| URL: | https://dnp.motorhinoafrica.com/b#bnBkL2NjdmlkQW9wdHNmZW1iL3Rmb2hiMDMzbjhOWmhRTFpjVnRpTnlrWHkyNjlFe1d0eGI4aEZCMzFQSjVOV3NpbjpSMmxaQjVQbXlwSk90WG00RGZ3czN4RGJiZGZpQ1dHblZneDZnMWQyWk5jc3NCMWNSVU9VaVsxdWhDRllOTTg2N0dqZE9PREpWU3lGcnM4TnNkZ01Ha1J2VUlkUFRKREl1RFJidDp2bzNlODU0NntxM2h1e0d0Q3RKb3FwV3VrYklyZUt0ZjhlSXFXdzNwSHtDbnRwRHBac0tiMm5aNmM6WFVoNW1OQzFsR20zQnE0UWtkOkpicEhqWlYyb3toMk1Jak1LdjZITWQ2dTk4UjpbVWpuZlJ5T2dZRE9mbkRGcTpxR3lPZklQVTFQc1l1M01HdkRVZUlPNHQ0RTFPZ1BLeExCRmtbZ054ZWpXdzdxNHlXSUNpb0lGOGNUdk54b3F2T0pIY3lKY0hUcUJEcEVLZnRiS3ZMMjI4TmIyb0RJTm9vMkVsQndvb3tMeHY4Tm06Y3h0MTQ2eHR7MkdGNzM0THt4W0RjTE9IV1lCbHg2c2czbVk1VEtzRnVlQzdyc295S01mQmJIUjdvZ3BOZWlLWDNubXAxTXd1STpaWGwzZ3pySENHc1lLNFE5NkhrOmhra0tqVDMxbVBIbTdEVm9GbVQ5e3l4U2pZd05SOXVzeUxKcVREZVt3V0tERHpMV2VoRWtUN2ZwaFd3Z1p4V3Uye3tIe1JKYmYzck5rdlsxamJqNG1bQ3BwUGpZb1RCW2RzRzVRUUJ7U3tCeG1MaEpqbk5SeGZCSXV3RDd3UUdJMUpqY3ZpWFhZZ2dbN2VLajhCMjFvaWVSVWlIeTRCNGY3N0I1UEJLRndkOTJwaGxTM0xbVHIxc1h7cXZvS1ZWSzR4V1JjVlo4SG1vaVlbQkYzT0cyTVh7aEhKTW5kSFRmTWJwbmcyeHtzQ1RGUltCRW9qSG5LZHdyamxbZE1iR29jeWtmSk9MRjQ2S3N6e0JabDZ7WEp0OWt2RGVQTENDbWRtNmpKNVhqS3puV1tOaUpFVFU6cHl4aklqVUQ1U0d0ZXg0NElyazZ5RklaUDExbmJDekhmRXlrW250SGkyN1JFZWJrRUdpRHp7SFI1dkVFSUVETGtkbVZmMjFHRllLTjROUndETWNEV1szW2UzRk9tSjlabTFZb0tvd202dGRlW251OXJ2UXpNe1FncVZPSEx4czJWcGNFMkhPVFpNOlRNT0xQN1FWQjM1aXZyd2hVSXBkY0xoRUhQS2htSXFCc0d4SEpncDVbdXtxWzdtR1tWa297eU9pbFljOEl2V0gxWlU3aHBaaDQ5bThsU2owcWpwdzBmZS93b2p5Zm1iaXFmZDAwO3RxdXVp |
| Full analysis: | https://app.any.run/tasks/fd1d7a4c-48a9-49fe-8871-7f2d4c79de71 |
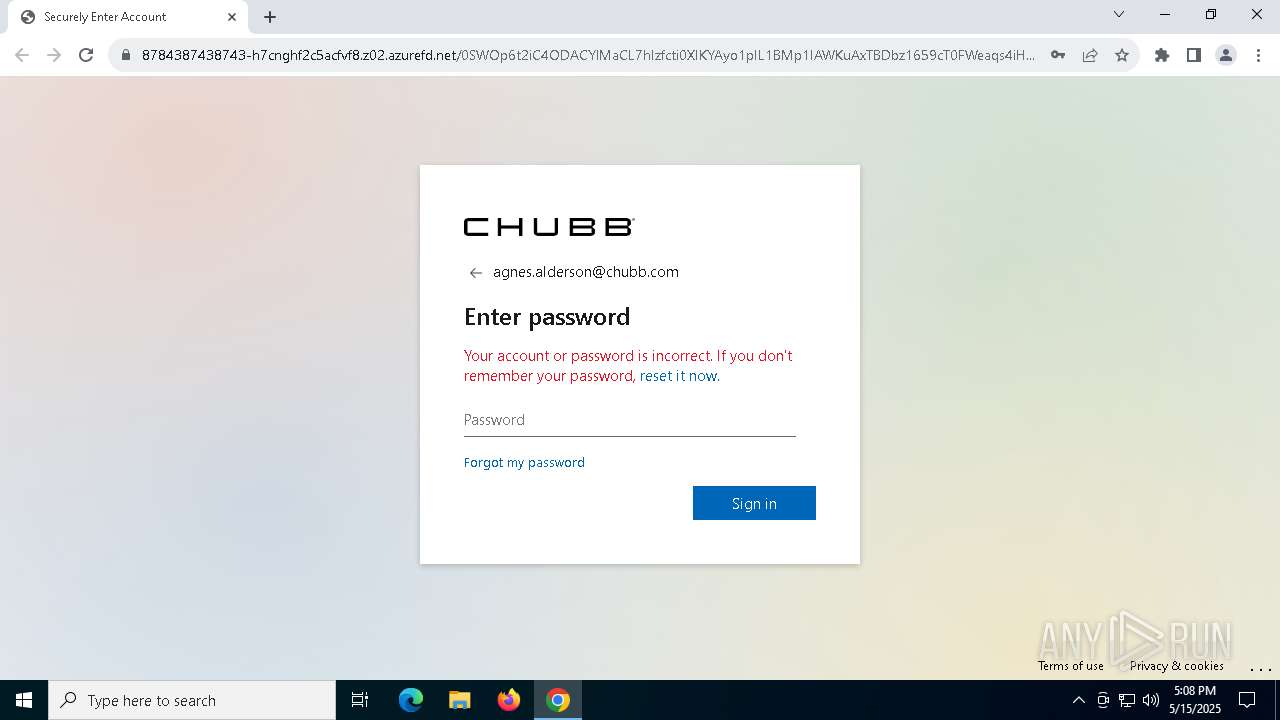
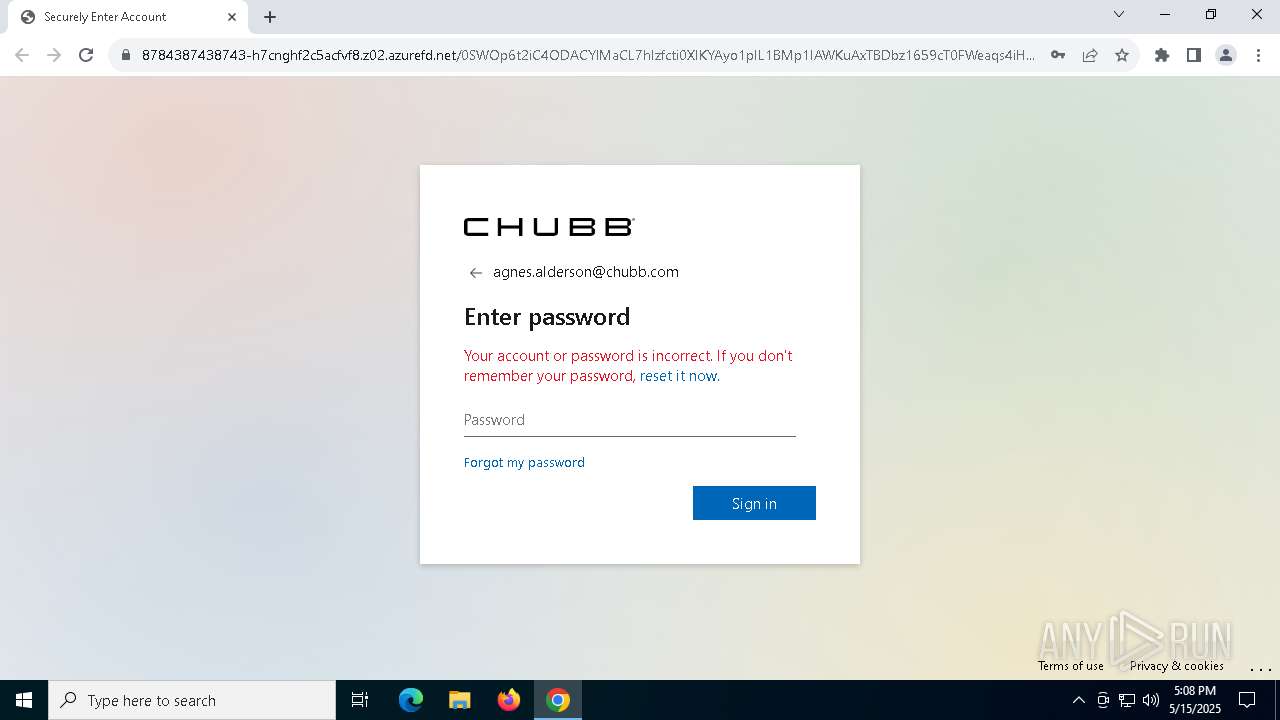
| Verdict: | Malicious activity |
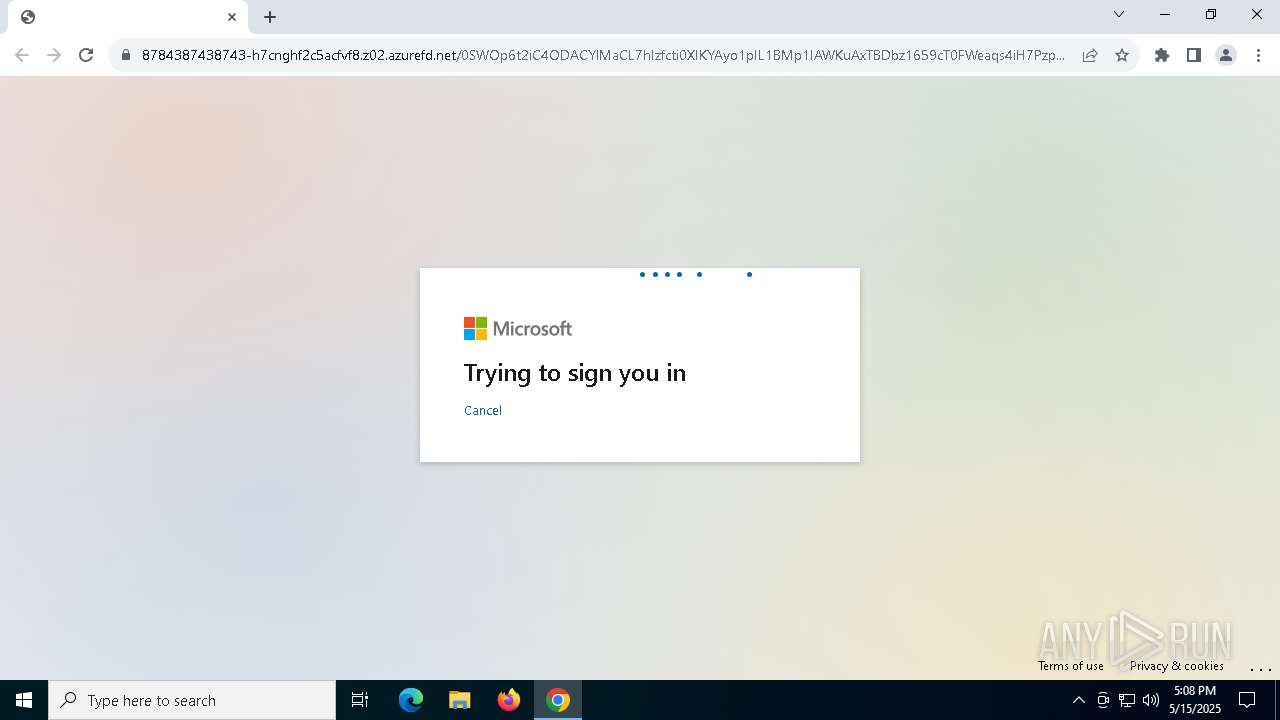
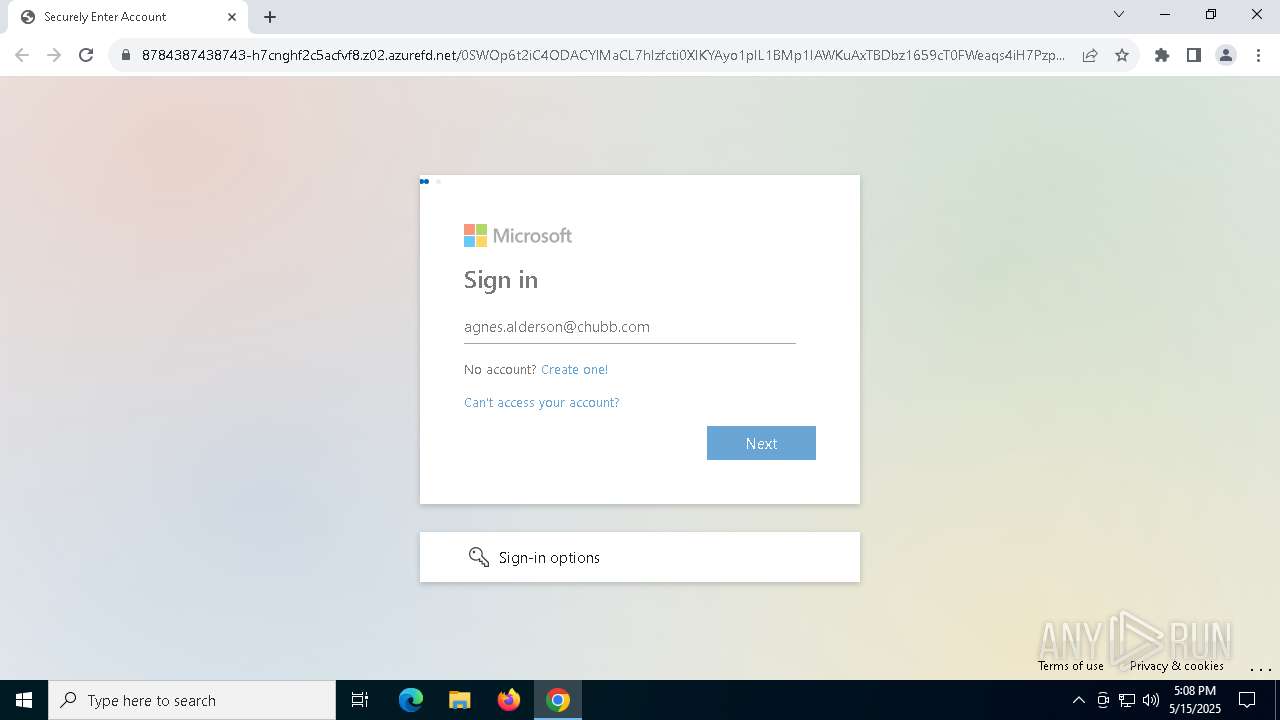
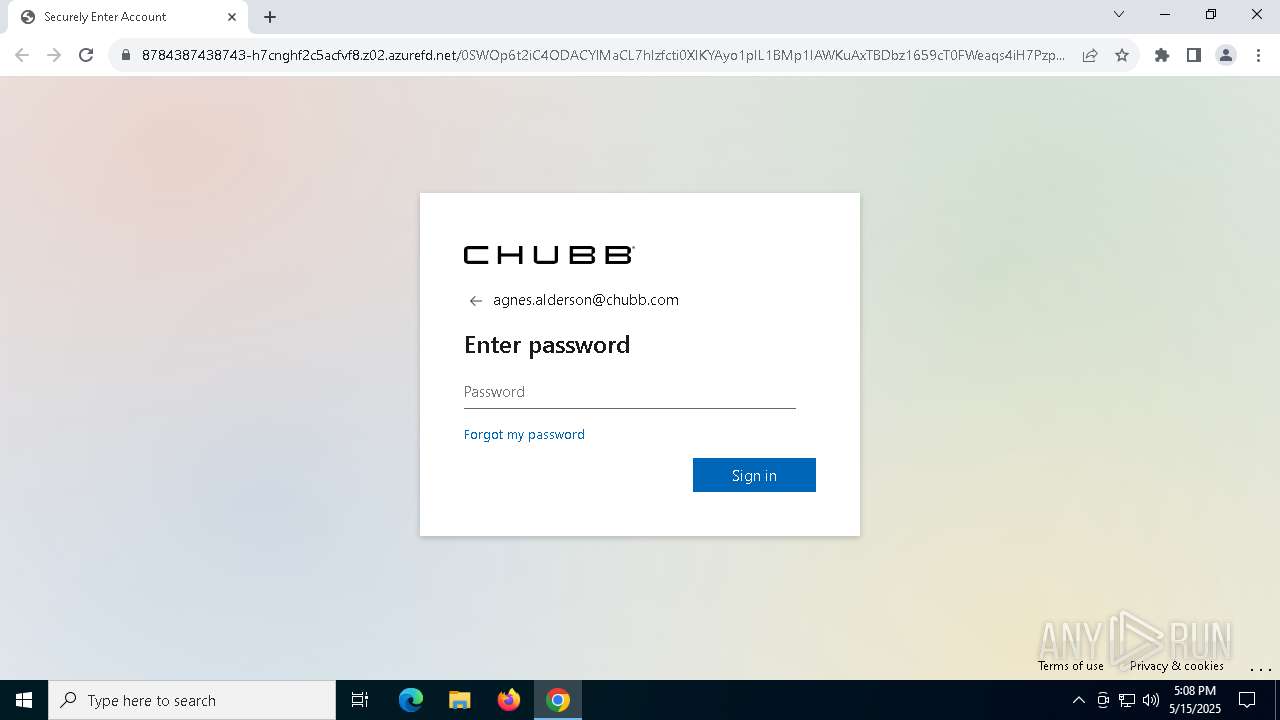
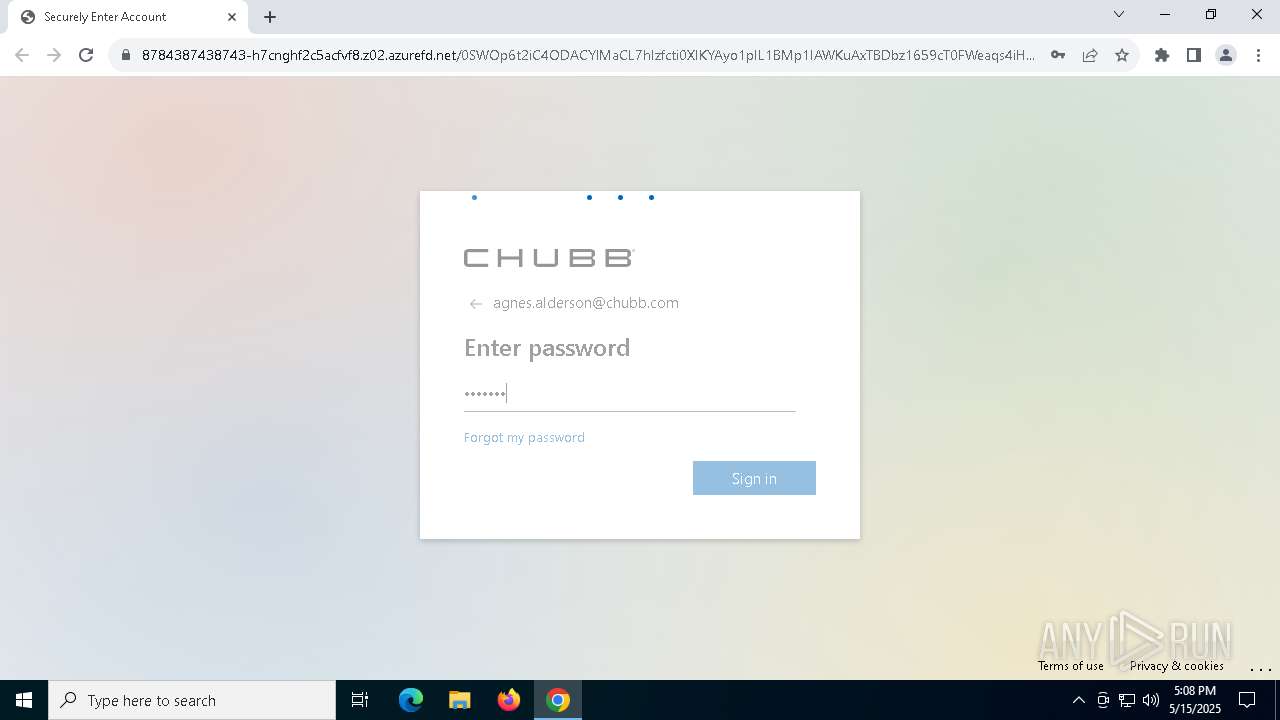
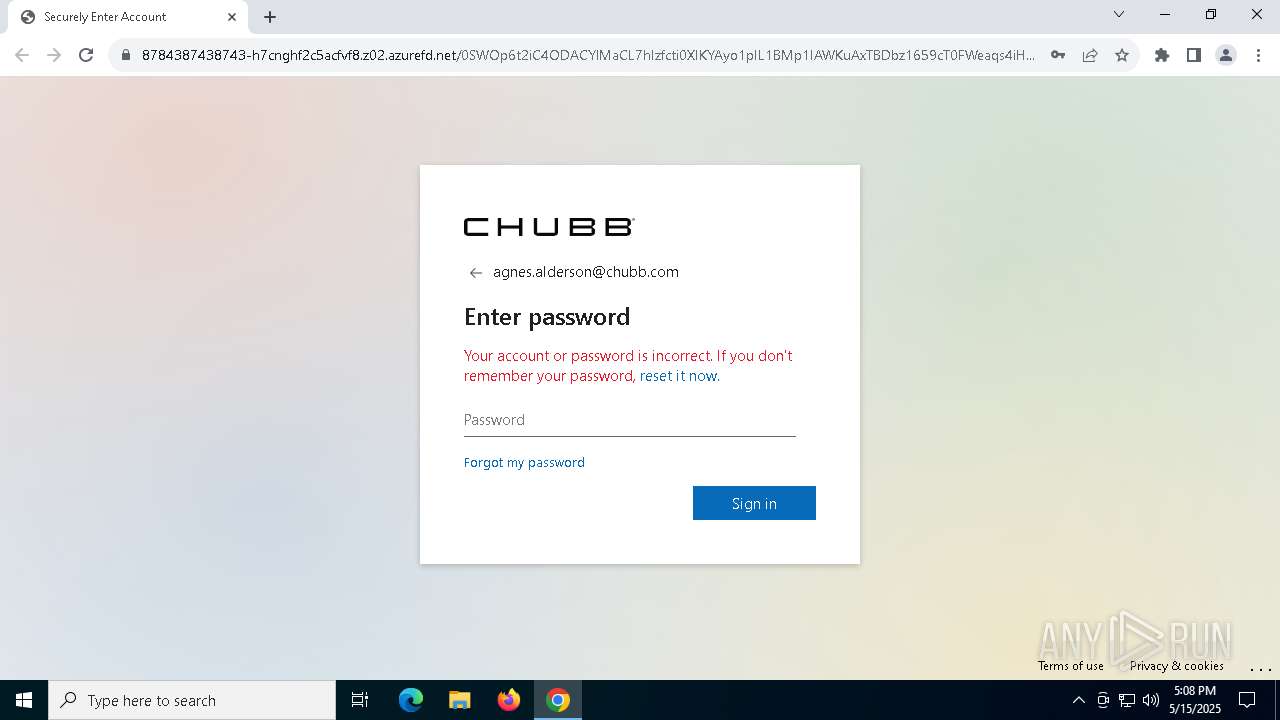
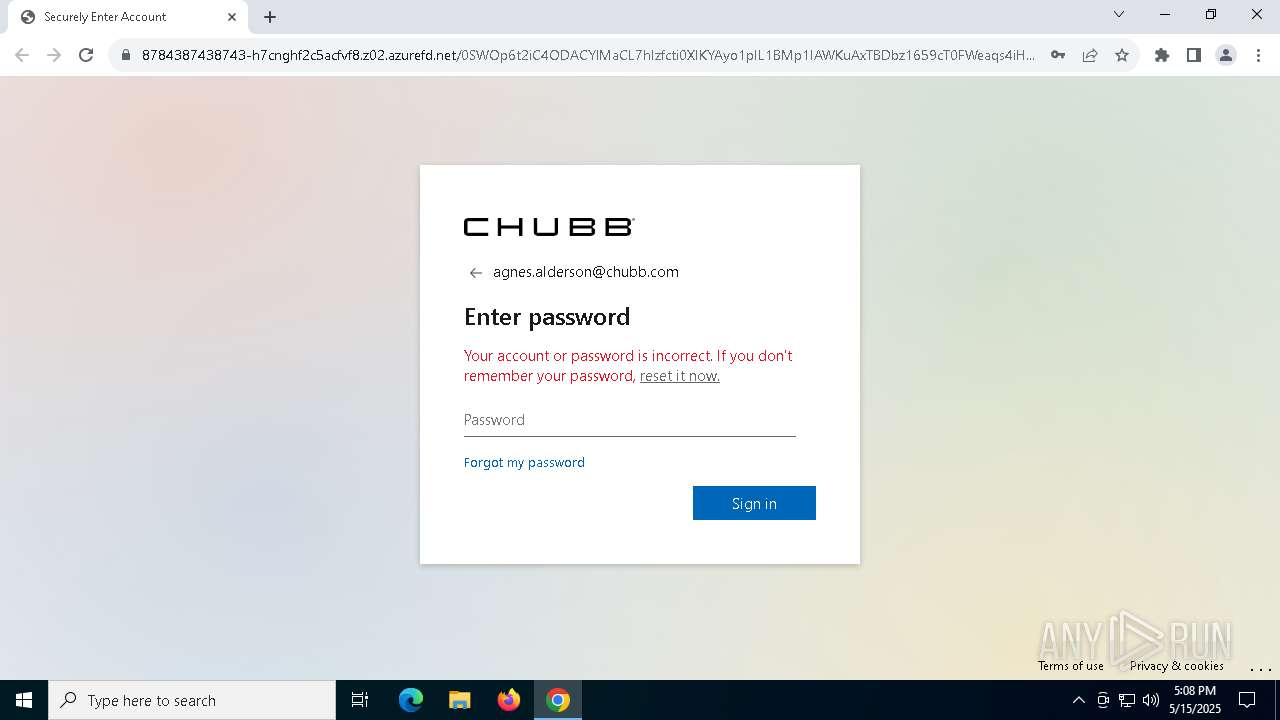
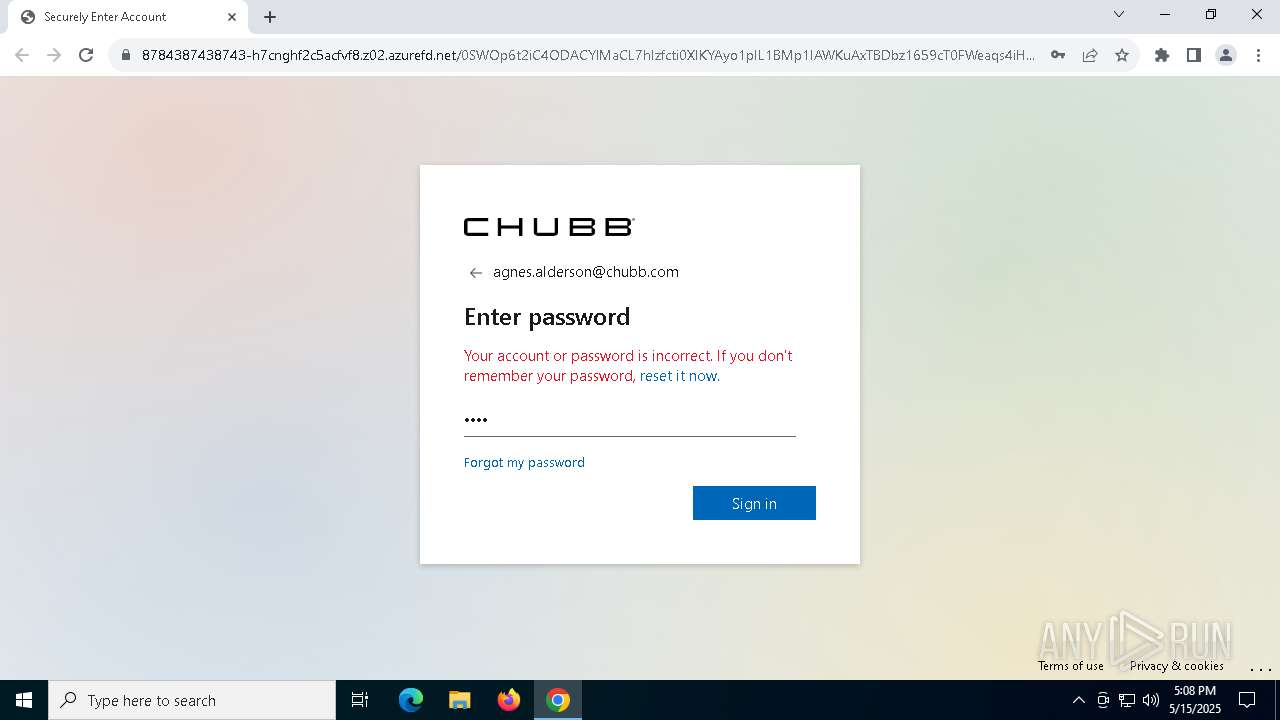
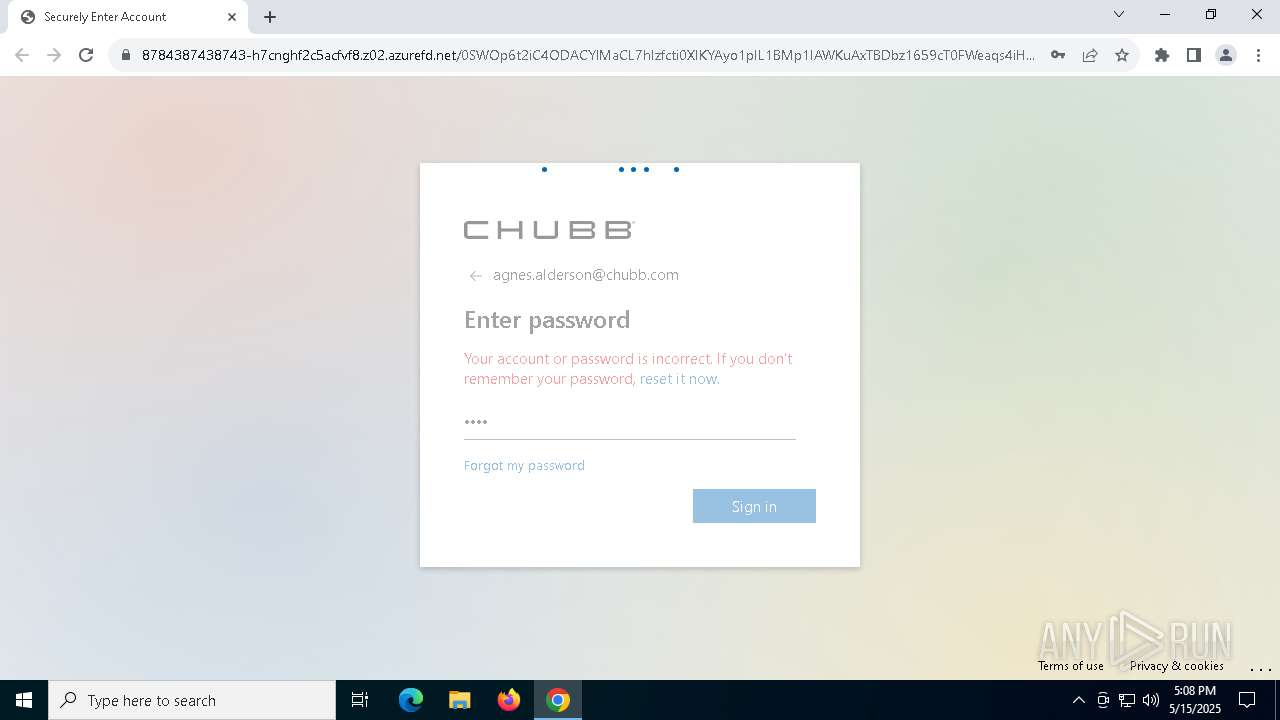
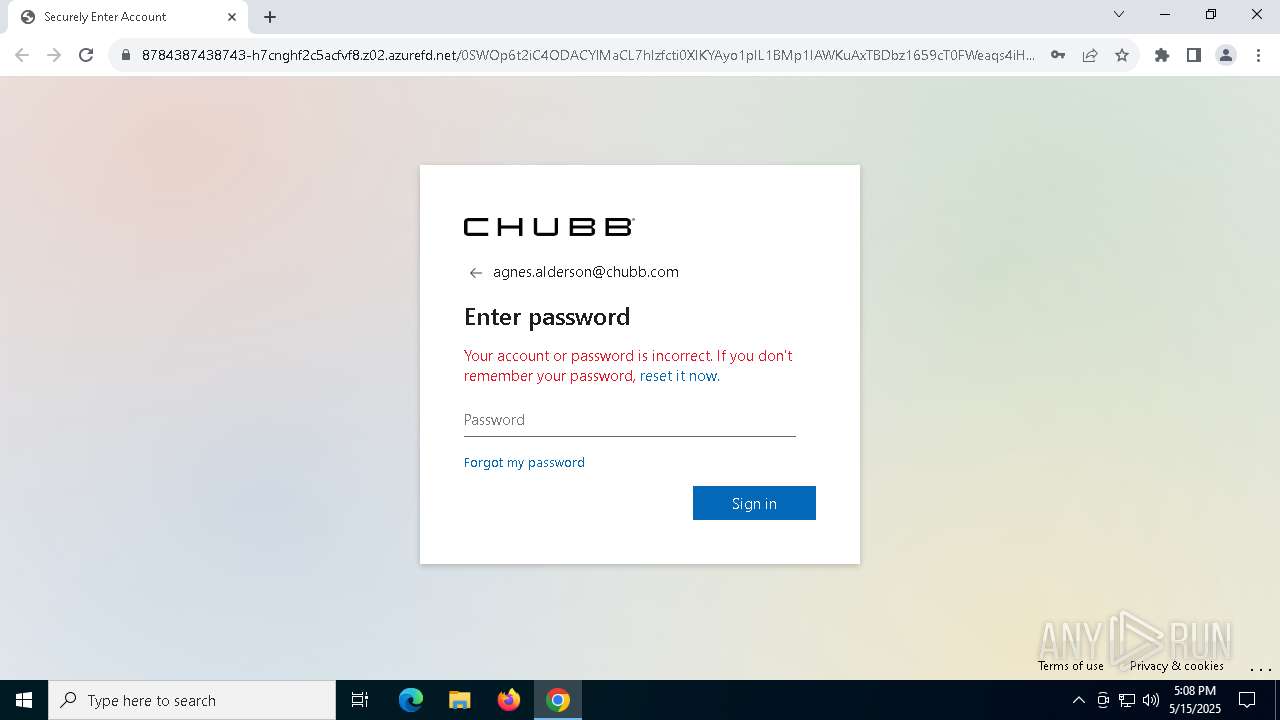
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | May 15, 2025, 17:07:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D56D961C80716D2030BA8FD538FA3E2 |
| SHA1: | 18B7E6C76C4ABFEFA615E5EA8C5634F06408BB77 |
| SHA256: | C9268C40BB289E934A5B8EAA6727AE8D0E69F21651C568775CF5A33391E7E790 |
| SSDEEP: | 24:2VwJIXkTpSUI2HOTEgsI+EHDURRDAGdwqLu5uJ1p4F3W0SIZgxhR0yd7VUc:xuipSn2qEghUjDAGdwqLkuJ1uG0UrysT |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7536)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 7308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4804 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://dnp.motorhinoafrica.com/b#bnBkL2NjdmlkQW9wdHNmZW1iL3Rmb2hiMDMzbjhOWmhRTFpjVnRpTnlrWHkyNjlFe1d0eGI4aEZCMzFQSjVOV3NpbjpSMmxaQjVQbXlwSk90WG00RGZ3czN4RGJiZGZpQ1dHblZneDZnMWQyWk5jc3NCMWNSVU9VaVsxdWhDRllOTTg2N0dqZE9PREpWU3lGcnM4TnNkZ01Ha1J2VUlkUFRKREl1RFJidDp2bzNlODU0NntxM2h1e0d0Q3RKb3FwV3VrYklyZUt0ZjhlSXFXdzNwSHtDbnRwRHBac0tiMm5aNmM6WFVoNW1OQzFsR20zQnE0UWtkOkpicEhqWlYyb3toMk1Jak1LdjZITWQ2dTk4UjpbVWpuZlJ5T2dZRE9mbkRGcTpxR3lPZklQVTFQc1l1M01HdkRVZUlPNHQ0RTFPZ1BLeExCRmtbZ054ZWpXdzdxNHlXSUNpb0lGOGNUdk54b3F2T0pIY3lKY0hUcUJEcEVLZnRiS3ZMMjI4TmIyb0RJTm9vMkVsQndvb3tMeHY4Tm06Y3h0MTQ2eHR7MkdGNzM0THt4W0RjTE9IV1lCbHg2c2czbVk1VEtzRnVlQzdyc295S01mQmJIUjdvZ3BOZWlLWDNubXAxTXd1STpaWGwzZ3pySENHc1lLNFE5NkhrOmhra0tqVDMxbVBIbTdEVm9GbVQ5e3l4U2pZd05SOXVzeUxKcVREZVt3V0tERHpMV2VoRWtUN2ZwaFd3Z1p4V3Uye3tIe1JKYmYzck5rdlsxamJqNG1bQ3BwUGpZb1RCW2RzRzVRUUJ7U3tCeG1MaEpqbk5SeGZCSXV3RDd3UUdJMUpqY3ZpWFhZZ2dbN2VLajhCMjFvaWVSVWlIeTRCNGY3N0I1UEJLRndkOTJwaGxTM0xbVHIxc1h7cXZvS1ZWSzR4V1JjVlo4SG1vaVlbQkYzT0cyTVh7aEhKTW5kSFRmTWJwbmcyeHtzQ1RGUltCRW9qSG5LZHdyamxbZE1iR29jeWtmSk9MRjQ2S3N6e0JabDZ7WEp0OWt2RGVQTENDbWRtNmpKNVhqS3puV1tOaUpFVFU6cHl4aklqVUQ1U0d0ZXg0NElyazZ5RklaUDExbmJDekhmRXlrW250SGkyN1JFZWJrRUdpRHp7SFI1dkVFSUVETGtkbVZmMjFHRllLTjROUndETWNEV1szW2UzRk9tSjlabTFZb0tvd202dGRlW251OXJ2UXpNe1FncVZPSEx4czJWcGNFMkhPVFpNOlRNT0xQN1FWQjM1aXZyd2hVSXBkY0xoRUhQS2htSXFCc0d4SEpncDVbdXtxWzdtR1tWa297eU9pbFljOEl2V0gxWlU3aHBaaDQ5bThsU2owcWpwdzBmZS93b2p5Zm1iaXFmZDAwO3RxdXVp" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc88e5dc40,0x7ffc88e5dc4c,0x7ffc88e5dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1904 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2100 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2240 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3048 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3120 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3508 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 8008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3228 --field-trial-handle=1872,i,10003240948664620681,17329768951442890682,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 | |||||||||||||||
Total events
2 656
Read events
2 651
Write events
5
Delete events
0
Modification events
| (PID) Process: | (7308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7308) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
25
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c797.TMP | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c797.TMP | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c797.TMP | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c797.TMP | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c797.TMP | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
50
DNS requests
57
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7308 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7536 | chrome.exe | 142.251.173.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7536 | chrome.exe | 167.172.166.226:443 | dnp.motorhinoafrica.com | DIGITALOCEAN-ASN | DE | unknown |
7536 | chrome.exe | 13.107.253.45:443 | 4839794398349343-g4eydqdkguhcdvgs.z02.azurefd.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
dnp.motorhinoafrica.com |
| unknown |
accounts.google.com |
| whitelisted |
4839794398349343-g4eydqdkguhcdvgs.z02.azurefd.net |
| malicious |
cephalexinv.de |
| unknown |
8784387438743-h7cnghf2c5acfvf8.z02.azurefd.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7536 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (g4eydqdkguhcdvgs .z02 .azurefd .net) |
7536 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (g4eydqdkguhcdvgs .z02 .azurefd .net) |
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7536 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7536 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Fake Microsoft Sign-In Page (Login w/o Signin) |