| File name: | file |
| Full analysis: | https://app.any.run/tasks/4a622be3-d22a-48e9-bbff-e65e50b21e6d |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | December 02, 2023, 14:27:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F5D6E5056DEA42913C3191340B0A4C0B |
| SHA1: | 1D7138A2BBD768CD32A5FB1F69B2FC1F9A8C51AC |
| SHA256: | CB1C506BE26EB65BD7C79ABC7E54D356ADEA2C3E0993E605E98CC39611F7ADD1 |
| SSDEEP: | 6144:bvT8NHBPdEqJnqo2c6ZdhJLfXlsYZo5fgxsSdMeOuTb+X:bgEKnqFc6lVfXlsLa6X |
MALICIOUS
Drops the executable file immediately after the start
- file.exe (PID: 1584)
- cmd.exe (PID: 1760)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2648)
Connects to the CnC server
- svchost.exe (PID: 2648)
TOFSEE has been detected (SURICATA)
- svchost.exe (PID: 572)
Creates a writable file in the system directory
- svchost.exe (PID: 572)
TOFSEE has been detected (YARA)
- svchost.exe (PID: 572)
SUSPICIOUS
Reads the Internet Settings
- file.exe (PID: 1584)
Starts CMD.EXE for commands execution
- file.exe (PID: 1584)
Starts SC.EXE for service management
- file.exe (PID: 1584)
Executes as Windows Service
- getbukfb.exe (PID: 2548)
Connects to unusual port
- svchost.exe (PID: 2648)
- svchost.exe (PID: 572)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 572)
Uses NETSH.EXE to add a firewall rule or allowed programs
- file.exe (PID: 1584)
Creates or modifies Windows services
- svchost.exe (PID: 572)
Application launched itself
- svchost.exe (PID: 572)
Connects to SMTP port
- svchost.exe (PID: 572)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 572)
INFO
Checks supported languages
- file.exe (PID: 1584)
- getbukfb.exe (PID: 2548)
Create files in a temporary directory
- file.exe (PID: 1584)
Reads the computer name
- file.exe (PID: 1584)
- getbukfb.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Tofsee
(PID) Process(572) svchost.exe
C2 (2)vanaheim.cn
jotunheim.name
Encrypted Strings (59)c:\Windows
\system32\
ImagePath
.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
MSConfig
/r
.exe
cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s
svchost.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
ConsentPromptBehaviorAdmin
PromptOnSecureDesktop
MSConfig
:.repos
USERPROFILE
\Local Settings:.repos
USERPROFILE
\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos
USERPROFILE
\wincookie.repos
TMP
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
SYSTEM\CurrentControlSet\services
ImagePath
SYSTEM\CurrentControlSet\services
SYSTEM\CurrentControlSet\services
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
.exe
qazwsxed
%s%i%i%i%i.bat
@echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0
svchost.exe
.exe
/u
USERPROFILE
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/d
/e
/d
/e
.exe
"%s" /u"%s"
USERPROFILE
.exe
USERPROFILE
USERPROFILE
ver=%d lid=%d
win=%X/%d sid=%s
rep=%s
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Clipper DOS Executable (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:01:06 07:37:57+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 95744 |
| InitializedDataSize: | 3866112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x898e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 21.0.0.0 |
| ProductVersionNumber: | 34.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0373) |
| CharacterSet: | Unknown (63B6) |
| FileDescriptions: | Vellting |
| InternalName: | Bastard.exe |
| LegalTrademark1: | Fractal |
| OriginalFileName: | Lameros.exe |
| ProductName: | Jadocka |
| ProductVersion: | 57.38.26 |
Total processes
53
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | svchost.exe | C:\Windows\SysWOW64\svchost.exe | getbukfb.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Tofsee(PID) Process(572) svchost.exe C2 (2)vanaheim.cn jotunheim.name Encrypted Strings (59)c:\Windows \system32\ ImagePath .exe SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows\CurrentVersion\Run MSConfig /r .exe cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s svchost.exe SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System ConsentPromptBehaviorAdmin PromptOnSecureDesktop MSConfig :.repos USERPROFILE \Local Settings:.repos USERPROFILE \Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos USERPROFILE \wincookie.repos TMP Config Control Panel\Buses Config SOFTWARE\Microsoft\Buses Config Control Panel\Buses Config SOFTWARE\Microsoft\Buses SYSTEM\CurrentControlSet\services ImagePath SYSTEM\CurrentControlSet\services SYSTEM\CurrentControlSet\services SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows\CurrentVersion\Run .exe qazwsxed %s%i%i%i%i.bat @echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0 svchost.exe .exe /u USERPROFILE SOFTWARE\Microsoft\Windows\CurrentVersion\Run /d /e /d /e .exe "%s" /u"%s" USERPROFILE .exe USERPROFILE USERPROFILE ver=%d lid=%d
win=%X/%d sid=%s
rep=%s | |||||||||||||||
| 640 | sc description ytqpvkdx "wifi internet conection" | C:\Windows\System32\sc.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | sc start ytqpvkdx | C:\Windows\System32\sc.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1104 | cmd /C mkdir C:\Windows\SysWOW64\ytqpvkdx\ | C:\Windows\System32\cmd.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1212 | netsh advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\SysWOW64\svchost.exe" enable=yes>nul | C:\Windows\System32\netsh.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1760 | cmd /C move /Y "C:\Users\admin\AppData\Local\Temp\getbukfb.exe" C:\Windows\SysWOW64\ytqpvkdx\ | C:\Windows\System32\cmd.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1776 | sc create ytqpvkdx binPath= "C:\Windows\SysWOW64\ytqpvkdx\getbukfb.exe /d\"C:\Users\admin\AppData\Local\Temp\file.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\System32\sc.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
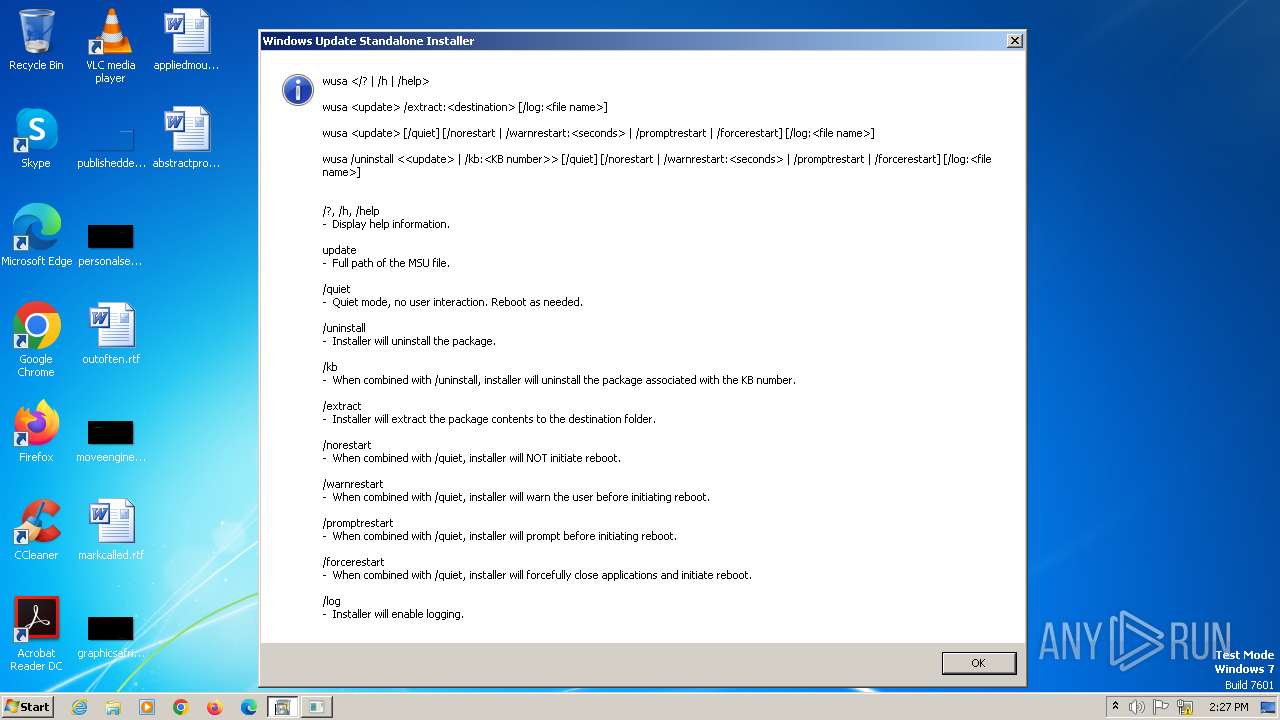
| 2216 | "C:\Windows\System32\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | C:\Windows\SysWOW64\ytqpvkdx\getbukfb.exe /d"C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Windows\SysWOW64\ytqpvkdx\getbukfb.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
Total events
1 062
Read events
1 006
Write events
56
Delete events
0
Modification events
| (PID) Process: | (1584) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1584) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1584) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1584) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (572) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\ytqpvkdx |
| Operation: | write | Name: | ImagePath |
Value: C:\Windows\SysWOW64\ytqpvkdx\getbukfb.exe /d"C:\Users\admin\AppData\Local\Temp\file.exe" | |||
| (PID) Process: | (572) svchost.exe | Key: | HKEY_USERS\.DEFAULT\Control Panel\Buses |
| Operation: | write | Name: | Config0 |
Value: 84C6503D69D2710024EDB47D450DD49D084297DCE82E72BAA49B15FDF47A751D27D1C2D087CD945D24EDB47D470DD49D024195DAF71261ADC06D04FDA6E22673BBC9154961CDA56813D886447235E3AC644490BDB57C26E9905B02CBF7BA54758DF21D5904FCAC6E1CDA824E753EE09D084295D9E13F4BB4C06D00FDADFD5430D59A430F3DFBAD6516DBB40E367B8BE90D4091BDB77F27E4975C0CCAC4E13B7E85C12B496DA0F15D15D883487634E2A5531AF459A44414B0BB8869FDC48D541CE4AD744A6BBFFF02579FC27D440DD49D642DF4D793E33598A46D34FDC741461EE4AD743C3CFDBA6B12C383486A3AE39D642DF4BD844D14DDA46D34FDC48D541DE4AD743D04CD945D24EDB47D440DD49D642DF4BD844D14DDA46D34FDC48D541DE4AD743DE1CC945D | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1584 | file.exe | C:\Users\admin\AppData\Local\Temp\getbukfb.exe | executable | |
MD5:D694A0AEF37E5A9C3A5F3475E06DE5F5 | SHA256:E380E29086F3E998472AAD4824B9A408A9E401396C14DE257C74DD8D4E53E398 | |||
| 1760 | cmd.exe | C:\Windows\SysWOW64\ytqpvkdx\getbukfb.exe | executable | |
MD5:D694A0AEF37E5A9C3A5F3475E06DE5F5 | SHA256:E380E29086F3E998472AAD4824B9A408A9E401396C14DE257C74DD8D4E53E398 | |||
| 572 | svchost.exe | C:\Windows\SysWOW64\config\systemprofile:.repos | binary | |
MD5:63E4C870245555F110BB465AAFDB1D3C | SHA256:1C3BE4021A55E95730F5D2FE0C89C4B86C300EB409F333B5FE17D4DFECCD44EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
32
DNS requests
17
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
572 | svchost.exe | GET | 200 | 142.250.184.196:80 | http://www.google.com/ | unknown | html | 2.00 Kb | unknown |
572 | svchost.exe | GET | 200 | 142.250.184.196:80 | http://www.google.com/ | unknown | html | 2.00 Kb | unknown |
572 | svchost.exe | GET | 200 | 142.250.184.196:80 | http://www.google.com/ | unknown | html | 2.00 Kb | unknown |
572 | svchost.exe | GET | 200 | 142.250.184.196:80 | http://www.google.com/ | unknown | html | 2.00 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
572 | svchost.exe | 20.112.250.133:80 | microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
572 | svchost.exe | 158.160.82.150:443 | vanaheim.cn | Yandex.Cloud LLC | RU | unknown |
572 | svchost.exe | 52.101.40.26:25 | microsoft-com.mail.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
572 | svchost.exe | 80.66.75.77:485 | — | Kakharov Orinbassar Maratuly | RU | unknown |
2648 | svchost.exe | 213.91.128.133:10060 | fastpool.xyz | Vivacom | BG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
vanaheim.cn |
| malicious |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
15.216.24.216.dnsbl.sorbs.net |
| unknown |
15.216.24.216.bl.spamcop.net |
| unknown |
15.216.24.216.zen.spamhaus.org |
| unknown |
15.216.24.216.sbl-xbl.spamhaus.org |
| unknown |
15.216.24.216.cbl.abuseat.org |
| unknown |
fastpool.xyz |
| unknown |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
572 | svchost.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Tofsee Successful Connection |
2648 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
572 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 20 |
572 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 20 |
572 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 20 |
572 | svchost.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2648 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2648 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
5 ETPRO signatures available at the full report