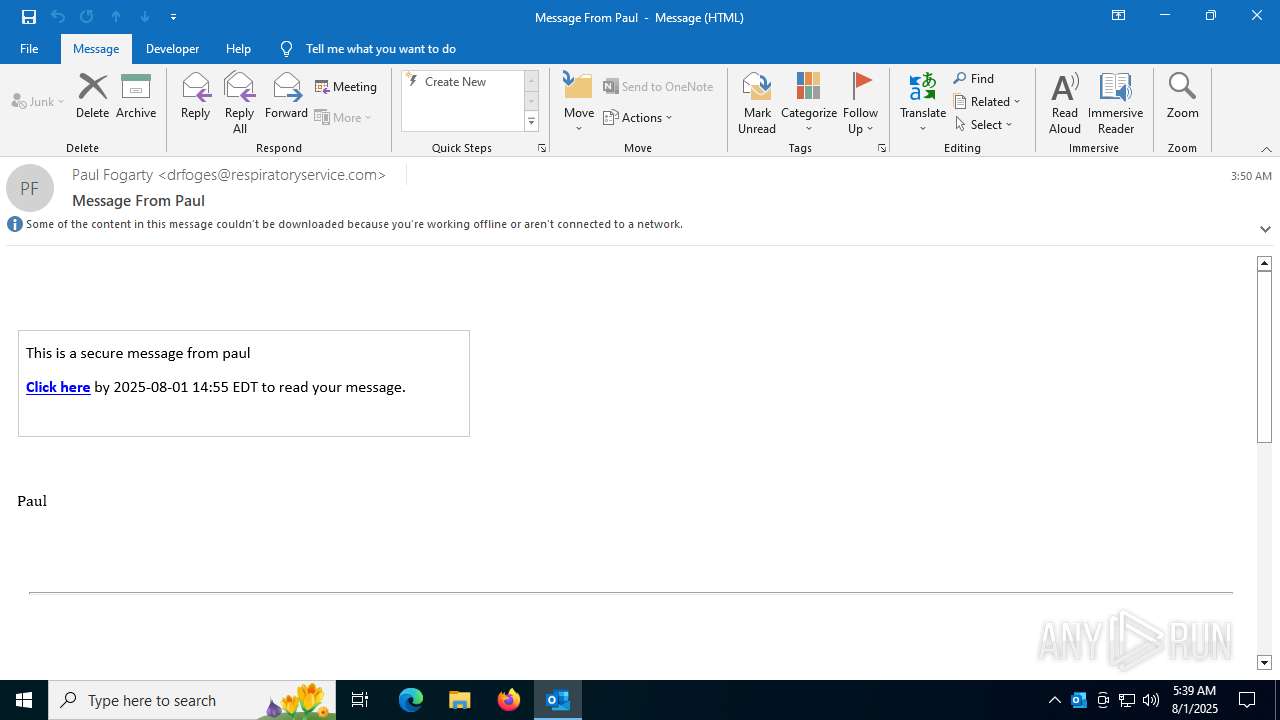
| File name: | 20250801-035050_Message-From-Paul.eml |
| Full analysis: | https://app.any.run/tasks/d12ddbd8-d40b-4d07-a1a2-16362a2f13f8 |
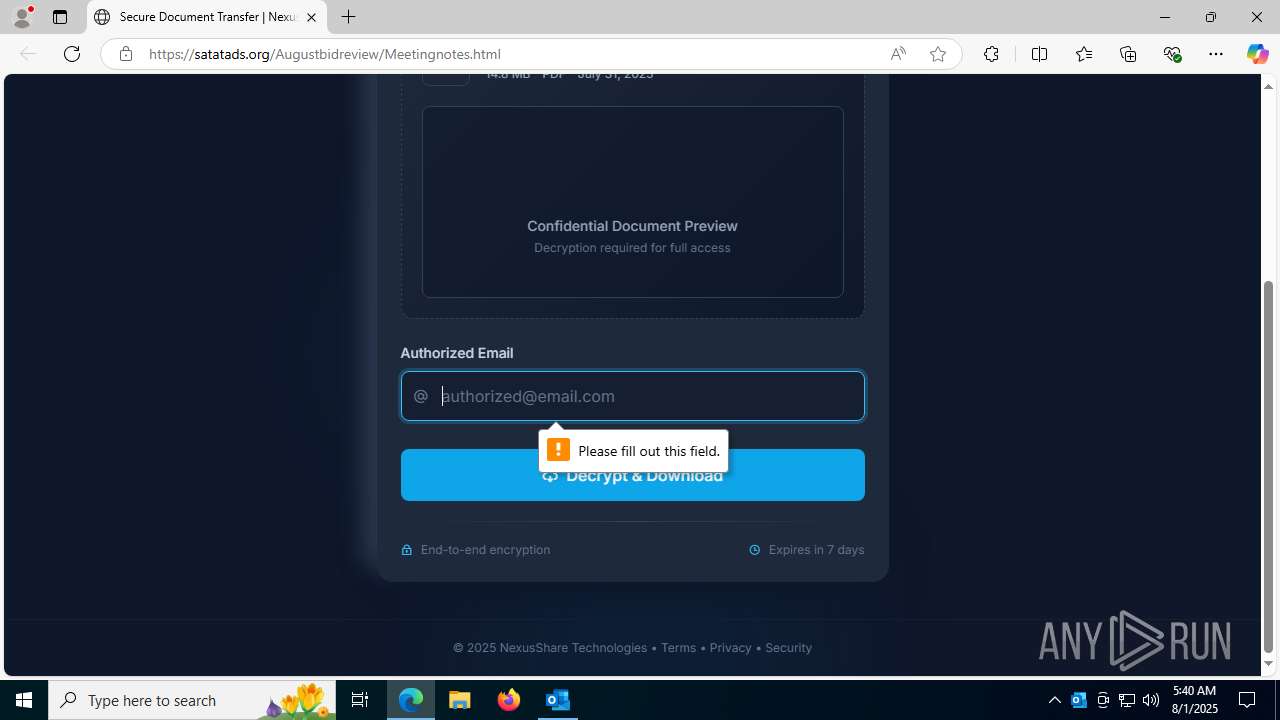
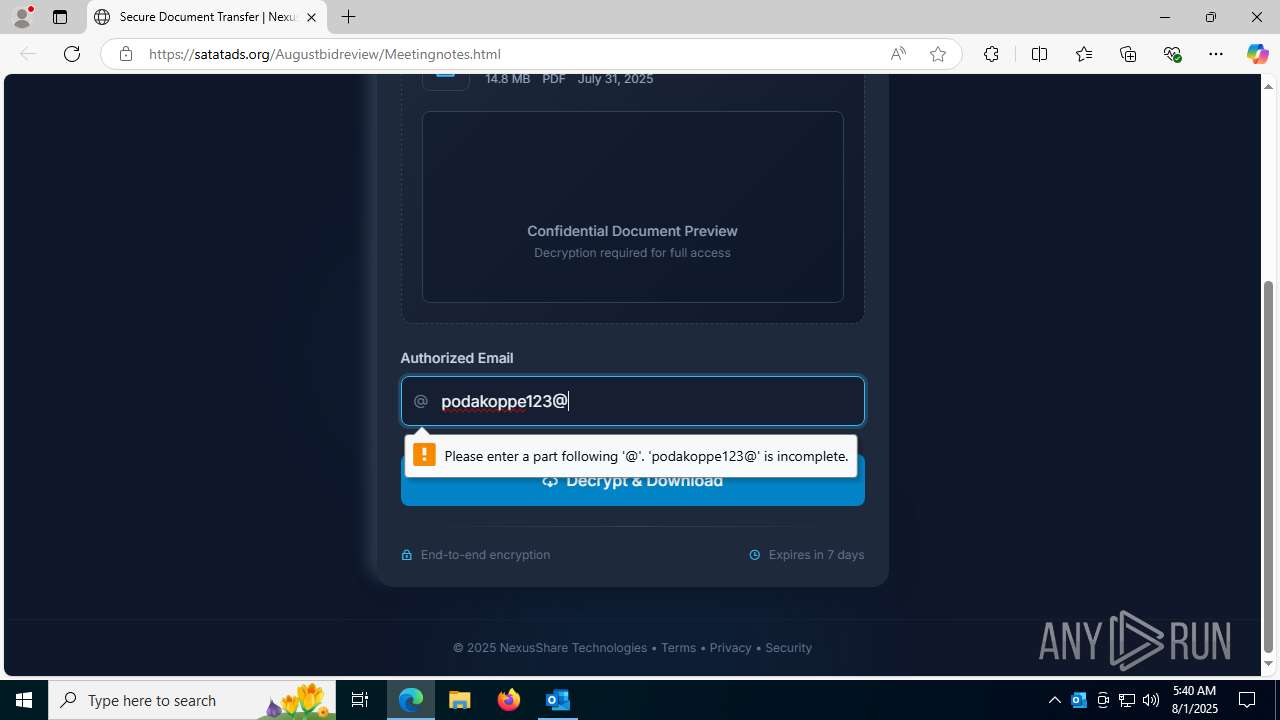
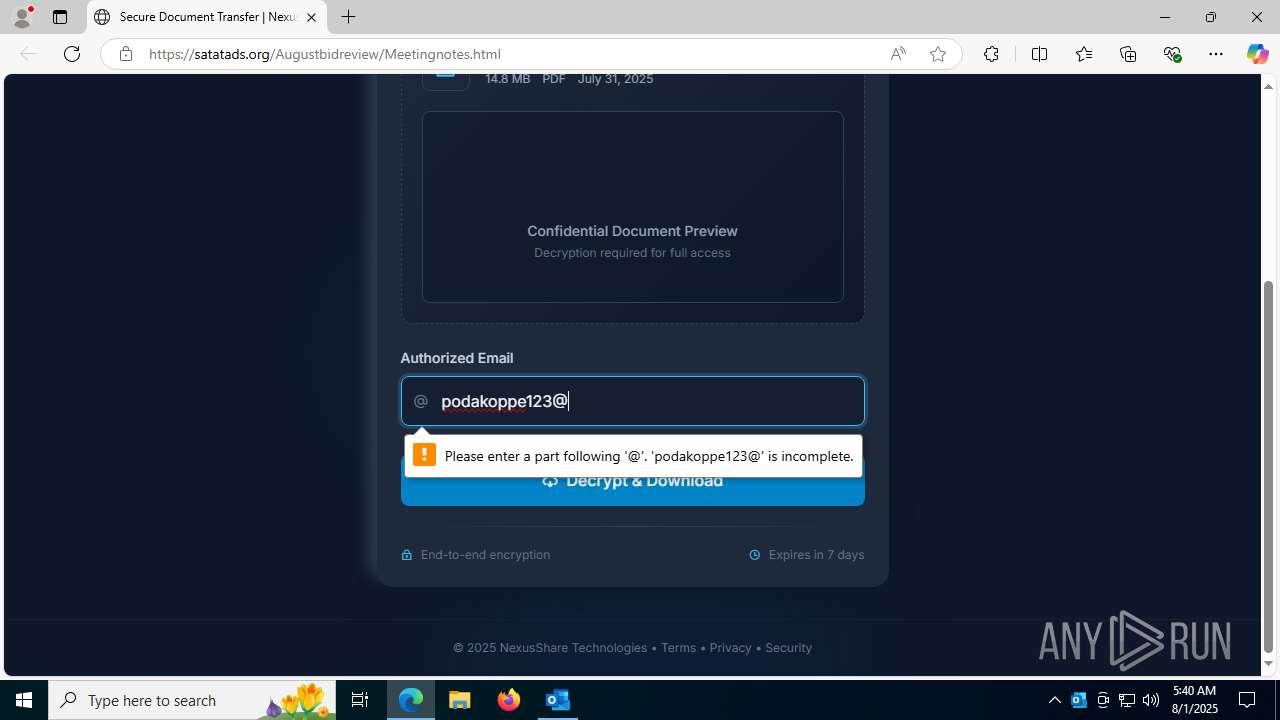
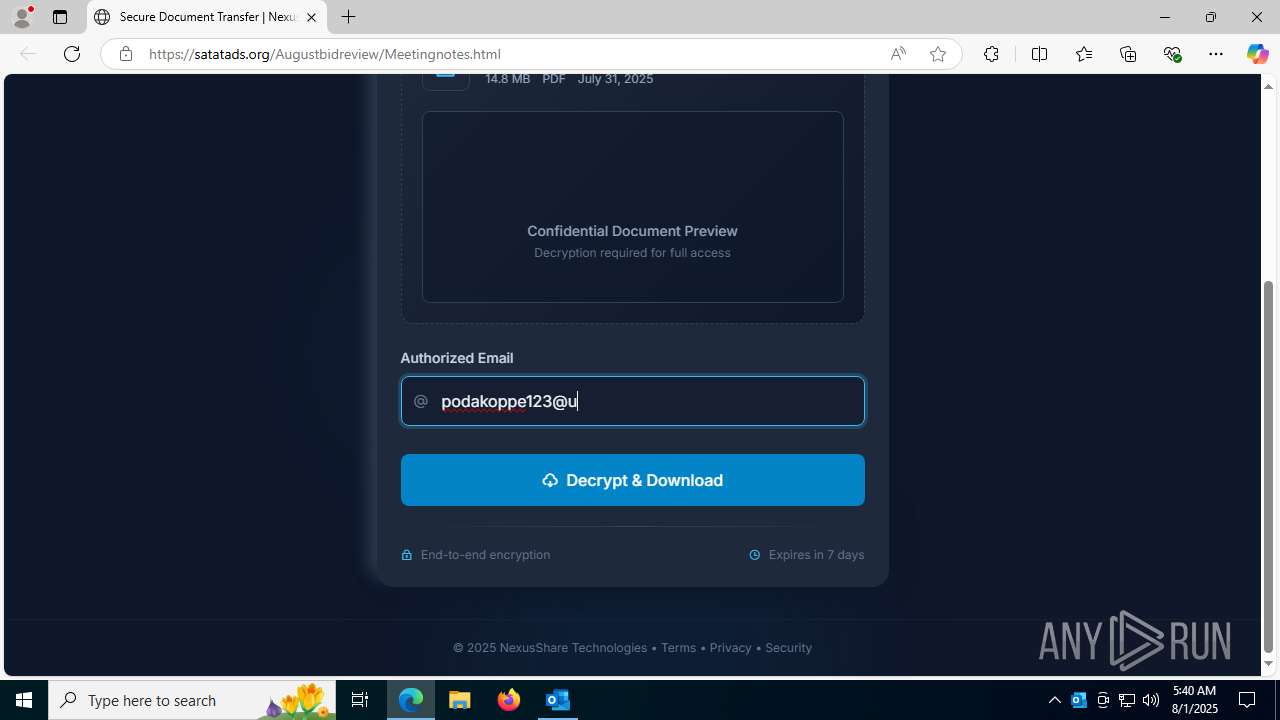
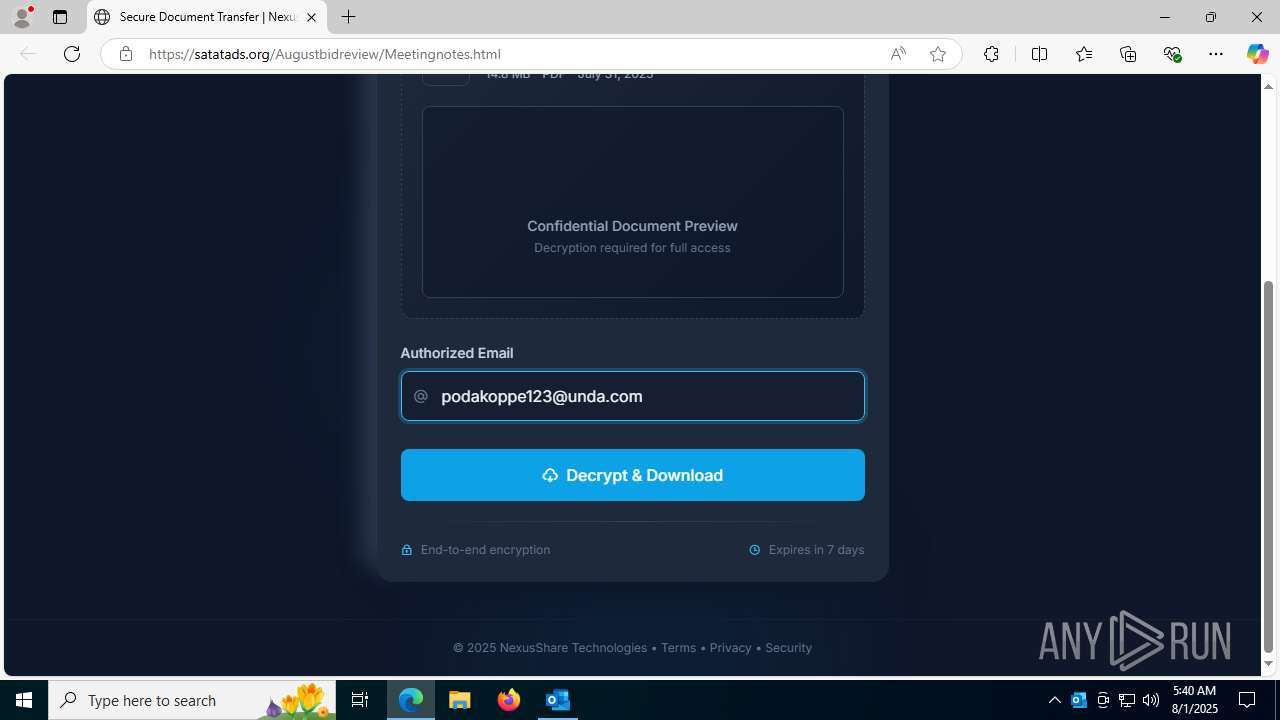
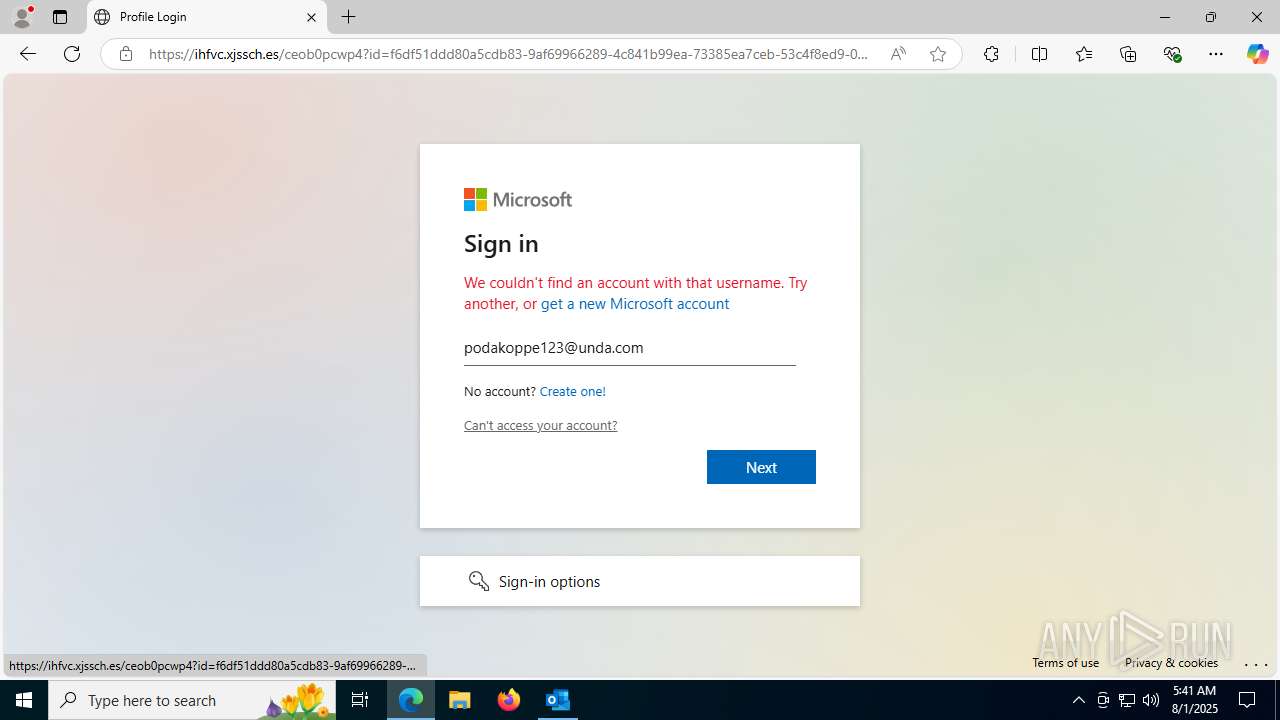
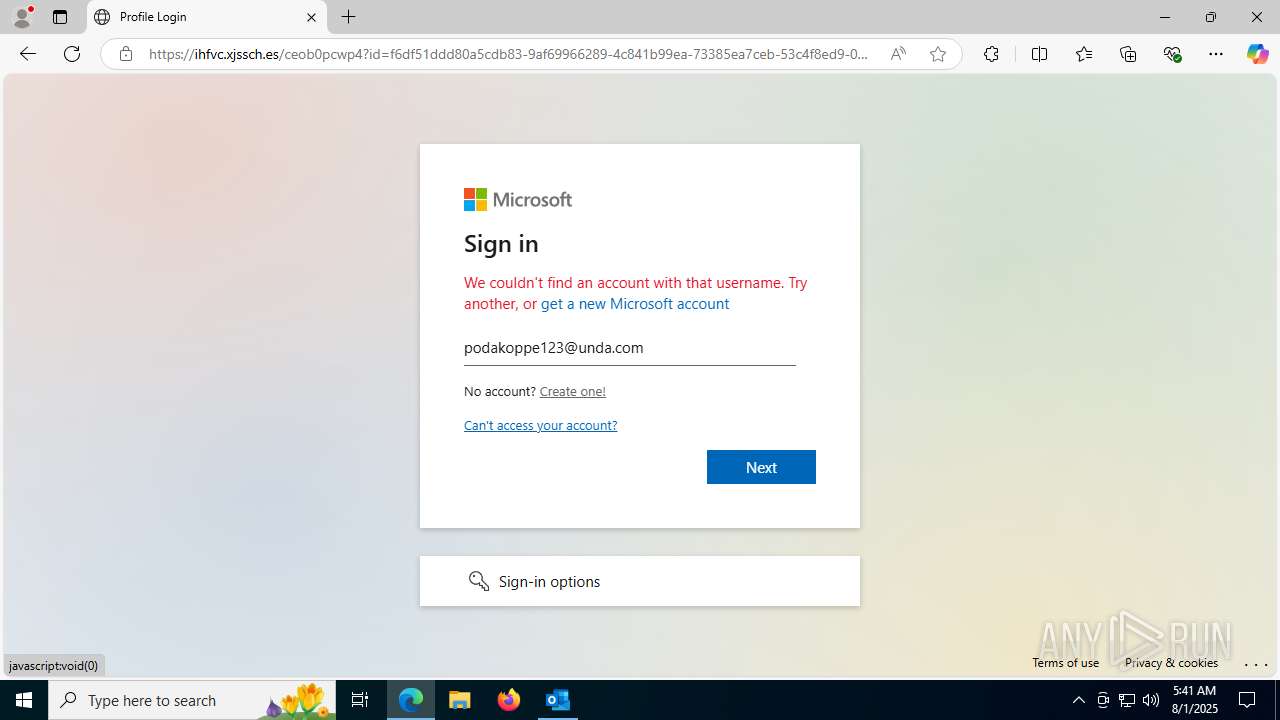
| Verdict: | Malicious activity |
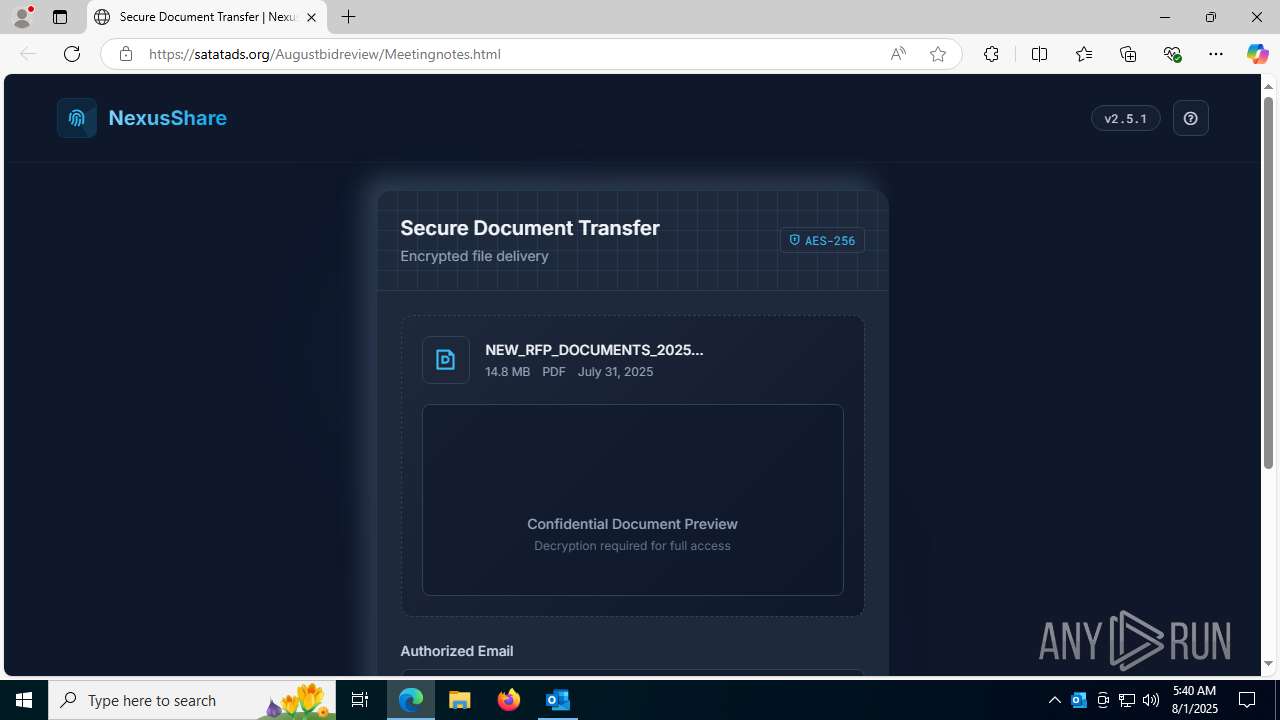
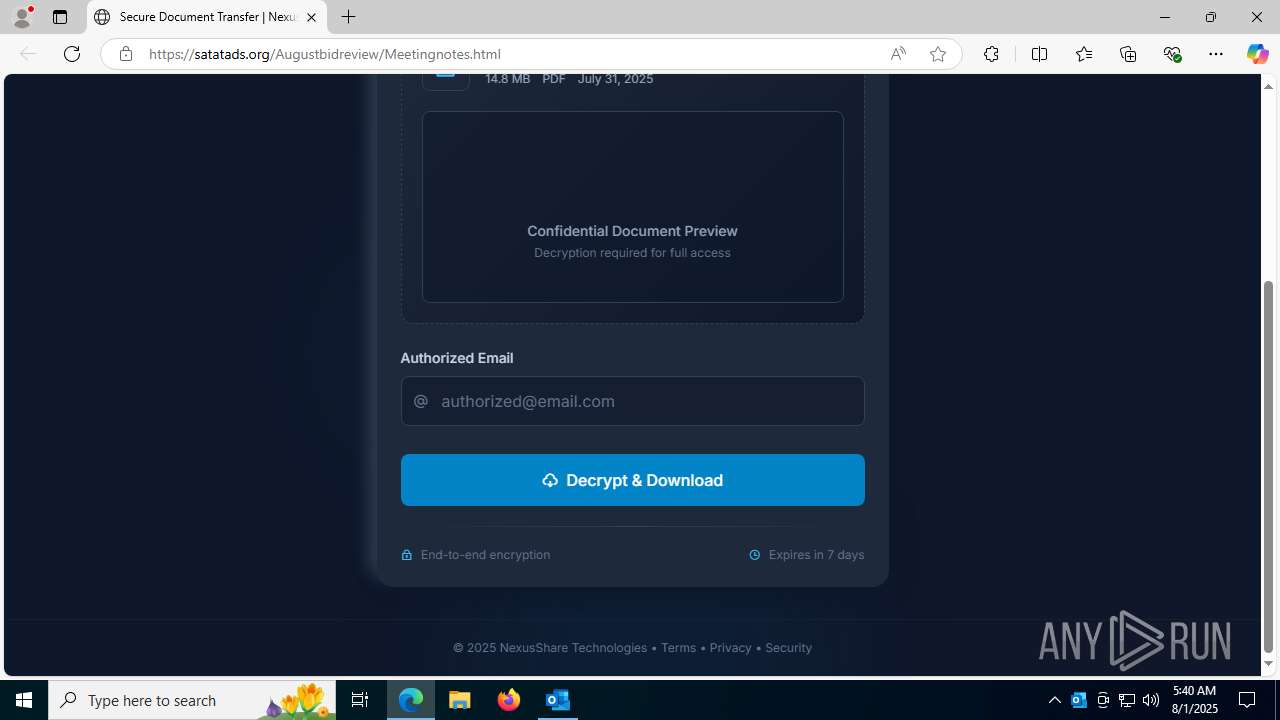
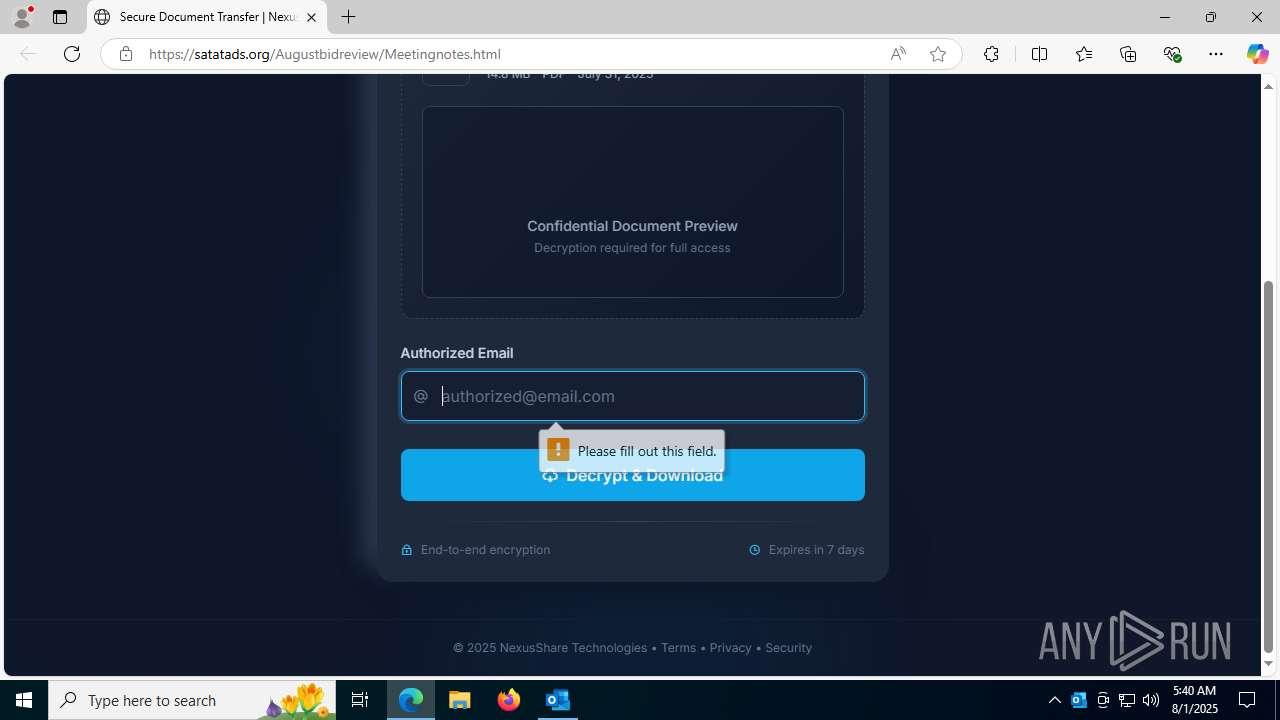
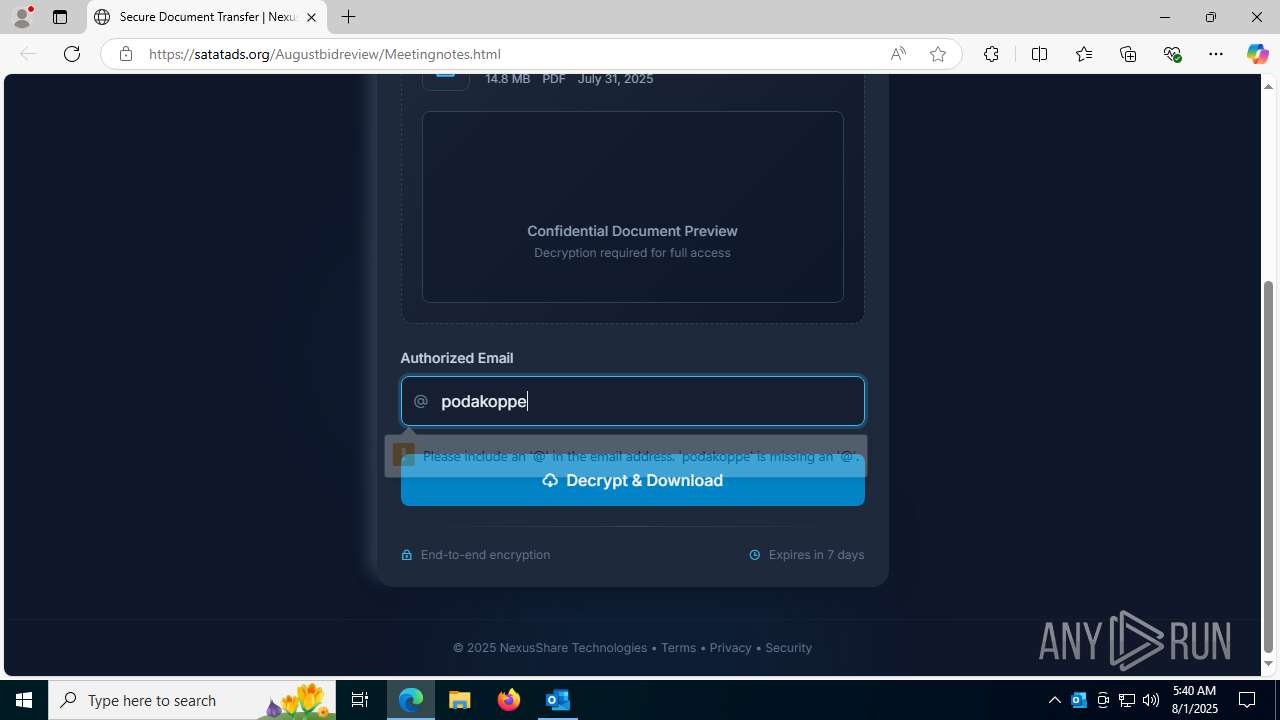
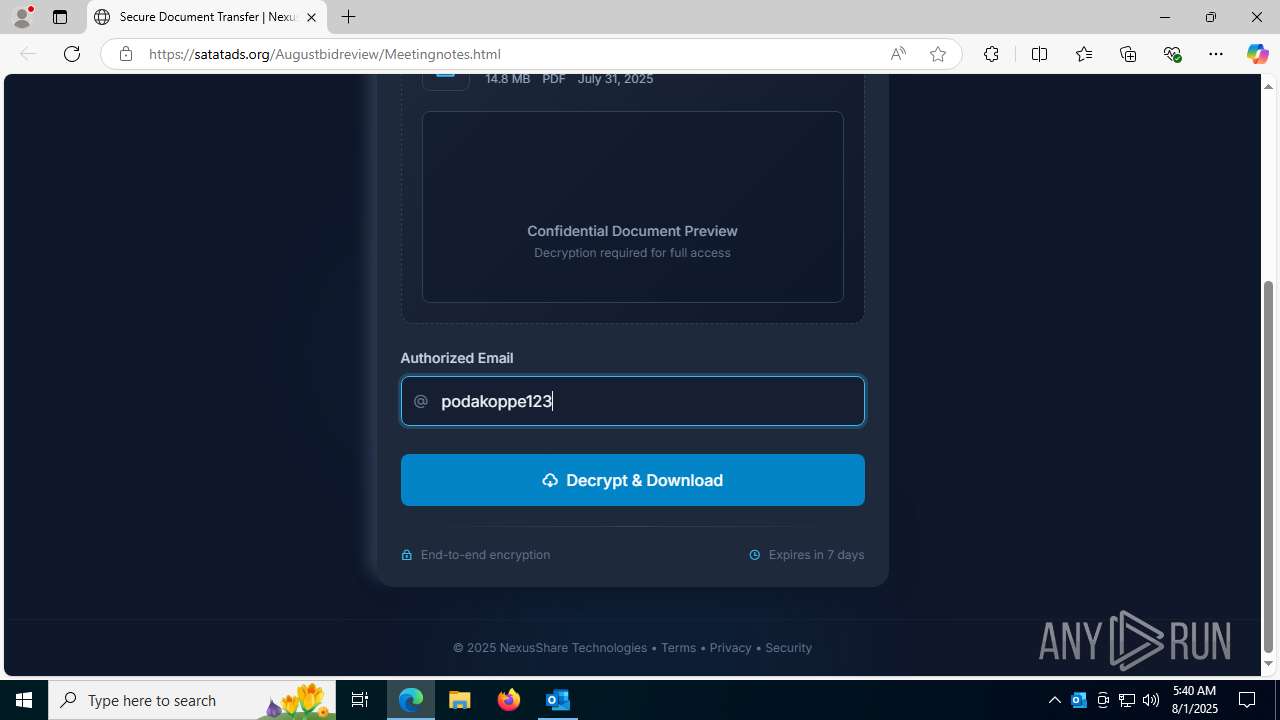
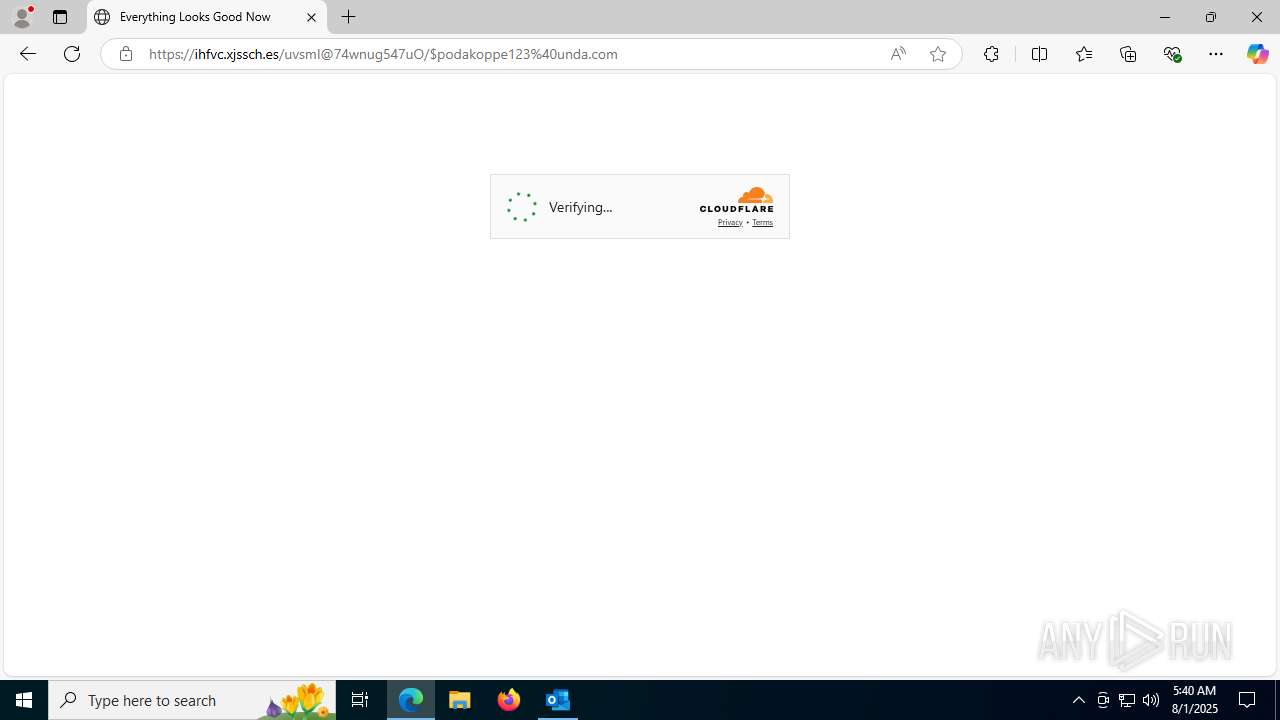
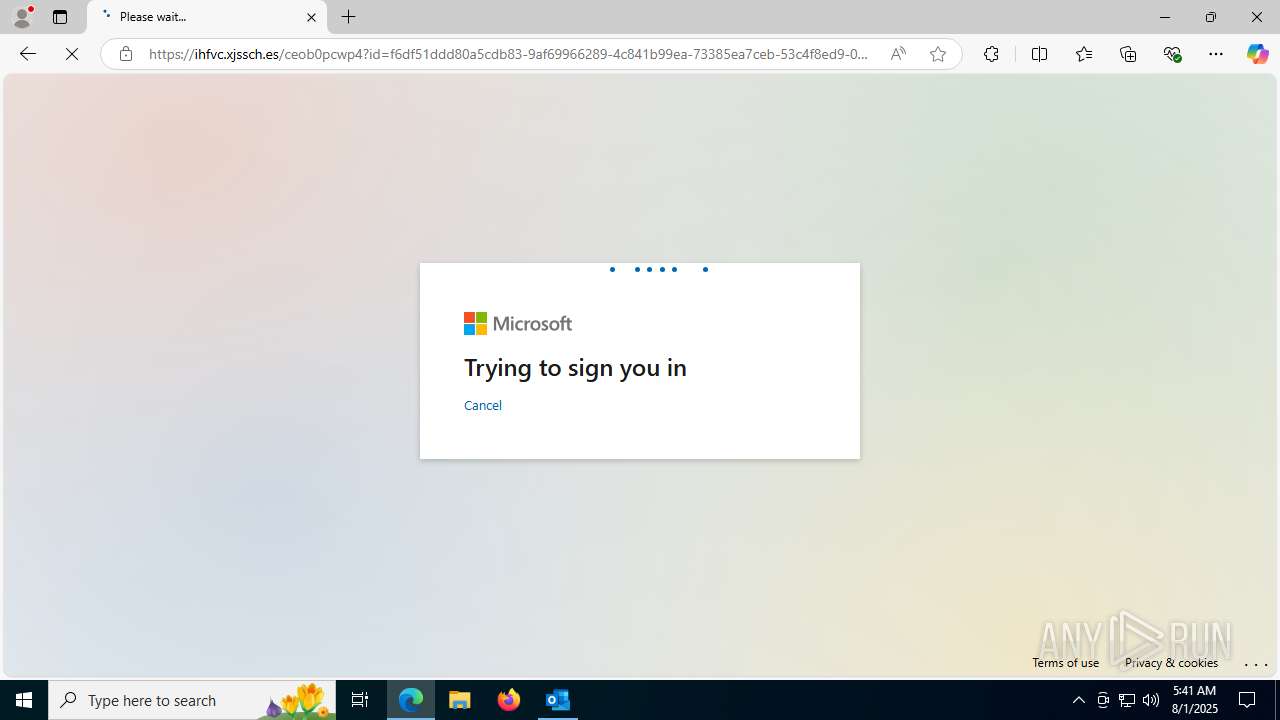
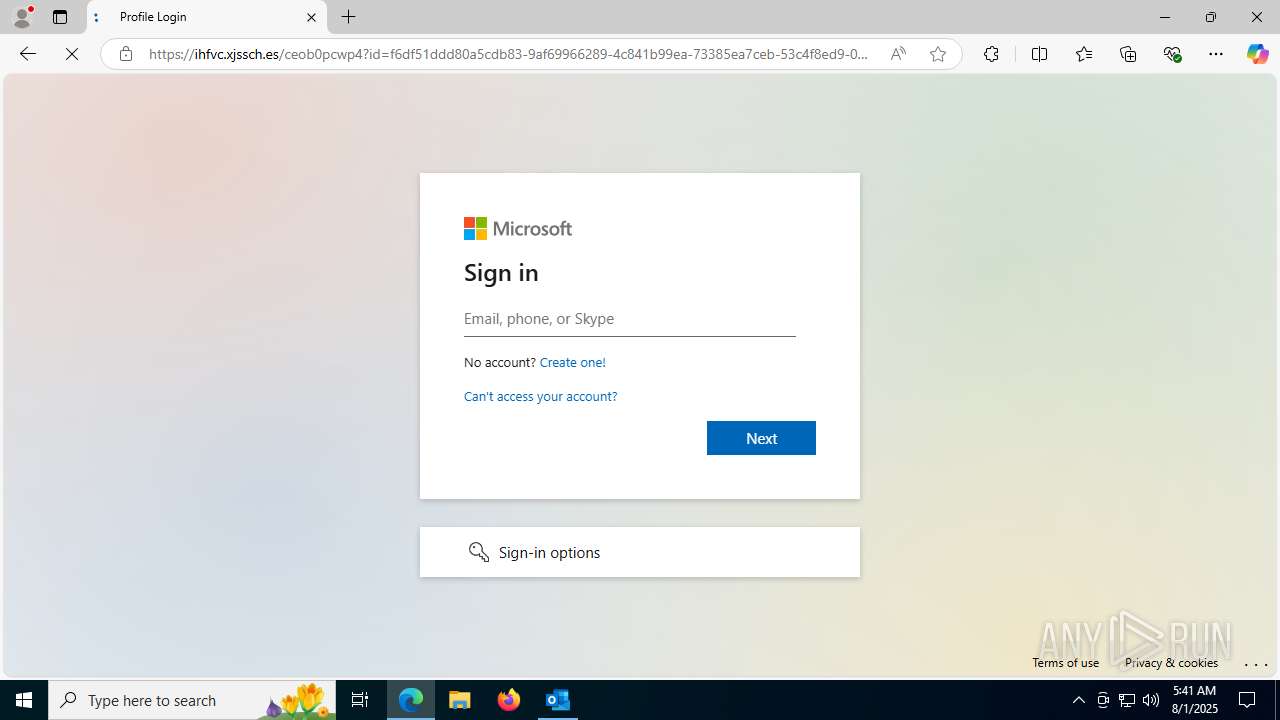
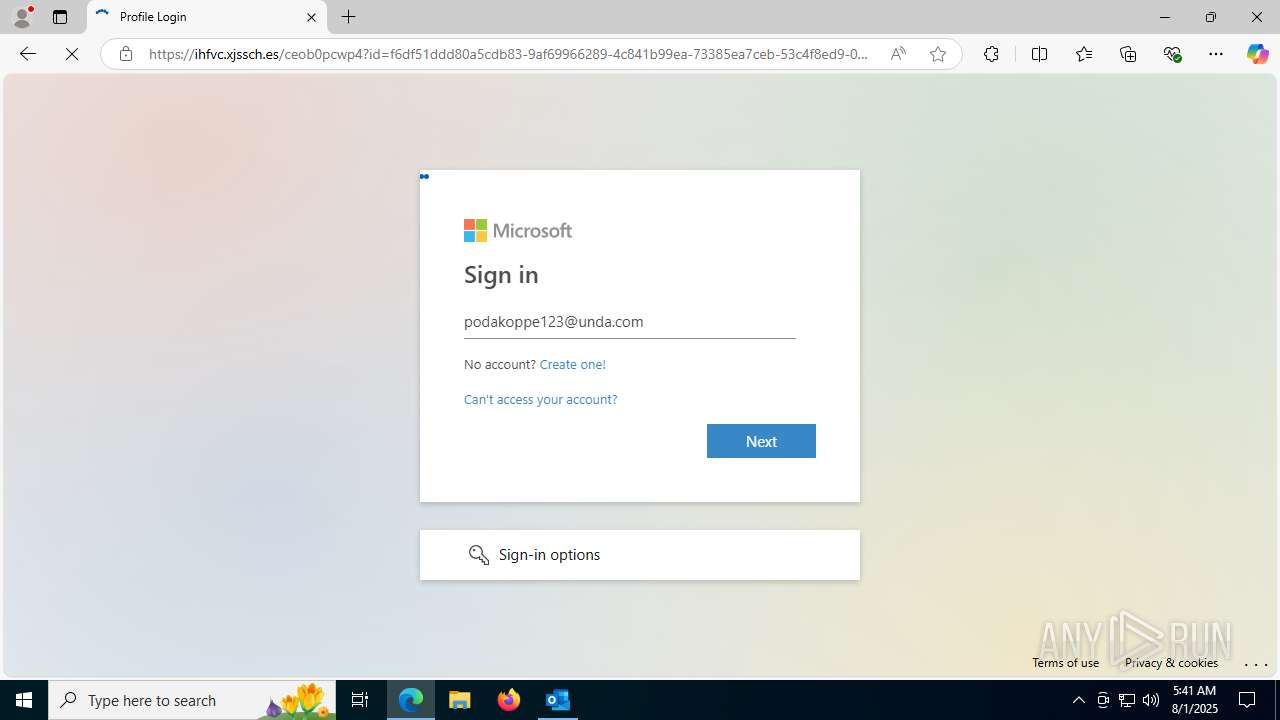
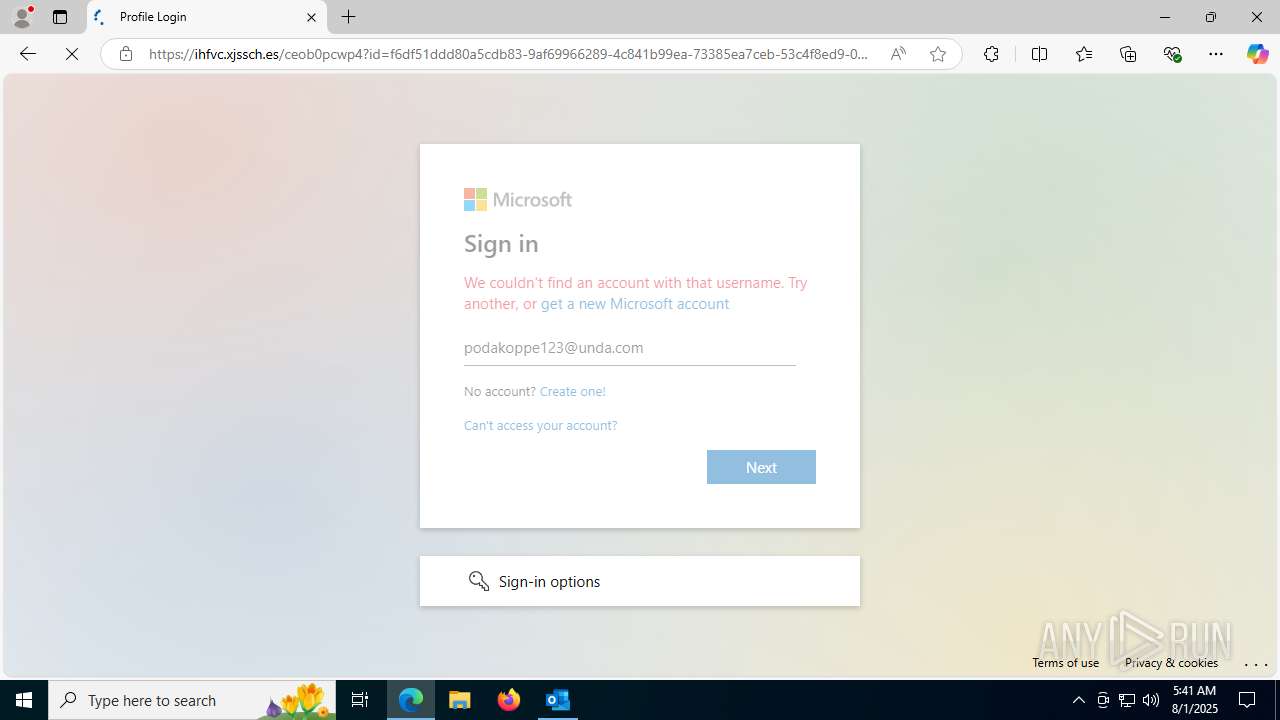
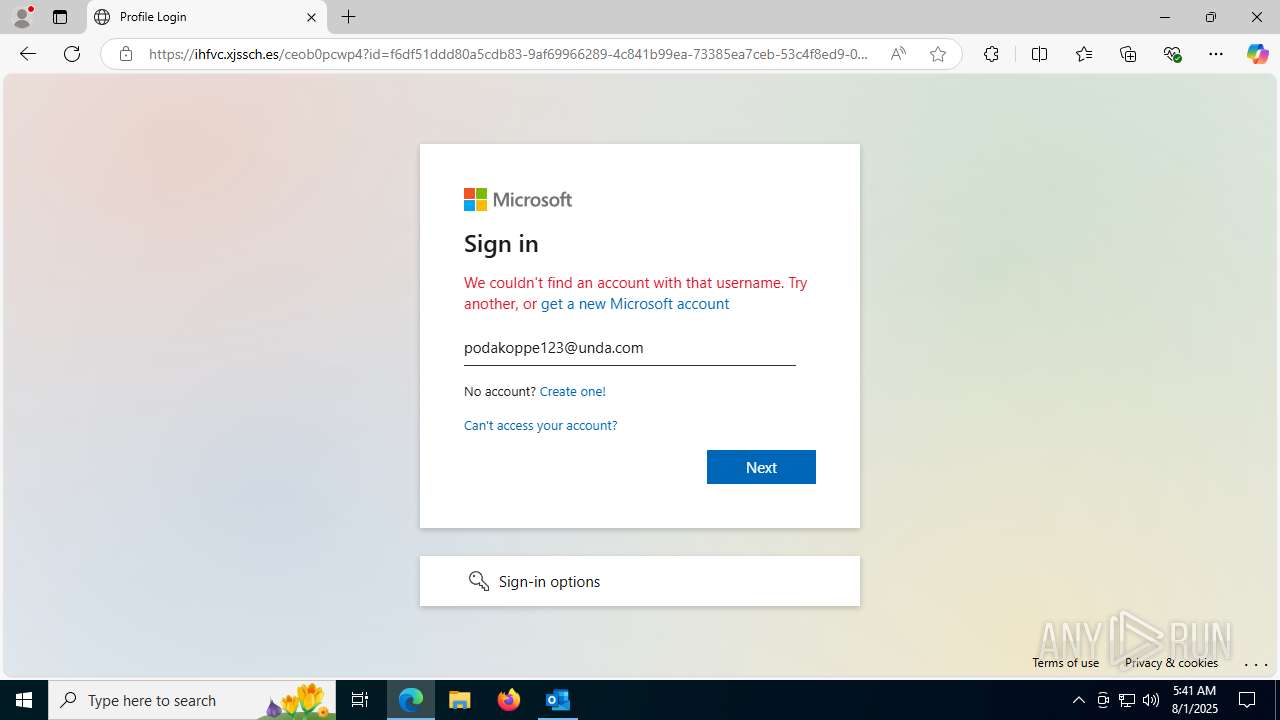
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | August 01, 2025, 05:39:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines (347), with CRLF line terminators |
| MD5: | 568F73E66007DB91E047855F0FB05021 |
| SHA1: | 350A5B78FF855225DC888633E9E1B1092A579C46 |
| SHA256: | CAA4DC616E669E55DA1D9E4F1EF060FF45EDE14DD4E19D1C7687F33EE5DF258C |
| SSDEEP: | 3072:Eu5pWi9V7KKIcLGHfWtQBf84wLfVZyYa+Nir75UKnANrRMLRepiLKz1OBqZnuS+P:Eu5ppEAHP0gqKxO0ZZtBq/PmO6yl |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 4836)
SUSPICIOUS
No suspicious indicators.INFO
Reads Environment values
- identity_helper.exe (PID: 7936)
Reads the computer name
- identity_helper.exe (PID: 7936)
Application launched itself
- msedge.exe (PID: 1180)
Checks supported languages
- identity_helper.exe (PID: 7936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
170
Monitored processes
30
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3624,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
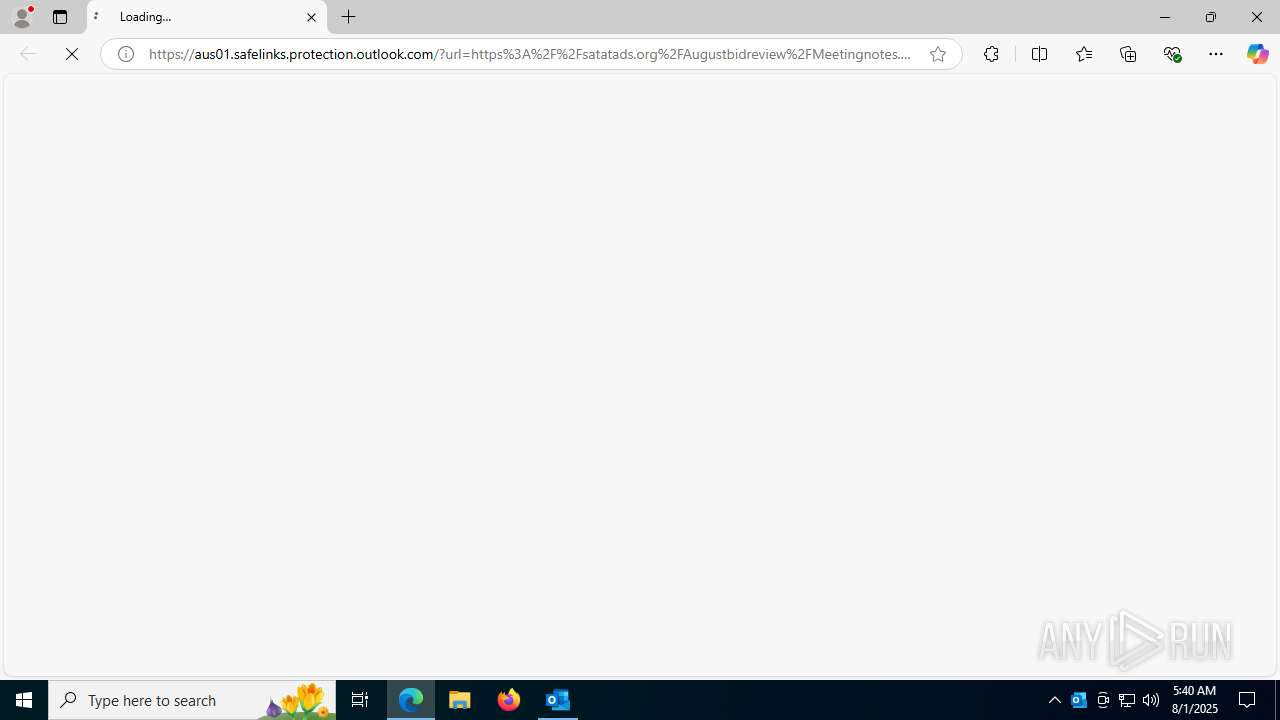
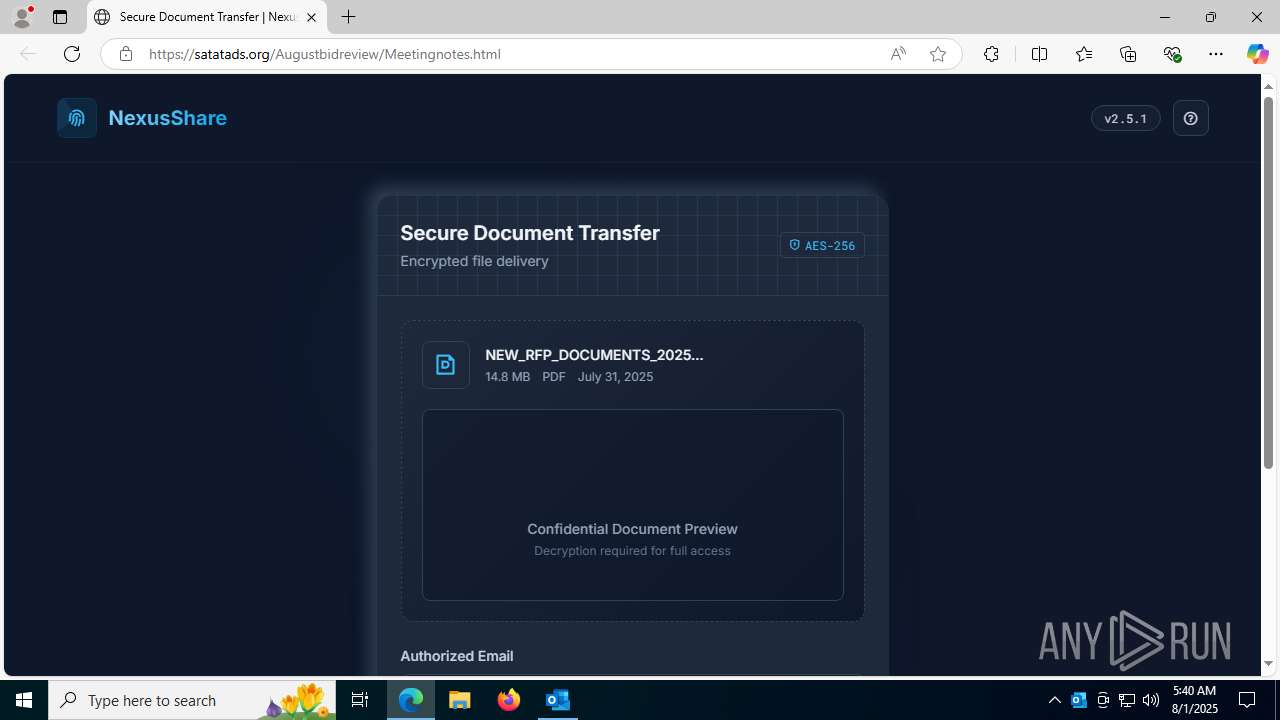
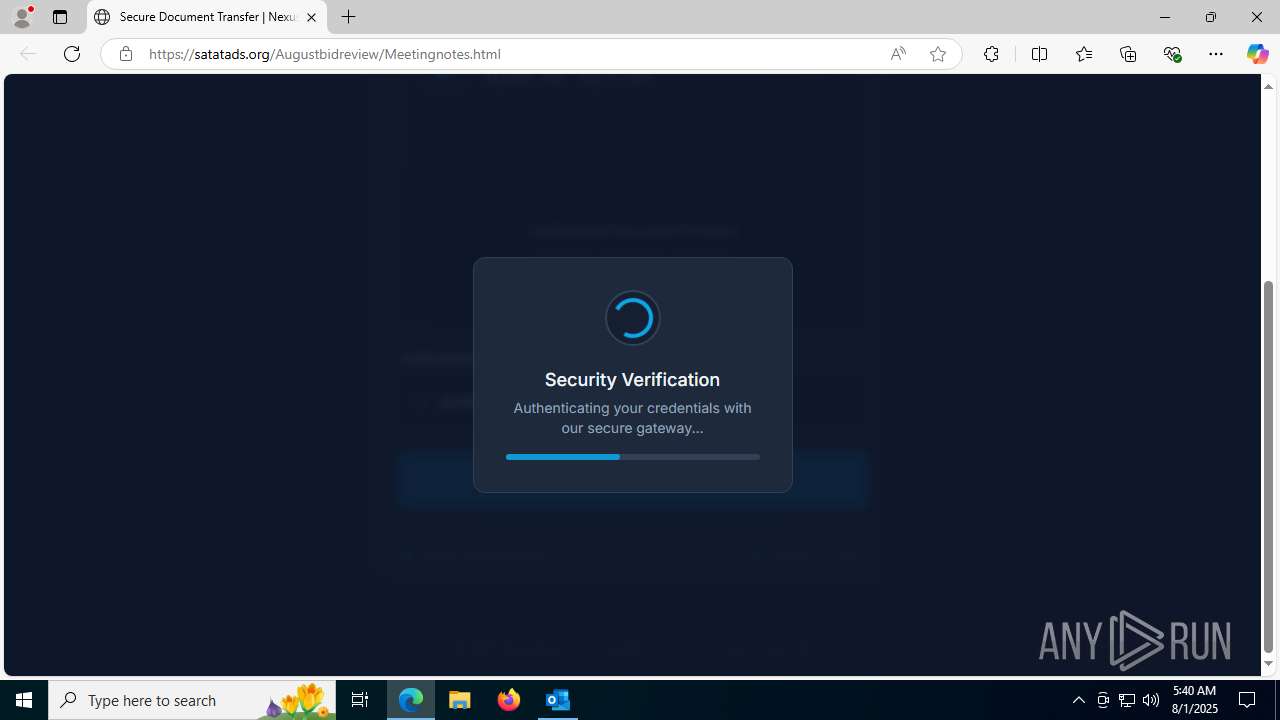
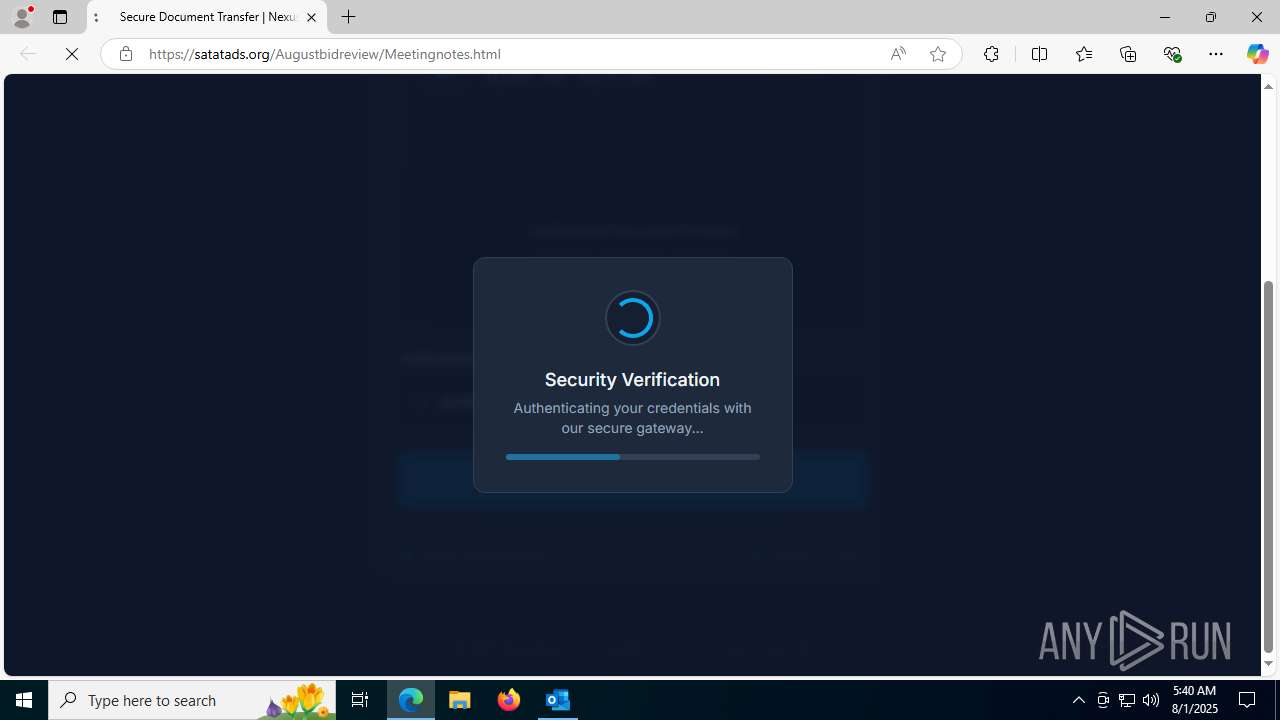
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://aus01.safelinks.protection.outlook.com/?url=https%3A%2F%2Fsatatads.org%2FAugustbidreview%2FMeetingnotes.html&data=05%7C02%7Cdanielle%40redhealth.com.au%7C1017b84c0eb4456442b108ddd0ae7618%7Cd18634b93b8a4170bcad02b7960460c8%7C0%7C0%7C638896170500591544%7CUnknown%7CTWFpbGZsb3d8eyJFbXB0eU1hcGkiOnRydWUsIlYiOiIwLjAuMDAwMCIsIlAiOiJXaW4zMiIsIkFOIjoiTWFpbCIsIldUIjoyfQ%3D%3D%7C0%7C%7C%7C&sdata=oqa74QX7eCkNRYog0PWtkKuvCsAwb5%2BKYRsYO6ew14g%3D&reserved=0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "02062B9D-E122-41B3-BCFA-CB7C29FFB856" "46408767-4787-4912-A58C-14EC67D750AF" "7096" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2452,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=2788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=4324,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=4280 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --always-read-main-dll --field-trial-handle=4088,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=5236 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6600,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=6324 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2408,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=2352 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1468,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2228,i,6017241776497109676,17232272477034660766,262144 --variations-seed-version --mojo-platform-channel-handle=2464 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
14 003
Read events
13 531
Write events
392
Delete events
80
Modification events
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsData |
| Operation: | write | Name: | SessionId |
Value: DBA04505-3F3E-4BFD-8B24-06943B275D6D | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Preferences |
| Operation: | delete value | Name: | ChangeProfileOnRestart |
Value: | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Licensing |
| Operation: | delete value | Name: | EligibleForExtendedGrace |
Value: | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Experiment\outlook |
| Operation: | write | Name: | BuildNumber |
Value: 16.0.16026 | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ExperimentConfigs\Ecs\outlook |
| Operation: | write | Name: | Expires |
Value: int64_t|0 | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ExperimentConfigs\Ecs\outlook |
| Operation: | delete value | Name: | ConfigIds |
Value: | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ExperimentConfigs\Ecs\outlook |
| Operation: | delete value | Name: | ETag |
Value: | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency\StartupItems |
| Operation: | delete value | Name: | /b3 |
Value: 戯3᮸ | |||
| (PID) Process: | (7096) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency\StartupItems |
| Operation: | delete value | Name: | w>3 |
Value: 㹷3᮸ | |||
Executable files
0
Suspicious files
230
Text files
76
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7096 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7096 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:F0AEE4DAD144C9B2621184B98AD0782E | SHA256:ECA18F5D4806BE7C4836A6796E71968B4FCC33C04BDF766D97FE61BBC6DD3FC1 | |||
| 7096 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\718354E7.dat | image | |
MD5:C174053A25DB51161385B4FE348DF058 | SHA256:98F1771C8EFA6980AA65CF5948EE73451D2C4AC3B08AC07E8E6912F2269593AA | |||
| 7096 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:426BDB17DCBC29161EAA1F4D578E9309 | SHA256:2A9BD4EF262097DC4C1DAB3ED7B8E5377757B6B82B30791426C0E761CC5B68FA | |||
| 7096 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\5475cb191e478c39370a215b2da98a37e9dc813d.tbres | binary | |
MD5:D8E79D2A08FC9E11B3AA9731639E6E09 | SHA256:53AE4F74490CCCF4C5C04F3AD99B155F9DC6355D85EE26CC59ABCD0CDE722FB8 | |||
| 1180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18f0b4.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_04AEA08F1C3CFB4293C5E57188EF63B2.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
| 1180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:DA6ED6E62DD0F5AF5A233F33A8D0EC67 | SHA256:06A36E4ED13DCC531714348C2E8BC392BED1B6CDD510EDFCF08CCF8113D0E2CC | |||
