| URL: | https://www.googleadservices.com/pagead/aclk?sa=L&ai=CBLG3LRZyZYenD5Wy9fgPvI6A0AijkNavc-DM5-DbEOCluNb5PhABINLa8wxg7fzdhawboAGX3Oa5KMgBCakC9LOtpXAasj7gAgCoAwHIAwiqBNoDT9ADv1h7_EvMuZwktX_Zdphc3pwvVs2bssQE2eIX8rxu3P0xMVJQF3YdBAdcpTKDuI4C6CMoNGKa9lHWBRRN1Fheic_RXVQAFFLeza65UbQTMQTgyh4Ln6QEckBuJV1LySGGx90QCB4LtvNH4g5T5Vj6THnoVBEOTIO6J8kDD2l91IfdbB-qpyspkUktZb8DbhdVZrIvUr65Tn14nsNmFAq9NVUwN_FH_tAkSI8ALrkgP_GEnHdMQwEqAvLvtmDXJYKvhoSJOeG6WCaMWXZL-6L8xqtdAu-cS0lN3BW9ItA8xD8VVHTXfbsLqaqdKClGiSw10IZe7z6RtcweAiY1SYEpgg-6GSpzswSLnka9q5UaZymc4AHBFL5rX1GzvFzmzXc1j13rR-RIcz5aDNtc9hOZqRzMjK6JhWw8Y7na2D7dKHMi-wtJxK9XJ9Lf8yJm90N_RQdYsQaqot1W3IQj_Q-qcs0znKWn0scwSH-lXWSiMMa5Dfu5qlsVfJx0vqJJ6L1GZYABENRoYCSoIAdAh8yGwJ-7CbdsDNPu0apNJQGi0WprYmC9DqL5FIX4pjoXTMCYMK5-X4uBUquEC409RoDTglV9AOitWlT_AtRgLDkIVy1j_Mw6jAkFwATh6YiFlQTgBAGIBbKI7vFIoAYugAeXlLeZA6gH2baxAqgHjs4bqAeT2BuoB-6WsQKoB_6esQKoB9XJG6gHpr4bqAeaBqgH89EbqAeW2BuoB6qbsQKoB4OtsQKoB_-esQKoB9-fsQKoB8qpsQKoB-ulsQLYBwDSCCYIiOGAeBABGB0yBPuCgQ46B5rQg4iAiAxIvf3BOliKiY6Xgf6CA5oJH2h0dHBzOi8vd3d3Lm9uaS5wdC9wdC9nLWJhY2t1cC-xCcI8jK-eMAuOgAoDmAsByAsBgAwBogwQKg4KDOS0sQLutbECtbixAtoMEQoLEPCQ7eKNrpD9_QESAgEDqg0CUFTIDQHiDRMItM-Ol4H-ggMVFVkdCR08BwCK2BMN0BUBmBYB-BYBgBcB&ae=1&ase=2&gclid=EAIaIQobChMIx_GPl4H-ggMVFVkdCR08BwCKEAEYASAAEgLWq_D_BwE&num=1&cid=CAQSLQDICaaN-FnTf3Jw3ehSS_4pQgIjuKvl_0krso2AFsizyFOPM0_oYI8Hc78n8RgB&client=ca-pub-8597818050436831&rf=6&nx=102&ny=115&nis=4&dblrd=1&sig=AOD64_1sj0hyWT1yu0K2Rgk3fN_8NJEHJQ&adurl=https://tinyurl.com/J02Fz3EJzi |
| Full analysis: | https://app.any.run/tasks/70b9e402-16fe-482e-aedd-a0f7e4e4572a |
| Verdict: | Malicious activity |
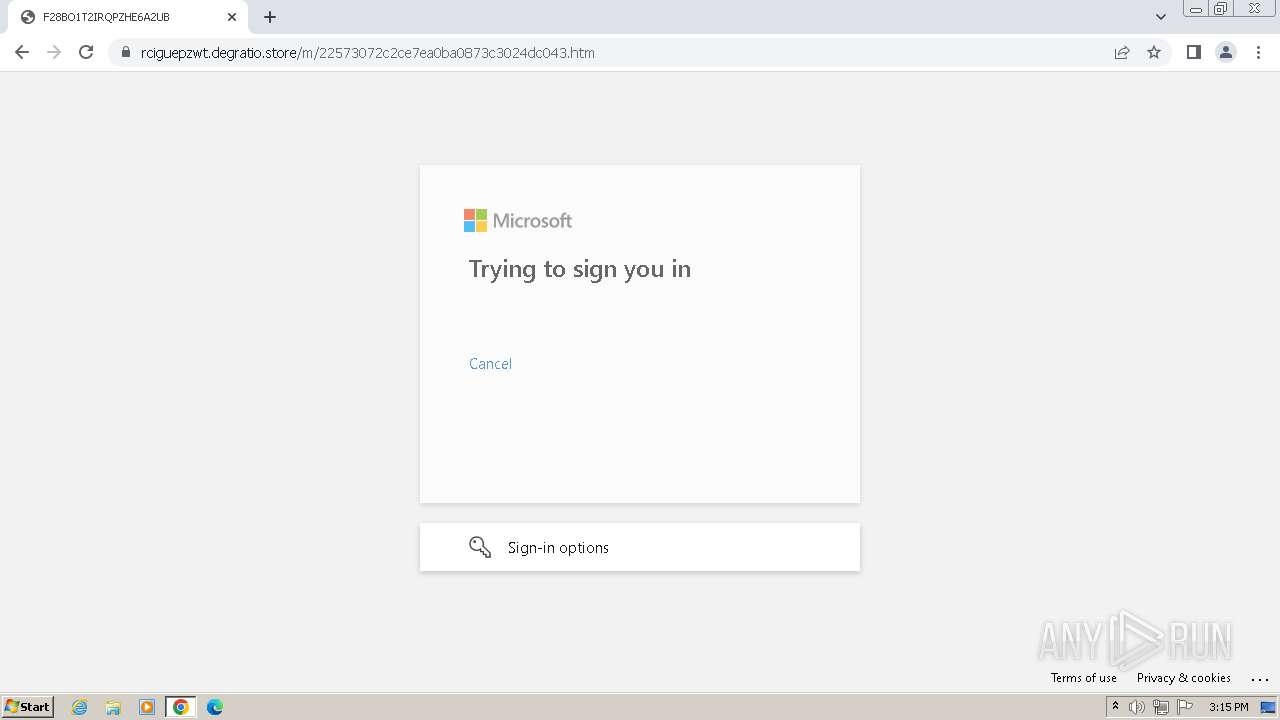
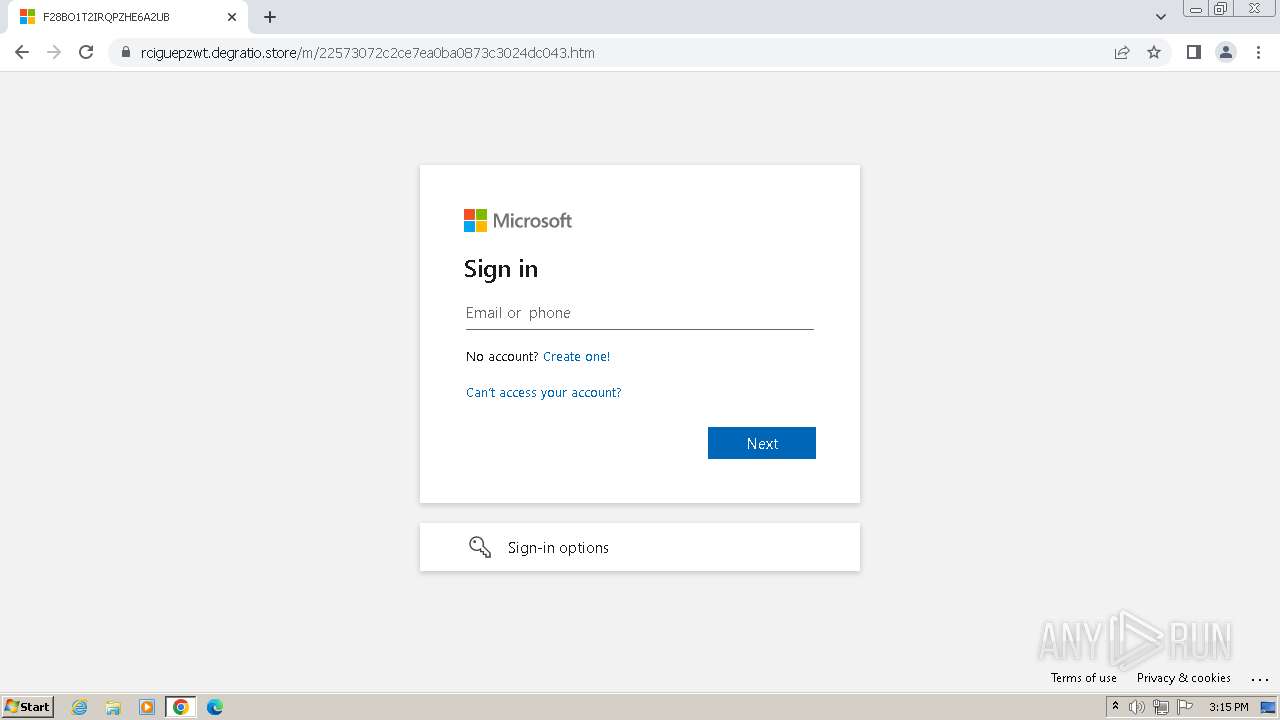
| Threats: | EvilProxy is a phishing-as-a-service (PhaaS) platform that enables cybercriminals to bypass multi-factor authentication (MFA) and hijack user sessions. It leverages reverse proxy techniques to harvest credentials and session cookies, posing a serious threat to both individuals and enterprises. |
| Analysis date: | May 07, 2024, 14:15:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 61AEA369E4E1937C0F6AD3705C2B9B14 |
| SHA1: | 37539E22E3718A47BA1387181181223339F605DB |
| SHA256: | CB9E80CD23746C150E76996198A24B3D42A89E1FB06BD82F64859E2C17CC92AE |
| SSDEEP: | 24:2DGx2dsVjyTaYCv3MmNwSvwvCsS1KMeUZFLrPcaKIYzzCNQcAKhd17q3E77kGCFM:5xKsVjWav3MmygwKRE4FnPRKIfCRKhMM |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 820)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 1980)
Reads the computer name
- wmpnscfg.exe (PID: 1980)
Manual execution by a user
- wmpnscfg.exe (PID: 1980)
Application launched itself
- chrome.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1508 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1268 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=3548 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3132 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=3572 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2036 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2012 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2972 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1116 --field-trial-handle=1152,i,1117334135831838817,2964213590998632800,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
2 868
Read events
2 831
Write events
37
Delete events
0
Modification events
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
18
Text files
19
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1042b8.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1042b8.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10471d.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF1056fb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
23
DNS requests
24
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
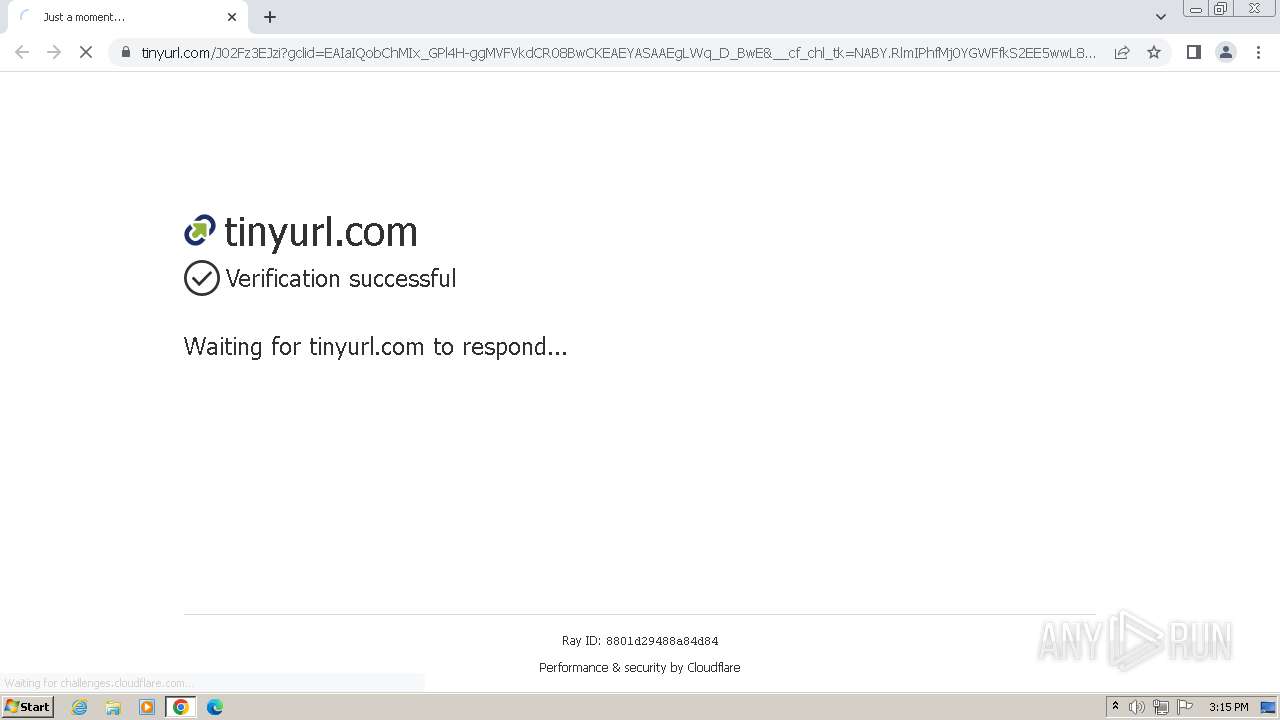
820 | chrome.exe | GET | 200 | 203.161.38.167:80 | http://j02fz3ejzi.newsmontanawalker.org/?gclid=EAIaIQobChMIx_GPl4H-ggMVFVkdCR08BwCKEAEYASAAEgLWq_D_BwE | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
820 | chrome.exe | 172.217.16.194:443 | www.googleadservices.com | GOOGLE | US | whitelisted |
3968 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
820 | chrome.exe | 74.125.193.84:443 | accounts.google.com | GOOGLE | US | unknown |
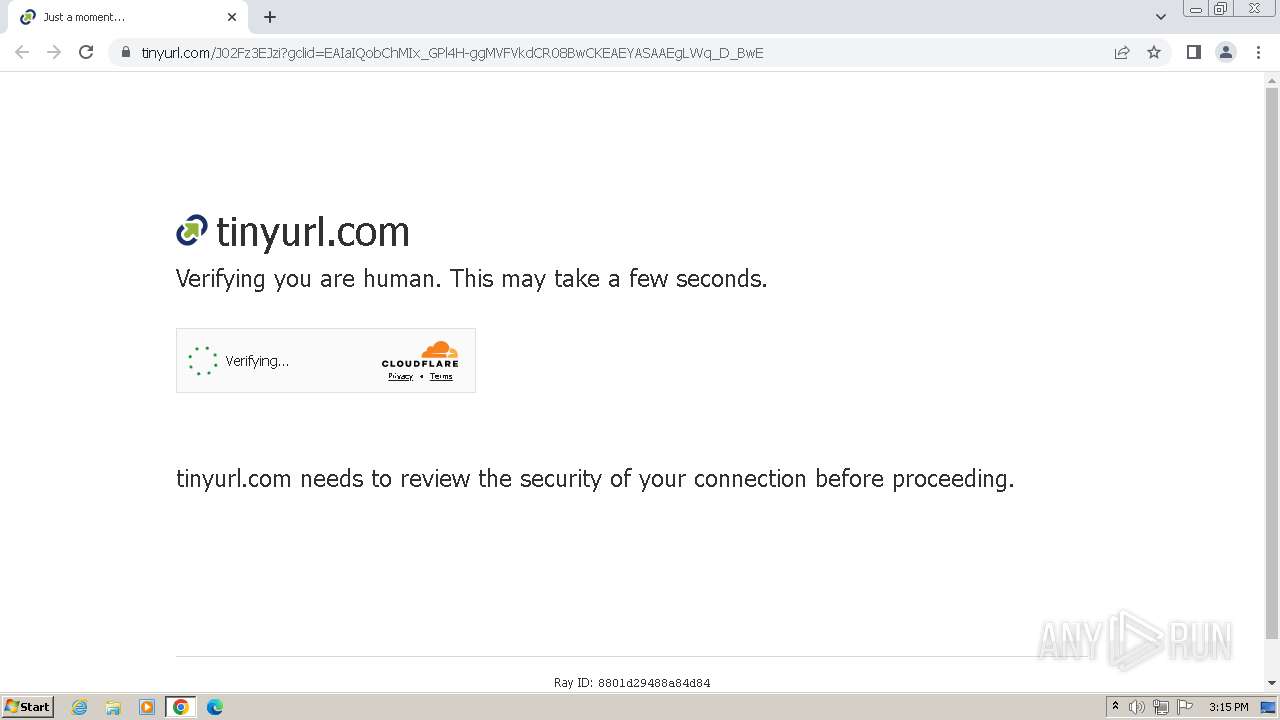
820 | chrome.exe | 172.67.1.225:443 | tinyurl.com | CLOUDFLARENET | US | unknown |
820 | chrome.exe | 104.17.2.184:443 | challenges.cloudflare.com | CLOUDFLARENET | — | unknown |
820 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.googleadservices.com |
| whitelisted |
accounts.google.com |
| shared |
tinyurl.com |
| shared |
challenges.cloudflare.com |
| whitelisted |
www.google.com |
| whitelisted |
j02fz3ejzi.newsmontanawalker.org |
| unknown |
rciguepzwt.degratio.store |
| unknown |
api.ipify.org |
| shared |
content-autofill.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
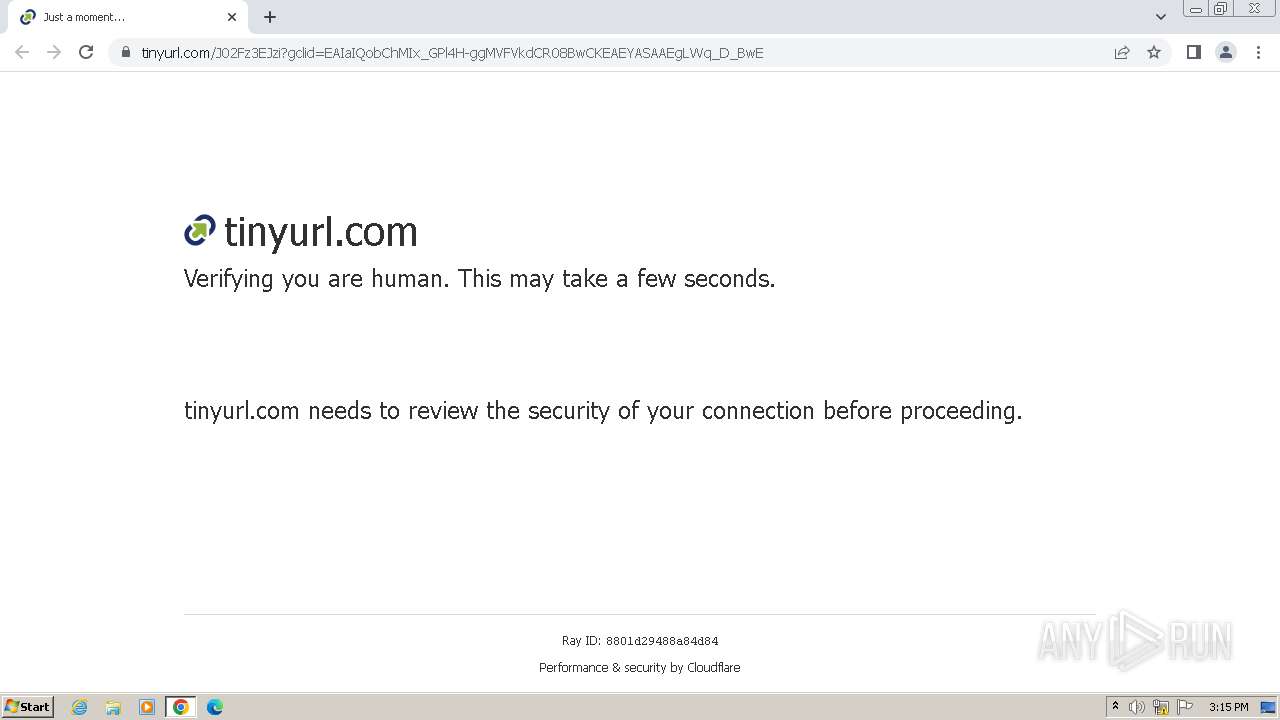
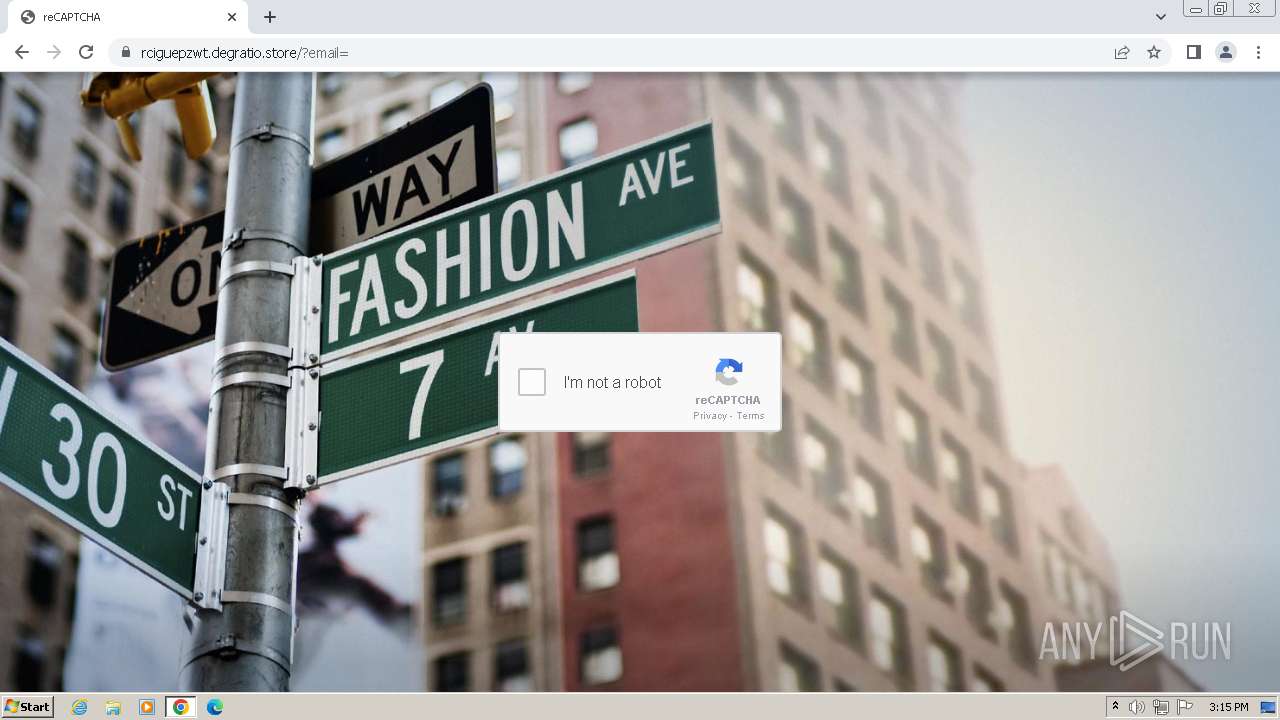
820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
820 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
820 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
820 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
820 | chrome.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
820 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] EvilProxy Connection Chain |