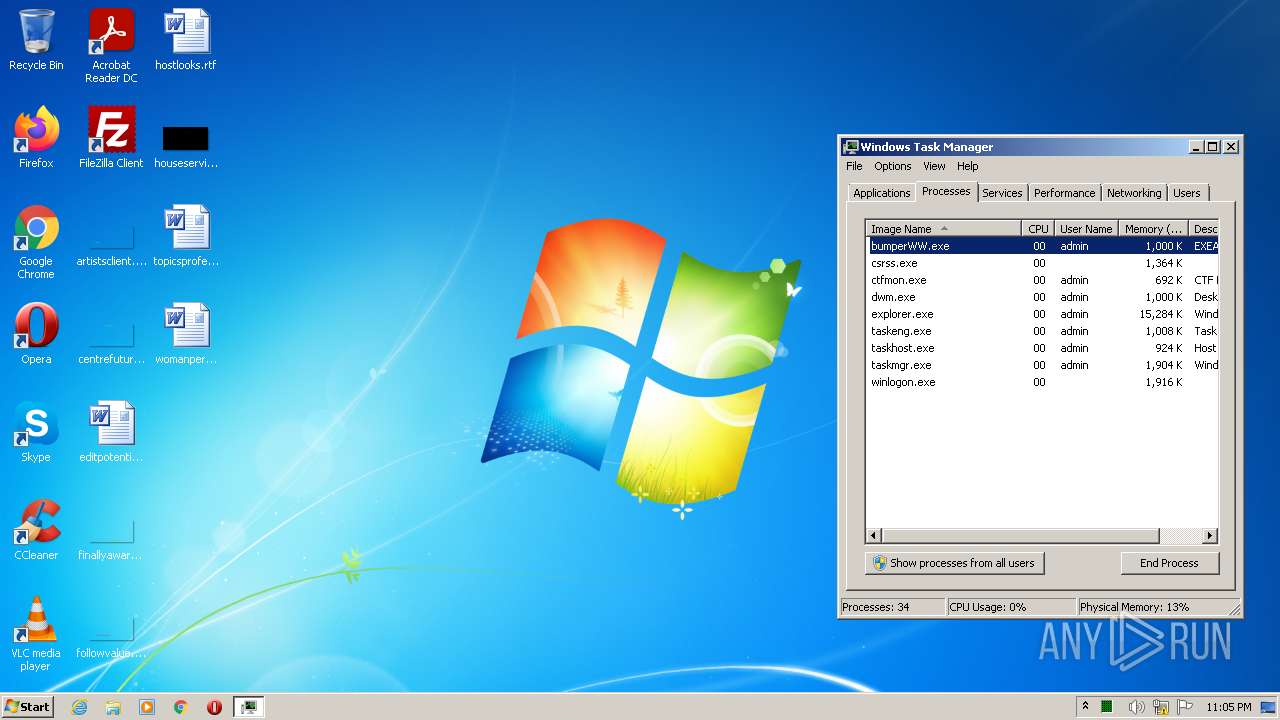
| File name: | C:\Users\admin\AppData\Local\Temp\askpwtwz.5rj\bumperWW.exe |
| Full analysis: | https://app.any.run/tasks/e218a889-1ce7-46c9-860e-74b3d39693af |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | January 14, 2022, 23:04:49 |
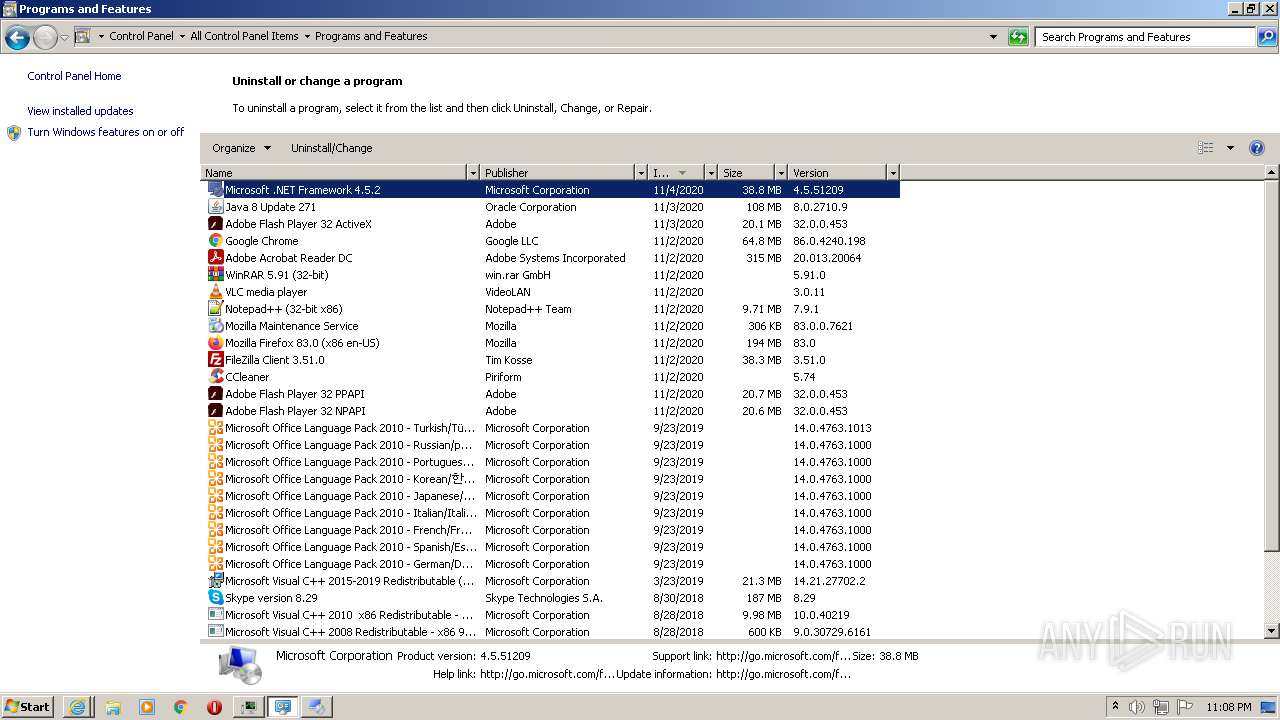
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7A132B76835C9958E249E98BDAD510DB |
| SHA1: | 2397BA104B77A90B55A29D2BE838914C9D1740A6 |
| SHA256: | C7F2DB83E5023E93538A91B009F459E8FD9468B1AC2C2ED6D9F187C487AC8597 |
| SSDEEP: | 6144:CBuJe81HMMQT0/u0agpEv1pE0EAPMrGWsWDWidF0HQszCZ2Ftppb9Y81+k7pq7FR:CAemHz/u0a9S2z+5 |
MALICIOUS
Changes settings of System certificates
- bumperWW.exe (PID: 2064)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
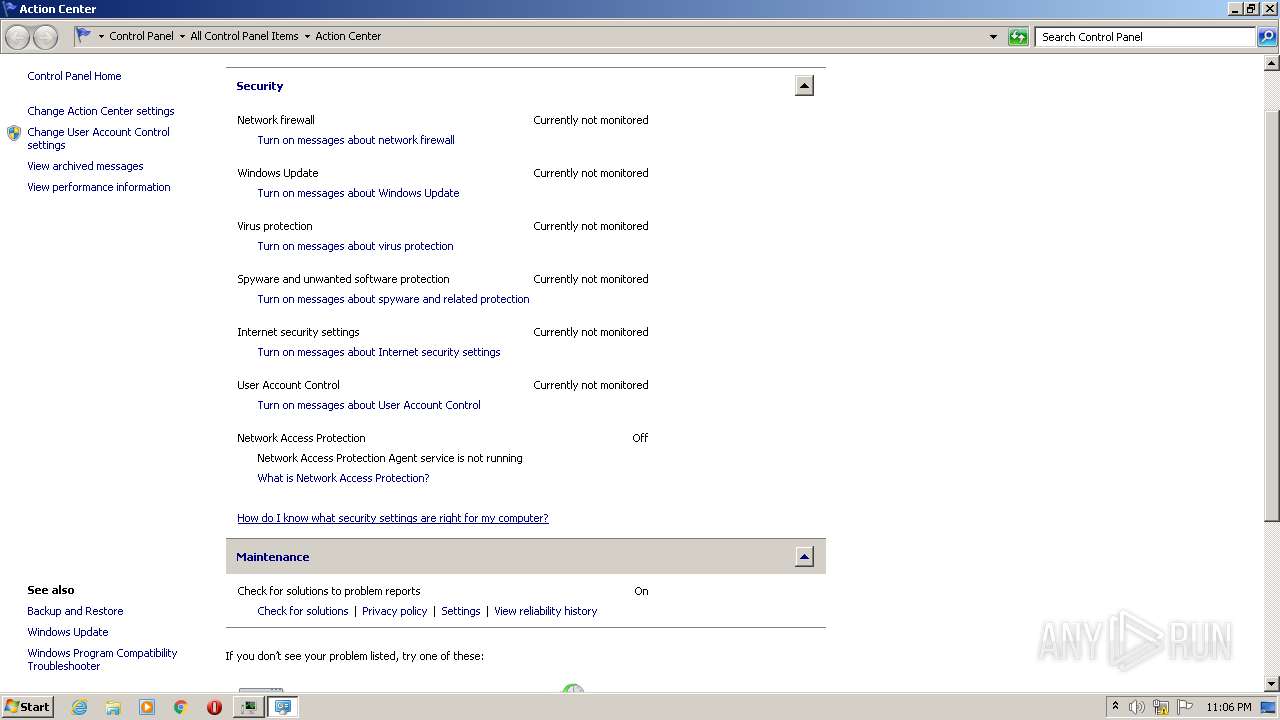
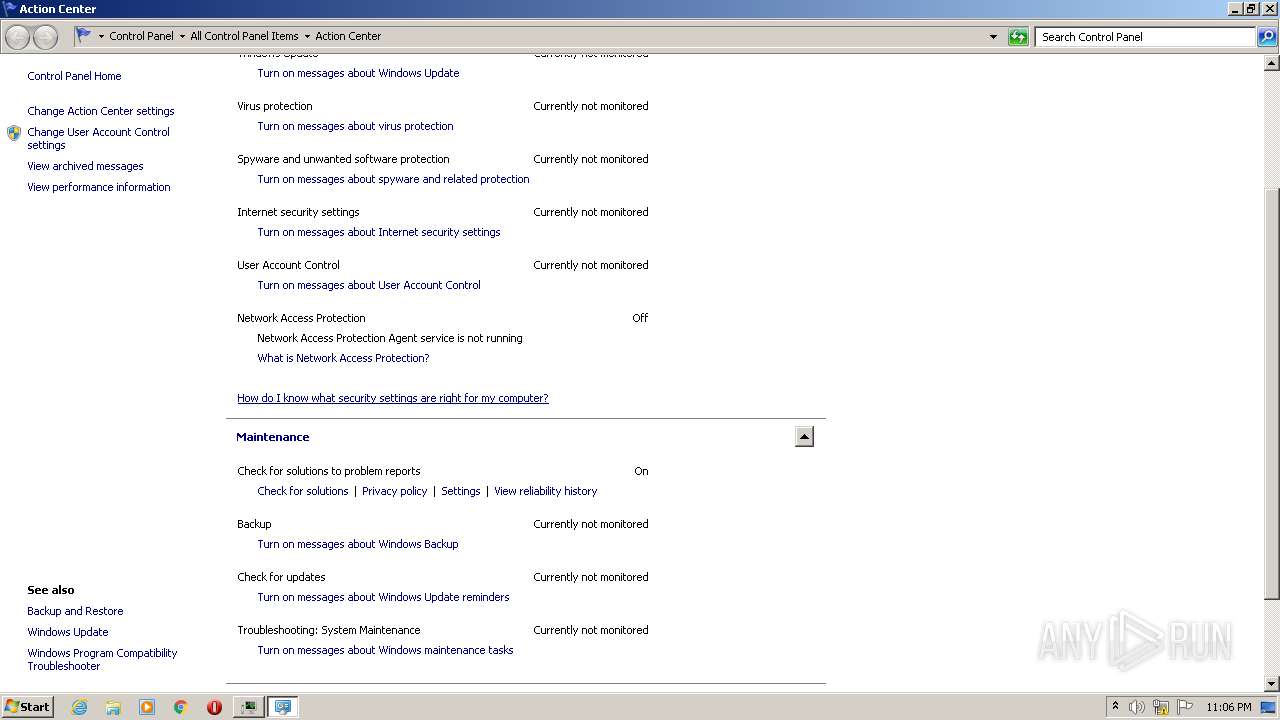
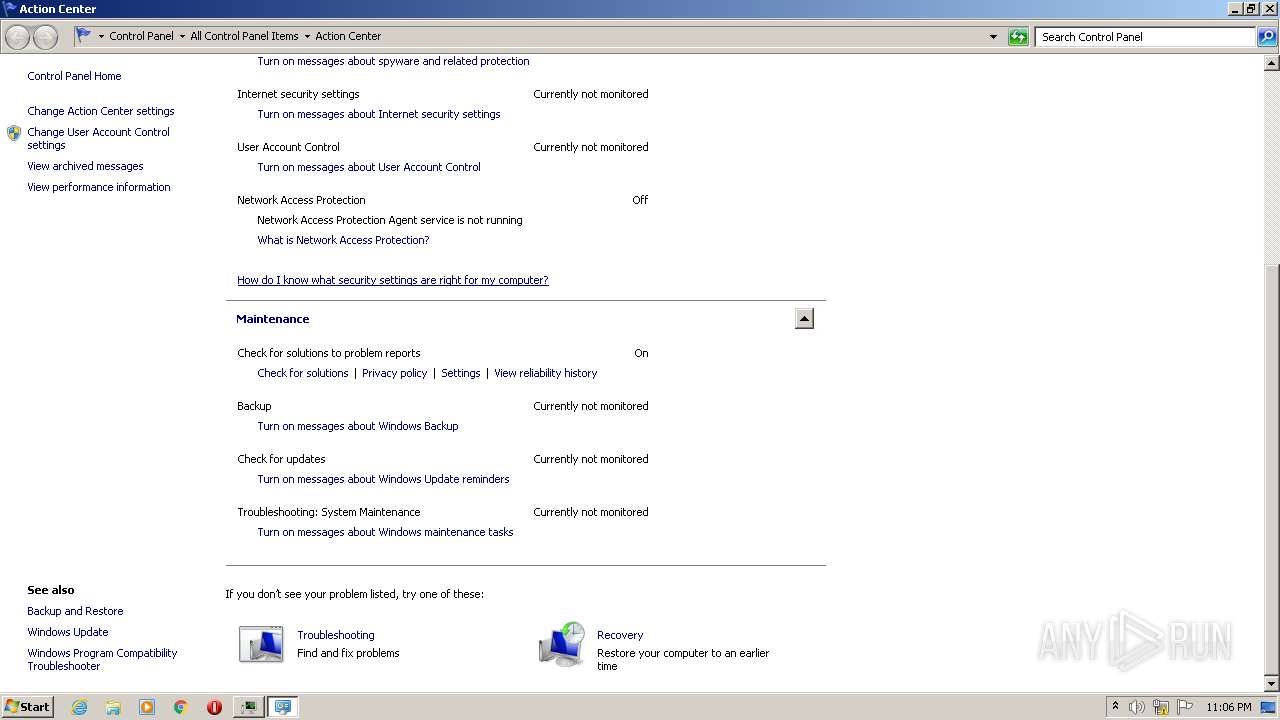
Disables Windows Defender
- bumperWW.exe (PID: 2064)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
Connects to CnC server
- bumperWW.exe (PID: 2064)
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
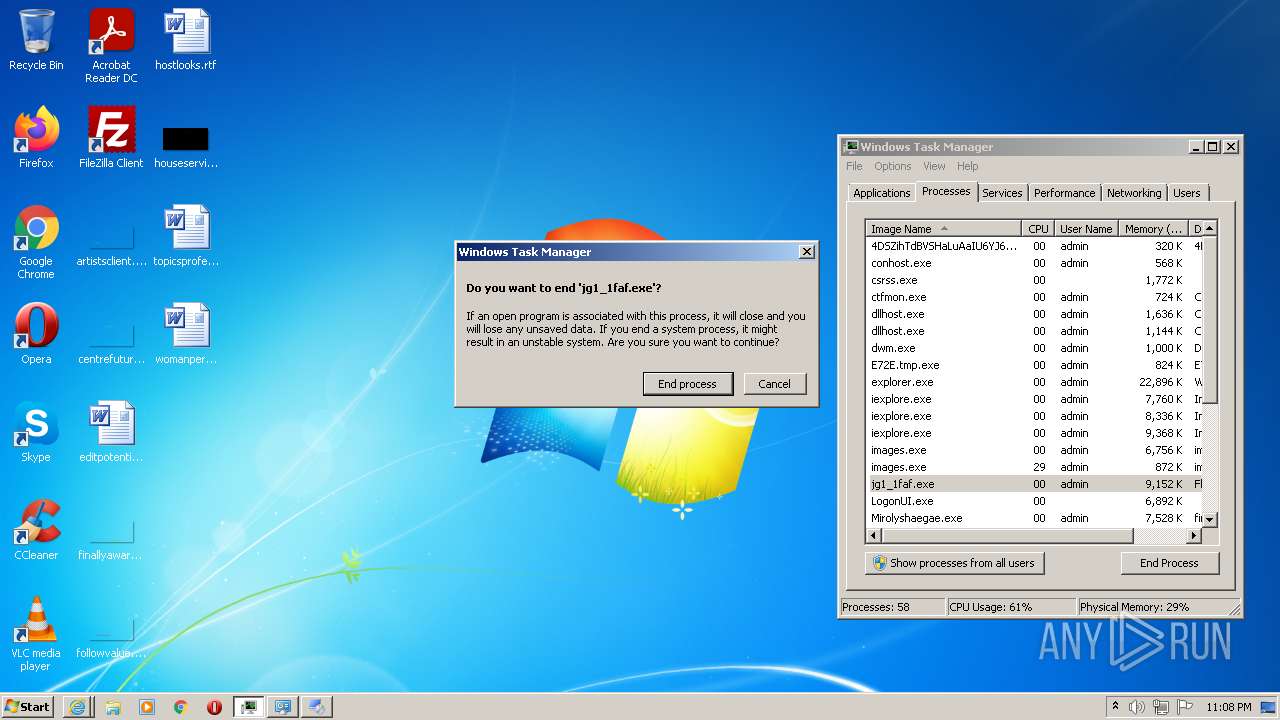
- jg1_1faf.exe (PID: 3260)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- xdx.exe (PID: 1144)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- FnwhRy2qeCCcdgcIfbJ47wm7.exe (PID: 3032)
- AppLaunch.exe (PID: 3400)
- AppLaunch.exe (PID: 3720)
- jg1_1faf.exe (PID: 4052)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
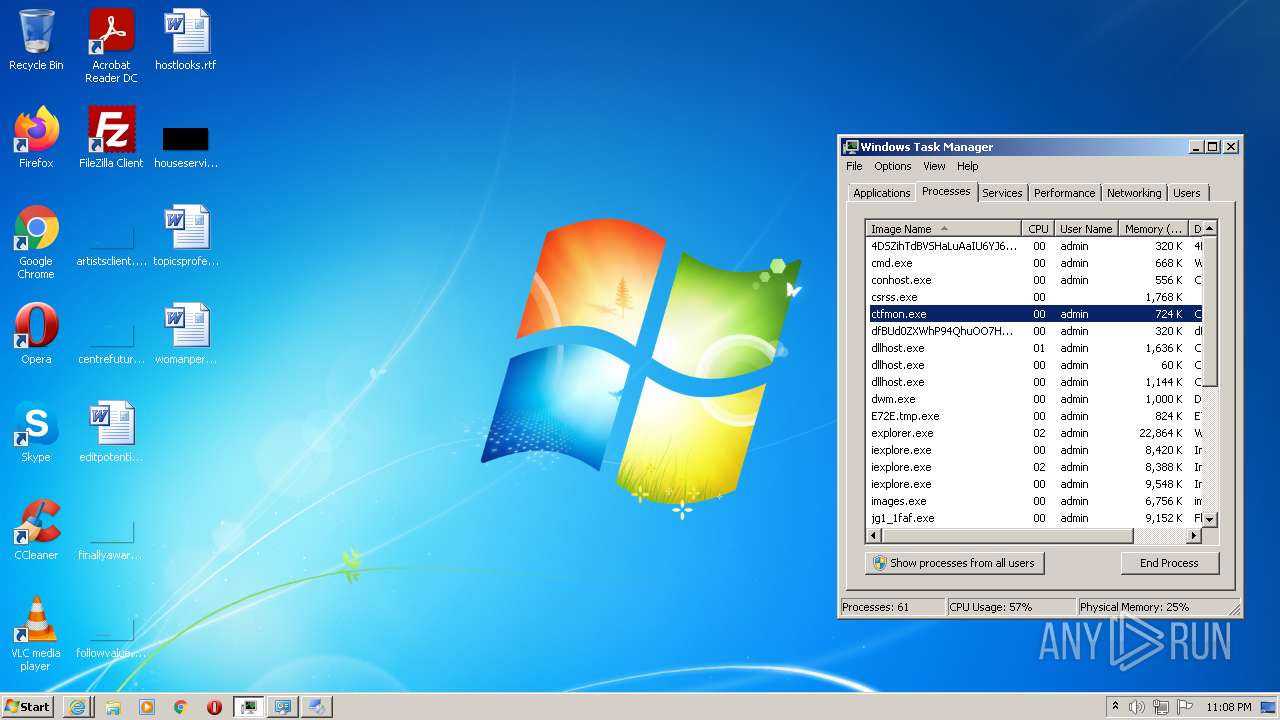
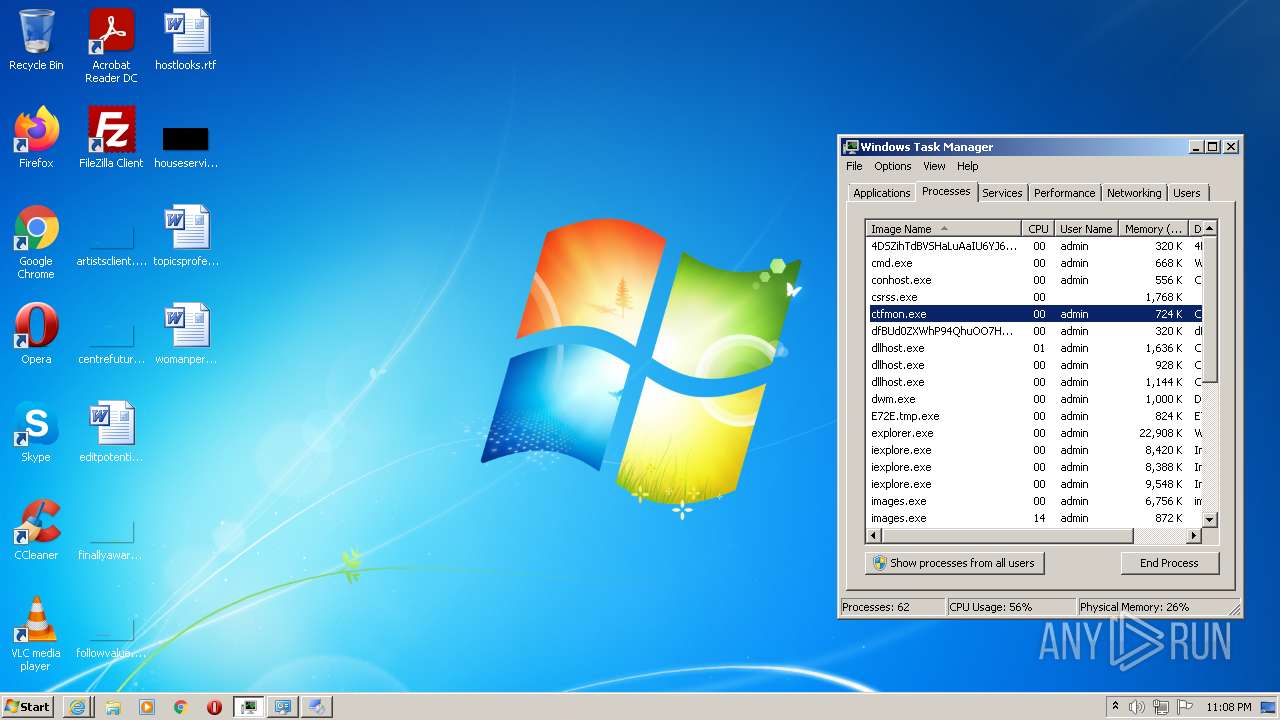
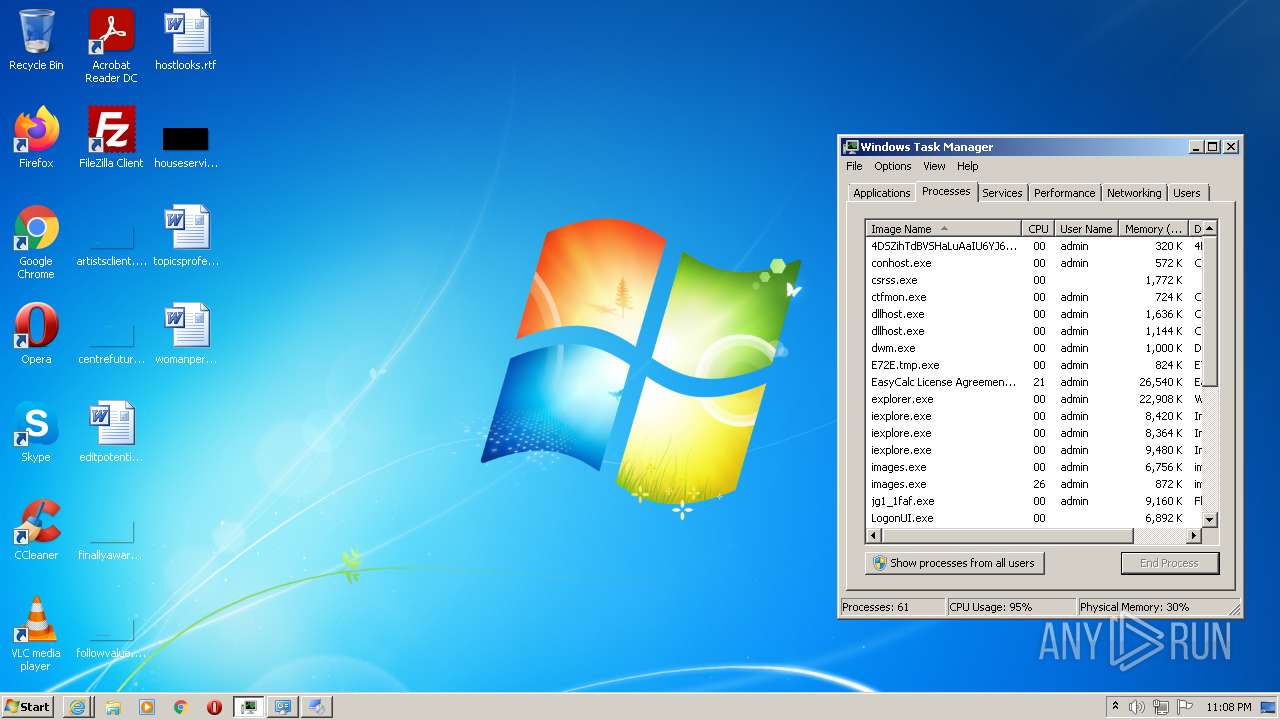
- images.exe (PID: 1112)
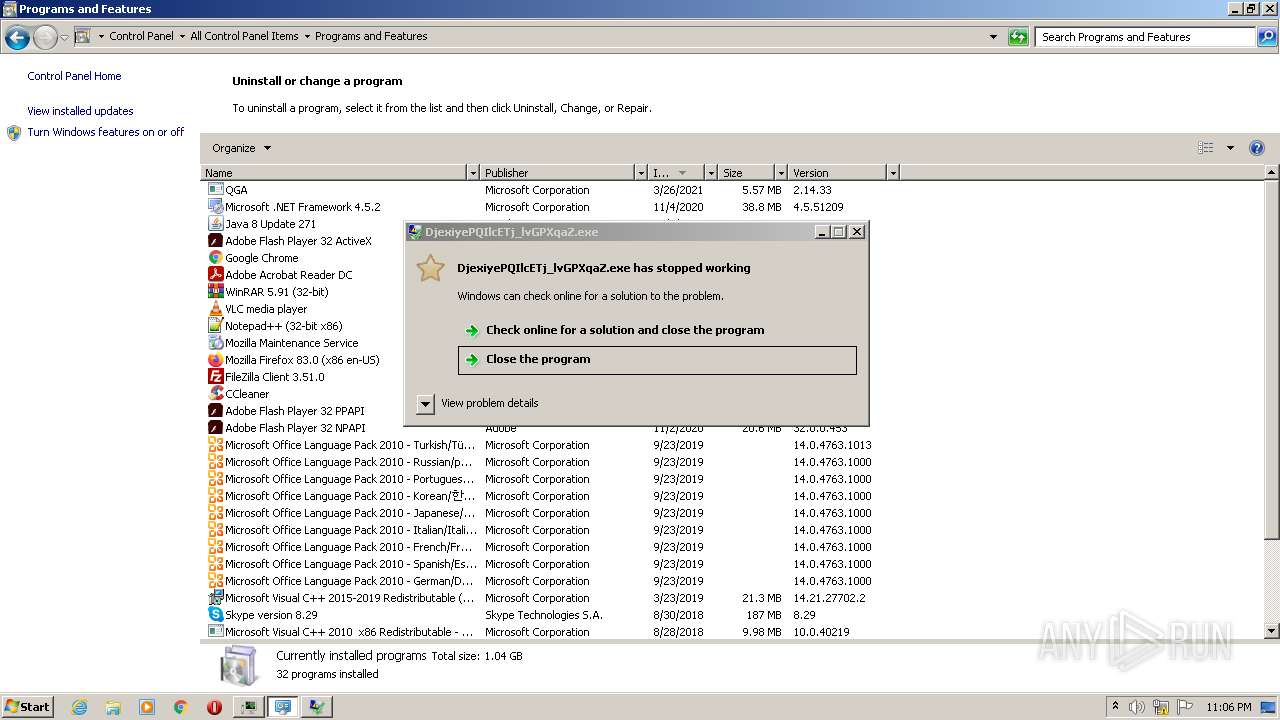
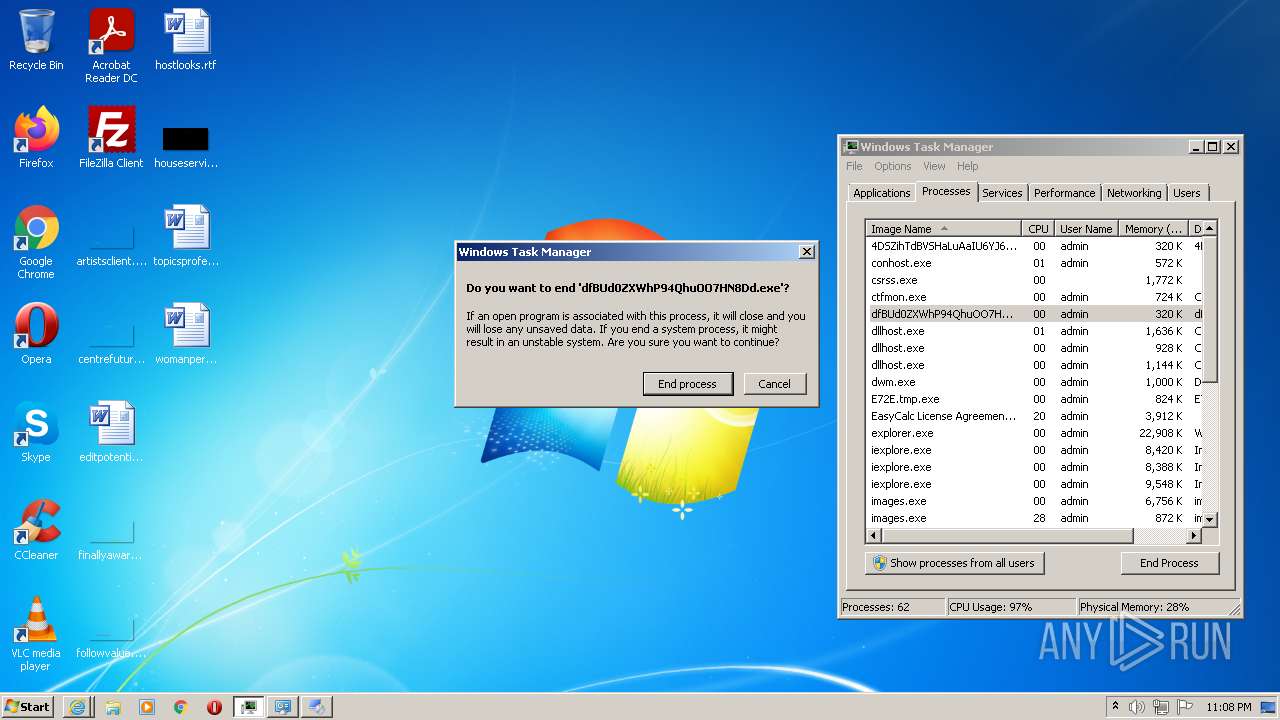
Application was dropped or rewritten from another process
- dfBUd0ZXWhP94QhuOO7HN8Dd.exe (PID: 3444)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- neRfUhqhUSljLEGIs9zyswBE.exe (PID: 2752)
- HrtdCvq0OW6t_LuWkmrv2XSL.exe (PID: 3528)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- 9gqhoLvblcW2BC9hjHC4tkno.exe (PID: 3148)
- 9gqhoLvblcW2BC9hjHC4tkno.exe (PID: 2596)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- 9FBpMmeA1jfTd4IUnavS64qZ.exe (PID: 3280)
- 9FBpMmeA1jfTd4IUnavS64qZ.exe (PID: 1844)
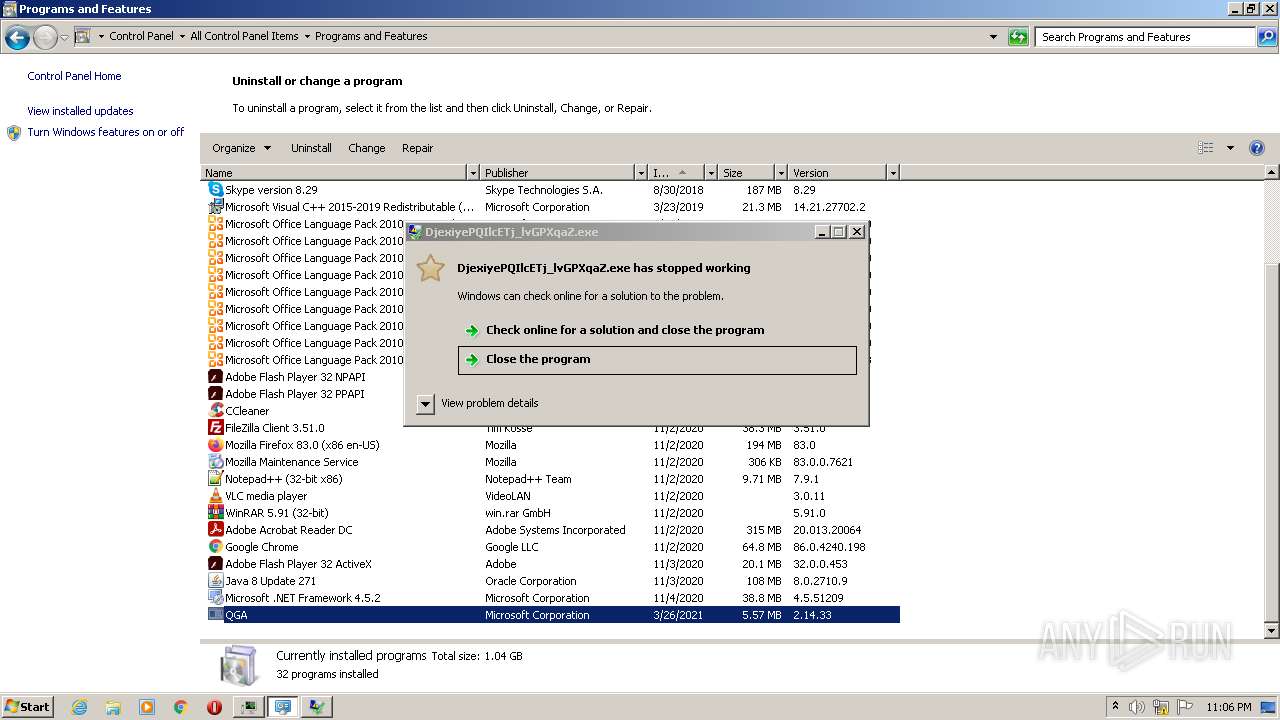
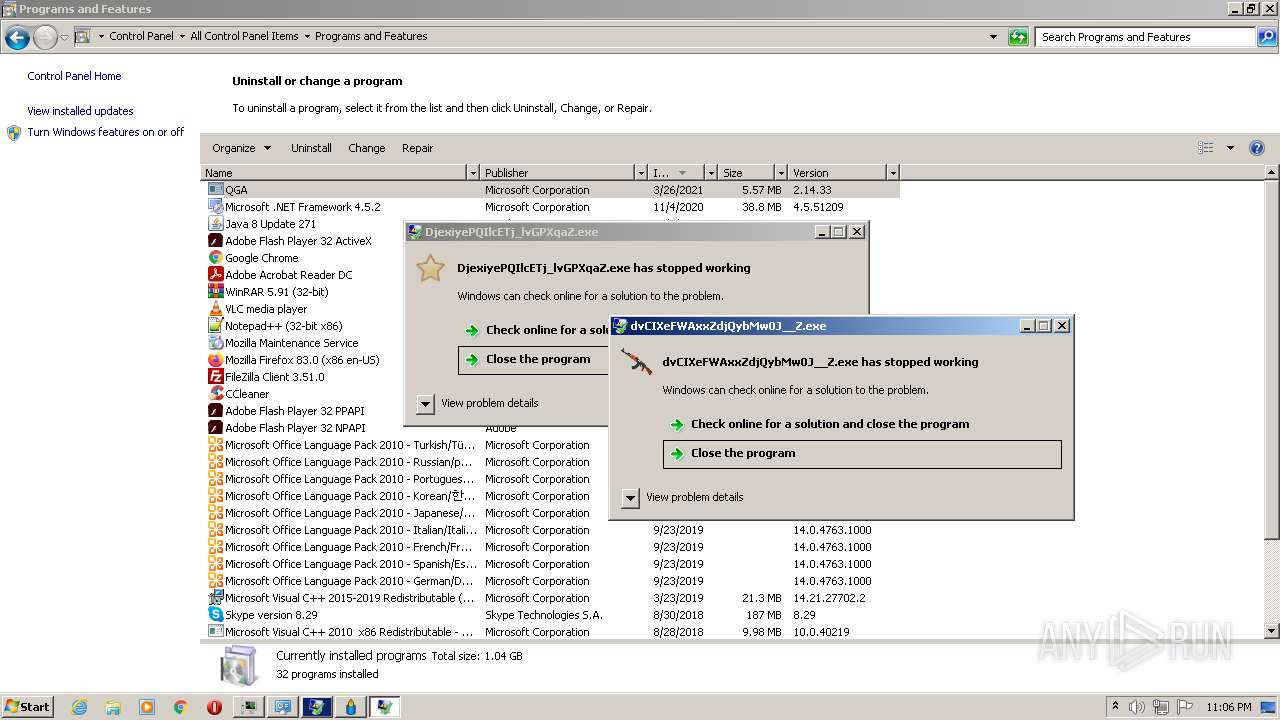
- DjexiyePQIlcETj_lvGPXqaZ.exe (PID: 348)
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- 4DSZihTdBVSHaLuAaIU6YJ6U.exe (PID: 2596)
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- 4562707.exe (PID: 284)
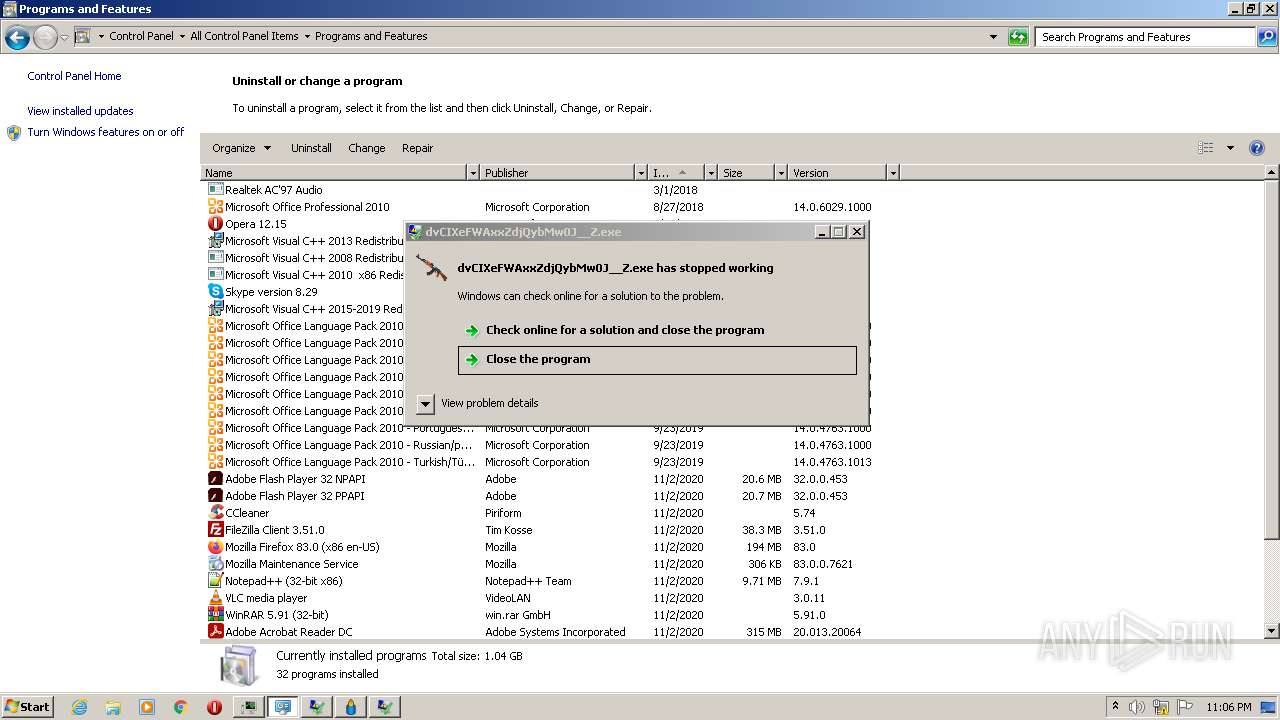
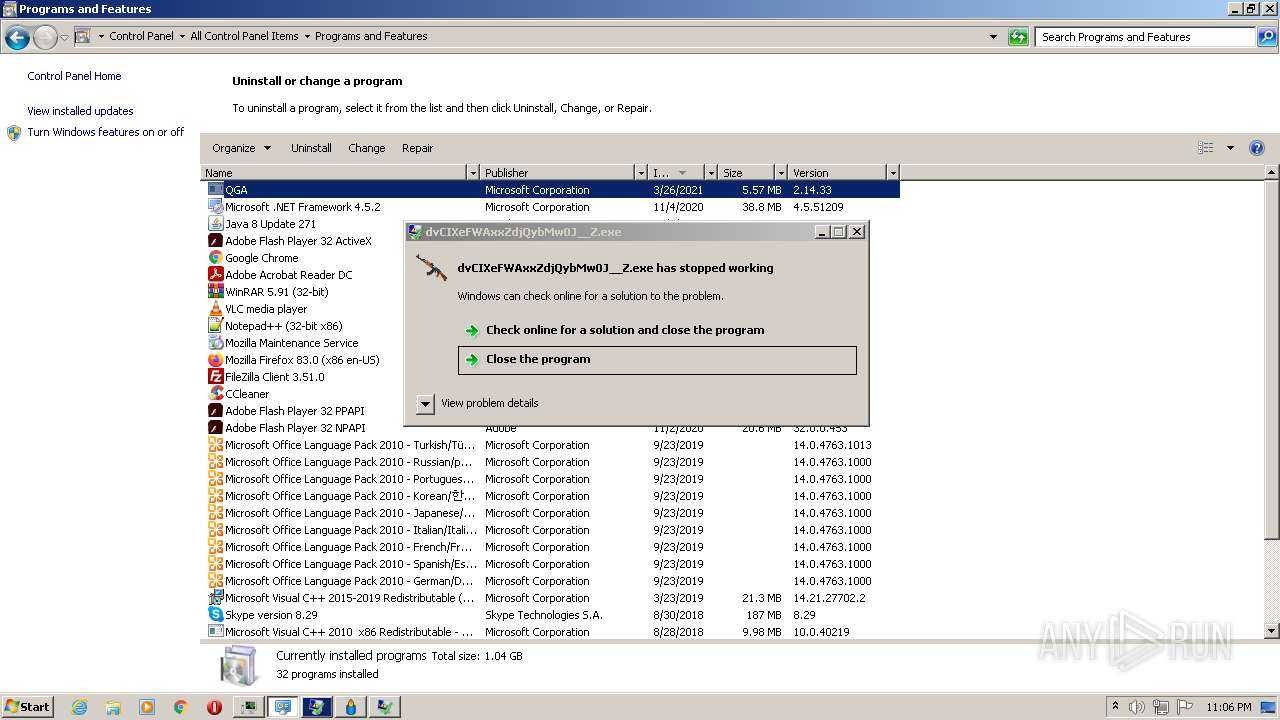
- dvCIXeFWAxxZdjQybMw0J__Z.exe (PID: 3696)
- 8759100.exe (PID: 3692)
- 6E3Q636UZ_jxOTrwYG_ceTus.exe (PID: 3136)
- ZkwtnHdG_m2bKB9EmX4uHvtq.exe (PID: 2136)
- Tchyv7ZBUnKnNuyhYUovsnxZ.exe (PID: 1088)
- WpPbrnpT74x_bdTWeekwIAeG.exe (PID: 3248)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- UtAVW52g78C8W8MI1VhAXbFk.exe (PID: 3768)
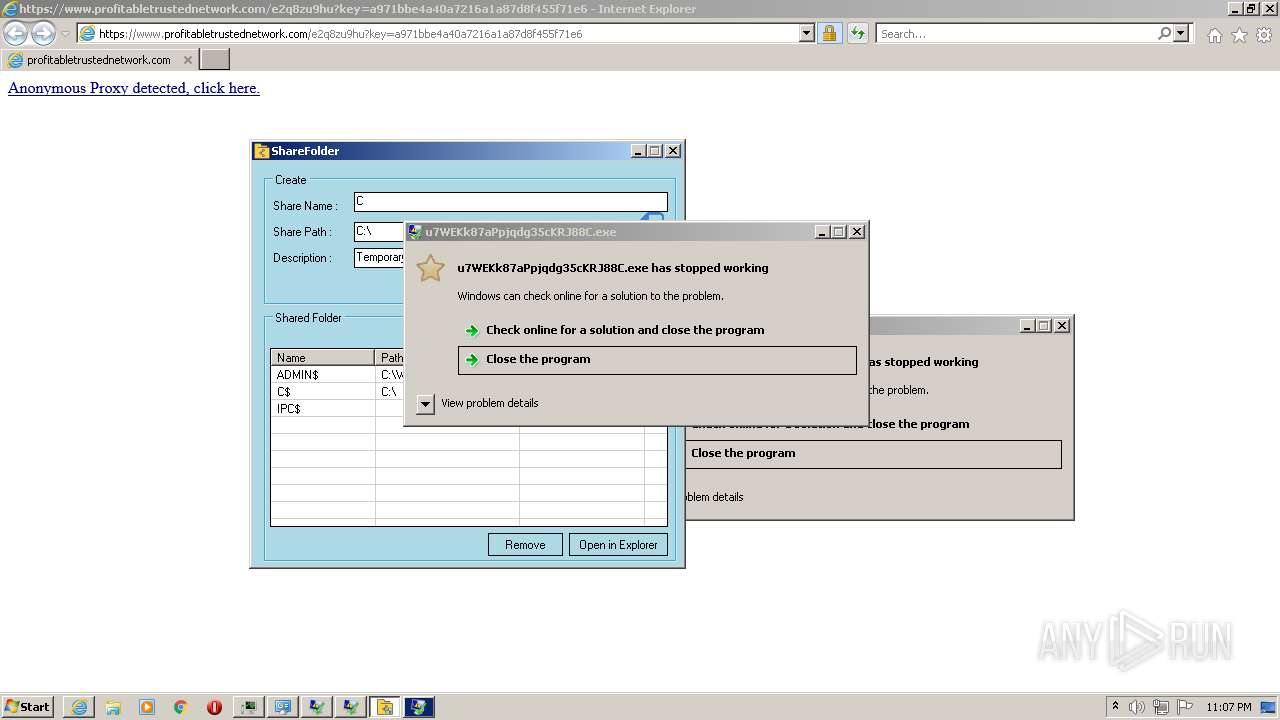
- u7WEKk87aPpjqdg35cKRJ88C.exe (PID: 3536)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- dj5n0fIAdPiFan12Qw_AkTG5.exe (PID: 3496)
- E72E.tmp.exe (PID: 408)
- C9FF.tmp.exe (PID: 2144)
- cd203ebd-200a-40f9-9e6a-803d7b729eab.exe (PID: 2696)
- b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe (PID: 3052)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- 6E3Q636UZ_jxOTrwYG_ceTus.exe (PID: 664)
- jZR4CnxOPLtgsLUr86lbO5IW.exe (PID: 2144)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 3924)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
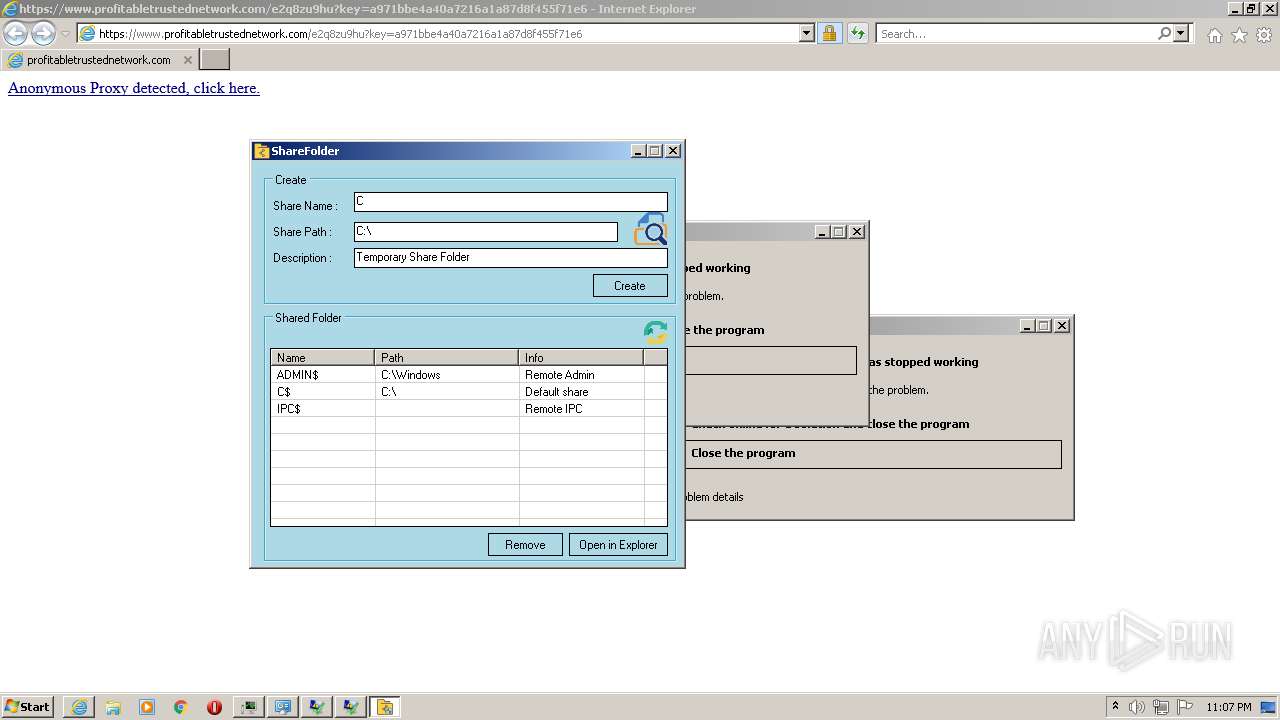
- foldershare.exe (PID: 2148)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 2836)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- kl6jlya2lGXvnSofBqImr58S.exe (PID: 3156)
- UtAVW52g78C8W8MI1VhAXbFk.exe (PID: 2492)
- 0kKg8XdX1FMWLfp6lSCcsHgz.exe (PID: 3832)
- mJvXRf_FxI_P9pEThrtt6Qsw.exe (PID: 2544)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- Install.exe (PID: 404)
- foldershare.exe (PID: 3396)
- FnwhRy2qeCCcdgcIfbJ47wm7.exe (PID: 3032)
- GYxbLEmkDx_32VVLIq03V9zU.exe (PID: 3124)
- images.exe (PID: 1112)
- itsKH9nklSVzS8685ht2UoGd.exe (PID: 2296)
- BC15TjOS_lv9Lp0pSnvpDPpd.exe (PID: 2724)
- Uninstall.exe (PID: 480)
- Uninstall.exe (PID: 3824)
- images.exe (PID: 3152)
Drops executable file immediately after starts
- dfBUd0ZXWhP94QhuOO7HN8Dd.exe (PID: 3444)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
Actions looks like stealing of personal data
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- jg1_1faf.exe (PID: 3260)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- xdx.exe (PID: 1144)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- AppLaunch.exe (PID: 3400)
- jg1_1faf.exe (PID: 4052)
- AppLaunch.exe (PID: 3720)
- DllHost.exe (PID: 3912)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
Steals credentials from Web Browsers
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- jg1_1faf.exe (PID: 3260)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- xdx.exe (PID: 1144)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- AppLaunch.exe (PID: 3400)
- jg1_1faf.exe (PID: 4052)
- AppLaunch.exe (PID: 3720)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
REDLINE was detected
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- xdx.exe (PID: 1144)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- FnwhRy2qeCCcdgcIfbJ47wm7.exe (PID: 3032)
- AppLaunch.exe (PID: 3400)
- AppLaunch.exe (PID: 3720)
Uses Task Scheduler to autorun other applications
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2080)
- schtasks.exe (PID: 2772)
Writes to a start menu file
- E72E.tmp.exe (PID: 408)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
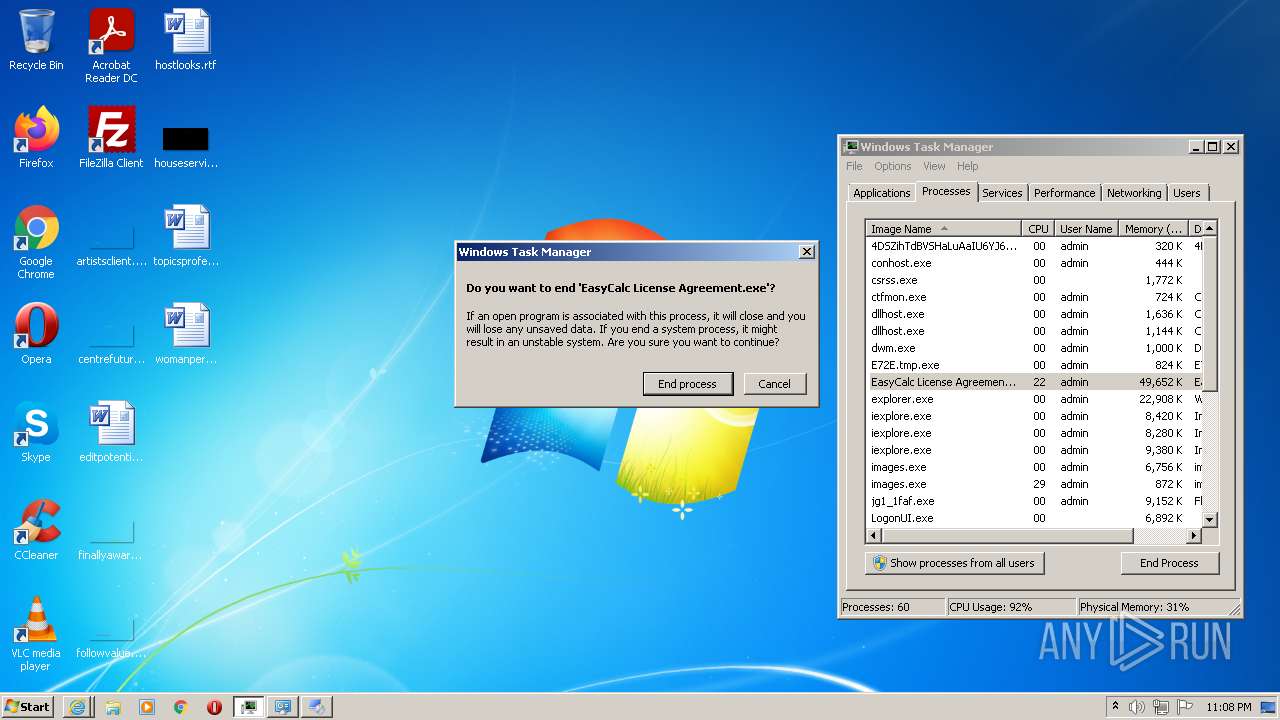
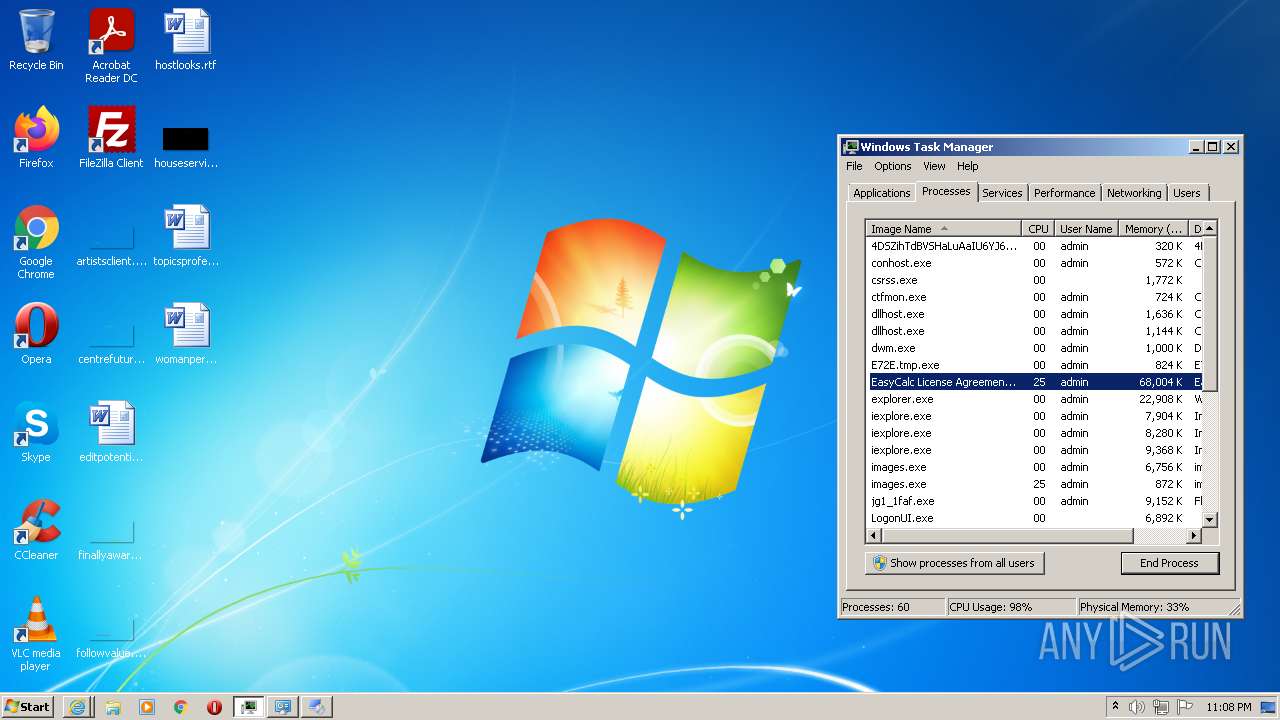
Loads dropped or rewritten executable
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- Tchyv7ZBUnKnNuyhYUovsnxZ.exe (PID: 1088)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- Roads License Agreement.exe (PID: 2632)
- EasyCalc License Agreement.exe (PID: 2360)
- MsiExec.exe (PID: 3384)
Stealing of credential data
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
Uses Task Scheduler to run other applications
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- Install.exe (PID: 2728)
Changes the autorun value in the registry
- ________djskjT76(((.exe (PID: 3732)
- ________djskjT76(((.exe (PID: 2032)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- Roads License Agreement.exe (PID: 2632)
VIDAR was detected
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
Runs injected code in another process
- rundll32.exe (PID: 576)
- images.exe (PID: 1112)
Application was injected by another process
- svchost.exe (PID: 860)
- Explorer.EXE (PID: 740)
RACCOON was detected
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
AVEMARIA was detected
- images.exe (PID: 1112)
SUSPICIOUS
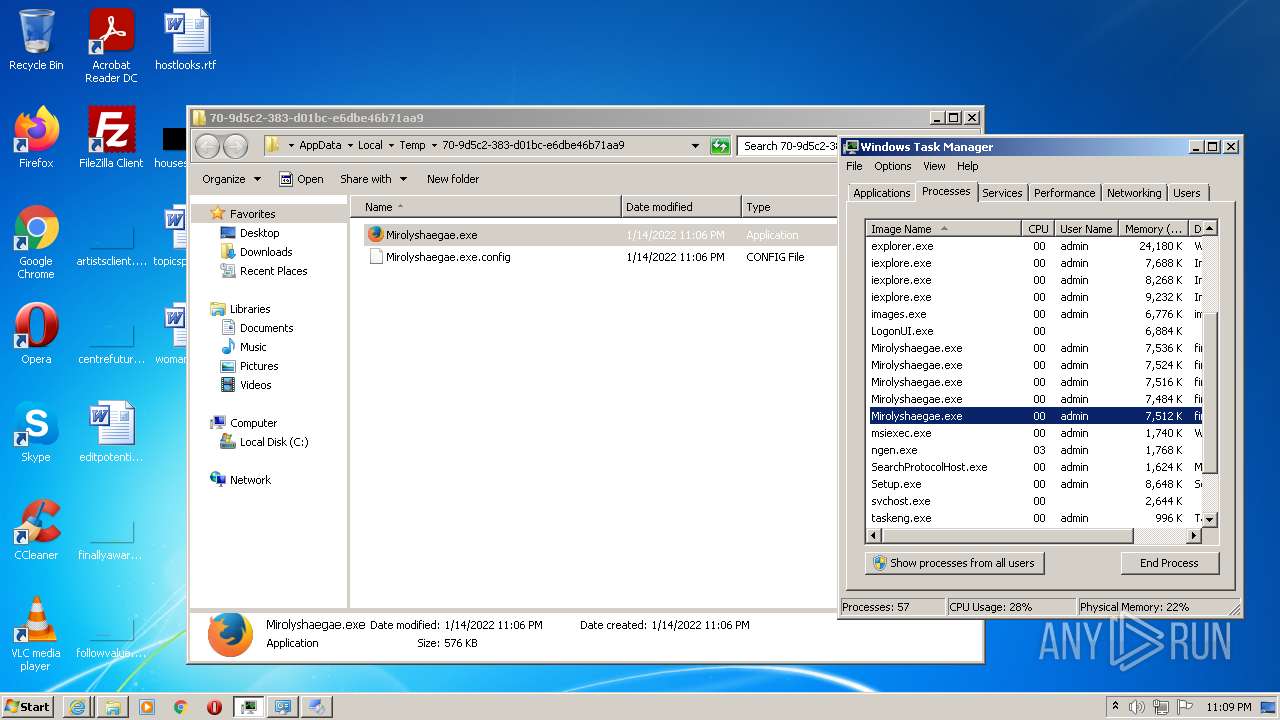
Reads the computer name
- bumperWW.exe (PID: 2064)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- neRfUhqhUSljLEGIs9zyswBE.exe (PID: 2752)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- dvCIXeFWAxxZdjQybMw0J__Z.exe (PID: 3696)
- ZkwtnHdG_m2bKB9EmX4uHvtq.exe (PID: 2136)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- RegAsm.exe (PID: 320)
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- C9FF.tmp.exe (PID: 2144)
- HrtdCvq0OW6t_LuWkmrv2XSL.exe (PID: 3528)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- ________djskjT76(((.exe (PID: 3732)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
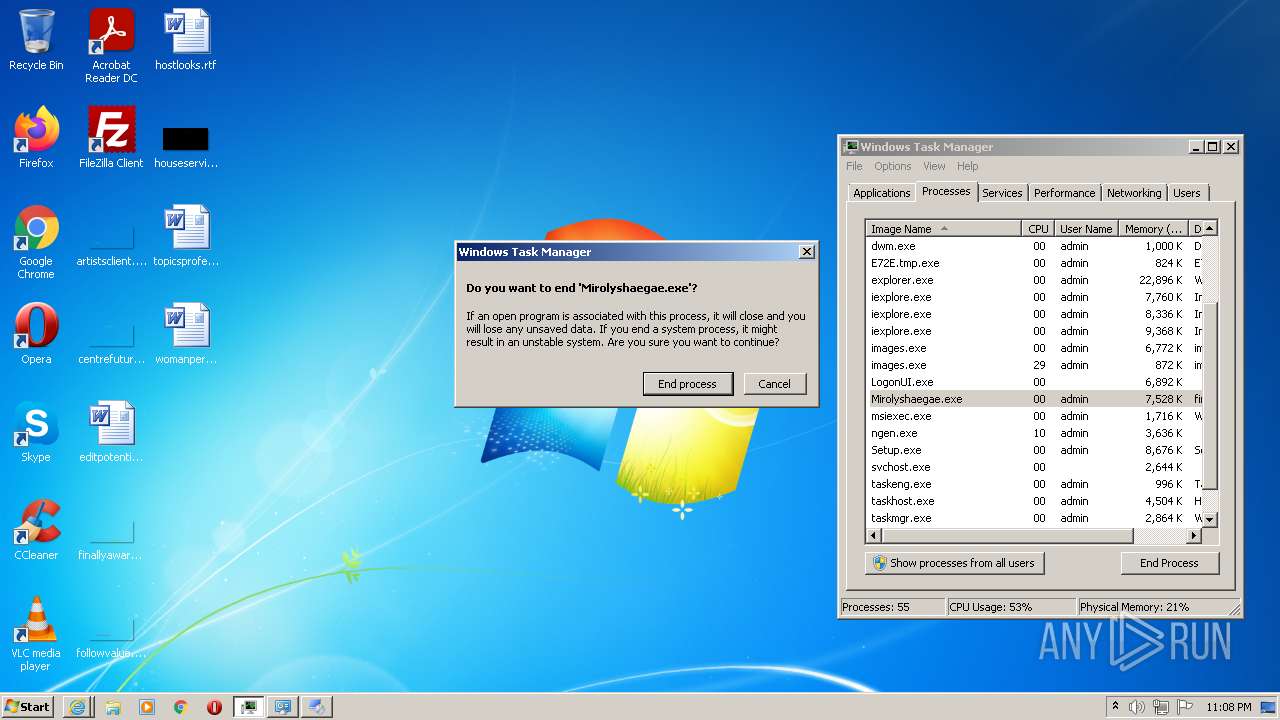
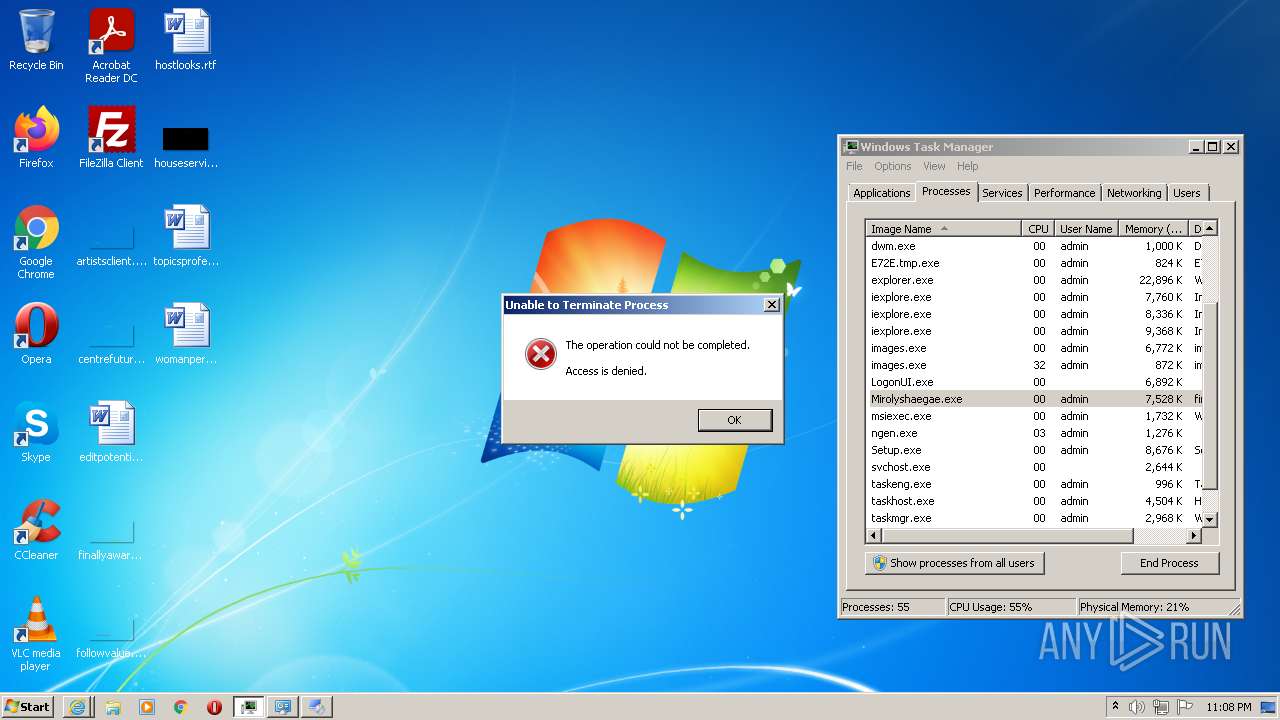
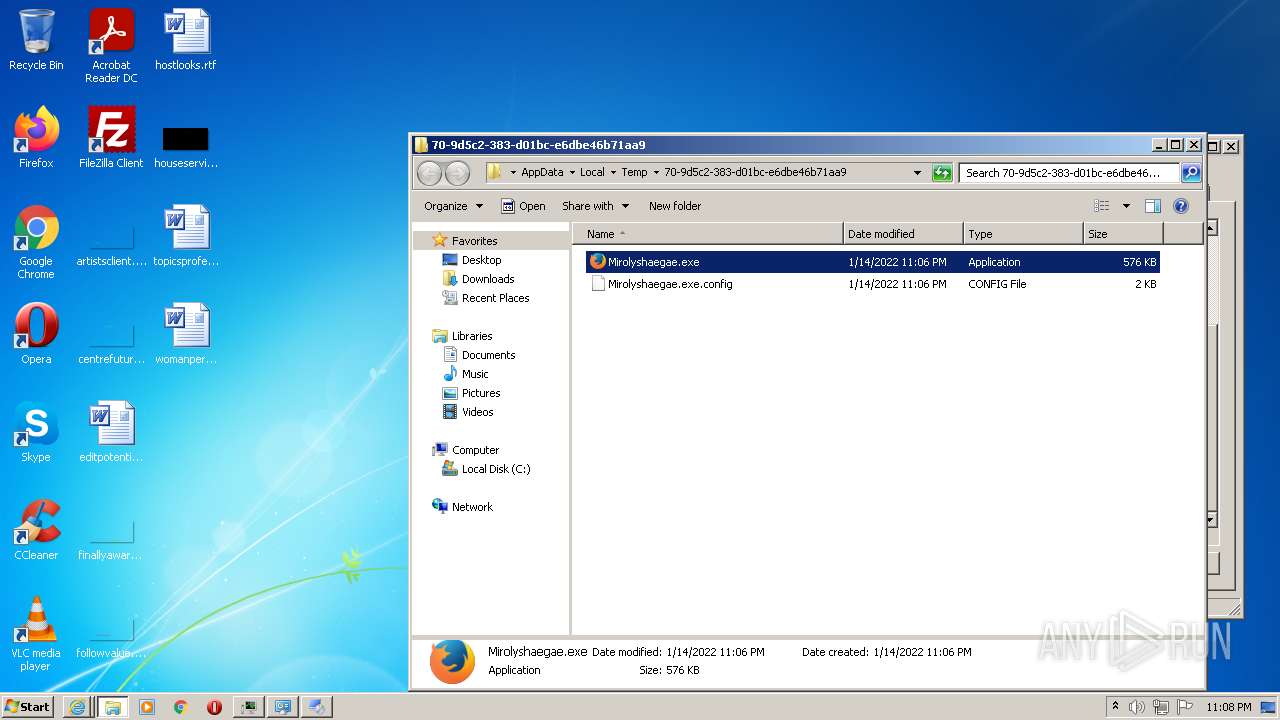
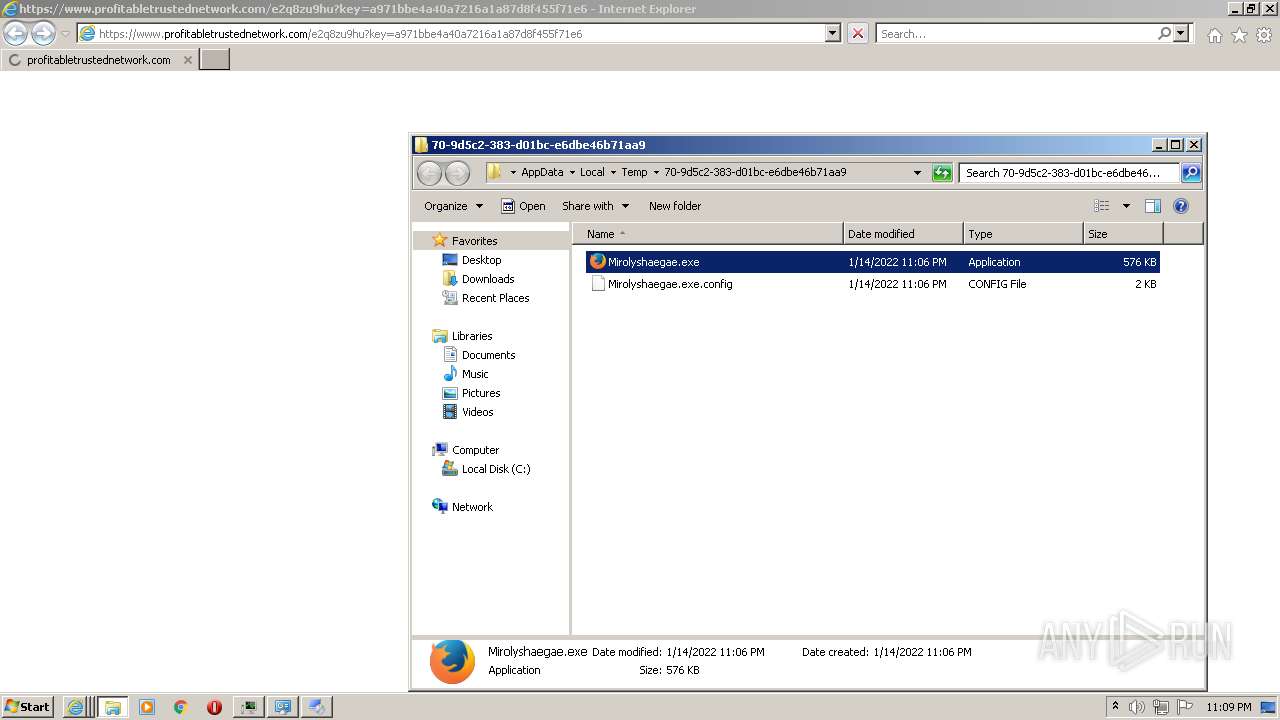
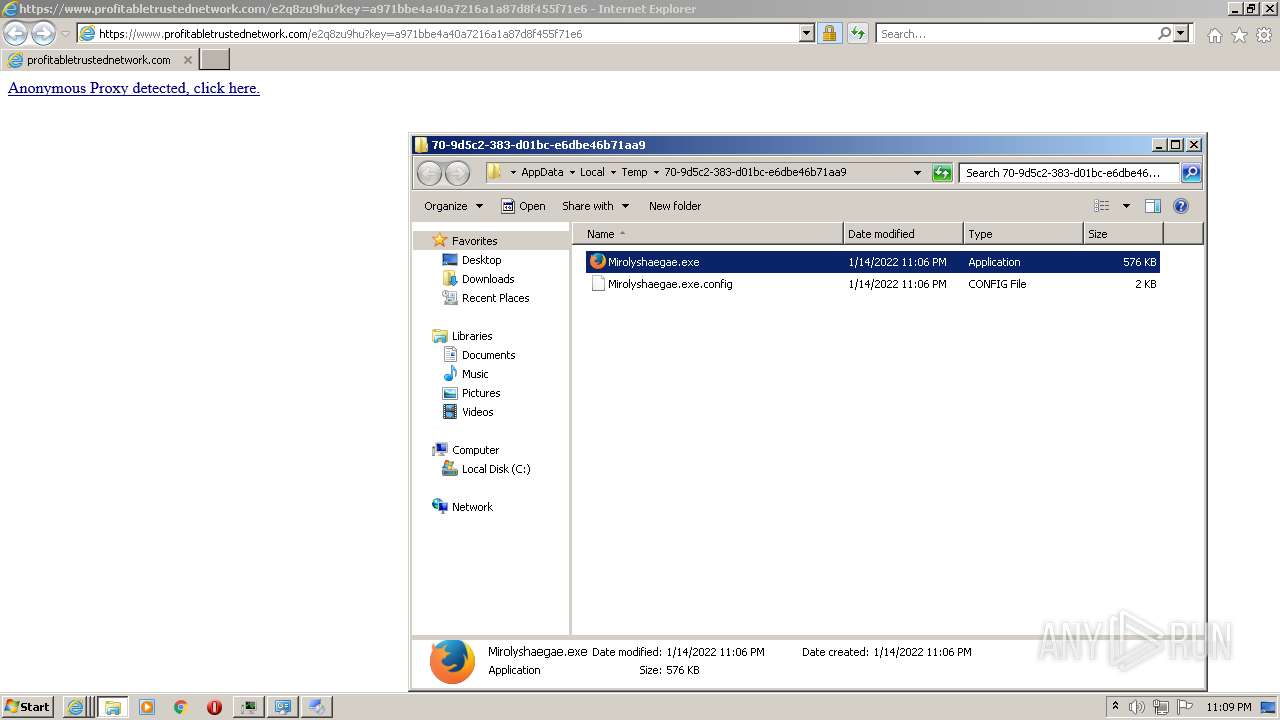
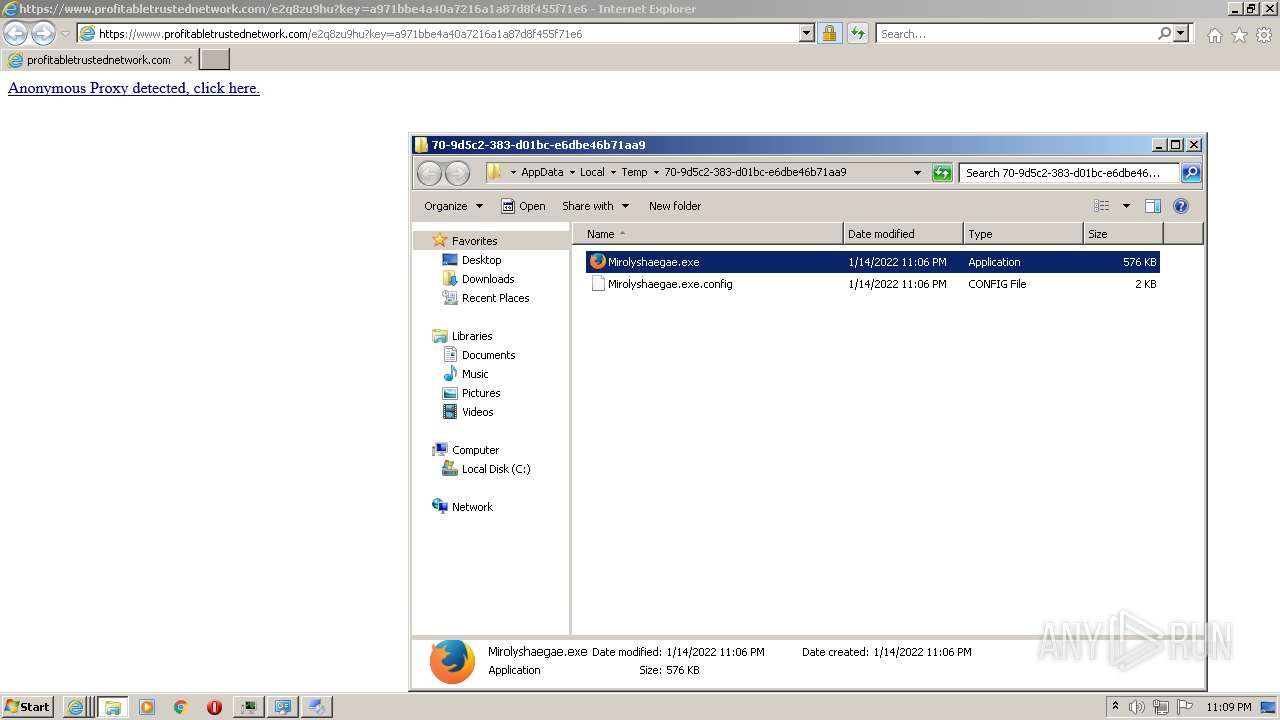
- Mirolyshaegae.exe (PID: 4004)
- b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe (PID: 3052)
- cd203ebd-200a-40f9-9e6a-803d7b729eab.exe (PID: 2696)
- jZR4CnxOPLtgsLUr86lbO5IW.exe (PID: 2144)
- Deqytihetu.exe (PID: 3256)
- foldershare.tmp (PID: 2296)
- FolderShare.exe (PID: 656)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- jg1_1faf.exe (PID: 3260)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- 4562707.exe (PID: 284)
- 8759100.exe (PID: 3692)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- Tchyv7ZBUnKnNuyhYUovsnxZ.exe (PID: 1088)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 2836)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 3924)
- dj5n0fIAdPiFan12Qw_AkTG5.exe (PID: 3496)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- kl6jlya2lGXvnSofBqImr58S.tmp (PID: 2852)
- 0kKg8XdX1FMWLfp6lSCcsHgz.exe (PID: 3832)
- xdx.exe (PID: 1144)
- ________djskjT76(((.exe (PID: 2032)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- Sybevyqebu.exe (PID: 2848)
- Install.exe (PID: 2728)
- FnwhRy2qeCCcdgcIfbJ47wm7.exe (PID: 3032)
- Bydaqusyry.exe (PID: 2784)
- foldershare.exe (PID: 2148)
- foldershare.tmp (PID: 2808)
- AppLaunch.exe (PID: 3400)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- AppLaunch.exe (PID: 3720)
- powershell.exe (PID: 3696)
- jg1_1faf.exe (PID: 4052)
- _iu14D2N.tmp (PID: 576)
- Uninstall.exe (PID: 480)
- Uninstall.exe (PID: 3824)
- Setup.exe (PID: 4052)
- images.exe (PID: 1112)
- powershell.exe (PID: 1284)
- Roads License Agreement.exe (PID: 2632)
- ngen.exe (PID: 4064)
- EasyCalc License Agreement.exe (PID: 2360)
- ngen.exe (PID: 3372)
- ngen.exe (PID: 668)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 1284)
- ngen.exe (PID: 3108)
- mscorsvw.exe (PID: 2772)
- ngen.exe (PID: 992)
- ngen.exe (PID: 1808)
- ngen.exe (PID: 636)
- ngen.exe (PID: 3516)
- ngen.exe (PID: 1152)
- ngen.exe (PID: 468)
- mscorsvw.exe (PID: 3548)
- ngen.exe (PID: 696)
- ngen.exe (PID: 2252)
- ngen.exe (PID: 668)
- ngen.exe (PID: 532)
- ngen.exe (PID: 4088)
- ngen.exe (PID: 3716)
- ngen.exe (PID: 2072)
- ngen.exe (PID: 3364)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 2088)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 2200)
- ngen.exe (PID: 2752)
- ngen.exe (PID: 3648)
- ngen.exe (PID: 696)
- ngen.exe (PID: 2192)
- mscorsvw.exe (PID: 2632)
- ngen.exe (PID: 3032)
- mscorsvw.exe (PID: 1152)
- ngen.exe (PID: 2556)
- mscorsvw.exe (PID: 756)
- ngen.exe (PID: 4000)
- ngen.exe (PID: 3332)
- ngen.exe (PID: 2428)
- ngen.exe (PID: 3628)
- ngen.exe (PID: 2520)
- ngen.exe (PID: 2060)
- ngen.exe (PID: 508)
- ngen.exe (PID: 1512)
- ngen.exe (PID: 2604)
- mscorsvw.exe (PID: 1368)
- ngen.exe (PID: 3876)
- ngen.exe (PID: 3500)
- ngen.exe (PID: 1728)
- mscorsvw.exe (PID: 3776)
- ngen.exe (PID: 3388)
- ngen.exe (PID: 532)
- mscorsvw.exe (PID: 3012)
- ngen.exe (PID: 2496)
- mscorsvw.exe (PID: 348)
- ngen.exe (PID: 3544)
- ngen.exe (PID: 2984)
- mscorsvw.exe (PID: 2384)
- ngen.exe (PID: 2292)
- mscorsvw.exe (PID: 3728)
- ngen.exe (PID: 3196)
- ngen.exe (PID: 272)
- ngen.exe (PID: 3640)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 2284)
- ngen.exe (PID: 448)
- ngen.exe (PID: 2972)
- mscorsvw.exe (PID: 388)
- ngen.exe (PID: 3972)
- ngen.exe (PID: 3648)
- mscorsvw.exe (PID: 1996)
- ngen.exe (PID: 1120)
- ngen.exe (PID: 3324)
- mscorsvw.exe (PID: 3732)
- ngen.exe (PID: 2880)
- mscorsvw.exe (PID: 1808)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 2352)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 3260)
- mscorsvw.exe (PID: 3776)
- ngen.exe (PID: 2416)
- ngen.exe (PID: 2492)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 1996)
- ngen.exe (PID: 3928)
- images.exe (PID: 3152)
- mscorsvw.exe (PID: 1036)
- ngen.exe (PID: 3012)
- Mirolyshaegae.exe (PID: 2732)
- ngen.exe (PID: 1400)
- mscorsvw.exe (PID: 344)
- ngen.exe (PID: 284)
- Mirolyshaegae.exe (PID: 2880)
- mscorsvw.exe (PID: 4064)
- ngen.exe (PID: 2356)
- Mirolyshaegae.exe (PID: 1284)
- ngen.exe (PID: 2792)
- ngen.exe (PID: 2068)
- ngen.exe (PID: 2072)
- ngen.exe (PID: 4064)
Checks supported languages
- bumperWW.exe (PID: 2064)
- dfBUd0ZXWhP94QhuOO7HN8Dd.exe (PID: 3444)
- 9gqhoLvblcW2BC9hjHC4tkno.exe (PID: 3148)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- DjexiyePQIlcETj_lvGPXqaZ.exe (PID: 348)
- 9FBpMmeA1jfTd4IUnavS64qZ.exe (PID: 3280)
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- 9gqhoLvblcW2BC9hjHC4tkno.exe (PID: 2596)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- neRfUhqhUSljLEGIs9zyswBE.exe (PID: 2752)
- dvCIXeFWAxxZdjQybMw0J__Z.exe (PID: 3696)
- ZkwtnHdG_m2bKB9EmX4uHvtq.exe (PID: 2136)
- WpPbrnpT74x_bdTWeekwIAeG.exe (PID: 3248)
- 9FBpMmeA1jfTd4IUnavS64qZ.exe (PID: 1844)
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- RegAsm.exe (PID: 320)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- C9FF.tmp.exe (PID: 2144)
- HrtdCvq0OW6t_LuWkmrv2XSL.exe (PID: 3528)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- ________djskjT76(((.exe (PID: 3732)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- E72E.tmp.exe (PID: 408)
- cmd.exe (PID: 2924)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- Mirolyshaegae.exe (PID: 4004)
- b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe (PID: 3052)
- cd203ebd-200a-40f9-9e6a-803d7b729eab.exe (PID: 2696)
- jZR4CnxOPLtgsLUr86lbO5IW.exe (PID: 2144)
- Deqytihetu.exe (PID: 3256)
- inst2.exe (PID: 4024)
- jg1_1faf.exe (PID: 3260)
- foldershare.exe (PID: 2148)
- foldershare.tmp (PID: 2296)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- FolderShare.exe (PID: 656)
- cmd.exe (PID: 3556)
- 4DSZihTdBVSHaLuAaIU6YJ6U.exe (PID: 2596)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- 4562707.exe (PID: 284)
- 8759100.exe (PID: 3692)
- 6E3Q636UZ_jxOTrwYG_ceTus.exe (PID: 3136)
- Tchyv7ZBUnKnNuyhYUovsnxZ.exe (PID: 1088)
- UtAVW52g78C8W8MI1VhAXbFk.exe (PID: 3768)
- u7WEKk87aPpjqdg35cKRJ88C.exe (PID: 3536)
- dj5n0fIAdPiFan12Qw_AkTG5.exe (PID: 3496)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 2836)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 3924)
- 6E3Q636UZ_jxOTrwYG_ceTus.exe (PID: 664)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- kl6jlya2lGXvnSofBqImr58S.exe (PID: 3156)
- kl6jlya2lGXvnSofBqImr58S.tmp (PID: 2852)
- UtAVW52g78C8W8MI1VhAXbFk.exe (PID: 2492)
- xdx.exe (PID: 1144)
- ________djskjT76(((.exe (PID: 2032)
- mJvXRf_FxI_P9pEThrtt6Qsw.exe (PID: 2544)
- 0kKg8XdX1FMWLfp6lSCcsHgz.exe (PID: 3832)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- Install.exe (PID: 404)
- Sybevyqebu.exe (PID: 2848)
- Install.exe (PID: 2728)
- cmd.exe (PID: 2108)
- Bydaqusyry.exe (PID: 2784)
- FnwhRy2qeCCcdgcIfbJ47wm7.exe (PID: 3032)
- GYxbLEmkDx_32VVLIq03V9zU.exe (PID: 3124)
- foldershare.exe (PID: 3396)
- foldershare.tmp (PID: 2808)
- FolderShare.exe (PID: 2124)
- AppLaunch.exe (PID: 3400)
- itsKH9nklSVzS8685ht2UoGd.exe (PID: 2296)
- BC15TjOS_lv9Lp0pSnvpDPpd.exe (PID: 2724)
- jg1_1faf.exe (PID: 4052)
- AppLaunch.exe (PID: 3720)
- images.exe (PID: 1112)
- powershell.exe (PID: 3696)
- unins000.exe (PID: 1980)
- _iu14D2N.tmp (PID: 576)
- Uninstall.exe (PID: 480)
- Uninstall.exe (PID: 3824)
- Setup.exe (PID: 4052)
- powershell.exe (PID: 1284)
- cmd.exe (PID: 2768)
- Roads License Agreement.exe (PID: 2632)
- ngen.exe (PID: 4064)
- images.exe (PID: 3152)
- EasyCalc License Agreement.exe (PID: 2360)
- ngen.exe (PID: 3372)
- ngen.exe (PID: 668)
