| File name: | Invoice.doc |
| Full analysis: | https://app.any.run/tasks/5c4cfbd2-3197-4374-9e1f-3589622c24b7 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | April 23, 2019, 22:23:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | DB48DEB53AA74B7F496C64F0B6B57376 |
| SHA1: | 4CE470D928D82A62A92B730132DDA993ED4B0242 |
| SHA256: | C98FA0A99DE5B9720E234F6AFE60940FAE10C8A010AB43BD6B68DD3398F2B870 |
| SSDEEP: | 24576:cHqSe9lnP5Sbba9lDuS7TzbRsqNMEhLgEYpJY+tJZ1ai4QOwu4ldTO:7 |
MALICIOUS
Application was dropped or rewritten from another process
- A.X (PID: 2780)
- A.X (PID: 3040)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3332)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 3292)
Detected Hawkeye Keylogger
- A.X (PID: 3040)
Changes the autorun value in the registry
- A.X (PID: 3040)
Actions looks like stealing of personal data
- vbc.exe (PID: 3512)
Changes settings of System certificates
- A.X (PID: 3040)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 3664)
- A.X (PID: 2780)
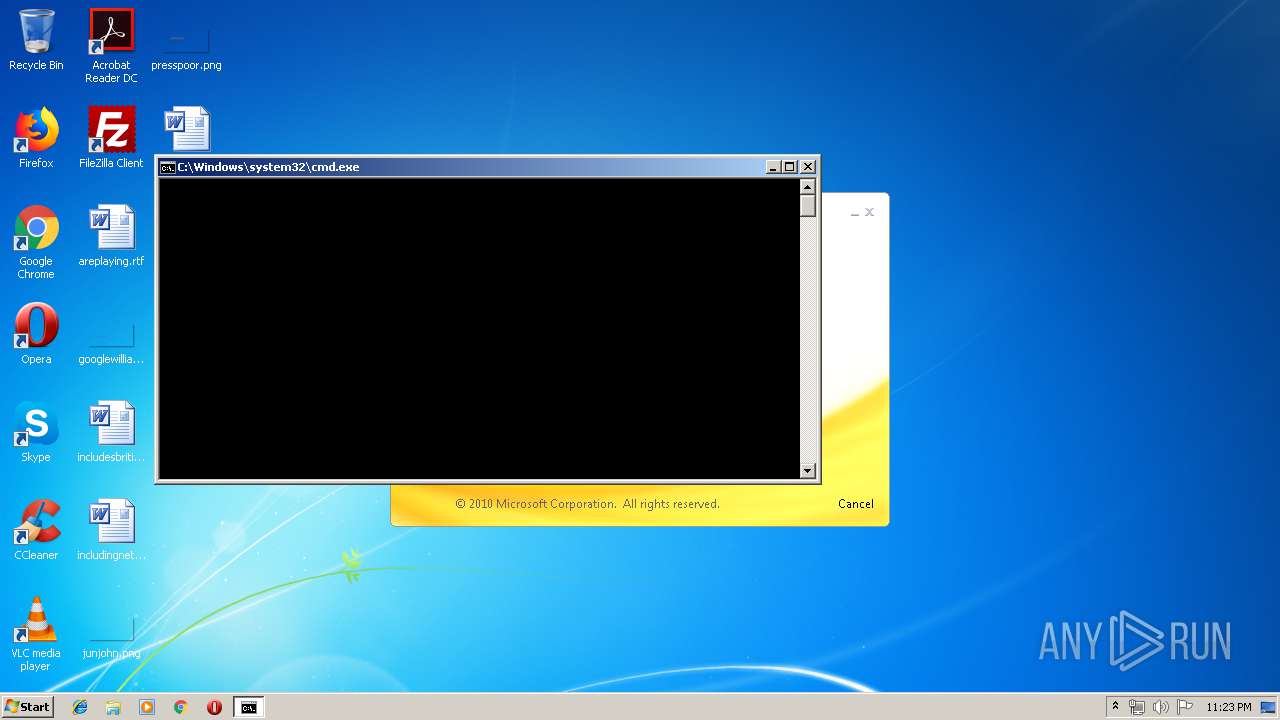
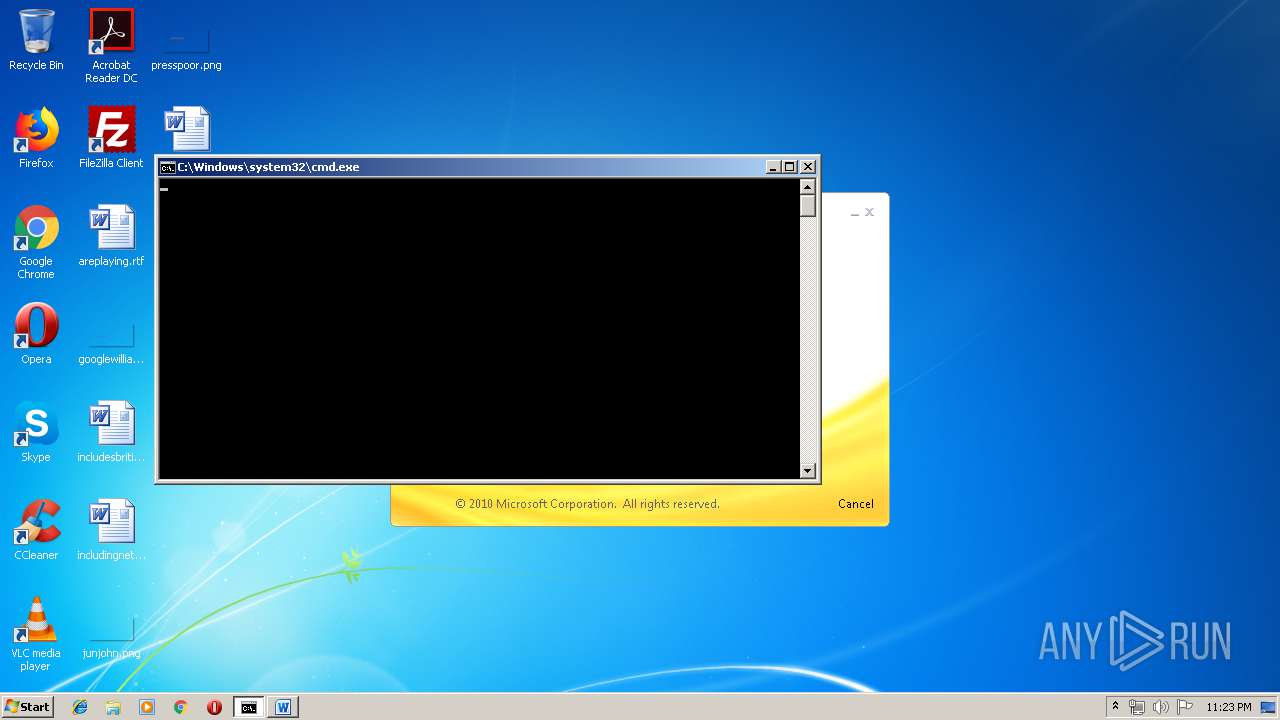
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 3332)
Application launched itself
- A.X (PID: 2780)
Creates files in the user directory
- A.X (PID: 3040)
Executable content was dropped or overwritten
- A.X (PID: 3040)
Executes scripts
- A.X (PID: 3040)
Checks for external IP
- A.X (PID: 3040)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3220)
Adds / modifies Windows certificates
- A.X (PID: 3040)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2932)
