| File name: | b7f10d62278881361a6d77d405bc4b00facf1a05.vbs |
| Full analysis: | https://app.any.run/tasks/a1e7a891-ae60-418f-b1d7-8248a87e0922 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | April 25, 2019, 19:41:39 |
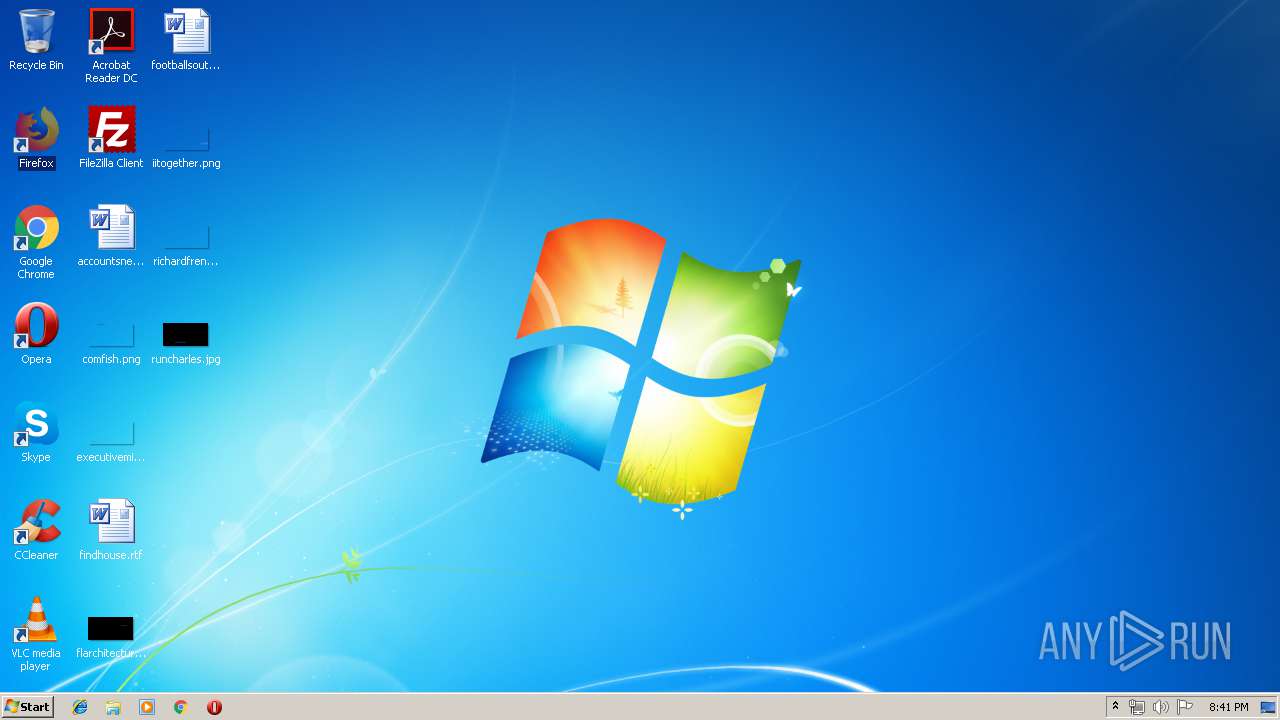
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | DF92439ED5C2584F18890B34B1E0D115 |
| SHA1: | B7F10D62278881361A6D77D405BC4B00FACF1A05 |
| SHA256: | CE0798BB742C32D5EFB1643EF400A92A4F559C7A322CCD554E33E3EA6748C4F9 |
| SSDEEP: | 12288:i3MdwwJm5zQdBLZ4ltu2enoCDYvfx8tFxNOA9Rw9ASvhs0+DDO2C4A3U2rNM:ic9m5zQzF4ltLeoqY3xlA9JSStvOZL6 |
MALICIOUS
Writes to a start menu file
- WScript.exe (PID: 2316)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1928)
AdWind was detected
- java.exe (PID: 2376)
- java.exe (PID: 672)
Loads dropped or rewritten executable
- javaw.exe (PID: 3456)
- javaw.exe (PID: 2532)
- java.exe (PID: 2376)
- WScript.exe (PID: 2668)
- cmd.exe (PID: 2108)
- javaw.exe (PID: 3256)
- java.exe (PID: 672)
- iexplore.exe (PID: 2556)
Changes the autorun value in the registry
- WScript.exe (PID: 2316)
- reg.exe (PID: 2224)
- WScript.exe (PID: 2668)
Application was dropped or rewritten from another process
- java.exe (PID: 2376)
- javaw.exe (PID: 2532)
- javaw.exe (PID: 3456)
- java.exe (PID: 672)
- javaw.exe (PID: 3256)
UAC/LUA settings modification
- regedit.exe (PID: 3216)
Uses TASKKILL.EXE to kill security tools
- javaw.exe (PID: 3256)
ADWIND was detected
- javaw.exe (PID: 3256)
Turns off system restore
- regedit.exe (PID: 3216)
Changes Image File Execution Options
- regedit.exe (PID: 3216)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2172)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 2668)
- javaw.exe (PID: 2532)
- xcopy.exe (PID: 3448)
- WScript.exe (PID: 2316)
Executes scripts
- cmd.exe (PID: 2664)
- cmd.exe (PID: 2612)
- WScript.exe (PID: 2668)
- cmd.exe (PID: 3596)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 1768)
- cmd.exe (PID: 1968)
Executes JAVA applets
- javaw.exe (PID: 2532)
- cmd.exe (PID: 2108)
- WScript.exe (PID: 2668)
Starts CMD.EXE for commands execution
- java.exe (PID: 2376)
- javaw.exe (PID: 2532)
- WScript.exe (PID: 2668)
- javaw.exe (PID: 3256)
- java.exe (PID: 672)
- WScript.exe (PID: 2316)
Application launched itself
- WScript.exe (PID: 2668)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2532)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2532)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3448)
- javaw.exe (PID: 3256)
Starts itself from another location
- javaw.exe (PID: 2532)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 3256)
INFO
Changes internet zones settings
- iexplore.exe (PID: 916)
Reads internet explorer settings
- iexplore.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
480
Monitored processes
233
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | taskkill /IM fmon.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 252 | taskkill /IM MWAGENT.EXE /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | taskkill /IM ScSecSvc.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | taskkill /IM K7RTScan.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | taskkill /IM K7SysMon.Exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 300 | taskkill /IM QUHLPSVC.EXE /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | taskkill /IM econceal.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | taskkill /IM MCShieldRTM.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | taskkill /IM Zlh.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 672 | C:\Users\admin\AppData\Roaming\Oracle\bin\java.exe -jar C:\Users\admin\AppData\Local\Temp\_0.68075014541784486379920805805294580.class | C:\Users\admin\AppData\Roaming\Oracle\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
2 097
Read events
1 726
Write events
371
Delete events
0
Modification events
| (PID) Process: | (2668) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2668) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2668) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ntfsmgr |
Value: "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\ntfsmgr.jar" | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\nuFssOPRVm |
| Operation: | write | Name: | |
Value: false - 4/25/2019 | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | nuFssOPRVm |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\nuFssOPRVm.vbs" | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | nuFssOPRVm |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\nuFssOPRVm.vbs" | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2316) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
111
Suspicious files
10
Text files
84
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | javaw.exe | C:\Users\admin\AppData\Local\Temp\Retrive3978545713953750632.vbs | — | |
MD5:— | SHA256:— | |||
| 2668 | WScript.exe | C:\Users\admin\AppData\Roaming\nuFssOPRVm.vbs | text | |
MD5:— | SHA256:— | |||
| 2108 | cmd.exe | C:\Users\admin\AppData\Local\Temp\output.txt | text | |
MD5:— | SHA256:— | |||
| 2316 | WScript.exe | C:\Users\admin\AppData\Local\Temp\meee.vbs | text | |
MD5:— | SHA256:— | |||
| 2532 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3456 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2316 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\nuFssOPRVm.vbs | text | |
MD5:— | SHA256:— | |||
| 2668 | WScript.exe | C:\Users\admin\AppData\Roaming\ntfsmgr.jar | java | |
MD5:— | SHA256:— | |||
| 2376 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2532 | javaw.exe | C:\Users\admin\AppData\Local\Temp\_0.41436736119452481955374249029752090.class | java | |
MD5:781FB531354D6F291F1CCAB48DA6D39F | SHA256:97D585B6AFF62FB4E43E7E6A5F816DCD7A14BE11A88B109A9BA9E8CD4C456EB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
45
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
916 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2316 | WScript.exe | 23.105.131.191:3355 | brothersjoy.nl | Nobis Technology Group, LLC | US | malicious |
3256 | javaw.exe | 178.239.21.4:1604 | jsbc-pcs.linkpc.net | Telekomunikacije Republike Srpske akcionarsko drustvo Banja Luka | BA | malicious |
916 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 23.105.131.191:3355 | brothersjoy.nl | Nobis Technology Group, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
brothersjoy.nl |
| unknown |
jsbc-pcs.linkpc.net |
| malicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3256 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
1 ETPRO signatures available at the full report