| File name: | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813 |
| Full analysis: | https://app.any.run/tasks/2e51b816-f0fd-4b30-94e6-327b7246d96e |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | August 31, 2024, 14:02:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | D22E179506087D412CA827A42FCB87AC |
| SHA1: | CF9B754EF6AA60BFE8E0A63843555AB276A456FA |
| SHA256: | C95139D7900239A1091FF272F01953A9535144F6F4EA4A61FEBC262AB4537813 |
| SSDEEP: | 98304:yXEb4NKbjgidO4jQ1mVlZyeH/+/12F5wwSEvqgRO2Mboeo/agHV1MvPmyPRNr2hH:k8KgPdu9Mb |
MALICIOUS
COBALTSTRIKE has been detected (YARA)
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
SUSPICIOUS
Drops the executable file immediately after the start
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
Process drops python dynamic module
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
Executable content was dropped or overwritten
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
The process drops C-runtime libraries
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
Process drops legitimate windows executable
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
Application launched itself
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
Loads Python modules
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
Reads security settings of Internet Explorer
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
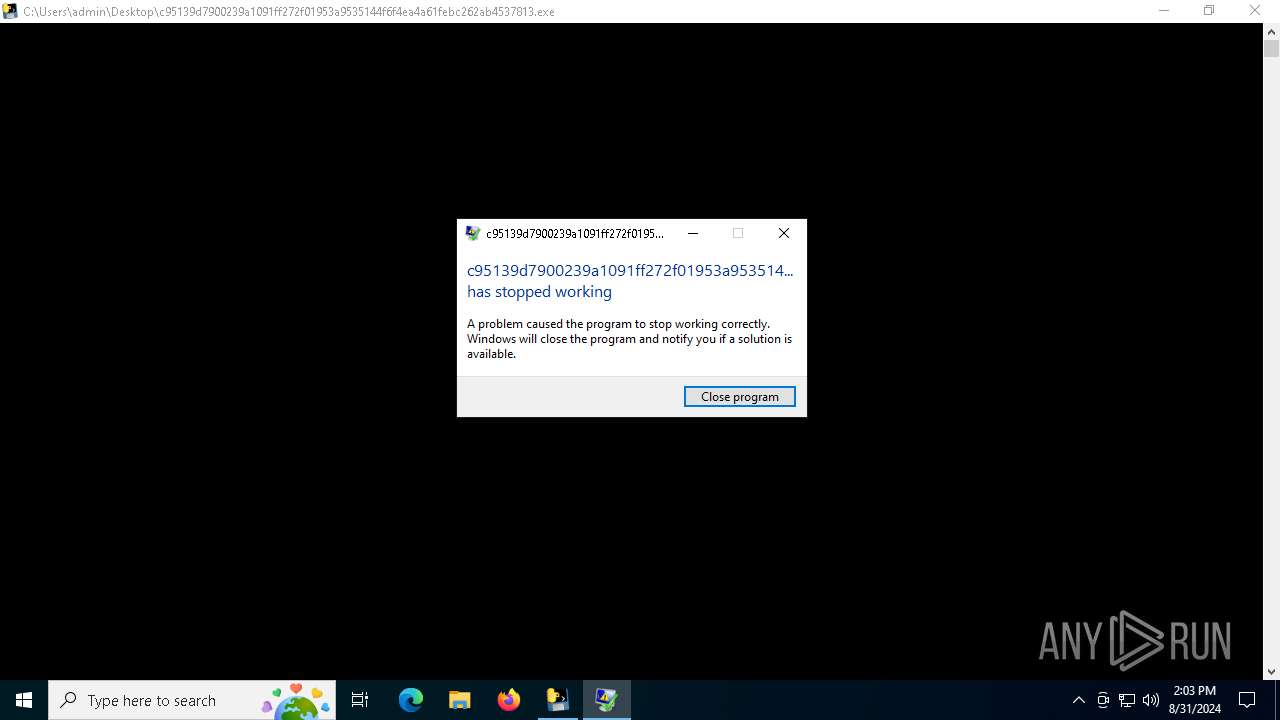
Executes application which crashes
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
INFO
Reads the computer name
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
Checks supported languages
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
Create files in a temporary directory
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
Reads the machine GUID from the registry
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
Checks proxy server information
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
- WerFault.exe (PID: 2640)
PyInstaller has been detected (YARA)
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6988)
- c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe (PID: 6188)
Creates files or folders in the user directory
- WerFault.exe (PID: 2640)
Reads the software policy settings
- WerFault.exe (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
CobalStrike
(PID) Process(6188) c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe
C2192.168.5.5:8888/6xLc
HeadersUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.0; Trident/5.0; BO1IE8_v1;ENUS)
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:24 07:03:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.34 |
| CodeSize: | 166400 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa6a0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
129
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2640 | C:\WINDOWS\system32\WerFault.exe -u -p 6188 -s 1264 | C:\Windows\System32\WerFault.exe | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6188 | "C:\Users\admin\Desktop\c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe" | C:\Users\admin\Desktop\c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
CobalStrike(PID) Process(6188) c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe C2192.168.5.5:8888/6xLc HeadersUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.0; Trident/5.0; BO1IE8_v1;ENUS) | |||||||||||||||
| 6988 | "C:\Users\admin\Desktop\c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe" | C:\Users\admin\Desktop\c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 7052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 239
Read events
8 231
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6188) c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6188) c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6188) c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6188) c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
55
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:F2CA4A6E2407BCF67377D03F98142CD6 | SHA256:C97CDCF64732821D8308627F0488B7259ABB6A382027BDC2EDFC92A9B170826A | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:D315B2886B0F6D6AB9FB887D99FFEA3B | SHA256:AAA9AEDD77AC911F4D96443382CC82A6183E02F104DB63166BCEEF3869B780FD | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_cbc.pyd | executable | |
MD5:E8AF5BDF9B56FC0DC73007467484AECC | SHA256:784B715E8B281E7FF4E427043828BEC8765ACF36D152A48E37692C8296445D46 | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:65B1F115C735A1C6A3D701C856A5C851 | SHA256:B3EE740DFD11F3EA140ECBBADFA2381E38EC167A46946DF101C1DE80D1989EFC | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_cast.pyd | executable | |
MD5:DCCCB22EFD32F63C7B37C7528EA13EEE | SHA256:F3EB020866EB533652E43FB1331E9132FACE1653DDE88D670B9A4E0AFA556466 | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_eksblowfish.pyd | executable | |
MD5:03677AD74C2F76C0364E788BB9632A0A | SHA256:D07467563D30557C9EDAF491069014BBDCCBDFB9ED0F6C6A2F2CFDF11A408C7B | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_arc2.pyd | executable | |
MD5:363C6F822AF8A36367A81F2097649FB1 | SHA256:C026C3A21D29F60CE2FFCC21A077E79B79EA678D707BD8C307C5BE5F69A1A1D9 | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:C97C824F8A8D88A360587A30BAE38A9B | SHA256:E2C4A5BF9D1D506690BBF2B602F7047B17A0F997D6CD84194BED131565326D5E | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_des3.pyd | executable | |
MD5:4E0AD735ED79B02DD7341EF4F58FFD54 | SHA256:8B972C0433D674EB3D086393E6D81836B40EB16721B53FA91784E9EC2C601F99 | |||
| 6988 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | C:\Users\admin\AppData\Local\Temp\_MEI69882\Crypto\Cipher\_raw_ctr.pyd | executable | |
MD5:335F119A67EFD51C2D6FD959915FFBB3 | SHA256:9C149AADE4E4A724C3945FED423300C41BB77CEEBF61C9ACF29D1B97D98260A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
5
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6876 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1356 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.134:49785 | — | — | — | unknown |
4324 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2640 | WerFault.exe | 104.208.16.94:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6188 | c95139d7900239a1091ff272f01953a9535144f6f4ea4a61febc262ab4537813.exe | A Network Trojan was detected | AV TROJAN Observed Cobalt Strike User-Agent |