| File name: | recovery42.exe |
| Full analysis: | https://app.any.run/tasks/2af1a82e-8447-4cbe-a6a1-18b089a6111d |
| Verdict: | Malicious activity |
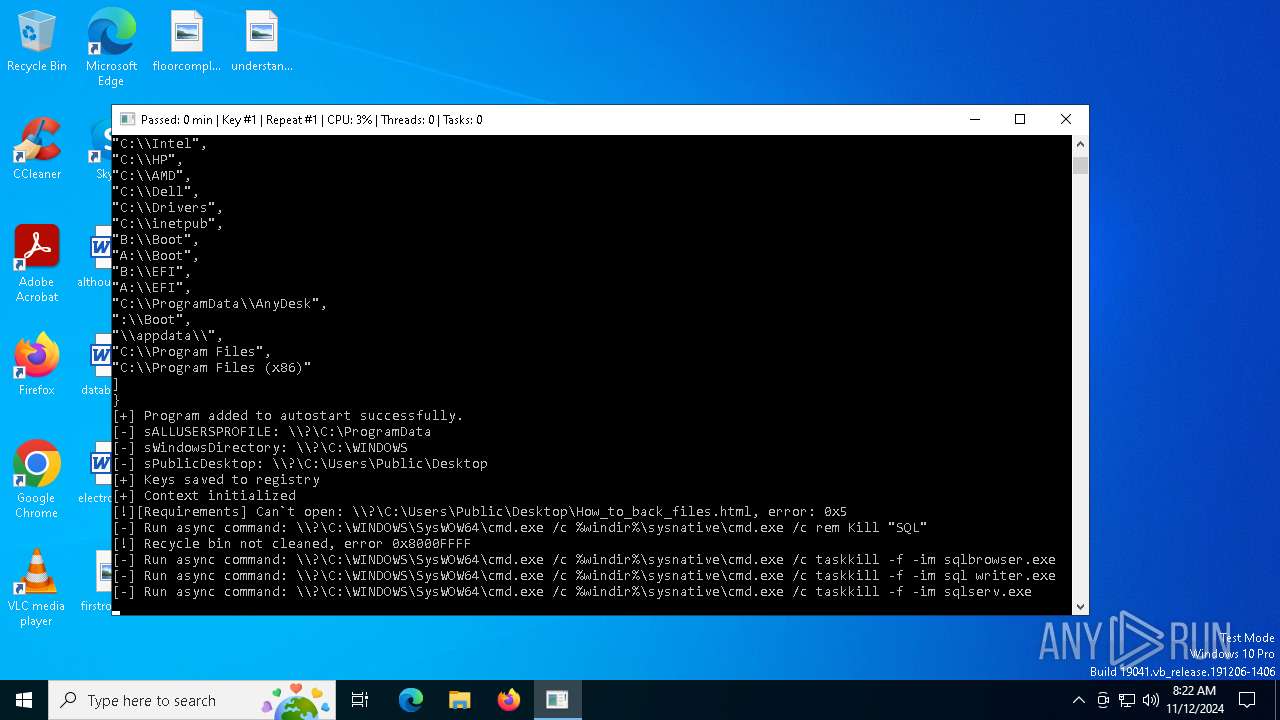
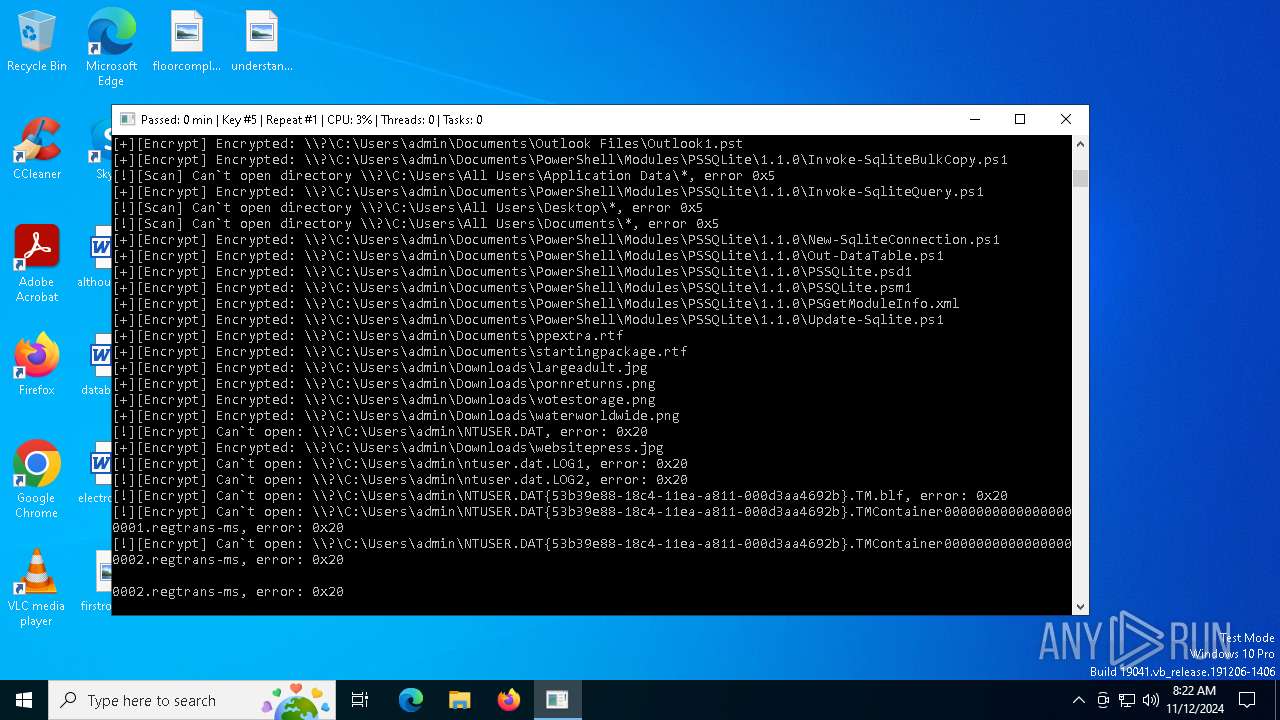
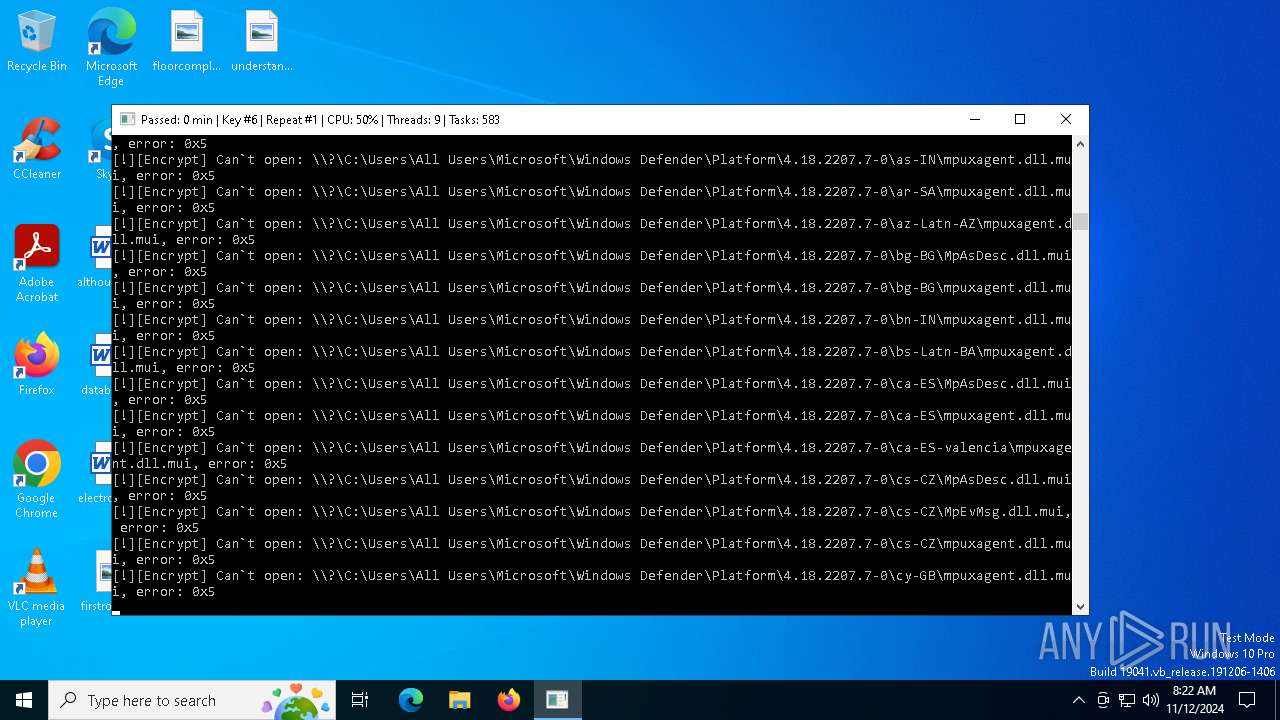
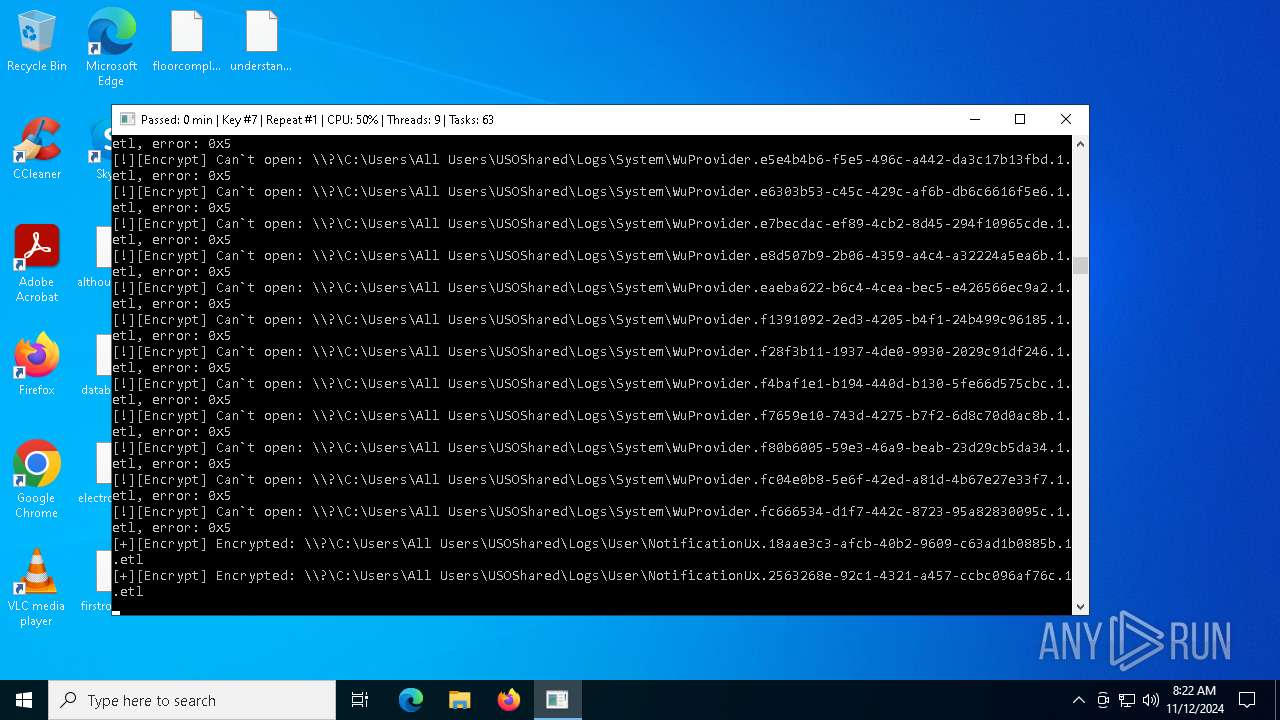
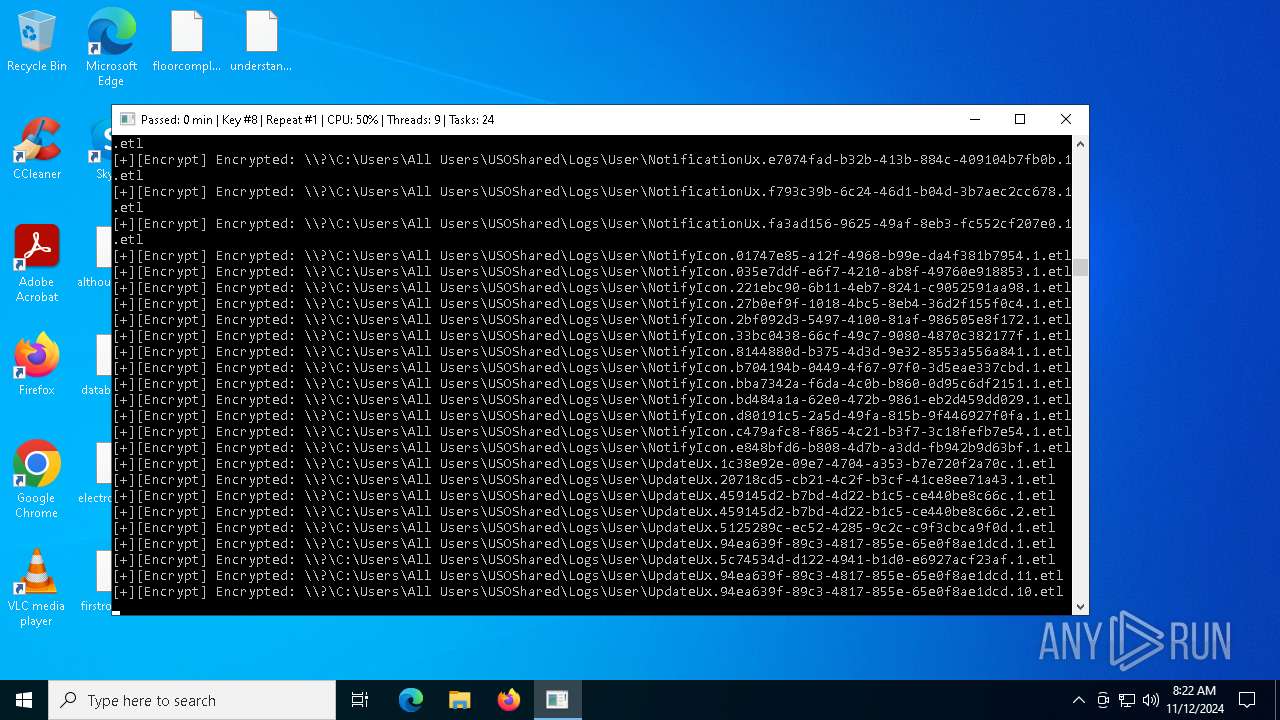
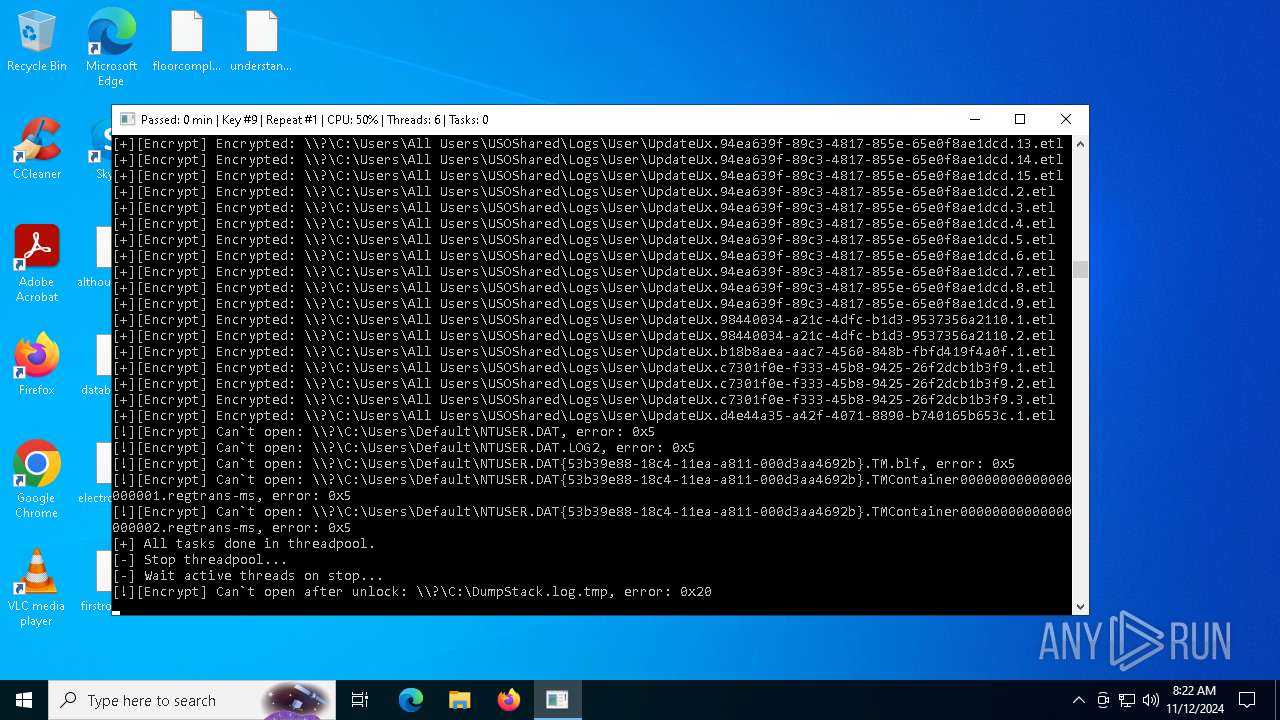
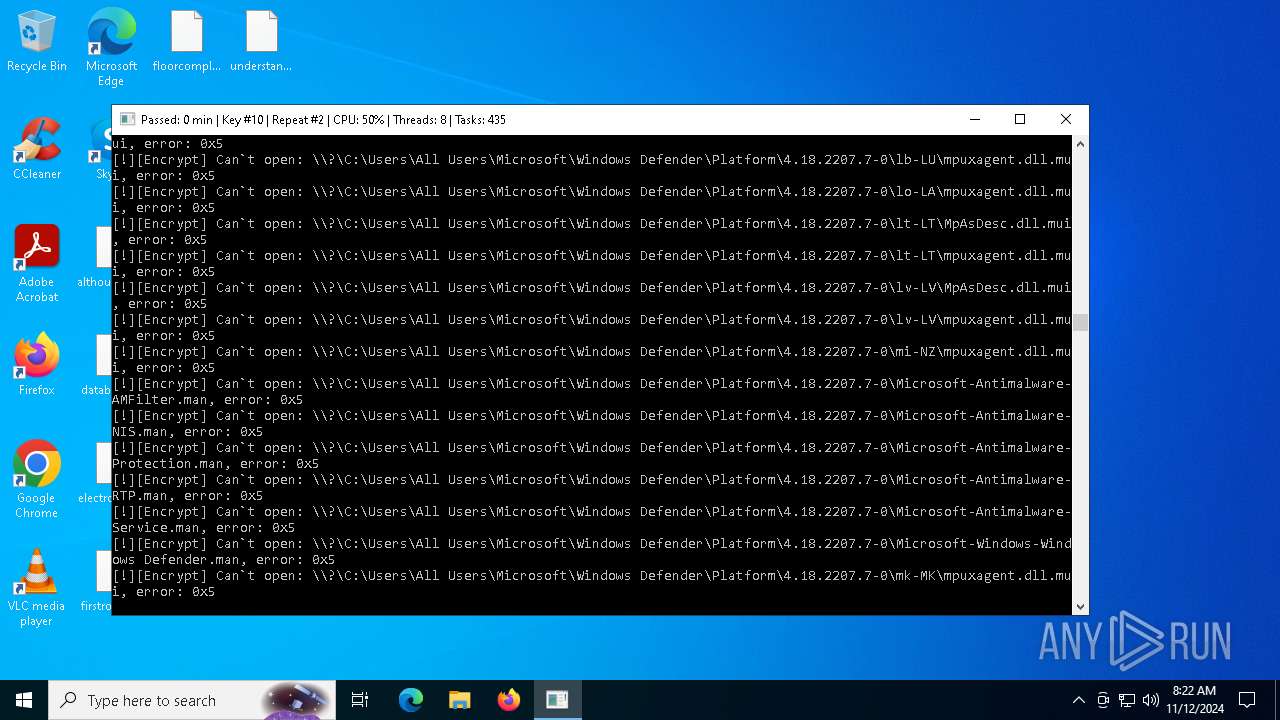
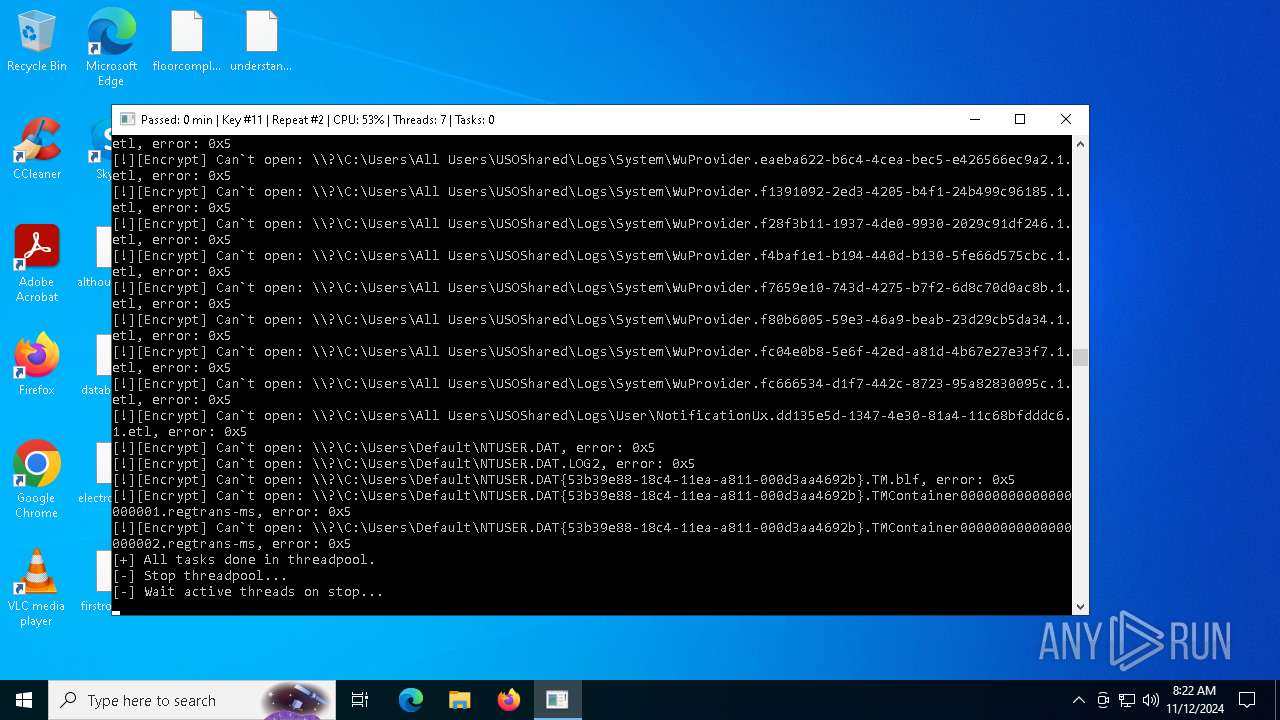
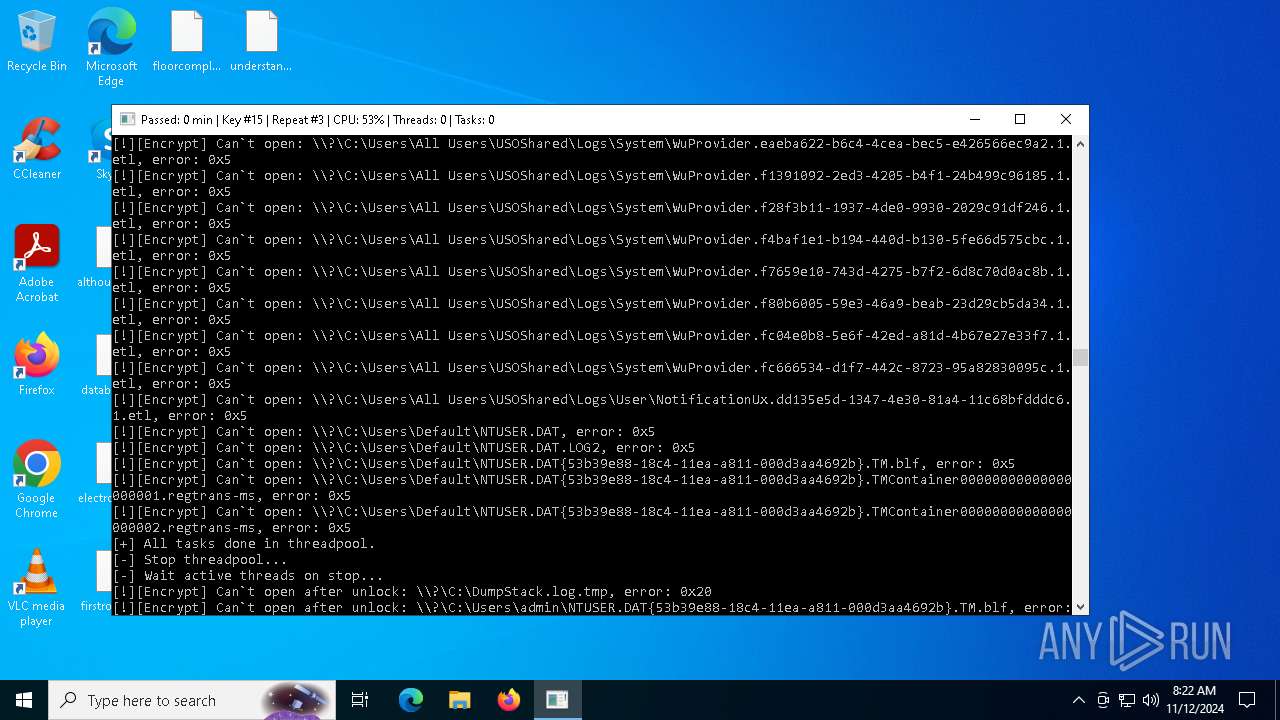
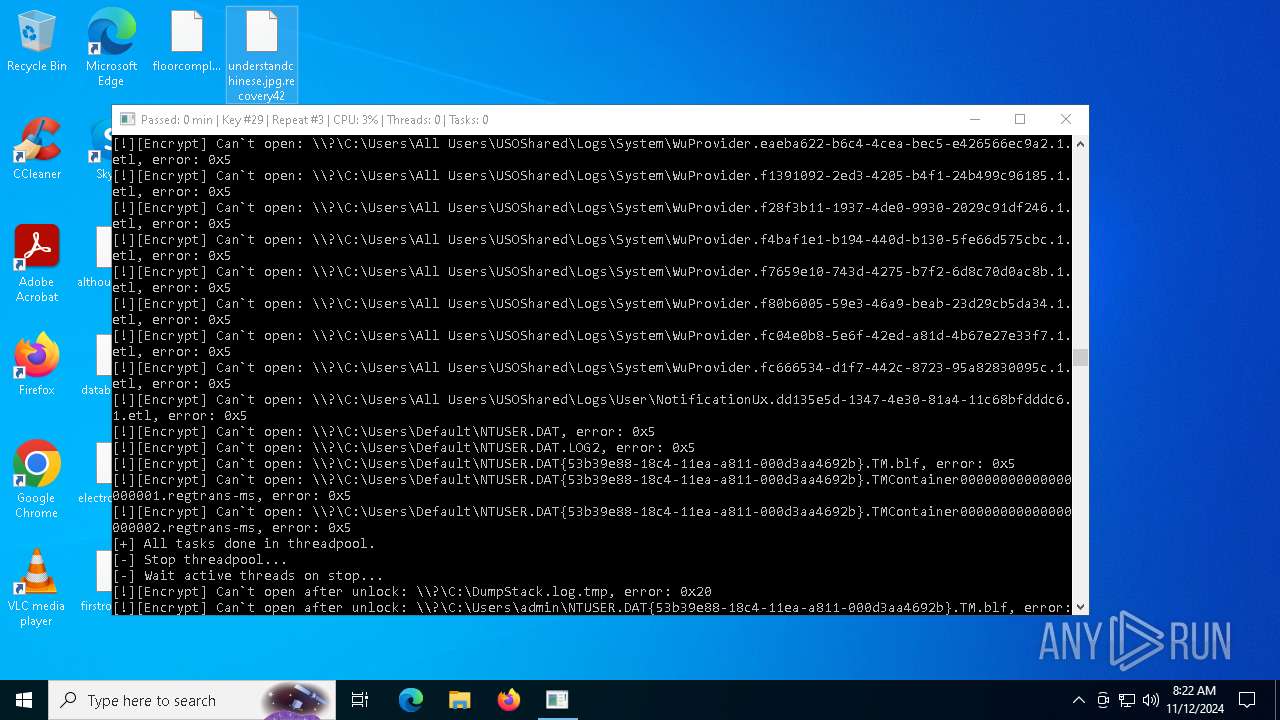
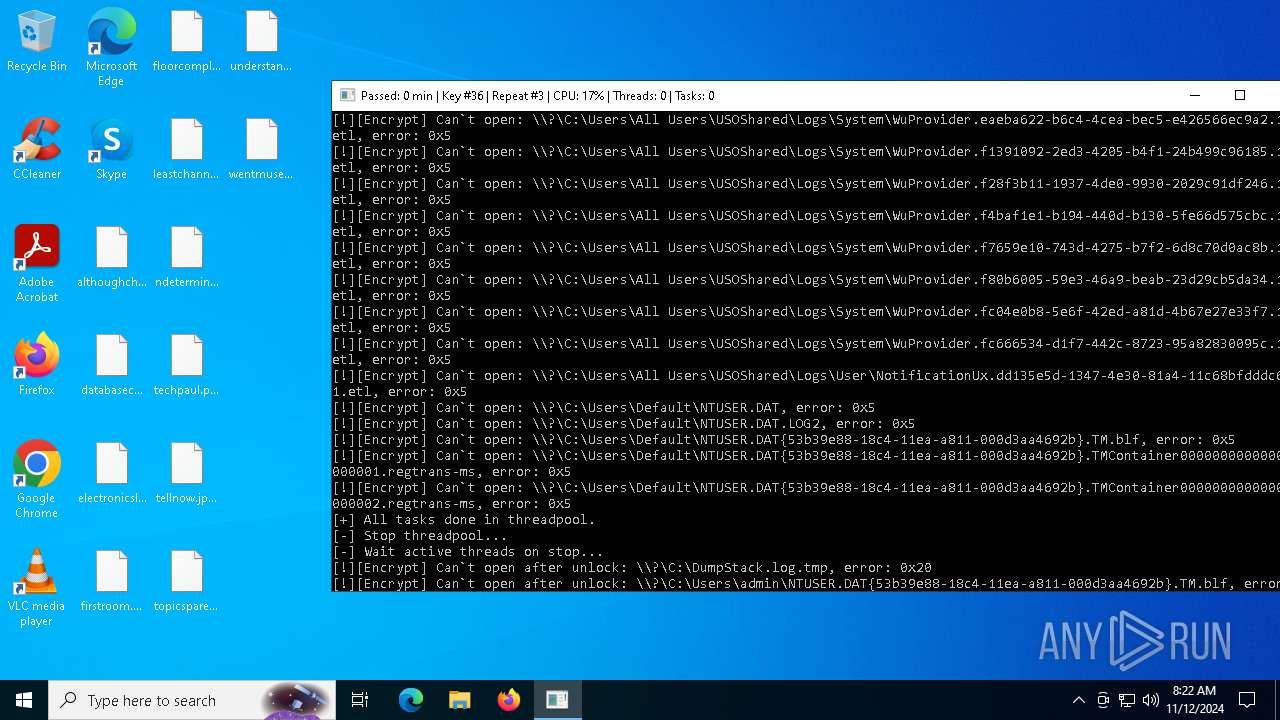
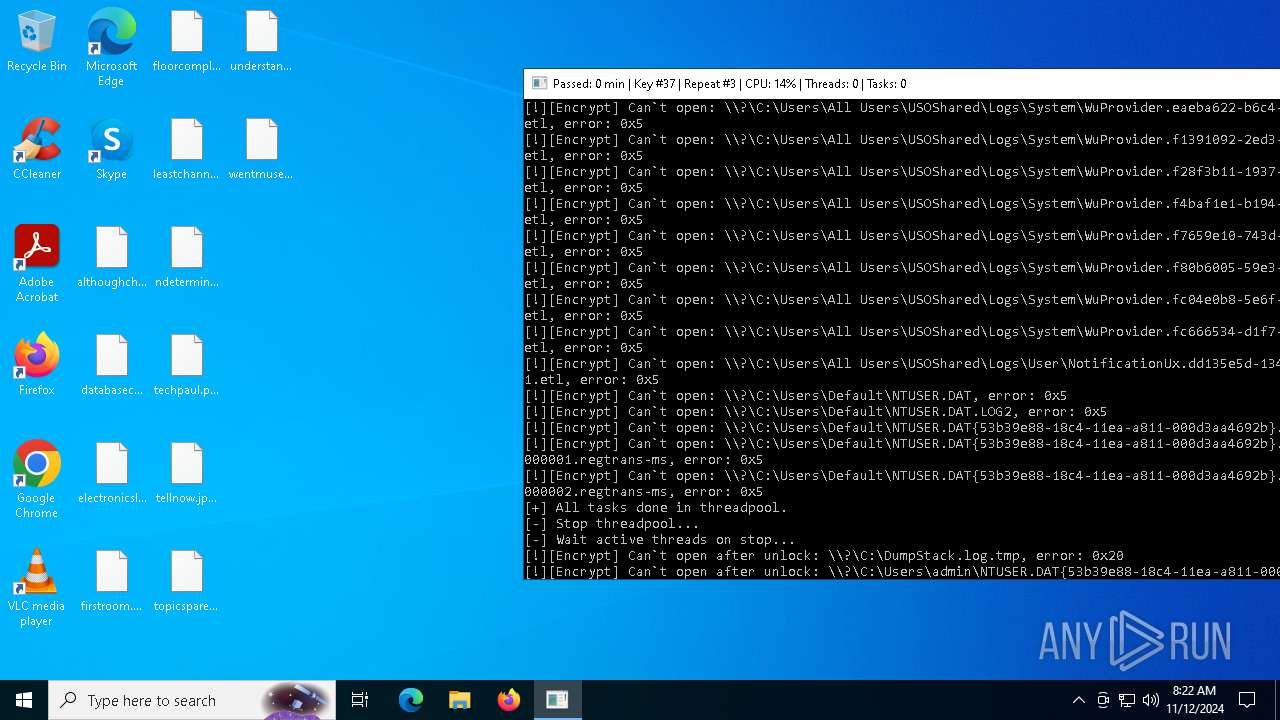
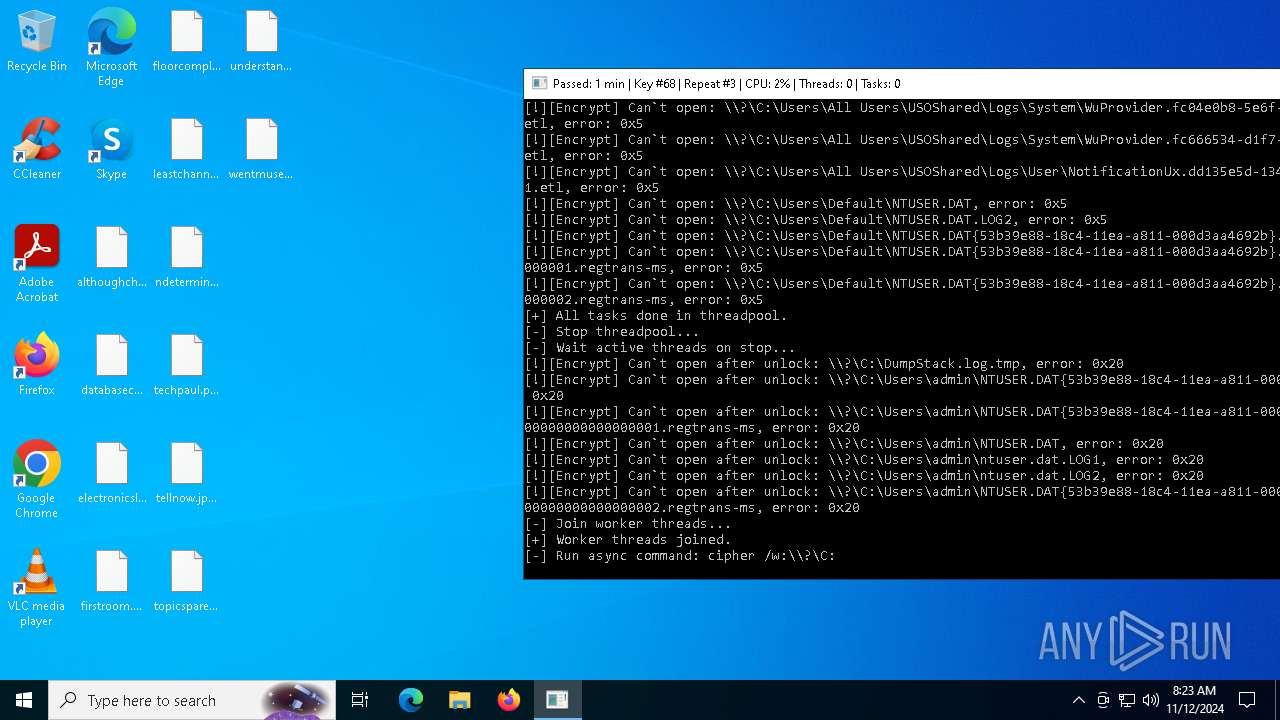
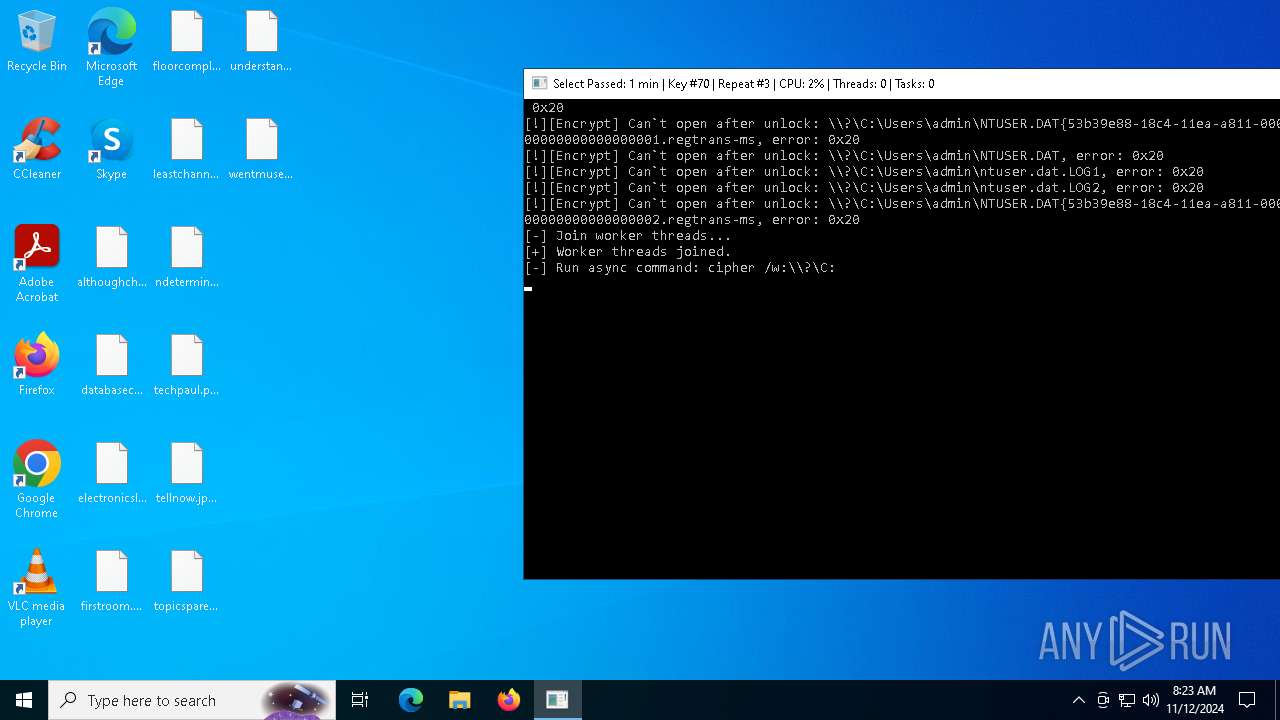
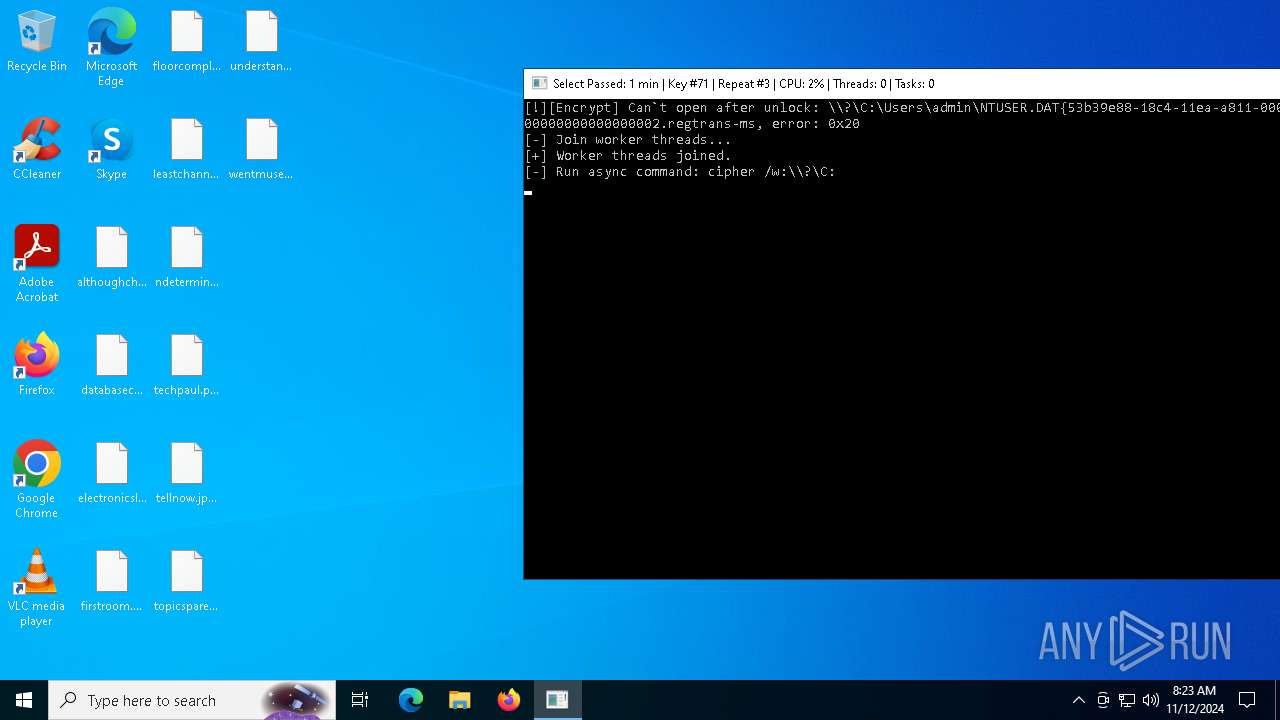
| Threats: | Medusa is a ransomware malware family targeting businesses and institutions. Medusa encrypts crucial data, rendering it inaccessible, and attempts to pressure users to pay to regain control of their information. The group behind this malicious software hosts a TOR website where it shares the list of the organizations whose infrastructure has been compromised. This malware utilizes various tactics, including exploiting vulnerabilities and employs a unique file extension (".MEDUSA") to mark encrypted files. |
