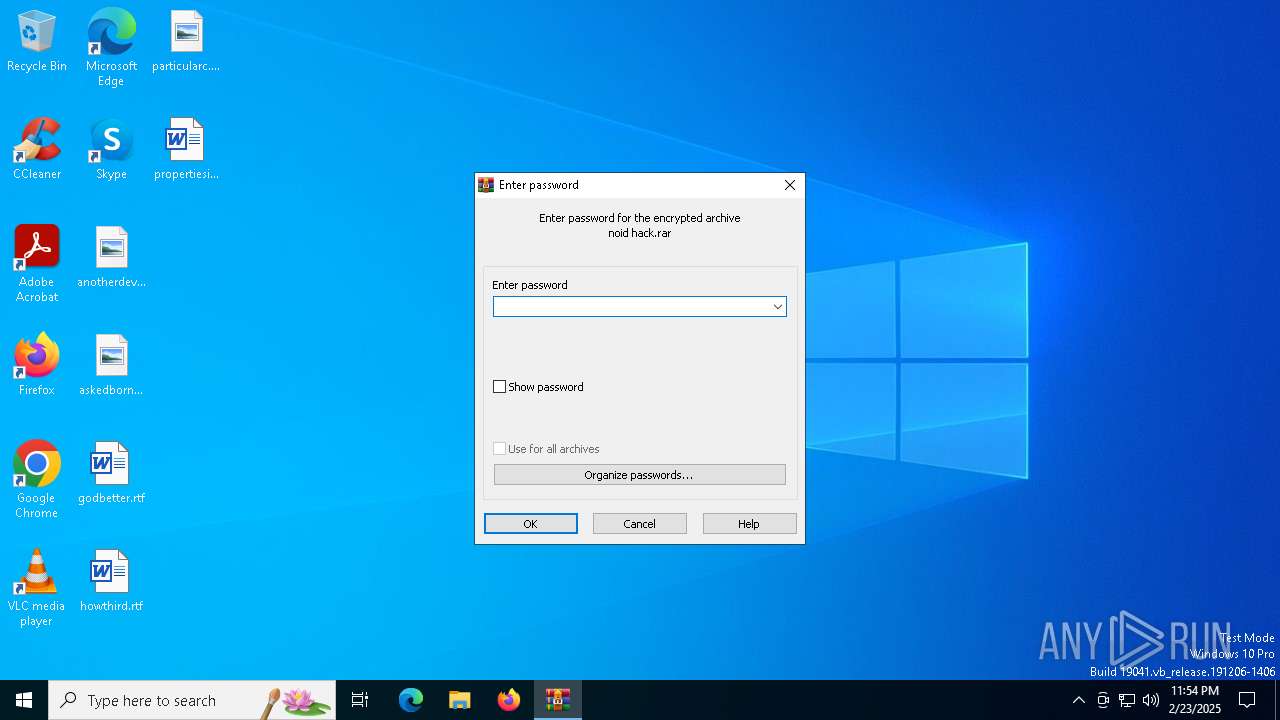
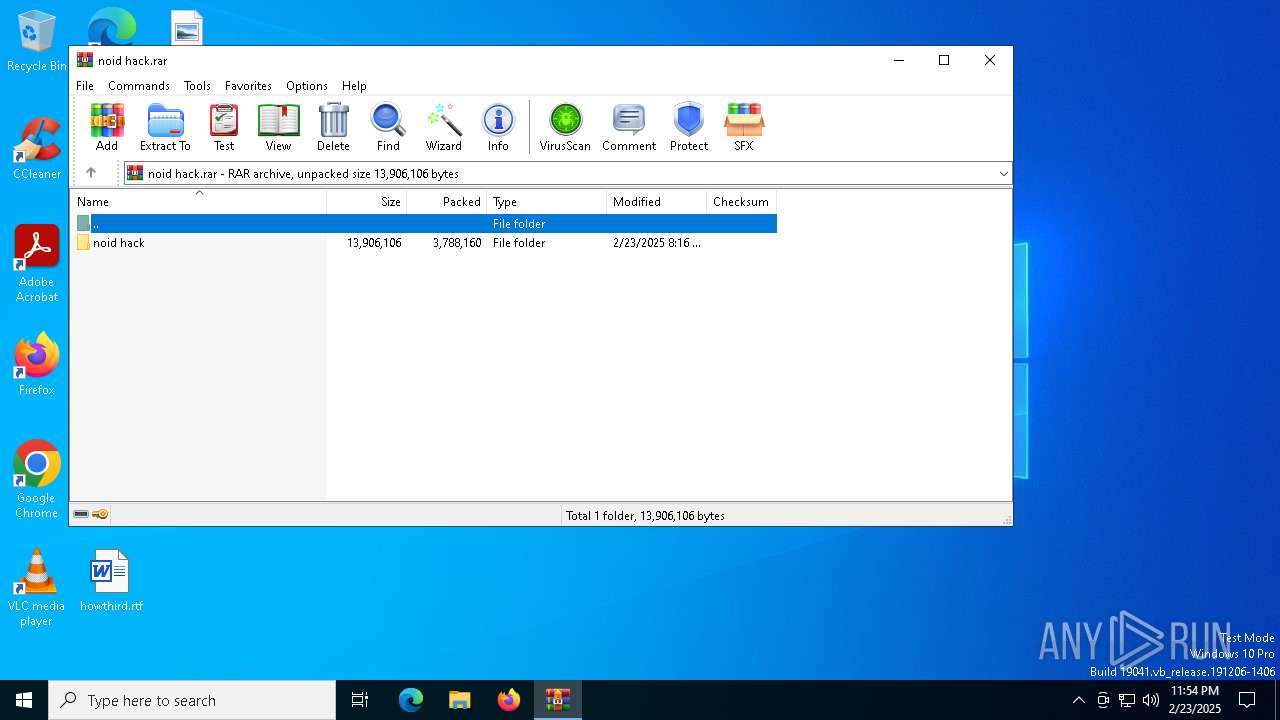
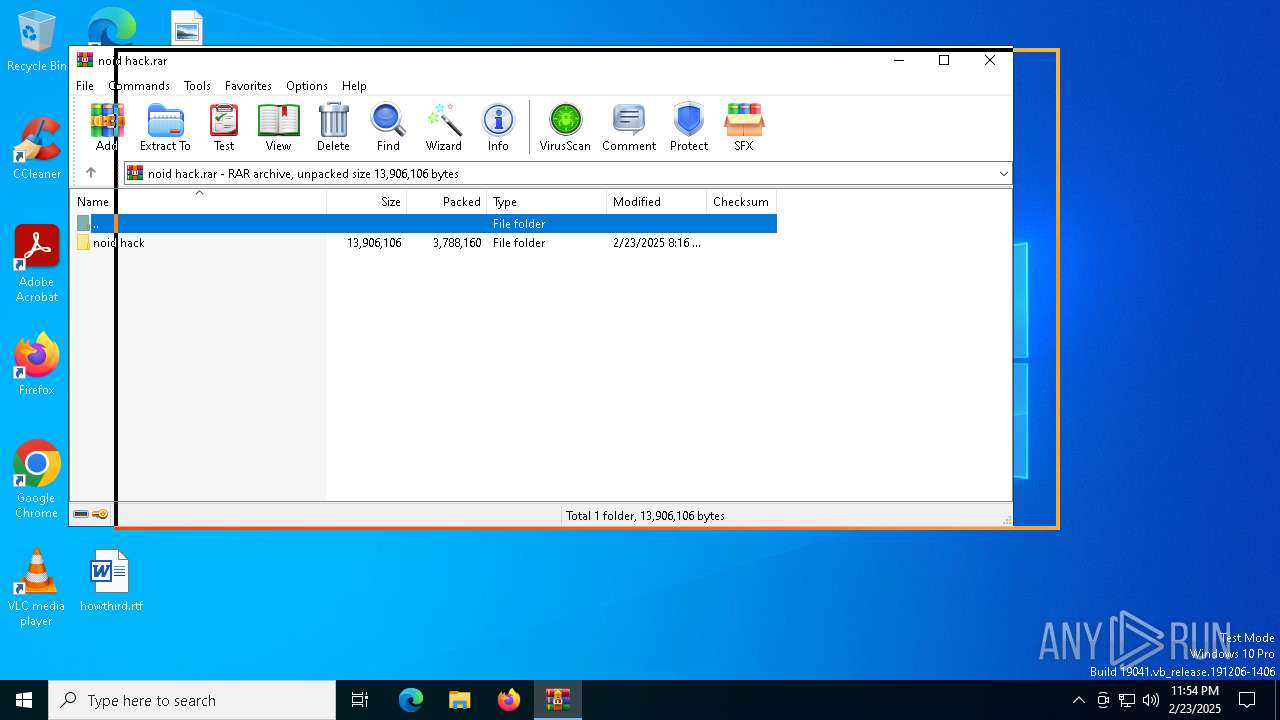
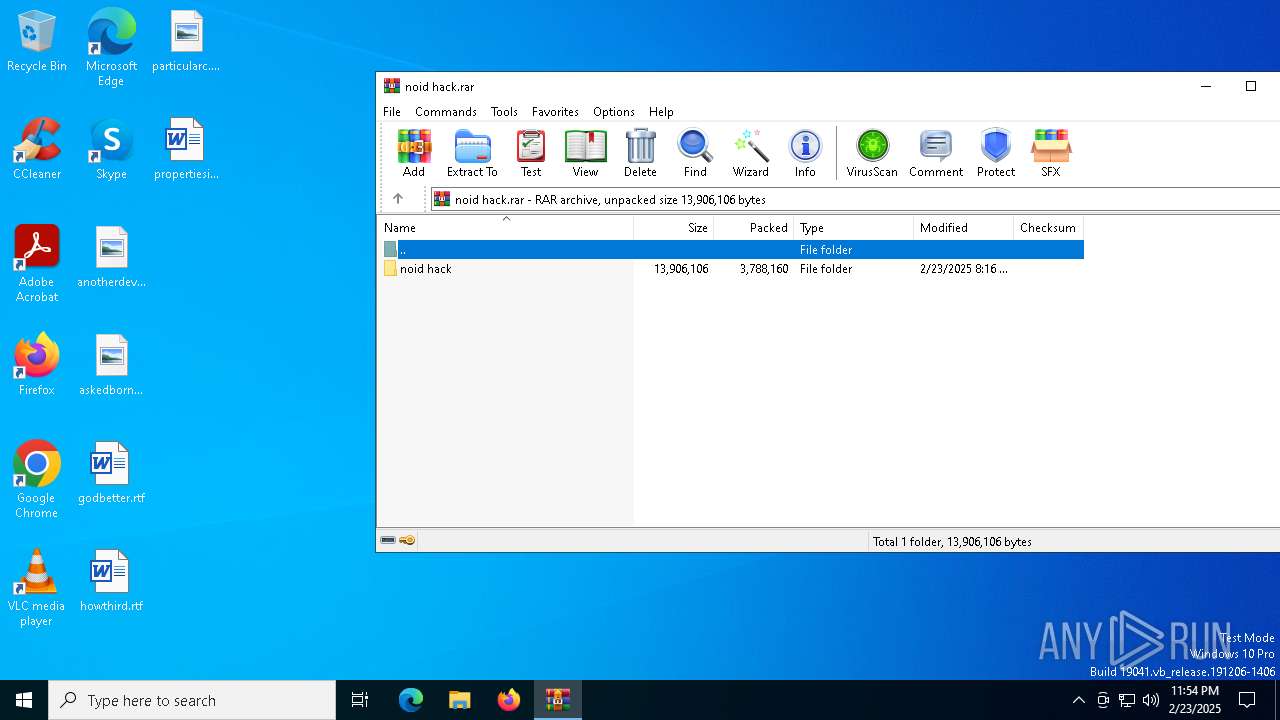
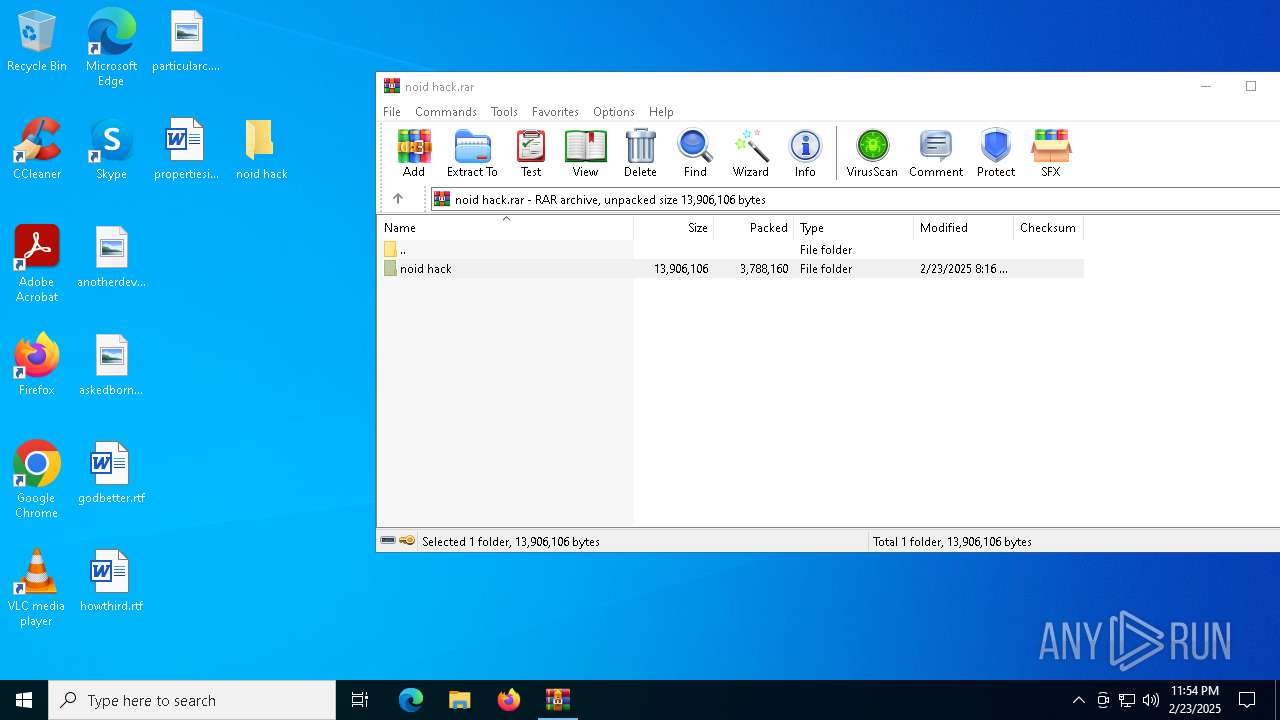
| File name: | noid hack.rar |
| Full analysis: | https://app.any.run/tasks/4f7c3391-00d4-49ed-8c53-e004980016ba |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 23, 2025, 23:53:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 340812C85DC6E493F60ADF85534A094E |
| SHA1: | BAD1D3131891C2B97C4E7B377D2207063B8FEBBB |
| SHA256: | C9397E4E4BB4718E3FD5A995A68682BD654DD7CF9DAF96508DA7C85808C5393E |
| SSDEEP: | 98304:9A5gfoNGqfKq+6F+OLBbXk+v2zTVgrcdJzUQgwmbeoXMP+EdPztsvFQBCxFTevWi:ICK77s7z |
MALICIOUS
LUMMA mutex has been found
- BitLockerToGo.exe (PID: 7060)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 7060)
Steals credentials from Web Browsers
- BitLockerToGo.exe (PID: 7060)
LUMMA has been detected (YARA)
- BitLockerToGo.exe (PID: 7060)
SUSPICIOUS
There is functionality for communication over UDP network (YARA)
- noid v1.7.exe (PID: 6776)
Searches for installed software
- BitLockerToGo.exe (PID: 7060)
There is functionality for taking screenshot (YARA)
- BitLockerToGo.exe (PID: 7060)
INFO
Detects GO elliptic curve encryption (YARA)
- noid v1.7.exe (PID: 6776)
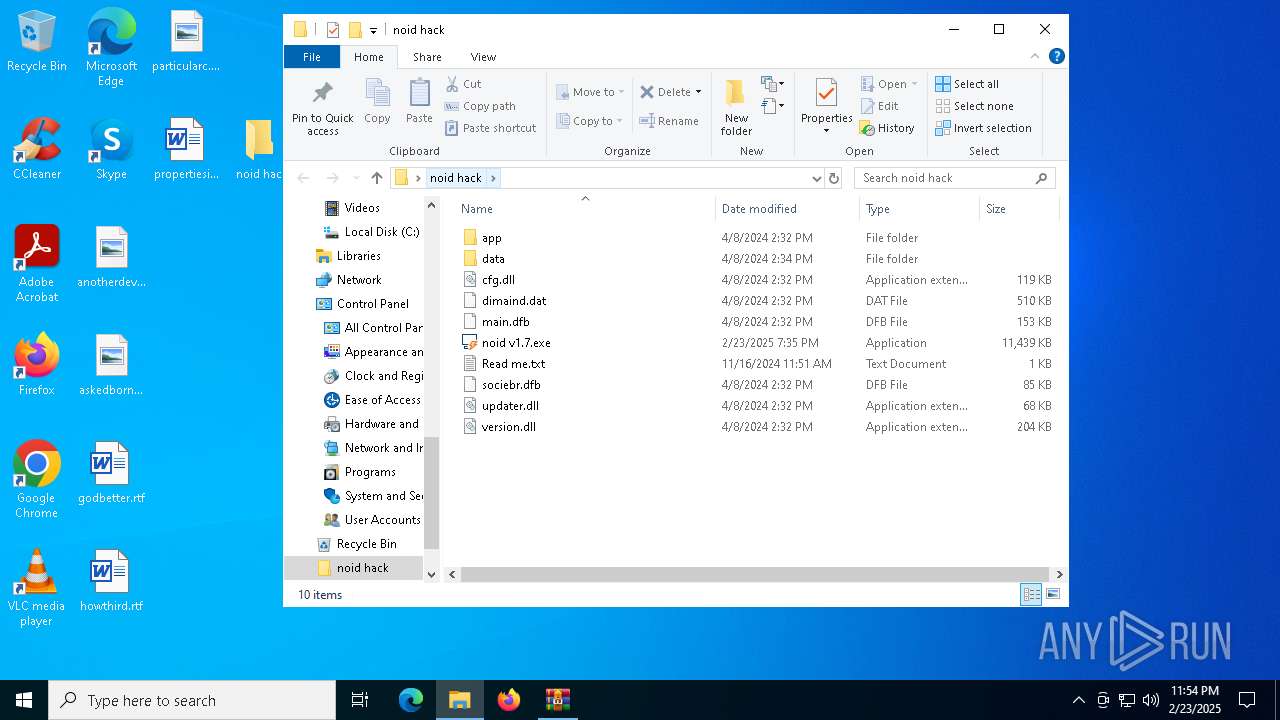
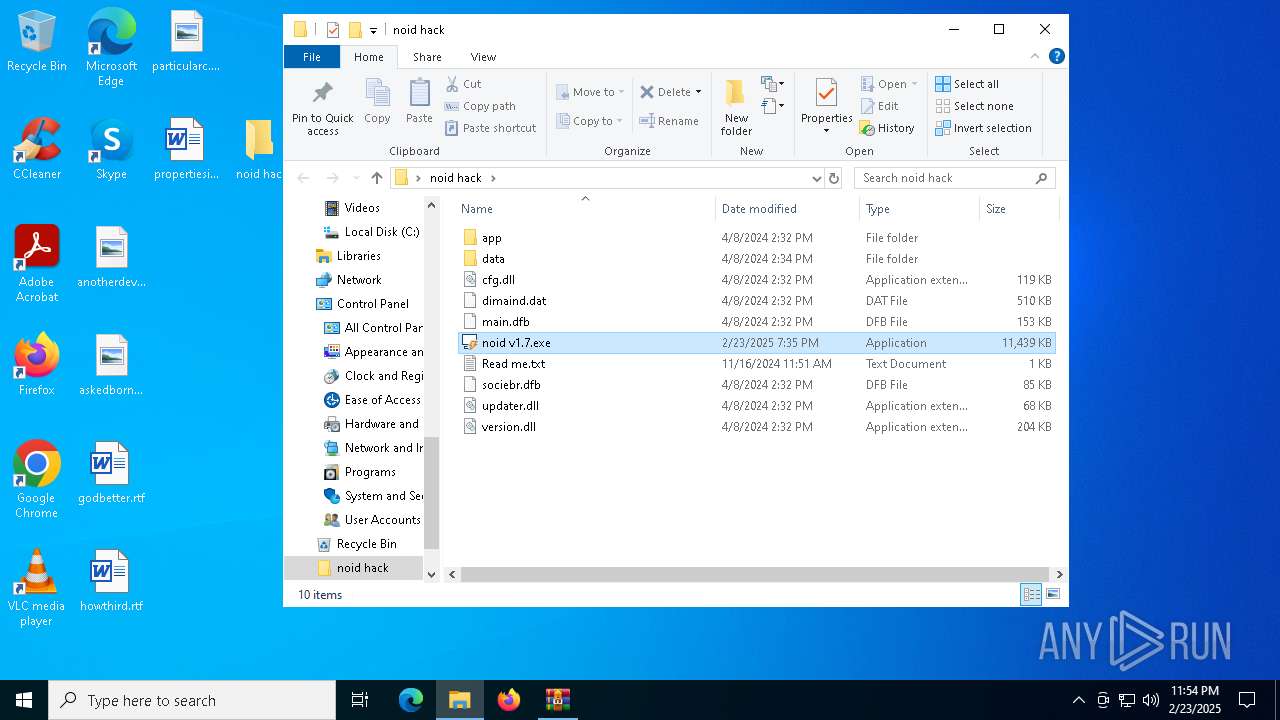
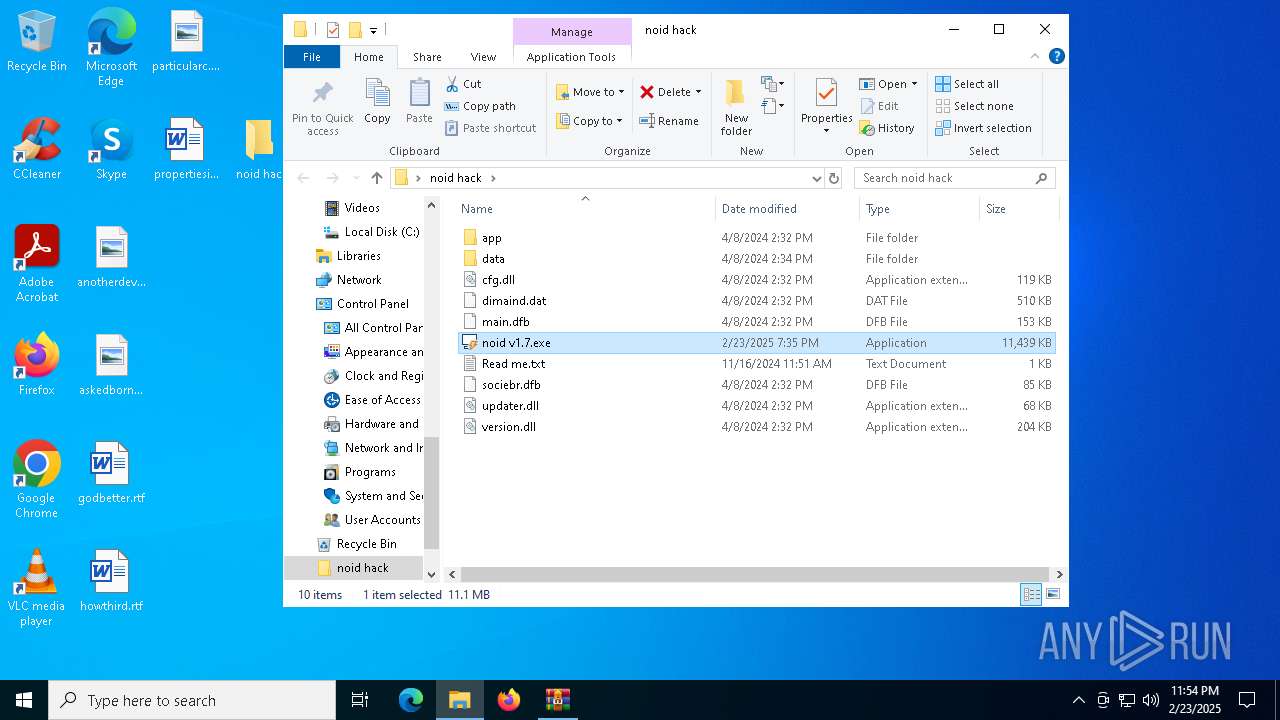
Manual execution by a user
- noid v1.7.exe (PID: 6776)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2144)
The sample compiled with english language support
- WinRAR.exe (PID: 2144)
Checks supported languages
- noid v1.7.exe (PID: 6776)
- BitLockerToGo.exe (PID: 7060)
Reads the computer name
- BitLockerToGo.exe (PID: 7060)
Application based on Golang
- noid v1.7.exe (PID: 6776)
Creates files in the program directory
- BitLockerToGo.exe (PID: 7060)
Reads the software policy settings
- BitLockerToGo.exe (PID: 7060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
130
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\noid hack.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6736 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
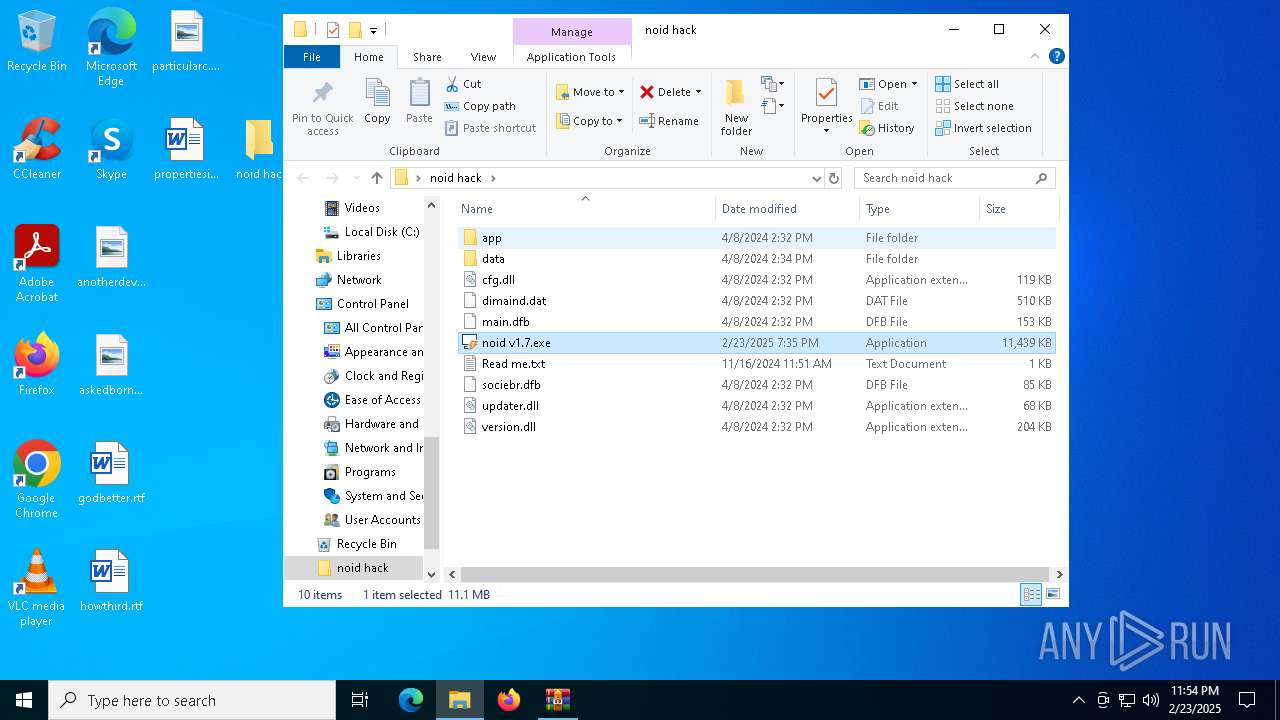
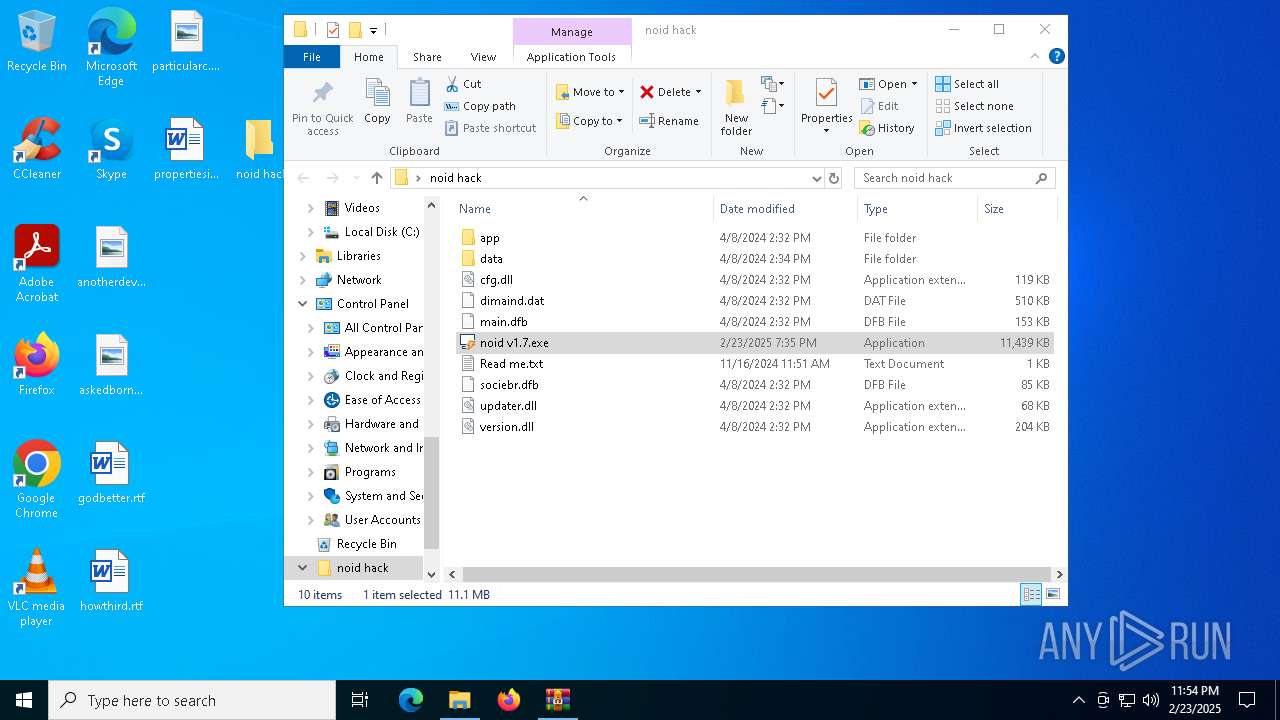
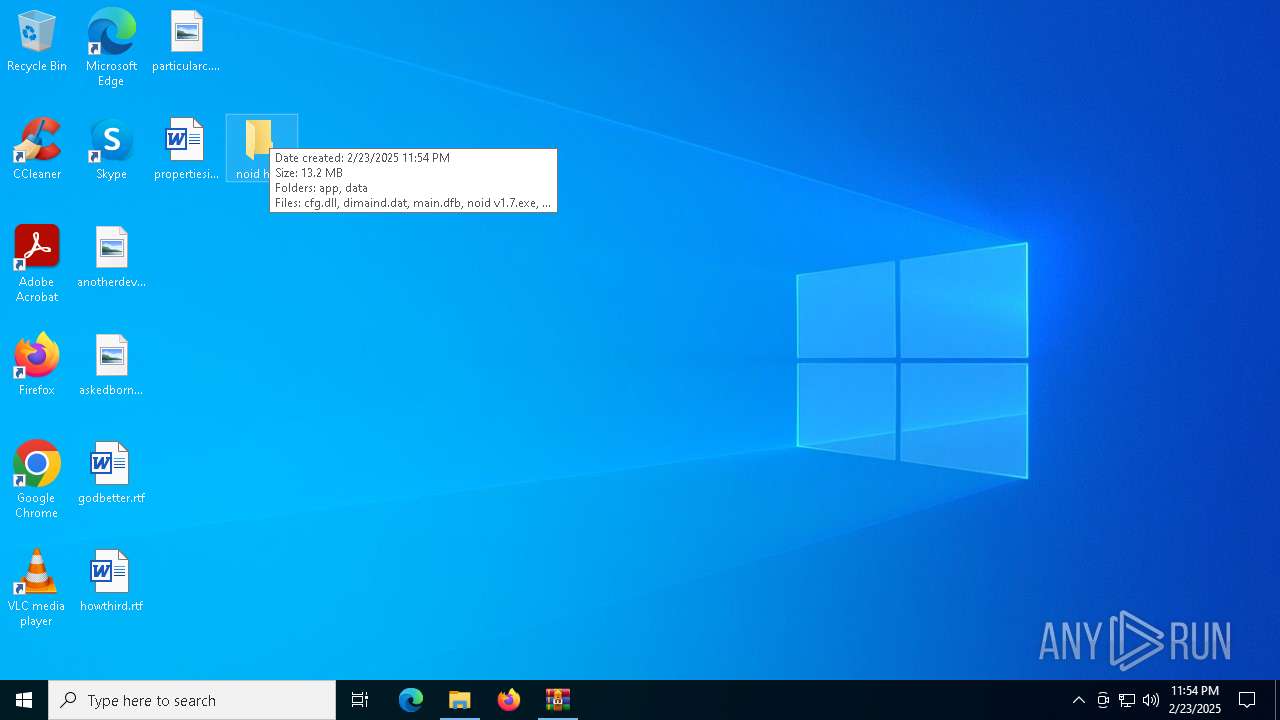
| 6776 | "C:\Users\admin\Desktop\noid hack\noid v1.7.exe" | C:\Users\admin\Desktop\noid hack\noid v1.7.exe | — | explorer.exe | |||||||||||
User: admin Company: MiTeC Integrity Level: MEDIUM Description: Task Manager DeLuxe Exit code: 666 Version: 4.8.8.0 Modules
| |||||||||||||||
| 7060 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | noid v1.7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 390
Read events
2 381
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\noid hack.rar | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
13
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2144.15917\noid hack\cfg.dll | text | |
MD5:DFEAA87A10DB2D555593E92F295F5A25 | SHA256:36CC45BFE3B63EA42AF564DD2C221219F7FB2E3F3CE93CA8CBA3A53539BCEB0F | |||
| 2144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2144.15917\noid hack\data\aim.dll | text | |
MD5:34D2AE40522C8ACA067172F3108D4BAC | SHA256:0416210832C265BD2BAD1319C65478194EC64789A7587CB35B51D1B4869586ED | |||
| 2144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2144.15917\noid hack\noid v1.7.exe | executable | |
MD5:A86EB878B2F5706507B2EA6D1FD0A051 | SHA256:59895A7BD49C7E17F52038172E0E417F2CBE9FBC176E8EDA1936974408FE2F94 | |||
| 2144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2144.15917\noid hack\dimaind.dat | text | |
MD5:1040F641D8DD01F38EE4888772506C2A | SHA256:51CB1292C9198346C8F943B5787D57502B8A580BC20B1DE9A425970ABB02A7C5 | |||
| 7060 | BitLockerToGo.exe | C:\ProgramData\F87377FFE6A749E3.dat | binary | |
MD5:FDDE63730E15DD2E18C540BA52B6A945 | SHA256:40740EAABD14FC0E08D3B5EE340C1E1B372E158F61EF58AEED1EE4B3A3F4492E | |||
| 2144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2144.15917\noid hack\updater.dll | text | |
MD5:DECACA5914D4409681C179F0F2A314F3 | SHA256:4D32733CCAC8B13505472B3B107E5FCD313D8E192433997DFD5F33548D4245B7 | |||
| 7060 | BitLockerToGo.exe | C:\ProgramData\55AFAD486E70443D.dat | binary | |
MD5:0B2213BCE3950F1E95FEEB8E8B3B9543 | SHA256:71DB3D87713A320BA9FD3043392509B430630CFCF574EE84118406D6471CFC5A | |||
| 7060 | BitLockerToGo.exe | C:\ProgramData\39094FF5C4E5785E.dat | — | |
MD5:— | SHA256:— | |||
| 2144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2144.15917\noid hack\main.dfb | text | |
MD5:20B8E57E778D8C1B65A9F965B5B7050C | SHA256:99E7FFDB58BFBDB05B3F326655029CACB932809567B01392C63DC3D6D50FA50F | |||
| 7060 | BitLockerToGo.exe | C:\ProgramData\094C2031D68848F4.dat | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
40
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4504 | svchost.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4504 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6372 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6904 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6904 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6072 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4504 | svchost.exe | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4504 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4504 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |