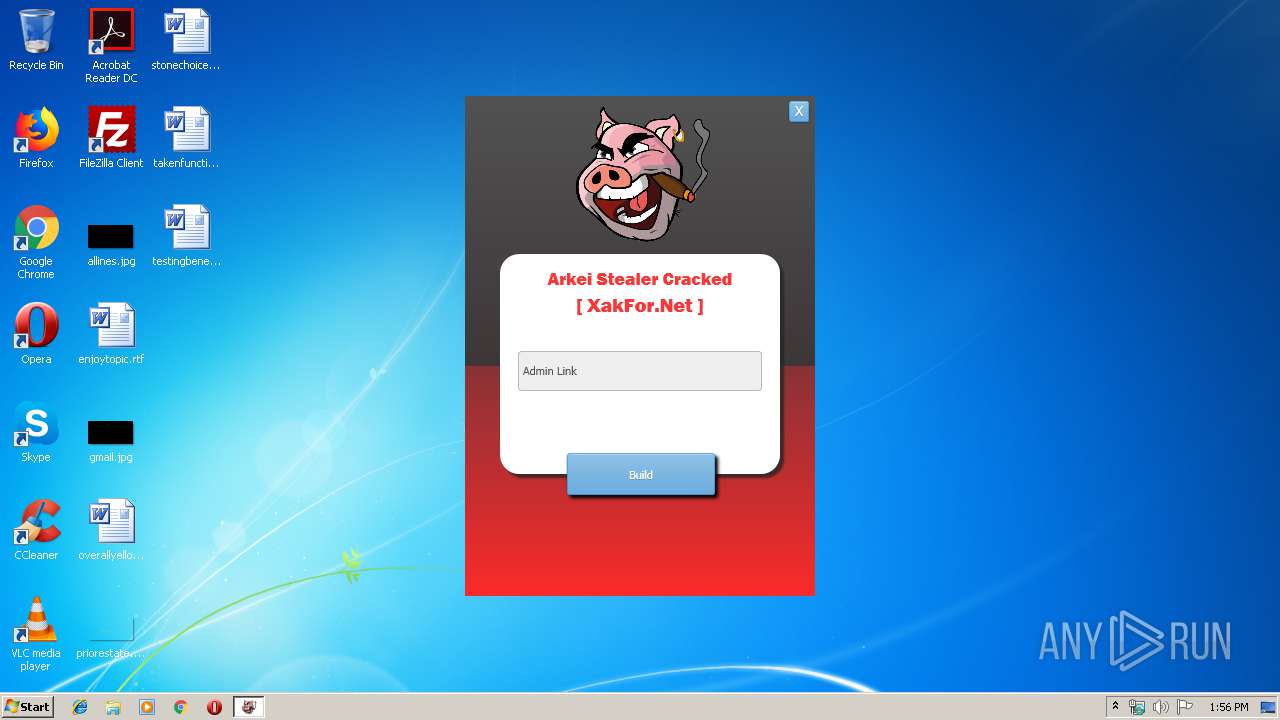
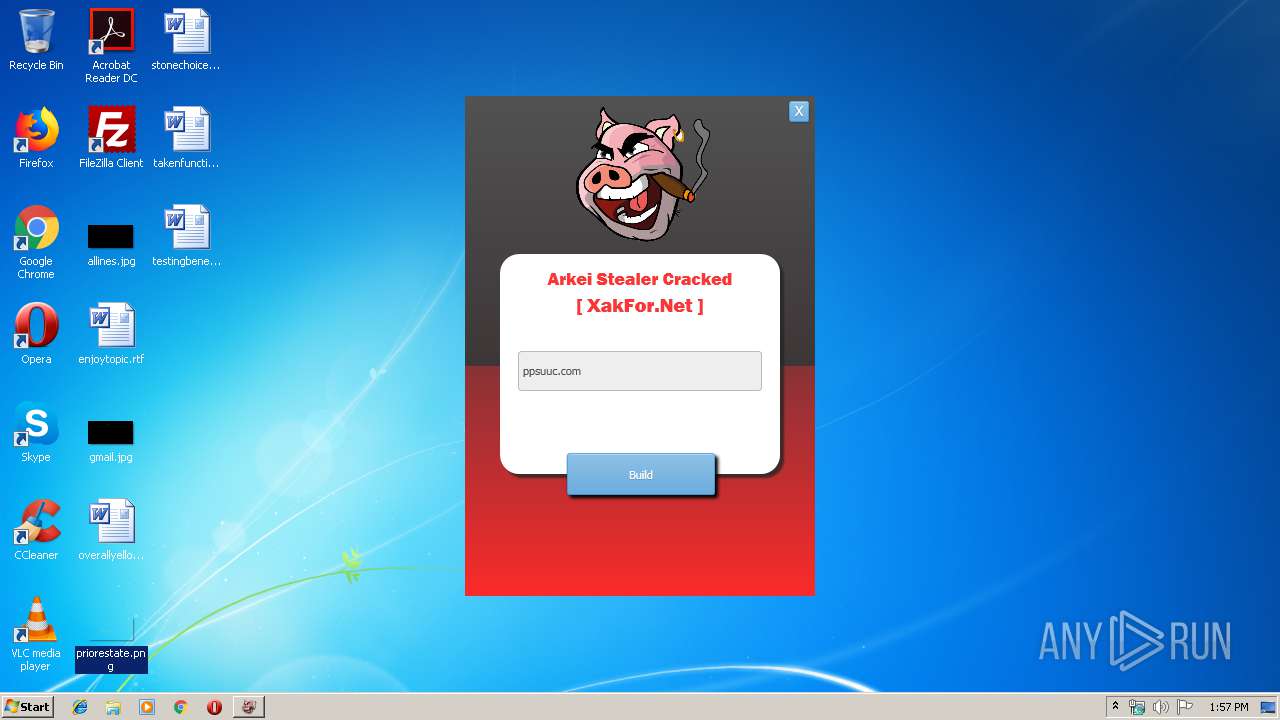
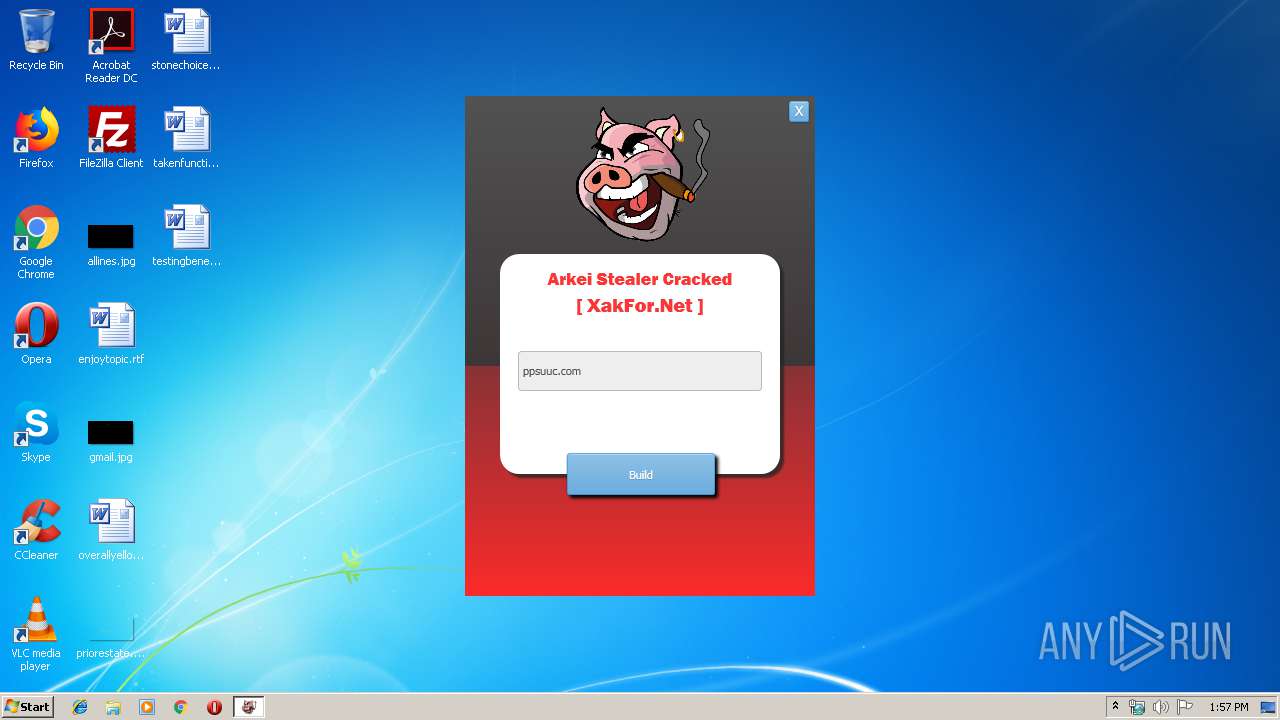
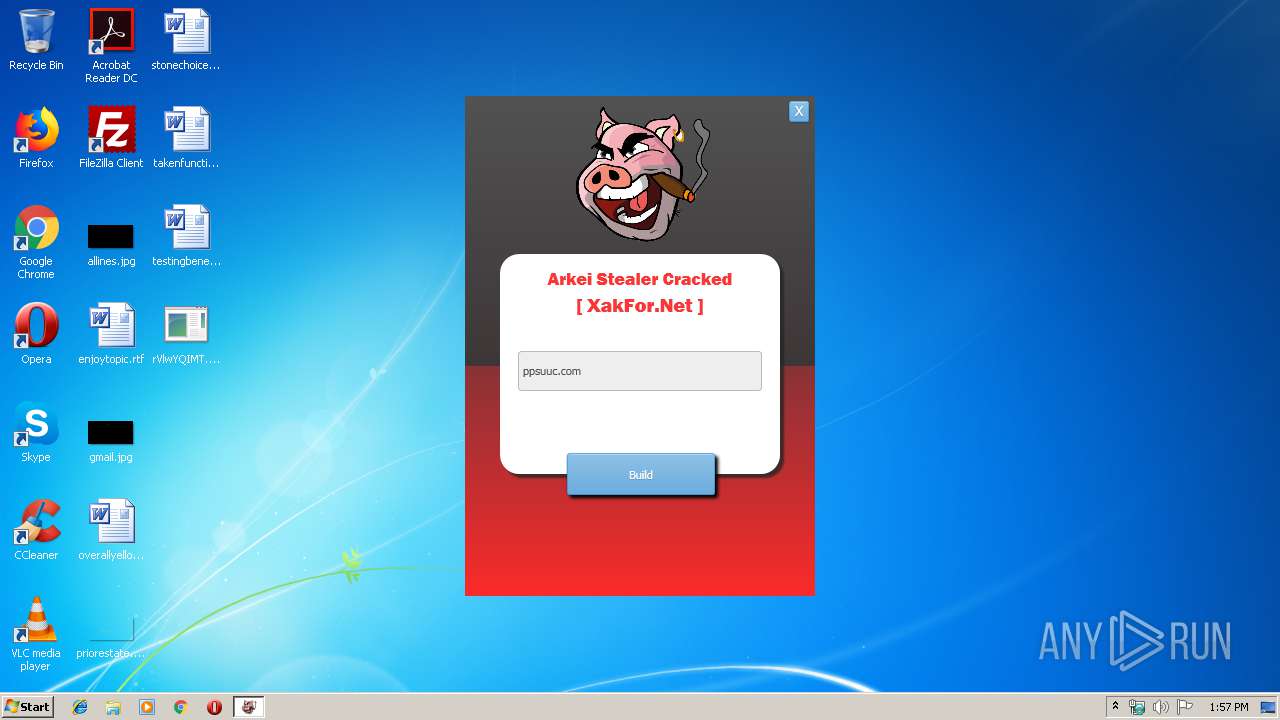
| File name: | Arkei Stealer Cracked .exe |
| Full analysis: | https://app.any.run/tasks/f05373da-37de-4c0e-ab82-9e2aeb372025 |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | April 25, 2019, 12:56:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0AD401CBC0492E0CB137A4627502F982 |
| SHA1: | 9BD43D94D10A3B3B4F3B8A0191C7CB153A35E0CB |
| SHA256: | CC0292C3965A1387F7CC6F6B35F472EC676326A52692DE029447DBFA2CB267F4 |
| SSDEEP: | 24576:MjL6J5JIWG9SFk/loz0gIT6Ckx9/py06aqkkeaFB9D+/vpXUf+:MjM5xG9rs0gLz9wBIZXUf+ |
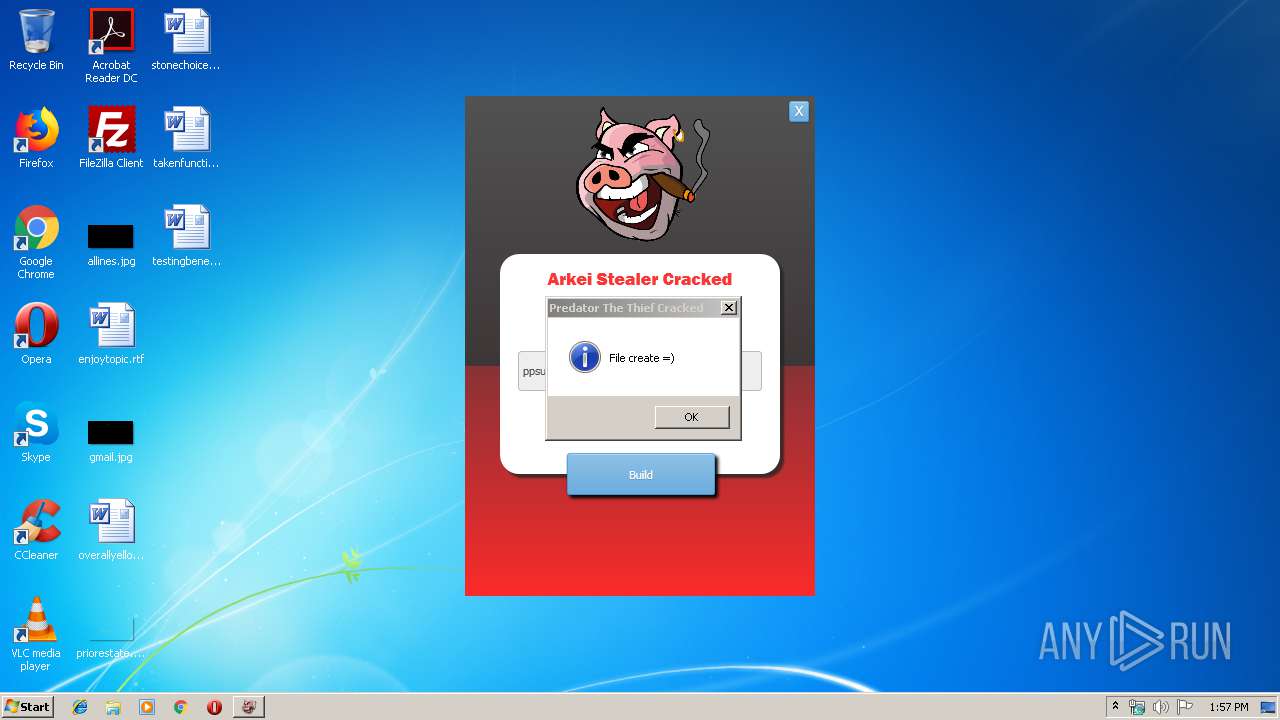
MALICIOUS
Application was dropped or rewritten from another process
- 5571576226.exe (PID: 2752)
- rVlwYQIMT.exe (PID: 4040)
Stealing of credential data
- 5571576226.exe (PID: 2752)
ARKEI was detected
- 5571576226.exe (PID: 2752)
SUSPICIOUS
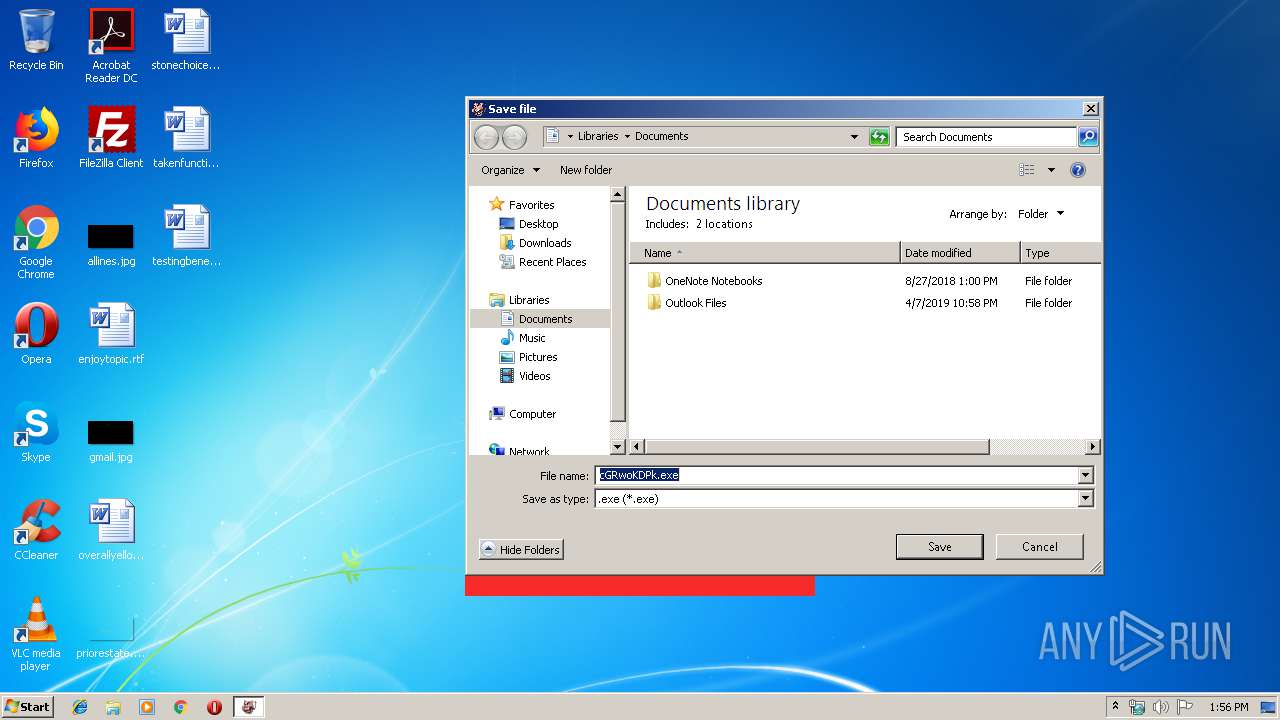
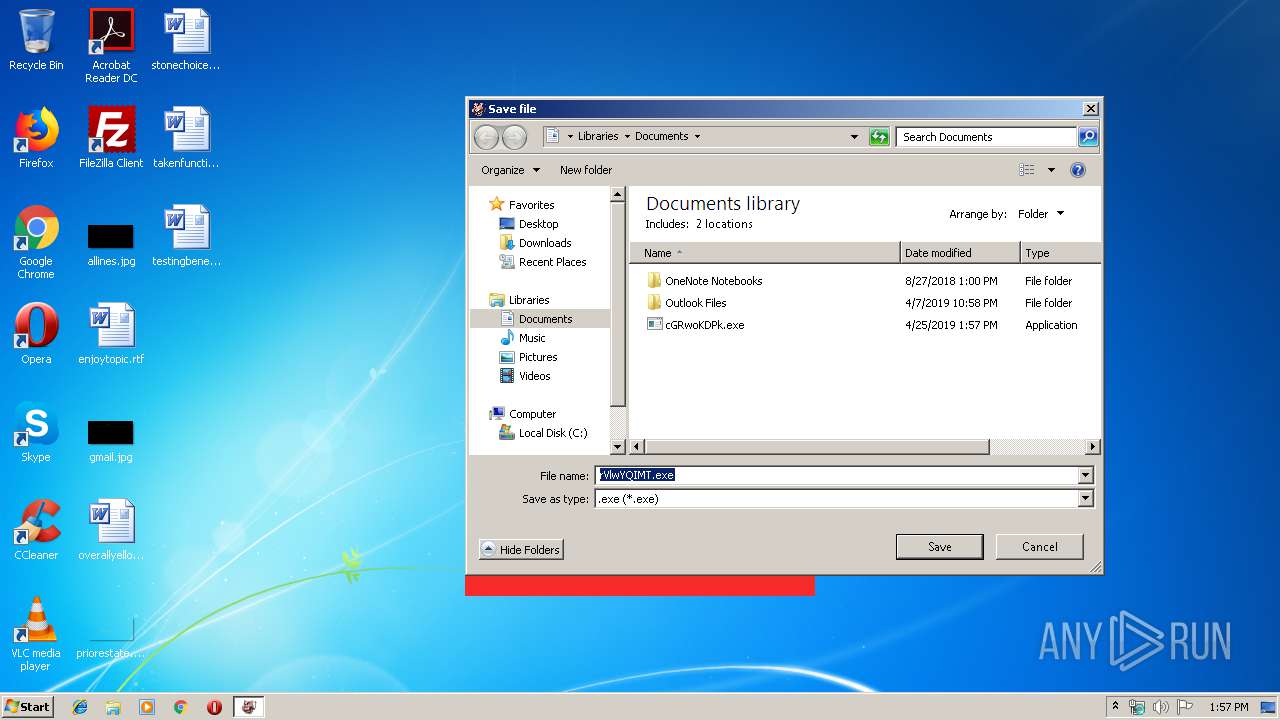
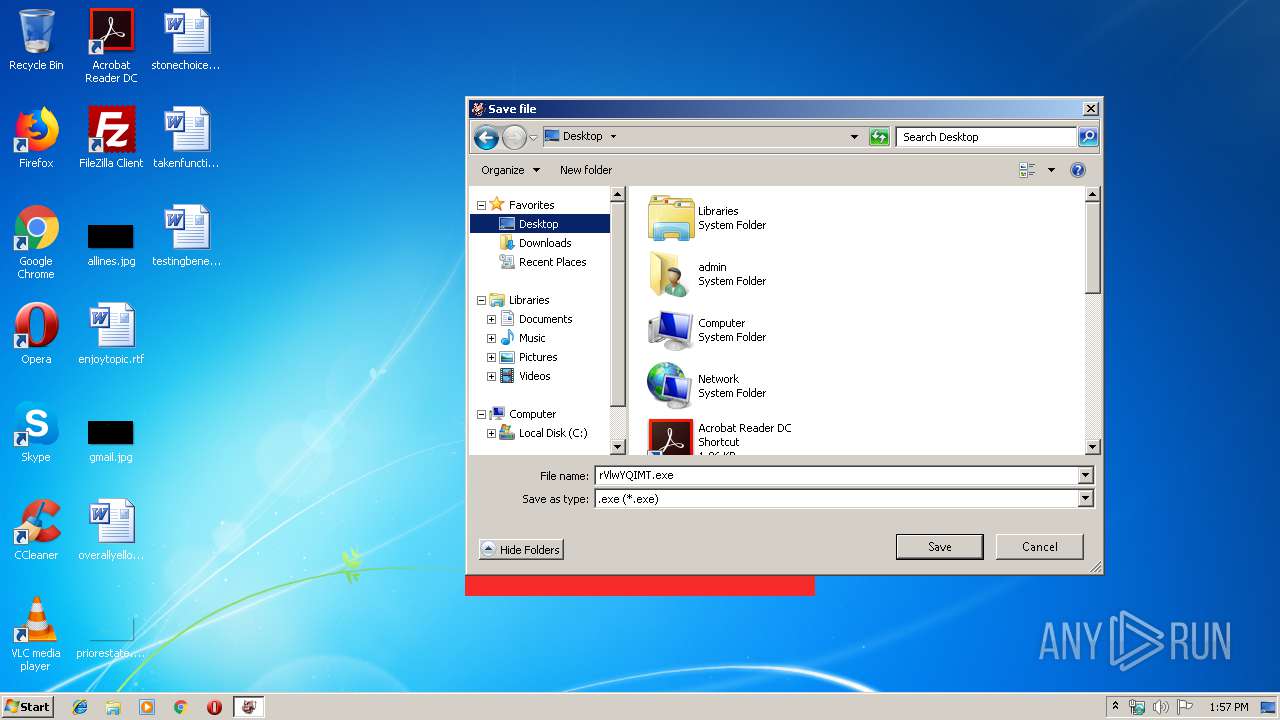
Executable content was dropped or overwritten
- Arkei Stealer Cracked .exe (PID: 3092)
- rVlwYQIMT.exe (PID: 4040)
Creates files in the program directory
- rVlwYQIMT.exe (PID: 4040)
- 5571576226.exe (PID: 2752)
Starts itself from another location
- rVlwYQIMT.exe (PID: 4040)
Reads the cookies of Google Chrome
- 5571576226.exe (PID: 2752)
Starts CMD.EXE for commands execution
- rVlwYQIMT.exe (PID: 4040)
- 5571576226.exe (PID: 2752)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3020)
- cmd.exe (PID: 2116)
Reads the cookies of Mozilla Firefox
- 5571576226.exe (PID: 2752)
Checks for external IP
- 5571576226.exe (PID: 2752)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:02 11:14:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 35840 |
| InitializedDataSize: | 1658880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a600a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | Arkei Stealer Cracked |
| FileVersion: | 1.0.0.0 |
| InternalName: | Arkei Stealer Cracked.exe |
| LegalCopyright: | Copyright © Microsoft 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | Arkei Stealer Cracked.exe |
| ProductName: | Arkei Stealer Cracked |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2018 09:14:15 |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | Arkei Stealer Cracked |
| FileVersion: | 1.0.0.0 |
| InternalName: | Arkei Stealer Cracked.exe |
| LegalCopyright: | Copyright © Microsoft 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | Arkei Stealer Cracked.exe |
| ProductName: | Arkei Stealer Cracked |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Aug-2018 09:14:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\x1b\x14ePMN5nd$\x15 | 0x00002000 | 0x00152464 | 0x00152600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99988 |
.text | 0x00156000 | 0x00008968 | 0x00008A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.3043 |
.rsrc | 0x00160000 | 0x000426F8 | 0x00042800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.44239 |
.reloc | 0x001A4000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x001A6000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.67095 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
42
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2116 | "C:\Windows\System32\cmd.exe" /c taskkill /im 5571576226.exe /f & erase C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\5571576226.exe & exit | C:\Windows\System32\cmd.exe | — | 5571576226.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2252 | taskkill /im rVlwYQIMT.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2752 | "C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\5571576226.exe" | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\5571576226.exe | rVlwYQIMT.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2772 | taskkill /im 5571576226.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | "C:\Windows\System32\cmd.exe" /c taskkill /im rVlwYQIMT.exe /f & erase C:\Users\admin\Desktop\rVlwYQIMT.exe & exit | C:\Windows\System32\cmd.exe | — | rVlwYQIMT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\Arkei Stealer Cracked .exe" | C:\Users\admin\AppData\Local\Temp\Arkei Stealer Cracked .exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Arkei Stealer Cracked Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\Desktop\rVlwYQIMT.exe" | C:\Users\admin\Desktop\rVlwYQIMT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
746
Read events
613
Write events
125
Delete events
8
Modification events
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Arkei Stealer Cracked .exe | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 0 |
Value: 410072006B0065006900200053007400650061006C0065007200200043007200610063006B006500640020002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3092) Arkei Stealer Cracked .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 0 |
Value: 410072006B0065006900200053007400650061006C0065007200200043007200610063006B006500640020002E00650078006500000014001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20000000 | |||
Executable files
3
Suspicious files
1
Text files
10
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | Arkei Stealer Cracked .exe | C:\Users\admin\AppData\Local\Temp\stub.bin | — | |
MD5:— | SHA256:— | |||
| 2752 | 5571576226.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\c-shm | — | |
MD5:— | SHA256:— | |||
| 2752 | 5571576226.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\files\Desktop.zip | — | |
MD5:— | SHA256:— | |||
| 3092 | Arkei Stealer Cracked .exe | C:\Users\admin\Documents\cGRwoKDPk.exe | executable | |
MD5:— | SHA256:— | |||
| 3092 | Arkei Stealer Cracked .exe | C:\Users\admin\Desktop\rVlwYQIMT.exe | executable | |
MD5:— | SHA256:— | |||
| 4040 | rVlwYQIMT.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\5571576226.exe | executable | |
MD5:— | SHA256:— | |||
| 2752 | 5571576226.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\files\passwords.log | text | |
MD5:— | SHA256:— | |||
| 2752 | 5571576226.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\files\information.log | text | |
MD5:— | SHA256:— | |||
| 2752 | 5571576226.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\files\autofill_Google Chrome_Default.log | text | |
MD5:— | SHA256:— | |||
| 2752 | 5571576226.exe | C:\ProgramData\Arkei-90059c37-1320-41a4-b58d-2b75a9850d2f\wd | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
2
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | 5571576226.exe | POST | 200 | 185.194.141.58:80 | http://ip-api.com/line/?fields=query | DE | text | 15 b | malicious |
2752 | 5571576226.exe | POST | 200 | 185.194.141.58:80 | http://ip-api.com/line/?fields=countryCode | DE | text | 3 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | 5571576226.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
ppsuuc.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | 5571576226.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2752 | 5571576226.exe | A Network Trojan was detected | ET TROJAN Arkei Stealer IP Lookup |
2752 | 5571576226.exe | A Network Trojan was detected | MALWARE [PTsecurity] Generic.PWS.Arkei Stealers Header (Vidar) |
2752 | 5571576226.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2752 | 5571576226.exe | A Network Trojan was detected | ET TROJAN Arkei Stealer IP Lookup |
2752 | 5571576226.exe | A Network Trojan was detected | MALWARE [PTsecurity] Generic.PWS.Arkei Stealers Header (Vidar) |
2 ETPRO signatures available at the full report