- WINWORD.EXE (PID: 3292)
- excelcnv.exe (PID: 1012)
Application was crashed
- EQNEDT32.EXE (PID: 3332)
- EQNEDT32.EXE (PID: 2232)
Creates files in the user directory
- WINWORD.EXE (PID: 3292)
Reads settings of System Certificates
- A.X (PID: 3040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
45
Monitored processes
10
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2780 | C:\Users\admin\AppData\Local\Temp\A.X | C:\Users\admin\AppData\Local\Temp\A.X | — | cmd.exe | |||||||||||
User: admin Company: TEXas INStruments INCorporated Integrity Level: MEDIUM Description: tOdO: <COMpany Name> Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3040 | C:\Users\admin\AppData\Local\Temp\A.X | C:\Users\admin\AppData\Local\Temp\A.X | A.X | ||||||||||||
User: admin Company: TEXas INStruments INCorporated Integrity Level: MEDIUM Description: tOdO: <COMpany Name> Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3220 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holderwb.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | A.X | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
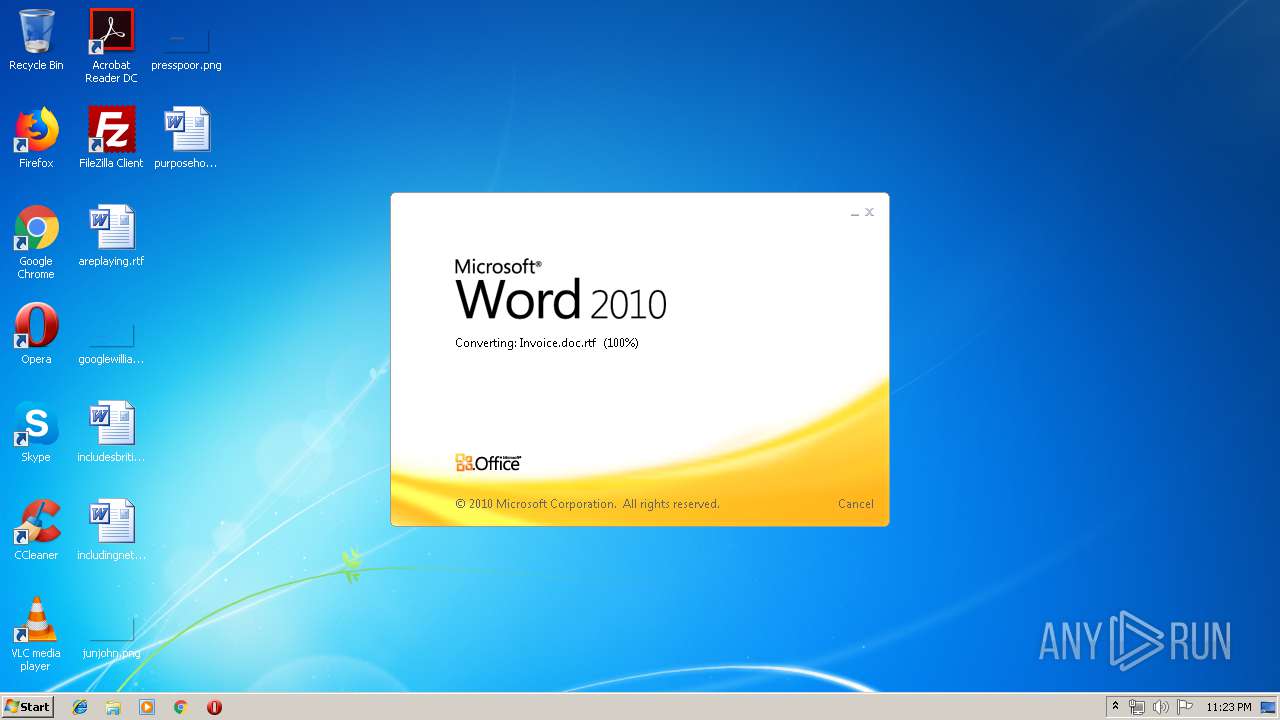
| 3292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3512 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | A.X | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3664 | cmd /c %tmp%\A.X | C:\Windows\system32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 935
Read events
1 171
Write events
744
Delete events
20
Modification events
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v.= |
Value: 762E3D00DC0C0000010000000000000000000000 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518814 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518928 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518929 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: DC0C00008619FB3923FAD40100000000 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | //= |
Value: 2F2F3D00DC0C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | //= |
Value: 2F2F3D00DC0C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5A76.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2932 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR64C7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1012 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\CVR73CA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7641F9DBBD907685.TMP | — | |
MD5:— | SHA256:— | |||
| 3512 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 3292 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\A.X | executable | |
MD5:— | SHA256:— | |||
| 3040 | A.X | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | A.X | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
3040 | A.X | 204.141.43.189:587 | smtp.zoho.com | ZOHO | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtp.zoho.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3040 | A.X | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
3040 | A.X | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report