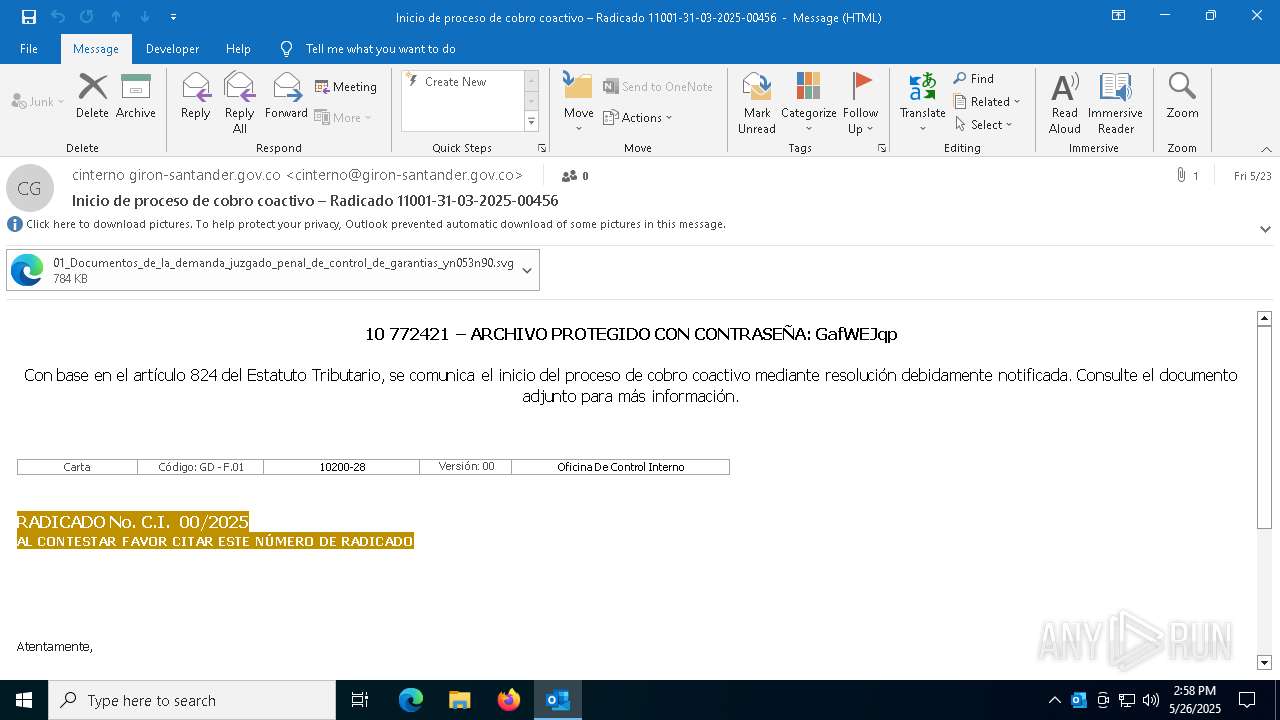
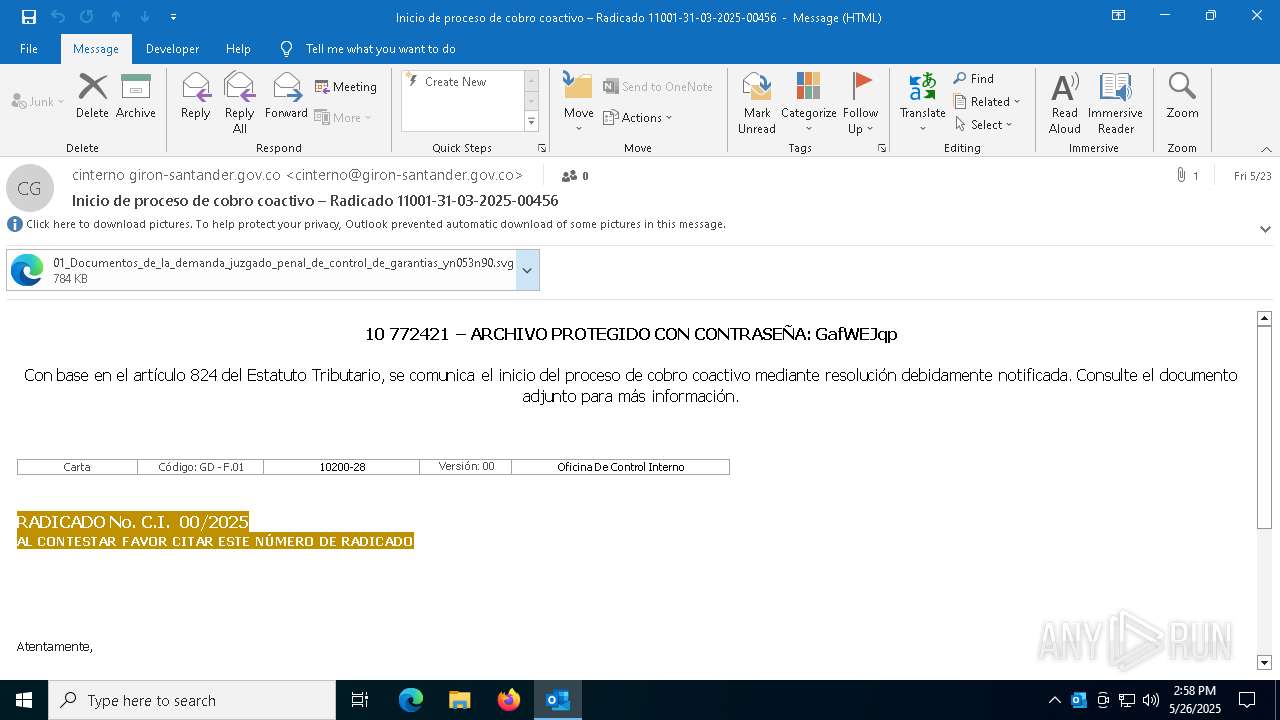
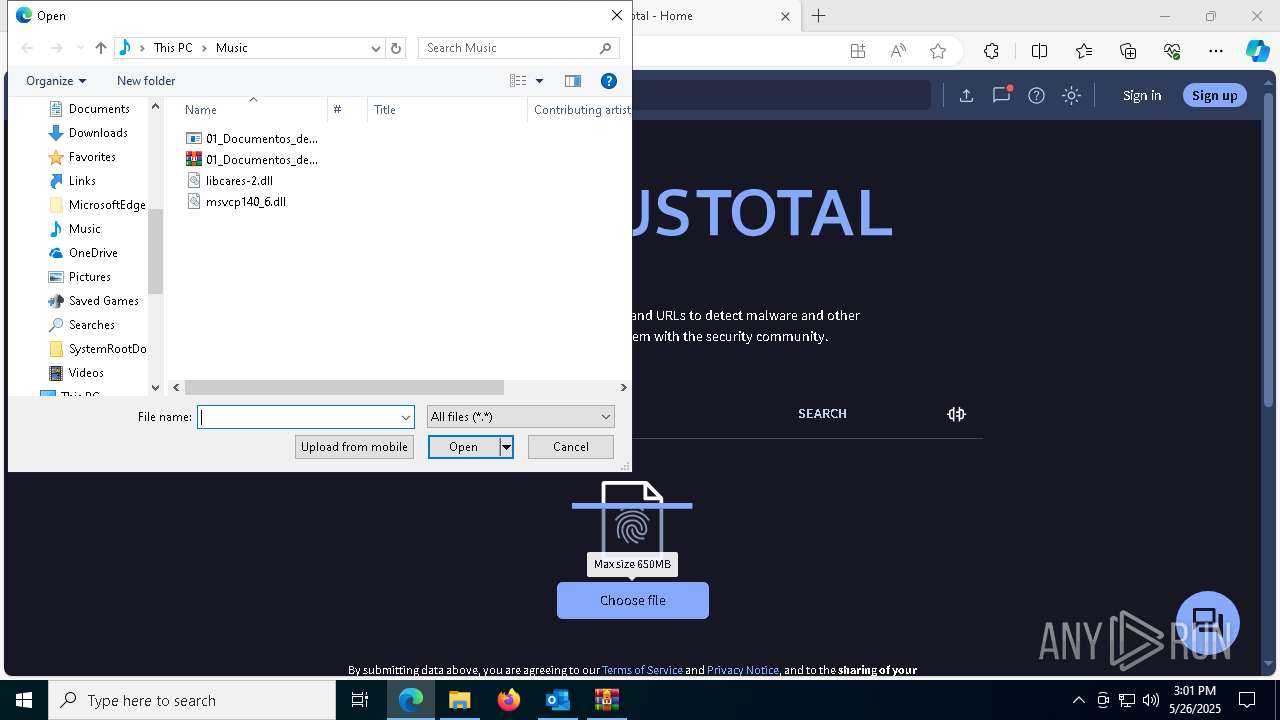
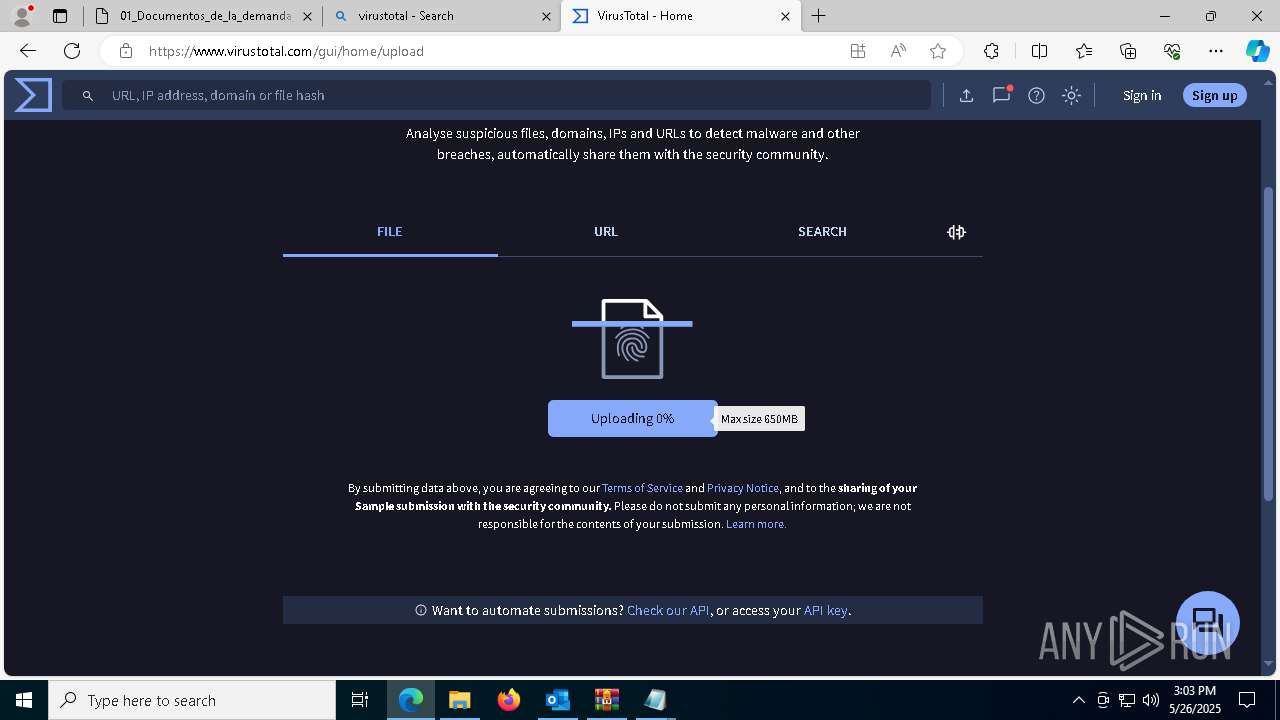
| File name: | Inicio de proceso de cobro coactivo – Radicado 11001-31-03-2025-00456.eml |
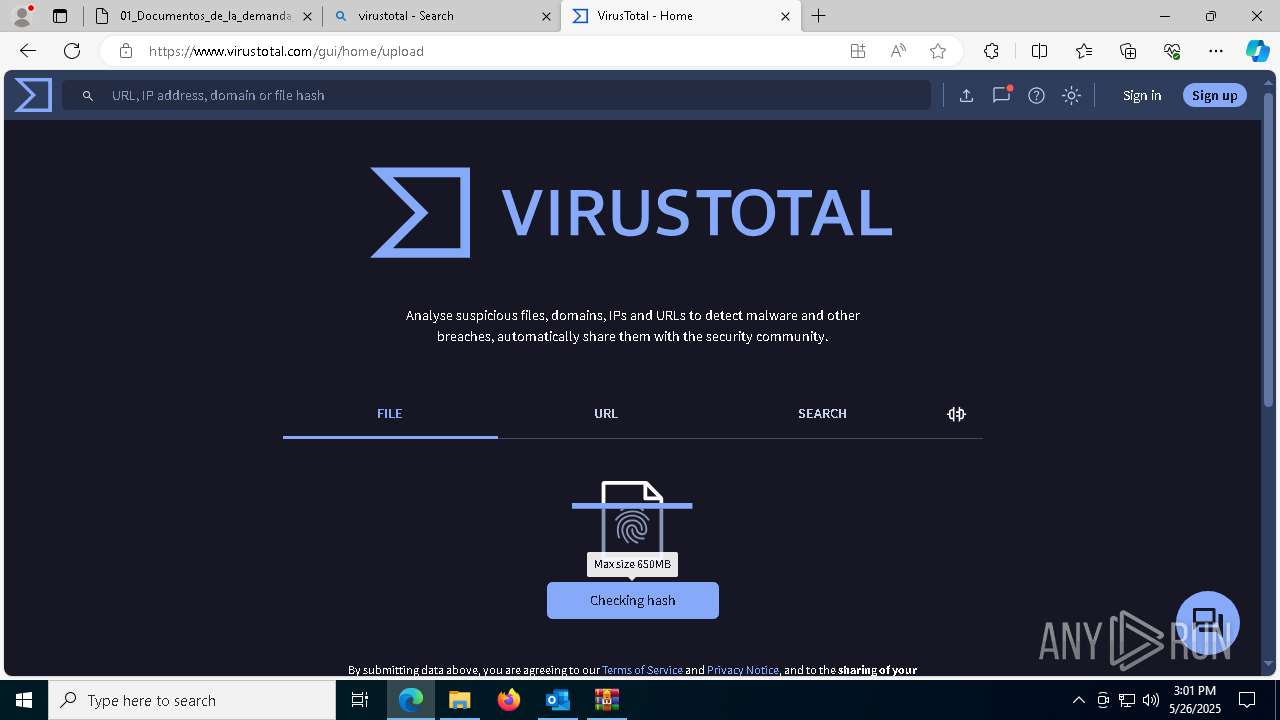
| Full analysis: | https://app.any.run/tasks/2d381885-096d-429b-aa31-f158ce923ddd |
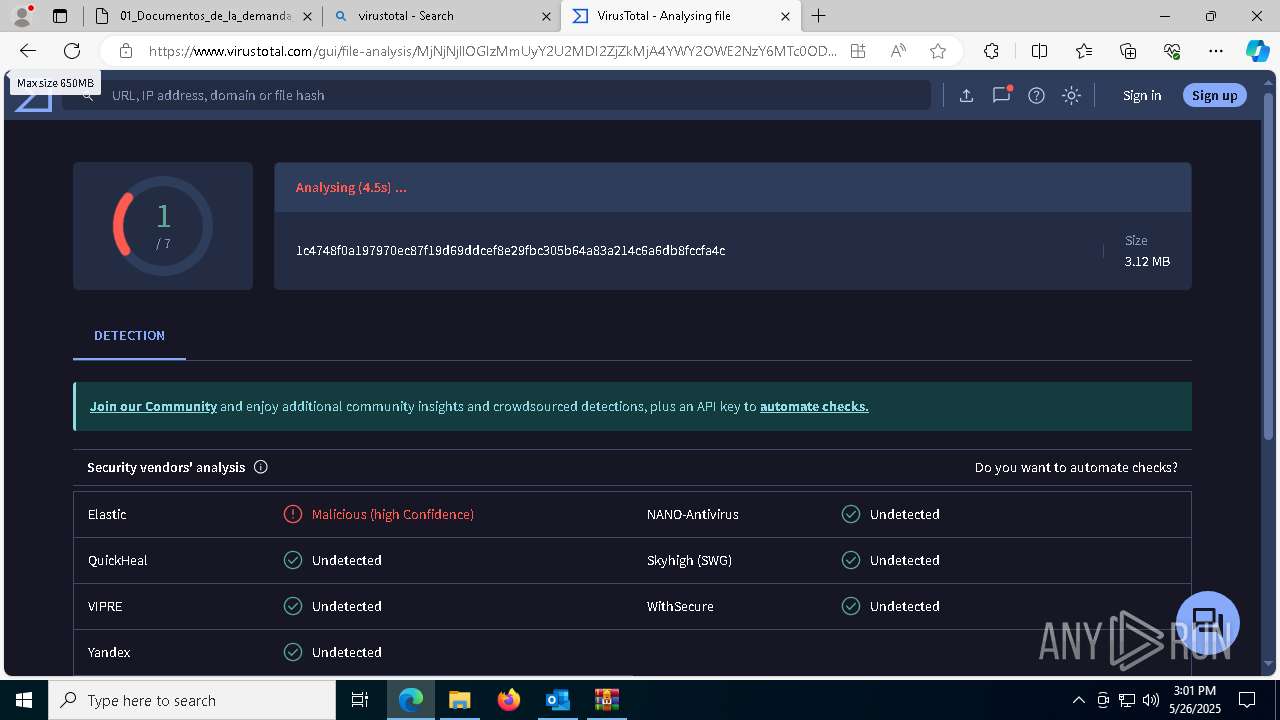
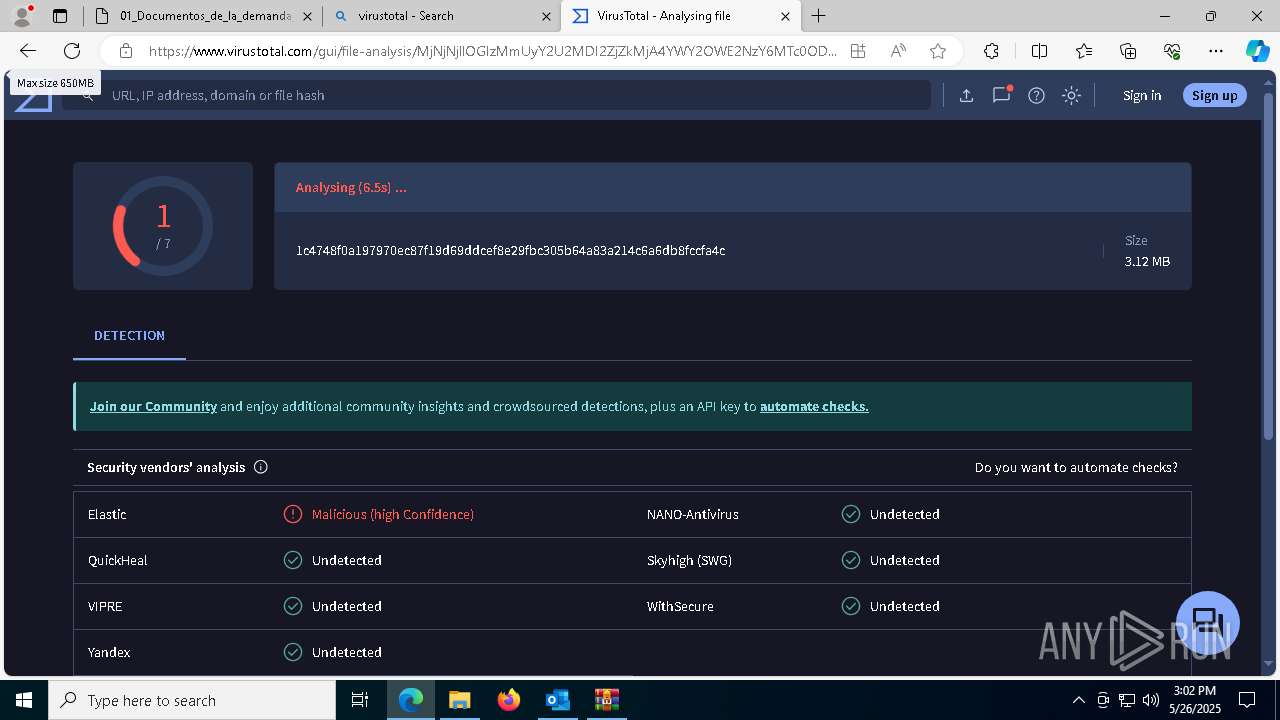
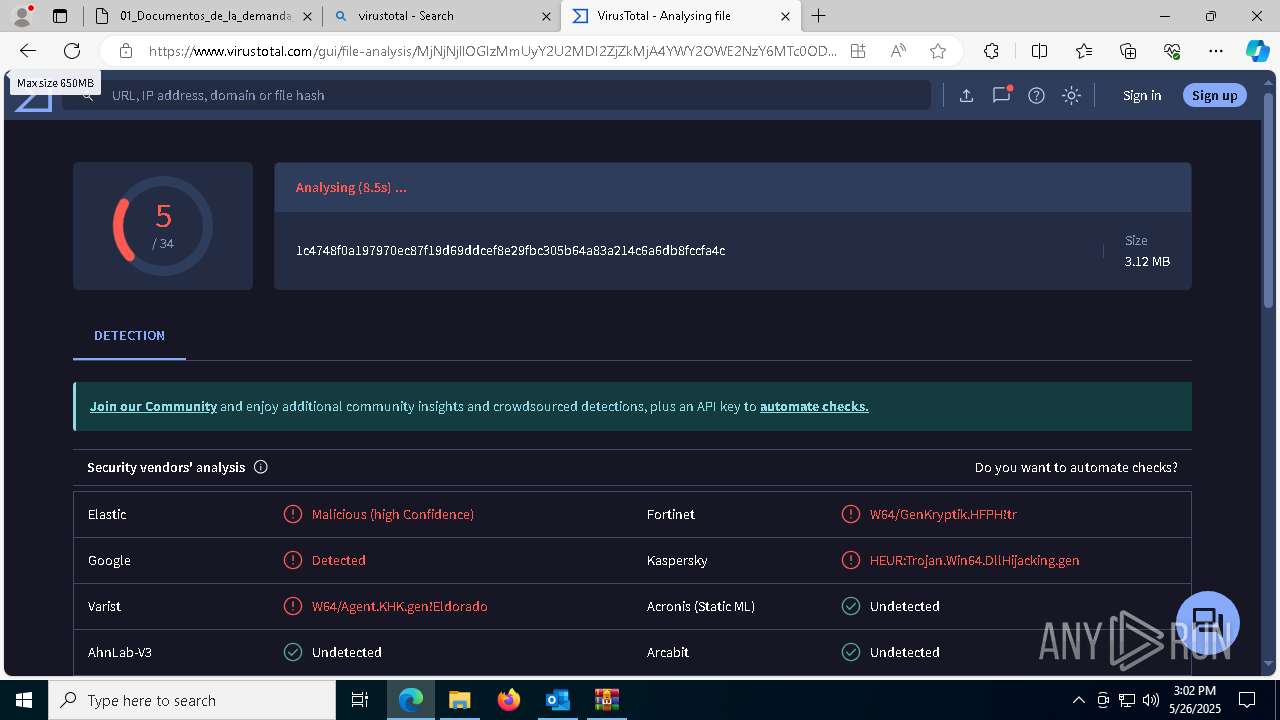
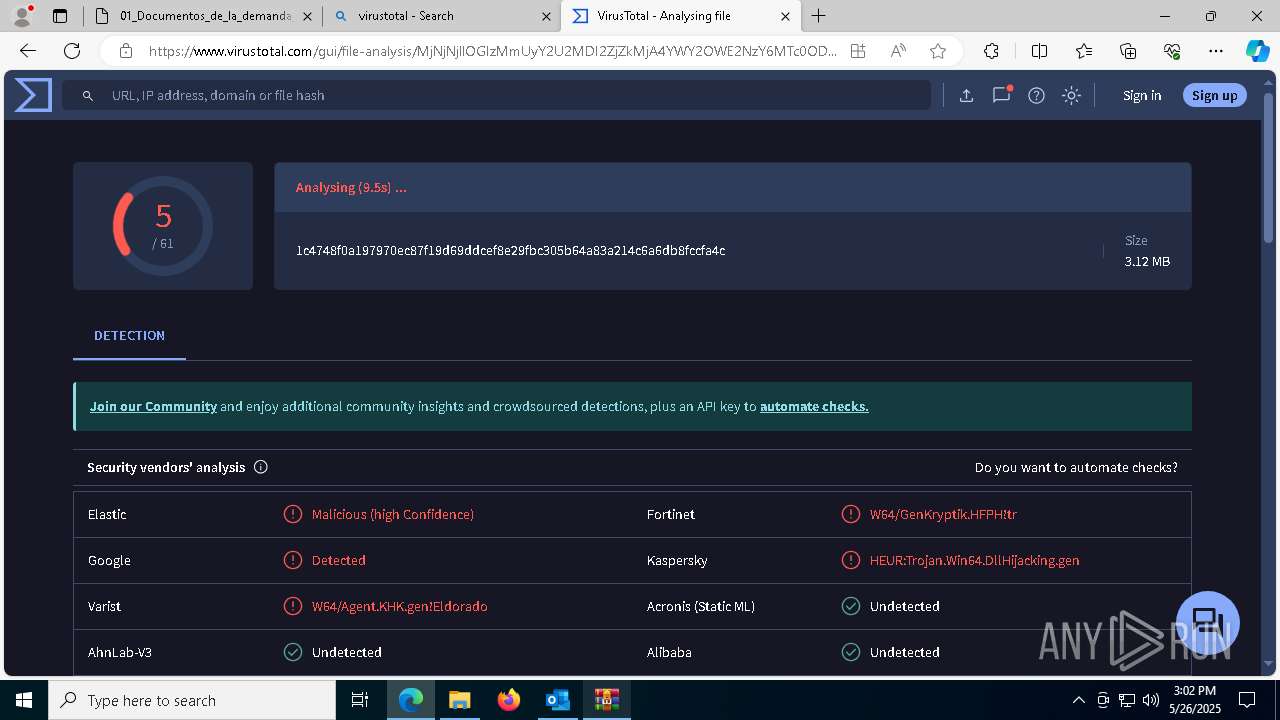
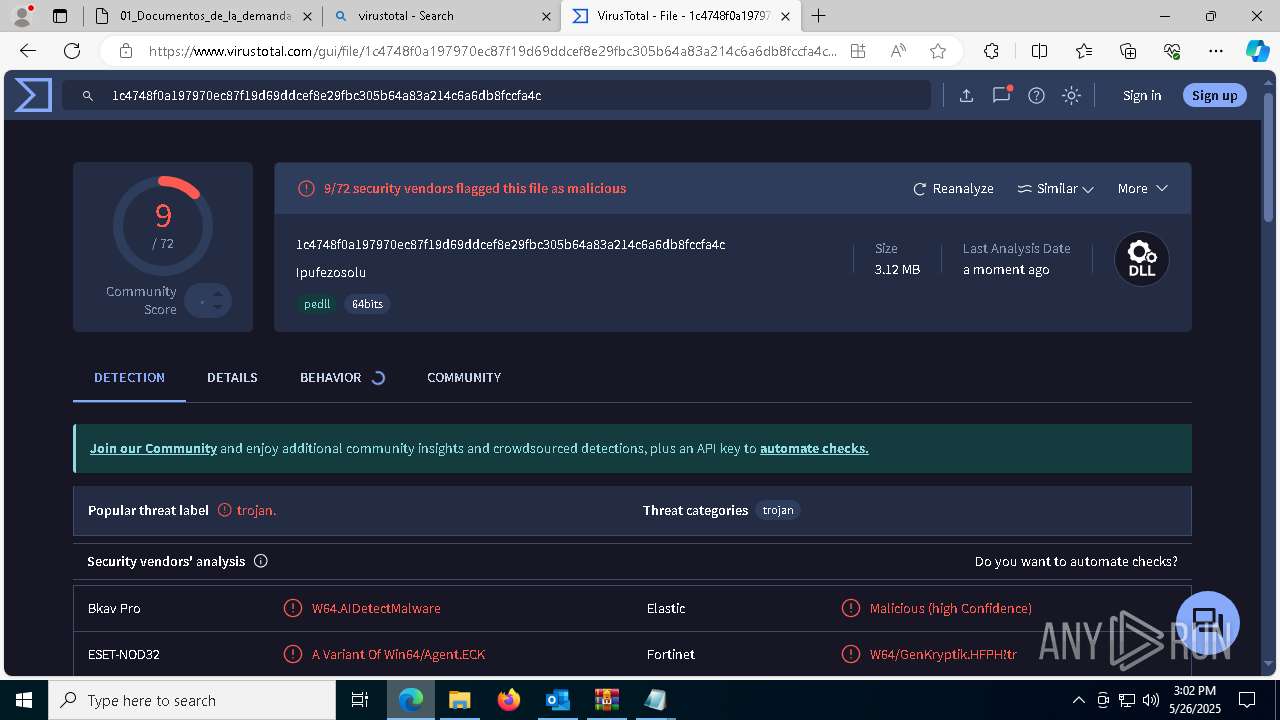
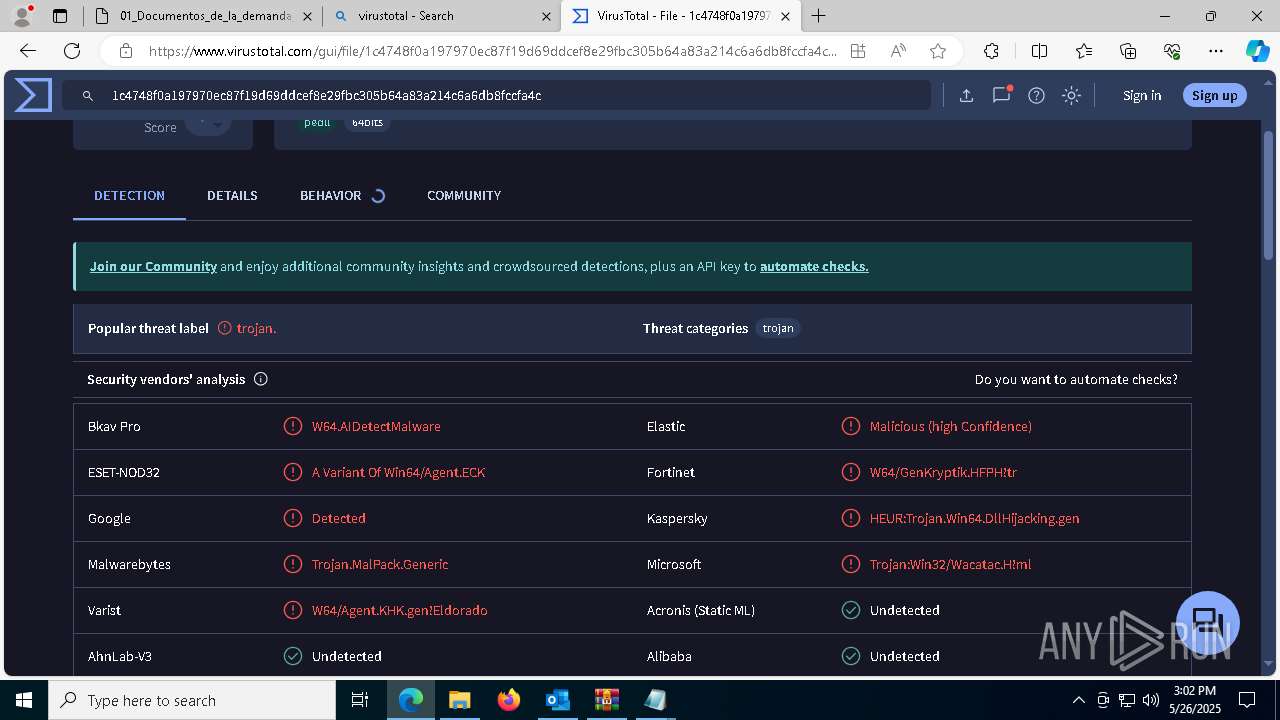
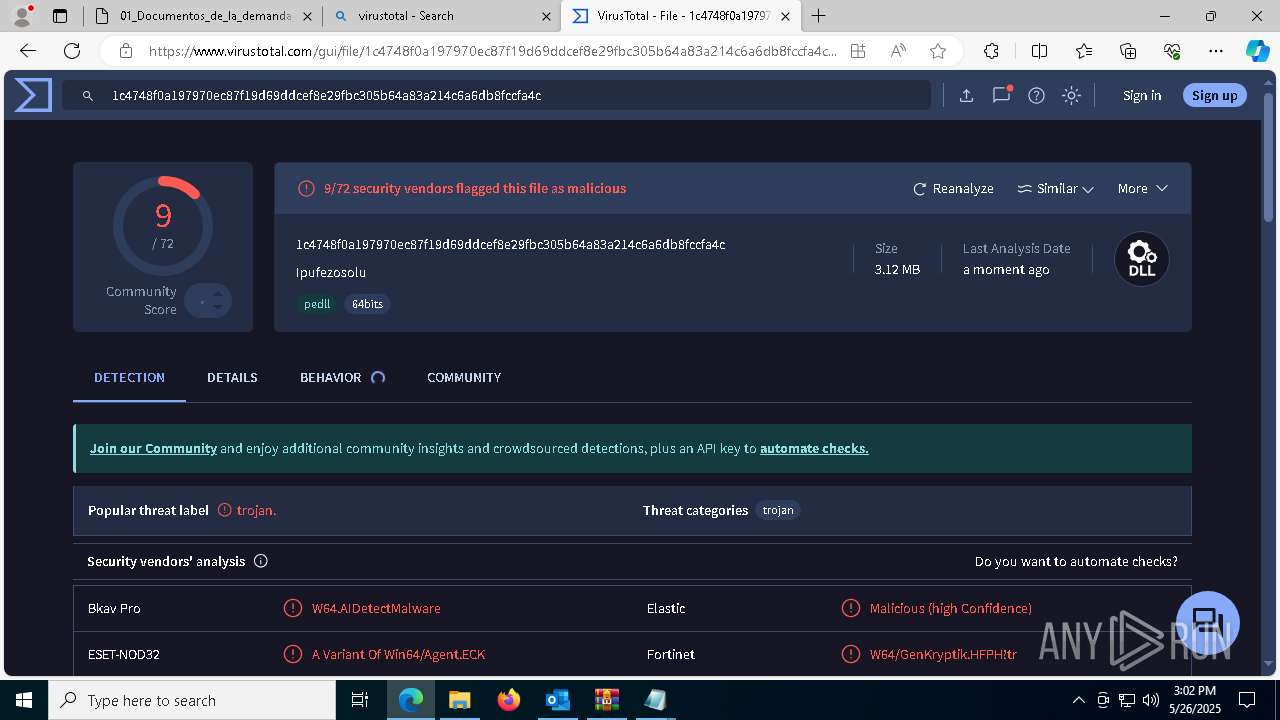
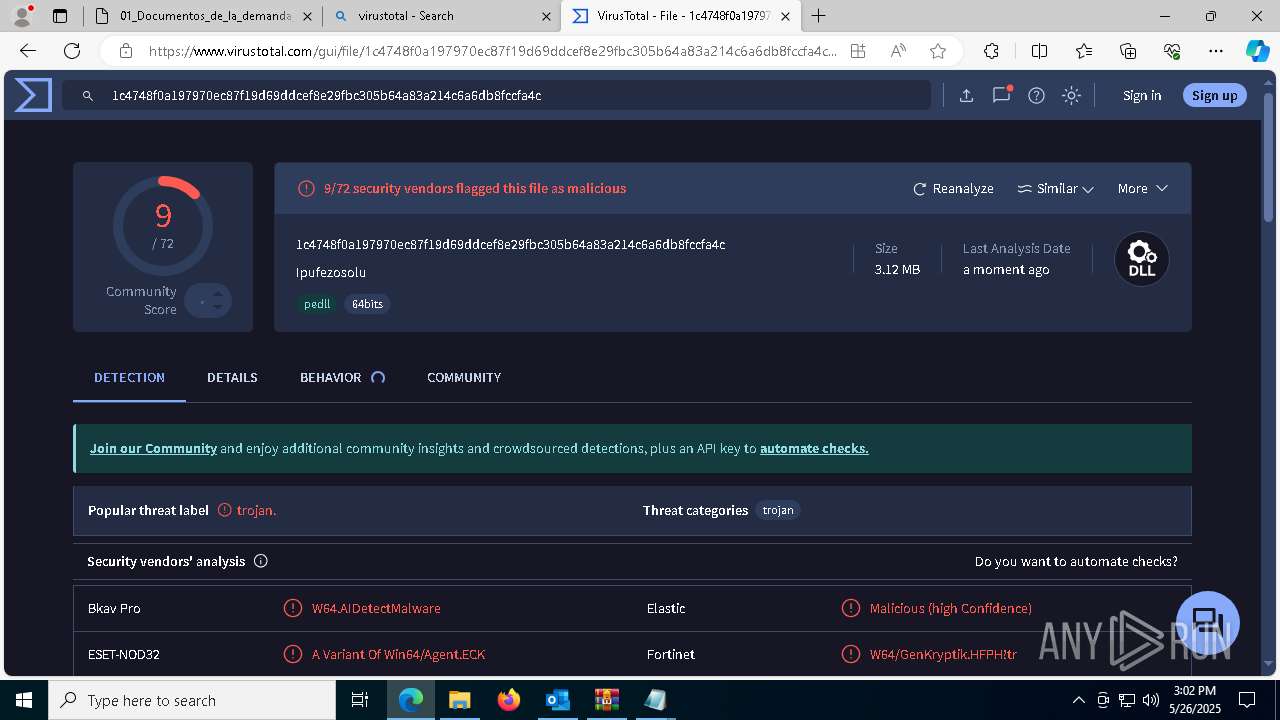
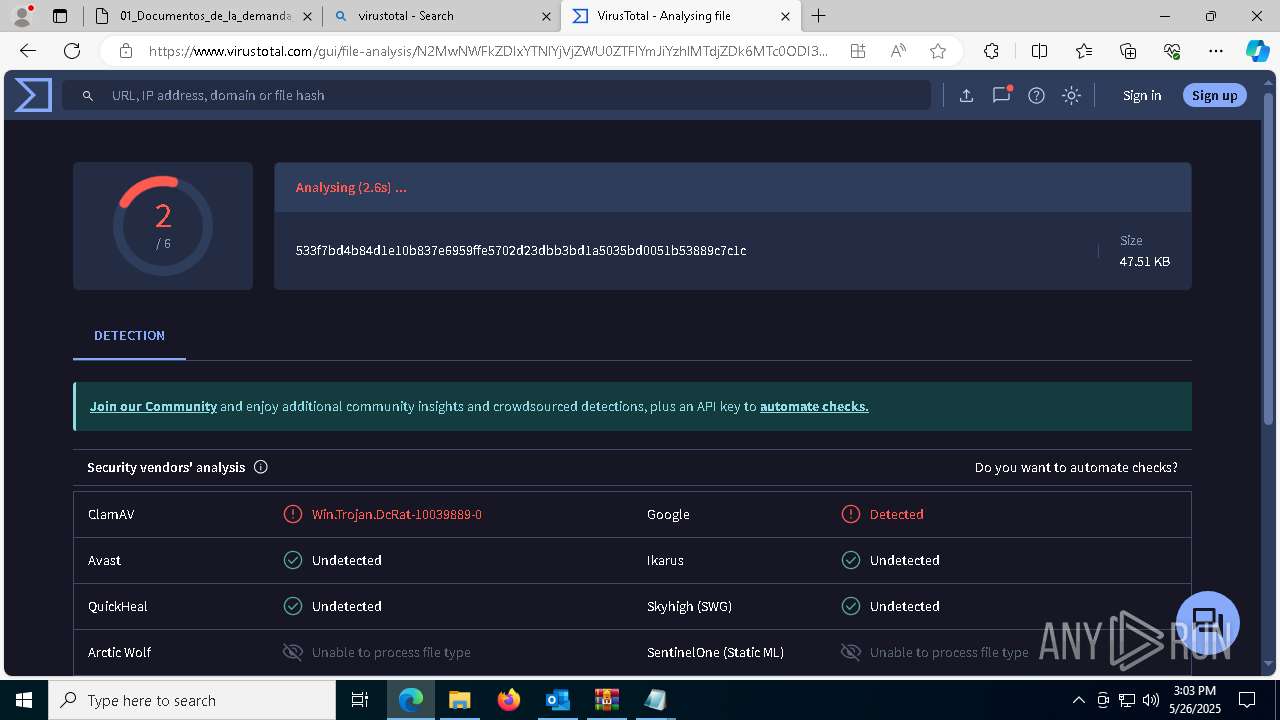
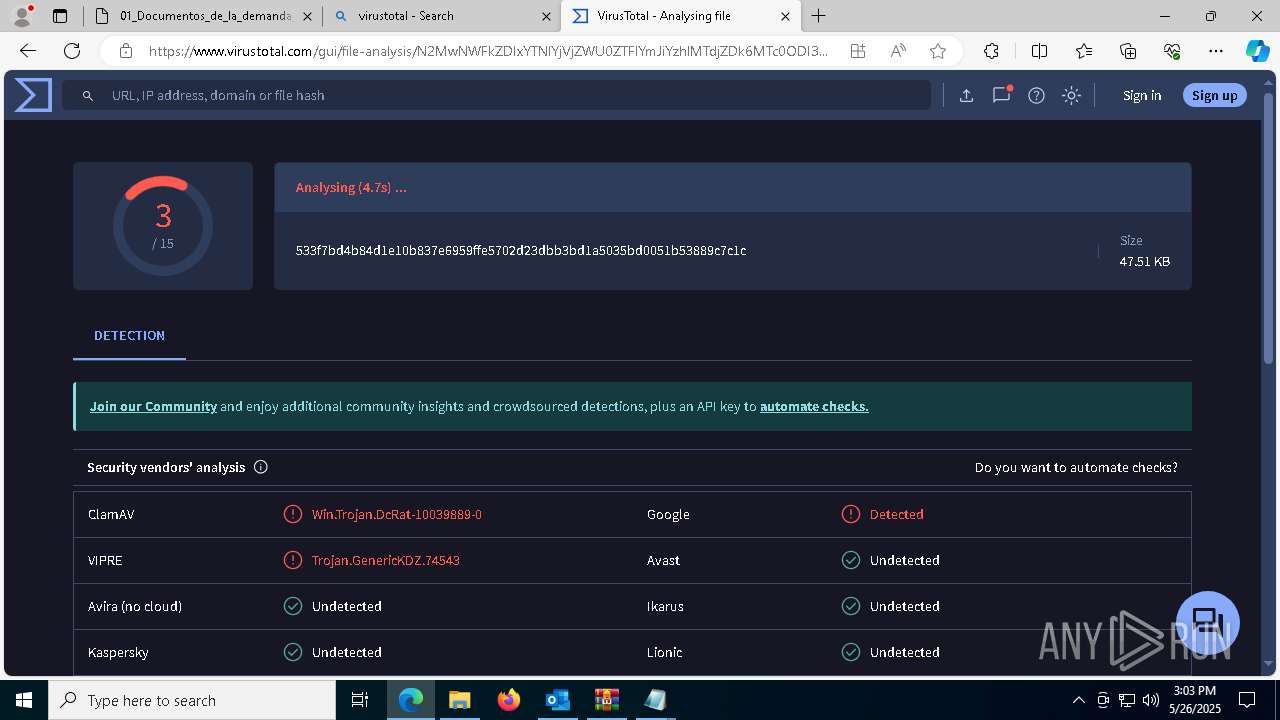
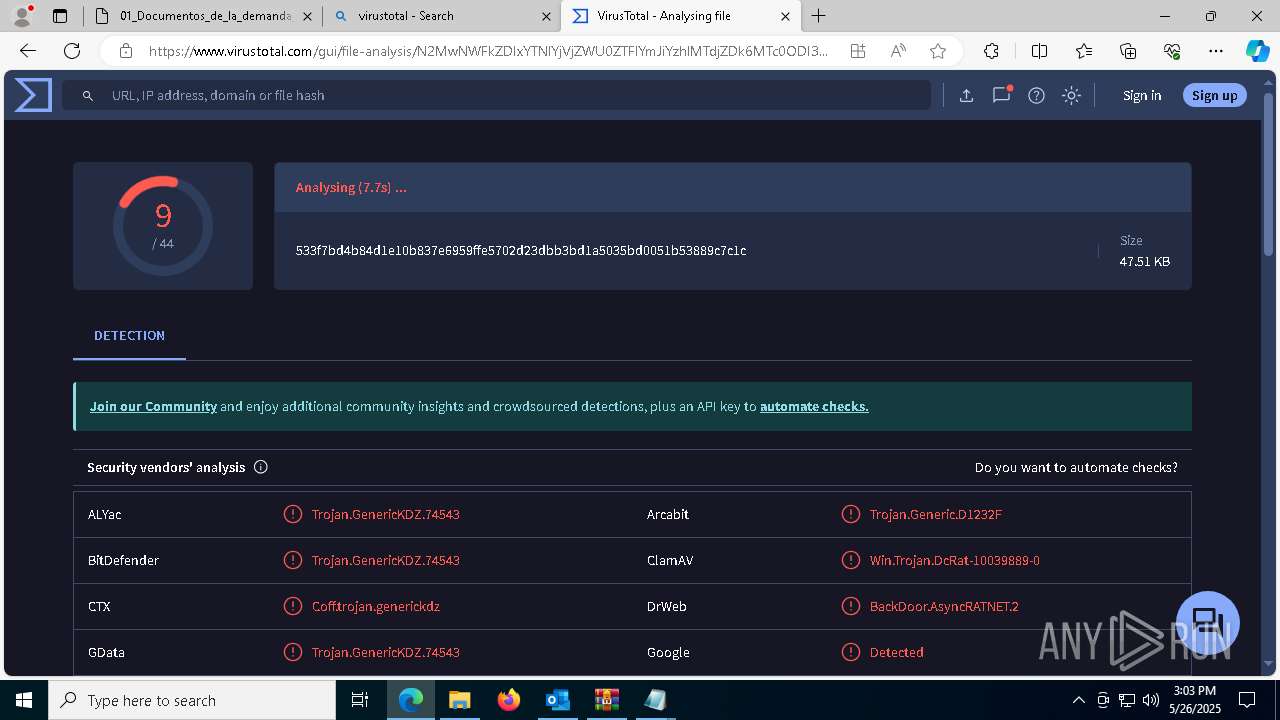
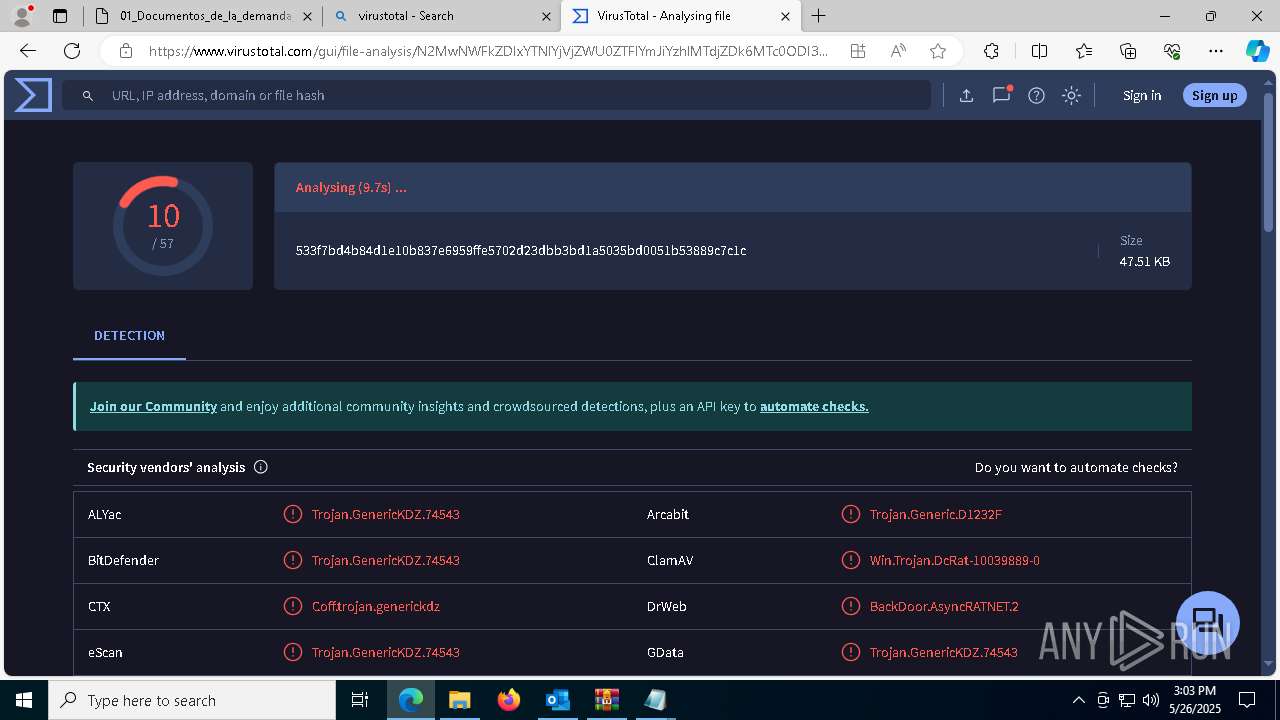
| Verdict: | Malicious activity |
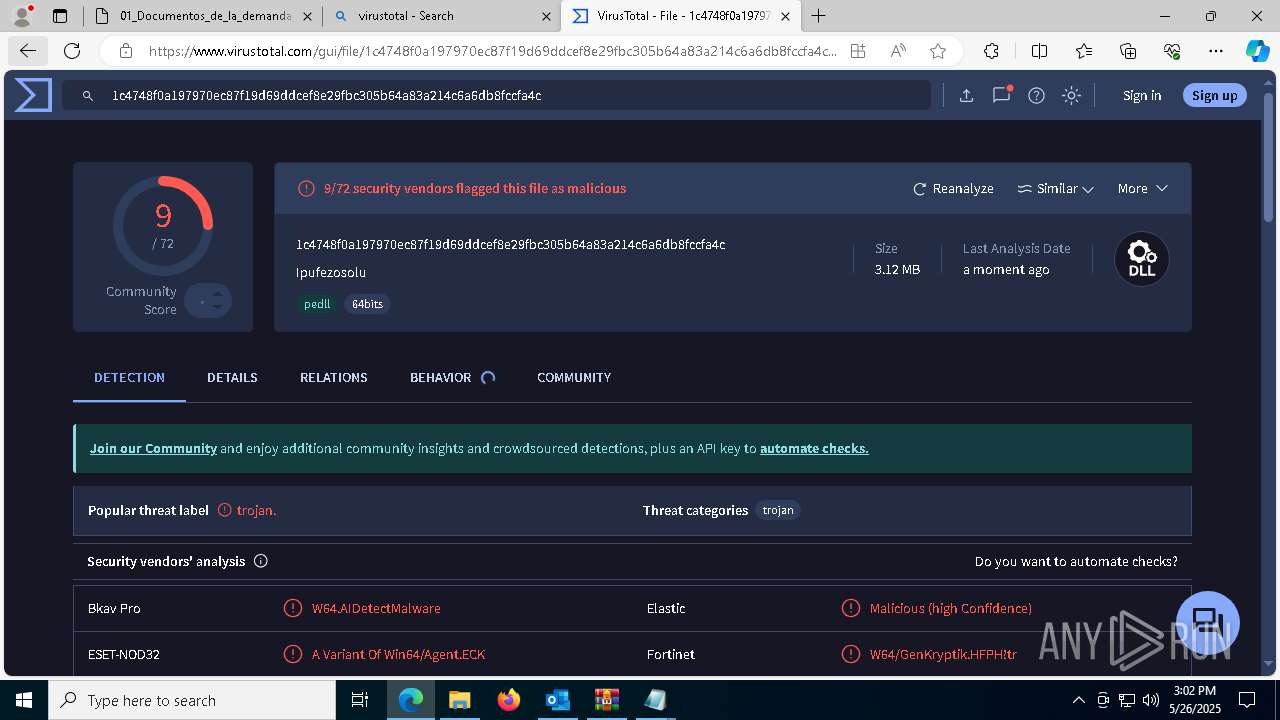
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 26, 2025, 14:58:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | AFFCD4C93E18E24D8102D37864EACA44 |
| SHA1: | A3B1F757839BAE2E3CC4A6C7F68CFBBC82C029D2 |
| SHA256: | CA1BE473B68BC9E3533D8B35B6D7B1916AAC37C8D04B4DDB3EB7E1E64C008319 |
| SSDEEP: | 12288:+7xz/LbTfMCPlPzQb5tN84w8ithSb3lZMgALD5ePAl3DIh7WT7pe5prtdR0Qgkrg:+N3H65t+lSzPMgAkAE6otdawMHn |
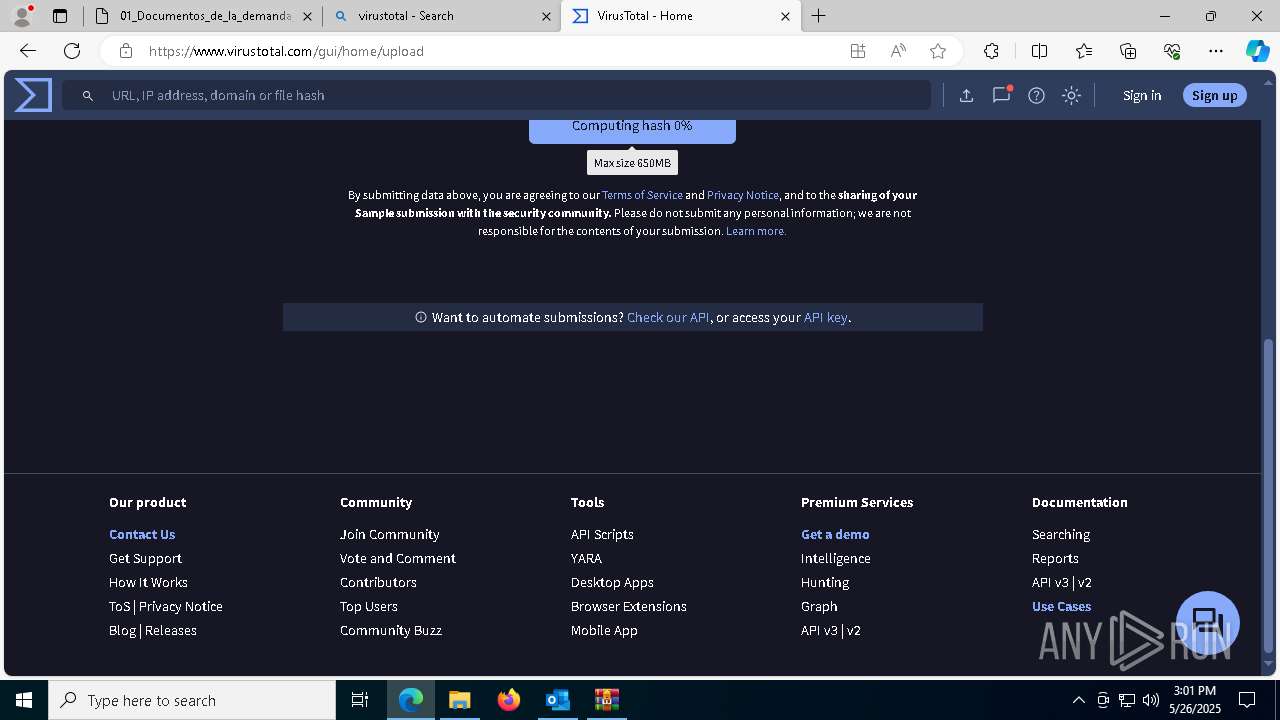
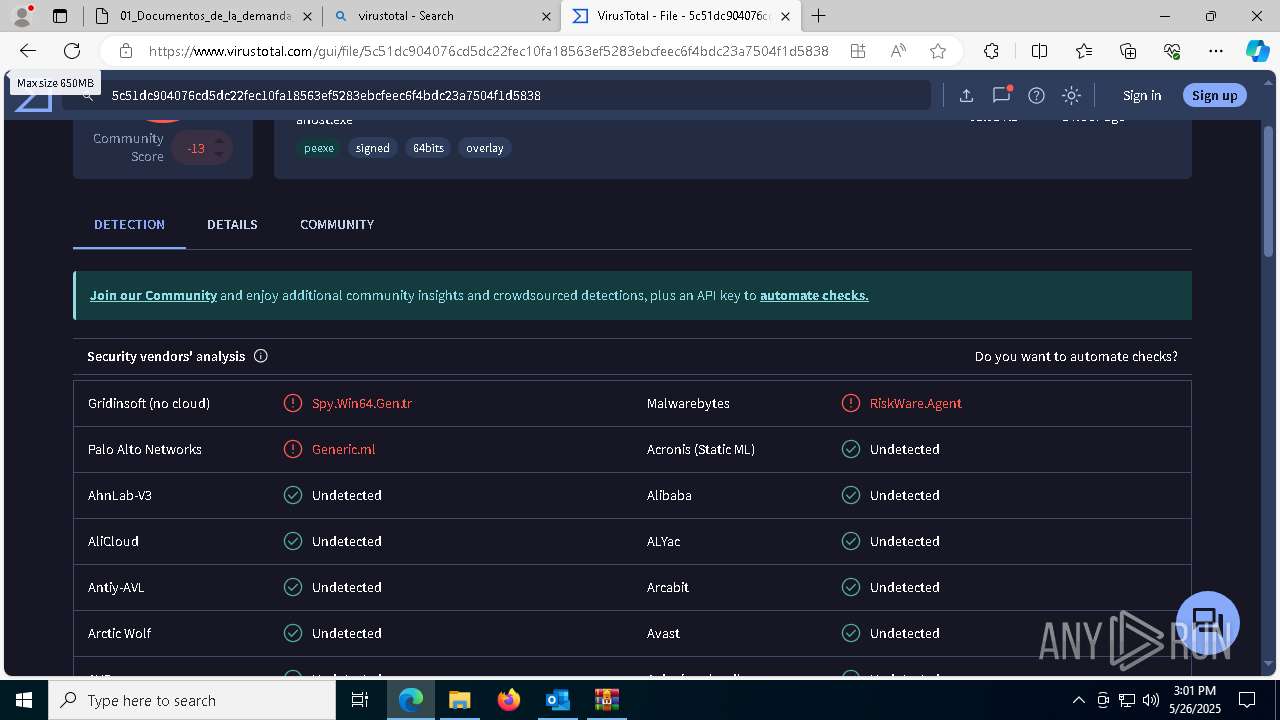
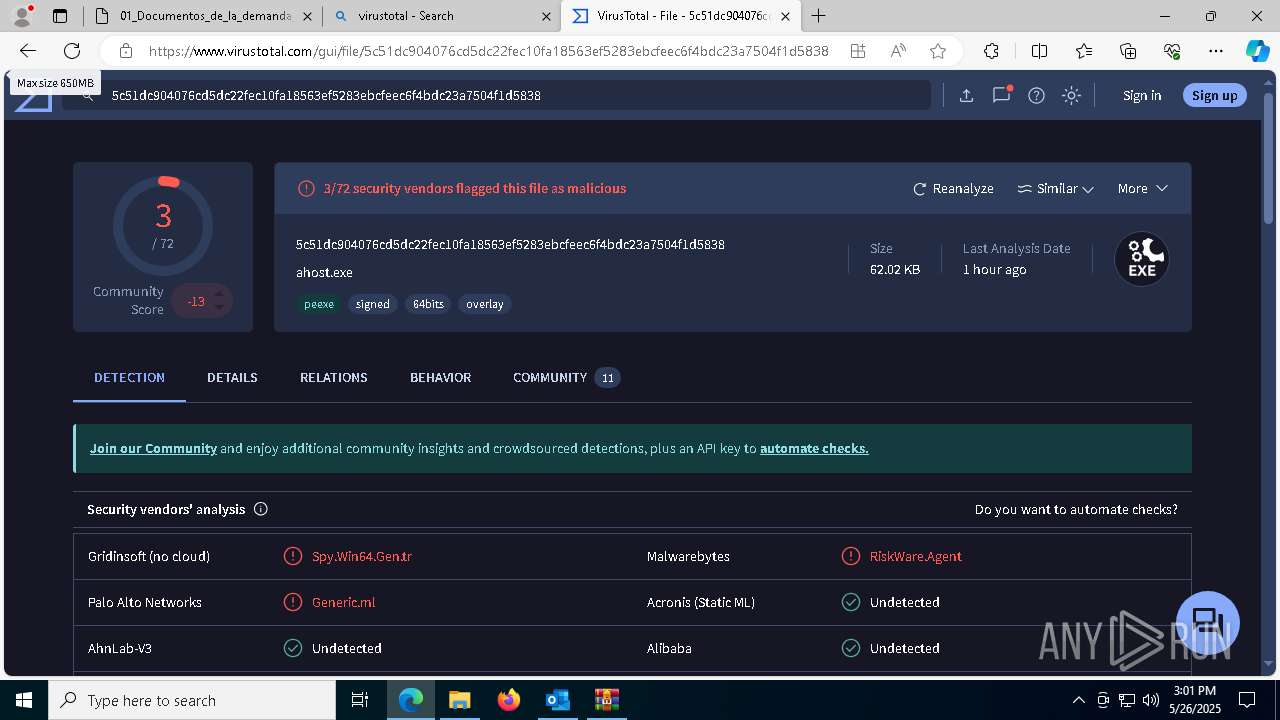
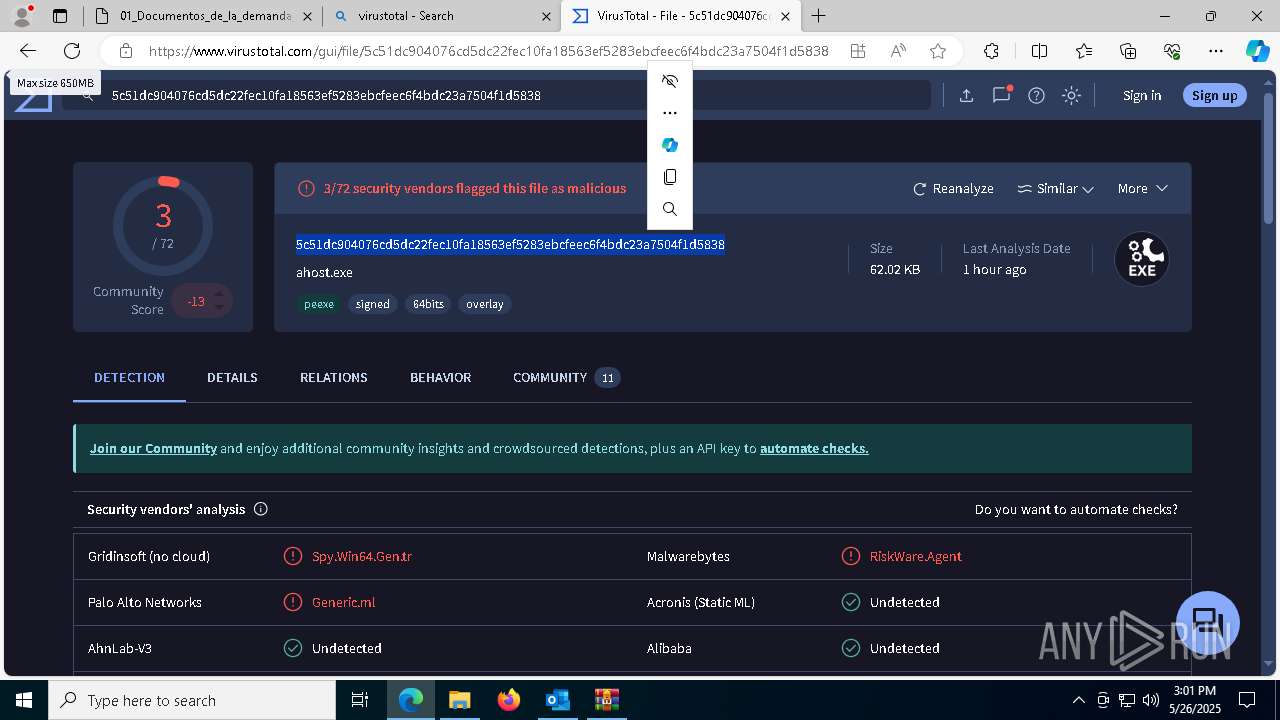
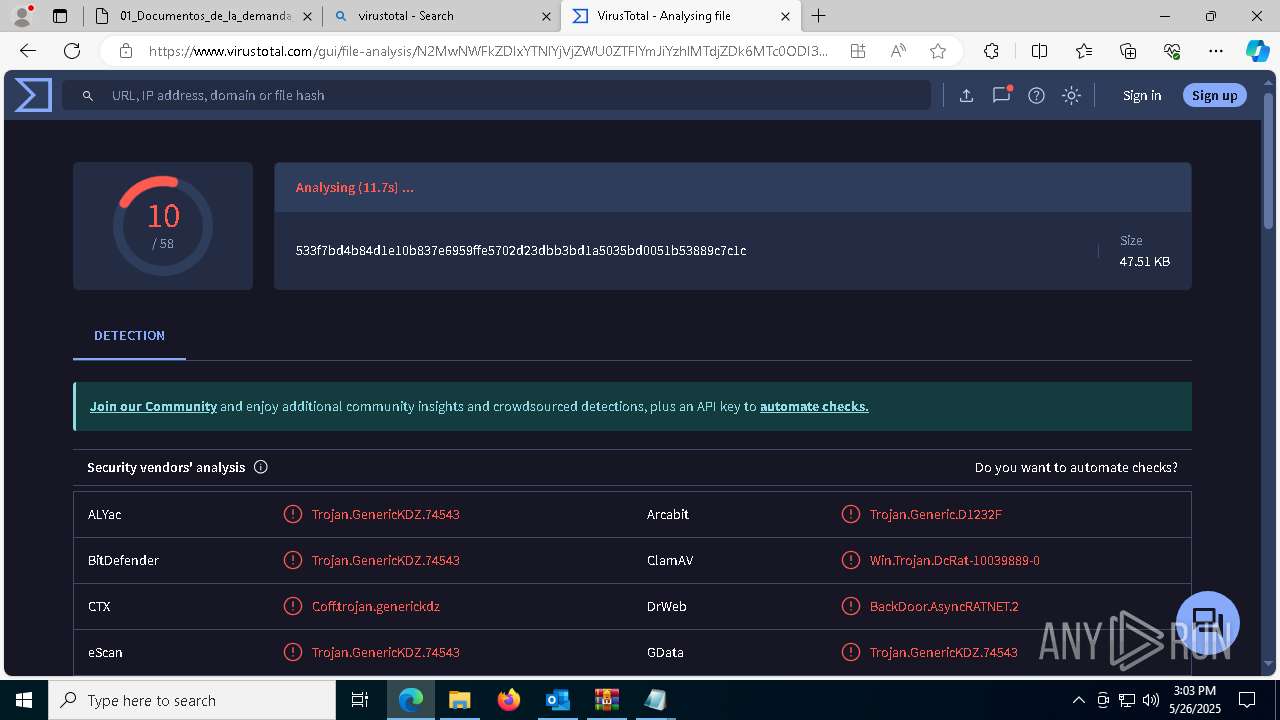
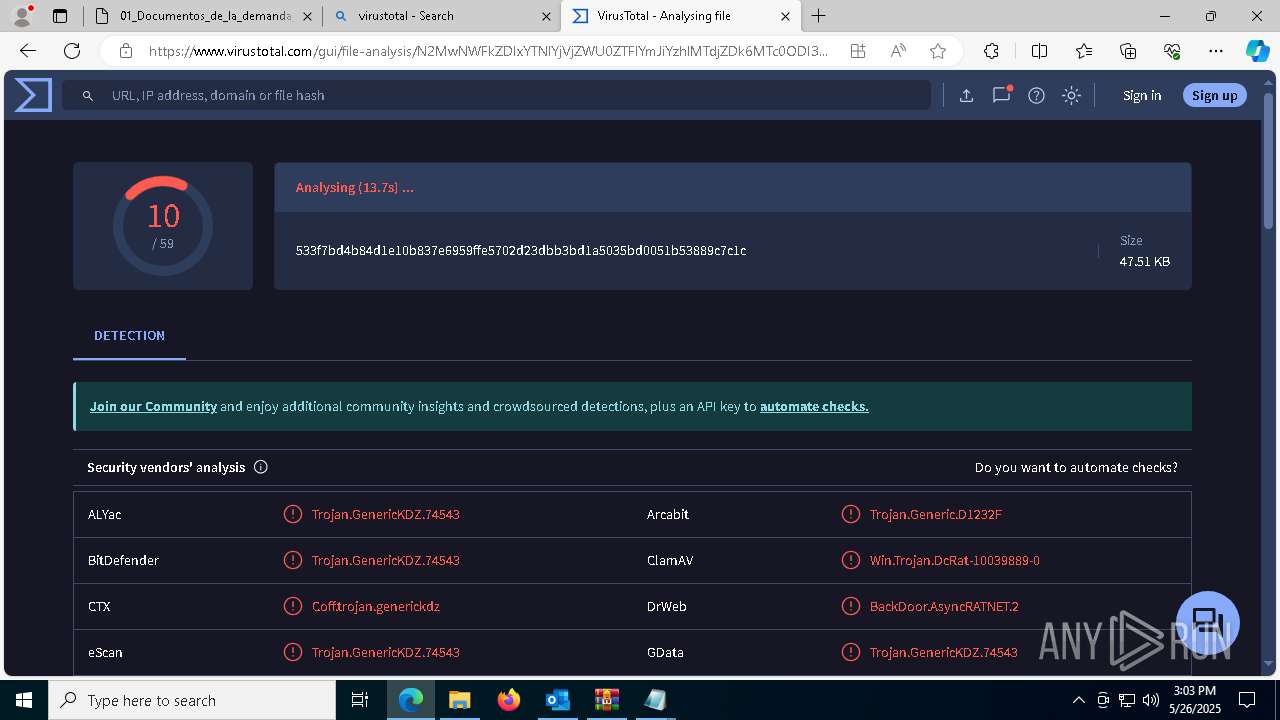
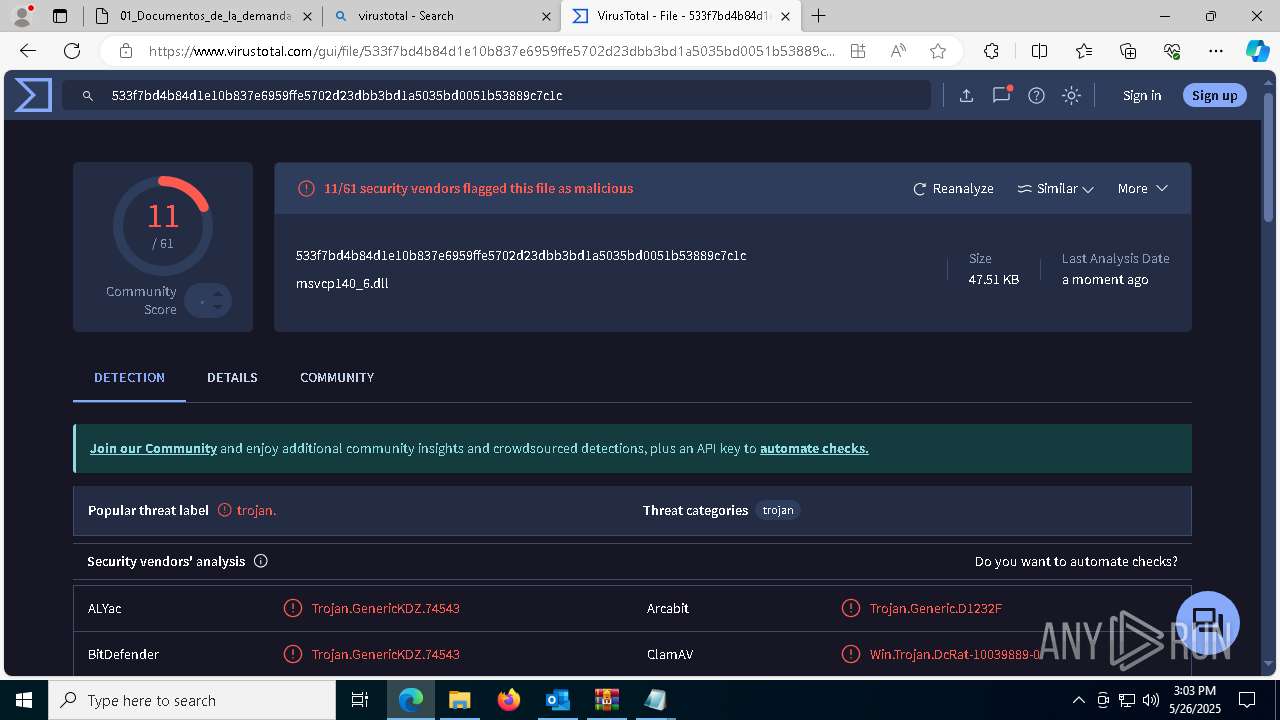
MALICIOUS
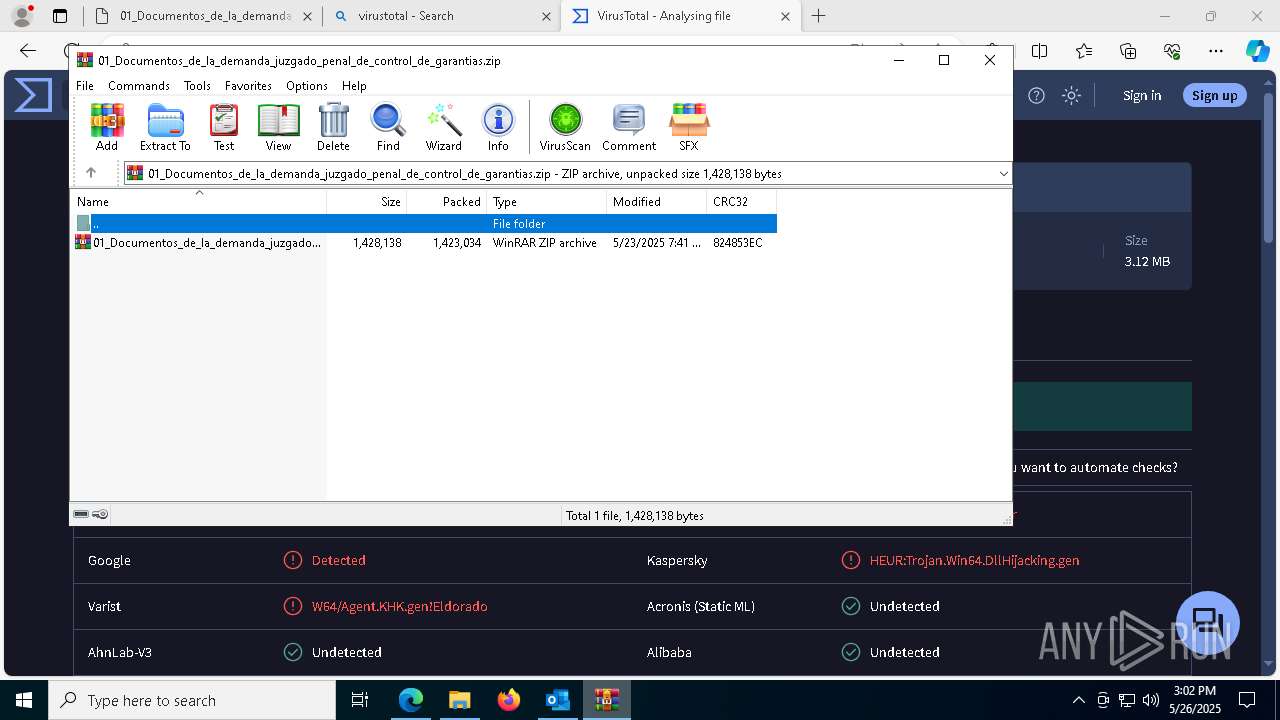
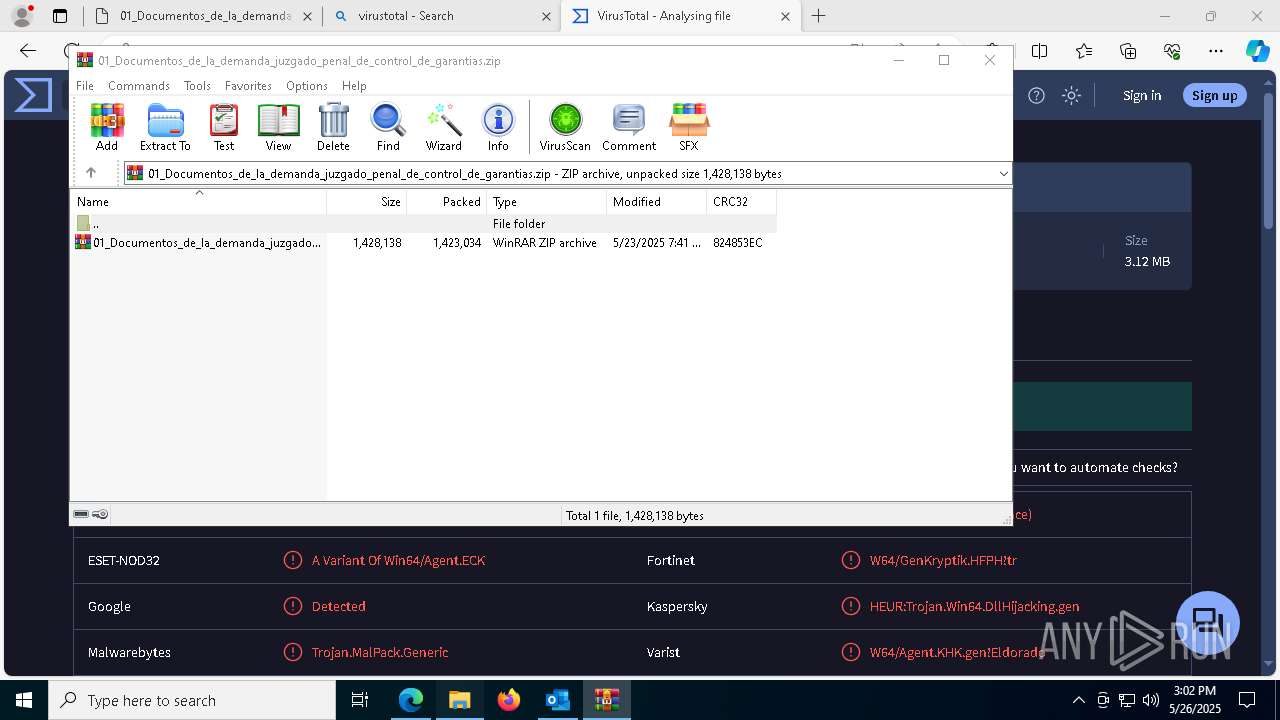
GENERIC has been found (auto)
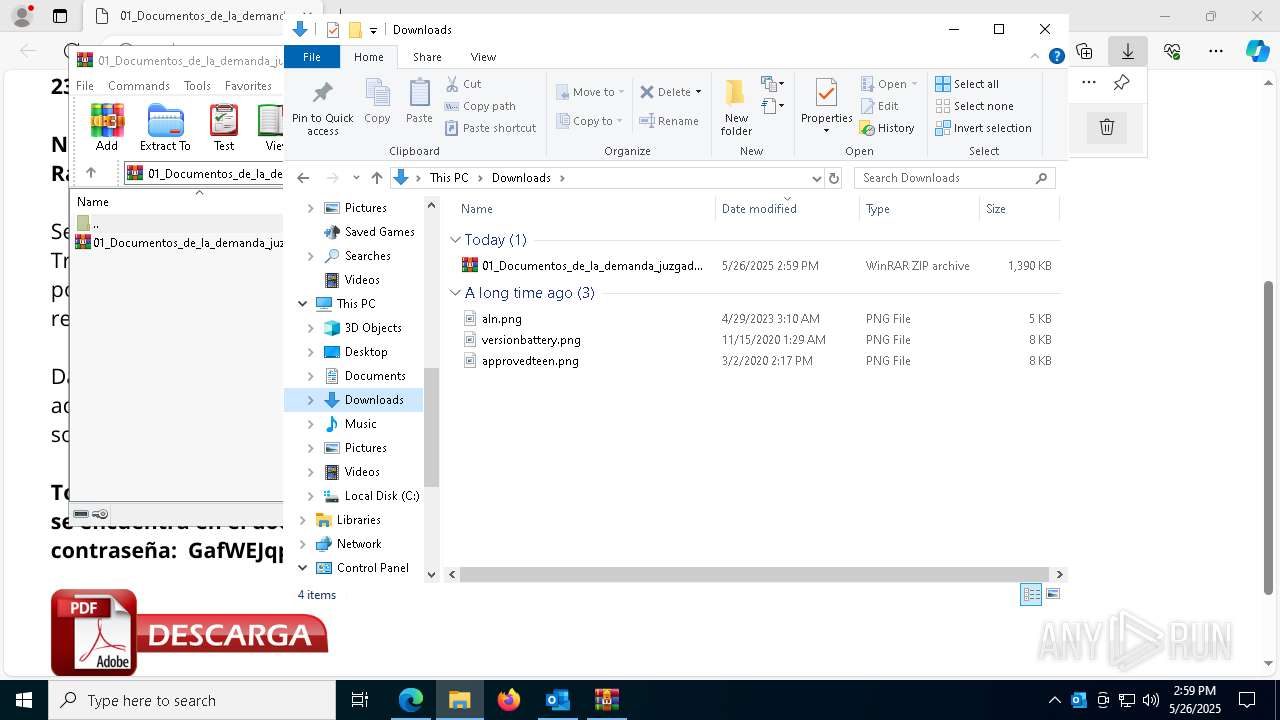
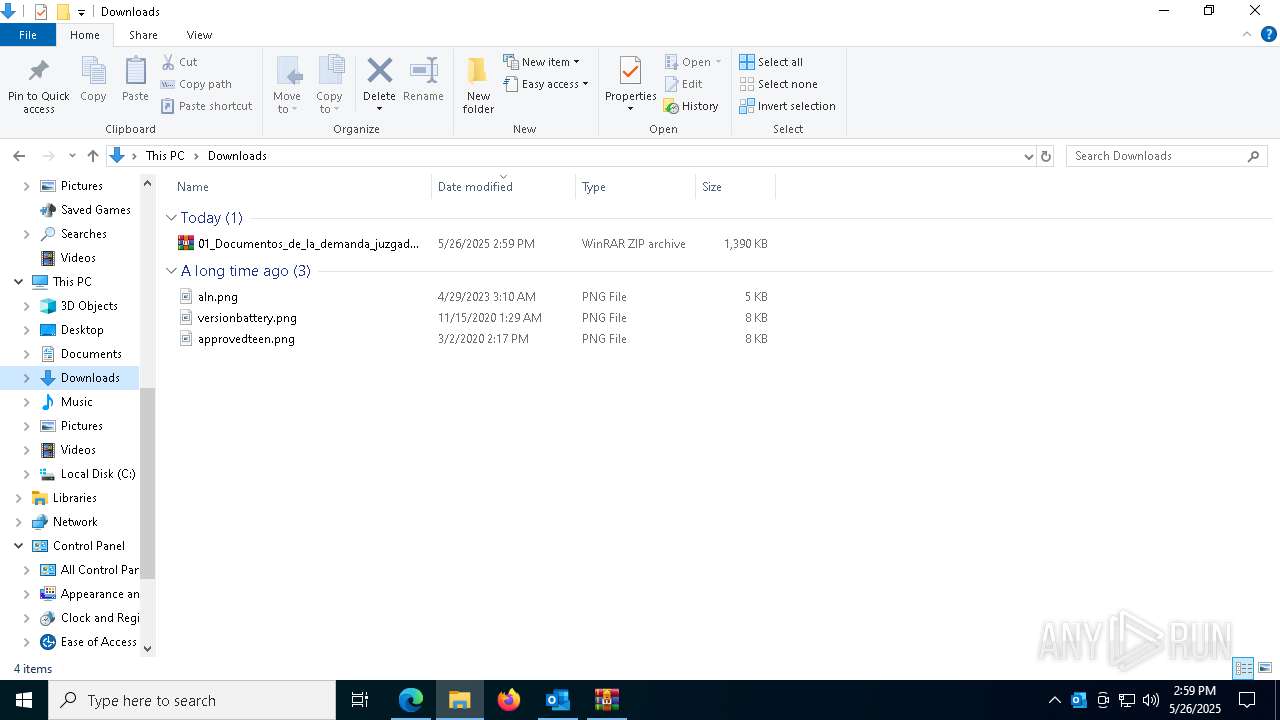
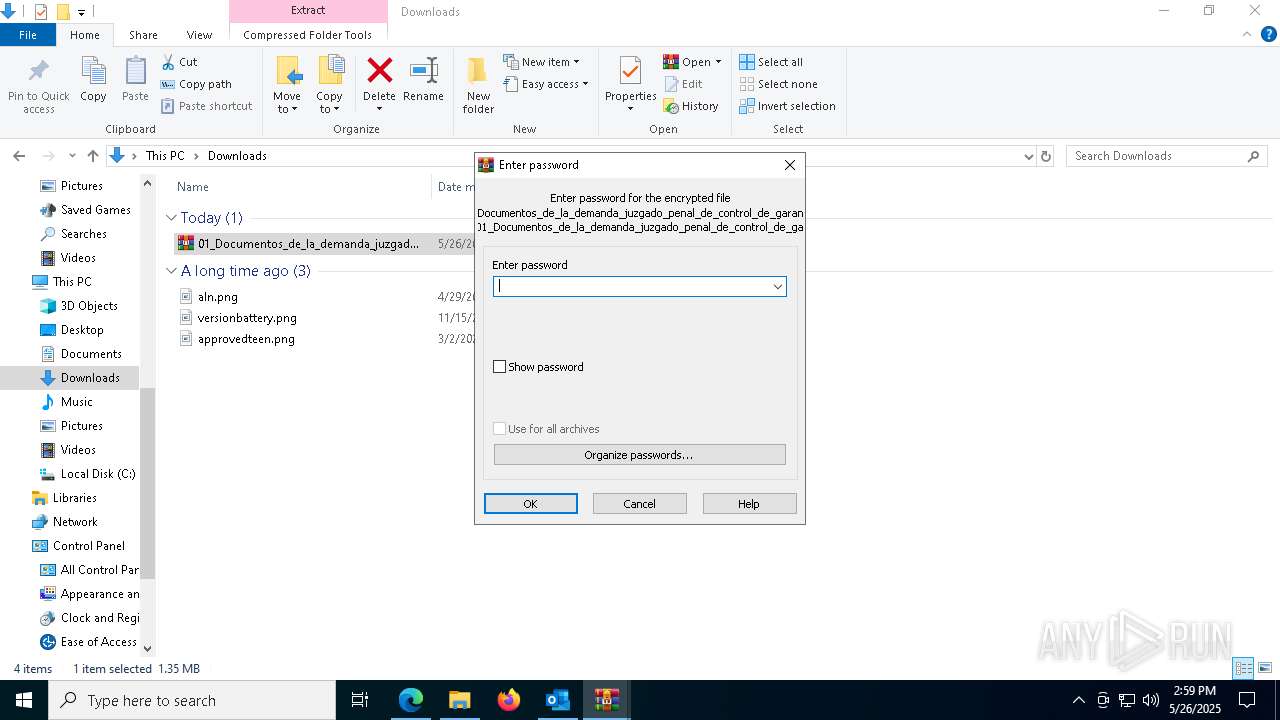
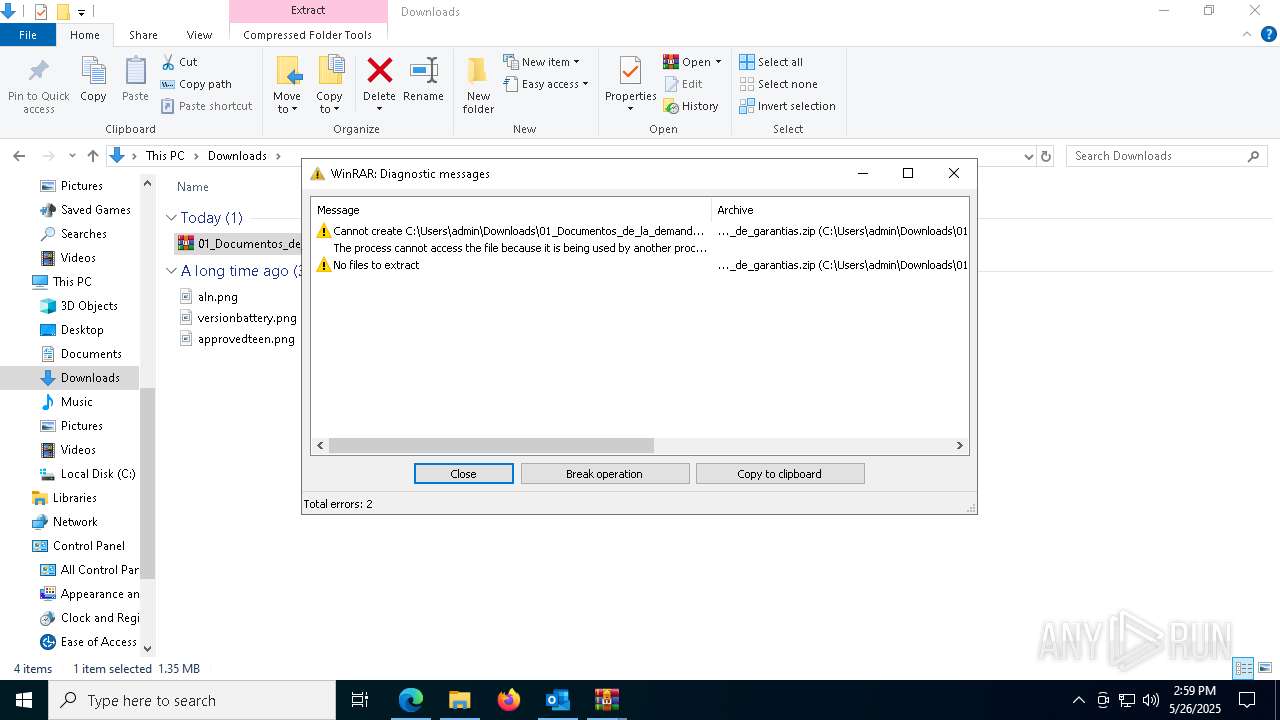
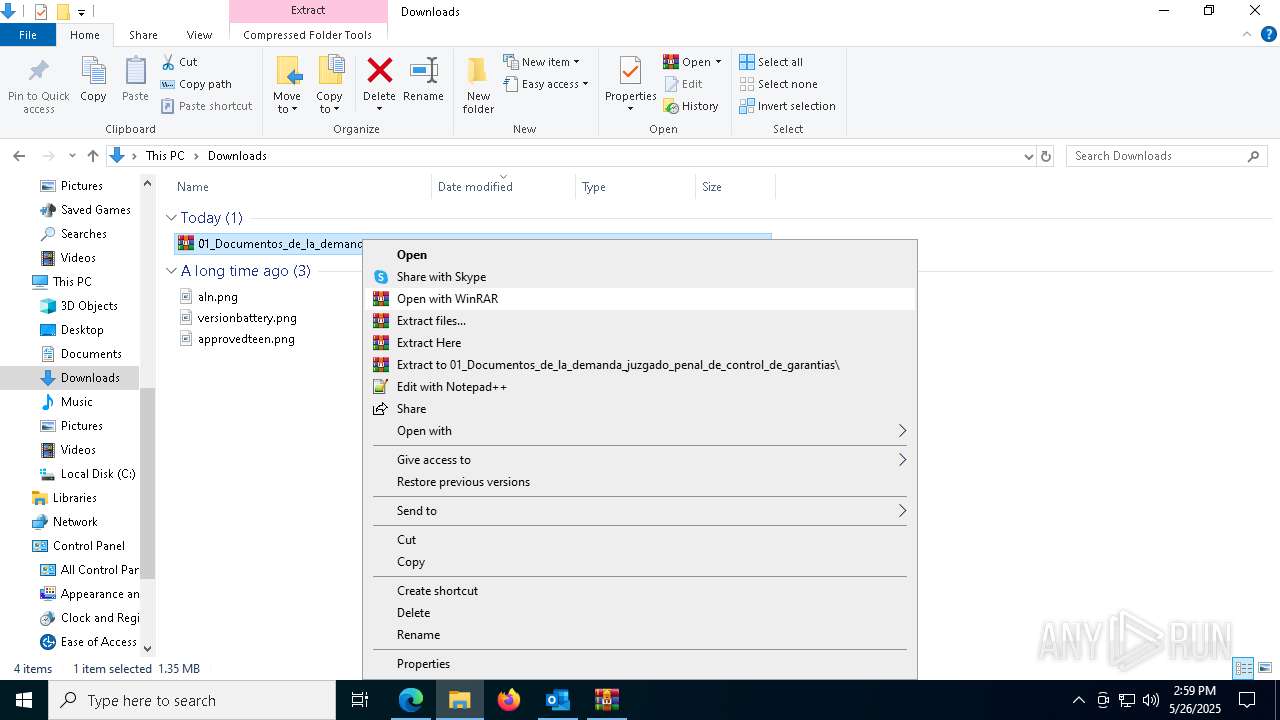
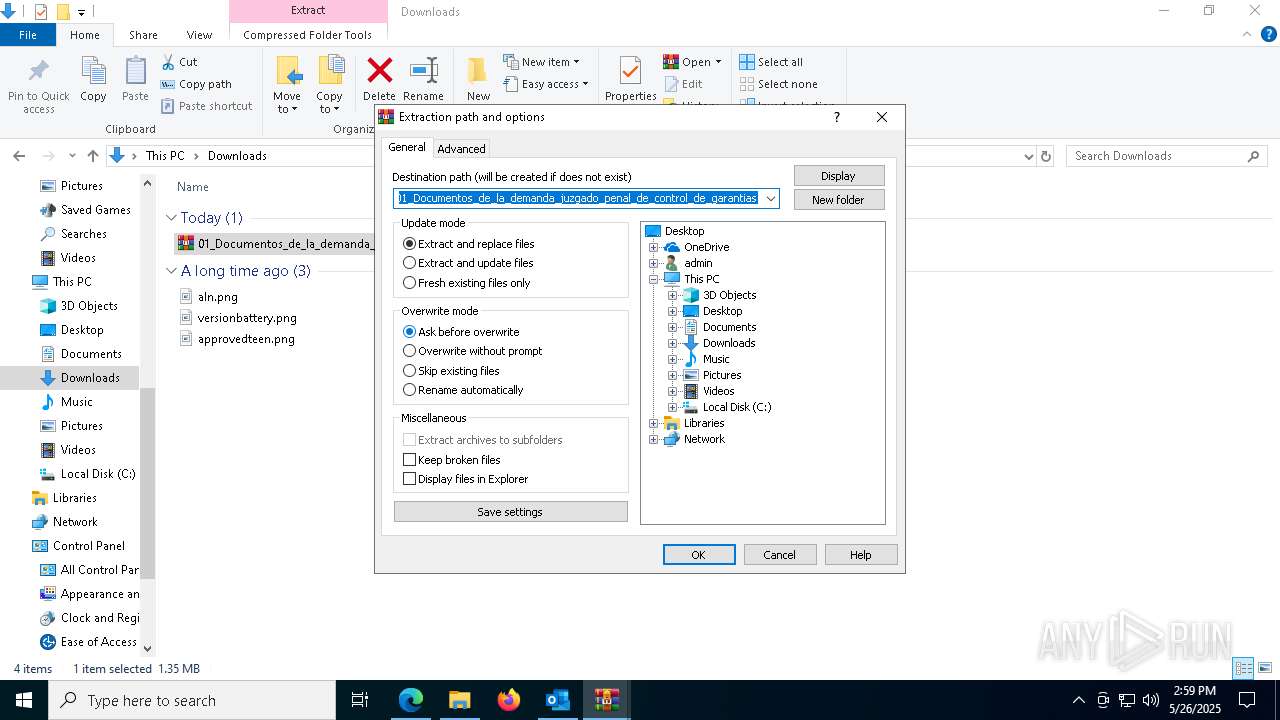
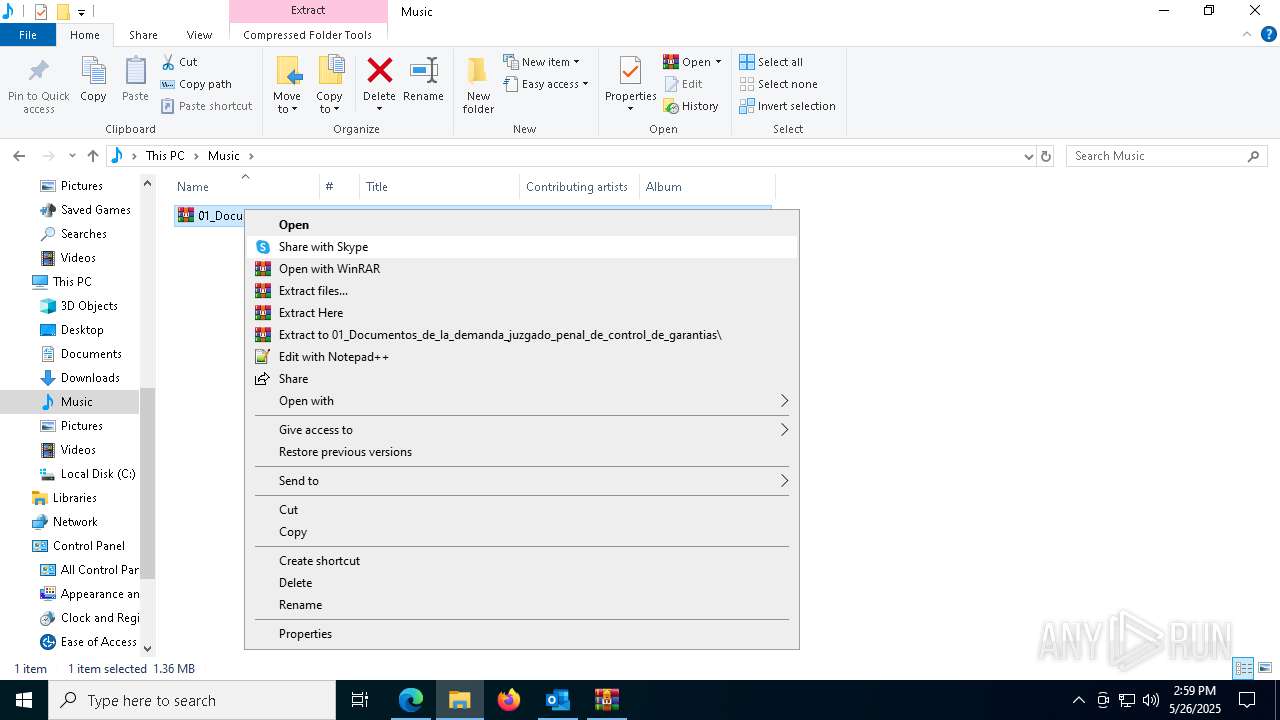
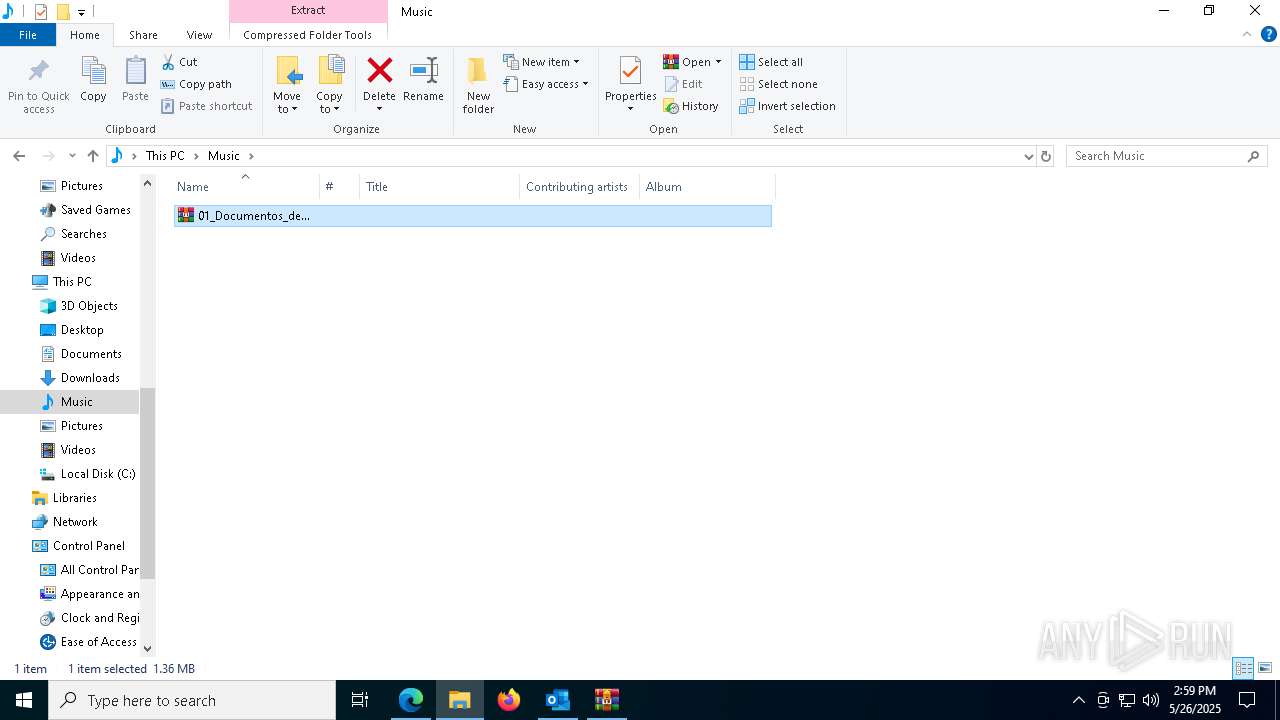
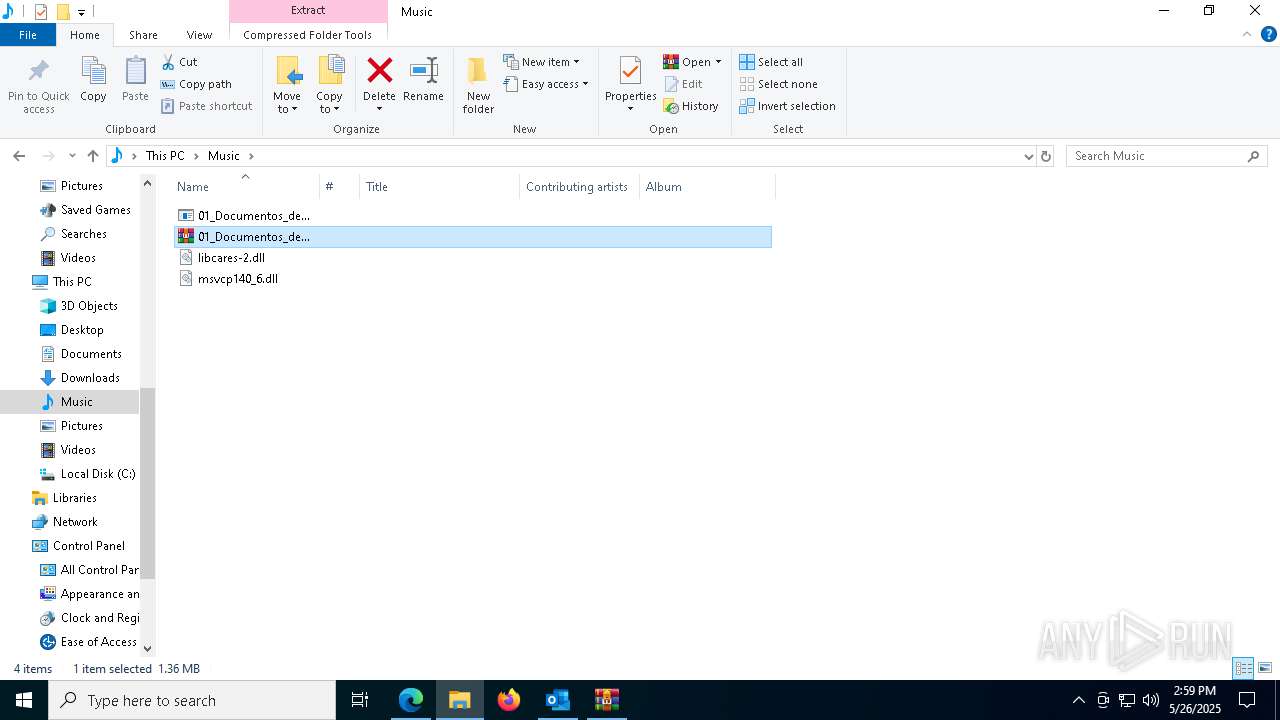
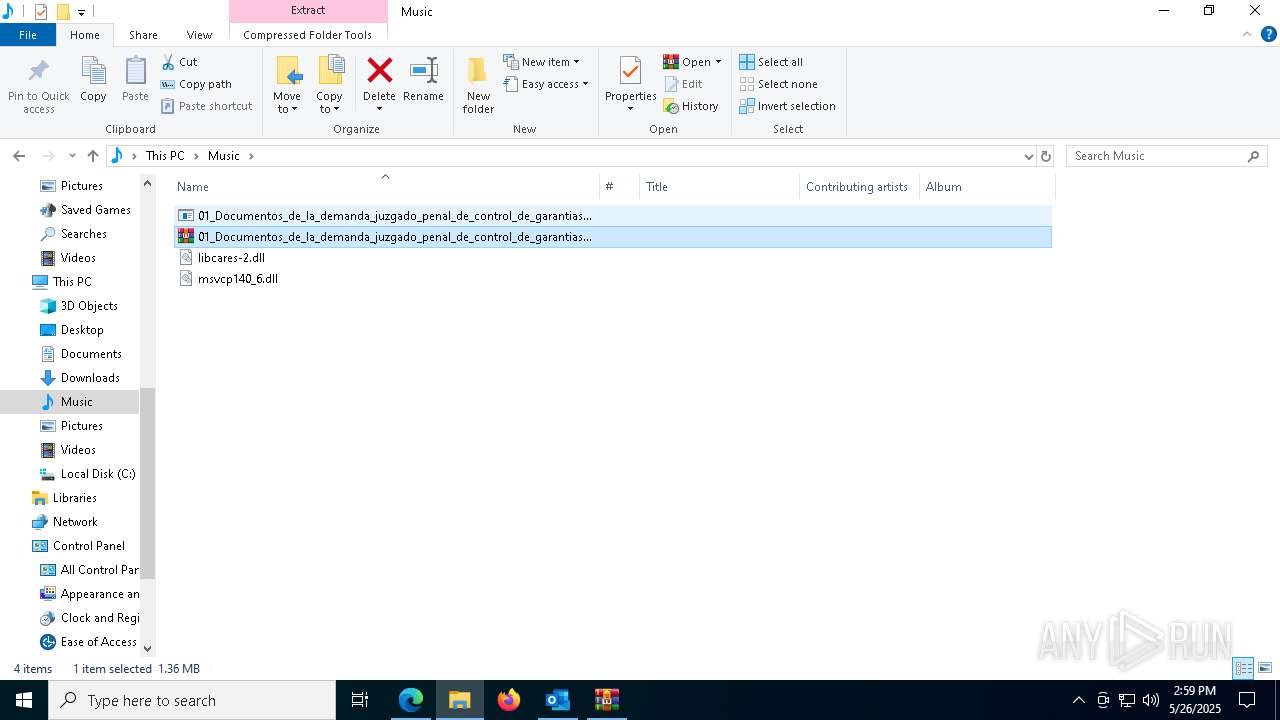
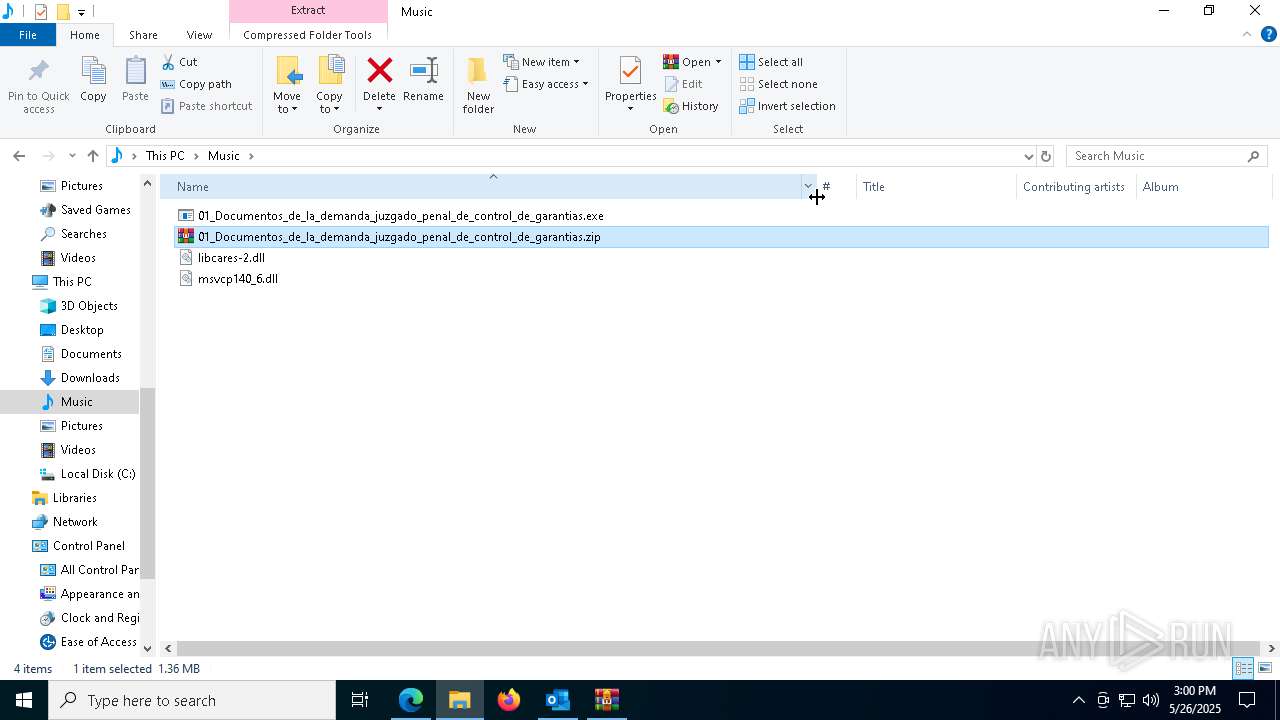
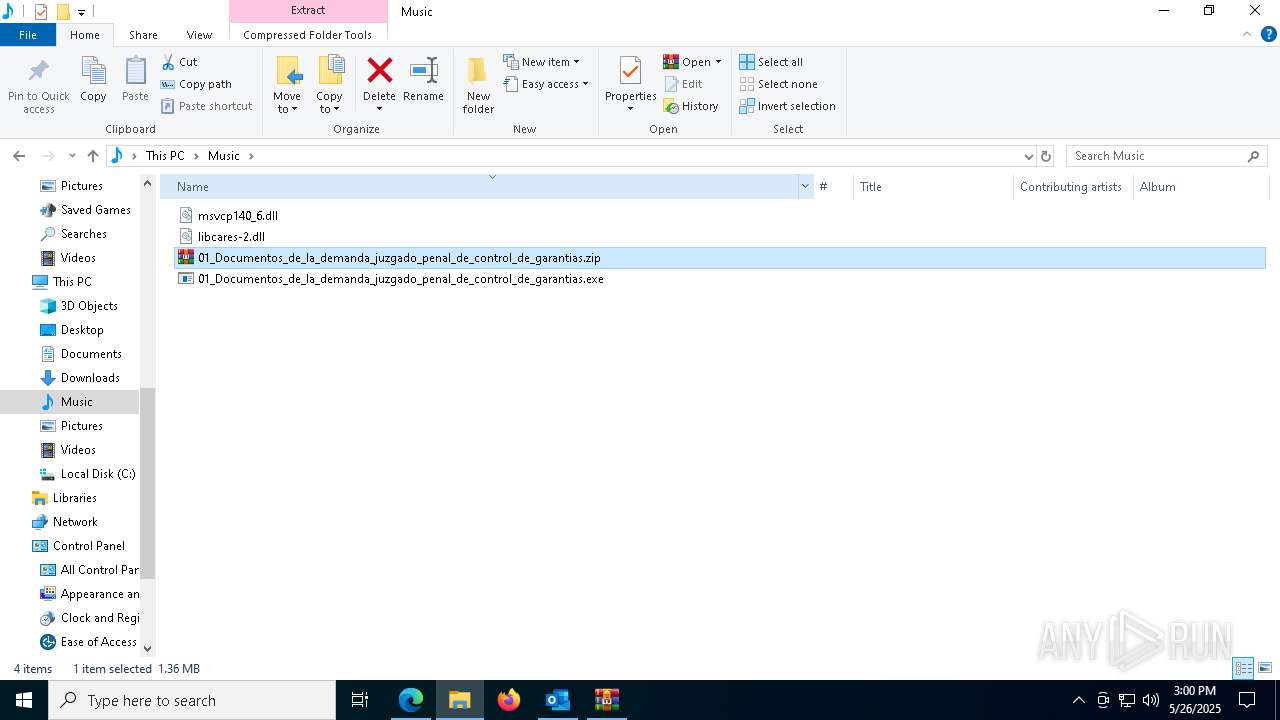
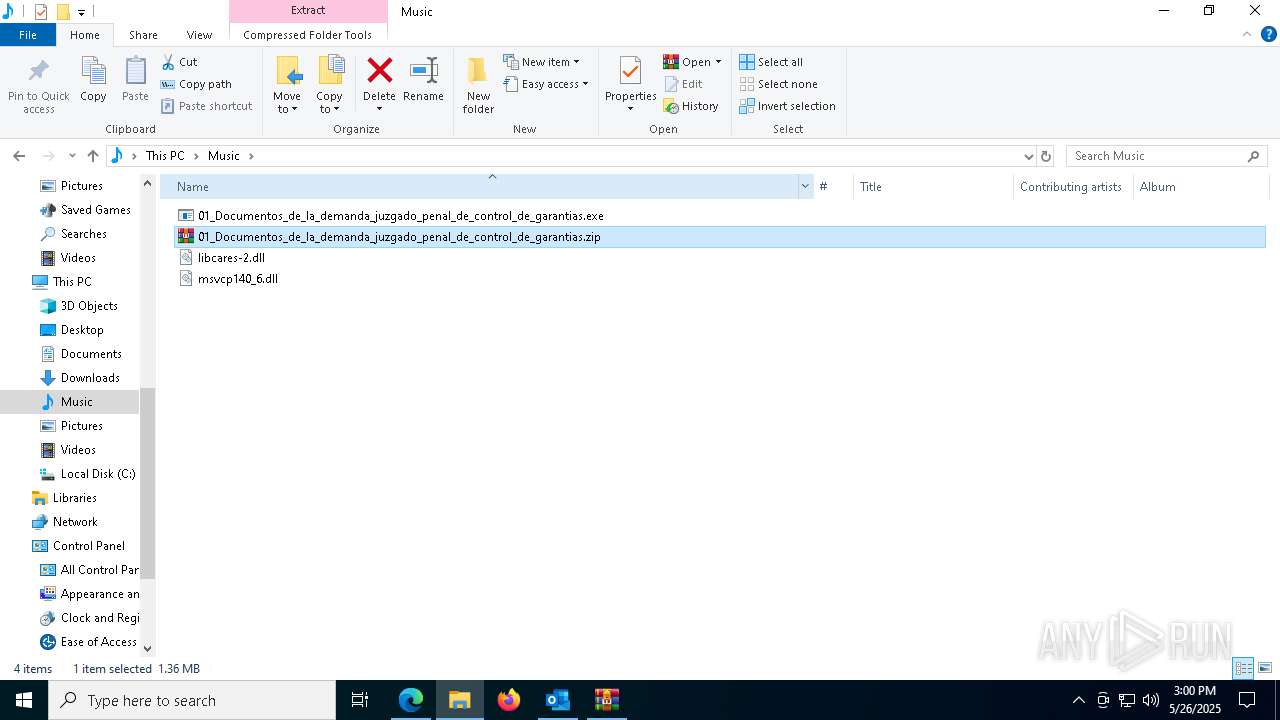
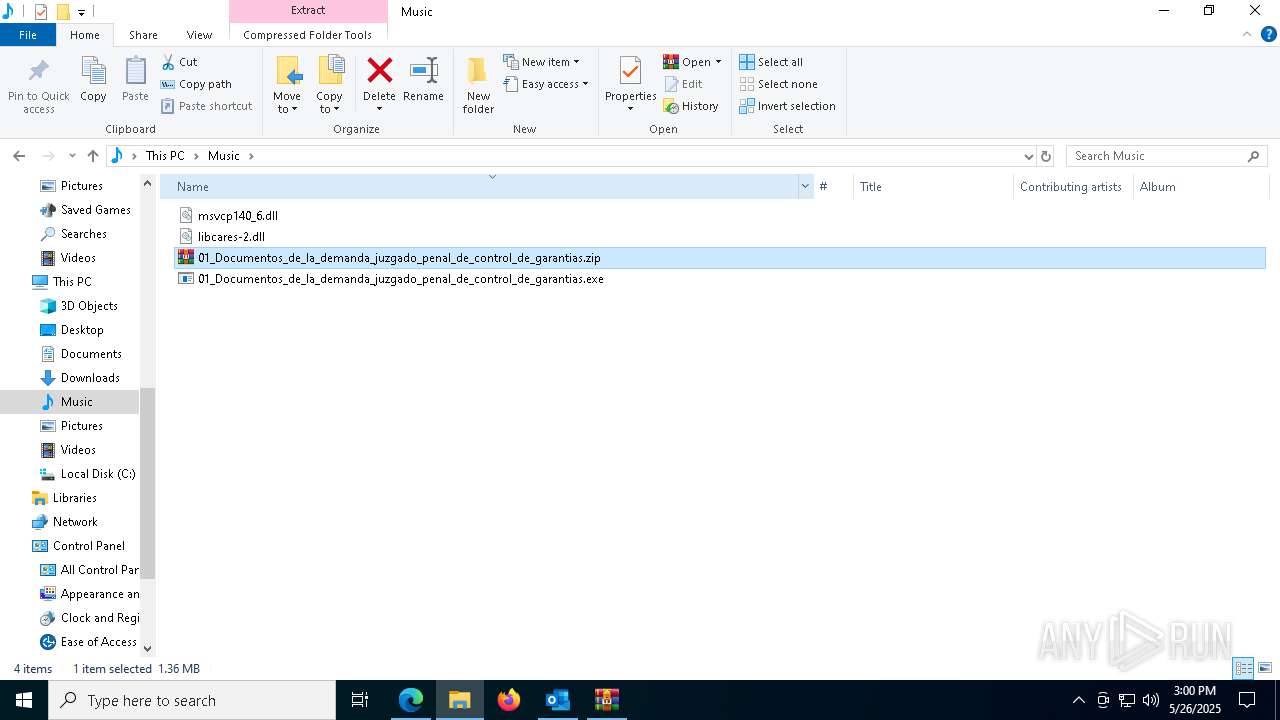
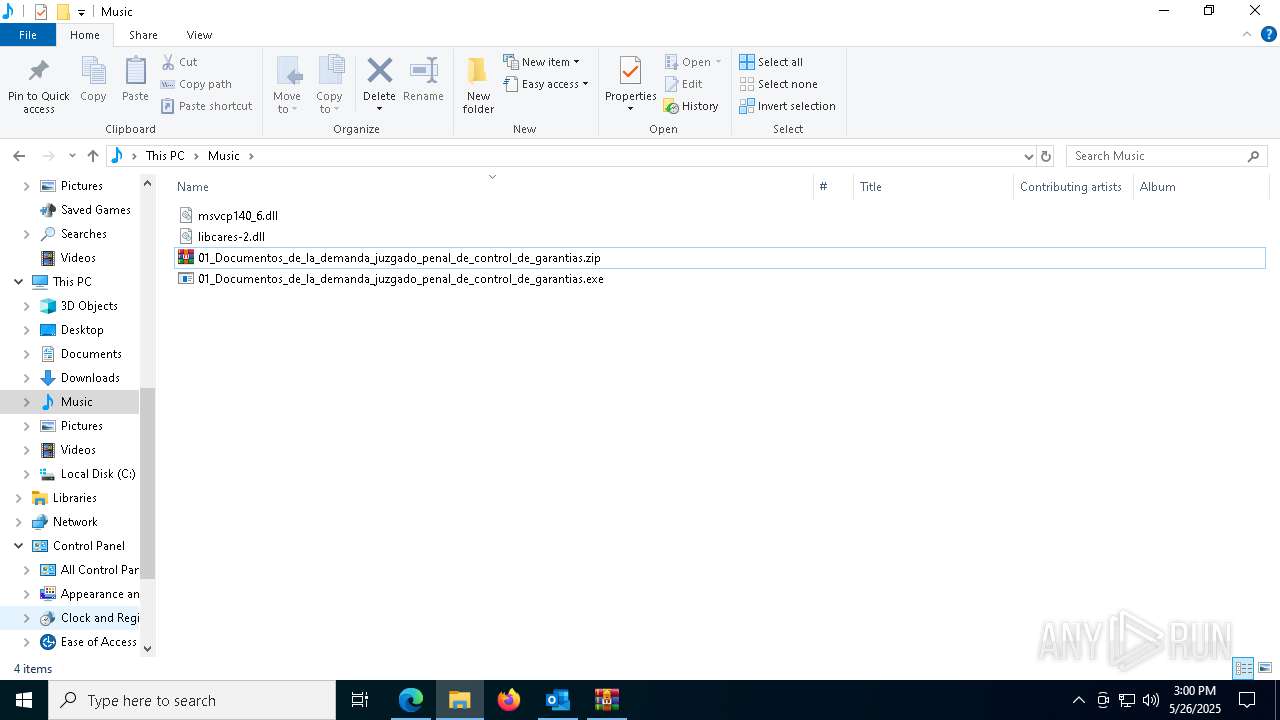
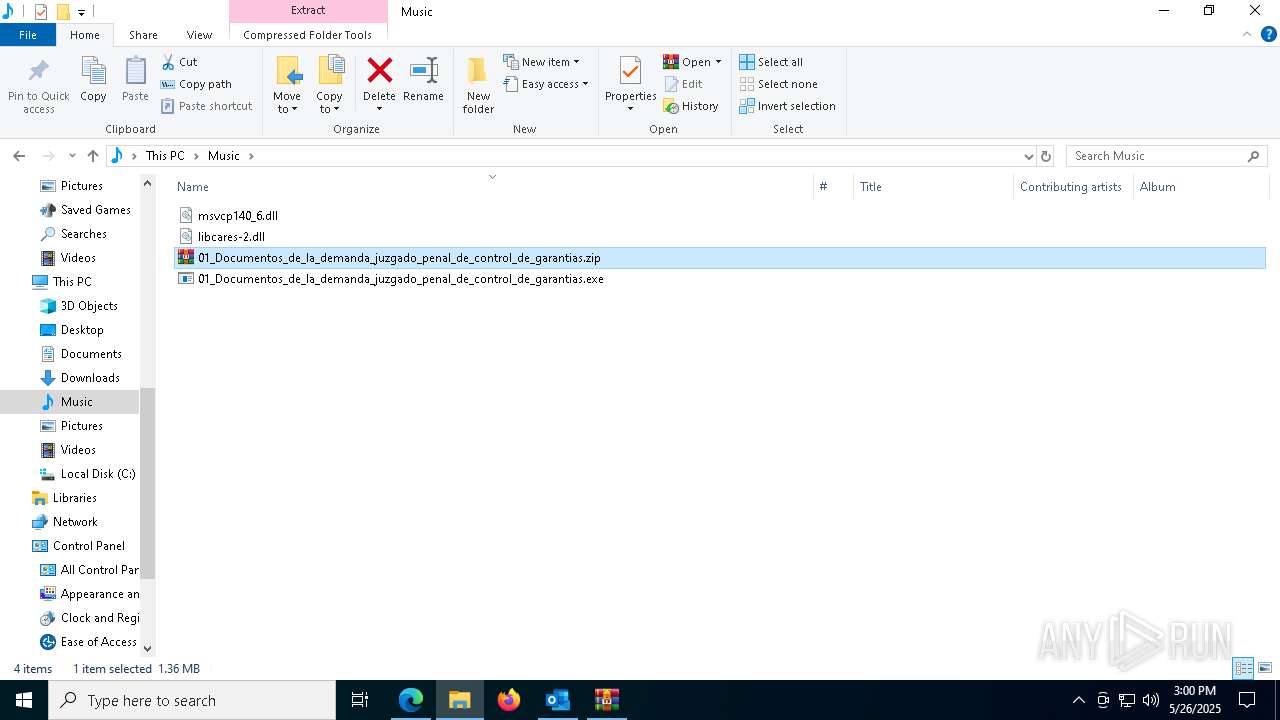
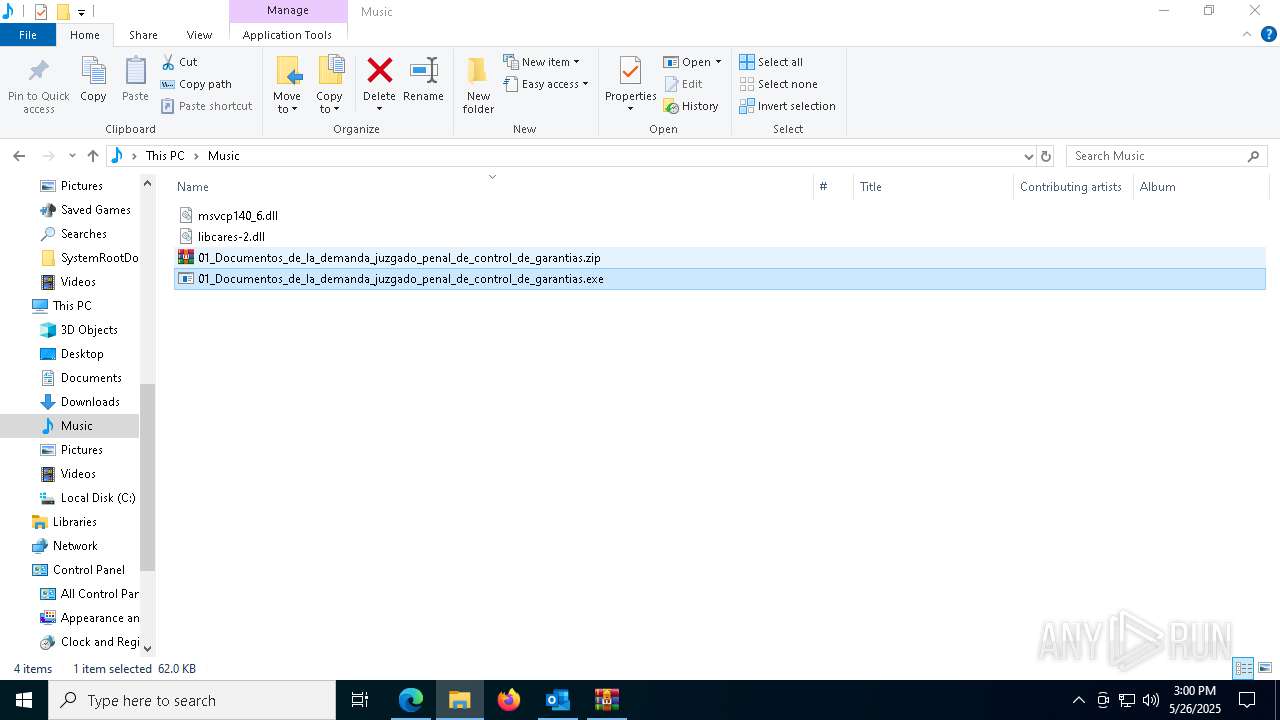
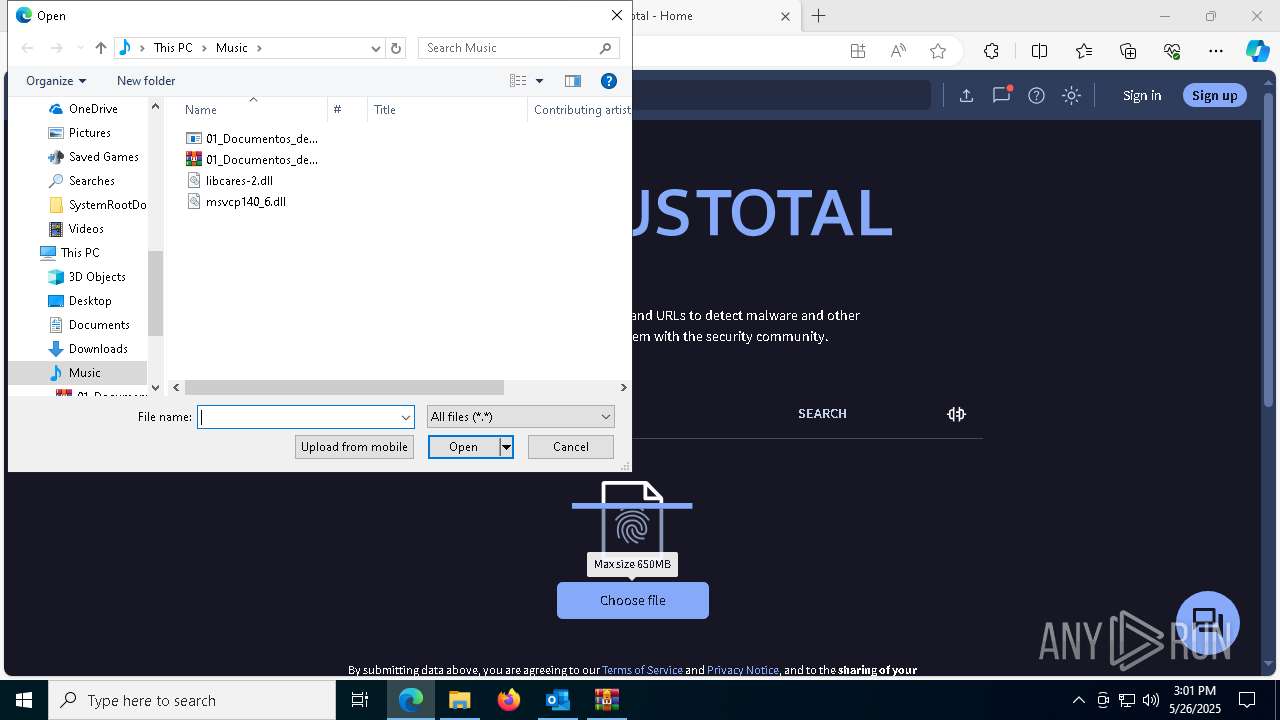
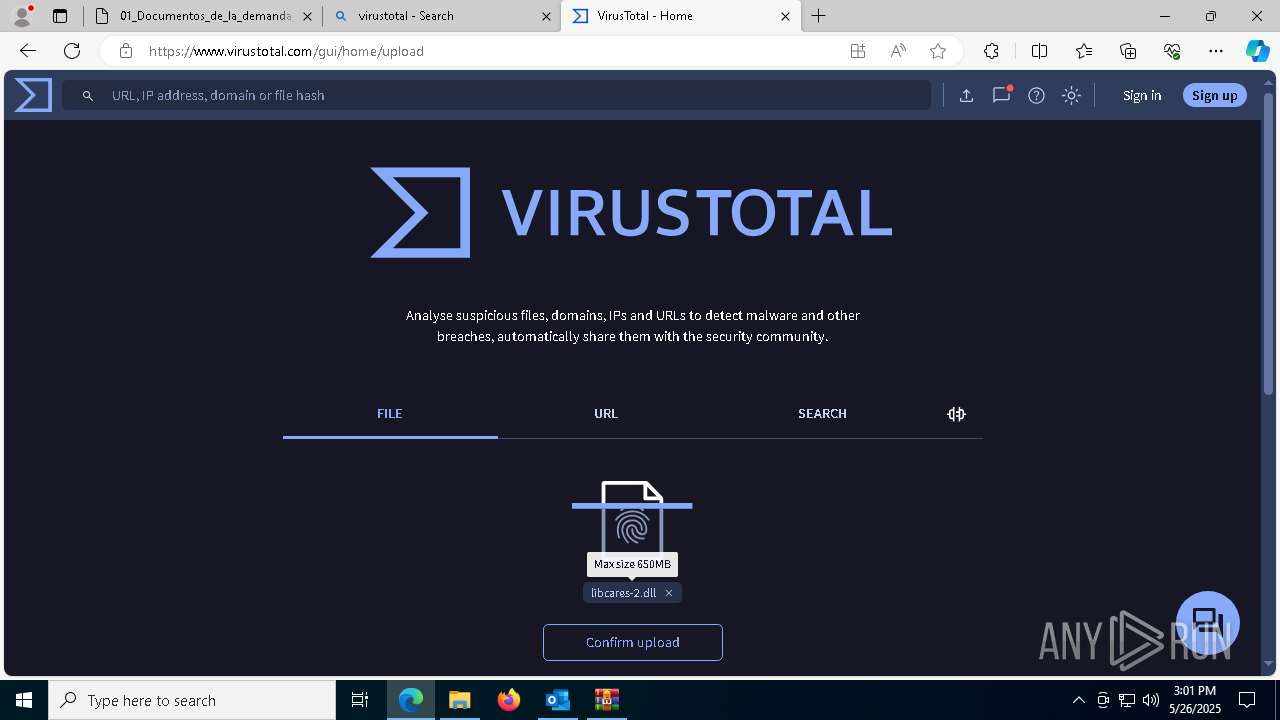
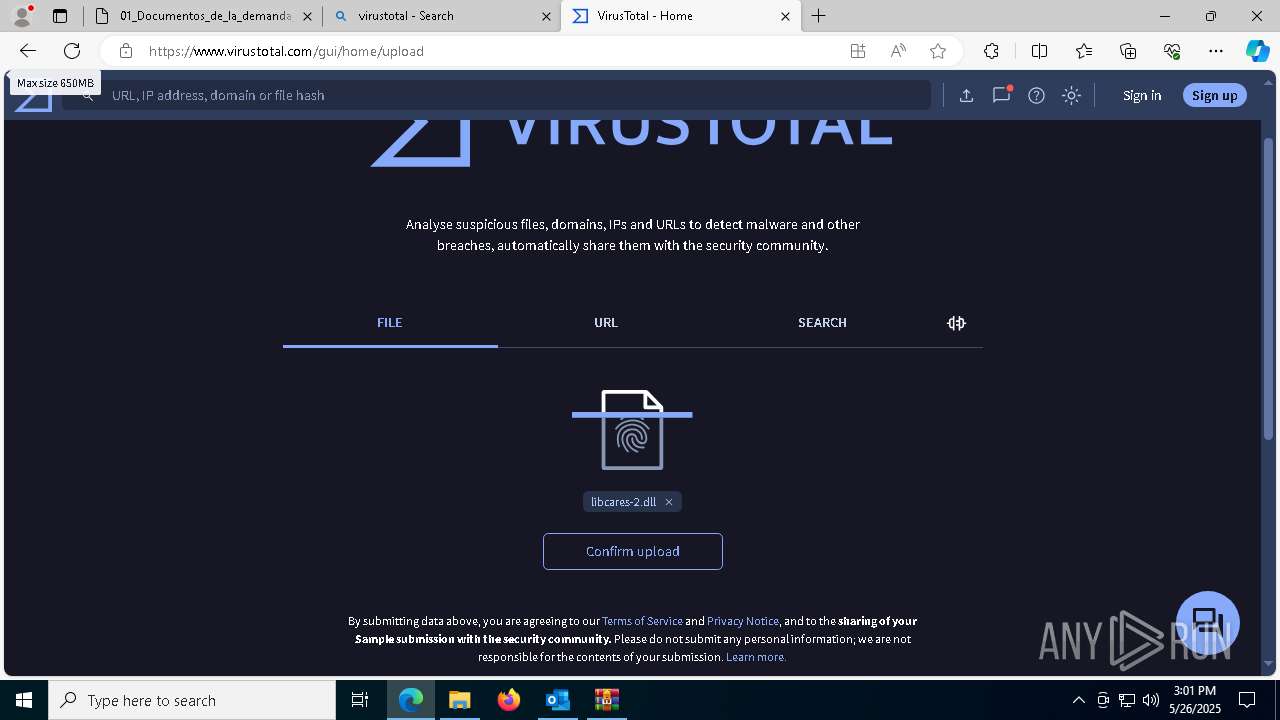
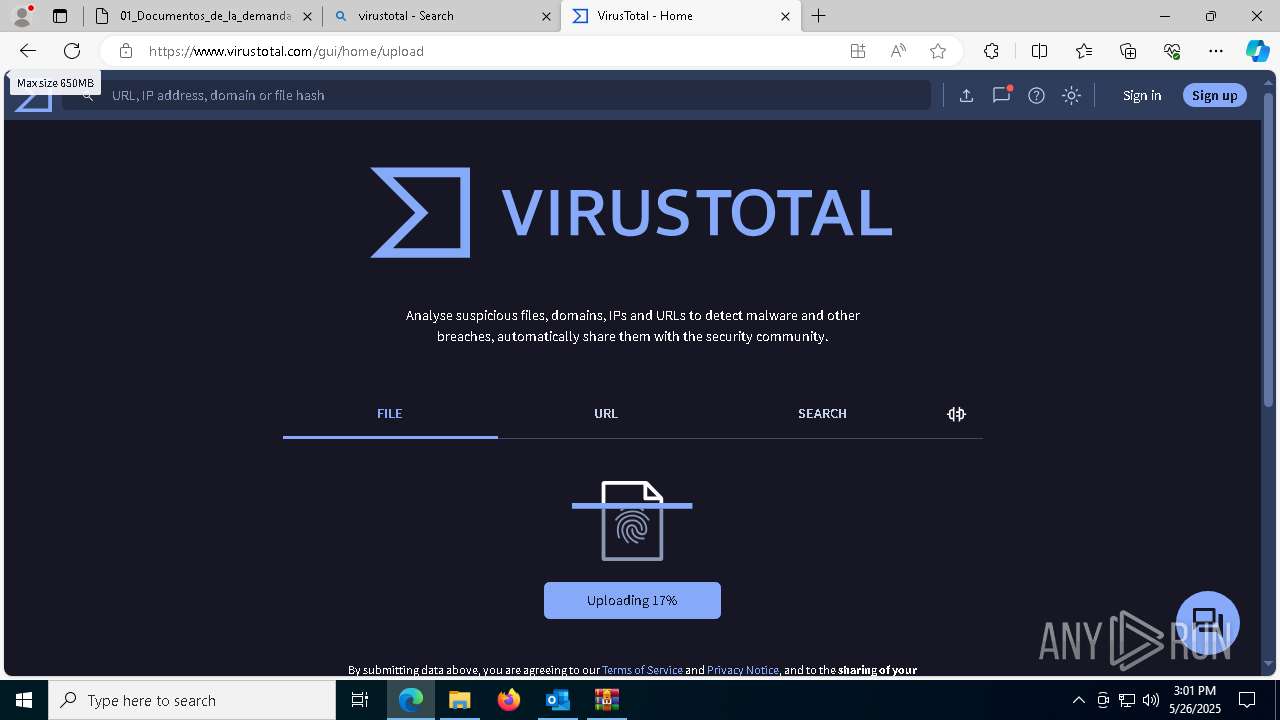
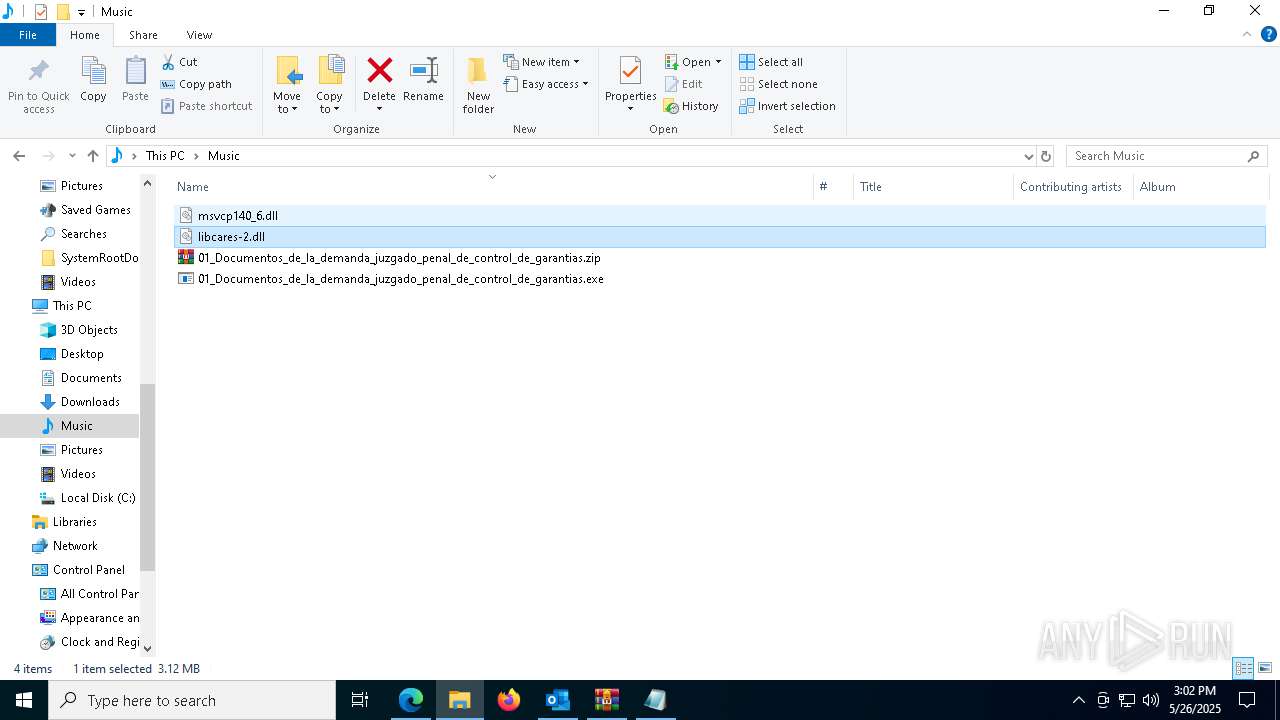
- WinRAR.exe (PID: 6668)
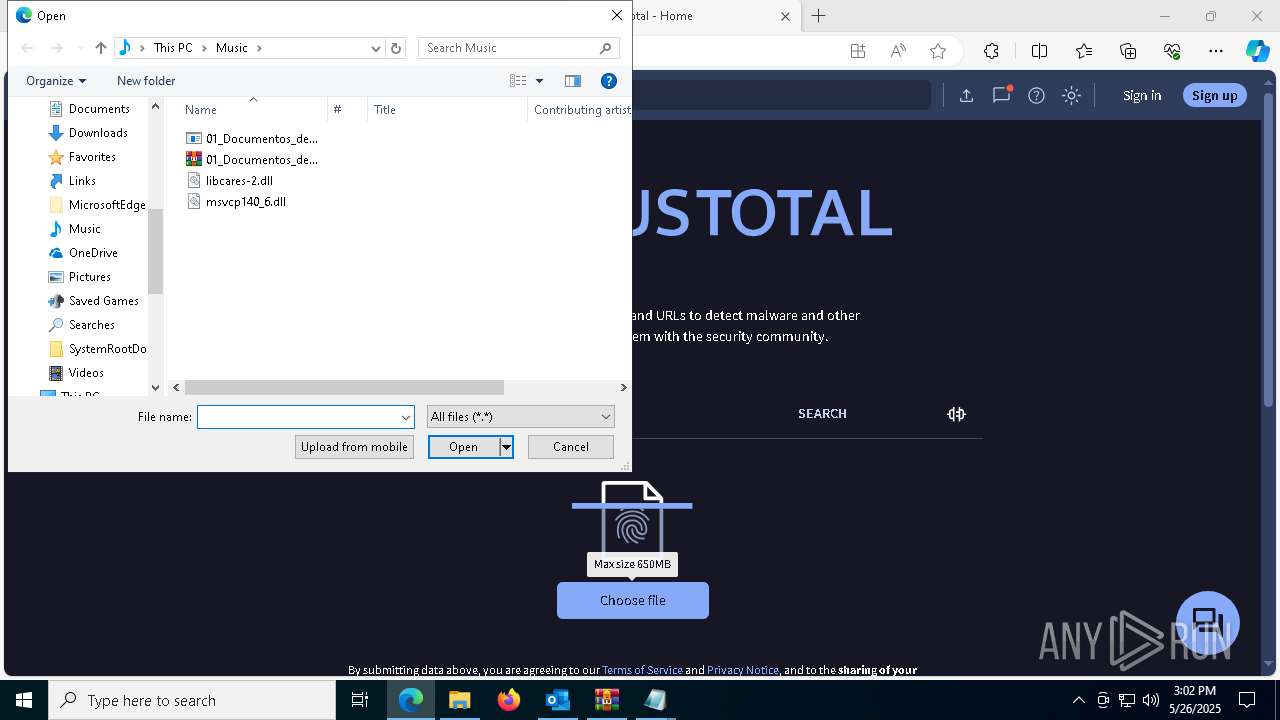
- 01_Documentos_de_la_demanda_juzgado_penal_de_control_de_garantias.exe (PID: 1128)
- WinRAR.exe (PID: 2340)
ASYNCRAT has been detected (SURICATA)
- AddInProcess32.exe (PID: 6712)
ASYNCRAT has been detected (YARA)
- AddInProcess32.exe (PID: 6712)
SUSPICIOUS
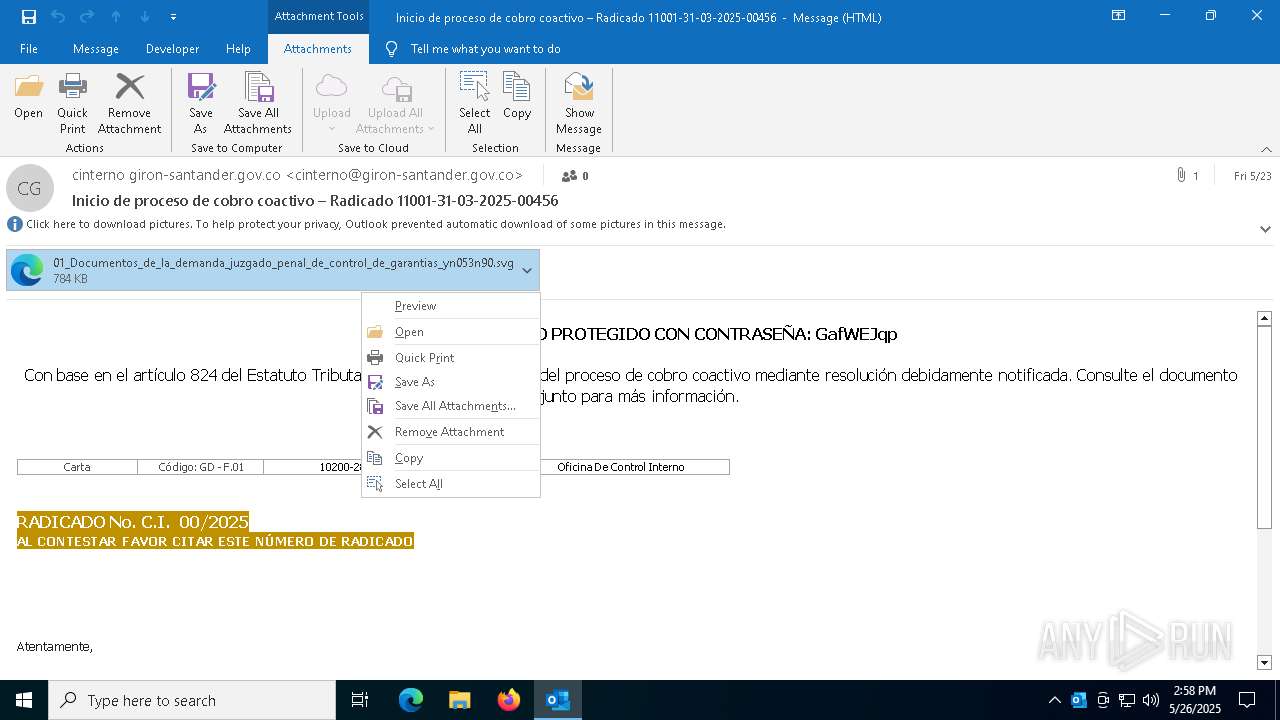
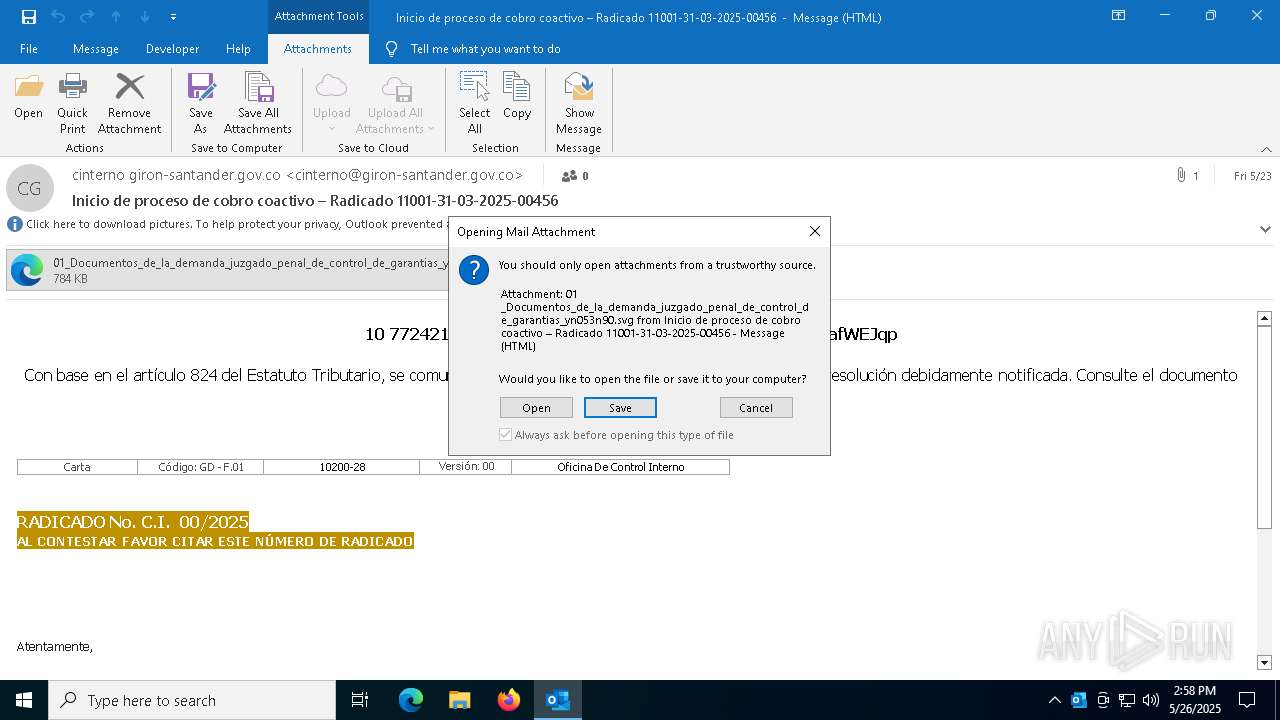
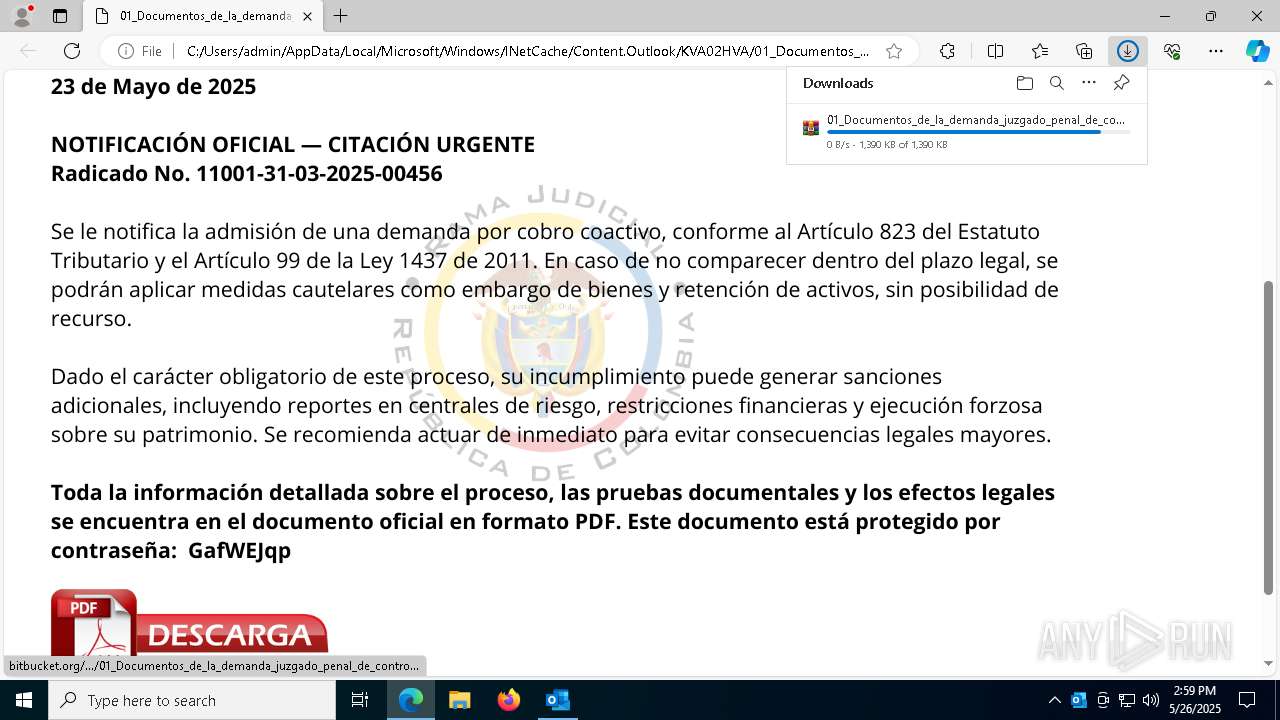
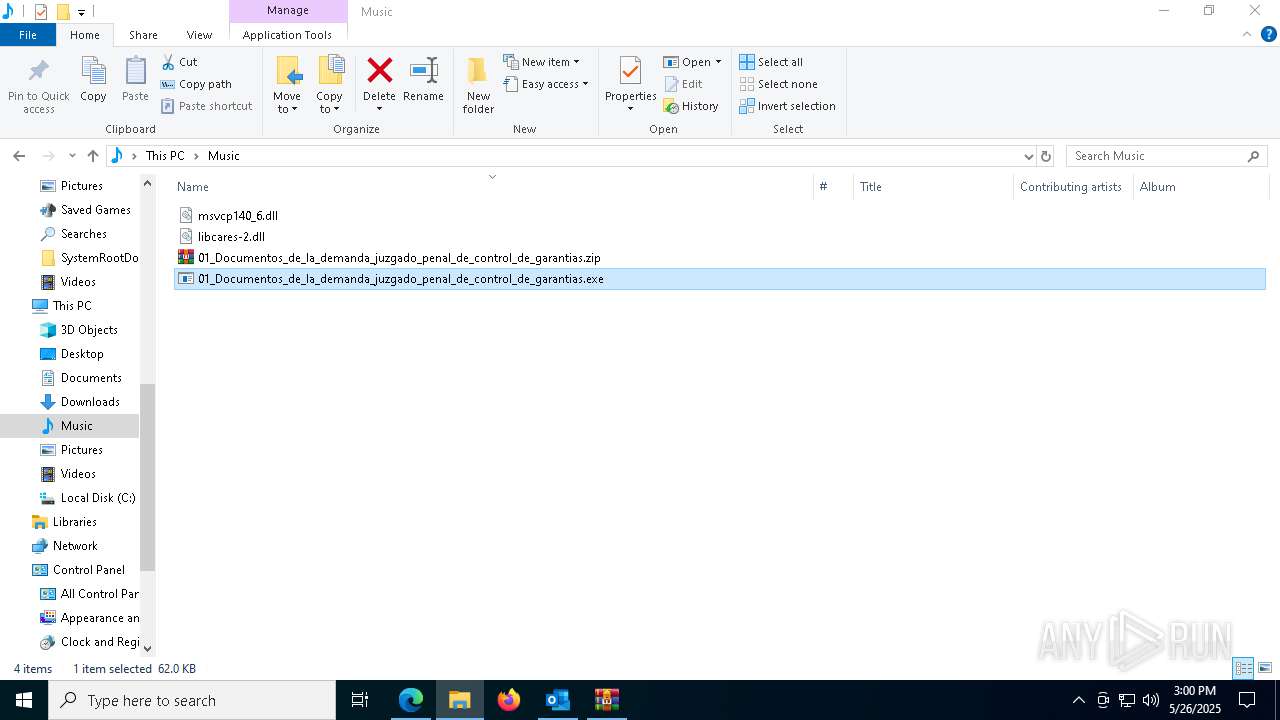
Email with suspicious attachment
- OUTLOOK.EXE (PID: 1196)
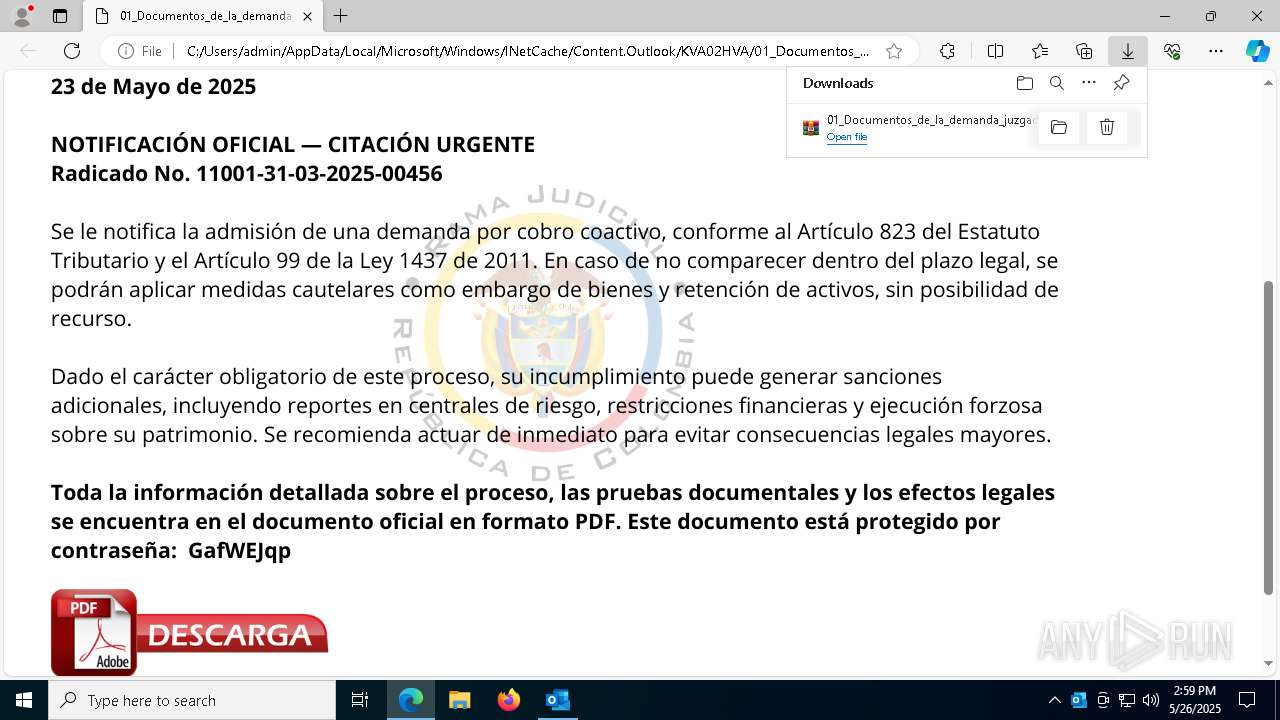
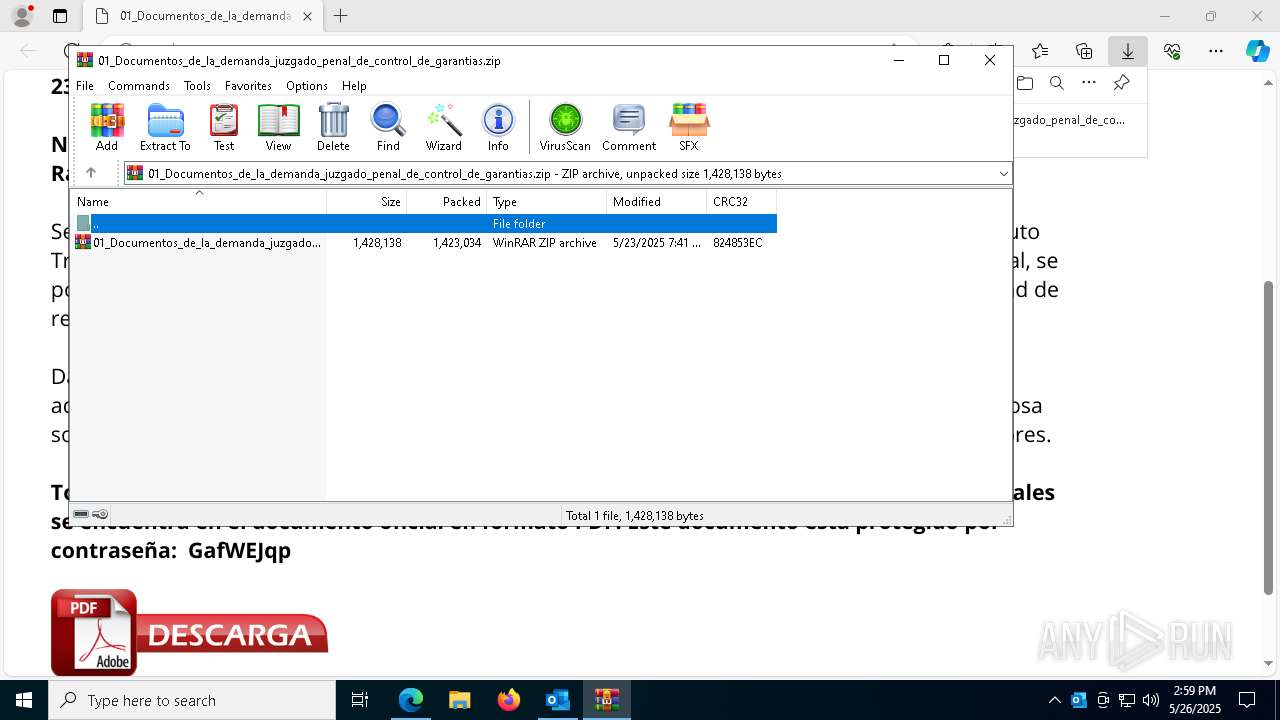
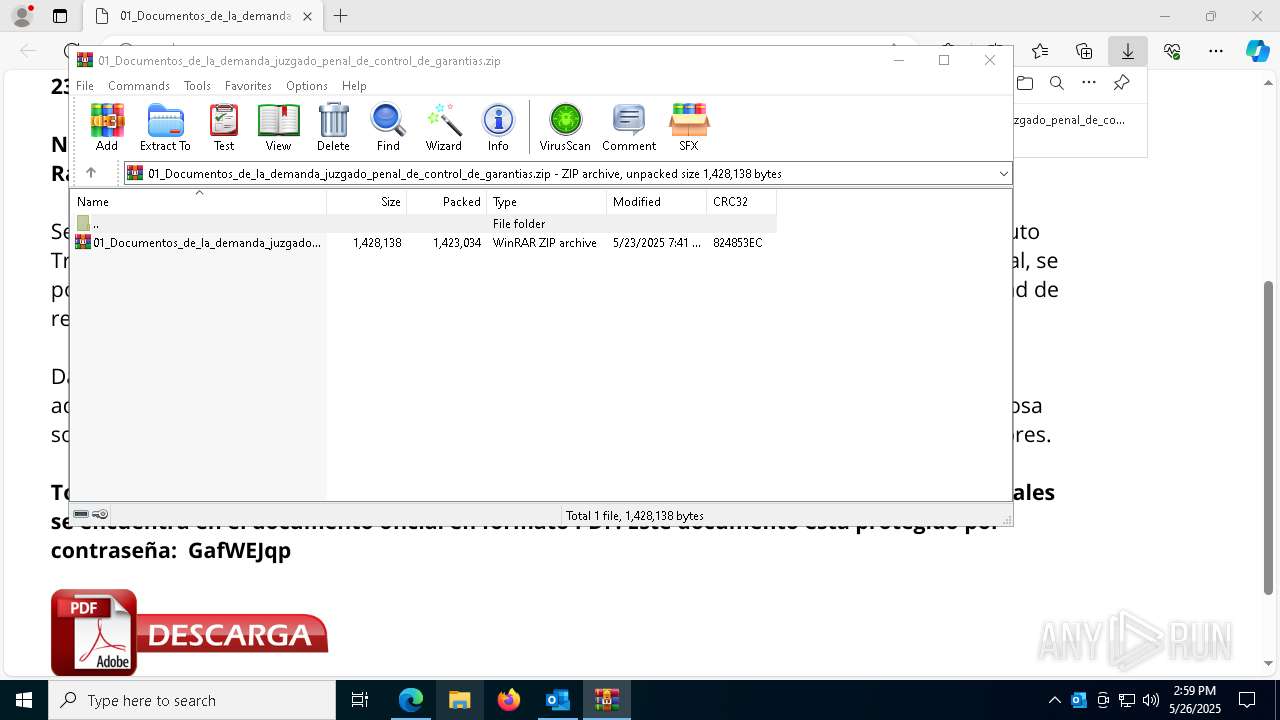
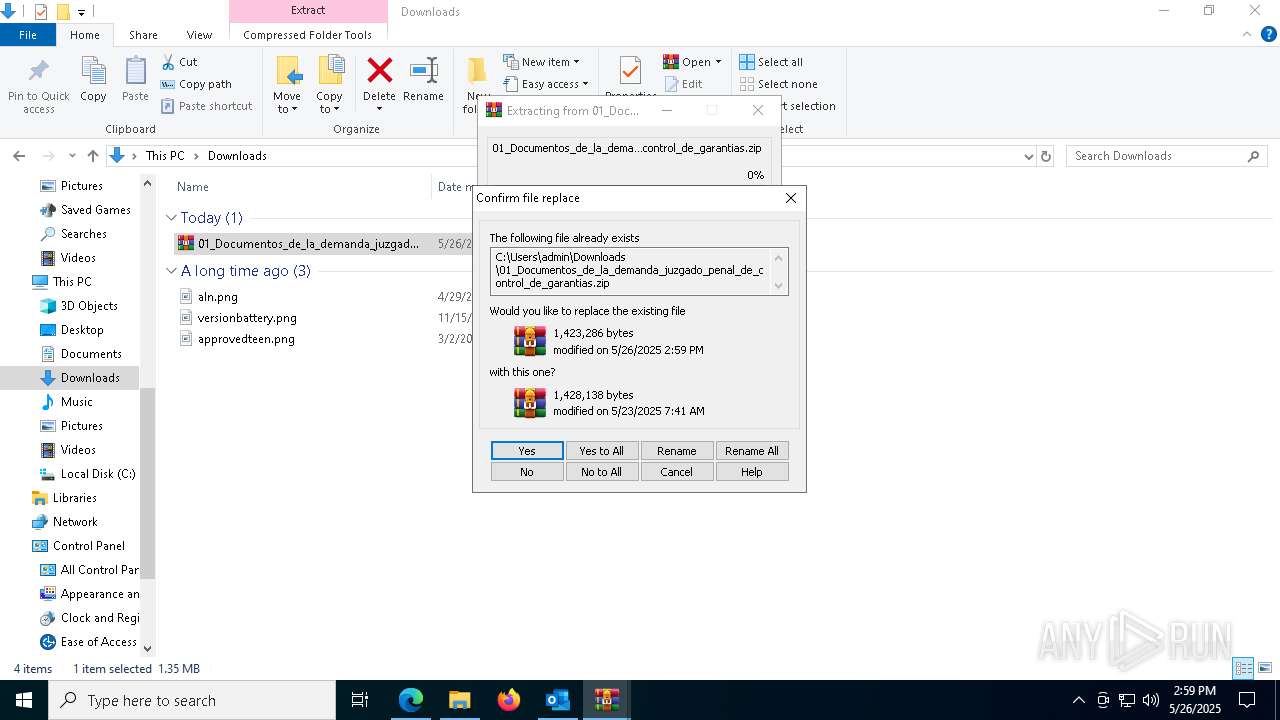
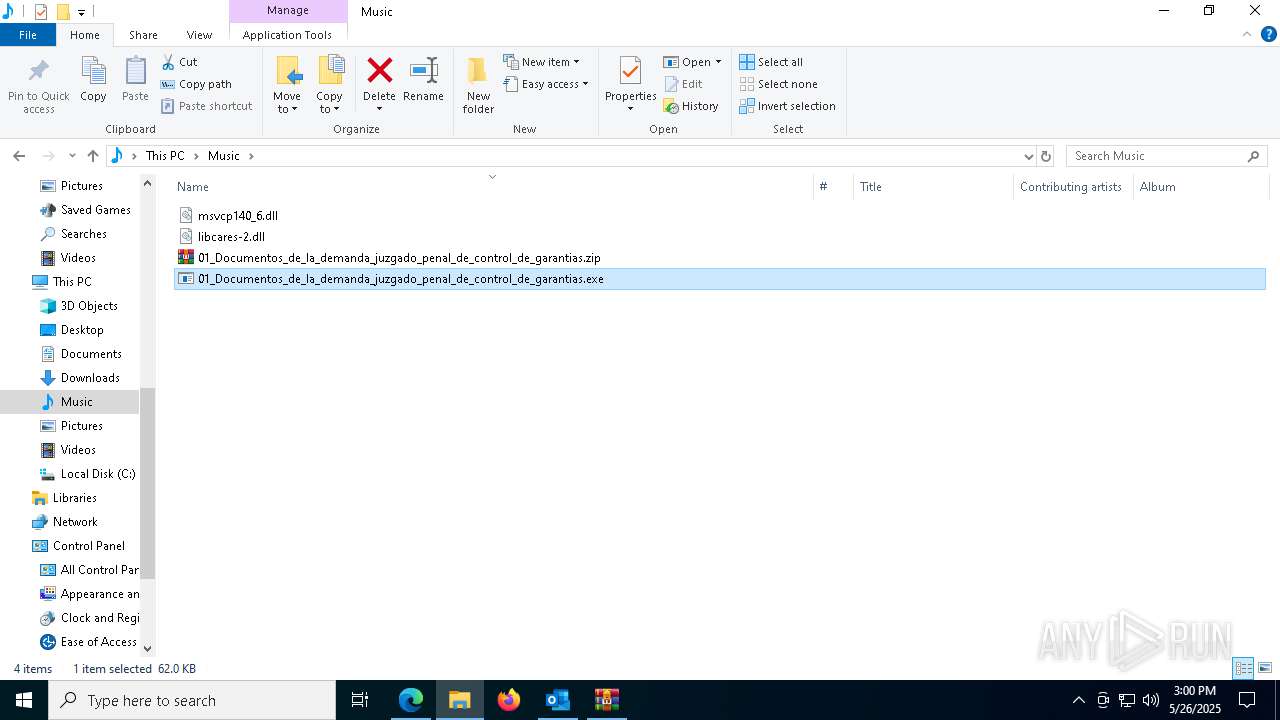
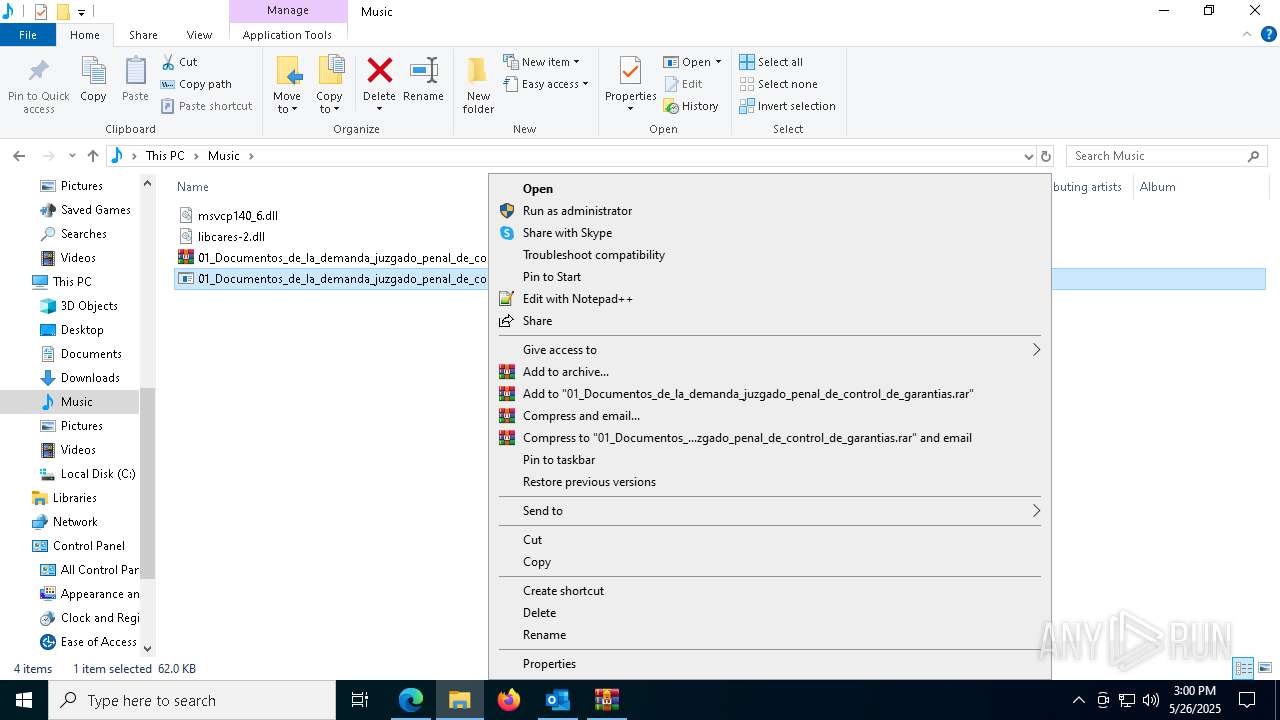
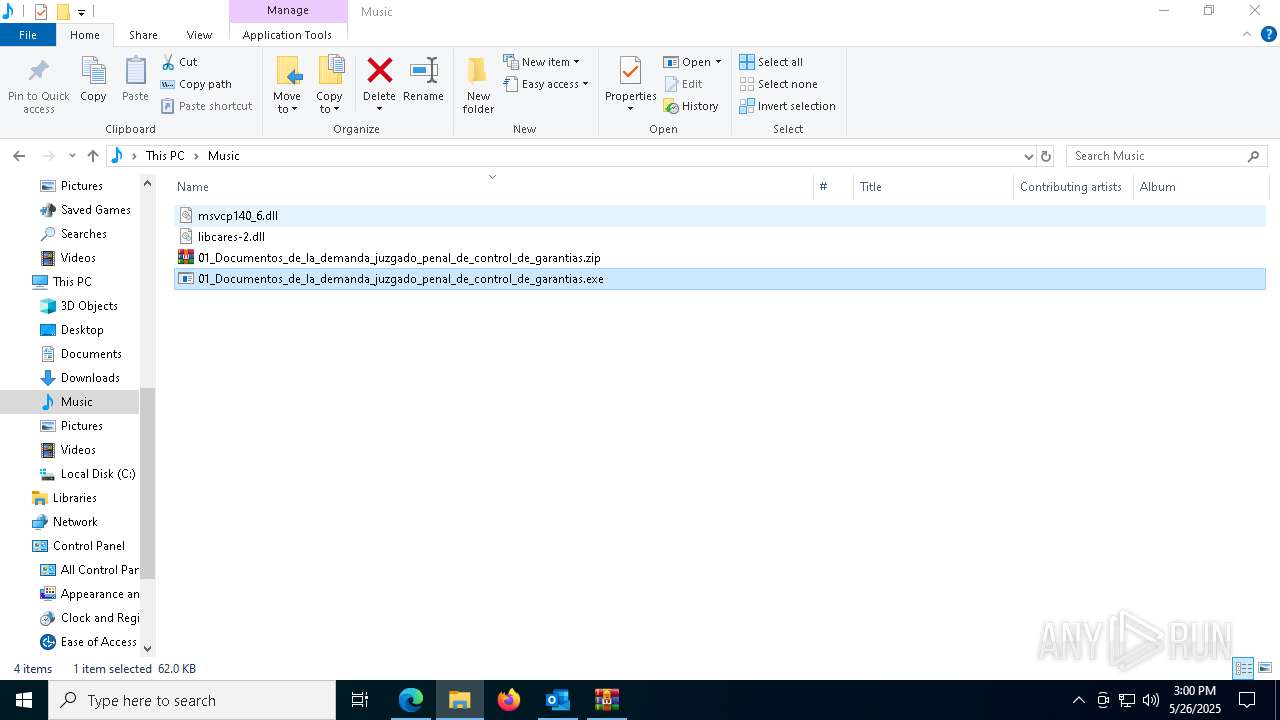
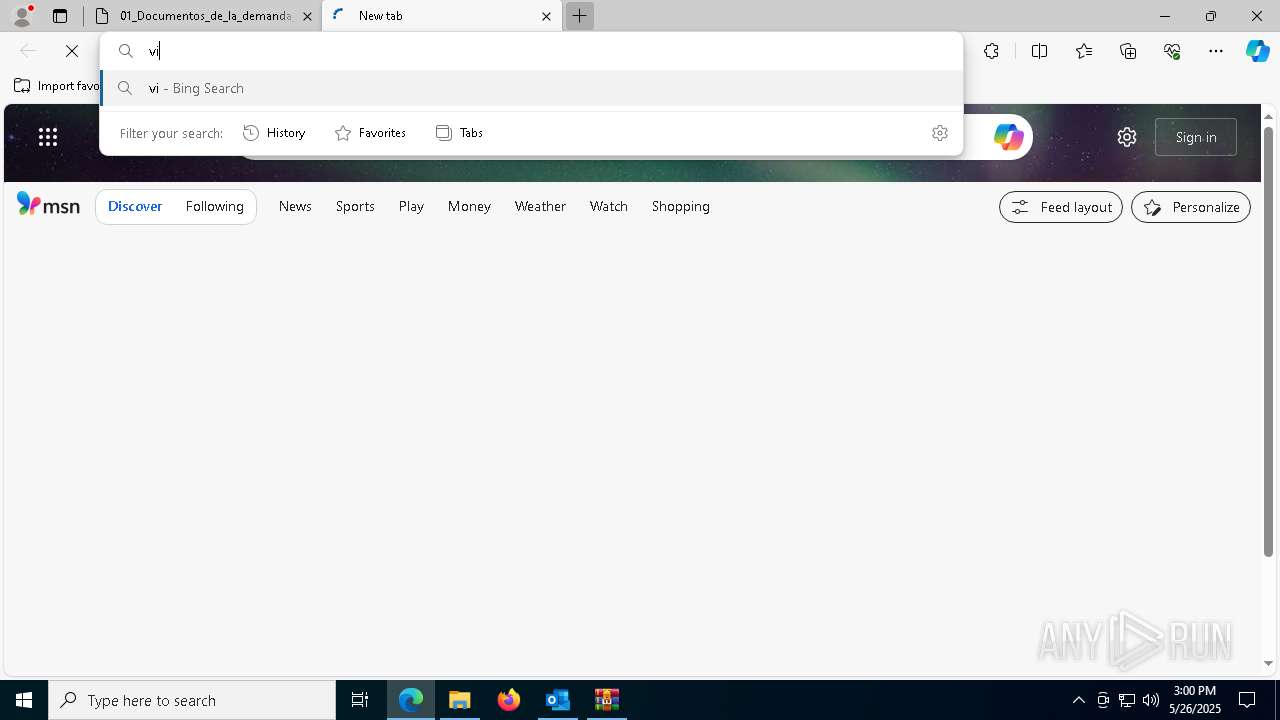
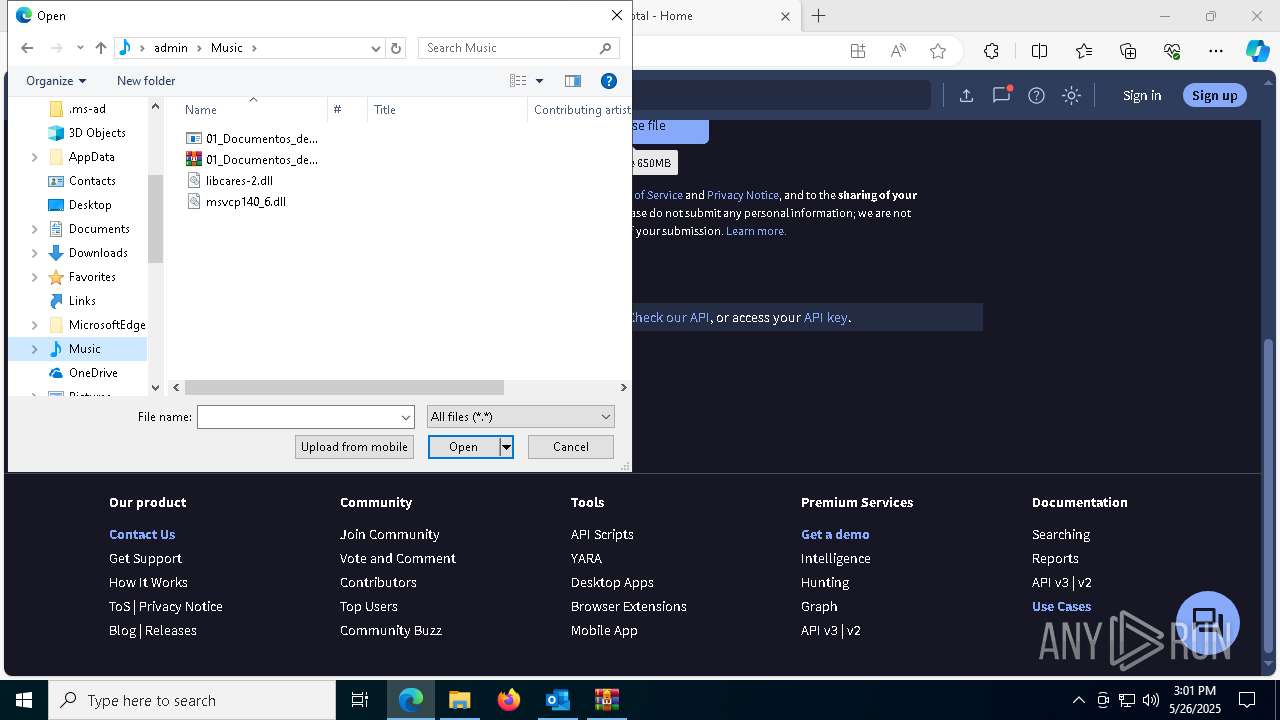
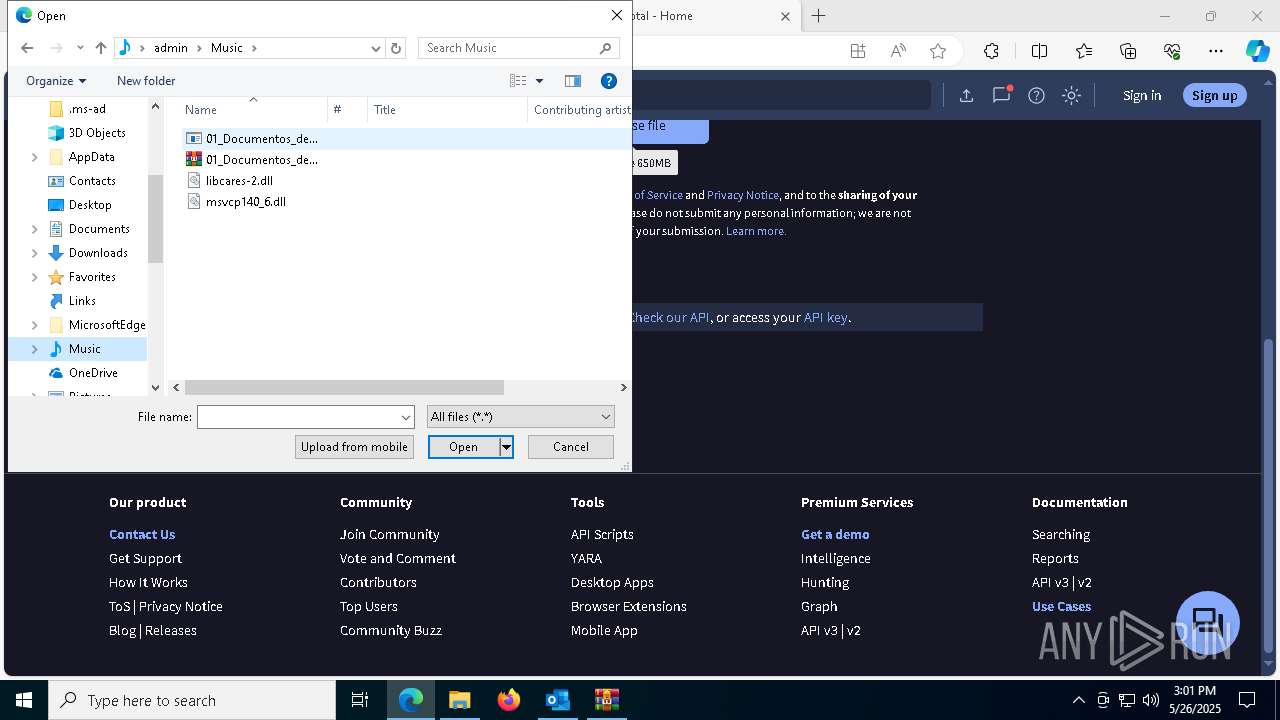
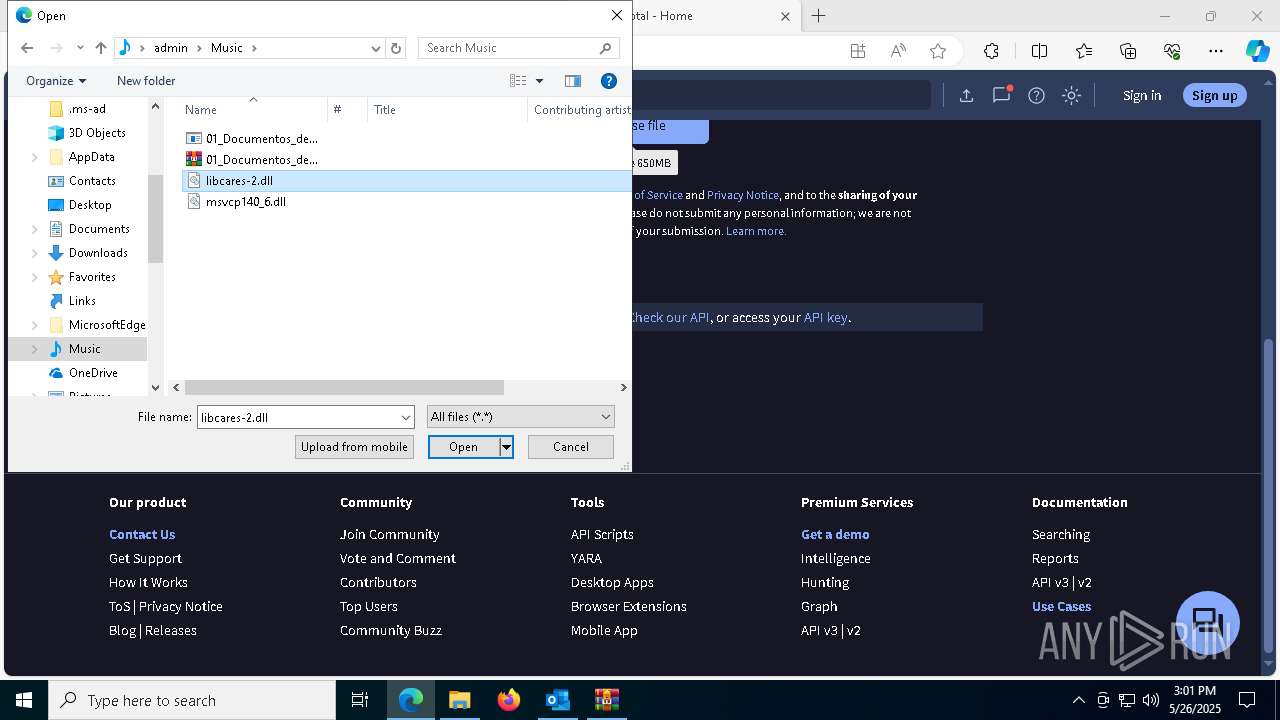
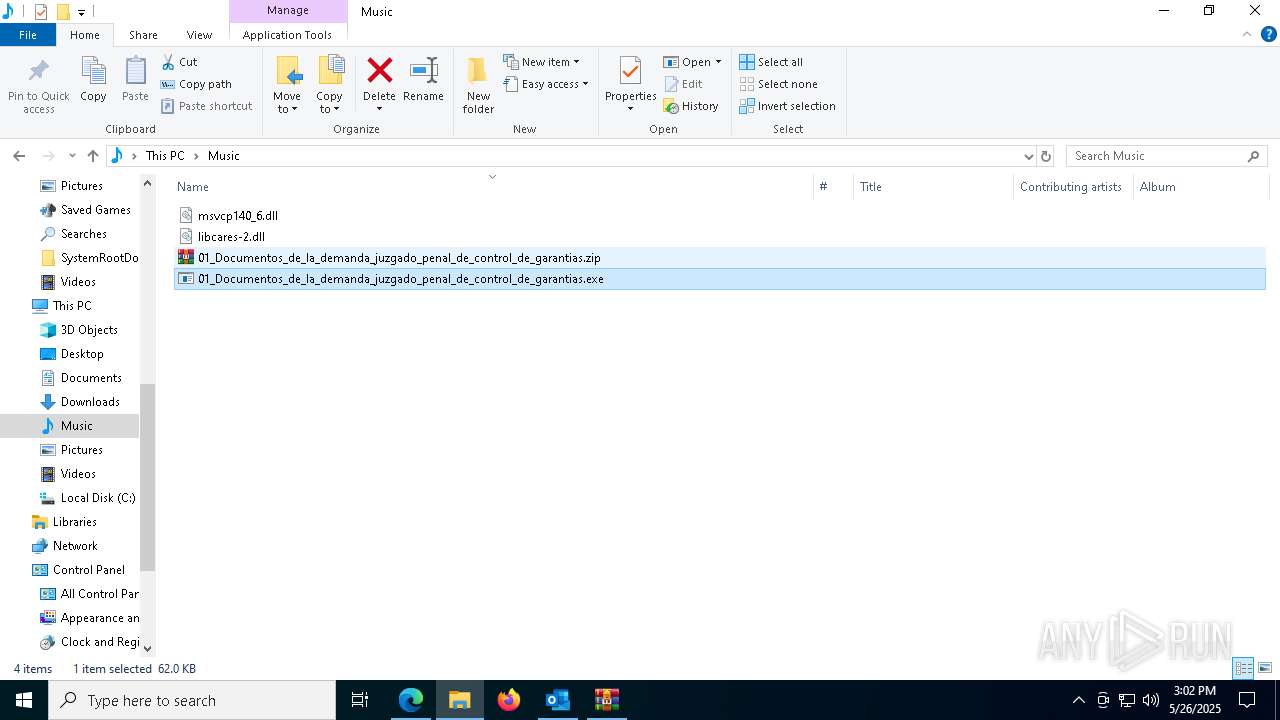
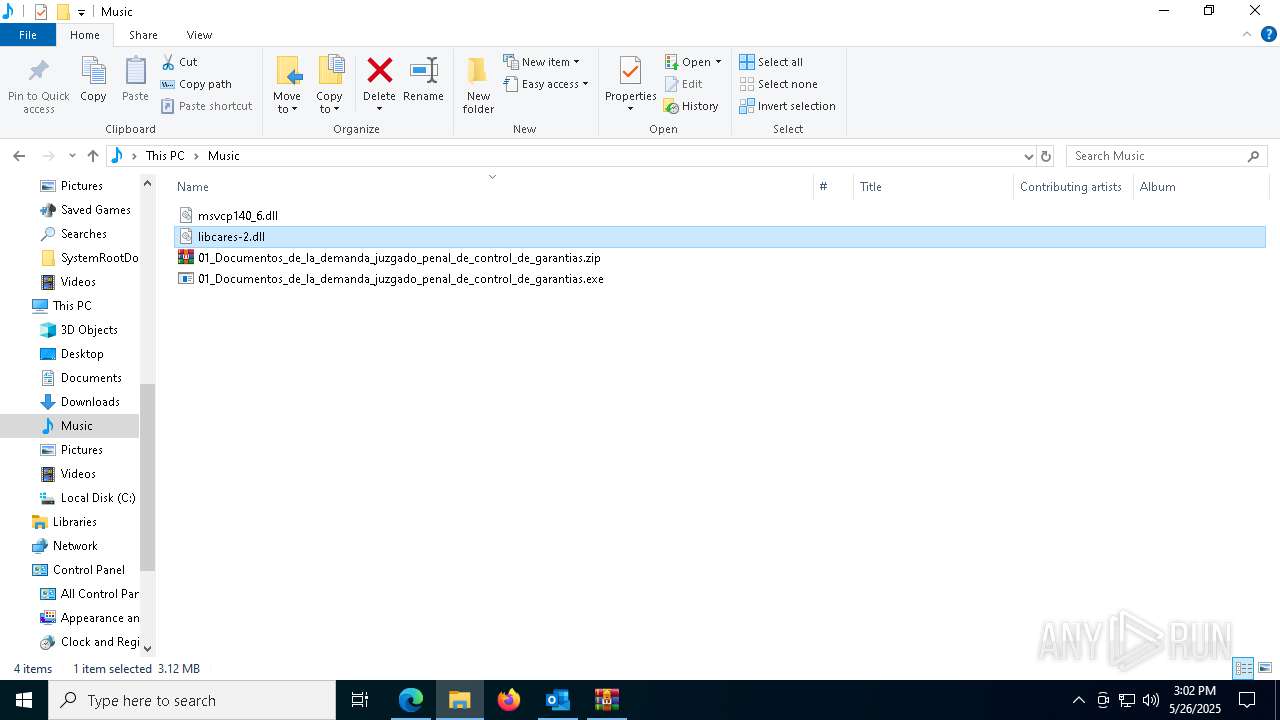
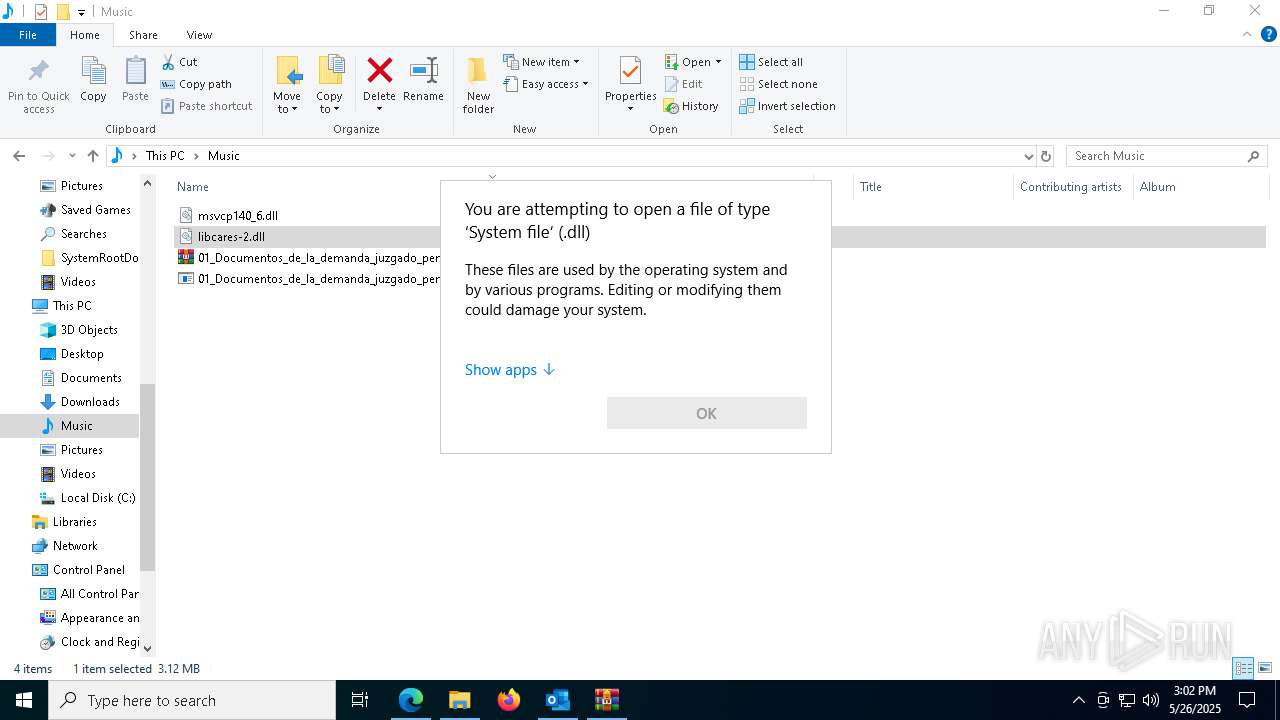
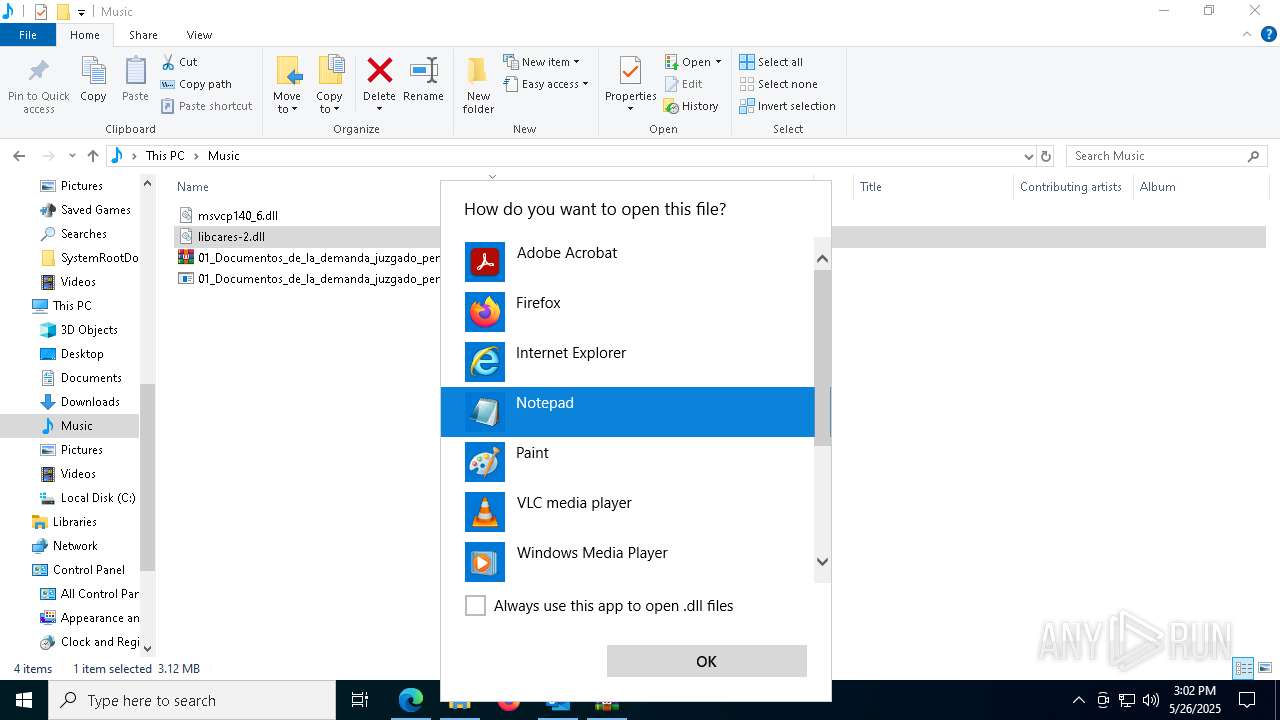
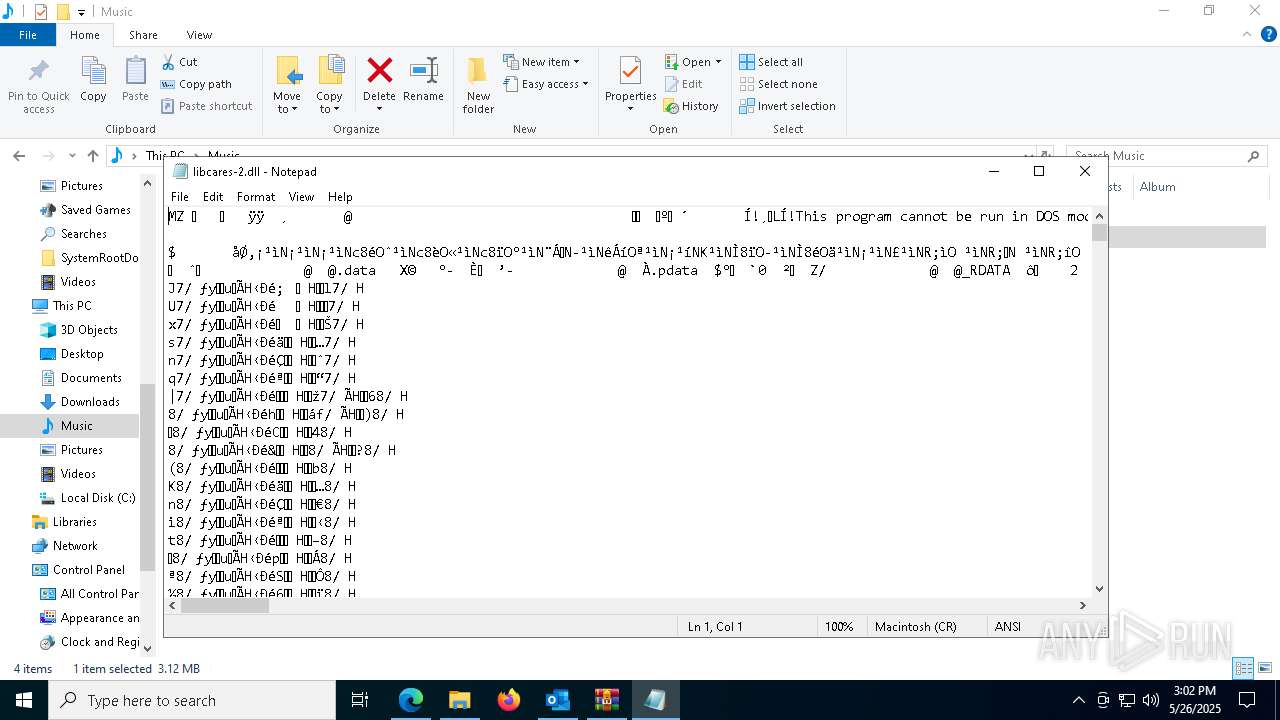
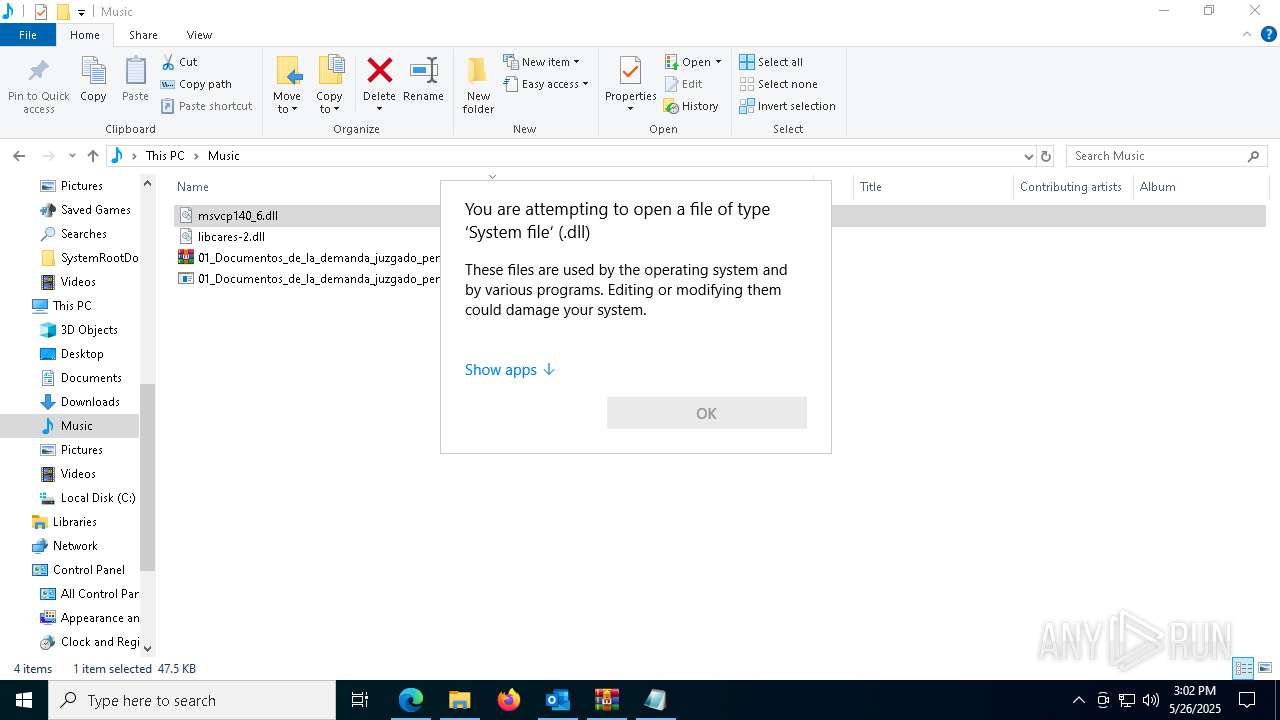
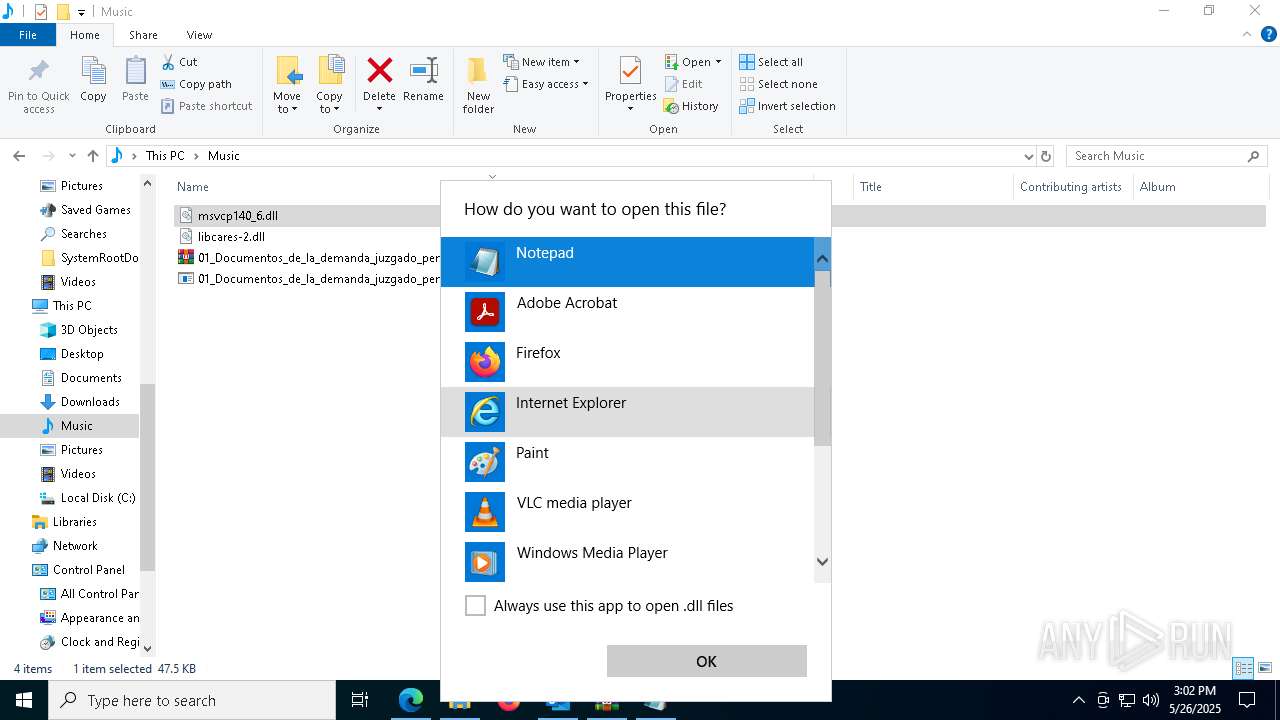
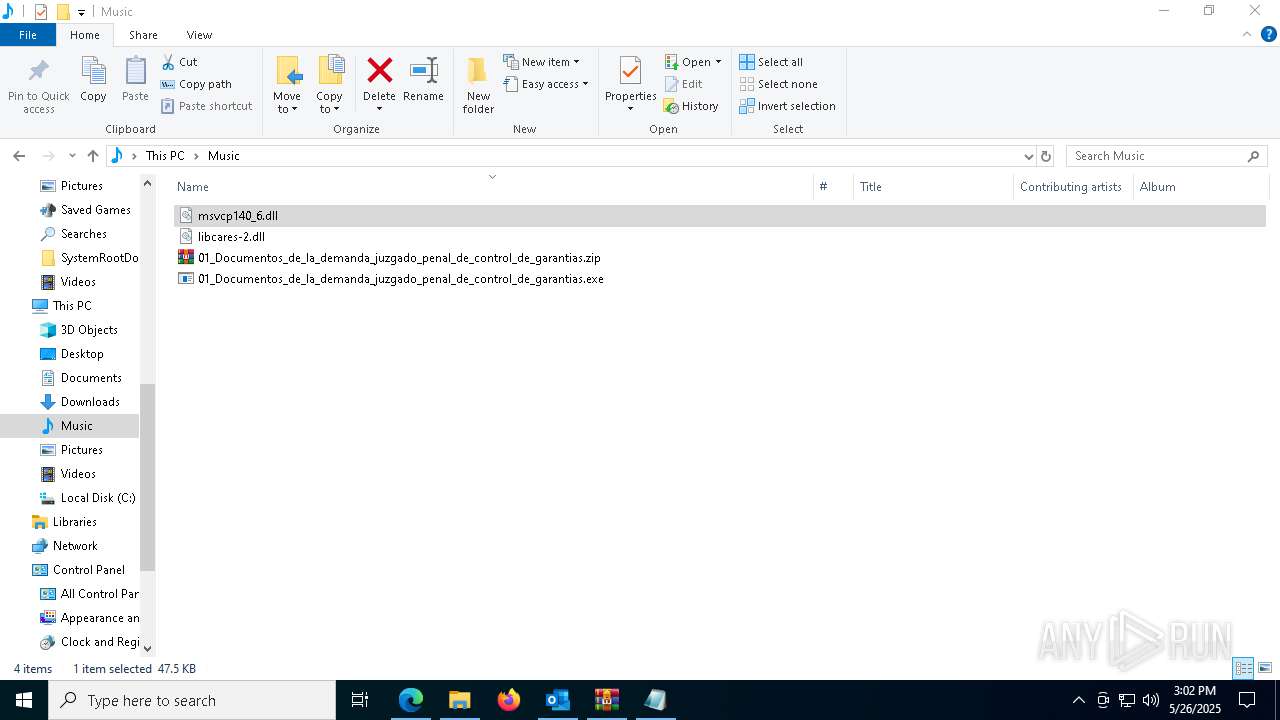
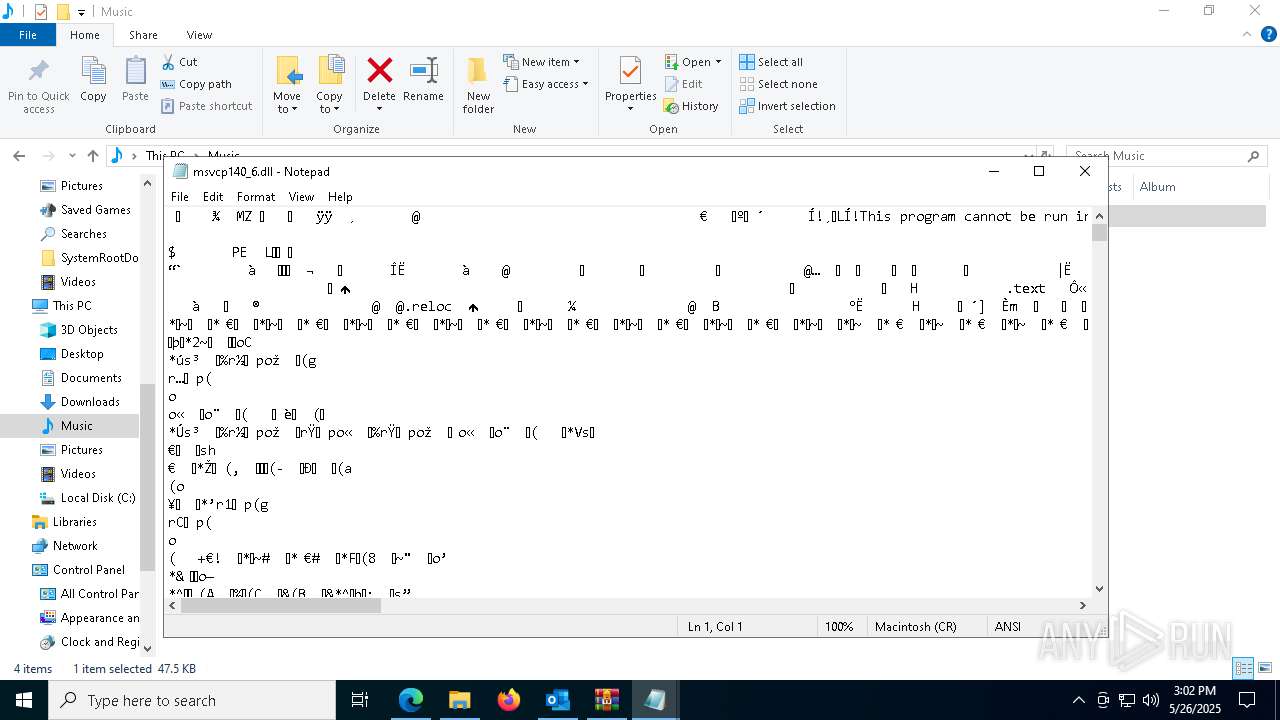
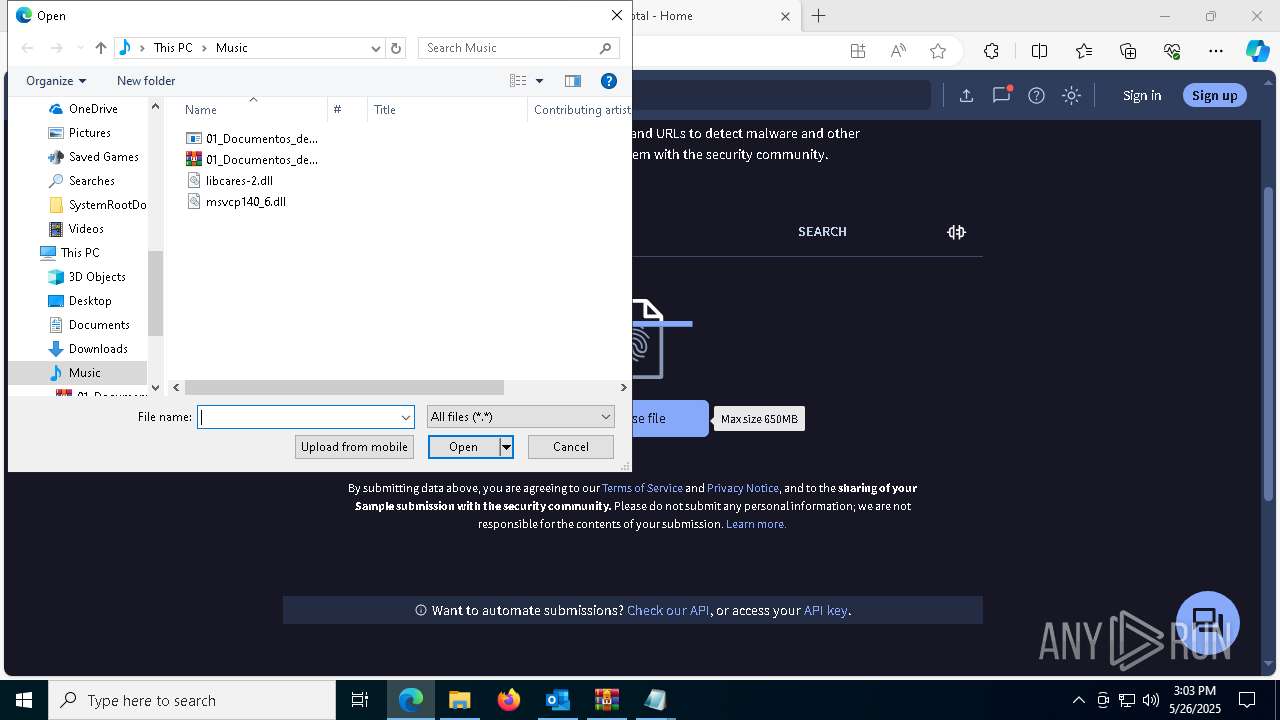
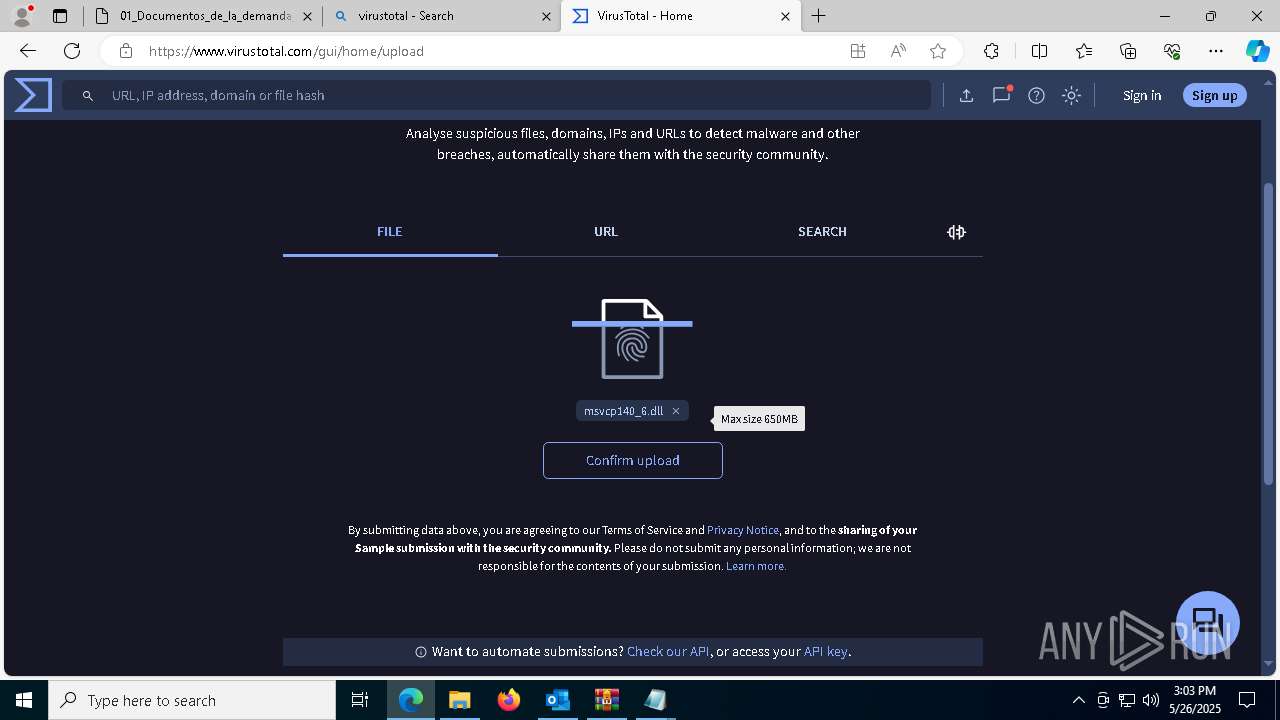
Executable content was dropped or overwritten
- 01_Documentos_de_la_demanda_juzgado_penal_de_control_de_garantias.exe (PID: 1128)
Contacting a server suspected of hosting an CnC
- AddInProcess32.exe (PID: 6712)
Connects to unusual port
- AddInProcess32.exe (PID: 6712)
INFO
Checks supported languages
- identity_helper.exe (PID: 4464)
Application launched itself
- msedge.exe (PID: 7548)
Reads the computer name
- identity_helper.exe (PID: 4464)
Reads Environment values
- identity_helper.exe (PID: 4464)
Email with attachments
- OUTLOOK.EXE (PID: 1196)
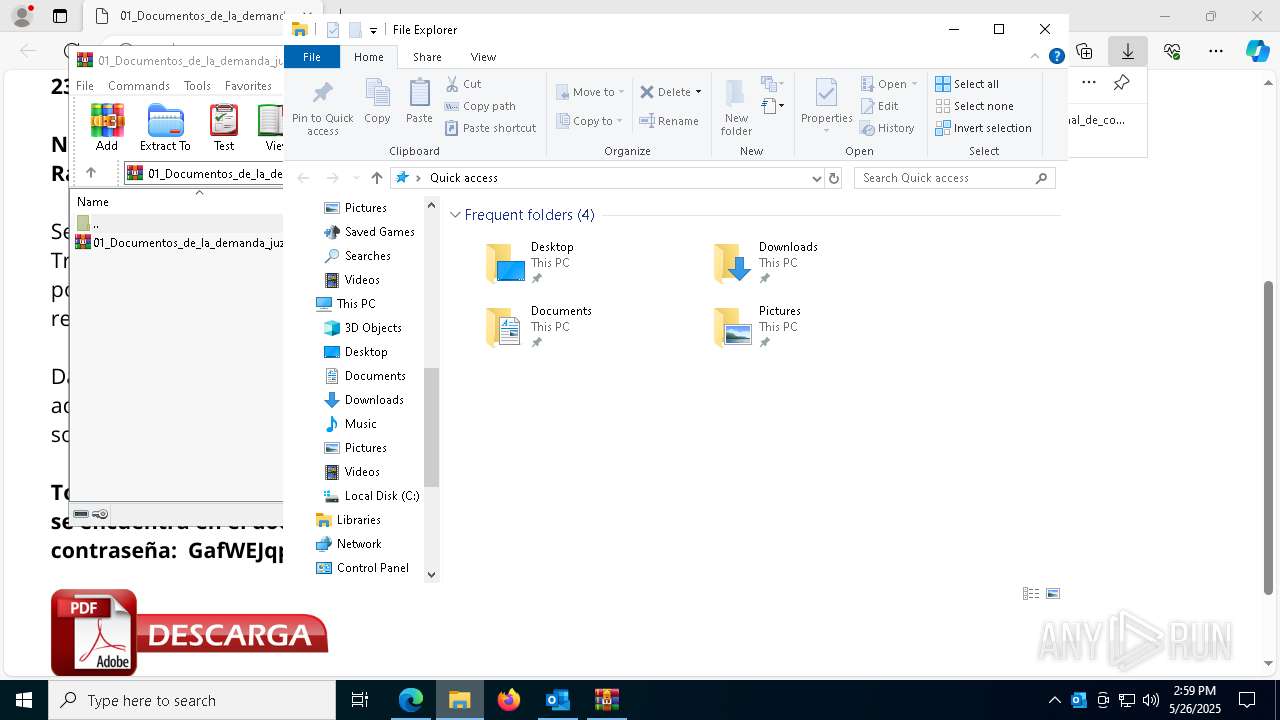
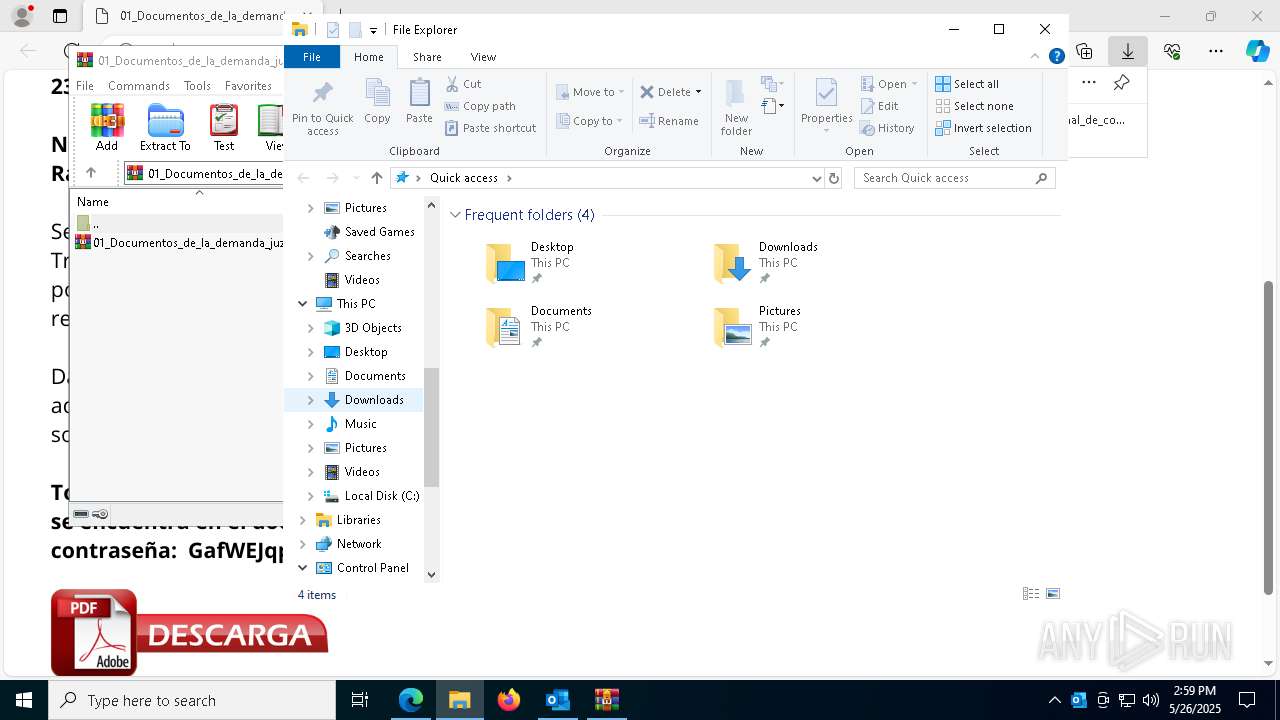
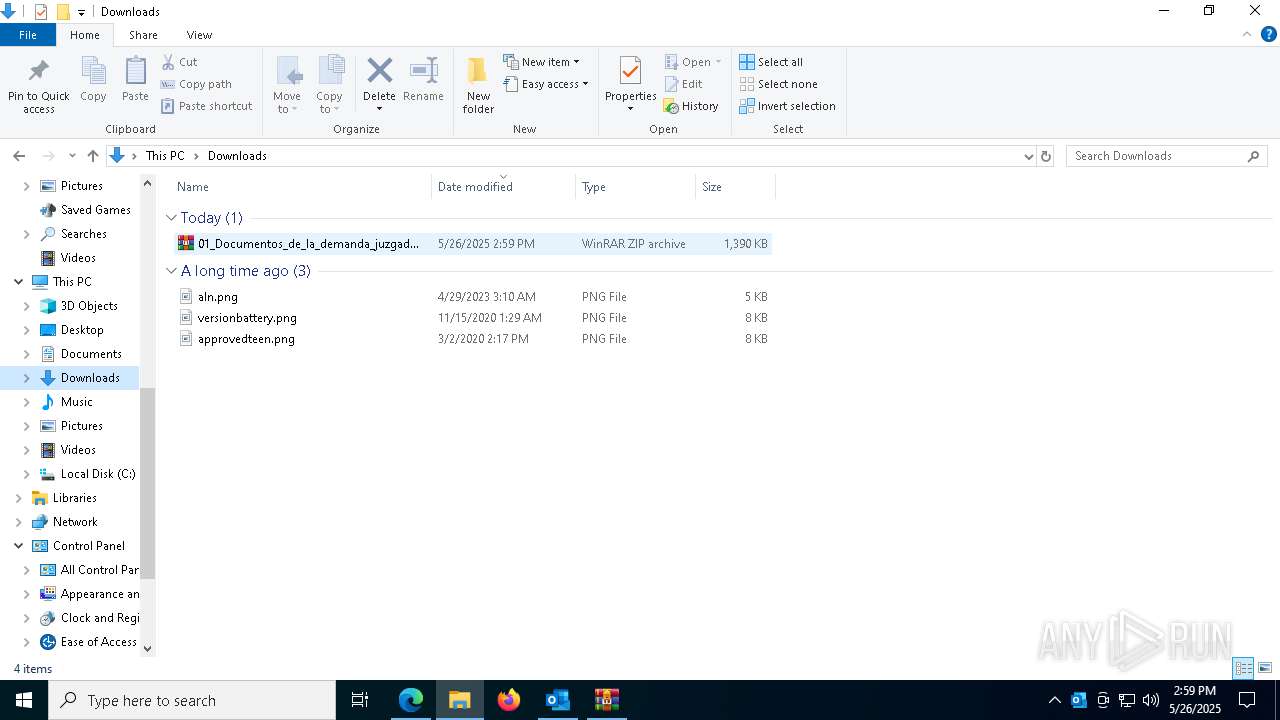
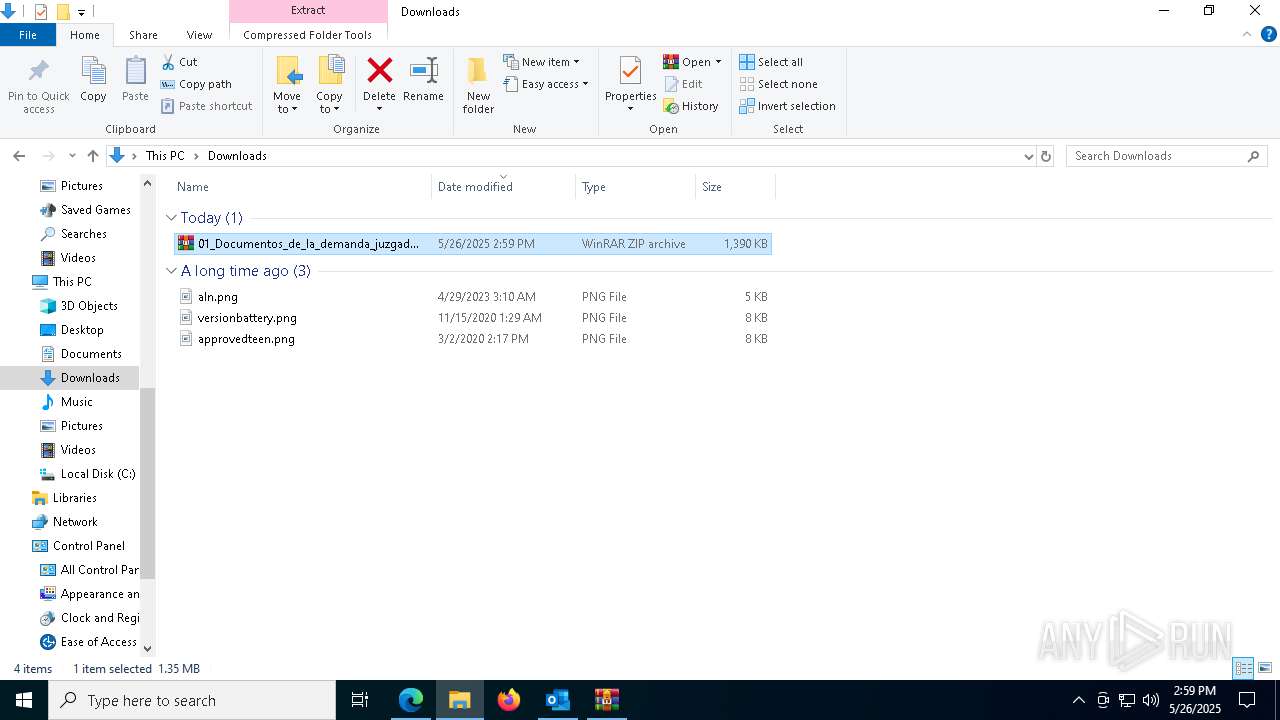
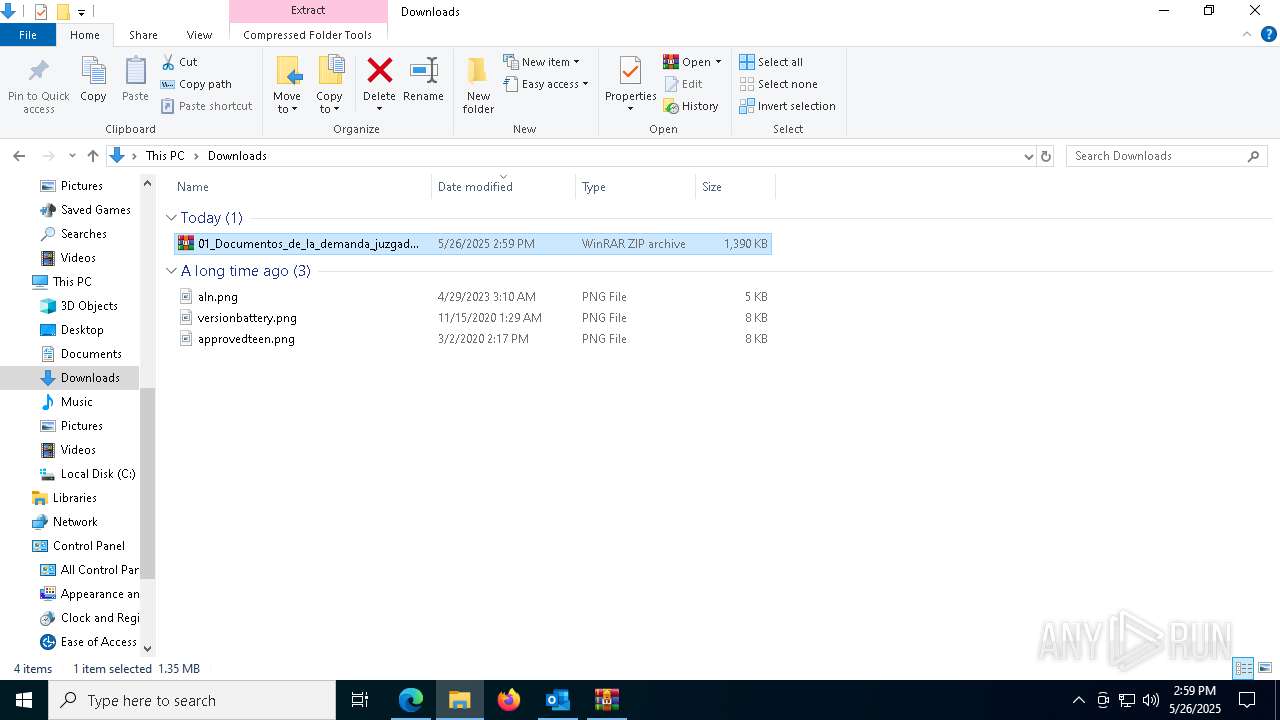
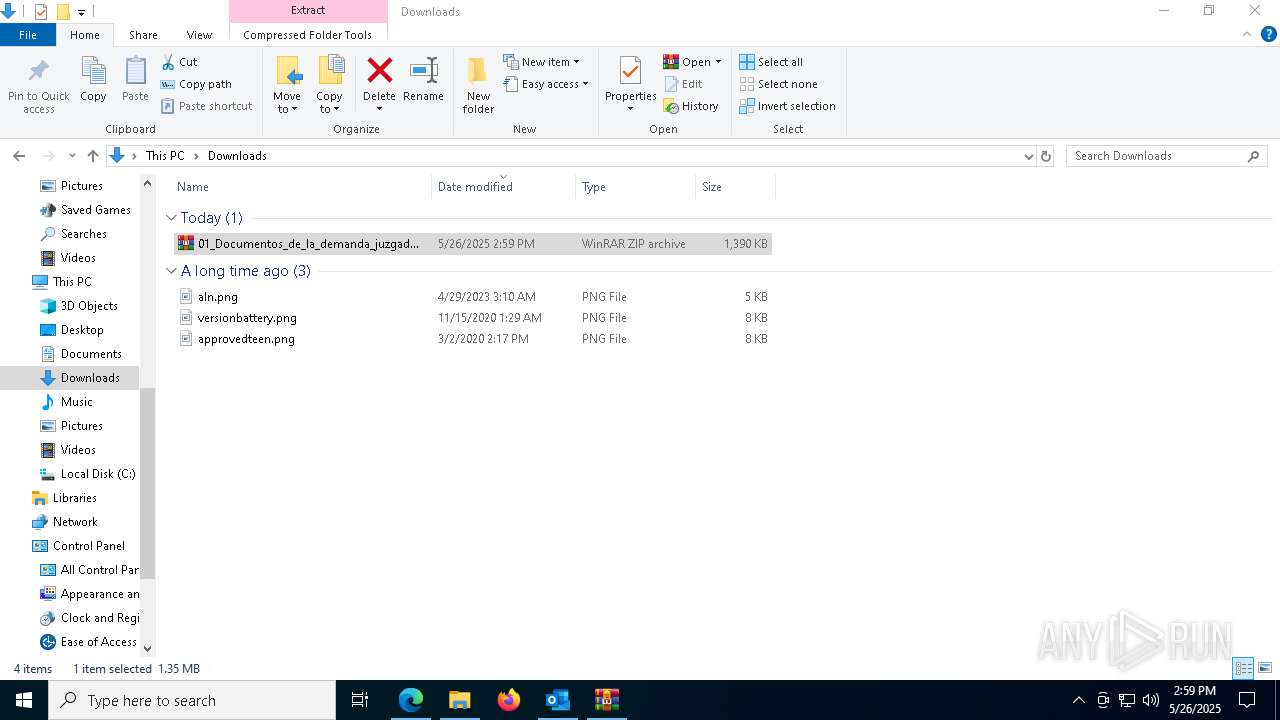
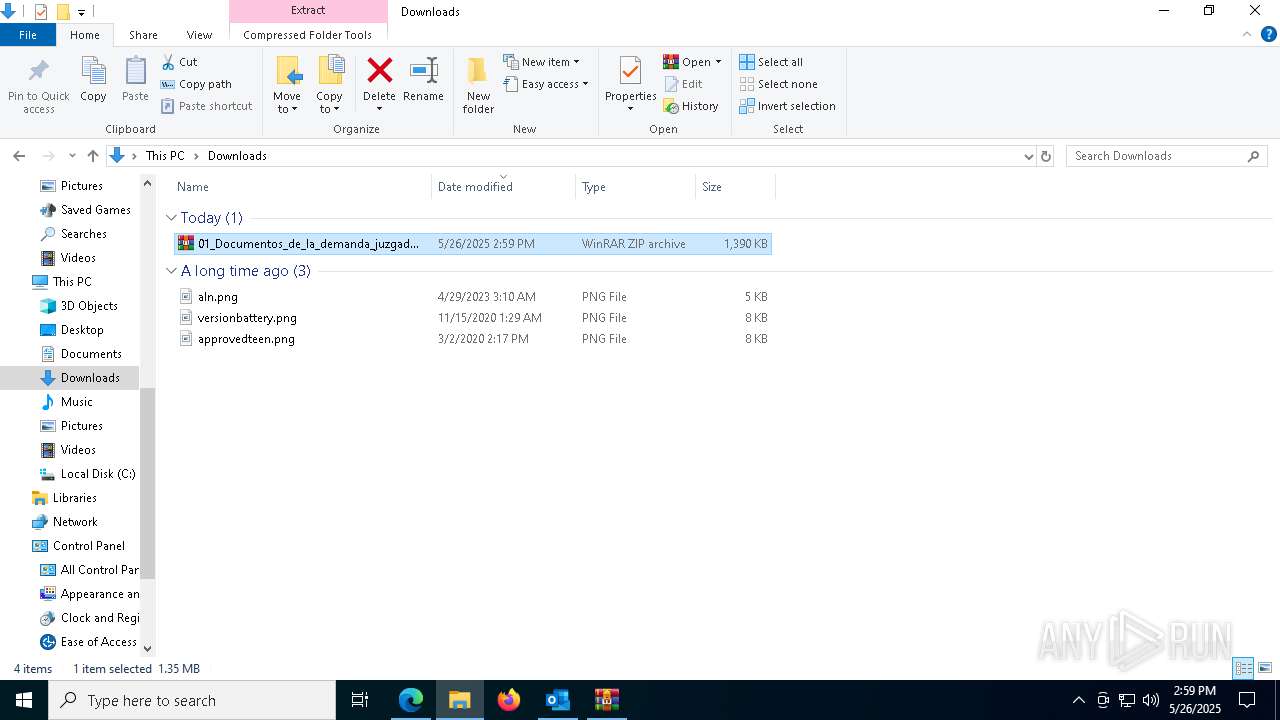
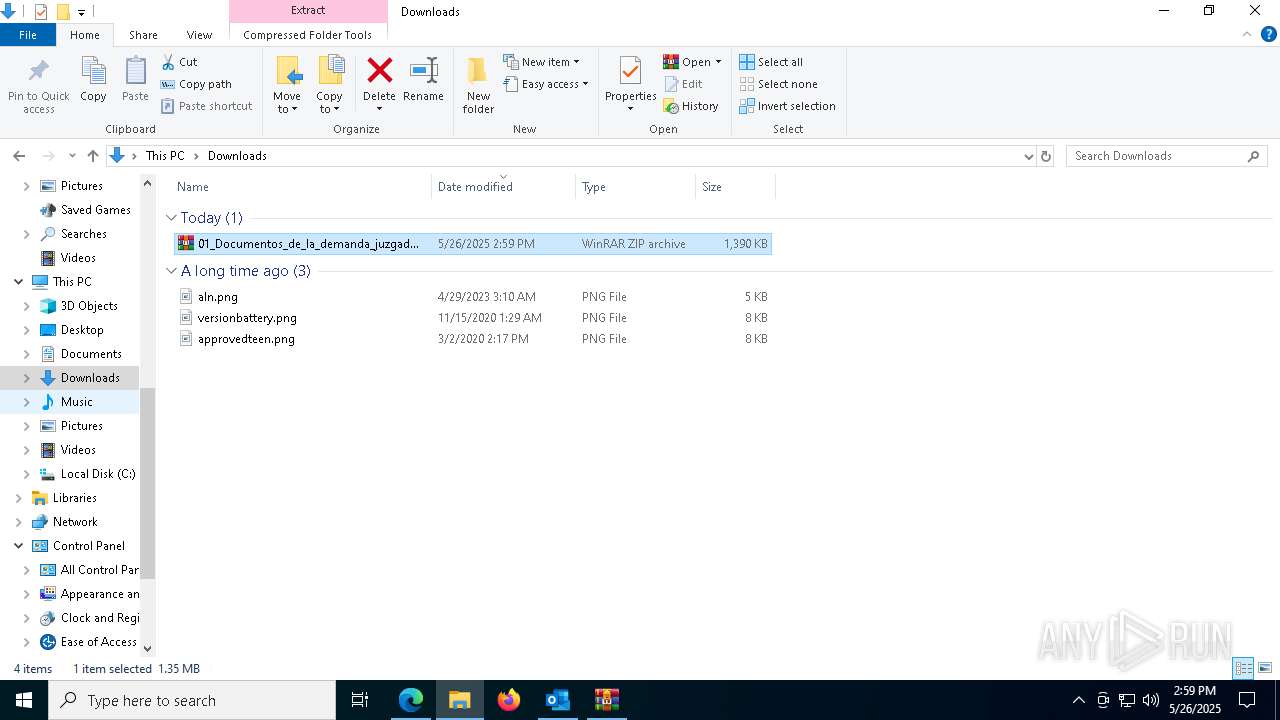
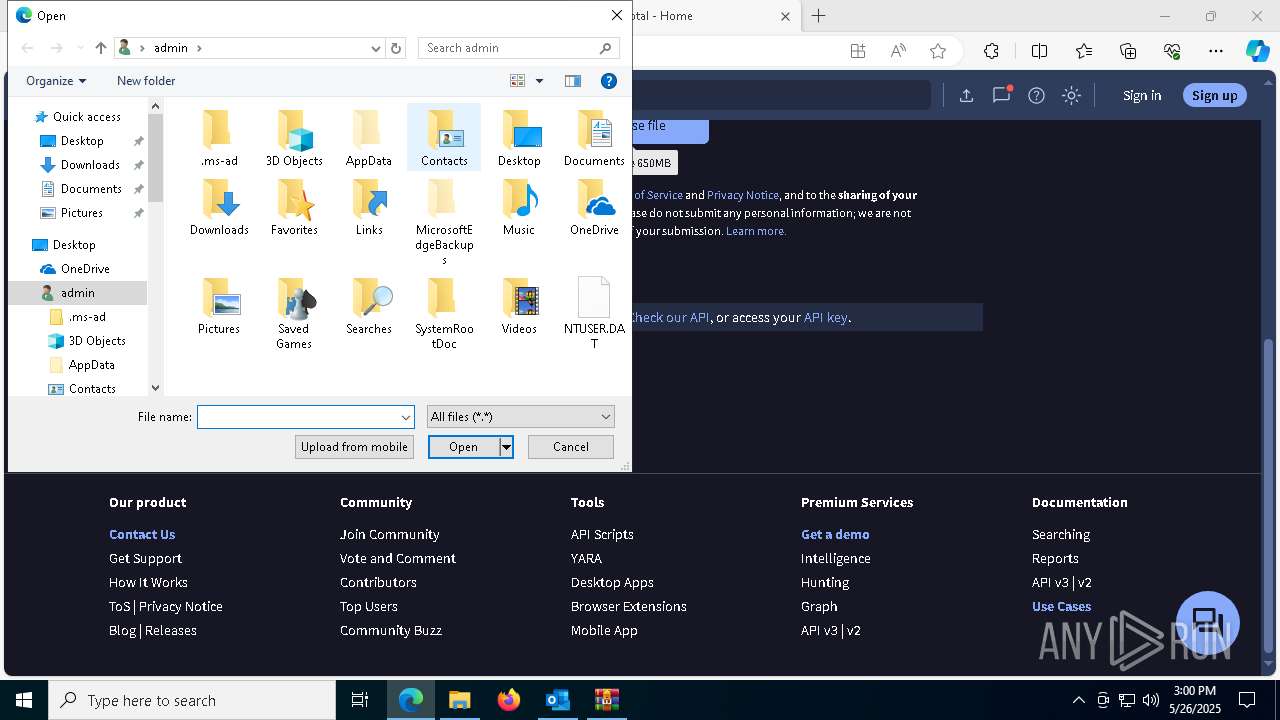
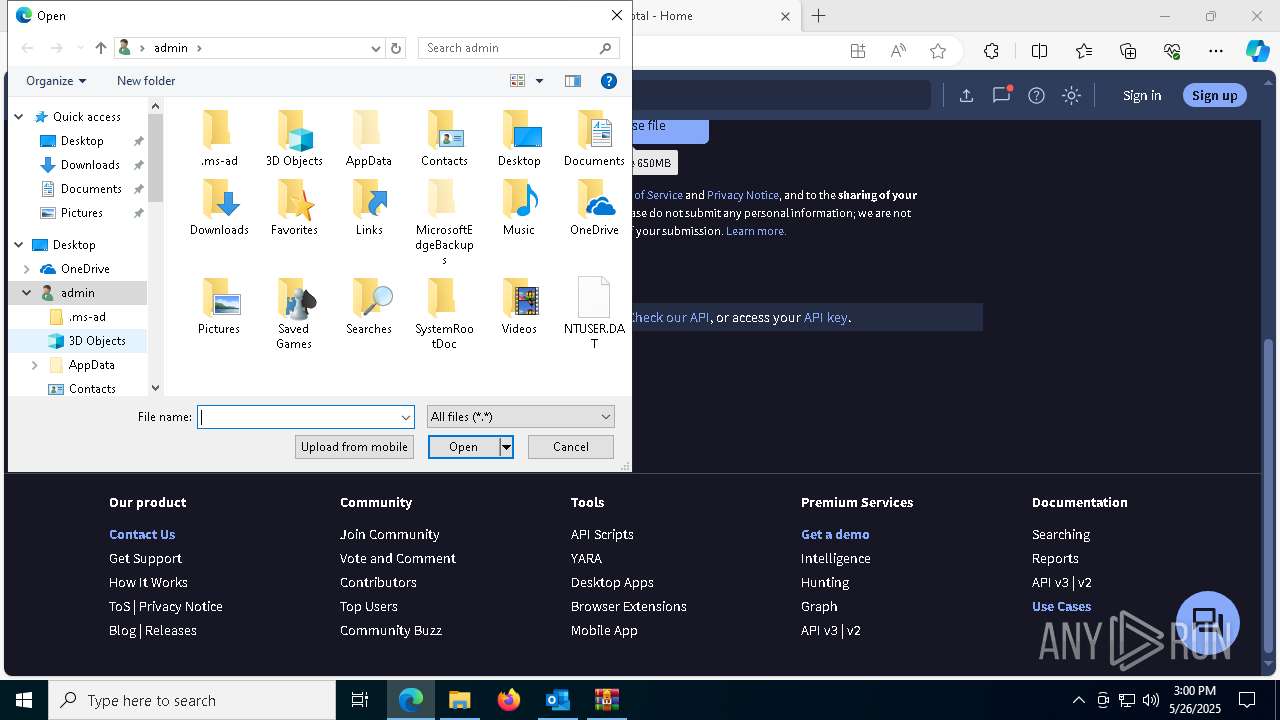
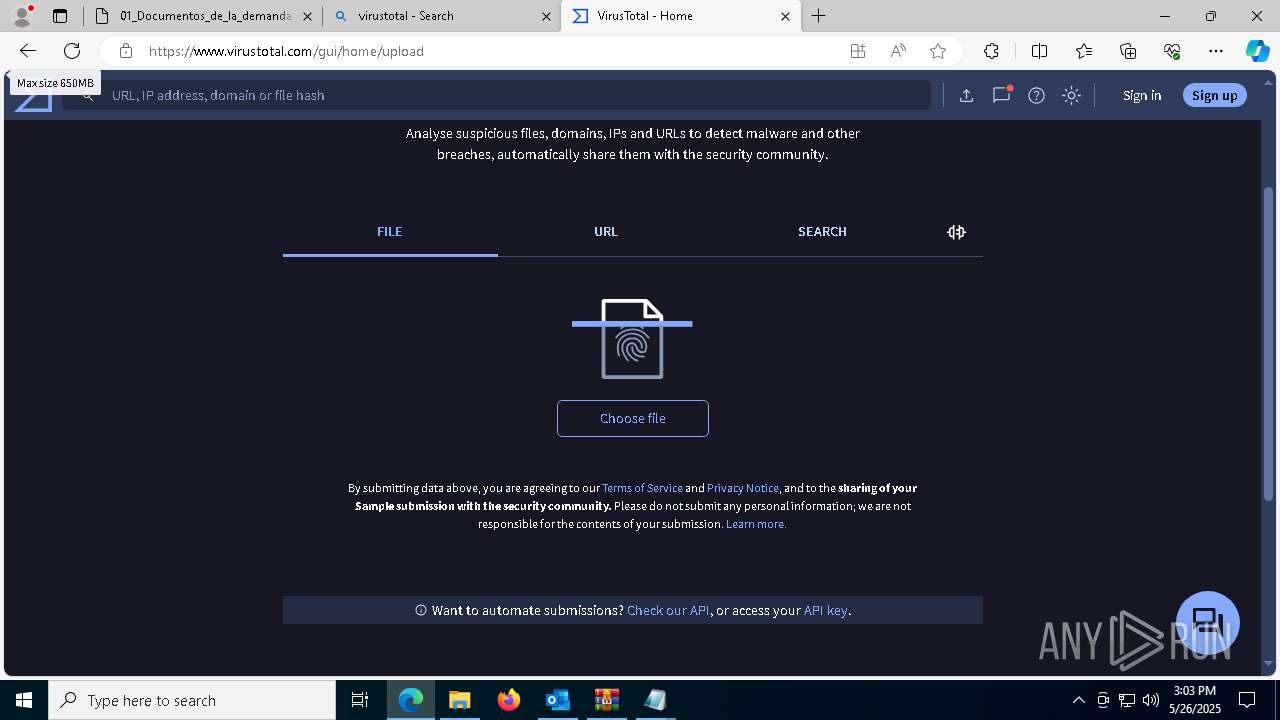
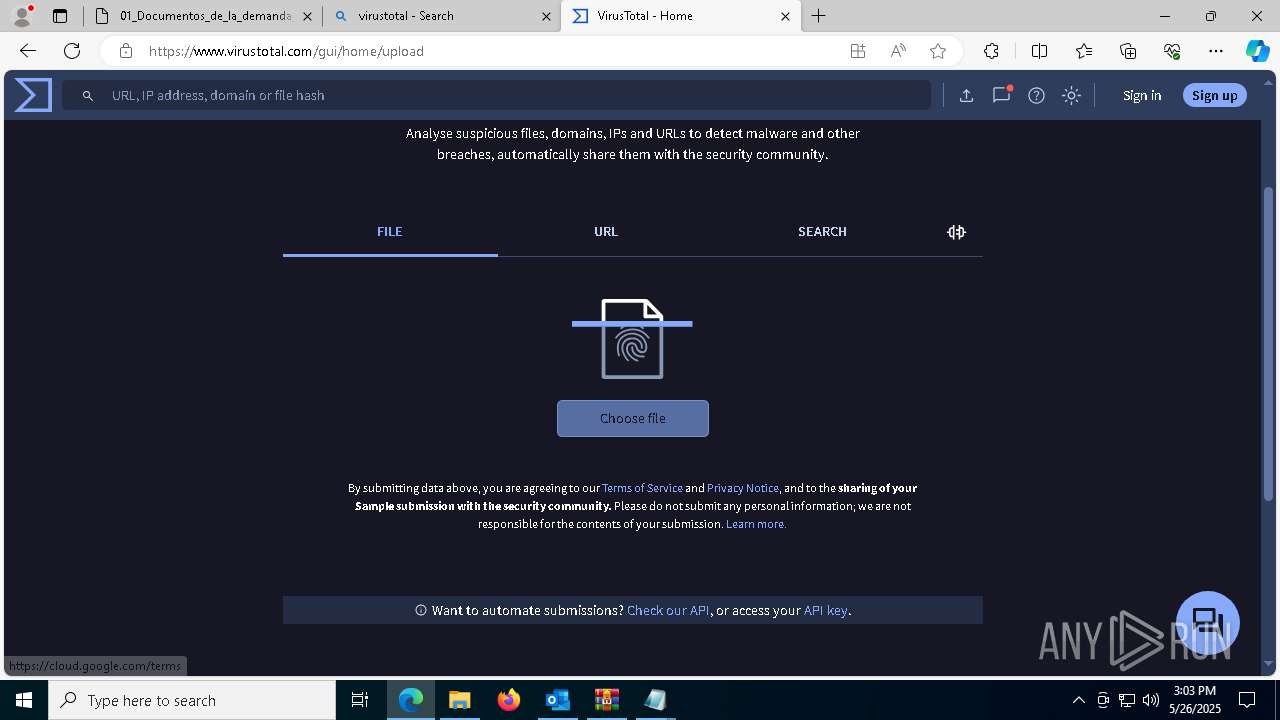
Launch of the file from Downloads directory
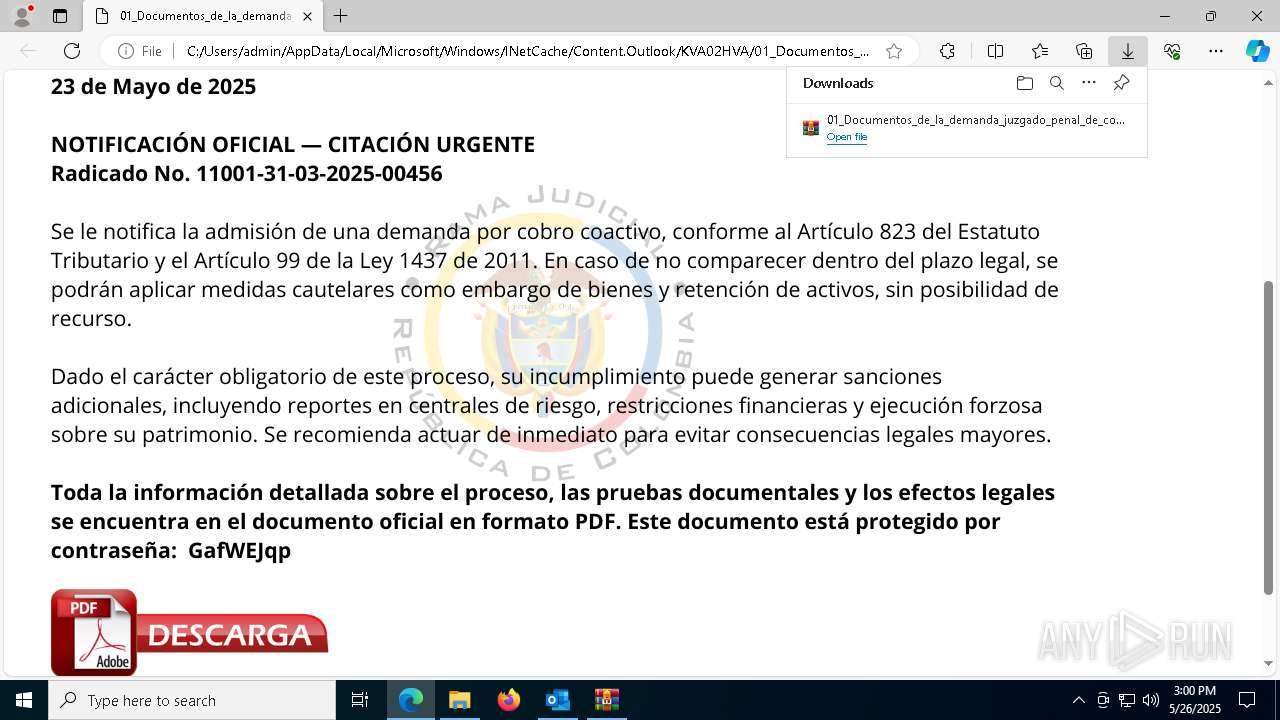
- msedge.exe (PID: 5512)
- msedge.exe (PID: 7548)
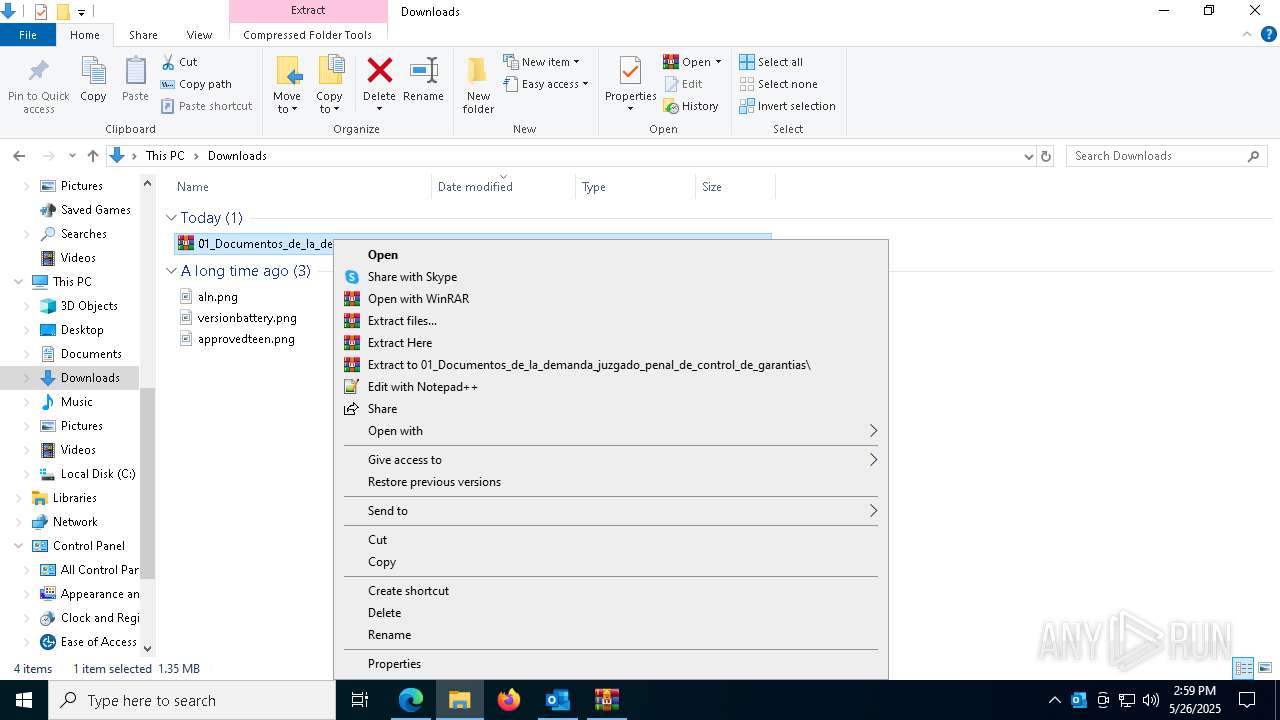
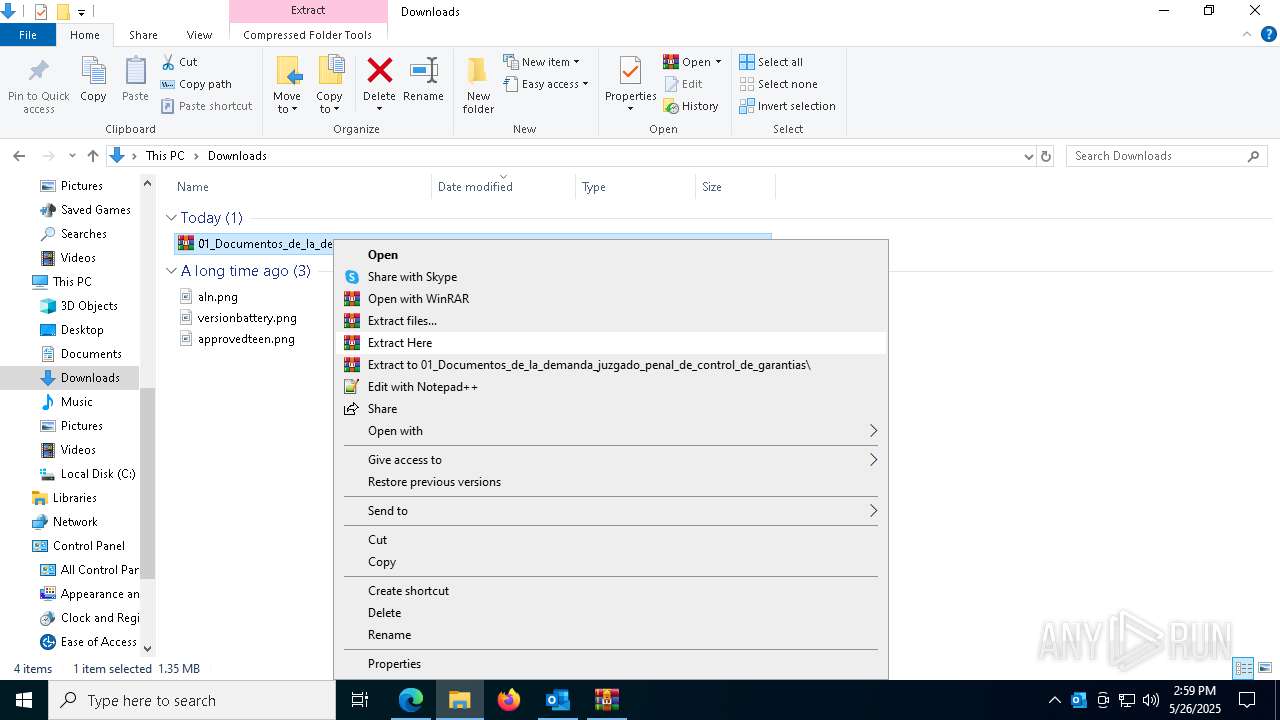
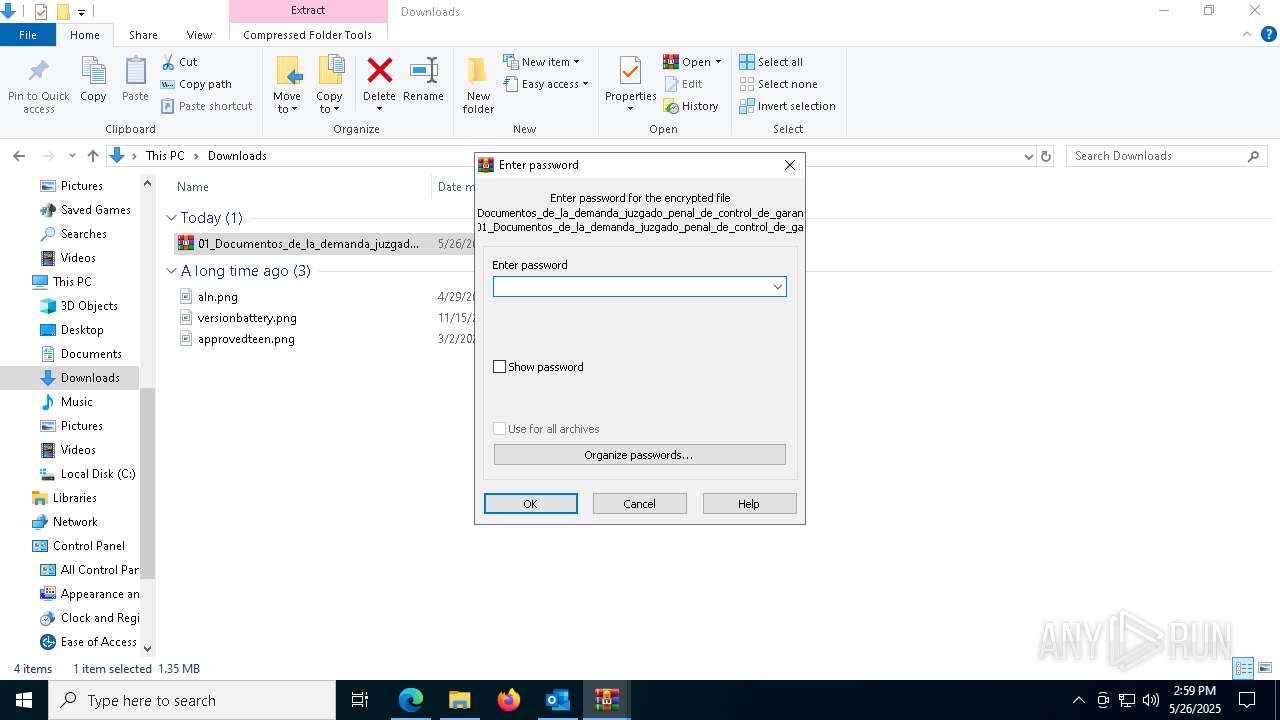
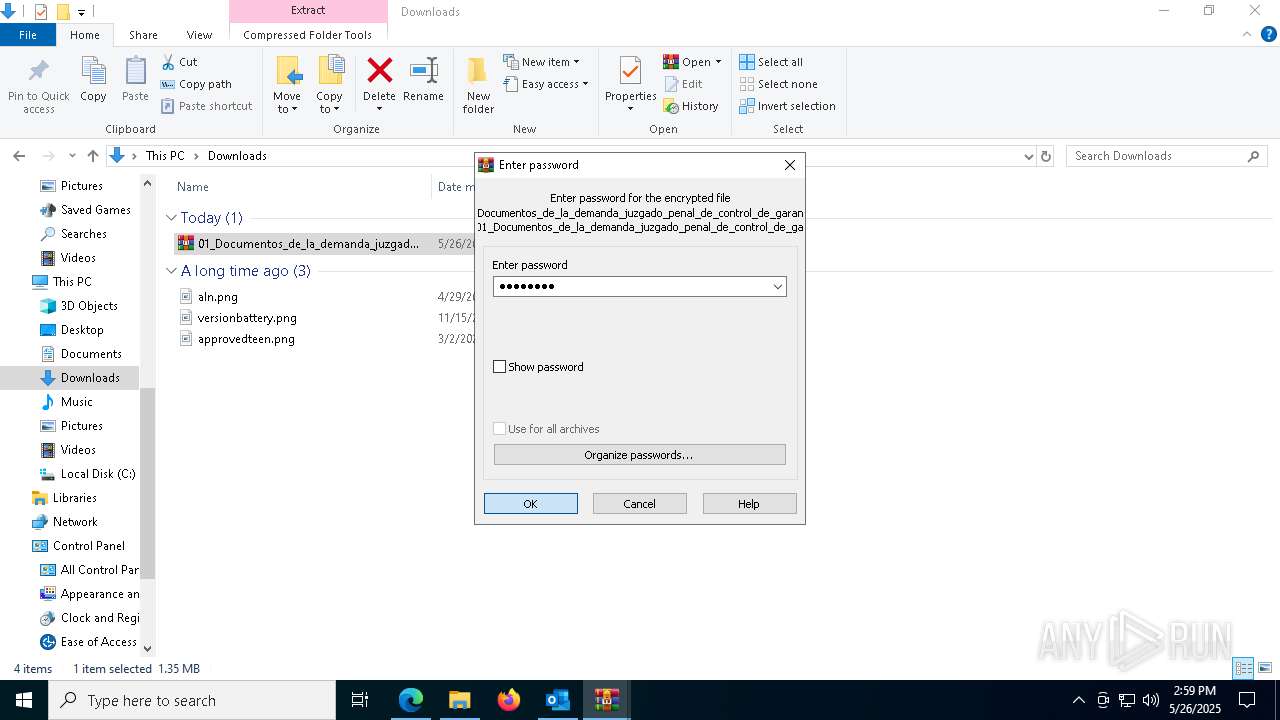
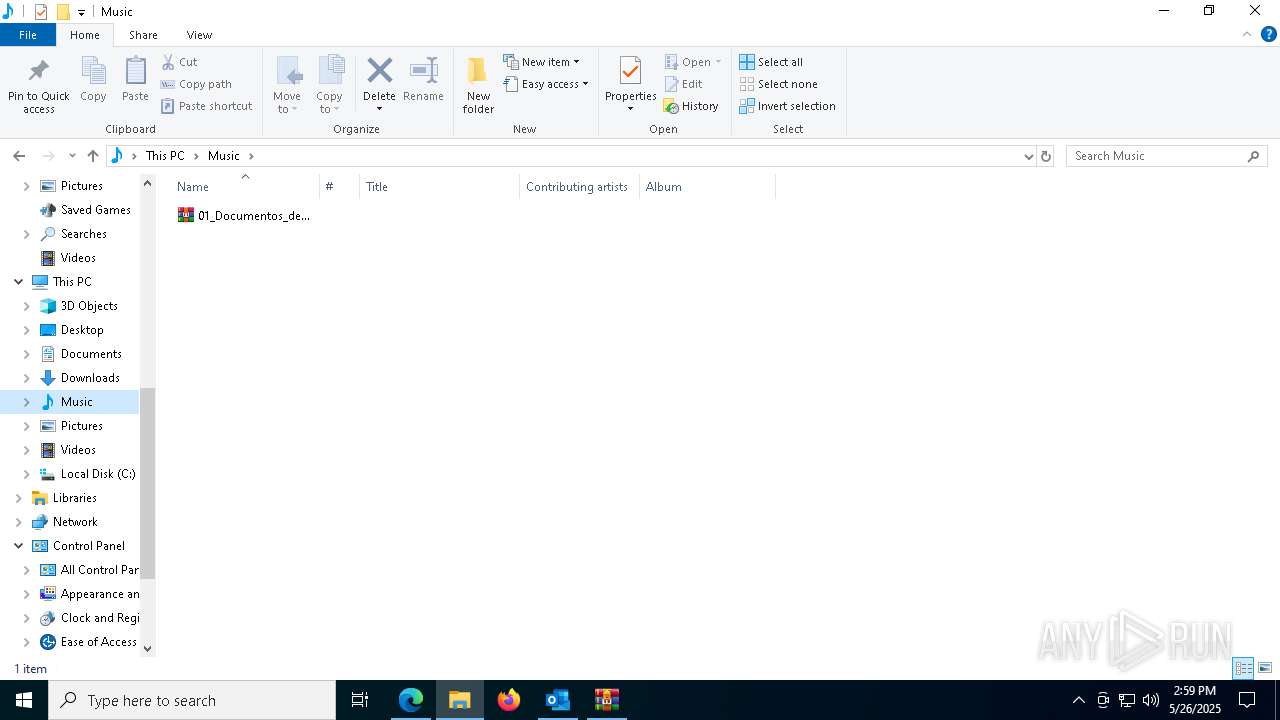
Manual execution by a user
- WinRAR.exe (PID: 8116)
- WinRAR.exe (PID: 6668)
- WinRAR.exe (PID: 2340)
- 01_Documentos_de_la_demanda_juzgado_penal_de_control_de_garantias.exe (PID: 1128)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7548)
Executable content was dropped or overwritten
- msedge.exe (PID: 2136)
- WinRAR.exe (PID: 2340)
The sample compiled with english language support
- msedge.exe (PID: 2136)
Reads the software policy settings
- slui.exe (PID: 5800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(6712) AddInProcess32.exe
C2 (1)envio21-005.duckdns.org
Ports (1)3020
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdanchun
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALv/XcwQnmQIwA3z8xW4ctTaHXVBMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMTAyMjIxNTY1NVoXDTMzMDczMTIxNTY1NVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureK9OIL9O1dPVRLLo8WUx01NPjIiGBSljaZ0ymX8Ff2A2kHSi7z1ANFoDa35u0ai+CtsAGaR5lFLKhBi+JmtUy5/MrwIRdbLcstg7Yfb2bvduO0oOdx6tlbX49VOYVOfpLj/asvBMDg0fBbXwAQKhjh1JcW6E9NJs/EbmUqQlnieM=
Keys
AESb216978c9c7636b47da26bc1d26225f7cc2470fd5d3fc0e8b1e173b6254308f8
SaltDcRatByqwqdanchun
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
222
Monitored processes
82
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=4220 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=7560 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=6288 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7340 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5284 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\Music\01_Documentos_de_la_demanda_juzgado_penal_de_control_de_garantias.exe" | C:\Users\admin\Music\01_Documentos_de_la_demanda_juzgado_penal_de_control_de_garantias.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Inicio de proceso de cobro coactivo – Radicado 11001-31-03-2025-00456.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=4064 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5716 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=3676 --field-trial-handle=2396,i,17132806204286155257,17230050802613314458,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
45 778
Read events
44 247
Write events
1 362
Delete events
169
Modification events
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\1196 |
| Operation: | write | Name: | 0 |
Value: 0B0E1097CCEF6BB68F1E4B9DB8AFF0F47E5A4F230046B7FEEDAFEAC9F3ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511AC09D2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
45
Suspicious files
802
Text files
119
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1196 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:70D2517509CCAF28B2456991DEF171E5 | SHA256:80329DBA97B2DEF1EE86AEC0AA5C0FC8E4C7FCF8A696CB04B6E64CB67FF3CE84 | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:1C0F0A244F3B76F00E4286577C3FA498 | SHA256:1176CE70E4A6E46E393014C73554F1D15E1FE4679A79C6C2D1FA6FC8ADAB5F28 | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:95AF8001542CFDF0CCC1136E3D0956FF | SHA256:A1A4B9FE98A454A5887EC49923FFC87509DE87D3383C4F7D4A8C5F88CAE62E6B | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:9985883D541D8934724FADF79C587A7A | SHA256:41BAE071951E9C97EE772BDC8F3605787CE40EE557E1CC66D1F4C515E576C08C | |||
| 7548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:C7E2197BAE099B13BBB3ADEB1433487D | SHA256:3460EEAF45D581DD43A6E4E17AF8102DDAFF5AEAA88B10099527CF85211629E9 | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\KVA02HVA\01_Documentos_de_la_demanda_juzgado_penal_de_control_de_garantias_yn053n90 (002).svg | image | |
MD5:0CBD3BC471765411713A2E3DC65CA583 | SHA256:8957F0968688E14A6BDFFC00D020C554F307EE160A7217F06B47C126B4000495 | |||
| 7548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1110b6.TMP | — | |
MD5:— | SHA256:— | |||
| 7548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1110b6.TMP | — | |
MD5:— | SHA256:— | |||
| 7548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1110c6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
179
DNS requests
180
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1196 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1196 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5132 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3ab36512-8e78-4855-9d3c-00fc48298f23?P1=1748581918&P2=404&P3=2&P4=RvpINR9qGhQo3knnBA2n3Ev0yuy2kyMpCJ0yezQXUpMZ8jIJc050HlleVxqszQKM6FagtuQ4l%2fRs7ZHFyy9%2fuw%3d%3d | unknown | — | — | whitelisted |
5132 | svchost.exe | HEAD | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3ab36512-8e78-4855-9d3c-00fc48298f23?P1=1748581918&P2=404&P3=2&P4=RvpINR9qGhQo3knnBA2n3Ev0yuy2kyMpCJ0yezQXUpMZ8jIJc050HlleVxqszQKM6FagtuQ4l%2fRs7ZHFyy9%2fuw%3d%3d | unknown | — | — | whitelisted |
5132 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3ab36512-8e78-4855-9d3c-00fc48298f23?P1=1748581918&P2=404&P3=2&P4=RvpINR9qGhQo3knnBA2n3Ev0yuy2kyMpCJ0yezQXUpMZ8jIJc050HlleVxqszQKM6FagtuQ4l%2fRs7ZHFyy9%2fuw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1196 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1196 | OUTLOOK.EXE | 52.109.28.47:443 | roaming.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
1196 | OUTLOOK.EXE | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1196 | OUTLOOK.EXE | 23.48.23.11:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
6712 | AddInProcess32.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6712 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
6712 | AddInProcess32.exe | A Network Trojan was detected | ET MALWARE Observed Malicious SSL Cert (Various RAT) |
6712 | AddInProcess32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
7792 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7792 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7792 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7792 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |