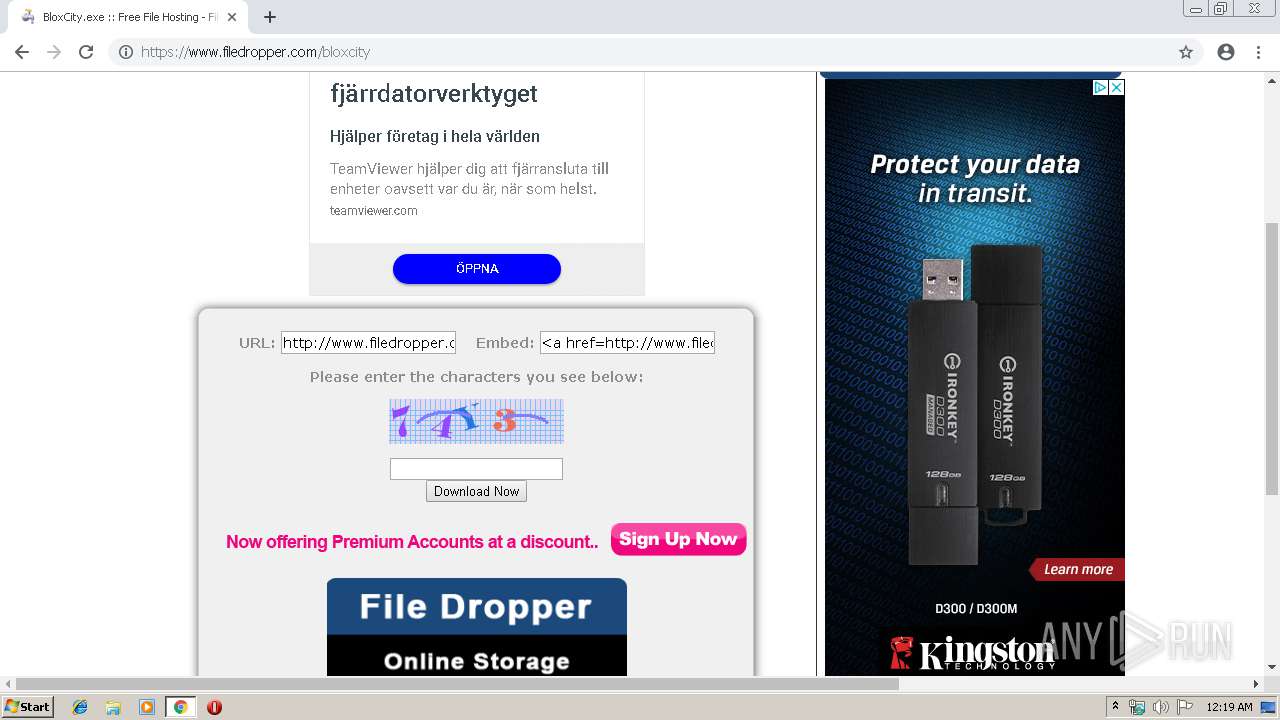
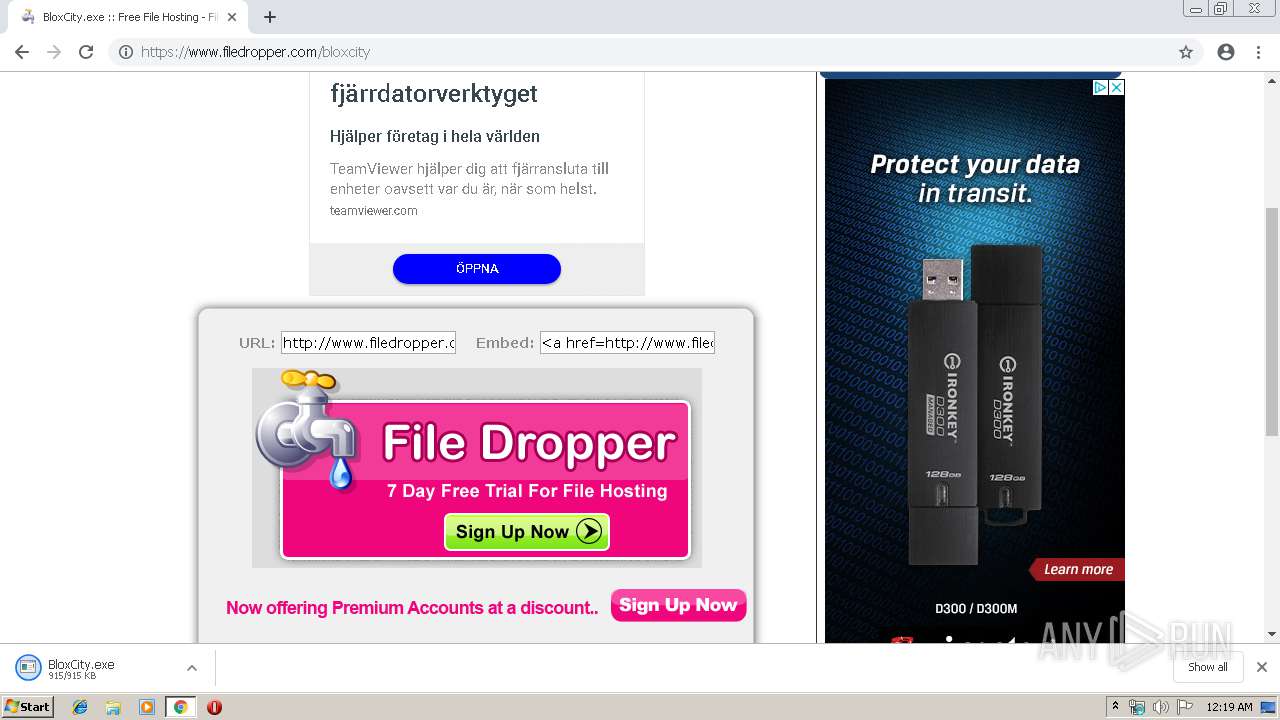
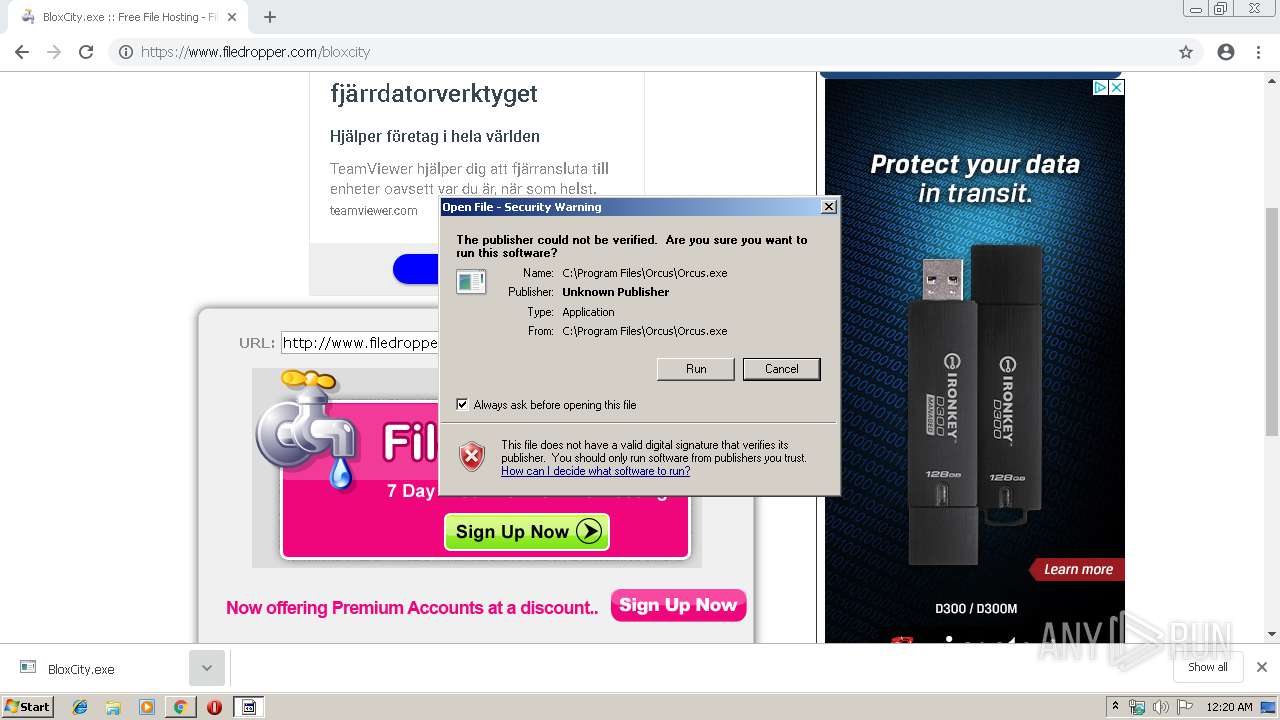
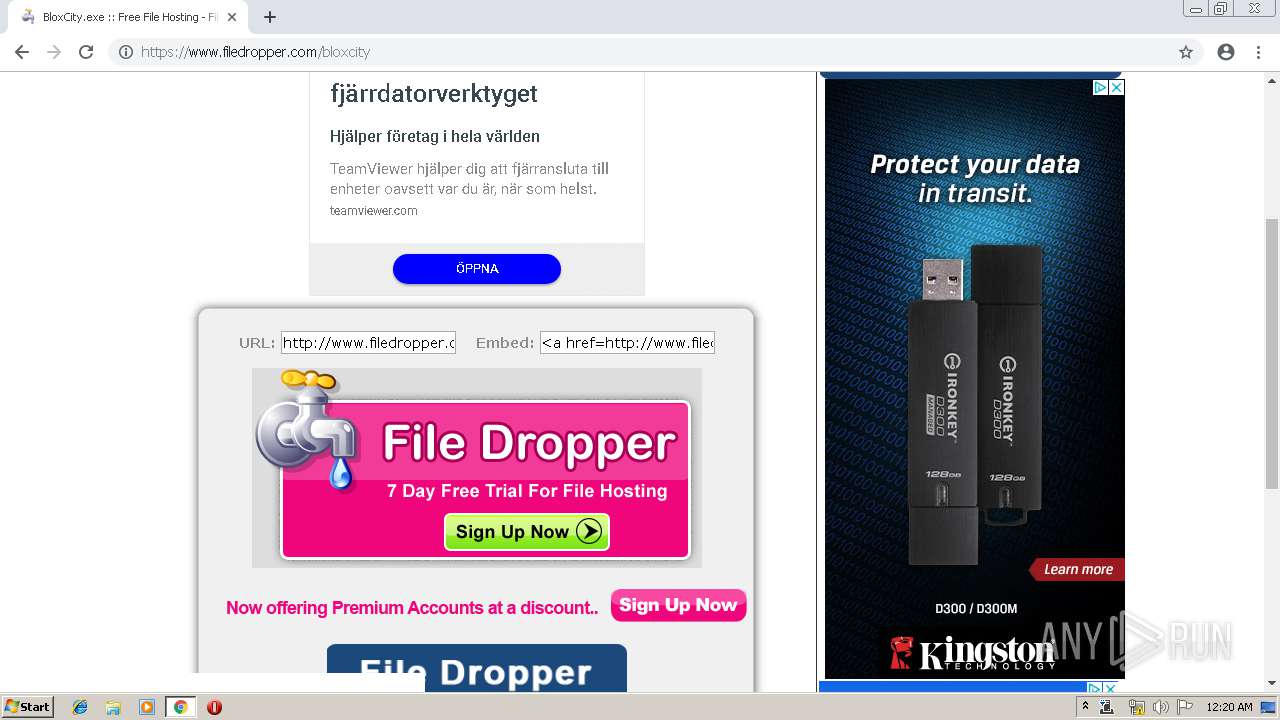
| URL: | http://www.filedropper.com/bloxcity |
| Full analysis: | https://app.any.run/tasks/069c18e5-fb28-42f8-91ee-2ccee27cb411 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | June 09, 2019, 23:19:02 |
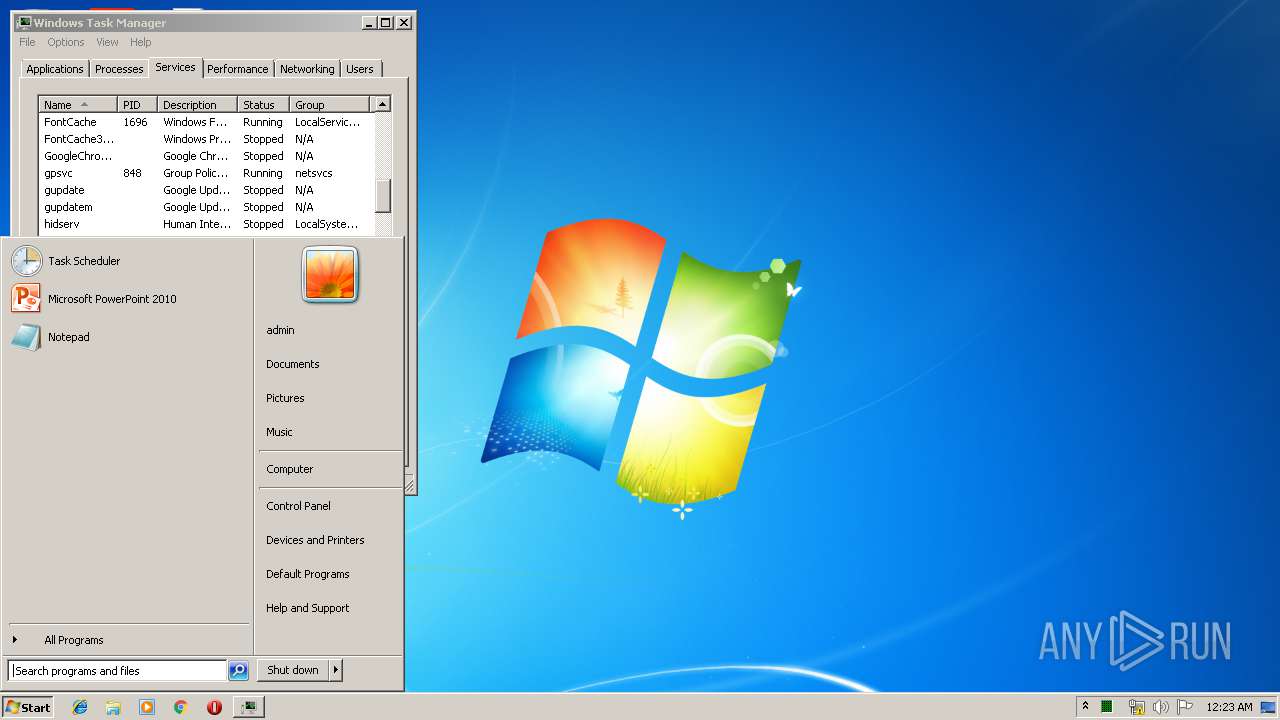
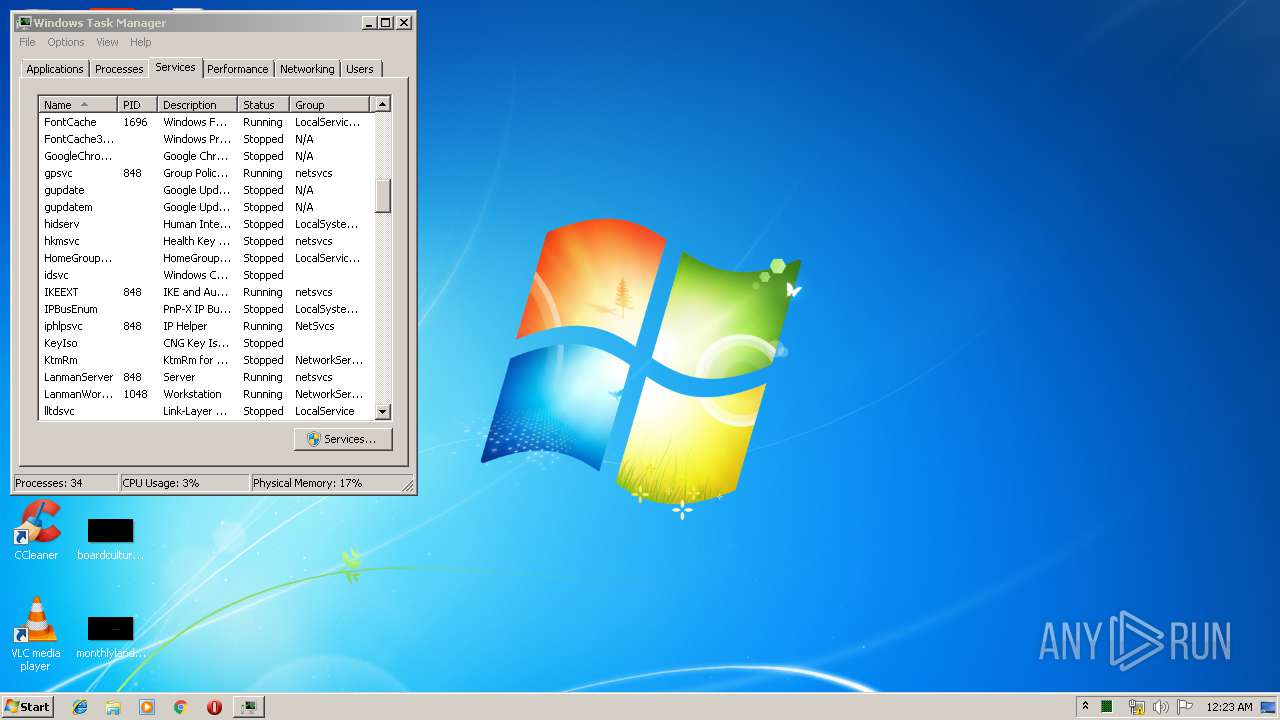
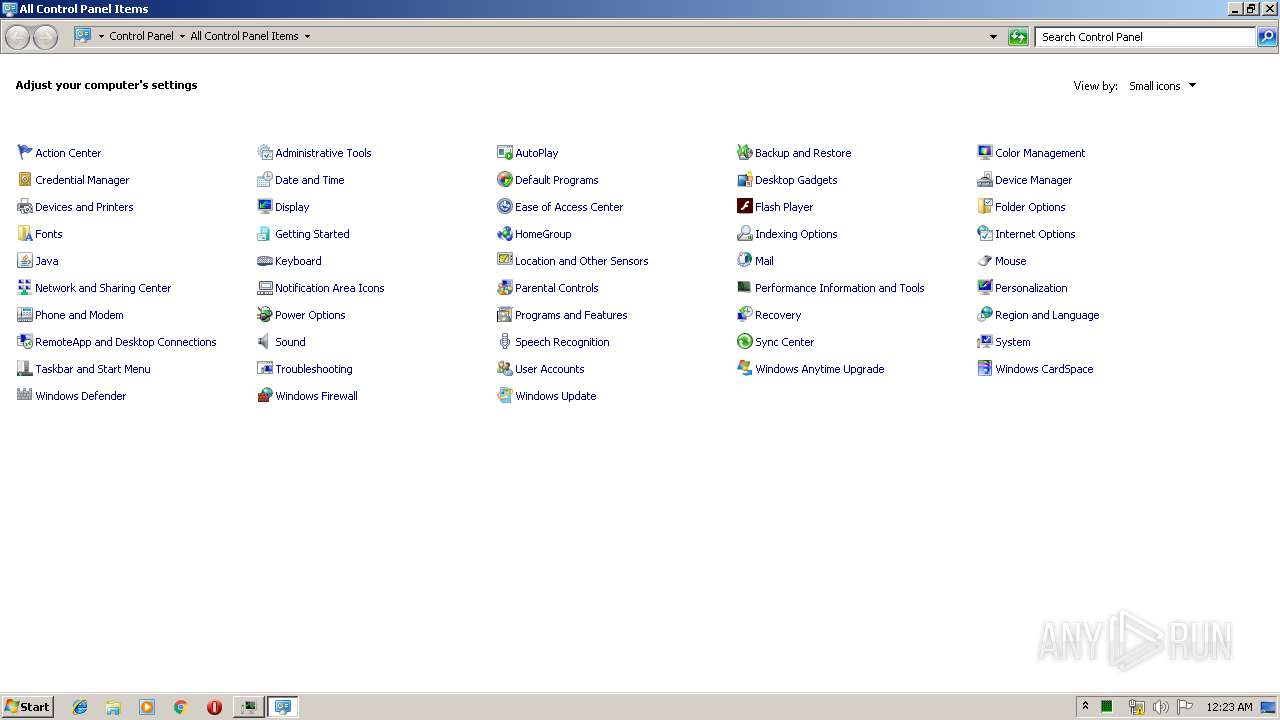
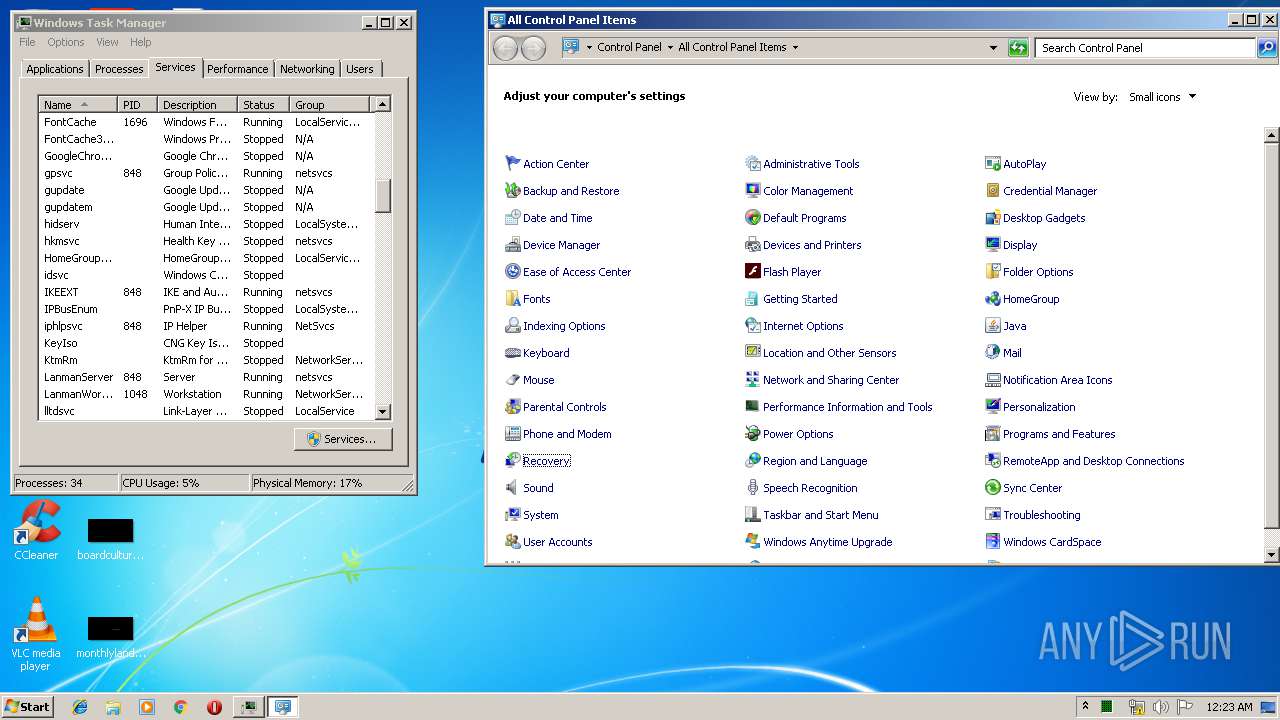
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FEB655DC23E244518B3FB0D7D81E132F |
| SHA1: | 2F019C2E2CCB16A2635673EFA87638983BDF8425 |
| SHA256: | C86744BBB559F994ADB9D4E42EE5826470068824E5662A243F328E414C42432F |
| SSDEEP: | 3:N1KJS4QuXrKGJ:Cc4Qw |
MALICIOUS
Application was dropped or rewritten from another process
- BloxCity.exe (PID: 3132)
- BloxCity.exe (PID: 2744)
- WindowsInput.exe (PID: 2224)
- WindowsInput.exe (PID: 3480)
- Orcus.exe (PID: 3292)
- Orcus.exe (PID: 2260)
- OrcusWatchdog.exe (PID: 3452)
- OrcusWatchdog.exe (PID: 2940)
Orcus was detected
- BloxCity.exe (PID: 2744)
- Orcus.exe (PID: 3292)
- Orcus.exe (PID: 2260)
Changes the autorun value in the registry
- Orcus.exe (PID: 3292)
Loads the Task Scheduler COM API
- Orcus.exe (PID: 3292)
Orcus RAT was detected
- OrcusWatchdog.exe (PID: 3452)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2868)
Executable content was dropped or overwritten
- BloxCity.exe (PID: 2744)
- chrome.exe (PID: 2868)
- Orcus.exe (PID: 3292)
Creates files in the Windows directory
- BloxCity.exe (PID: 2744)
- WindowsInput.exe (PID: 2224)
Executed as Windows Service
- WindowsInput.exe (PID: 3480)
Creates files in the program directory
- BloxCity.exe (PID: 2744)
Starts itself from another location
- BloxCity.exe (PID: 2744)
Executed via Task Scheduler
- Orcus.exe (PID: 2260)
Creates files in the user directory
- Orcus.exe (PID: 3292)
Application launched itself
- OrcusWatchdog.exe (PID: 3452)
INFO
Changes settings of System certificates
- chrome.exe (PID: 2868)
Application launched itself
- chrome.exe (PID: 2868)
Reads Internet Cache Settings
- chrome.exe (PID: 2868)
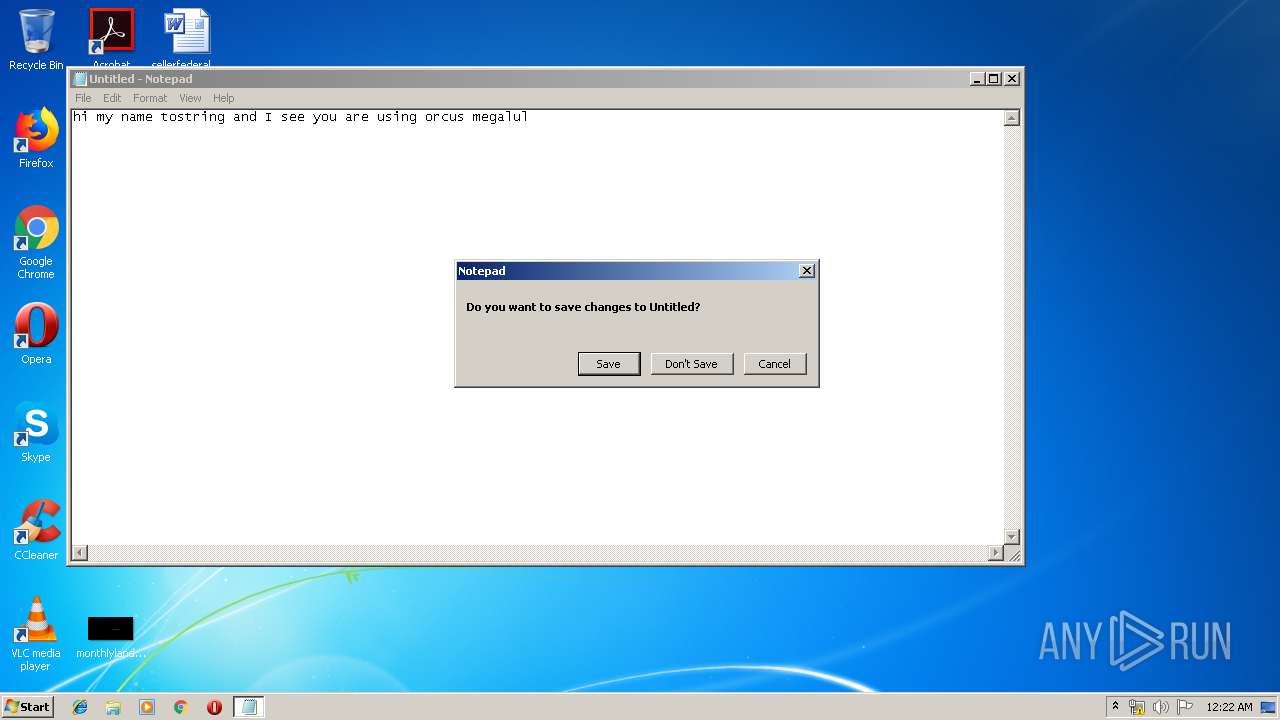
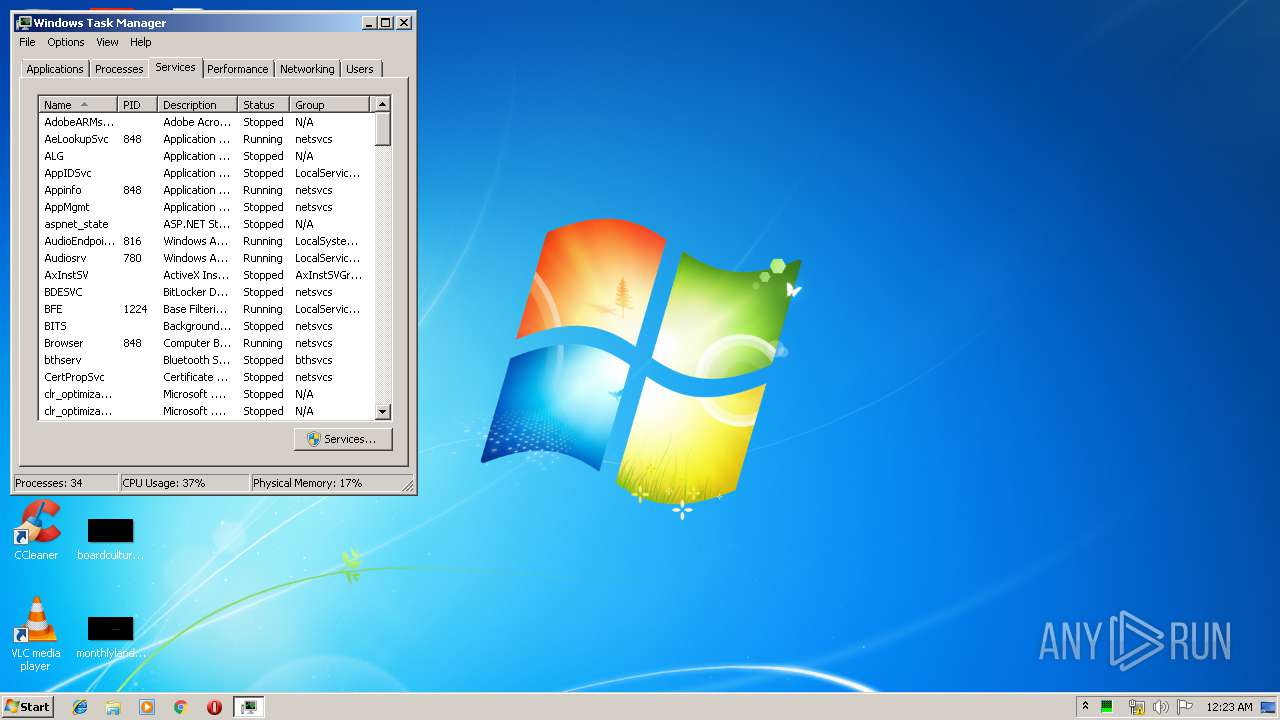
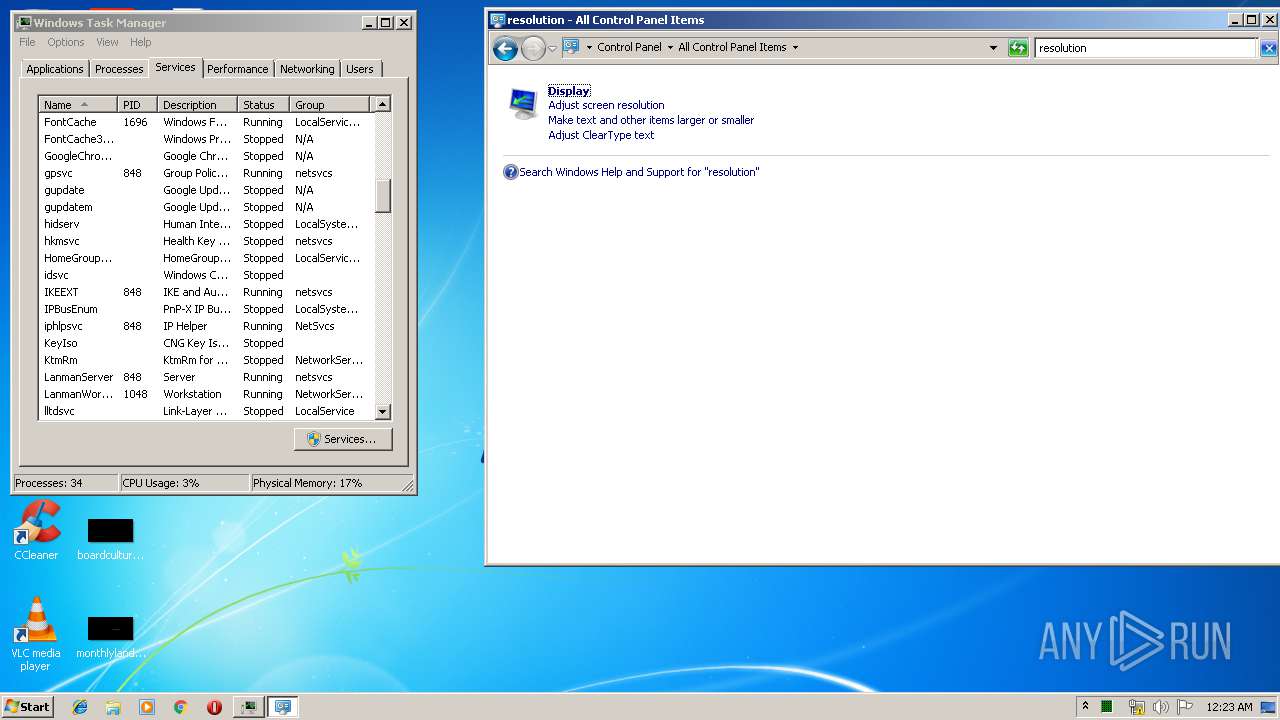
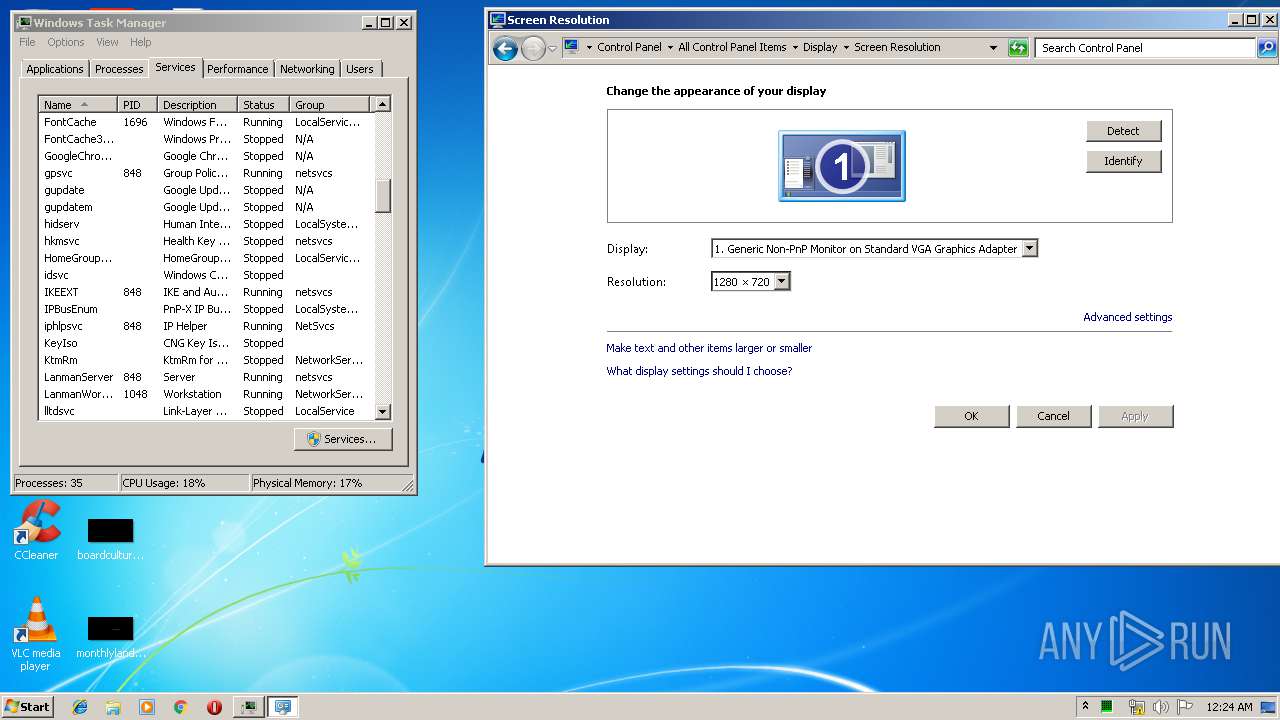
Manual execution by user
- notepad.exe (PID: 1772)
- taskmgr.exe (PID: 3208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
34
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1772 | "C:\Windows\system32\notepad.exe" | C:\Windows\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3535594587273070365 --mojo-platform-channel-handle=4424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2224 | "C:\Windows\system32\WindowsInput.exe" --install | C:\Windows\system32\WindowsInput.exe | — | BloxCity.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Windows Input Exit code: 0 Version: 0.1.0 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Orcus\Orcus.exe" | C:\Program Files\Orcus\Orcus.exe | taskeng.exe | ||||||||||||
User: admin Company: 3dsBoi Integrity Level: HIGH Description: Made by an 3lite Hacker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=9224297308187589924 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9224297308187589924 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4845652204187610948 --mojo-platform-channel-handle=4408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5404049539730795637 --mojo-platform-channel-handle=4436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2872 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\Downloads\BloxCity.exe" | C:\Users\admin\Downloads\BloxCity.exe | chrome.exe | ||||||||||||
User: admin Company: 3dsBoi Integrity Level: HIGH Description: Made by an 3lite Hacker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.filedropper.com/bloxcity | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 763
Read events
1 639
Write events
119
Delete events
5
Modification events
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2868-13204595958459250 |
Value: 259 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
6
Suspicious files
113
Text files
220
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
75
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2868 | chrome.exe | GET | 301 | 144.76.226.41:80 | http://www.filedropper.com/bloxcity | DE | html | 244 b | suspicious |
2868 | chrome.exe | GET | 301 | 144.76.226.41:80 | http://www.filedropper.com/images/filedropper_banner.png | DE | html | 265 b | suspicious |
2868 | chrome.exe | GET | 200 | 173.194.19.137:80 | http://r3---sn-5go7yn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=46.246.1.160&mm=28&mn=sn-5go7yn7e&ms=nvh&mt=1560121727&mv=u&pl=26&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2868 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 503 b | whitelisted |
2868 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2868 | chrome.exe | GET | 200 | 104.20.3.47:80 | http://c.statcounter.com/3541212/0/872cdcc5/1/ | US | image | 49 b | whitelisted |
2868 | chrome.exe | GET | 200 | 104.20.3.47:80 | http://c.statcounter.com/3541212/0/872cdcc5/1/ | US | image | 49 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2868 | chrome.exe | 104.20.3.47:80 | c.statcounter.com | Cloudflare Inc | US | shared |
2868 | chrome.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.205.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 172.217.16.194:443 | adservice.google.se | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.206.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2868 | chrome.exe | 172.217.22.40:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.208.34:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 144.76.226.41:80 | www.filedropper.com | Hetzner Online GmbH | DE | unknown |
2868 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.filedropper.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
c.statcounter.com |
| whitelisted |
adservice.google.se |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |