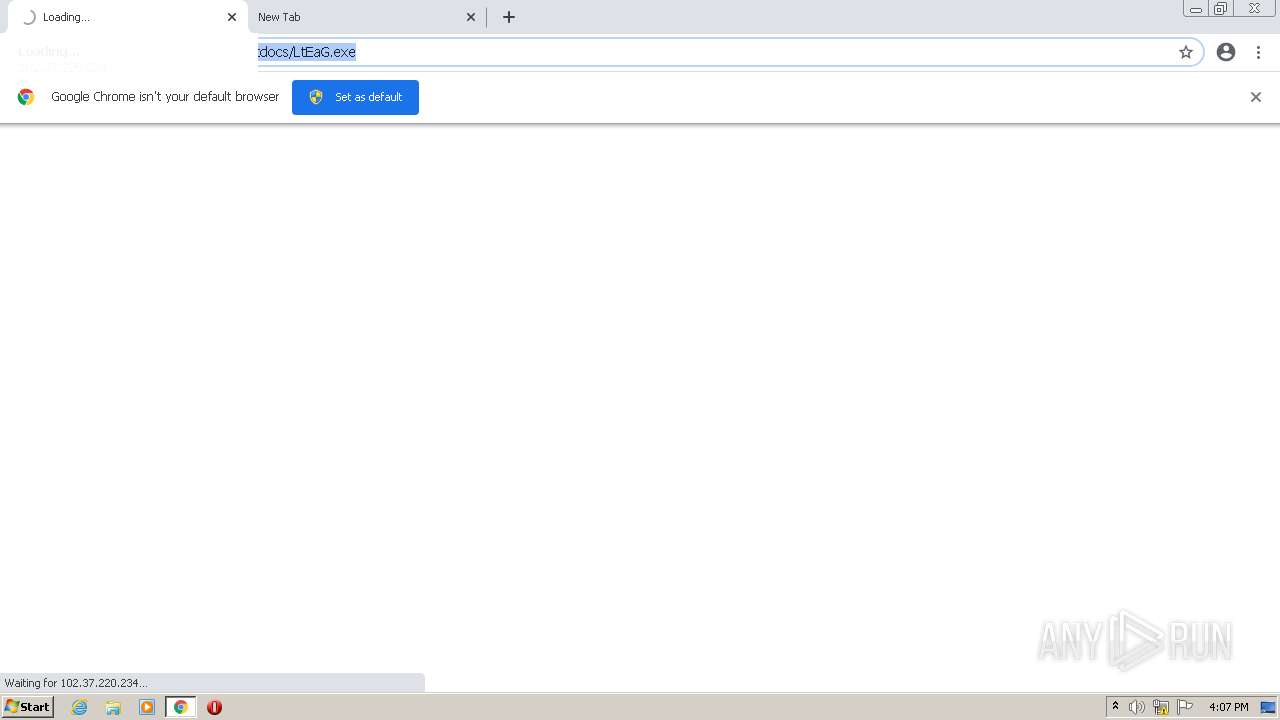
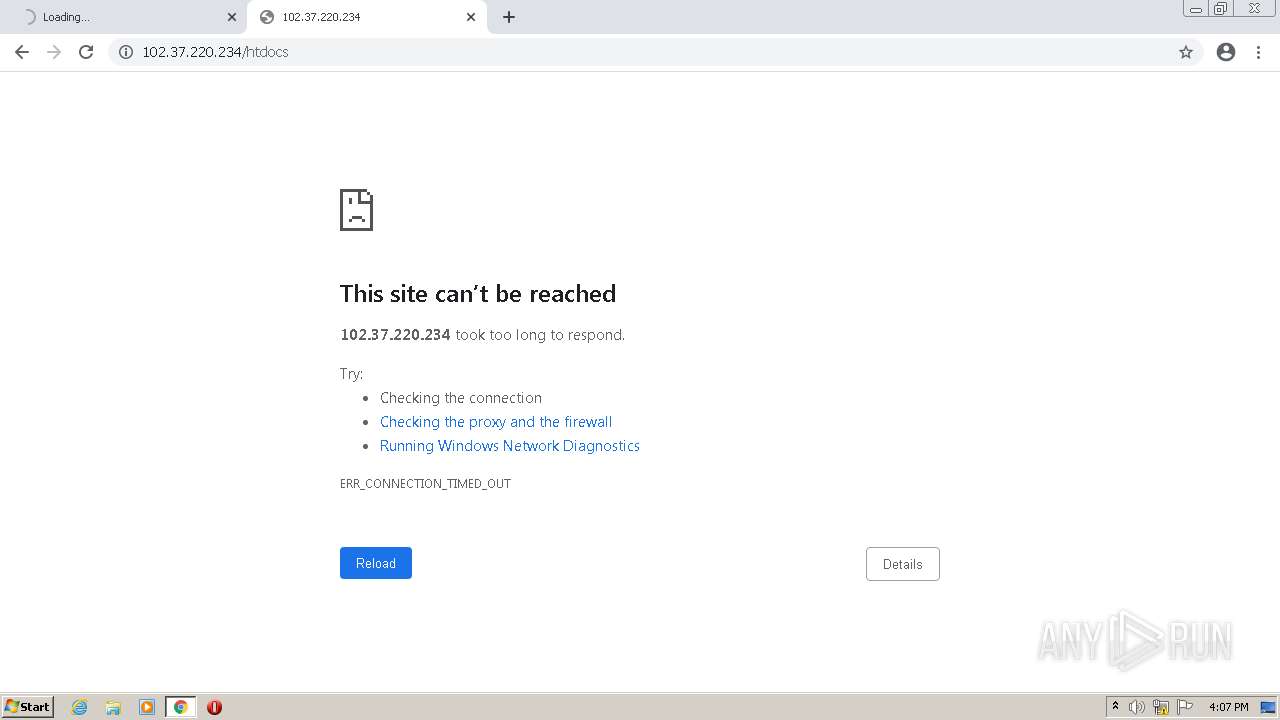
| URL: | http://102.37.220.234/htdocs/LtEaG%2Eexe |
| Full analysis: | https://app.any.run/tasks/4e530531-442a-4d12-9c37-02fa1973538d |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 12, 2022, 15:07:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6D0030B2C5BA7522F29F2324D08DF74D |
| SHA1: | DFB2B534E306075E83F215F68069432E91AA93CD |
| SHA256: | CE266D82EFFDF8645A4F23C6CB34DA543D6C8D5FD1D3C6C49A25F227D29325E9 |
| SSDEEP: | 3:N1KtB9XNdK2Qn:Cn9dI2Qn |
MALICIOUS
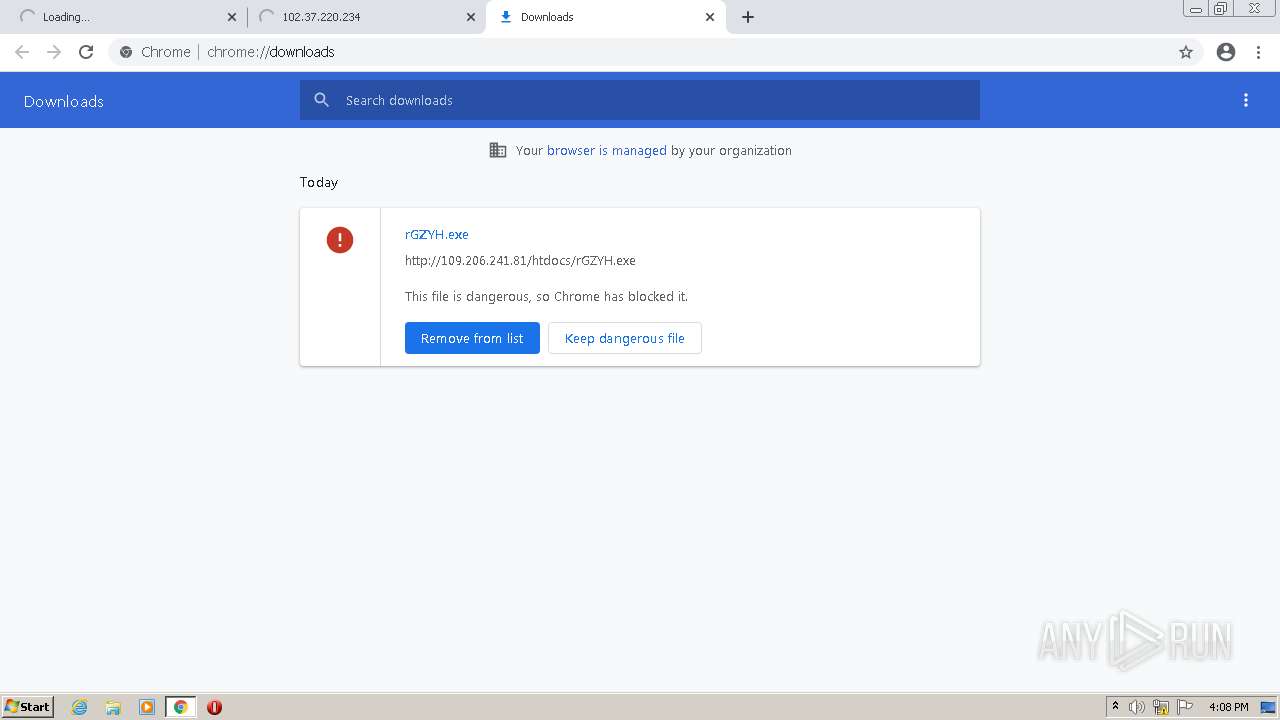
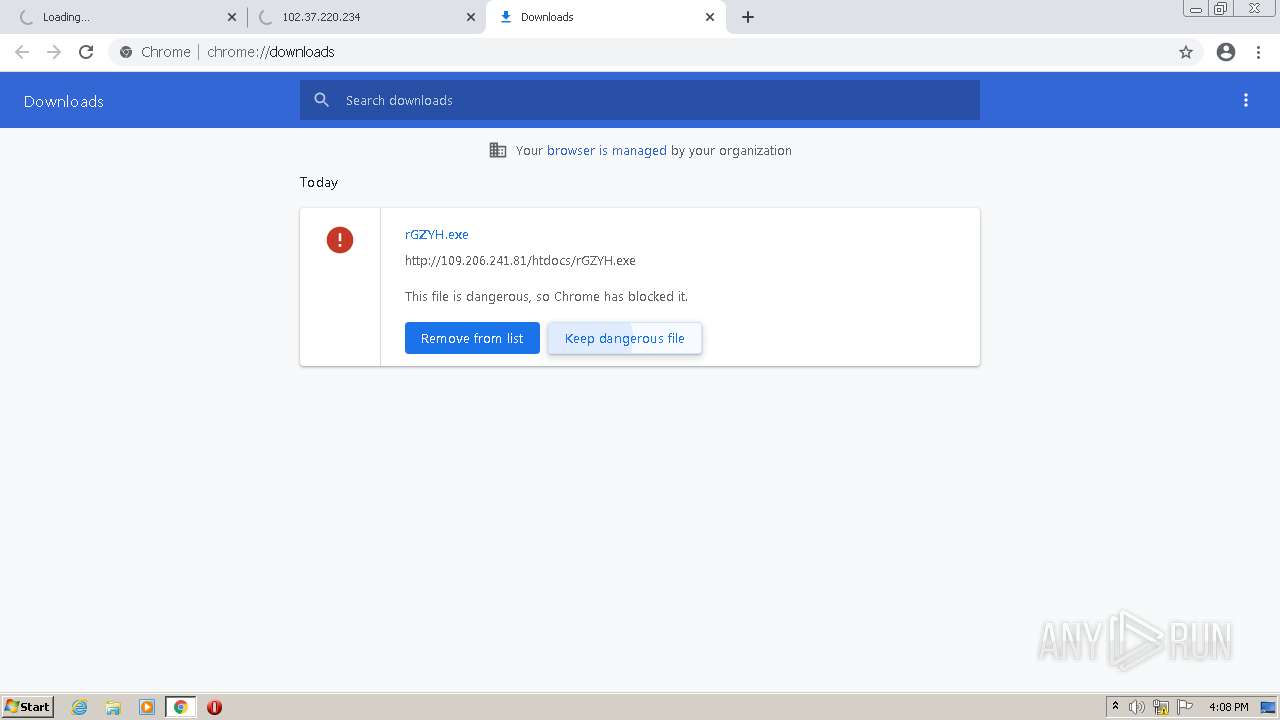
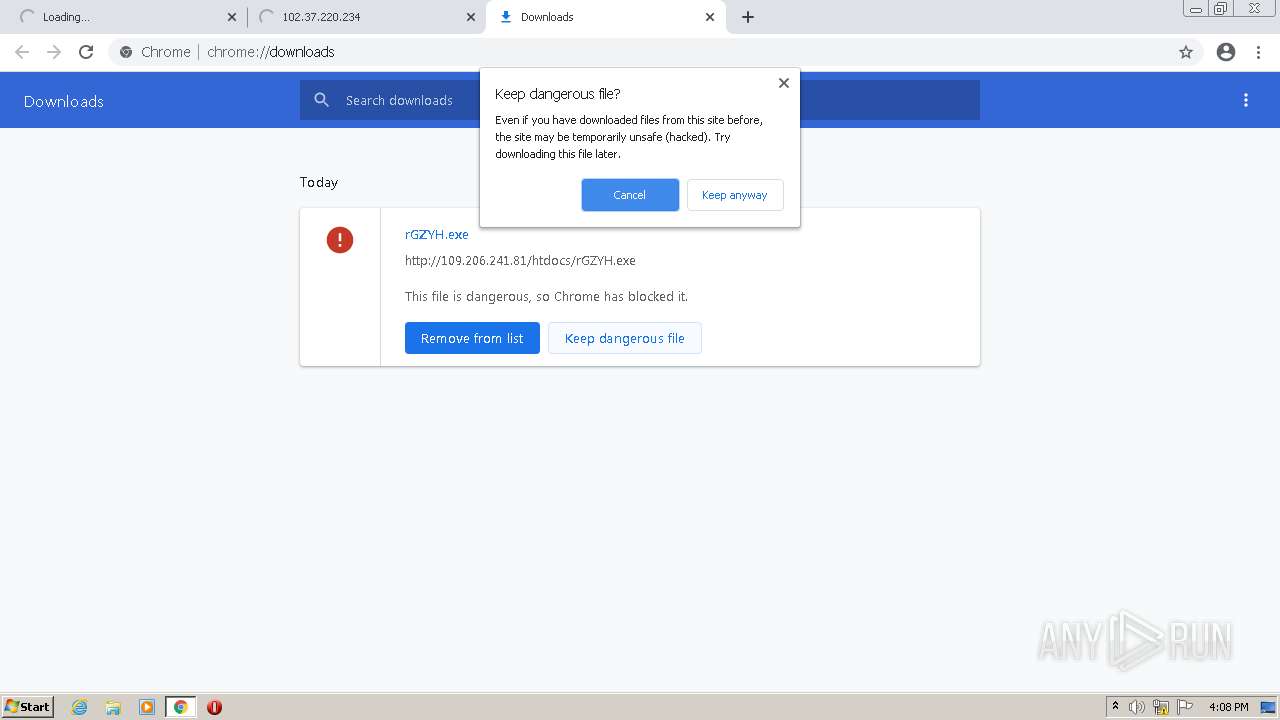
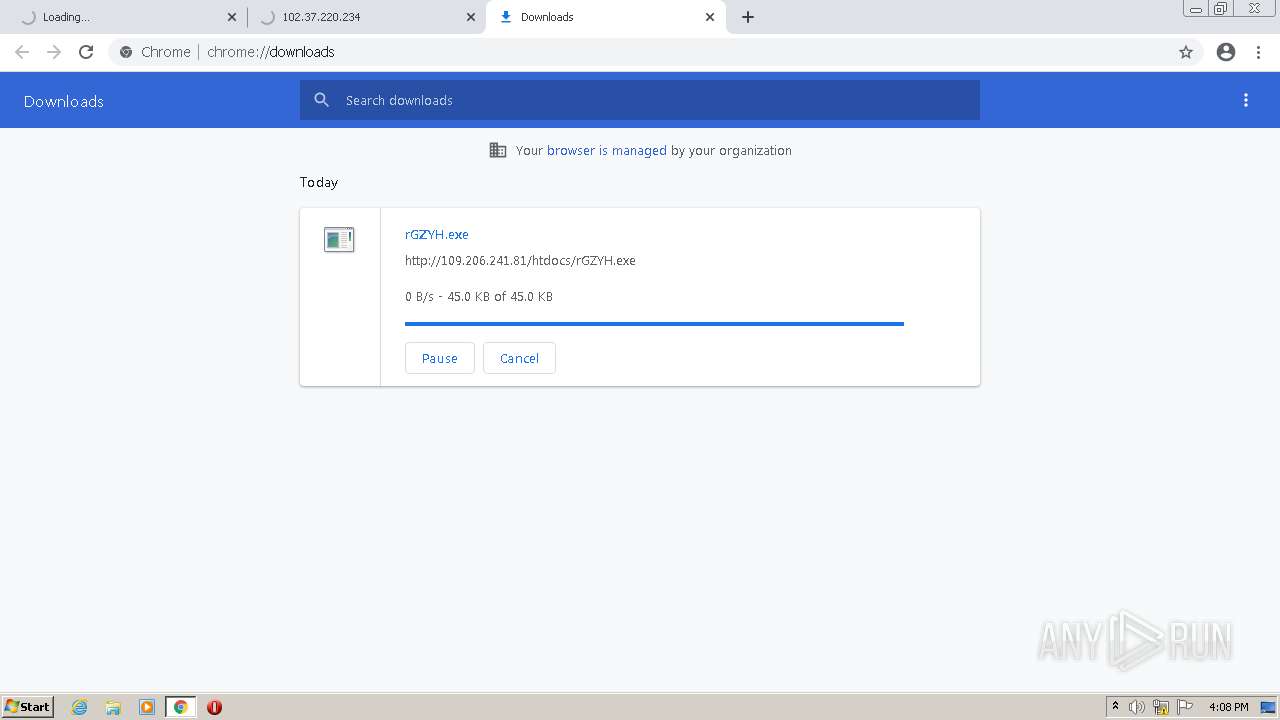
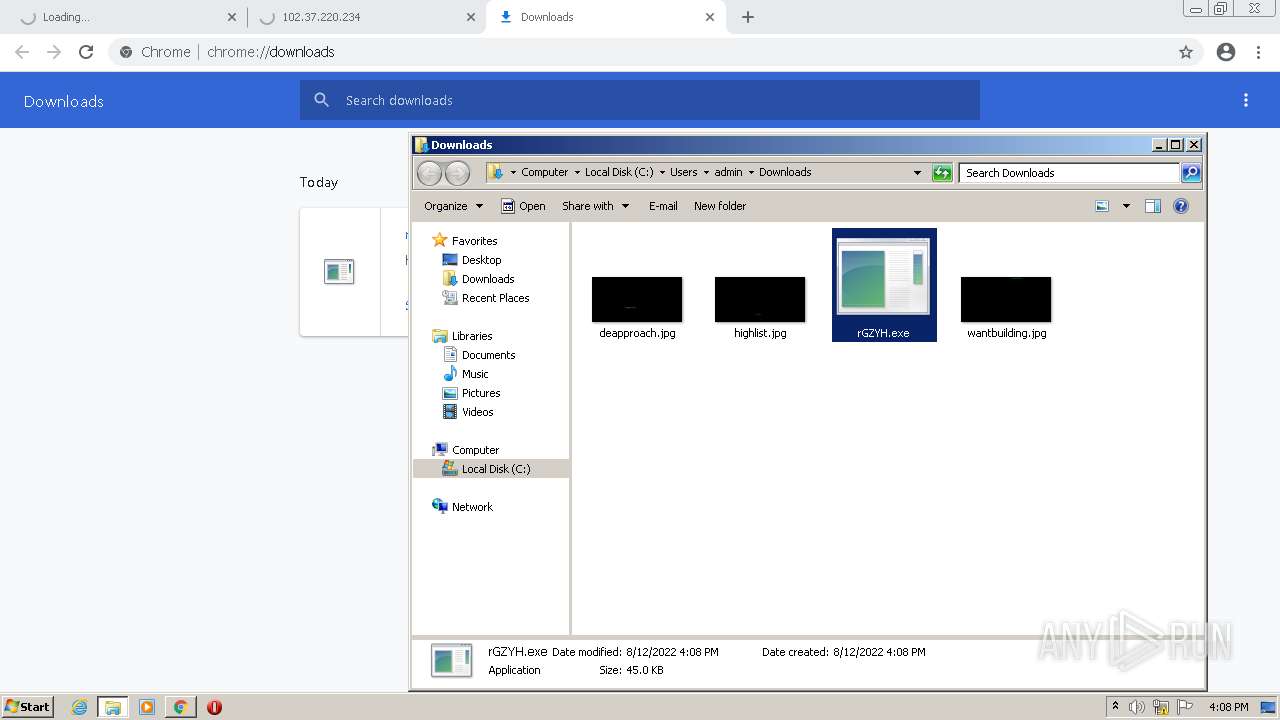
Drops executable file immediately after starts
- chrome.exe (PID: 3908)
- chrome.exe (PID: 2840)
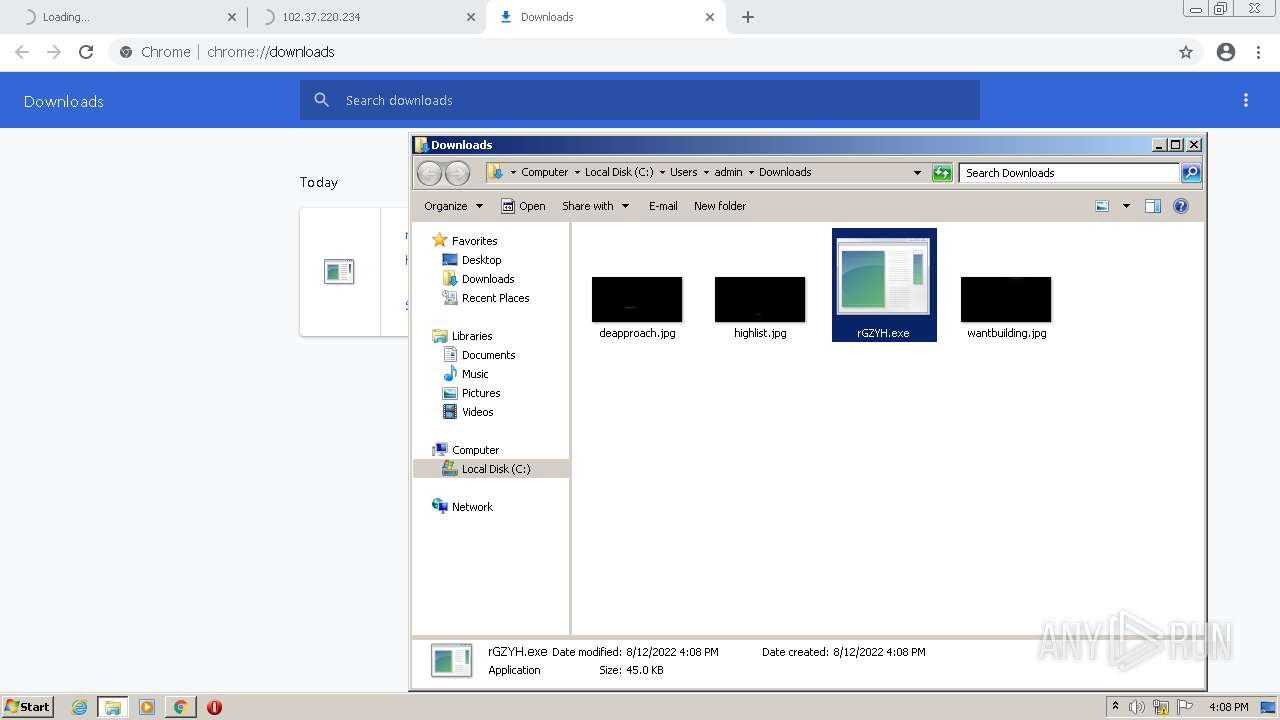
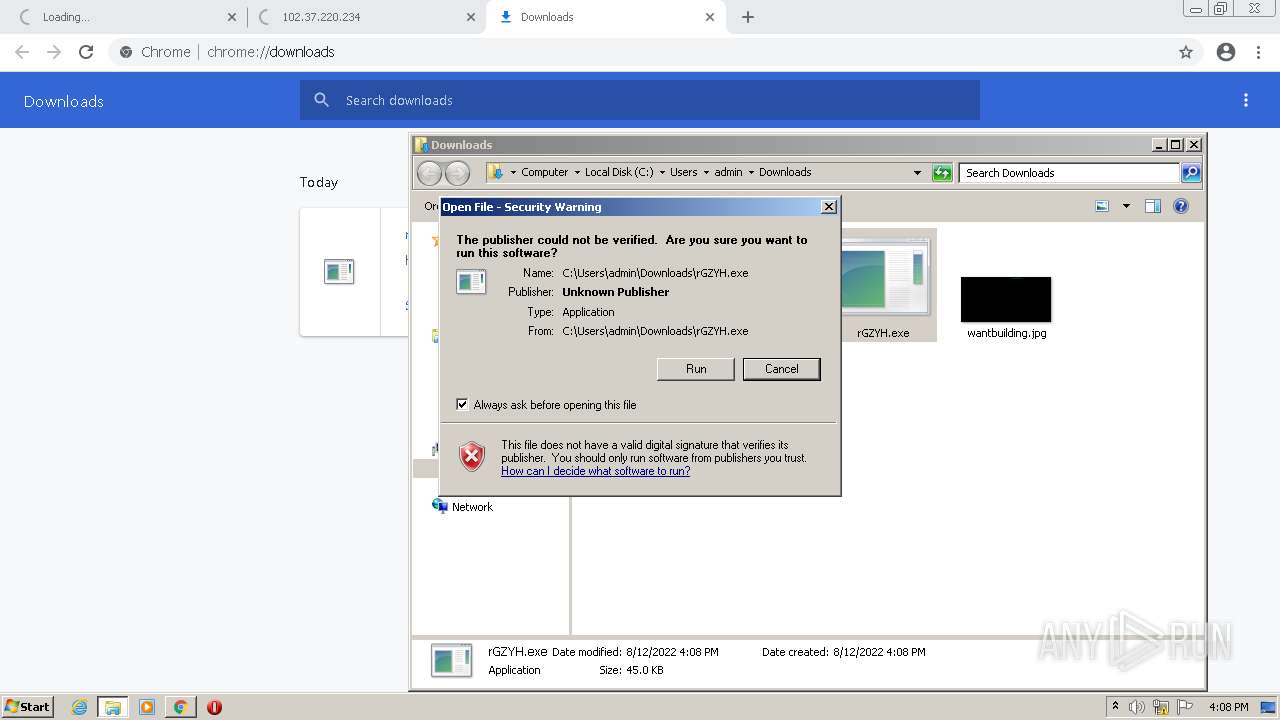
Application was dropped or rewritten from another process
- rGZYH.exe (PID: 3604)
ASYNCRAT detected by memory dumps
- rGZYH.exe (PID: 3604)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2840)
Executable content was dropped or overwritten
- chrome.exe (PID: 2840)
Drops a file with a compile date too recent
- chrome.exe (PID: 2840)
- chrome.exe (PID: 3908)
Reads the computer name
- rGZYH.exe (PID: 3604)
Checks supported languages
- rGZYH.exe (PID: 3604)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3908)
Checks supported languages
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 860)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 1064)
- chrome.exe (PID: 984)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 824)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3444)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 408)
- chrome.exe (PID: 672)
- chrome.exe (PID: 752)
- chrome.exe (PID: 1752)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 752)
- chrome.exe (PID: 688)
Reads the computer name
- chrome.exe (PID: 824)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 672)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 3912)
Application launched itself
- chrome.exe (PID: 2840)
Checks Windows Trust Settings
- chrome.exe (PID: 2840)
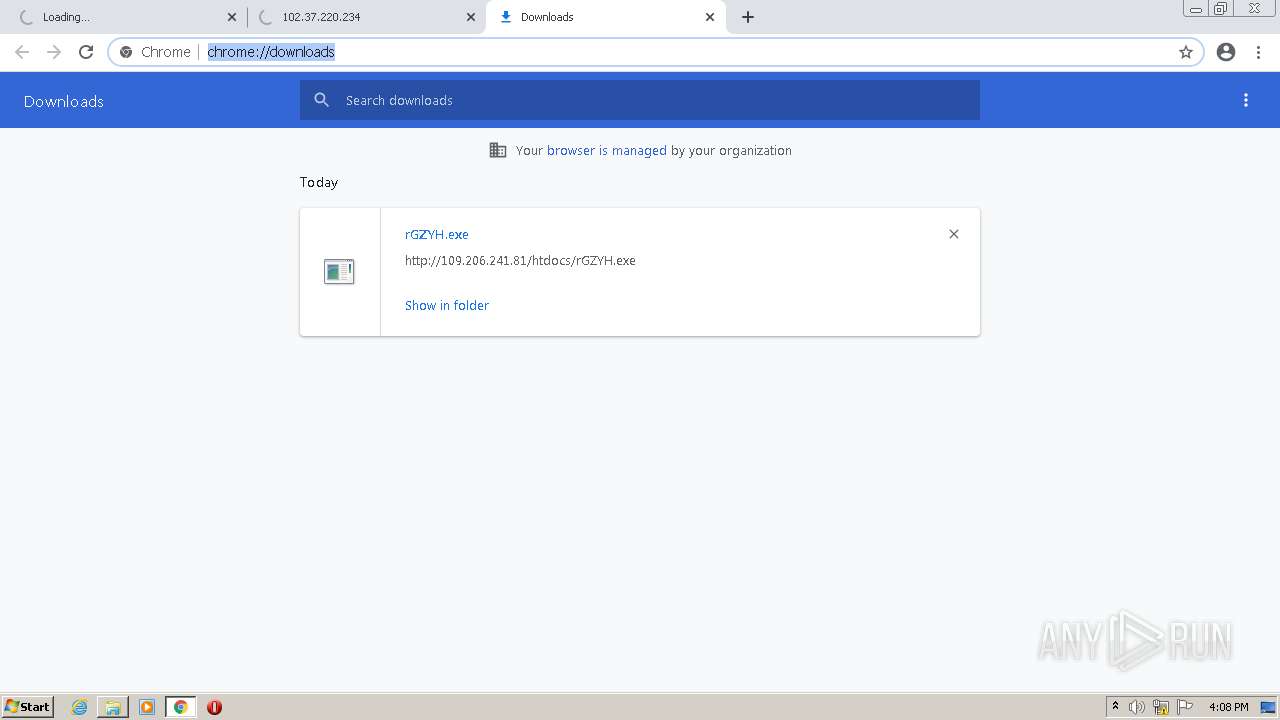
Manual execution by user
- rGZYH.exe (PID: 3604)
Reads the date of Windows installation
- chrome.exe (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3604) rGZYH.exe
C2 (1)192.168.1.4
Ports (3)6606
7707
8808
Version0.5.7B
Autorunfalse
MutexAsyncMutex_6SI8OkPnk
CertificateMIIE8jCCAtqgAwIBAgIQAIueiMi0Tm8cqYkZ5FhU9zANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwODA3MDEzMTU3WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAOXNed9gsiCTH2fX6vtkx+y32r9wBZ606jcsG9Ug/Cw1tCvewEpeornQub0ICNnb+Ijlfjd5rtsy...
Server_SignaturedGOmrIHDiZOy/WsZDuxFnngXb6JN1anudw4OQFUApuqTkUKGfeViLSKW4a4dA9VU614w3BO8b0I5QG2pCCe2/uF6yriVSCIP3EBaTpm5A1CtWmzGcbWHQAVy9hzjw+Uz366S+XTxJkRy1963fhJccTDZTM2FrBF7jtLR9qVcdlihMRgTu0BKLQZcazeEvG4LLdFGDxJNO/Gk22mUZdsEy/+kc2w+INTH9AiRq2+tqmjy3V3M88HlcNXU3qkGgCUxfc5pA6vOzdUWTyQmX0wCsgDY1iDaVQmrLQm/ieJI7J+f...
AntiVMfalse
PasteBinnull
bdosfalse
BotnetDefault
Aes_Key7742869abdeaa7d848a4749439ae87d592f75f1e3a30d6027cf6749b21aa978b
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Install_Folder%AppData%
Total processes
66
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4876 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4708 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2688 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1060,18270905066931150298,5944304157618418974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
9 963
Read events
9 849
Write events
108
Delete events
6
Modification events
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
3
Suspicious files
21
Text files
124
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F66CAF-B18.pma | — | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e9365e99-ec15-4524-9c7b-d48fb075d0b8.tmp | text | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFda27a.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFd9f3e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFd9f8c.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFda0b5.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd9dc7.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
56
DNS requests
14
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
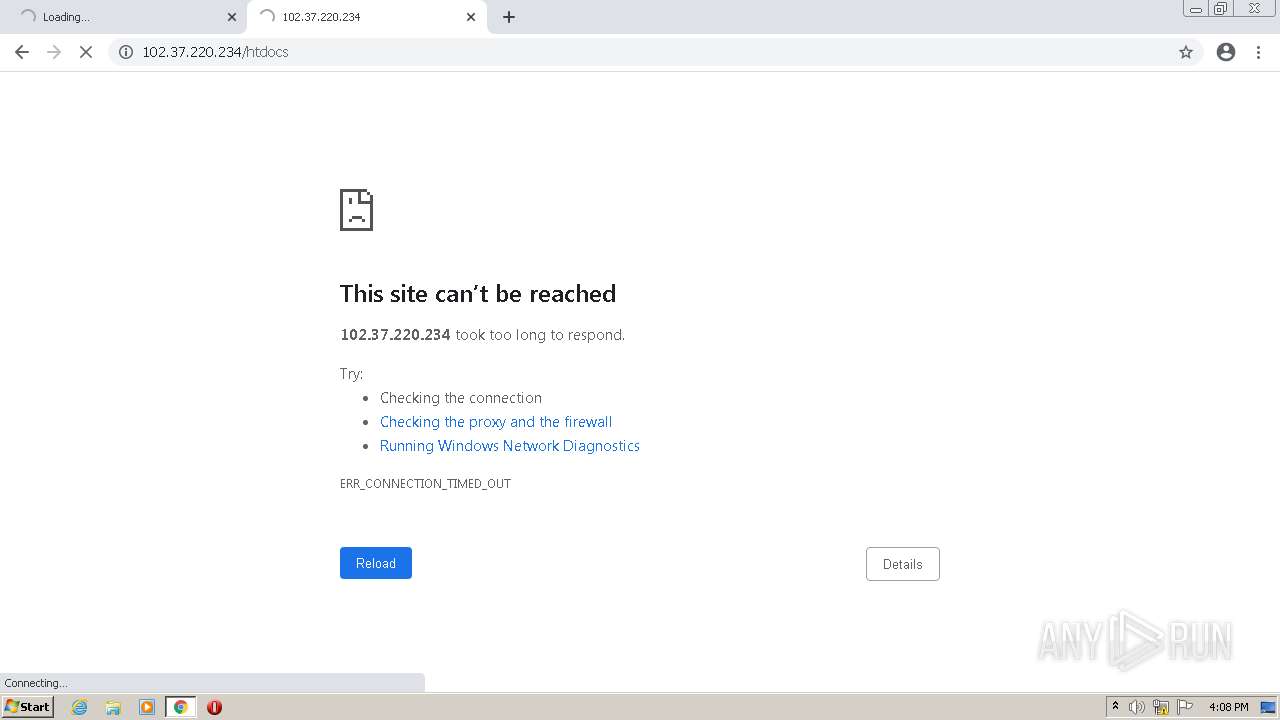
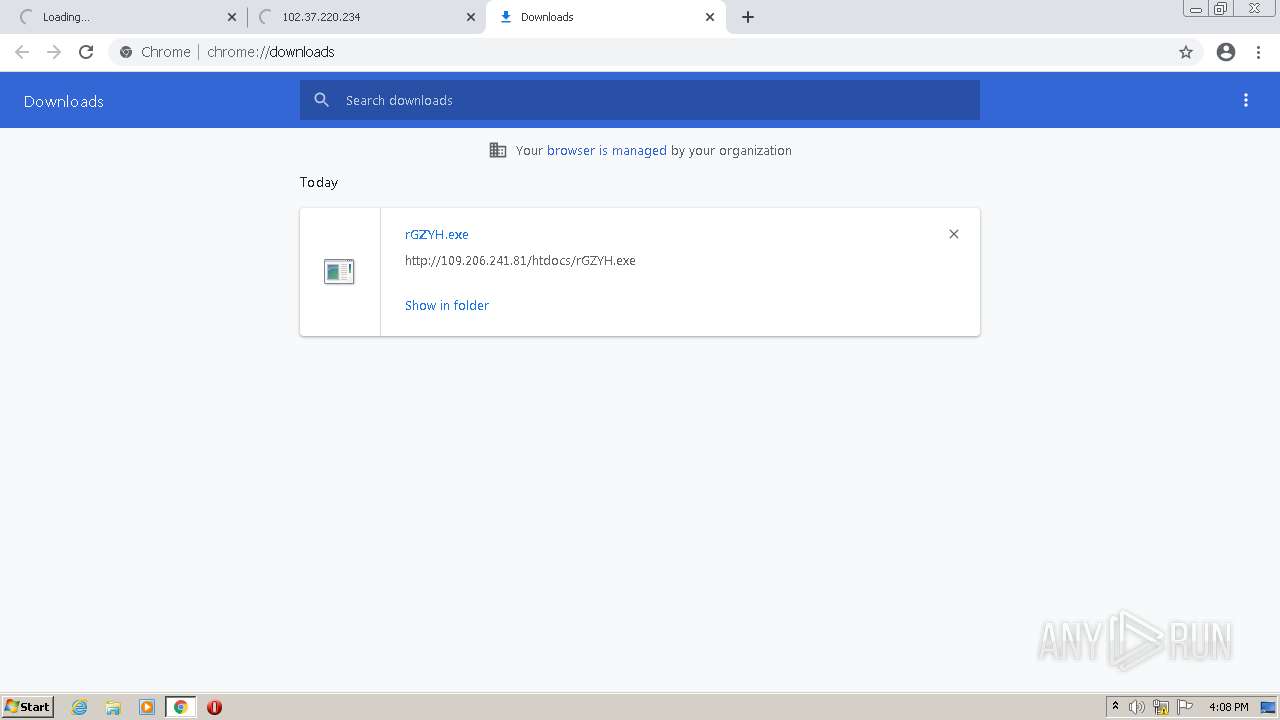
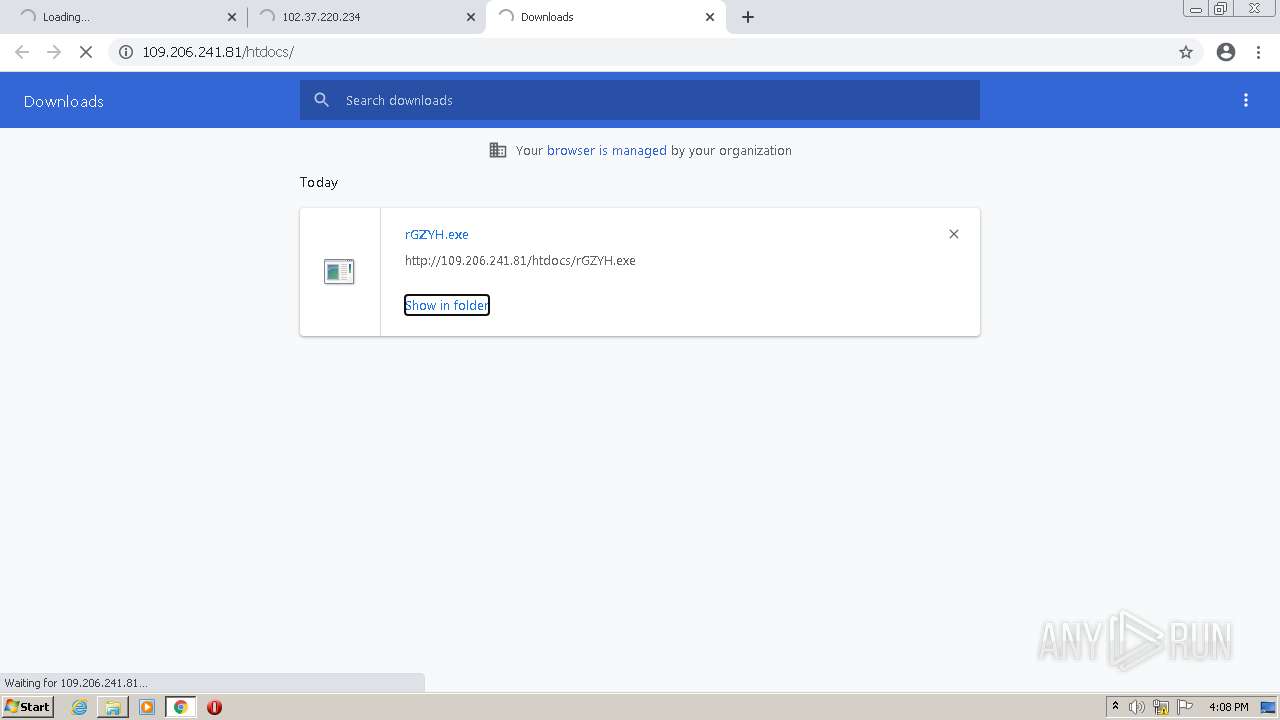
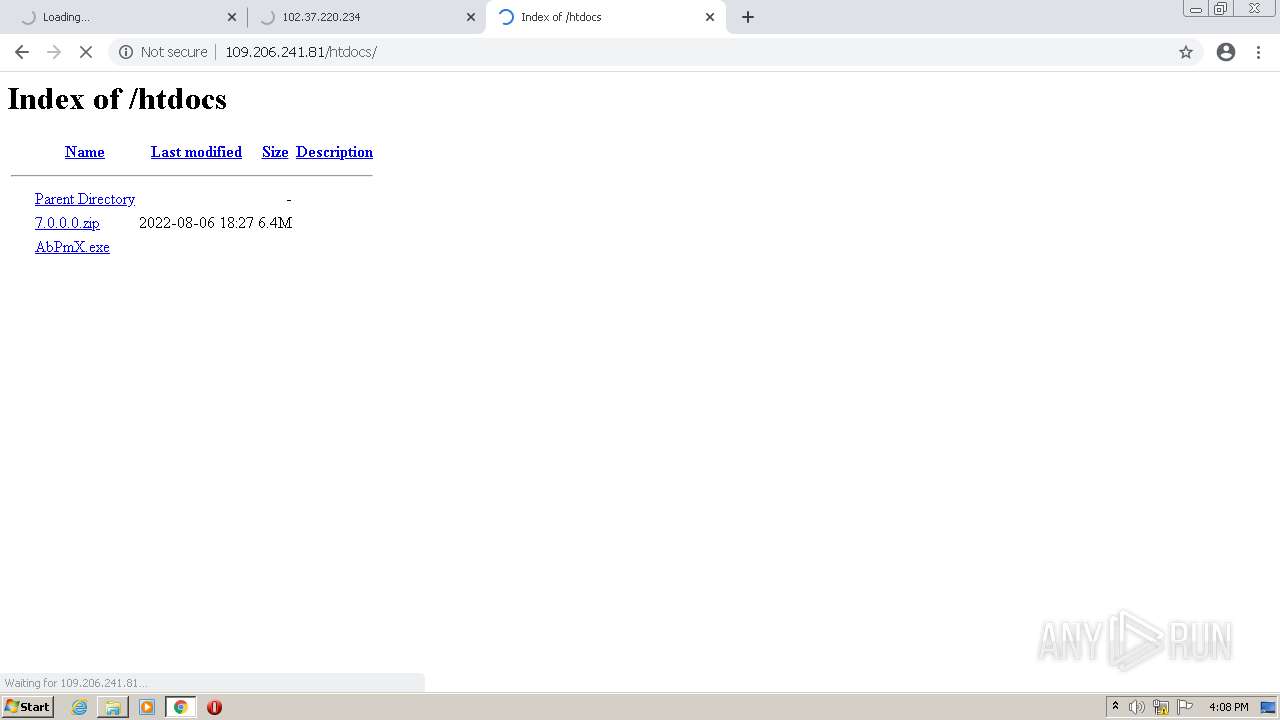
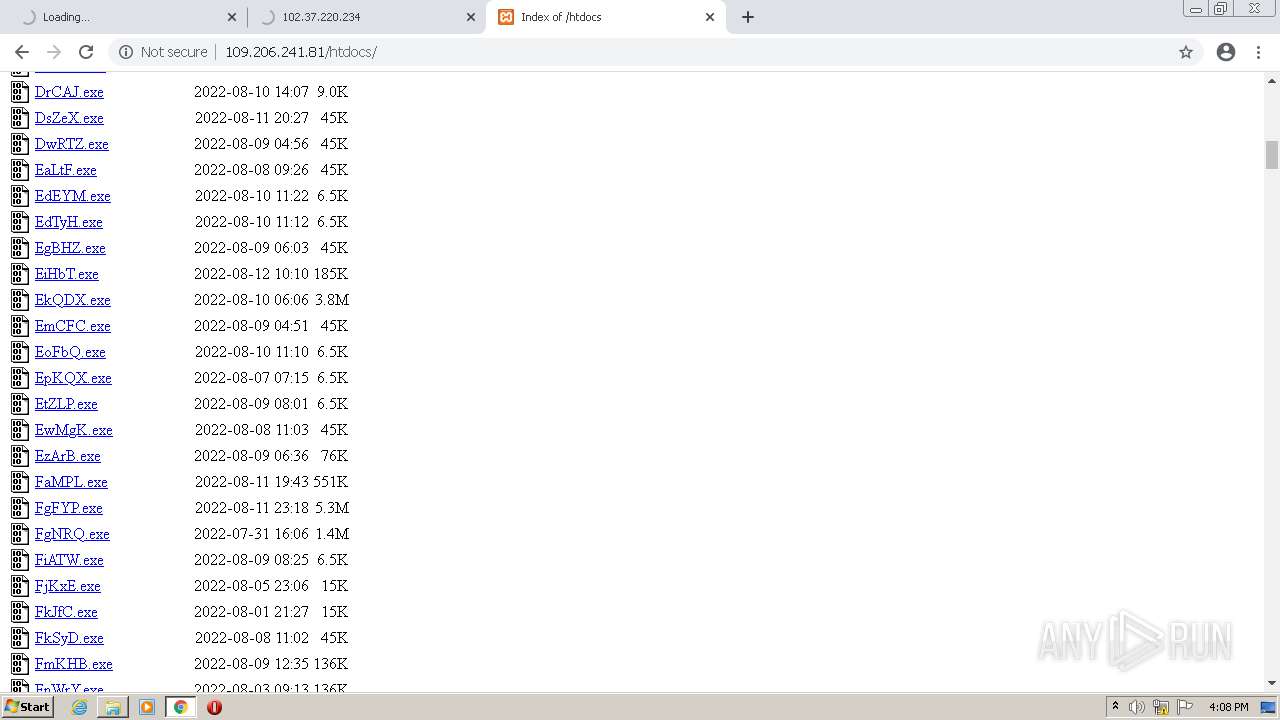
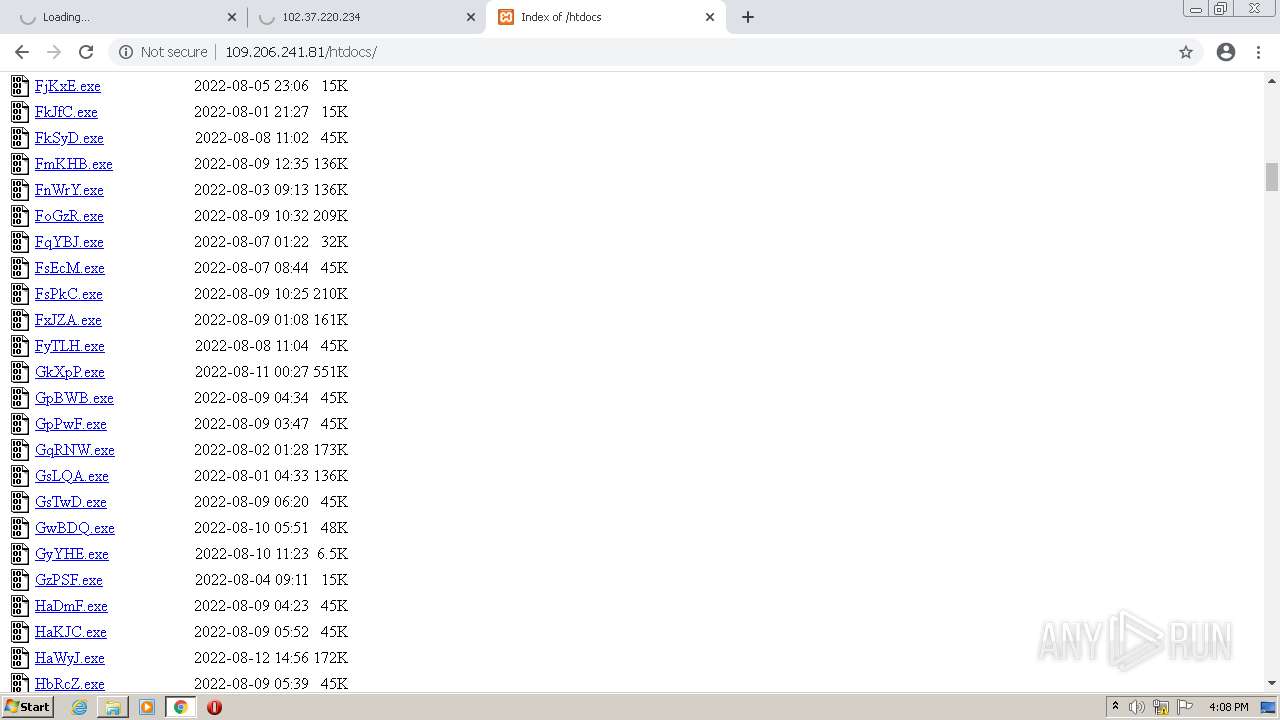
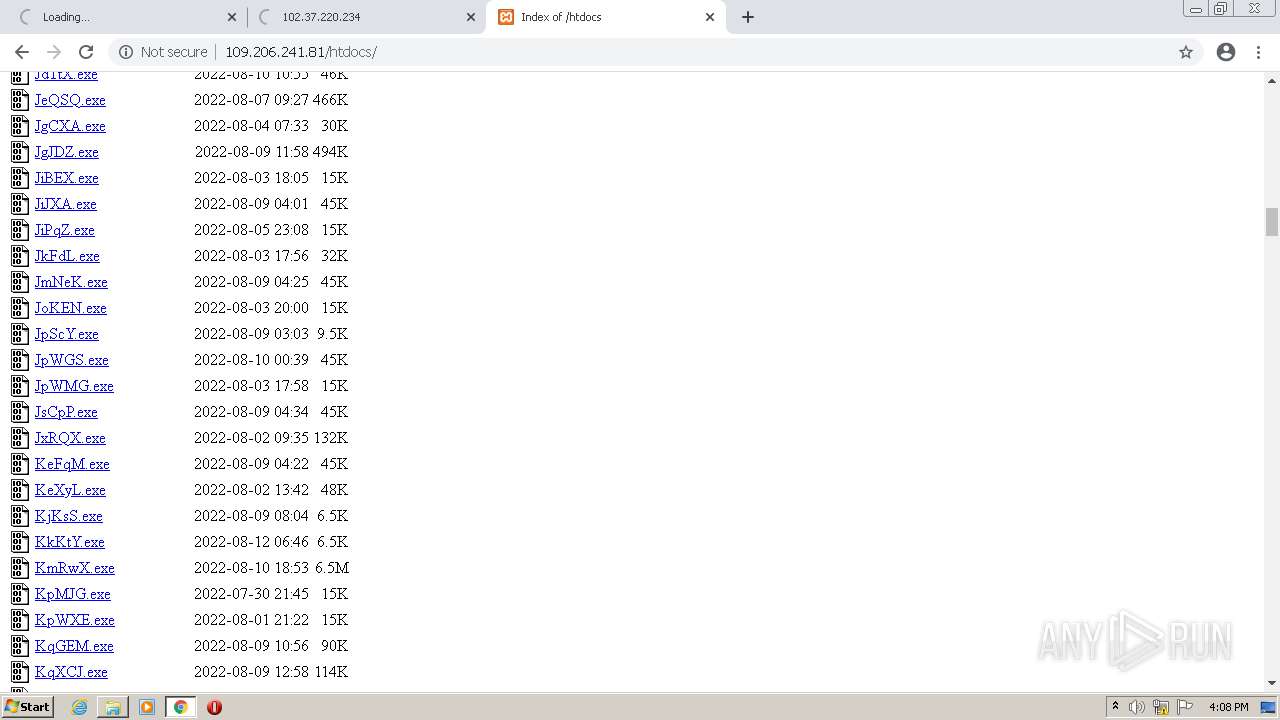
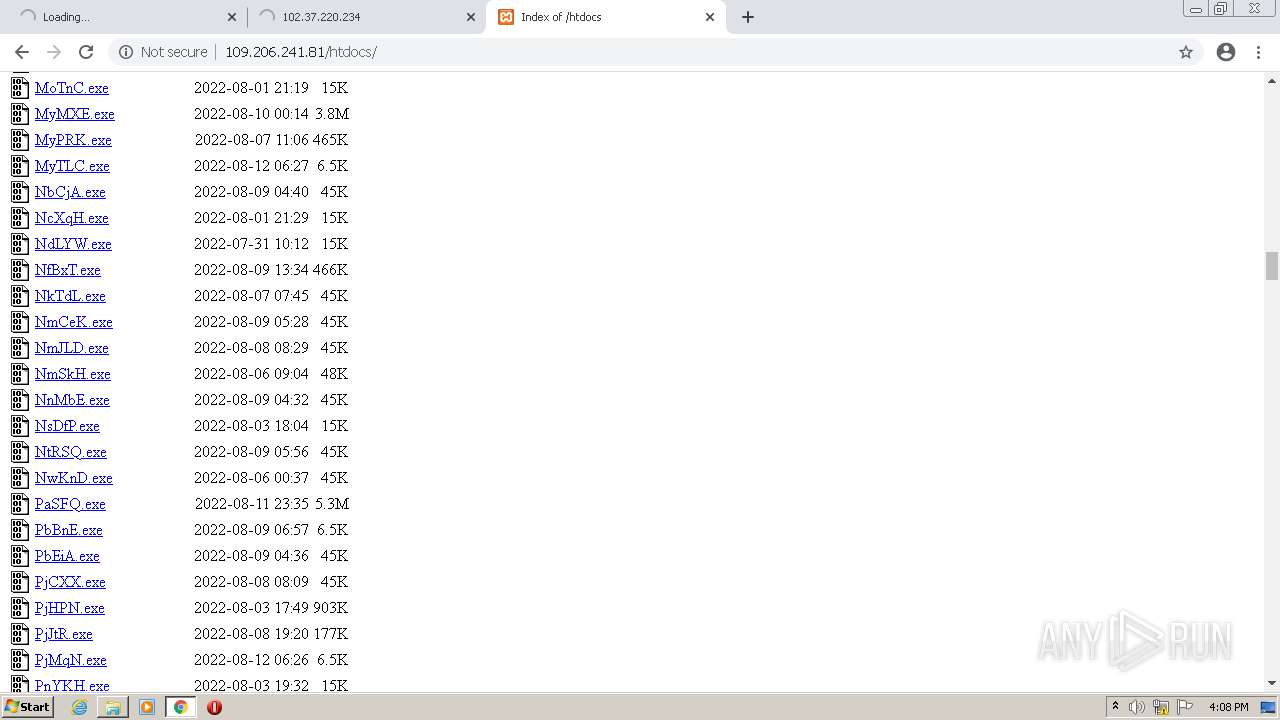
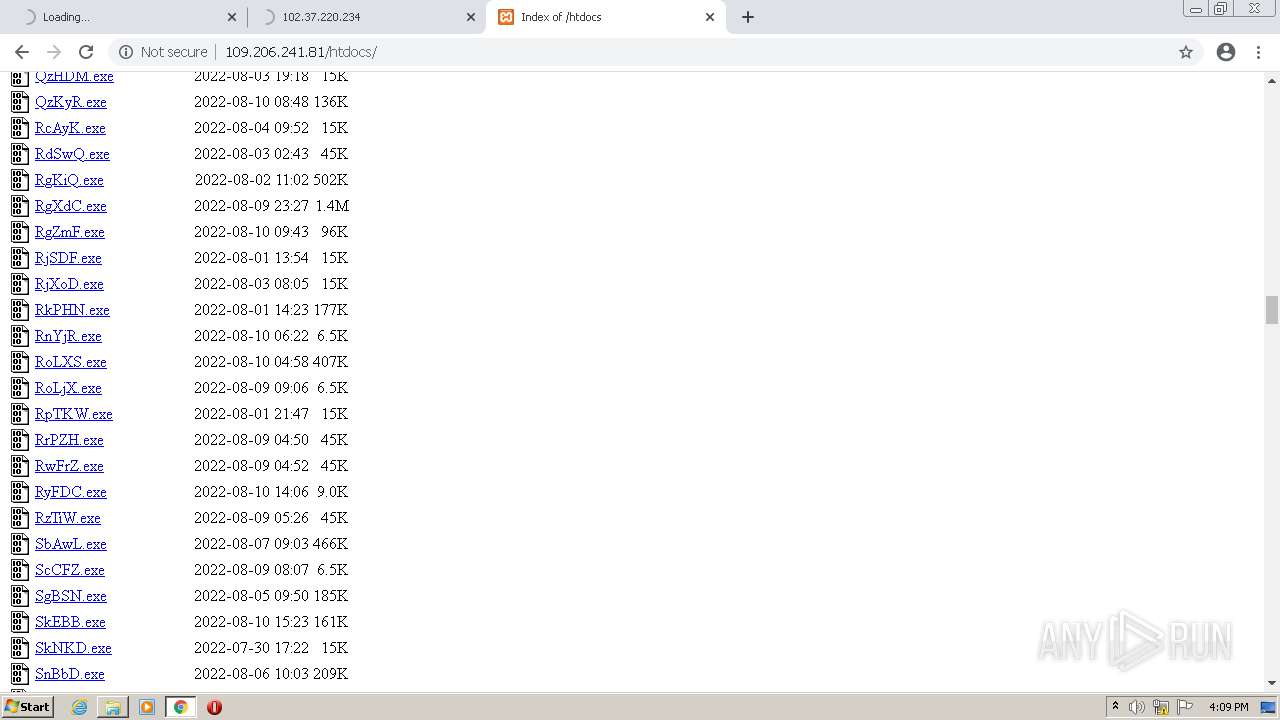
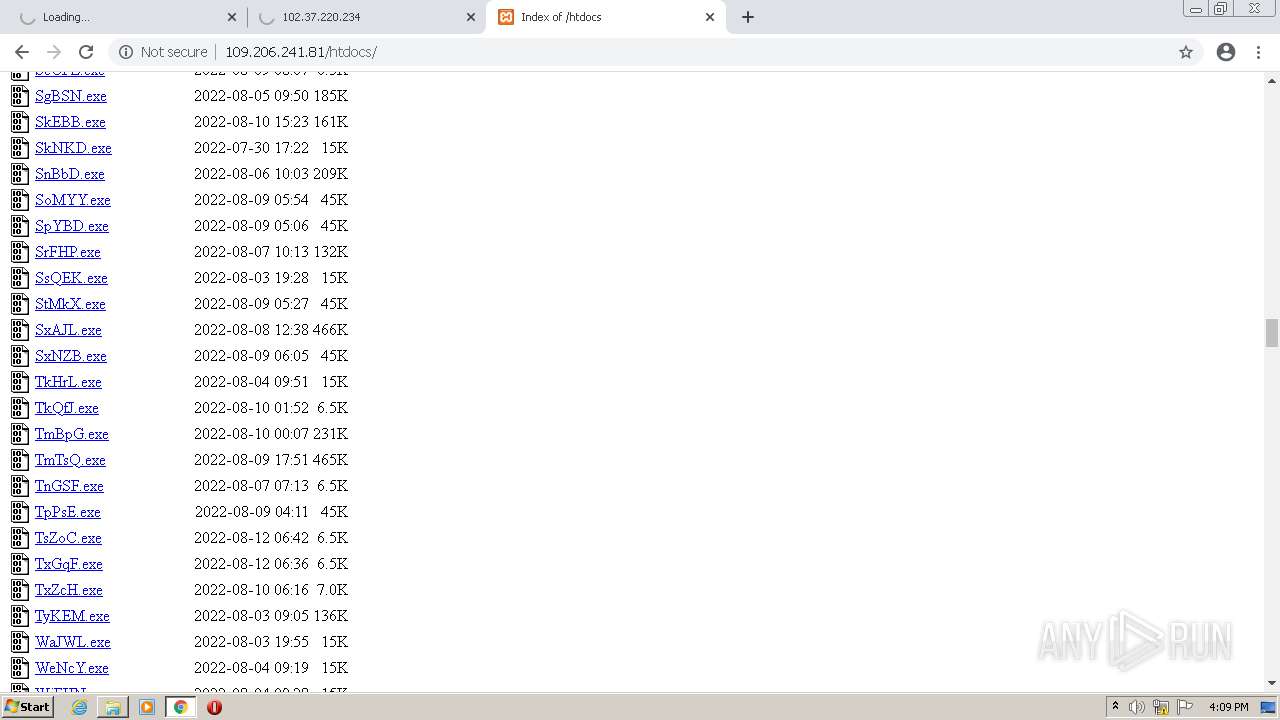
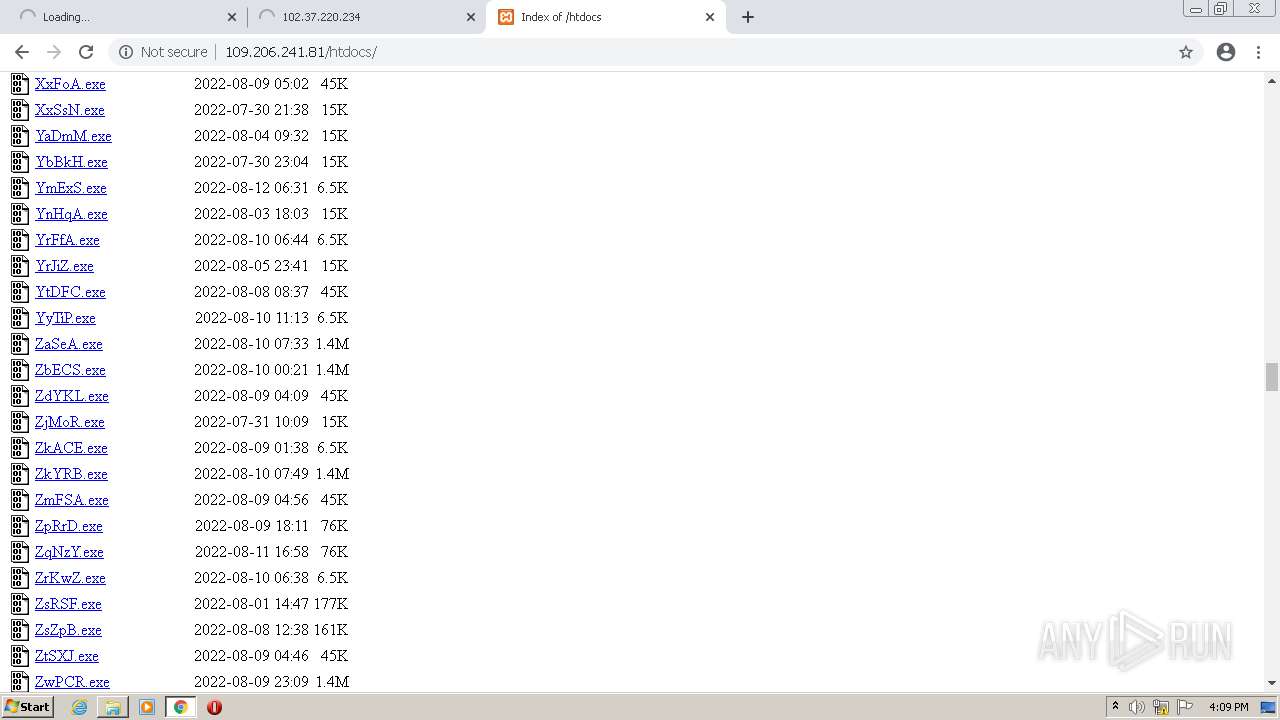
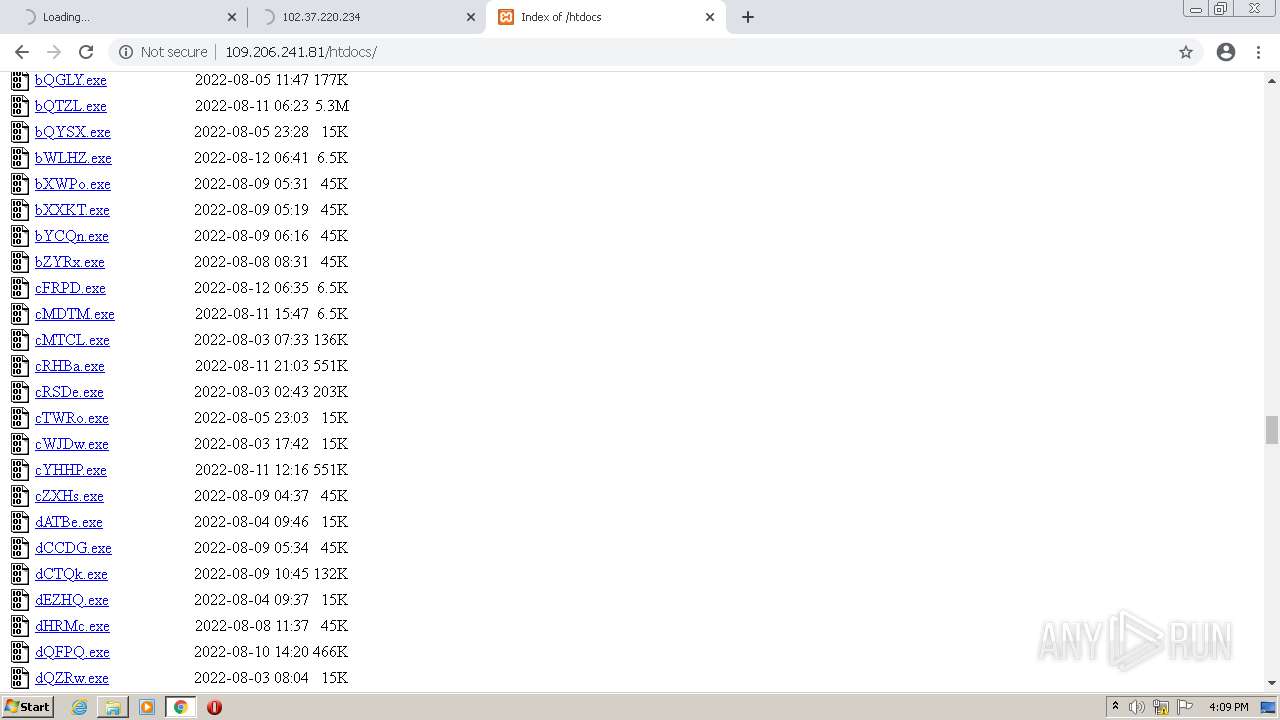
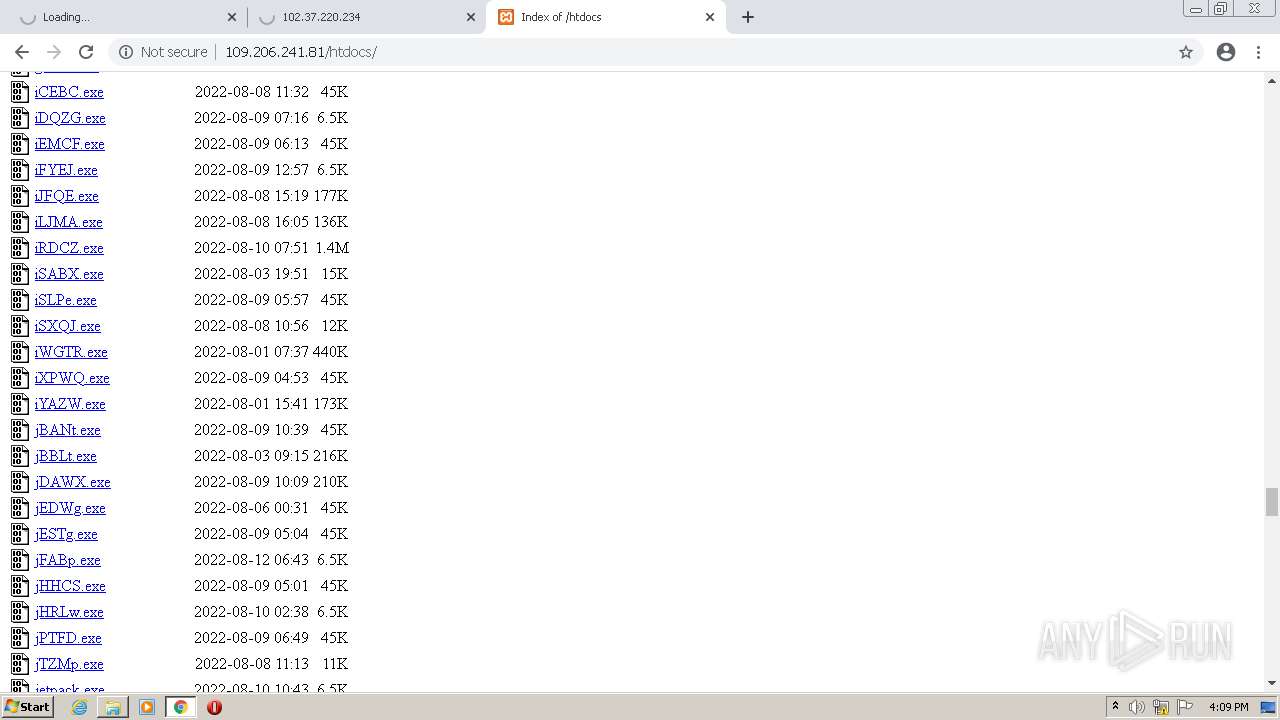
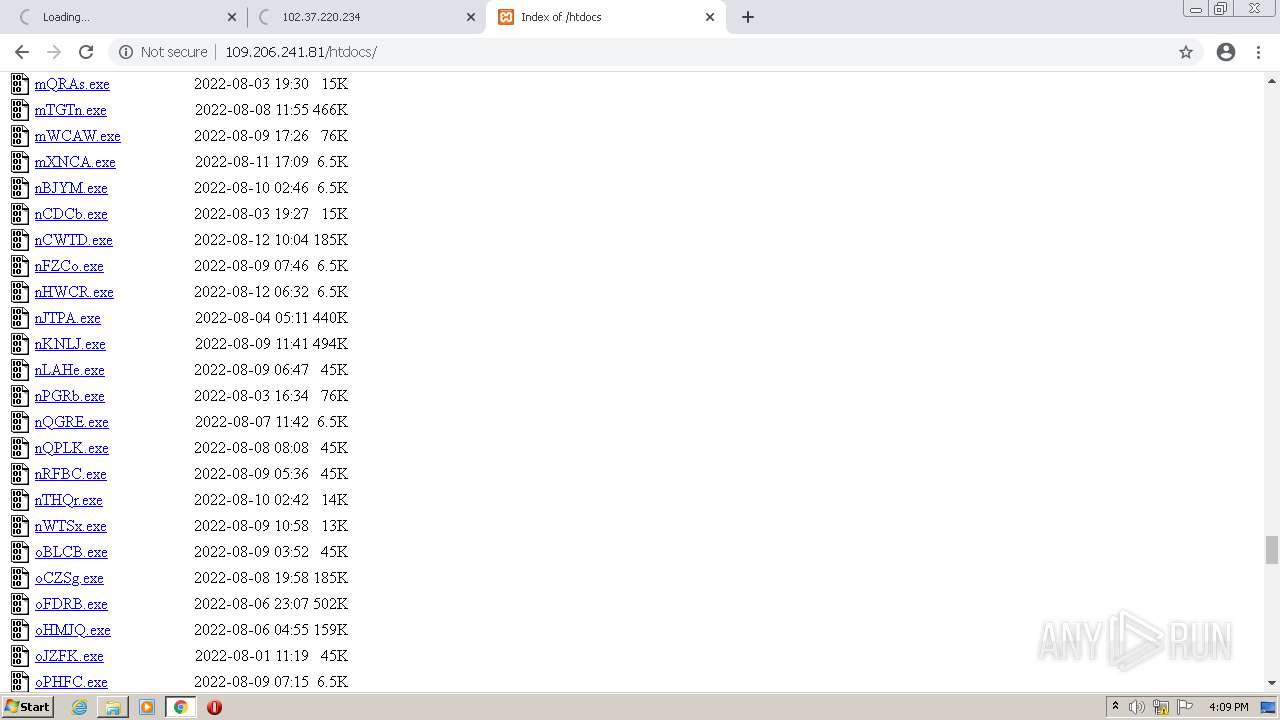
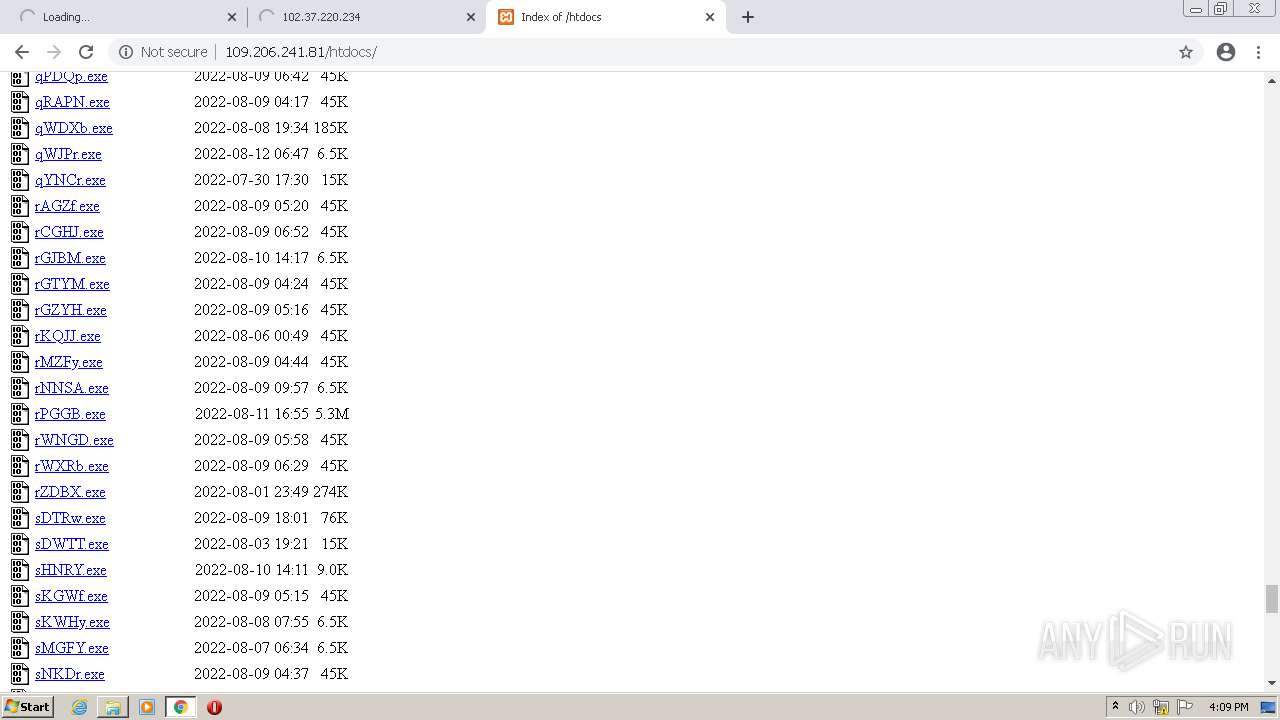
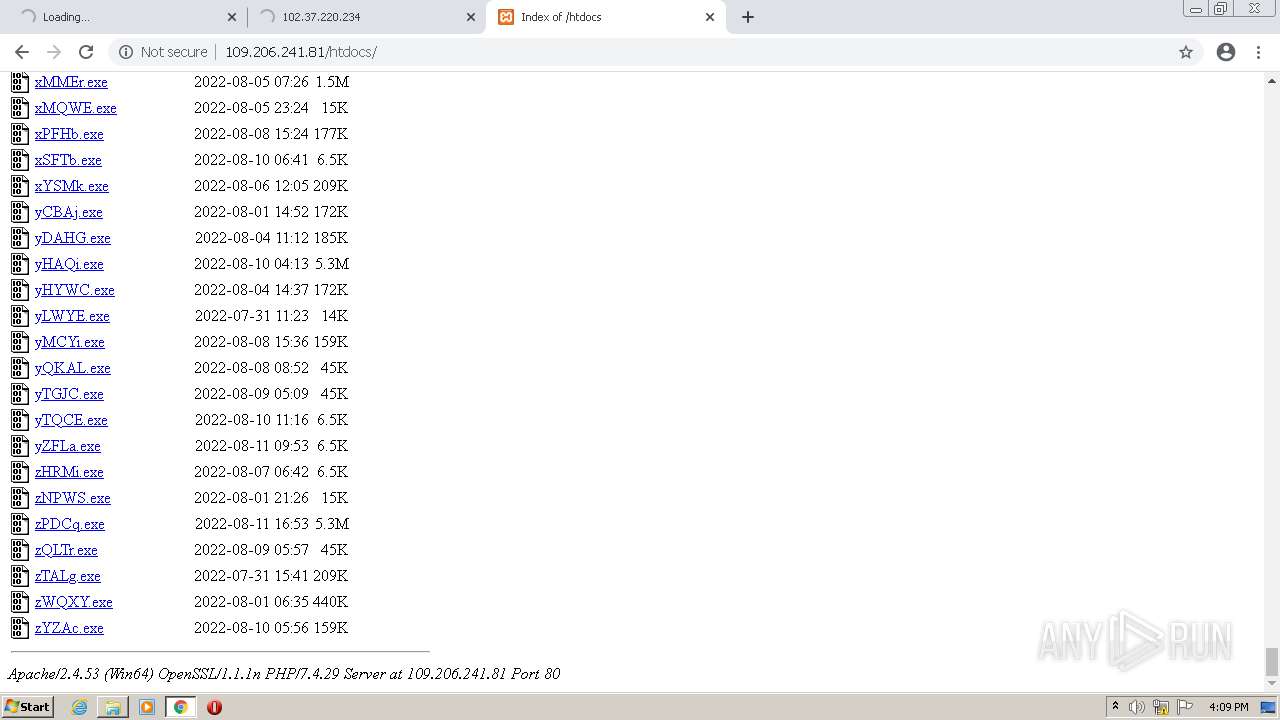
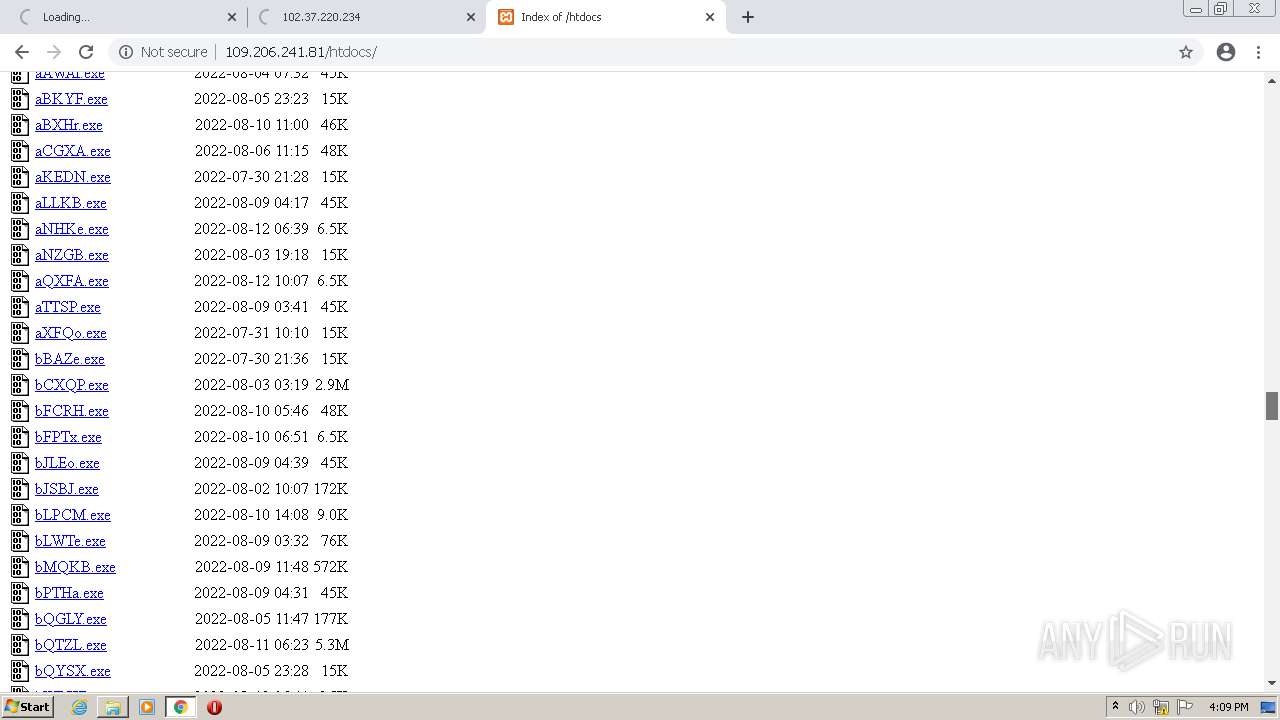
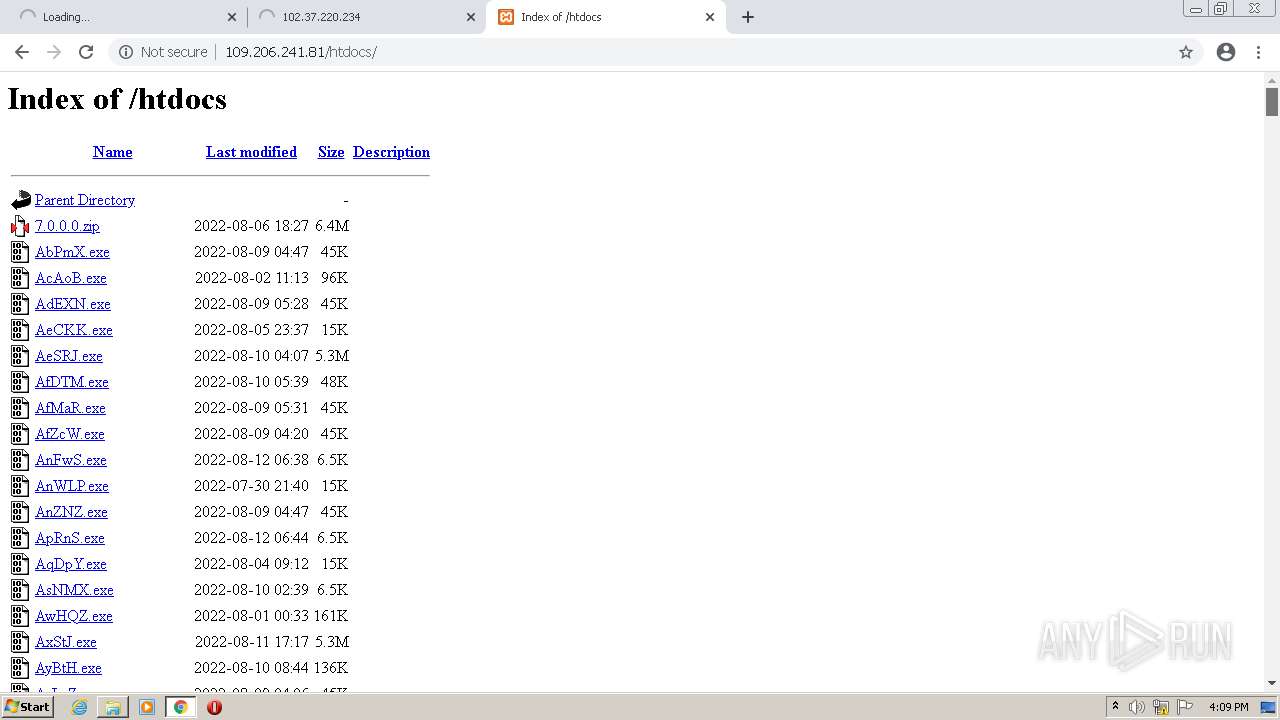
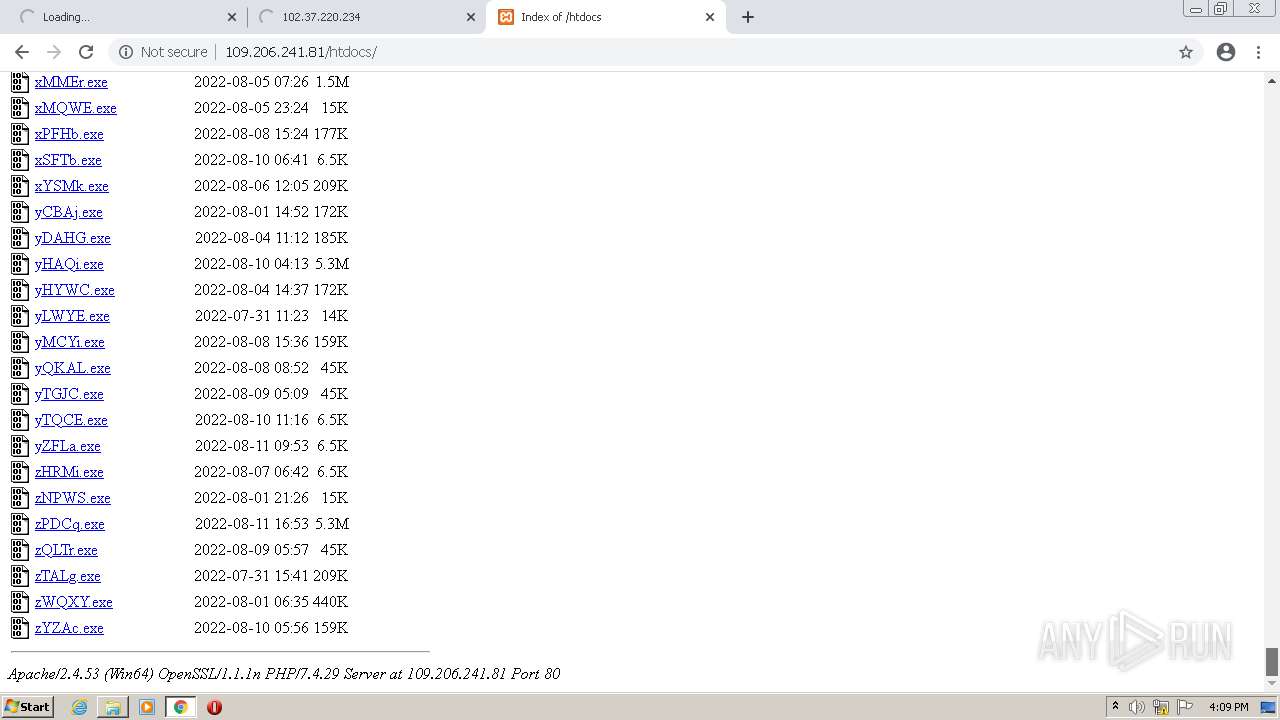
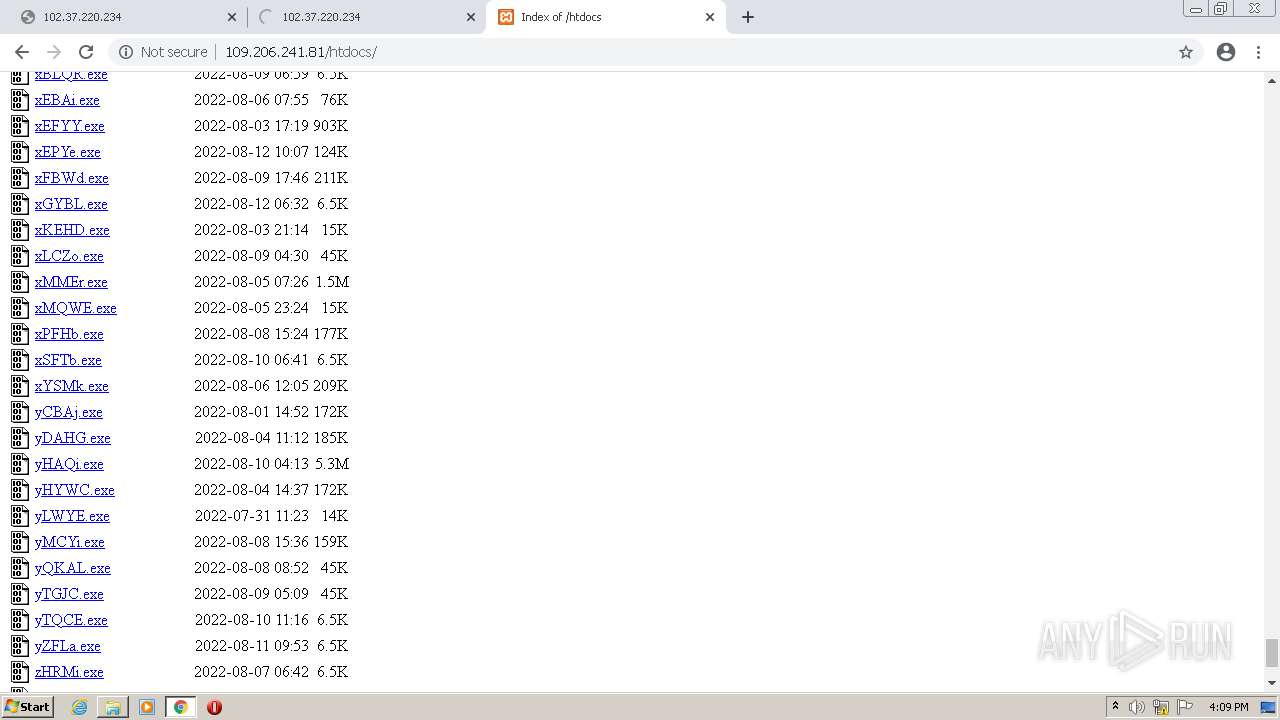
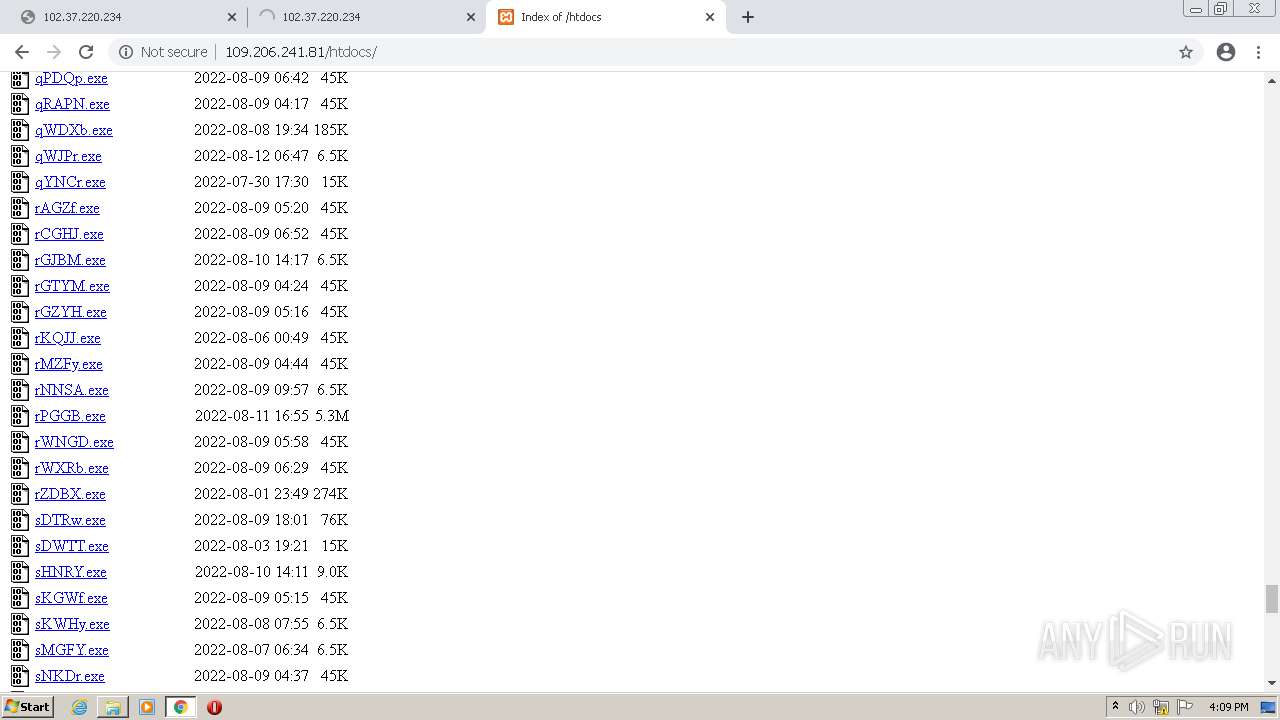
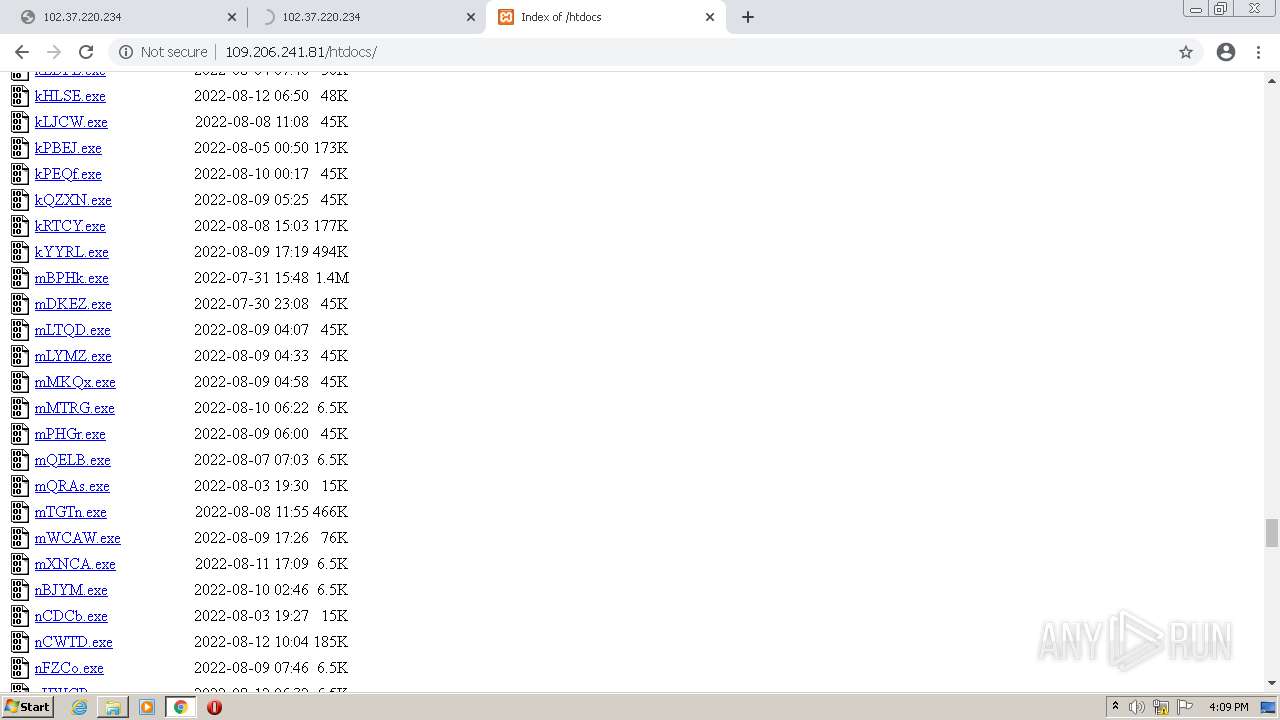
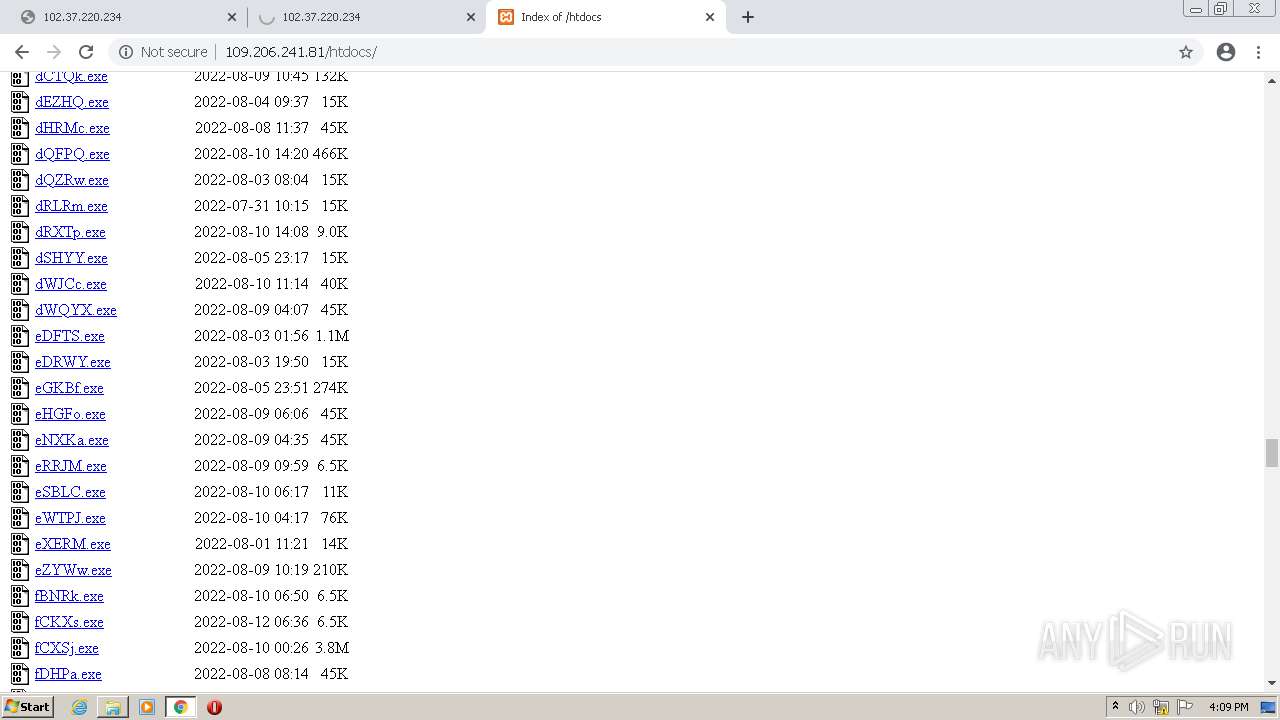
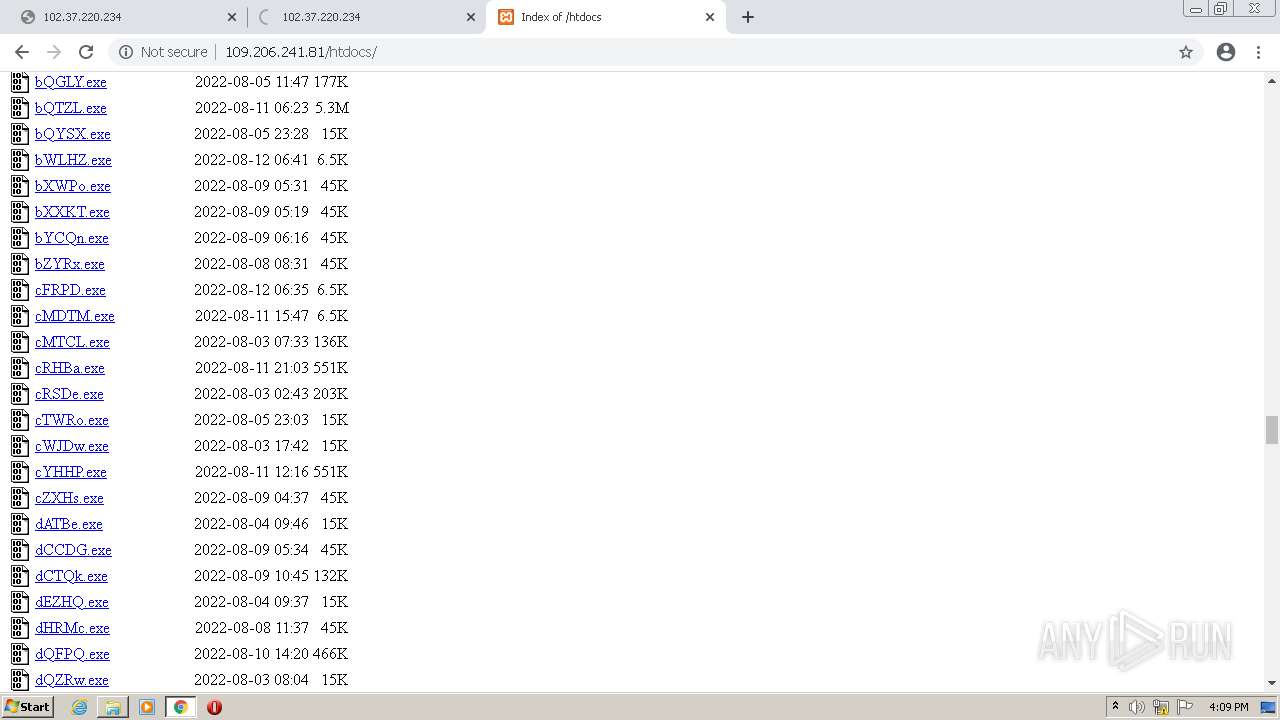
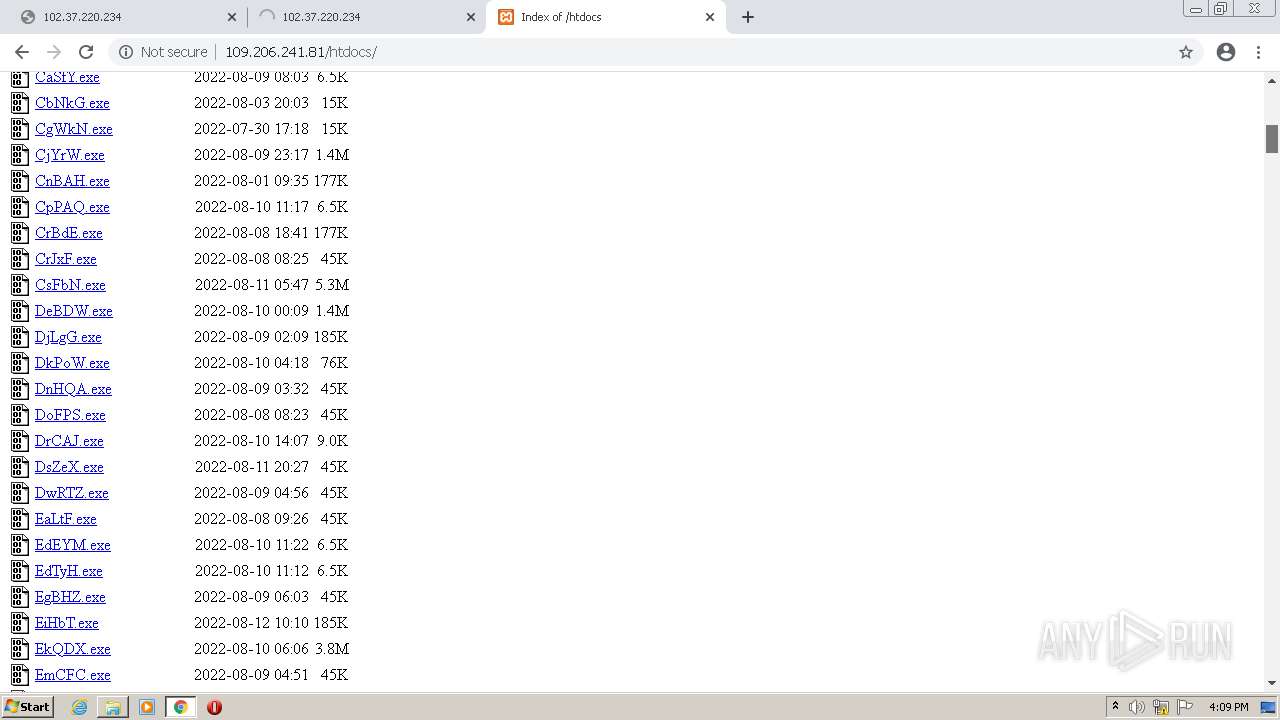
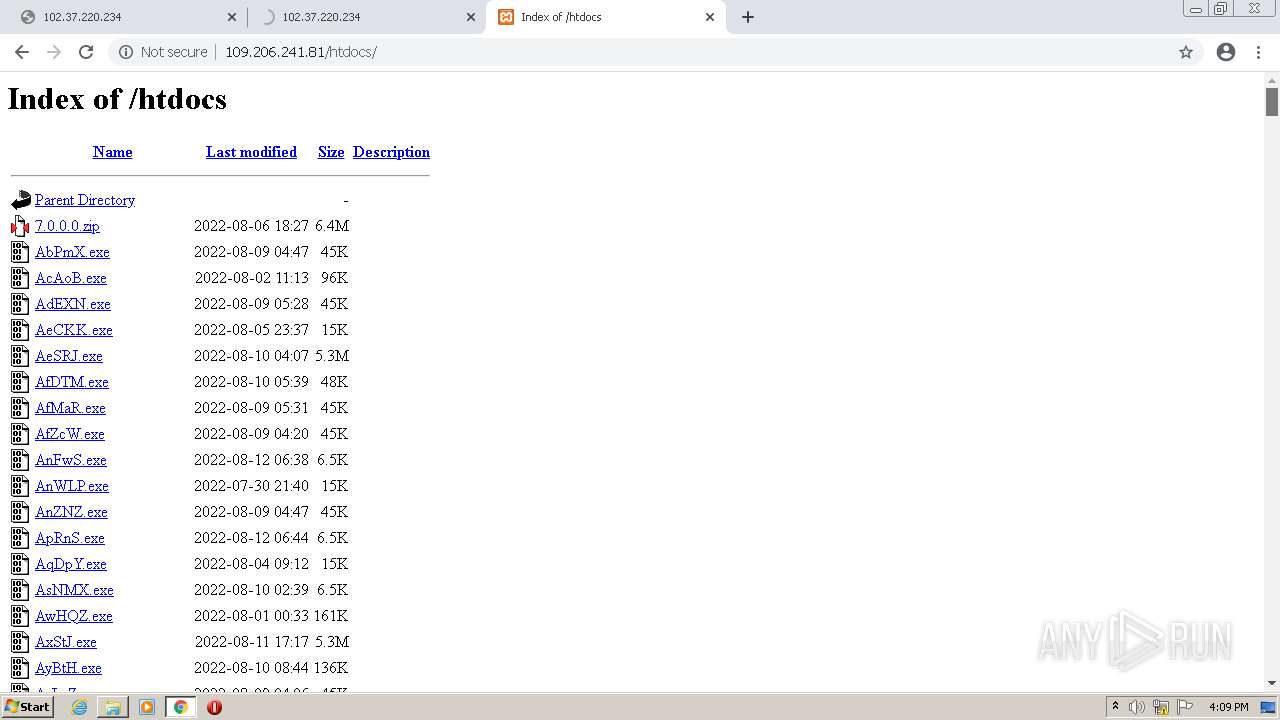
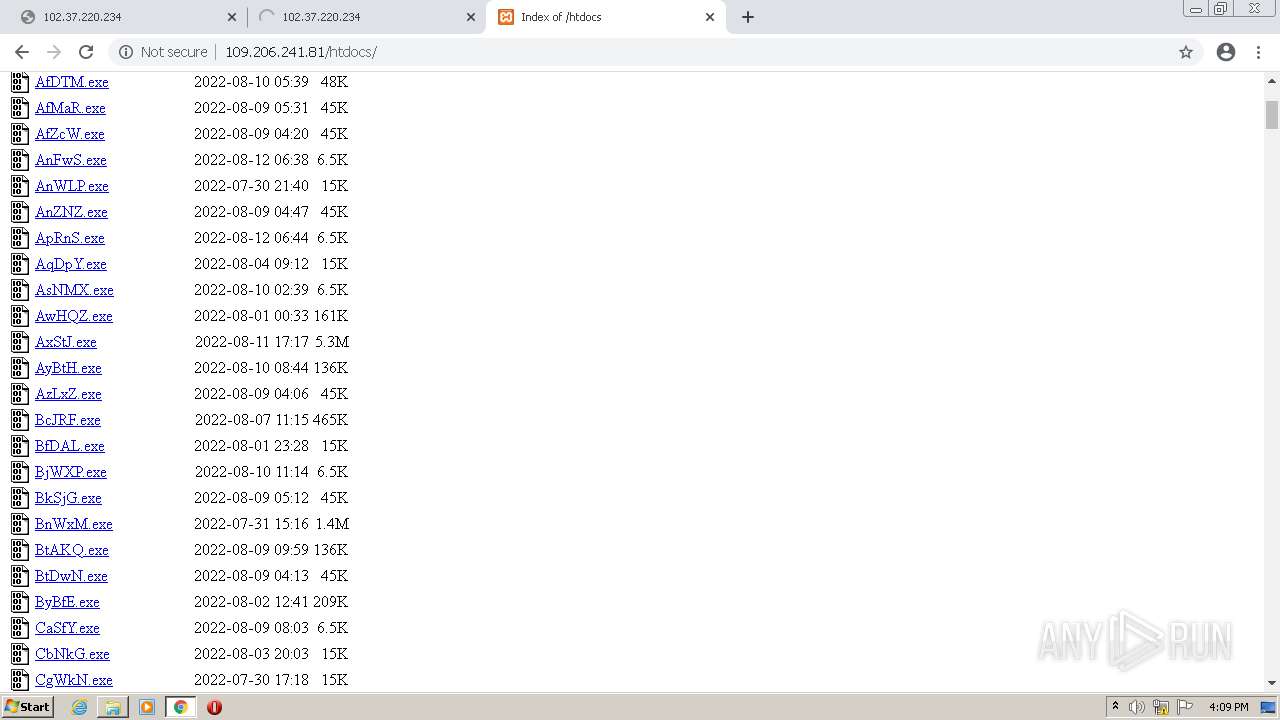
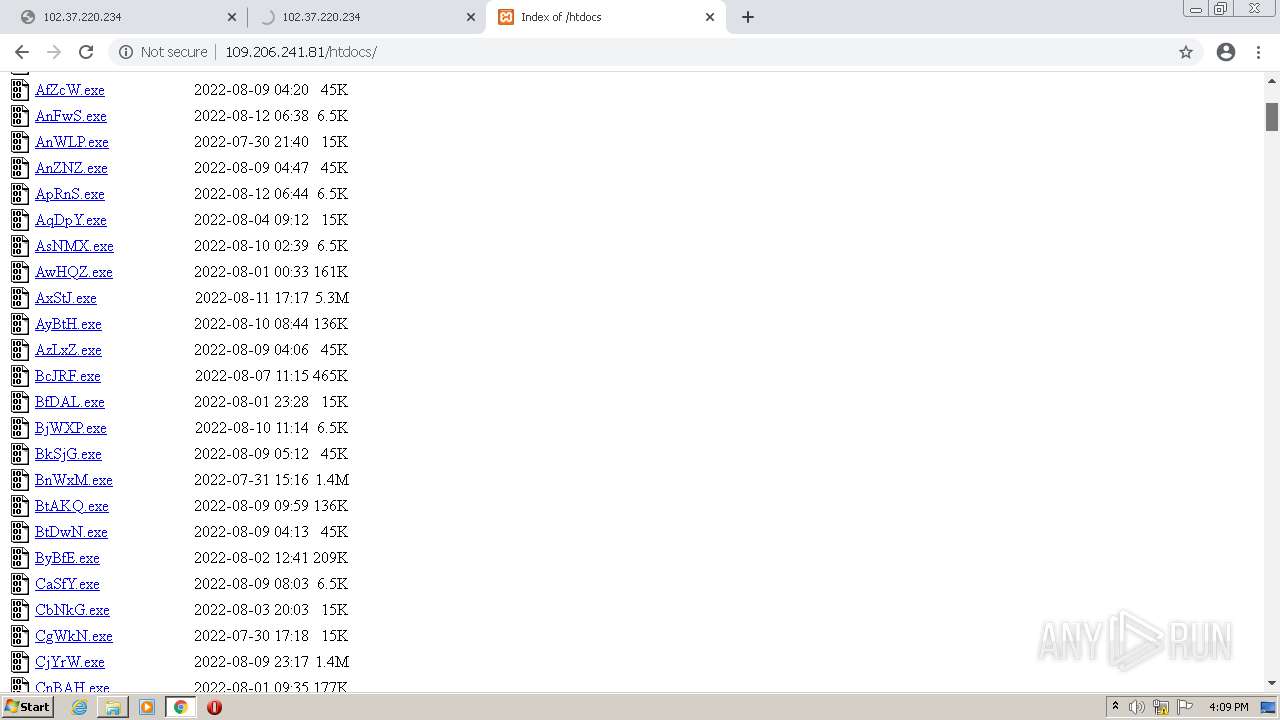
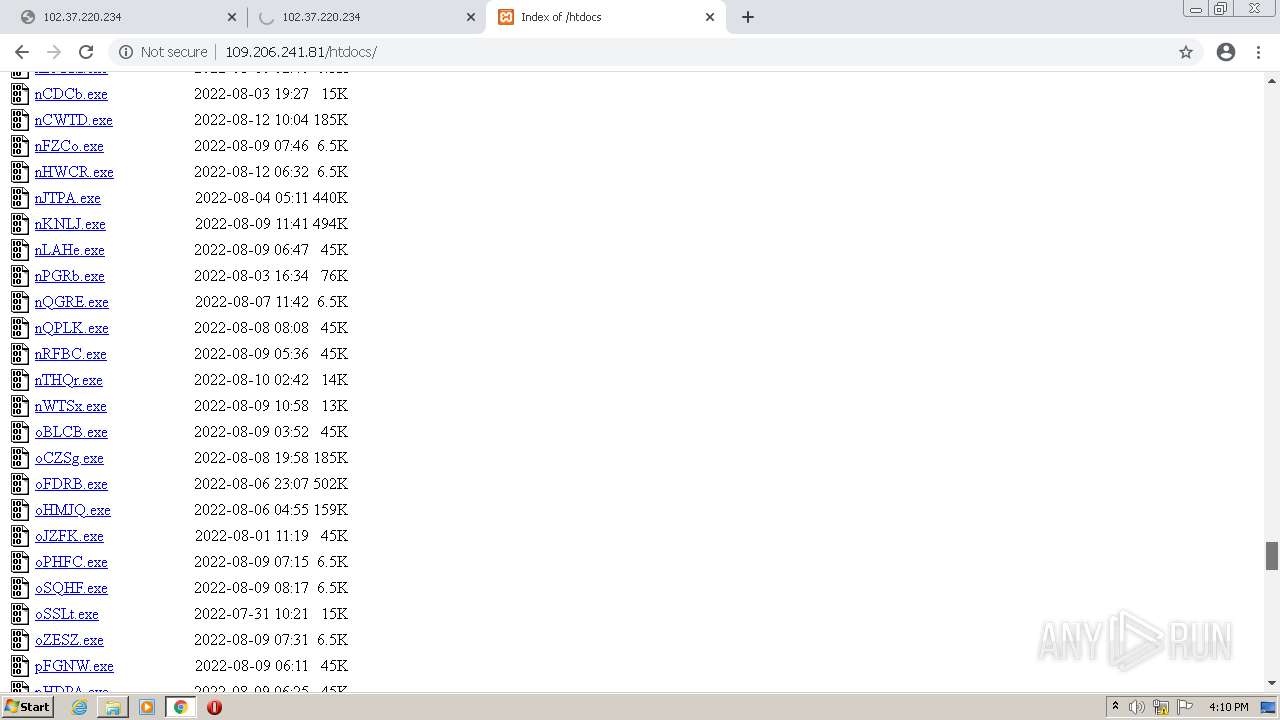
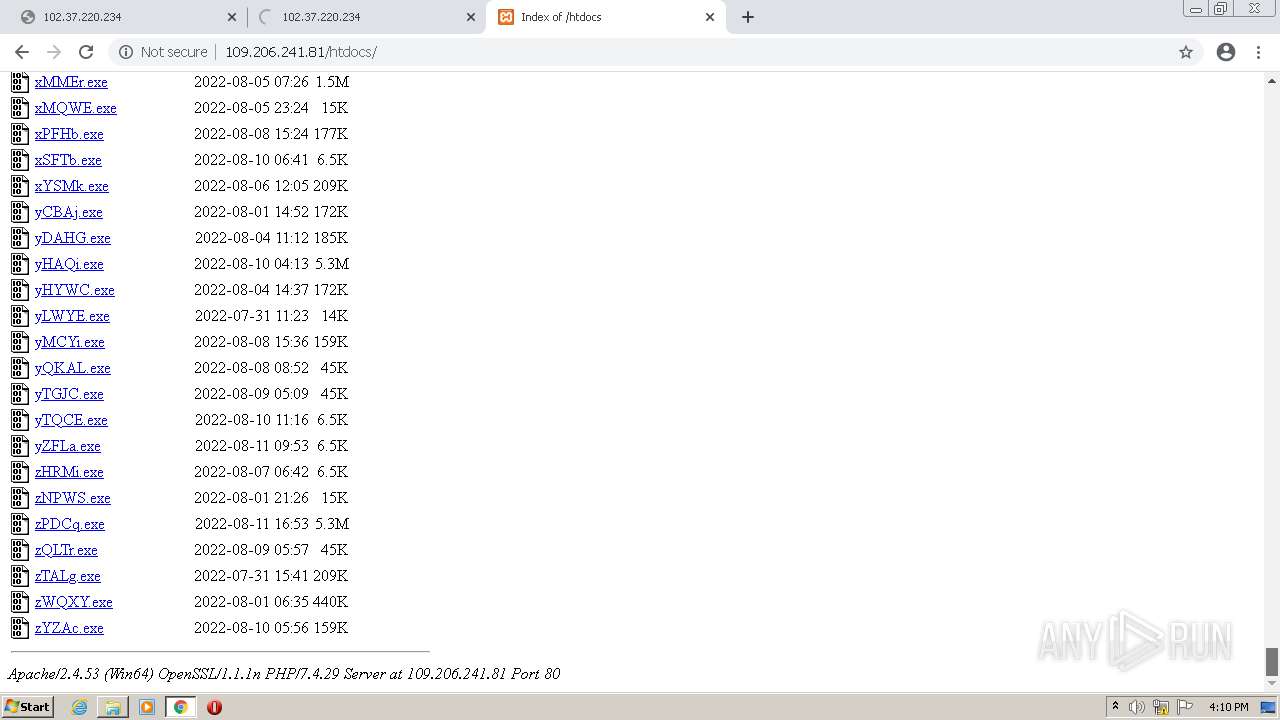
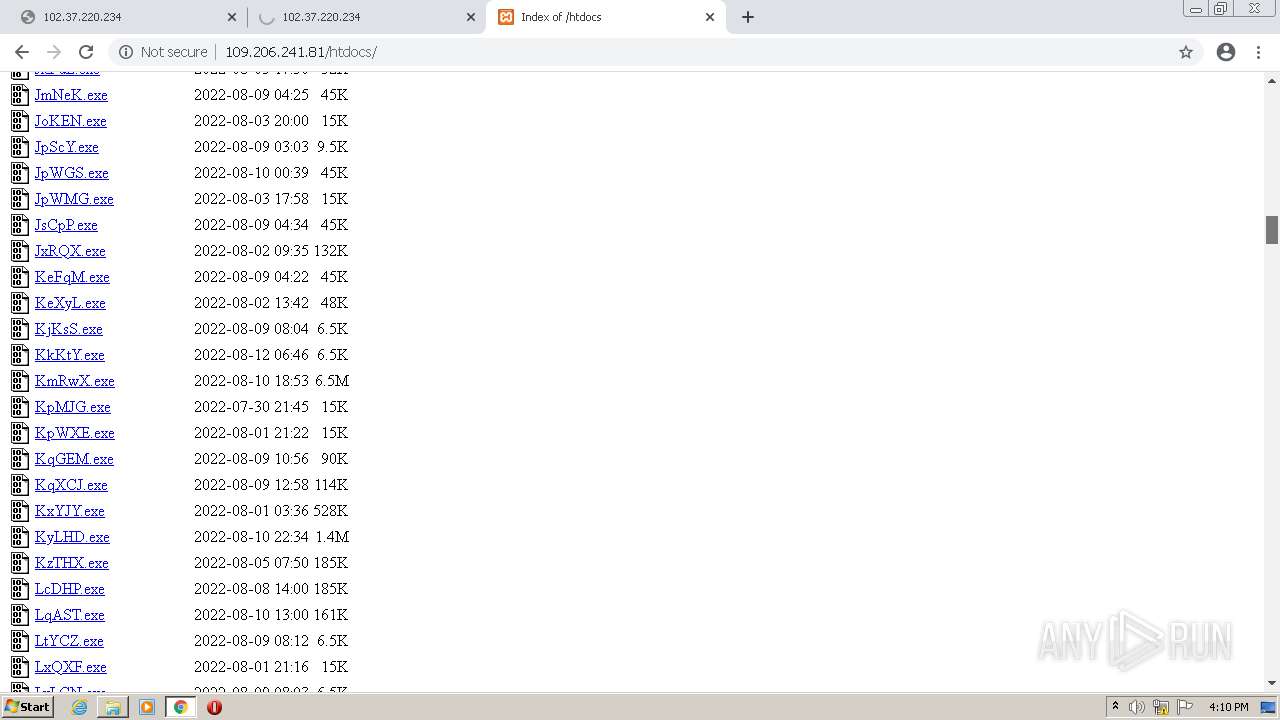
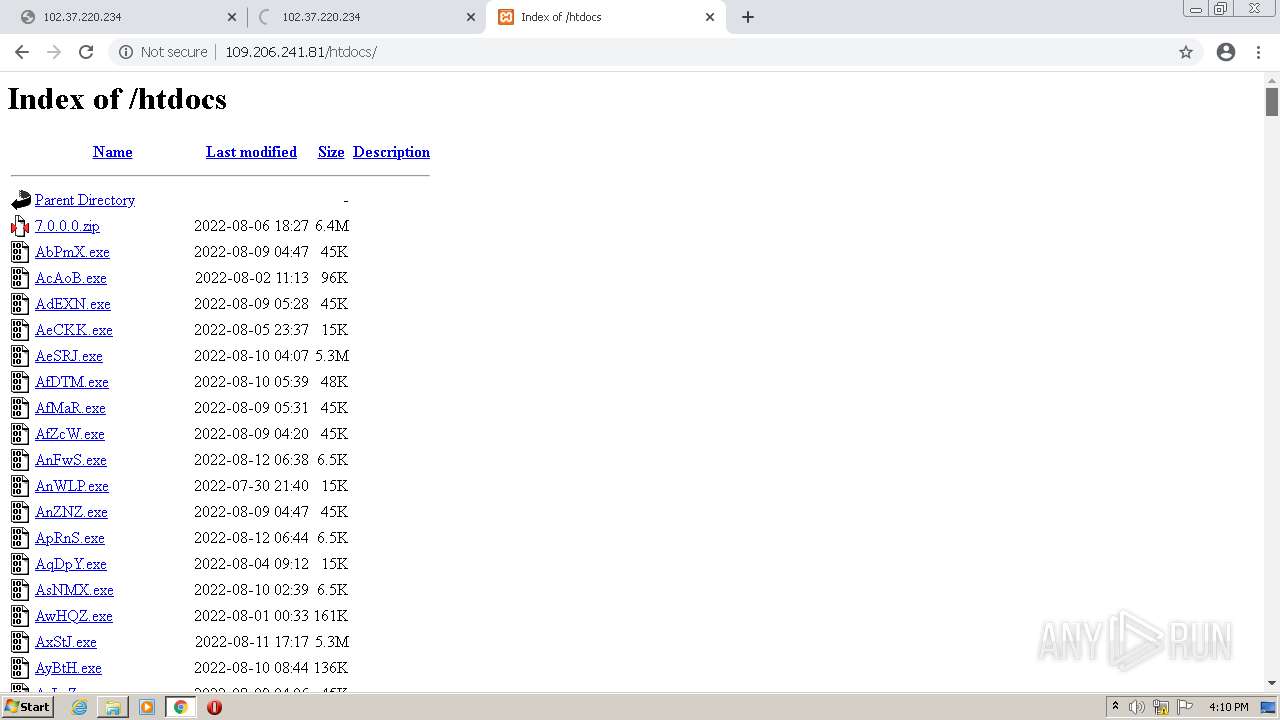
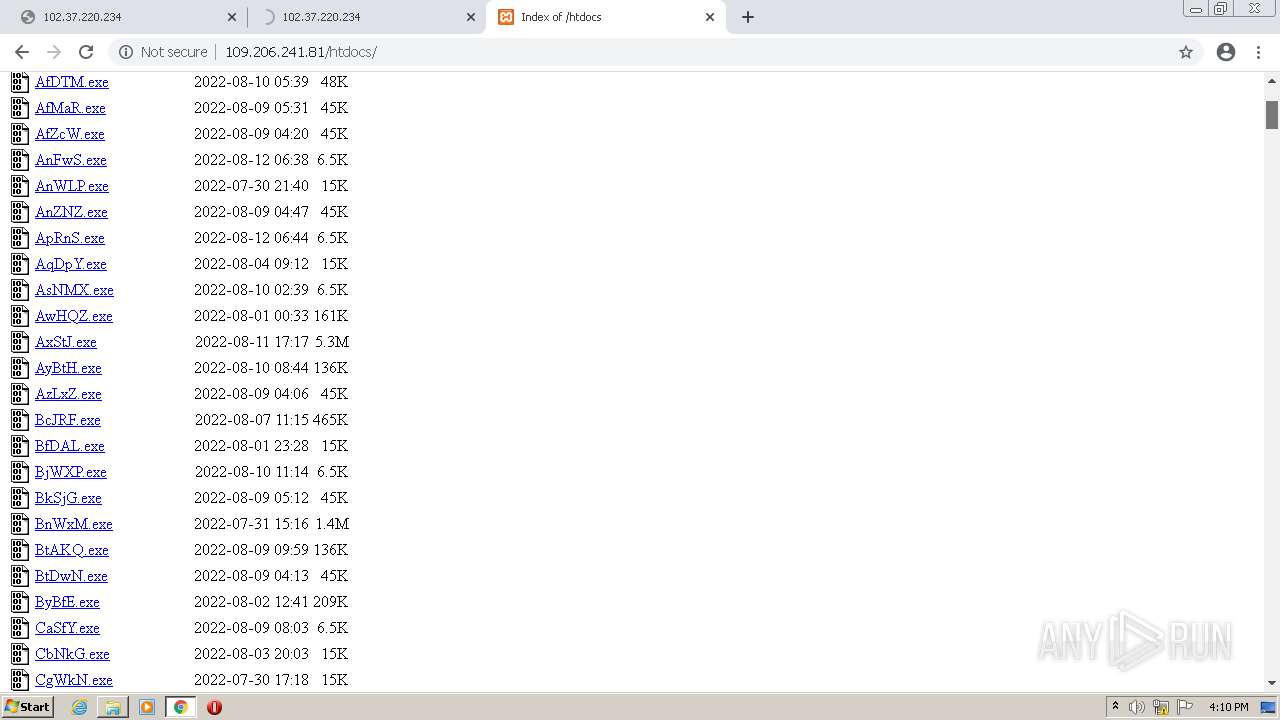
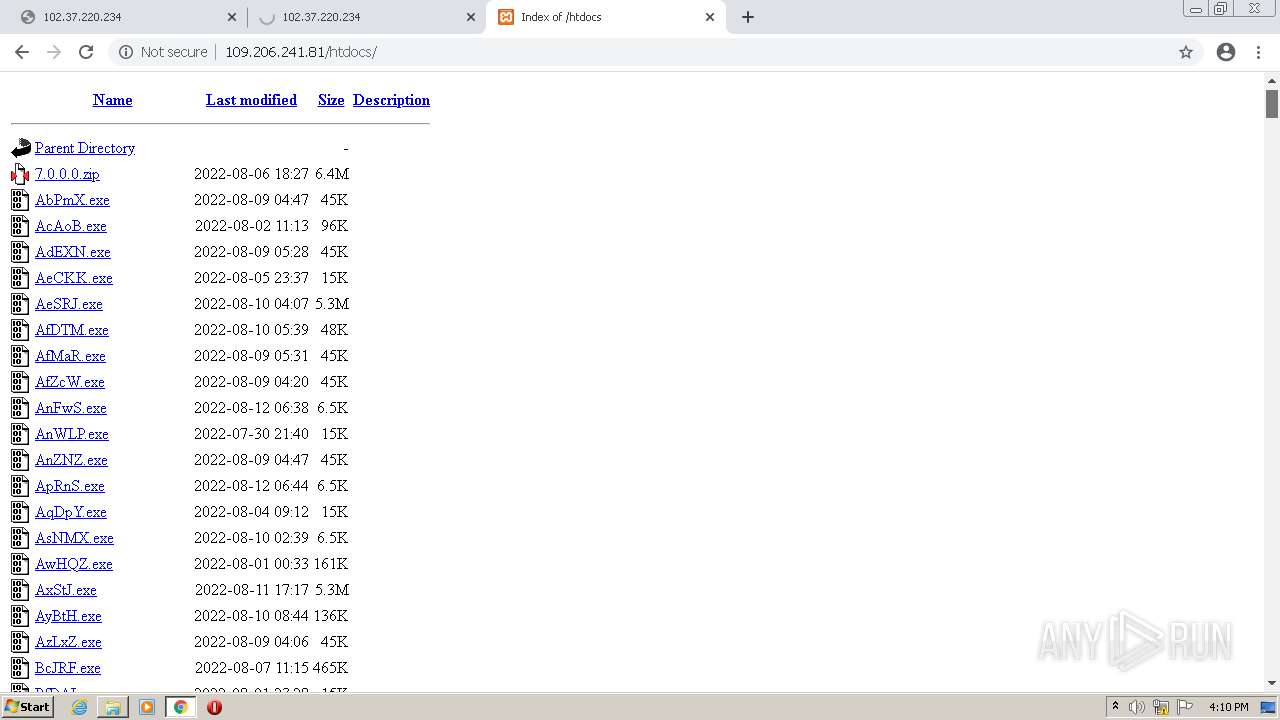
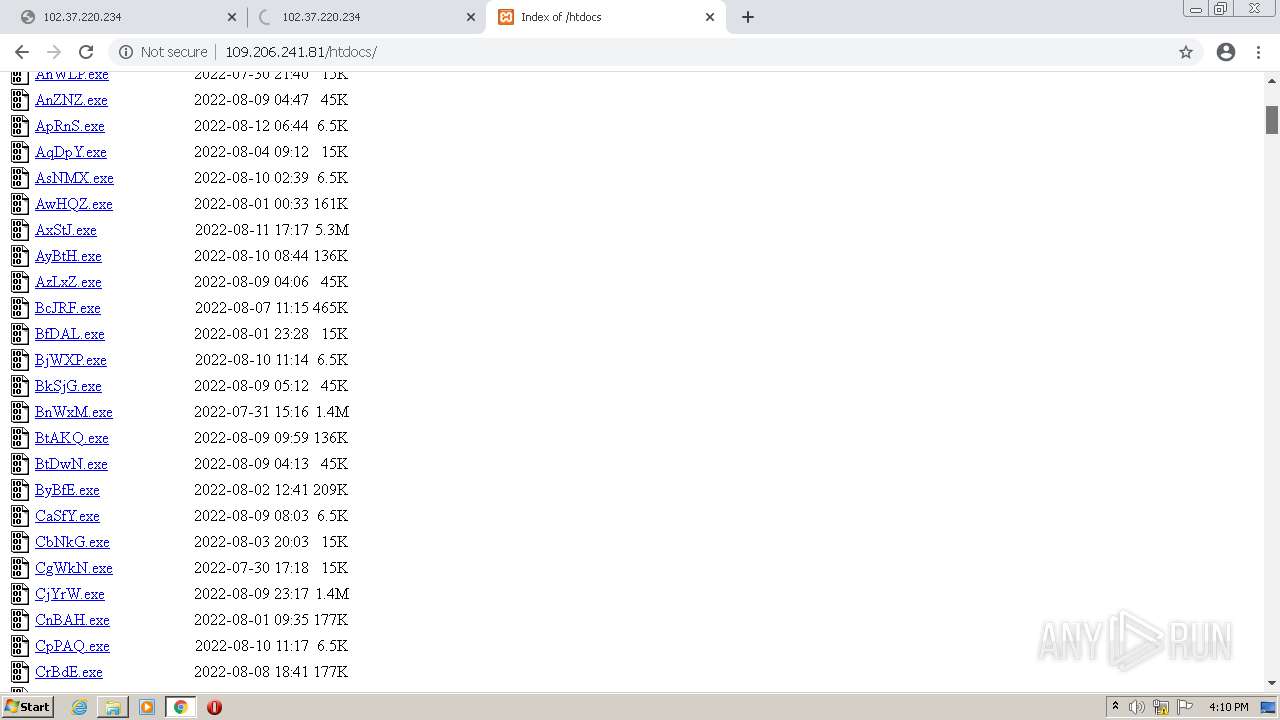
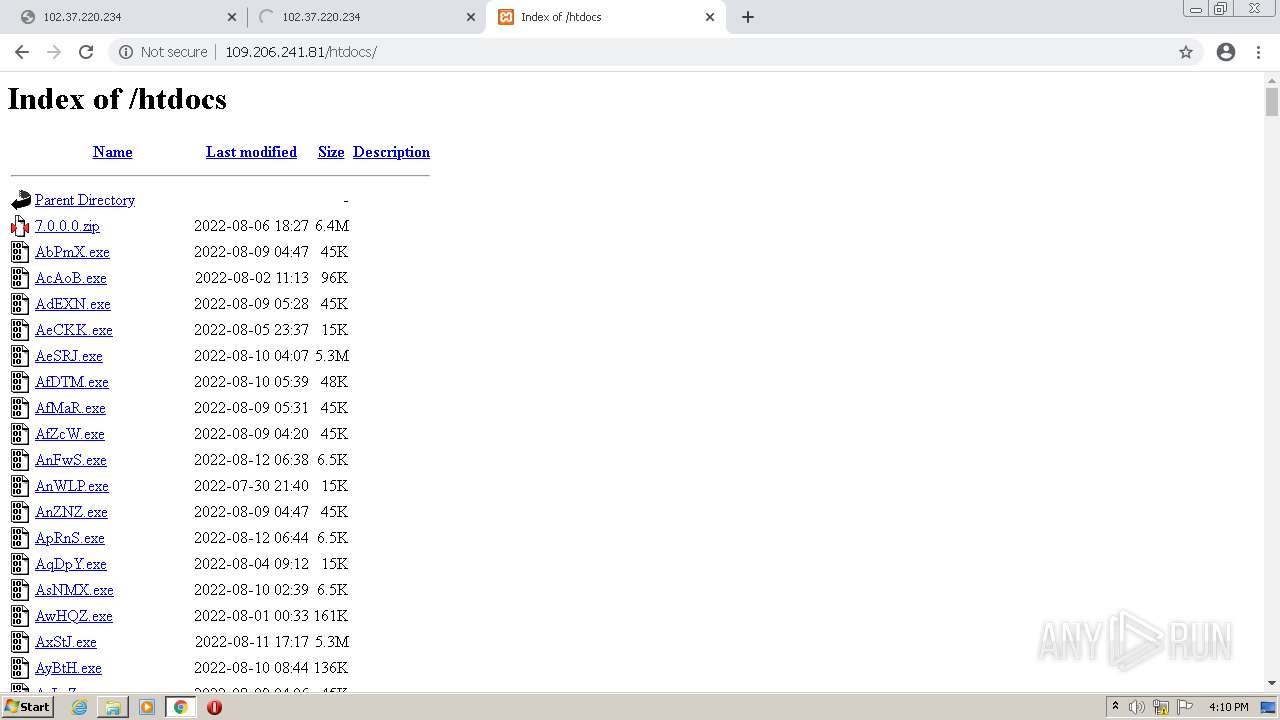
3908 | chrome.exe | GET | — | 102.37.220.234:80 | http://102.37.220.234/htdocs/LtEaG.exe | unknown | — | — | suspicious |
3908 | chrome.exe | GET | — | 102.37.220.234:80 | http://102.37.220.234/htdocs | unknown | — | — | suspicious |
880 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
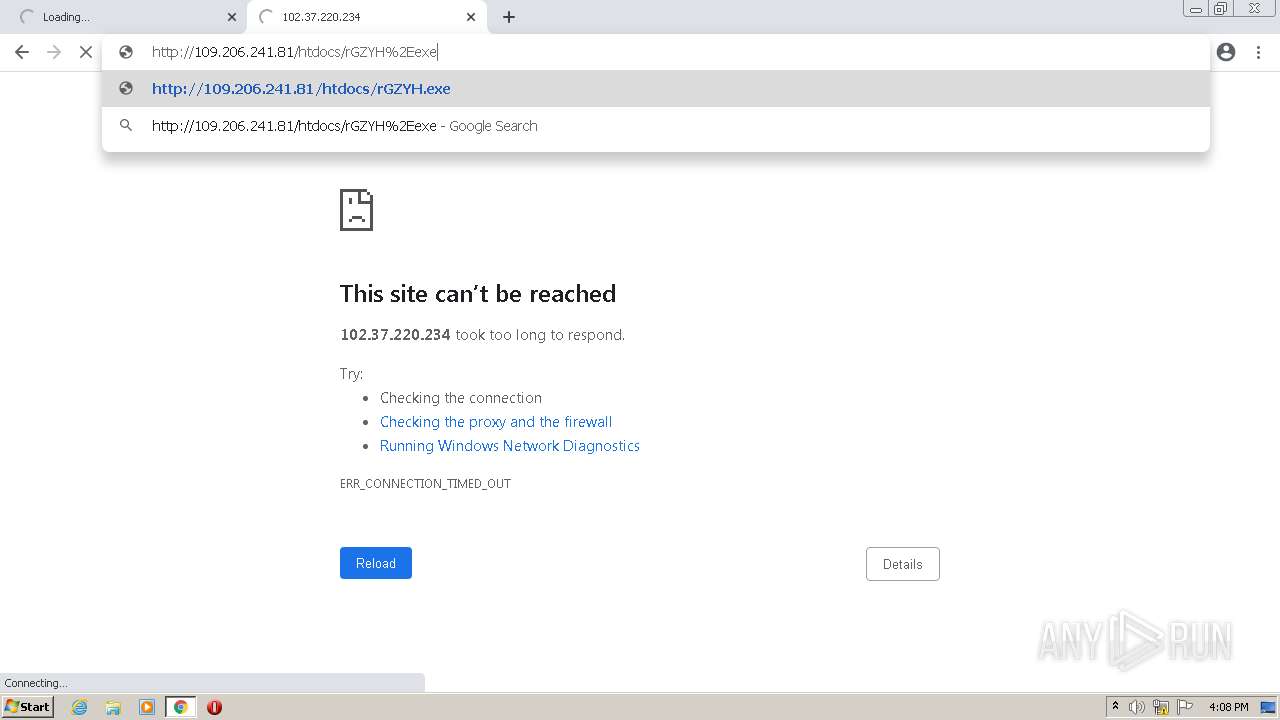
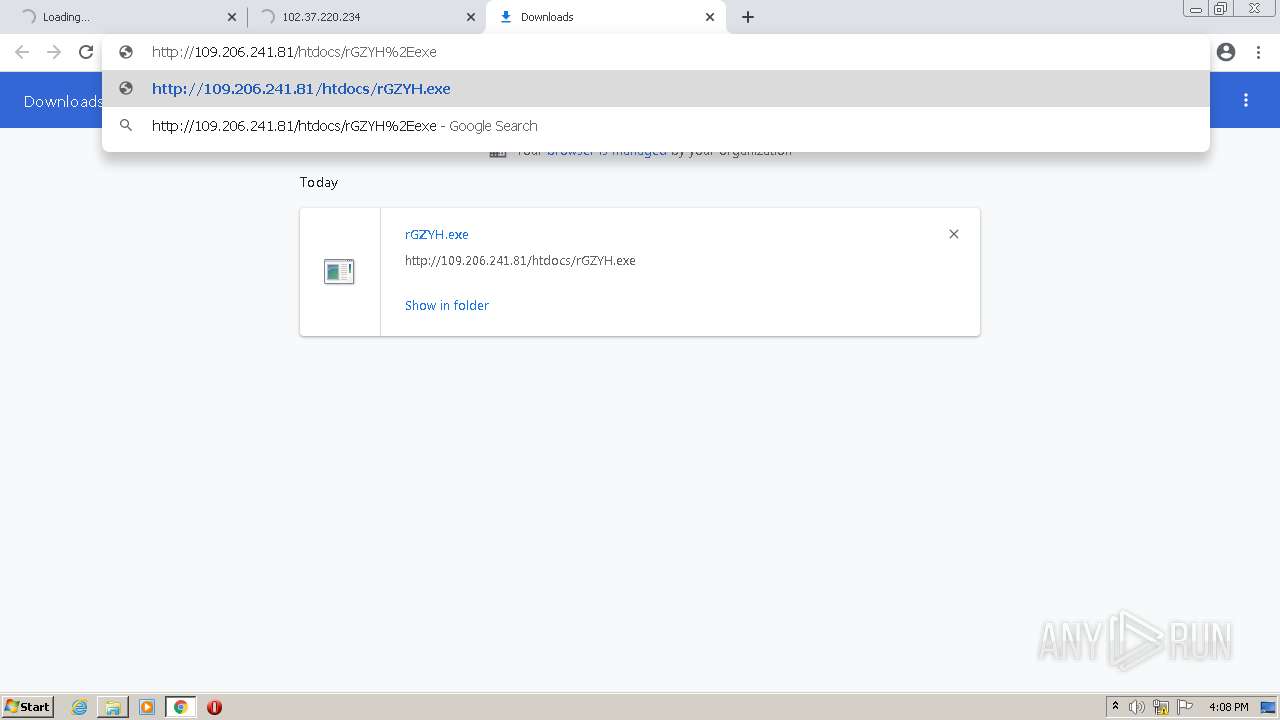
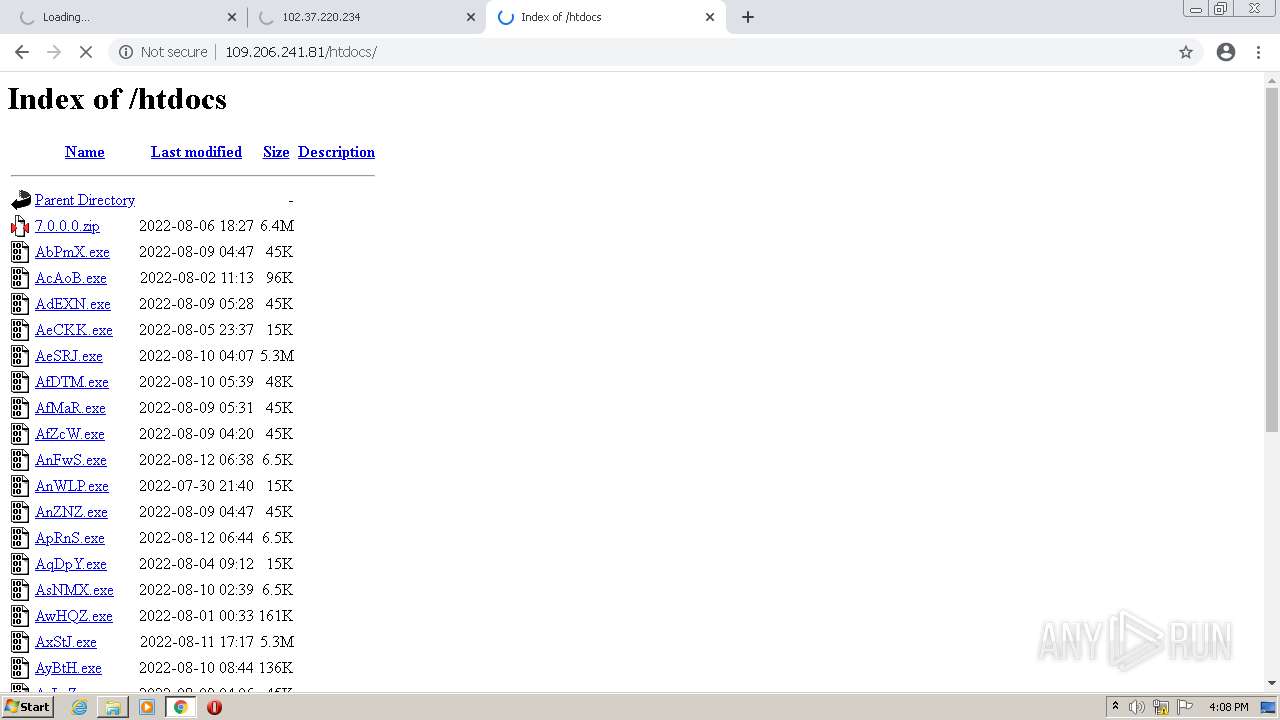
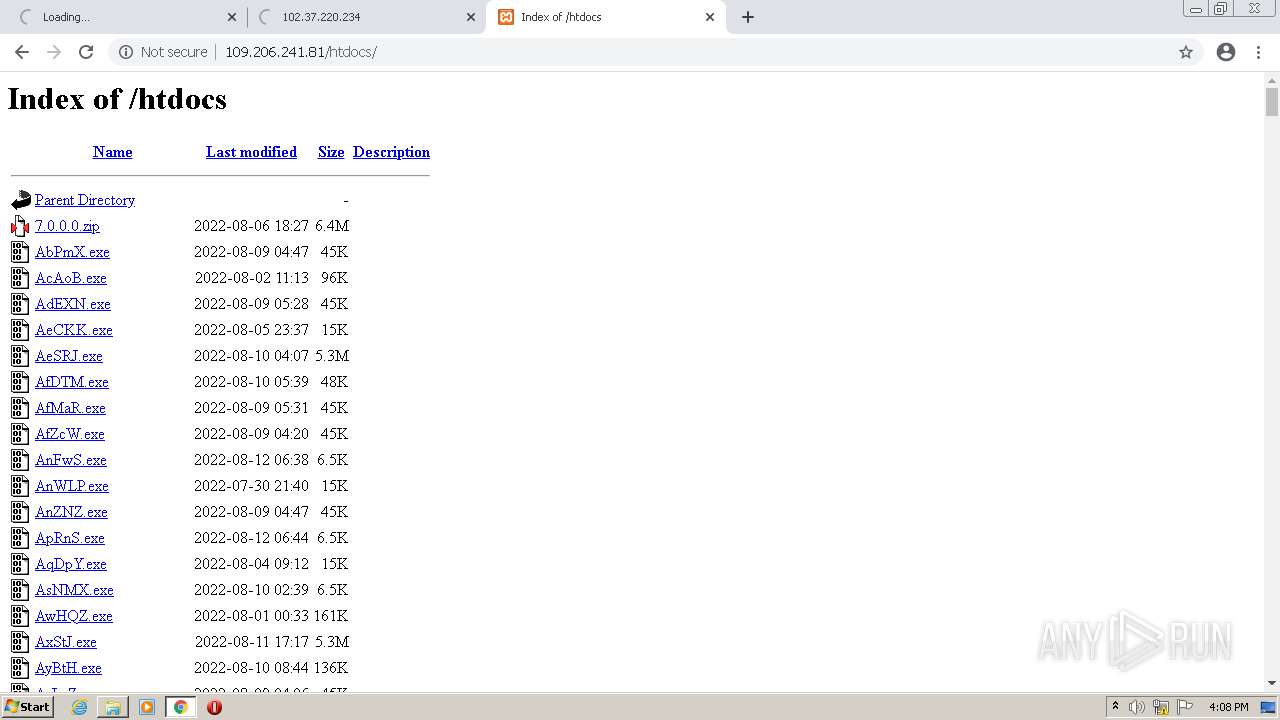
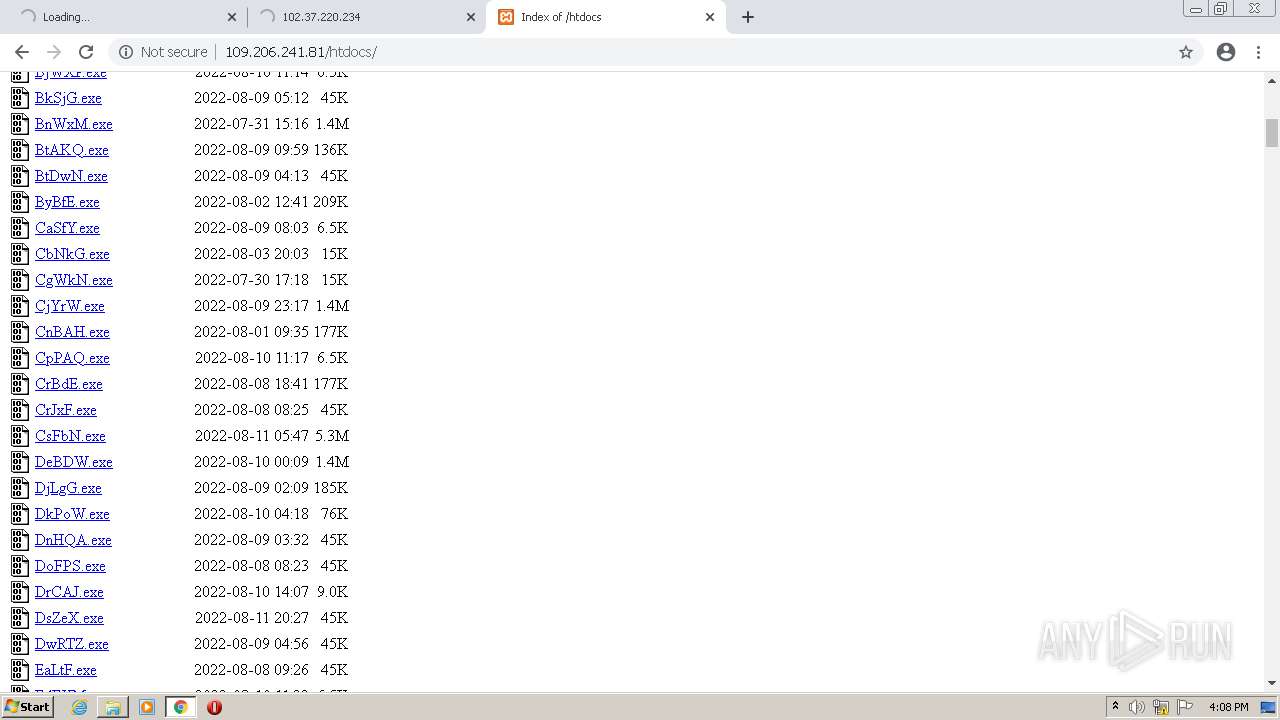
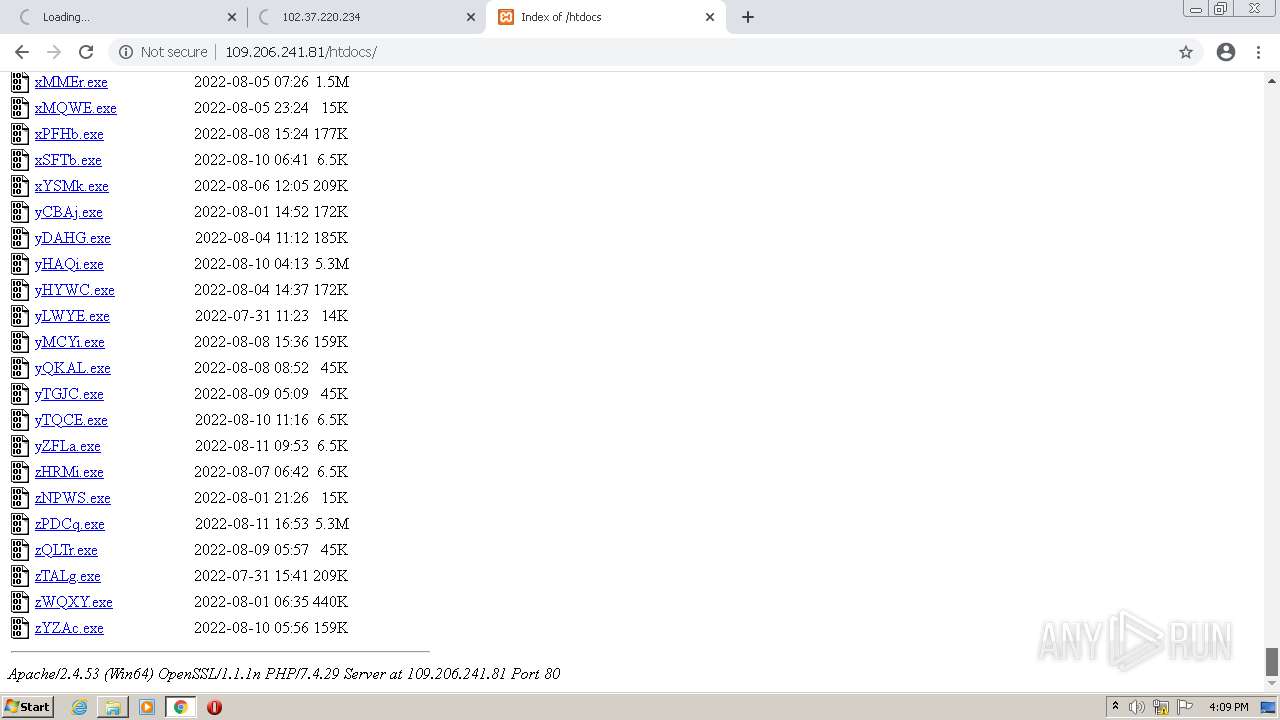
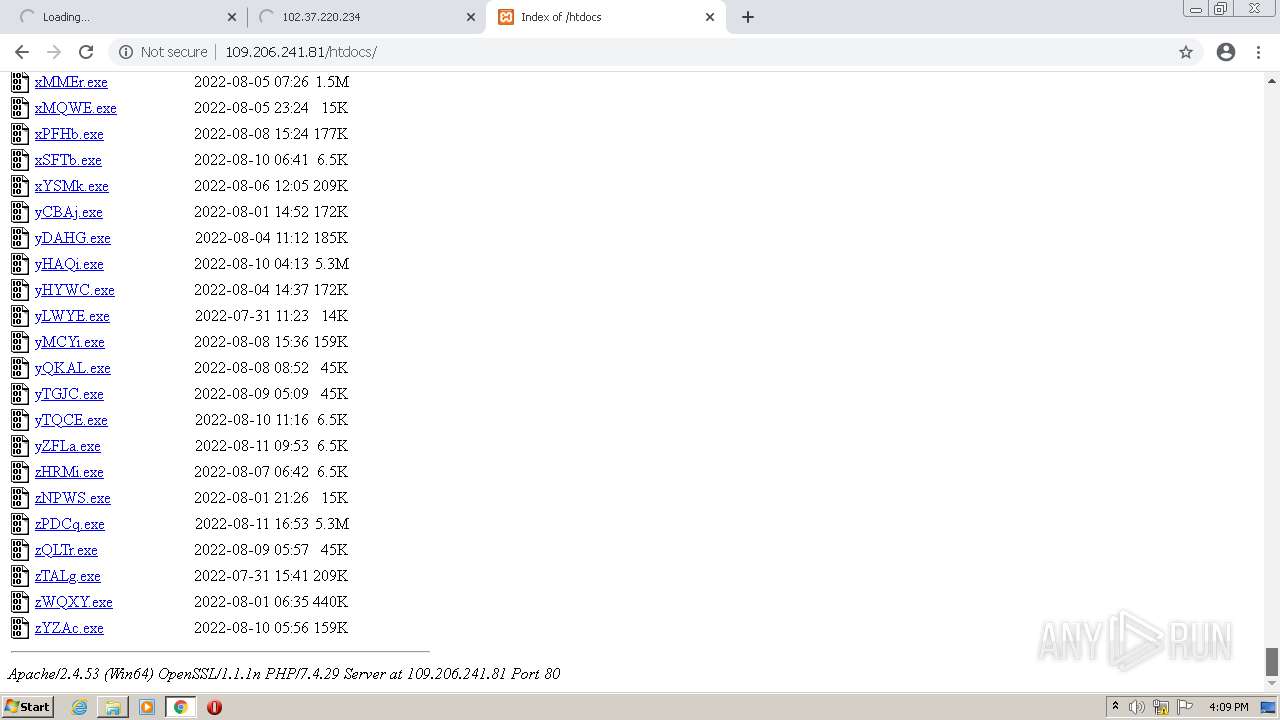
3908 | chrome.exe | GET | 200 | 109.206.241.81:80 | http://109.206.241.81/htdocs/rGZYH.exe | unknown | executable | 45.0 Kb | malicious |
3908 | chrome.exe | GET | 200 | 109.206.241.81:80 | http://109.206.241.81/htdocs/ | unknown | html | 104 Kb | malicious |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.70 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 12.2 Kb | whitelisted |
3908 | chrome.exe | GET | 200 | 109.206.241.81:80 | http://109.206.241.81/icons/compressed.gif | unknown | image | 1.01 Kb | malicious |
3908 | chrome.exe | GET | 200 | 109.206.241.81:80 | http://109.206.241.81/icons/binary.gif | unknown | image | 246 b | malicious |
3908 | chrome.exe | GET | 200 | 109.206.241.81:80 | http://109.206.241.81/icons/blank.gif | unknown | image | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 142.250.186.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 102.37.220.234:80 | — | — | — | suspicious |
3908 | chrome.exe | 142.250.184.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 109.206.241.81:80 | — | — | — | malicious |
— | — | 142.251.36.14:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3908 | chrome.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3908 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3908 | chrome.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3908 | chrome.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |