| File name: | Eclipse.exe |
| Full analysis: | https://app.any.run/tasks/5c6701c7-a3ab-4789-987b-3db99d98f143 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | April 05, 2024, 06:17:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 8FB7A6BD32200AEA3F517923285E39A8 |
| SHA1: | DC5C1E8293CCE5D82C5D7D338FB3CEE57D2B997D |
| SHA256: | CCC95AFA02727297EB7F6BBBE5E06D011CE4656C3B563E2841FAD60D471E2F26 |
| SSDEEP: | 384:20Fjyor85Z6coSQJ14p9FJoujEaCLyg+CMH/VCfBI473IvJVUFX1IaZBjQj4osii:fa5ZRo34pB3xfApIzTzjYR+ZhW |
MALICIOUS
Drops the executable file immediately after the start
- Eclipse.exe (PID: 3392)
- powershell.exe (PID: 2408)
RHADAMANTHYS has been detected (SURICATA)
- dialer.exe (PID: 1236)
Actions looks like stealing of personal data
- dialer.exe (PID: 1236)
SUSPICIOUS
Reads the Internet Settings
- Eclipse.exe (PID: 3392)
- powershell.exe (PID: 2408)
- cmd.exe (PID: 1556)
BASE64 encoded PowerShell command has been detected
- Eclipse.exe (PID: 3392)
Reads security settings of Internet Explorer
- Eclipse.exe (PID: 3392)
Base64-obfuscated command line is found
- Eclipse.exe (PID: 3392)
Starts POWERSHELL.EXE for commands execution
- Eclipse.exe (PID: 3392)
- powershell.exe (PID: 2408)
Application launched itself
- powershell.exe (PID: 2408)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2408)
The Powershell connects to the Internet
- powershell.exe (PID: 2408)
Unusual connection from system programs
- powershell.exe (PID: 2408)
The process checks if it is being run in the virtual environment
- dialer.exe (PID: 1236)
Connects to unusual port
- dialer.exe (PID: 1236)
Loads DLL from Mozilla Firefox
- dialer.exe (PID: 1236)
Reads browser cookies
- dialer.exe (PID: 1236)
Searches for installed software
- dialer.exe (PID: 1236)
Accesses Microsoft Outlook profiles
- dialer.exe (PID: 1236)
Executed via WMI
- olZ6z2(Pf2.exe (PID: 2888)
Executing commands from a ".bat" file
- olZ6z2(Pf2.exe (PID: 2888)
Starts CMD.EXE for commands execution
- olZ6z2(Pf2.exe (PID: 2888)
INFO
Reads the computer name
- Eclipse.exe (PID: 3392)
Checks supported languages
- Eclipse.exe (PID: 3392)
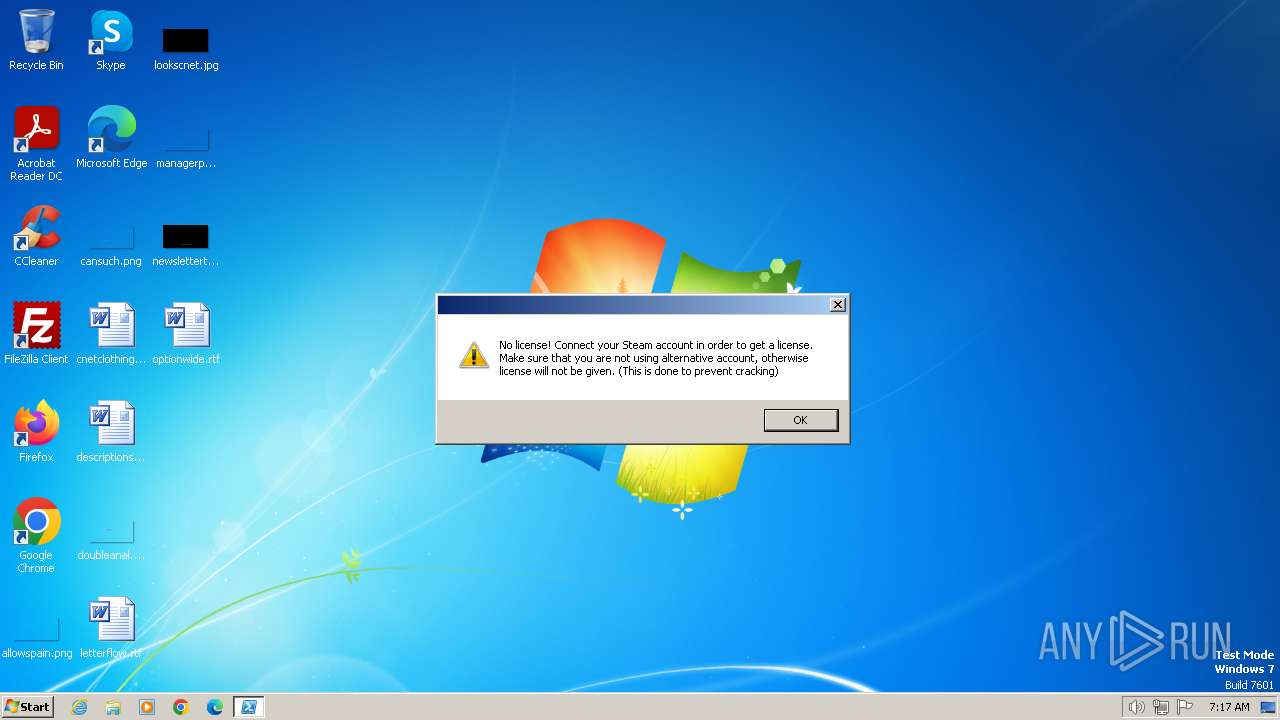
- liccheck.exe (PID: 2832)
- olZ6z2(Pf2.exe (PID: 2888)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2408)
The executable file from the user directory is run by the Powershell process
- liccheck.exe (PID: 2832)
Creates files or folders in the user directory
- dialer.exe (PID: 1236)
Create files in a temporary directory
- olZ6z2(Pf2.exe (PID: 2888)
Application launched itself
- msedge.exe (PID: 1772)
- msedge.exe (PID: 1780)
Drops the executable file immediately after the start
- dialer.exe (PID: 1236)
Manual execution by a user
- msedge.exe (PID: 1780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1024 |
| InitializedDataSize: | 74240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1159 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.16.1.0 |
| ProductVersionNumber: | 4.16.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Telegram FZ-LLC |
| FileTitle: | - |
| FileDescription: | Telegram Desktop |
| FileVersion: | 4,16,1,0 |
| LegalCopyright: | Copyright (C) 2014-2024 |
| LegalTrademark: | - |
| ProductName: | Telegram Desktop |
| ProductVersion: | 4,16,1,0 |
Total processes
69
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1480 --field-trial-handle=1336,i,17166879336548728689,5072211971796328615,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1236 | "C:\Windows\system32\dialer.exe" | C:\Windows\System32\dialer.exe | liccheck.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Phone Dialer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1160 --field-trial-handle=1328,i,14774596087287723812,16209244250088865740,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1556 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\A8BE.tmp\A8BF.tmp\A8C0.bat C:\Users\admin\AppData\Local\Microsoft\olZ6z2(Pf2.exe" | C:\Windows\System32\cmd.exe | — | olZ6z2(Pf2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1256 --field-trial-handle=1336,i,17166879336548728689,5072211971796328615,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
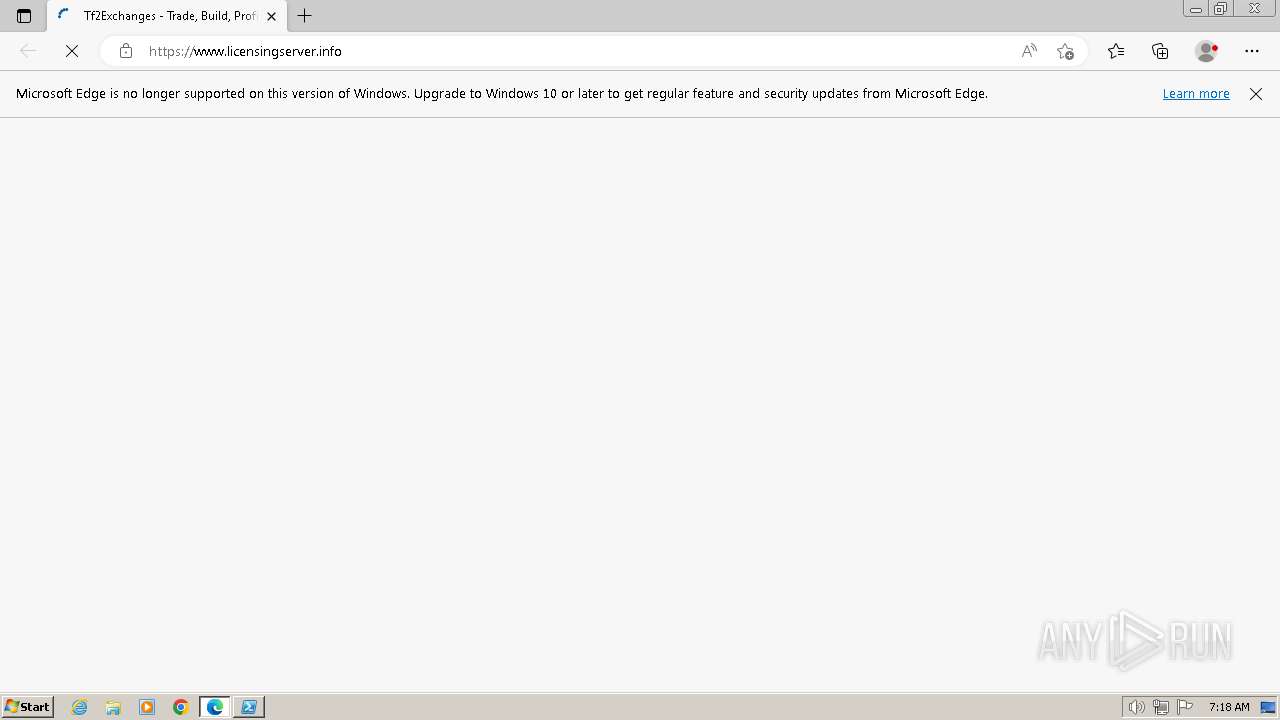
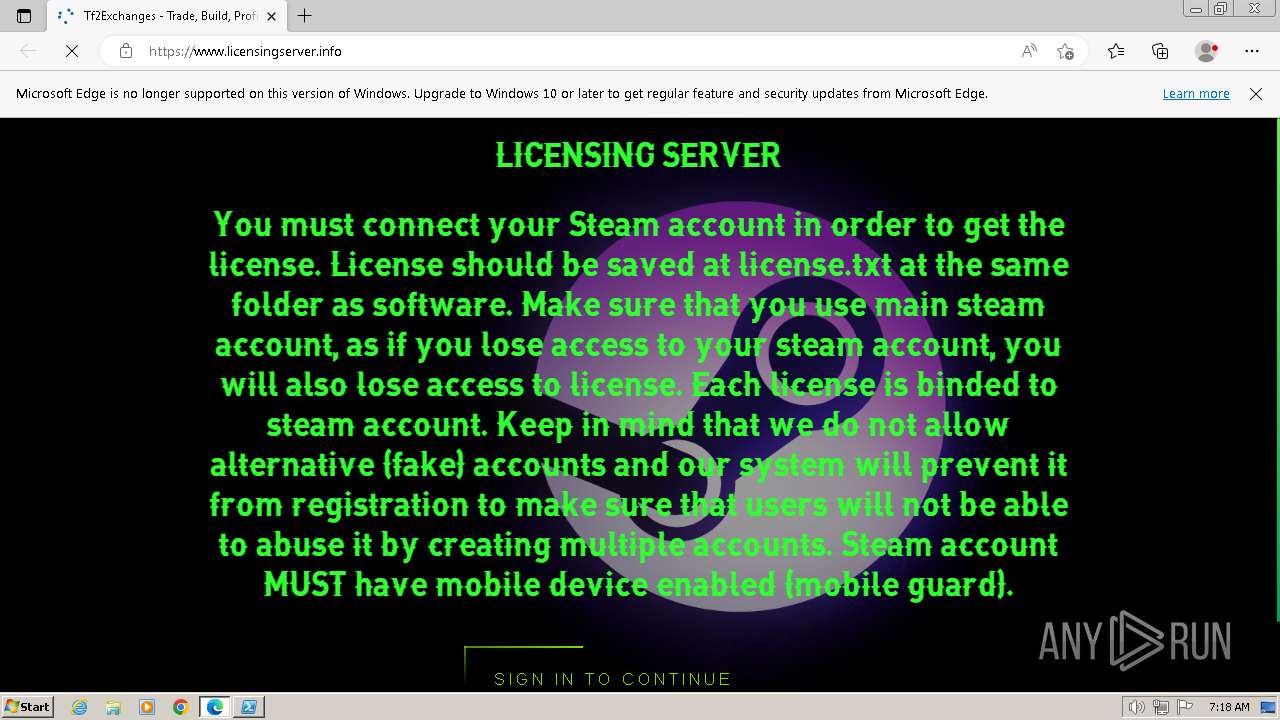
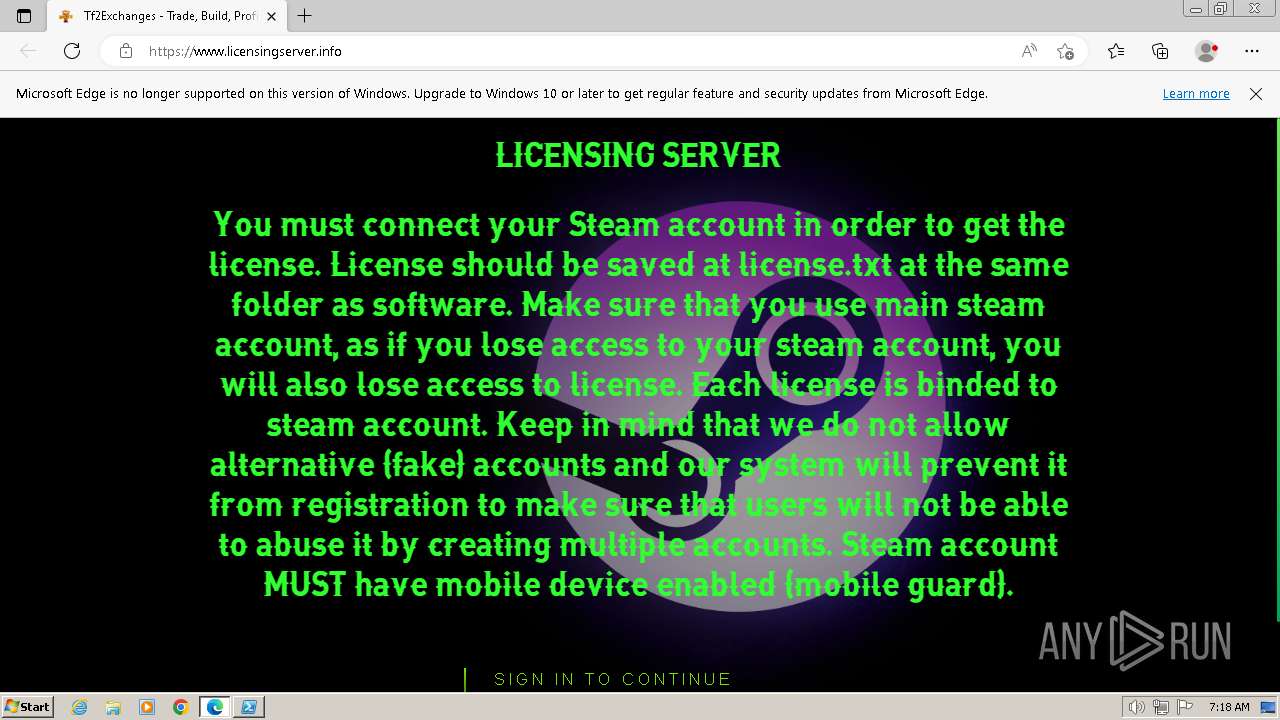
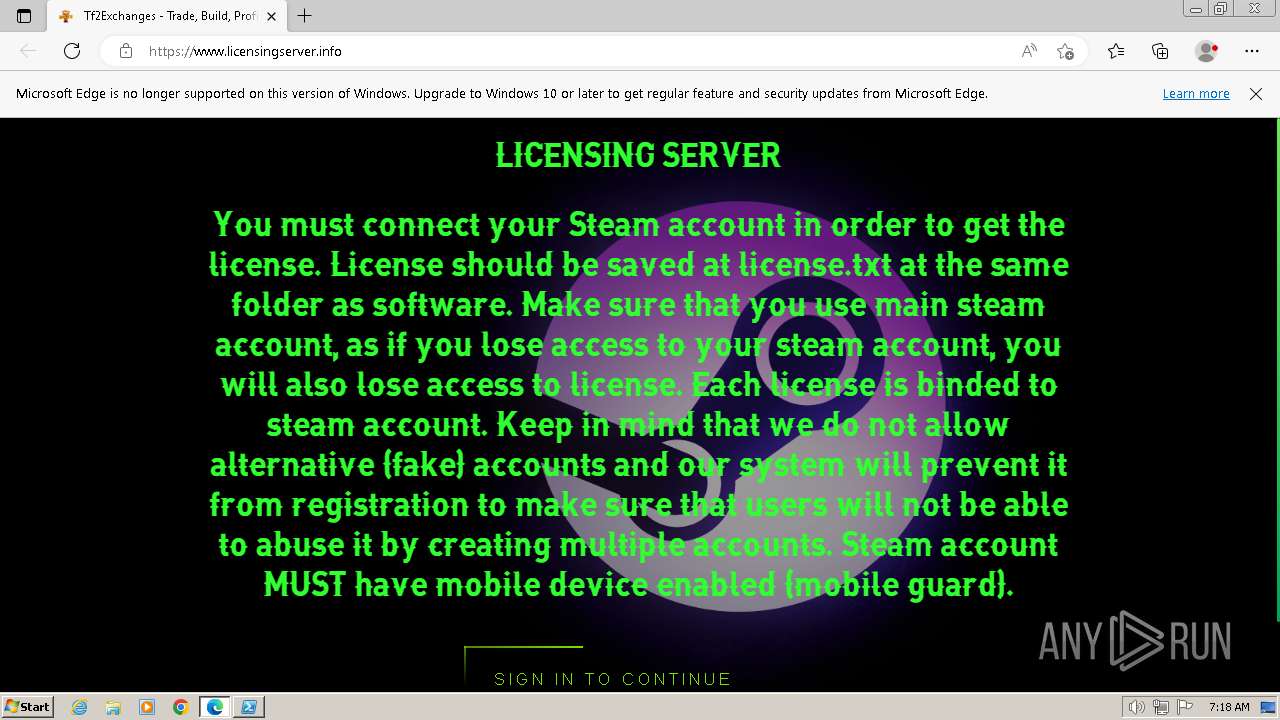
| 1772 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.licensingserver.info/ | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate https://www.licensingserver.info/ | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2024 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2292 --field-trial-handle=1336,i,17166879336548728689,5072211971796328615,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3996 --field-trial-handle=1336,i,17166879336548728689,5072211971796328615,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4080 --field-trial-handle=1336,i,17166879336548728689,5072211971796328615,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
15 950
Read events
15 863
Write events
77
Delete events
10
Modification events
| (PID) Process: | (3392) Eclipse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3392) Eclipse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3392) Eclipse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3392) Eclipse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
Executable files
5
Suspicious files
6
Text files
57
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\paquncle.0kv.ps1 | binary | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hz251obg.2kz.psm1 | binary | |
MD5:— | SHA256:— | |||
| 3724 | powershell.exe | C:\Users\admin\AppData\Local\Temp\c5pzippm.ve1.ps1 | binary | |
MD5:— | SHA256:— | |||
| 3724 | powershell.exe | C:\Users\admin\AppData\Local\Temp\l0a11qxp.y11.psm1 | binary | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Roaming\lic.exe | executable | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Roaming\liccheck.exe | executable | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Roaming\LicGet.exe | executable | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 3724 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 1236 | dialer.exe | C:\Users\admin\AppData\Local\Microsoft\olZ6z2(Pf2.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
33
DNS requests
27
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2408 | powershell.exe | 104.192.141.1:443 | bitbucket.org | AMAZON-02 | US | unknown |
1236 | dialer.exe | 185.125.50.38:3034 | — | — | RU | unknown |
1780 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
948 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
948 | msedge.exe | 104.21.50.91:443 | www.licensingserver.info | CLOUDFLARENET | — | unknown |
948 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
948 | msedge.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bitbucket.org |
| shared |
www.licensingserver.info |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
code.jquery.com |
| whitelisted |
i.imgur.com |
| shared |
community.cloudflare.steamstatic.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1236 | dialer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
948 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
6 ETPRO signatures available at the full report