| File name: | PO_20190710.doc |
| Full analysis: | https://app.any.run/tasks/74dfc842-0152-495a-a293-8360258161d2 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | July 11, 2019, 14:49:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | A2E5506DF4004D8E3956E9EAA559A1BE |
| SHA1: | 089A0CCC94BF01A24372E79F45F658C4794DFBA6 |
| SHA256: | CC5009B4240A06E5BFB4AAB5C6C0BE22A18C8DC1429F58F3FA4F8844F85A843C |
| SSDEEP: | 12288:QtLLlyutb9WI5Pmn9Ya2ivgPS/Cjoo+xzxP4LLksDrJt3:QxpP+I5aYZ/PM2b+6H3 |
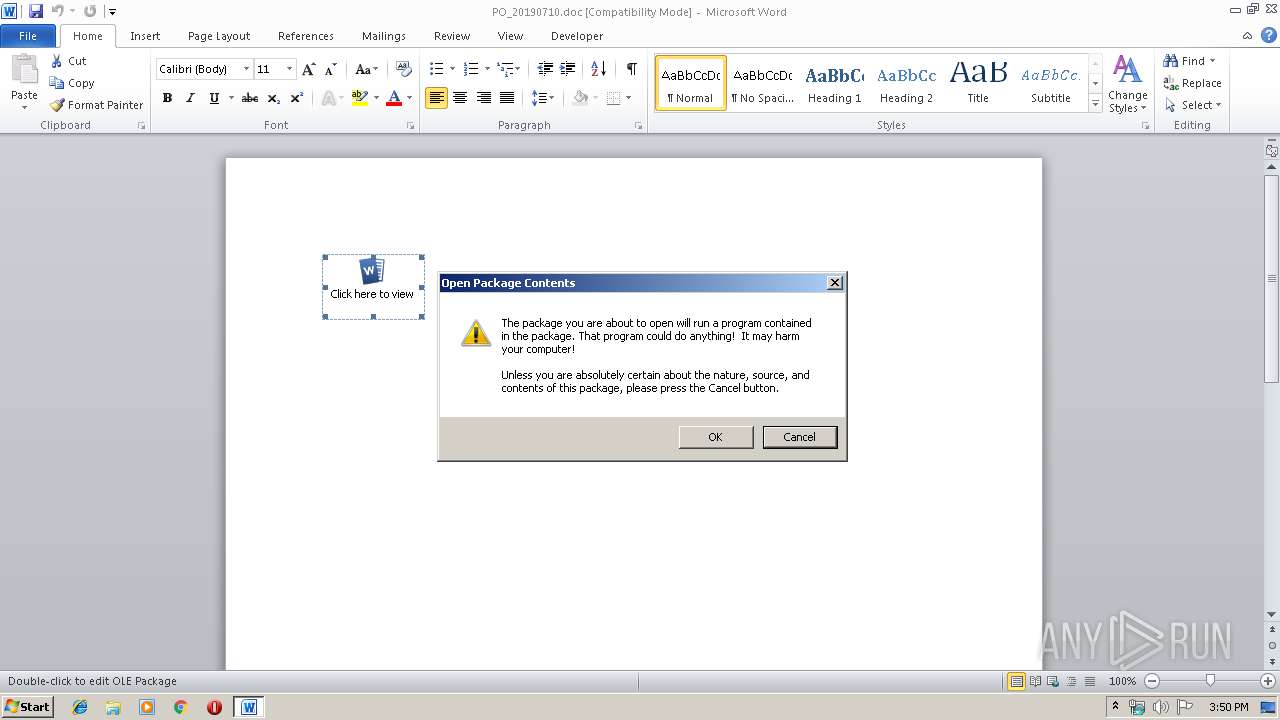
MALICIOUS
Application was dropped or rewritten from another process
- PO_20190710.exe (PID: 2652)
- PO_20190710.exe (PID: 3048)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3468)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 3468)
Detected artifacts of LokiBot
- PO_20190710.exe (PID: 3048)
LOKIBOT was detected
- PO_20190710.exe (PID: 3048)
Connects to CnC server
- PO_20190710.exe (PID: 3048)
Actions looks like stealing of personal data
- PO_20190710.exe (PID: 3048)
SUSPICIOUS
Application launched itself
- PO_20190710.exe (PID: 2652)
Loads DLL from Mozilla Firefox
- PO_20190710.exe (PID: 3048)
Creates files in the user directory
- PO_20190710.exe (PID: 3048)
Executable content was dropped or overwritten
- PO_20190710.exe (PID: 3048)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3468)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x7fcf3406 |
| ZipCompressedSize: | 386 |
| ZipUncompressedSize: | 1460 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Brokenskull |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Brokenskull |
| RevisionNumber: | 1 |
| CreateDate: | 2019:07:10 22:40:00Z |
| ModifyDate: | 2019:07:10 22:40:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | - |
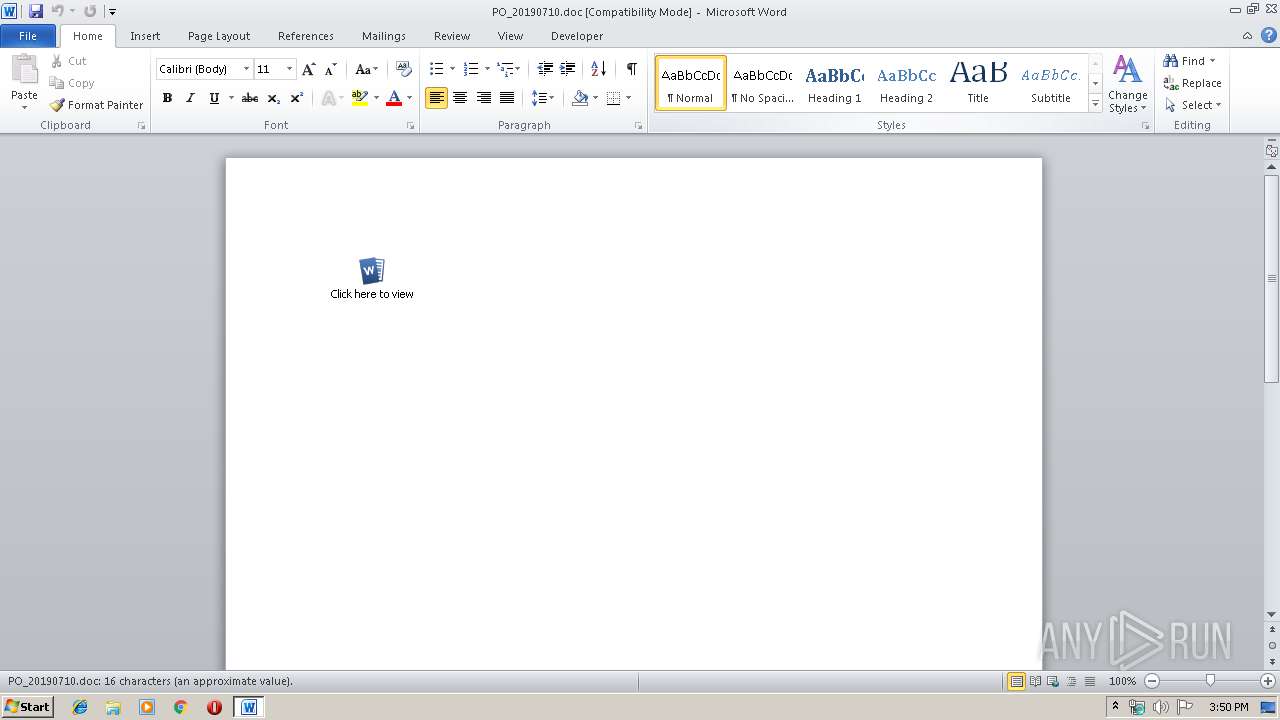
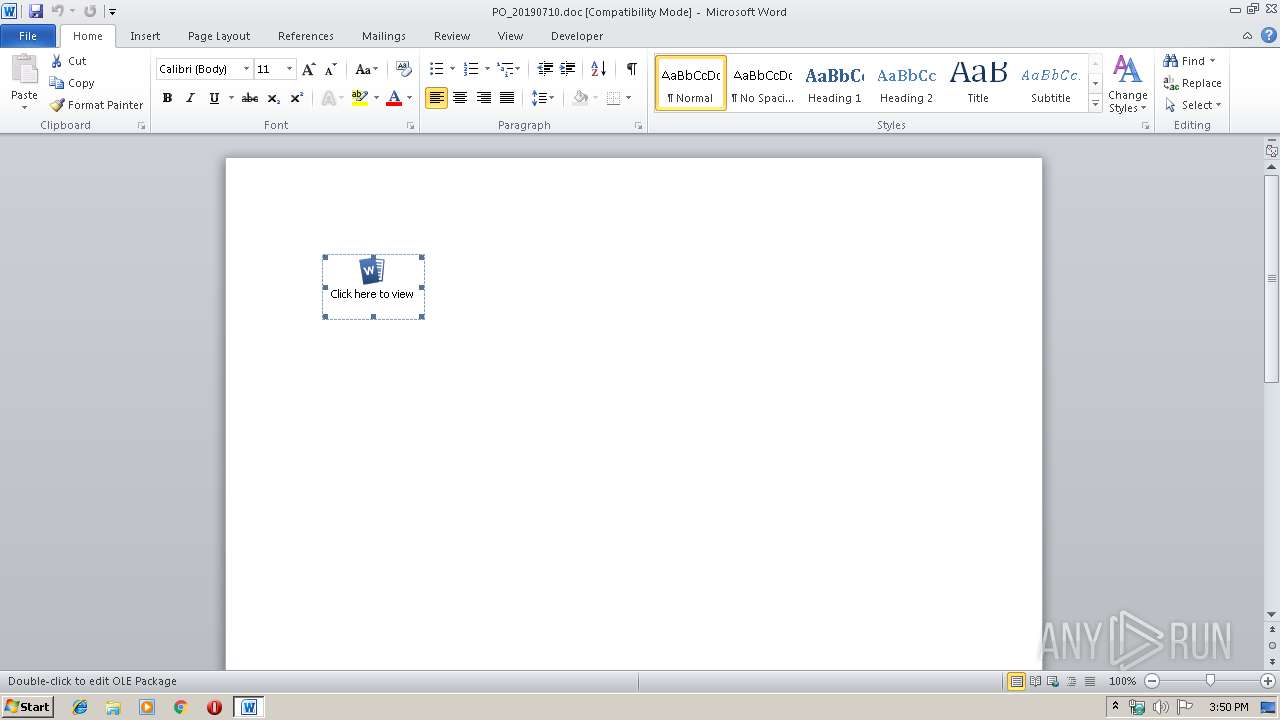
| Pages: | 1 |
| Words: | 3 |
| Characters: | 18 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 20 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
40
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2652 | "C:\Users\admin\AppData\Local\Temp\PO_20190710.exe" | C:\Users\admin\AppData\Local\Temp\PO_20190710.exe | — | WINWORD.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3048 | "C:\Users\admin\AppData\Local\Temp\PO_20190710.exe" | C:\Users\admin\AppData\Local\Temp\PO_20190710.exe | PO_20190710.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\PO_20190710.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 311
Read events
897
Write events
409
Delete events
5
Modification events
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | g$ |
Value: 206724008C0D0000010000000000000000000000 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324023838 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324023952 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324023953 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 8C0D00003E564EEEF737D50100000000 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | zh$ |
Value: 7A6824008C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | zh$ |
Value: 7A6824008C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B80.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3048 | PO_20190710.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3048 | PO_20190710.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 3468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6B2A1346.emf | emf | |
MD5:— | SHA256:— | |||
| 3468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\PO_20190710.exe | executable | |
MD5:— | SHA256:— | |||
| 3468 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3048 | PO_20190710.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.exe | executable | |
MD5:— | SHA256:— | |||
| 3468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$_20190710.doc | pgc | |
MD5:— | SHA256:— | |||
| 3048 | PO_20190710.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:18B8CFC0185C50383AAC0A4F30A9DAC8 | SHA256:913E8CED6A447FE791954D382ABA52D490513C5D2F689B391866C7E561F89A03 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
1
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3048 | PO_20190710.exe | POST | 404 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | text | 15 b | malicious |
3048 | PO_20190710.exe | POST | 200 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | binary | 23 b | malicious |
3048 | PO_20190710.exe | POST | 404 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | text | 15 b | malicious |
3048 | PO_20190710.exe | POST | 200 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | binary | 23 b | malicious |
3048 | PO_20190710.exe | POST | 200 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | binary | 23 b | malicious |
3048 | PO_20190710.exe | POST | 200 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | binary | 23 b | malicious |
3048 | PO_20190710.exe | POST | 200 | 5.101.152.144:80 | http://gama247.beget.tech/Agama2/fre.php | RU | binary | 23 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3048 | PO_20190710.exe | 5.101.152.144:80 | gama247.beget.tech | Beget Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gama247.beget.tech |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3048 | PO_20190710.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3048 | PO_20190710.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3048 | PO_20190710.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
8 ETPRO signatures available at the full report