analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| URL: | https://onedrive.live.com/download?cid=3532DFEA8D347CCE&resid=3532DFEA8D347CCE%212331&authkey=AHyO-BBl9XHNNbI |
| Full analysis: | https://app.any.run/tasks/8db21d12-72b2-4283-8b36-cfac27bb165a |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 19, 2019, 05:58:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 785AC3DB80BDDC8D7EFCAB11A2E622FD |
| SHA1: | 36E72165897DB8A2E408F33CA24F79B342C3EF96 |
| SHA256: | C9DBCCA2E57D458BDAB4235C26F5D6EE7D73AAA5AD2E1C20408010A7B449A9B1 |
| SSDEEP: | 3:N8Ck3CTwKblv1gU0SRgDgQQ1gU0SRgAXIPgpkbsJys:2CkST/ZdGo7X7pkwgs |
MALICIOUS
Application was dropped or rewritten from another process
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1064)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3068)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
Detected artifacts of LokiBot
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
LOKIBOT was detected
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
Connects to CnC server
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
Actions looks like stealing of personal data
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2912)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3312)
- firefox.exe (PID: 2912)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
Application launched itself
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1064)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3068)
Loads DLL from Mozilla Firefox
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
Creates files in the user directory
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3212)
INFO
Reads CPU info
- firefox.exe (PID: 2912)
Application launched itself
- firefox.exe (PID: 2912)
Creates files in the user directory
- firefox.exe (PID: 2912)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2912)
Reads settings of System Certificates
- firefox.exe (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
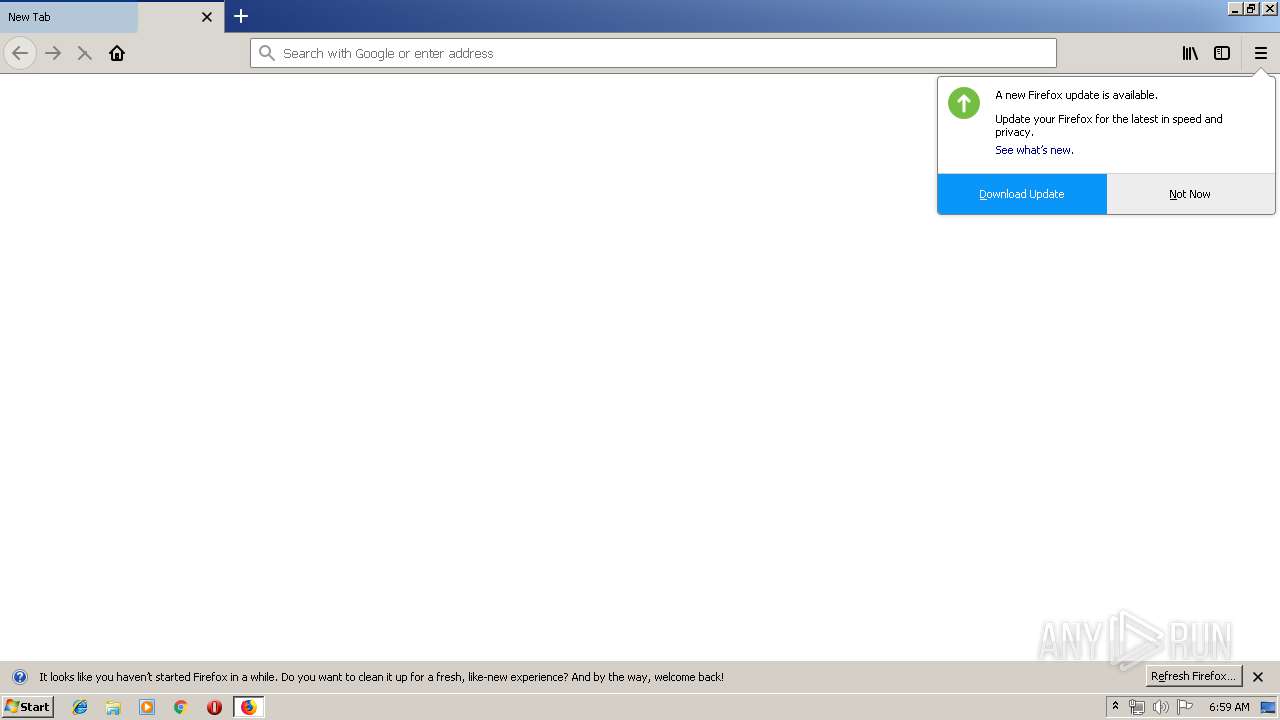
| 2912 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://onedrive.live.com/download?cid=3532DFEA8D347CCE&resid=3532DFEA8D347CCE%212331&authkey=AHyO-BBl9XHNNbI | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 65.0.2 | ||||
| 3832 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2912.0.480228716\920549496" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 2912 "\\.\pipe\gecko-crash-server-pipe.2912" 1108 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 65.0.2 | ||||
| 1080 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2912.6.2007454497\78801253" -childID 1 -isForBrowser -prefsHandle 1636 -prefMapHandle 1624 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2912 "\\.\pipe\gecko-crash-server-pipe.2912" 820 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | |
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 65.0.2 | ||||
| 1644 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2912.13.564543359\733986287" -childID 2 -isForBrowser -prefsHandle 2672 -prefMapHandle 2676 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2912 "\\.\pipe\gecko-crash-server-pipe.2912" 2688 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | |
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 65.0.2 | ||||
| 1524 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2912.20.1737298645\2117968300" -childID 3 -isForBrowser -prefsHandle 3384 -prefMapHandle 3404 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2912 "\\.\pipe\gecko-crash-server-pipe.2912" 3396 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | |
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 65.0.2 | ||||
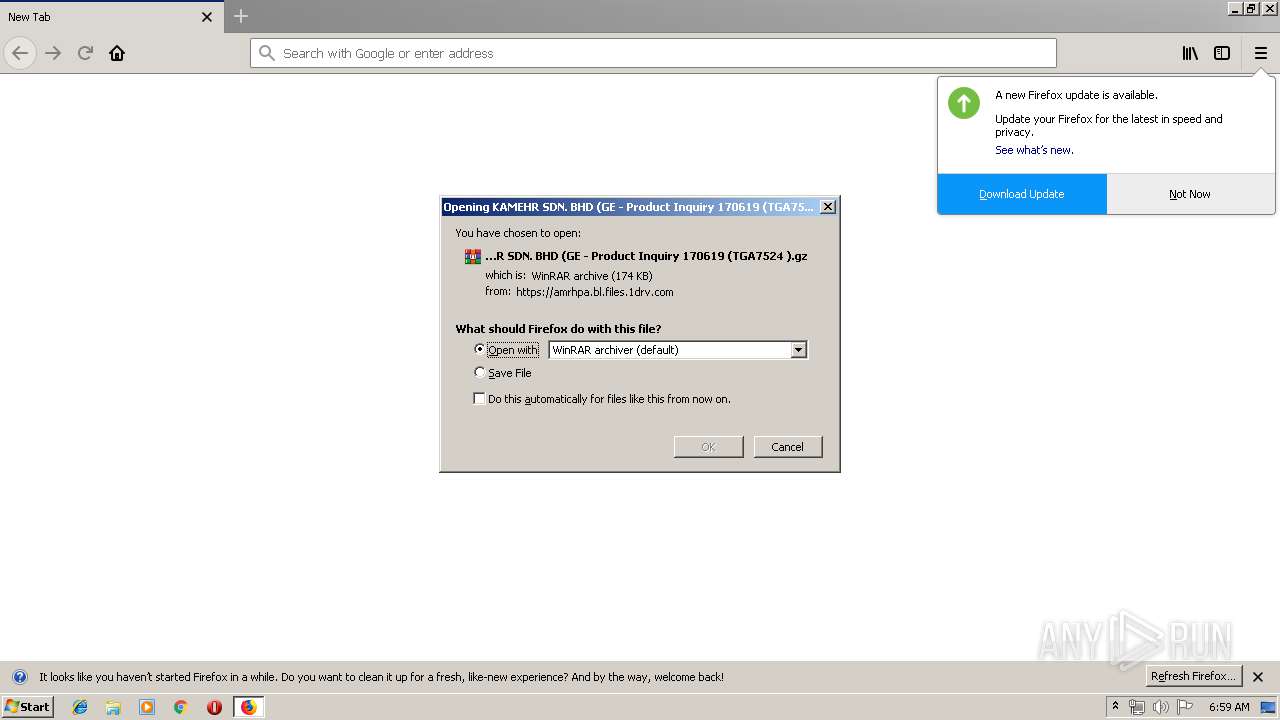
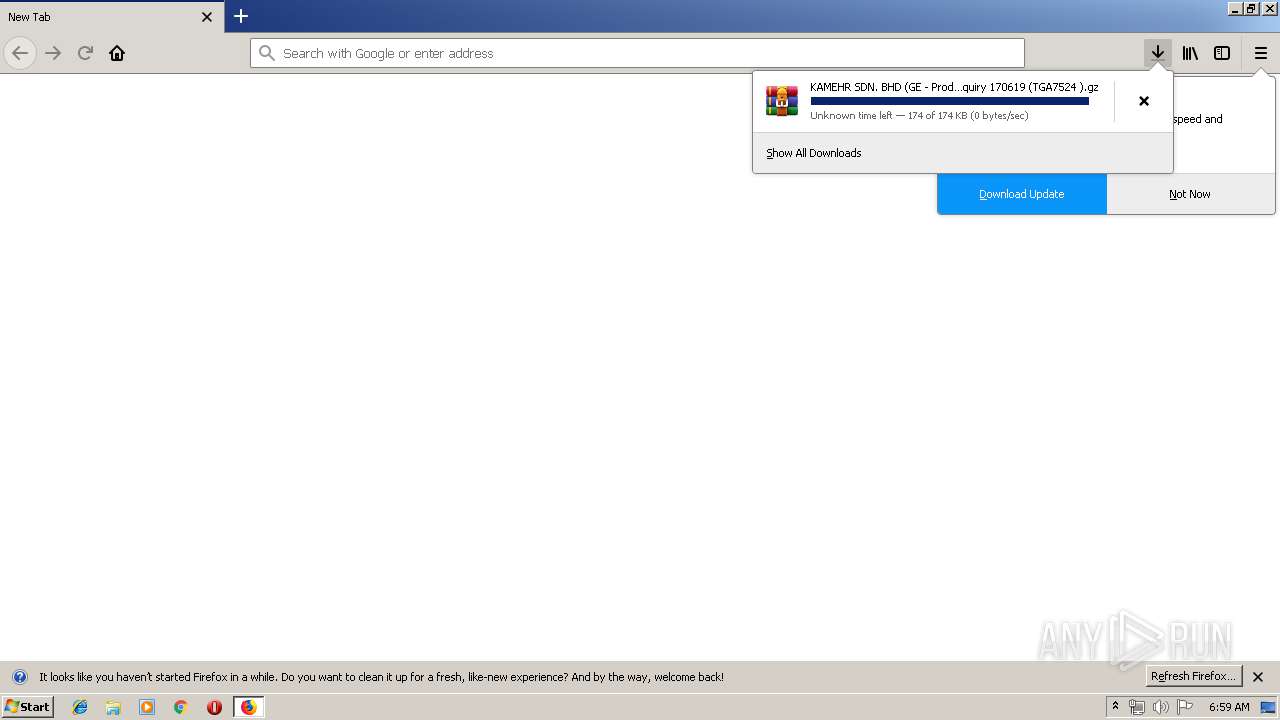
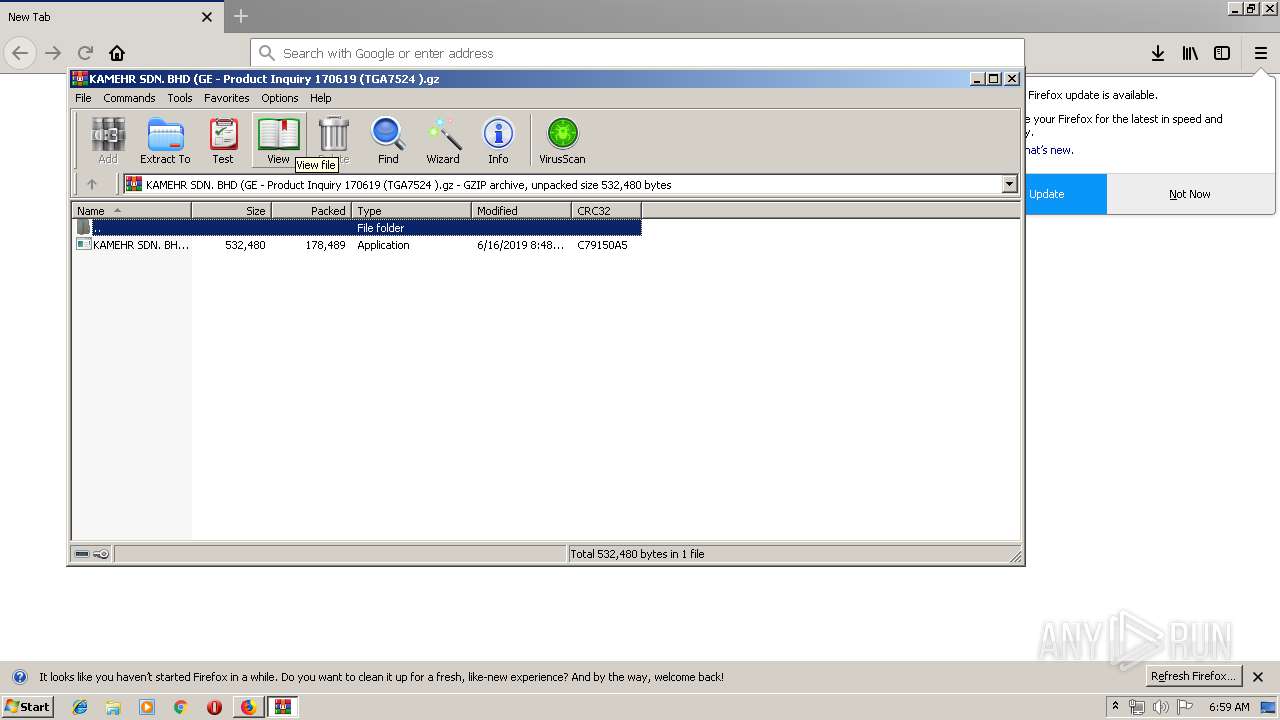
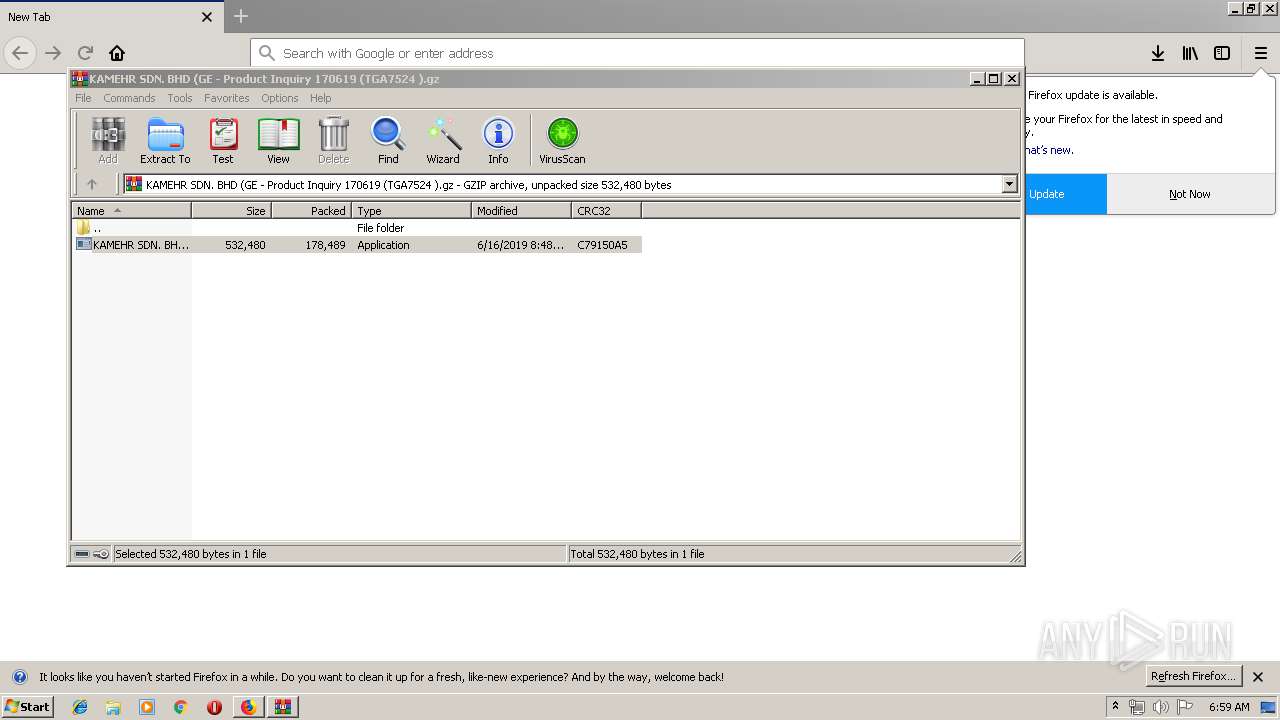
| 3312 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).gz" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.60.0 | ||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.46260\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.46260\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | — | WinRAR.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 | ||||
| 3068 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.46260\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.46260\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | — | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe |
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 | ||||
| 3212 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.46260\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.46260\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | |
User: admin Integrity Level: MEDIUM Version: 1.00 | ||||
Total events
1 725
Read events
1 695
