| File name: | avp.dll |
| Full analysis: | https://app.any.run/tasks/104d0666-0a70-46e2-a677-6747affa4117 |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
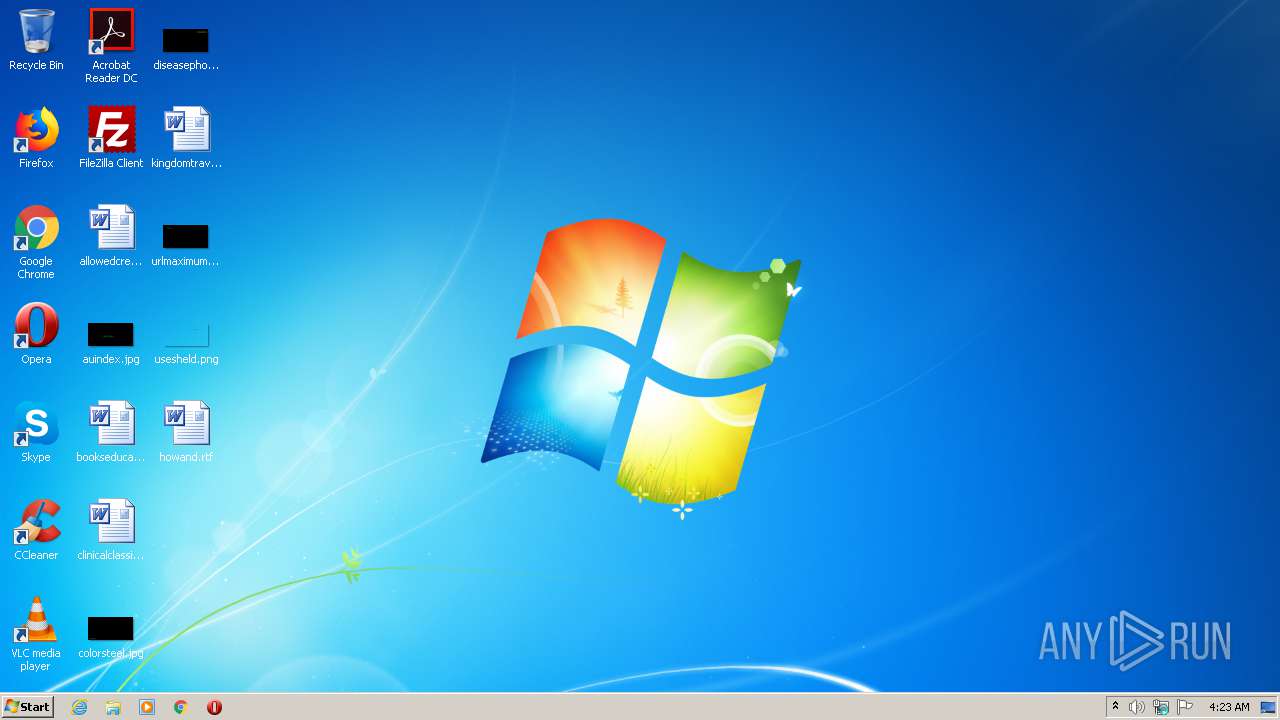
| Analysis date: | April 28, 2021, 03:23:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 1A295E304BE80266A832CD648EE7DB9D |
| SHA1: | 21490CB65A07BD2E0401233E91D13D0A42F925BF |
| SHA256: | C94D6649FE5C879AC2E4CCB313958736AC4C86F217C3A68C799F9641B6AC9F2A |
| SSDEEP: | 24576:W1s6AOGWFzyAhDsgD1mW4JkSLk/77rel7GMP2XZHzPu2809czQTyvOkjaLk:WbbbO3j2pzPuL09xTMOkjaLk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3636)
INFO
Loads main object executable
- rundll32.exe (PID: 696)
Manual execution by user
- explorer.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 1.0.0.1 |
|---|---|
| LegalCopyright: | Copyright (C) 2020 |
| FileVersion: | 1.0.0.1 |
| CharacterSet: | Unicode |
| LanguageCode: | Unknown (0009) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x13566 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 561664 |
| CodeSize: | 1232896 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:03:10 07:32:24+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Mar-2021 06:32:24 |
| Detected languages: |
|
| FileVersion: | 1.0.0.1 |
| LegalCopyright: | Copyright (C) 2020 |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 10-Mar-2021 06:32:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0012CE8A | 0x0012D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60364 |
.rdata | 0x0012E000 | 0x0007021E | 0x00070400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.41173 |
.data | 0x0019F000 | 0x00009A68 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.63055 |
.gfids | 0x001A9000 | 0x00000148 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.67532 |
.rsrc | 0x001AA000 | 0x00000718 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.92196 |
.reloc | 0x001AB000 | 0x0000E72C | 0x0000E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60411 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.19387 | 396 | UNKNOWN | Chinese - PRC | RT_VERSION |
107 | 0.4689 | 1256 | UNKNOWN | Chinese - PRC | RT_BITMAP |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
WS2_32.dll |
bcrypt.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Start | 1 | 0x00012120 |
Total processes
45
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
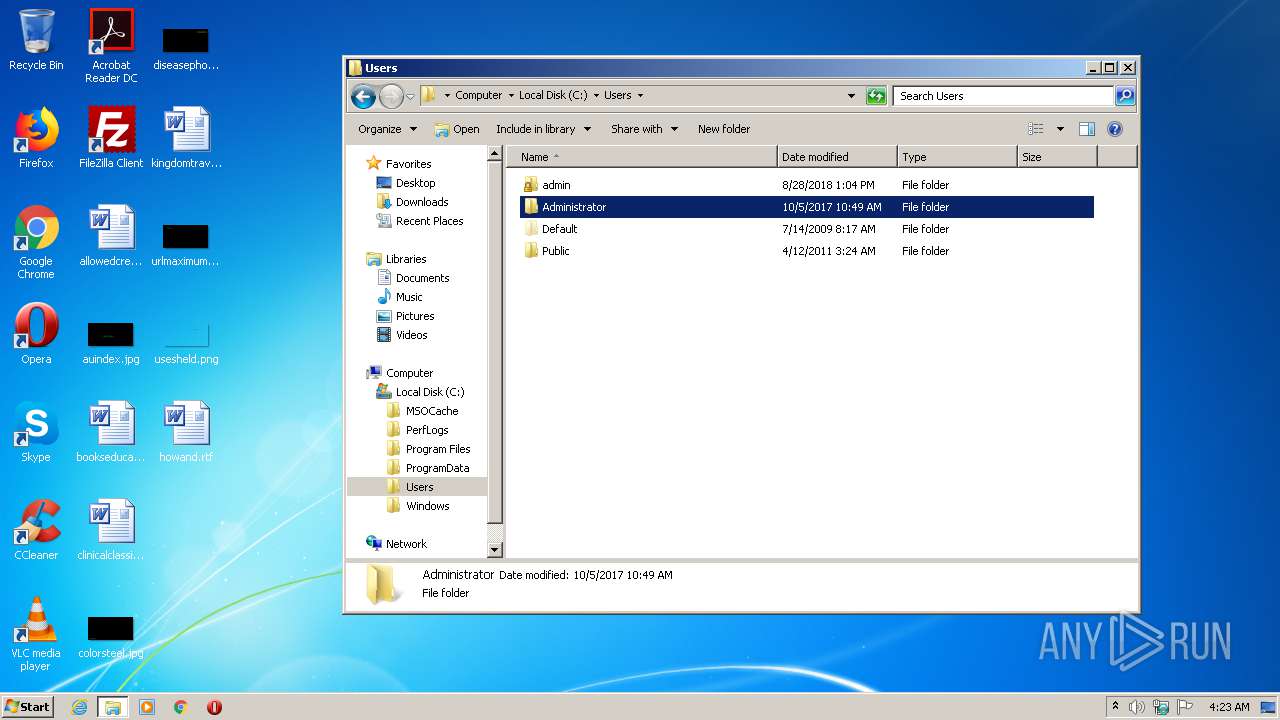
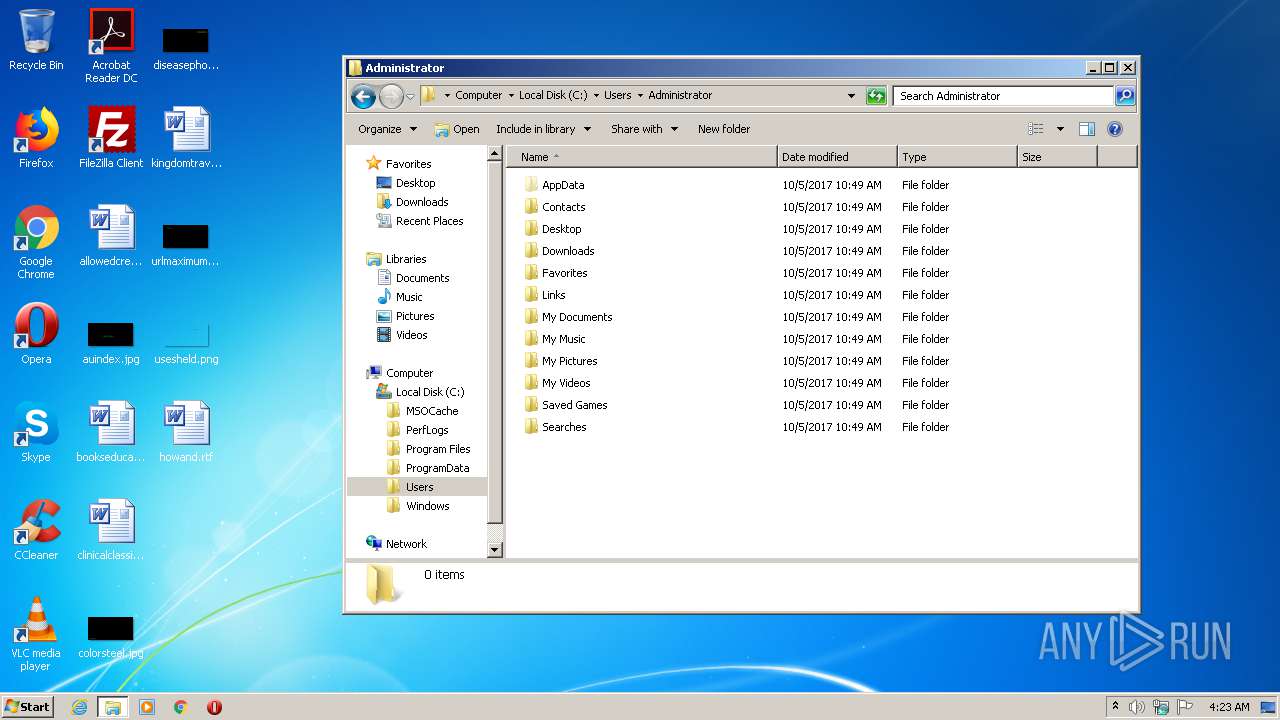
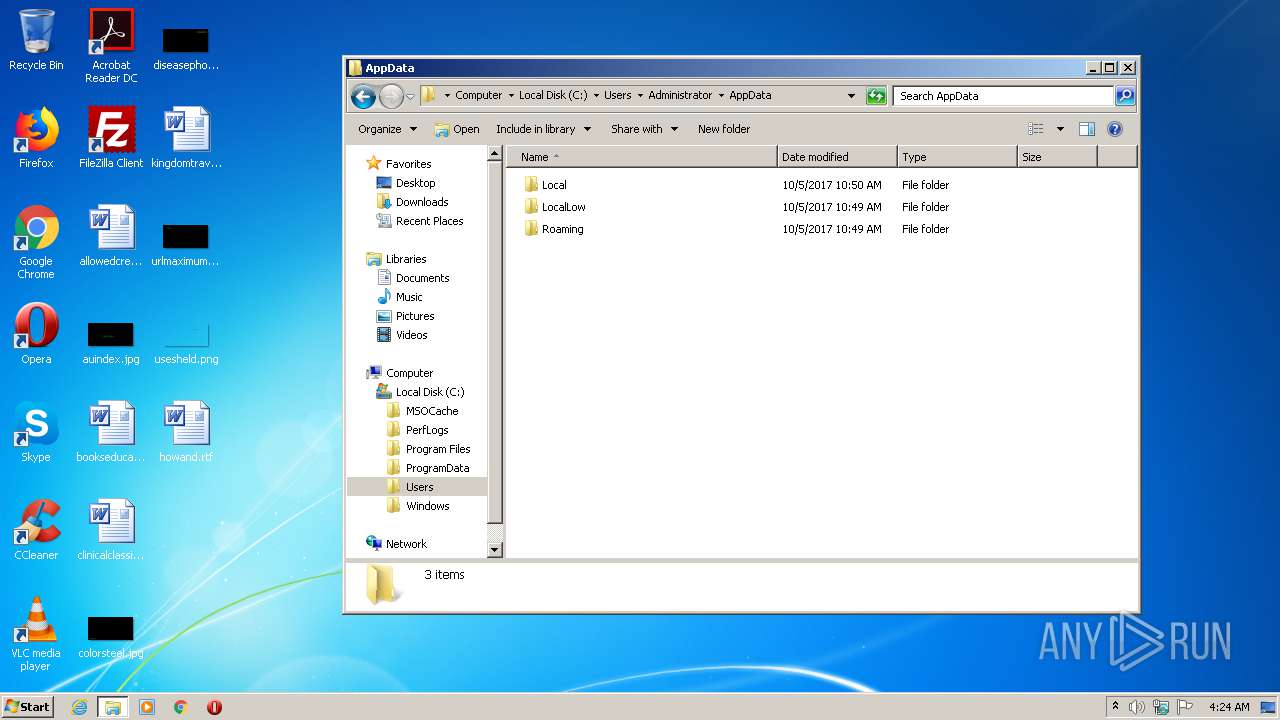
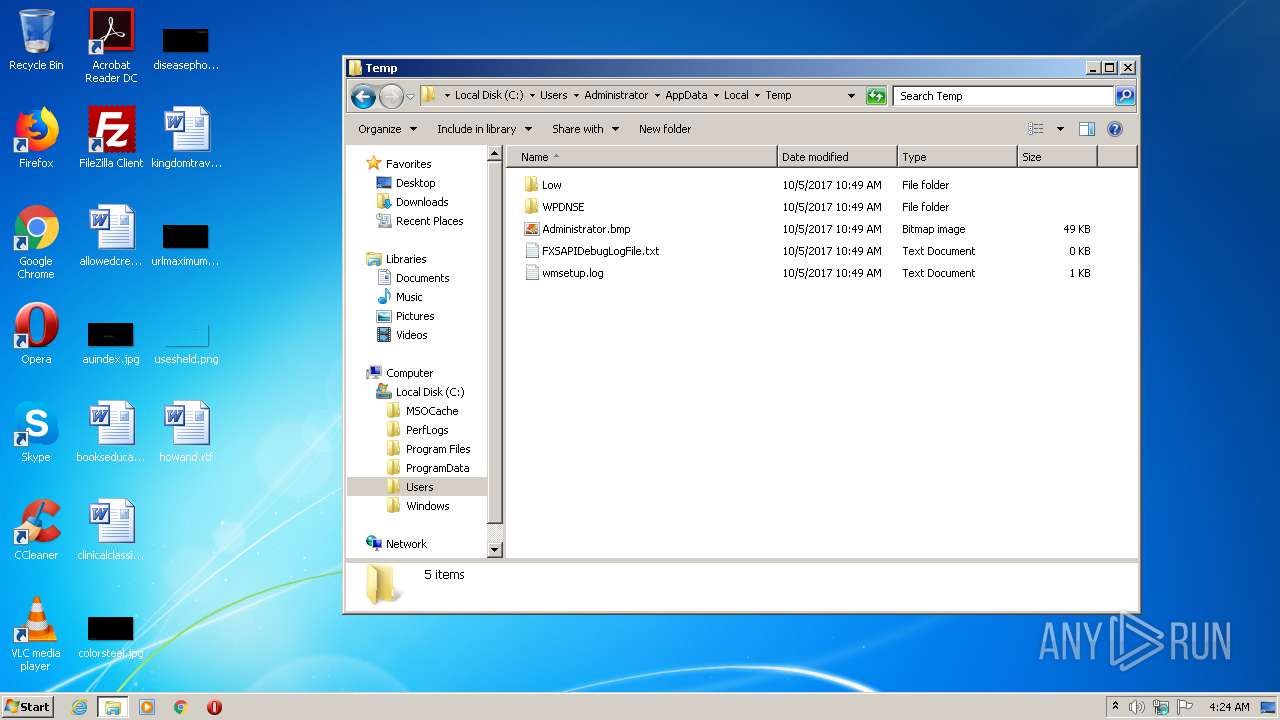
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
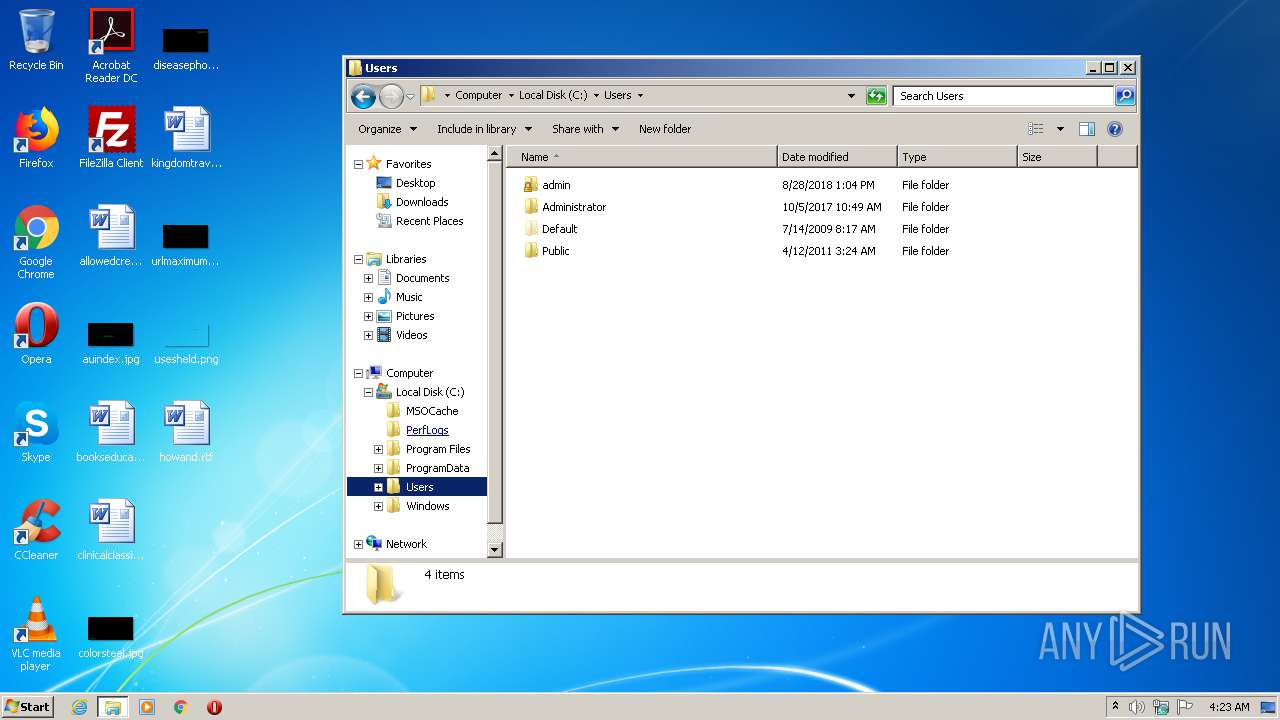
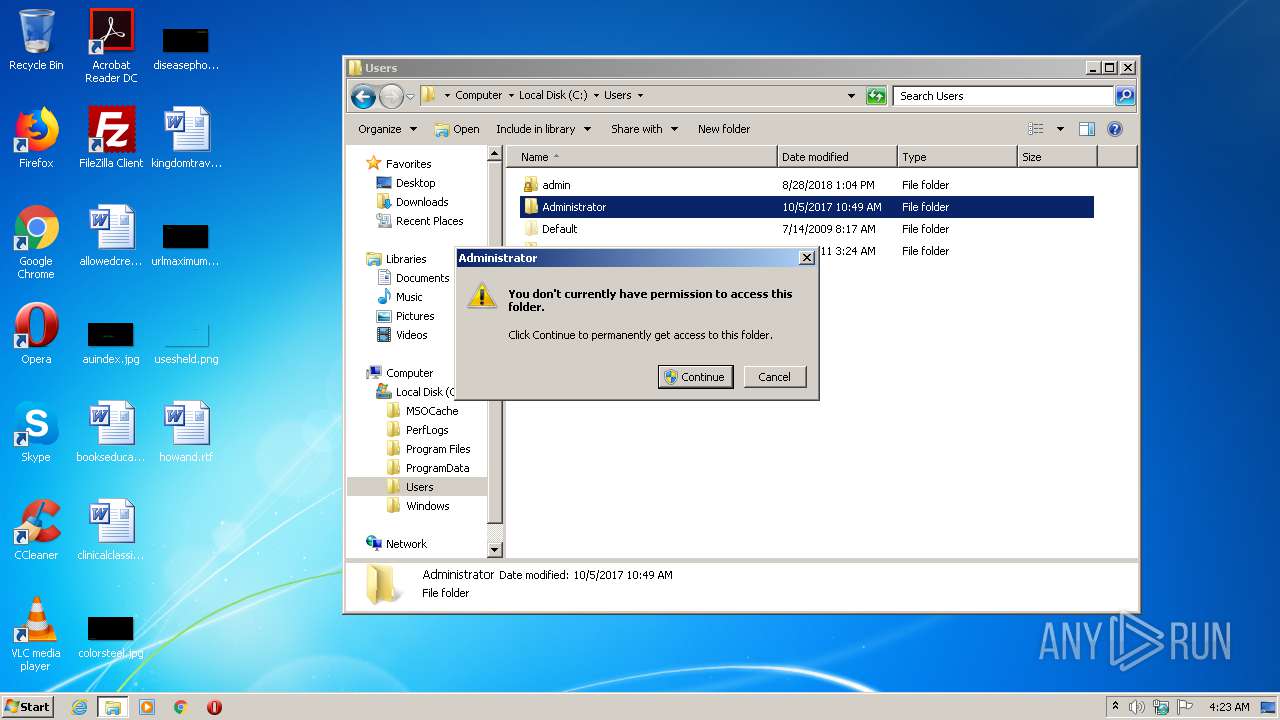
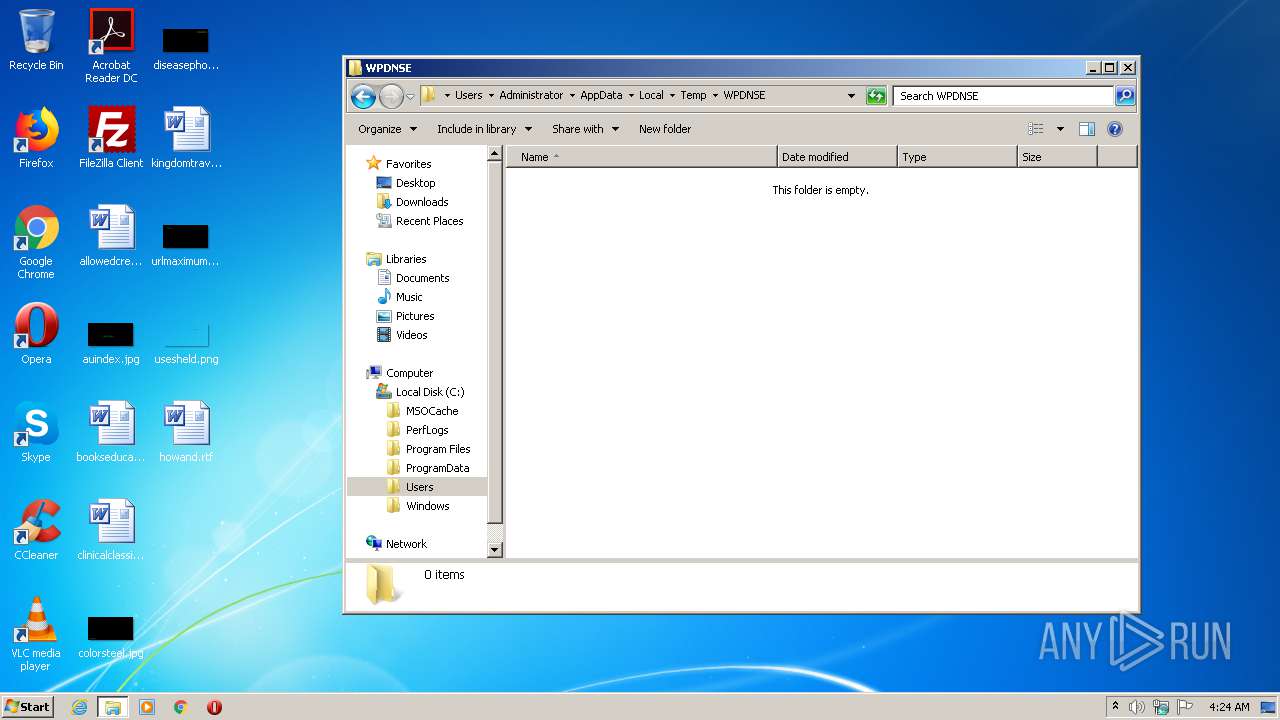
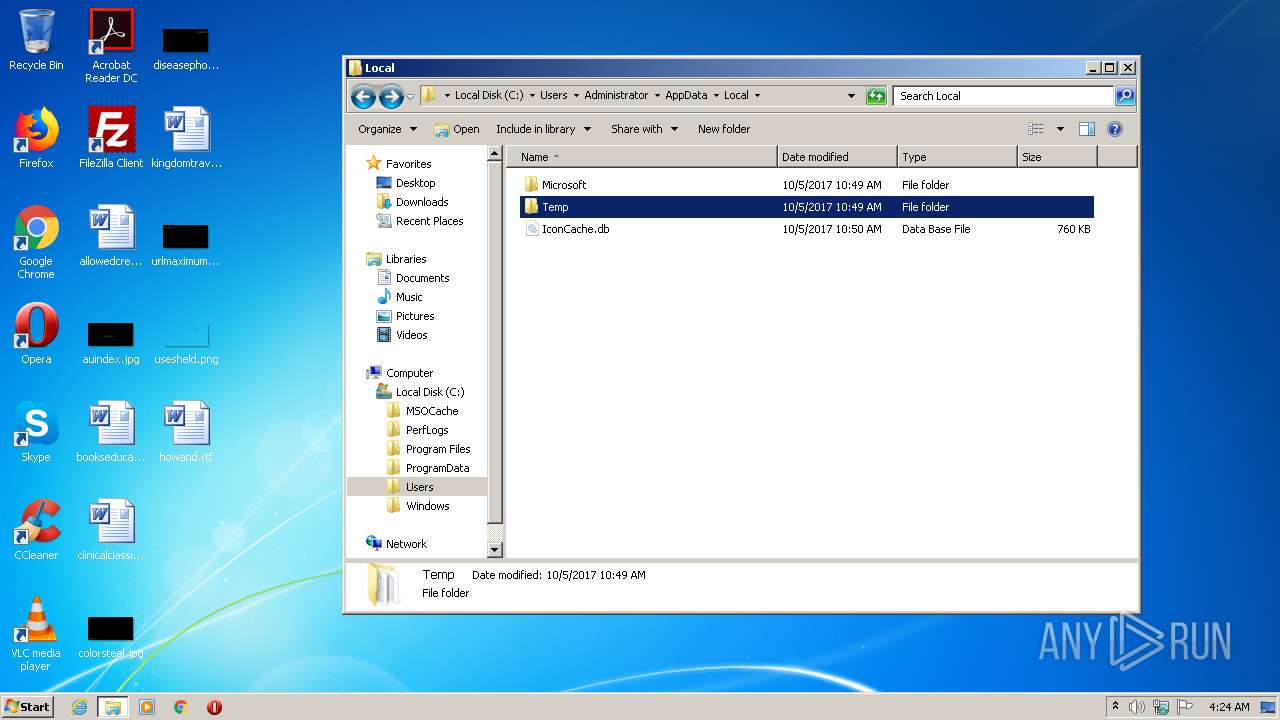
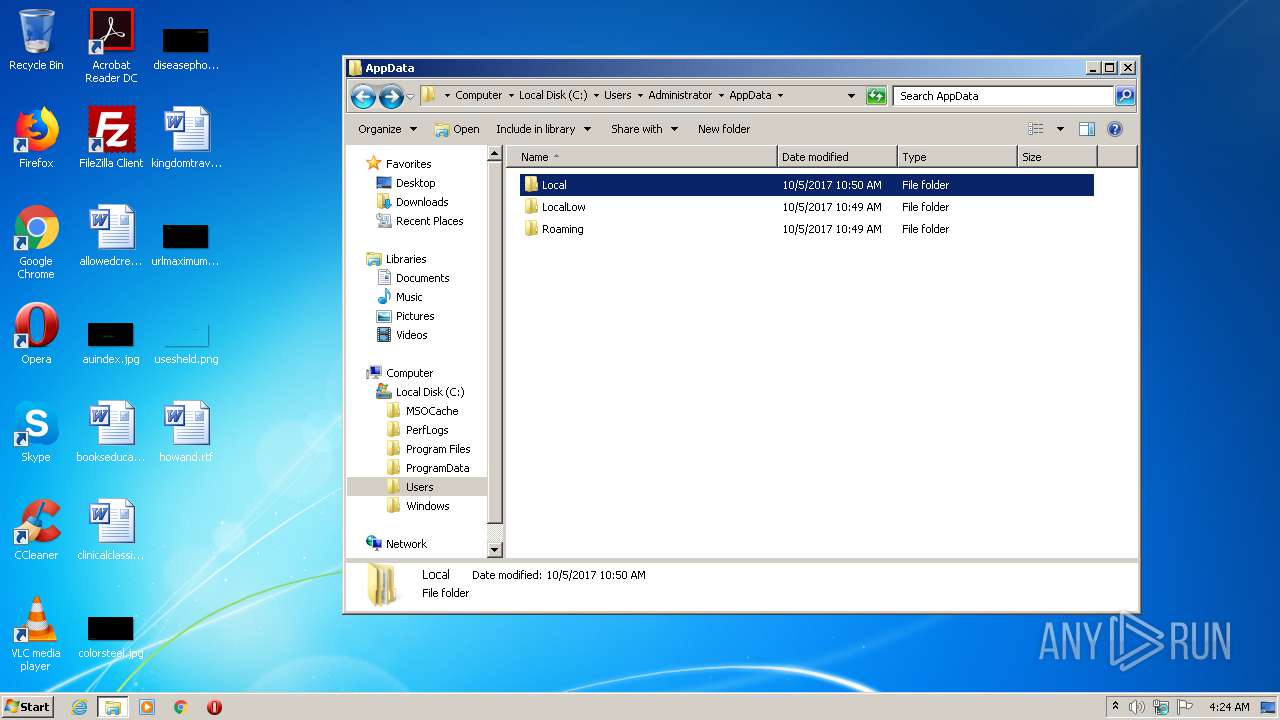
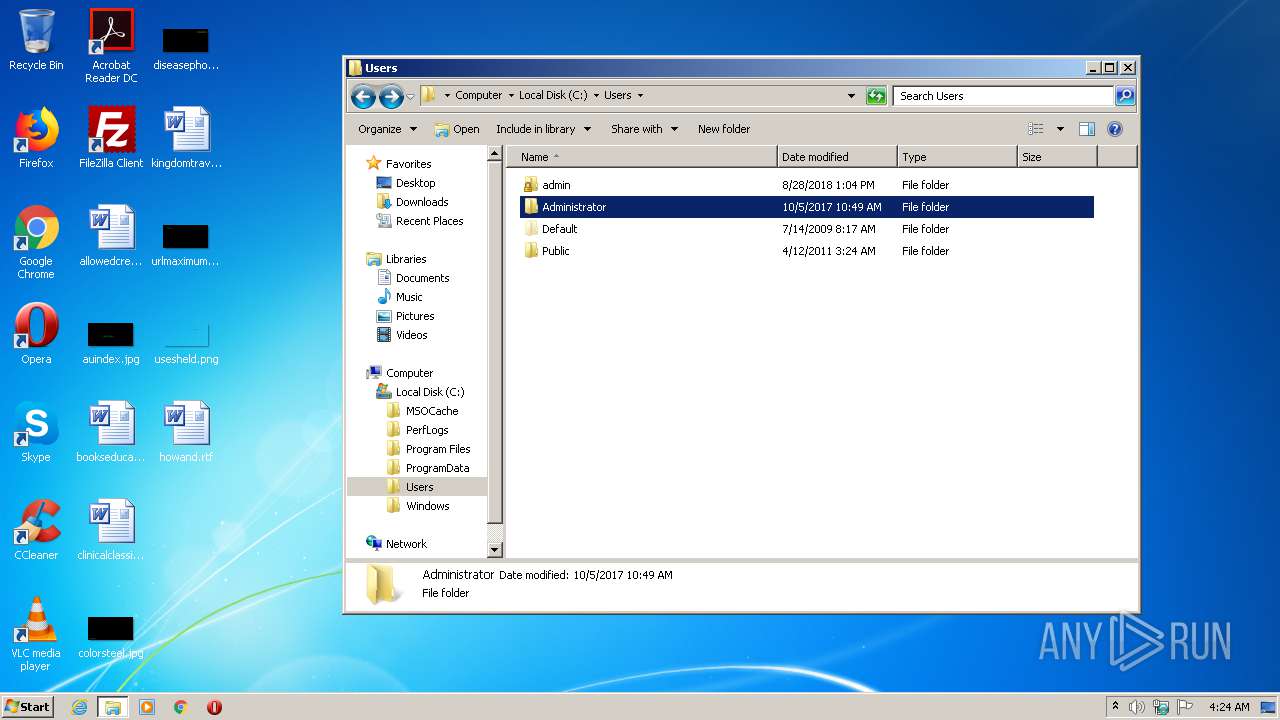
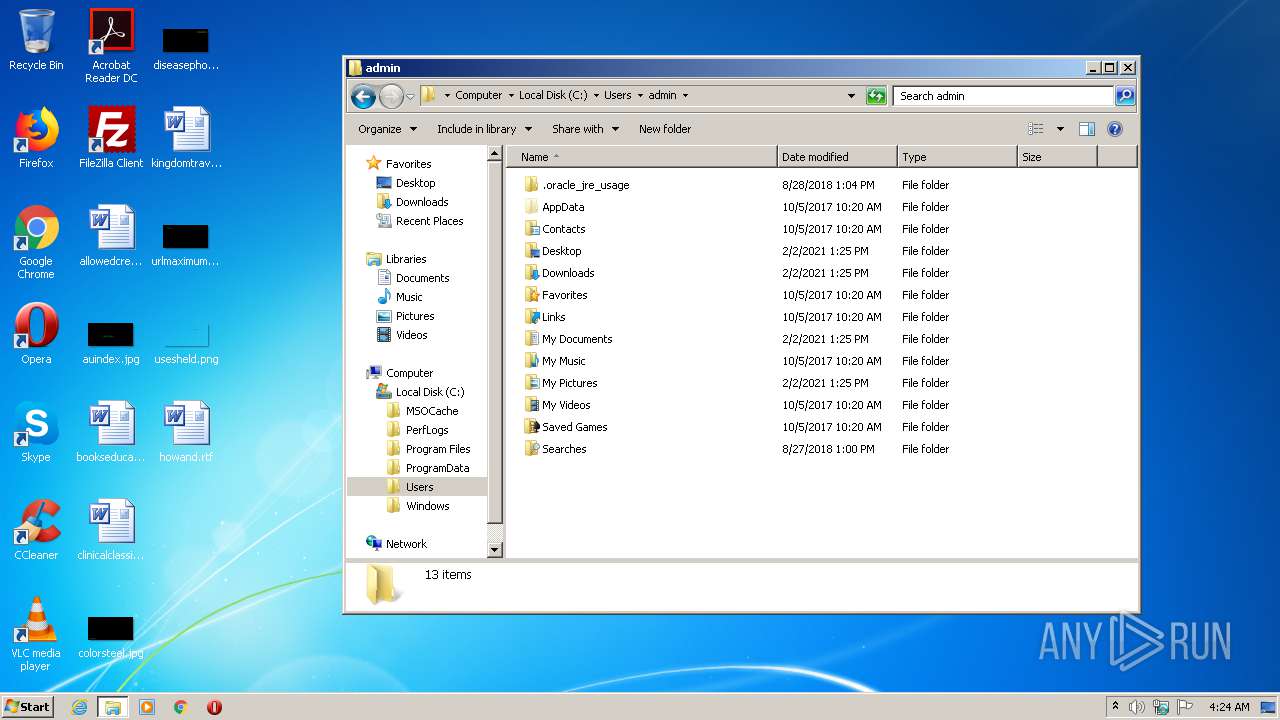
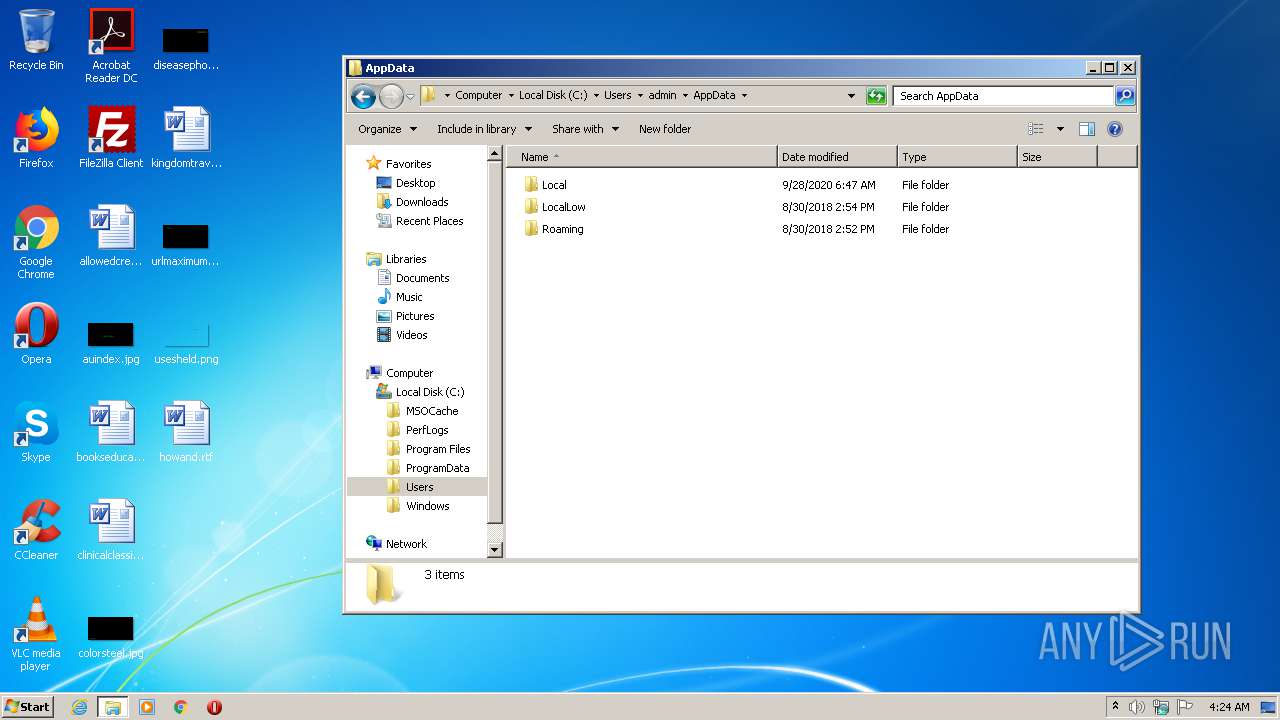
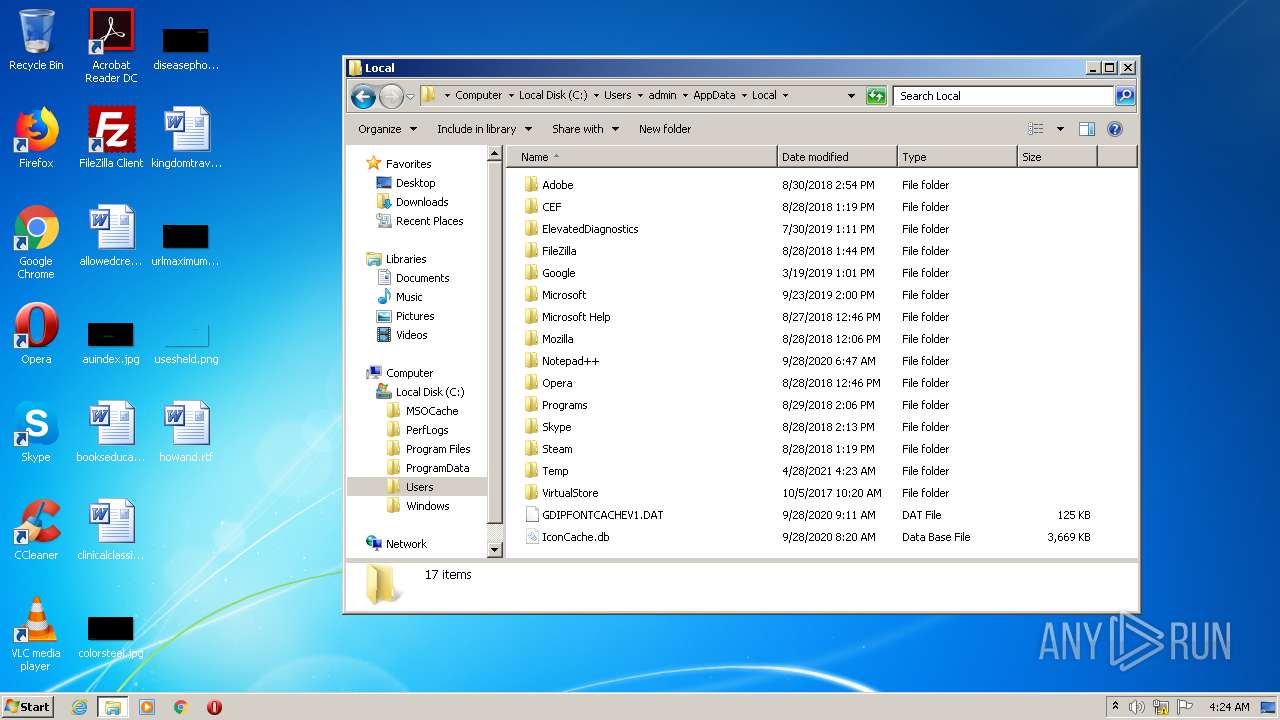
| 696 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\avp.dll.exe", Start | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3636 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3876 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30
Read events
30
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
696 | rundll32.exe | CONNECT | — | 172.16.22.22:8080 | http://www.rninhsss.com:8080www.rninhsss.com:80 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
696 | rundll32.exe | 172.16.22.22:8080 | — | — | — | unknown |
696 | rundll32.exe | 124.156.222.4:80 | www.rninhsss.com | — | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.rninhsss.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | A Network Trojan was detected | ET TROJAN Gh0st Variant CnC Domain in DNS Lookup (rninhsss .com) |