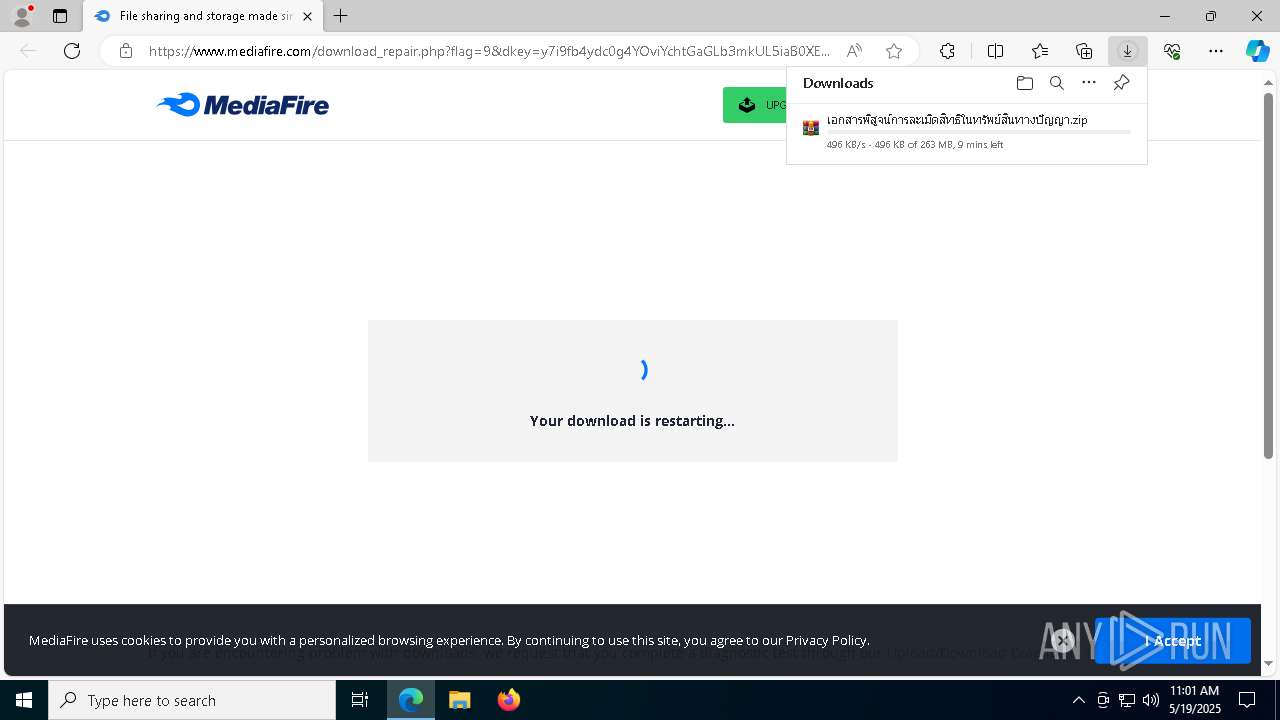
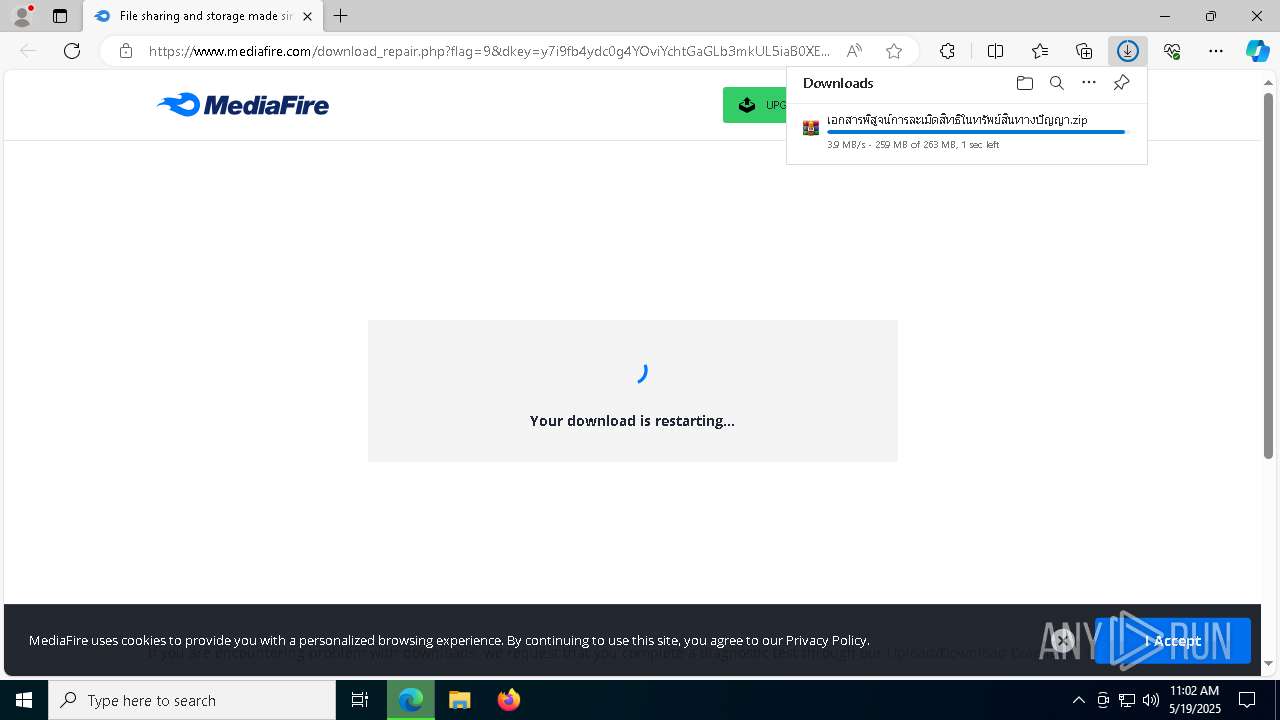
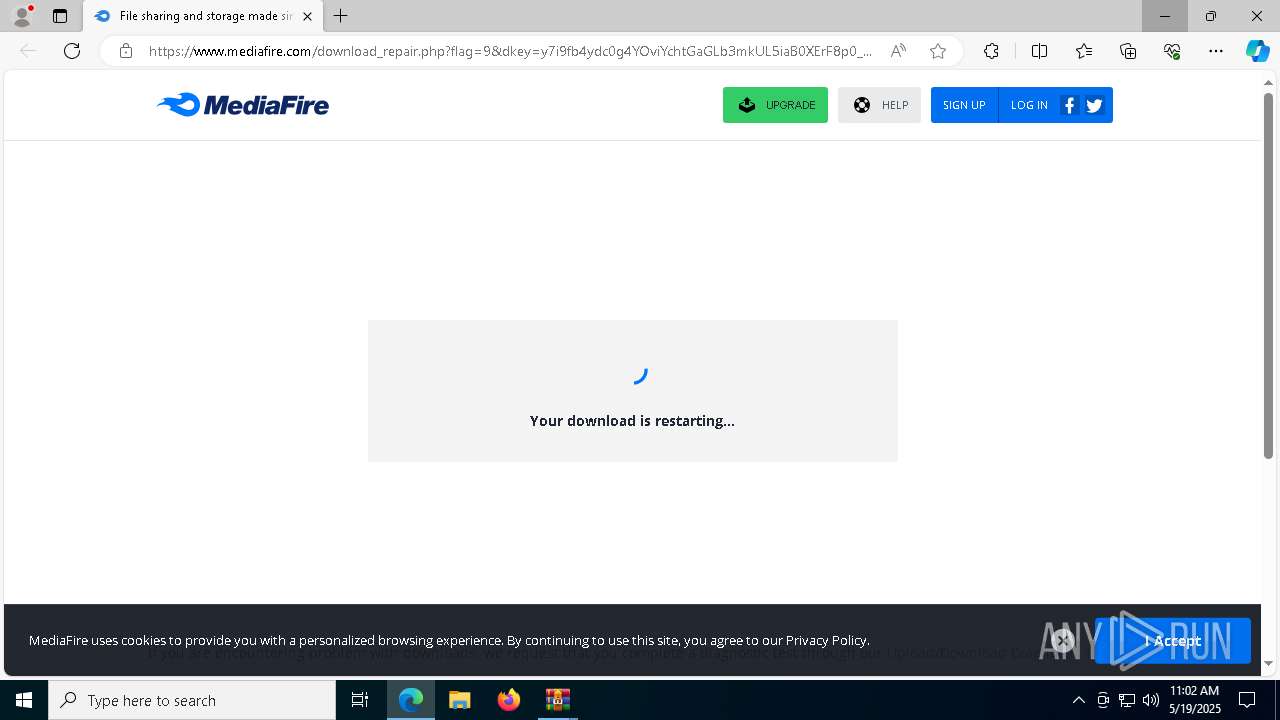
| URL: | https://www.mediafire.com/download_repair.php?flag=9&dkey=y7i9fb4ydc0g4YOviYchtGaGLb3mkUL5iaB0XErF8p0%5Fh0ATGkrV4guHXNc96ijD2RfAp972y%2DW2D%5FfTQWpOivov7buIm229mIDvx8BskAW7j08DqgeYON0SNMBKayu8vxVmzefEh3LBfGgUSvLDzj06h%2D0dDUqczHK8r2qa2dM8&qkey=ktqcwdh7yowjis3&ip=94%2E69%2E191%2E202 |
| Full analysis: | https://app.any.run/tasks/f44d62e3-d0c1-46dd-82eb-6f63a6a5b7e7 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | May 19, 2025, 11:00:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FF8C0934E5C3C3964EBF673BCAED73A0 |
| SHA1: | 25EBBC1171653D538F183BD31EBA44757C3837CC |
| SHA256: | CDD8302CA0B2A5A5B27C2FABD6830286FF33889D80B153DB0EC2C88B768FD4DE |
| SSDEEP: | 6:2OLw3eGNdU9cM5StipWzP4I4u9stSMRM72nWGSMZQWduVmf6u7ycs:273eKdrM5Sti/MstQ7zGSYQ1g6uWX |
MALICIOUS
RHADAMANTHYS mutex has been found
- svchost.exe (PID: 6344)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 976)
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 2980)
- svchost.exe (PID: 7896)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 6040)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 2596)
Application launched itself
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 6040)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 2596)
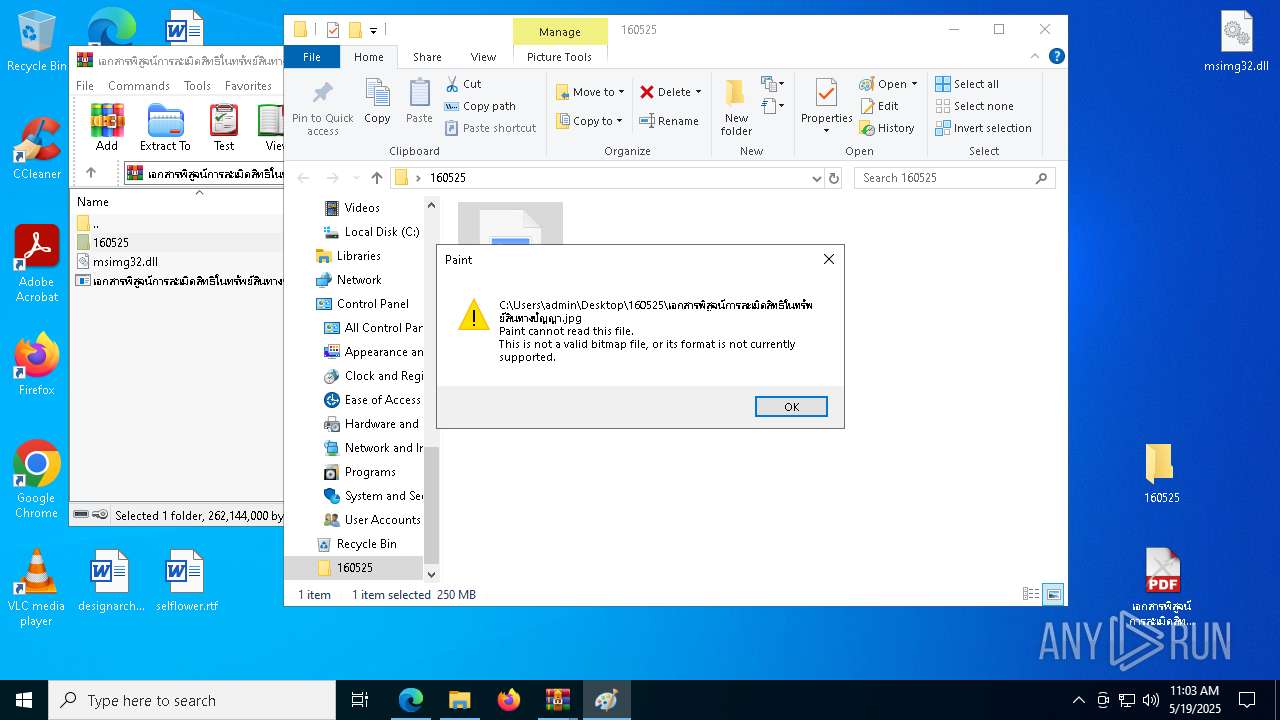
Executes application which crashes
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 976)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 8396)
Connects to unusual port
- svchost.exe (PID: 6344)
- svchost.exe (PID: 2980)
- svchost.exe (PID: 8420)
- svchost.exe (PID: 7896)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 6344)
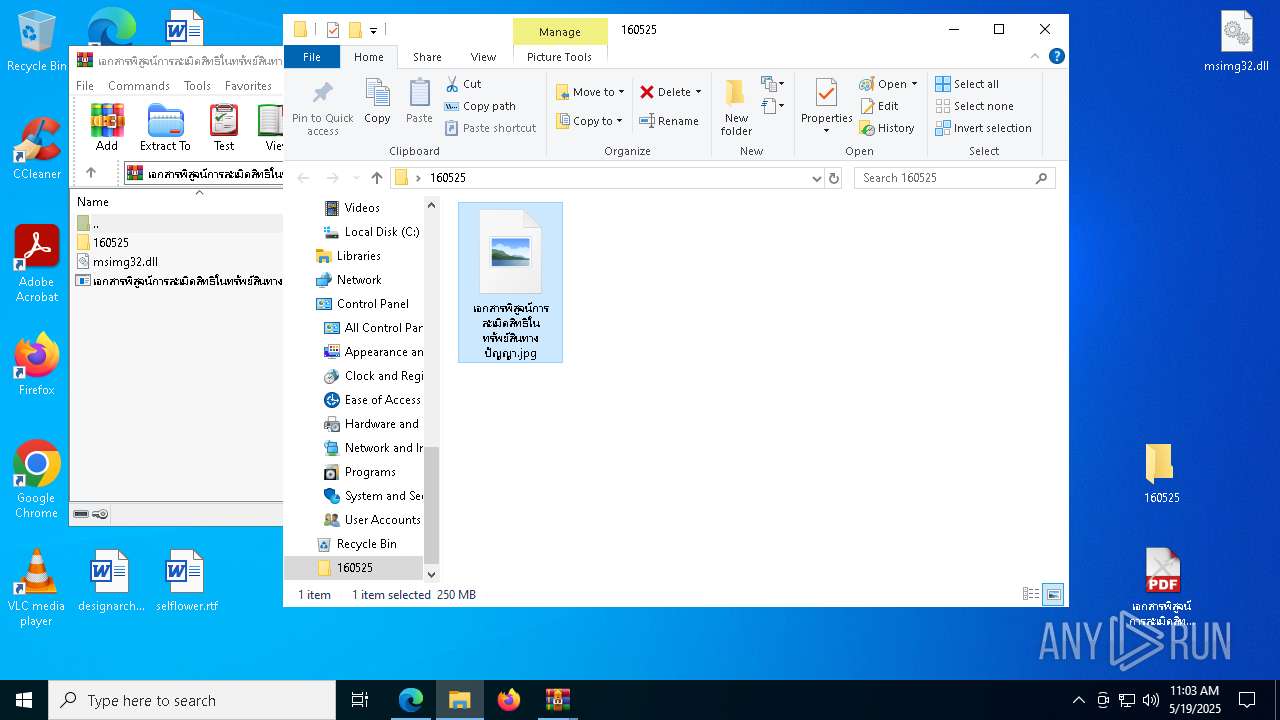
Executable content was dropped or overwritten
- wmpnscfg.exe (PID: 3192)
- svchost.exe (PID: 2980)
- svchost.exe (PID: 7896)
INFO
Application launched itself
- msedge.exe (PID: 6652)
- chrome.exe (PID: 7036)
- msedge.exe (PID: 4304)
- msedge.exe (PID: 7808)
- chrome.exe (PID: 8668)
Checks supported languages
- identity_helper.exe (PID: 7760)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 2596)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 6040)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 976)
Reads the computer name
- identity_helper.exe (PID: 7760)
Reads the software policy settings
- slui.exe (PID: 8180)
- slui.exe (PID: 4152)
Reads Environment values
- identity_helper.exe (PID: 7760)
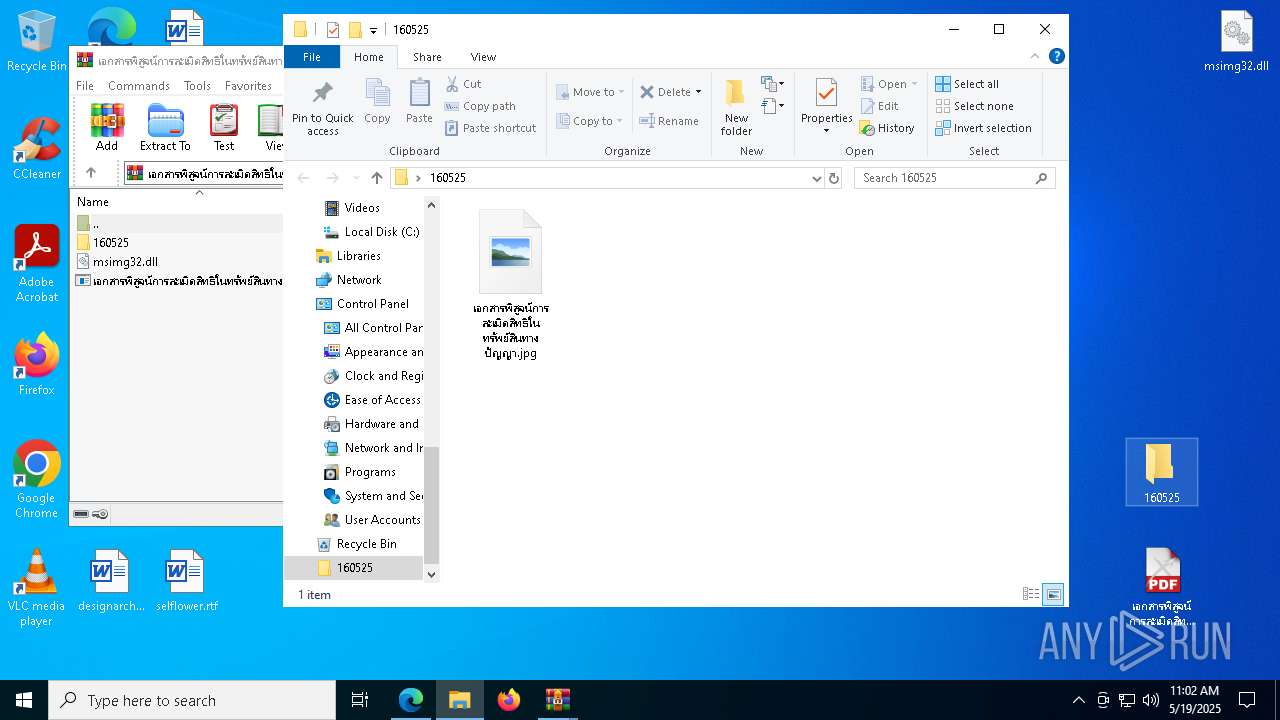
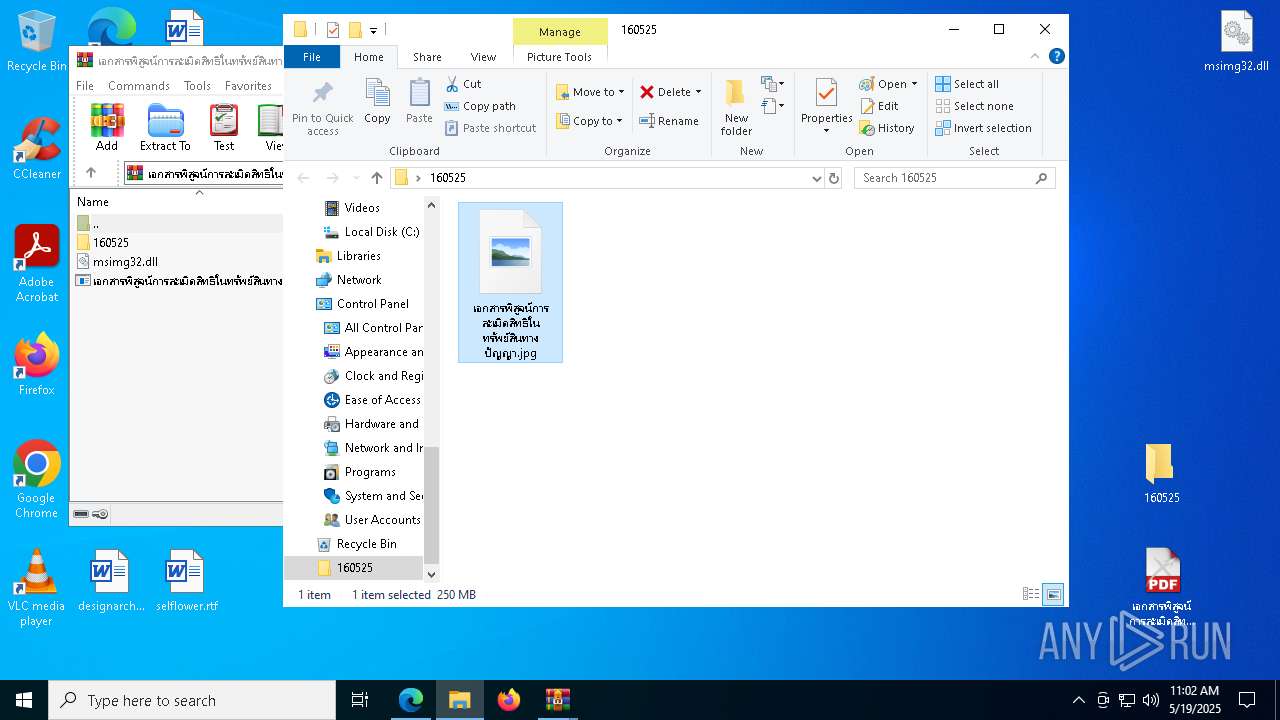
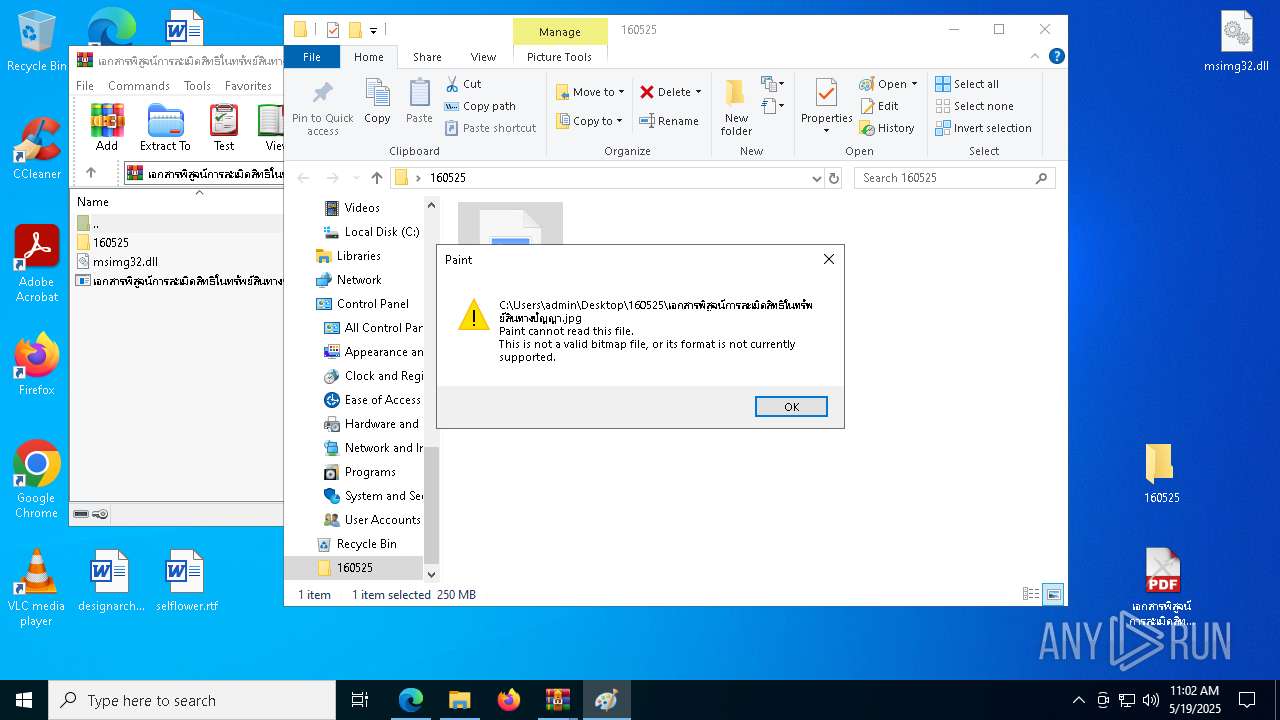
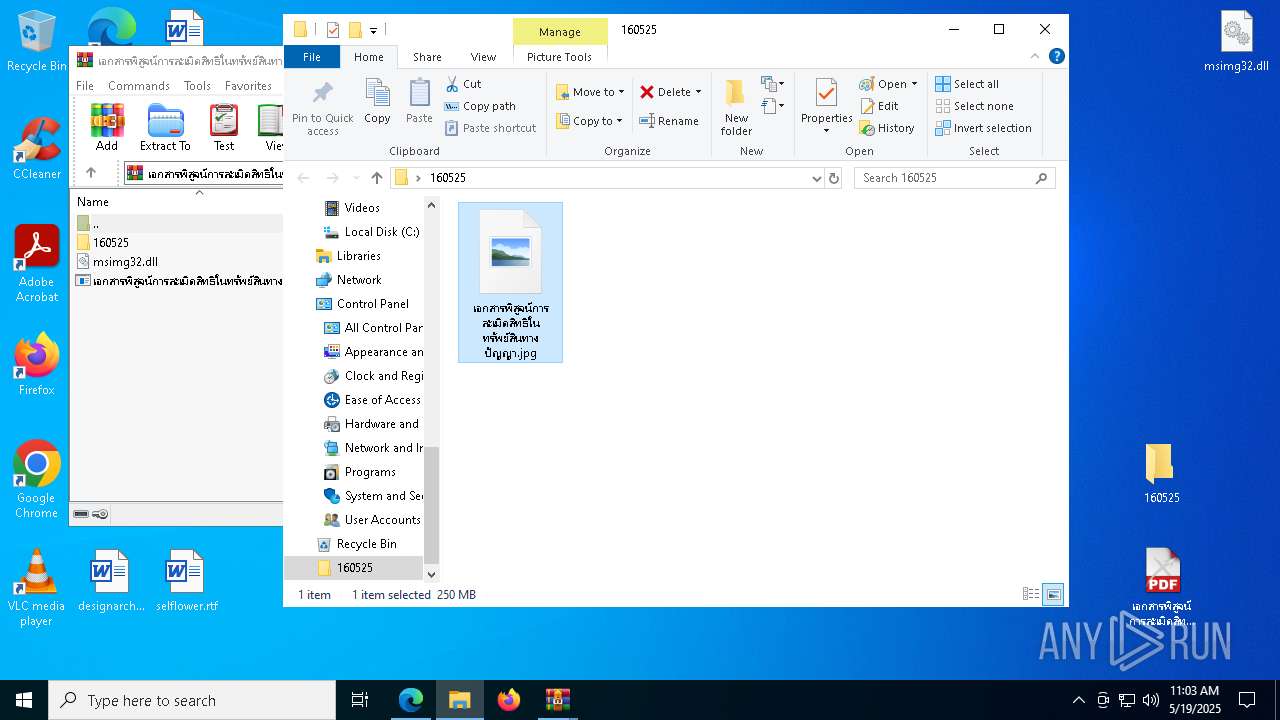
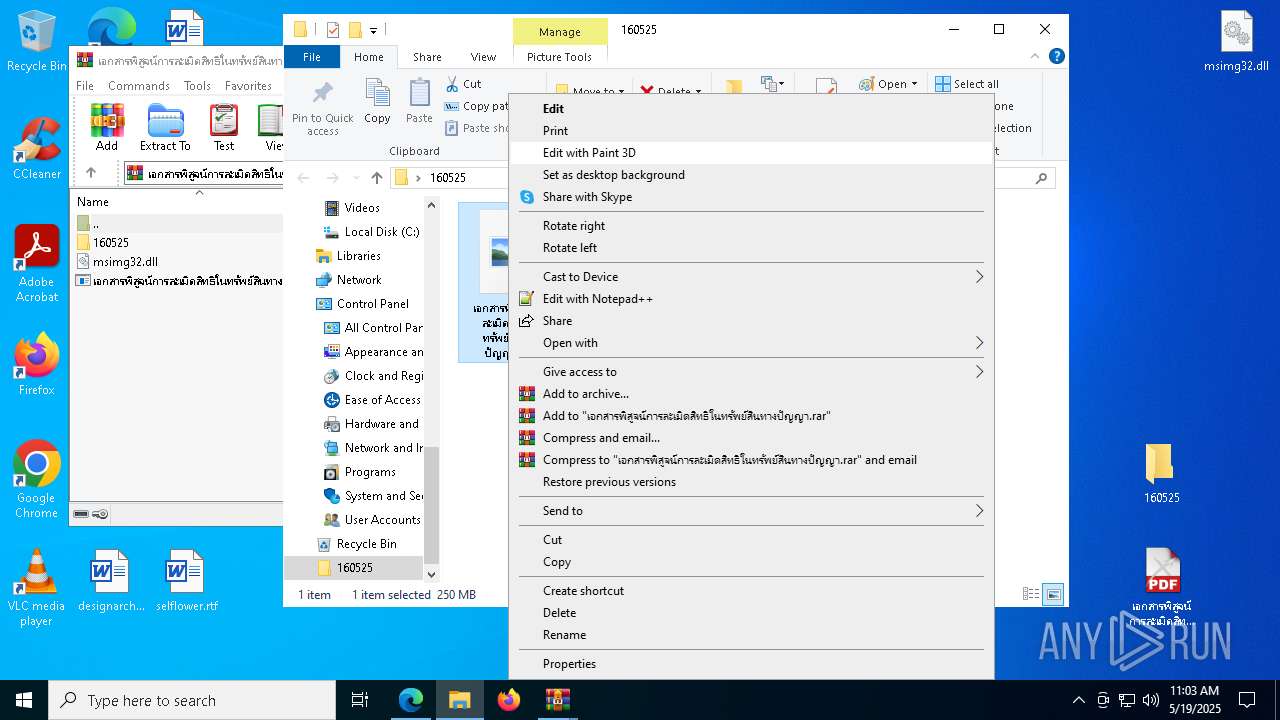
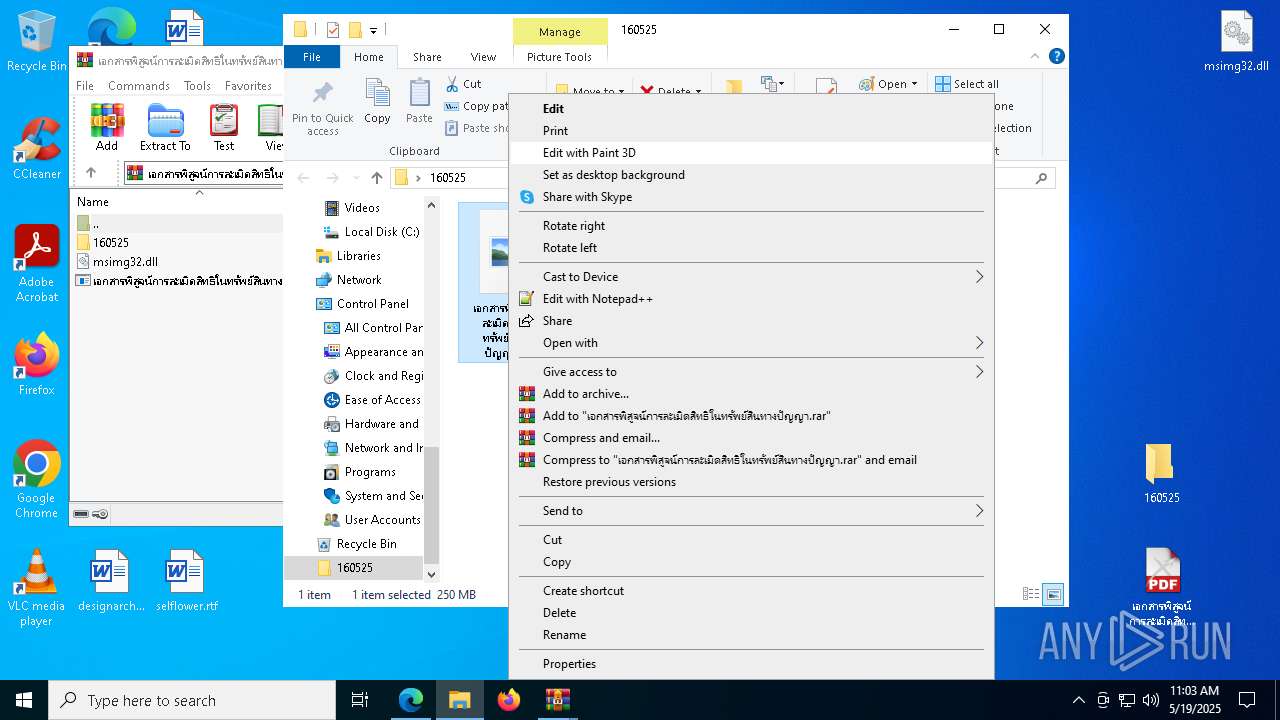
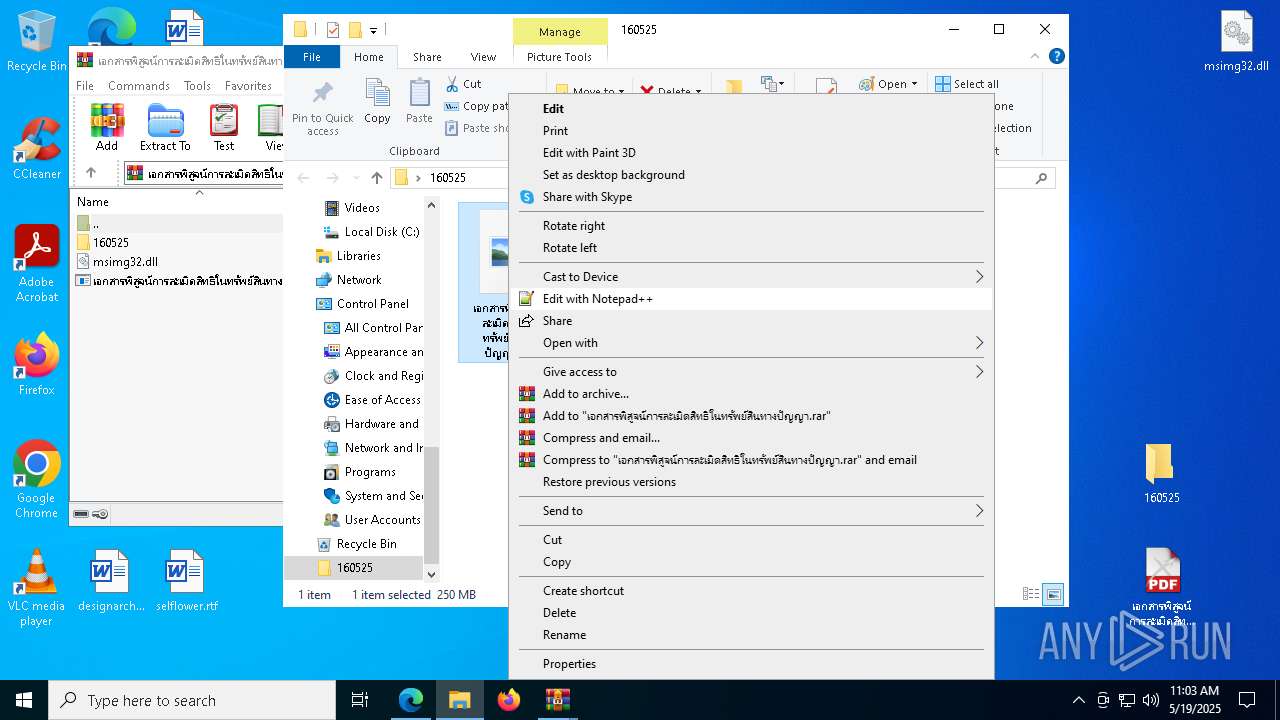
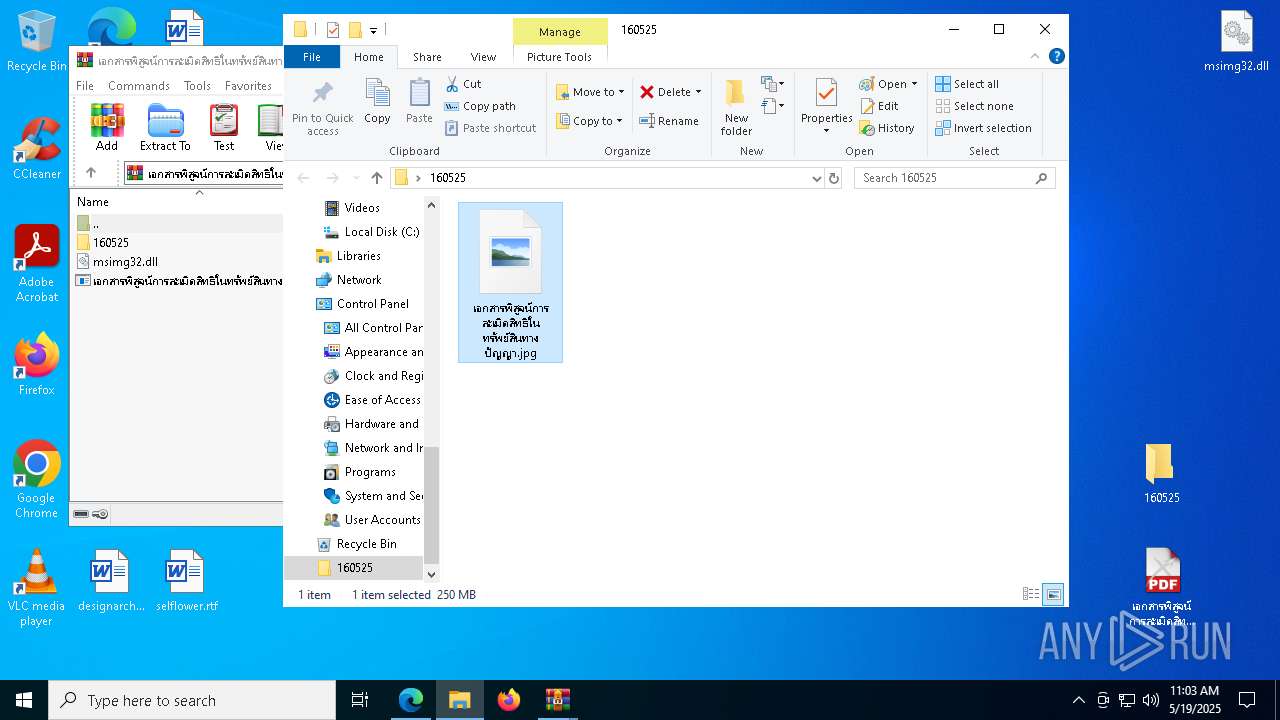
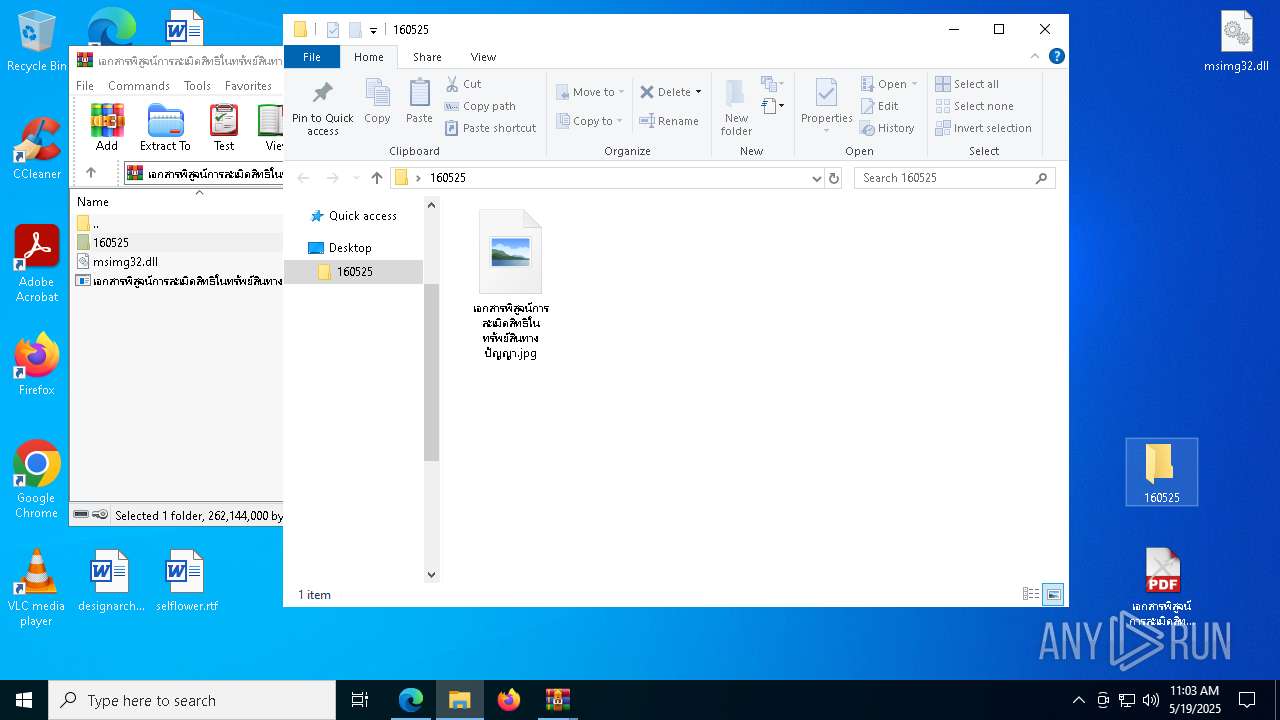
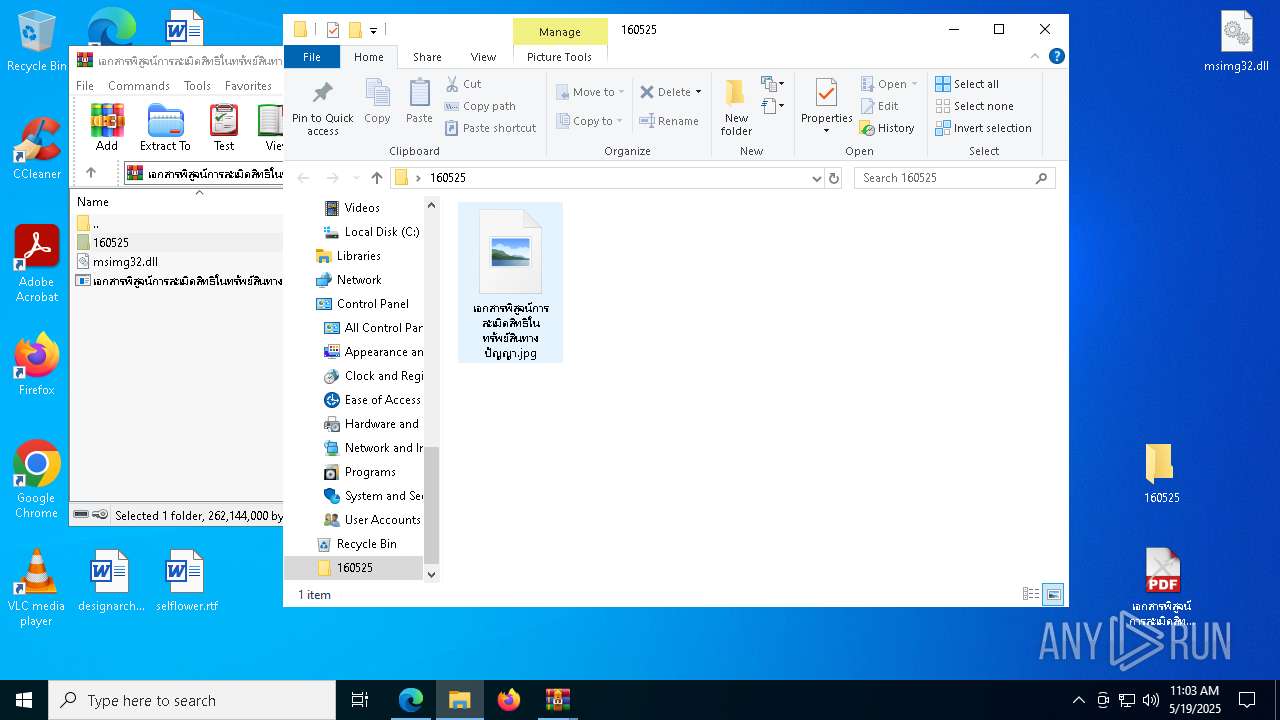
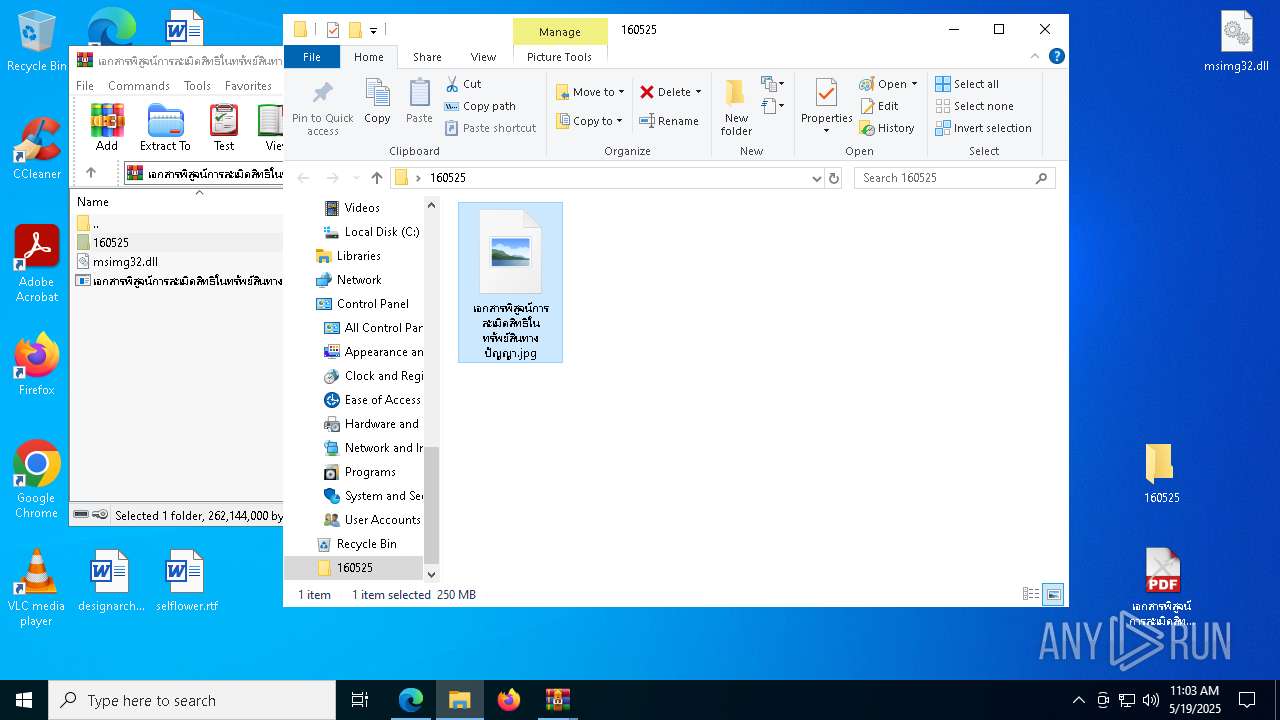
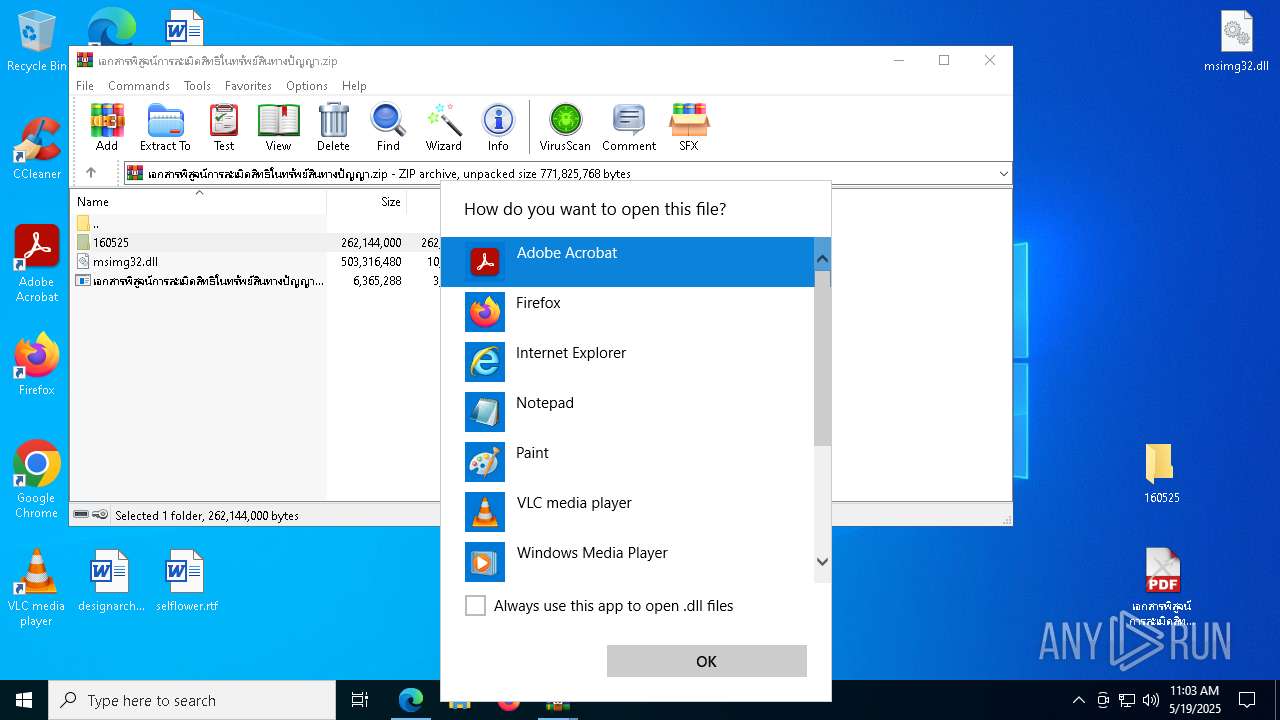
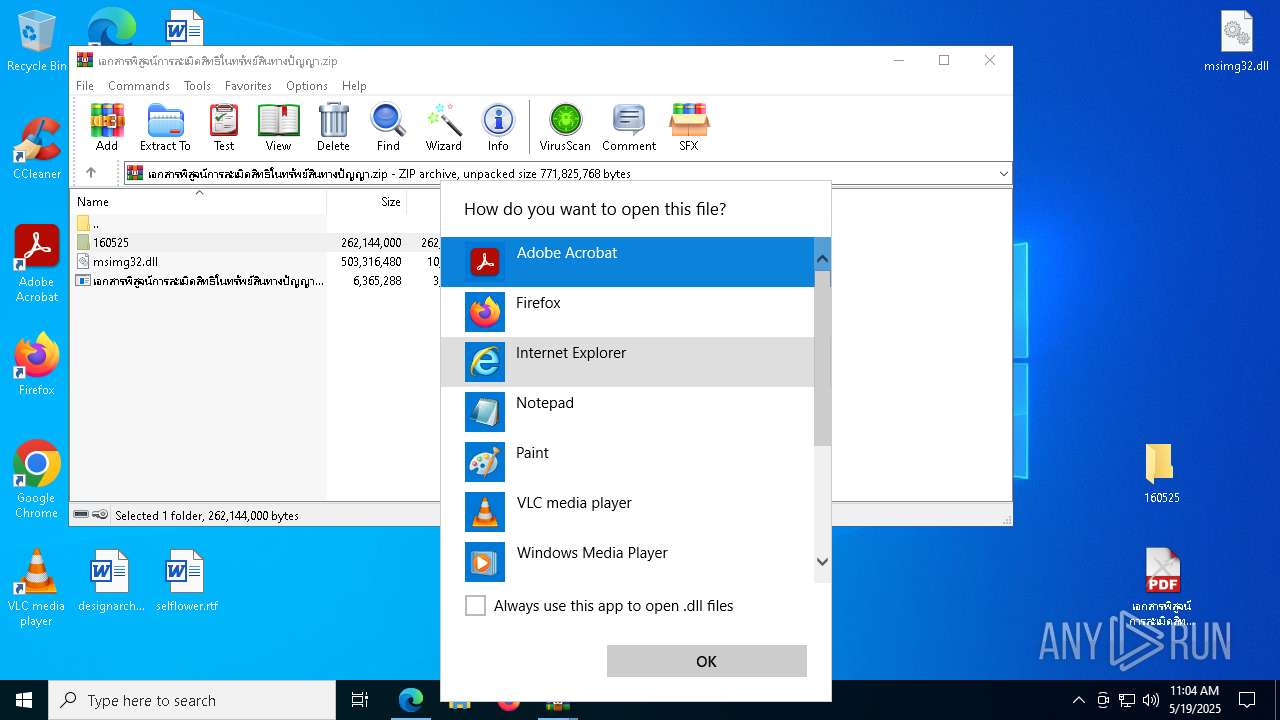
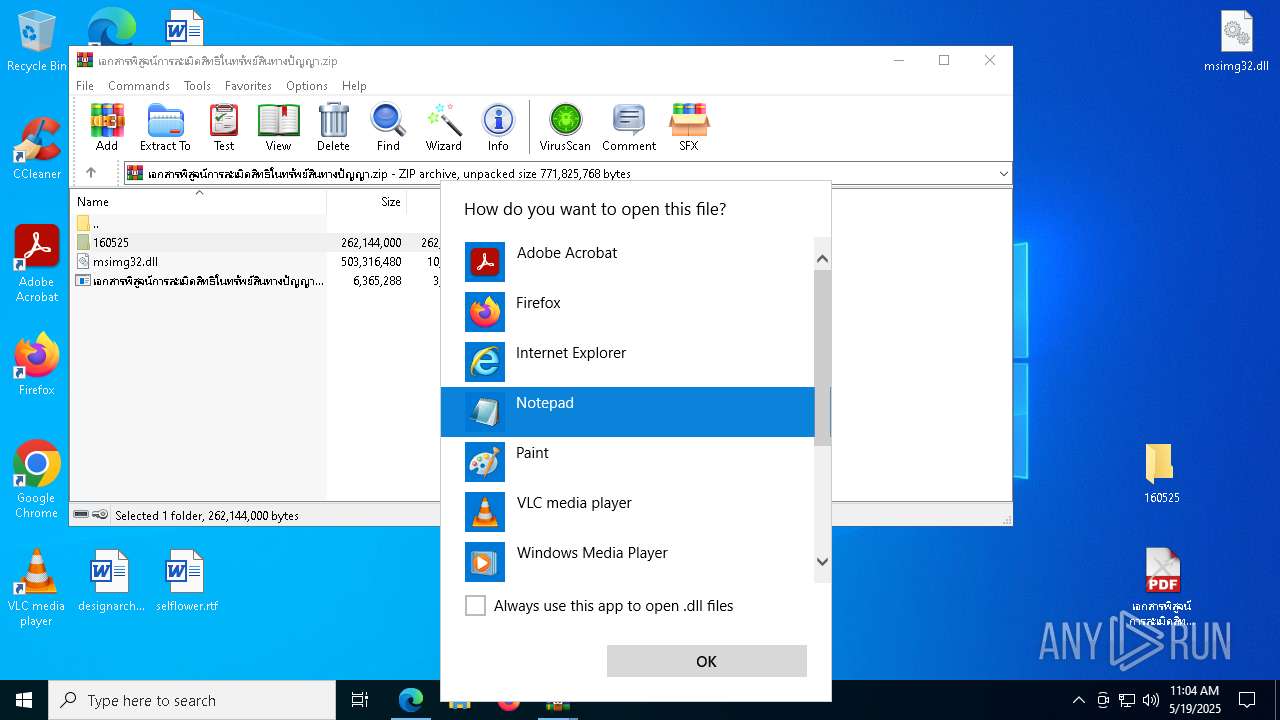
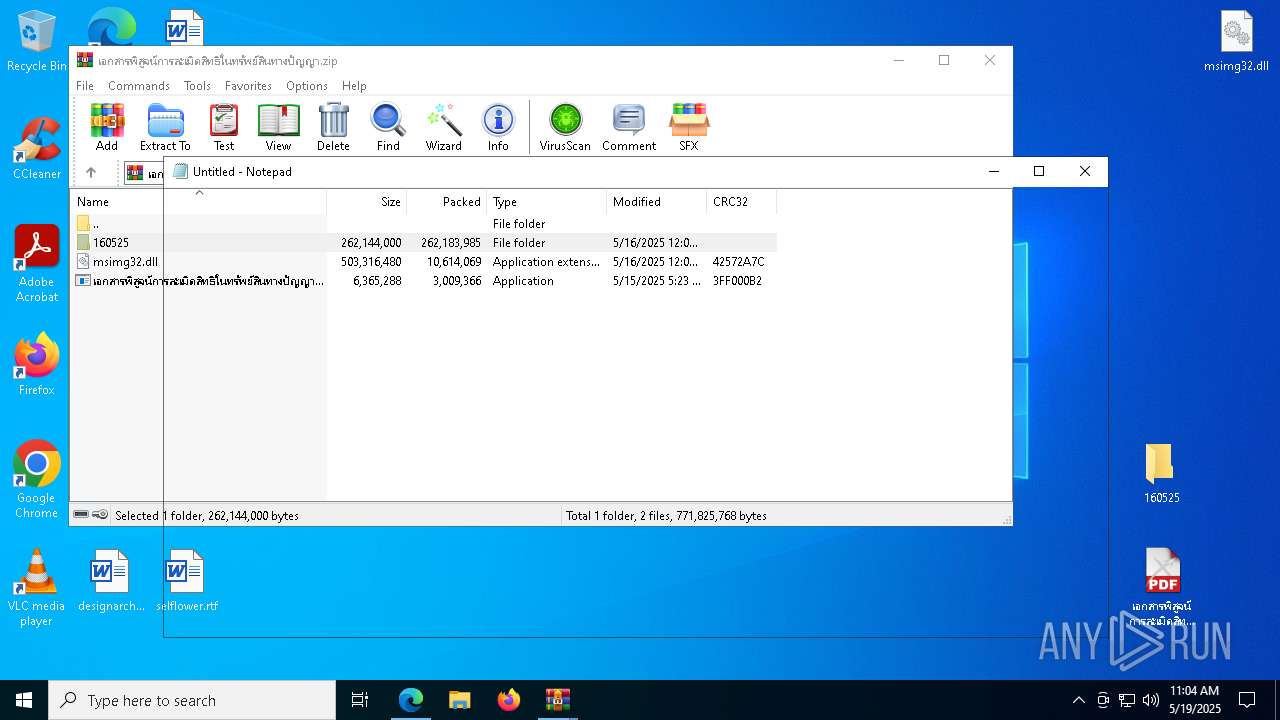
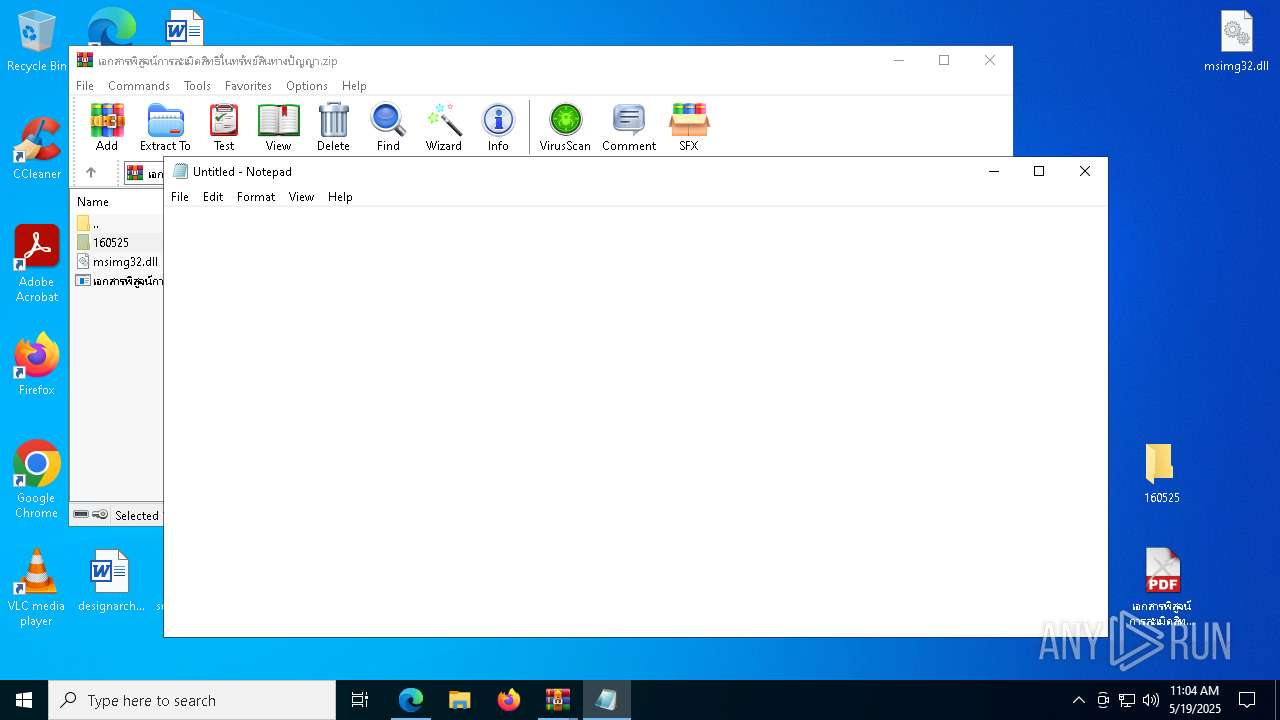
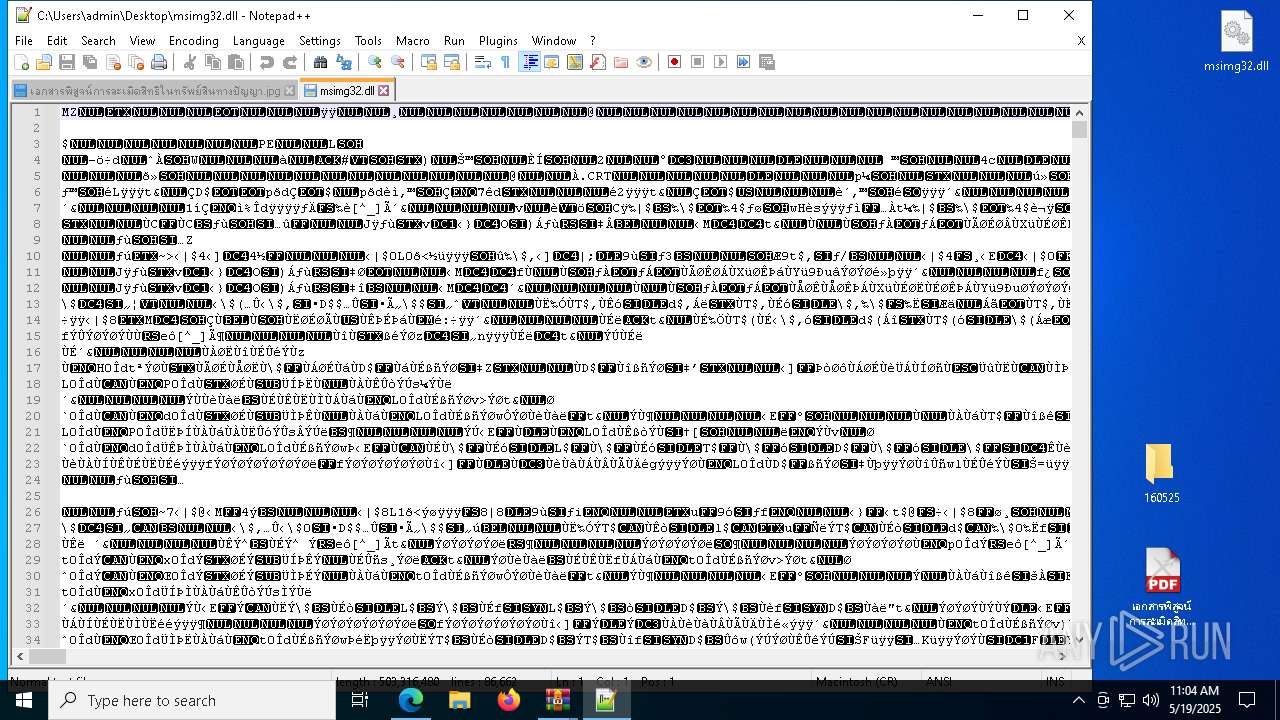
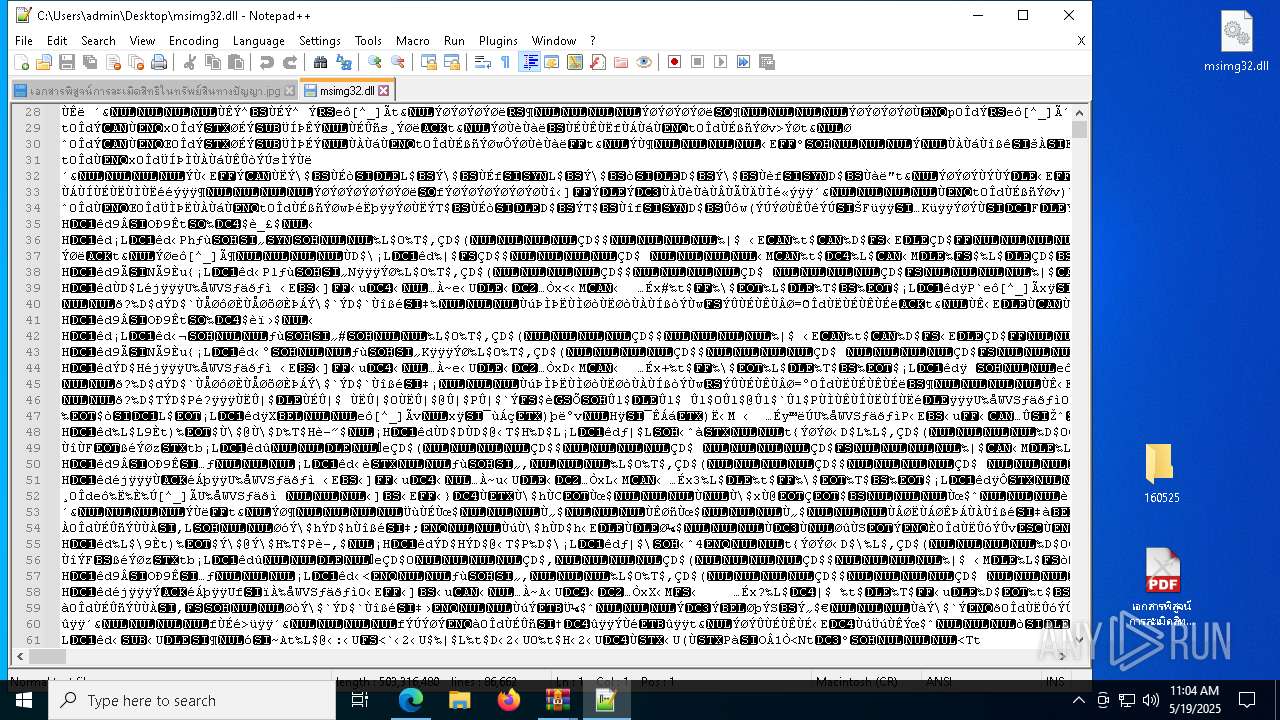
Manual execution by a user
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 6040)
- mspaint.exe (PID: 4120)
- notepad++.exe (PID: 5592)
- mspaint.exe (PID: 6944)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 2596)
- svchost.exe (PID: 6344)
- svchost.exe (PID: 2980)
- notepad++.exe (PID: 1616)
- svchost.exe (PID: 8420)
- svchost.exe (PID: 7896)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 8884)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 9088)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 8700)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 6676)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 8996)
- เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe (PID: 8772)
Checks proxy server information
- slui.exe (PID: 4152)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6652)
- OpenWith.exe (PID: 7100)
Executable content was dropped or overwritten
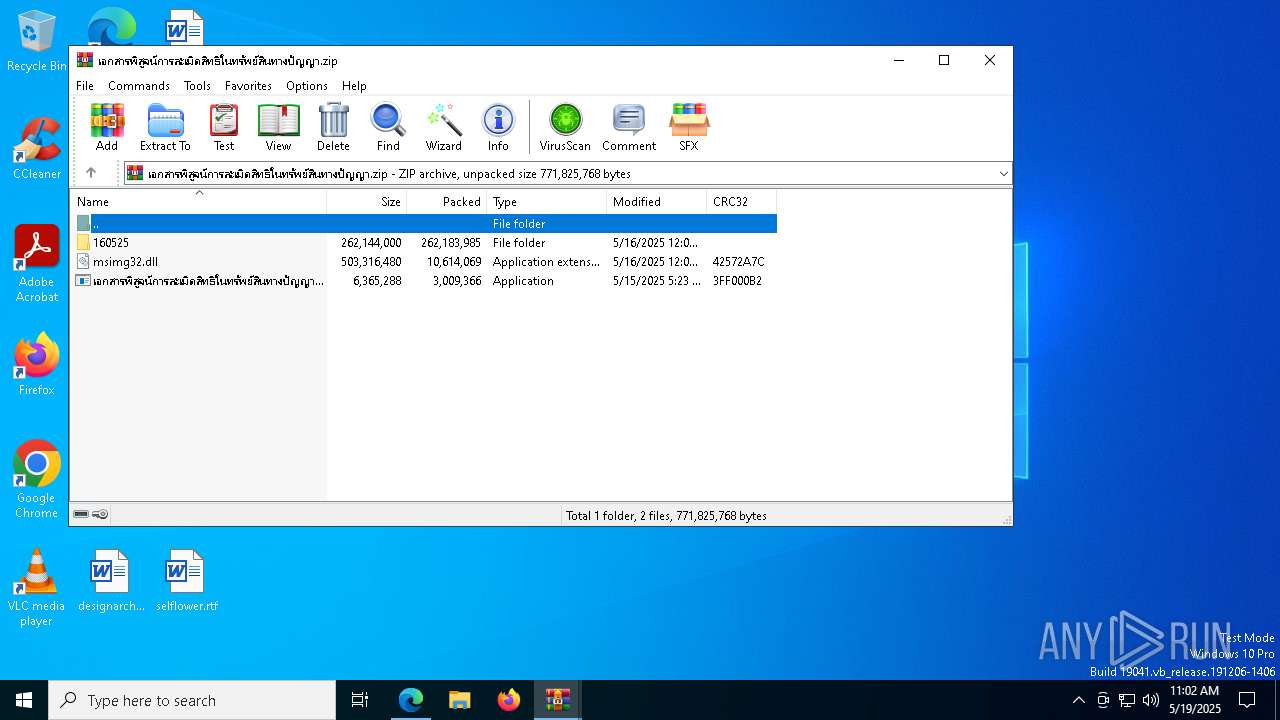
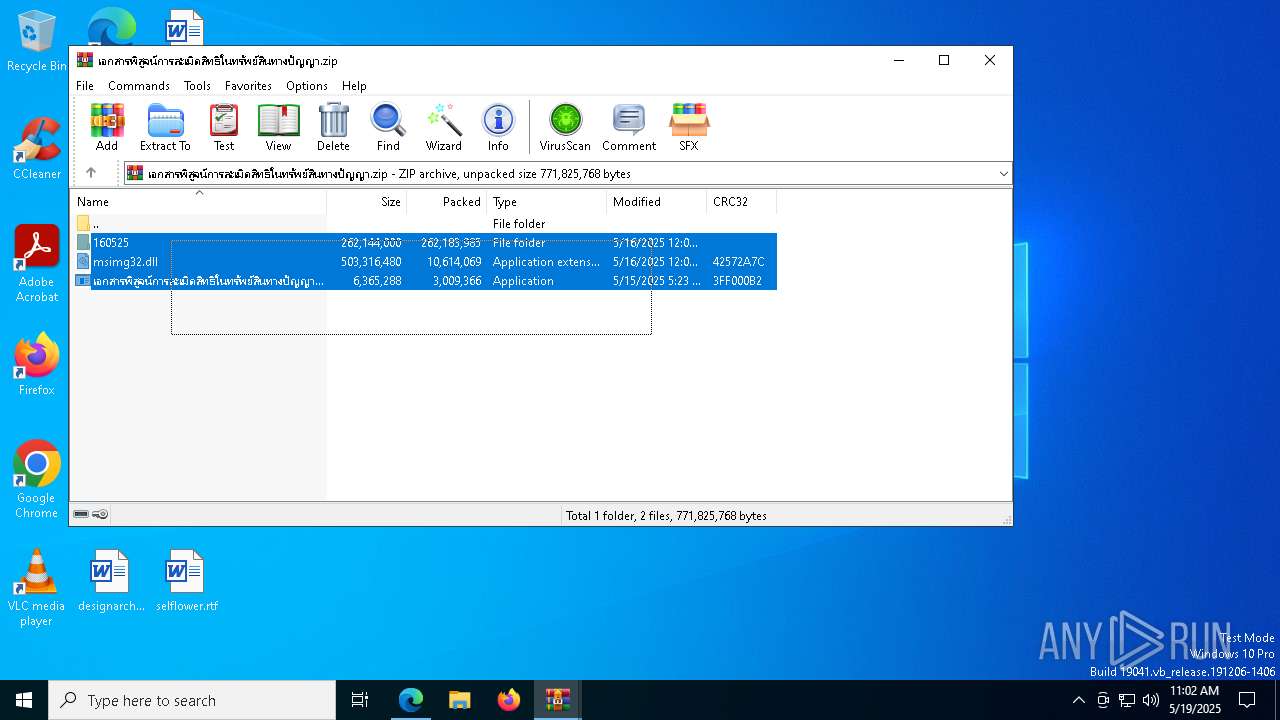
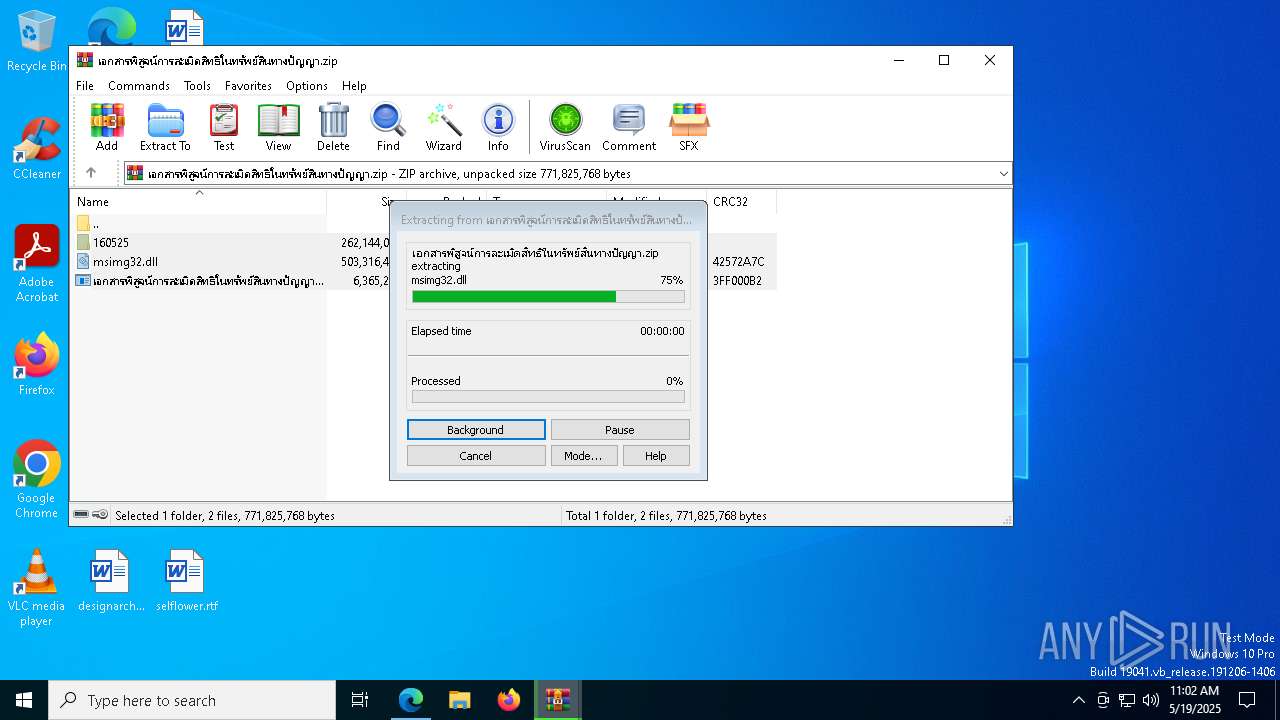
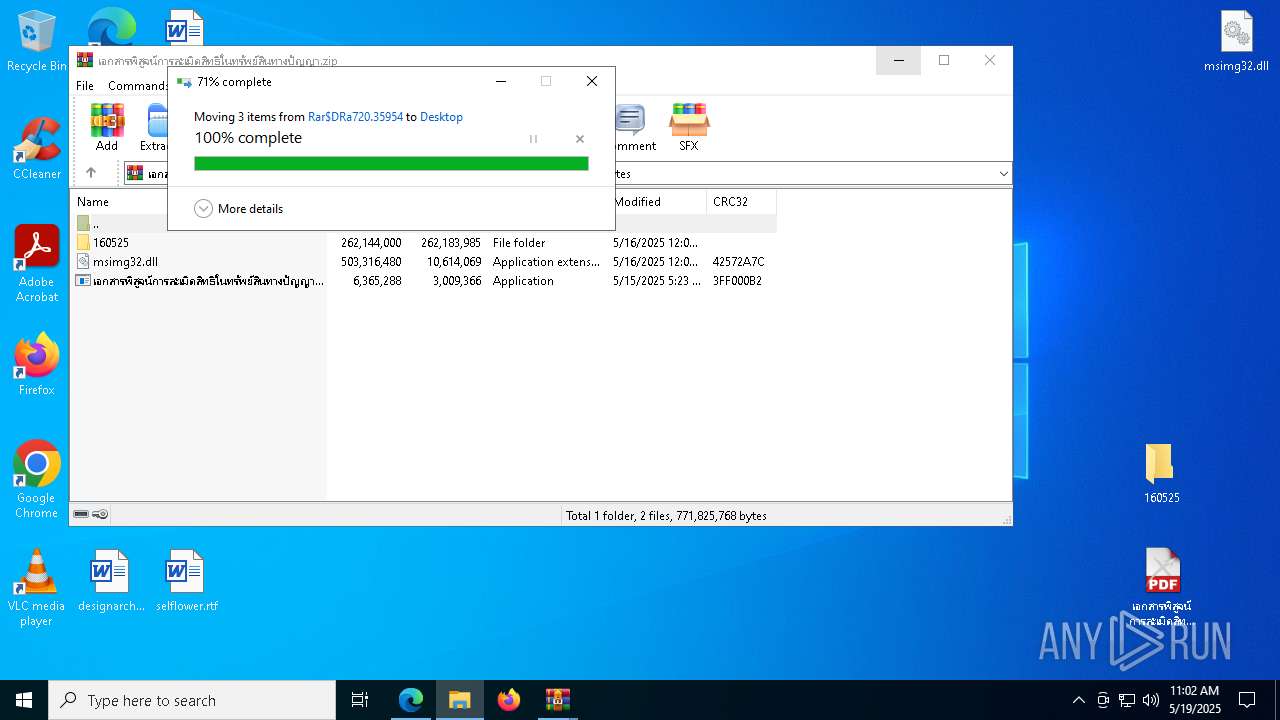
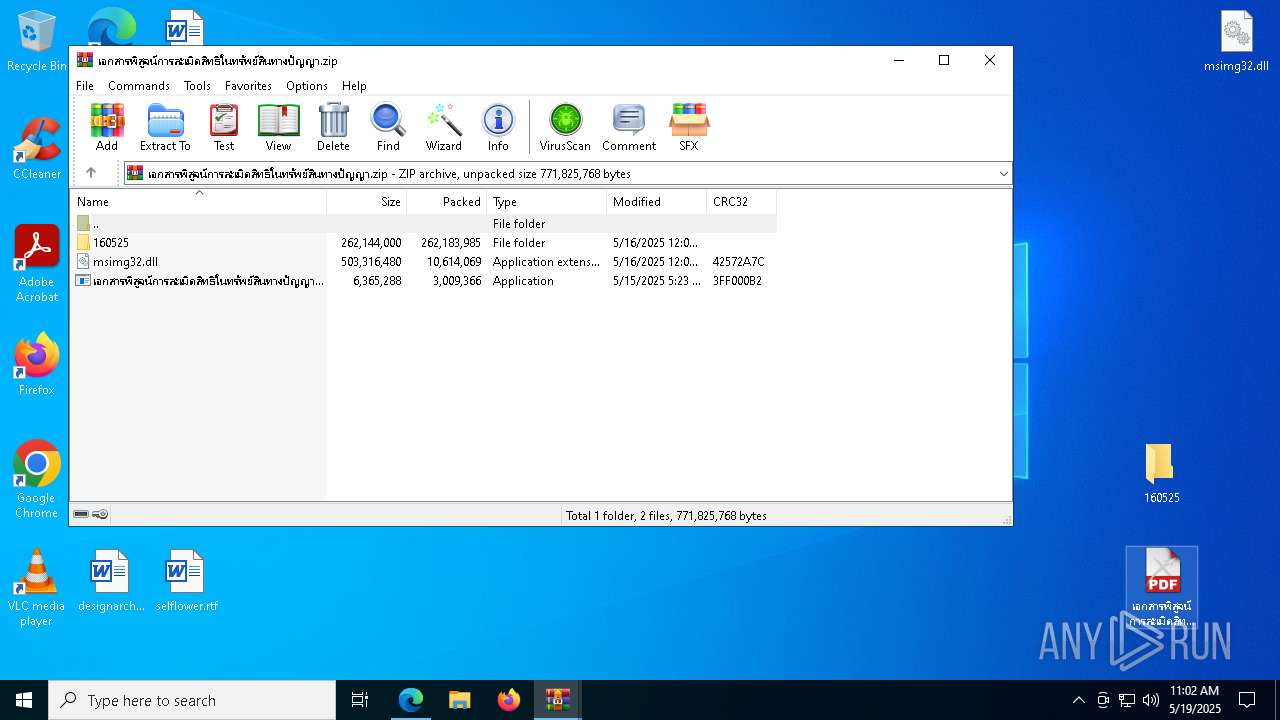
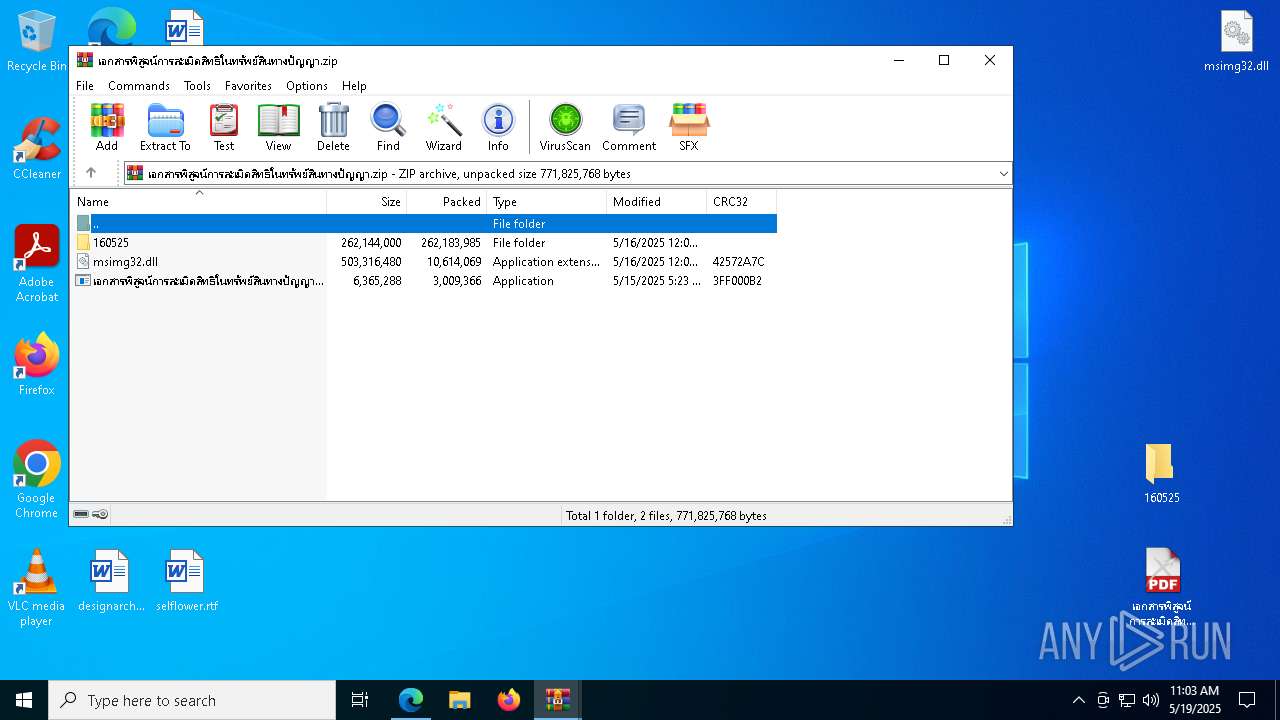
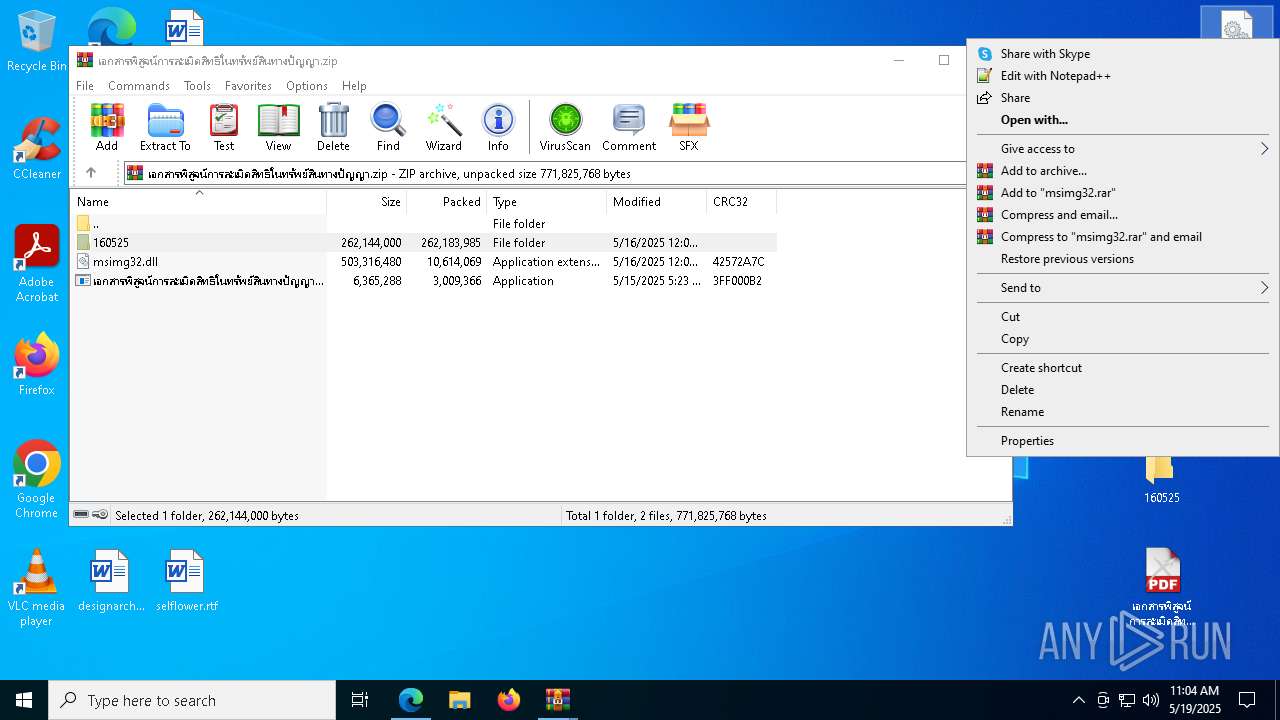
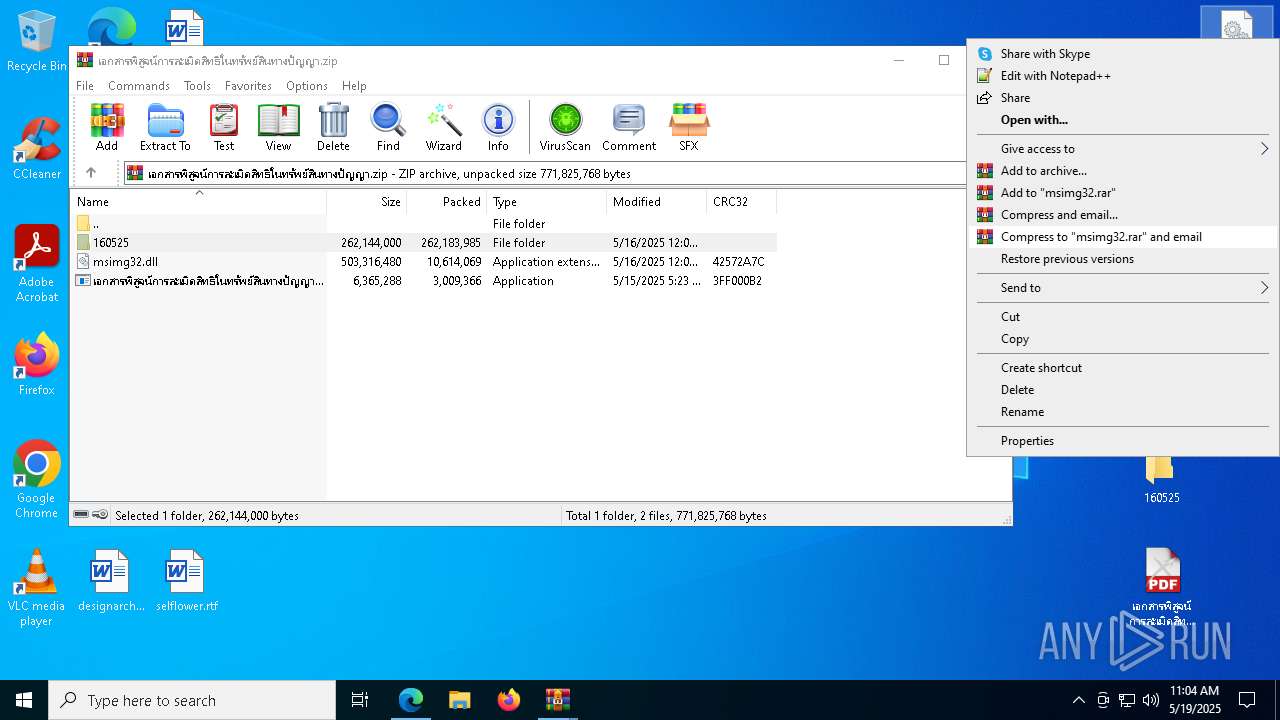
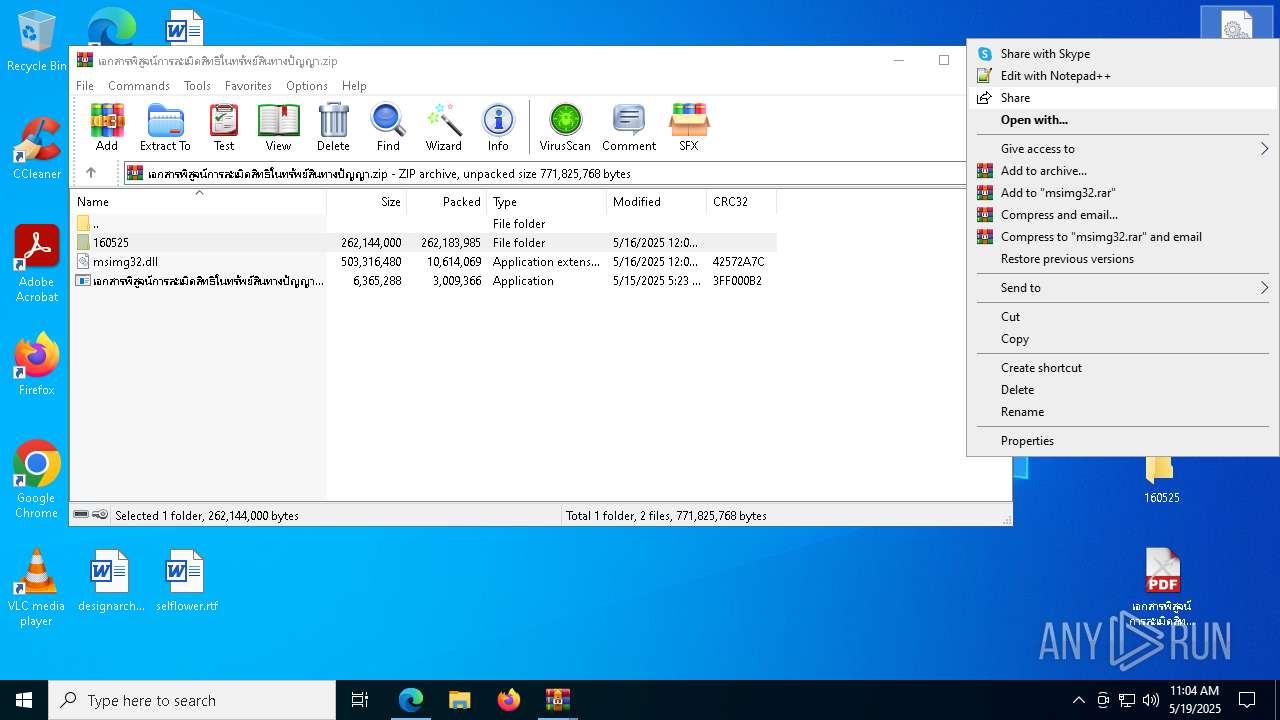
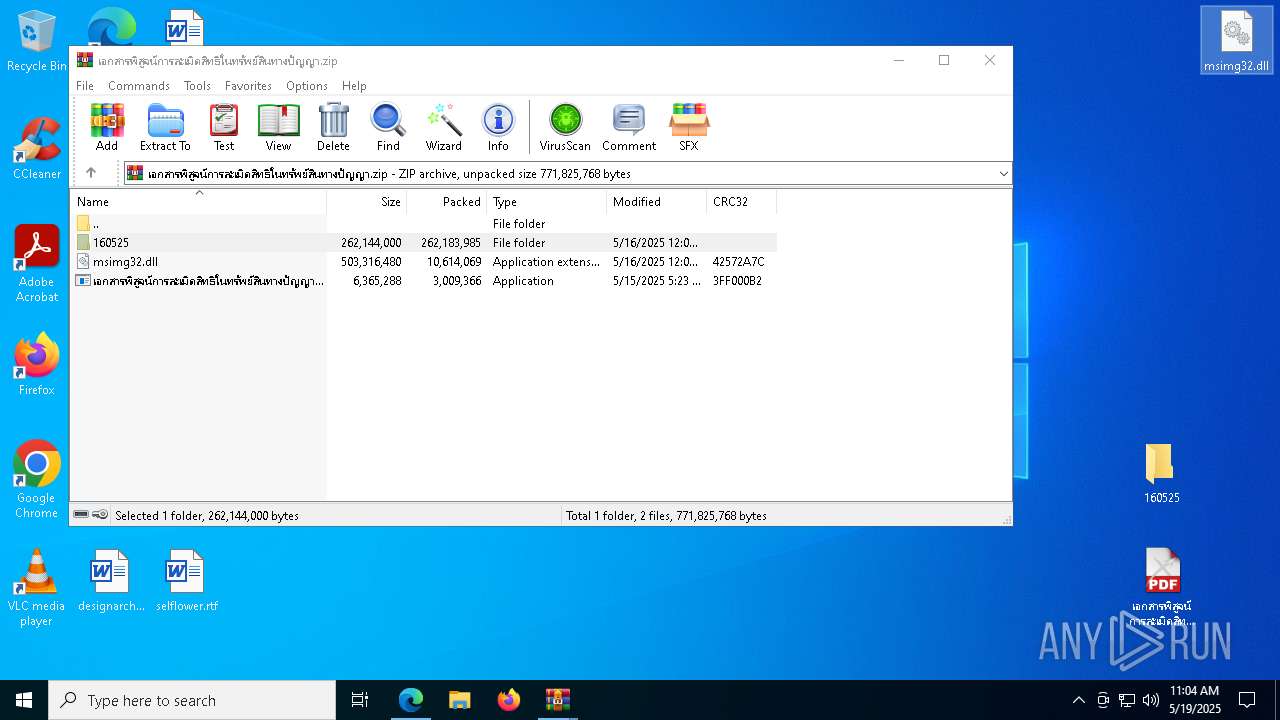
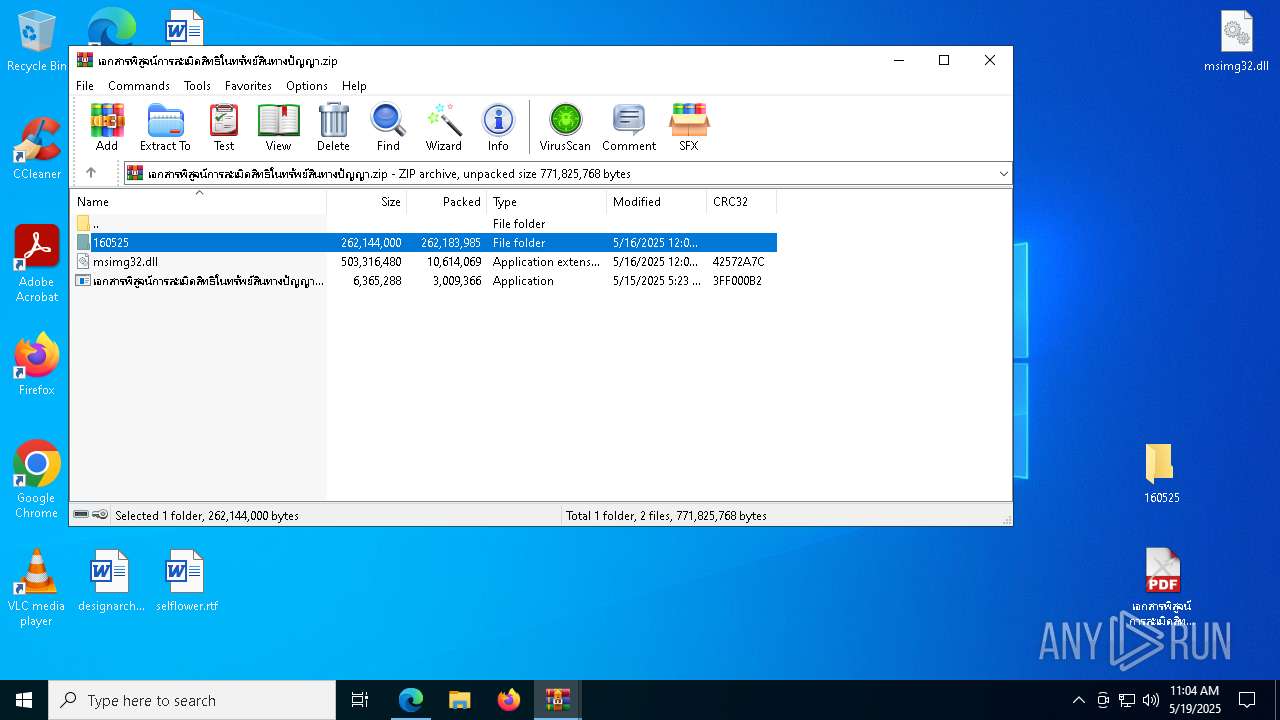
- WinRAR.exe (PID: 720)
- msedge.exe (PID: 1616)
The sample compiled with english language support
- WinRAR.exe (PID: 720)
- msedge.exe (PID: 1616)
- wmpnscfg.exe (PID: 3192)
- svchost.exe (PID: 2980)
- svchost.exe (PID: 7896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
273
Monitored processes
129
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
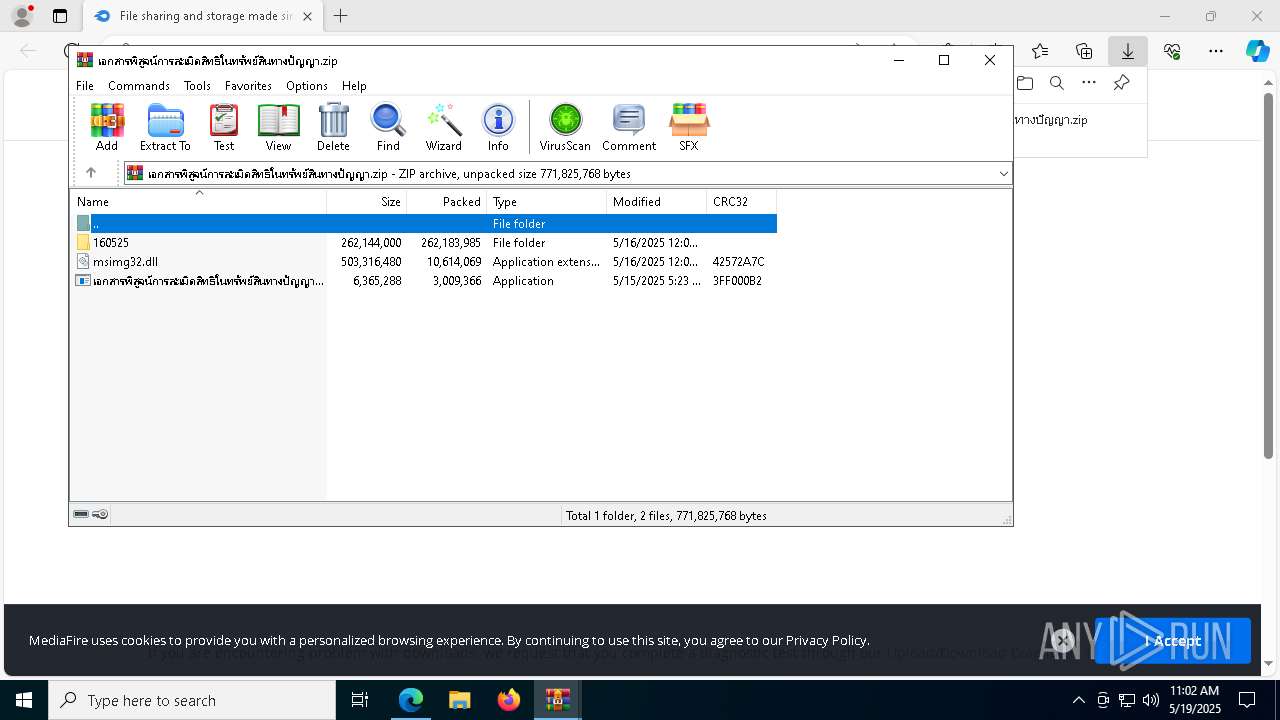
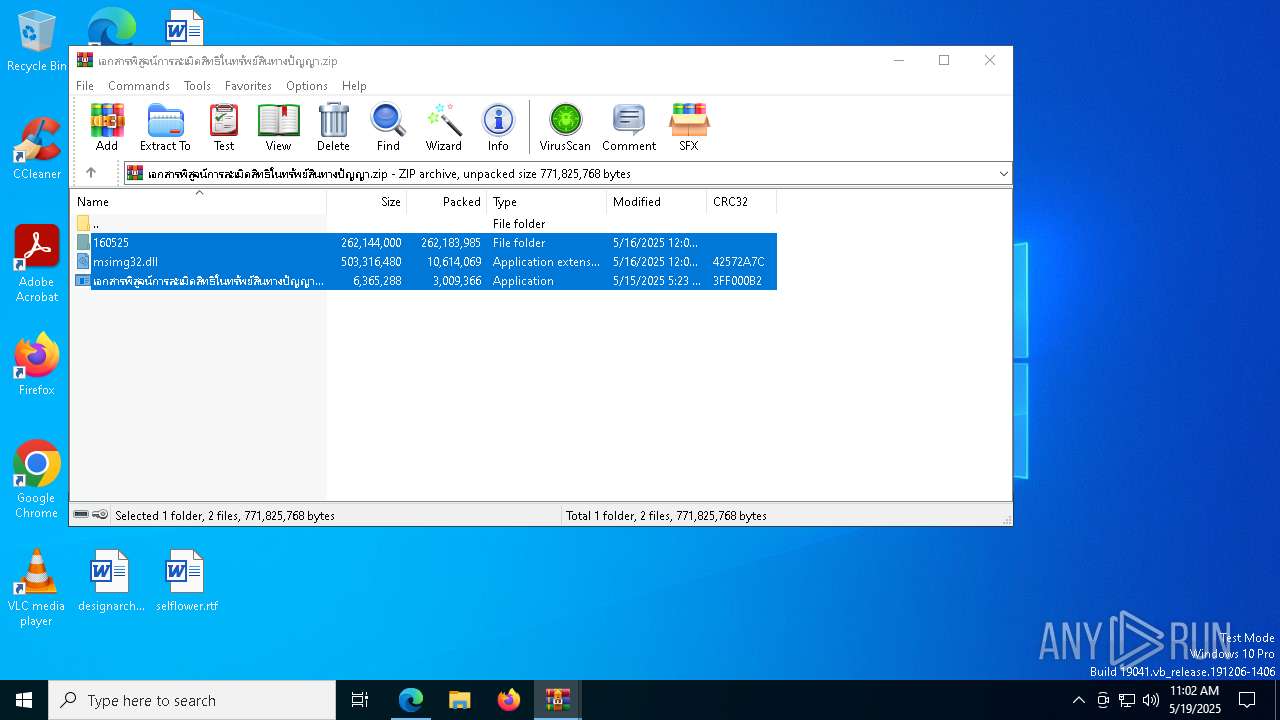
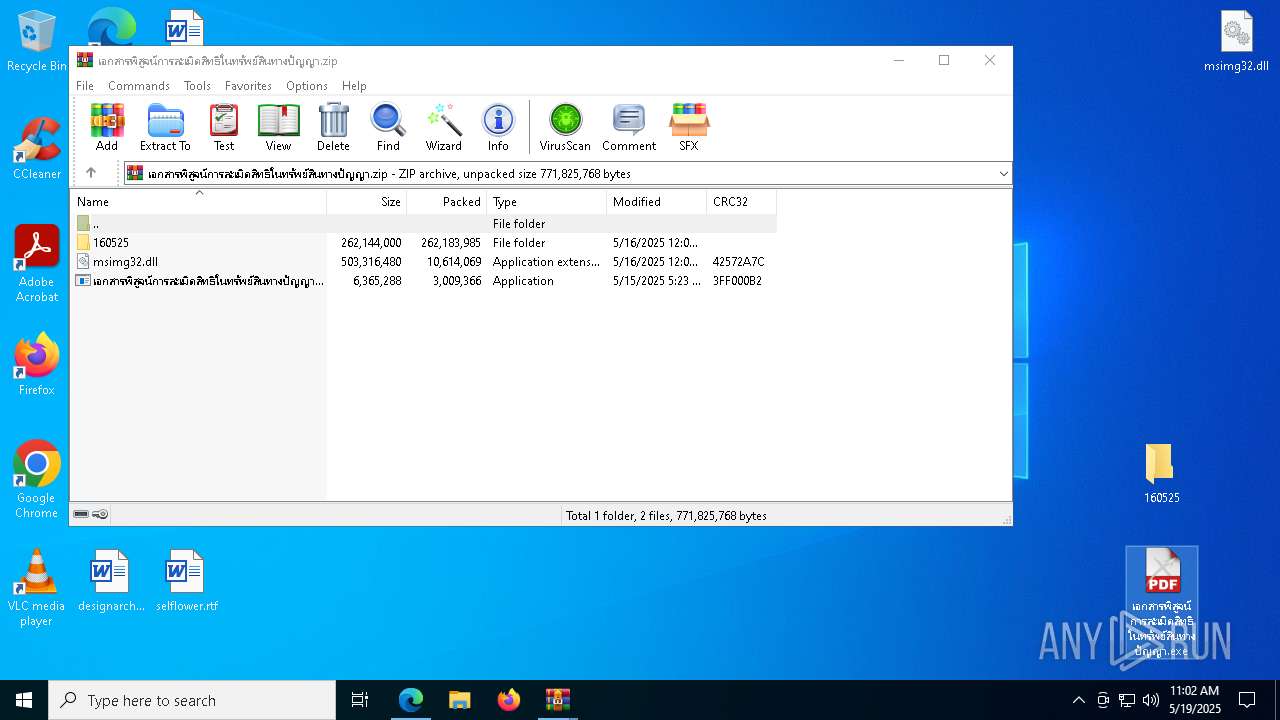
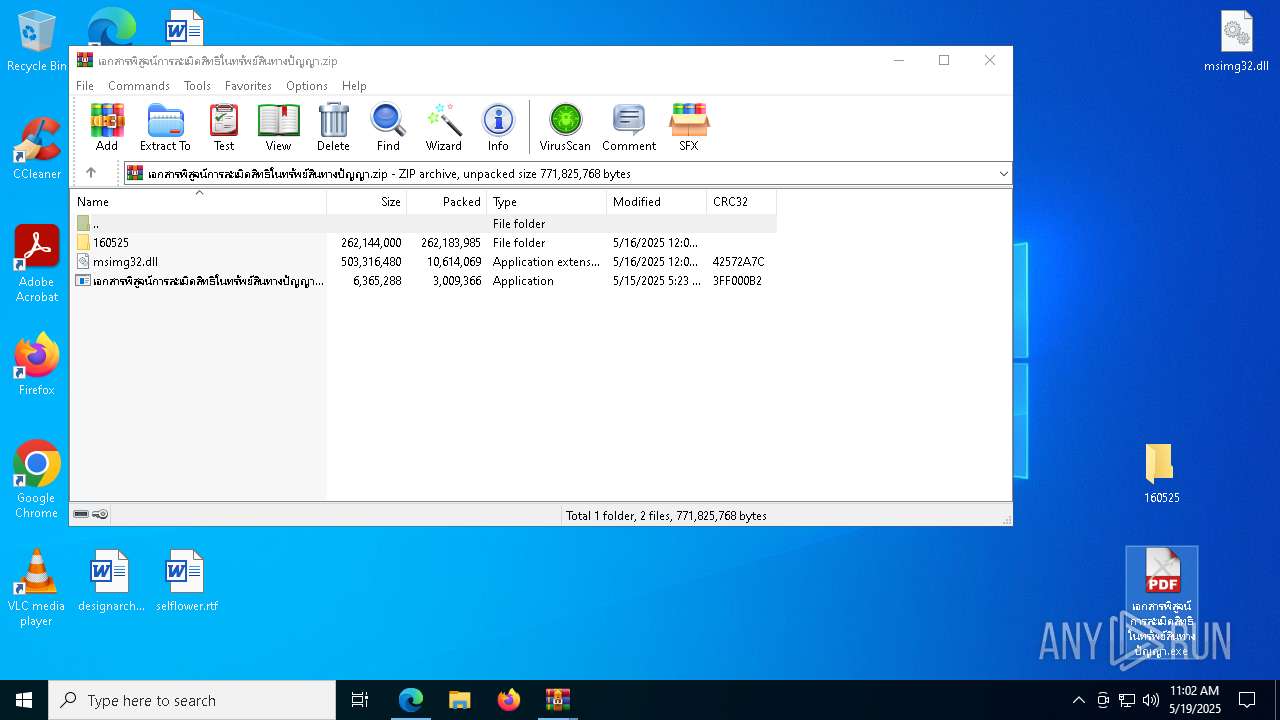
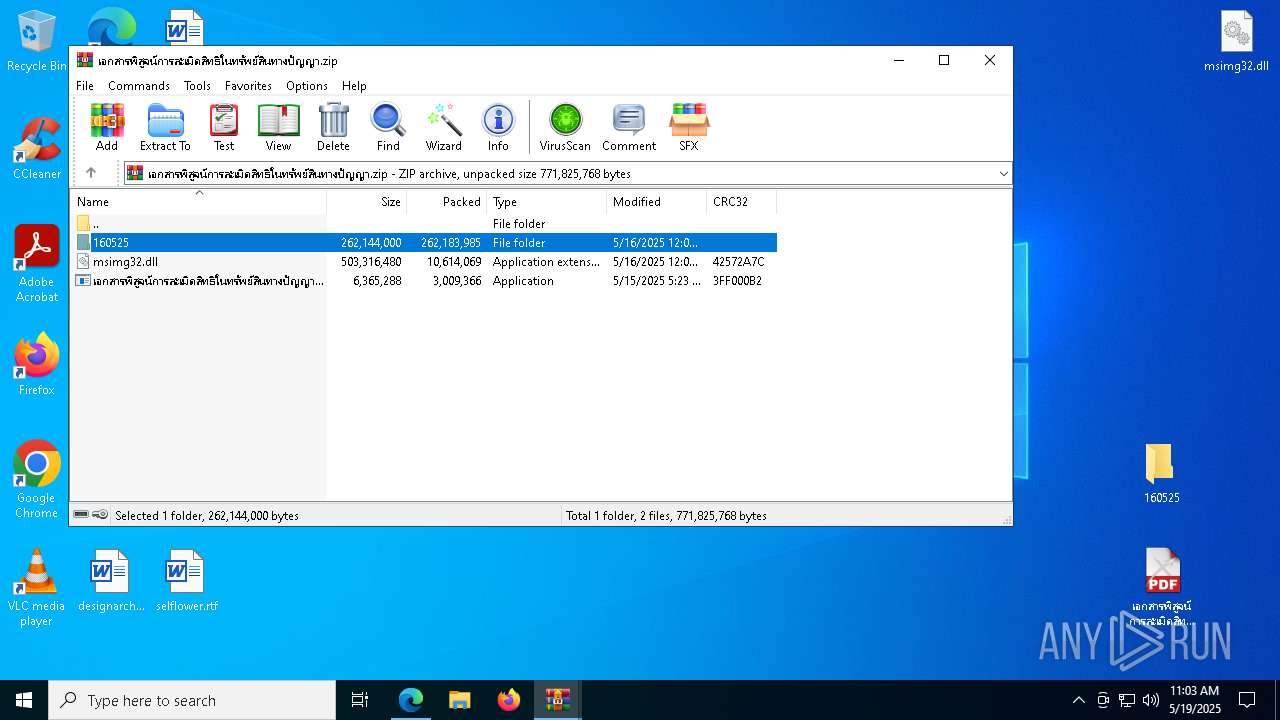
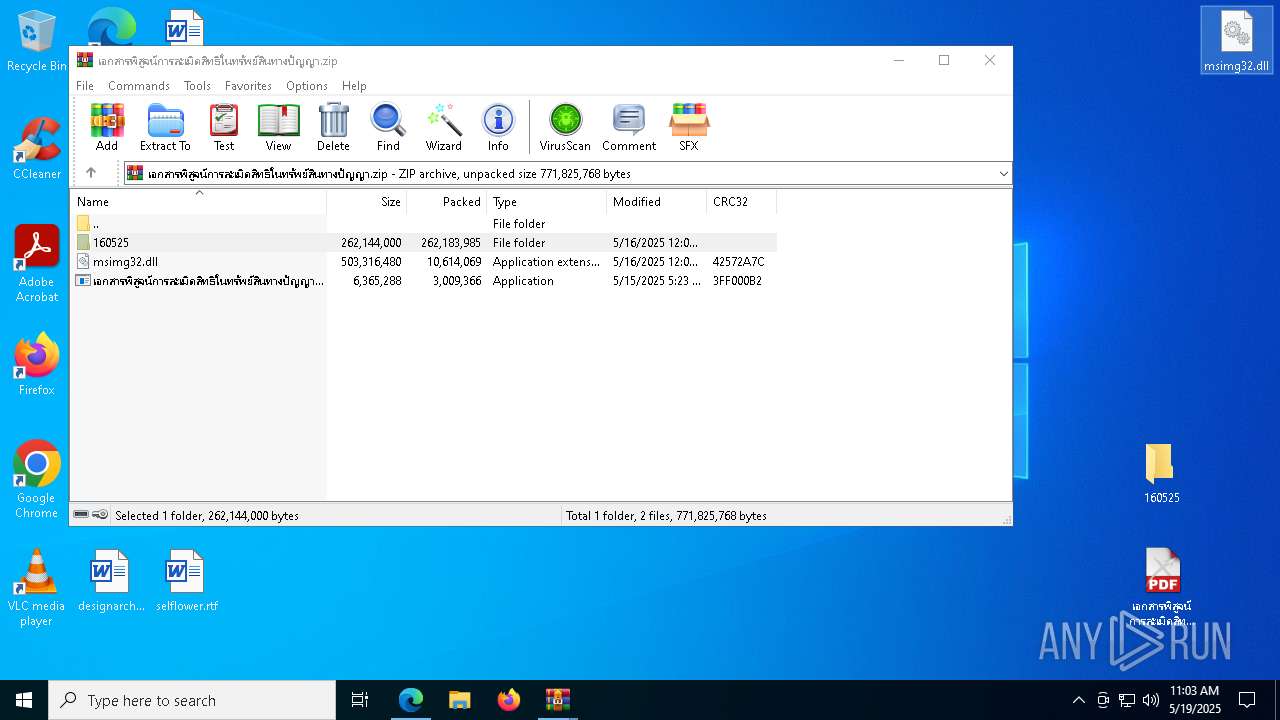
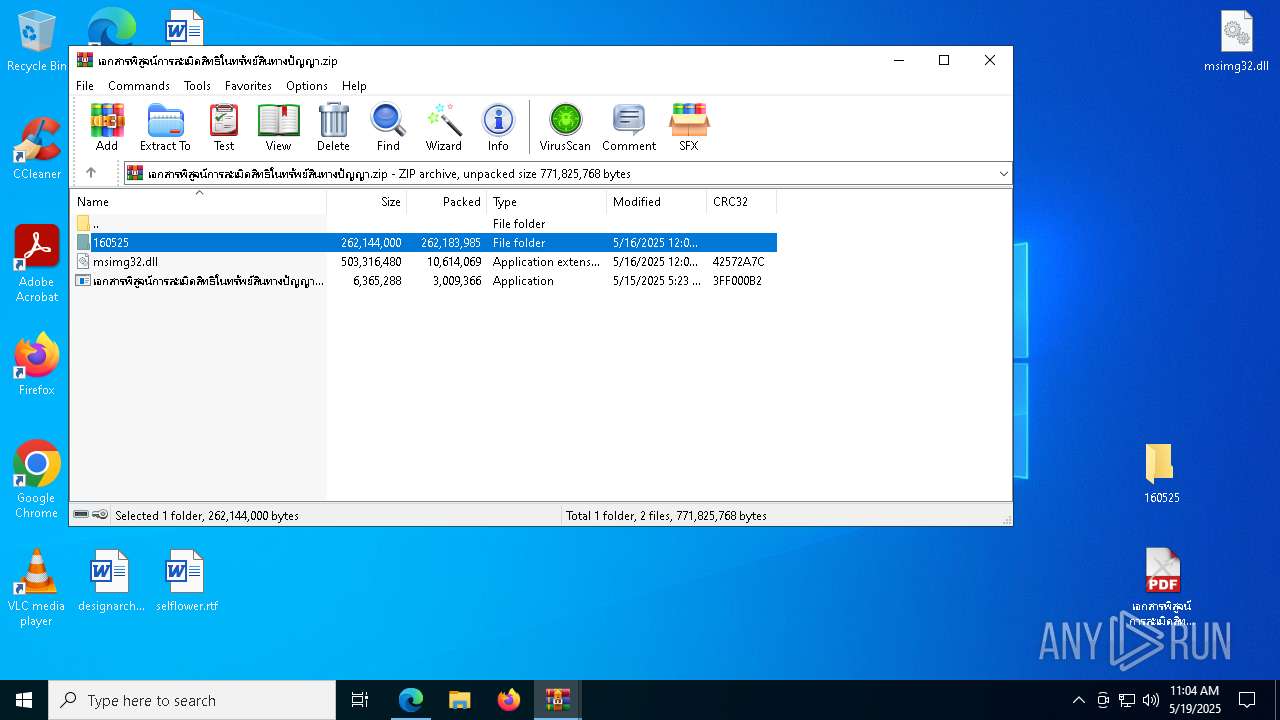
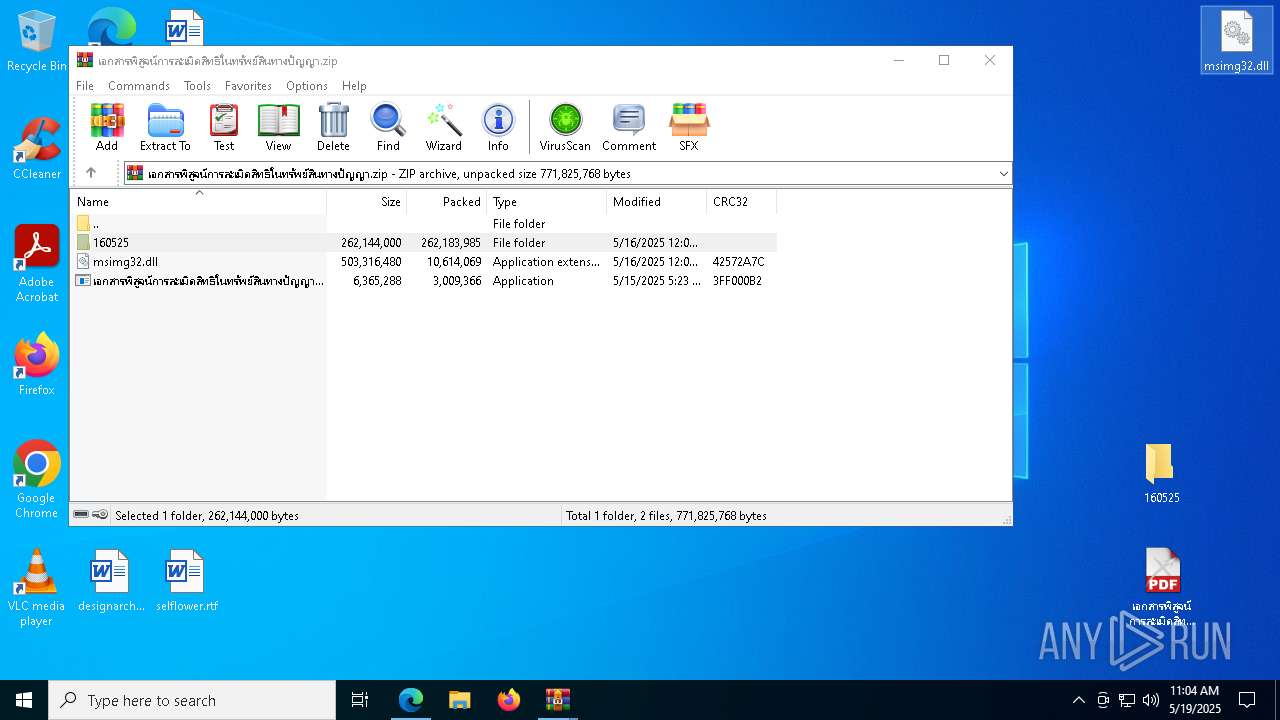
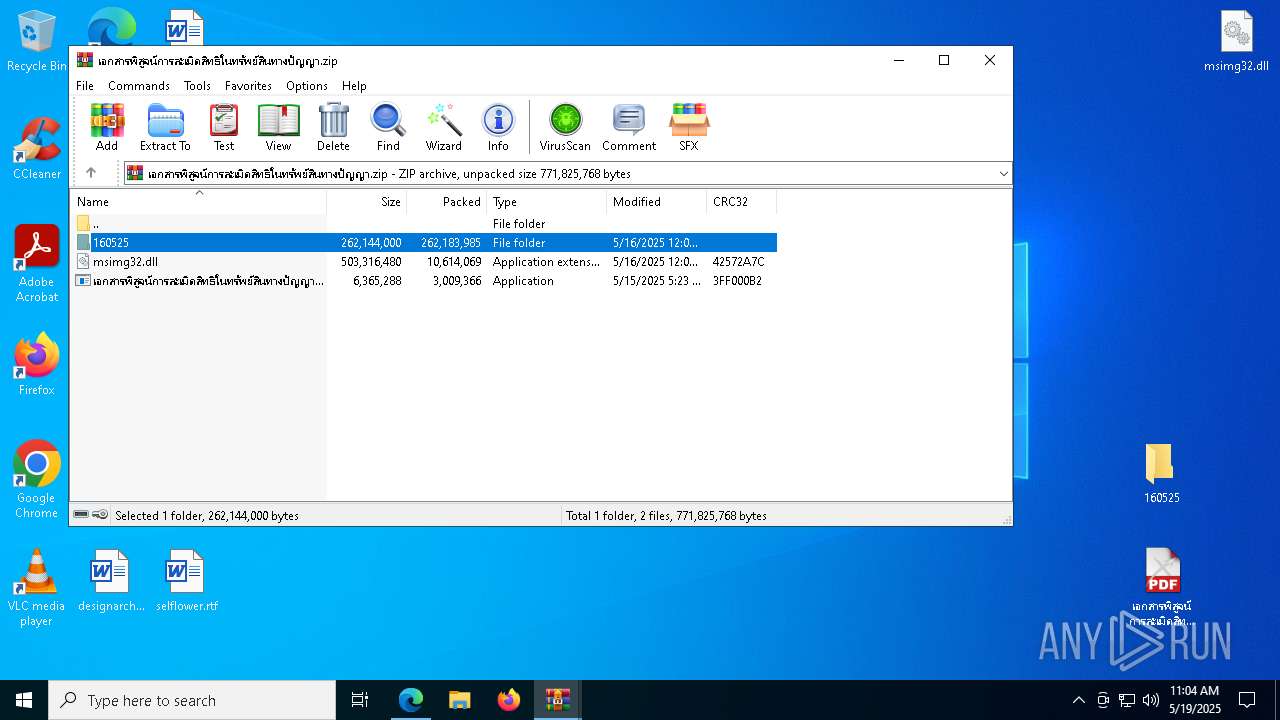
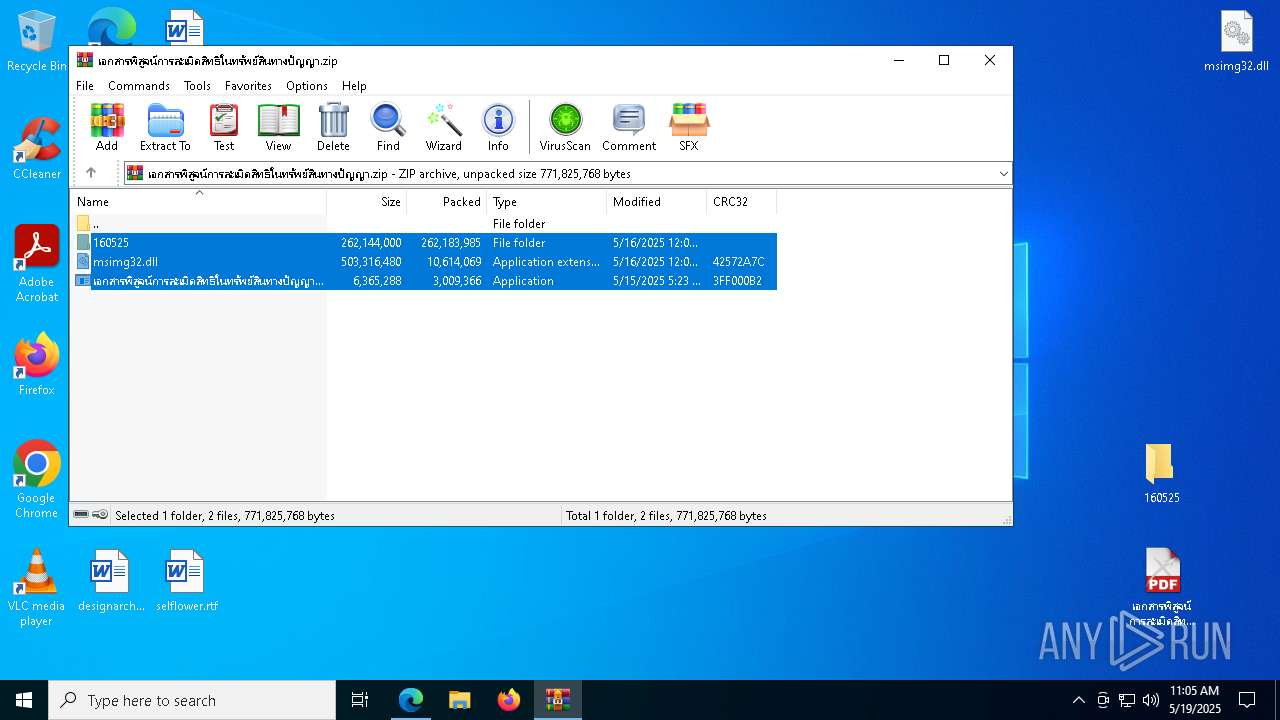
| 720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chr46FB.tmp /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chr46FB.tmp\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2a0,0x2a4,0x2a8,0x16c,0x320,0x7ffc89845fd8,0x7ffc89845fe4,0x7ffc89845ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chr8A90.tmp /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chr8A90.tmp\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ffc8630dc40,0x7ffc8630dc4c,0x7ffc8630dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
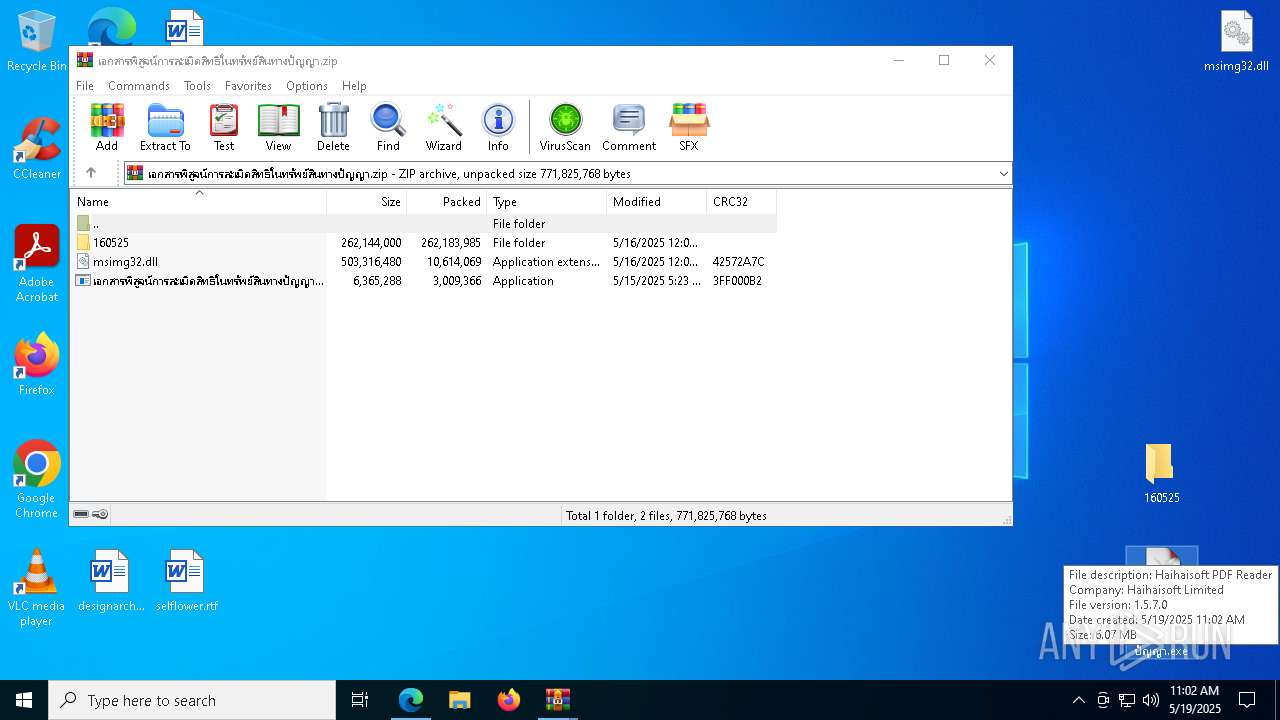
| 976 | "C:\Users\admin\Desktop\เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe" | C:\Users\admin\Desktop\เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe | เอกสารพิสูจน์การละเมิดสิทธิในทรัพย์สินทางปัญญา.exe | ||||||||||||
User: admin Company: Haihaisoft Limited Integrity Level: MEDIUM Description: Haihaisoft PDF Reader Exit code: 3221225477 Version: 1.5.7.0 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5132 --field-trial-handle=1976,i,15178553629297200341,16613733296077605674,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7864 --field-trial-handle=2400,i,15475794864431964164,1394710477752650637,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3096 --field-trial-handle=1968,i,11903966732008199996,15685586288754118394,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7720 --field-trial-handle=2400,i,15475794864431964164,1394710477752650637,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
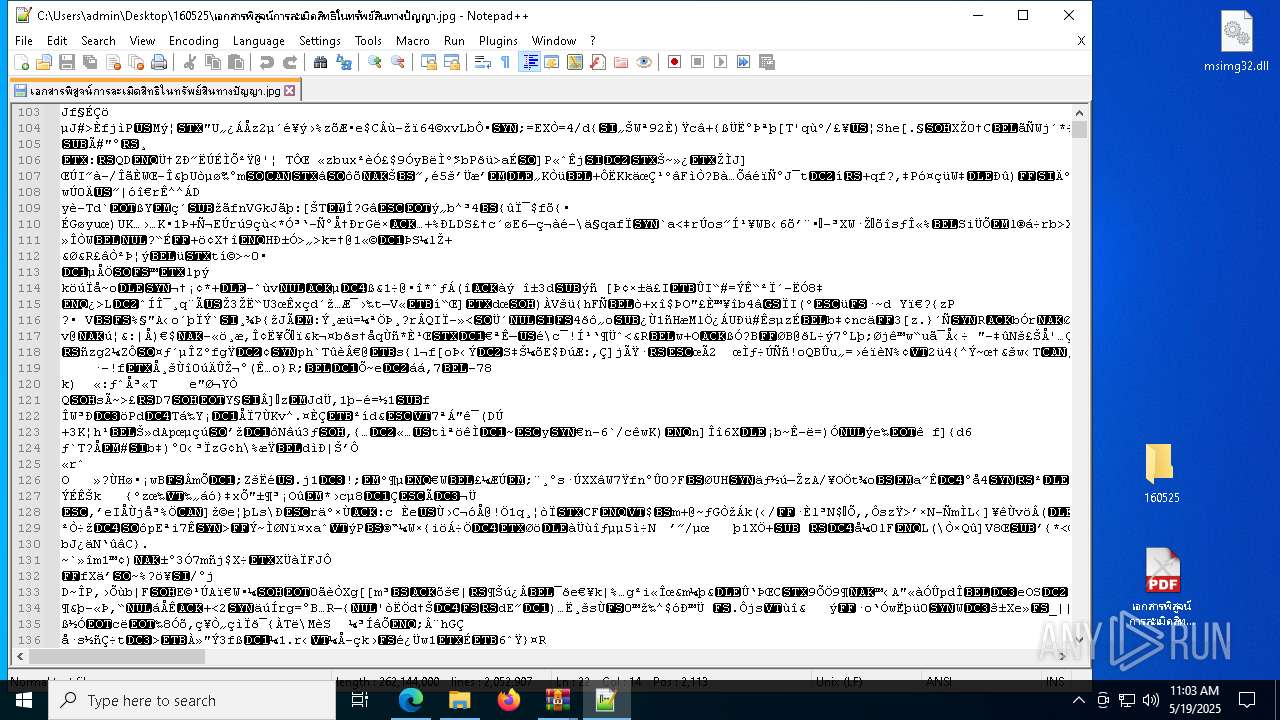
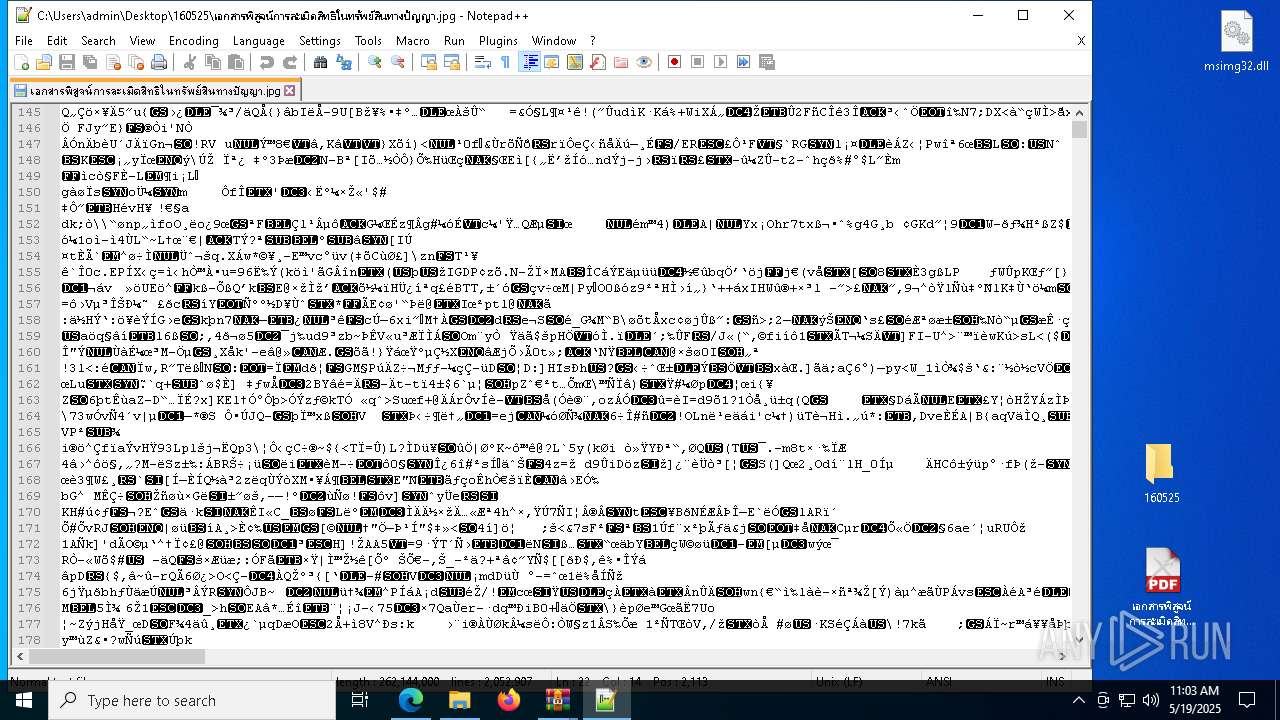
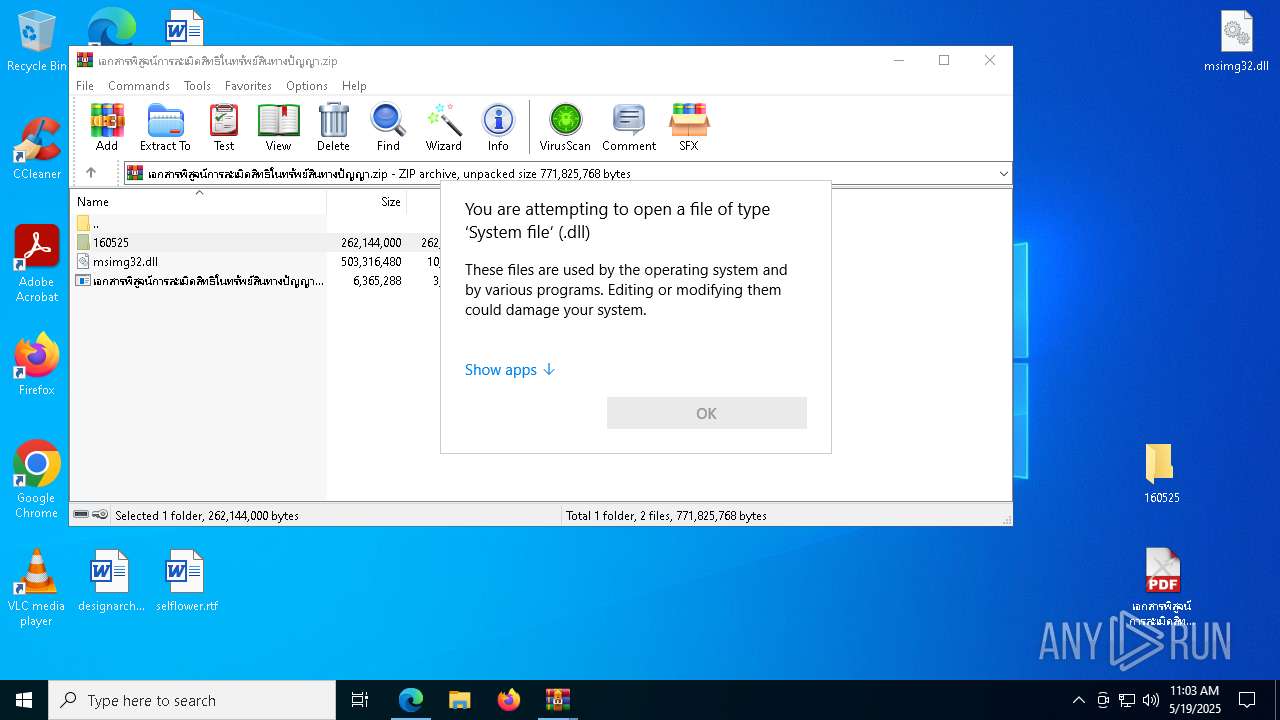
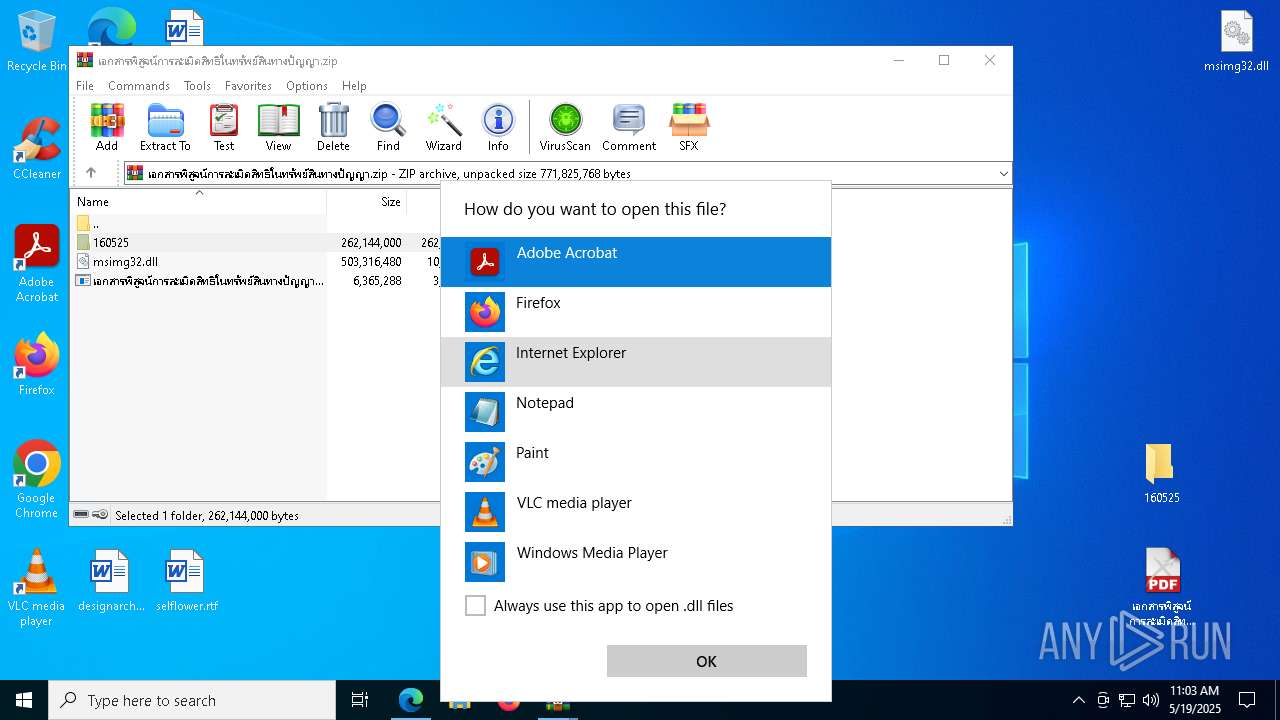
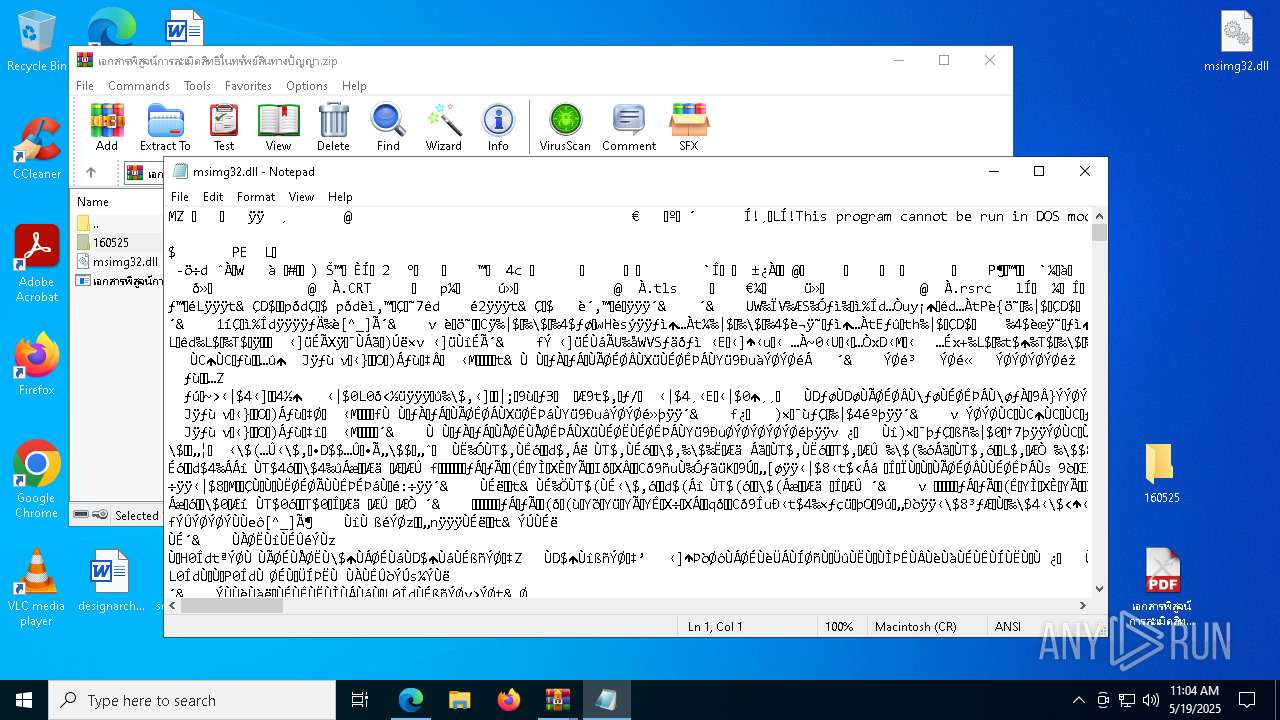
| 1616 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\msimg32.dll" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6204 --field-trial-handle=2400,i,15475794864431964164,1394710477752650637,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
22 916
Read events
22 770
Write events
143
Delete events
3
Modification events
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF229B5411942F00 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6279A35411942F00 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {47ECEAD2-A6C2-451E-BF93-F9E94BC9FA9E} | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4C846DBC-3869-4A3D-AE66-A3AEC52521D3} | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C73F8D53-C356-4ADE-AFC0-9A88A018C556} | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5ABB04BF-D48A-406B-8963-09655011090A} | |||
Executable files
30
Suspicious files
521
Text files
190
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b548.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
147
DNS requests
175
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747705071&P2=404&P3=2&P4=XY3Pude%2fVGOjF2SJgY8xGF%2bAUqFfqQm5wEfPAcNCvQY%2bHNQ325lhxFtFo%2bfDYNF2OoeBsYLySyOOycTfletXiQ%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705072&P2=404&P3=2&P4=FbVVenyoCvfFbr%2bg0%2fsoNyRNo811Deu8YhyofLXkdDra%2bAKKUncExGuCItaNTSU1P7a%2bm2TwwSdEYq%2bmetCeNw%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705072&P2=404&P3=2&P4=FbVVenyoCvfFbr%2bg0%2fsoNyRNo811Deu8YhyofLXkdDra%2bAKKUncExGuCItaNTSU1P7a%2bm2TwwSdEYq%2bmetCeNw%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747705071&P2=404&P3=2&P4=XY3Pude%2fVGOjF2SJgY8xGF%2bAUqFfqQm5wEfPAcNCvQY%2bHNQ325lhxFtFo%2bfDYNF2OoeBsYLySyOOycTfletXiQ%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705072&P2=404&P3=2&P4=FbVVenyoCvfFbr%2bg0%2fsoNyRNo811Deu8YhyofLXkdDra%2bAKKUncExGuCItaNTSU1P7a%2bm2TwwSdEYq%2bmetCeNw%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705072&P2=404&P3=2&P4=FbVVenyoCvfFbr%2bg0%2fsoNyRNo811Deu8YhyofLXkdDra%2bAKKUncExGuCItaNTSU1P7a%2bm2TwwSdEYq%2bmetCeNw%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705072&P2=404&P3=2&P4=FbVVenyoCvfFbr%2bg0%2fsoNyRNo811Deu8YhyofLXkdDra%2bAKKUncExGuCItaNTSU1P7a%2bm2TwwSdEYq%2bmetCeNw%3d%3d | unknown | — | — | whitelisted |
8052 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705072&P2=404&P3=2&P4=FbVVenyoCvfFbr%2bg0%2fsoNyRNo811Deu8YhyofLXkdDra%2bAKKUncExGuCItaNTSU1P7a%2bm2TwwSdEYq%2bmetCeNw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6068 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7252 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7252 | msedge.exe | 104.17.150.117:443 | www.mediafire.com | — | — | whitelisted |
6652 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
static.mediafire.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7252 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7252 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7252 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7252 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7252 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7252 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7252 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7252 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7252 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7252 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |