| File name: | svhost.exe |
| Full analysis: | https://app.any.run/tasks/684f9809-f012-43b2-92c6-00158b4fe9b7 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | August 13, 2019, 14:11:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 827156E633E18F8EABC3D7ADB7B94FEF |
| SHA1: | 6CA24AC0DAD6B7BE4128F9C2DE624EA513438C23 |
| SHA256: | C8267562616B9257CAD37631F513DC20C5549E2A69B427786F7976518E73F559 |
| SSDEEP: | 12288:DihWL2ZoOunrvuJ0yokjU76AKtCw8+tfwFZse:DikLQoVr2J87XKv88MZT |
MALICIOUS
Runs app for hidden code execution
- svhost.exe (PID: 1388)
Loads dropped or rewritten executable
- svhost.exe (PID: 1388)
Changes the autorun value in the registry
- wlanext.exe (PID: 1088)
FORMBOOK was detected
- explorer.exe (PID: 128)
Formbook was detected
- wlanext.exe (PID: 1088)
- Firefox.exe (PID: 2460)
Actions looks like stealing of personal data
- wlanext.exe (PID: 1088)
Connects to CnC server
- explorer.exe (PID: 128)
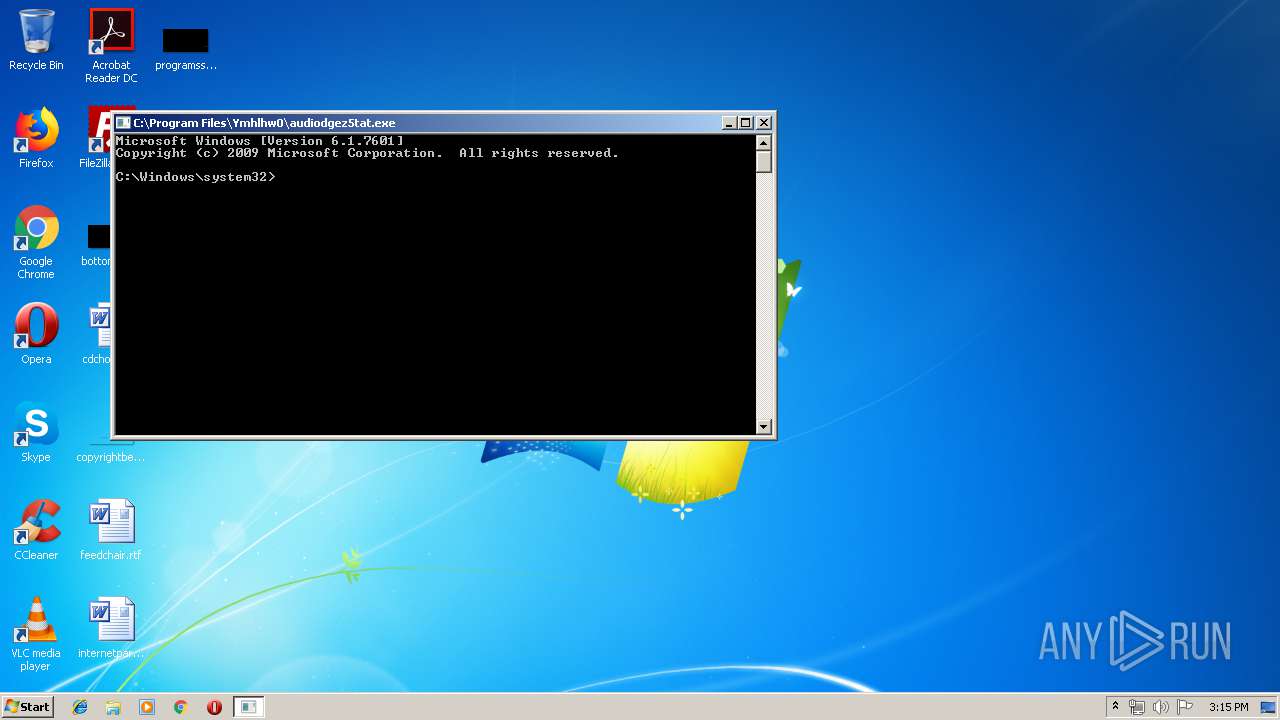
Application was dropped or rewritten from another process
- cmd.exe (PID: 1644)
- audiodgez5tat.exe (PID: 3344)
- cmd.exe (PID: 3464)
Stealing of credential data
- wlanext.exe (PID: 1088)
SUSPICIOUS
Starts CMD.EXE for commands execution
- wlanext.exe (PID: 1088)
- svhost.exe (PID: 1388)
Executable content was dropped or overwritten
- svhost.exe (PID: 1388)
- explorer.exe (PID: 128)
- DllHost.exe (PID: 4092)
Creates files in the user directory
- svhost.exe (PID: 1388)
- wlanext.exe (PID: 1088)
Loads DLL from Mozilla Firefox
- wlanext.exe (PID: 1088)
Executed via COM
- DllHost.exe (PID: 4092)
Creates files in the program directory
- DllHost.exe (PID: 4092)
INFO
Manual execution by user
- wlanext.exe (PID: 1088)
Creates files in the user directory
- Firefox.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45178 |
.rdata | 0x00008000 | 0x000014A2 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02518 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x000028D8 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.49628 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2992 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.22067 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 5.95079 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.50016 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
44
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Windows\System32\wlanext.exe" | C:\Windows\System32\wlanext.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wireless LAN 802.11 Extensibility Framework Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1644 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | svhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wlanext.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Ymhlhw0\audiodgez5tat.exe" | C:\Program Files\Ymhlhw0\audiodgez5tat.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3464 | /c del "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | wlanext.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4092 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 255
Read events
1 254
Write events
1
Delete events
0
Modification events
| (PID) Process: | (1088) wlanext.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | YV10OR5XEL6 |
Value: C:\Program Files\Ymhlhw0\audiodgez5tat.exe | |||
Executable files
6
Suspicious files
75
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1388 | svhost.exe | C:\Users\admin\AppData\Local\Temp\publisher\mtime\sserver\winforms03162004fig10.gif | image | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Roaming\bulk\prune\vnd.ms-cab-compressed.xml | xml | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Roaming\bulk\prune\co3449isnegativeinfinity.cs | text | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Local\Temp\publisher\mtime\sserver\test10finally.il | text | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Roaming\bulk\prune\devenv.exe | xml | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Local\Temp\comments\re\RedCircle42,8,8.gif | image | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Local\Temp\comments\re\doc-ditroff | text | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Local\Temp\comments\re\cups-common.list | text | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Local\Temp\comments\re\73.opends60.dll | binary | |
MD5:— | SHA256:— | |||
| 1388 | svhost.exe | C:\Users\admin\AppData\Roaming\keyword\date1\detail\goback\imx1-clock.h | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
15
DNS requests
13
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
128 | explorer.exe | GET | — | 34.231.113.65:80 | http://www.noelleandjonjon.com/c191/?Q0A=Ch9GMNhNZ1UZSNZEziAWGse7bp5AUha+h+jt/xJ2v1Vbg/gQqJ9nGSv5ooTW70PjtPhkDQ==&0pq=FtI0wNn | US | — | — | malicious |
128 | explorer.exe | GET | — | 47.107.46.6:80 | http://www.ysxxedu.com/c191/?Q0A=C4s2N2hZxEcDe2HW0jPs3UT9k69NPHXA7iUPxlNTrIRRfYZK8H8vTAKRqfl1cGhfo5XNrA==&0pq=FtI0wNn | CN | — | — | malicious |
128 | explorer.exe | POST | 404 | 199.192.26.170:80 | http://www.yodaug.com/c191/ | US | html | 292 b | malicious |
128 | explorer.exe | POST | — | 199.192.26.170:80 | http://www.yodaug.com/c191/ | US | — | — | malicious |
128 | explorer.exe | POST | — | 34.231.113.65:80 | http://www.noelleandjonjon.com/c191/ | US | — | — | malicious |
128 | explorer.exe | POST | — | 34.231.113.65:80 | http://www.noelleandjonjon.com/c191/ | US | — | — | malicious |
128 | explorer.exe | POST | — | 47.107.46.6:80 | http://www.ysxxedu.com/c191/ | CN | — | — | malicious |
128 | explorer.exe | GET | — | 61.188.37.244:80 | http://www.njlgmq.com/c191/?Q0A=ODEz2JwIj1JOy8wWo+EZCT03kPlsrzKDnX69xbHDWztE7xxVsyyq2RA5U0yMJ7MIT3EX7w==&0pq=FtI0wNn | CN | — | — | malicious |
128 | explorer.exe | POST | 404 | 199.192.26.170:80 | http://www.yodaug.com/c191/ | US | html | 292 b | malicious |
128 | explorer.exe | POST | — | 47.107.46.6:80 | http://www.ysxxedu.com/c191/ | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
128 | explorer.exe | 61.188.37.244:80 | www.njlgmq.com | CHINANET SiChuan Telecom Internet Data Center | CN | malicious |
128 | explorer.exe | 199.192.26.170:80 | www.yodaug.com | — | US | malicious |
128 | explorer.exe | 34.231.113.65:80 | www.noelleandjonjon.com | Amazon.com, Inc. | US | malicious |
128 | explorer.exe | 47.107.46.6:80 | www.ysxxedu.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.njlgmq.com |
| malicious |
www.yodaug.com |
| malicious |
www.noelleandjonjon.com |
| malicious |
www.ysxxedu.com |
| malicious |
www.lofscc.online |
| unknown |
www.karmabypallavi.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
128 | explorer.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
128 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
11 ETPRO signatures available at the full report