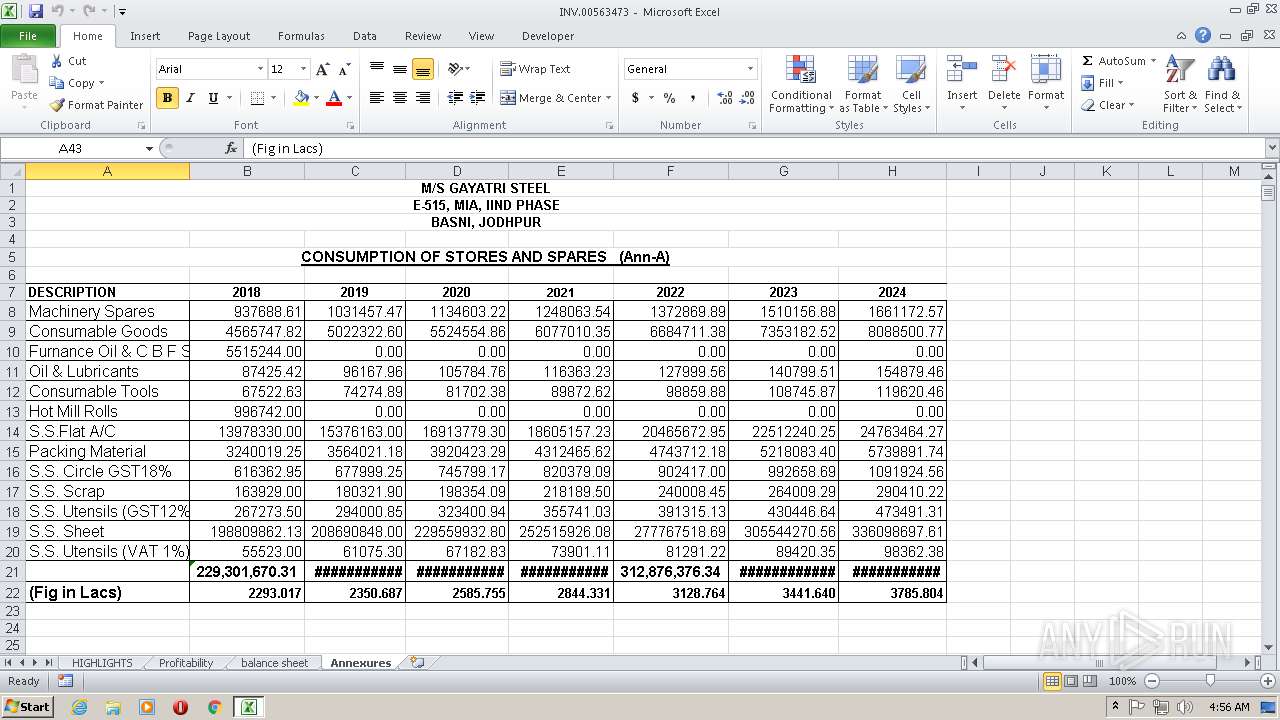
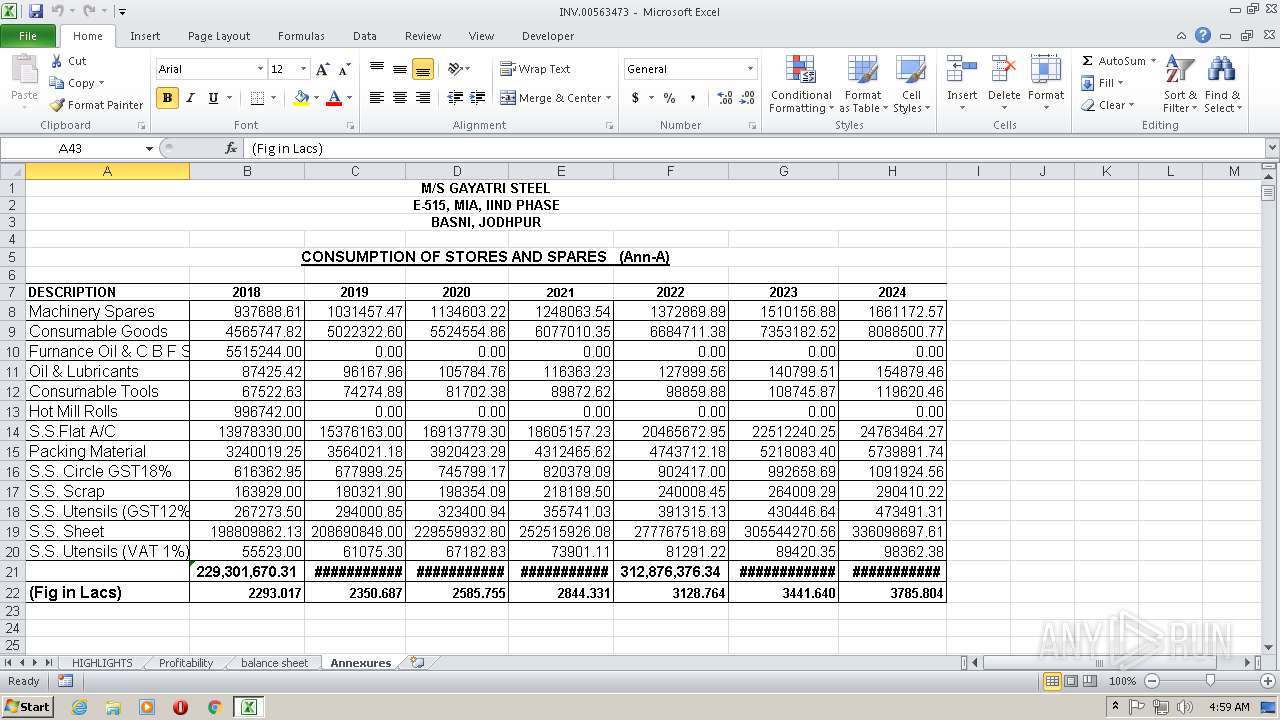
| File name: | INV.00563473.xlsx |
| Full analysis: | https://app.any.run/tasks/95095ce2-dd3b-4071-8ebd-7c3e55f6e640 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | March 15, 2019, 04:55:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 7F0CEC6FC9140D690FF466BCE3FD3D7A |
| SHA1: | 1922A69F4032DD8FC75BC7192F9108F1A022C80B |
| SHA256: | CA06928FA89F2208BC8AF2C651EB0AC75594913D1A0B890E7D825A2B6F5CB4D1 |
| SSDEEP: | 768:+rfvEyYBvycV++H+/e0FNOuvS3oOJjxqmMnYGt4AovwF:+rL4tVDHSFnOejYGpEi |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 1116)
Application was dropped or rewritten from another process
- regasms.exe (PID: 2380)
- app.exe (PID: 2648)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 1116)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 1116)
Changes the autorun value in the registry
- app.exe (PID: 2648)
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 2644)
Actions looks like stealing of personal data
- vbc.exe (PID: 2924)
- vbc.exe (PID: 3032)
Stealing of credential data
- vbc.exe (PID: 3032)
- vbc.exe (PID: 2924)
SUSPICIOUS
Creates files in the user directory
- EQNEDT32.EXE (PID: 1116)
- cmd.exe (PID: 2484)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 1116)
- cmd.exe (PID: 2484)
Starts CMD.EXE for commands execution
- regasms.exe (PID: 2380)
Executes scripts
- RegAsm.exe (PID: 2644)
Connects to SMTP port
- RegAsm.exe (PID: 2644)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 324)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 324)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:14 13:45:22 |
| ZipCRC: | 0x7782a3b5 |
| ZipCompressedSize: | 425 |
| ZipUncompressedSize: | 2041 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | COMPAQ |
|---|
XML
| LastModifiedBy: | COMPAQ |
|---|---|
| LastPrinted: | 2017:04:29 14:02:28Z |
| CreateDate: | 2010:02:14 08:32:05Z |
| ModifyDate: | 2018:09:22 03:48:48Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
45
Monitored processes
9
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2380 | C:\Users\admin\AppData\Roaming\regasms.exe | C:\Users\admin\AppData\Roaming\regasms.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: SARTEXIM SRL Integrity Level: MEDIUM Description: Outlook Express Backup plugin Exit code: 0 Version: 2.4.28.2 Modules
| |||||||||||||||
| 2484 | "C:\Windows\System32\cmd.exe" /c copy "C:\Users\admin\AppData\Roaming\regasms.exe" "C:\Users\admin\AppData\Roaming\app.exe" | C:\Windows\SysWOW64\cmd.exe | regasms.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | app.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Roaming\app.exe" | C:\Users\admin\AppData\Roaming\app.exe | cmd.exe | ||||||||||||
User: admin Company: SARTEXIM SRL Integrity Level: MEDIUM Description: Outlook Express Backup plugin Exit code: 0 Version: 2.4.28.2 Modules
| |||||||||||||||
| 2924 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp2D89.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2948 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\AppData\Roaming\app.exe" | C:\Windows\SysWOW64\cmd.exe | — | regasms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3032 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp57E5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
