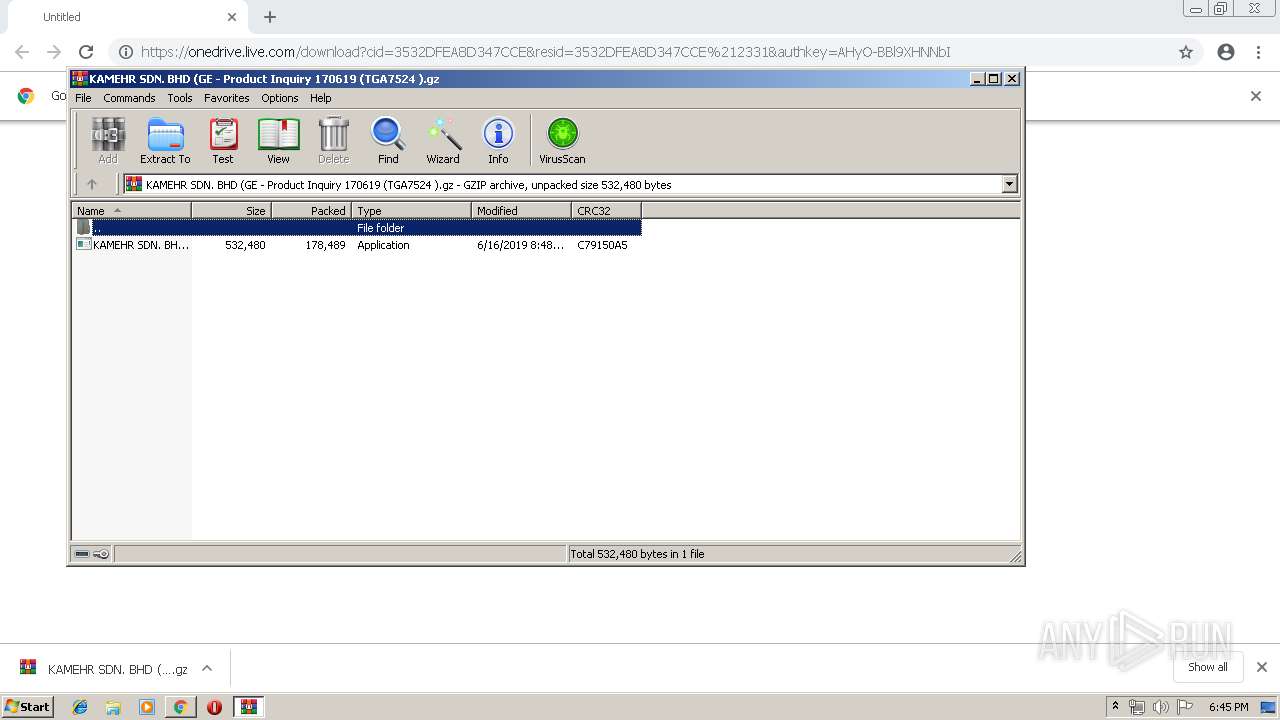
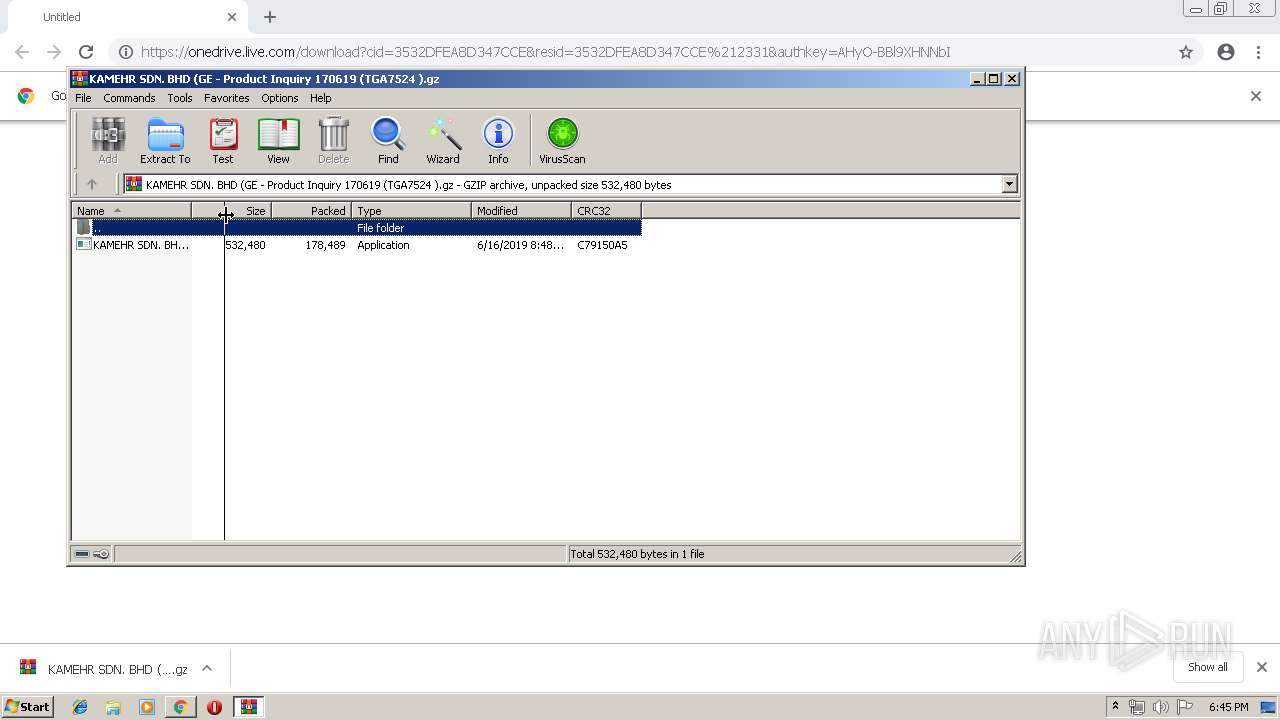
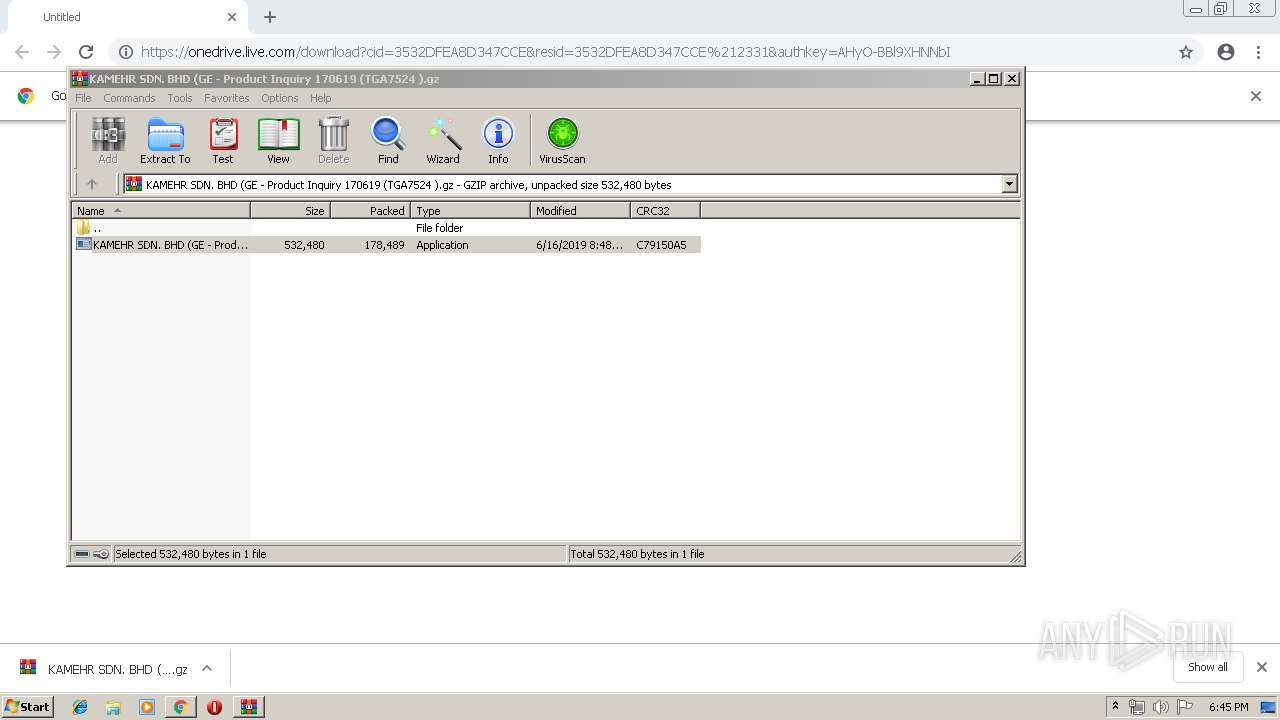
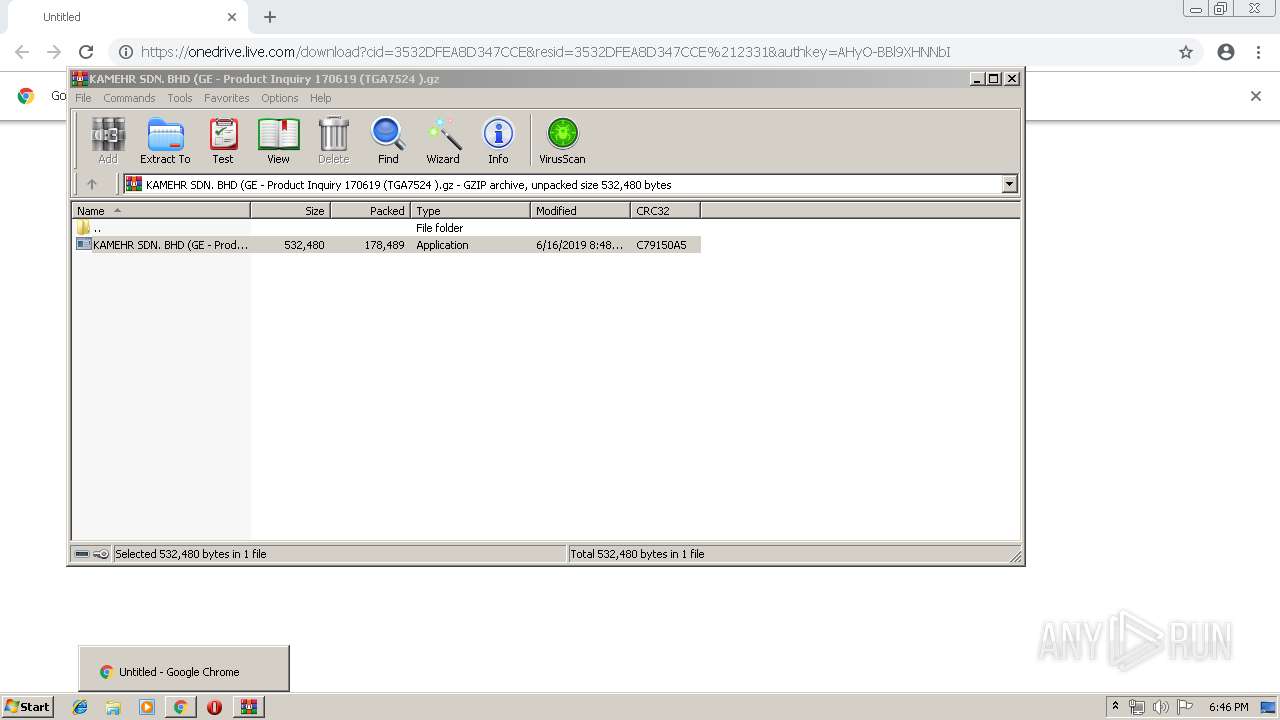
| URL: | https://onedrive.live.com/download?cid=3532DFEA8D347CCE&resid=3532DFEA8D347CCE%212331&authkey=AHyO-BBl9XHNNbI |
| Full analysis: | https://app.any.run/tasks/7b239589-4ae9-48cd-9f18-cba0c27690d5 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 18, 2019, 17:45:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 785AC3DB80BDDC8D7EFCAB11A2E622FD |
| SHA1: | 36E72165897DB8A2E408F33CA24F79B342C3EF96 |
| SHA256: | C9DBCCA2E57D458BDAB4235C26F5D6EE7D73AAA5AD2E1C20408010A7B449A9B1 |
| SSDEEP: | 3:N8Ck3CTwKblv1gU0SRgDgQQ1gU0SRgAXIPgpkbsJys:2CkST/ZdGo7X7pkwgs |
MALICIOUS
Application was dropped or rewritten from another process
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 980)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3792)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
Detected artifacts of LokiBot
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
LOKIBOT was detected
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
Connects to CnC server
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
Actions looks like stealing of personal data
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3956)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
Application launched itself
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 3792)
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 980)
Loads DLL from Mozilla Firefox
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
Creates files in the user directory
- KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe (PID: 1664)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 868)
Application launched itself
- chrome.exe (PID: 868)
Reads Internet Cache Settings
- chrome.exe (PID: 868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
14
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=11167921306620372008 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11167921306620372008 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://onedrive.live.com/download?cid=3532DFEA8D347CCE&resid=3532DFEA8D347CCE%212331&authkey=AHyO-BBl9XHNNbI | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 980 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3956.45752\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3956.45752\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10302654564132382749 --mojo-platform-channel-handle=1800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=15907371985053690175 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15907371985053690175 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2124 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1664 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3956.45752\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3956.45752\KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4913299141082011705 --mojo-platform-channel-handle=1824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3164041565415620397 --mojo-platform-channel-handle=4132 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ea50f18,0x6ea50f28,0x6ea50f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 328
Read events
1 252
Write events
73
Delete events
3
Modification events
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 868-13205353537805500 |
Value: 259 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
26
Text files
57
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
16
DNS requests
11
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | POST | — | 193.29.187.29:80 | http://theoutlookglow.co.ke/maxcot/Panel/fre.php | TR | — | — | malicious |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | POST | — | 193.29.187.29:80 | http://theoutlookglow.co.ke/maxcot/Panel/fre.php | TR | — | — | malicious |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | POST | — | 193.29.187.29:80 | http://theoutlookglow.co.ke/maxcot/Panel/fre.php | TR | — | — | malicious |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | POST | — | 193.29.187.29:80 | http://theoutlookglow.co.ke/maxcot/Panel/fre.php | TR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
868 | chrome.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
868 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
868 | chrome.exe | 13.107.42.12:443 | amrhpa.bl.files.1drv.com | Microsoft Corporation | US | suspicious |
868 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
868 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | 193.29.187.29:80 | theoutlookglow.co.ke | THC Projects SRL | TR | malicious |
868 | chrome.exe | 216.58.205.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
868 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
amrhpa.bl.files.1drv.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
theoutlookglow.co.ke |
| malicious |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
1664 | KAMEHR SDN. BHD (GE - Product Inquiry 170619 (TGA7524 ).exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
4 ETPRO signatures available at the full report