| download: | freebitcobot.exe |
| Full analysis: | https://app.any.run/tasks/cd43629e-72ff-476a-b2fe-04f2eccbb22c |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | December 18, 2018, 22:33:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9A7F750064DFF2E55ACEE5ACC252360E |
| SHA1: | B32CB598D495615332092266F65F2E7EB53C18C5 |
| SHA256: | CC1329593DDA325C4CACE629A6B212A0451C103C892BA274F7C77EF480F782AE |
| SSDEEP: | 49152:w+t+z6ibqWTIxFBXo/2WnUCWTKjo3rkiPB/nngs9TKozMO70pLhOTmWTPRkIYWRT:w+gzBttUXoa2ozOu |
MALICIOUS
Application was dropped or rewritten from another process
- spolsv.exe (PID: 2932)
- spolsv.exe (PID: 3224)
- Java.exe (PID: 2588)
- spoolsv.exe (PID: 3252)
- spoolsv.exe (PID: 3044)
Changes the login/logoff helper path in the registry
- freebitcobot.exe (PID: 3076)
Changes settings of System certificates
- freebitcobot.exe (PID: 3076)
Stealing of credential data
- spoolsv.exe (PID: 3044)
Actions looks like stealing of personal data
- spoolsv.exe (PID: 3044)
ARKEI was detected
- spoolsv.exe (PID: 3044)
Connects to CnC server
- spolsv.exe (PID: 2932)
PREDATOR was detected
- spolsv.exe (PID: 2932)
SUSPICIOUS
Creates files in the program directory
- spoolsv.exe (PID: 3044)
- freebitcobot.exe (PID: 3076)
Reads the cookies of Google Chrome
- spolsv.exe (PID: 2932)
- spoolsv.exe (PID: 3044)
Application launched itself
- spoolsv.exe (PID: 3252)
- spolsv.exe (PID: 3224)
Executable content was dropped or overwritten
- freebitcobot.exe (PID: 3076)
Creates files in the user directory
- spoolsv.exe (PID: 3044)
- spolsv.exe (PID: 2932)
Loads DLL from Mozilla Firefox
- spoolsv.exe (PID: 3044)
Reads the cookies of Mozilla Firefox
- spoolsv.exe (PID: 3044)
- spolsv.exe (PID: 2932)
Connects to unusual port
- RegSvcs.exe (PID: 3988)
Checks for external IP
- spoolsv.exe (PID: 3044)
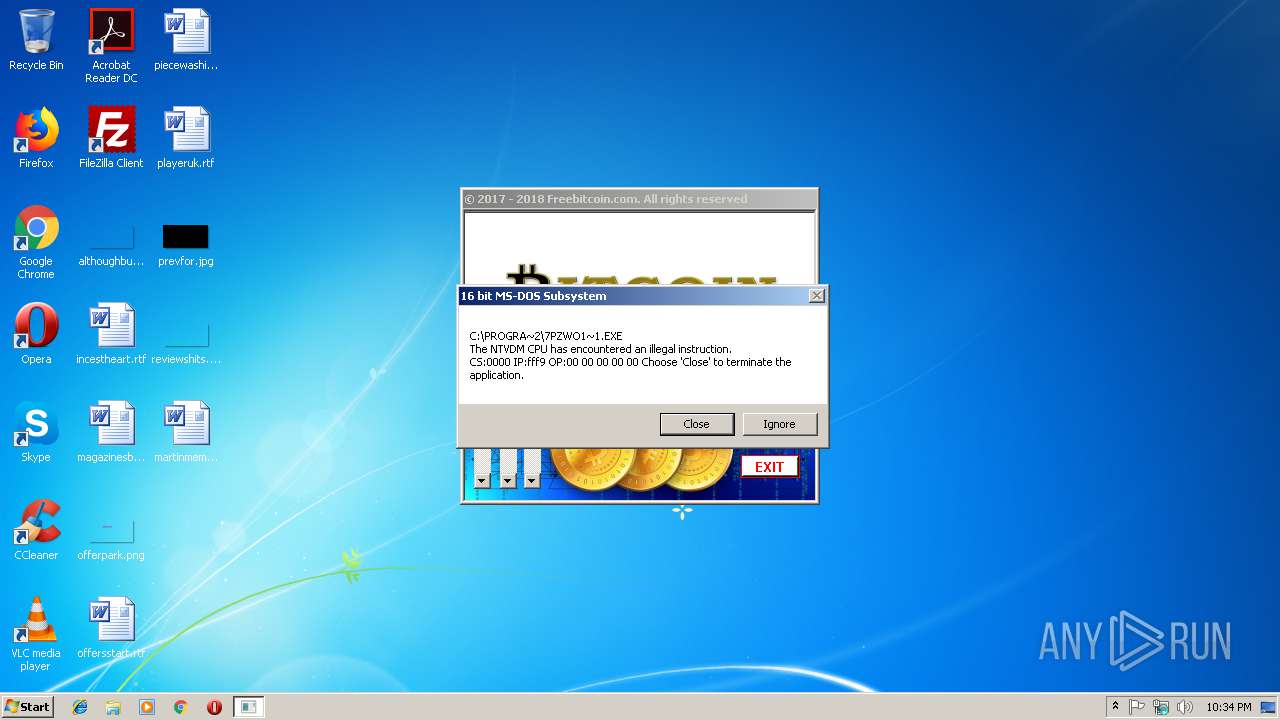
Executes application which crashes
- spoolsv.exe (PID: 3044)
Starts CMD.EXE for commands execution
- spoolsv.exe (PID: 3044)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:17 14:16:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 5347328 |
| InitializedDataSize: | 19456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x51b771 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.25 |
| ProductVersionNumber: | 1.0.0.28 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | G5.50 |
| CompanyName: | SoftBalance |
| FileDescription: | SoftBalane Licence Server |
| FileVersion: | 1, 0, 0, 25 |
| InternalName: | sbsvr.exe |
| LegalCopyright: | (c) 2010, JS "SoftBalance" |
| OriginalFileName: | sbsvr.exe |
| ProductName: | sbsvr |
| ProductVersion: | 1.0.0.28 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Dec-2018 13:16:34 |
| Detected languages: |
|
| Comments: | G5.50 |
| CompanyName: | SoftBalance |
| FileDescription: | SoftBalane Licence Server |
| FileVersion: | 1, 0, 0, 25 |
| InternalName: | sbsvr.exe |
| LegalCopyright: | (c) 2010, JS "SoftBalance" |
| OriginalFilename: | sbsvr.exe |
| ProductName: | sbsvr |
| ProductVersion: | 1.0.0.28 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Dec-2018 13:16:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00519777 | 0x00519800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.39341 |
.rsrc | 0x0051C000 | 0x00004846 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.42129 |
.reloc | 0x00522000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
128 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
40
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2588 | "C:\ProgramData\Oracle\Java\Java.exe" | C:\ProgramData\Oracle\Java\Java.exe | — | freebitcobot.exe | |||||||||||
User: admin Company: Aignesberger Software GmbH Integrity Level: MEDIUM Exit code: 0 Version: 16.3.0.100 Modules
| |||||||||||||||
| 2932 | "C:\Users\admin\AppData\Local\spolsv.exe" | C:\Users\admin\AppData\Local\spolsv.exe | spolsv.exe | ||||||||||||
User: admin Company: HQ Trivia, a live trivia game on mobiles, became hugely Integrity Level: MEDIUM Description: his girlfriend reportedly asked them to check on him Exit code: 1 Version: 4.2.5.3 Modules
| |||||||||||||||
| 3044 | "C:\Users\admin\AppData\Local\spoolsv.exe" | C:\Users\admin\AppData\Local\spoolsv.exe | spoolsv.exe | ||||||||||||
User: admin Company: HQ Trivia, a live trivia game on mobiles, became hugely Integrity Level: MEDIUM Description: his girlfriend reportedly asked them to check on him Exit code: 0 Version: 4.2.5.3 Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\freebitcobot.exe" | C:\Users\admin\AppData\Local\Temp\freebitcobot.exe | explorer.exe | ||||||||||||
User: admin Company: SoftBalance Integrity Level: MEDIUM Description: SoftBalane Licence Server Exit code: 0 Version: 1, 0, 0, 25 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\spolsv.exe" | C:\Users\admin\AppData\Local\spolsv.exe | — | freebitcobot.exe | |||||||||||
User: admin Company: HQ Trivia, a live trivia game on mobiles, became hugely Integrity Level: MEDIUM Description: his girlfriend reportedly asked them to check on him Exit code: 0 Version: 4.2.5.3 Modules
| |||||||||||||||
| 3252 | "C:\Users\admin\AppData\Local\spoolsv.exe" | C:\Users\admin\AppData\Local\spoolsv.exe | — | freebitcobot.exe | |||||||||||
User: admin Company: HQ Trivia, a live trivia game on mobiles, became hugely Integrity Level: MEDIUM Description: his girlfriend reportedly asked them to check on him Exit code: 0 Version: 4.2.5.3 Modules
| |||||||||||||||
| 3808 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | spoolsv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3908 | "C:\Windows\system32\cmd.exe" rd /s /q C:\ProgramData\7Z6MJ77EOZV3K8 | C:\Windows\system32\cmd.exe | — | spoolsv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3988 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe | Java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
618
Read events
561
Write events
57
Delete events
0
Modification events
| (PID) Process: | (3076) freebitcobot.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3076) freebitcobot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\CA\Certificates\F5AD0BCC1AD56CD150725B1C866C30AD92EF21B0 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000F5AD0BCC1AD56CD150725B1C866C30AD92EF21B0140000000100000014000000BBAF7E023DFAA6F13C848EADEE3898ECD93232D40400000001000000100000001EDAF9AE99CE2920667D0E9A8B3F8C9C0F00000001000000300000007CE102D63C57CB48F80A65D1A5E9B350A7A618482AA5A36775323CA933DDFCB00DEF83796A6340DEC5EBF7596CFD8E5D19000000010000001000000082218FFB91733E64136BE5719F57C3A118000000010000001000000045ED9BBC5E43D3B9ECD63C060DB78E5C200000000100000078050000308205743082045CA00302010202102766EE56EB49F38EABD770A2FC84DE22300D06092A864886F70D01010C0500306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F74301E170D3030303533303130343833385A170D3230303533303130343833385A308185310B3009060355040613024742311B30190603550408131247726561746572204D616E636865737465723110300E0603550407130753616C666F7264311A3018060355040A1311434F4D4F444F204341204C696D69746564312B302906035504031322434F4D4F444F205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010091E85492D20A56B1AC0D24DDC5CF446774992B37A37D23700071BC53DFC4FA2A128F4B7F1056BD9F7072B7617FC94B0F17A73DE3B00461EEFF1197C7F4863E0AFA3E5CF993E6347AD9146BE79CB385A0827A76AF7190D7ECFD0DFA9C6CFADFB082F4147EF9BEC4A62F4F7F997FB5FC674372BD0C00D689EB6B2CD3ED8F981C14AB7EE5E36EFCD8A8E49224DA436B62B855FDEAC1BC6CB68BF30E8D9AE49B6C6999F878483045D5ADE10D3C4560FC32965127BC67C3CA2EB66BEA46C7C720A0B11F65DE4808BAA44EA9F283463784EBE8CC814843674E722A9B5CBD4C1B288A5C227BB4AB98D9EEE05183C309464E6D3E99FA9517DA7C3357413C8D51ED0BB65CAF2C631ADF57C83FBCE95DC49BAF4599E2A35A24B4BAA9563DCF6FAAFF4958BEF0A8FFF4B8ADE937FBBAB8F40B3AF9E843421E89D884CB13F1D9BBE18960B88C2856AC141D9C0AE771EBCF0EDD3DA996A148BD3CF7AFB50D224CC01181EC563BF6D3A2E25BB7B204225295809369E88E4C65F191032D707402EA8B671529695202BBD7DF506A5546BFA0A328617F70D0C3A2AA2C21AA47CE289C064576BF821827B4D5AEB4CB50E66BF44C867130E9A6DF1686E0D8FF40DDFBD042887FA3333A2E5C1E41118163CE18716B2BECA68AB7315C3A6A47E0C37959D6201AAFF26A98AA72BC574AD24B9DBB10FCB04C41E5ED1D3D5E289D9CCCBFB351DAA747E584530203010001A381F43081F1301F0603551D23041830168014ADBD987A34B426F7FAC42654EF03BDE024CB541A301D0603551D0E04160414BBAF7E023DFAA6F13C848EADEE3898ECD93232D4300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF30110603551D20040A300830060604551D200030440603551D1F043D303B3039A037A0358633687474703A2F2F63726C2E7573657274727573742E636F6D2F416464547275737445787465726E616C4341526F6F742E63726C303506082B0601050507010104293027302506082B060105050730018619687474703A2F2F6F6373702E7573657274727573742E636F6D300D06092A864886F70D01010C0500038201010064BF83F15F9A85D0CDB8A129570DE85AF7D1E93EF276046EF15270BB1E3CFF4D0D746ACC818225D3C3A02A5D4CF5BA8BA16DC4540975C7E3270E5D847937401377F5B4AC1CD03BAB1712D6EF34187E2BE979D3AB57450CAF28FAD0DBE5509588BBDF8557697D92D852CA7381BF1CF3E6B86E661105B31E942D7F91959259F14CCEA391714C7C470C3B0B19F6A1B16C863E5CAAC42E82CBF90796BA484D90F294C8A973A2EB067B239DDEA2F34D559F7A6145981868C75E406B23F5797AEF8CB56B8BB76F46F47BF13D4B04D89380595AE041241DB28F15605847DBEF6E46FD15F5D95F9AB3DBD8B8E440B3CD9739AE85BB1D8EBCDC879BD1A6EFF13B6F10386F | |||
| (PID) Process: | (3076) freebitcobot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe, C:\ProgramData\Oracle\Java\Java.exe | |||
| (PID) Process: | (3076) freebitcobot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3076) freebitcobot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3988) RegSvcs.exe | Key: | HKEY_CURRENT_USER\Software\{ZIRJJHV7-142469-FPYQQO-FPYQQOB71E} |
| Operation: | write | Name: | H |
Value: cHVrLnNlcnZlYmVlci5jb206OTA0OCxtYWluY29pbi5obGRucy5ydTo4MDQ4LA== | |||
| (PID) Process: | (3044) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spoolsv_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3044) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spoolsv_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3044) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spoolsv_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3044) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spoolsv_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
4
Text files
18
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\Temp\CabAEA2.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\Temp\TarAEA3.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\Temp\CabAEC3.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\Temp\TarAEC4.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\Temp\CabAED5.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\Temp\TarAED6.tmp | — | |
MD5:— | SHA256:— | |||
| 3044 | spoolsv.exe | C:\ProgramData\7Z6MJ77EOZV3K8\c-shm | — | |
MD5:— | SHA256:— | |||
| 3044 | spoolsv.exe | C:\ProgramData\7Z6MJ77EOZV3K8\history | — | |
MD5:— | SHA256:— | |||
| 3044 | spoolsv.exe | C:\ProgramData\7Z6MJ77EOZV3K8\history-shm | — | |
MD5:— | SHA256:— | |||
| 3076 | freebitcobot.exe | C:\Users\admin\AppData\Local\spolsv.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
17
DNS requests
8
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | spolsv.exe | GET | — | 173.249.41.72:80 | http://pruf.coinpot.city/api/info.get | US | — | — | malicious |
3044 | spoolsv.exe | POST | 200 | 104.31.67.6:80 | http://ark.surfeth.com/index.php | US | text | 75 b | malicious |
3076 | freebitcobot.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3044 | spoolsv.exe | POST | 200 | 185.194.141.58:80 | http://ip-api.com/line/ | DE | text | 141 b | malicious |
2932 | spolsv.exe | POST | 200 | 173.249.41.72:80 | http://pruf.coinpot.city/api/gate.get?p1=0&p2=6&p3=0&p4=2&p5=0&p6=0&p7=0 | US | binary | 1 b | malicious |
3044 | spoolsv.exe | POST | 200 | 104.31.67.6:80 | http://ark.surfeth.com/index.php | US | text | 50 b | malicious |
3044 | spoolsv.exe | POST | 404 | 173.249.41.72:80 | http://coinpot.city/send.exehttp://crmine.com/svhost.exe | US | html | 234 b | malicious |
2932 | spolsv.exe | GET | 404 | 173.249.41.72:80 | http://panel.coinpot.city/send.exe | US | html | 206 b | malicious |
2932 | spolsv.exe | GET | 200 | 173.249.41.72:80 | http://pruf.coinpot.city/api/download.get | US | text | 34 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | freebitcobot.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
2932 | spolsv.exe | 173.249.41.72:80 | pruf.coinpot.city | Contabo GmbH | US | malicious |
3988 | RegSvcs.exe | 5.188.60.183:8048 | puk.servebeer.com | Sinarohost LTD | RU | malicious |
3988 | RegSvcs.exe | 5.188.60.183:9048 | puk.servebeer.com | Sinarohost LTD | RU | malicious |
3044 | spoolsv.exe | 173.249.41.72:80 | pruf.coinpot.city | Contabo GmbH | US | malicious |
3044 | spoolsv.exe | 104.31.67.6:80 | ark.surfeth.com | Cloudflare Inc | US | shared |
3044 | spoolsv.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crt.comodoca.com |
| whitelisted |
ark.surfeth.com |
| malicious |
ip-api.com |
| malicious |
pruf.coinpot.city |
| malicious |
puk.servebeer.com |
| malicious |
maincoin.hldns.ru |
| malicious |
coinpot.city |
| malicious |
panel.coinpot.city |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3044 | spoolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
3044 | spoolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
3044 | spoolsv.exe | A Network Trojan was detected | ET TROJAN Arkei Stealer Client Data Upload |
3044 | spoolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Nocturnal Stealer |
3044 | spoolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Nocturnal Stealer |
3044 | spoolsv.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3044 | spoolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
3044 | spoolsv.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious downloader - 404 Not Found for .exe |
3044 | spoolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
2932 | spolsv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Agent.PLQ (Predator Stealer) CnC Checkin |
5 ETPRO signatures available at the full report