- ngen.exe (PID: 1284)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 3108)
- mscorsvw.exe (PID: 2772)
- ngen.exe (PID: 992)
- mscorsvw.exe (PID: 3548)
- ngen.exe (PID: 1808)
- ngen.exe (PID: 636)
- ngen.exe (PID: 3516)
- ngen.exe (PID: 1152)
- ngen.exe (PID: 468)
- ngen.exe (PID: 696)
- ngen.exe (PID: 668)
- ngen.exe (PID: 532)
- ngen.exe (PID: 4088)
- ngen.exe (PID: 3716)
- ngen.exe (PID: 2072)
- ngen.exe (PID: 2252)
- ngen.exe (PID: 3364)
- ngen.exe (PID: 2088)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 2200)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 2752)
- ngen.exe (PID: 696)
- ngen.exe (PID: 3648)
- ngen.exe (PID: 2192)
- mscorsvw.exe (PID: 2632)
- ngen.exe (PID: 3032)
- mscorsvw.exe (PID: 756)
- ngen.exe (PID: 4000)
- ngen.exe (PID: 3332)
- ngen.exe (PID: 2428)
- mscorsvw.exe (PID: 1152)
- ngen.exe (PID: 2556)
- ngen.exe (PID: 508)
- ngen.exe (PID: 3628)
- ngen.exe (PID: 2060)
- ngen.exe (PID: 1512)
- ngen.exe (PID: 3388)
- ngen.exe (PID: 2520)
- mscorsvw.exe (PID: 1368)
- ngen.exe (PID: 3876)
- ngen.exe (PID: 1728)
- ngen.exe (PID: 3500)
- mscorsvw.exe (PID: 3776)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 532)
- mscorsvw.exe (PID: 3012)
- ngen.exe (PID: 2496)
- mscorsvw.exe (PID: 348)
- ngen.exe (PID: 4064)
- ngen.exe (PID: 3544)
- mscorsvw.exe (PID: 2384)
- ngen.exe (PID: 2292)
- mscorsvw.exe (PID: 3728)
- ngen.exe (PID: 448)
- ngen.exe (PID: 2984)
- ngen.exe (PID: 272)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 2284)
- ngen.exe (PID: 3640)
- ngen.exe (PID: 1120)
- ngen.exe (PID: 3196)
- ngen.exe (PID: 2972)
- mscorsvw.exe (PID: 388)
- ngen.exe (PID: 3972)
- ngen.exe (PID: 3648)
- mscorsvw.exe (PID: 1996)
- ngen.exe (PID: 3324)
- mscorsvw.exe (PID: 3732)
- ngen.exe (PID: 2880)
- mscorsvw.exe (PID: 1808)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 2352)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 3260)
- mscorsvw.exe (PID: 3776)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 2416)
- ngen.exe (PID: 2492)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 1996)
- ngen.exe (PID: 1400)
- ngen.exe (PID: 3928)
- mscorsvw.exe (PID: 1036)
- ngen.exe (PID: 3012)
- Mirolyshaegae.exe (PID: 2732)
- ngen.exe (PID: 284)
- mscorsvw.exe (PID: 344)
- Mirolyshaegae.exe (PID: 2880)
- ngen.exe (PID: 2792)
- mscorsvw.exe (PID: 4064)
- ngen.exe (PID: 2356)
- Mirolyshaegae.exe (PID: 1284)
- Mirolyshaegae.exe (PID: 1948)
- ngen.exe (PID: 2072)
- ngen.exe (PID: 2068)
Adds / modifies Windows certificates
- bumperWW.exe (PID: 2064)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
Checks for external IP
- bumperWW.exe (PID: 2064)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
Executed via COM
- DllHost.exe (PID: 2788)
- DllHost.exe (PID: 2280)
- DllHost.exe (PID: 3912)
Creates files in the user directory
- Explorer.EXE (PID: 740)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- E72E.tmp.exe (PID: 408)
- b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe (PID: 3052)
- cd203ebd-200a-40f9-9e6a-803d7b729eab.exe (PID: 2696)
- 0kKg8XdX1FMWLfp6lSCcsHgz.exe (PID: 3832)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- Roads License Agreement.exe (PID: 2632)
- EasyCalc License Agreement.exe (PID: 2360)
Executable content was dropped or overwritten
- bumperWW.exe (PID: 2064)
- dfBUd0ZXWhP94QhuOO7HN8Dd.exe (PID: 3444)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- ________djskjT76(((.exe (PID: 3732)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- msiexec.exe (PID: 3824)
Drops a file with a compile date too recent
- bumperWW.exe (PID: 2064)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
Drops a file that was compiled in debug mode
- bumperWW.exe (PID: 2064)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- msiexec.exe (PID: 3824)
Application launched itself
- 9gqhoLvblcW2BC9hjHC4tkno.exe (PID: 3148)
- 9FBpMmeA1jfTd4IUnavS64qZ.exe (PID: 3280)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 2836)
- 6E3Q636UZ_jxOTrwYG_ceTus.exe (PID: 3136)
- UtAVW52g78C8W8MI1VhAXbFk.exe (PID: 3768)
- msiexec.exe (PID: 3824)
Reads Environment values
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- C9FF.tmp.exe (PID: 2144)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- ________djskjT76(((.exe (PID: 3732)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- Mirolyshaegae.exe (PID: 4004)
- b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe (PID: 3052)
- cd203ebd-200a-40f9-9e6a-803d7b729eab.exe (PID: 2696)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- Deqytihetu.exe (PID: 3256)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- ________djskjT76(((.exe (PID: 2032)
- Sybevyqebu.exe (PID: 2848)
- xdx.exe (PID: 1144)
- Bydaqusyry.exe (PID: 2784)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- AppLaunch.exe (PID: 3400)
- vssvc.exe (PID: 796)
- AppLaunch.exe (PID: 3720)
- Setup.exe (PID: 4052)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
- Mirolyshaegae.exe (PID: 2732)
- Mirolyshaegae.exe (PID: 2880)
- Mirolyshaegae.exe (PID: 1284)
Drops a file with too old compile date
- bumperWW.exe (PID: 2064)
- ________djskjT76(((.exe (PID: 3732)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
Reads the Windows organization settings
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- foldershare.tmp (PID: 2296)
- kl6jlya2lGXvnSofBqImr58S.tmp (PID: 2852)
- foldershare.tmp (PID: 2808)
- msiexec.exe (PID: 1160)
- msiexec.exe (PID: 3824)
Reads Windows owner or organization settings
- WpPbrnpT74x_bdTWeekwIAeG.tmp (PID: 3472)
- foldershare.tmp (PID: 2296)
- kl6jlya2lGXvnSofBqImr58S.tmp (PID: 2852)
- foldershare.tmp (PID: 2808)
- msiexec.exe (PID: 1160)
- msiexec.exe (PID: 3824)
Reads the cookies of Google Chrome
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- xdx.exe (PID: 1144)
- AppLaunch.exe (PID: 3400)
- AppLaunch.exe (PID: 3720)
Reads the cookies of Mozilla Firefox
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- RegAsm.exe (PID: 320)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- jg1_1faf.exe (PID: 3260)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- xdx.exe (PID: 1144)
- qYPfAyFc0l3KM6bIXSXem2Kx.exe (PID: 3224)
- AppLaunch.exe (PID: 3400)
- jg1_1faf.exe (PID: 4052)
- AppLaunch.exe (PID: 3720)
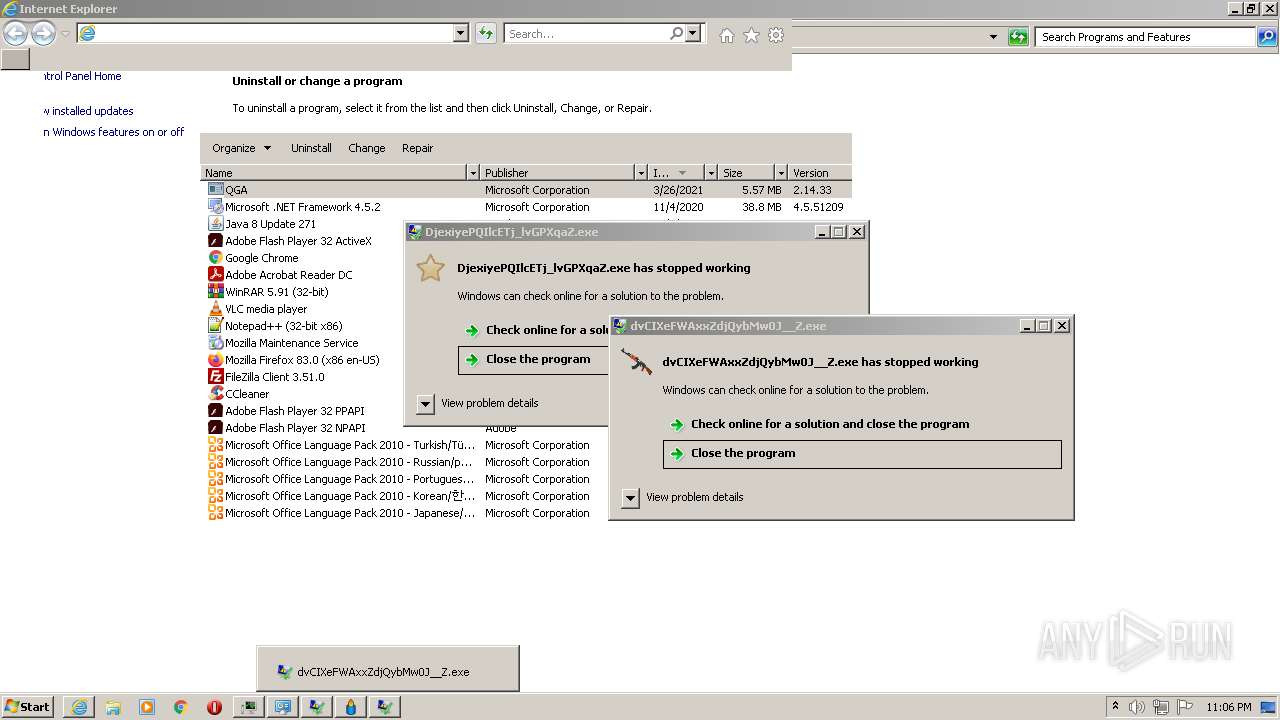
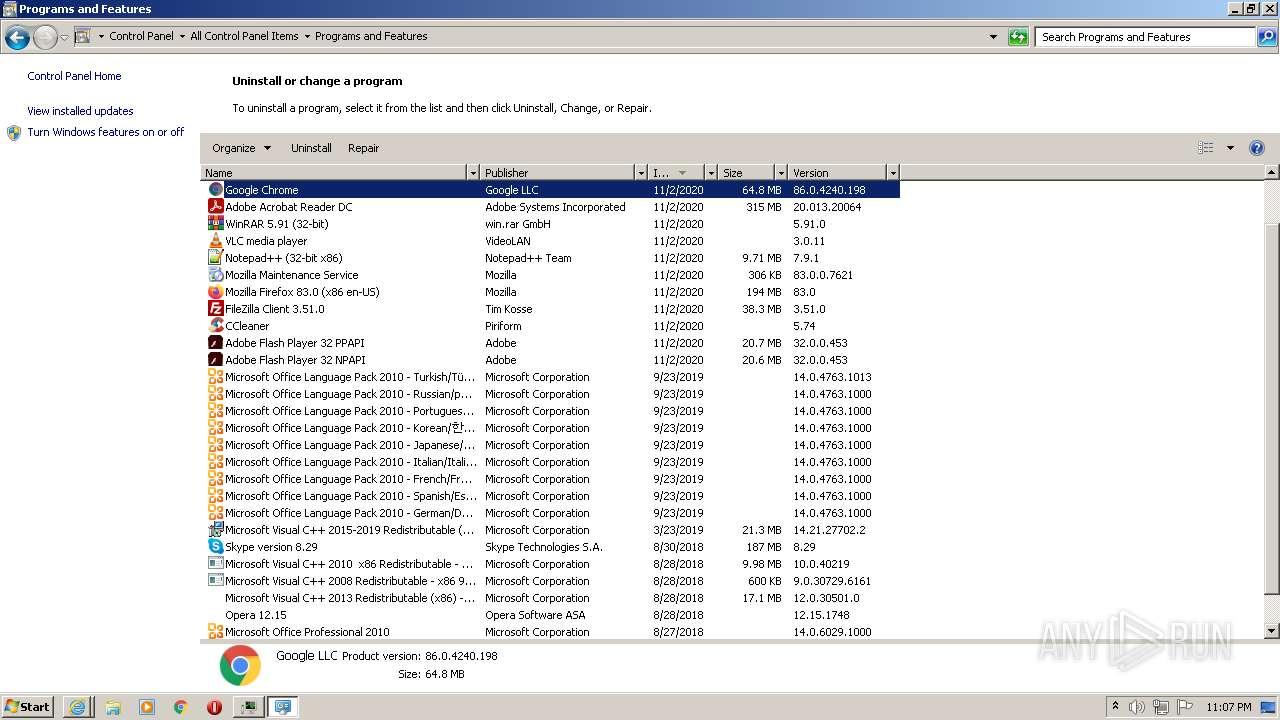
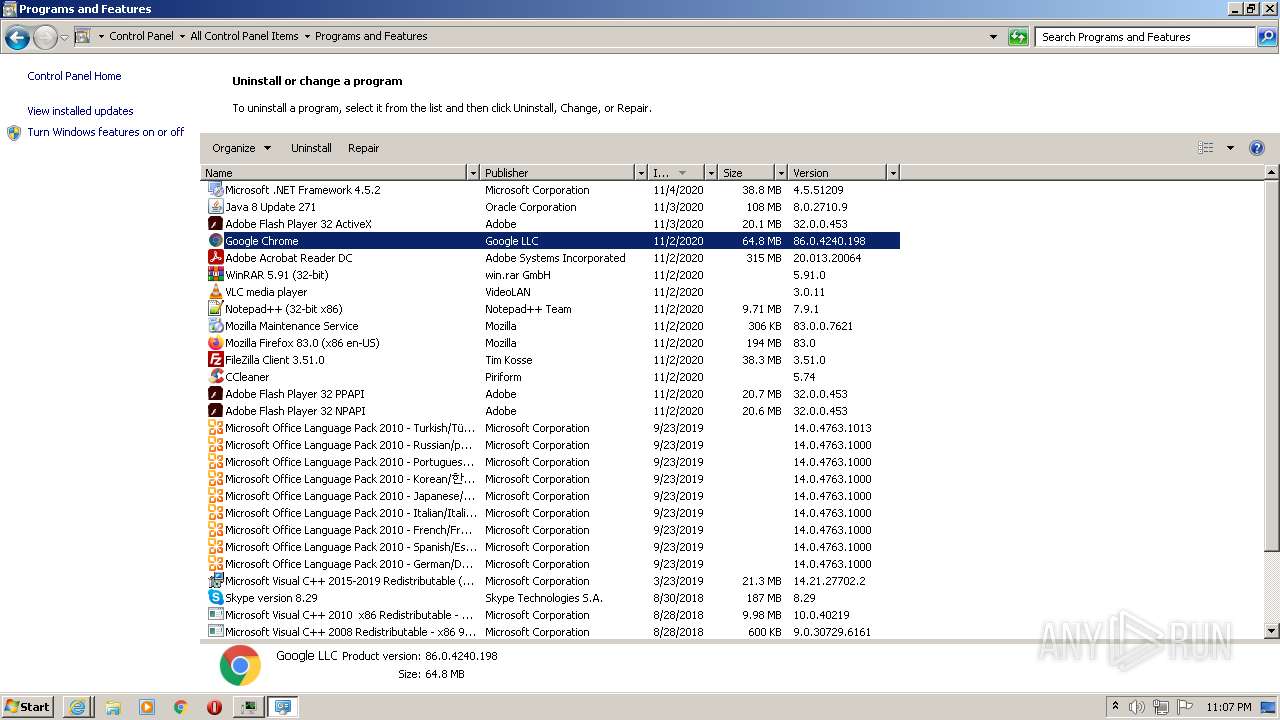
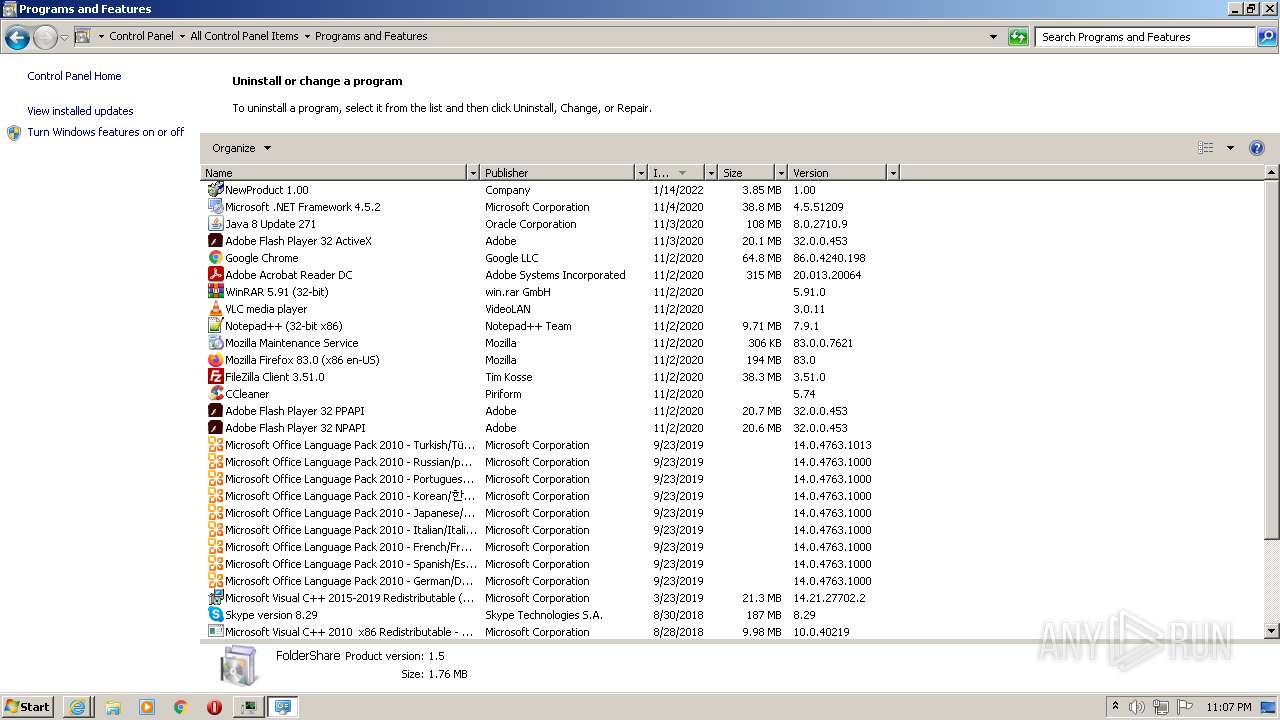
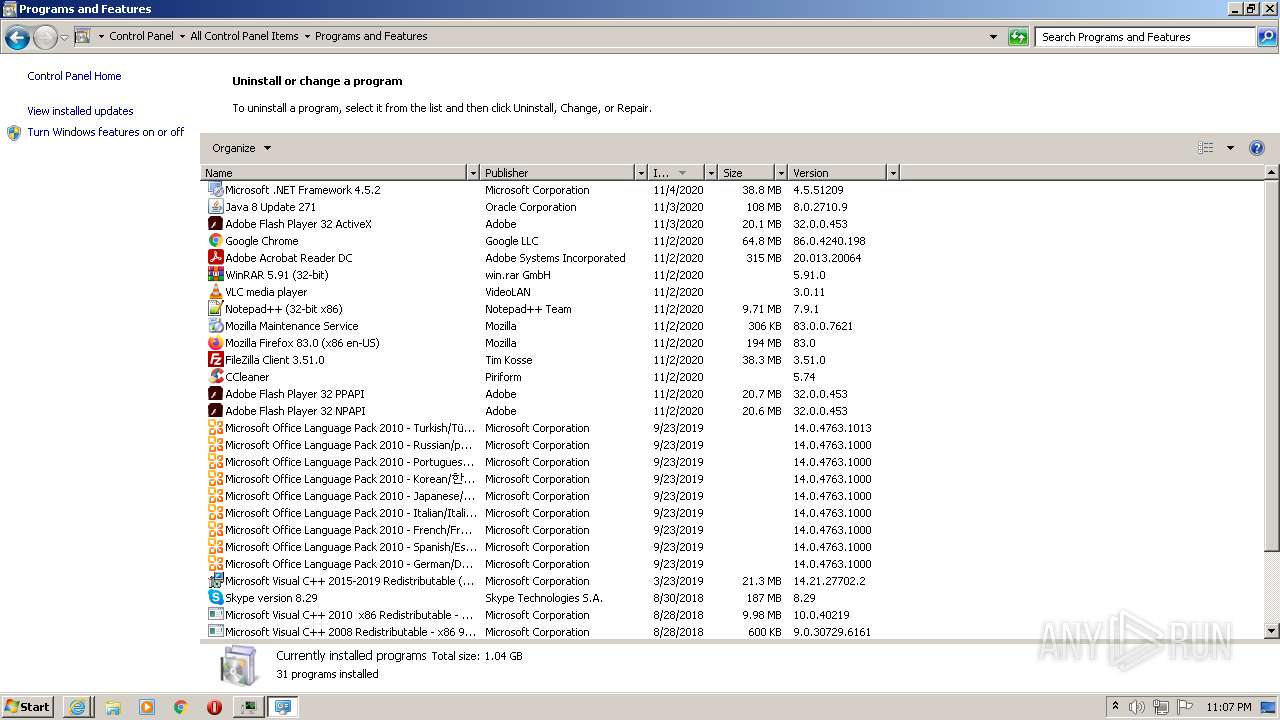
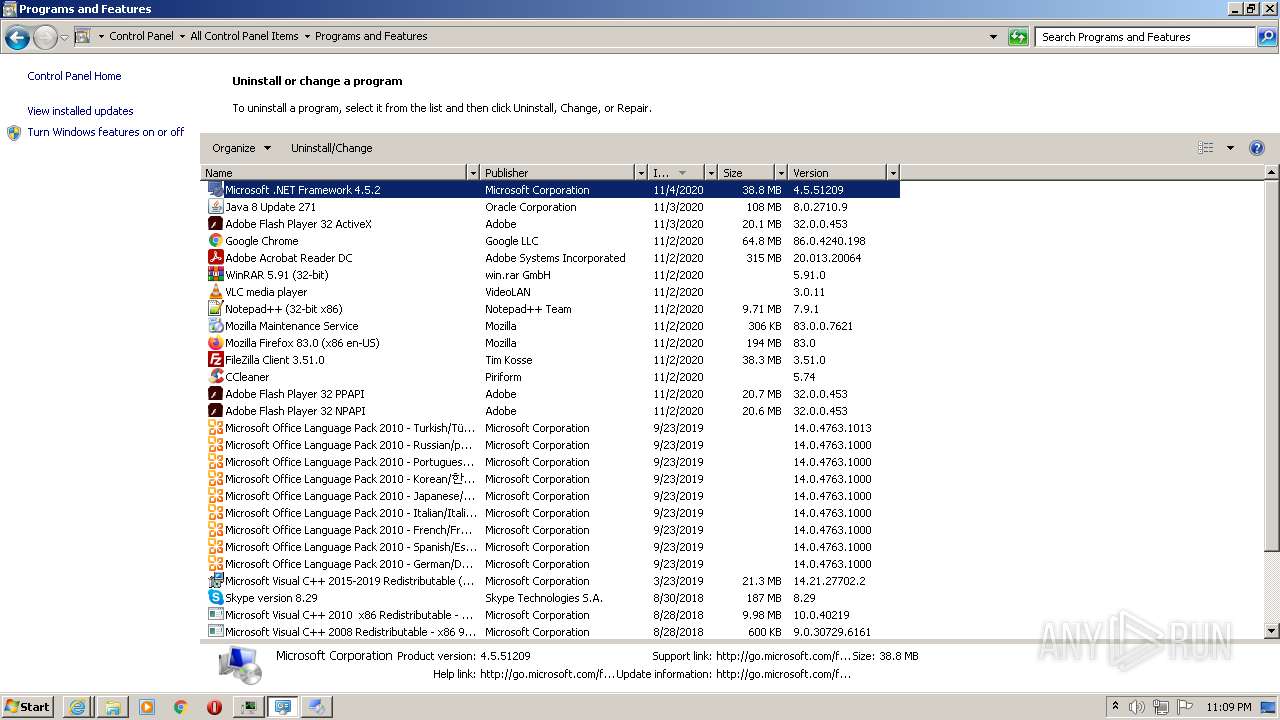
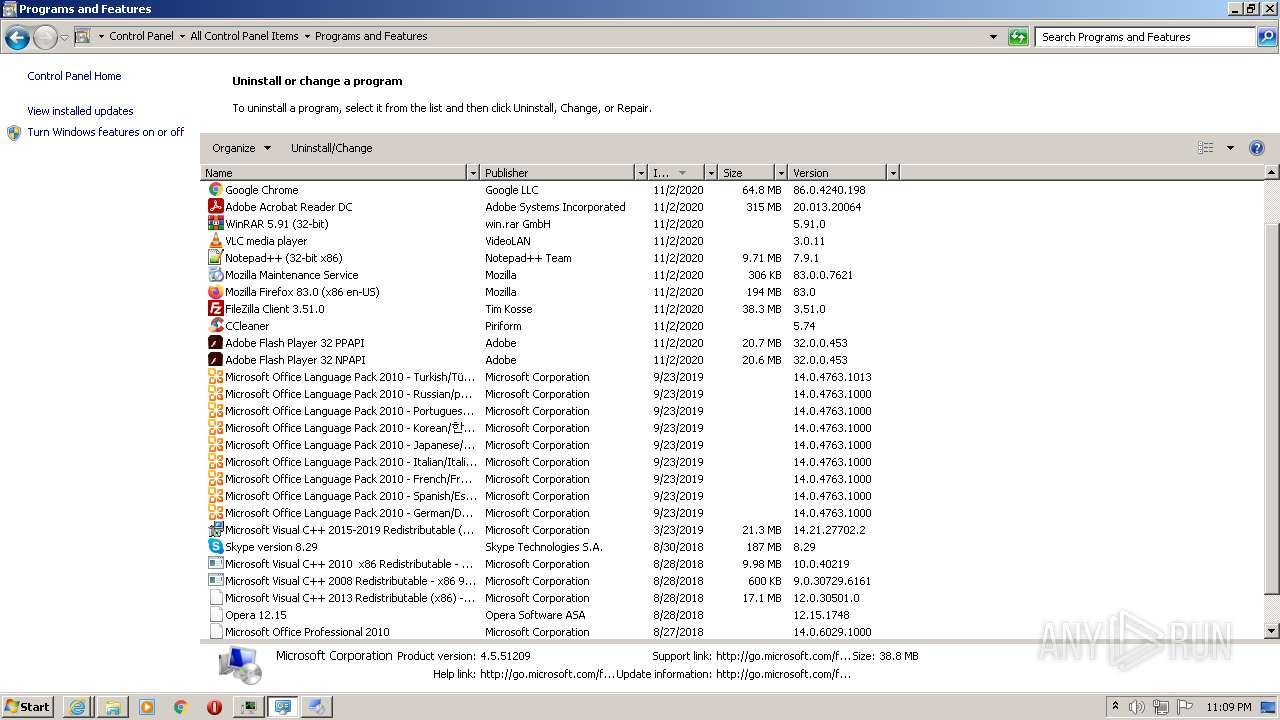
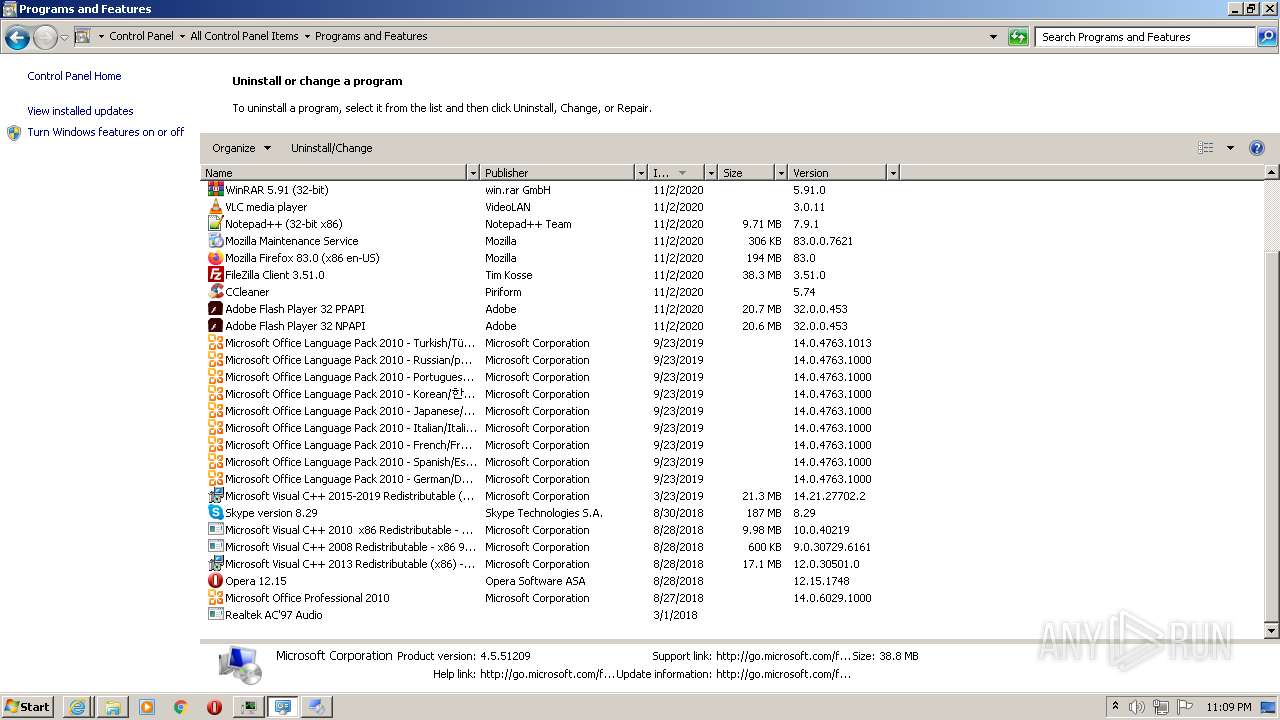
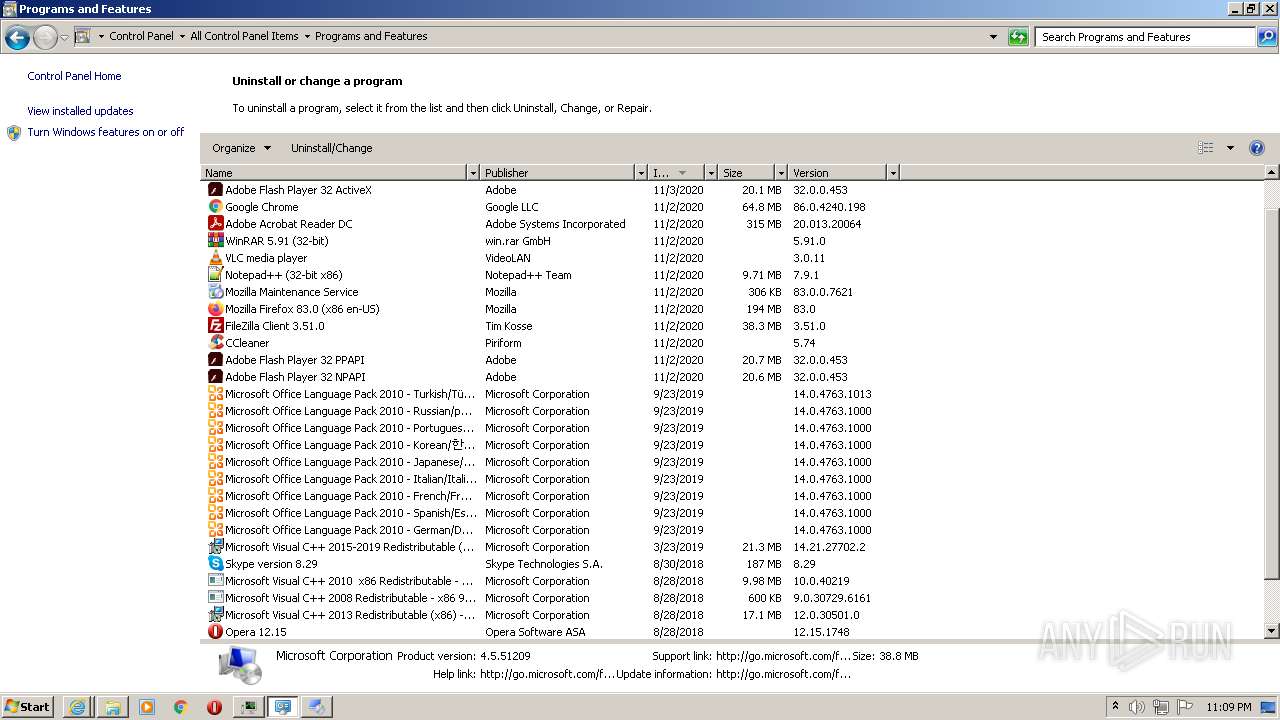
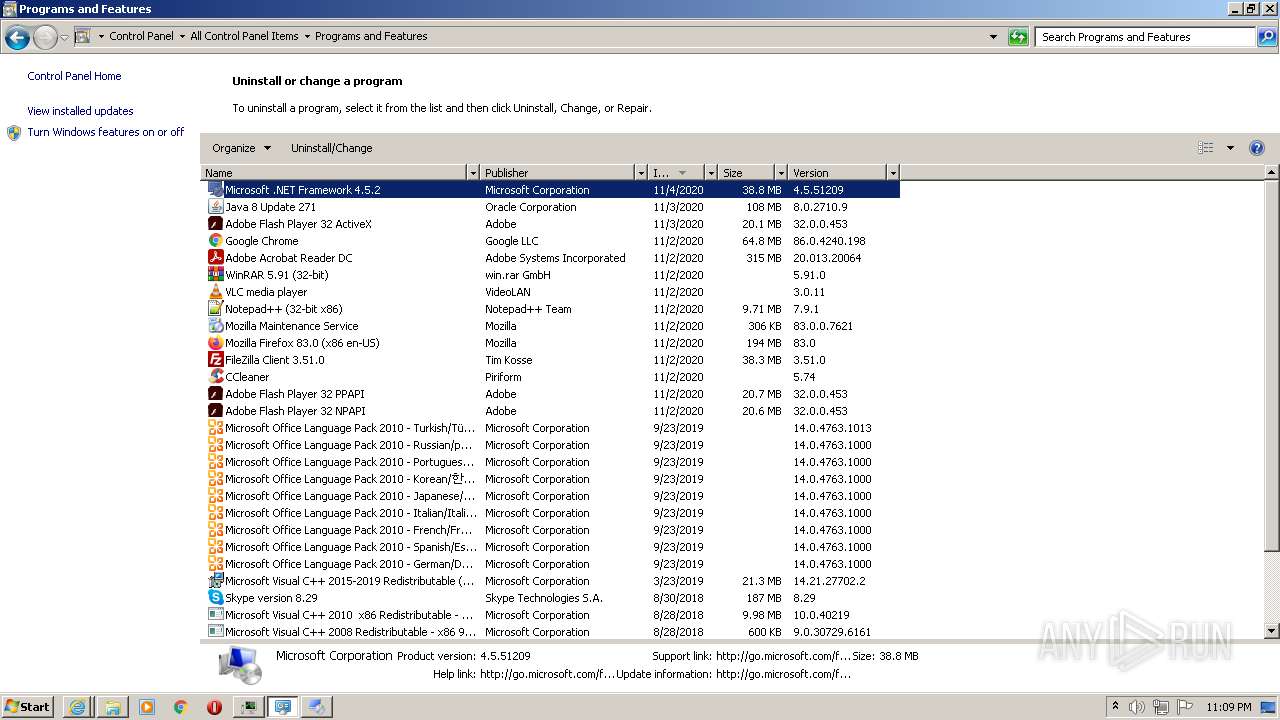
Searches for installed software
- VerK1NM_Tep9DEVvr19a89qM.exe (PID: 2060)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- aM7Ergzxxy9ZDTTIv9FsCrMI.exe (PID: 3844)
- gQWqKFNtkMWWYQjMsceH7auq.exe (PID: 2744)
- h1qn6mHjfy3ngUezI969Rxav.exe (PID: 308)
- RegAsm.exe (PID: 320)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- Lz_rfAwMdgqUGgqOrgDw5k4c.exe (PID: 2132)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- S31qFsauBdydjSM_c3dZq1nh.exe (PID: 2684)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- Explorer.EXE (PID: 740)
- xdx.exe (PID: 1144)
- foldershare.tmp (PID: 2808)
- AppLaunch.exe (PID: 3400)
- msiexec.exe (PID: 1160)
- AppLaunch.exe (PID: 3720)
- DllHost.exe (PID: 3912)
- msiexec.exe (PID: 3824)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
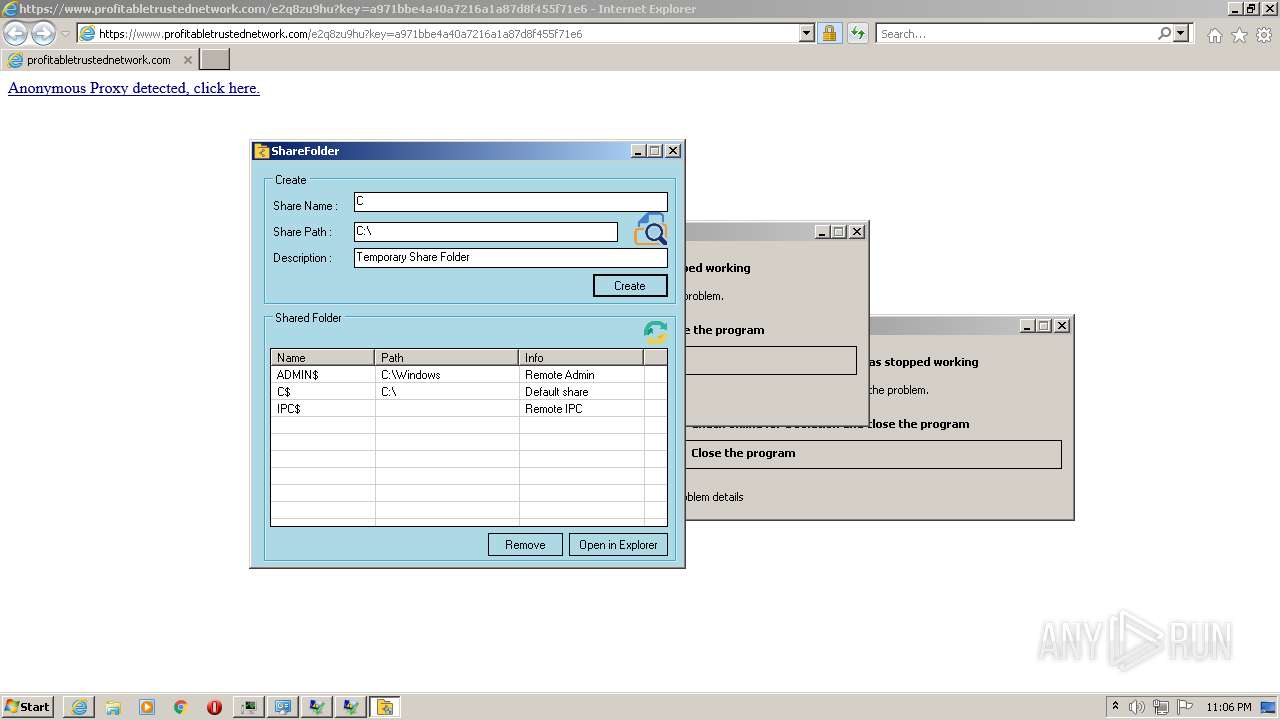
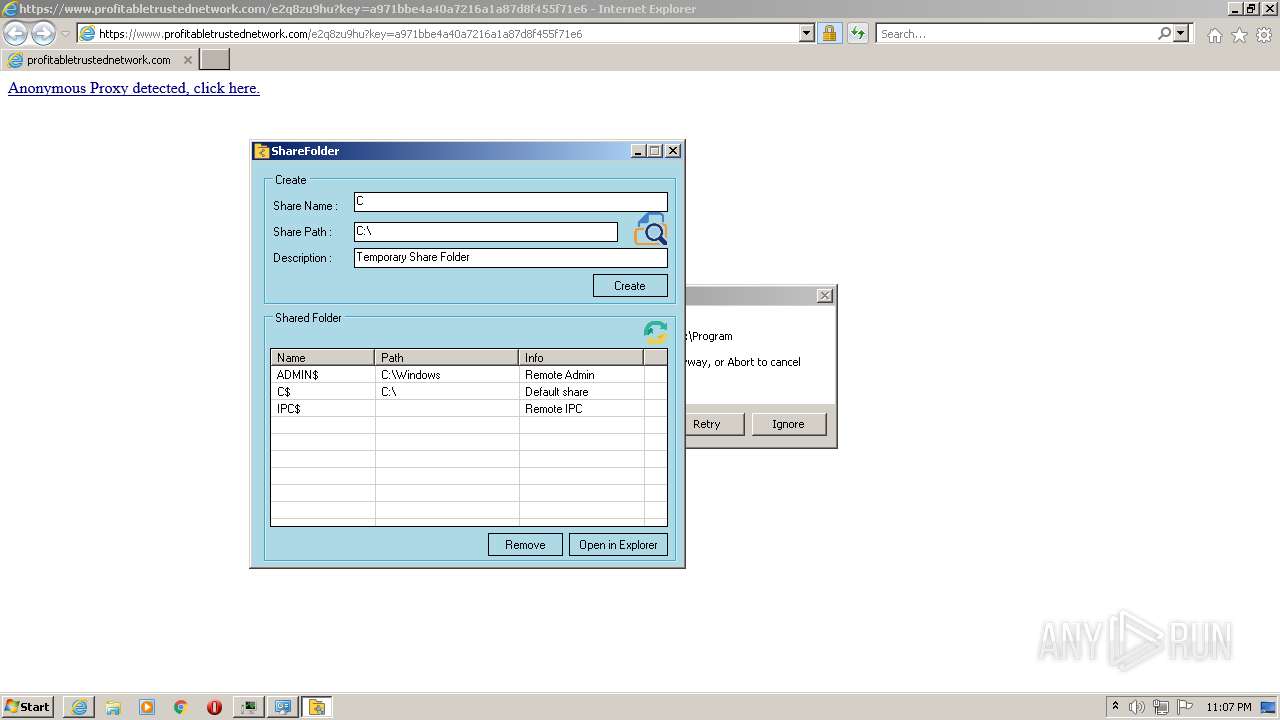
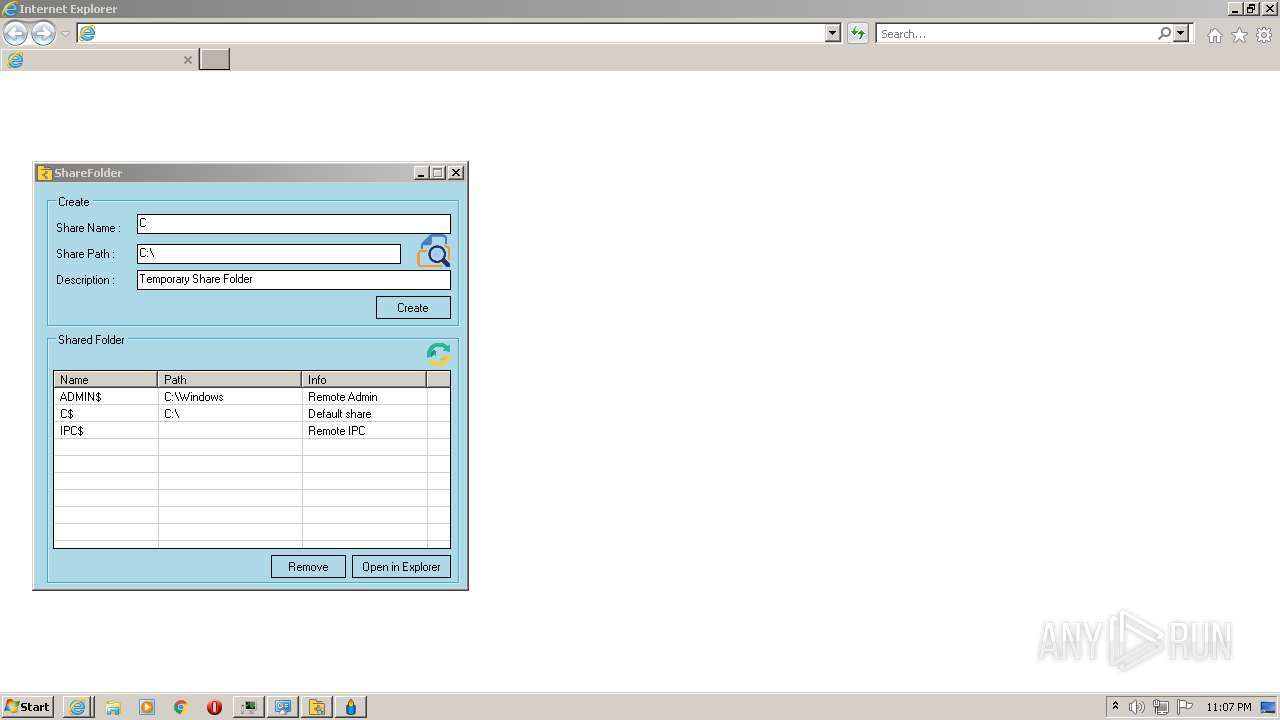
Creates a directory in Program Files
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- jZR4CnxOPLtgsLUr86lbO5IW.exe (PID: 2144)
- ________djskjT76(((.exe (PID: 3732)
- foldershare.tmp (PID: 2296)
- ________djskjT76(((.exe (PID: 2032)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
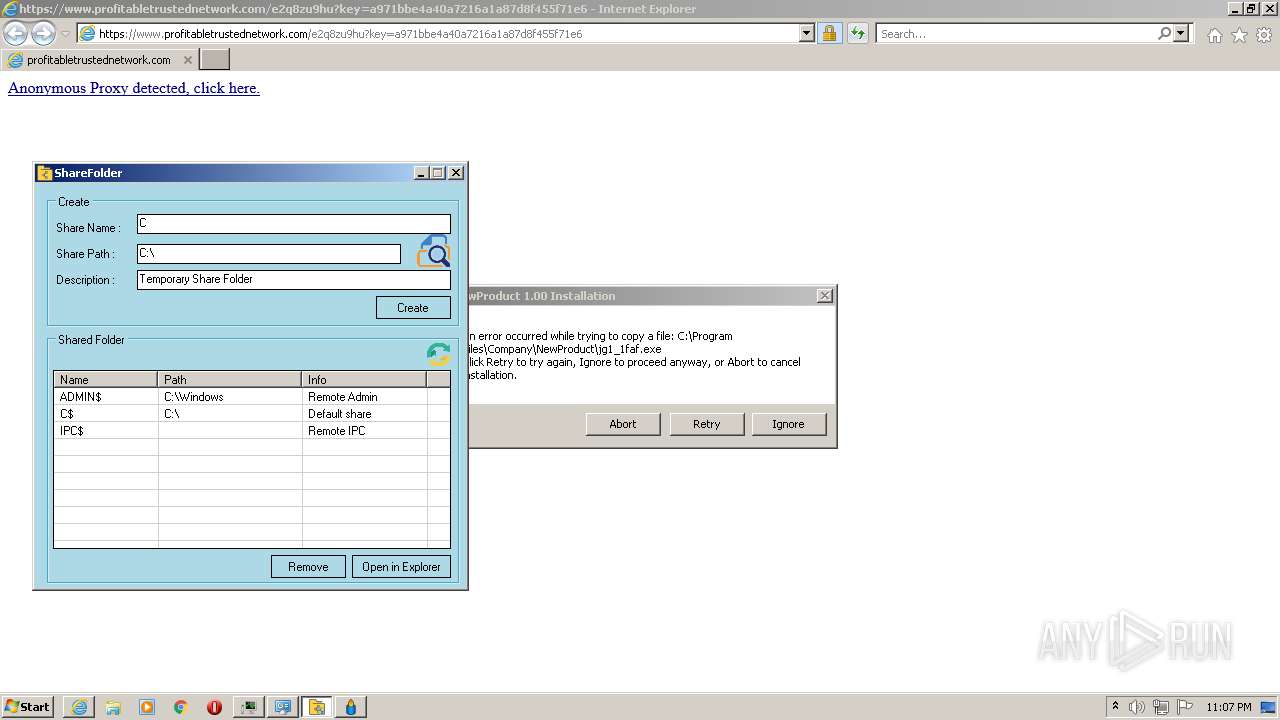
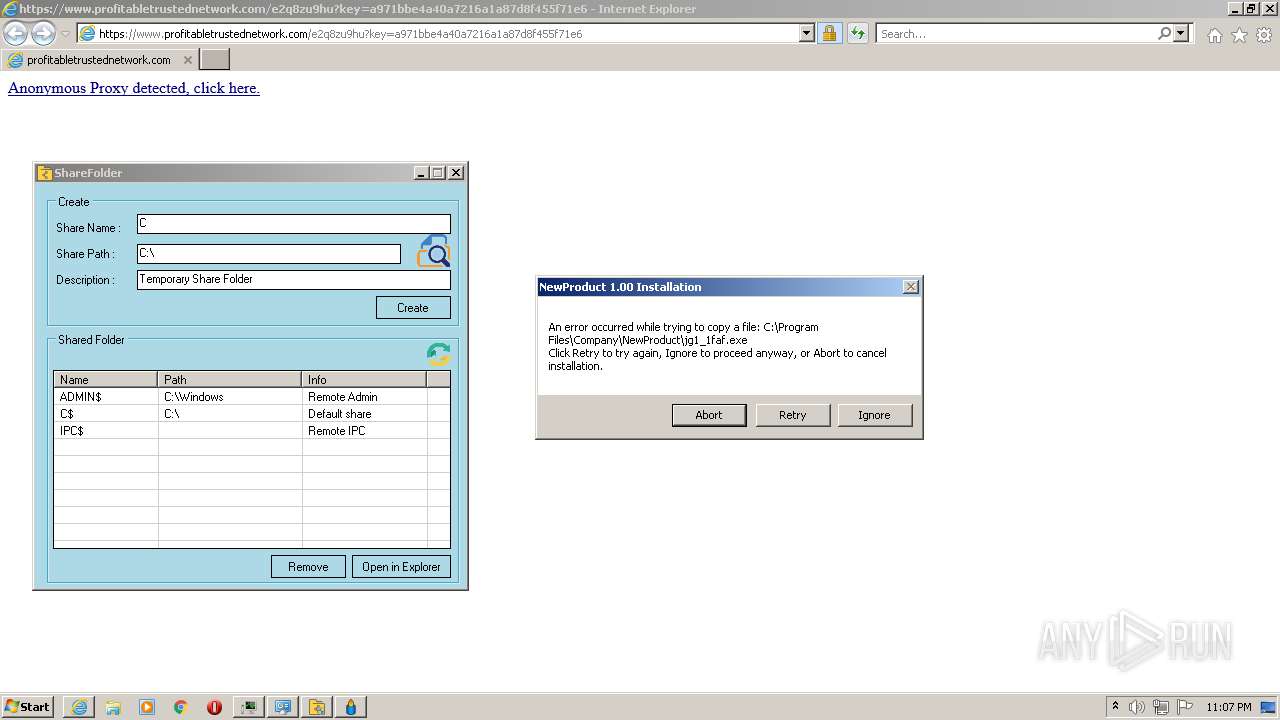
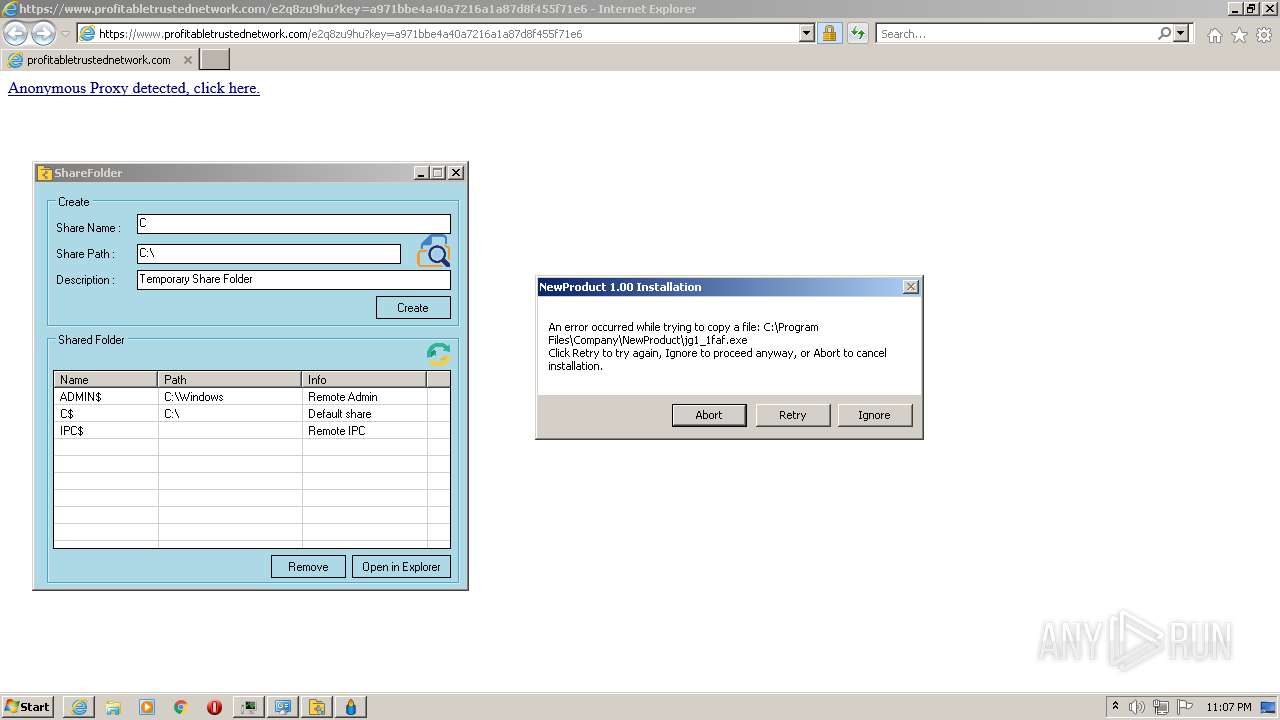
Creates files in the program directory
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- jZR4CnxOPLtgsLUr86lbO5IW.exe (PID: 2144)
- jg1_1faf.exe (PID: 3260)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- jg1_1faf.exe (PID: 4052)
Creates files in the Windows directory
- svchost.exe (PID: 860)
- Bydaqusyry.exe (PID: 2784)
- Setup.exe (PID: 4052)
- ngen.exe (PID: 4064)
- ngen.exe (PID: 3372)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 1284)
- ngen.exe (PID: 3108)
- mscorsvw.exe (PID: 2772)
- ngen.exe (PID: 992)
- ngen.exe (PID: 668)
- mscorsvw.exe (PID: 3548)
- ngen.exe (PID: 1808)
- ngen.exe (PID: 3516)
- ngen.exe (PID: 636)
- ngen.exe (PID: 1152)
- ngen.exe (PID: 468)
- ngen.exe (PID: 696)
- ngen.exe (PID: 2252)
- ngen.exe (PID: 668)
- ngen.exe (PID: 532)
- ngen.exe (PID: 4088)
- ngen.exe (PID: 3716)
- ngen.exe (PID: 2072)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 3364)
- ngen.exe (PID: 2088)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 2200)
- ngen.exe (PID: 2752)
- ngen.exe (PID: 3648)
- ngen.exe (PID: 696)
- ngen.exe (PID: 2192)
- mscorsvw.exe (PID: 2632)
- ngen.exe (PID: 3032)
- mscorsvw.exe (PID: 1152)
- ngen.exe (PID: 4000)
- ngen.exe (PID: 2556)
- ngen.exe (PID: 3332)
- ngen.exe (PID: 2428)
- mscorsvw.exe (PID: 756)
- ngen.exe (PID: 2520)
- ngen.exe (PID: 2060)
- ngen.exe (PID: 3628)
- ngen.exe (PID: 508)
- ngen.exe (PID: 1512)
- ngen.exe (PID: 3388)
- mscorsvw.exe (PID: 1368)
- ngen.exe (PID: 3876)
- ngen.exe (PID: 1728)
- ngen.exe (PID: 3500)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 532)
- mscorsvw.exe (PID: 3012)
- ngen.exe (PID: 2496)
- ngen.exe (PID: 4064)
- mscorsvw.exe (PID: 348)
- mscorsvw.exe (PID: 3776)
- ngen.exe (PID: 3544)
- ngen.exe (PID: 2984)
- mscorsvw.exe (PID: 2384)
- ngen.exe (PID: 2292)
- mscorsvw.exe (PID: 3728)
- ngen.exe (PID: 3196)
- ngen.exe (PID: 272)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 2284)
- ngen.exe (PID: 3640)
- ngen.exe (PID: 448)
- ngen.exe (PID: 2972)
- mscorsvw.exe (PID: 388)
- ngen.exe (PID: 3972)
- ngen.exe (PID: 3648)
- mscorsvw.exe (PID: 1996)
- ngen.exe (PID: 1120)
- ngen.exe (PID: 3324)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 2880)
- mscorsvw.exe (PID: 3732)
- mscorsvw.exe (PID: 1808)
- ngen.exe (PID: 2352)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 3260)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 2492)
- ngen.exe (PID: 2416)
- ngen.exe (PID: 3436)
- ngen.exe (PID: 1996)
- mscorsvw.exe (PID: 3776)
- mscorsvw.exe (PID: 1036)
- ngen.exe (PID: 3012)
- ngen.exe (PID: 284)
- ngen.exe (PID: 1400)
- ngen.exe (PID: 3928)
- mscorsvw.exe (PID: 344)
- mscorsvw.exe (PID: 4064)
- ngen.exe (PID: 2356)
- ngen.exe (PID: 2792)
- ngen.exe (PID: 2072)
- ngen.exe (PID: 2068)
Starts CMD.EXE for self-deleting
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
Starts CMD.EXE for commands execution
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- forfiles.exe (PID: 376)
- forfiles.exe (PID: 3052)
- XzaSJi8d9iZAMRxdLlbojsA4.exe (PID: 3320)
Reads CPU info
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- Setup.exe (PID: 4052)
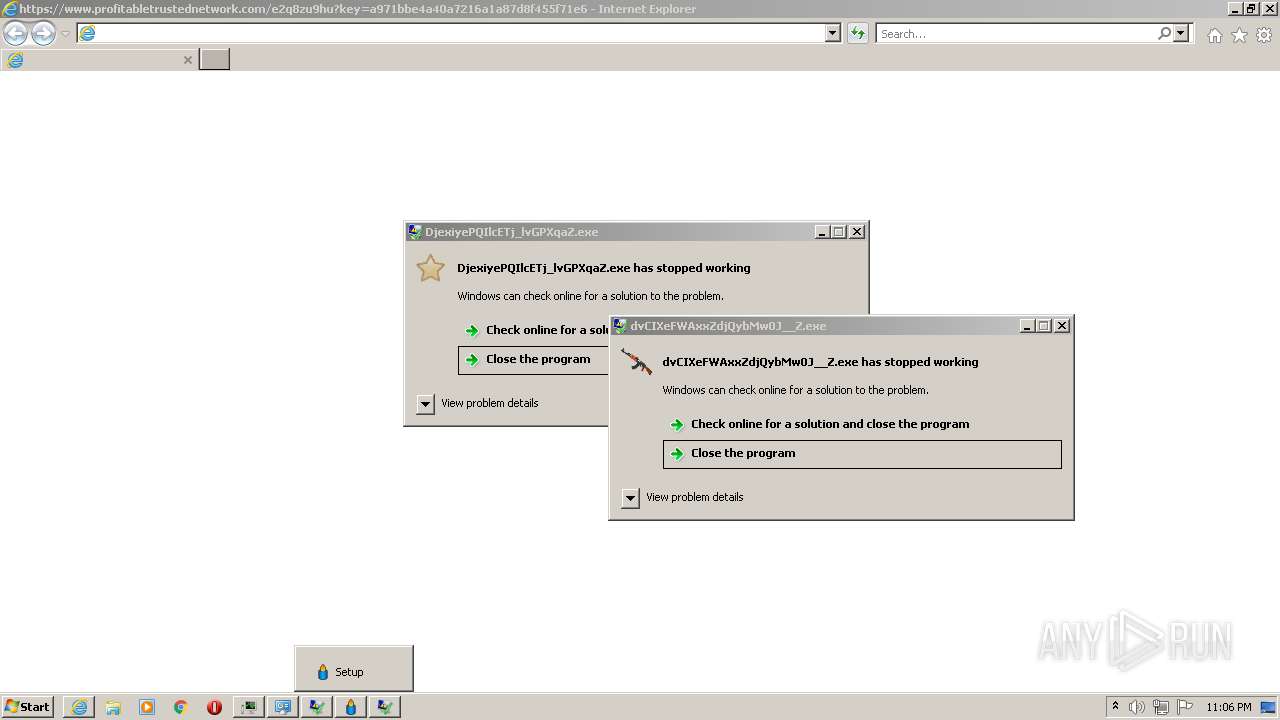
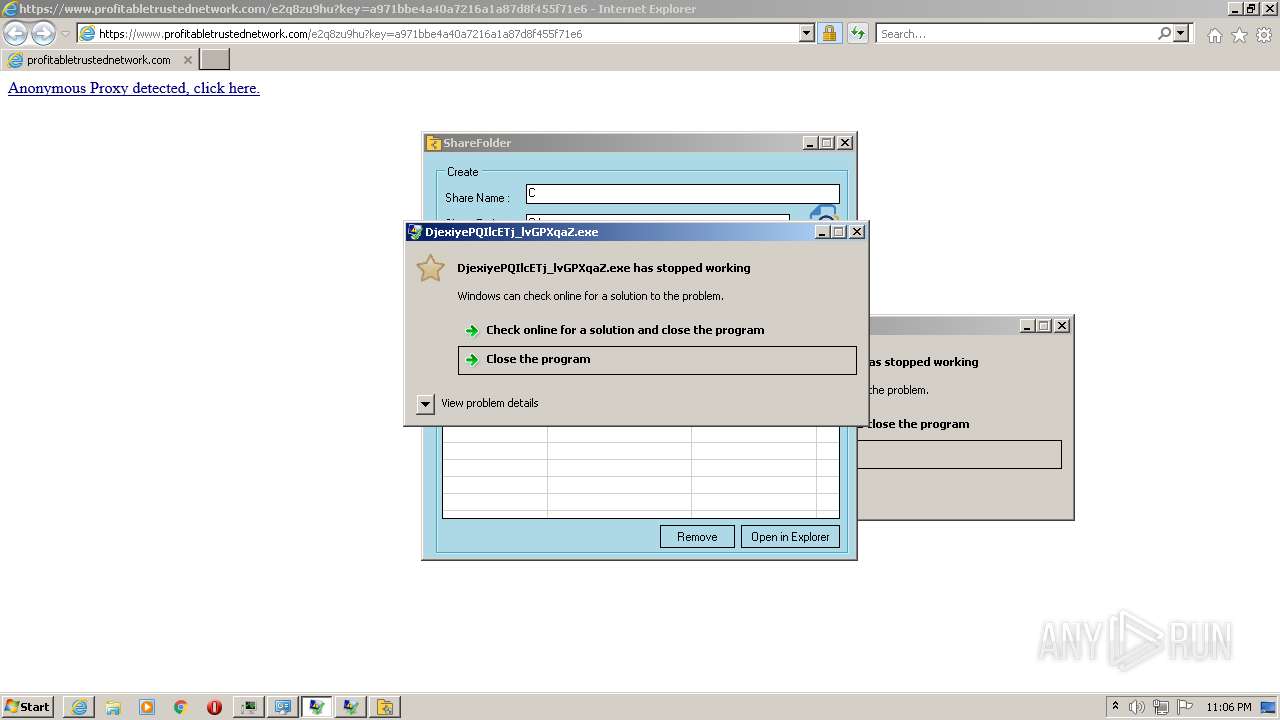
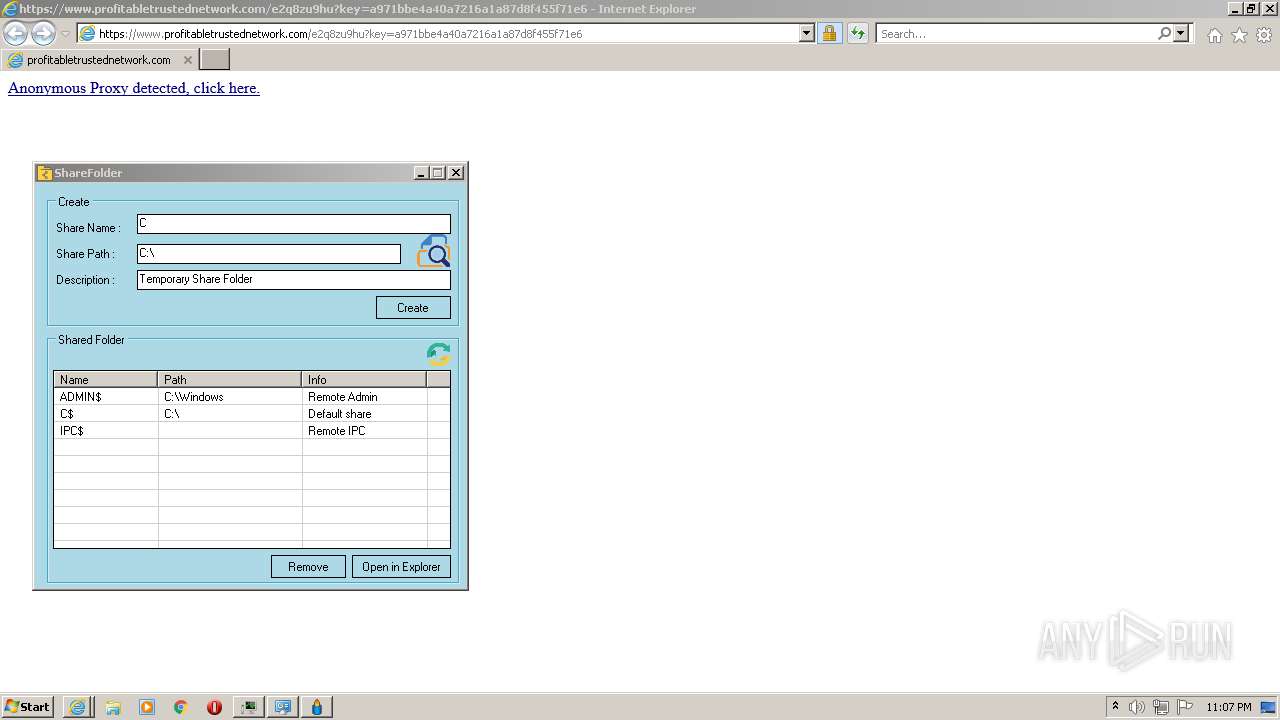
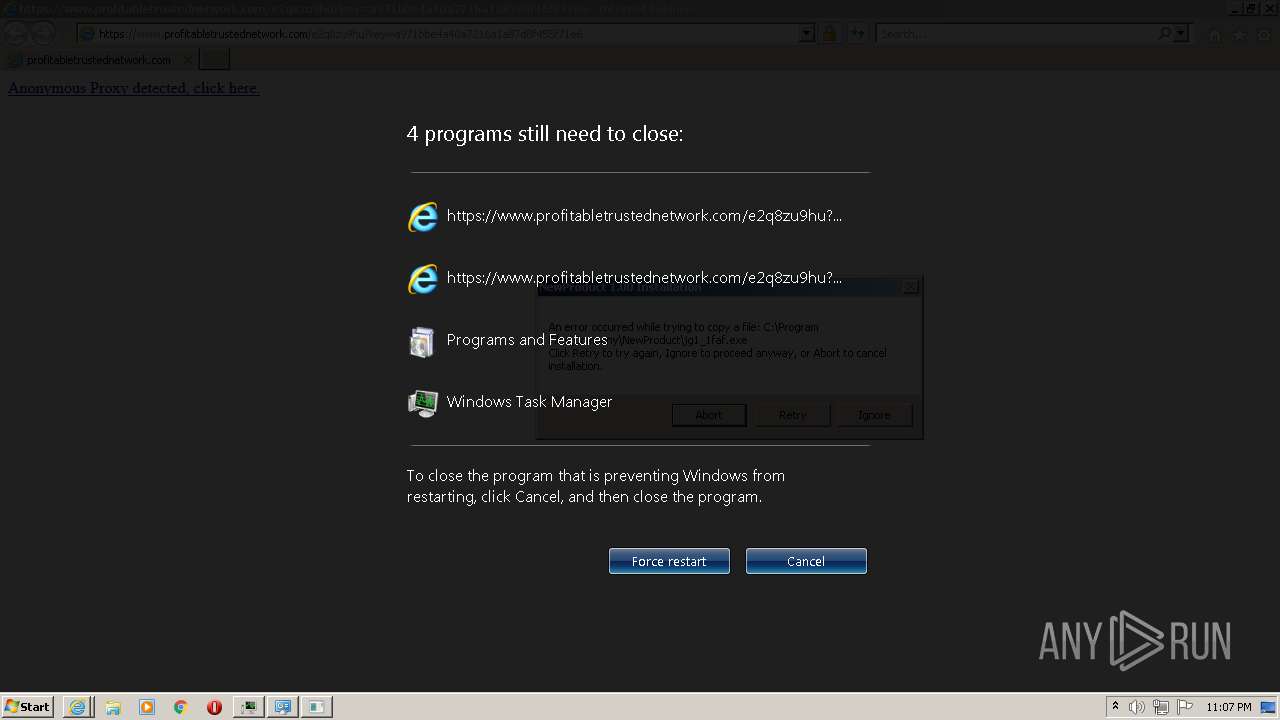
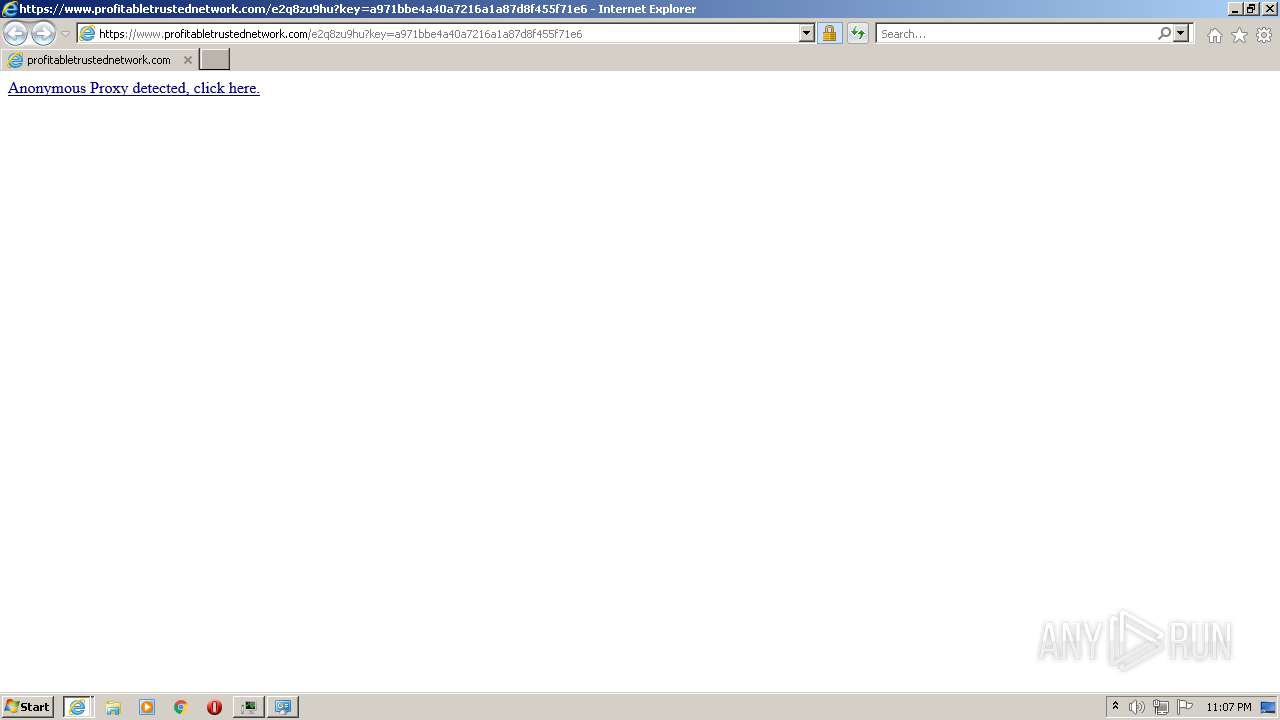
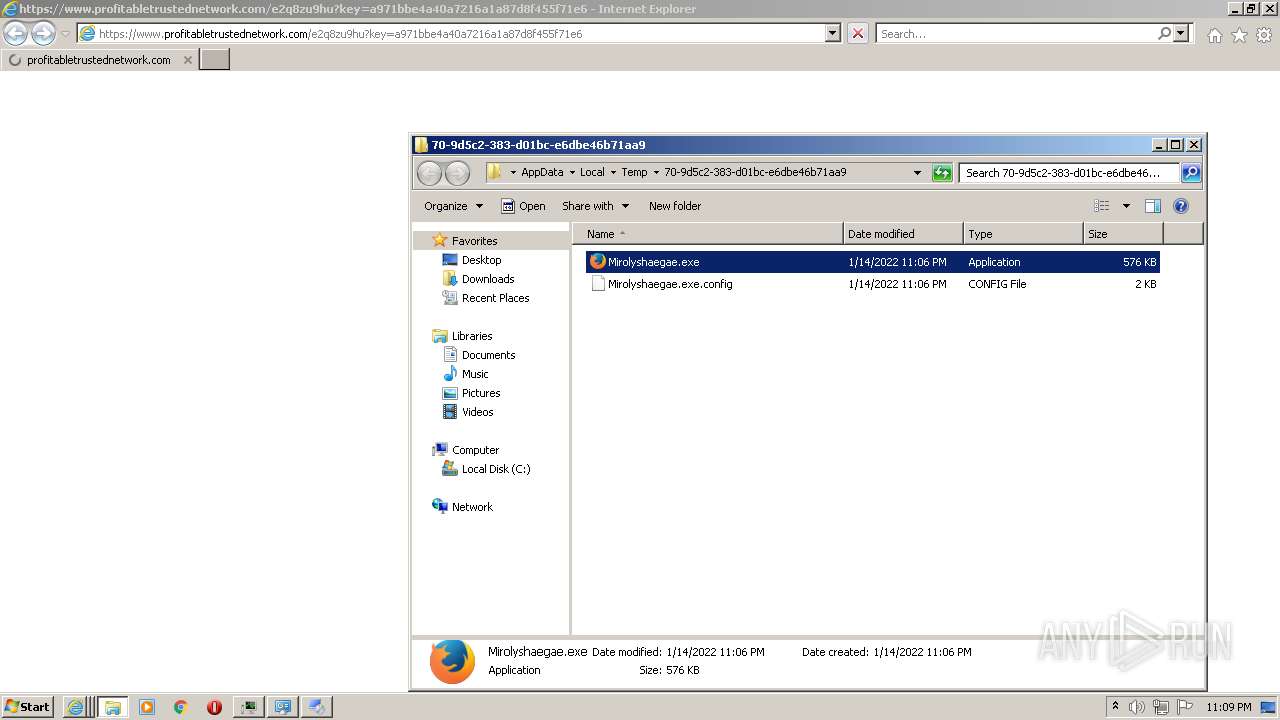
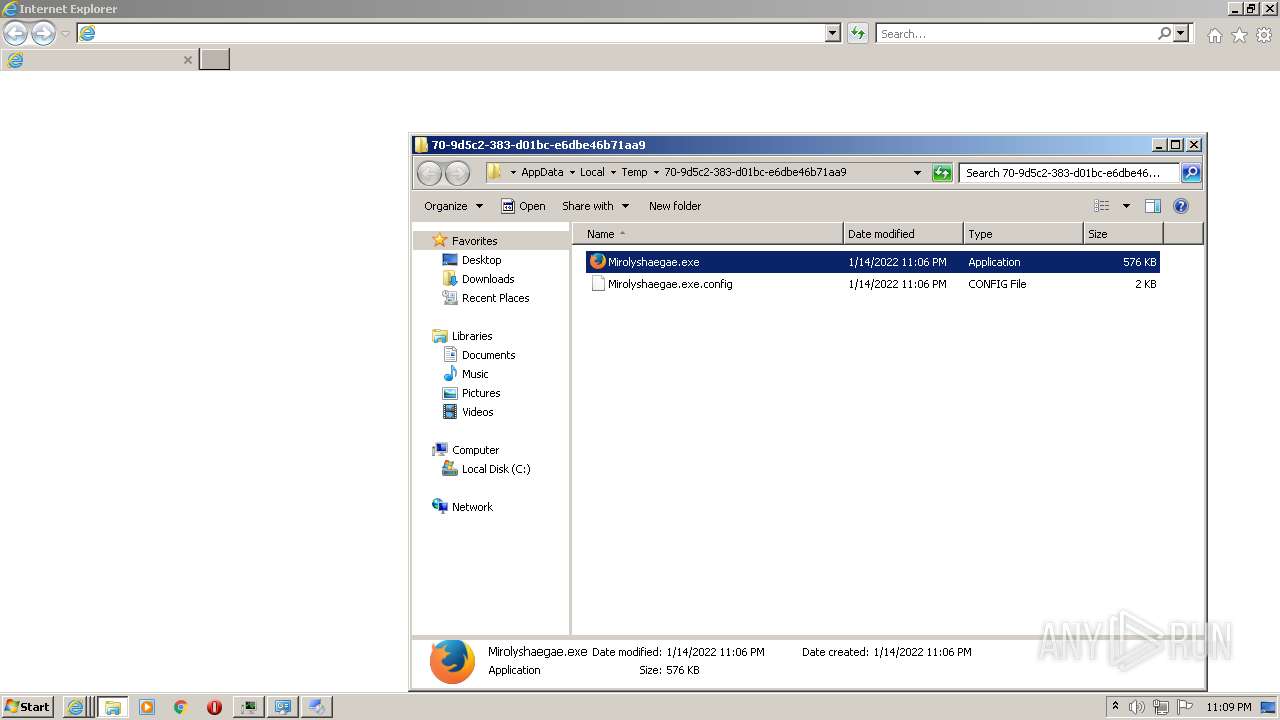
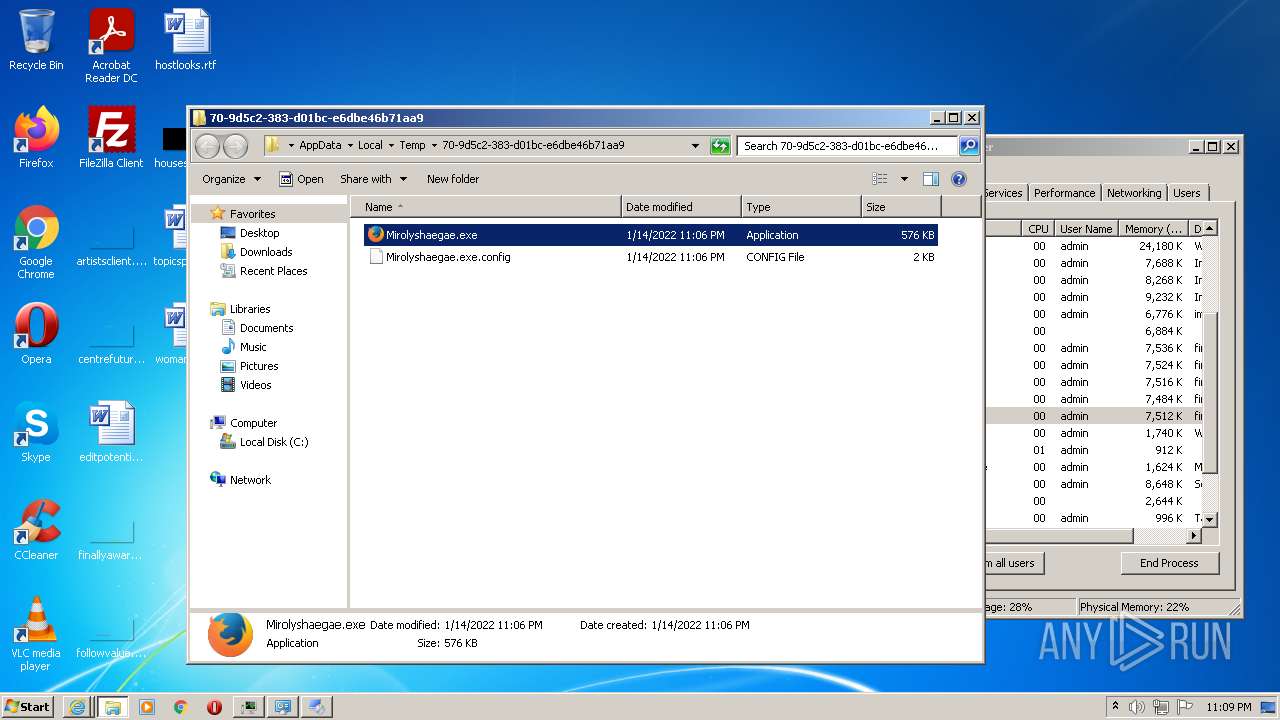
Starts Internet Explorer
- Mirolyshaegae.exe (PID: 4004)
- Sybevyqebu.exe (PID: 2848)
- Mirolyshaegae.exe (PID: 2732)
- Mirolyshaegae.exe (PID: 2880)
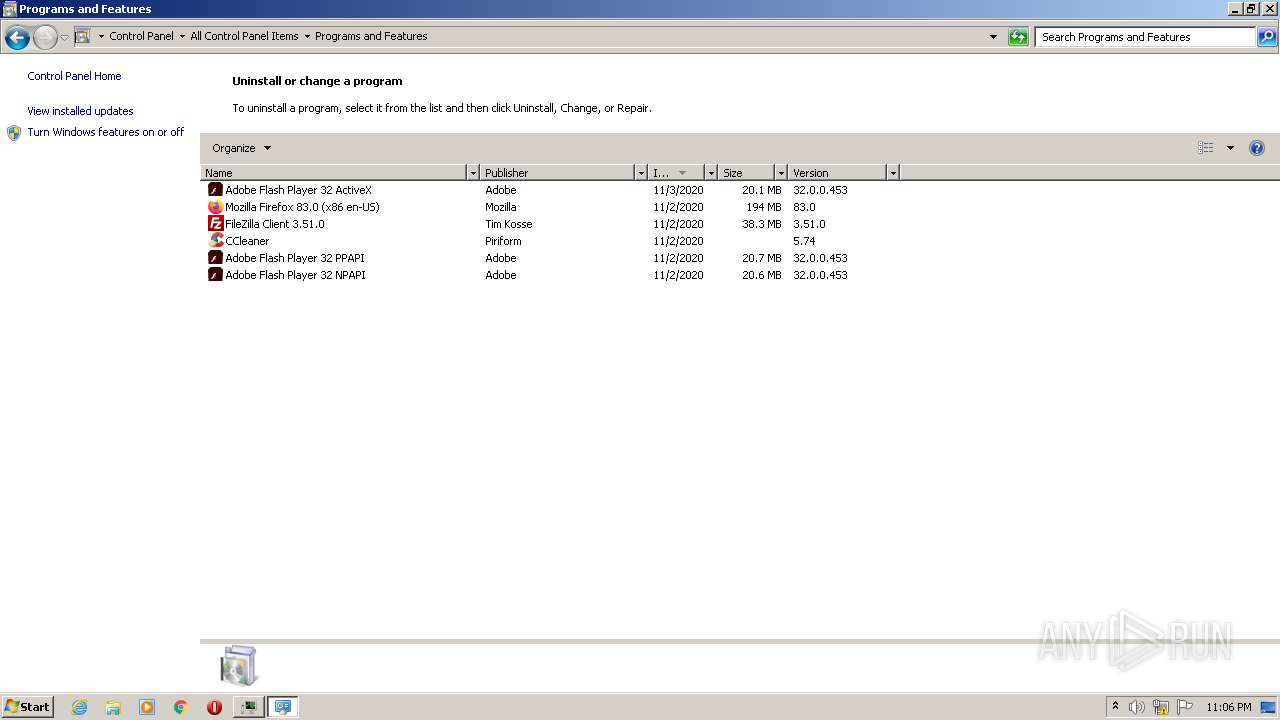
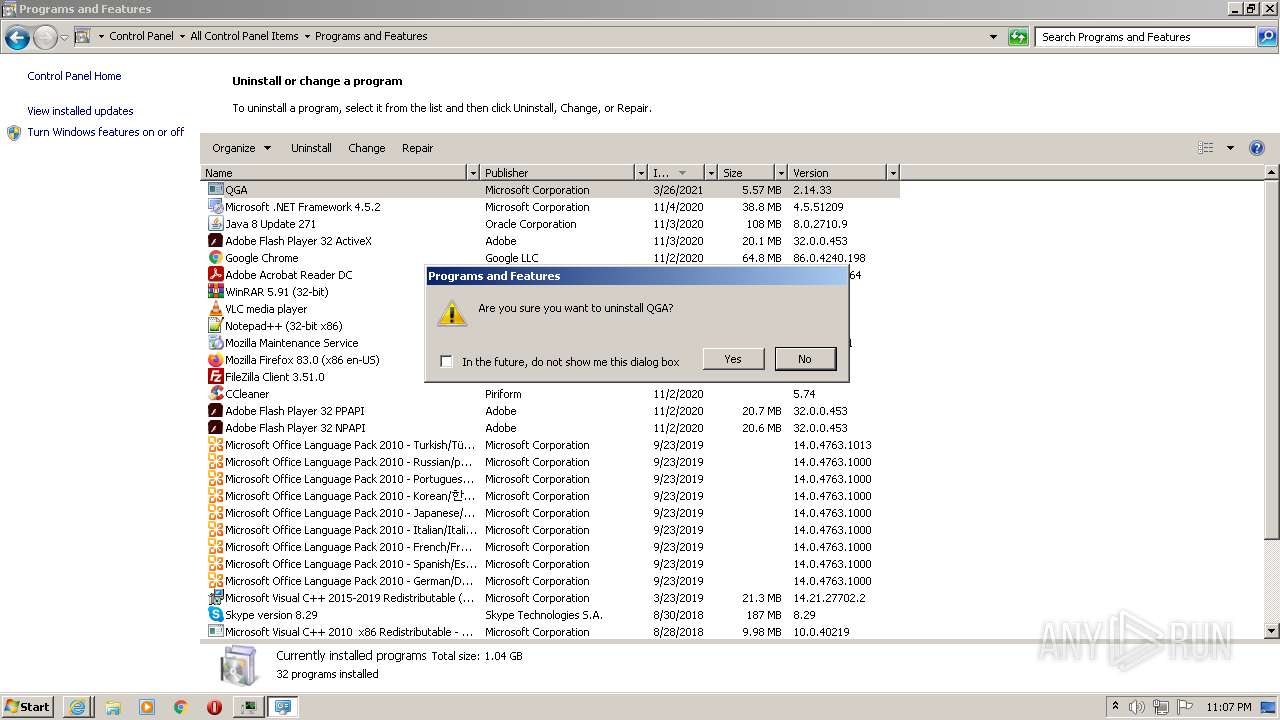
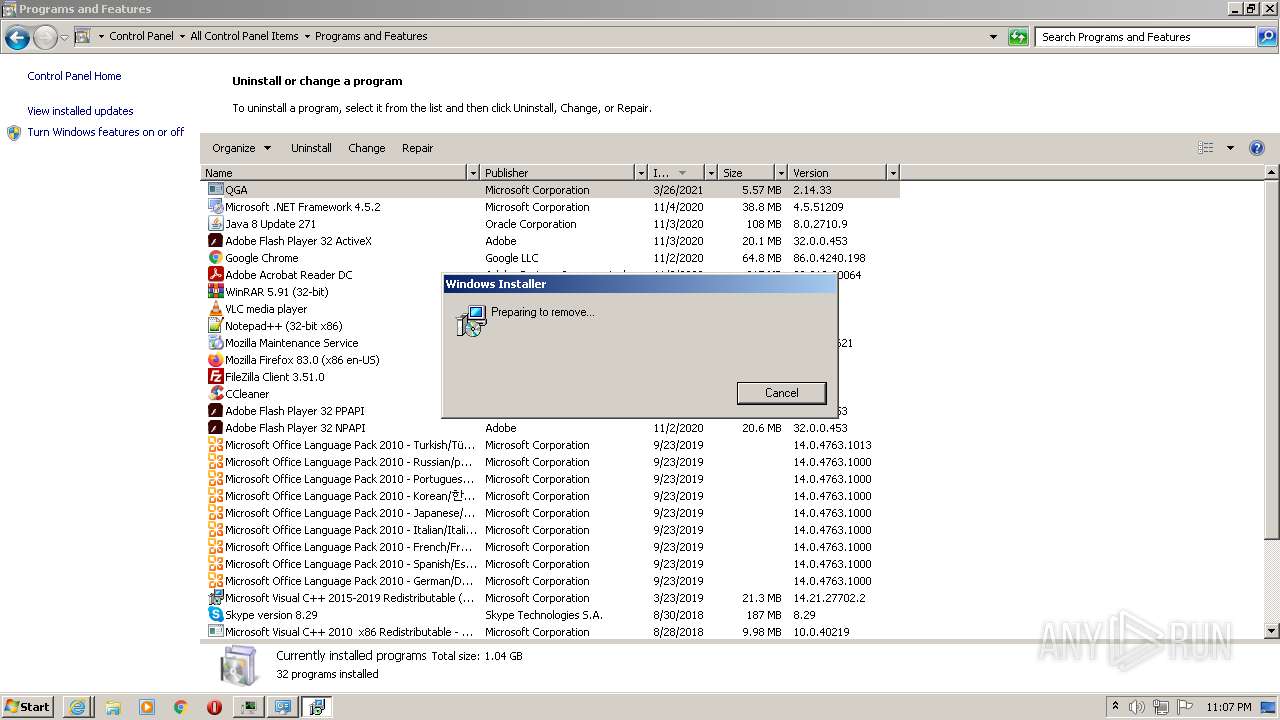
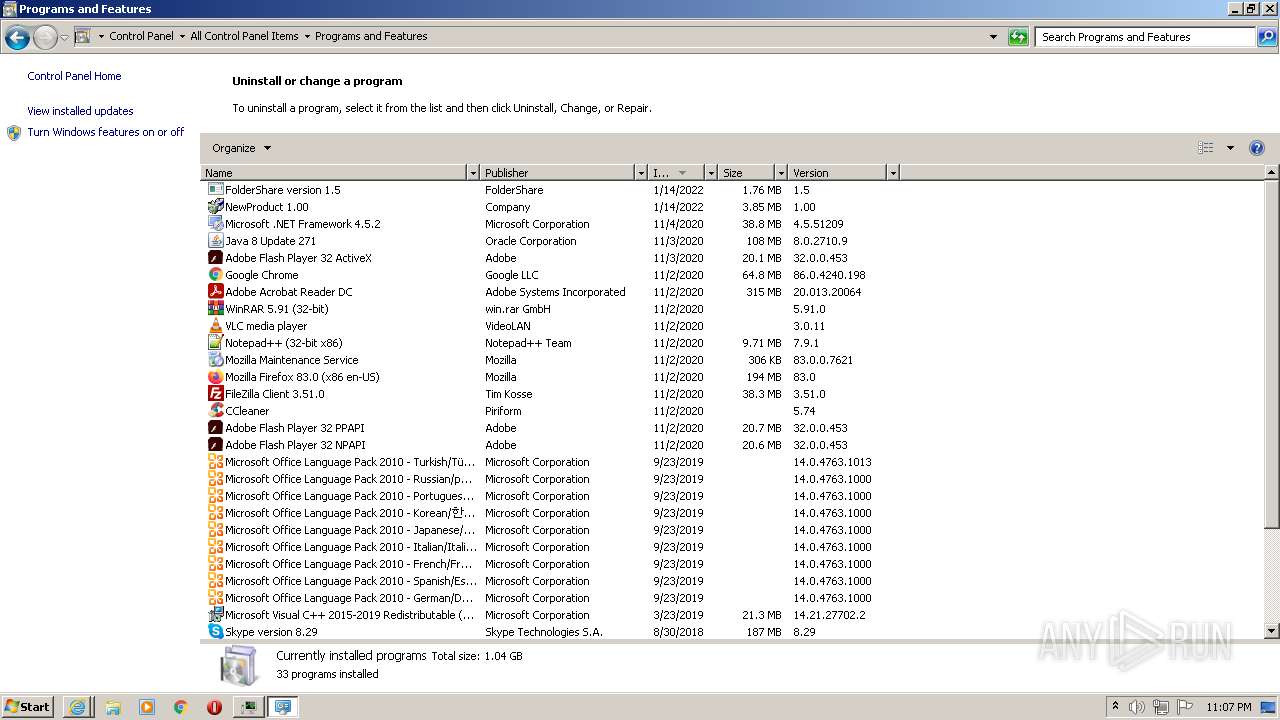
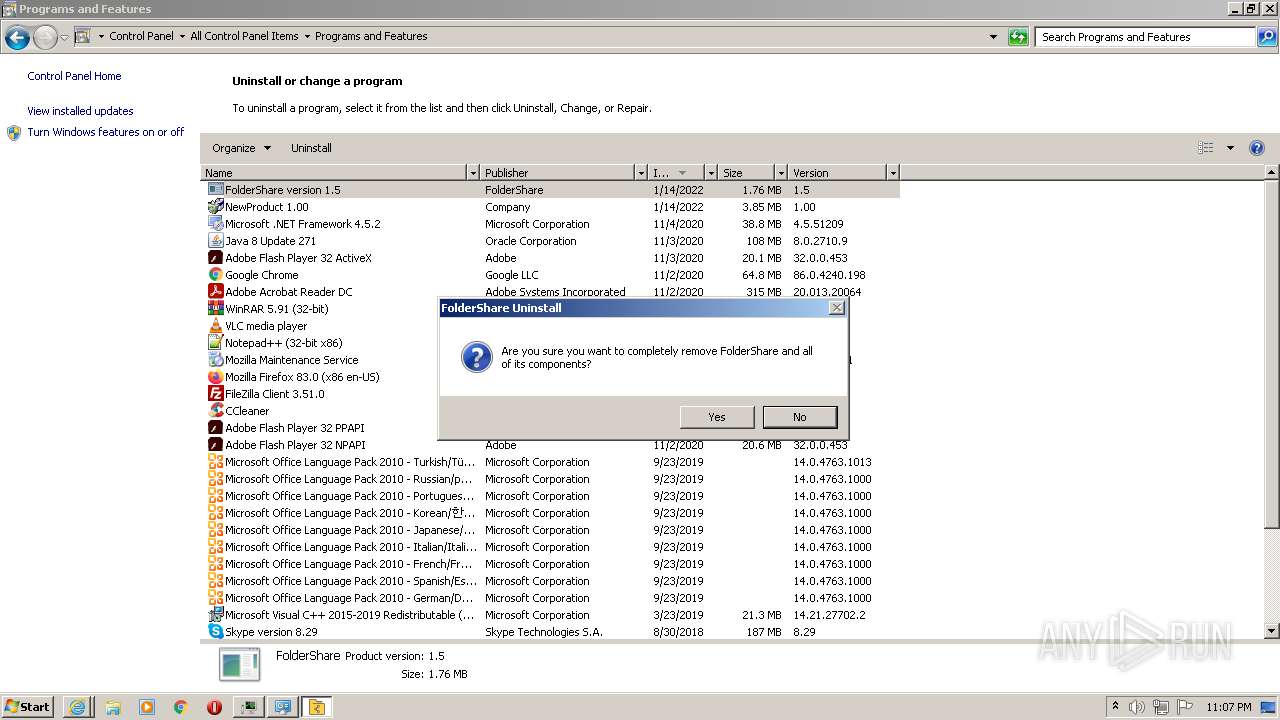
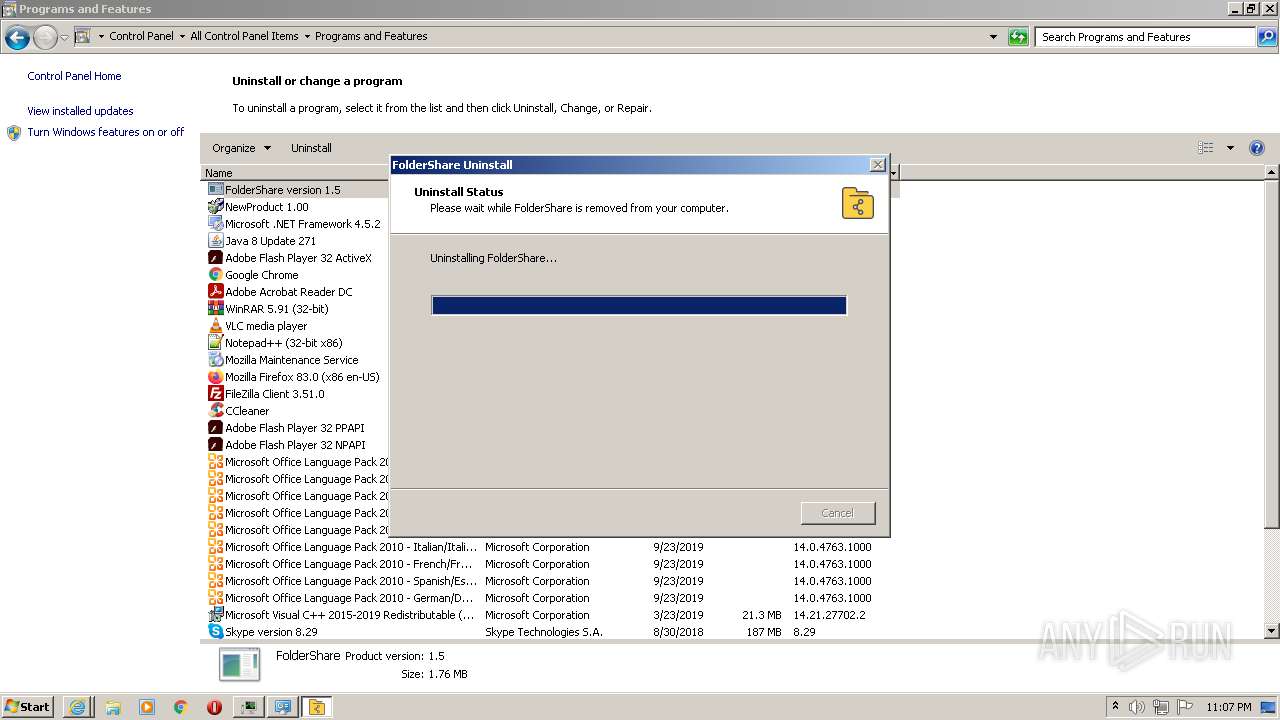
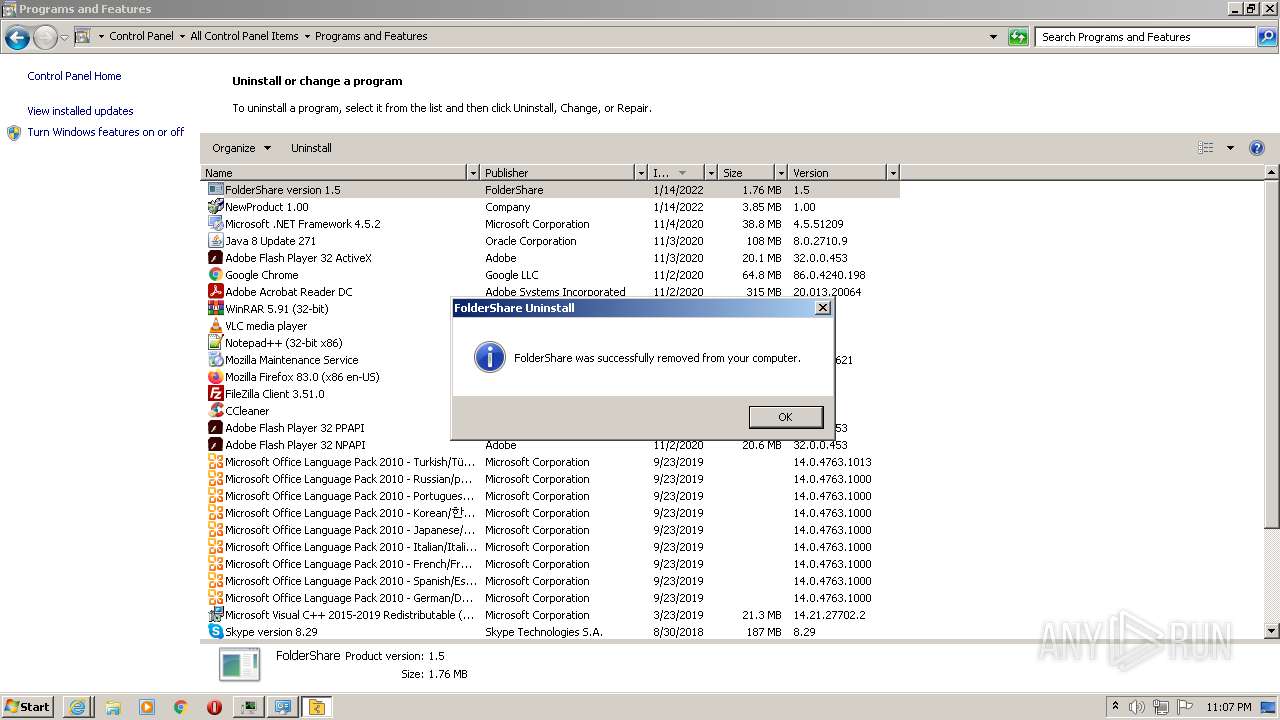
Creates a software uninstall entry
- jZR4CnxOPLtgsLUr86lbO5IW.exe (PID: 2144)
- 8oInWBwPiVaPPO3O1QxcHTRe.exe (PID: 2212)
- Roads License Agreement.exe (PID: 2632)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 2632)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3556)
- cmd.exe (PID: 2108)
Executed via WMI
- rundll32.exe (PID: 576)
Starts itself from another location
- mJvXRf_FxI_P9pEThrtt6Qsw.exe (PID: 2544)
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- unins000.exe (PID: 1980)
- Uninstall.exe (PID: 480)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3756)
- cmd.exe (PID: 2052)
Executes PowerShell scripts
- 2_PxP5Po7eELeS6U3w4rJGyd.exe (PID: 924)
- images.exe (PID: 1112)
Executed as Windows Service
- msiexec.exe (PID: 1160)
- vssvc.exe (PID: 796)
- msiexec.exe (PID: 3824)
Reads the date of Windows installation
- _iu14D2N.tmp (PID: 576)
Starts application with an unusual extension
- unins000.exe (PID: 1980)
Removes files from Windows directory
- Setup.exe (PID: 4052)
- mscorsvw.exe (PID: 2772)
- mscorsvw.exe (PID: 3548)
- mscorsvw.exe (PID: 2632)
- mscorsvw.exe (PID: 1152)
- mscorsvw.exe (PID: 756)
- mscorsvw.exe (PID: 1368)
- mscorsvw.exe (PID: 3012)
- mscorsvw.exe (PID: 348)
- mscorsvw.exe (PID: 3776)
- mscorsvw.exe (PID: 2384)
- mscorsvw.exe (PID: 3728)
- mscorsvw.exe (PID: 388)
- mscorsvw.exe (PID: 3732)
- mscorsvw.exe (PID: 1808)
- mscorsvw.exe (PID: 1996)
- mscorsvw.exe (PID: 3776)
- mscorsvw.exe (PID: 1036)
- mscorsvw.exe (PID: 344)
- mscorsvw.exe (PID: 4064)
Reads default file associations for system extensions
- Explorer.EXE (PID: 740)
INFO
Reads the computer name
- taskmgr.exe (PID: 4084)
- DllHost.exe (PID: 2788)
- useraccountcontrolsettings.exe (PID: 2768)
- DllHost.exe (PID: 2280)
- schtasks.exe (PID: 2772)
- schtasks.exe (PID: 2080)
- PING.EXE (PID: 2896)
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 2996)
- taskkill.exe (PID: 4032)
- rundll32.exe (PID: 576)
- taskkill.exe (PID: 1400)
- iexplore.exe (PID: 460)
- iexplore.exe (PID: 3092)
- msiexec.exe (PID: 1160)
- vssvc.exe (PID: 796)
- DllHost.exe (PID: 3912)
- msiexec.exe (PID: 3824)
- MsiExec.exe (PID: 3384)
- iexplore.exe (PID: 3320)
- iexplore.exe (PID: 2632)
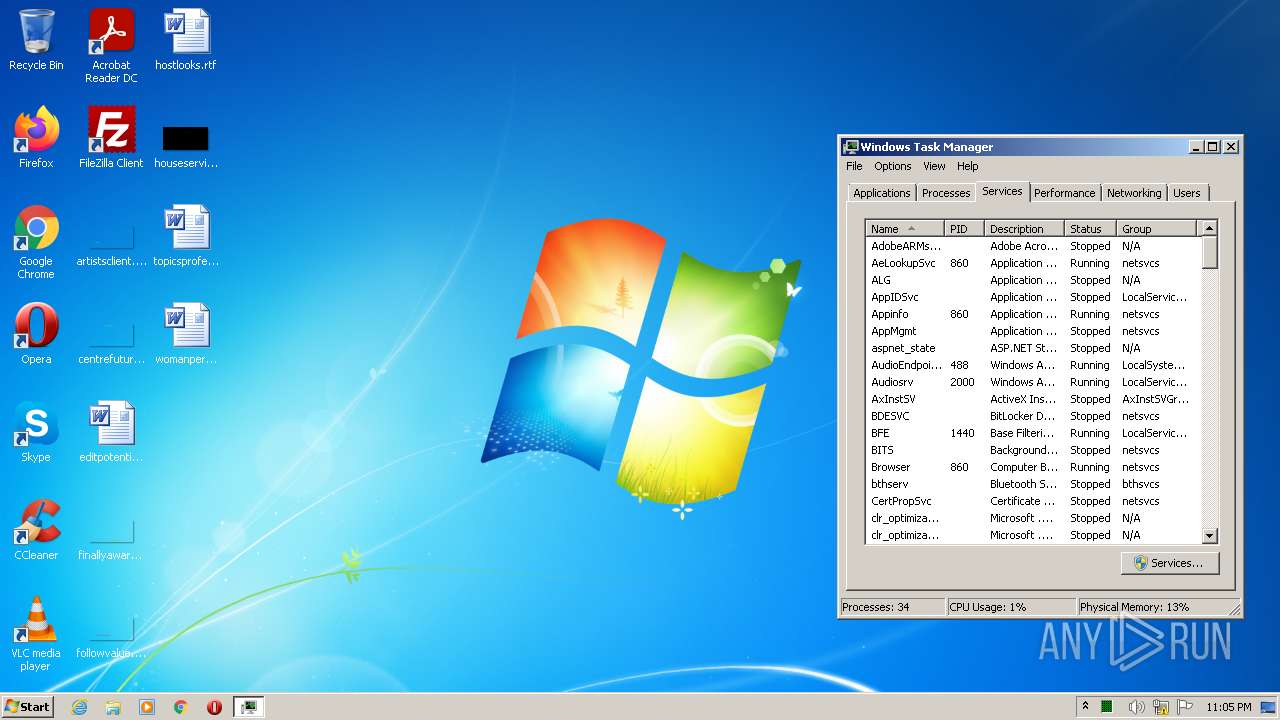
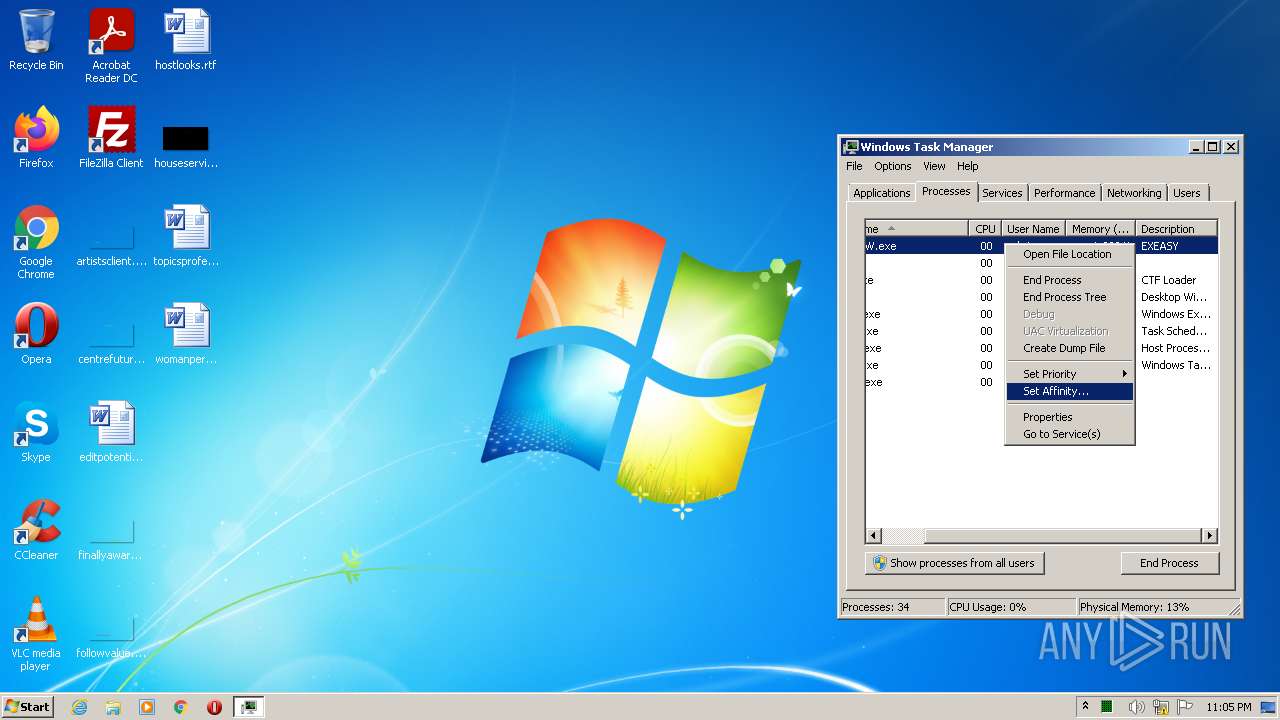
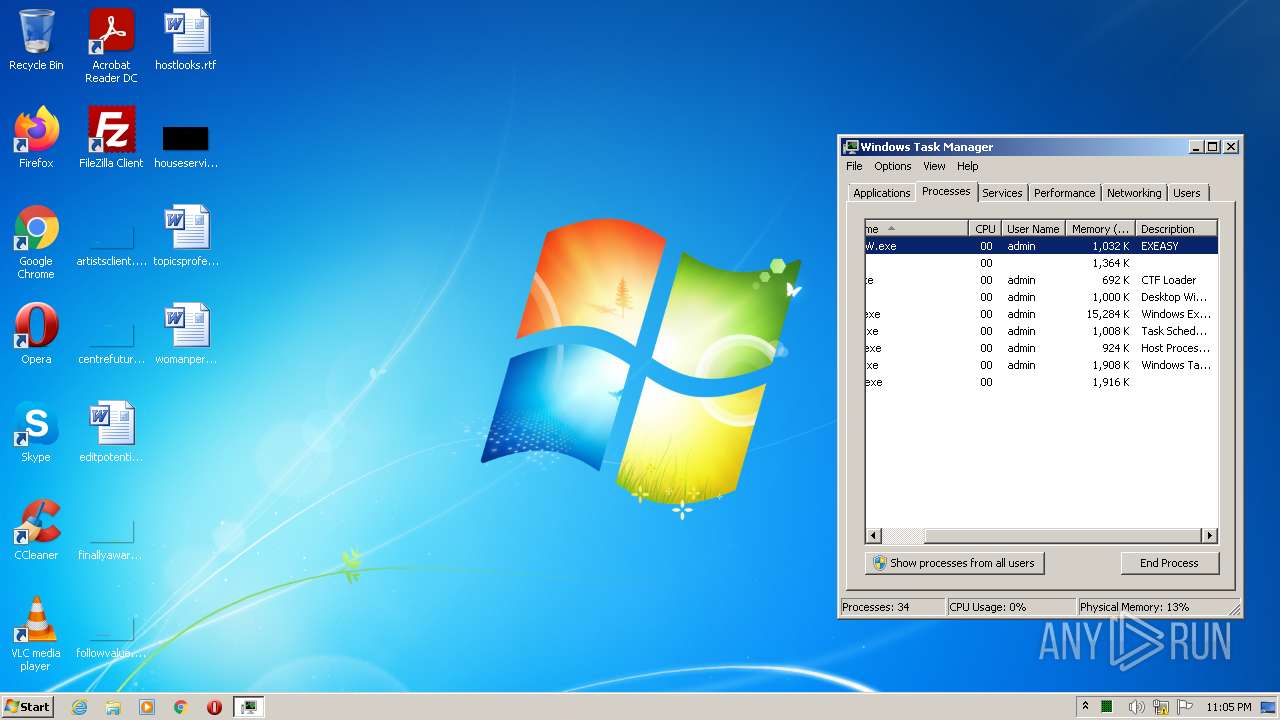
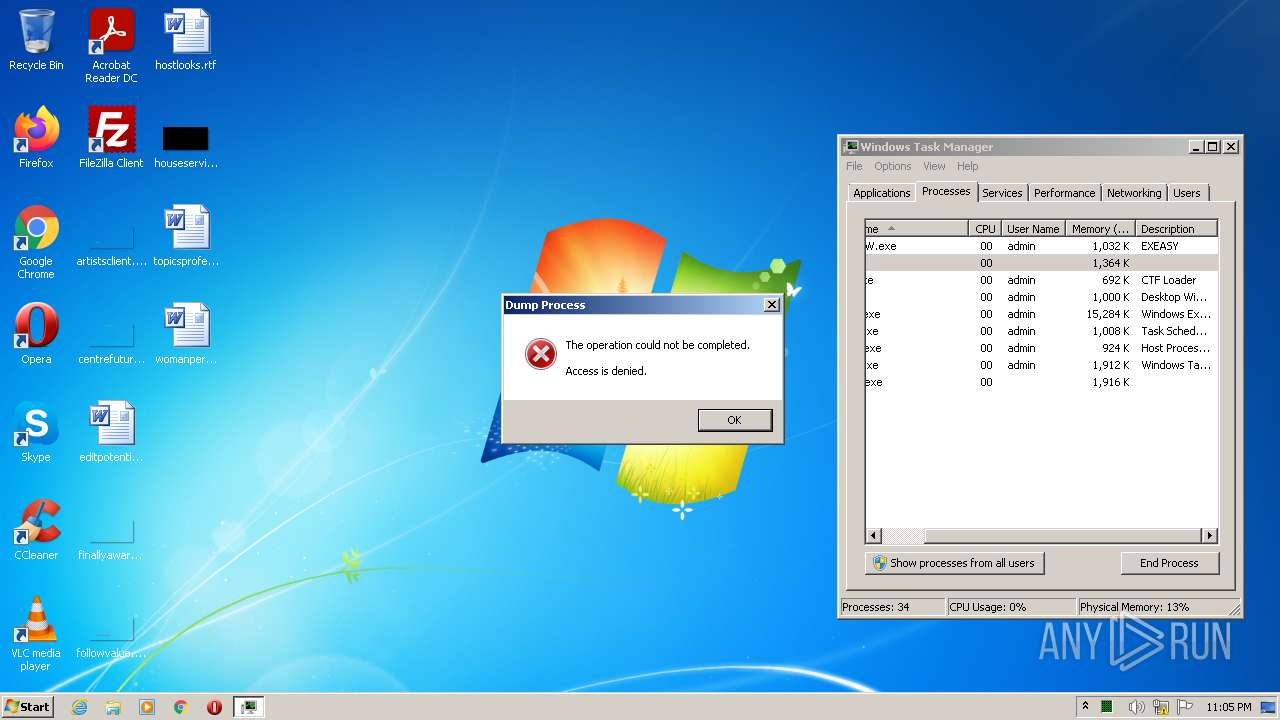
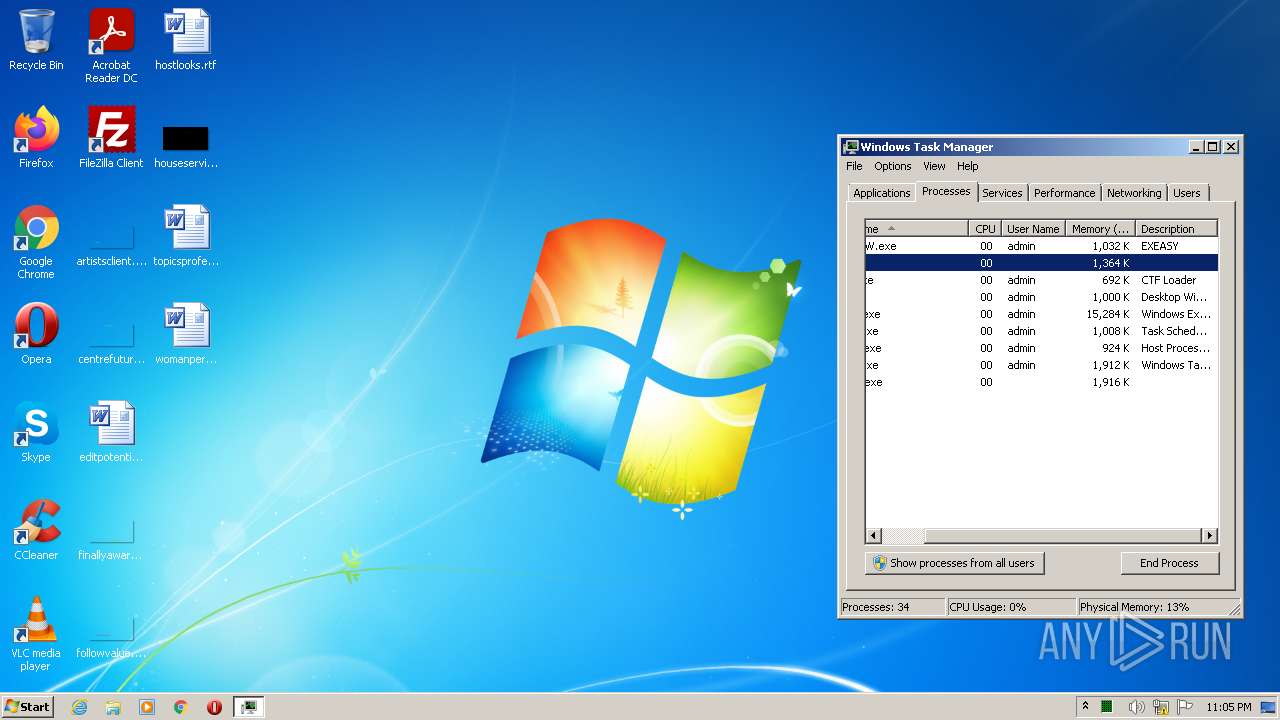
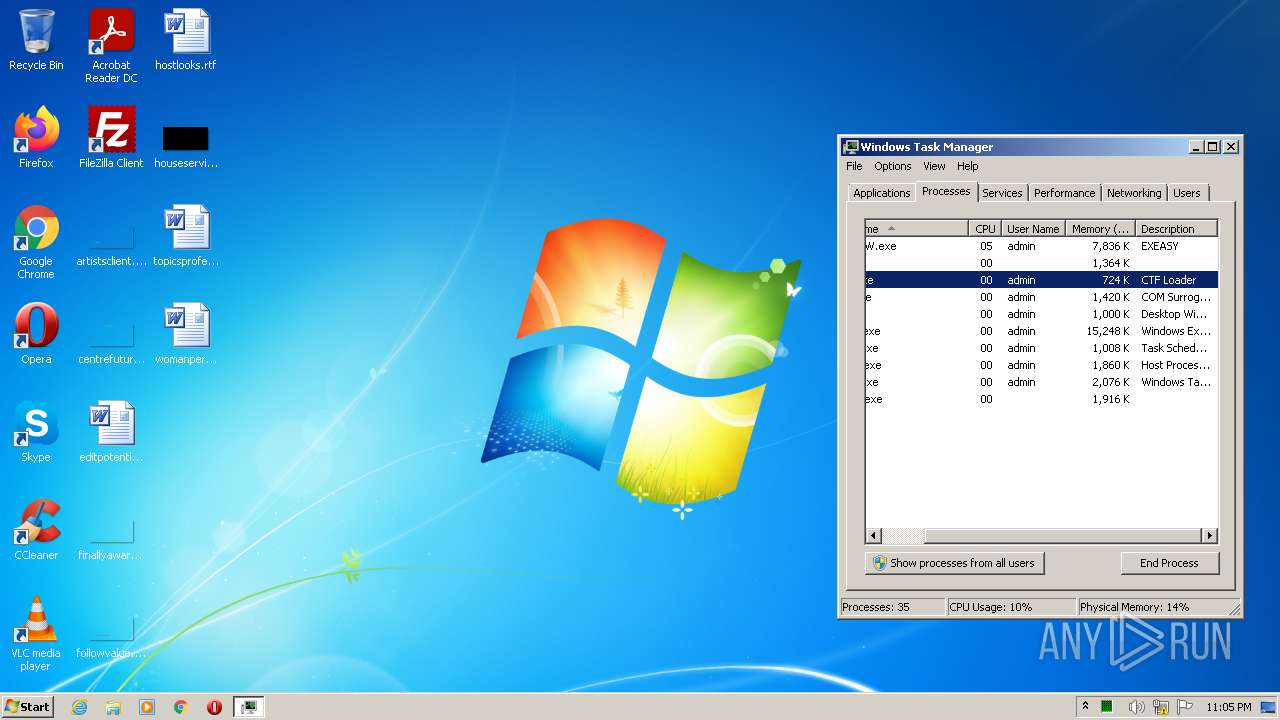
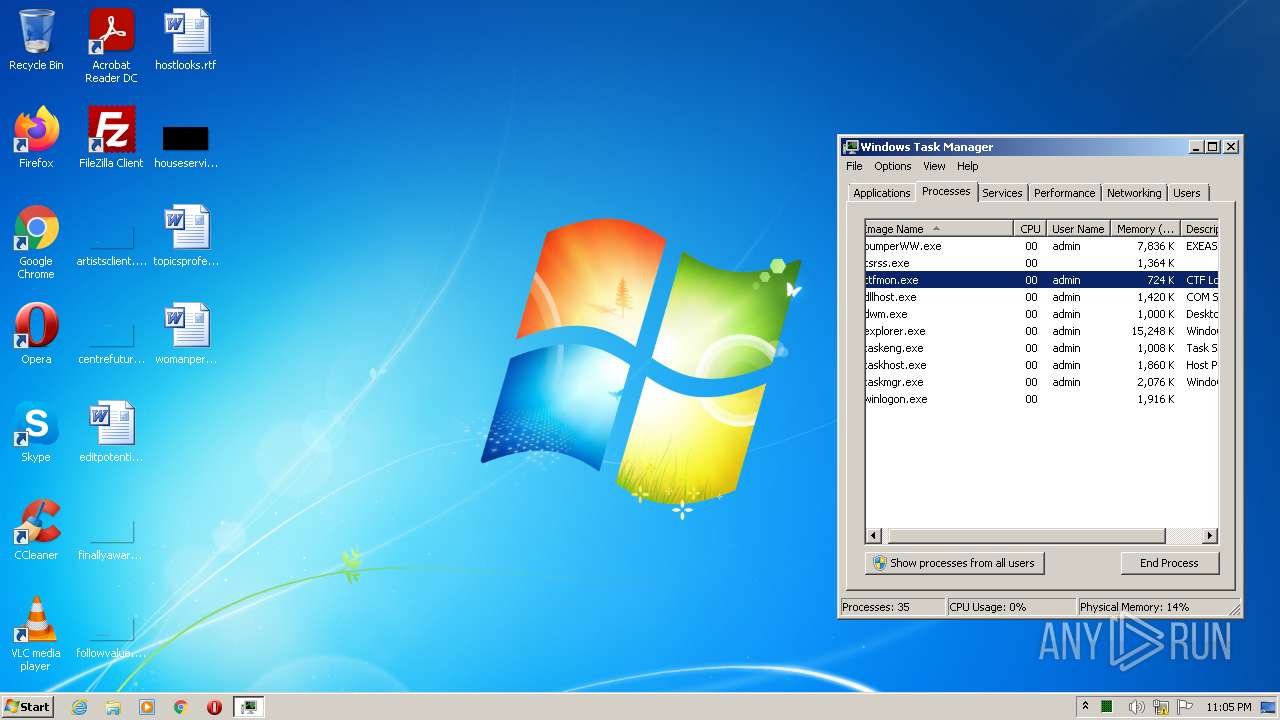
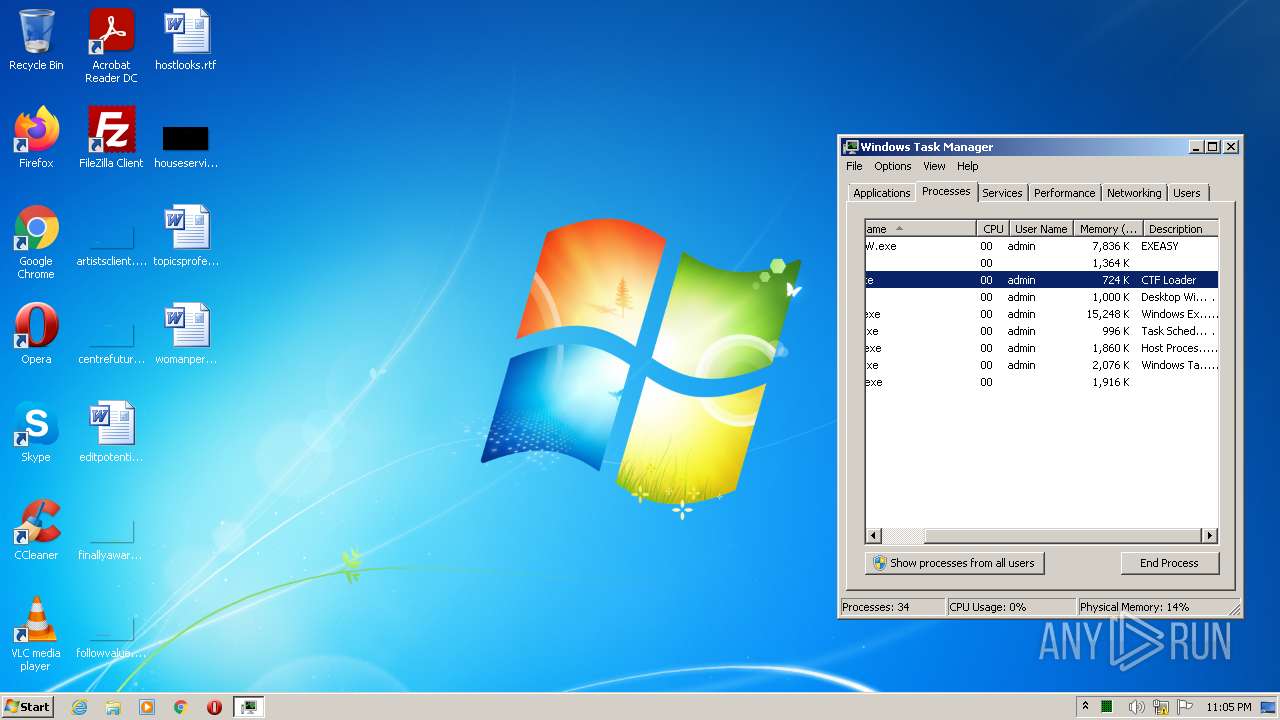
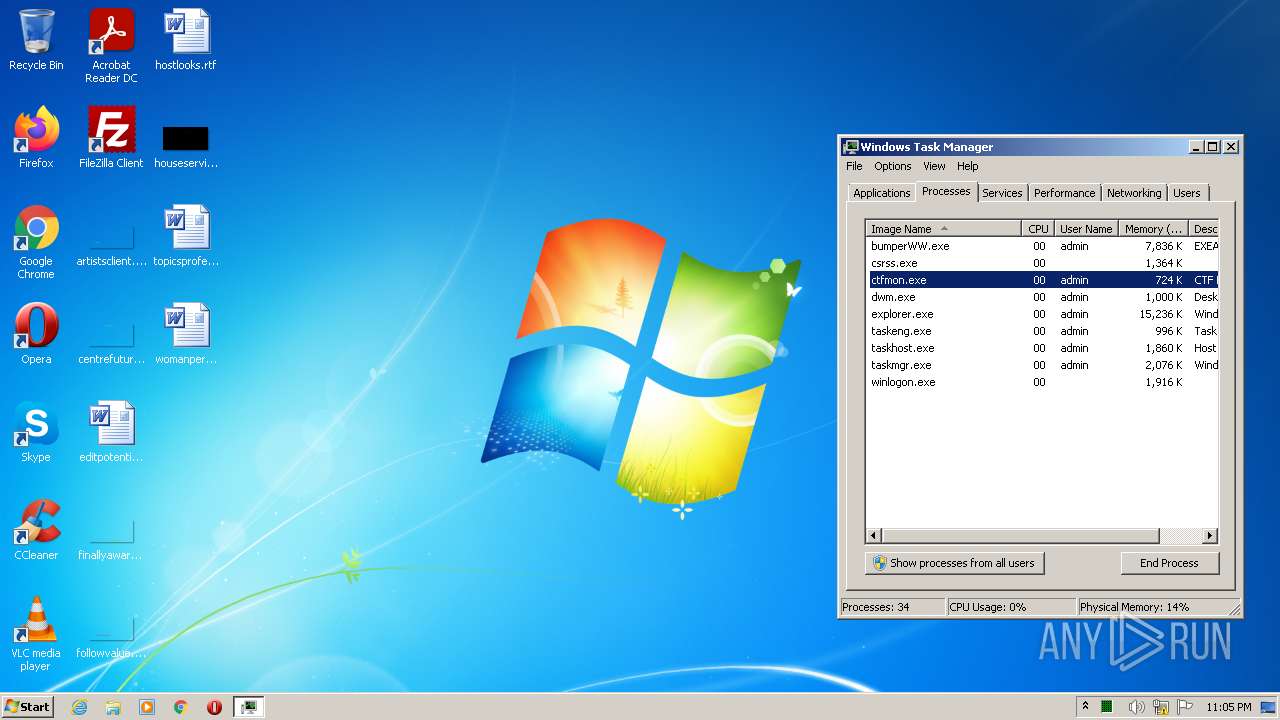
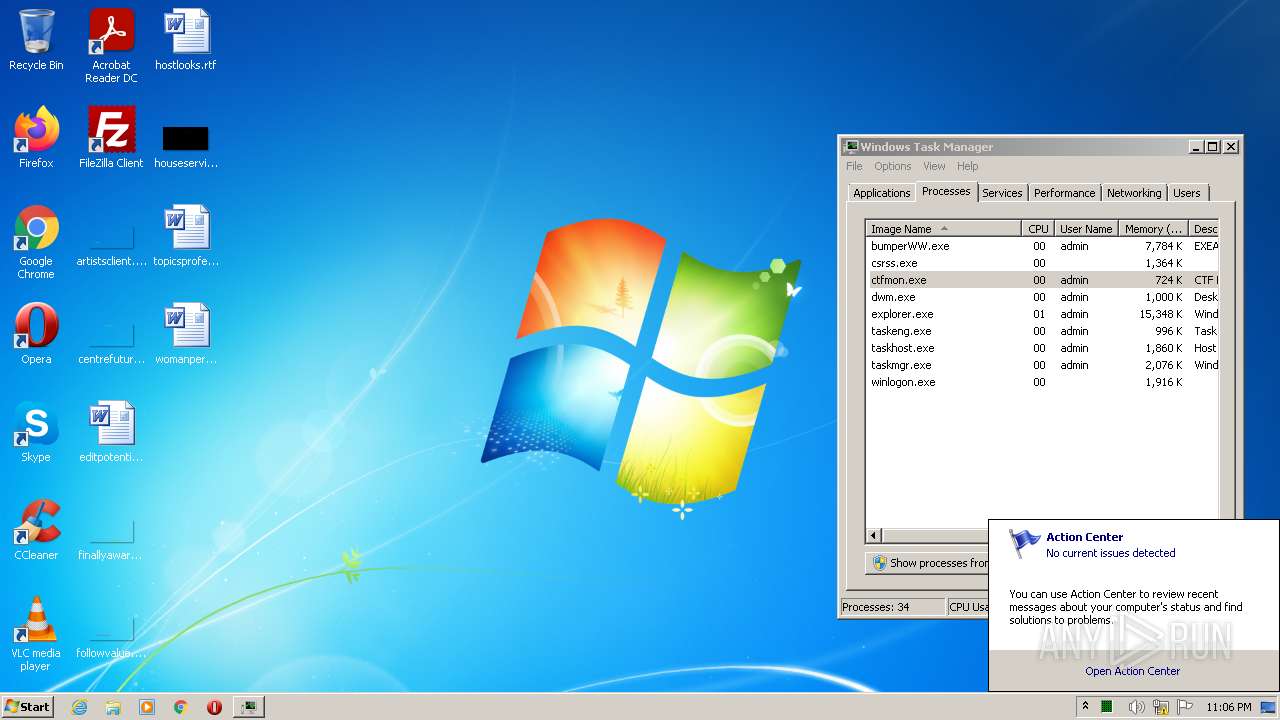
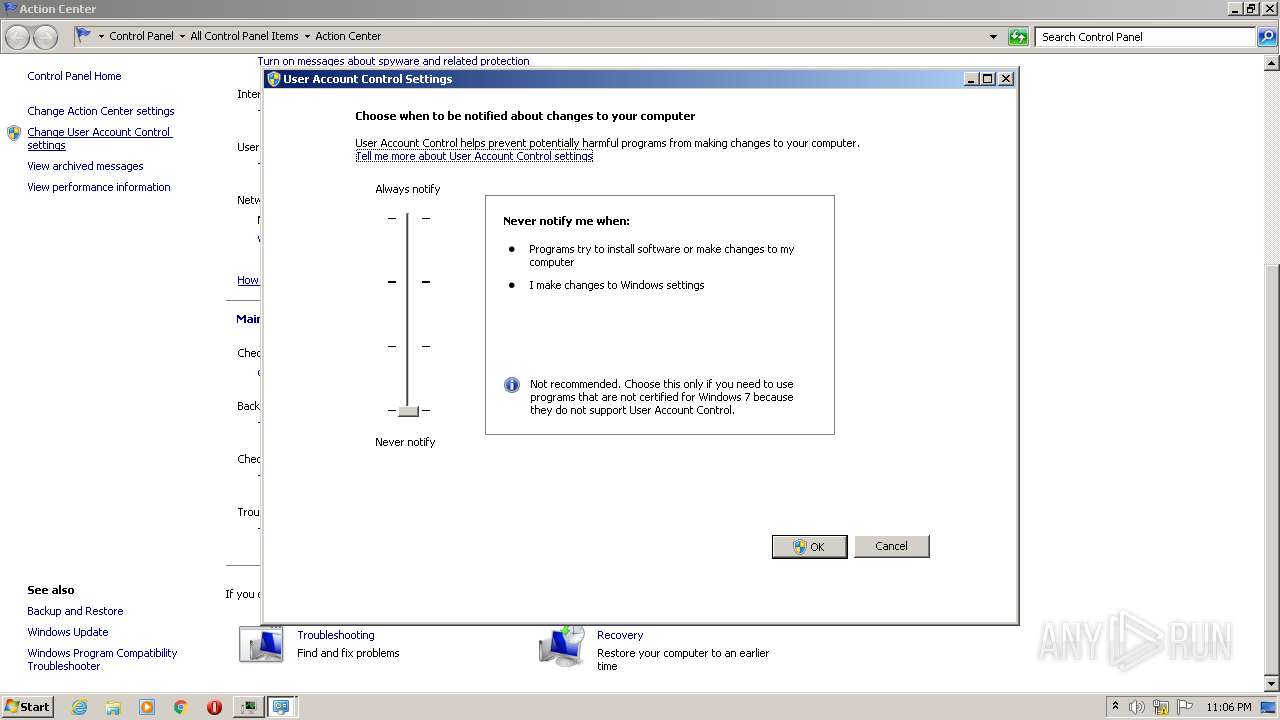
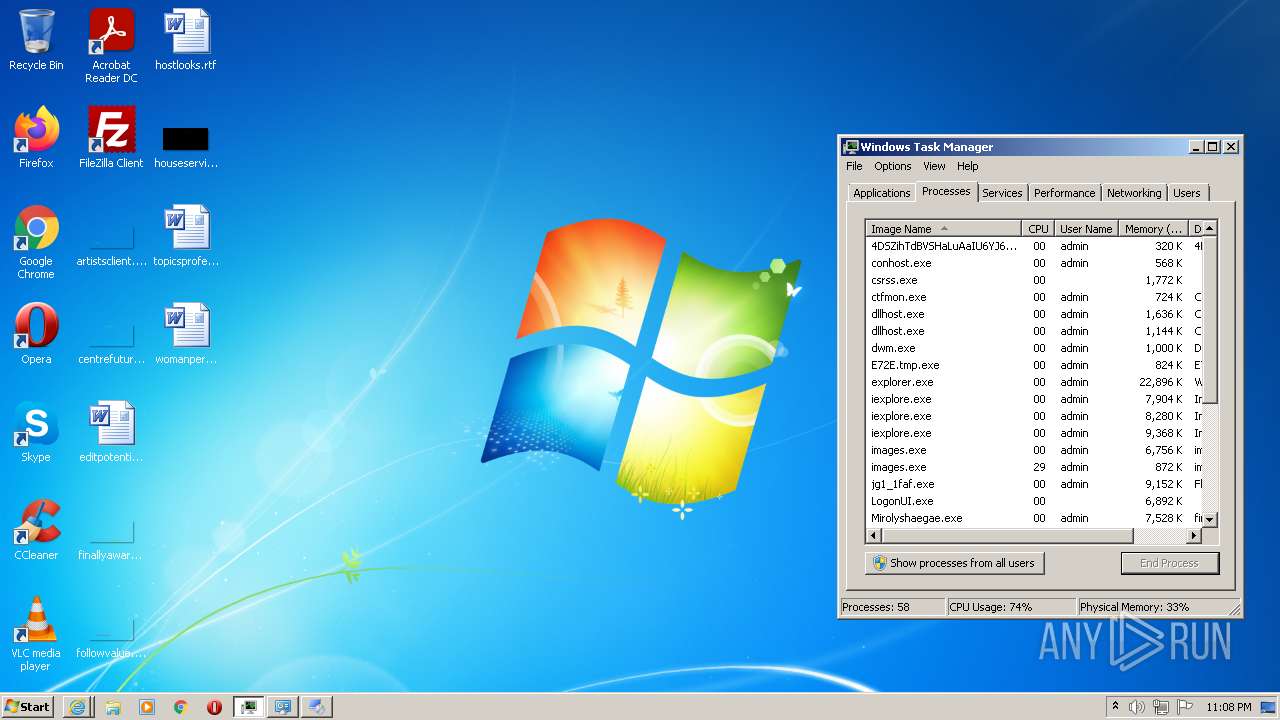
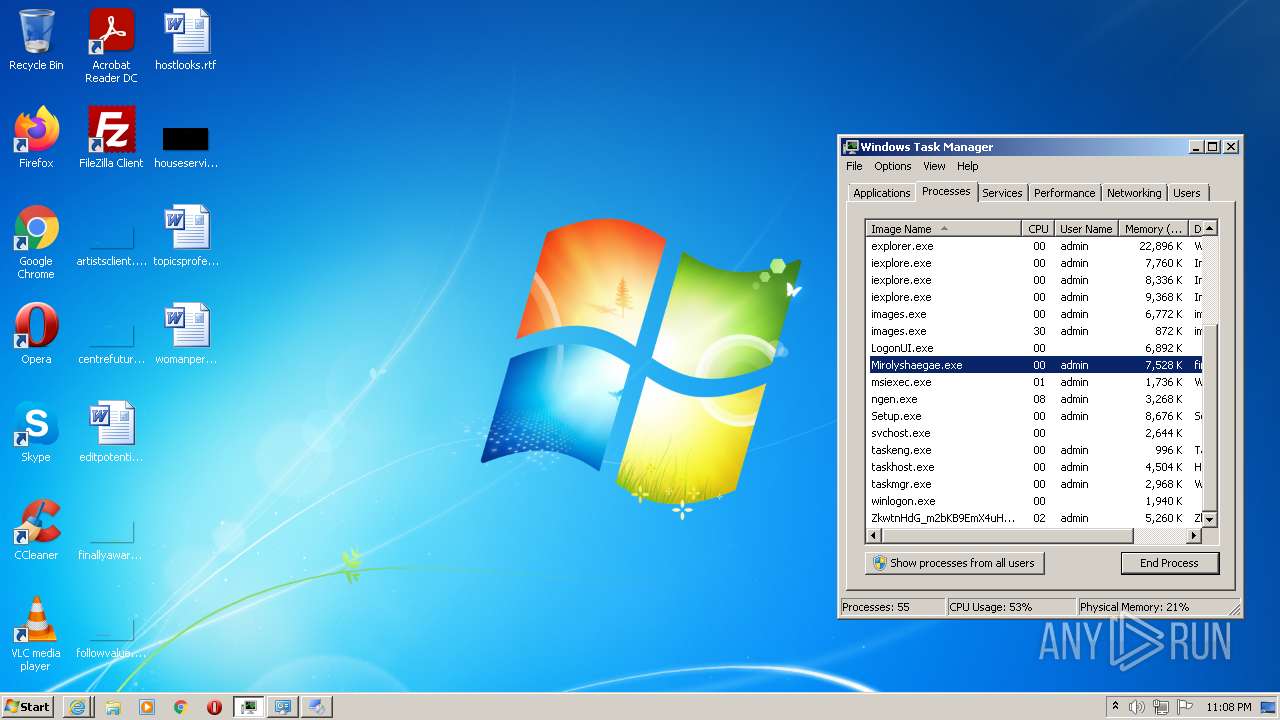
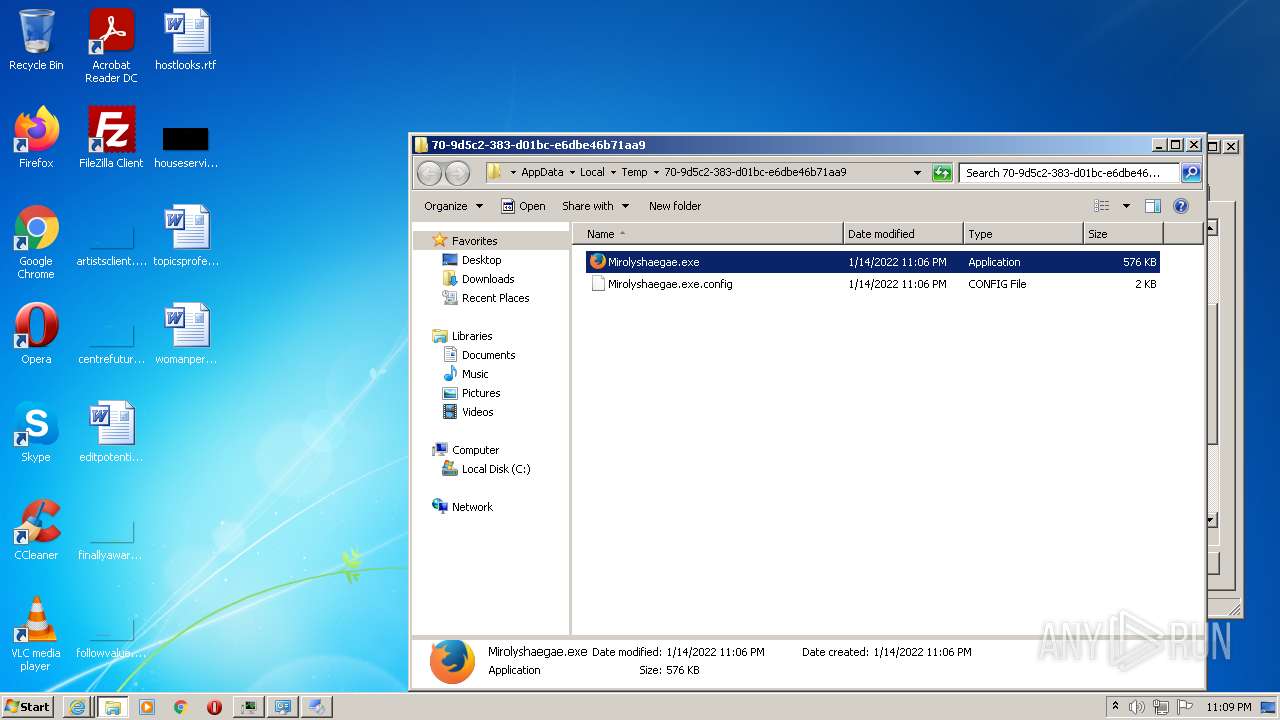
Manual execution by user
- taskmgr.exe (PID: 4084)
- useraccountcontrolsettings.exe (PID: 2768)
- images.exe (PID: 3152)
- Mirolyshaegae.exe (PID: 2732)
- Mirolyshaegae.exe (PID: 2880)
- Mirolyshaegae.exe (PID: 1284)
- Mirolyshaegae.exe (PID: 1948)
Reads settings of System Certificates
- bumperWW.exe (PID: 2064)
- C_IfcOV7u4j9fJtBk9dMyFqp.exe (PID: 3256)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- OCQdLemAUMV8IhUYlZQJtgRq.exe (PID: 2936)
- PINrdcDrNXUBZLBByZddkwyU.exe (PID: 388)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- dvCIXeFWAxxZdjQybMw0J__Z.exe (PID: 3696)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- a61196d6-e70d-4483-8980-680a8865a89d.exe (PID: 3136)
- 732ebb93-31fe-4cc9-99d9-1f8e9b48e656.exe (PID: 3536)
- ________djskjT76(((.exe (PID: 3732)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- d91957bf-10f3-4ccc-954b-9076e9c8bd23.exe (PID: 3676)
- 7a1181d2-6a43-4018-9d76-98be79e19ce1.exe (PID: 3204)
- cd203ebd-200a-40f9-9e6a-803d7b729eab.exe (PID: 2696)
- b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe (PID: 3052)
- Mirolyshaegae.exe (PID: 4004)
- Deqytihetu.exe (PID: 3256)
- 77d23f8a-1107-4bd5-a674-adeebfbd6dc7.exe (PID: 3852)
- 47d5bb8d-60ef-4a3e-a2d6-ecba2d47aa50.exe (PID: 4068)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3416)
- E373ZrEPGGDSsKCNPm6iQGpB.exe (PID: 3924)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- ________djskjT76(((.exe (PID: 2032)
- Sybevyqebu.exe (PID: 2848)
- iexplore.exe (PID: 3092)
- Bydaqusyry.exe (PID: 2784)
- powershell.exe (PID: 3696)
- AppLaunch.exe (PID: 3400)
- AppLaunch.exe (PID: 3720)
- Setup.exe (PID: 4052)
- powershell.exe (PID: 1284)
- Roads License Agreement.exe (PID: 2632)
- Mirolyshaegae.exe (PID: 2732)
- iexplore.exe (PID: 2632)
- Mirolyshaegae.exe (PID: 2880)
Checks supported languages
- taskmgr.exe (PID: 4084)
- useraccountcontrolsettings.exe (PID: 2768)
- DllHost.exe (PID: 2280)
- DllHost.exe (PID: 2788)
- msiexec.exe (PID: 2320)
- schtasks.exe (PID: 2080)
- schtasks.exe (PID: 2772)
- svchost.exe (PID: 860)
- PING.EXE (PID: 2896)
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 2996)
- taskkill.exe (PID: 4032)
- timeout.exe (PID: 2176)
- msiexec.exe (PID: 1208)
- msiexec.exe (PID: 2740)
- rundll32.exe (PID: 576)
- taskkill.exe (PID: 1400)
- forfiles.exe (PID: 376)
- iexplore.exe (PID: 460)
- reg.exe (PID: 3824)
- forfiles.exe (PID: 3052)
- cmd.exe (PID: 2052)
- timeout.exe (PID: 1460)
- reg.exe (PID: 1876)
- cmd.exe (PID: 3756)
- iexplore.exe (PID: 3092)
- vssvc.exe (PID: 796)
- msiexec.exe (PID: 1160)
- DllHost.exe (PID: 3912)
- msiexec.exe (PID: 3824)
- MsiExec.exe (PID: 3384)
- timeout.exe (PID: 3376)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 3320)
Checks Windows Trust Settings
- bumperWW.exe (PID: 2064)
- xzN5GaKjoNlrwtkK68rT1IuA.exe (PID: 2880)
- maVnjPsGsZsopLBDjlnzkr0d.exe (PID: 2280)
- XNbfASHhKuIBxGbm5PCcWw4m.exe (PID: 3856)
- dvCIXeFWAxxZdjQybMw0J__Z.exe (PID: 3696)
- g5AHqWG9N4mPsRjfElKIuyl2.exe (PID: 2224)
- 3TwFEEbWDEJrk8678_IZdcIG.exe (PID: 1112)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3416)
- admwU3xIo3TJWsla8ABt4zxu.exe (PID: 1972)
- iexplore.exe (PID: 3092)
- powershell.exe (PID: 3696)
- Setup.exe (PID: 4052)
- powershell.exe (PID: 1284)
- Roads License Agreement.exe (PID: 2632)
- iexplore.exe (PID: 2632)
Application was dropped or rewritten from another process
- ________djskjT76(((.exe (PID: 3732)
- ________djskjT76(((.exe (PID: 2032)
Creates files in the program directory
- ________djskjT76(((.exe (PID: 3732)
- foldershare.tmp (PID: 2296)
- ________djskjT76(((.exe (PID: 2032)
- foldershare.tmp (PID: 2808)
Changes internet zones settings
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 3320)
Application launched itself
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 3320)
Creates files in the user directory
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 2632)
Reads internet explorer settings
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 2632)
Creates a software uninstall entry
- foldershare.tmp (PID: 2296)
- foldershare.tmp (PID: 2808)
Dropped object may contain Bitcoin addresses
- bumperWW.exe (PID: 2064)
Changes settings of System certificates
- iexplore.exe (PID: 3416)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
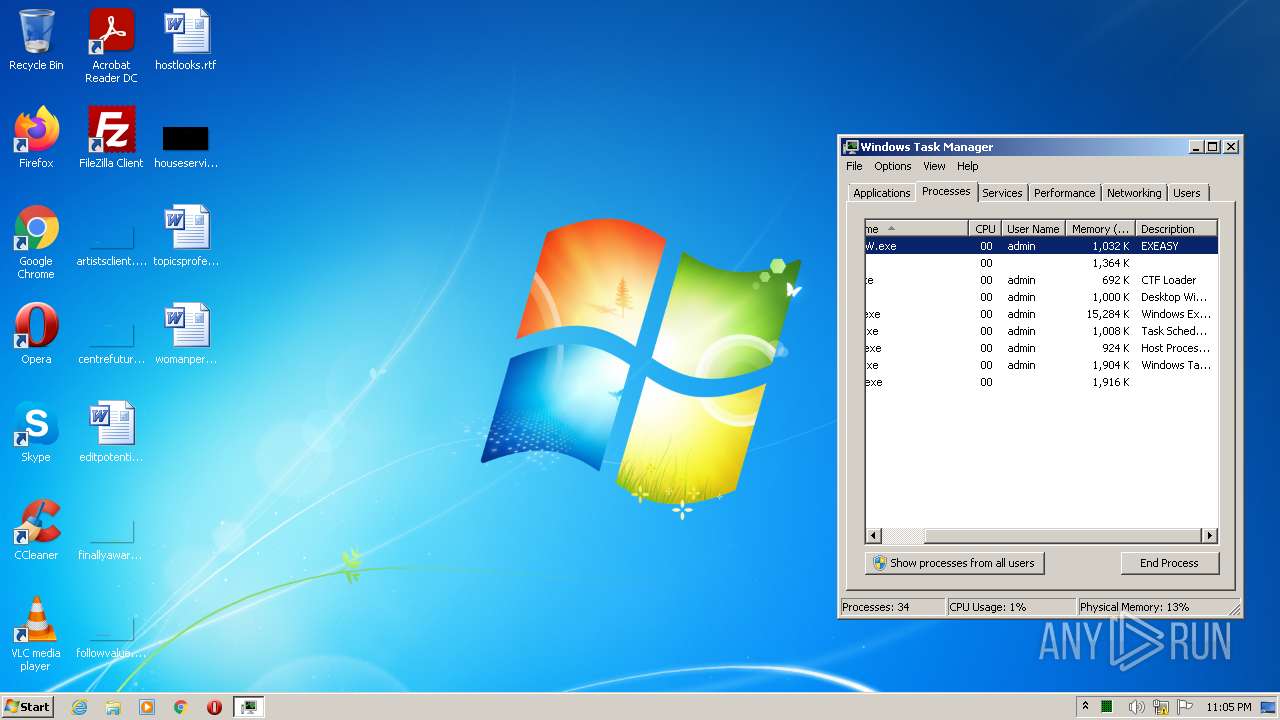
EXIF
EXE
| ProductVersion: | 25.15.2.5 |
|---|---|
| ProductName: | EXEASY |
| OriginalFileName: | EXEASY.exe |
| LegalCopyright: | Copyright (C) 2021 EXEASY |
| InternalName: | EXEASY.exe |
| FileVersion: | 25.15.2.5 |
| FileDescription: | EXEASY |
| CompanyName: | EXEASY |
| CharacterSet: | Unicode |
| LanguageCode: | Unknown (0006) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Unknown (0x50000) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 25.15.2.5 |
| FileVersionNumber: | 25.15.2.5 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x9770 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 325632 |
| CodeSize: | 89088 |
| LinkerVersion: | 14.25 |
| PEType: | PE32 |
| TimeStamp: | 2021:10:11 09:12:28+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Oct-2021 07:12:28 |
| Detected languages: |
|
| CompanyName: | EXEASY |
| FileDescription: | EXEASY |
| FileVersion: | 25.15.2.5 |
| InternalName: | EXEASY.exe |
| LegalCopyright: | Copyright (C) 2021 EXEASY |
| OriginalFilename: | EXEASY.exe |
| ProductName: | EXEASY |
| ProductVersion: | 25.15.2.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Oct-2021 07:12:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015B52 | 0x00015C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67754 |
.rdata | 0x00017000 | 0x00006A82 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.77858 |