| Analysis date: | November 12, 2024, 08:22:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 68E664C654BCF9D558FB7B4F8DA1F28D |
| SHA1: | 9DEB213F58E48725BCC7974460B5E22CC3866CC1 |
| SHA256: | CB03C1677C165261557F0710DDC2E39790ACAC48EF038C71358AB5AD4F366CCA |
| SSDEEP: | 12288:K9DXaoCPeb+iYDhhpyh9ooS99QesGKLqDTaBh4F42:K9DKo3b+vvpRoSwGTaBh4y |
MALICIOUS
MEDUSA has been detected
- recovery42.exe (PID: 6316)
Changes the autorun value in the registry
- recovery42.exe (PID: 6316)
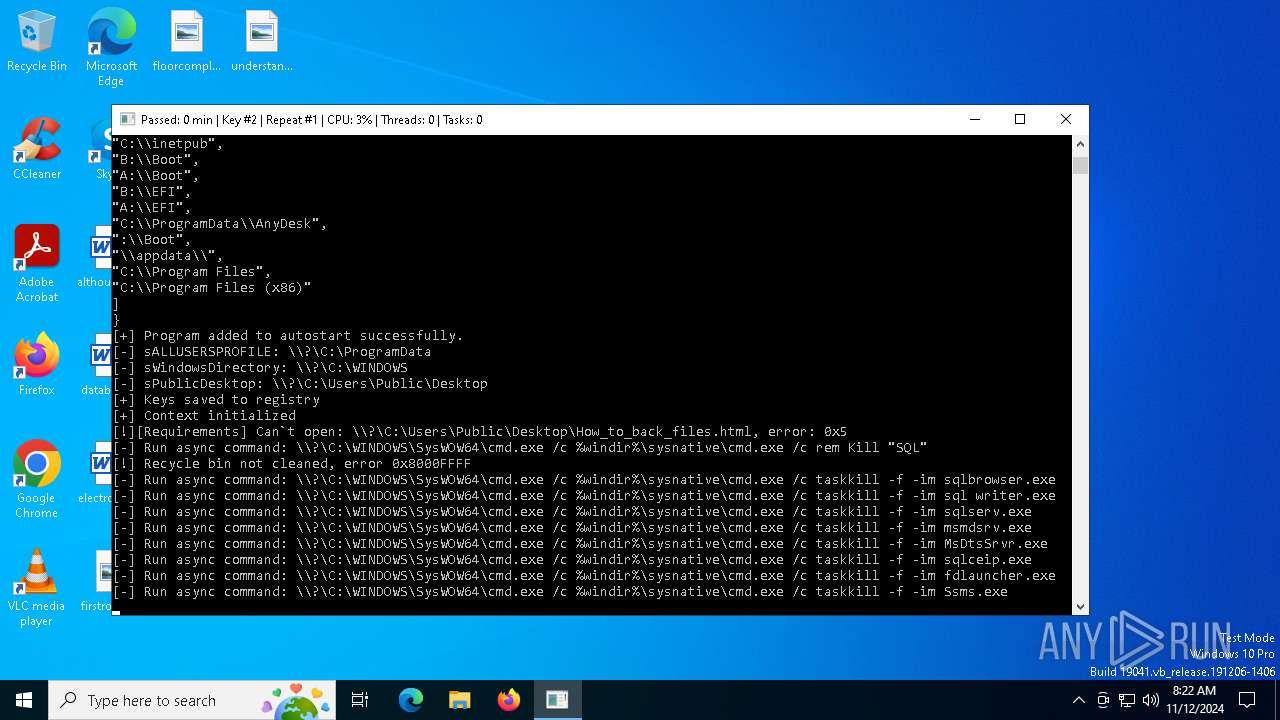
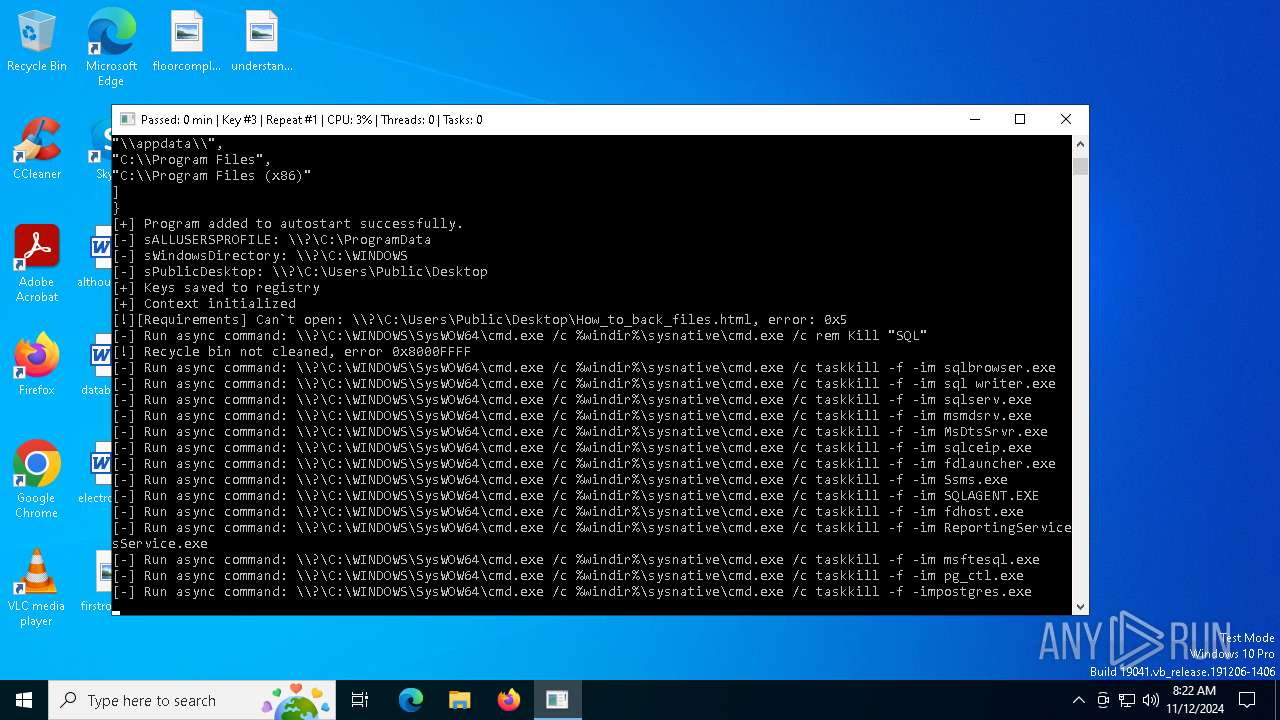
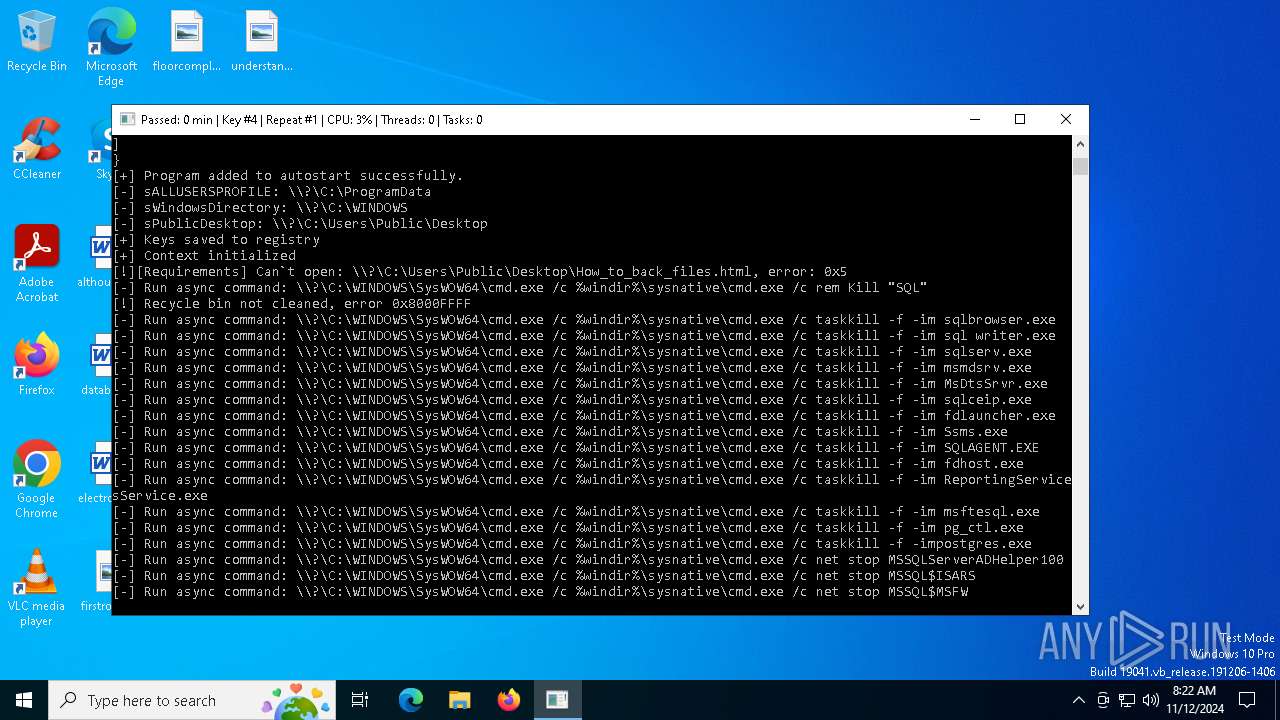
Starts NET.EXE for service management
- net.exe (PID: 920)
- cmd.exe (PID: 4692)
- net.exe (PID: 7132)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 6168)
- net.exe (PID: 1952)
- cmd.exe (PID: 7096)
- cmd.exe (PID: 4228)
- net.exe (PID: 948)
- cmd.exe (PID: 4476)
- net.exe (PID: 3960)
- net.exe (PID: 3732)
- net.exe (PID: 4508)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 6384)
- net.exe (PID: 6248)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 6224)
Deletes shadow copies
- cmd.exe (PID: 5892)
- cmd.exe (PID: 6216)
- cmd.exe (PID: 204)
- cmd.exe (PID: 4692)
SUSPICIOUS
Starts CMD.EXE for commands execution
- recovery42.exe (PID: 6316)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 5604)
- cmd.exe (PID: 1788)
- cmd.exe (PID: 632)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 3772)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 5184)
- cmd.exe (PID: 624)
- cmd.exe (PID: 6088)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 1792)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 6804)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 4904)
- cmd.exe (PID: 1248)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 7116)
- cmd.exe (PID: 7120)
- cmd.exe (PID: 6408)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6844)
- cmd.exe (PID: 1784)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 6124)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 5196)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 1792)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 3772)
- cmd.exe (PID: 4828)
- cmd.exe (PID: 3844)
Uses WMIC.EXE to obtain shadow copy information
- cmd.exe (PID: 4340)
INFO
Checks supported languages
- recovery42.exe (PID: 6316)
Reads the machine GUID from the registry
- recovery42.exe (PID: 6316)
Reads the computer name
- recovery42.exe (PID: 6316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:11:28 13:04:49+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 301568 |
| InitializedDataSize: | 126464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x254e8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
251
Monitored processes
124
Malicious processes
5
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | C:\WINDOWS\sysnative\cmd.exe /c vssadmin.exe Delete Shadows /All /Quiet | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | \\?\C:\WINDOWS\SysWOW64\cmd.exe /c %windir%\sysnative\cmd.exe /c taskkill -f -im ReportingServicesService.exe | C:\Windows\SysWOW64\cmd.exe | — | recovery42.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \\?\C:\WINDOWS\SysWOW64\cmd.exe /c %windir%\sysnative\cmd.exe /c taskkill -f -im sqlserv.exe | C:\Windows\SysWOW64\cmd.exe | — | recovery42.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | C:\WINDOWS\system32\net1 stop SQLAgent$MSFW | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | wmic.exe SHADOWCOPY /nointeractive | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 44124 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | net stop MSSQLServerADHelper100 | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\net1 stop SQLWriter | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 948 | net stop SQLAgent$MSFW | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | recovery42.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 415
Read events
7 302
Write events
53
Delete events
60
Modification events
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | BabyLockerKZ |
Value: "C:\Users\admin\AppData\Local\Temp\recovery42.exe" | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\PAIDMEMES |
| Operation: | write | Name: | PUBLIC |
Value: BgIAAACkAABSU0ExAAgAAAEAAQDl1JG6PqRMXUmitFudwQ+W/mfQFQXSuTcrz6JUpHStRL0C5nGeqfkmdDOsjRi7dOj3LA3bqV+mQzYYJo4K+RDc81o/4cnJhq5GecFUW1/w+rt95hr8HfdQ4lZizTZfO/NZaGK6YXLS7u8dsVi5FEpplCDwldyAh5FplgLrX0iJdbFYMqIzTBn5zS9mtghgdrzsP2Zi3lg3py/pbmMUlfogk3So5ygnVtvYR8URMx3K7SlSiBCwV574N9+XQagDK0Gw9gcbUUqiqI9Veuab4lyYDDi3HFVe1XUOBXSmUHH0kMczvLRpk6kN/oCgurgE03+OMBBNRL/Epx6Urqi7f0ey | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\PAIDMEMES |
| Operation: | write | Name: | PRIVATE |
Value: XZJdfowsM8FcsPYyAGMq8H6p19kPFOJcS8KMtomWGAkTJdua5H97+J+qqLXm4Vis2NuN/0z22z2iLM/1hsQgRpbgeyeUTRm80hIt57ARs4yy1MQC7JykWOf72P1dp27H5kU7w+k20/4R5MvFf/MS3nOB8FM2iNAmwFTyQJgEa+ynTeadx4AlX35RYTBLnhWIYn1y9IJfYSgwZcY9P6A5jKDmz9zNLi7065P/BICwzbHsYpWckz3P9DXS2sr+CacxfxkiJyUfBEmksTBL5W7BQAdfZJN/5mi/WCIxzPn2oYgxWtEpSa9S88Y7mXTgQEqeXf4MsI6pZOe3ce2EMFJYRKfsviIe/3HyOnet8f8JCX08TR0z6k0jGa0+PGhr11df8OTrgwjW/FAgsf6TKVTYrqHvDW7KLTu7FX0InhLDs3uB6syLnxkyuwMiuCbhWurRiDBsMLC9QfRRLh8CPrKkWSH1EaBBu/Ai6HTngLUWcxdgjEr/TY9xqA77qihG1hTPoXiay7grdPWLqFSXWRfqbJejLU6NirU4mQ0T5R7YVWgYSOdnsPkmuNheoxANmn4B6SWHK2loTMNgtqO+7jEW6vwfddb20wRSNYFM0YZHag8WADjchlHzN4Tj/bFi447DCvXtG5WqAkLwTszlBadVSs3cnnTighuza+9V0ErRUZUa7RUGHKk5ZatD12gbzx3SD+12hCJqKROBNkrL95xuoS1rTBY5yTVIAzthwxwDTSsf0PIemkhudYJho9fZg0jumJMM9VJXjzXRHTwjImwQhL7zvqt6Szxsu4Ryajy0AP2eaRxanlJj3IJ2U+7V5XZQaGpWlHTDLV4+u1EP2dHNgTztuovPz1ilABnsOInH2WANdZ7Ca6WTiNYDvlm8yvVzmxA6RBxKz+F40DXcoJKG4AALHtJMwgyjIaZNhLJ/zc7k+uCLdjWhoEjaXrESf1C/HPlWLySVzkTKVRHeggDLPxgAgSIyLB5XNvqOIuqajt5rmB7Uj/NywbKa12/zF8iGGGYUO3sH5iKPBXfphqtJqW6JuDScA/5WwOkT3Hh+k7KPRPyDd8A8HgrLyWZzdkhUbPLmgY5E7OHV7PnONstnKof6uzUtQwHyVMZyqUUmrOTV9kcCScLb9fxWrrusgVwm3nY+VA/ccPZqKur/Nz2Zd3yr/YrPdiUAPNdNXyCZtDbL9pQL+FpYIWdVI4BUYchwaK23/uJH3u9hICa+E/QAseOYxRNGRjBYZTvbqa4ZL4E1GrOyQSopkNtUv/t42eUQvnIg1X0q7Uo+qGgTKOlRp5zY/DIrUf1sVd3nx4+fV57uUZm+RdZP8OOWr9uFpJLr/qi0wMZ3BXzzvPBYuhQ7tpjhkyQ8waG7FFch/Ga+HMX8Pjx5zsJ98/F5158rNxxDW/N0ArVs/s39Zr2g23cYgnoUflgG9+g2P7AmLbSR5p7hhkX99zvVml5e/KpApX10zqH8Y/VP/RBH3DVgb32qJjwcpk1n352TtGzTxrdoR9ul1h8nOrGUcuzTdXY4KLH2p0yE5+RywRkhfaKAGk4QvvDY5ISOyoa2dc9J3flSWxPeO2WBLl7Z9nQsqqwtHnYbRlNj/9QedCtX9ZwL9PH2N0un5B6ae0fO4Pphs7Z6G4ZiNAUCkW3x69UBKiBQr1qnixDFDo/lYy6ib4BtqmU93sKe347hq9zjoeIGKQVuyrk= | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: AC180000DCD2E2FFDB34DB01 | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: BDD94C2A0FEC9E691CD1BB9A117C219BA6C7AAED3D74E5EE7BA990BB2A127B4C | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: \\?\C:\Users\admin\ntuser.dat.LOG1 | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 5F26C27EBDD79F53F4488D687D3BACD048AB0369E33C110674E3F7D1475E481A | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | Owner |
Value: AC180000DCD2E2FFDB34DB01 | |||
| (PID) Process: | (6316) recovery42.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | SessionHash |
Value: B17CCA29EBE8AD8F2B03E56C1451F505A756302D28650FE4FAE9080F2BEFE035 | |||
Executable files
0
Suspicious files
224
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6316 | recovery42.exe | C:\Users\admin\Desktop\databasecurrency.rtf.recovery42 | binary | |
MD5:1FF8F3C54A77E09CA07BDF68299CC8B9 | SHA256:0CE114487A3B2CBD9C62BF07CBD02AD4C85815BD1D34DB9B204FA9EC101E4FF4 | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\althoughchinese.rtf.recovery42 | binary | |
MD5:393B0D5492643F431A6186A856BF4FFC | SHA256:0E8B6141FDA46652EF2DDA730D1CBC5406354E79763720FAF5E0DCFFE2BF7D5B | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\electronicslas.rtf.recovery42 | binary | |
MD5:9C063FBE1090E3984A3FD904F4B6C229 | SHA256:533DB89375C4FCFCEC35A480EADA834ACCDC5896E207B9F5EEEF9C09AA89809B | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\electronicslas.rtf | binary | |
MD5:9C063FBE1090E3984A3FD904F4B6C229 | SHA256:533DB89375C4FCFCEC35A480EADA834ACCDC5896E207B9F5EEEF9C09AA89809B | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\leastchannel.rtf | binary | |
MD5:9AC94CDAF16EA129AC6A081693A60C52 | SHA256:140745022E72EF68B7D7A8CDE20FC0BCB8777172343D6162C1D5B2D68AB17538 | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\leastchannel.rtf.recovery42 | binary | |
MD5:9AC94CDAF16EA129AC6A081693A60C52 | SHA256:140745022E72EF68B7D7A8CDE20FC0BCB8777172343D6162C1D5B2D68AB17538 | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\tellnow.jpg | binary | |
MD5:7E936DCBCE4D553E2850E2A7370F2575 | SHA256:C7292DA6BB9BC9196EC7D55A9B142FD5BB646F87CB9EF84E802BAB9F385CE958 | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\topicsparent.rtf | binary | |
MD5:9E0E649A29046BD429686B3E4D3A3529 | SHA256:F5CFD1DCB24597A30FE47FBFC827A7B929135BF6CB7B577BDA09112569DAF77F | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\ndetermine.rtf.recovery42 | binary | |
MD5:903FD8895E8AD71C79A57721A9C4DC2E | SHA256:216479586ED2C1B18386E05D916EB2C3600F6B01DF0AD655F345B5DF9123C597 | |||
| 6316 | recovery42.exe | C:\Users\admin\Desktop\techpaul.png | binary | |
MD5:FE5C5FE703630F50C7CA9E107325F9BB | SHA256:5402957180379241561C5411EDEAE37304475CE075E1F0B2BB09ADF8D5EDD29E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3600 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3600 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7036 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2364 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|