| File name: | 91f2f0e91da80c7212ca01194c48dc34 |
| Full analysis: | https://app.any.run/tasks/f7b098bc-62b1-480d-8d2f-31a09fd415e9 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 18, 2019, 15:40:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 91F2F0E91DA80C7212CA01194C48DC34 |
| SHA1: | 3C587BAC4BCC86741DE8C0C3C5719A80314F188A |
| SHA256: | CCA97A95D828D0F8E59D2515A59141E364048516EB8DFF5A10BA110D6BCEEC34 |
| SSDEEP: | 12288:LSQQIaMhgGYVe/iuvZgQmY89vnF4ffJKCUMYpKpBTn9sKJ:LSQuMq7qgzRnGZrlY4/J |
MALICIOUS
AGENTTESLA was detected
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Changes the autorun value in the registry
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Changes settings of System certificates
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Actions looks like stealing of personal data
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
SUSPICIOUS
Application launched itself
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3692)
Reads the cookies of Mozilla Firefox
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Creates files in the user directory
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Executable content was dropped or overwritten
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Reads the cookies of Google Chrome
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Checks for external IP
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Adds / modifies Windows certificates
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Connects to SMTP port
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
INFO
Dropped object may contain Bitcoin addresses
- 91f2f0e91da80c7212ca01194c48dc34.exe (PID: 3824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (90.6) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:09:06 20:46:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 897024 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1478 |
| OSVersion: | 4 |
| ImageVersion: | 8.5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.5.0.5 |
| ProductVersionNumber: | 8.5.0.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | ConcertinosKANSAN6 |
| ProductName: | ConcertinosPACIFIABLE6 |
| FileVersion: | 8.05.0005 |
| ProductVersion: | 8.05.0005 |
| InternalName: | ConcertinosDemipomada4 |
| OriginalFileName: | ConcertinosDemipomada4.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Sep-2002 18:46:10 |
| Detected languages: |
|
| CompanyName: | ConcertinosKANSAN6 |
| ProductName: | ConcertinosPACIFIABLE6 |
| FileVersion: | 8.05.0005 |
| ProductVersion: | 8.05.0005 |
| InternalName: | ConcertinosDemipomada4 |
| OriginalFilename: | ConcertinosDemipomada4.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Sep-2002 18:46:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000DAE90 | 0x000DB000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95042 |
.data | 0x000DC000 | 0x00001AA8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000DE000 | 0x00009E38 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.98189 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30229 | 656 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 4.12428 | 5864 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 4.37148 | 1640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 4.67212 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30004 | 4.51807 | 488 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30005 | 5.74711 | 11432 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30006 | 6.00866 | 3752 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30007 | 6.18611 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30008 | 4.42552 | 1384 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30009 | 5.7376 | 7336 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
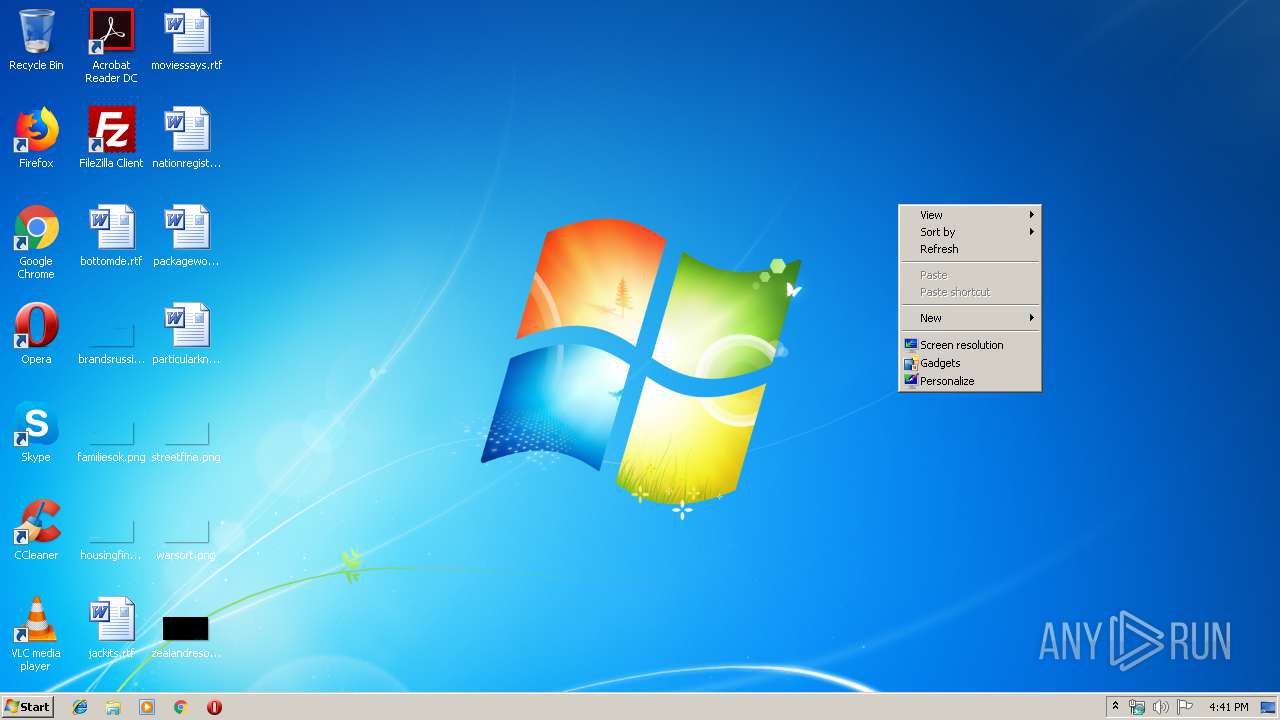
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3692 | "C:\Users\admin\AppData\Local\Temp\91f2f0e91da80c7212ca01194c48dc34.exe" | C:\Users\admin\AppData\Local\Temp\91f2f0e91da80c7212ca01194c48dc34.exe | — | explorer.exe | |||||||||||
User: admin Company: ConcertinosKANSAN6 Integrity Level: MEDIUM Exit code: 0 Version: 8.05.0005 Modules
| |||||||||||||||
| 3824 | "C:\Users\admin\AppData\Local\Temp\91f2f0e91da80c7212ca01194c48dc34.exe" | C:\Users\admin\AppData\Local\Temp\91f2f0e91da80c7212ca01194c48dc34.exe | 91f2f0e91da80c7212ca01194c48dc34.exe | ||||||||||||
User: admin Company: ConcertinosKANSAN6 Integrity Level: MEDIUM Exit code: 0 Version: 8.05.0005 Modules
| |||||||||||||||
Total events
89
Read events
59
Write events
29
Delete events
1
Modification events
| (PID) Process: | (3692) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Qp6eUFaOb2PPm1slPStXmx02l9KifB49\TvZJlG3T3dHBd9WSzHyvC69DGNEBzXT1i9s43iW9zRdBvkbTlTyTjo4rGARahv7FjdVGeMrMcpj9pYeIZGVnY2fGyZwDCujGs6acU2RWtgKVV1ot2wtBETXyRoqCzNK20 |
| Operation: | write | Name: | GpkrYsG55aGa24USYldK8GR9hwO72uvvK7FcsMqOdXMqzycHkLvfxT35QE2DVxfDhBRAgmEhl1kBzTcHqa4cMOoSaKBpioOwQhIhr5FEZK5n4Za1PZFhUk8DLdg5aXvjWA0V1SJ5GzRo5KoO1B59WmBxcuPlA8A98Sva1D9LYSpiF59ezr7rUP2KYW4PAQmdVB0GuhbNn5wLQTJs0UwPRCKpDZLbcY4DR9h6rH8nrAZqE95 |
Value: m98Sw5kwenv3zO7MVk8jPk9sahArwxgqNl86ajiJaQhj84w3LSb17f9cDOgzDLTESNC9wAlZ59 | |||
| (PID) Process: | (3692) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\NVktOn7W3WRJRc9SHcZ9LwDAA0HcBzp5173\uTbqi9wdIIEF6xsF8EHudWvm5f72HJYQpnTQnQEi7BImtbg2IPsoZdY1QFJGhnWlI1kkvDJLzzLkcYT9ifI4GVp2OJBPCYf4D01itaMymNj06yoW95ZV7IQjgDfTucWTutv837RxMpVMV195 |
| Operation: | write | Name: | CeWBTab3oox7US8oirEv9vNdOnOBAvjD7fmW9FPJuHTe8AY2QrKWIdsZfLxHtkrzr3FQT09CffMWNciu9nieX9CtO2TavWnkuV1TuZPIAjoNixKO174 |
Value: xRknIpDIcNhGQ65 | |||
| (PID) Process: | (3692) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\fXXKsMrPXmEwcYc2mwA163\CsbtyczAB529j6PvoBeLnGkSeSKUu9TIv6lGTnrPmqcbInsg8lf2BNuRPhMU7pFHI27 |
| Operation: | write | Name: | Gc5zjqiyTsb8EQcLRbDuUwkuS1TO8QVqmgGsI4NIlettZLIs2R09Ej1eg7Nqhr1v0CDvSHAhSZ2fjYyrEtOJPYkmGmyJCJhnyy6fc6kfp12X0ioHBieLSjUV30kfxvl3Tmfd43EFQCCavtQjNDoNc4pYhmhwsxSAWidXWlfz52WociBhaKtmc4vvgGx5MBw0AEaYaJKZ2zbavzjDAVBYh3PzUfhrUvXkLIhOc1PXBvs0O2DrZrXbQQ4b7mEaf0PAmKG0pZ7uH7YtxwdGfzHvibQoOiOK123 |
Value: PYkvevKtZw4DfDgJejK1iqGFq8r0QTrnPQ72YkdltLgfPKoWJhjTatyWPg5RLzYZhBrc2o88tHDAq2ei40UQ0REPDqVpR1uWYVlUIT2eLZdAlFjc26BN5LuKCfZzonvDFtP5hYr39h18PN83pfpEHjB5AqieFOxu9143 | |||
| (PID) Process: | (3692) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\vIS4DKuICgCnBFKja83rOixo1J132\GDzjD6CnaJJjIktOn7W3WRJRc9SHcZ9LwDAA0HcBzp5126 |
| Operation: | write | Name: | uTbqi9120 |
Value: CeWBTab3oox7US8oirEv9vNdOnOBAvjD7fmW9FPJuHTe8AY2QrKWIdsZfLxHtkrzr3FQT09CffMX9Ct251 | |||
| (PID) Process: | (3824) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NewApp |
Value: C:\Users\admin\AppData\Roaming\NewApp\NewApp.exe | |||
| (PID) Process: | (3824) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\91f2f0e91da80c7212ca01194c48dc34_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3824) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\91f2f0e91da80c7212ca01194c48dc34_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3824) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\91f2f0e91da80c7212ca01194c48dc34_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3824) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\91f2f0e91da80c7212ca01194c48dc34_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3824) 91f2f0e91da80c7212ca01194c48dc34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\91f2f0e91da80c7212ca01194c48dc34_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | C:\Users\admin\AppData\Roaming\zdahy1u4.he5\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | C:\Users\admin\AppData\Roaming\zdahy1u4.he5\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | C:\Users\admin\AppData\Local\Temp\637044216774872500_2200fa0a-ed27-4de6-9eb7-8c5d64b6fcd3.db | sqlite | |
MD5:— | SHA256:— | |||
| 3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | C:\Users\admin\AppData\Roaming\NewApp\NewApp.exe | executable | |
MD5:— | SHA256:— | |||
| 3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | C:\Users\admin\AppData\Roaming\zdahy1u4.he5.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | GET | 200 | 52.55.255.113:80 | http://checkip.amazonaws.com/ | US | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | 52.55.255.113:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | 77.88.21.158:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
smtp.yandex.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3824 | 91f2f0e91da80c7212ca01194c48dc34.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2 ETPRO signatures available at the full report