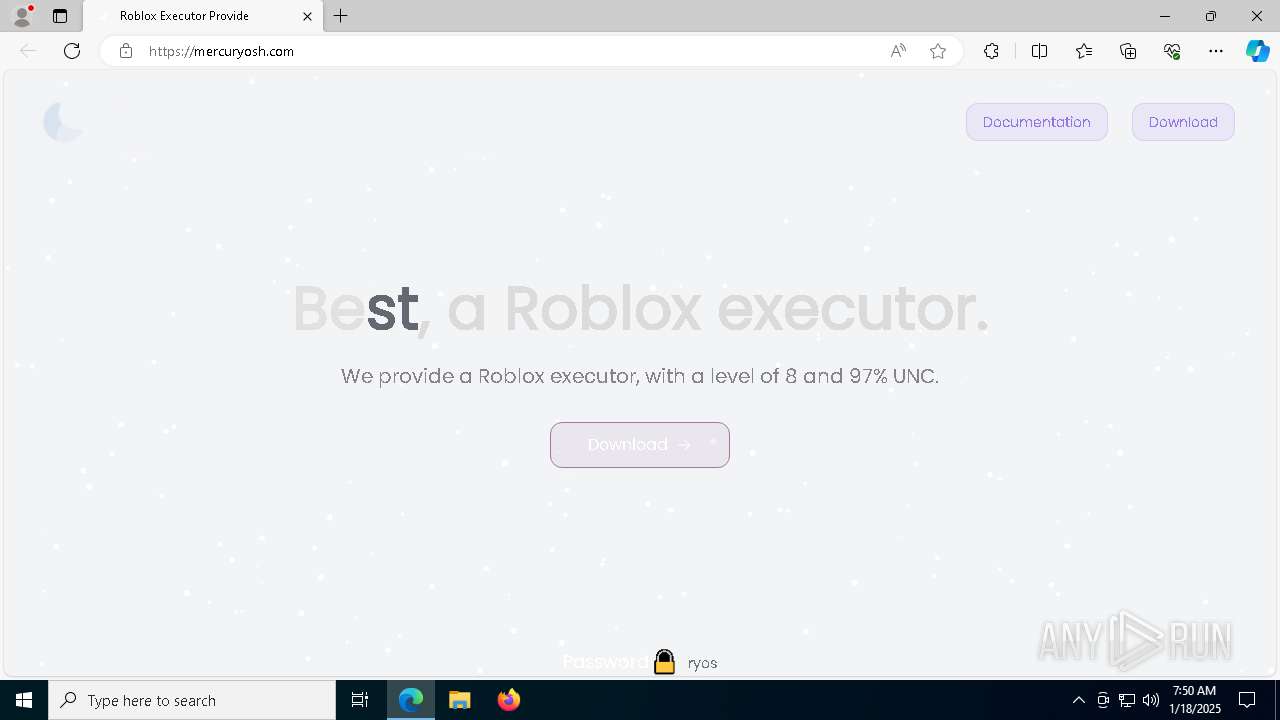
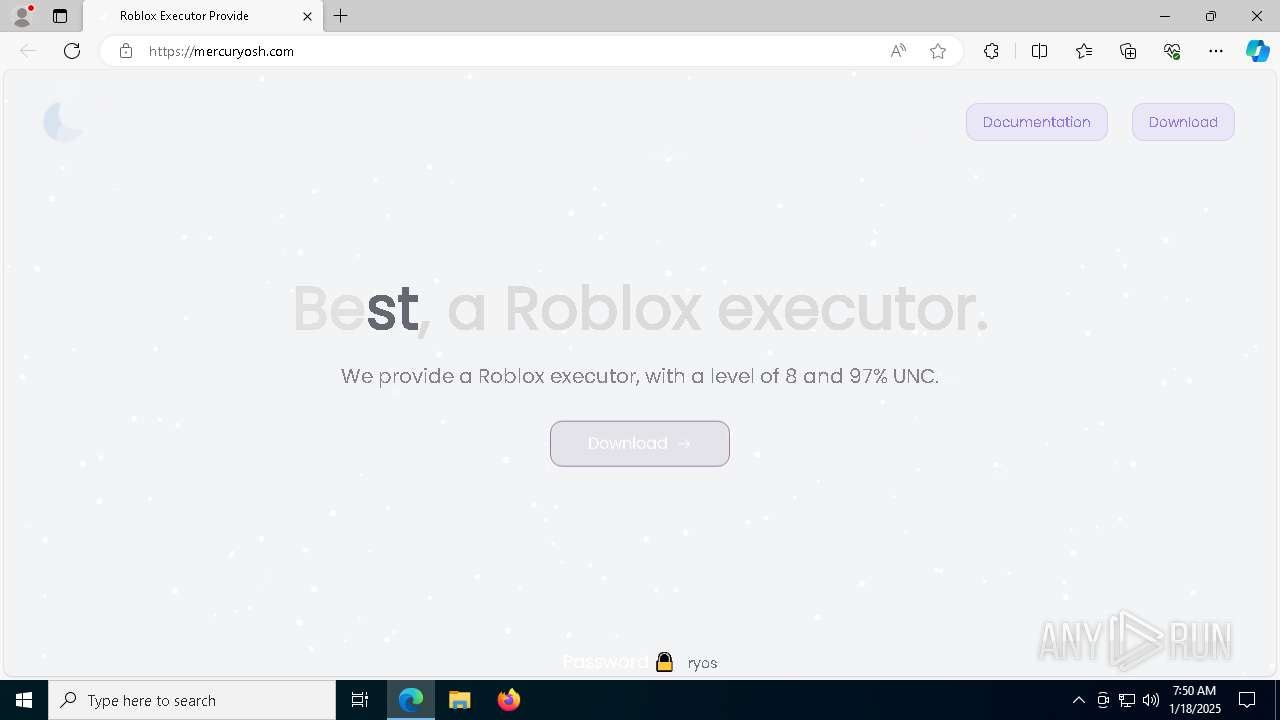
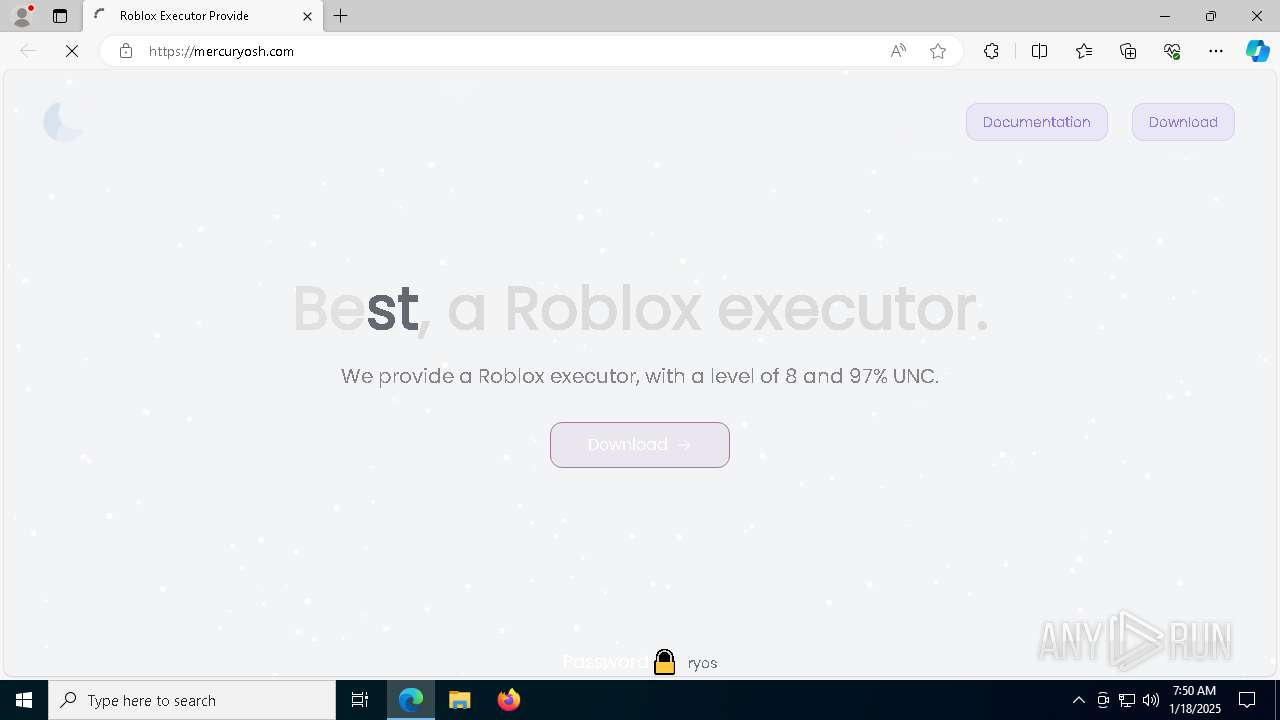
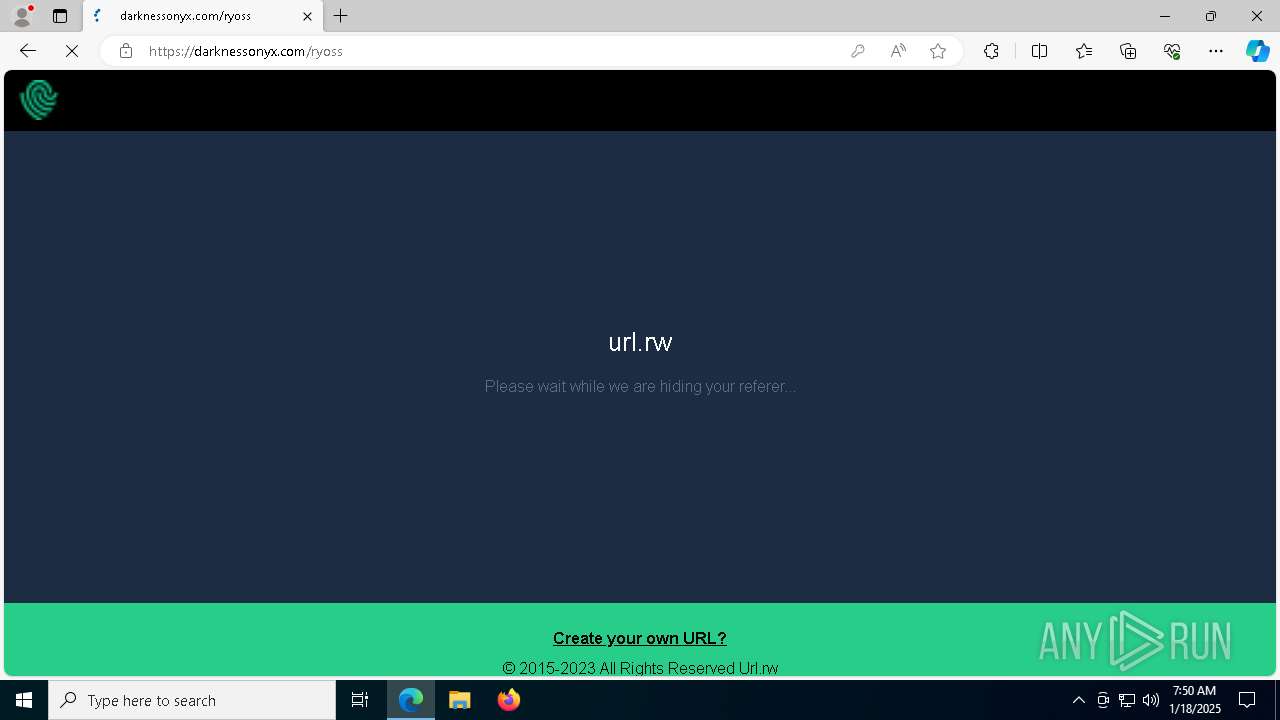
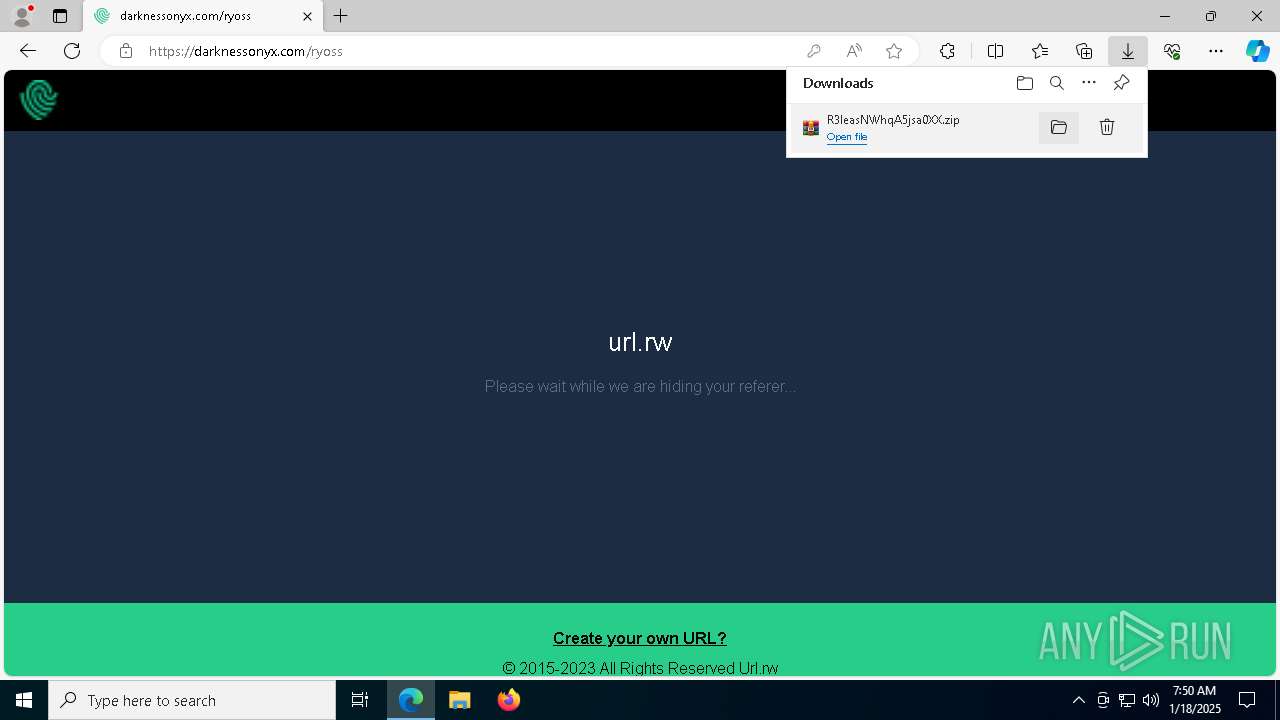
| URL: | https://mercuryosh.com/ |
| Full analysis: | https://app.any.run/tasks/49768d89-dc8f-45c1-a2c7-95f279900f10 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 18, 2025, 07:49:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BA791060250164904ADC6DDDD64B5ED5 |
| SHA1: | 216E36BD4AFCC602BB6550DBACB251D0F849236D |
| SHA256: | C96878D7F6D4505FBC38B02F826C7462E6866153F6DC70F1D221F4A402CC3268 |
| SSDEEP: | 3:N8sNHIK:2sNHIK |
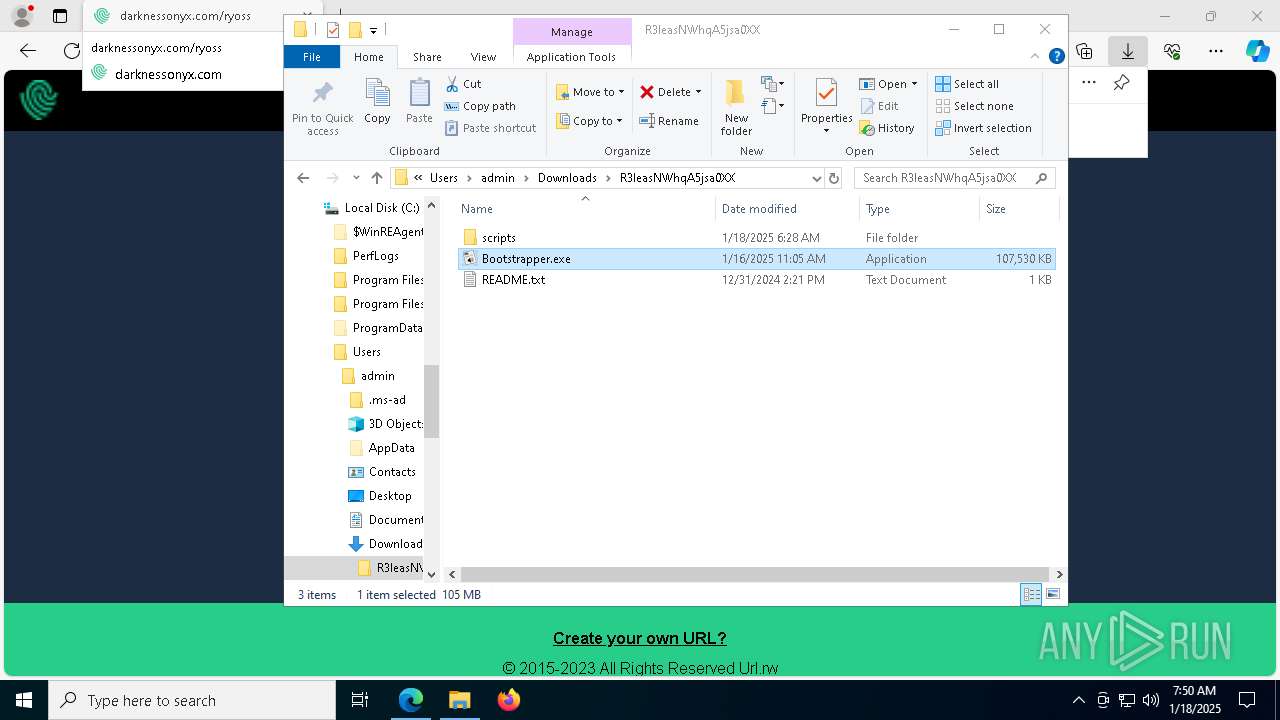
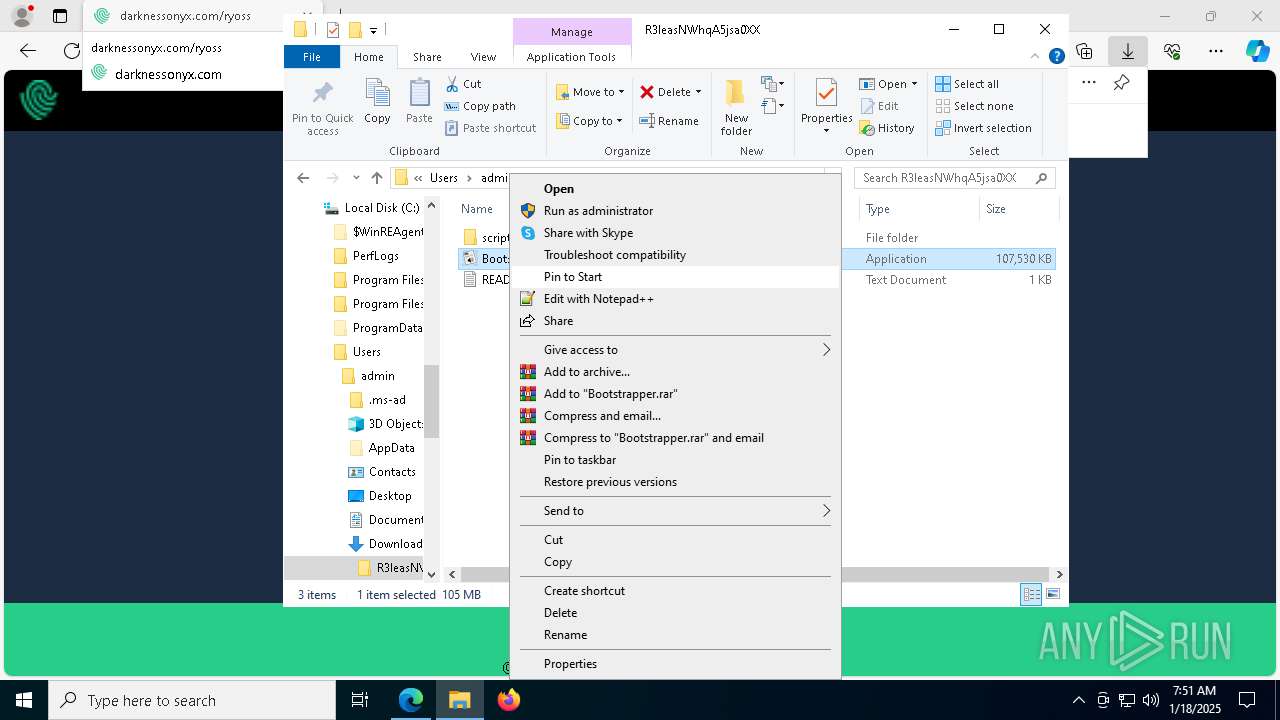
MALICIOUS
Executing a file with an untrusted certificate
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 1688)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 5568)
LUMMA mutex has been found
- Sun.com (PID: 3092)
- Sun.com (PID: 5972)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
Actions looks like stealing of personal data
- Sun.com (PID: 5972)
- Sun.com (PID: 3092)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
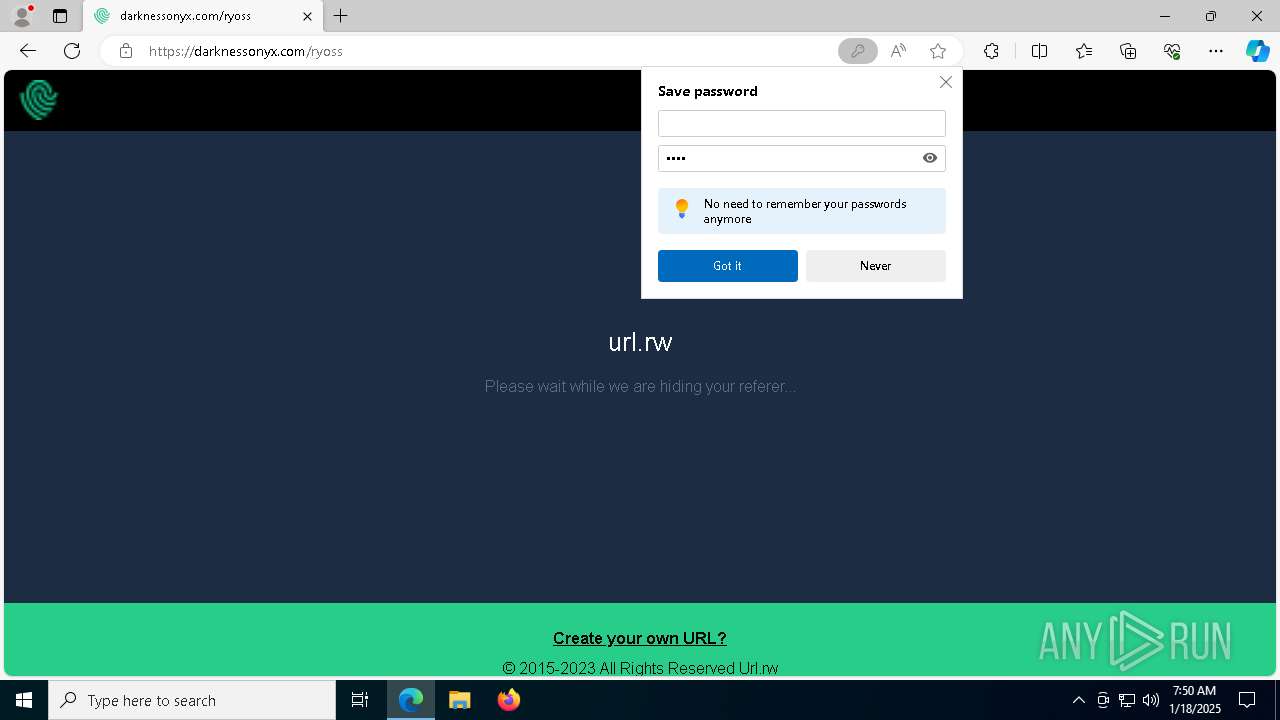
Steals credentials from Web Browsers
- Sun.com (PID: 5972)
- Sun.com (PID: 3092)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
SUSPICIOUS
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 1688)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 5568)
Executing commands from ".cmd" file
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 1688)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 5568)
Starts the AutoIt3 executable file
- cmd.exe (PID: 3188)
- cmd.exe (PID: 556)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 1476)
Get information on the list of running processes
- cmd.exe (PID: 3188)
- cmd.exe (PID: 556)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 1476)
Application launched itself
- cmd.exe (PID: 3188)
- cmd.exe (PID: 556)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 1476)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3188)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 2996)
- cmd.exe (PID: 556)
- Bootstrapper.exe (PID: 1688)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7616)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 7748)
- cmd.exe (PID: 4188)
- Bootstrapper.exe (PID: 5568)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 1476)
The executable file from the user directory is run by the CMD process
- Sun.com (PID: 3092)
- Sun.com (PID: 5972)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
- Sun.com (PID: 3144)
- Sun.com (PID: 3656)
- Sun.com (PID: 8140)
- Sun.com (PID: 6496)
Starts application with an unusual extension
- cmd.exe (PID: 3188)
- cmd.exe (PID: 556)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 1476)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3188)
- cmd.exe (PID: 556)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 1476)
Searches for installed software
- Sun.com (PID: 3092)
- Sun.com (PID: 5972)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
INFO
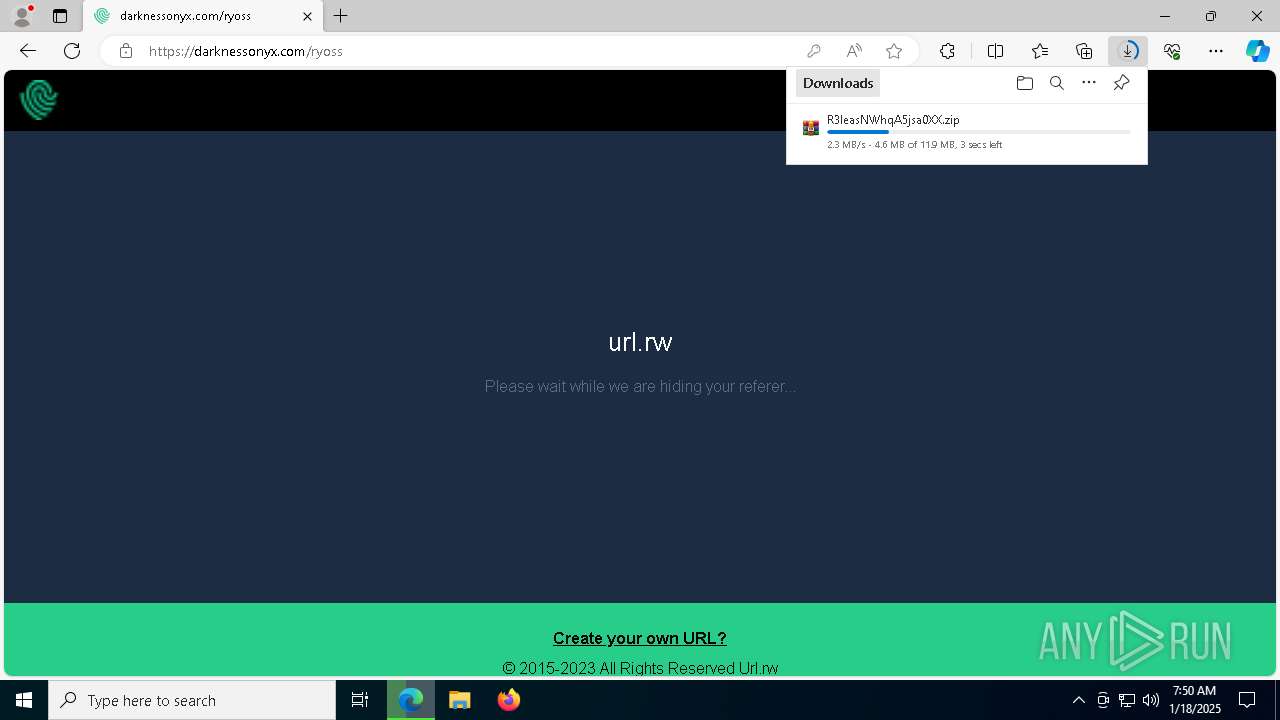
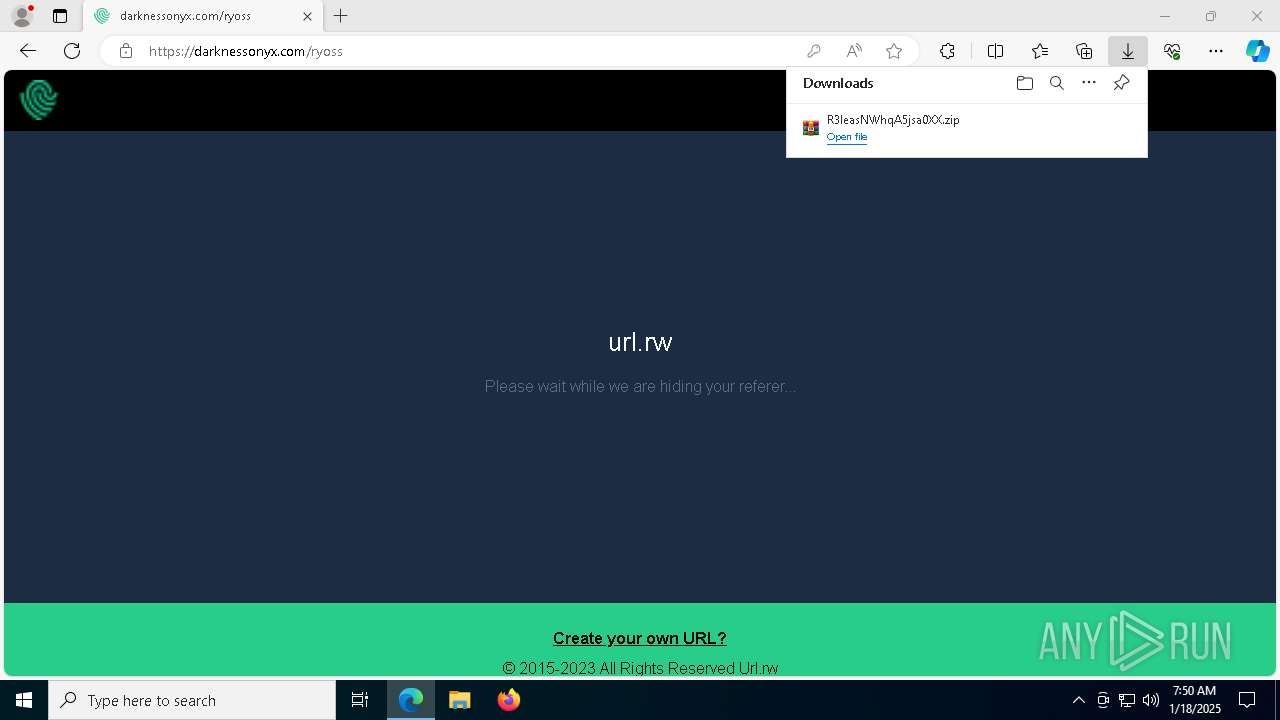
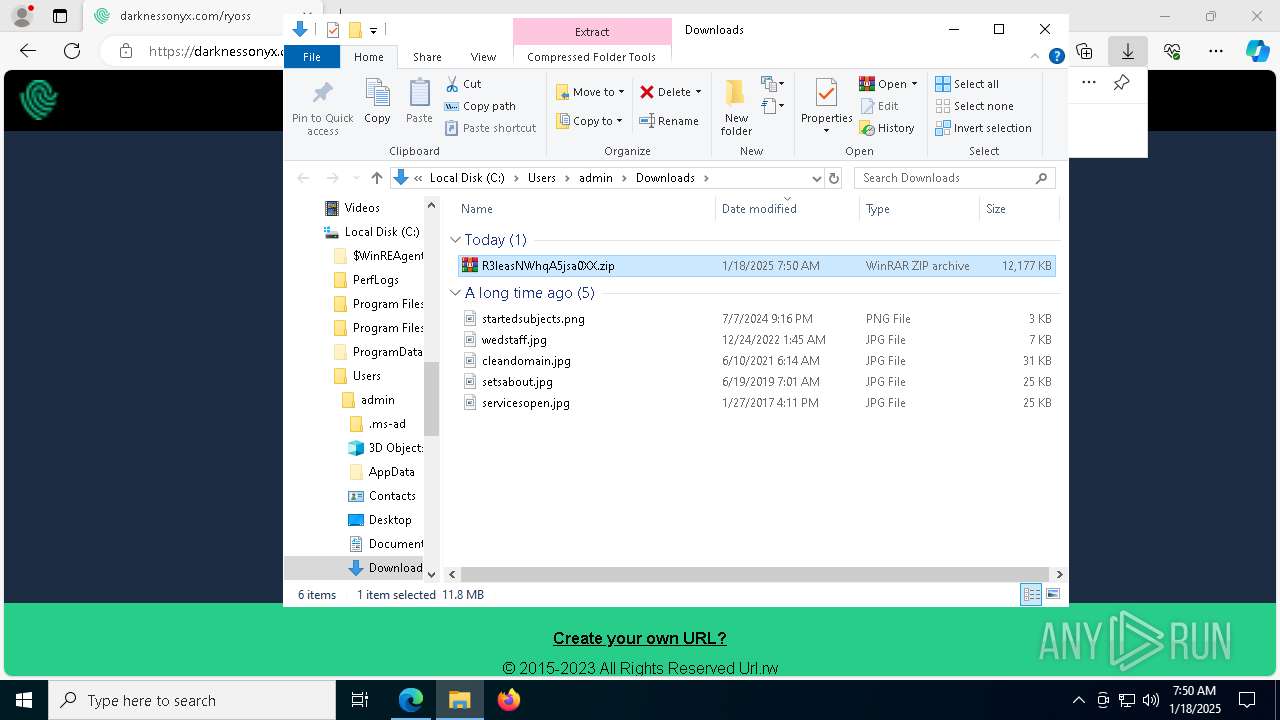
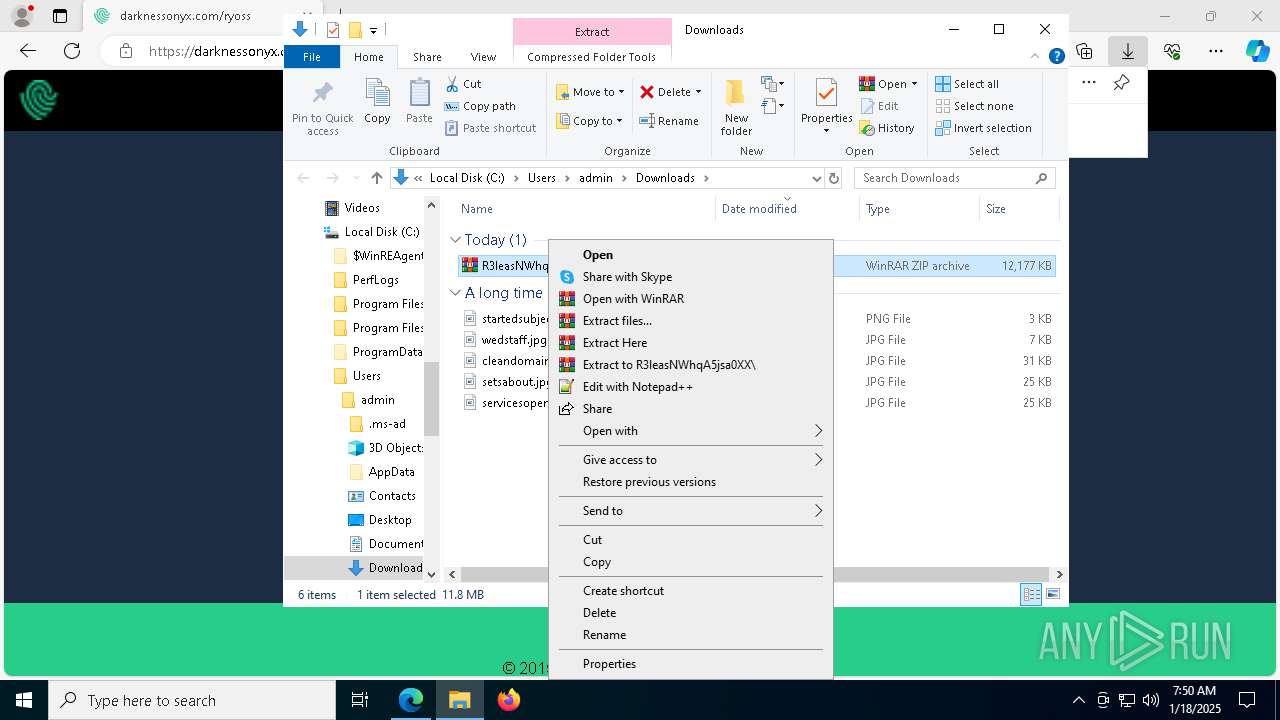
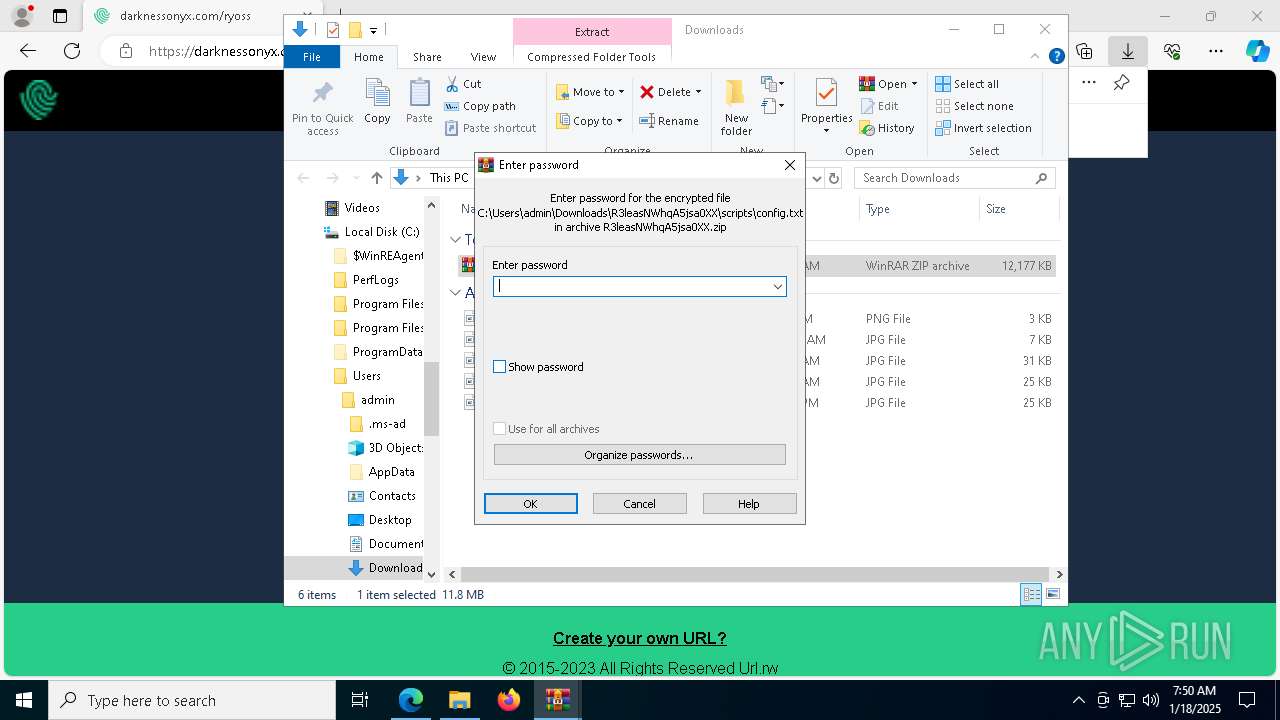
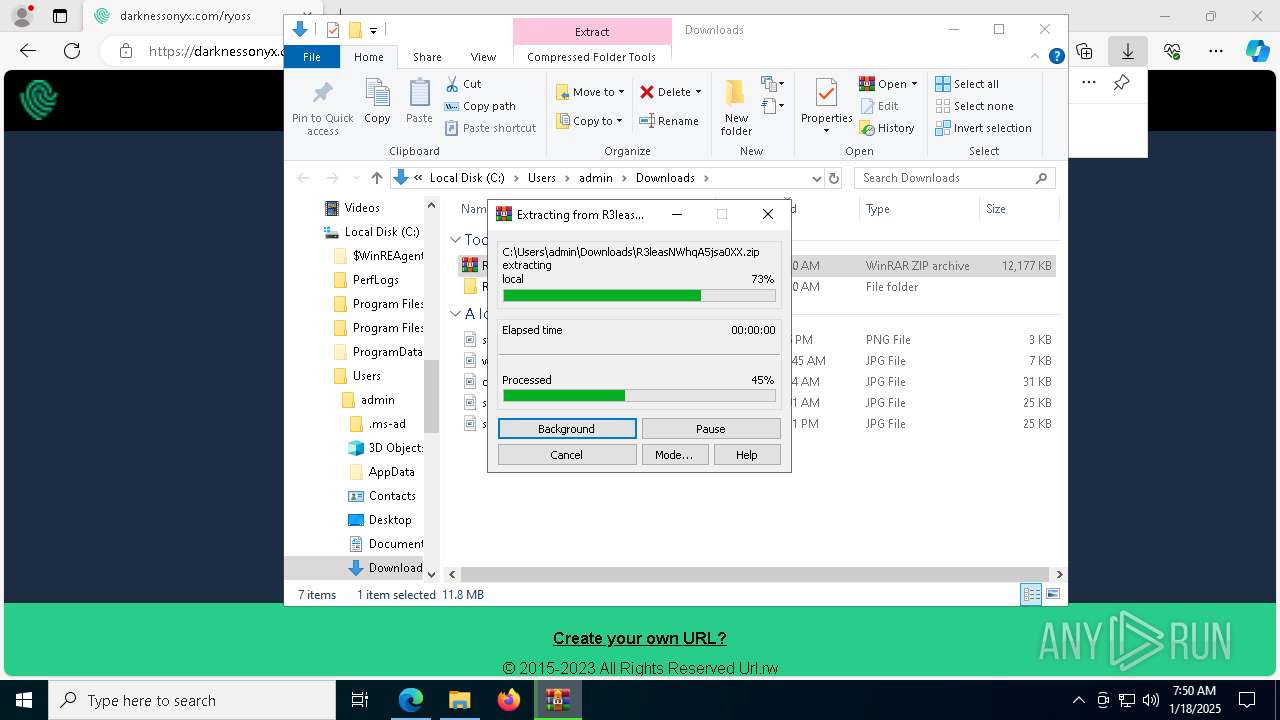
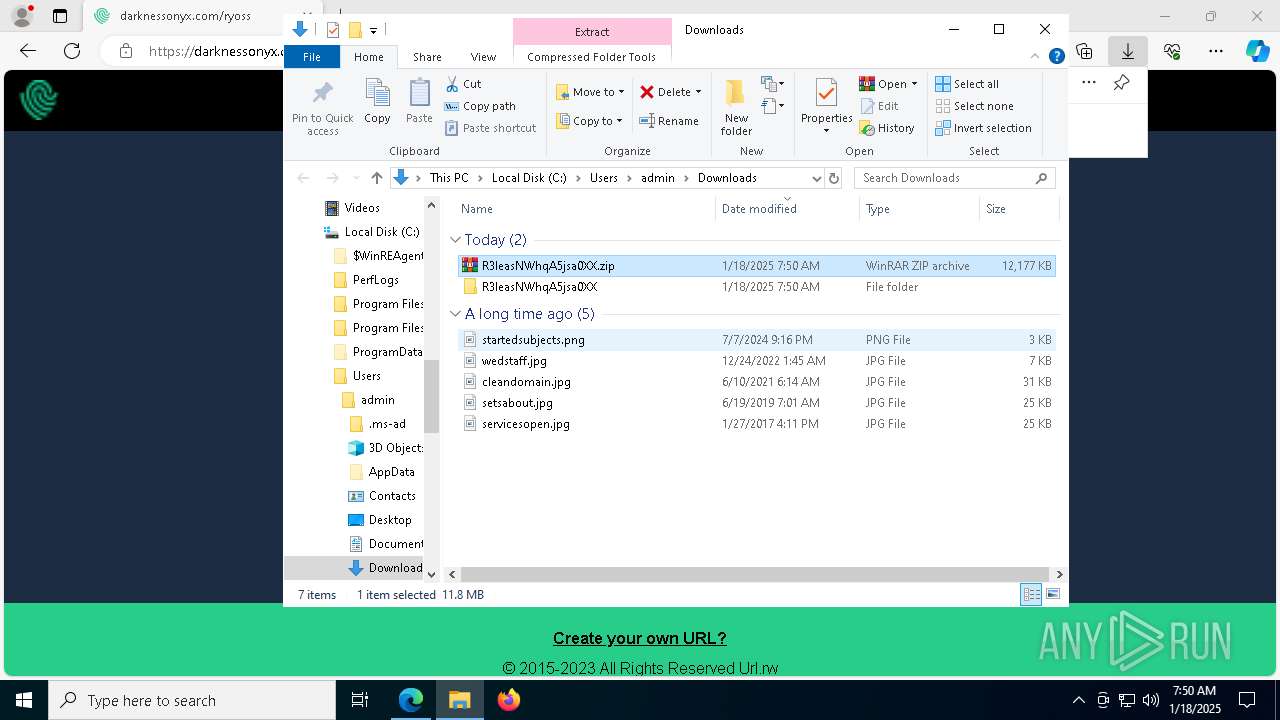
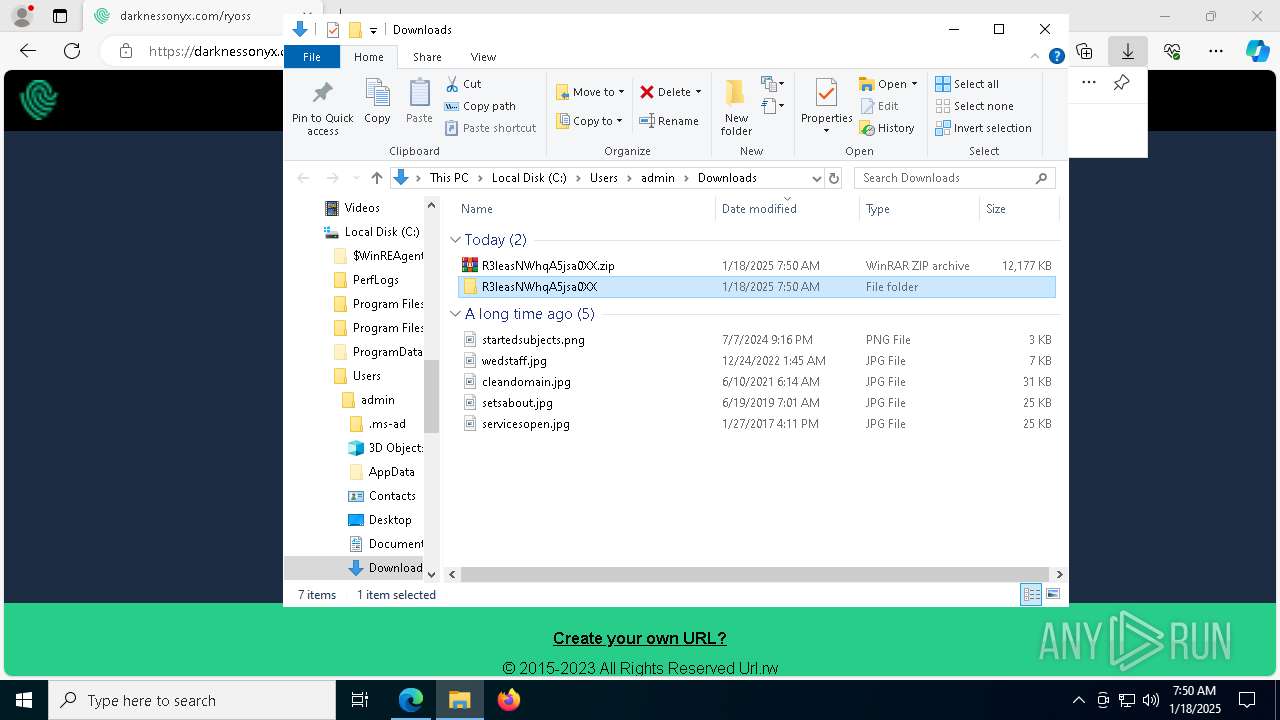
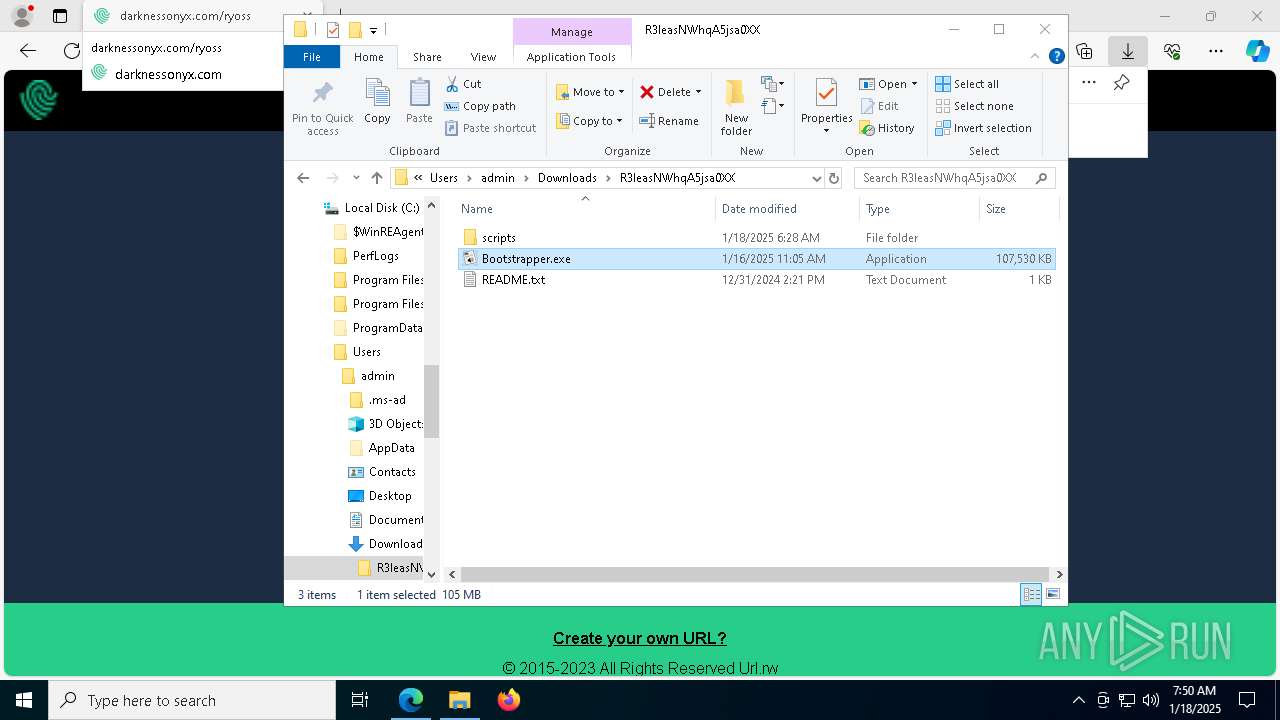
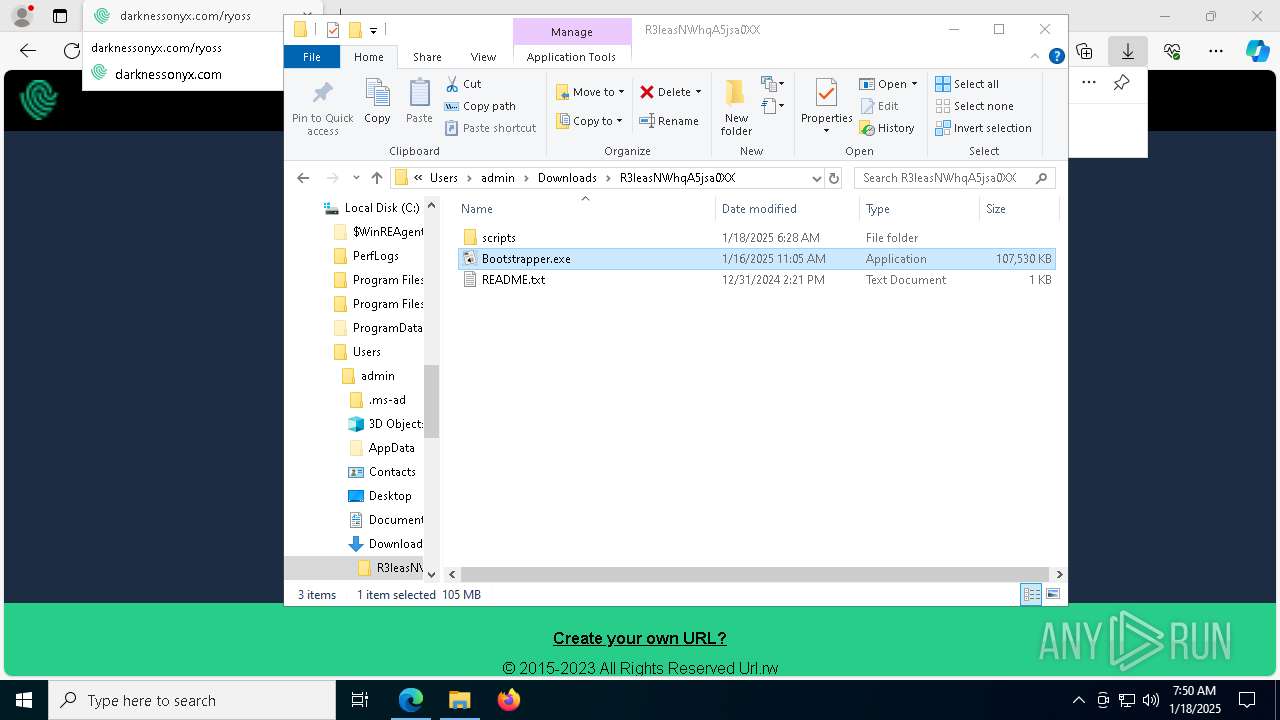
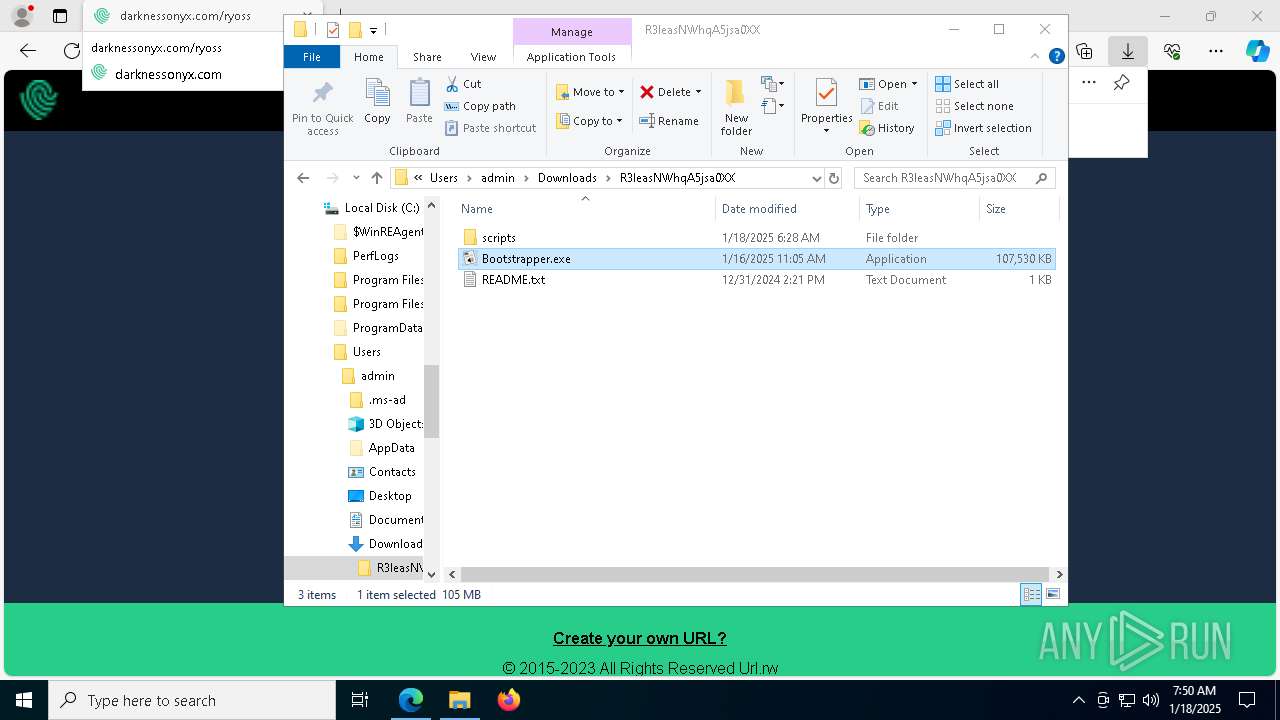
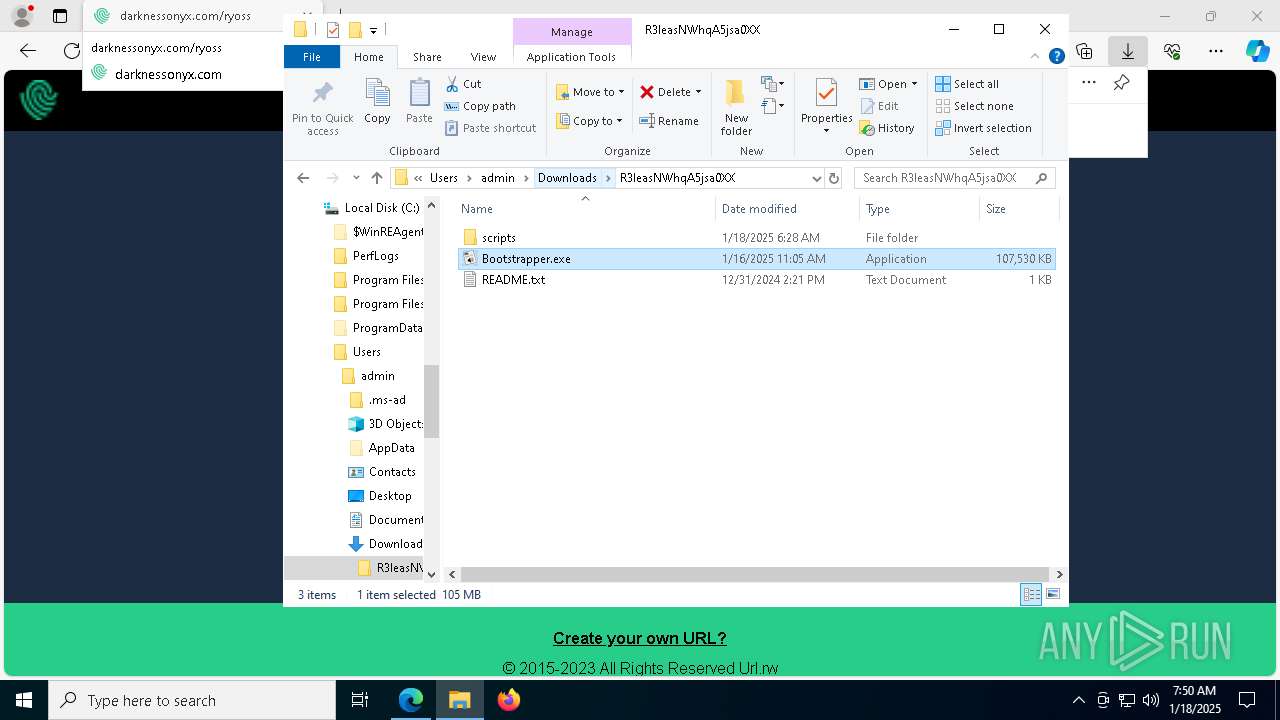
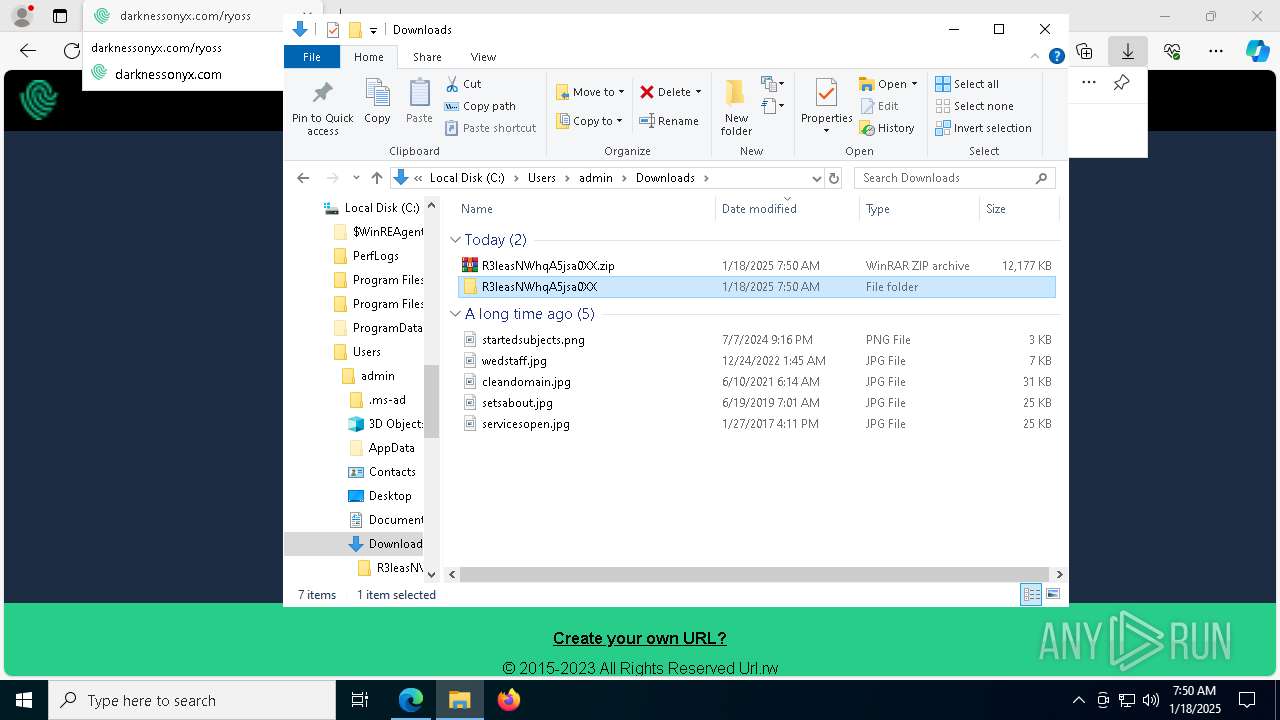
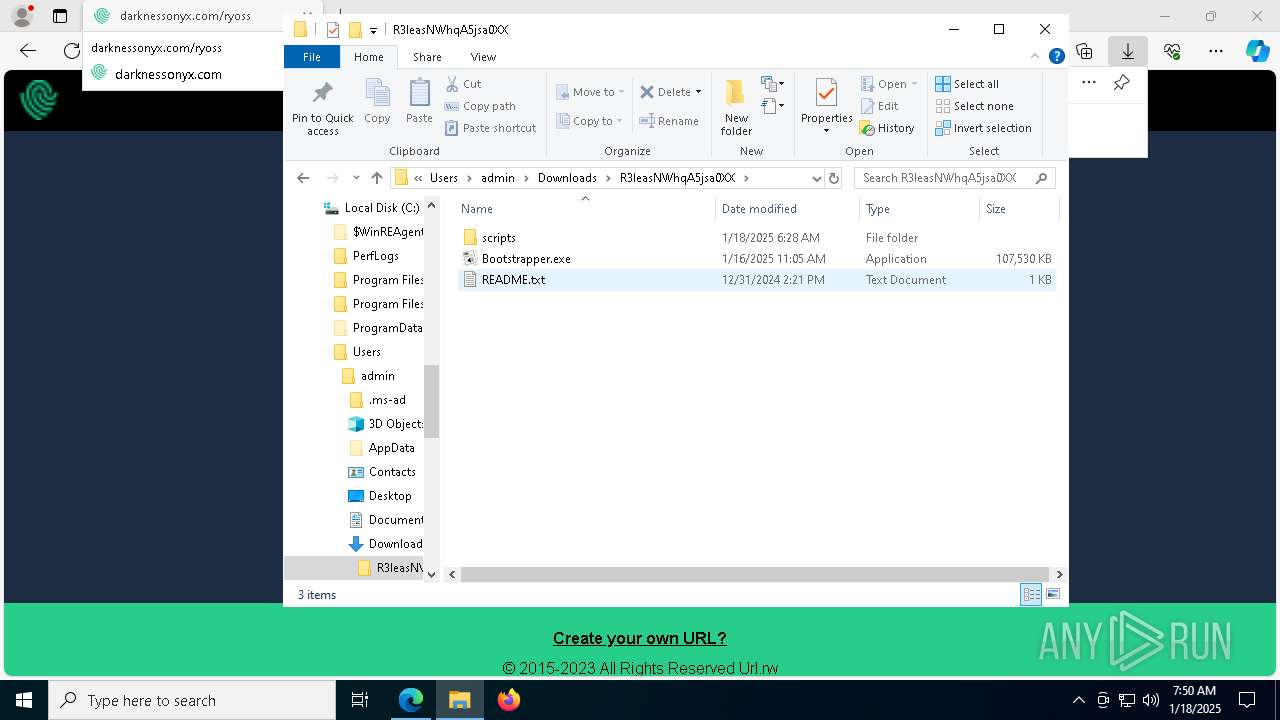
The process uses the downloaded file
- msedge.exe (PID: 5788)
- WinRAR.exe (PID: 7404)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 1688)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 5568)
Application launched itself
- msedge.exe (PID: 5764)
Reads Environment values
- identity_helper.exe (PID: 8100)
Checks supported languages
- identity_helper.exe (PID: 8100)
- Bootstrapper.exe (PID: 7568)
- extrac32.exe (PID: 7308)
- Sun.com (PID: 3092)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 2996)
- extrac32.exe (PID: 5696)
- Bootstrapper.exe (PID: 1688)
- Sun.com (PID: 5972)
- extrac32.exe (PID: 7960)
- extrac32.exe (PID: 4628)
- Sun.com (PID: 7976)
- Bootstrapper.exe (PID: 7212)
- Sun.com (PID: 7648)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 5568)
- extrac32.exe (PID: 7568)
- extrac32.exe (PID: 6976)
- extrac32.exe (PID: 4876)
- Sun.com (PID: 3144)
- Sun.com (PID: 3656)
- Sun.com (PID: 8140)
- Sun.com (PID: 6496)
- extrac32.exe (PID: 7892)
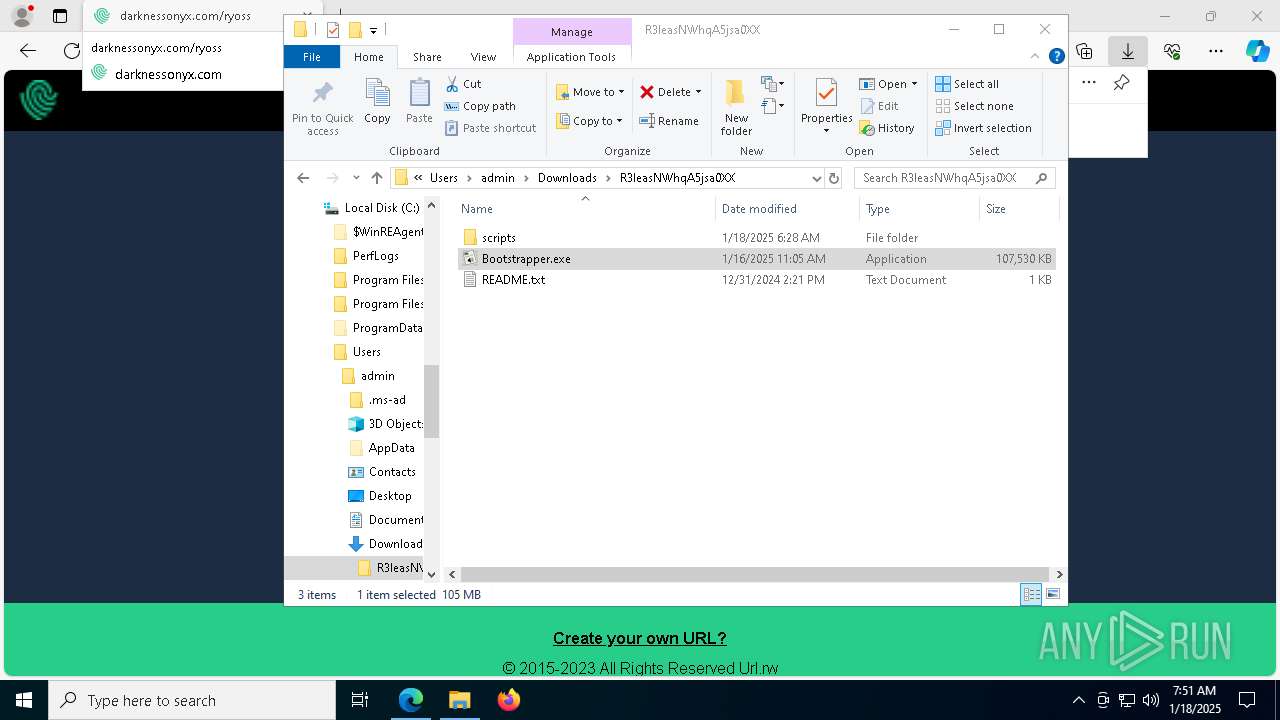
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7404)
The sample compiled with english language support
- WinRAR.exe (PID: 7404)
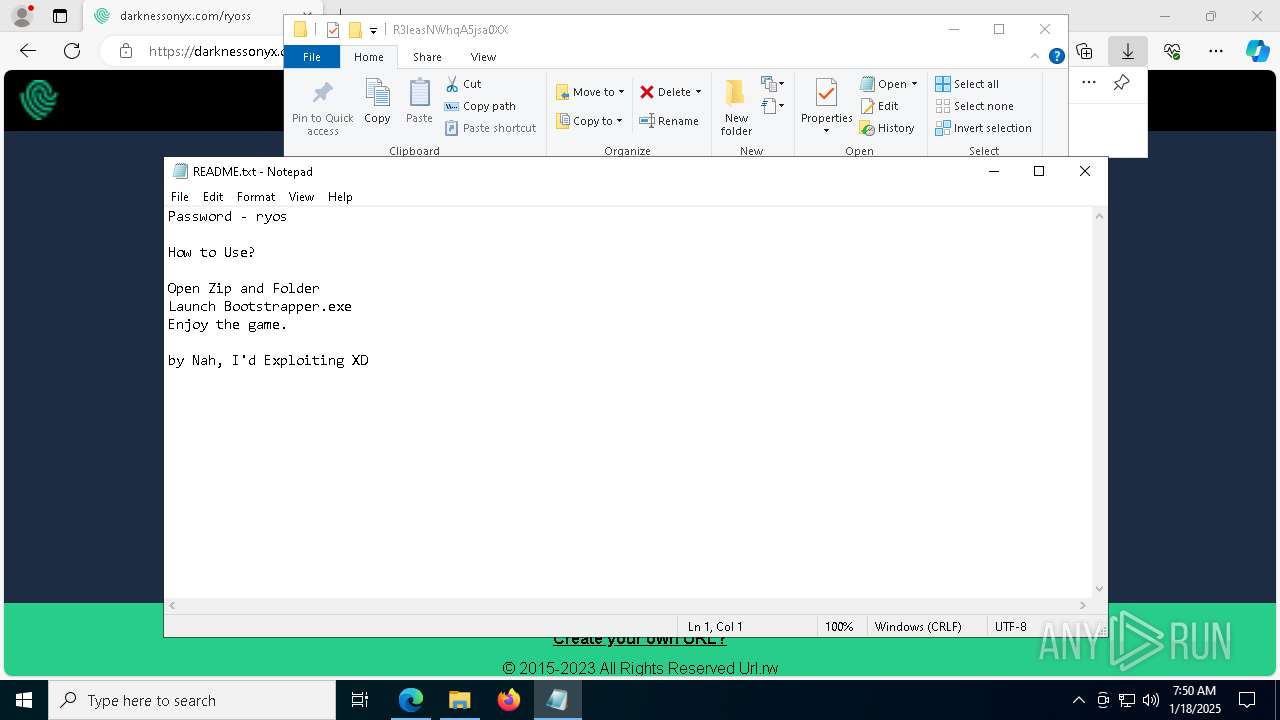
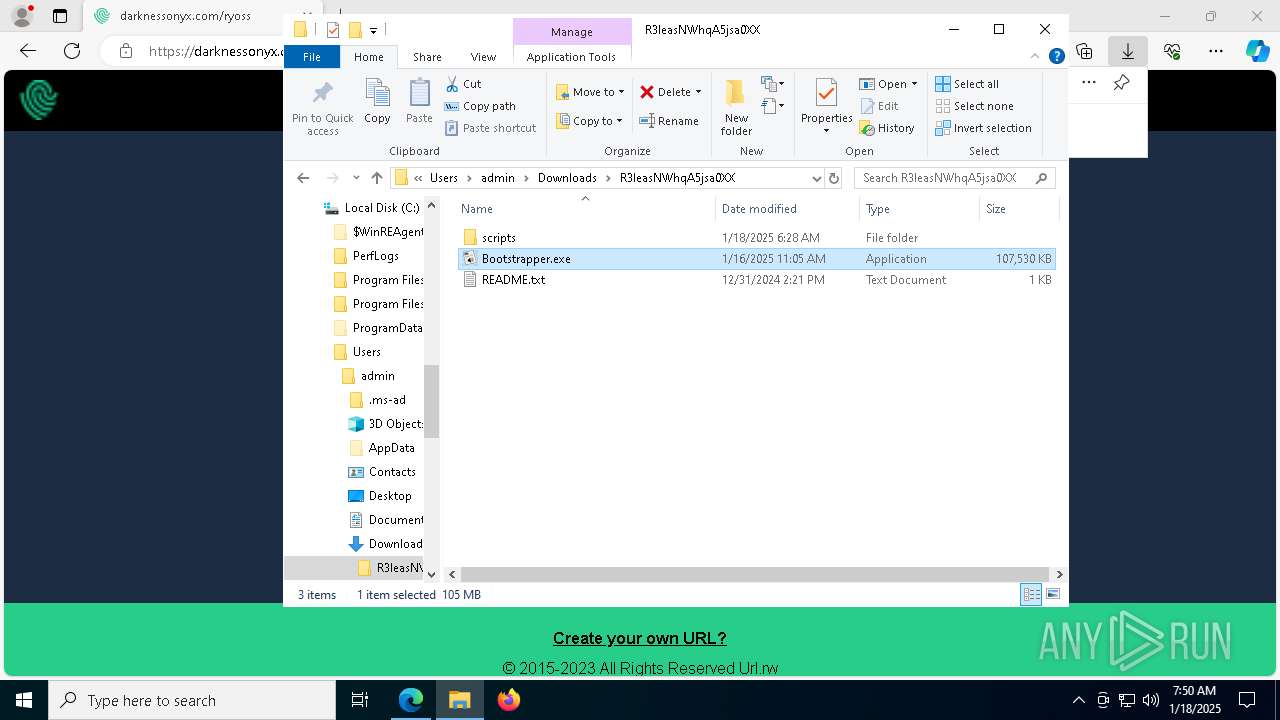
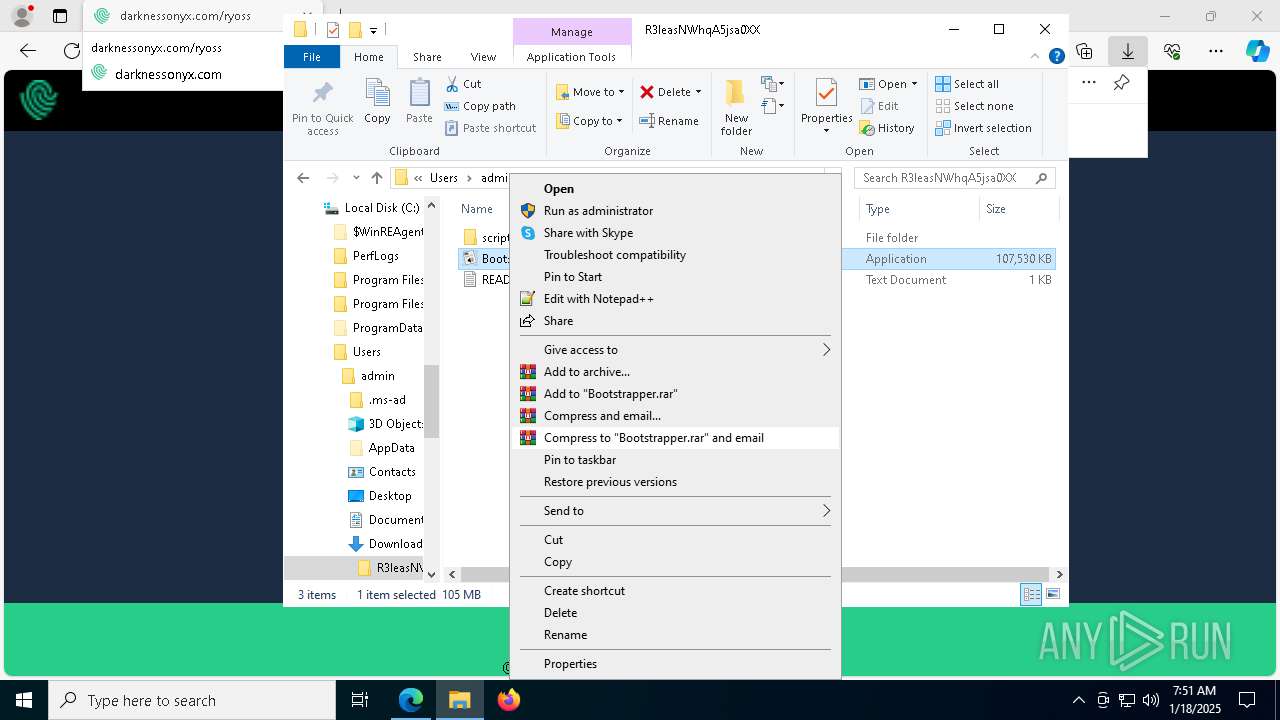
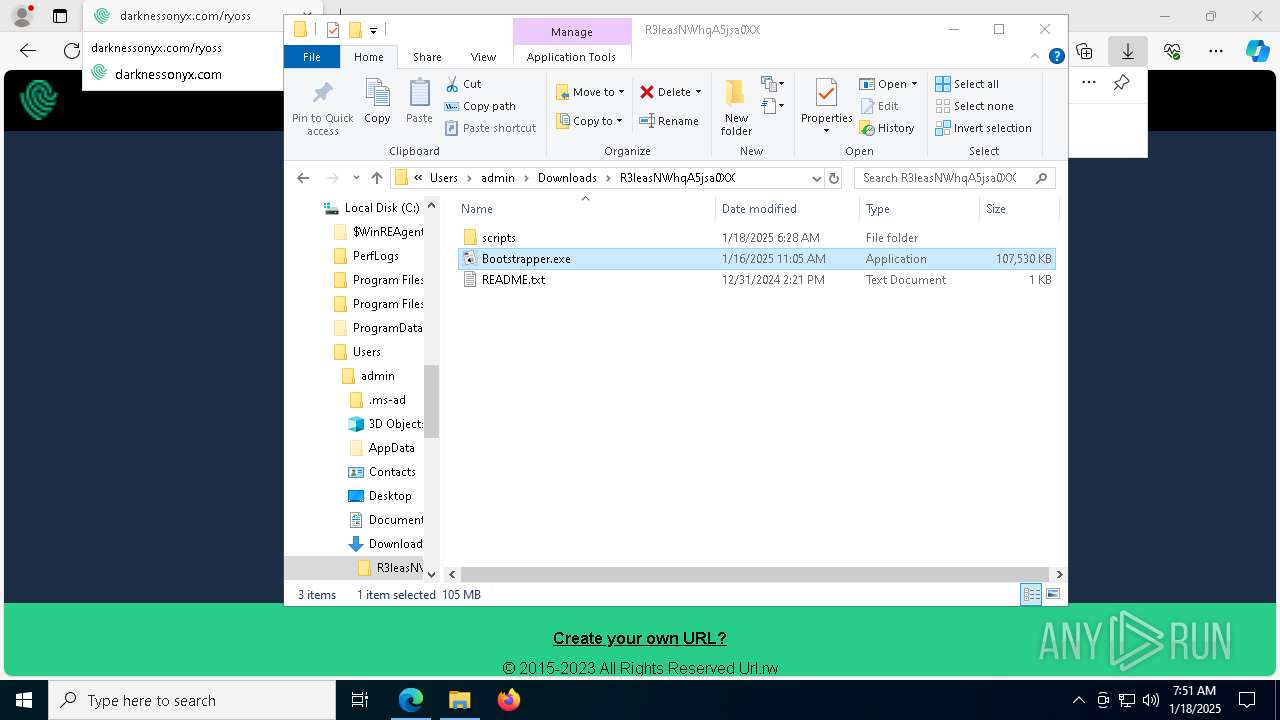
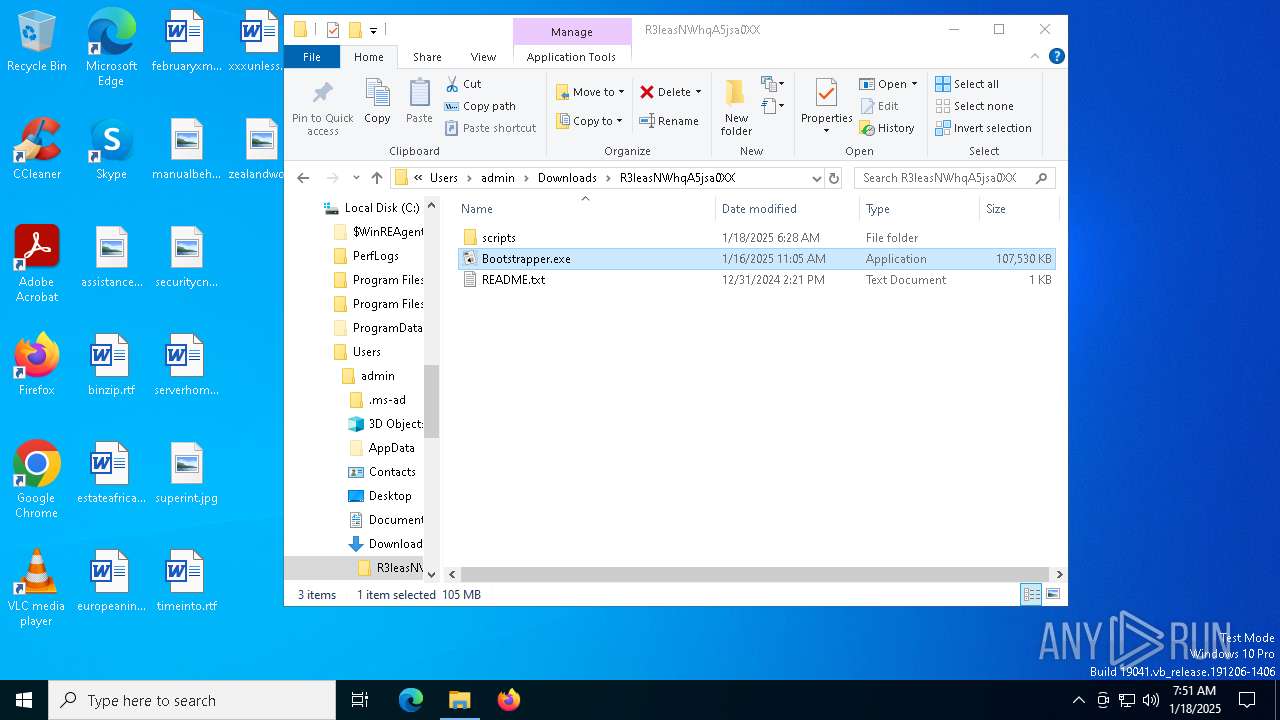
Manual execution by a user
- notepad.exe (PID: 7816)
- WinRAR.exe (PID: 7404)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 1688)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 5568)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7816)
Reads the computer name
- identity_helper.exe (PID: 8100)
- Bootstrapper.exe (PID: 7568)
- extrac32.exe (PID: 7308)
- Bootstrapper.exe (PID: 2996)
- Sun.com (PID: 3092)
- Bootstrapper.exe (PID: 8044)
- extrac32.exe (PID: 5696)
- Bootstrapper.exe (PID: 1688)
- extrac32.exe (PID: 7960)
- Sun.com (PID: 5972)
- extrac32.exe (PID: 4628)
- Sun.com (PID: 7976)
- Bootstrapper.exe (PID: 7212)
- Sun.com (PID: 7648)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 5568)
- extrac32.exe (PID: 7568)
- extrac32.exe (PID: 6976)
- extrac32.exe (PID: 4876)
- Sun.com (PID: 3144)
- Sun.com (PID: 3656)
- extrac32.exe (PID: 7892)
- Sun.com (PID: 6496)
- Sun.com (PID: 8140)
Create files in a temporary directory
- Bootstrapper.exe (PID: 7568)
- extrac32.exe (PID: 7308)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 8044)
- extrac32.exe (PID: 5696)
- Bootstrapper.exe (PID: 1688)
- extrac32.exe (PID: 7960)
- extrac32.exe (PID: 4628)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 5568)
- extrac32.exe (PID: 7568)
- extrac32.exe (PID: 4876)
- extrac32.exe (PID: 6976)
- extrac32.exe (PID: 7892)
Process checks computer location settings
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 8044)
- Bootstrapper.exe (PID: 2996)
- Bootstrapper.exe (PID: 1688)
- Bootstrapper.exe (PID: 7212)
- Bootstrapper.exe (PID: 6016)
- Bootstrapper.exe (PID: 7748)
- Bootstrapper.exe (PID: 5568)
Creates a new folder
- cmd.exe (PID: 7032)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 7816)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 1688)
Reads mouse settings
- Sun.com (PID: 3092)
- Sun.com (PID: 5972)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
- Sun.com (PID: 3144)
- Sun.com (PID: 3656)
- Sun.com (PID: 8140)
- Sun.com (PID: 6496)
Reads the software policy settings
- Sun.com (PID: 3092)
- Sun.com (PID: 5972)
- Sun.com (PID: 7976)
- Sun.com (PID: 7648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
281
Monitored processes
148
Malicious processes
21
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | "C:\Windows\System32\cmd.exe" /c move Lingerie Lingerie.cmd & Lingerie.cmd | C:\Windows\SysWOW64\cmd.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1468 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "C:\Windows\System32\cmd.exe" /c move Lingerie Lingerie.cmd & Lingerie.cmd | C:\Windows\SysWOW64\cmd.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6516 --field-trial-handle=2248,i,703226522507688984,9018332252787449714,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
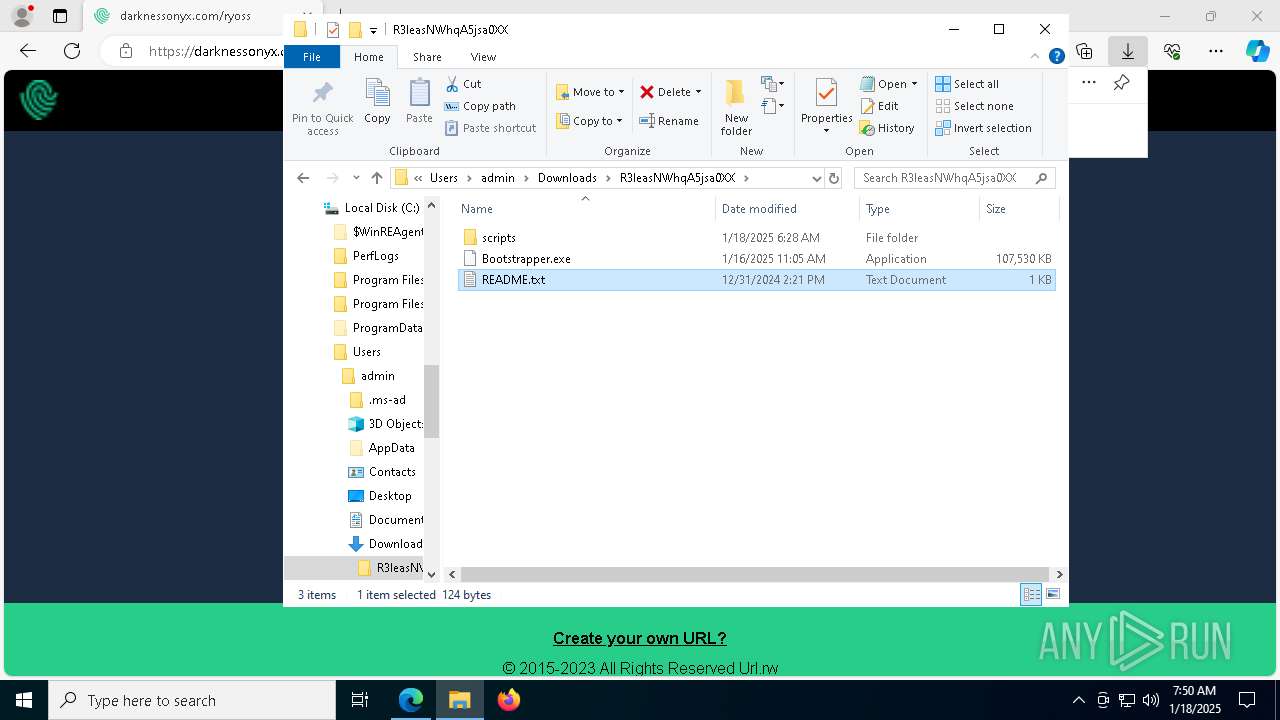
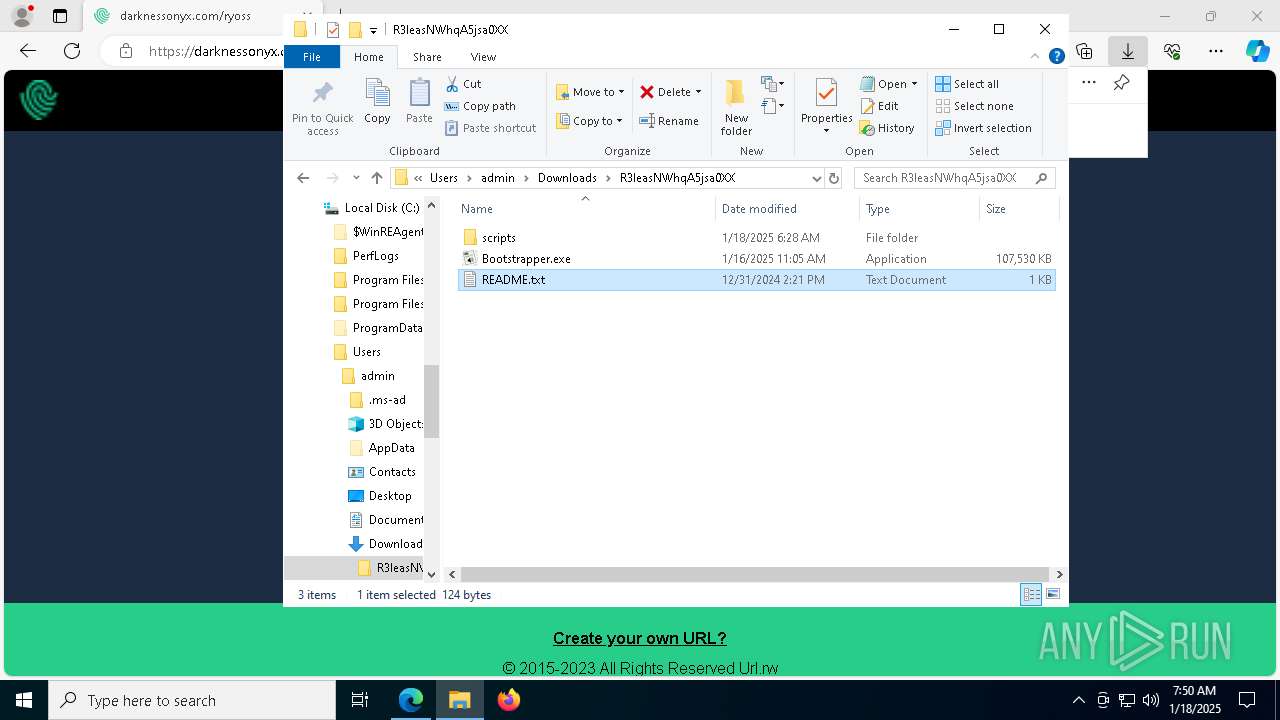
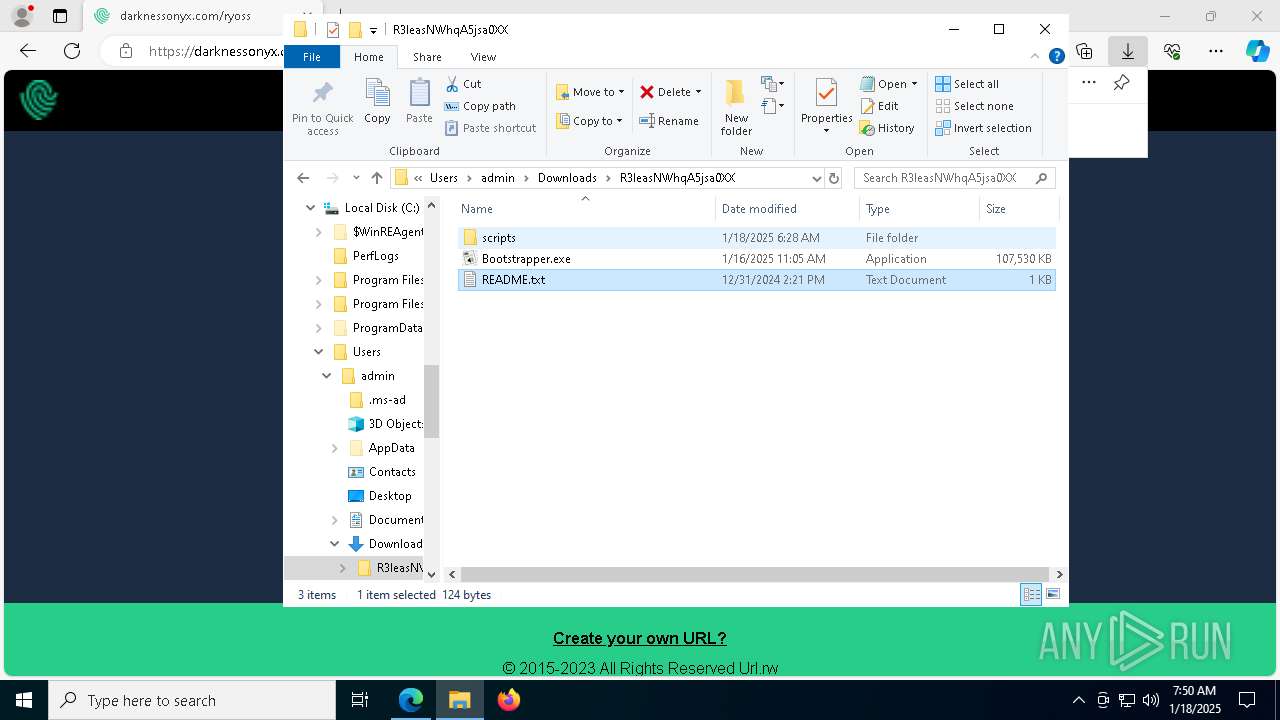
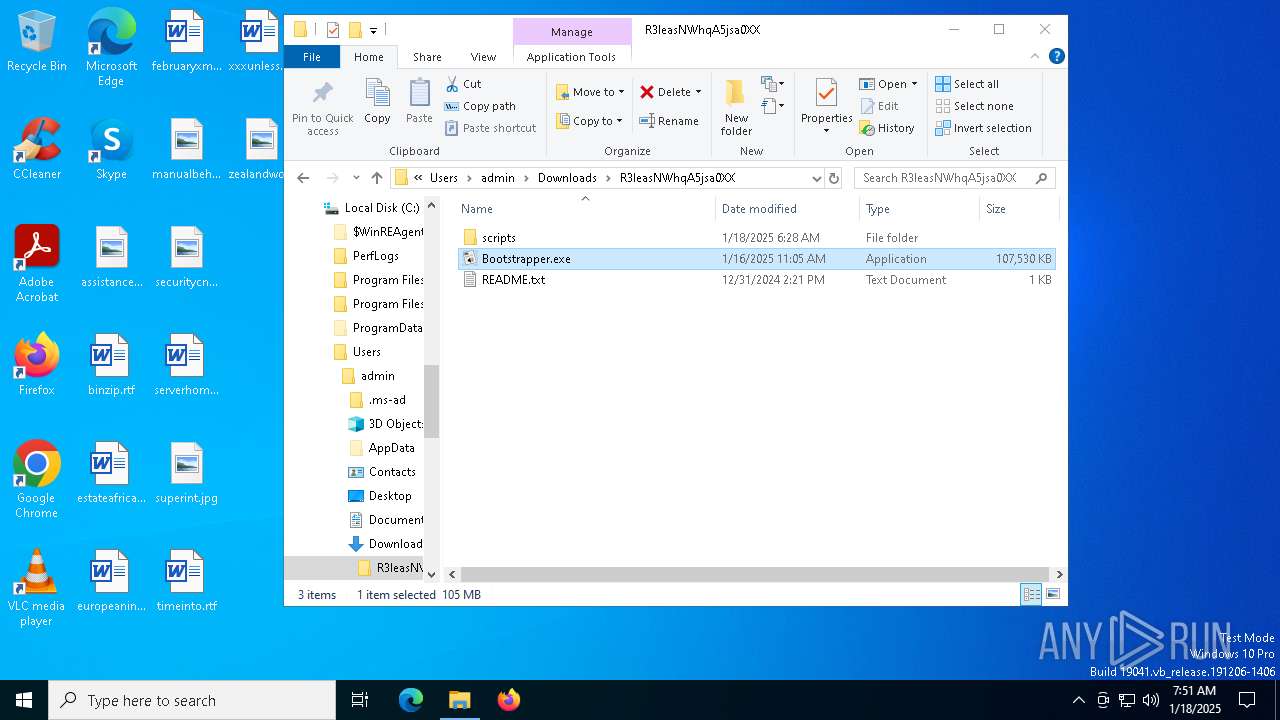
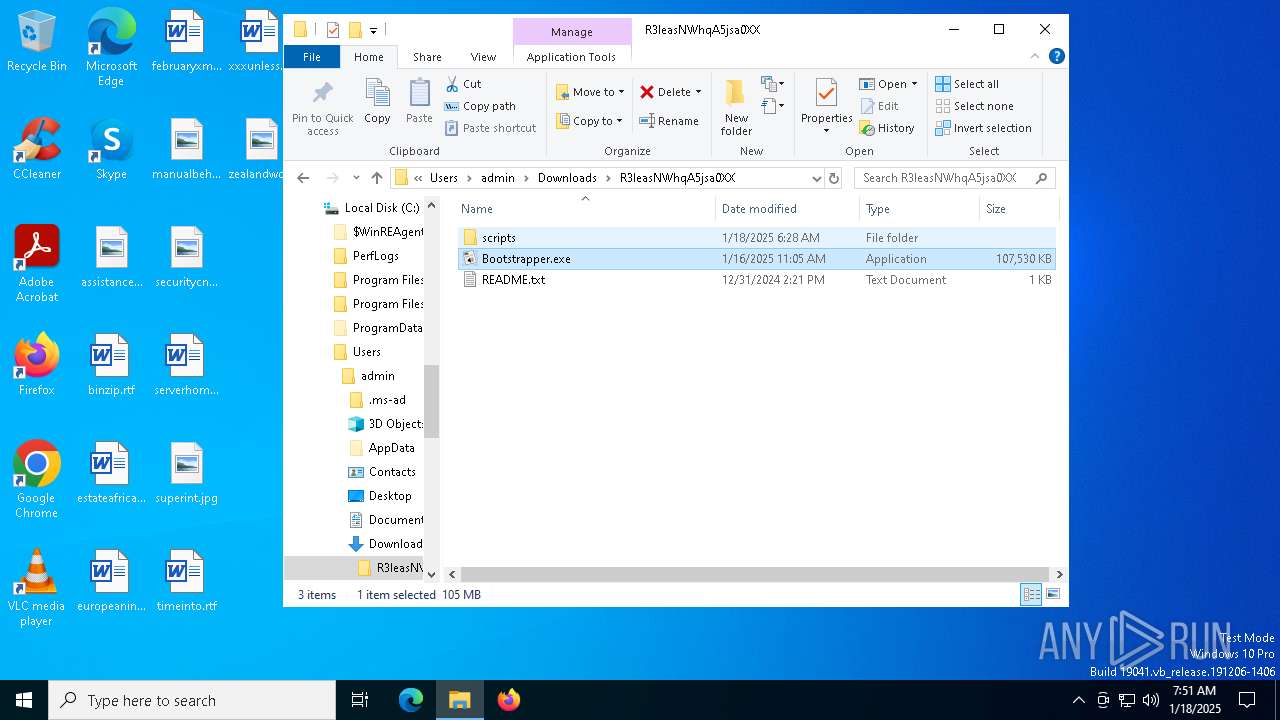
| 1688 | "C:\Users\admin\Downloads\R3leasNWhqA5jsa0XX\Bootstrapper.exe" | C:\Users\admin\Downloads\R3leasNWhqA5jsa0XX\Bootstrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1688 | cmd /c md 510820 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2012 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 048
Read events
14 024
Write events
24
Delete events
0
Modification events
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7675B58E8C8A2F00 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0F22CD8E8C8A2F00 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328534 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C090B16F-D56D-4FF6-8249-D8A21EF80CD3} | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328534 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4A473081-6540-492E-AFC0-A6B82D941846} | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328534 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CC32820F-EA94-4DD1-938E-51215BF9AF04} | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328534 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5345179E-CB21-454D-BDB1-4F74CE56E731} | |||
Executable files
5
Suspicious files
310
Text files
78
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1357b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1357b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1357c8.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1357d7.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1357e7.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
103
DNS requests
96
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6416 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7428 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7428 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6600 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5764 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
mercuryosh.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6600 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6600 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6600 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6600 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6600 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6600 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |