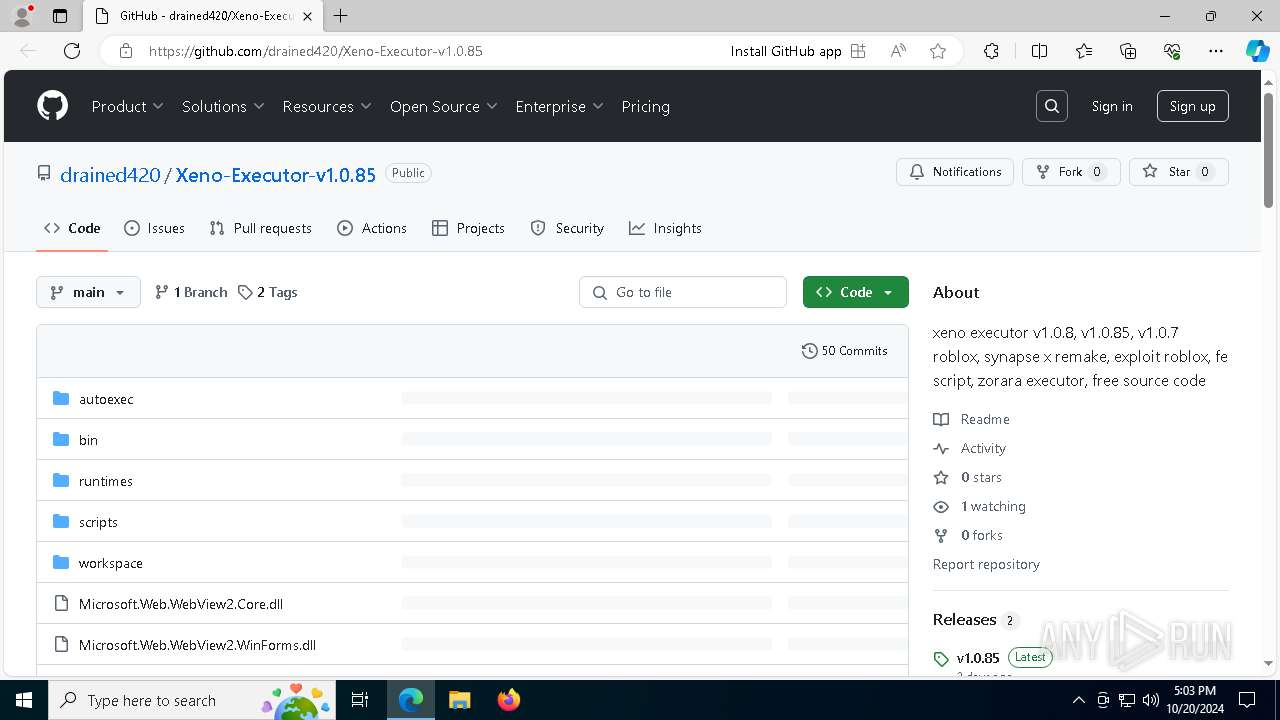
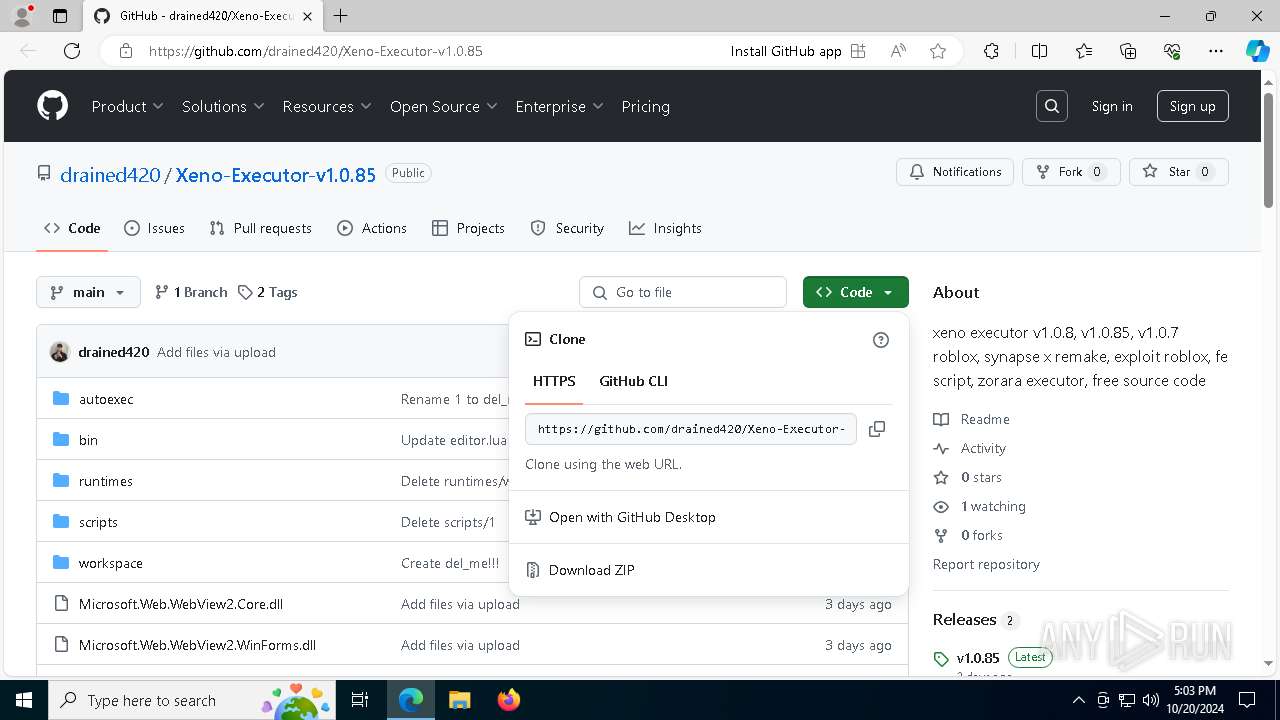
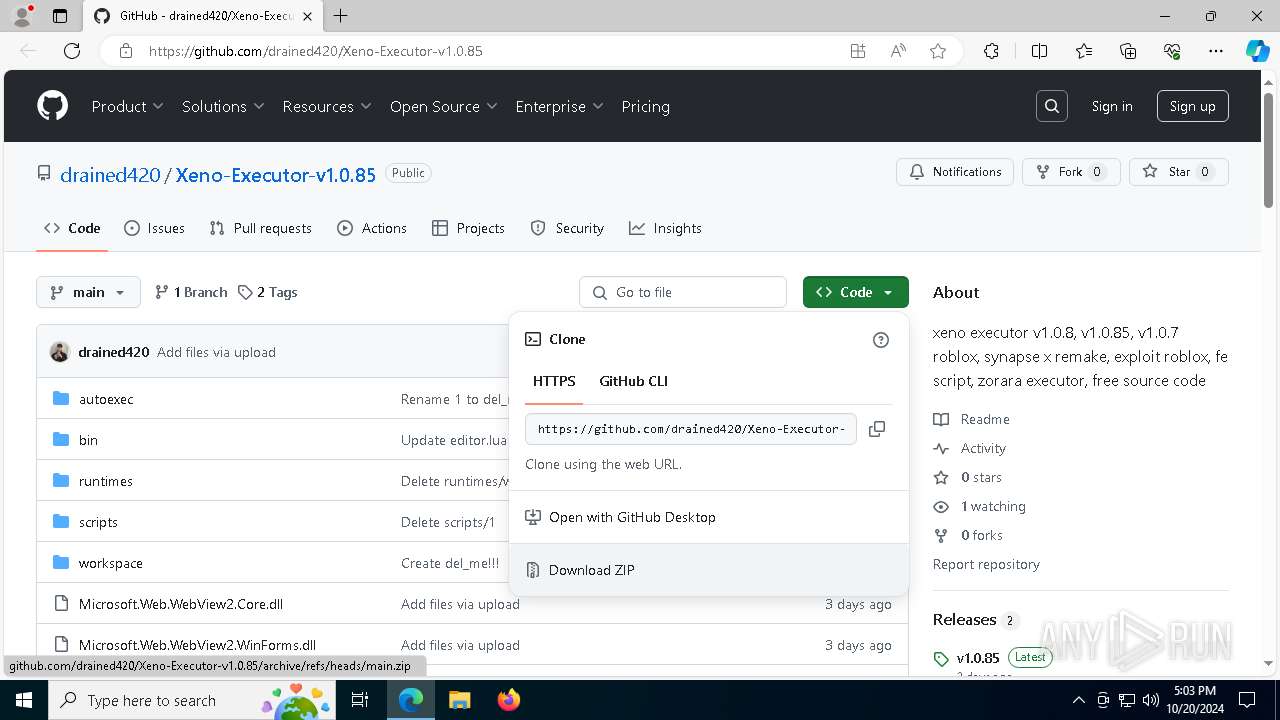
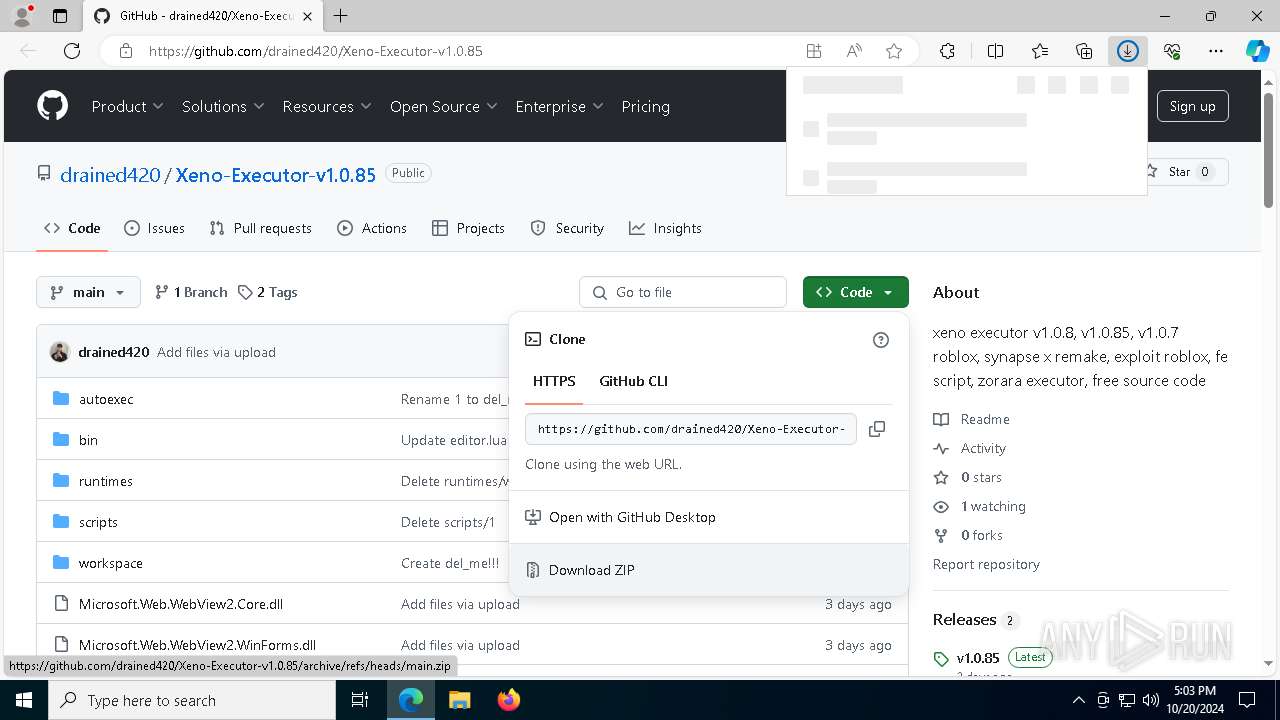
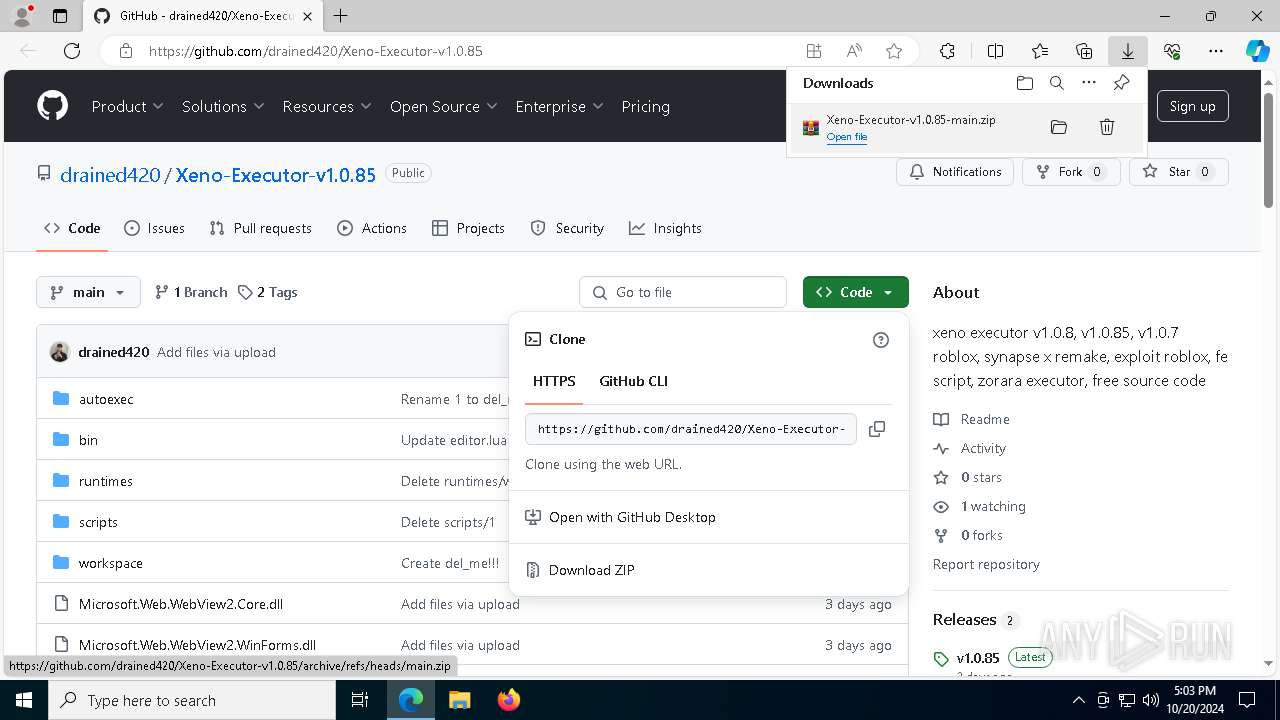
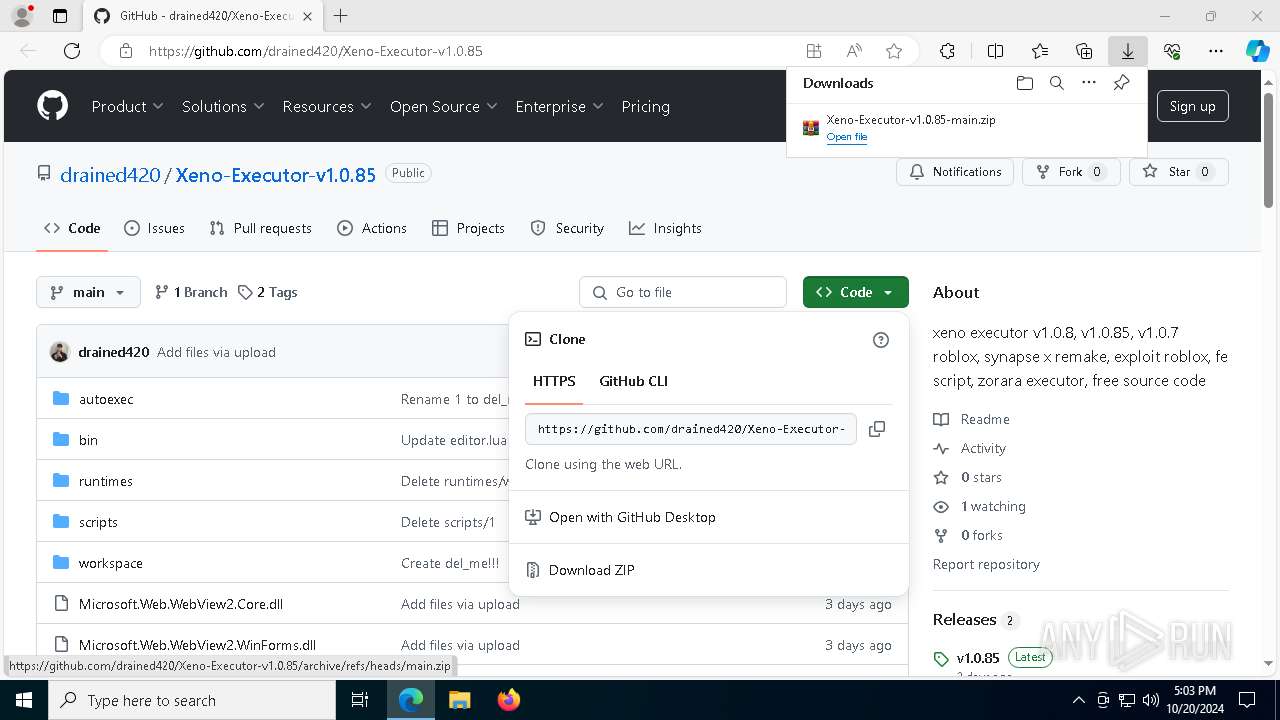
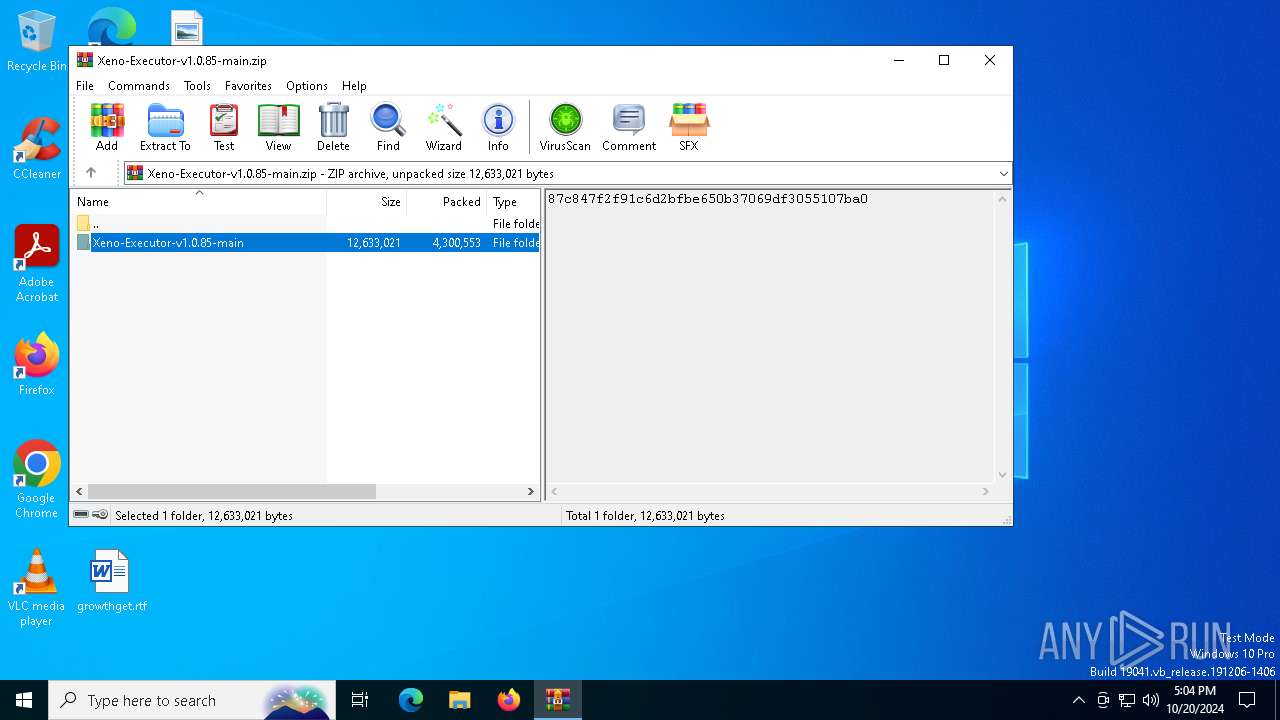
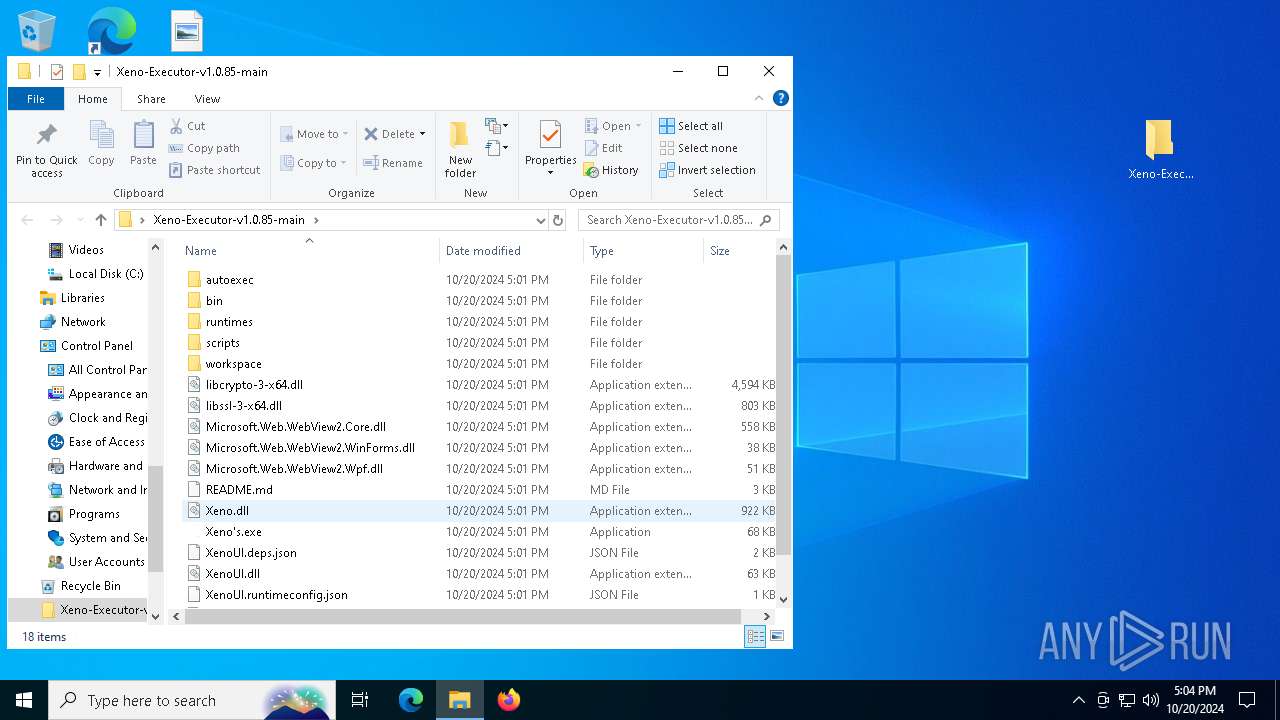
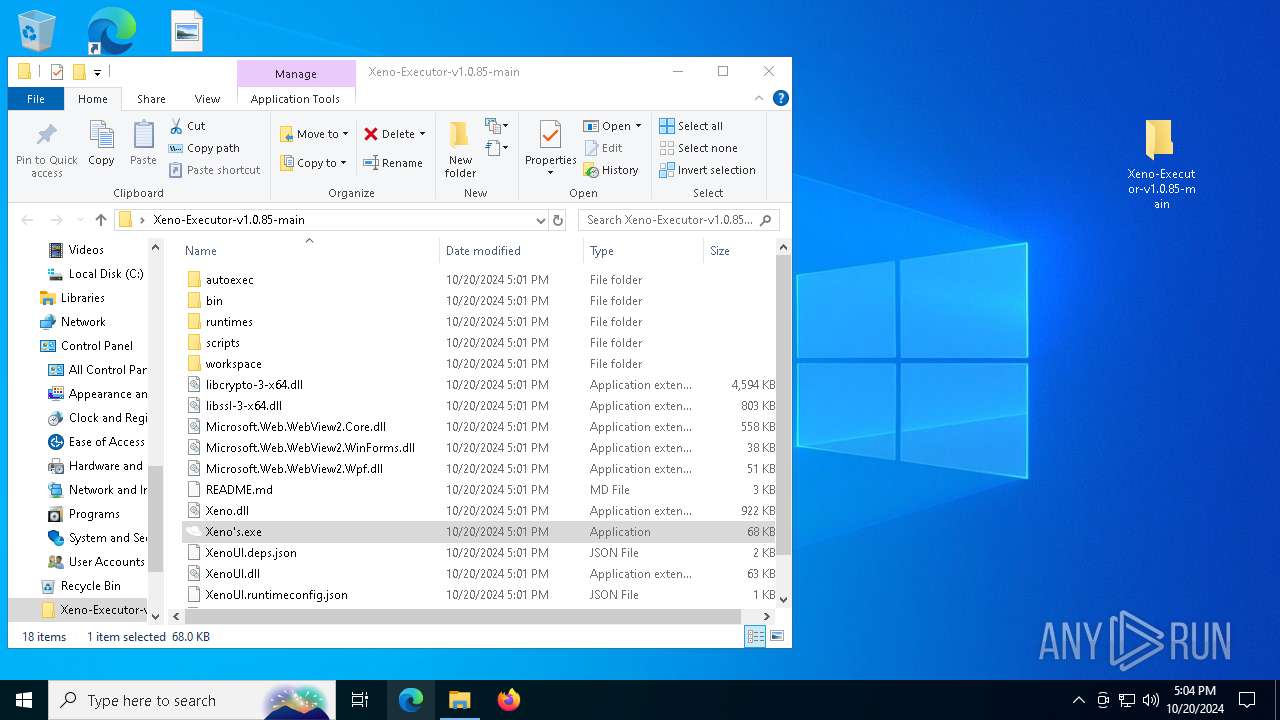
| URL: | https://github.com/drained420/Xeno-Executor-v1.0.85 |
| Full analysis: | https://app.any.run/tasks/d6f88607-dace-4fb0-8230-7b7163bbcf0c |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | October 20, 2024, 17:03:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C121D9B93EE5A51DEBB296CE7421BFD6 |
| SHA1: | 884D0322EB886B2BE148E6D64A536E15BD91A69E |
| SHA256: | CD7C6D368F3AC2373557BAF049E395169309BB83F27344A7B45670049144F34F |
| SSDEEP: | 3:N8tEdxX2xVOIgFQs+MQn:2uf0LR |
MALICIOUS
Changes the autorun value in the registry
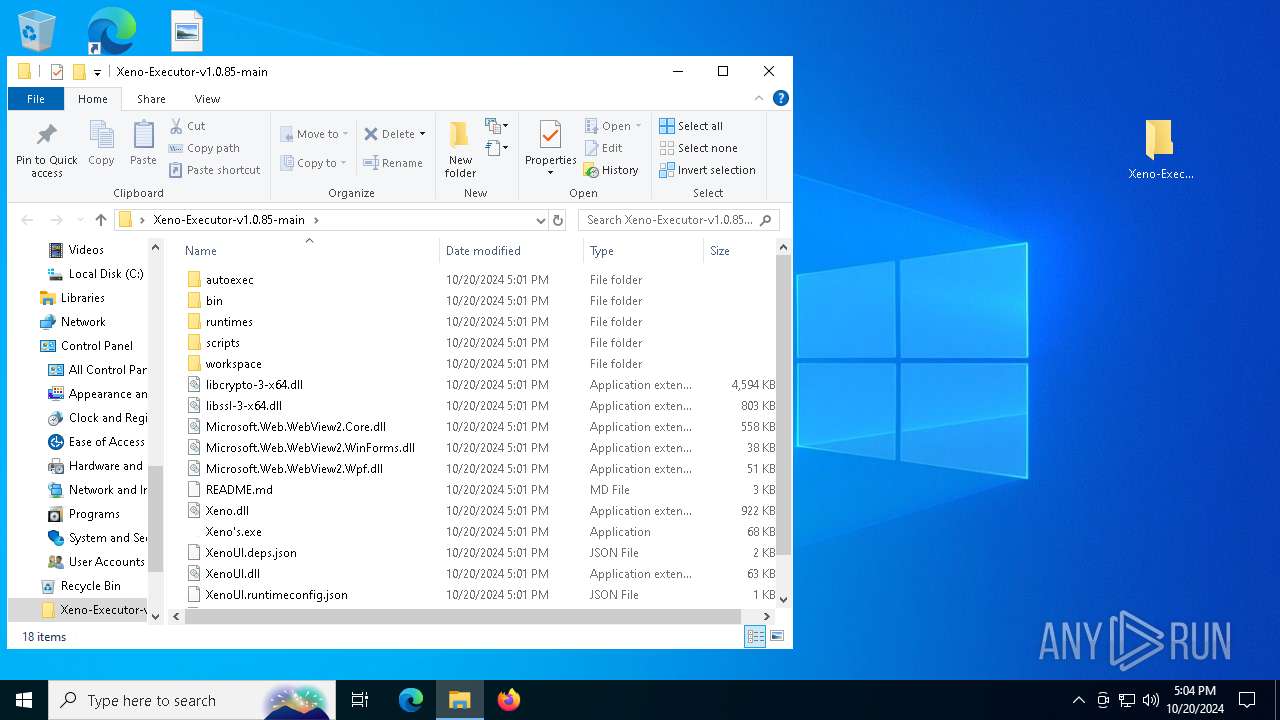
- Xeno's.exe (PID: 5100)
ASYNCRAT has been detected (YARA)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
ASYNCRAT has been detected (SURICATA)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Actions looks like stealing of personal data
- Xeno's.exe (PID: 3020)
Steals credentials from Web Browsers
- Xeno's.exe (PID: 3020)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 6704)
- msedge.exe (PID: 6276)
- WinRAR.exe (PID: 7964)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7108)
- cmd.exe (PID: 4380)
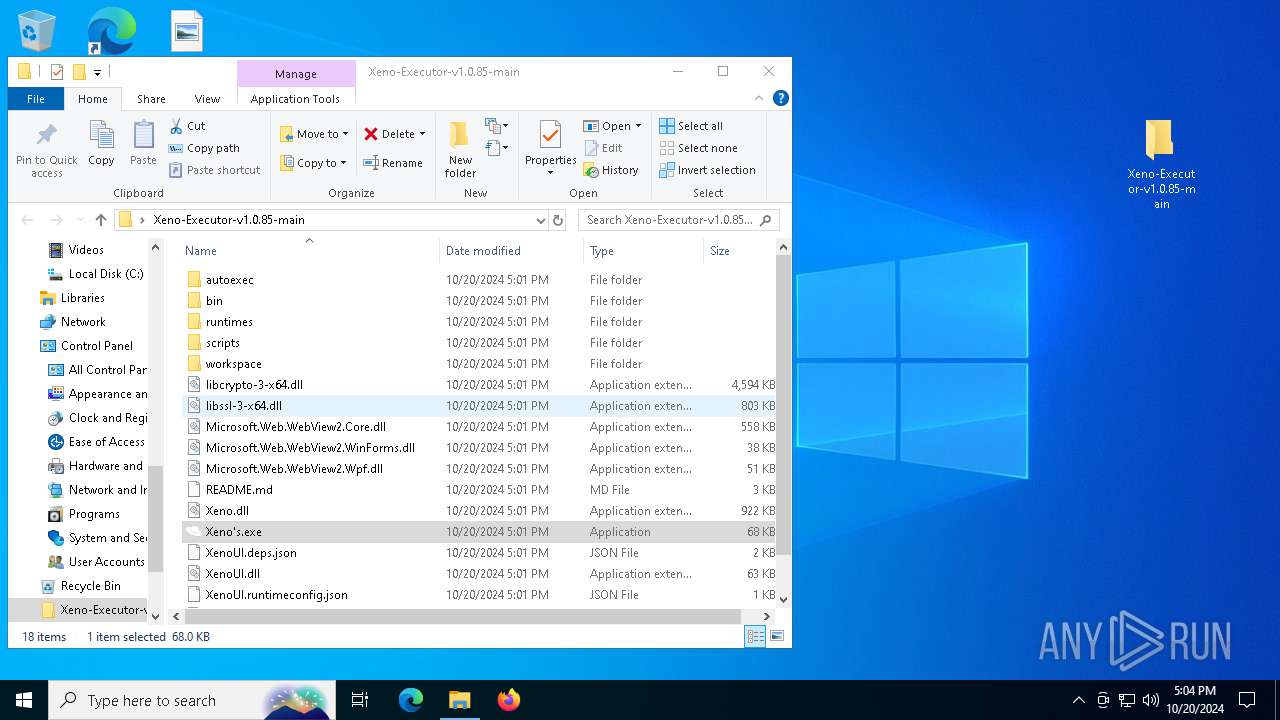
Executable content was dropped or overwritten
- Xeno's.exe (PID: 5100)
Contacting a server suspected of hosting an CnC
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
The executable file from the user directory is run by the CMD process
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Starts CMD.EXE for commands execution
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Connects to unusual port
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Reads security settings of Internet Explorer
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Reads the date of Windows installation
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Executing commands from a ".bat" file
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3020)
Loads DLL from Mozilla Firefox
- Xeno's.exe (PID: 3020)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 8000)
- cmd.exe (PID: 6892)
Starts application with an unusual extension
- cmd.exe (PID: 6892)
- cmd.exe (PID: 8000)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6892)
Checks for external IP
- svchost.exe (PID: 2172)
- Xeno's.exe (PID: 3020)
Potential Corporate Privacy Violation
- Xeno's.exe (PID: 3020)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 3744)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 612)
- msedge.exe (PID: 6704)
- msedge.exe (PID: 7684)
- WinRAR.exe (PID: 7964)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Application launched itself
- msedge.exe (PID: 6704)
- msedge.exe (PID: 7308)
Checks supported languages
- identity_helper.exe (PID: 7108)
- identity_helper.exe (PID: 6848)
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
- chcp.com (PID: 7816)
- chcp.com (PID: 7748)
Reads Environment values
- identity_helper.exe (PID: 7108)
- identity_helper.exe (PID: 6848)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Reads the computer name
- identity_helper.exe (PID: 7108)
- identity_helper.exe (PID: 6848)
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6704)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7964)
- msedge.exe (PID: 1196)
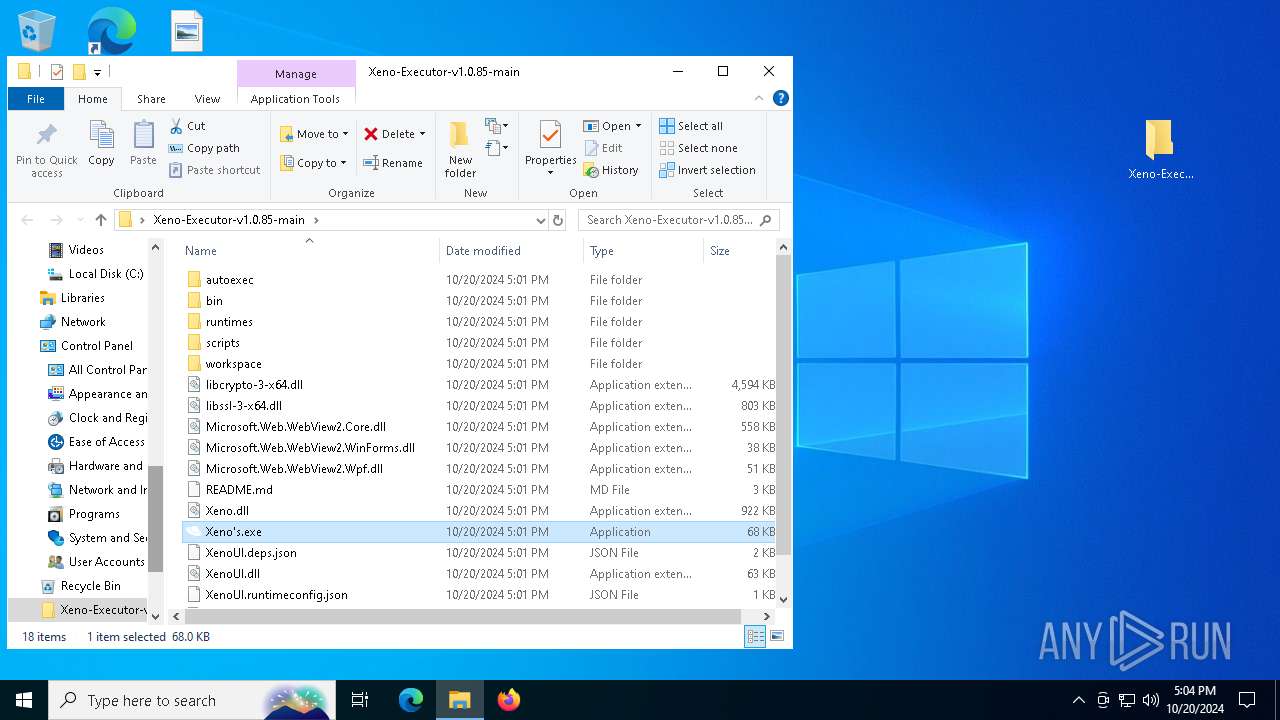
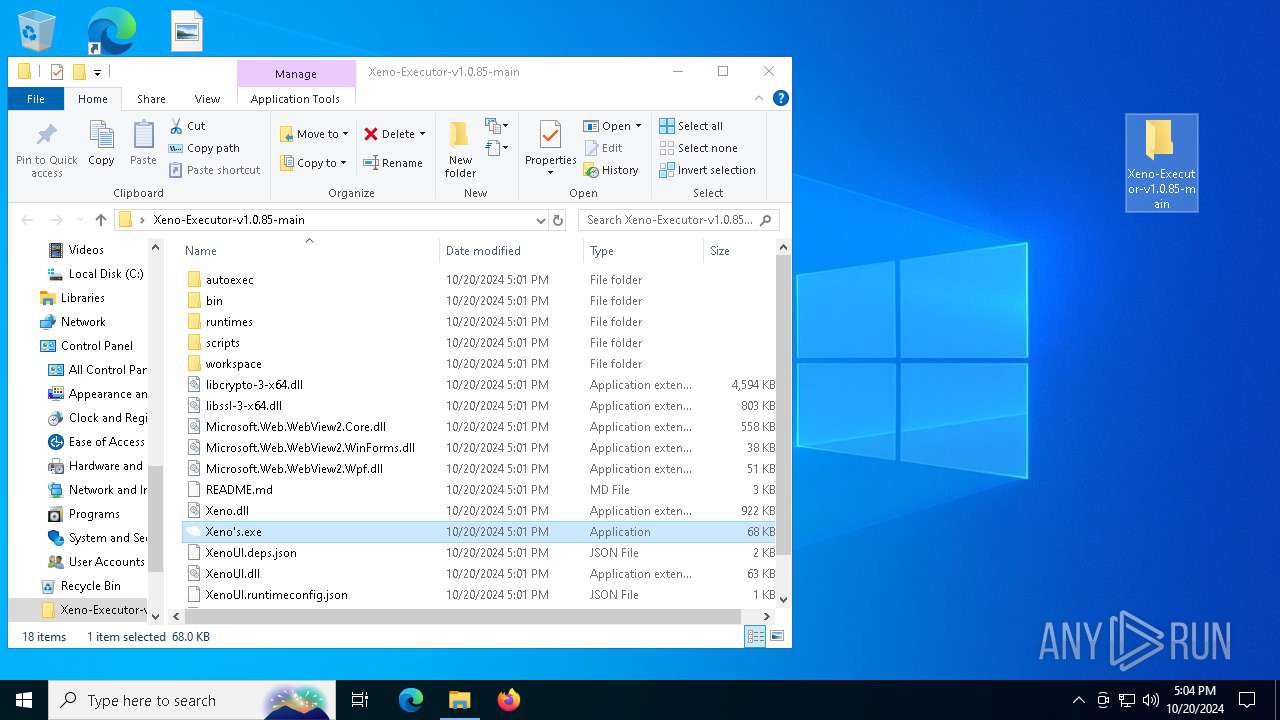
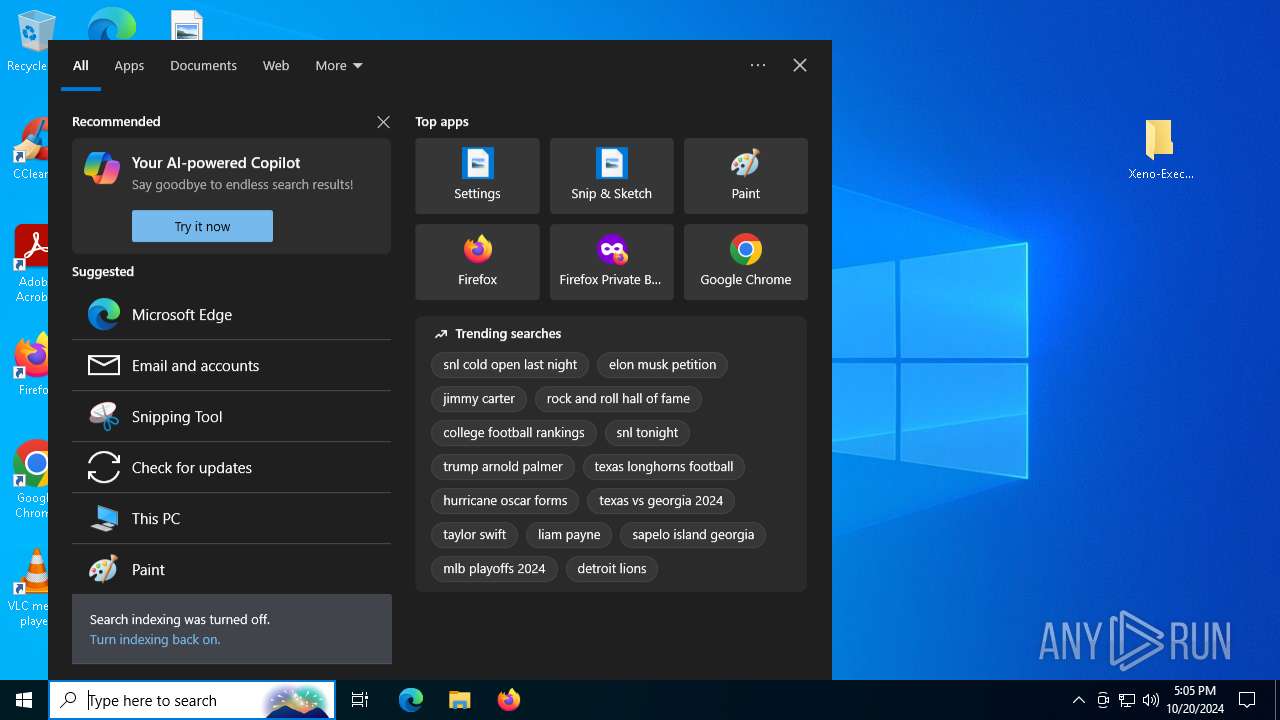
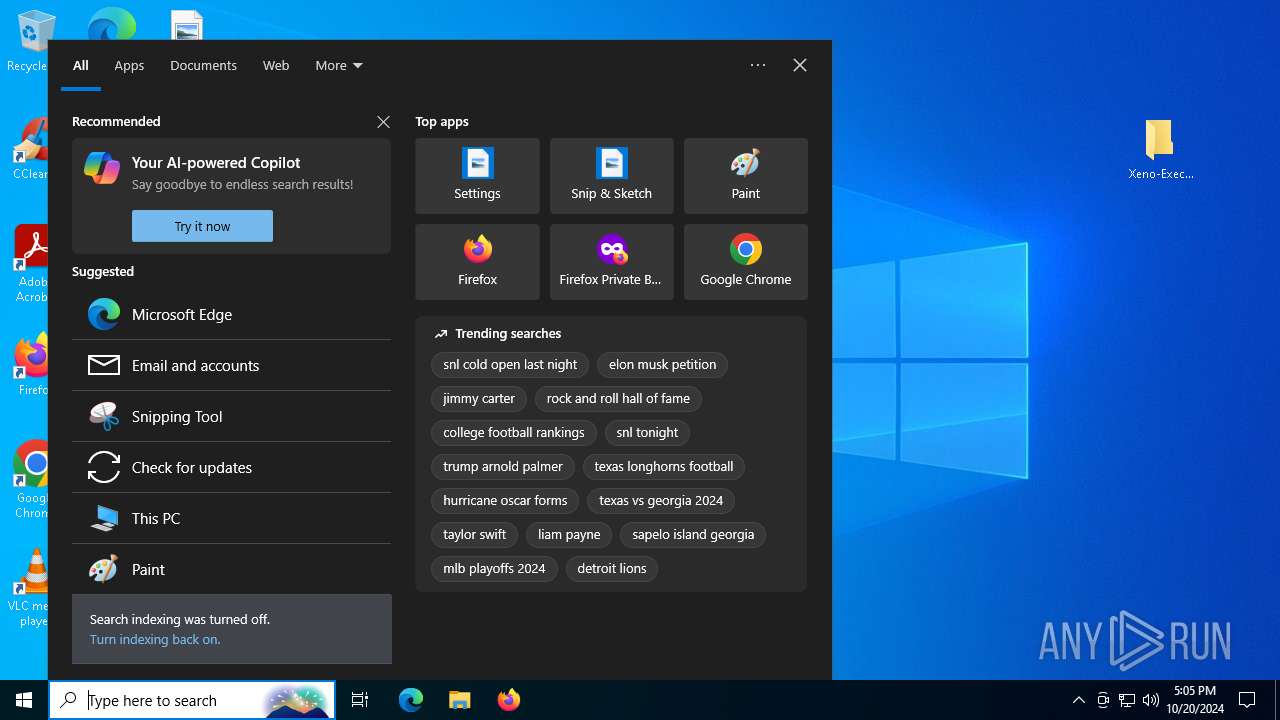
Manual execution by a user
- Xeno's.exe (PID: 5100)
Reads the machine GUID from the registry
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Create files in a temporary directory
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3020)
Creates files or folders in the user directory
- Xeno's.exe (PID: 5100)
- Xeno's.exe (PID: 3020)
Reads the software policy settings
- Xeno's.exe (PID: 3844)
- slui.exe (PID: 7376)
- slui.exe (PID: 8668)
- Xeno's.exe (PID: 3020)
Process checks computer location settings
- Xeno's.exe (PID: 3844)
- Xeno's.exe (PID: 3020)
Changes the display of characters in the console
- cmd.exe (PID: 6892)
- cmd.exe (PID: 8000)
Checks proxy server information
- slui.exe (PID: 8668)
- Xeno's.exe (PID: 3020)
Reads CPU info
- Xeno's.exe (PID: 3020)
Disables trace logs
- Xeno's.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3844) Xeno's.exe
C2 (1)like-minute.gl.at.ply.gg
Ports (1)57419
Version
Options
AutoRuntrue
MutexD0qZ杰HFVω0STaH诶pu弗Ζx诶U比e
InstallFolder%AppData%
Certificates
Cert1MIICKTCCAZKgAwIBAgIVAPb8BgnbpUe6h+g9fjCNjz1/UQj5MA0GCSqGSIb3DQEBDQUAMF0xDjAMBgNVBAMMBUVCT0xBMRMwEQYDVQQLDApxd3FkYW5jaHVuMRwwGgYDVQQKDBNEY1JhdCBCeSBxd3FkYW5jaHVuMQswCQYDVQQHDAJTSDELMAkGA1UEBhMCQ04wHhcNMjQwMTA5MTYyNjU3WhcNMzQxMDE4MTYyNjU3WjAQMQ4wDAYDVQQDDAVEY1JhdDCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEA...
Server_SignatureK+vELPYGuYw0JiF5aMpRxenETDRcLPDjqoLKwrncvJsDxs+OpHFlultUAjWBNF+v+II6LA9X93UnK3fdoQsMAWwKAIpND9qGhaZ0INp7zFBlWC0lq6PbSBmk3RRnGSmrKSYqZ/FfluqQReZnWWwwAxD5GDnAU4FsoL3UcumpUXE=
Keys
AES31fdd549983357cbac668fee4b85fc465d39262540fe481e7138e5d8084c6c88
SaltDcRatByqwqdanchun
(PID) Process(3020) Xeno's.exe
C2 (1)like-minute.gl.at.ply.gg
Ports (1)57419
Version
Options
AutoRuntrue
MutexD0qZ杰HFVω0STaH诶pu弗Ζx诶U比e
InstallFolder%AppData%
Certificates
Cert1MIICKTCCAZKgAwIBAgIVAPb8BgnbpUe6h+g9fjCNjz1/UQj5MA0GCSqGSIb3DQEBDQUAMF0xDjAMBgNVBAMMBUVCT0xBMRMwEQYDVQQLDApxd3FkYW5jaHVuMRwwGgYDVQQKDBNEY1JhdCBCeSBxd3FkYW5jaHVuMQswCQYDVQQHDAJTSDELMAkGA1UEBhMCQ04wHhcNMjQwMTA5MTYyNjU3WhcNMzQxMDE4MTYyNjU3WjAQMQ4wDAYDVQQDDAVEY1JhdDCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEA...
Server_SignatureK+vELPYGuYw0JiF5aMpRxenETDRcLPDjqoLKwrncvJsDxs+OpHFlultUAjWBNF+v+II6LA9X93UnK3fdoQsMAWwKAIpND9qGhaZ0INp7zFBlWC0lq6PbSBmk3RRnGSmrKSYqZ/FfluqQReZnWWwwAxD5GDnAU4FsoL3UcumpUXE=
Keys
AES31fdd549983357cbac668fee4b85fc465d39262540fe481e7138e5d8084c6c88
SaltDcRatByqwqdanchun
Total processes
236
Monitored processes
98
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/drained420/Xeno-Executor-v1.0.85" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x290,0x2a4,0x7ffbc23e5fd8,0x7ffbc23e5fe4,0x7ffbc23e5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 948 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4048 --field-trial-handle=2580,i,1618946444824556881,10866225897104655967,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5248 --field-trial-handle=2580,i,1618946444824556881,10866225897104655967,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5652 --field-trial-handle=2464,i,5069934521638999407,14616834256476148580,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4676 --field-trial-handle=2580,i,1618946444824556881,10866225897104655967,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3624 --field-trial-handle=2580,i,1618946444824556881,10866225897104655967,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6056 --field-trial-handle=2580,i,1618946444824556881,10866225897104655967,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5224 --field-trial-handle=2464,i,5069934521638999407,14616834256476148580,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
26 406
Read events
26 337
Write events
68
Delete events
1
Modification events
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (612) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6704) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6704) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6704) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6704) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
22
Suspicious files
586
Text files
209
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b53f.TMP | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b53f.TMP | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b54f.TMP | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b54f.TMP | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b53f.TMP | — | |
MD5:— | SHA256:— | |||
| 6704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
148
DNS requests
104
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5084 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1729772800&P2=404&P3=2&P4=fmbWXUVve7KZsDx%2by1UYLABKfFObj2h5%2b0VKyt410%2bHMaRMN4sEIouD12PQqB4EPnBQ18K0QKcU3dWCtELeYRA%3d%3d | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1729772800&P2=404&P3=2&P4=fmbWXUVve7KZsDx%2by1UYLABKfFObj2h5%2b0VKyt410%2bHMaRMN4sEIouD12PQqB4EPnBQ18K0QKcU3dWCtELeYRA%3d%3d | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1729772800&P2=404&P3=2&P4=fmbWXUVve7KZsDx%2by1UYLABKfFObj2h5%2b0VKyt410%2bHMaRMN4sEIouD12PQqB4EPnBQ18K0QKcU3dWCtELeYRA%3d%3d | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1729772800&P2=404&P3=2&P4=fmbWXUVve7KZsDx%2by1UYLABKfFObj2h5%2b0VKyt410%2bHMaRMN4sEIouD12PQqB4EPnBQ18K0QKcU3dWCtELeYRA%3d%3d | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1729772800&P2=404&P3=2&P4=fmbWXUVve7KZsDx%2by1UYLABKfFObj2h5%2b0VKyt410%2bHMaRMN4sEIouD12PQqB4EPnBQ18K0QKcU3dWCtELeYRA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6276 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6704 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6276 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6276 | msedge.exe | 185.199.108.133:443 | avatars.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3844 | Xeno's.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2172 | svchost.exe | Misc activity | ET INFO Tunneling Service in DNS Lookup (* .ply .gg) |
3844 | Xeno's.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
3020 | Xeno's.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
3020 | Xeno's.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
3020 | Xeno's.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
3020 | Xeno's.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6 ETPRO signatures available at the full report