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2912) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2912) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2912) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2912) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2912) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.gz\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).gz | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
3
Suspicious files
65
Text files
34
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db-journal | — | |
MD5:— | SHA256:— | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db | sqlite | |
MD5:501F4FD5F1B3A141B671B739BBC43421 | SHA256:7CC209BBFAD6F6E4C0D453191DD56CF32D35470939994CC574185176FC64F286 | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:82F61C08D68502377826CA7EA054CEA7 | SHA256:85801BCE5D7CE3A2ABC14E3208151AC9D324A6EA82FB2ADA1D10BAA8EF58E7DF | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\E1C11BF20450B6B2987240F50D97FD39E81D0B4A | der | |
MD5:19EACC135E7EFBDE59AC941D3536CEB4 | SHA256:6EB4764BE7BC46C9D1FFA1805CF70E5F908E8F3E18D54040EB79F61E066712F3 | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:79262A046A800BC3C3125FF94893CC51 | SHA256:EA78CB0E02CA9BD0DC9AE055B82486E63ED4643A53717970A20D5FED7D18A51E | |||
| 2912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:C52C31E2D546FC217645CD7F542CF3E0 | SHA256:73974F60357B038693803F51CA750E9ED609A3376548C88C117FA1FCBB328236 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
31
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2912 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2912 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2912 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | POST | — | 193.29.187.29:80 | http://theoutlookglow.co.ke/maxcot/Panel/fre.php | TR | — | — | malicious |
2912 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | POST | — | 193.29.187.29:80 | http://theoutlookglow.co.ke/maxcot/Panel/fre.php | TR | — | — | malicious |
2912 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2912 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2912 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2912 | firefox.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
2912 | firefox.exe | 35.244.181.201:443 | aus5.mozilla.org | — | US | suspicious |
2912 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2912 | firefox.exe | 54.190.222.97:443 | search.services.mozilla.com | Amazon.com, Inc. | US | malicious |
2912 | firefox.exe | 13.32.159.180:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2912 | firefox.exe | 54.149.115.79:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2912 | firefox.exe | 13.107.42.12:443 | amrhpa.bl.files.1drv.com | Microsoft Corporation | US | suspicious |
2912 | firefox.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2912 | firefox.exe | 13.32.158.45:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
detectportal.firefox.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
l-0004.l-msedge.net |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3212 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
7 ETPRO signatures available at the full report