| 1180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18f0b4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
103
DNS requests
123
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5724 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7888 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754481186&P2=404&P3=2&P4=V04Qi1Thy%2bjFRsZnE3MjV1xGxZp8Z9xeiei%2flIgqMGDOijEfH5V6Q%2btMB5Z9PJHzWc1aEITenCCjYtZYT5htYQ%3d%3d | unknown | — | — | whitelisted |
7888 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754481186&P2=404&P3=2&P4=V04Qi1Thy%2bjFRsZnE3MjV1xGxZp8Z9xeiei%2flIgqMGDOijEfH5V6Q%2btMB5Z9PJHzWc1aEITenCCjYtZYT5htYQ%3d%3d | unknown | — | — | whitelisted |
7888 | svchost.exe | HEAD | — | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1754481189&P2=404&P3=2&P4=MJq6Zs8TMhnhcwkZFkcO5Evdij0nErXOuFW0F%2b3aZM2cllXMSqajoE4NXWjGZDj1oiDxg6E4bD8tTqwrzBBctg%3d%3d | unknown | — | — | whitelisted |
7888 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754481186&P2=404&P3=2&P4=V04Qi1Thy%2bjFRsZnE3MjV1xGxZp8Z9xeiei%2flIgqMGDOijEfH5V6Q%2btMB5Z9PJHzWc1aEITenCCjYtZYT5htYQ%3d%3d | unknown | — | — | whitelisted |
4836 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:KmIUVYzw2QYf2iG08R1AovzVJPVLGMRda_pJxj8K1TE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7096 | OUTLOOK.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6312 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7096 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7096 | OUTLOOK.EXE | 2.19.198.51:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
7096 | OUTLOOK.EXE | 52.111.231.8:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7096 | OUTLOOK.EXE | 135.225.150.15:443 | nleditor.osi.office.net | LUCENT-CIO | US | whitelisted |
5724 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
nleditor.osi.office.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4836 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as Tycoon (xjssch .es) |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |