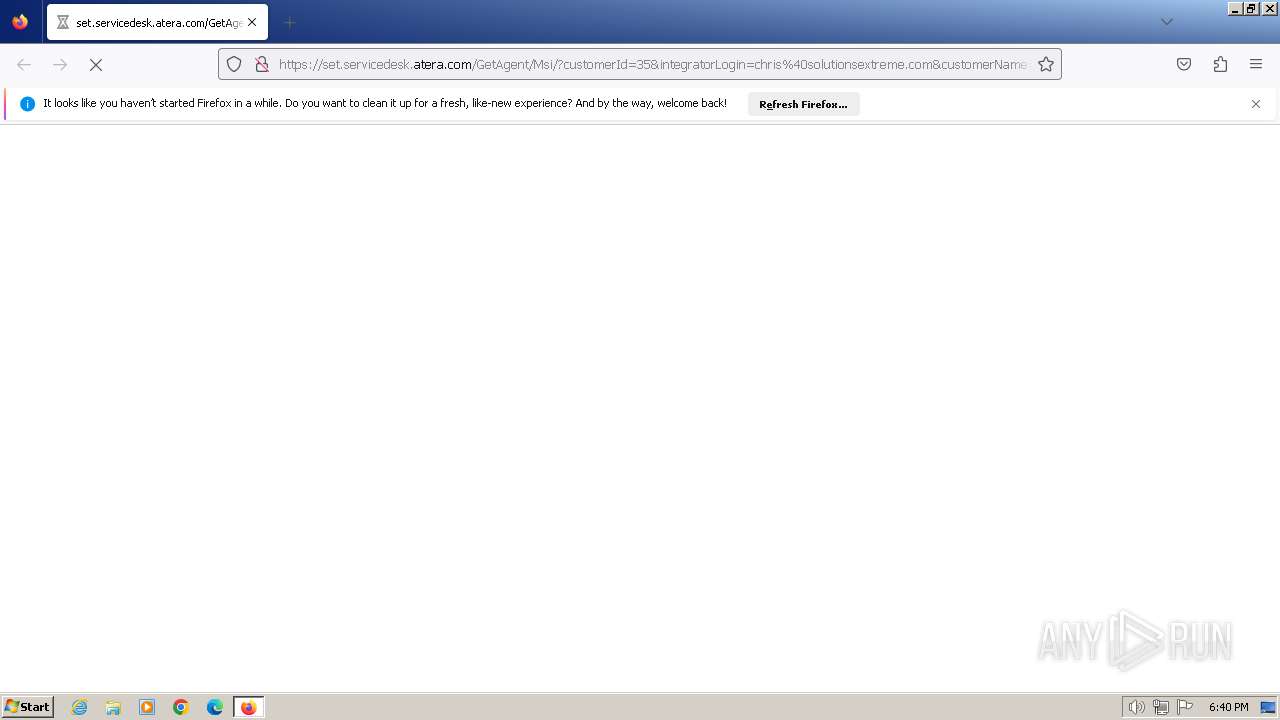
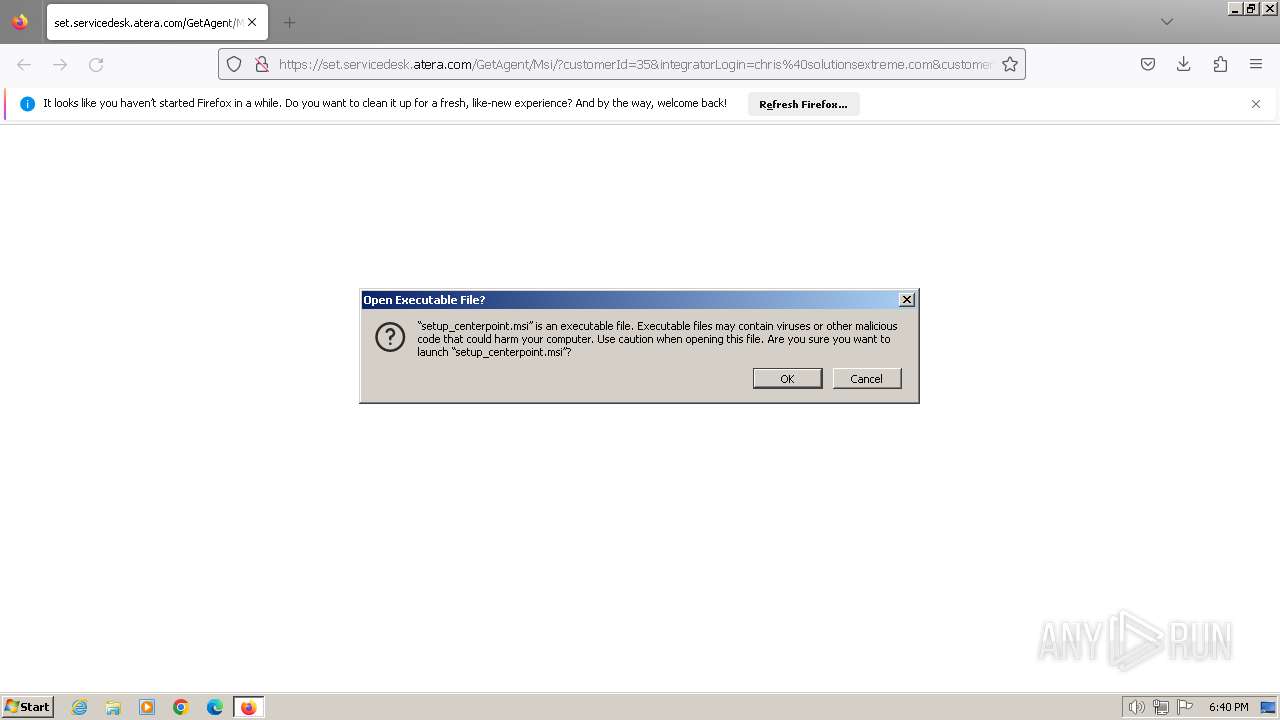
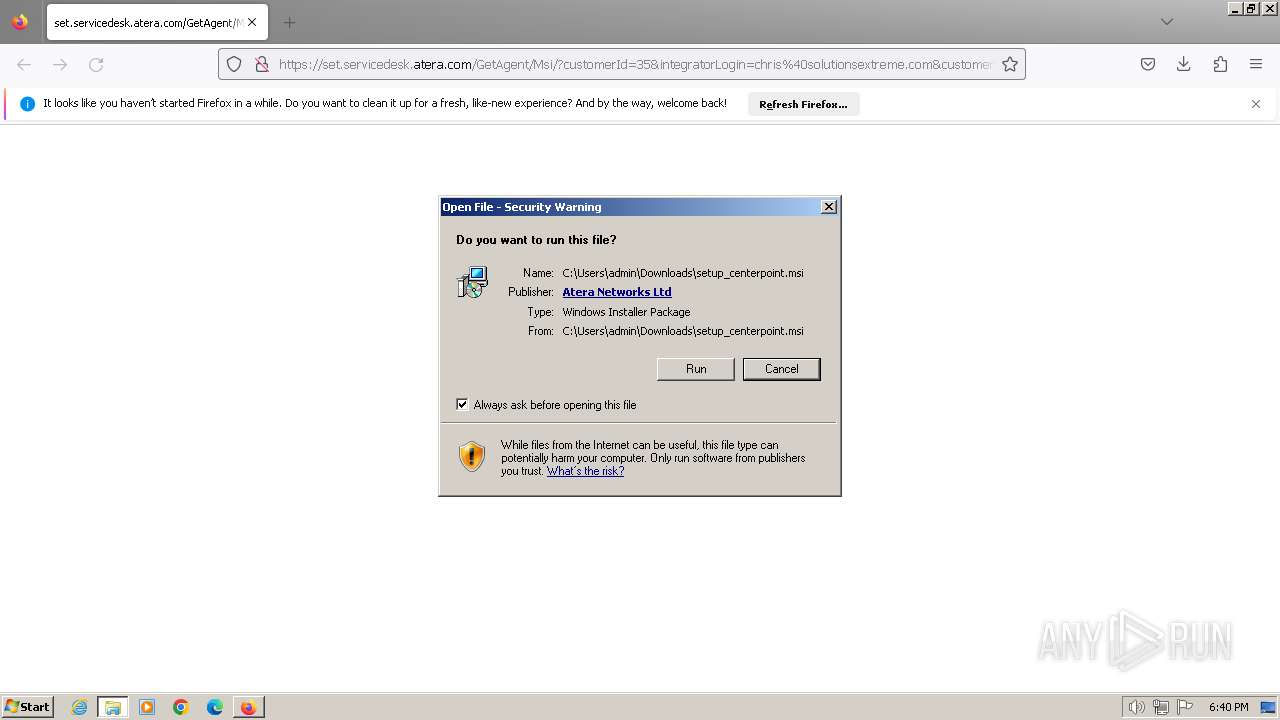
| URL: | https://set.servicedesk.atera.com/GetAgent/Msi/?customerId=35&integratorLogin=chris%40solutionsextreme.com&customerName=Centerpoint&accountId=0013z00002LHg1NAAT |
| Full analysis: | https://app.any.run/tasks/58b17a34-7fa6-4a5d-91ff-5271707e63e3 |
| Verdict: | Malicious activity |
| Threats: | Pikabot is a trojan malware with a focus on loader capabilities. Pikabot is also used for other activities, such as executing commands on the infected system. The earlier versions of the malware made use of extensive code obfuscation to evade detection. Upon infection, it collects system information and sends it to command-and-control servers. |
| Analysis date: | February 06, 2024, 18:40:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1515478962BBF03627A22463E95C3FCD |
| SHA1: | 87AAA779D4BE8225D45551604940F1E6EECE732F |
| SHA256: | CBCDBF9DE432A99EB0DCA675636EE6A2B8E1D3B5D317F7E82B11E78FA93F0B26 |
| SSDEEP: | 3:N8NZVJJUyG6lK1s9kGl0c8sjbtuGKIyRMAIALuRyV1ka4pf//Vx:2/6yblKu9kWKybthyRMAIALuQ1kL/Vx |
MALICIOUS
Pikabot has been detected
- rundll32.exe (PID: 2660)
Drops the executable file immediately after the start
- AteraAgent.exe (PID: 3720)
- AgentPackageTicketing.exe (PID: 4900)
- AteraAgent.exe (PID: 980)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- SplashtopStreamer.exe (PID: 2564)
- PreVerCheck.exe (PID: 2468)
- uninst.exe (PID: 2308)
- Au_.exe (PID: 2192)
Creates a writable file in the system directory
- AteraAgent.exe (PID: 3720)
- SRManager.exe (PID: 5664)
- SRServer.exe (PID: 5924)
Accesses system services(Win32_Service) via WMI (SCRIPT)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 2660)
- AteraAgent.exe (PID: 3720)
- AteraAgent.exe (PID: 980)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- AgentPackageTicketing.exe (PID: 4900)
- PreVerCheck.exe (PID: 2468)
- SplashtopStreamer.exe (PID: 2564)
- uninst.exe (PID: 2308)
- Au_.exe (PID: 2192)
Process drops legitimate windows executable
- rundll32.exe (PID: 2660)
- AteraAgent.exe (PID: 3720)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- AteraAgent.exe (PID: 980)
Executes as Windows Service
- AteraAgent.exe (PID: 3720)
- AteraAgent.exe (PID: 980)
- SSUService.exe (PID: 4684)
- SRService.exe (PID: 5824)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 3720)
- AteraAgent.exe (PID: 980)
- cmd.exe (PID: 5856)
- cmd.exe (PID: 5452)
Starts CMD.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 1348)
- AgentPackageAgentInformation.exe (PID: 5220)
- SRServer.exe (PID: 5924)
Searches for installed software
- AgentPackageAgentInformation.exe (PID: 1348)
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 5220)
- AgentPackageProgramManagement.exe (PID: 5488)
The process executes VB scripts
- cmd.exe (PID: 376)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 4376)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 5264)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
- cscript.exe (PID: 4412)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 3204)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 4412)
- cscript.exe (PID: 4568)
- cscript.exe (PID: 5304)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 3204)
Starts itself from another location
- AgentPackageUpgradeAgent.exe (PID: 4748)
- uninst.exe (PID: 2308)
The process creates files with name similar to system file names
- AteraAgent.exe (PID: 980)
- Au_.exe (PID: 2192)
Checks Windows Trust Settings
- SRManager.exe (PID: 5664)
Creates or modifies Windows services
- SRManager.exe (PID: 5664)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3308)
Application launched itself
- firefox.exe (PID: 572)
- firefox.exe (PID: 1264)
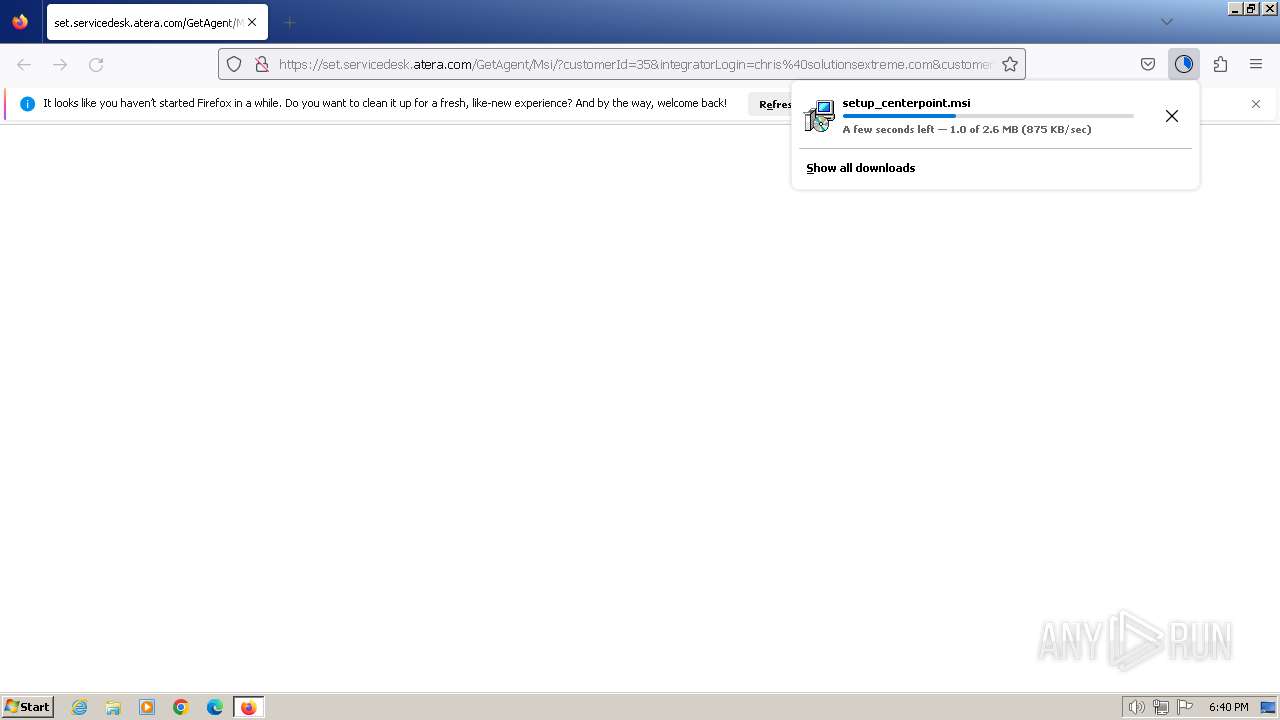
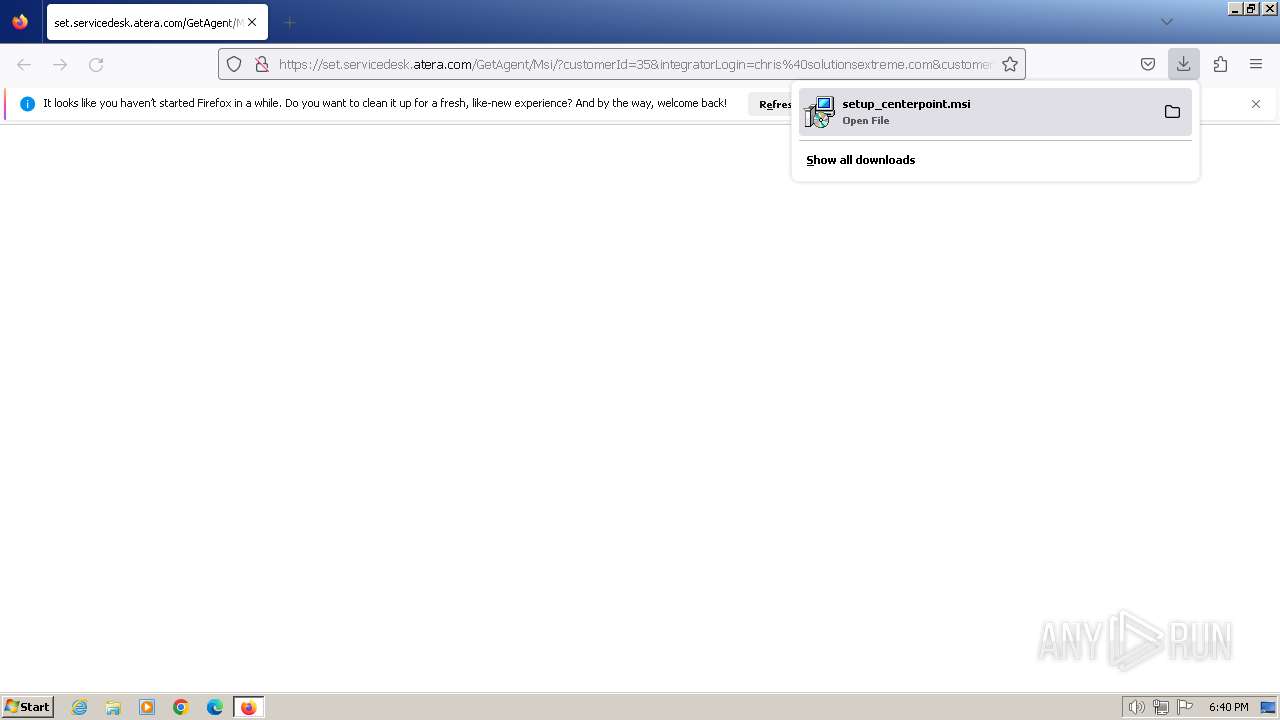
The process uses the downloaded file
- firefox.exe (PID: 1264)
Drops the executable file immediately after the start
- rundll32.exe (PID: 2660)
- firefox.exe (PID: 1264)
Manual execution by a user
- msiexec.exe (PID: 3308)
Create files in a temporary directory
- rundll32.exe (PID: 2660)
Reads the computer name
- AteraAgent.exe (PID: 3720)
- AgentPackageAgentInformation.exe (PID: 916)
- AgentPackageAgentInformation.exe (PID: 3768)
- AgentPackageAgentInformation.exe (PID: 2000)
- AgentPackageAgentInformation.exe (PID: 2108)
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 1348)
- AteraAgent.exe (PID: 980)
- AgentPackageMonitoring.exe (PID: 2124)
- AgentPackageMonitoring.exe (PID: 2296)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- AgentPackageUpgradeAgent.exe (PID: 4780)
- AgentPackageADRemote.exe (PID: 4932)
- AgentPackageTicketing.exe (PID: 4900)
- AgentPackageOsUpdates.exe (PID: 5136)
- AgentPackageInternalPoller.exe (PID: 5012)
- AgentPackageSTRemote.exe (PID: 4820)
- AgentPackageAgentInformation.exe (PID: 5220)
- AgentPackageMonitoring.exe (PID: 5360)
- AgentPackageProgramManagement.exe (PID: 5488)
- AgentPackageHeartbeat.exe (PID: 5520)
- AgentPackageMarketplace.exe (PID: 5596)
- AgentPackageSystemTools.exe (PID: 5756)
- AgentPackageRuntimeInstaller.exe (PID: 5876)
- AgentPackageHeartbeat.exe (PID: 6092)
- AgentPackageHeartbeat.exe (PID: 1928)
- AgentPackageMonitoring.exe (PID: 920)
- AgentPackageHeartbeat.exe (PID: 4392)
- AgentPackageInternalPoller.exe (PID: 4424)
- SplashtopStreamer.exe (PID: 2564)
- SSUService.exe (PID: 4684)
- SRService.exe (PID: 5824)
- SRManager.exe (PID: 5664)
- SRServer.exe (PID: 5924)
- SRAgent.exe (PID: 5400)
- SRFeature.exe (PID: 3032)
- uninst.exe (PID: 2308)
- Au_.exe (PID: 2192)
- SRAppPB.exe (PID: 5952)
Reads Environment values
- AteraAgent.exe (PID: 3720)
- AgentPackageAgentInformation.exe (PID: 916)
- AgentPackageAgentInformation.exe (PID: 2000)
- AgentPackageAgentInformation.exe (PID: 2108)
- AgentPackageAgentInformation.exe (PID: 3768)
- AteraAgent.exe (PID: 980)
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 1348)
- AgentPackageMonitoring.exe (PID: 2124)
- AgentPackageMonitoring.exe (PID: 2296)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- AgentPackageUpgradeAgent.exe (PID: 4780)
- AgentPackageSTRemote.exe (PID: 4820)
- AgentPackageOsUpdates.exe (PID: 5136)
- AgentPackageADRemote.exe (PID: 4932)
- AgentPackageInternalPoller.exe (PID: 5012)
- AgentPackageAgentInformation.exe (PID: 5220)
- AgentPackageProgramManagement.exe (PID: 5488)
- AgentPackageHeartbeat.exe (PID: 5520)
- AgentPackageMonitoring.exe (PID: 5360)
- AgentPackageSystemTools.exe (PID: 5756)
- AgentPackageHeartbeat.exe (PID: 6092)
- AgentPackageMarketplace.exe (PID: 5596)
- AgentPackageHeartbeat.exe (PID: 1928)
- AgentPackageMonitoring.exe (PID: 920)
- AgentPackageHeartbeat.exe (PID: 4392)
- AgentPackageInternalPoller.exe (PID: 4424)
- AgentPackageTicketing.exe (PID: 4900)
Checks supported languages
- AteraAgent.exe (PID: 3720)
- AgentPackageAgentInformation.exe (PID: 916)
- AgentPackageAgentInformation.exe (PID: 2000)
- AgentPackageAgentInformation.exe (PID: 3768)
- AgentPackageAgentInformation.exe (PID: 2108)
- AteraAgent.exe (PID: 980)
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 1348)
- AgentPackageMonitoring.exe (PID: 2124)
- AgentPackageMonitoring.exe (PID: 2296)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- AgentPackageSTRemote.exe (PID: 4820)
- AgentPackageADRemote.exe (PID: 4932)
- AgentPackageInternalPoller.exe (PID: 5012)
- AgentPackageOsUpdates.exe (PID: 5136)
- AgentPackageUpgradeAgent.exe (PID: 4780)
- AgentPackageTicketing.exe (PID: 4900)
- AgentPackageAgentInformation.exe (PID: 5220)
- AgentPackageProgramManagement.exe (PID: 5488)
- AgentPackageHeartbeat.exe (PID: 5520)
- AgentPackageMarketplace.exe (PID: 5596)
- AgentPackageMonitoring.exe (PID: 5360)
- AgentPackageSystemTools.exe (PID: 5756)
- AgentPackageRuntimeInstaller.exe (PID: 5876)
- AgentPackageHeartbeat.exe (PID: 6092)
- AgentPackageHeartbeat.exe (PID: 1928)
- AgentPackageMonitoring.exe (PID: 920)
- AgentPackageInternalPoller.exe (PID: 4424)
- AgentPackageHeartbeat.exe (PID: 4392)
- SSUService.exe (PID: 4684)
- SRService.exe (PID: 5824)
- SRManager.exe (PID: 5664)
- SplashtopStreamer.exe (PID: 2564)
- PreVerCheck.exe (PID: 2468)
- SRServer.exe (PID: 5924)
- SRAgent.exe (PID: 5400)
- SRDetect.exe (PID: 4316)
- SRUtility.exe (PID: 1956)
- uninst.exe (PID: 2308)
- Au_.exe (PID: 2192)
- SRAppPB.exe (PID: 5952)
- SRFeature.exe (PID: 3032)
- SRUtility.exe (PID: 6132)
- BdEpSDK_x86.exe (PID: 6116)
Executable content was dropped or overwritten
- firefox.exe (PID: 1264)
Reads the machine GUID from the registry
- AteraAgent.exe (PID: 3720)
- AgentPackageAgentInformation.exe (PID: 916)
- AgentPackageAgentInformation.exe (PID: 3768)
- AgentPackageAgentInformation.exe (PID: 2000)
- AgentPackageAgentInformation.exe (PID: 2108)
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 1348)
- AteraAgent.exe (PID: 980)
- AgentPackageMonitoring.exe (PID: 2124)
- AgentPackageMonitoring.exe (PID: 2296)
- AgentPackageUpgradeAgent.exe (PID: 4780)
- AgentPackageSTRemote.exe (PID: 4820)
- AgentPackageUpgradeAgent.exe (PID: 4748)
- AgentPackageTicketing.exe (PID: 4900)
- AgentPackageADRemote.exe (PID: 4932)
- AgentPackageInternalPoller.exe (PID: 5012)
- AgentPackageOsUpdates.exe (PID: 5136)
- AgentPackageAgentInformation.exe (PID: 5220)
