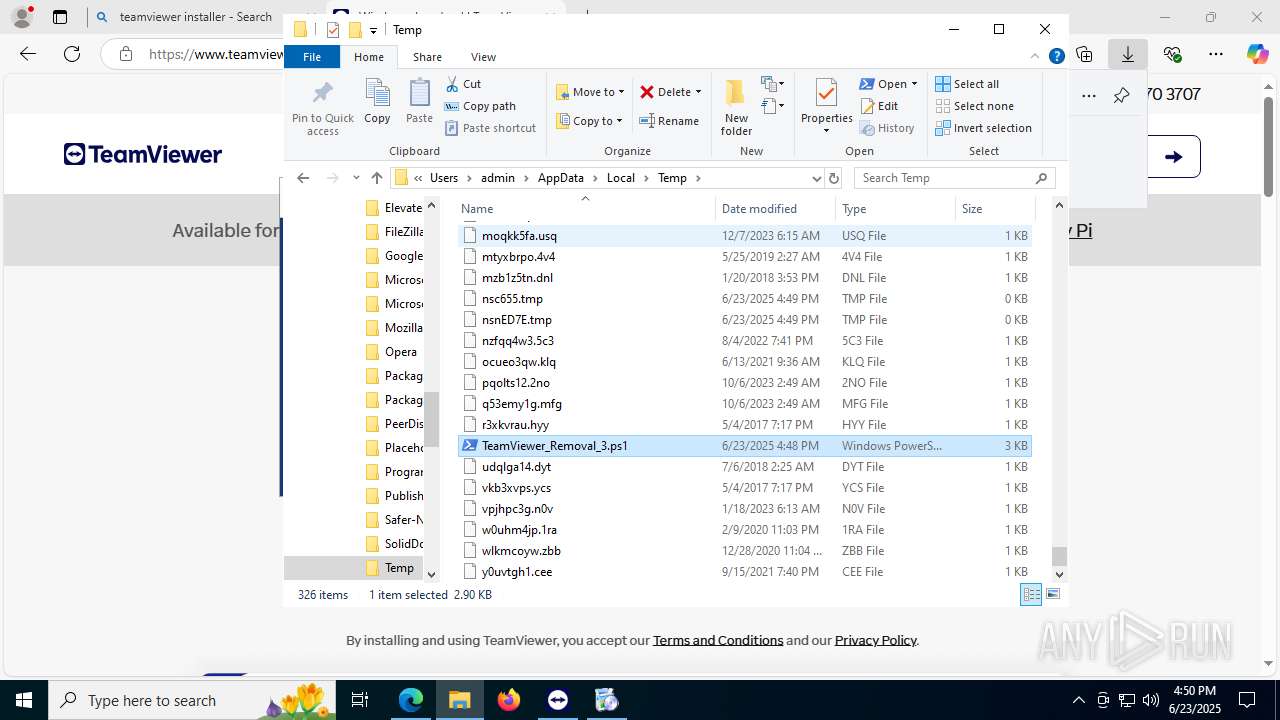
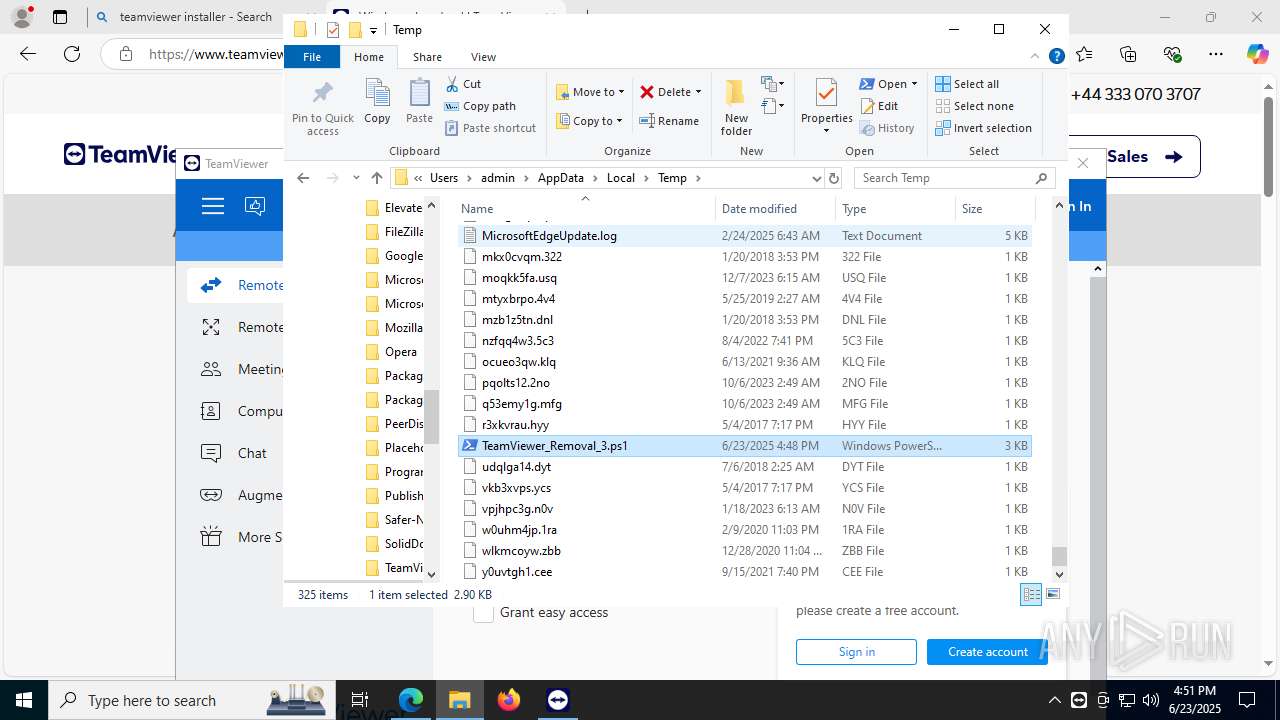
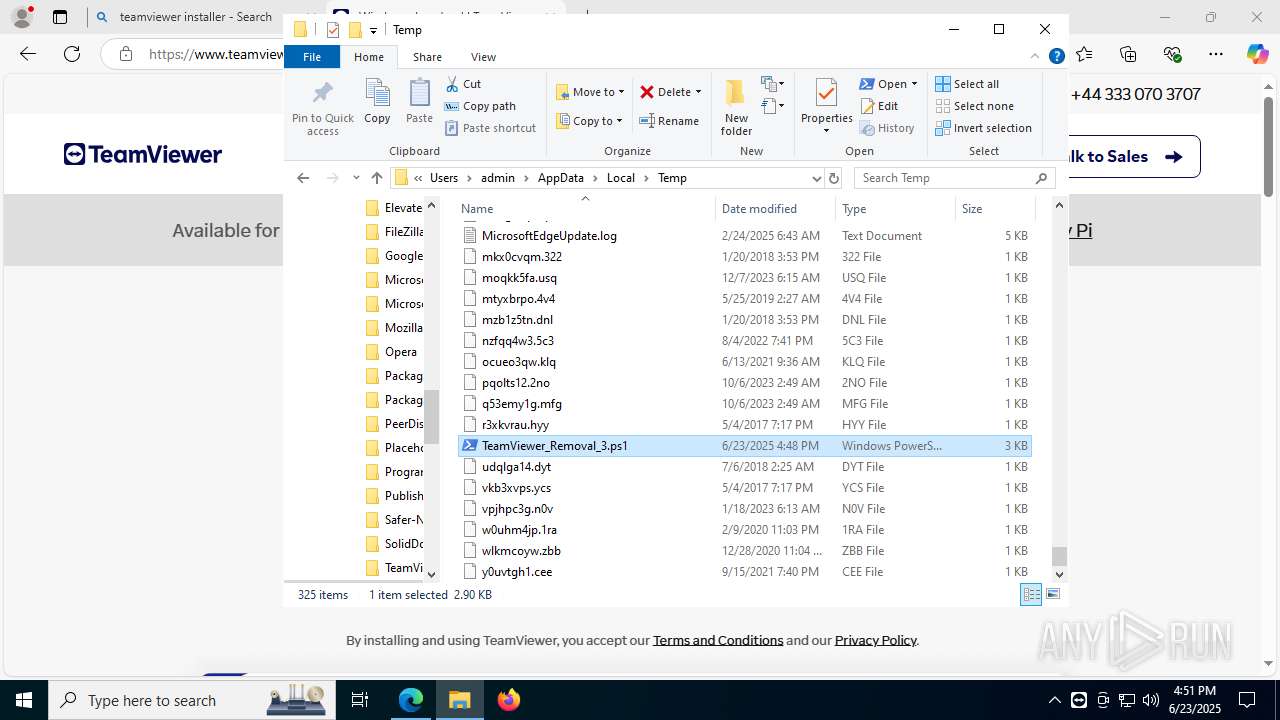
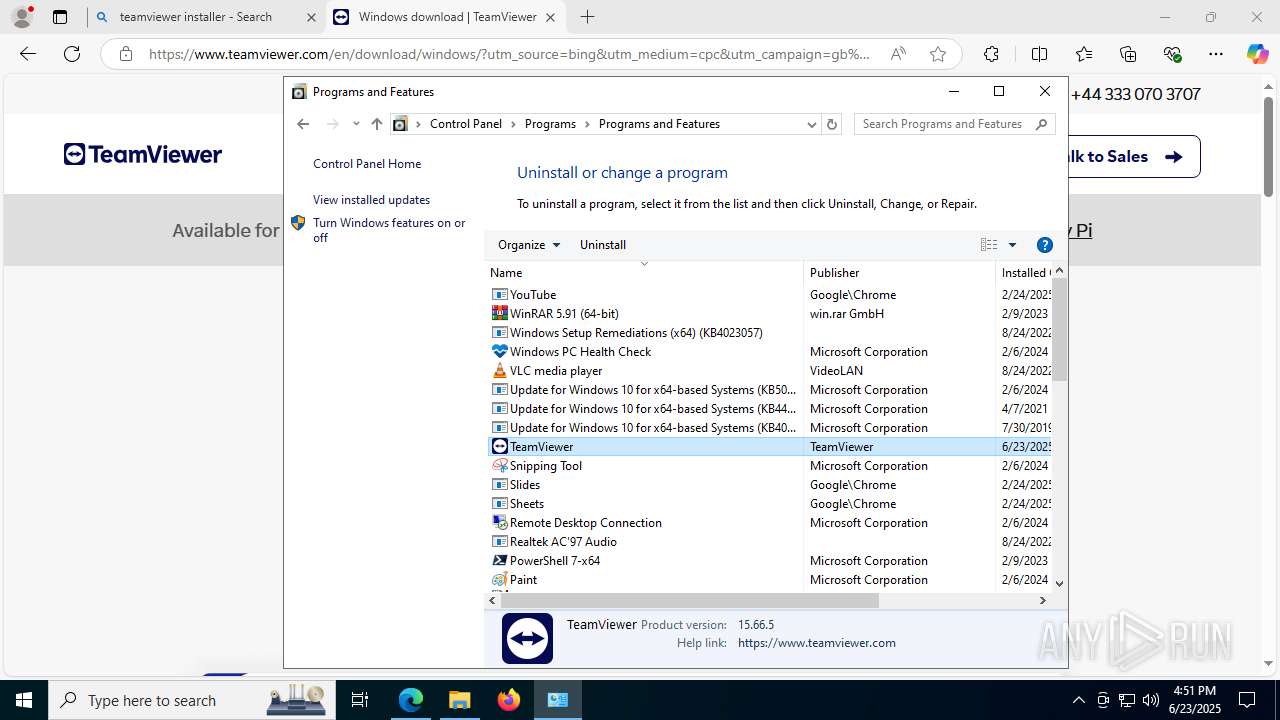
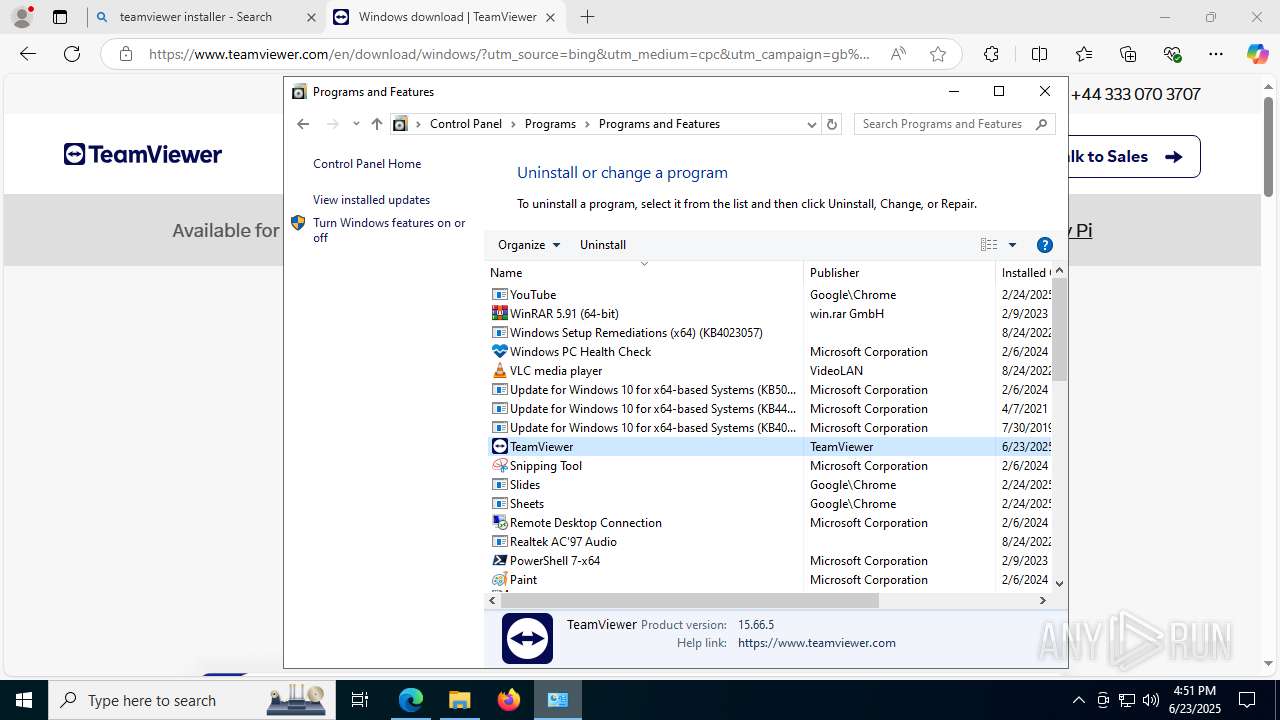
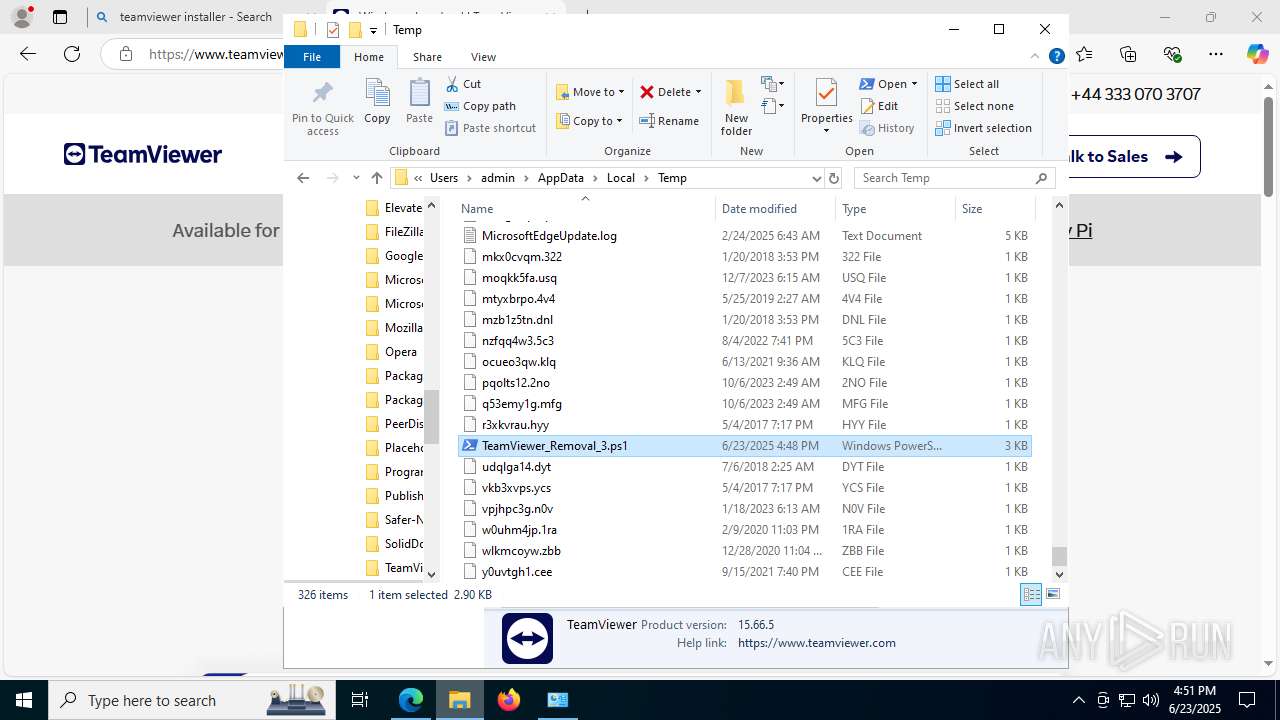
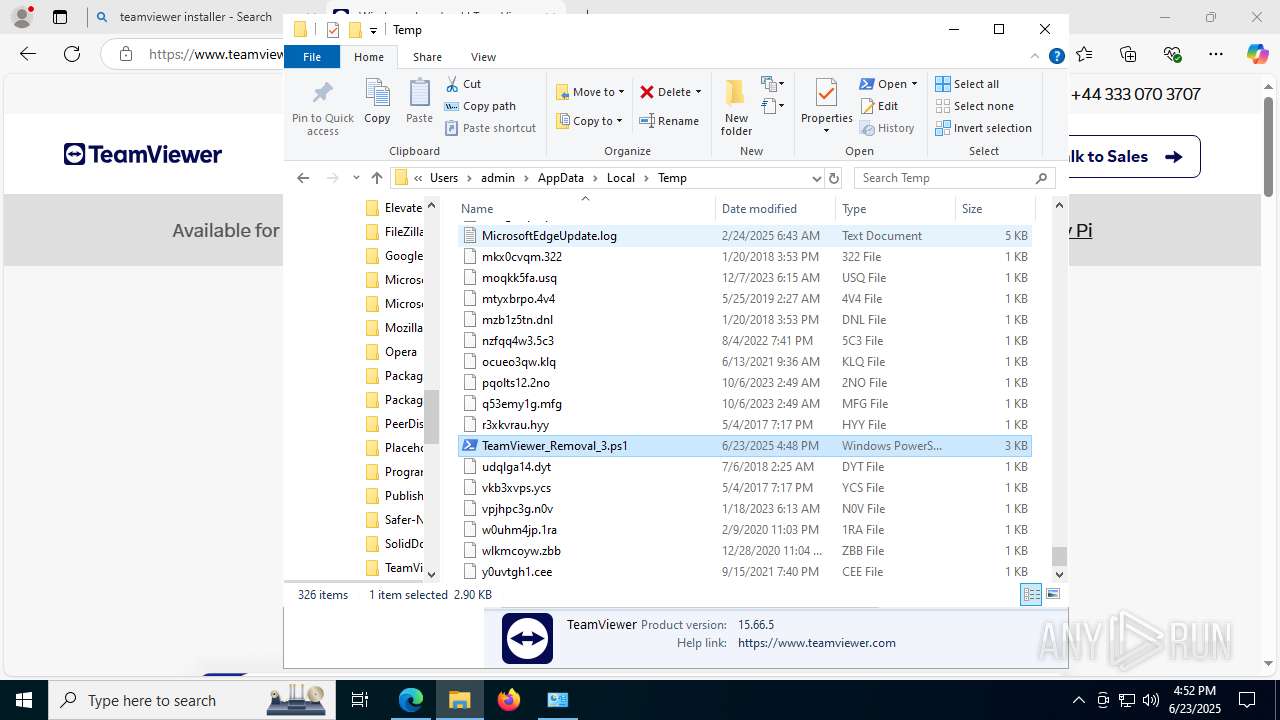
| File name: | TeamViewer_Removal_3.ps1 |
| Full analysis: | https://app.any.run/tasks/abb747c2-b2cc-4d81-8a76-fce25f576a0a |
| Verdict: | Malicious activity |
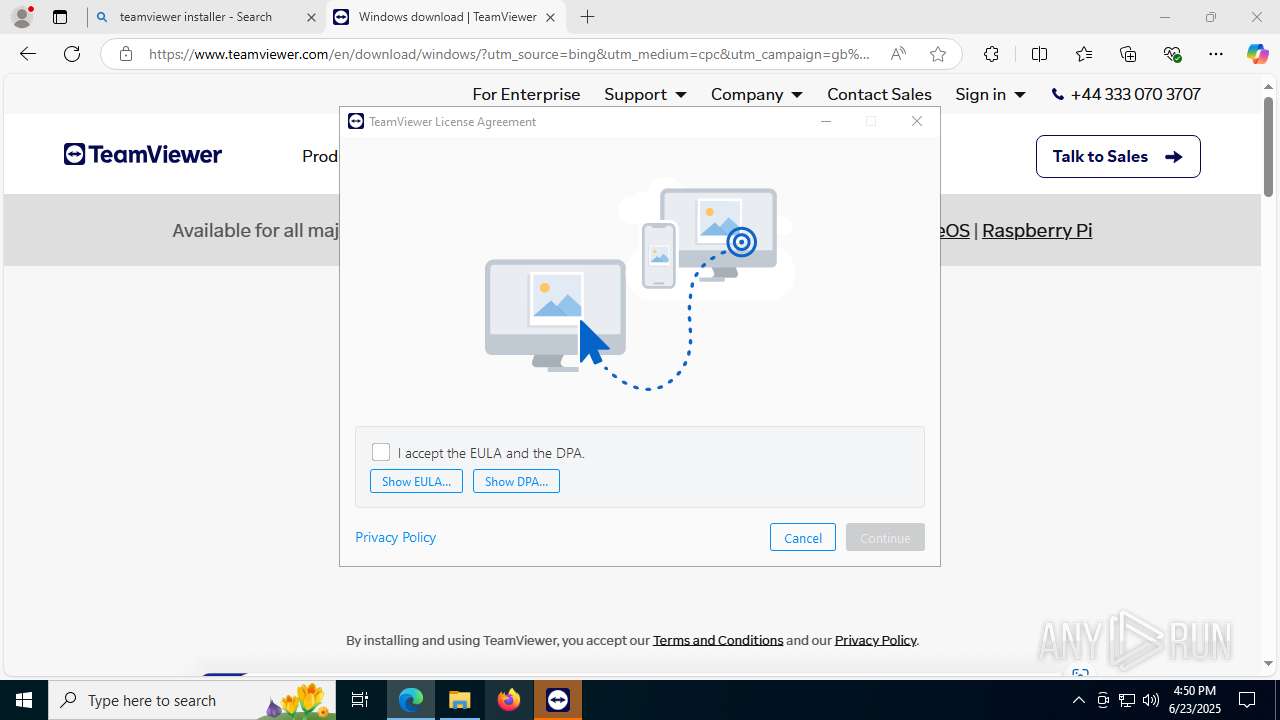
| Threats: | First identified in 2024, Emmenhtal operates by embedding itself within modified legitimate Windows binaries, often using HTA (HTML Application) files to execute malicious scripts. It has been linked to the distribution of malware such as CryptBot and Lumma Stealer. Emmenhtal is typically disseminated through phishing campaigns, including fake video downloads and deceptive email attachments. |
| Analysis date: | June 23, 2025, 16:48:28 |
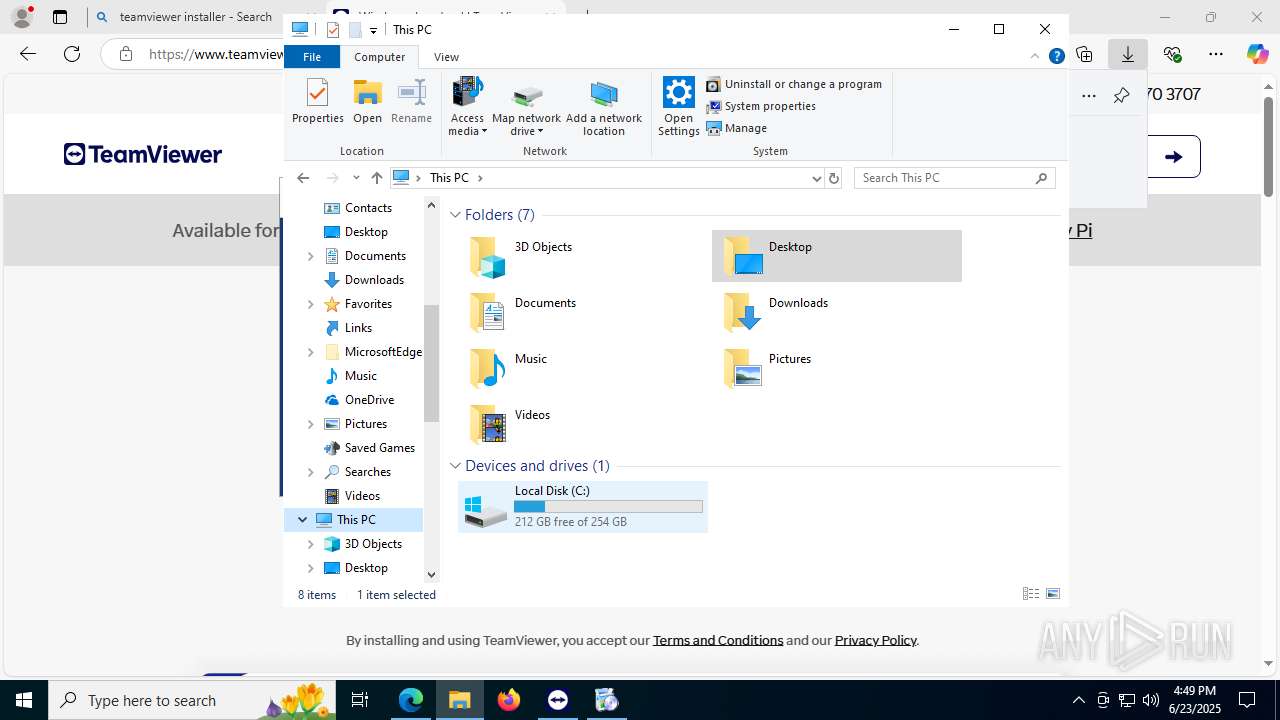
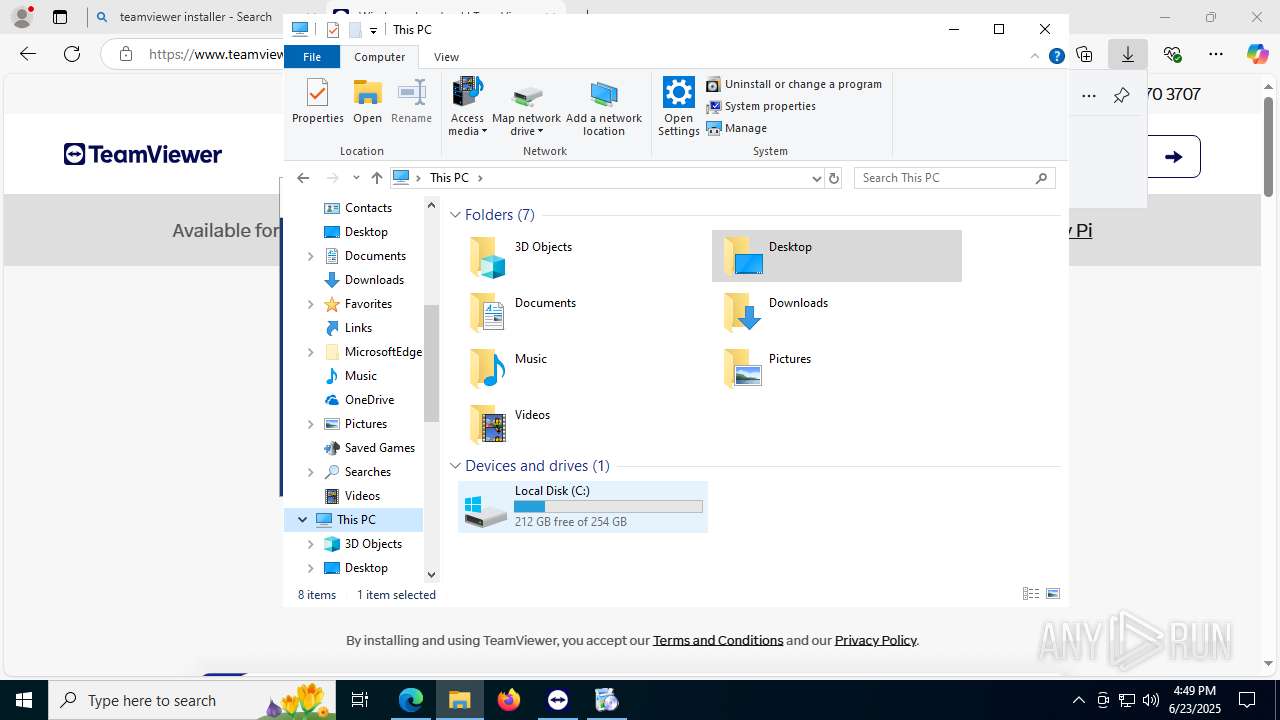
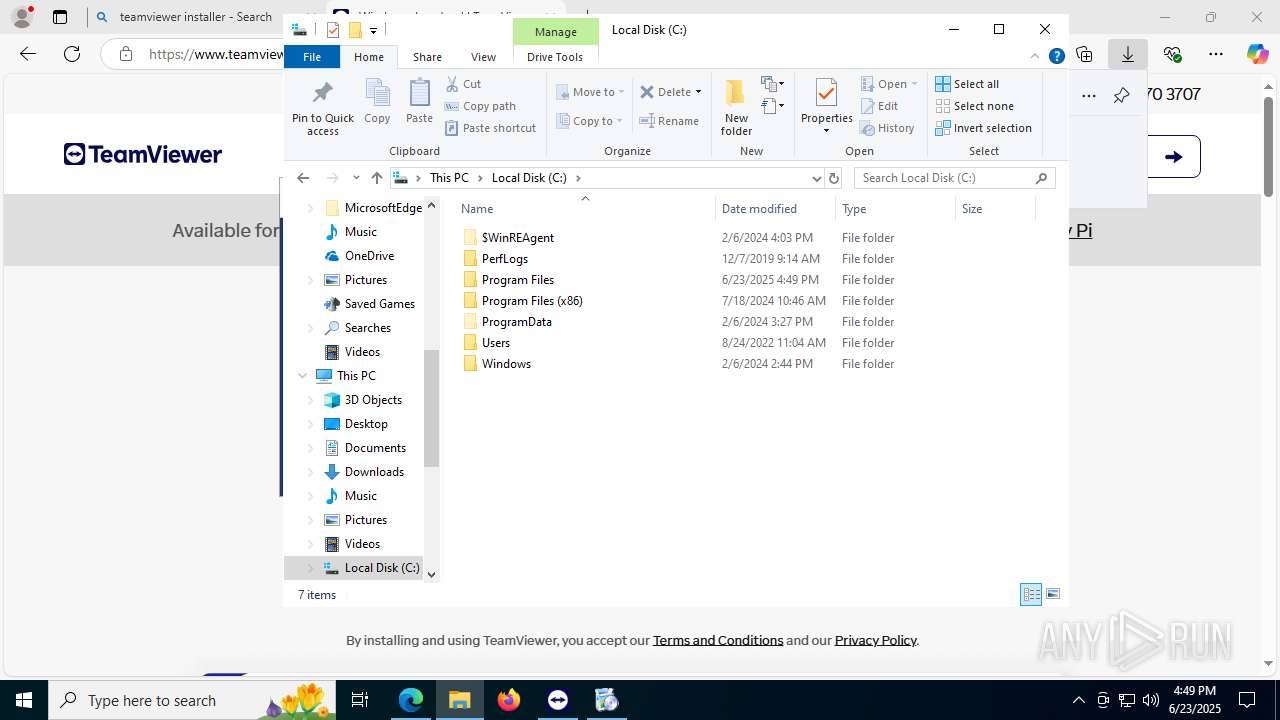
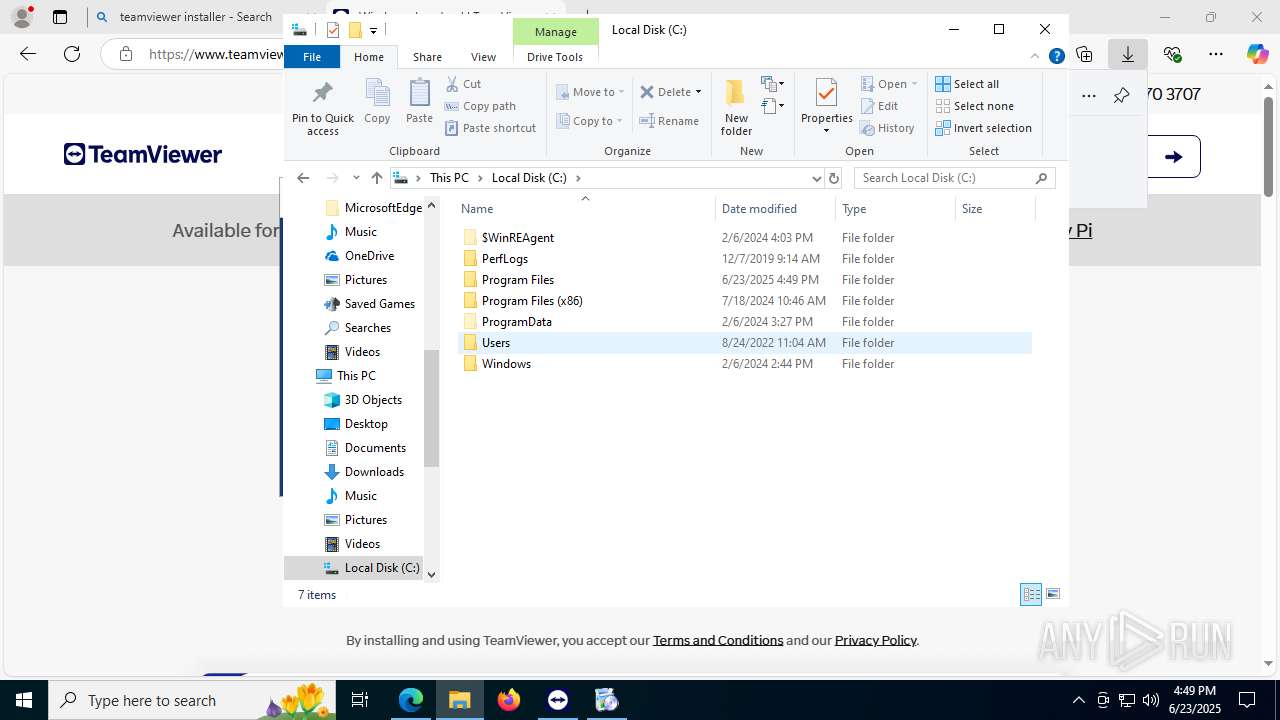
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | 07CF92E29D8745ED1BAAAC8B87FD7EE6 |
| SHA1: | E1070AFFCCDACEC12D816FDC7129F5FA0DD69059 |
| SHA256: | CBBB56829AE34630377B1157322389A3DCFEB33B8D77EA64C12865A243B4A3FE |
| SSDEEP: | 48:mZnbxAADbDDOeiiNOsXb6eY5SuqXlCSzD8g8Qo63AuxRiAjA4vSzDdakRqPQ18R7:gSALYSDum3X4x6wq84KXdh99Xti |
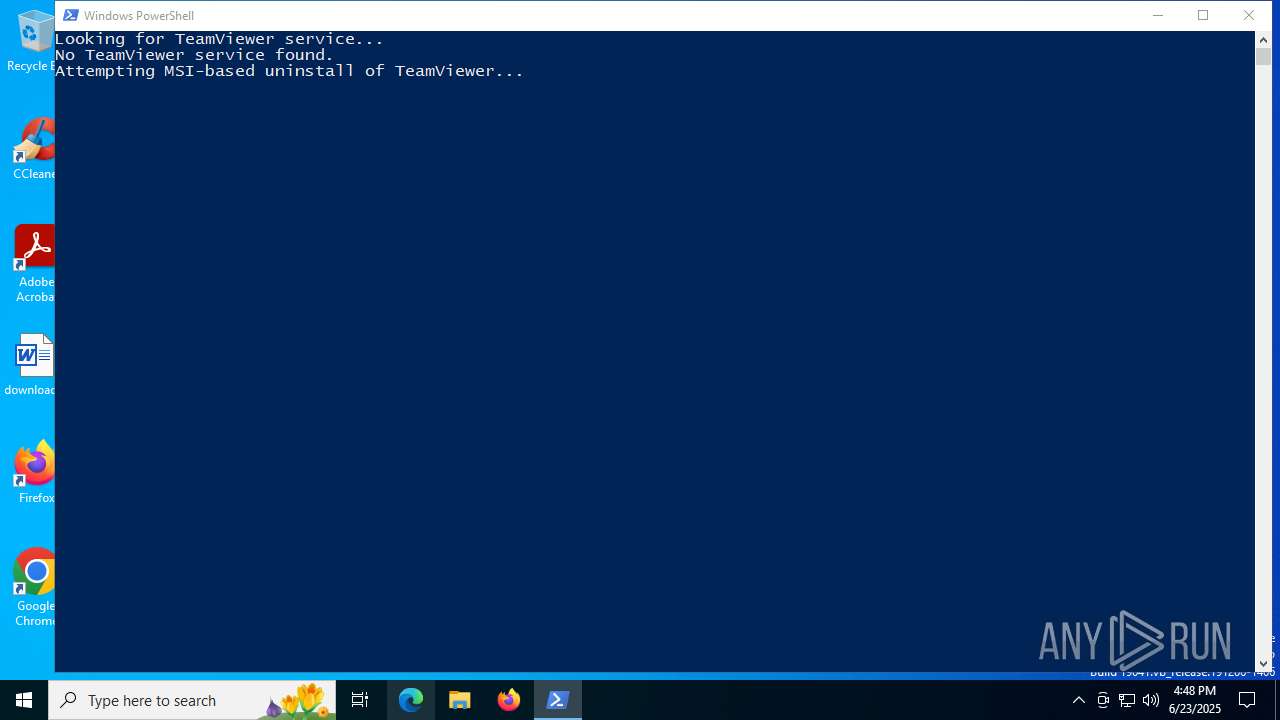
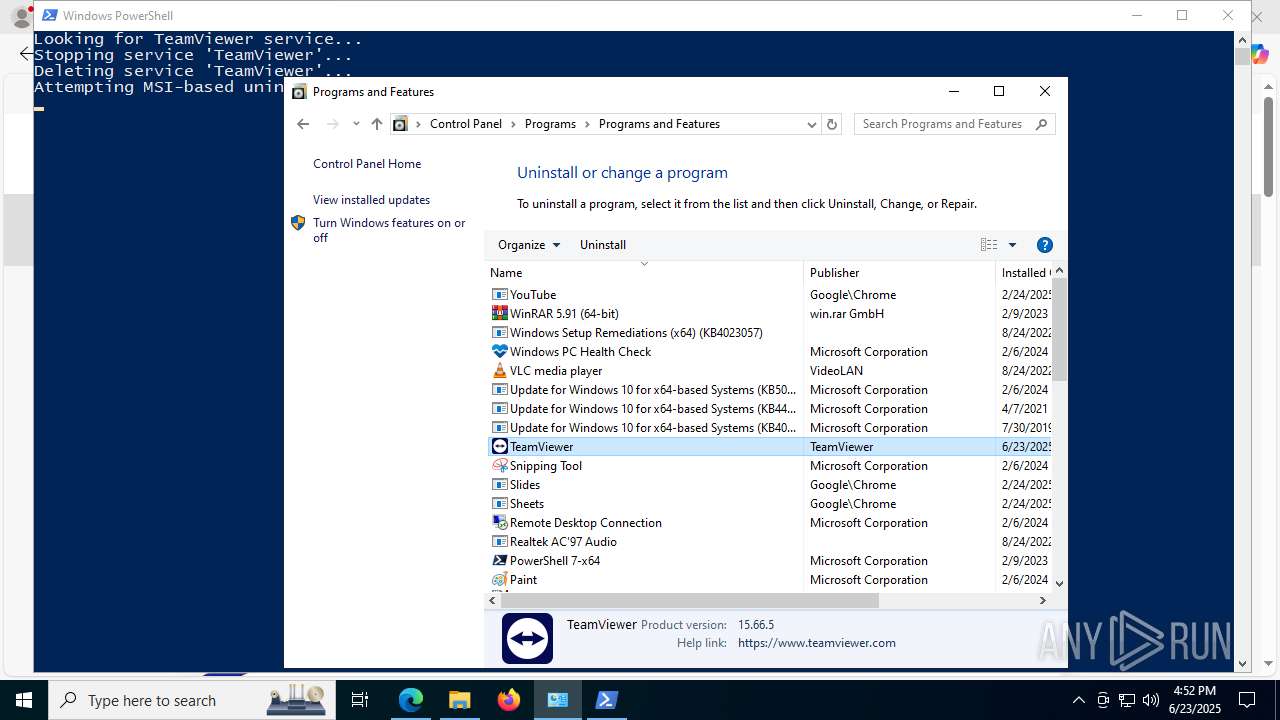
MALICIOUS
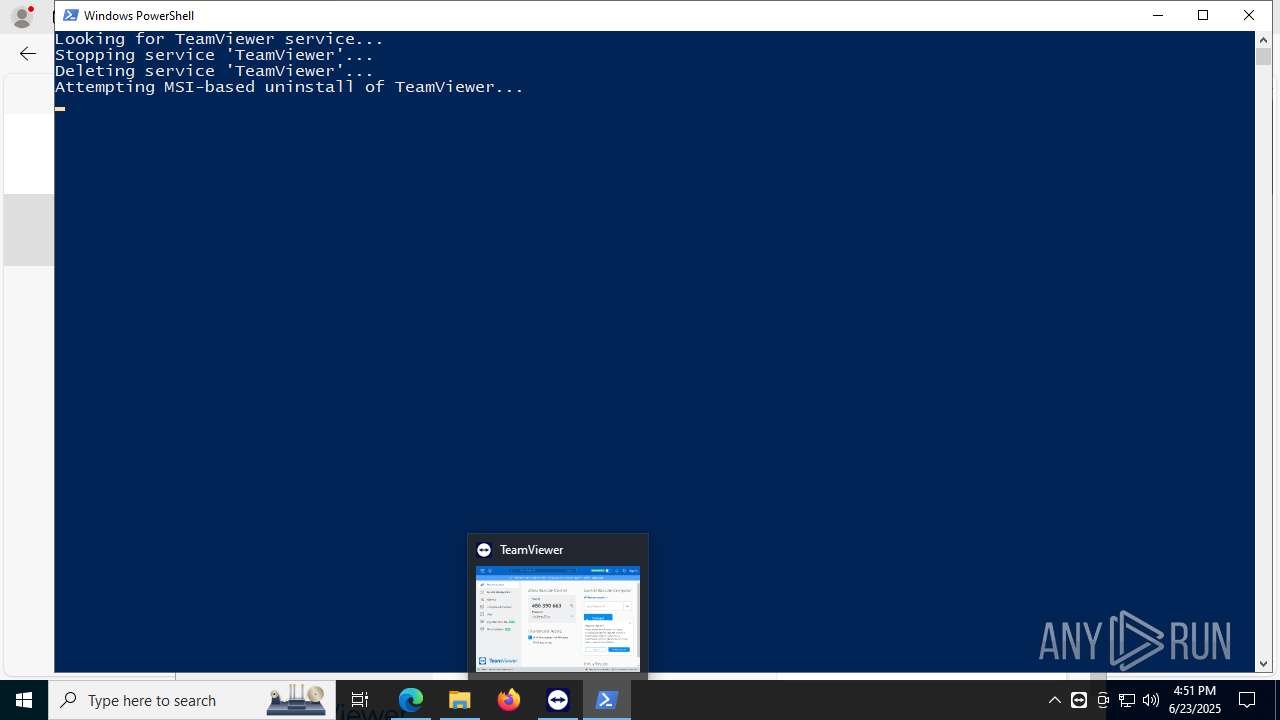
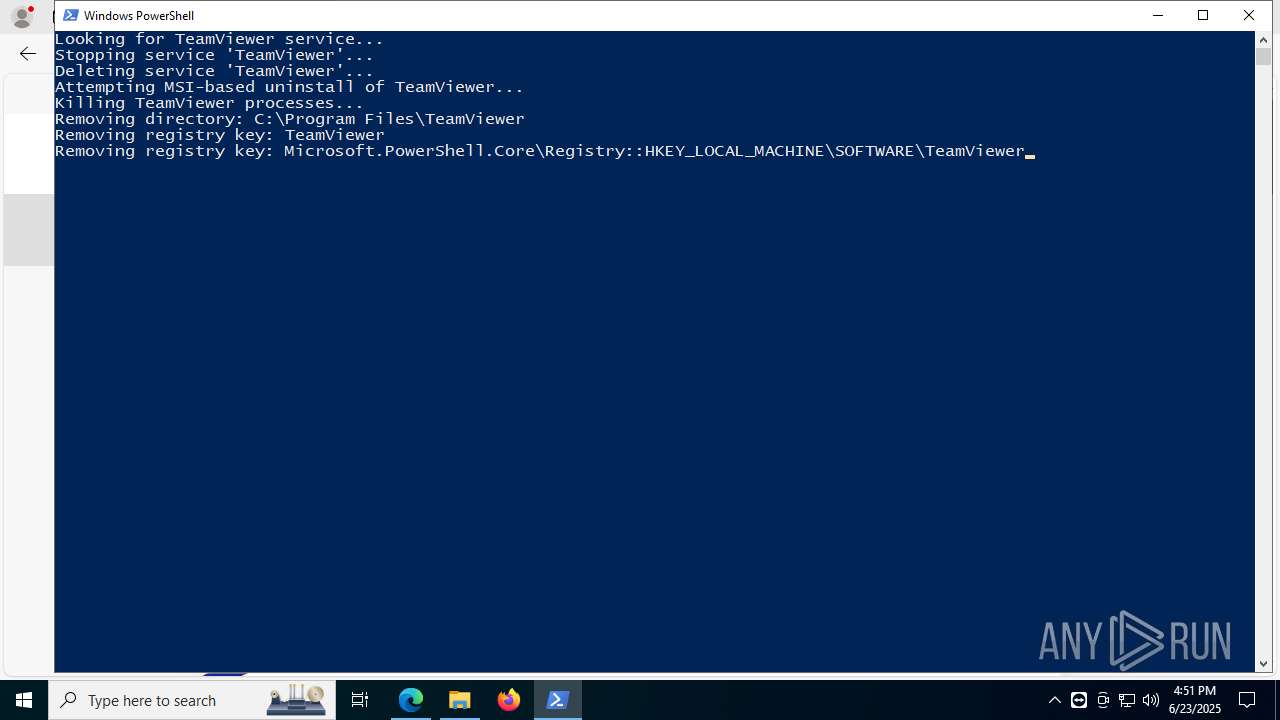
Bypass execution policy to execute commands
- powershell.exe (PID: 2076)
- powershell.exe (PID: 5908)
- powershell.exe (PID: 4984)
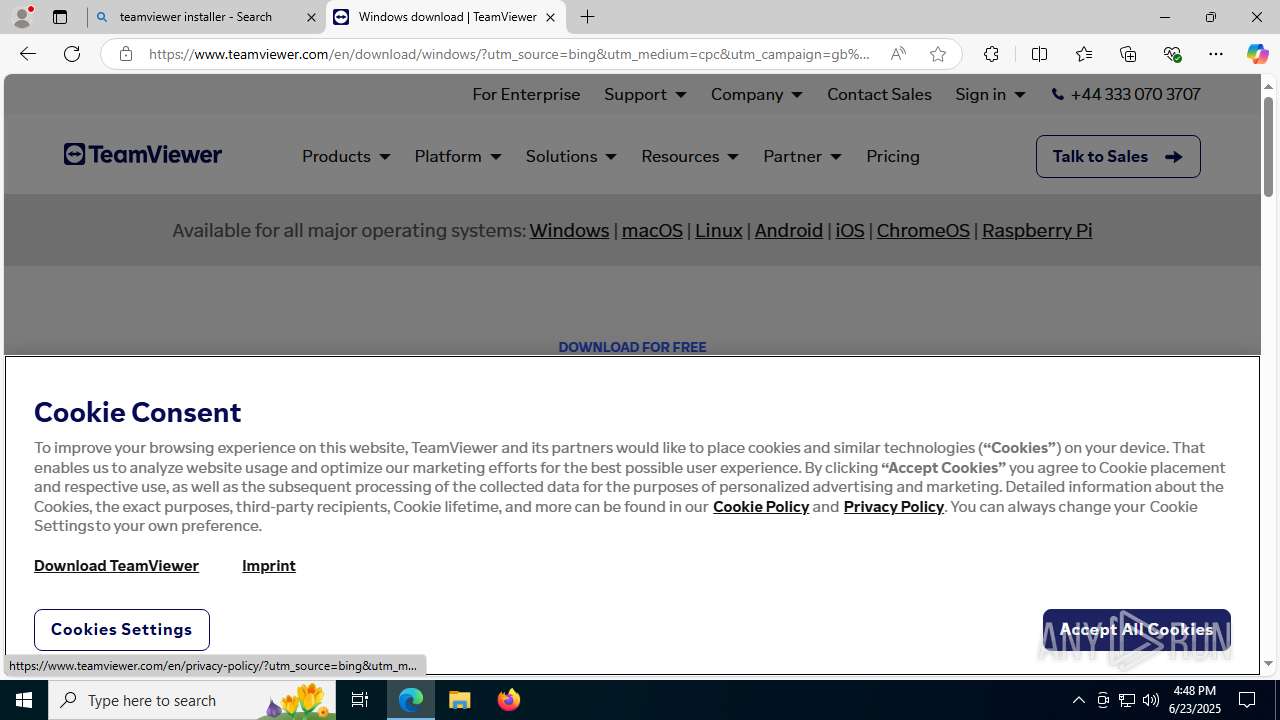
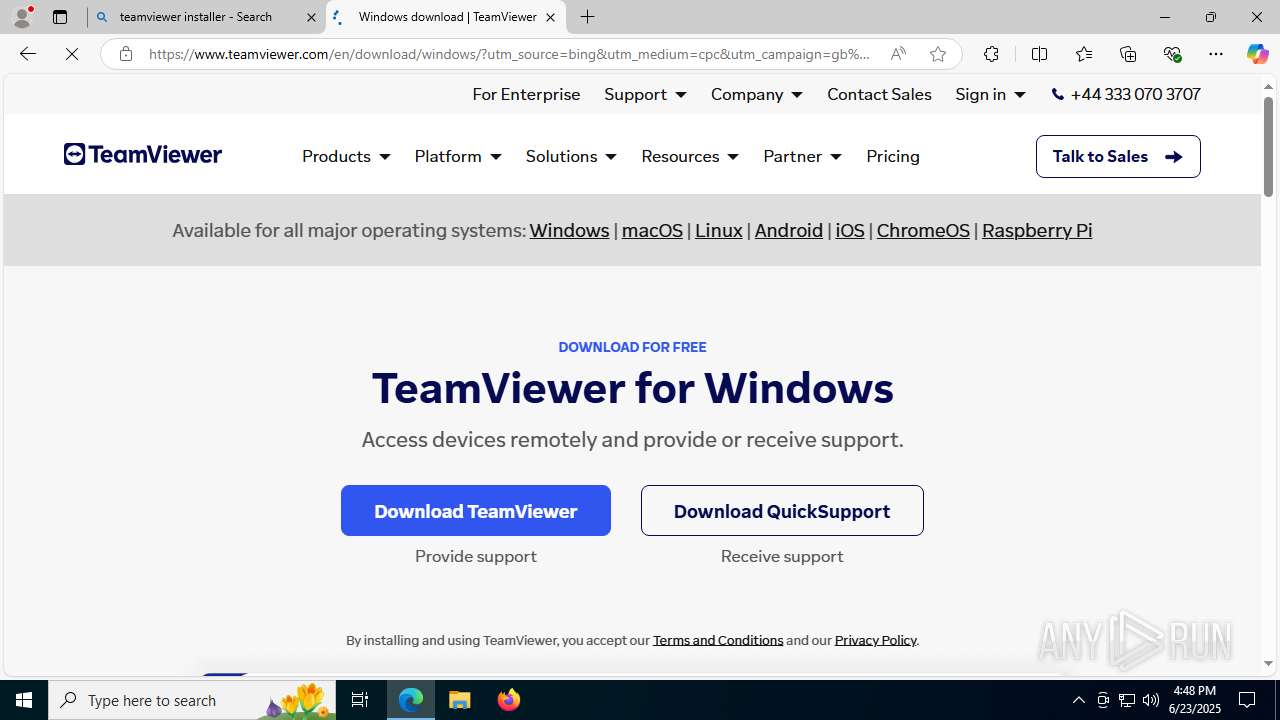
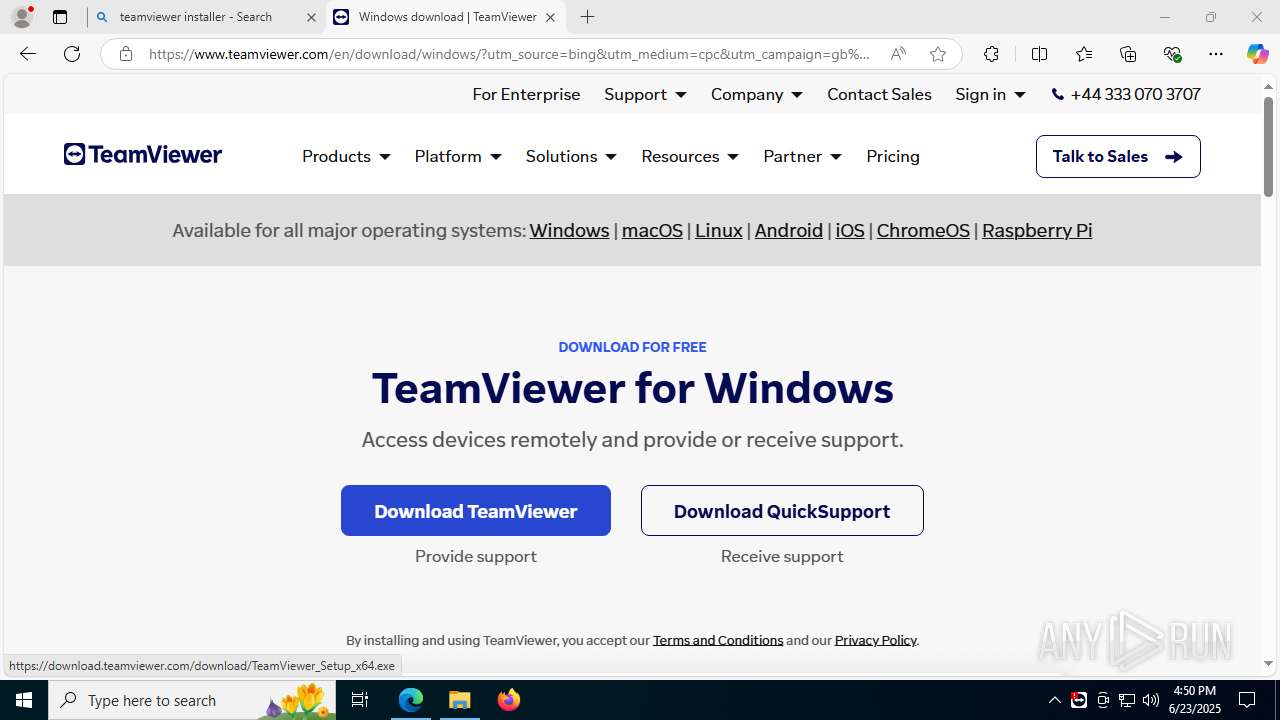
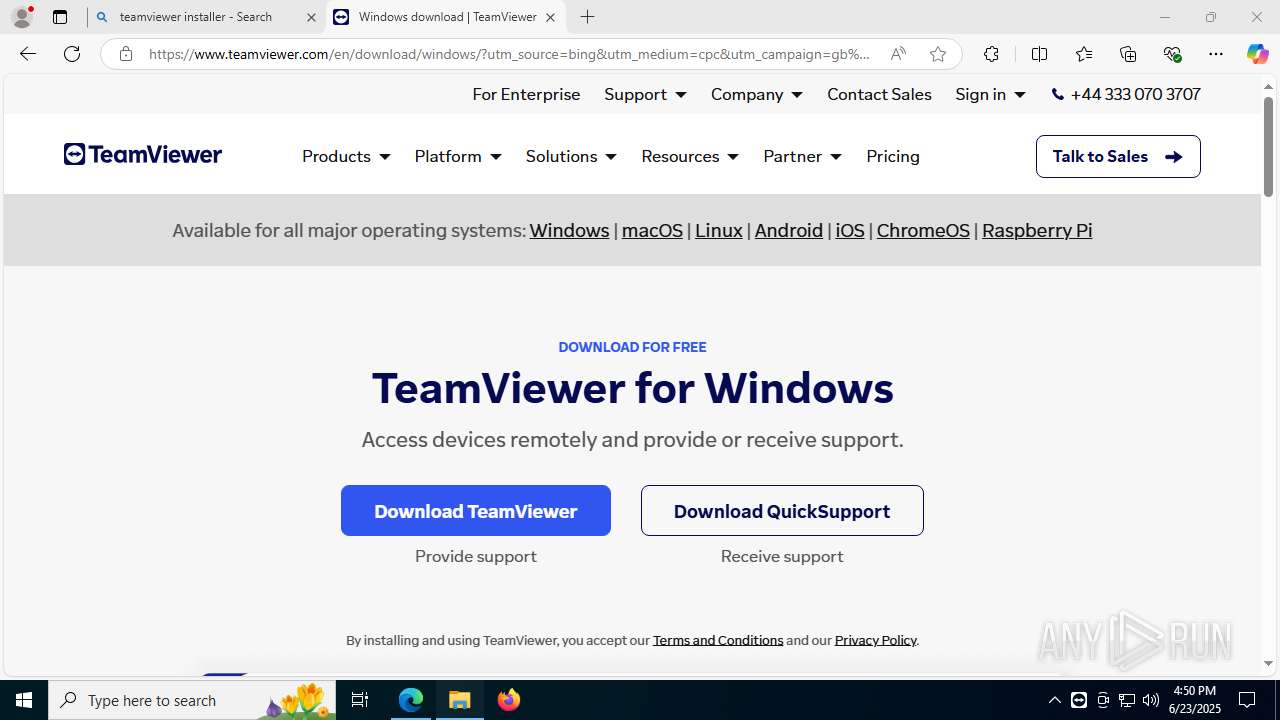
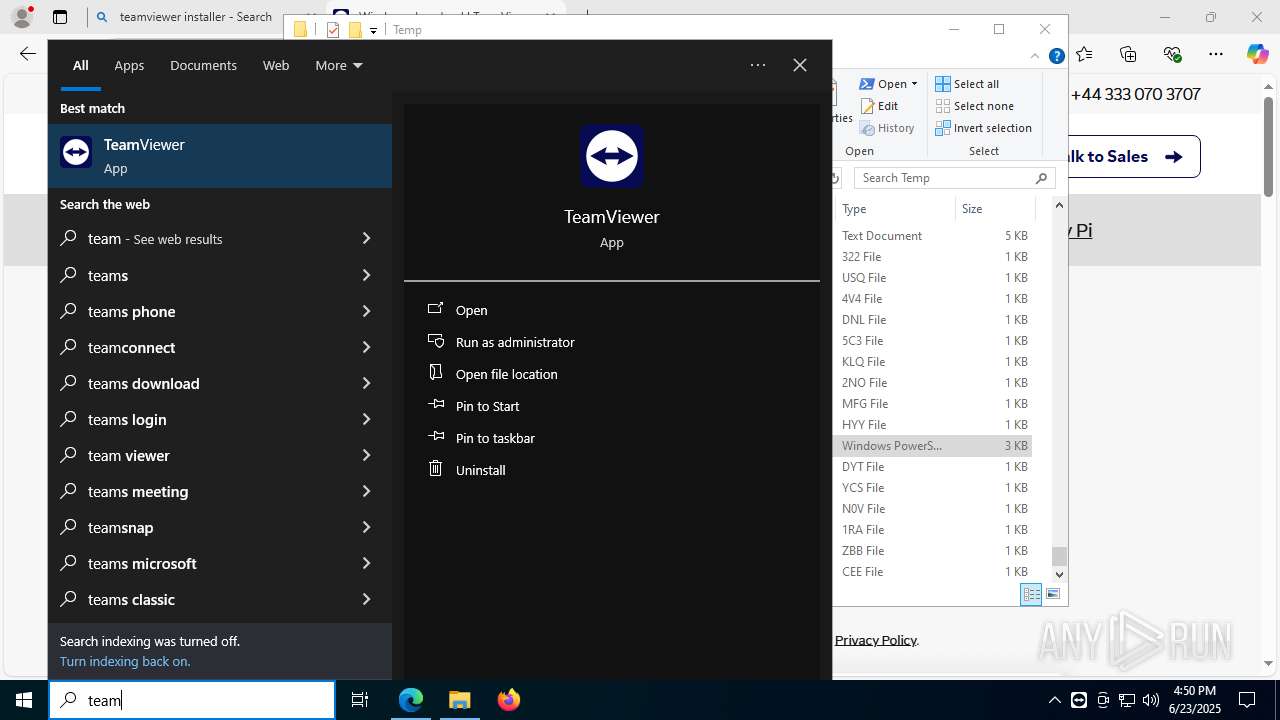
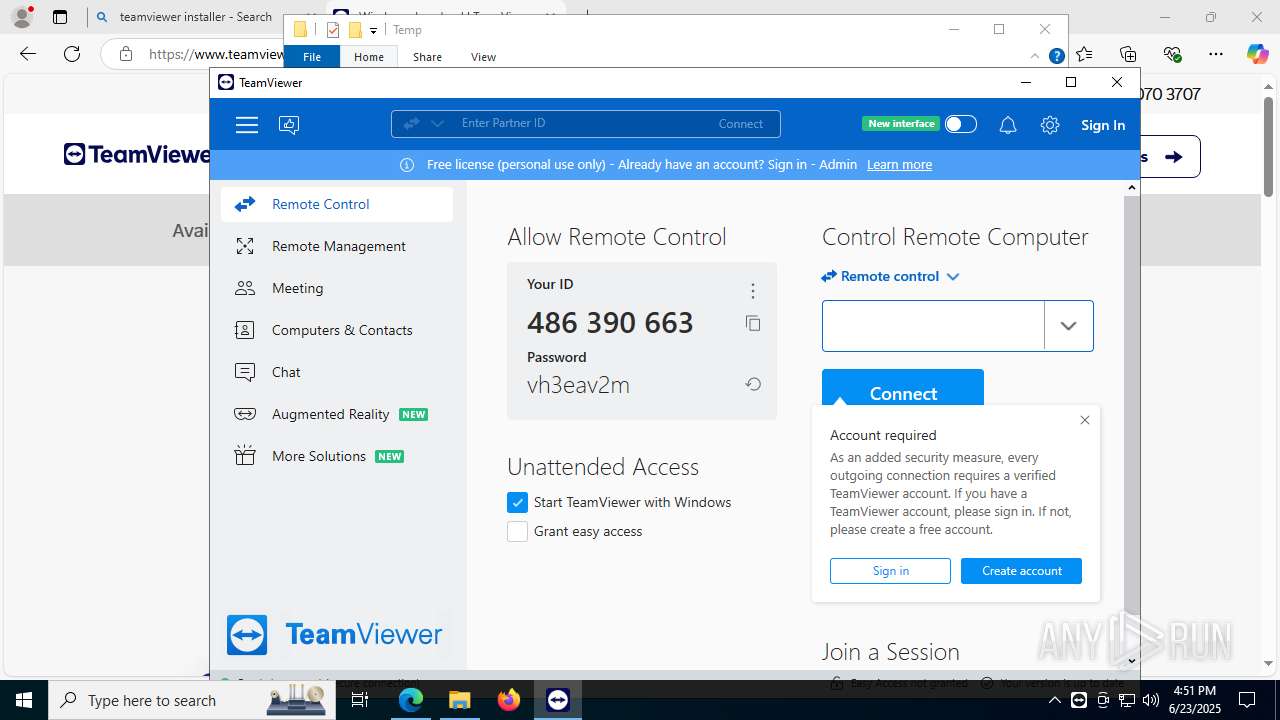
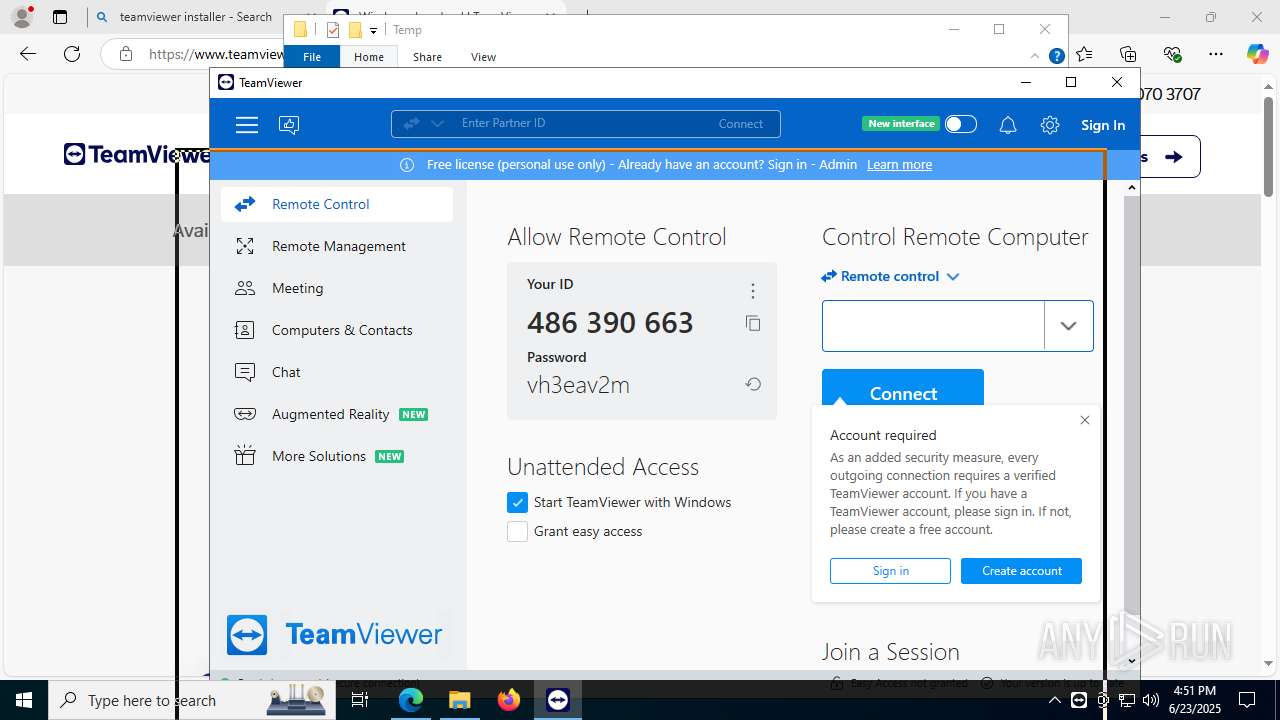
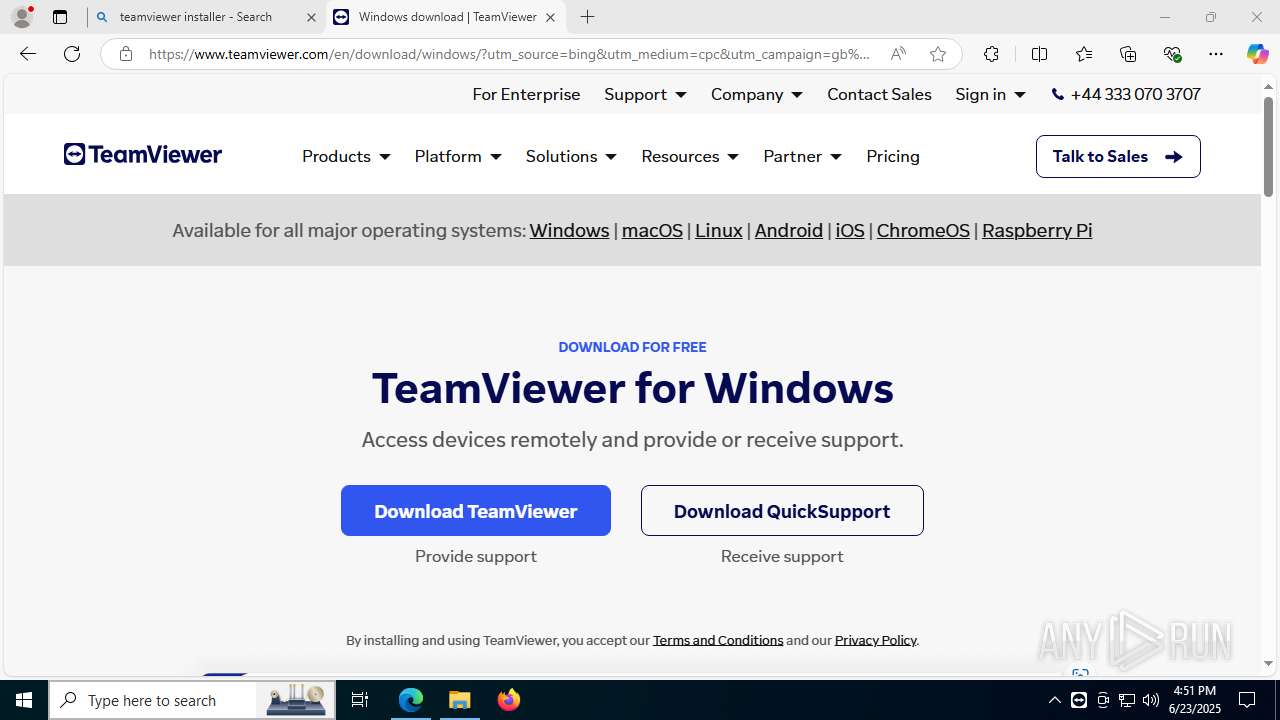
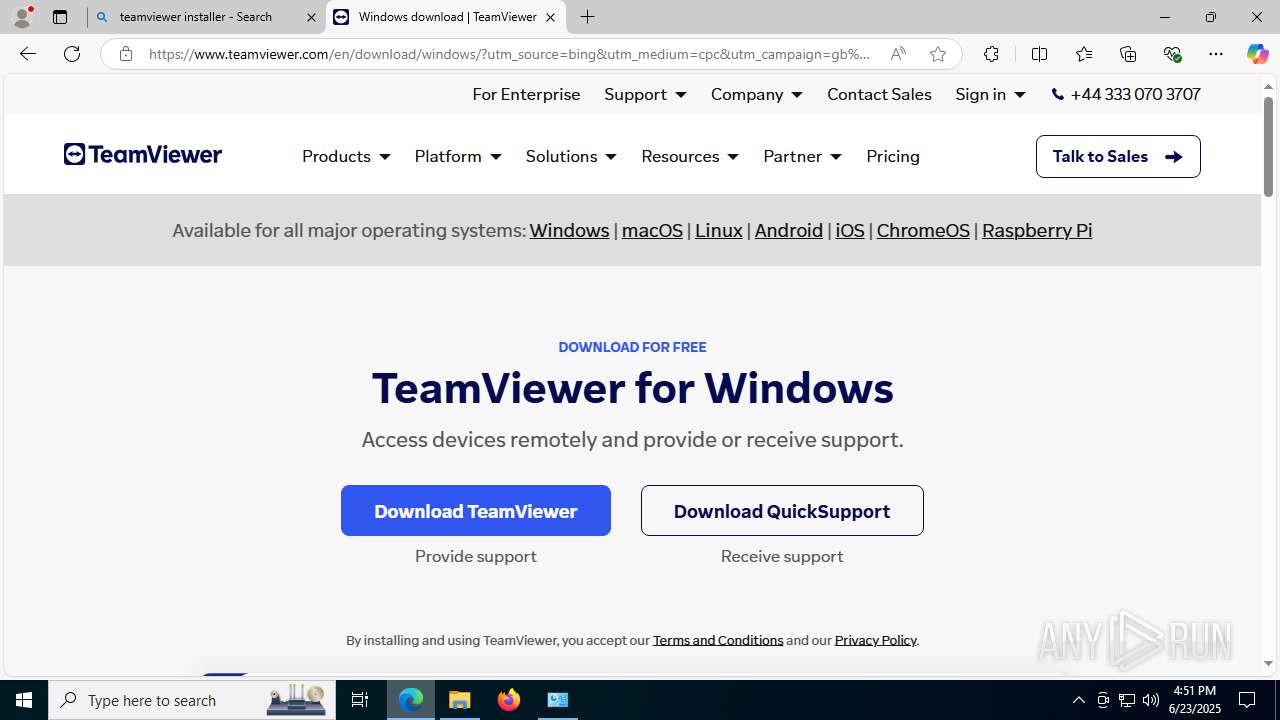
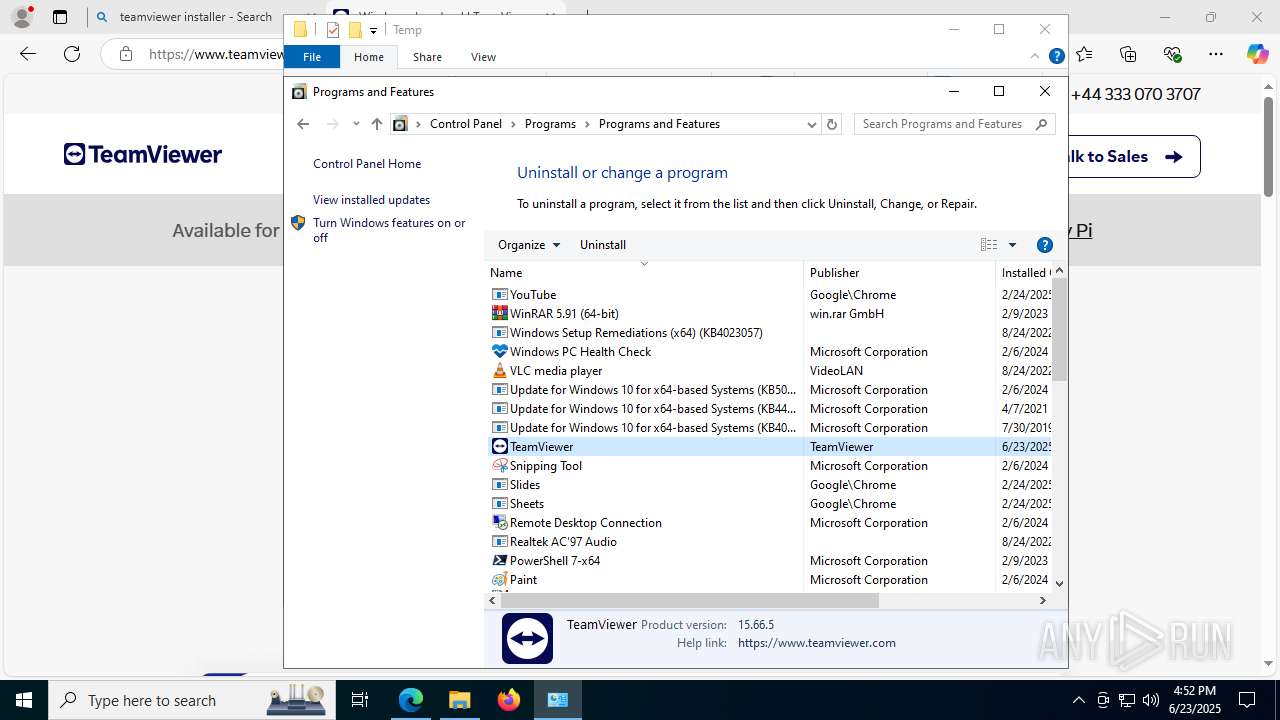
TEAMVIEWER has been detected (SURICATA)
- msedge.exe (PID: 4968)
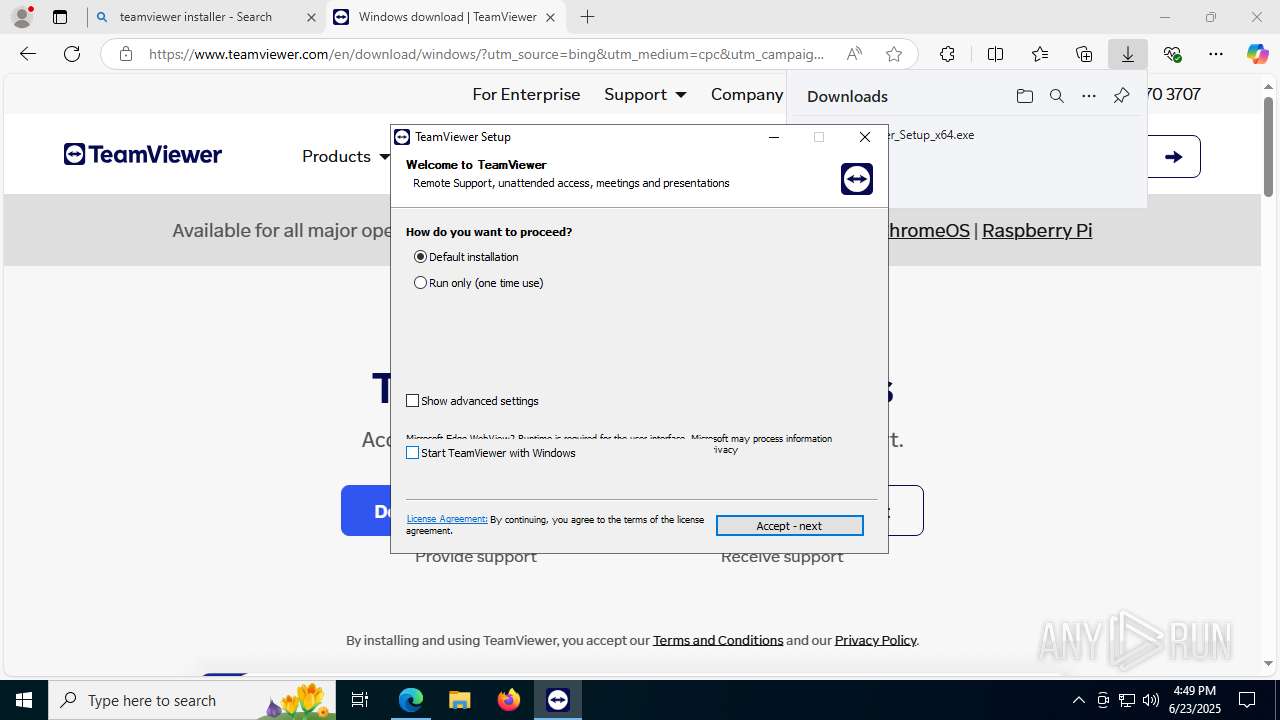
Uses Task Scheduler to autorun other applications
- TeamViewer_.exe (PID: 3836)
Registers / Runs the DLL via REGSVR32.EXE
- TeamViewer_.exe (PID: 3836)
Actions looks like stealing of personal data
- TeamViewer.exe (PID: 8120)
EMMENHTAL has been detected (YARA)
- TeamViewer.exe (PID: 8120)
SUSPICIOUS
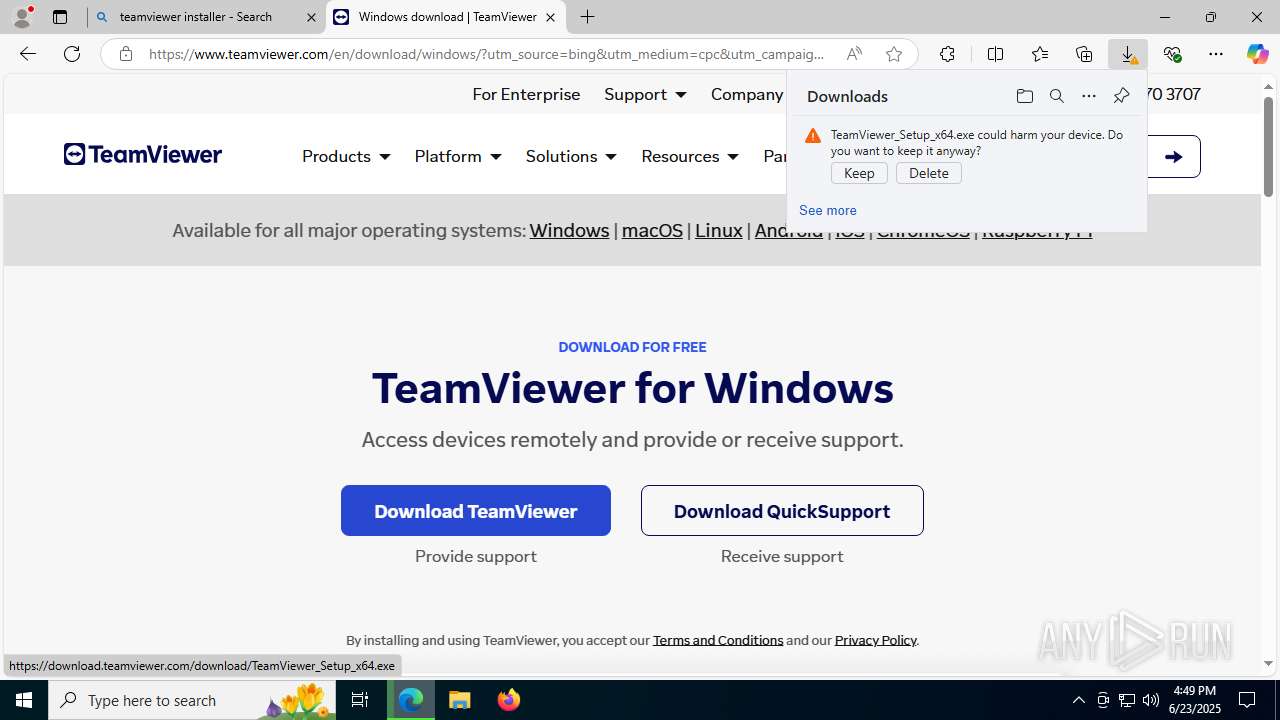
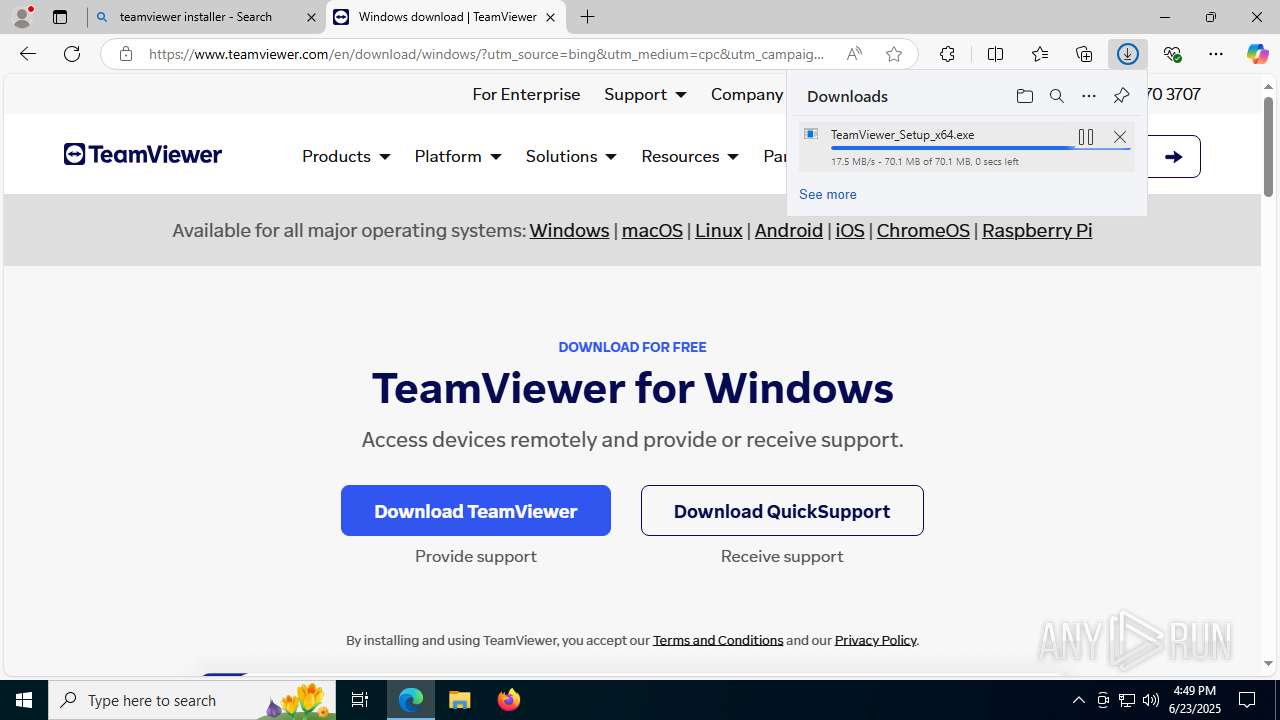
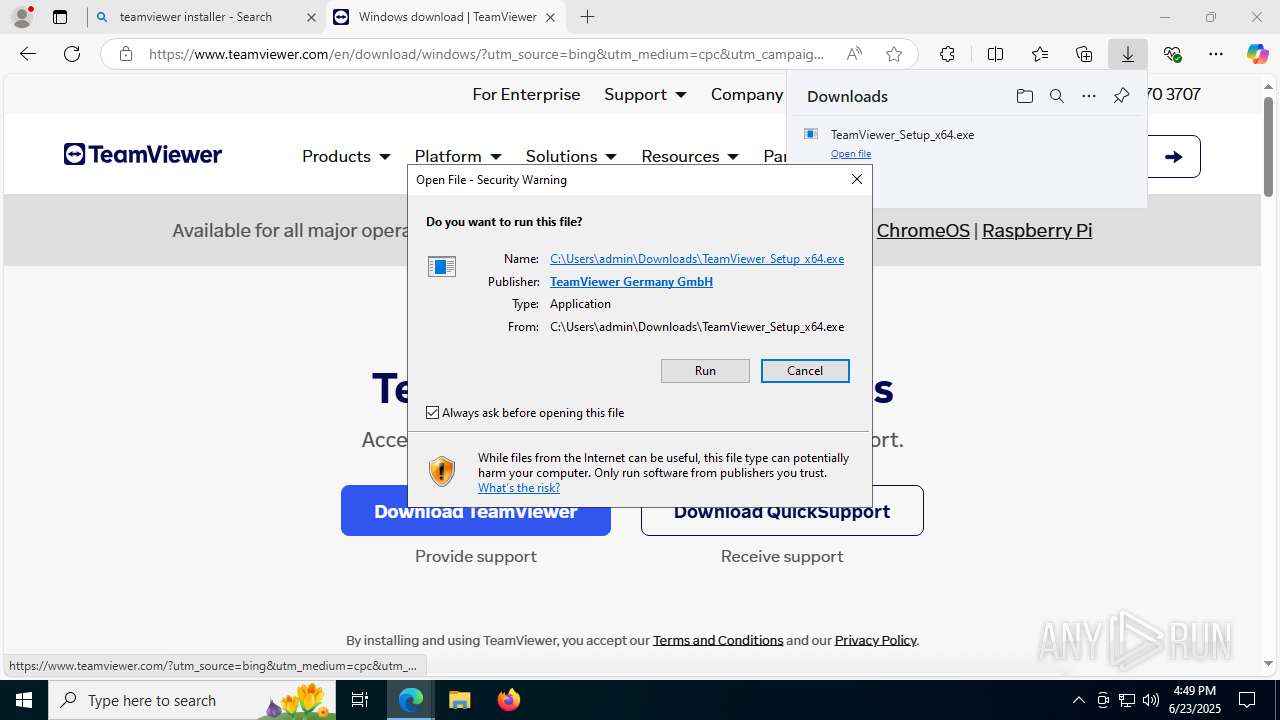
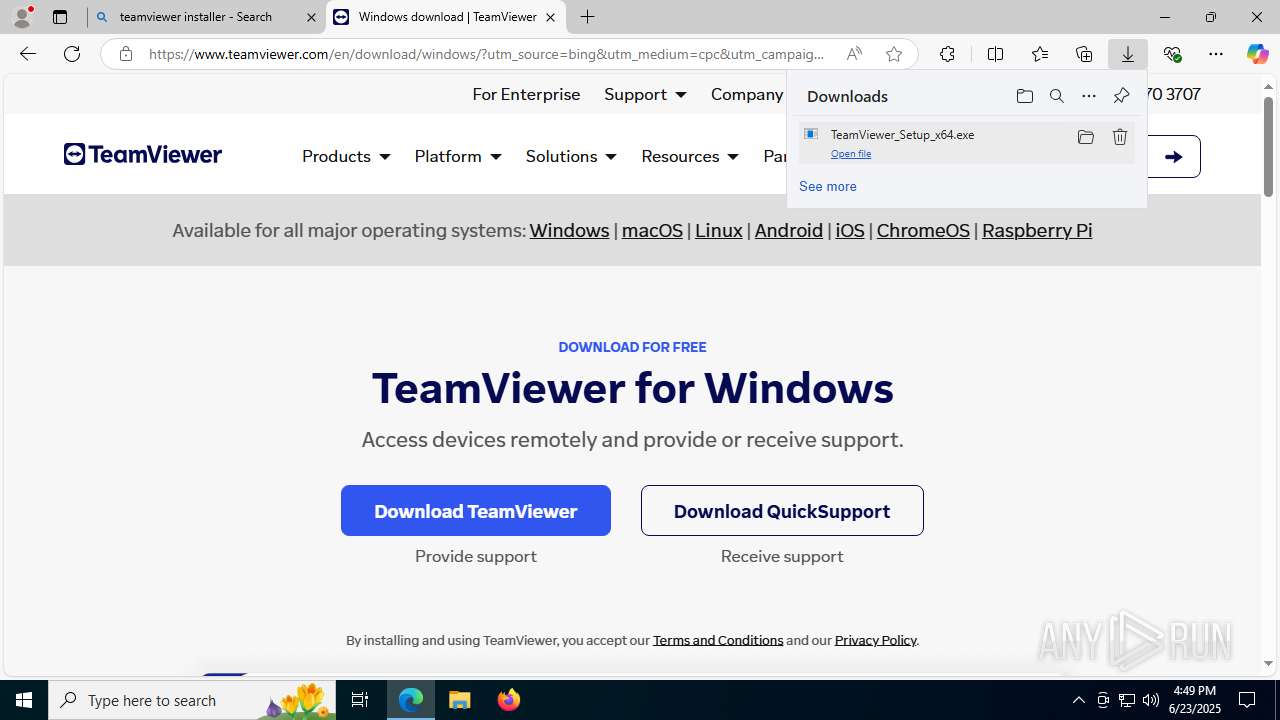
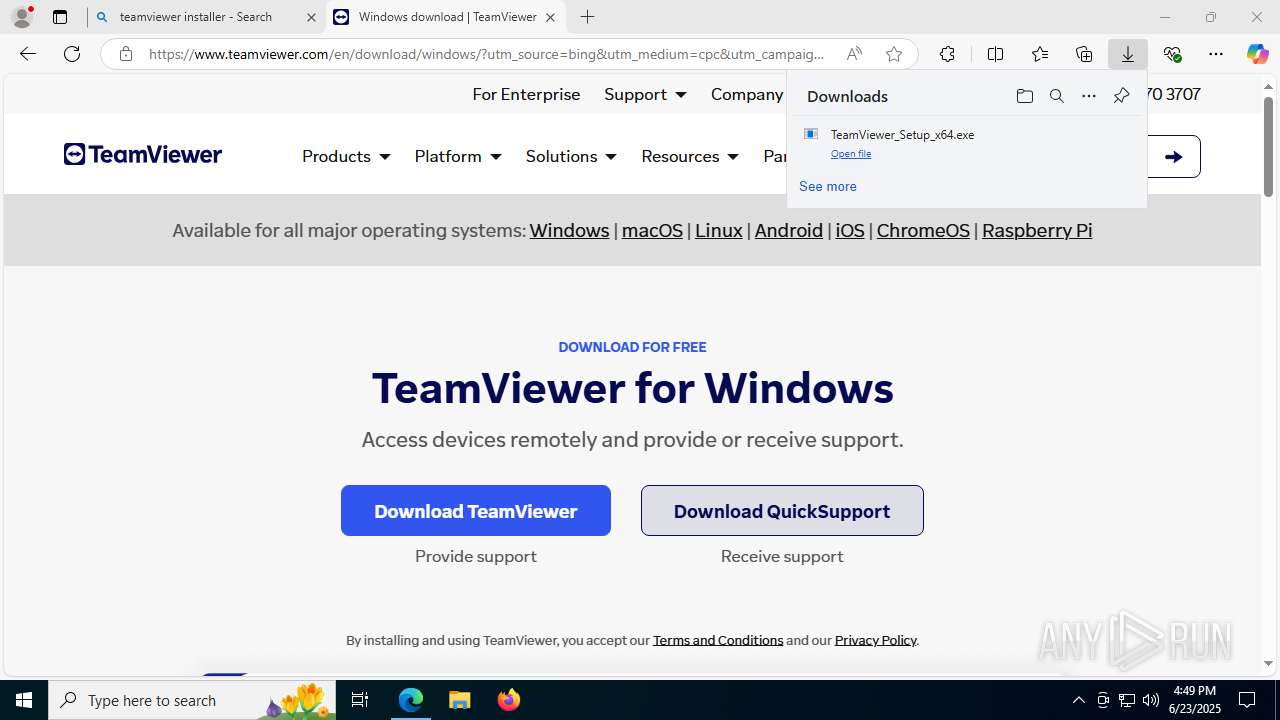
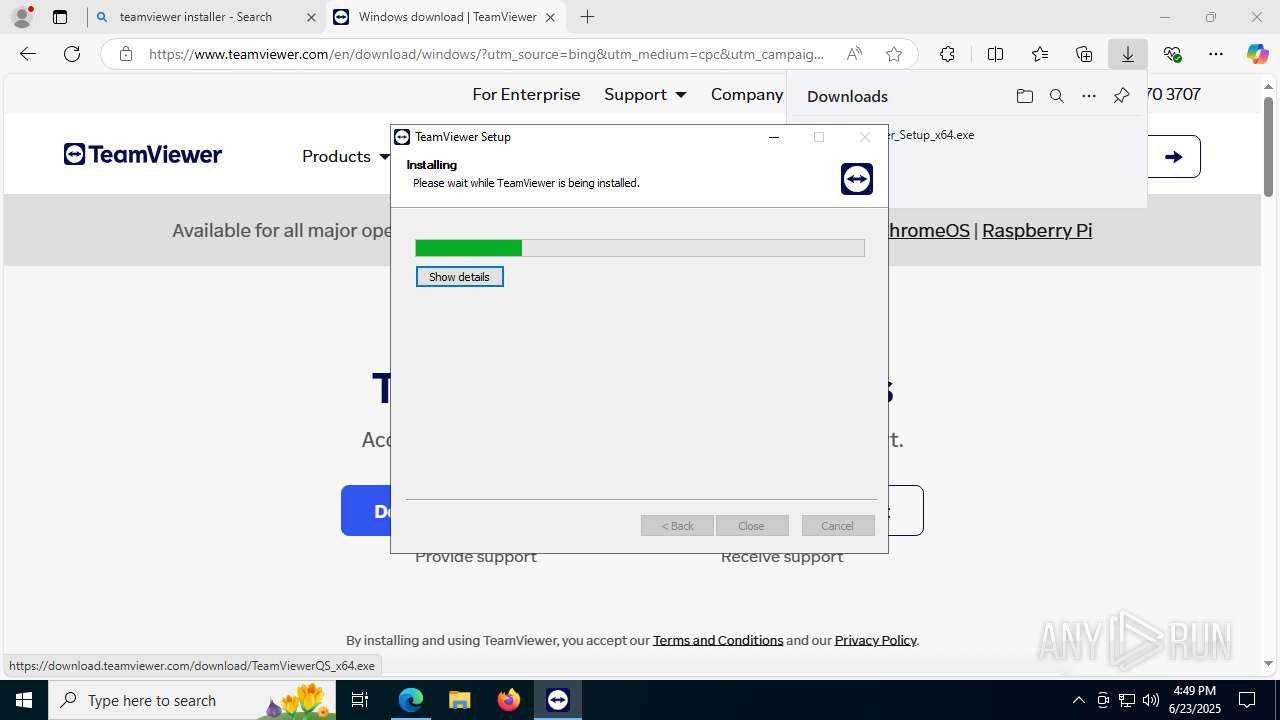
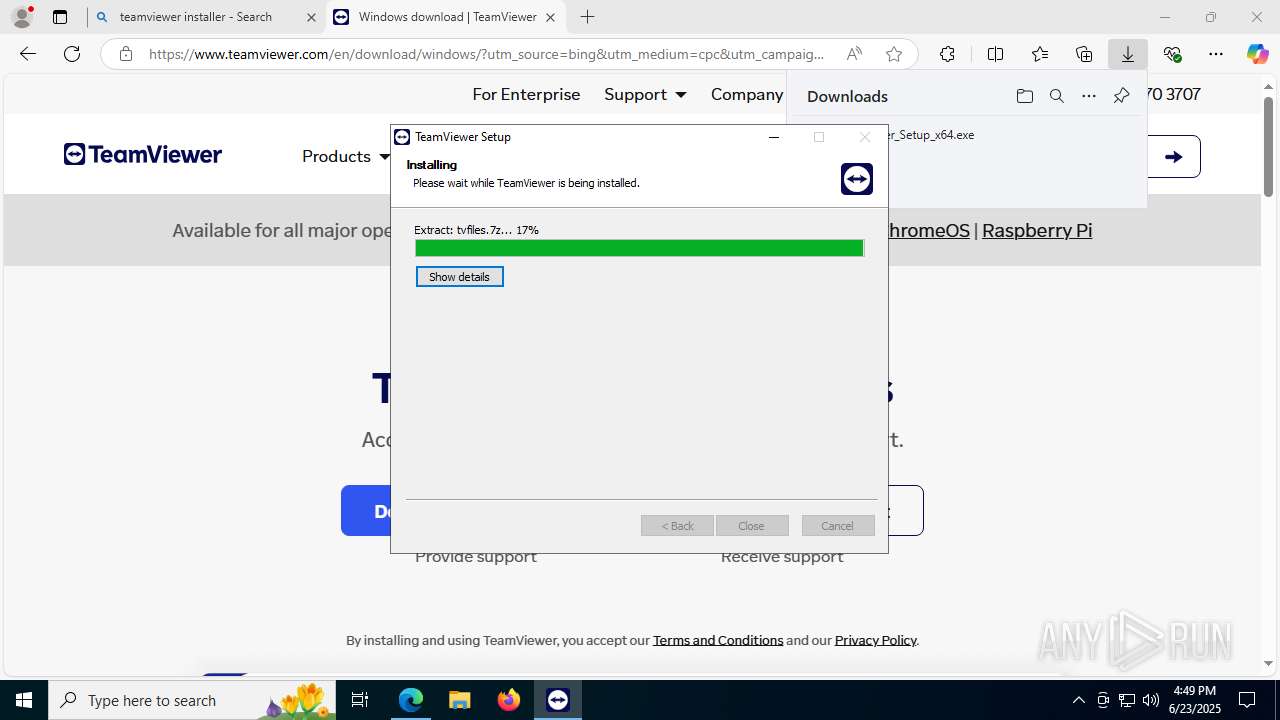
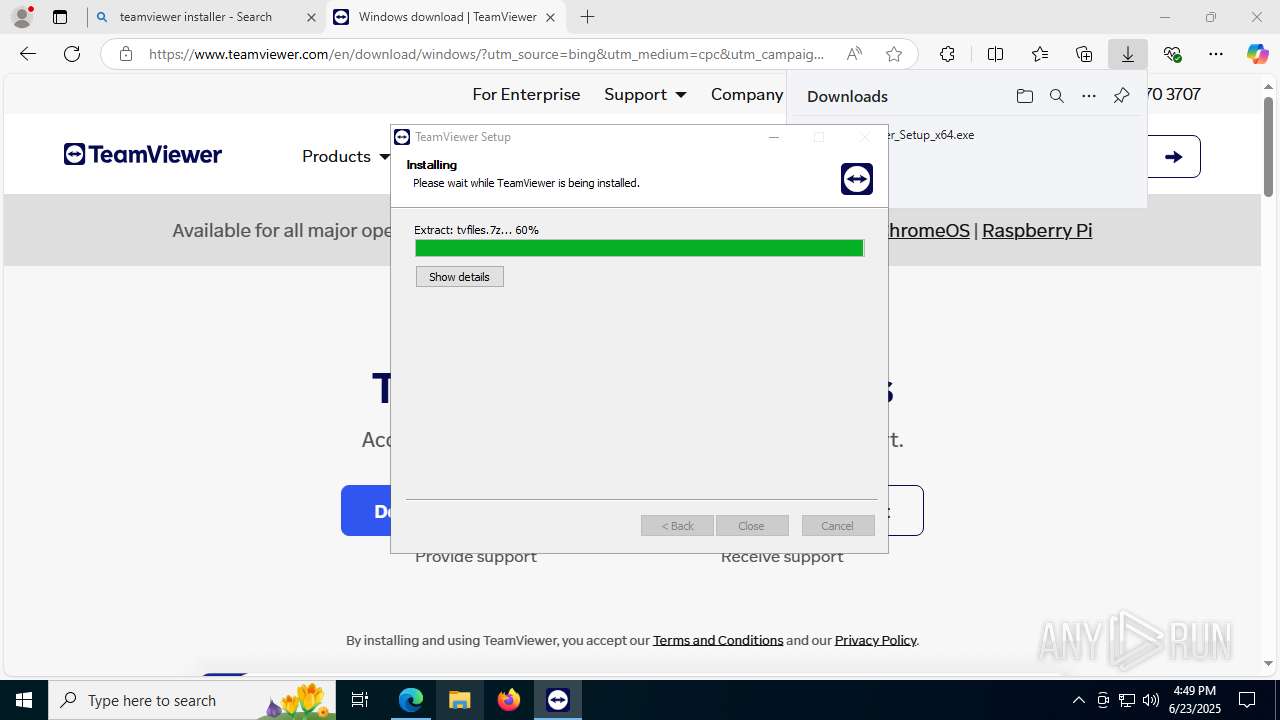
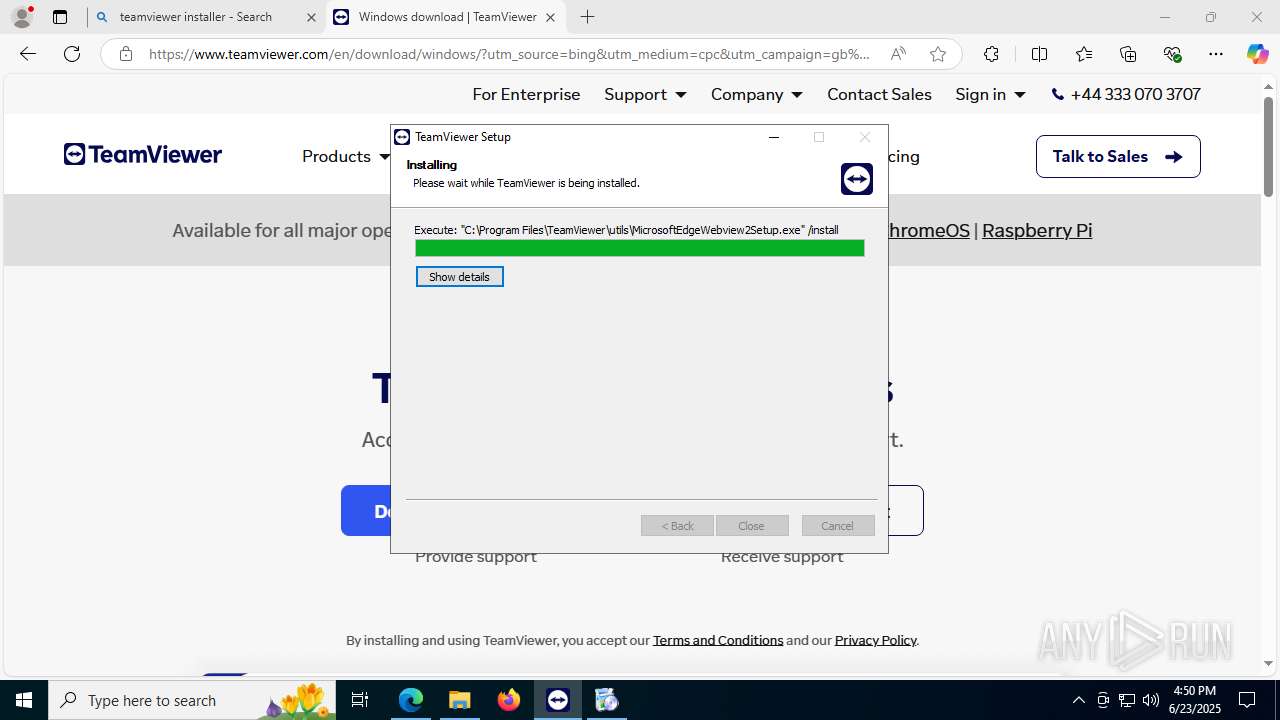
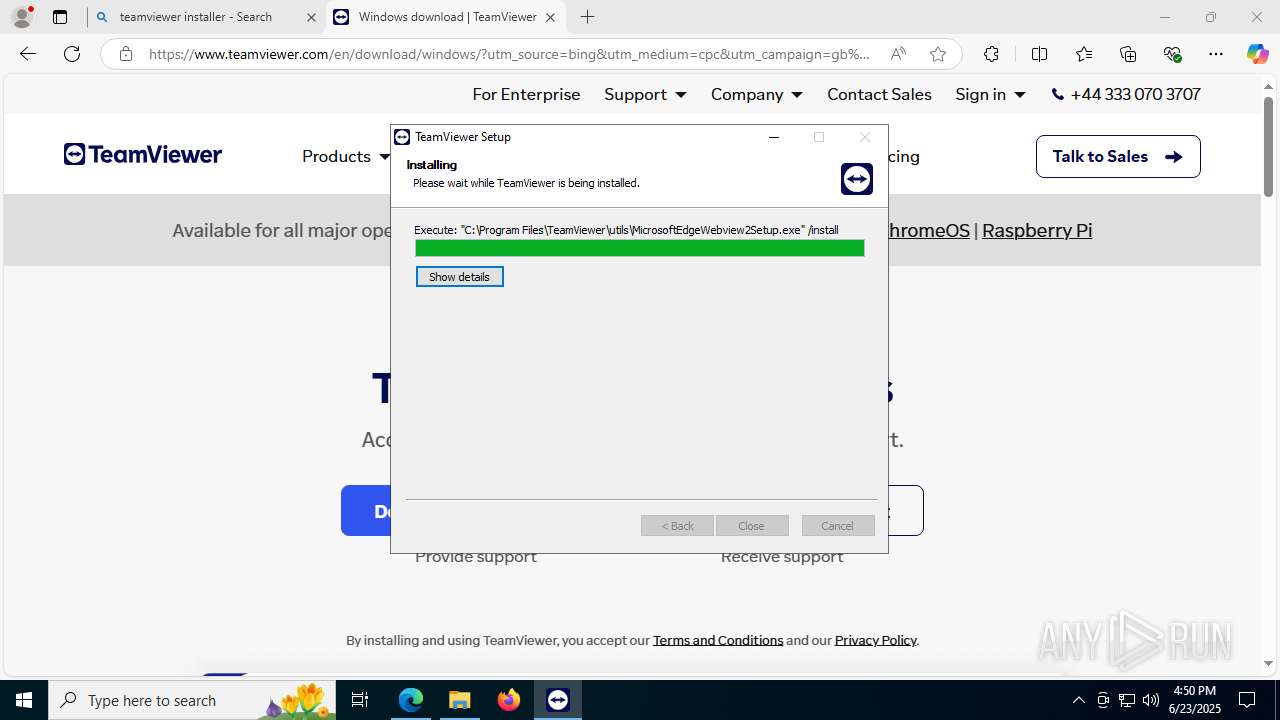
Executable content was dropped or overwritten
- TeamViewer_Setup_x64.exe (PID: 6940)
- TeamViewer_.exe (PID: 3836)
- TeamViewer_.exe (PID: 5252)
- tv_x64.exe (PID: 7968)
- drvinst.exe (PID: 7464)
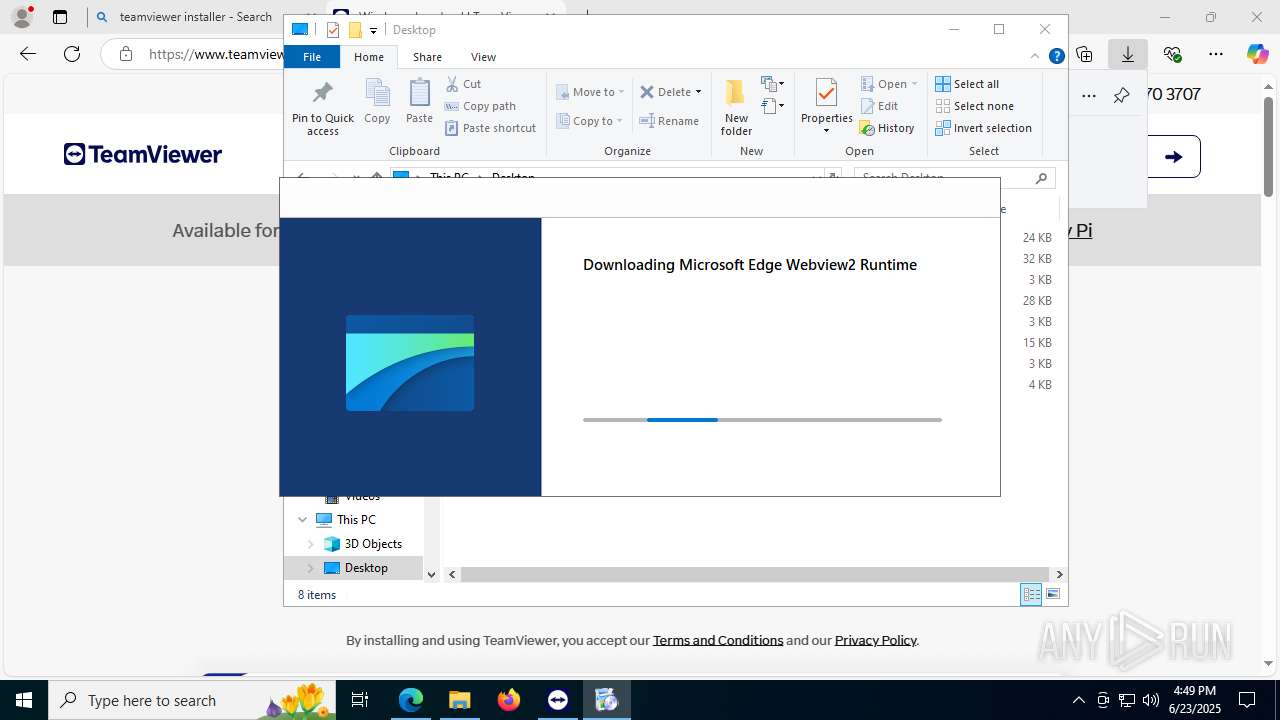
- MicrosoftEdgeWebview2Setup.exe (PID: 8176)
The process creates files with name similar to system file names
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
Application launched itself
- TeamViewer_.exe (PID: 5252)
Reads security settings of Internet Explorer
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 5992)
- tv_x64.exe (PID: 8140)
- tv_x64.exe (PID: 7968)
- MicrosoftEdgeUpdate.exe (PID: 2588)
- TeamViewer.exe (PID: 8120)
- TeamViewer.exe (PID: 7928)
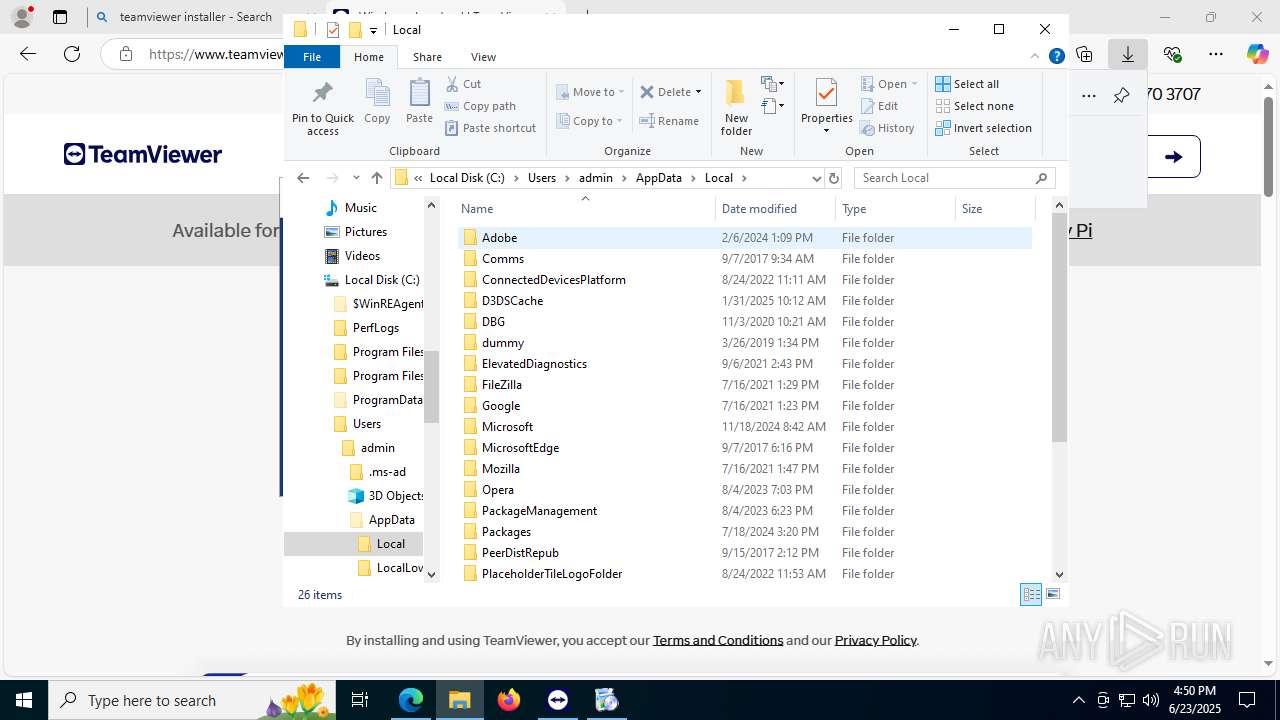
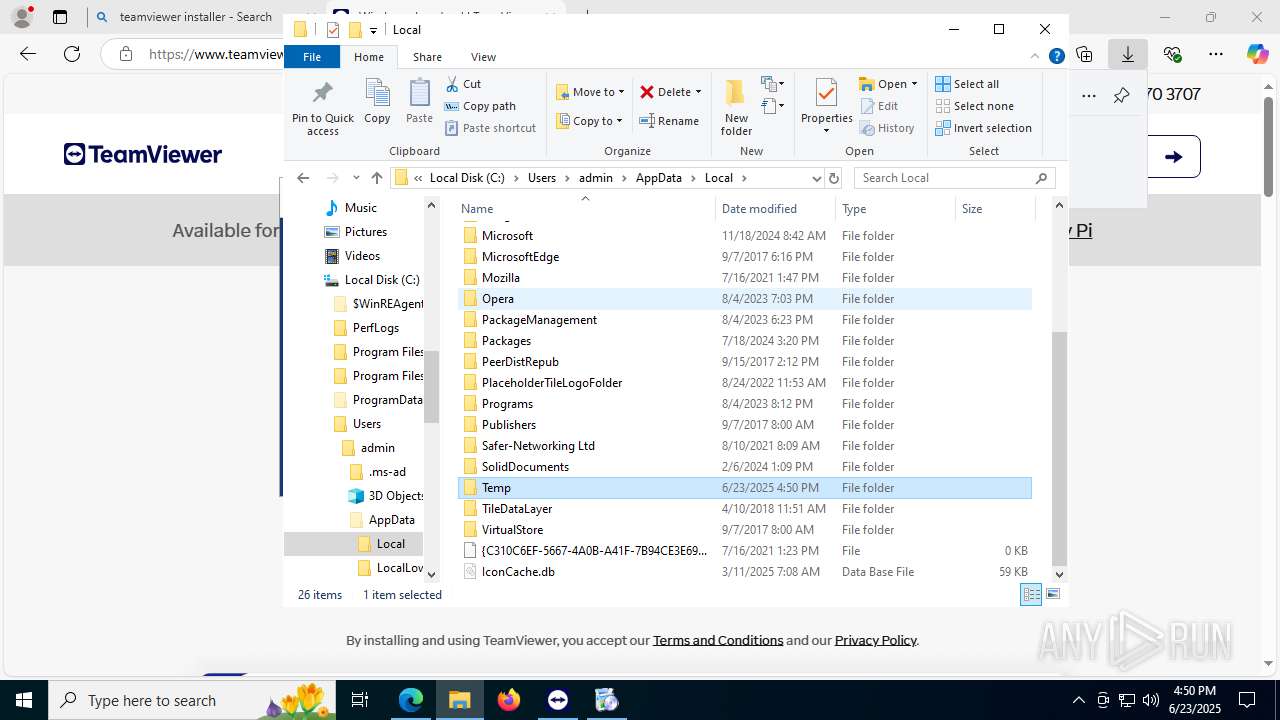
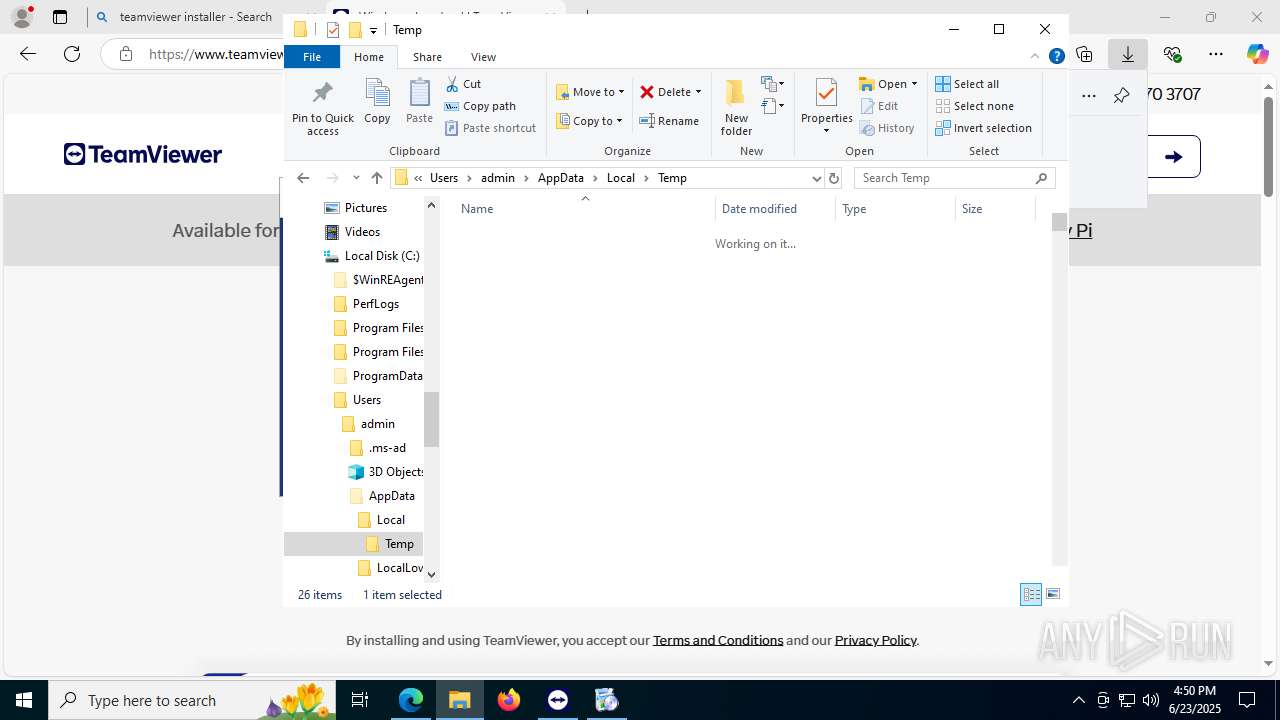
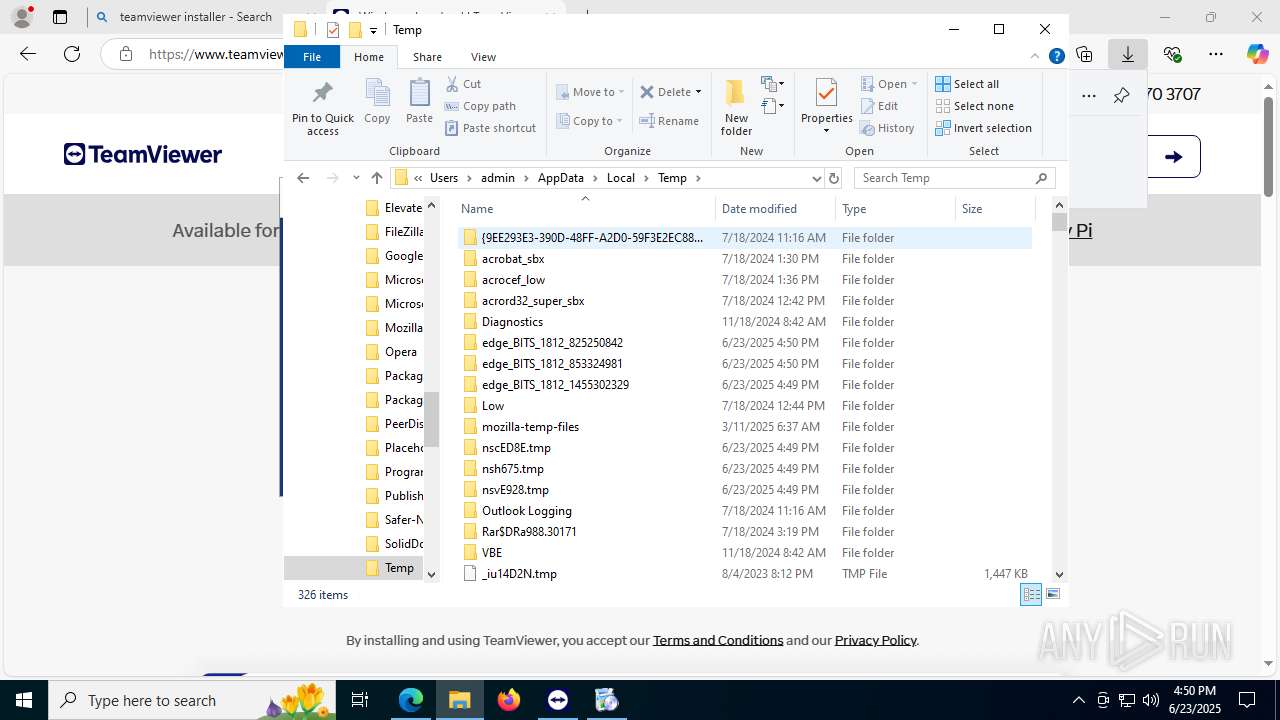
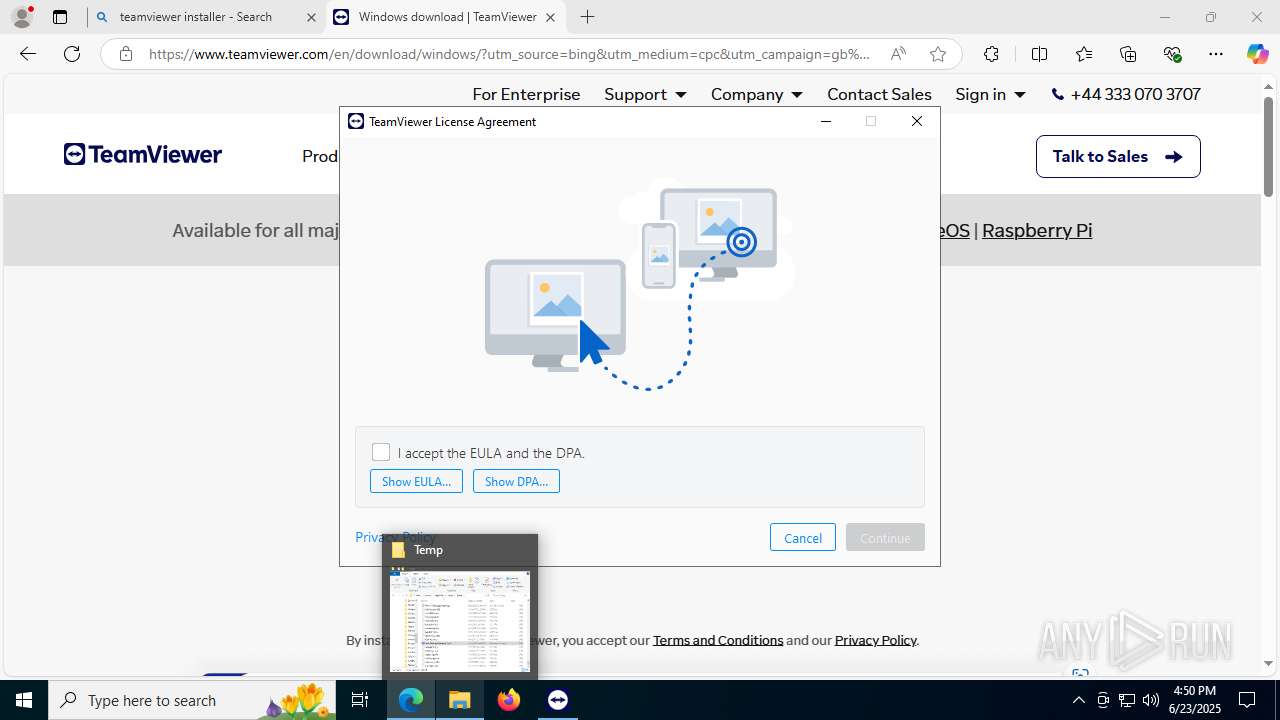
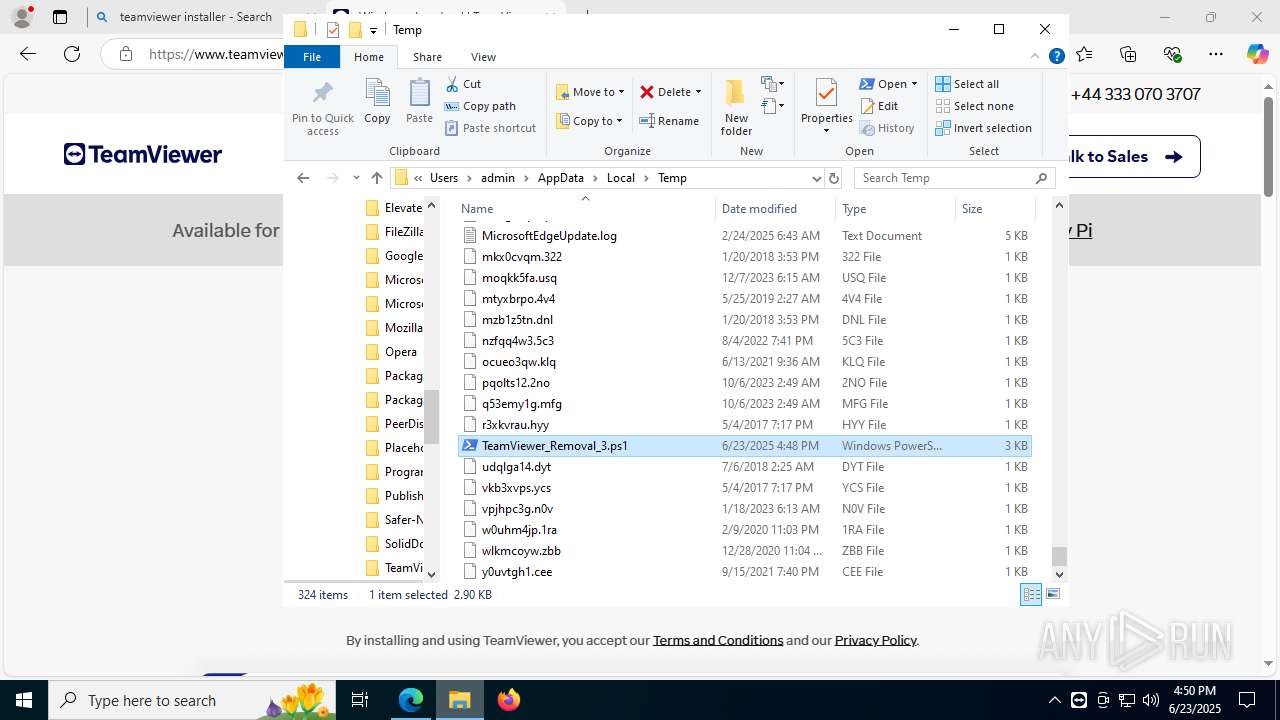
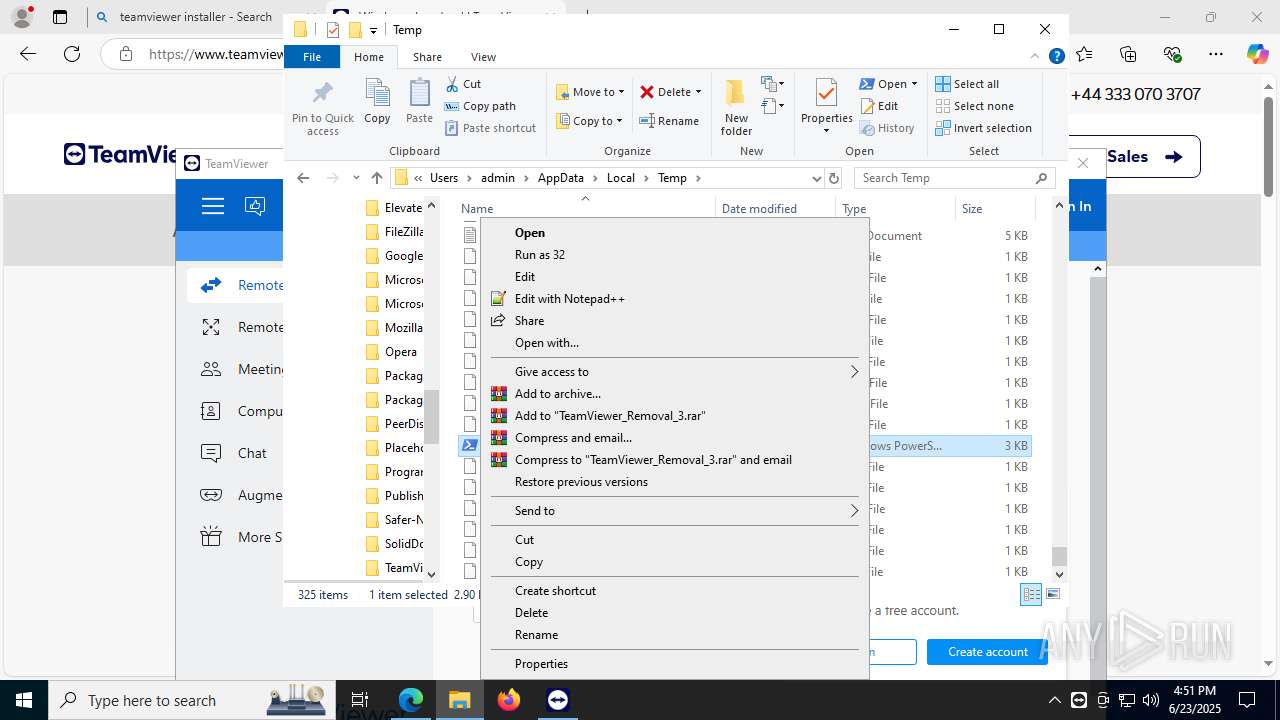
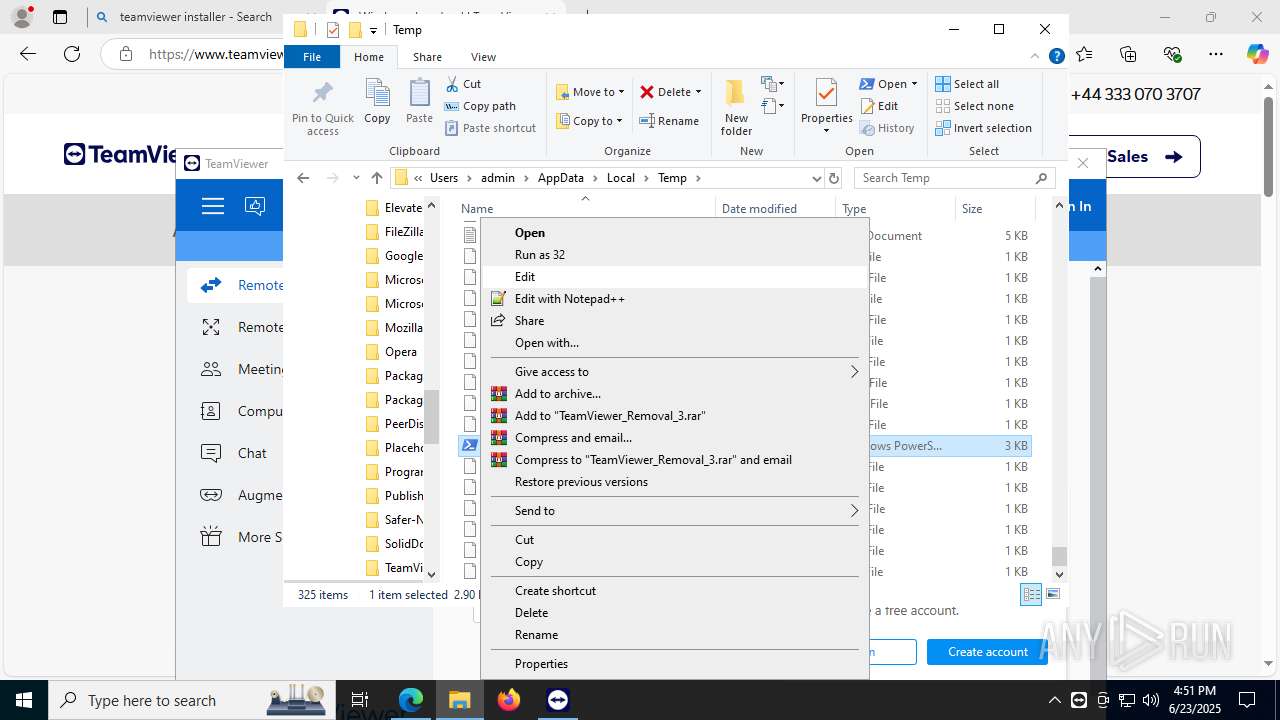
Malware-specific behavior (creating "System.dll" in Temp)
- TeamViewer_.exe (PID: 3836)
- TeamViewer_.exe (PID: 5252)
There is functionality for taking screenshot (YARA)
- TeamViewer_Setup_x64.exe (PID: 6940)
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
Drops 7-zip archiver for unpacking
- TeamViewer_.exe (PID: 3836)
Process drops legitimate windows executable
- TeamViewer_.exe (PID: 3836)
- MicrosoftEdgeWebview2Setup.exe (PID: 8176)
- MicrosoftEdgeUpdate.exe (PID: 2588)
Drops a system driver (possible attempt to evade defenses)
- TeamViewer_.exe (PID: 3836)
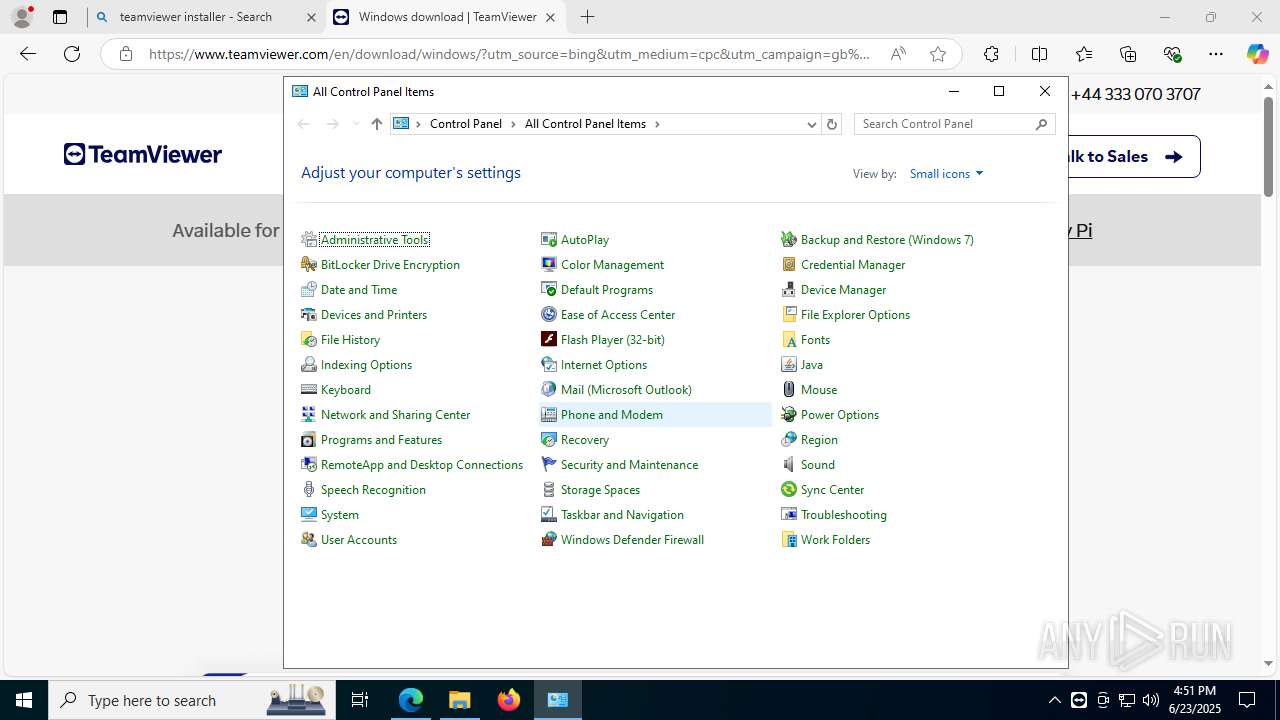
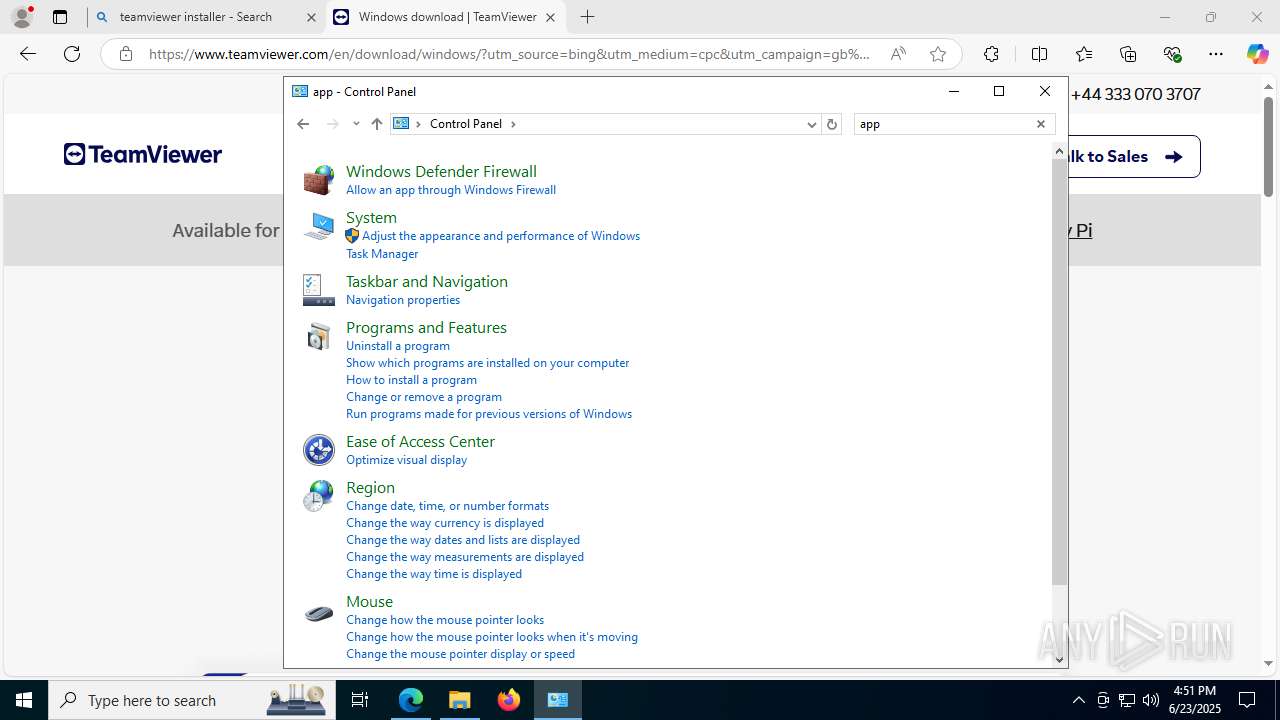
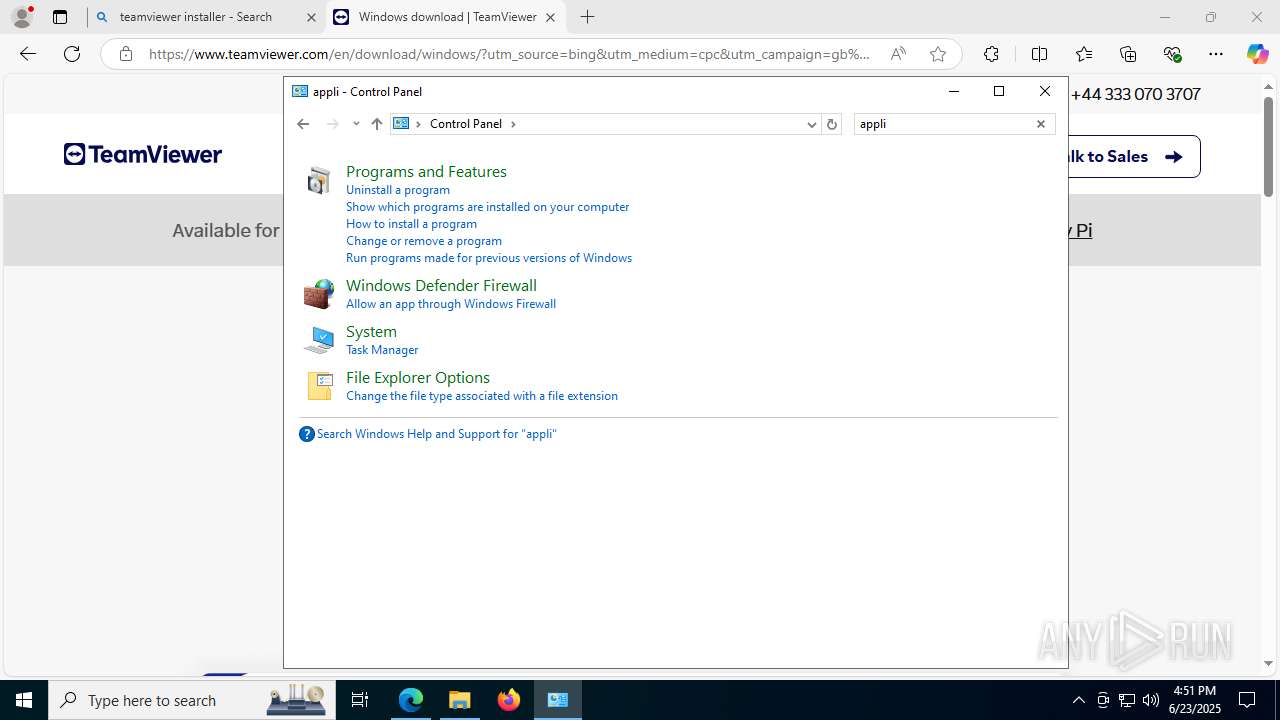
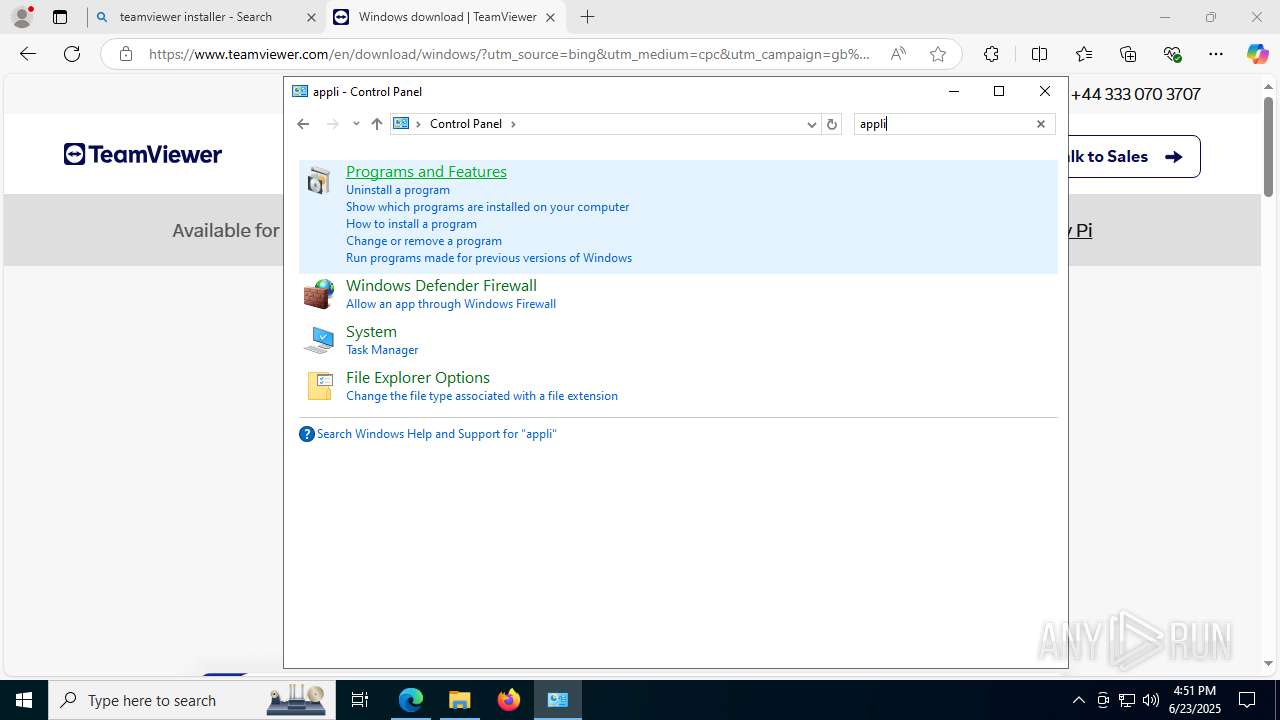
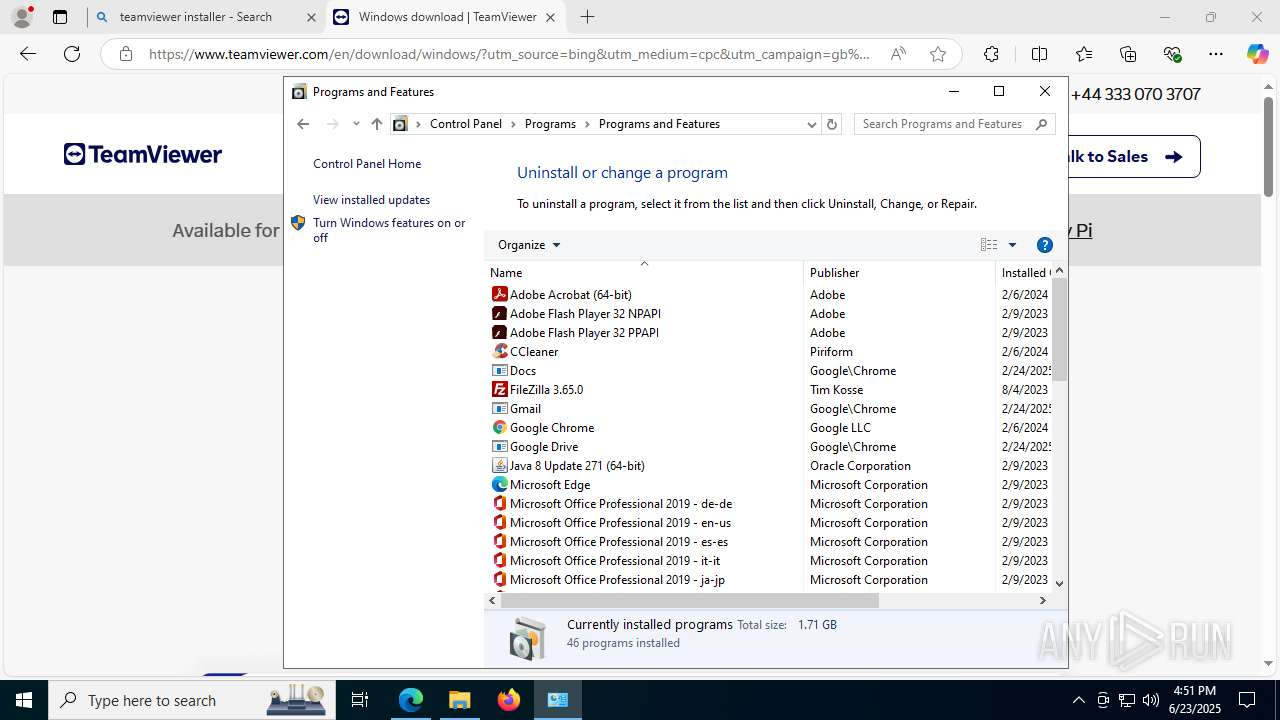
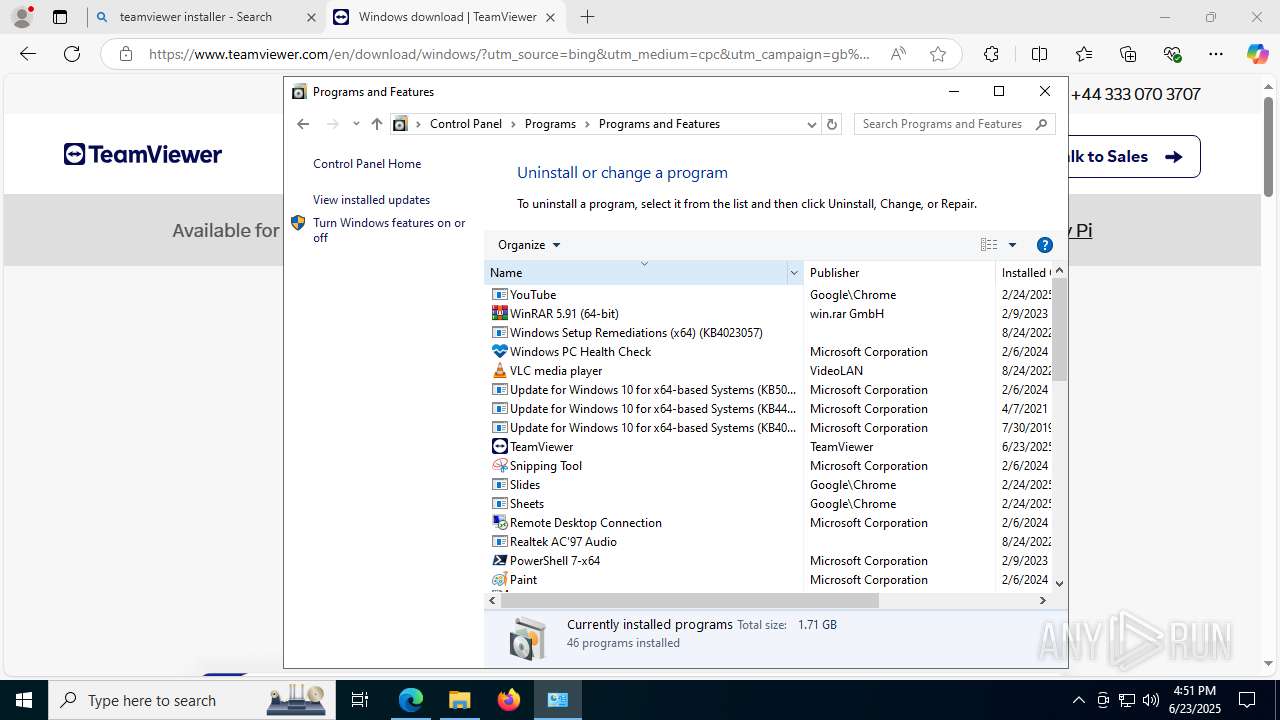
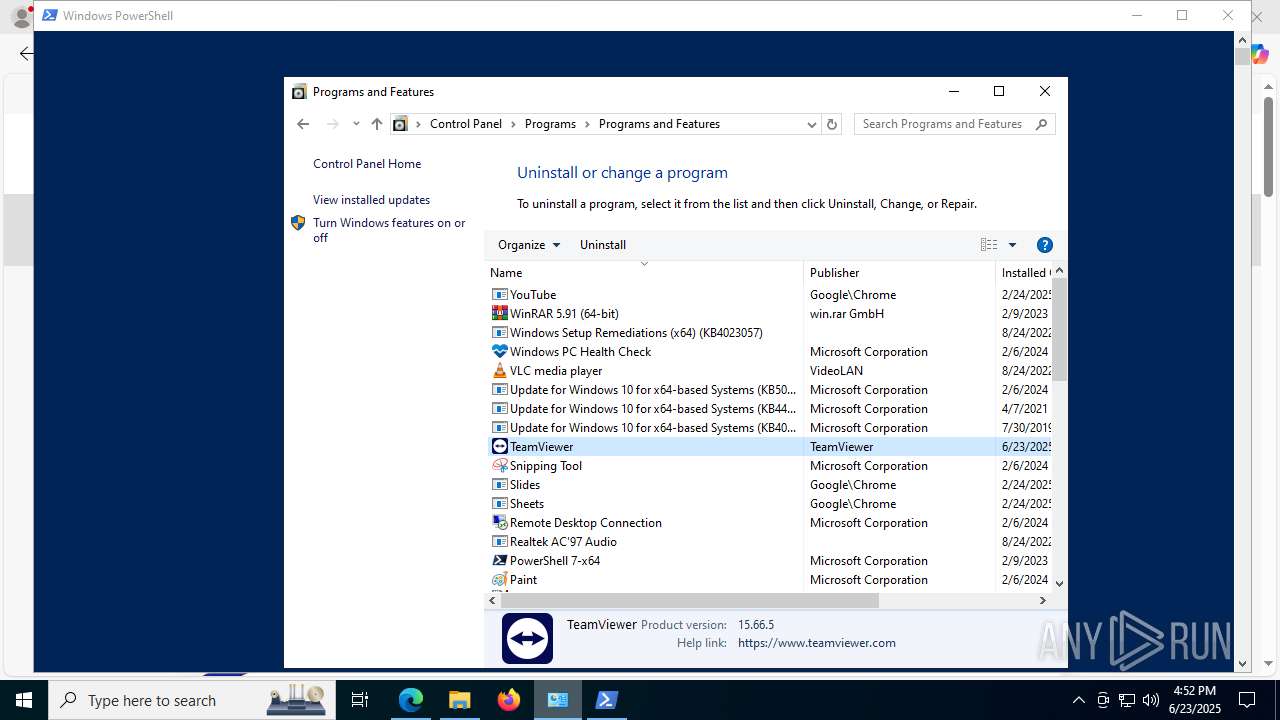
Searches for installed software
- TeamViewer_.exe (PID: 3836)
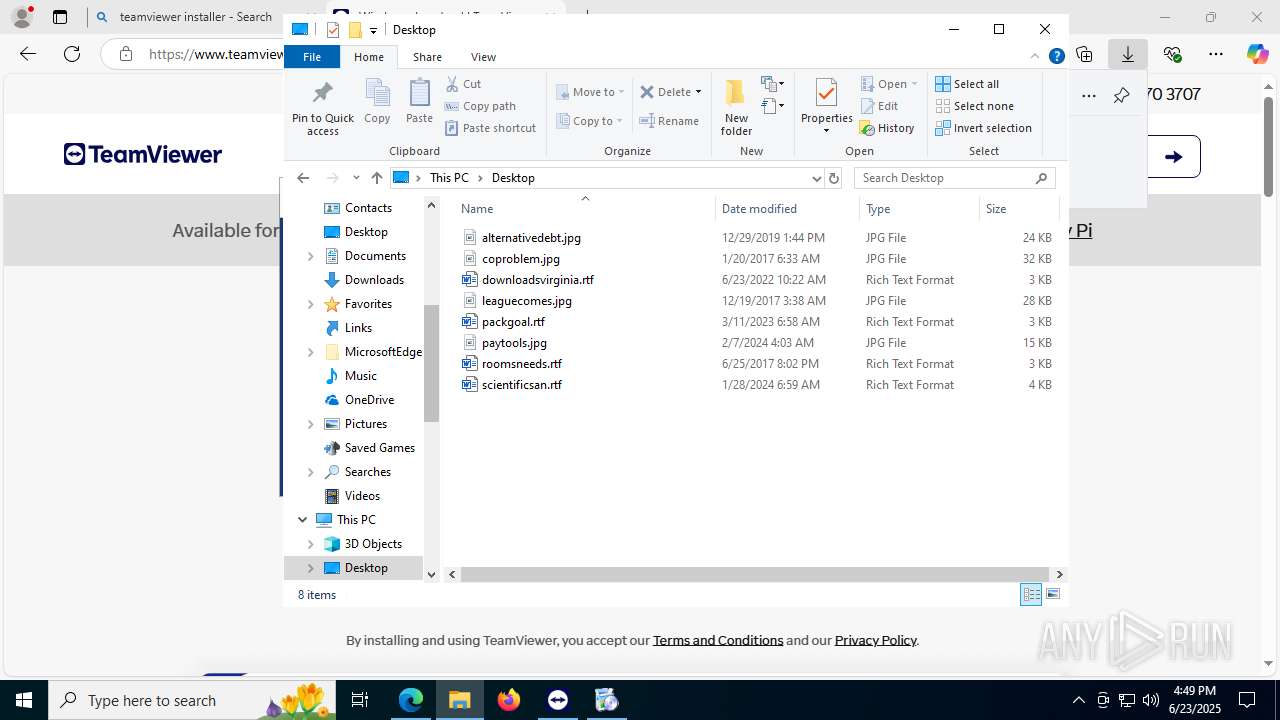
- explorer.exe (PID: 4380)
Creates a software uninstall entry
- TeamViewer_.exe (PID: 3836)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7688)
Creates files in the driver directory
- drvinst.exe (PID: 7464)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6676)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 2588)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 2588)
Reads Microsoft Outlook installation path
- TeamViewer.exe (PID: 8120)
Reads Internet Explorer settings
- TeamViewer.exe (PID: 8120)
Connects to unusual port
- TeamViewer_Service.exe (PID: 7304)
The process verifies whether the antivirus software is installed
- TeamViewer_Service.exe (PID: 7304)
Reads the Windows owner or organization settings
- TeamViewer.exe (PID: 8120)
Windows service management via SC.EXE
- sc.exe (PID: 7768)
- sc.exe (PID: 3656)
Starts SC.EXE for service management
- powershell.exe (PID: 5908)
- powershell.exe (PID: 4984)
Executes as Windows Service
- TeamViewer_Service.exe (PID: 7304)
INFO
Checks supported languages
- msiexec.exe (PID: 1816)
- identity_helper.exe (PID: 7668)
- TeamViewer_Setup_x64.exe (PID: 6940)
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 5992)
- tv_x64.exe (PID: 8140)
- tv_x64.exe (PID: 7968)
- drvinst.exe (PID: 7464)
- MicrosoftEdgeWebview2Setup.exe (PID: 8176)
- MicrosoftEdgeUpdate.exe (PID: 2588)
- TeamViewer_Service.exe (PID: 7304)
- crashpad_handler.exe (PID: 7060)
- TeamViewer.exe (PID: 8120)
- tv_w32.exe (PID: 2040)
- tv_x64.exe (PID: 5012)
- crashpad_handler.exe (PID: 6016)
- TeamViewer.exe (PID: 7928)
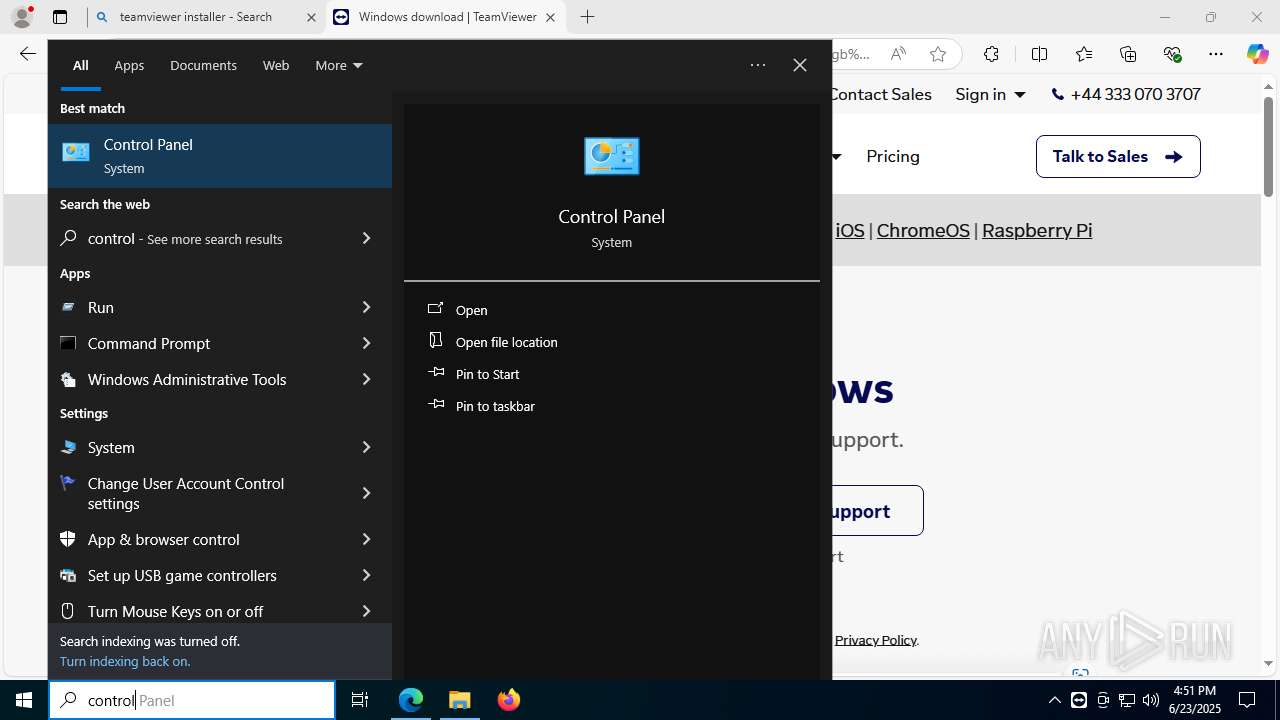
Manual execution by a user
- msedge.exe (PID: 1812)
- TeamViewer.exe (PID: 7928)
- powershell.exe (PID: 5908)
- powershell.exe (PID: 4984)
Reads the computer name
- msiexec.exe (PID: 1816)
- identity_helper.exe (PID: 7668)
- TeamViewer_.exe (PID: 3836)
- TeamViewer_.exe (PID: 5252)
- TeamViewer.exe (PID: 5992)
- TeamViewer_Service.exe (PID: 3028)
- tv_x64.exe (PID: 8140)
- tv_x64.exe (PID: 7968)
- drvinst.exe (PID: 7464)
- MicrosoftEdgeUpdate.exe (PID: 2588)
- TeamViewer.exe (PID: 8120)
- tv_x64.exe (PID: 5012)
- tv_w32.exe (PID: 2040)
- TeamViewer.exe (PID: 7928)
- TeamViewer_Service.exe (PID: 7304)
Reads Environment values
- identity_helper.exe (PID: 7668)
- MicrosoftEdgeUpdate.exe (PID: 2588)
- TeamViewer_Service.exe (PID: 7304)
- TeamViewer.exe (PID: 8120)
Application launched itself
- msedge.exe (PID: 1812)
Executable content was dropped or overwritten
- msedge.exe (PID: 1812)
The sample compiled with english language support
- msedge.exe (PID: 1812)
- TeamViewer_Setup_x64.exe (PID: 6940)
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
- MicrosoftEdgeWebview2Setup.exe (PID: 8176)
- MicrosoftEdgeUpdate.exe (PID: 2588)
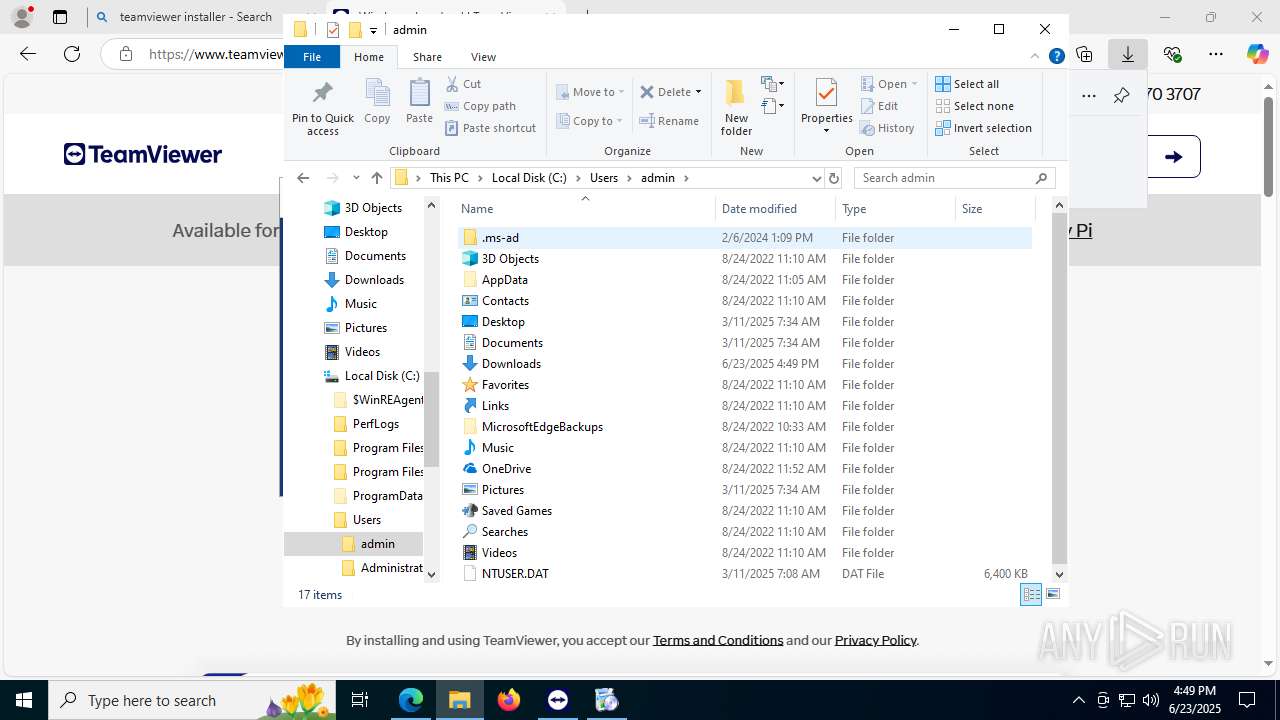
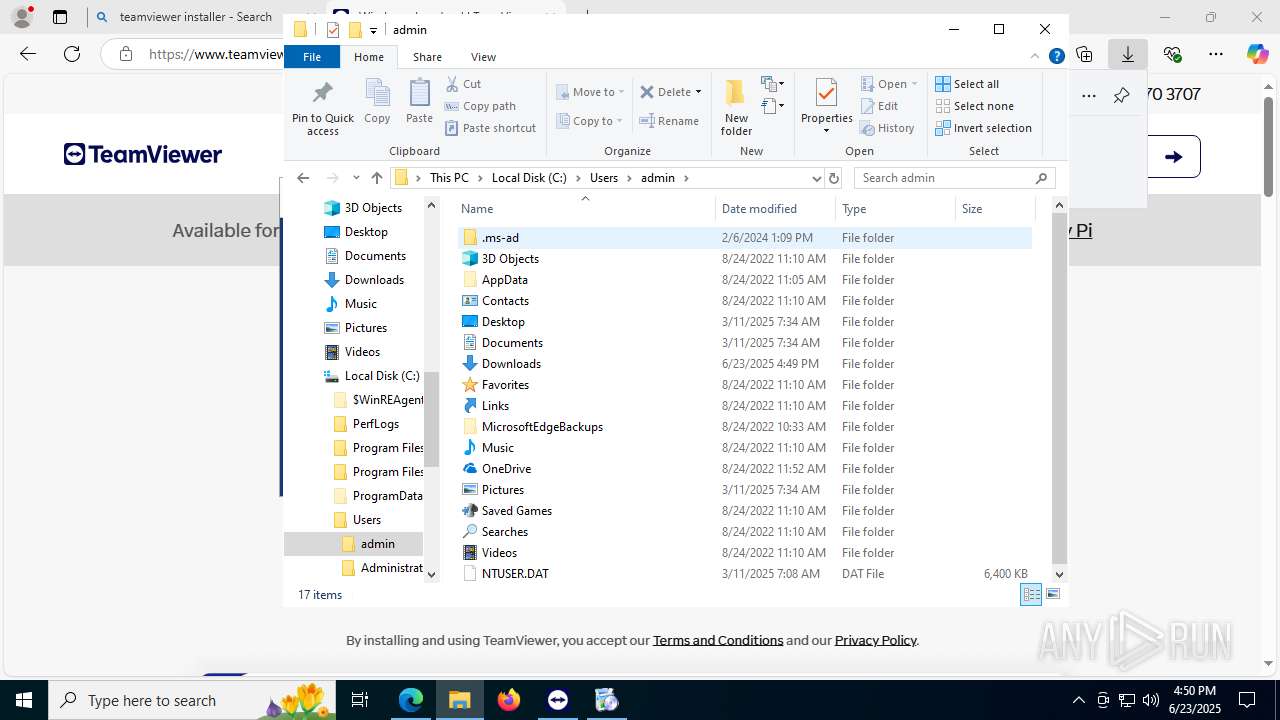
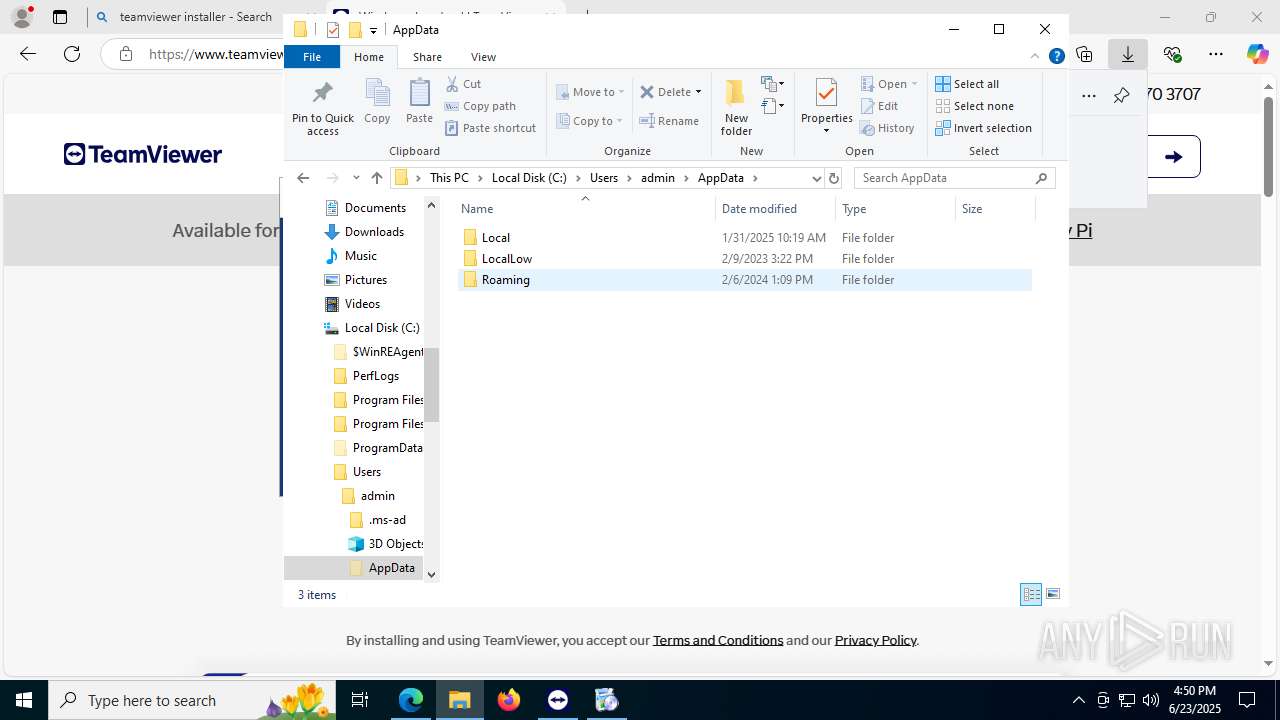
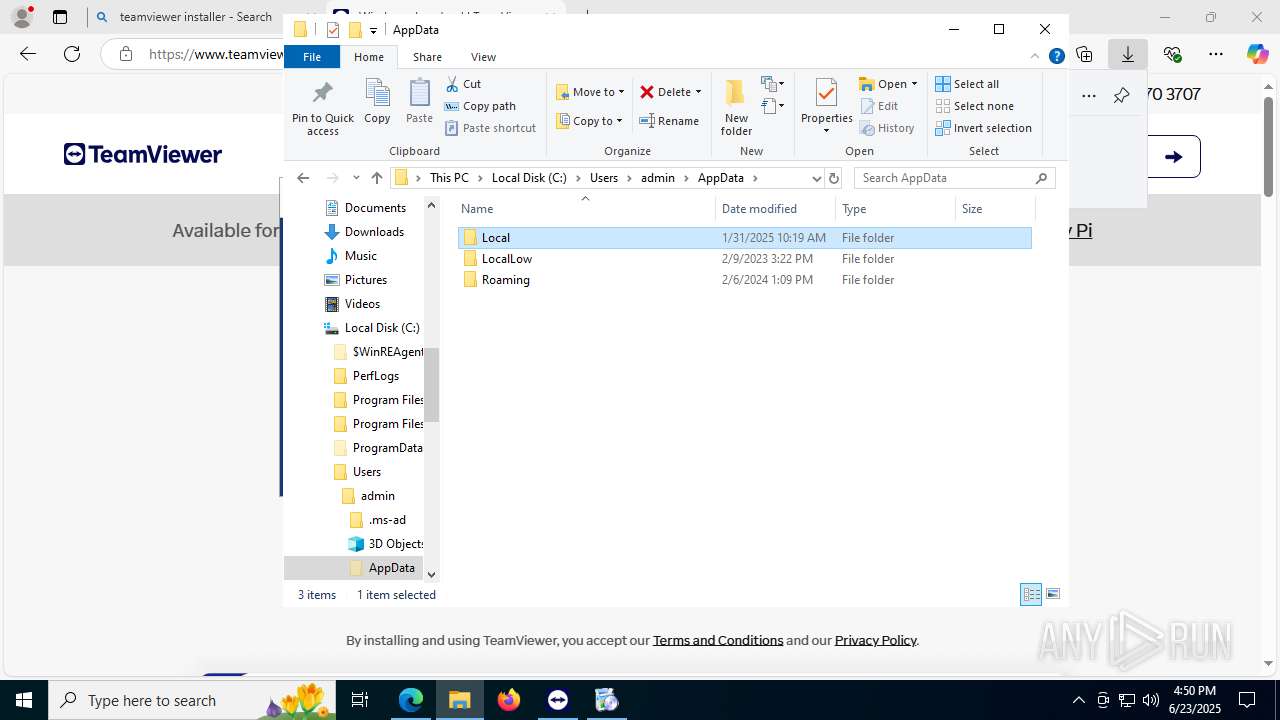
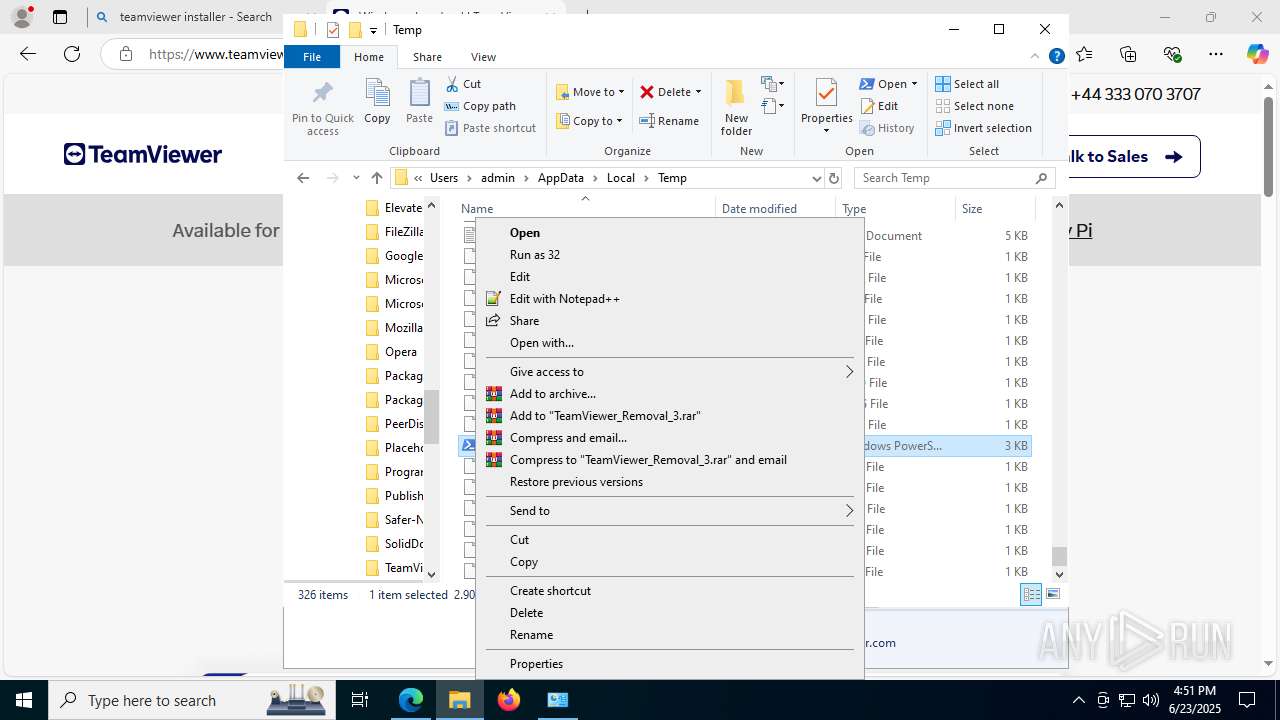
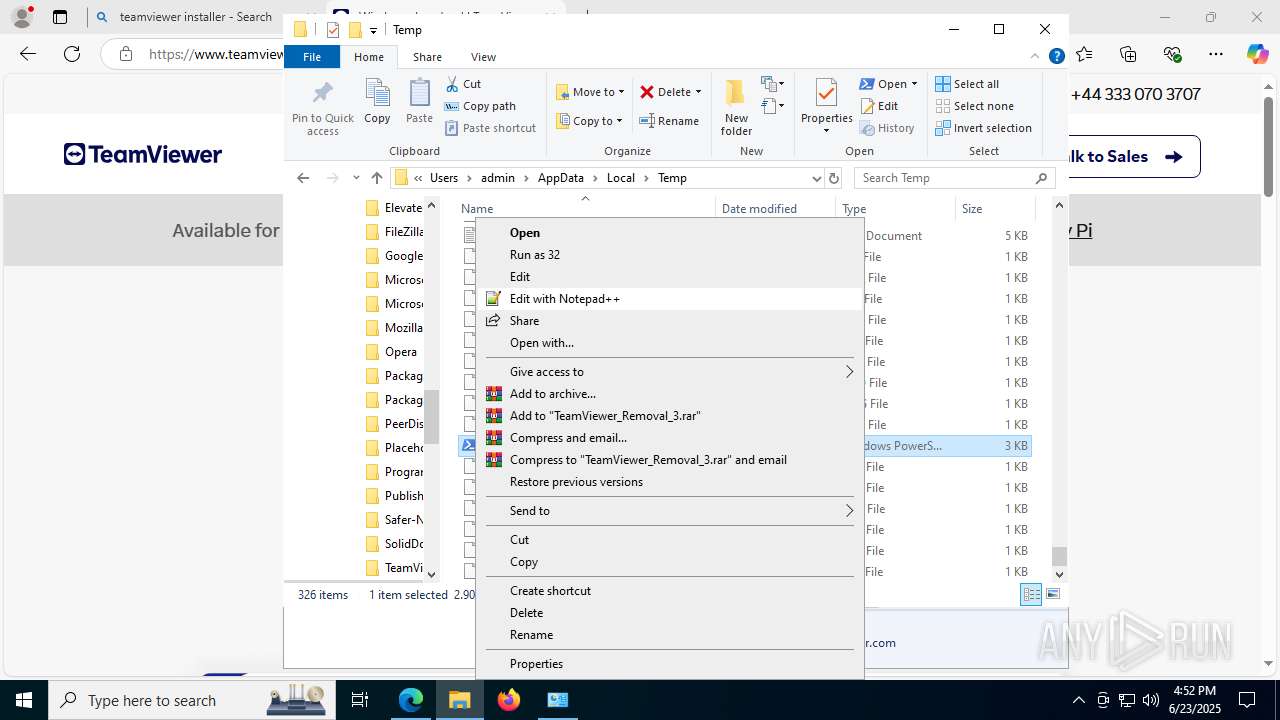
Create files in a temporary directory
- TeamViewer_Setup_x64.exe (PID: 6940)
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
- tv_x64.exe (PID: 7968)
- TeamViewer.exe (PID: 8120)
Reads Microsoft Office registry keys
- TeamViewer_.exe (PID: 5252)
- TeamViewer_.exe (PID: 3836)
Process checks whether UAC notifications are on
- TeamViewer_.exe (PID: 5252)
Process checks computer location settings
- TeamViewer_.exe (PID: 5252)
- MicrosoftEdgeUpdate.exe (PID: 2588)
- TeamViewer.exe (PID: 8120)
- TeamViewer_Service.exe (PID: 7304)
Creates files in the program directory
- TeamViewer_.exe (PID: 3836)
- tv_x64.exe (PID: 8140)
- MicrosoftEdgeWebview2Setup.exe (PID: 8176)
- TeamViewer_Service.exe (PID: 7304)
- crashpad_handler.exe (PID: 7060)
TEAMVIEWER has been detected
- TeamViewer_.exe (PID: 3836)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 5992)
- regsvr32.exe (PID: 7688)
- regsvr32.exe (PID: 7268)
- tv_x64.exe (PID: 7968)
- MicrosoftEdgeWebview2Setup.exe (PID: 8176)
- tv_x64.exe (PID: 8140)
- wermgr.exe (PID: 868)
- crashpad_handler.exe (PID: 7060)
- TeamViewer.exe (PID: 8120)
- tv_w32.exe (PID: 2040)
- tv_x64.exe (PID: 5012)
- crashpad_handler.exe (PID: 6016)
- powershell.exe (PID: 5908)
- TeamViewer.exe (PID: 7928)
- explorer.exe (PID: 4380)
- powershell.exe (PID: 4984)
- TeamViewer_Service.exe (PID: 7304)
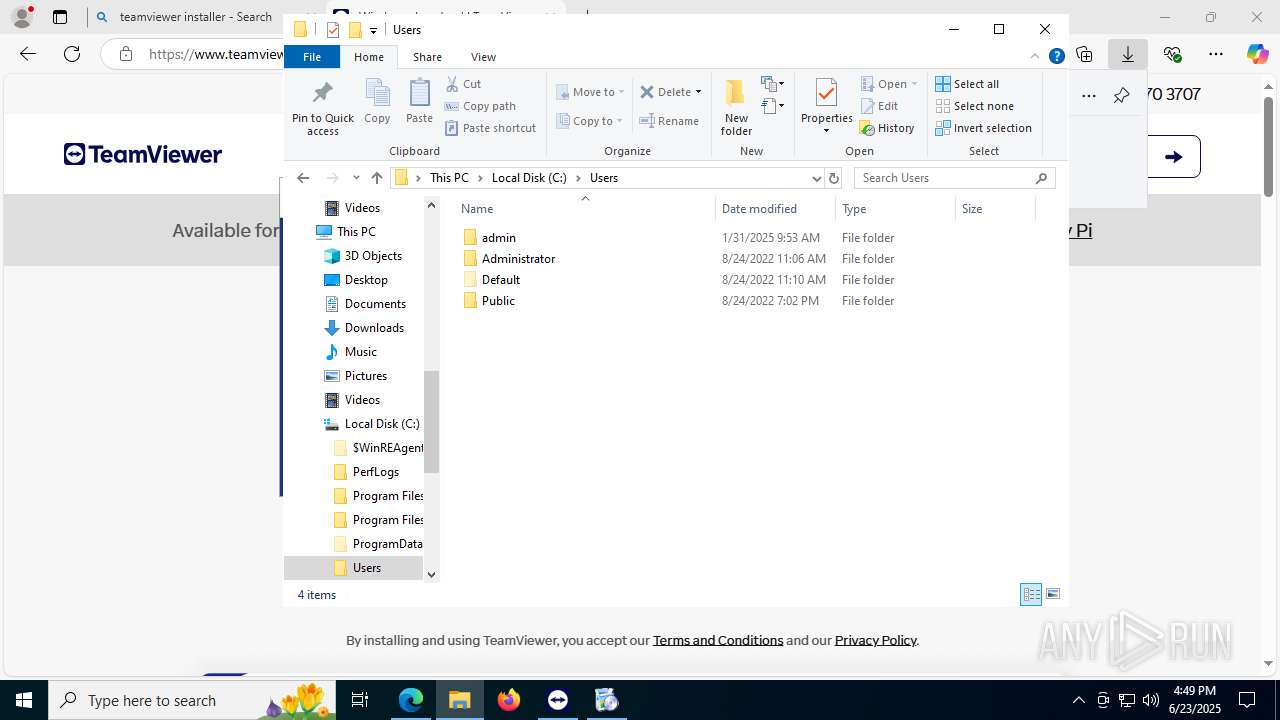
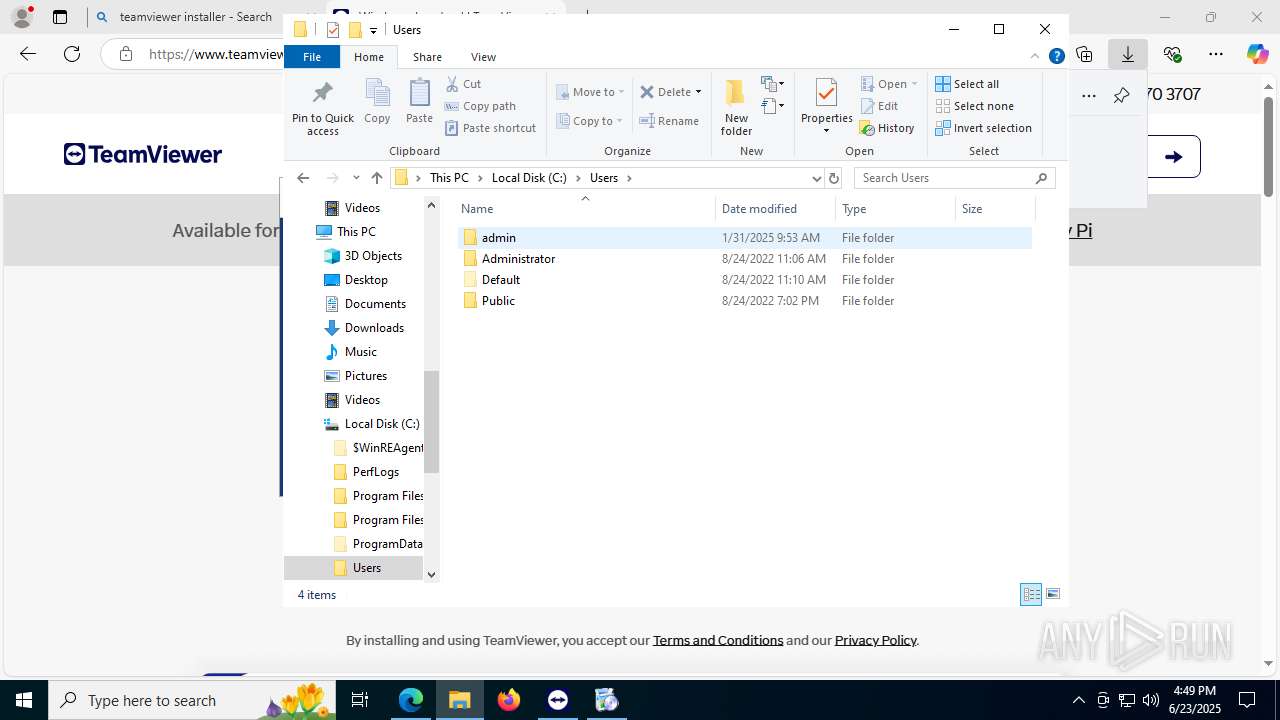
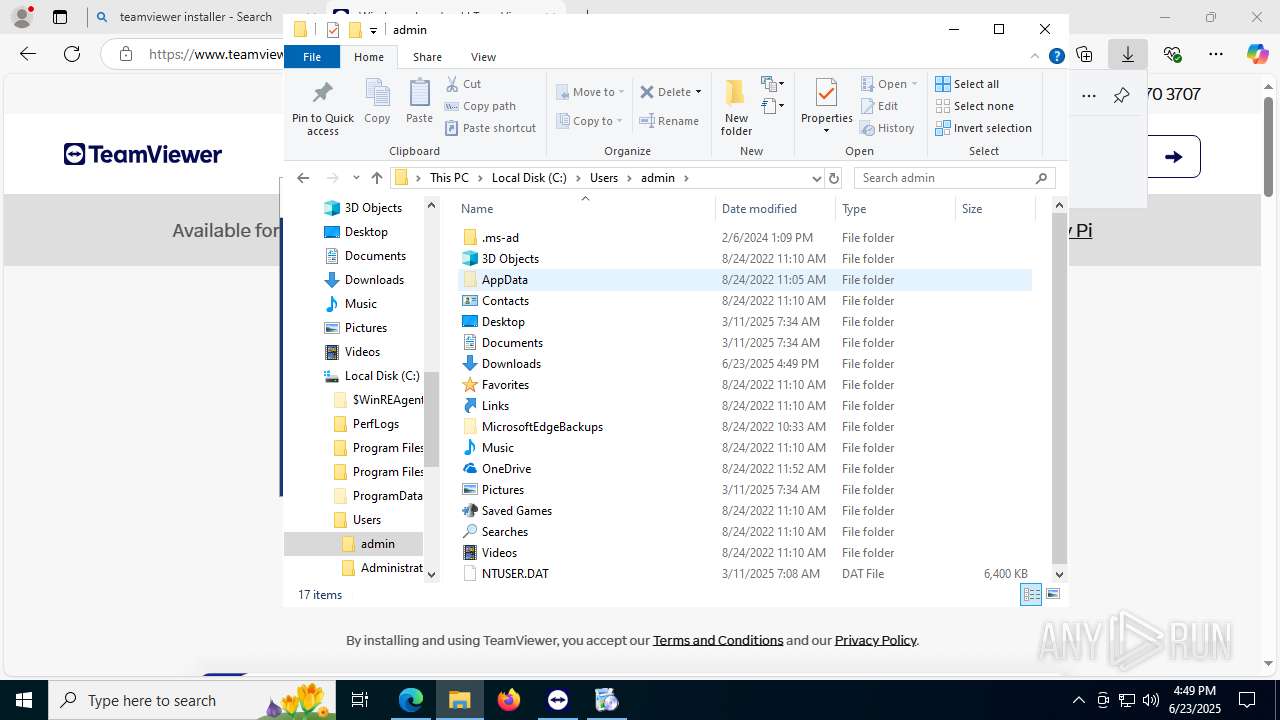
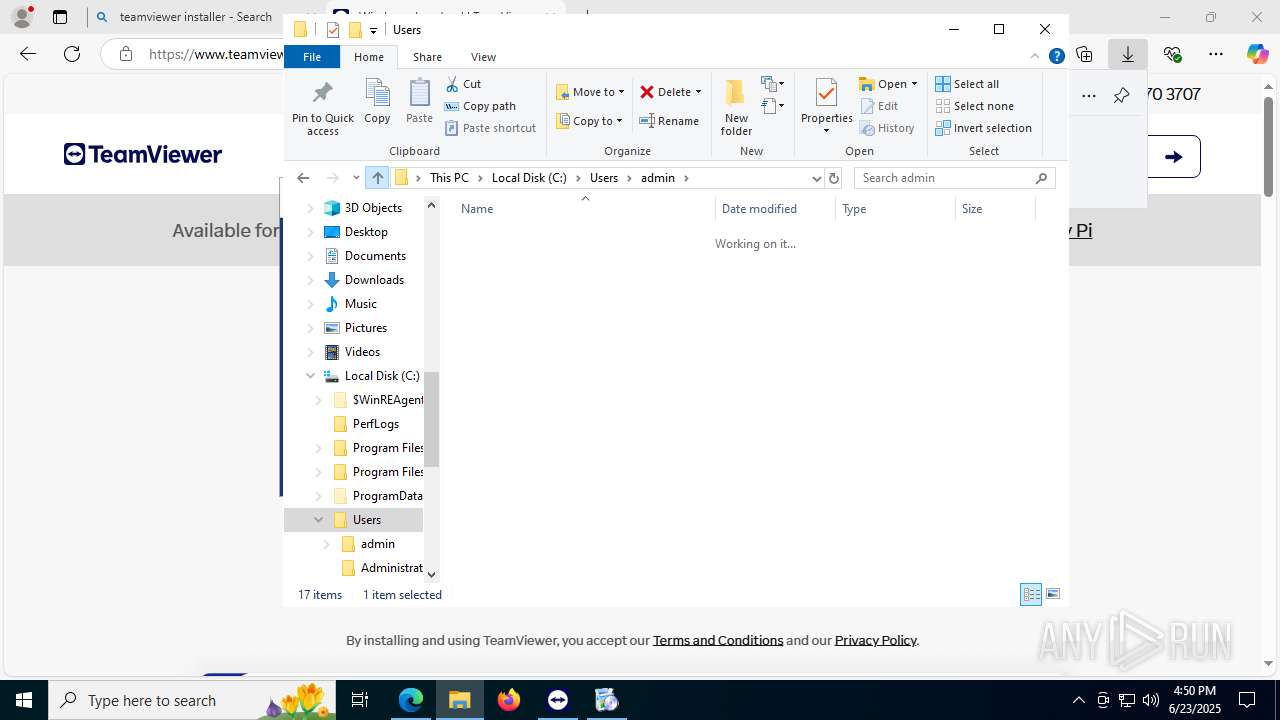
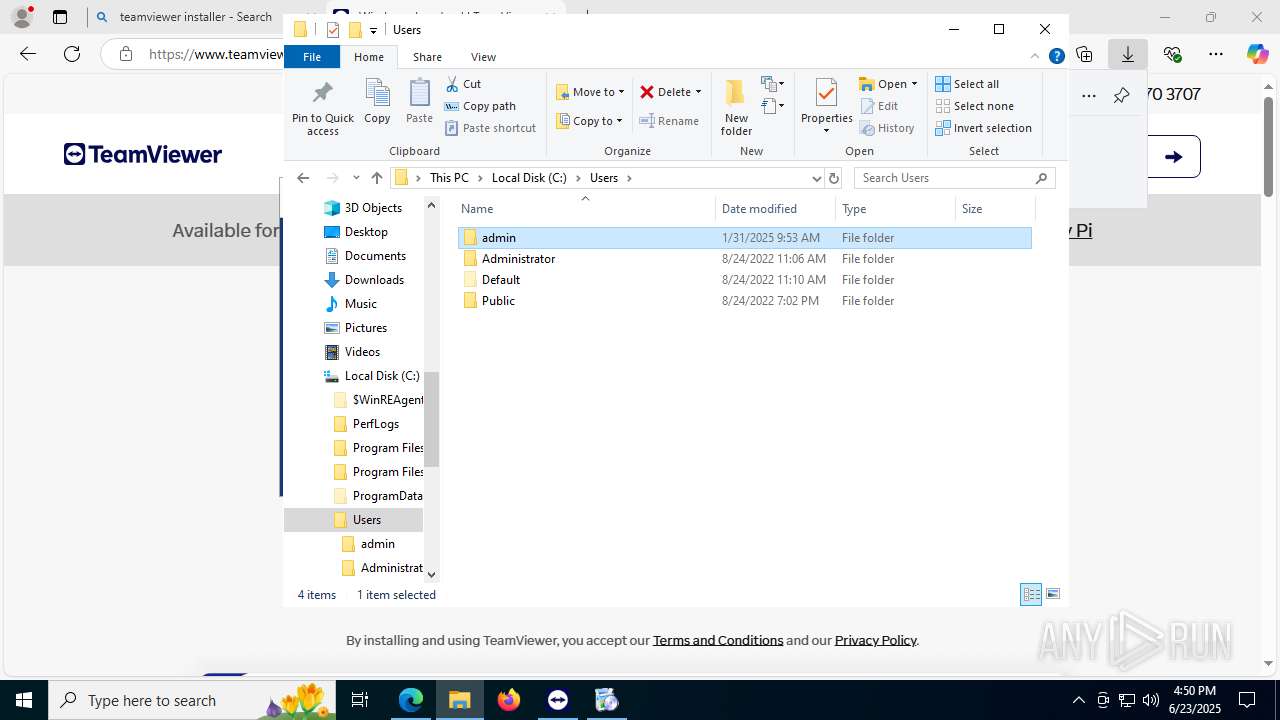
Creates files or folders in the user directory
- TeamViewer_.exe (PID: 3836)
- TeamViewer.exe (PID: 8120)
- crashpad_handler.exe (PID: 6016)
- TeamViewer.exe (PID: 7928)
- wermgr.exe (PID: 868)
TeamViewer related mutex has been found
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 5992)
- TeamViewer_.exe (PID: 5252)
- tv_x64.exe (PID: 8140)
- tv_x64.exe (PID: 7968)
- TeamViewer_Service.exe (PID: 7304)
- TeamViewer.exe (PID: 8120)
- tv_x64.exe (PID: 5012)
- tv_w32.exe (PID: 2040)
- TeamViewer.exe (PID: 7928)
UPX packer has been detected
- TeamViewer_.exe (PID: 3836)
Reads the machine GUID from the registry
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 5992)
- tv_x64.exe (PID: 8140)
- tv_x64.exe (PID: 7968)
- drvinst.exe (PID: 7464)
- TeamViewer_Service.exe (PID: 7304)
- TeamViewer.exe (PID: 8120)
- tv_x64.exe (PID: 5012)
- tv_w32.exe (PID: 2040)
- TeamViewer.exe (PID: 7928)
Reads the software policy settings
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 5992)
- tv_x64.exe (PID: 8140)
- tv_x64.exe (PID: 7968)
- drvinst.exe (PID: 7464)
- MicrosoftEdgeUpdate.exe (PID: 2588)
- wermgr.exe (PID: 868)
- TeamViewer_Service.exe (PID: 7304)
- TeamViewer.exe (PID: 8120)
- tv_x64.exe (PID: 5012)
- tv_w32.exe (PID: 2040)
- TeamViewer.exe (PID: 7928)
- slui.exe (PID: 5416)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 2588)
- slui.exe (PID: 5416)
- wermgr.exe (PID: 868)
- TeamViewer.exe (PID: 8120)
Reads the time zone
- TeamViewer_Service.exe (PID: 7304)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
243
Monitored processes
84
Malicious processes
12
Suspicious processes
1
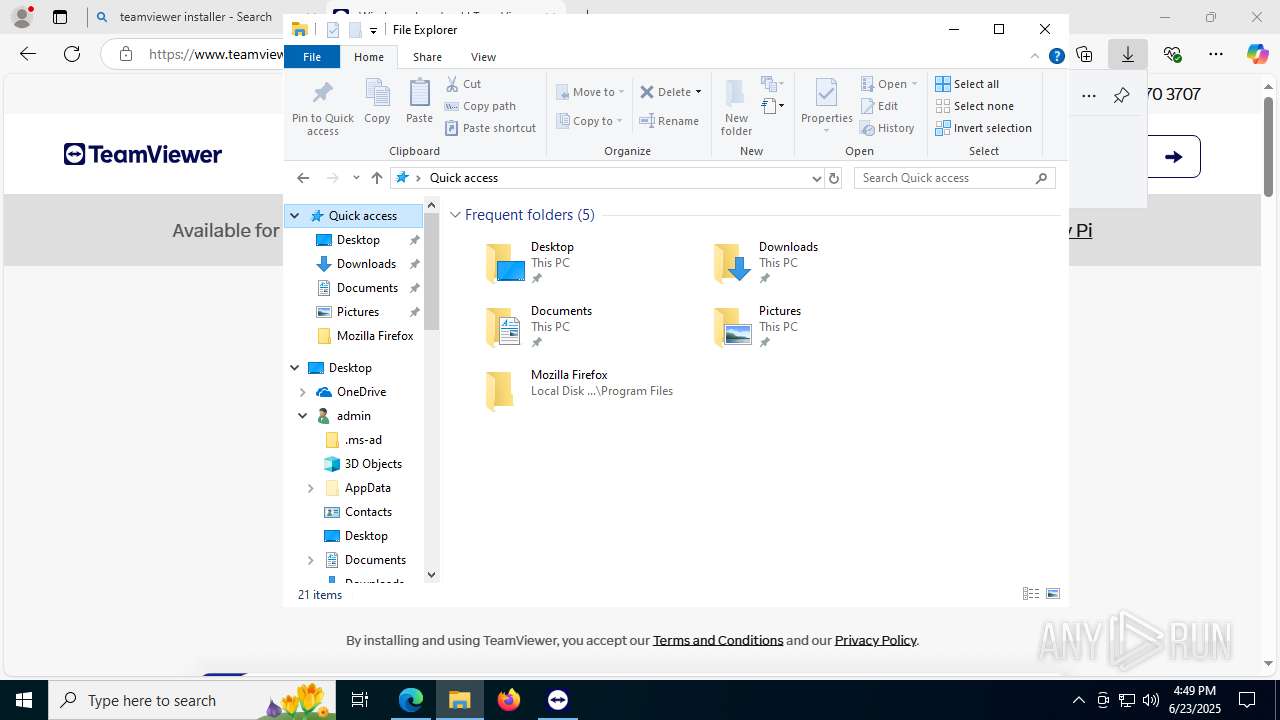
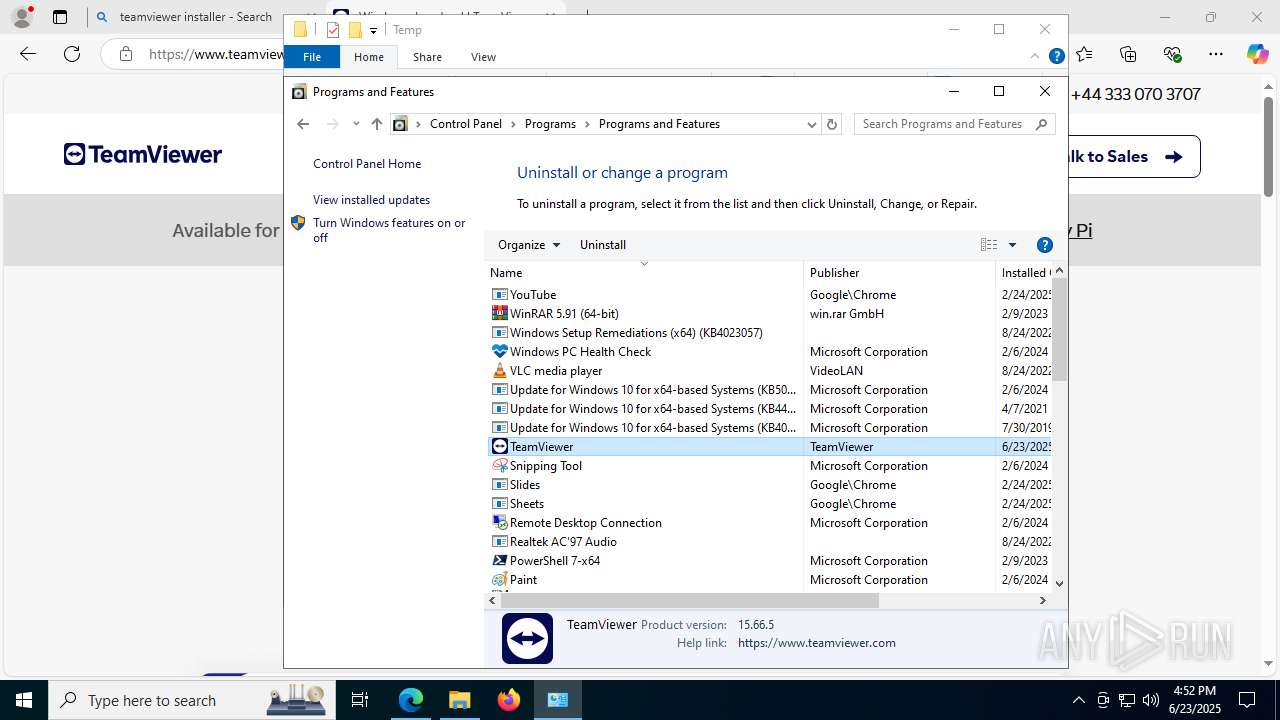
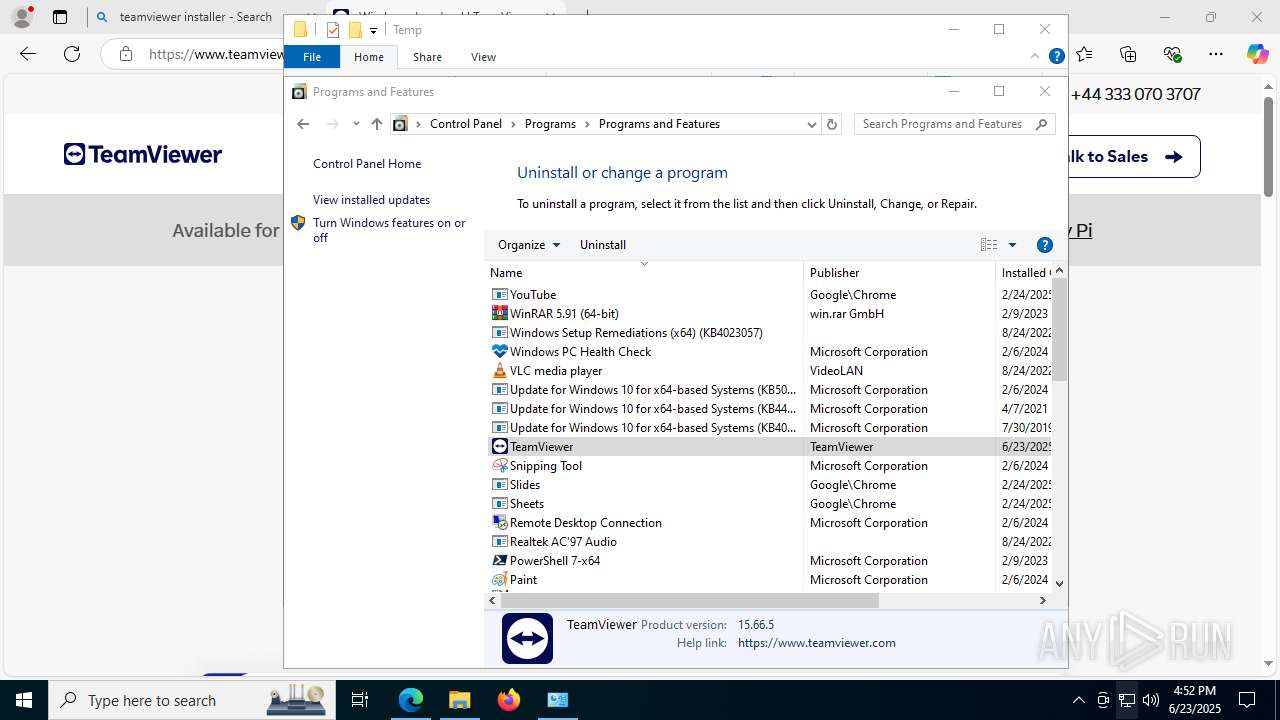
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "2588" "1032" "716" "1832" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc3e8ff208,0x7ffc3e8ff214,0x7ffc3e8ff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4384,i,12403426264272113781,3979248718328203493,262144 --variations-seed-version --mojo-platform-channel-handle=7600 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --always-read-main-dll --field-trial-handle=8104,i,12403426264272113781,3979248718328203493,262144 --variations-seed-version --mojo-platform-channel-handle=5552 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=8316,i,12403426264272113781,3979248718328203493,262144 --variations-seed-version --mojo-platform-channel-handle=8276 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1816 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\TeamViewer\tv_w32.exe" --action hooks --log C:\Program Files\TeamViewer\TeamViewer15_Logfile.log | C:\Program Files\TeamViewer\tv_w32.exe | — | TeamViewer_Service.exe | |||||||||||
User: SYSTEM Company: TeamViewer Germany GmbH Integrity Level: SYSTEM Description: TeamViewer Exit code: 9 Version: 15.66.5.0 Modules
| |||||||||||||||
| 2072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\TeamViewer_Removal_3.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
89 514
Read events
88 552
Write events
948
Delete events
14
Modification events
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 43C87C44D6962F00 | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E2D38244D6962F00 | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {72B8106E-0209-4963-90F3-91440E75395C} | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0F0DFF30-465D-4C46-AB5B-2E82057EB015} | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BF0D091E-B49E-4A22-9827-9299D5000074} | |||
| (PID) Process: | (1812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {61CB19BE-172B-4BA6-818C-F76434000125} | |||
Executable files
333
Suspicious files
657
Text files
196
Unknown types
86
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF177b4a.TMP | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF177b5a.TMP | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF177b5a.TMP | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF177b5a.TMP | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF177b98.TMP | — | |
MD5:— | SHA256:— | |||
| 1812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
291
DNS requests
308
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4968 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CJucFVOCs5BPvj2j8MmoAiFZvDjTekq66rn_SP3Ds28&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 184.24.77.23:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 184.24.77.23:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 184.24.77.23:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
1380 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAkQWITrlZ07yLmU%2BRintu4%3D | unknown | — | — | whitelisted |
6180 | WmiPrvSE.exe | GET | 200 | 184.24.77.23:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6700 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6180 | WmiPrvSE.exe | 184.24.77.23:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6180 | WmiPrvSE.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1380 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1380 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4968 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4968 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4968 | msedge.exe | Misc activity | ET REMOTE_ACCESS TeamViewer RMM Domain (teamviewer .com) in DNS Lookup |
4968 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4968 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4968 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4968 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
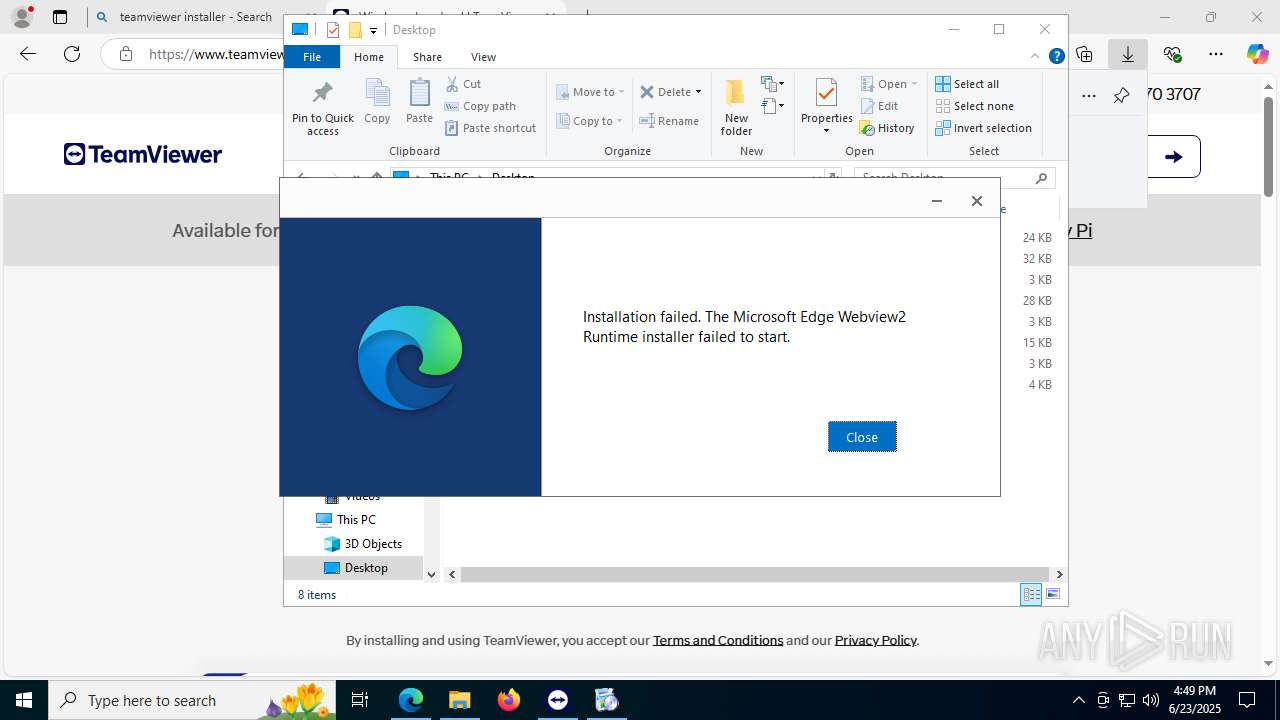
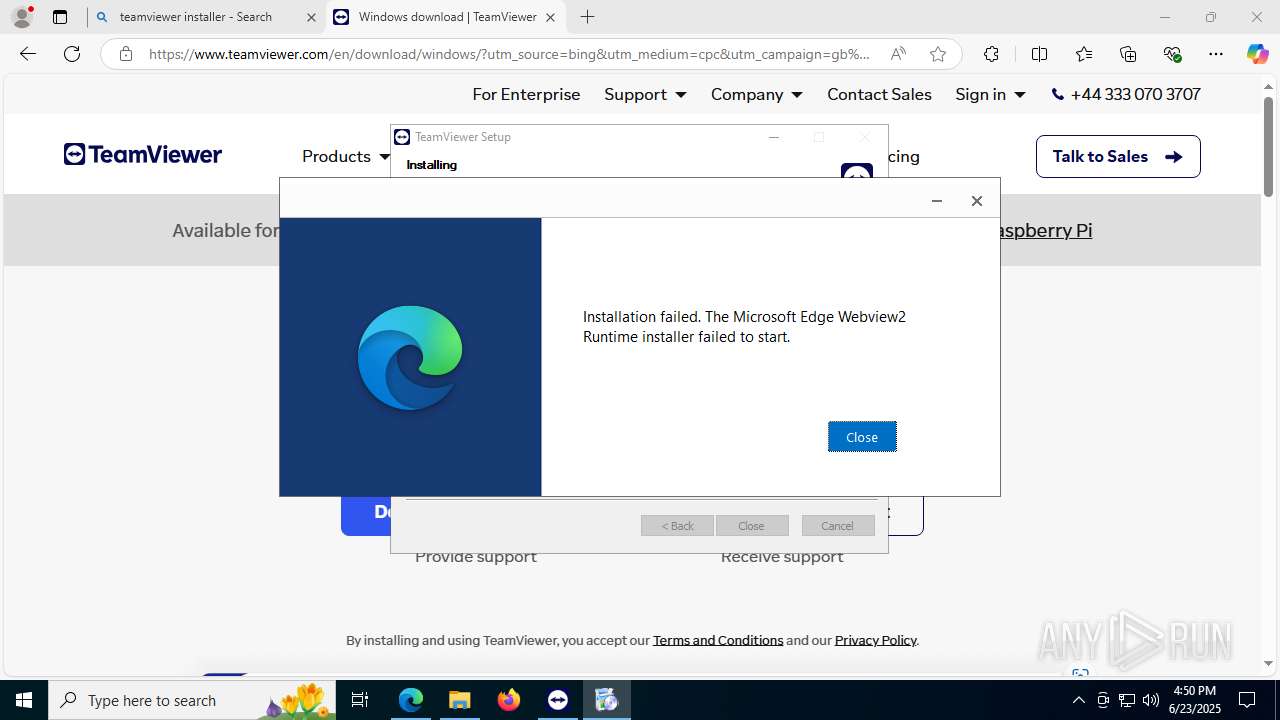
TeamViewer.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
TeamViewer.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
TeamViewer.exe | used displayLanguage: en
|
TeamViewer.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
TeamViewer.exe | used displayLanguage: en
|