Total events
580
Read events
508
Write events
65
Delete events
7
Modification events
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | z93 |
Value: 7A39330044010000010000000000000000000000 | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 44010000E6240765EBDAD40100000000 | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | z93 |
Value: 7A39330044010000010000000000000000000000 | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1315897367 | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897470 | |||
| (PID) Process: | (324) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
3
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 324 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR75EA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2924 | vbc.exe | C:\Users\admin\AppData\Local\Temp\bhv2E83.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\Cab691D.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\Tar691E.tmp | — | |
MD5:— | SHA256:— | |||
| 1116 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\ifycrypt8[1].exe | executable | |
MD5:— | SHA256:— | |||
| 324 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1116 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\regasms.exe | executable | |
MD5:— | SHA256:— | |||
| 324 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\INV.00563473.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2644 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E0F5C59F9FA661F6F4C50B87FEF3A15A | binary | |
MD5:— | SHA256:— | |||
| 2644 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1116 | EQNEDT32.EXE | GET | 200 | 217.182.138.150:80 | http://nexio.online/docs145677433568990/ifycrypt8.exe | FR | executable | 860 Kb | malicious |
2644 | RegAsm.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
2644 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 11 b | shared |
2644 | RegAsm.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?242a72bceac47fea | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1116 | EQNEDT32.EXE | 217.182.138.150:80 | nexio.online | OVH SAS | FR | malicious |
2644 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
2644 | RegAsm.exe | 64.37.52.2:587 | malwahselatan.com.my | HostDime.com, Inc. | US | malicious |
2644 | RegAsm.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
2644 | RegAsm.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nexio.online |
| malicious |
bot.whatismyipaddress.com |
| shared |
malwahselatan.com.my |
| malicious |
apps.identrust.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1116 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Possible Malicious Macro DL EXE Feb 2016 |
1116 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
1116 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2644 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
2644 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report