- AgentPackageMonitoring.exe (PID: 5360)
- AgentPackageProgramManagement.exe (PID: 5488)
- AgentPackageHeartbeat.exe (PID: 5520)
- AgentPackageMarketplace.exe (PID: 5596)
- AgentPackageSystemTools.exe (PID: 5756)
- AgentPackageRuntimeInstaller.exe (PID: 5876)
- AgentPackageHeartbeat.exe (PID: 6092)
- AgentPackageHeartbeat.exe (PID: 1928)
- AgentPackageMonitoring.exe (PID: 920)
- AgentPackageHeartbeat.exe (PID: 4392)
- AgentPackageInternalPoller.exe (PID: 4424)
- SSUService.exe (PID: 4684)
- SRManager.exe (PID: 5664)
- SRAgent.exe (PID: 5400)
Creates files in the program directory
- AteraAgent.exe (PID: 3720)
- AgentPackageMonitoring.exe (PID: 2124)
- AgentPackageMonitoring.exe (PID: 2296)
- AgentPackageAgentInformation.exe (PID: 1348)
- AgentPackageAgentInformation.exe (PID: 3504)
- AteraAgent.exe (PID: 980)
- AgentPackageTicketing.exe (PID: 4900)
- AgentPackageSTRemote.exe (PID: 4820)
- AgentPackageInternalPoller.exe (PID: 5012)
- AgentPackageOsUpdates.exe (PID: 5136)
- AgentPackageMonitoring.exe (PID: 5360)
- AgentPackageAgentInformation.exe (PID: 5220)
- AgentPackageProgramManagement.exe (PID: 5488)
- AgentPackageRuntimeInstaller.exe (PID: 5876)
- AgentPackageMonitoring.exe (PID: 920)
- SRManager.exe (PID: 5664)
- SRServer.exe (PID: 5924)
- SRAgent.exe (PID: 5400)
Reads Microsoft Office registry keys
- AgentPackageAgentInformation.exe (PID: 3504)
- AgentPackageAgentInformation.exe (PID: 1348)
- AgentPackageAgentInformation.exe (PID: 5220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
205
Monitored processes
76
Malicious processes
20
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Windows\System32\cmd.exe" /c cscript "C:\Program Files\Microsoft Office\Office14\ospp.vbs" /dstatus | C:\Windows\System32\cmd.exe | — | AgentPackageAgentInformation.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://set.servicedesk.atera.com/GetAgent/Msi/?customerId=35&integratorLogin=chris%40solutionsextreme.com&customerName=Centerpoint&accountId=0013z00002LHg1NAAT" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 916 | "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe" 99694ce7-4e33-492e-825c-4312a2d2933c "0a98b9bf-54b1-40a2-b5aa-6a475935599f" agent-api.atera.com/Production 443 or8ixLi90Mf "minimalIdentification" | C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageAgentInformation Exit code: 0 Version: 36.0.0.0 Modules
| |||||||||||||||
| 920 | "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\AgentPackageMonitoring.exe" 99694ce7-4e33-492e-825c-4312a2d2933c "11829445-d132-463d-9a97-ba76980d707b" agent-api.atera.com/Production 443 or8ixLi90Mf "monitor" | C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\AgentPackageMonitoring.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: AgentPackageMonitoring Exit code: 0 Version: 36.3.0.0 Modules
| |||||||||||||||
| 980 | "C:\Program Files\ATERA Networks\AteraAgent\AteraAgent.exe" | C:\Program Files\ATERA Networks\AteraAgent\AteraAgent.exe | services.exe | ||||||||||||
User: SYSTEM Company: ATERA Networks Ltd. Integrity Level: SYSTEM Description: AteraAgent Exit code: 0 Version: 1.8.6.7 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1264.0.711760780\150868849" -parentBuildID 20230710165010 -prefsHandle 1124 -prefMapHandle 1116 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {eadd62e8-3524-450c-8615-b1cb249f4f29} 1264 "\\.\pipe\gecko-crash-server-pipe.1264" 1196 daac1a0 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://set.servicedesk.atera.com/GetAgent/Msi/?customerId=35&integratorLogin=chris%40solutionsextreme.com&customerName=Centerpoint&accountId=0013z00002LHg1NAAT | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe" 99694ce7-4e33-492e-825c-4312a2d2933c "fc9e09da-bd35-4523-83b7-a52f1234c68c" agent-api.atera.com/Production 443 or8ixLi90Mf "generalinfo fromGui" | C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageAgentInformation Exit code: 0 Version: 36.0.0.0 Modules
| |||||||||||||||
| 1824 | "C:\Windows\System32\sc.exe" failure AteraAgent reset= 600 actions= restart/25000 | C:\Windows\System32\sc.exe | — | AteraAgent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageHeartbeat\AgentPackageHeartbeat.exe" 99694ce7-4e33-492e-825c-4312a2d2933c "982c33e7-c431-4a53-9300-c609b4065f80" agent-api.atera.com/Production 443 or8ixLi90Mf "heartbeat" | C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageHeartbeat\AgentPackageHeartbeat.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageHeartbeat Exit code: 0 Version: 17.11.0.0 Modules
| |||||||||||||||
Total events
101 476
Read events
101 000
Write events
468
Delete events
8
Modification events
| (PID) Process: | (572) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2166C0A101000000 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 044CC1A101000000 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SetDefaultBrowserUserChoice |
Value: 1 | |||
| (PID) Process: | (1264) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|AppLastRunTime |
Value: D14E5F3C23B0D901 | |||
Executable files
441
Suspicious files
229
Text files
103
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | binary | |
MD5:2A9F3DFAD414D2610FEF703D432282DD | SHA256:E4656DBCFE146D1EF160C27B12F2DE7E84FD2AC45041FD502A41B5BB8313CCA1 | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\targeting.snapshot.json.tmp | binary | |
MD5:54072529116C993B984F5E696A1A9632 | SHA256:F18B53D8F4FF0F600E68A93CC6BD50E12396AF46B0ACD5559E662BD13600808E | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\targeting.snapshot.json | binary | |
MD5:54072529116C993B984F5E696A1A9632 | SHA256:F18B53D8F4FF0F600E68A93CC6BD50E12396AF46B0ACD5559E662BD13600808E | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\datareporting\glean\db\data.safe.bin | dbf | |
MD5:B1C8AA9861B461806C9E738511EDD6AE | SHA256:7CEA48E7ADD3340B36F47BA4EA2DED8D6CB0423FFC2A64B44D7E86E0507D6B70 | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db-journal | binary | |
MD5:315045087B88CAA891A8C8CA0BFC3168 | SHA256:653B3B399DD5DC01A7463C09C83B20190F25CAEE225263DCDBE63AA97FC486CE | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:4C2B86263D45AF8D9CFB3E8B677F9B8F | SHA256:EBA507A22A506819B3C8104DA66604A94F85CB746293F4F34201D9897A4B058F | |||
| 1264 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
116
DNS requests
200
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1264 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
1264 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.76:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.76:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.76:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.76:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1264 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1264 | firefox.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
1264 | firefox.exe | 20.101.44.219:443 | set.servicedesk.atera.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1264 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1264 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
1264 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | unknown |
1264 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | unknown |
1264 | firefox.exe | 184.24.77.76:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
set.servicedesk.atera.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
firefox.settings.services.mozilla.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
servicedesk-eu.westeurope.cloudapp.azure.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Splashtop Domain in DNS Lookup (splashtop .com) |
4820 | AgentPackageSTRemote.exe | Misc activity | ET INFO Splashtop Domain (splashtop .com) in TLS SNI |
1080 | svchost.exe | Misc activity | ET INFO Splashtop Domain in DNS Lookup (splashtop .com) |
4820 | AgentPackageSTRemote.exe | Misc activity | ET INFO Splashtop Domain (splashtop .com) in TLS SNI |
1080 | svchost.exe | Misc activity | ET INFO Splashtop Domain in DNS Lookup (splashtop .com) |
1080 | svchost.exe | Misc activity | ET INFO Splashtop Domain in DNS Lookup (splashtop .com) |
29 ETPRO signatures available at the full report
Process | Message |
|---|---|
AgentPackageMonitoring.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\x86\SQLite.Interop.dll"...
|
AgentPackageMonitoring.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\x86\SQLite.Interop.dll"...
|
AgentPackageMonitoring.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\x86\SQLite.Interop.dll"...
|
AgentPackageMonitoring.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\x86\SQLite.Interop.dll"...
|
SplashtopStreamer.exe | [2564]2024-02-06 18:45:00 [CUtility::OSInfo] OS 6.1(7601) Service Pack 1 x64:0 (Last=0) |
SplashtopStreamer.exe | [2564]2024-02-06 18:45:00 [CUnPack::FindHeader] Name:C:\Windows\TEMP\SplashtopStreamer.exe (Last=0) |
SplashtopStreamer.exe | [2564]2024-02-06 18:45:00 [CUnPack::FindHeader] Sign Size:10248 (Last=0) |
SplashtopStreamer.exe | [2564]2024-02-06 18:45:00 [CUnPack::FindHeader] Header offset:433664 (Last=183) |
SplashtopStreamer.exe | [2564]2024-02-06 18:45:00 [CUnPack::UnPackFiles] FreeSpace:233127555072 FileSize:51532288 (Last=0) |
SplashtopStreamer.exe | [2564]2024-02-06 18:45:00 [CUnPack::UnPackFiles] (1/5)UnPack file name:C:\Windows\TEMP\unpack\setup.msi (51532288) (Last=0) |