.data | 0x0001E000 | 0x00001700 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.43746 |
.rsrc | 0x00020000 | 0x00045D88 | 0x00045E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.80308 |
.reloc | 0x00066000 | 0x00001470 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.39011 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.63378 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 0.777818 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 0.911008 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 0.983719 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 1.13797 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
124 | 6.22948 | 180224 | UNKNOWN | UNKNOWN | DLL |
Imports
KERNEL32.dll |
Total processes
464
Monitored processes
240
Malicious processes
63
Suspicious processes
118
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe uninstall "System.Transactions, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 284 | "C:\Users\admin\AppData\Roaming\4562707.exe" | C:\Users\admin\AppData\Roaming\4562707.exe | — | b697bc8a-f300-4ef2-87e7-cd7ff552a00f.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2147944514 Modules
| |||||||||||||||
| 284 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe uninstall "System.ServiceModel.Routing, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35" /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 308 | "C:\Users\admin\Pictures\Adobe Films\h1qn6mHjfy3ngUezI969Rxav.exe" | C:\Users\admin\Pictures\Adobe Films\h1qn6mHjfy3ngUezI969Rxav.exe | bumperWW.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 320 | #cmd | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | neRfUhqhUSljLEGIs9zyswBE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 344 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 118 -InterruptEvent 0 -NGENProcess 108 -Pipe 114 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 348 | "C:\Users\admin\Pictures\Adobe Films\DjexiyePQIlcETj_lvGPXqaZ.exe" | C:\Users\admin\Pictures\Adobe Films\DjexiyePQIlcETj_lvGPXqaZ.exe | bumperWW.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 348 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 118 -InterruptEvent 0 -NGENProcess 108 -Pipe 114 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 376 | "C:\Windows\System32\forfiles.exe" /p c:\windows\system32 /m cmd.exe /c "cmd /C REG ADD \"HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Extensions\" /f /v \"exe\" /t REG_SZ /d 0&" | C:\Windows\System32\forfiles.exe | — | Install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ForFiles - Executes a command on selected files Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | "C:\Users\admin\Pictures\Adobe Films\PINrdcDrNXUBZLBByZddkwyU.exe" | C:\Users\admin\Pictures\Adobe Films\PINrdcDrNXUBZLBByZddkwyU.exe | bumperWW.exe | ||||||||||||
User: admin Company: bgfdfgdf Integrity Level: HIGH Description: bgfdfgdf Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
556 750
Read events
515 037
Write events
37 039
Delete events
4 674
Modification events
| (PID) Process: | (740) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\gnfxzte.rkr |
Value: 00000000000000001A00000006690700000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (740) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000470100007B020000FF5A17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2064) bumperWW.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
277
Suspicious files
85
Text files
49
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
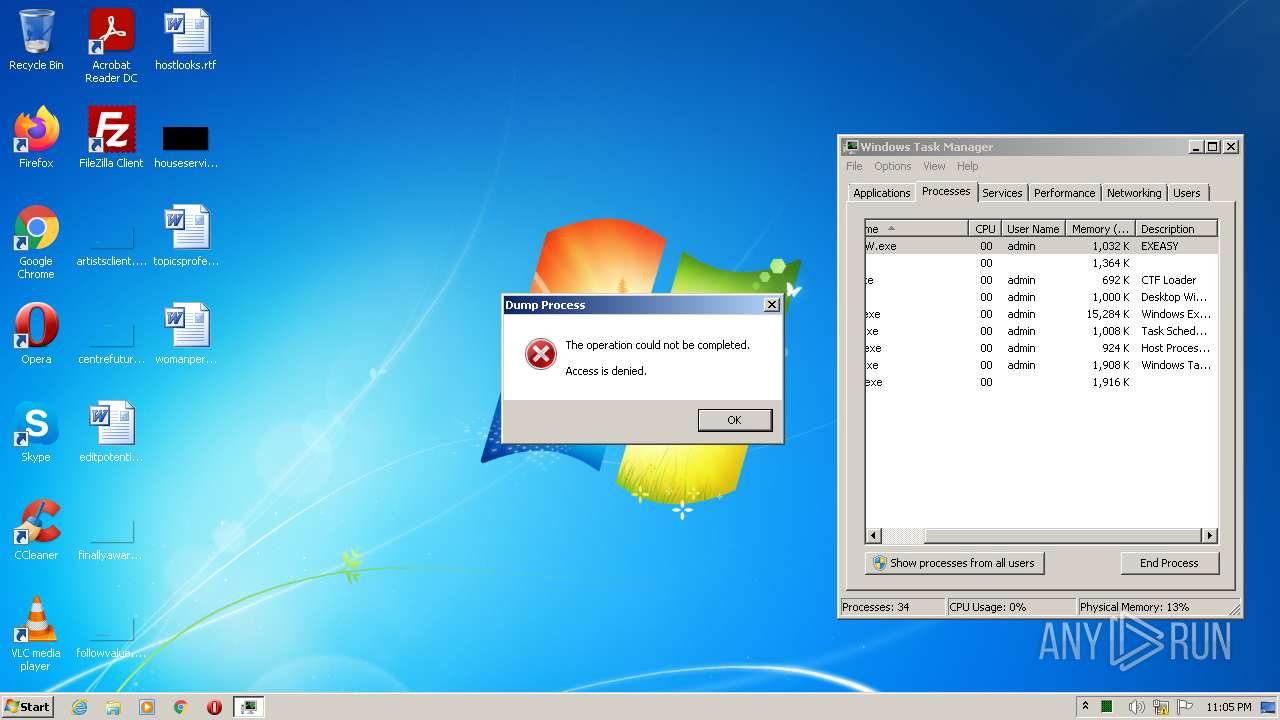
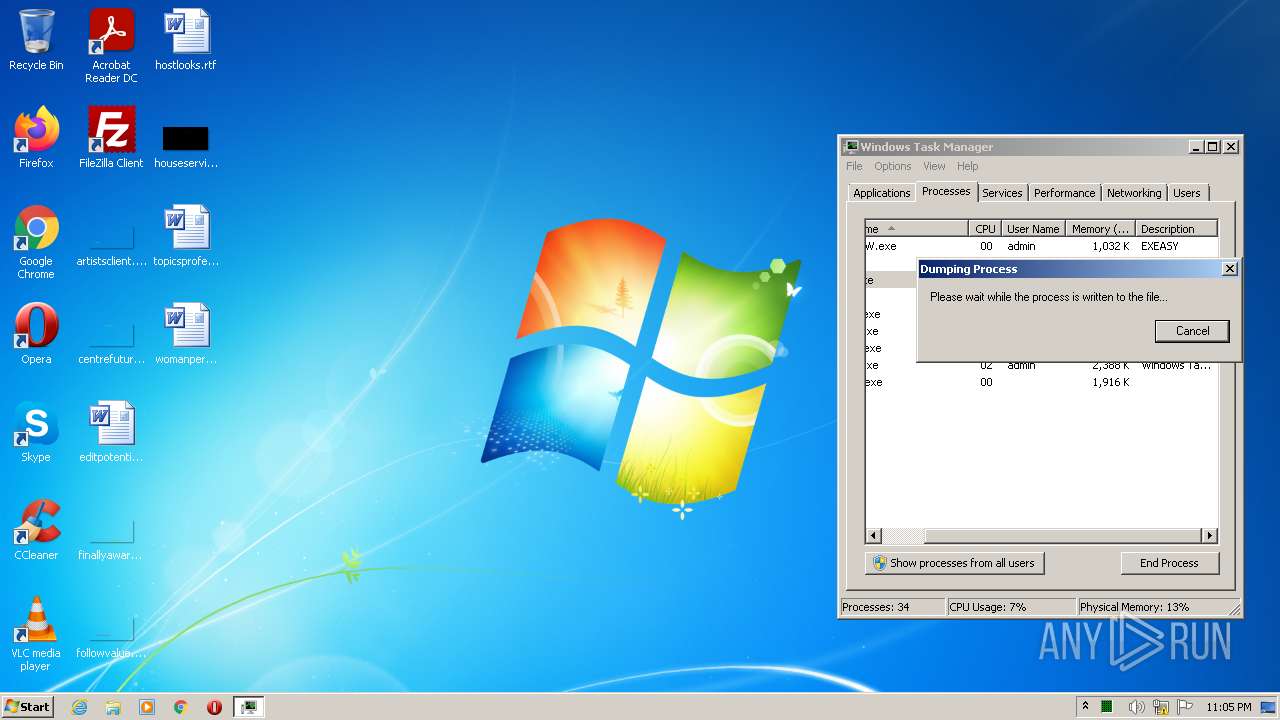
| 4084 | taskmgr.exe | C:\Users\admin\AppData\Local\Temp\ctfmon.DMP | — | |
MD5:— | SHA256:— | |||
| 2064 | bumperWW.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\PL_Client[1].bmp | binary | |
MD5:— | SHA256:— | |||
| 2064 | bumperWW.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\NiceProcessX32[1].bmp | executable | |
MD5:— | SHA256:— | |||
| 2064 | bumperWW.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2064 | bumperWW.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2064 | bumperWW.exe | C:\Users\admin\Pictures\Adobe Films\dfBUd0ZXWhP94QhuOO7HN8Dd.exe | executable | |
MD5:— | SHA256:— | |||
| 2064 | bumperWW.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 740 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\System and Security.lnk | lnk | |
MD5:F7193035ED26CB4312F50EF378674656 | SHA256:E76F96305B6195354B44214042C1EDEDF90D1246C06E7F28A3073C7E6FB3B771 | |||
| 740 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\7e4dca80246863e3.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3 846
TCP/UDP connections
4 022
DNS requests
120
Threats
564
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | bumperWW.exe | GET | — | 45.133.1.107:80 | http://45.133.1.107/server.txt | unknown | — | — | malicious |
2064 | bumperWW.exe | HEAD | 404 | 193.56.146.76:80 | http://193.56.146.76/Udp.exe | unknown | — | — | malicious |
2064 | bumperWW.exe | HEAD | 404 | 45.144.225.57:80 | http://45.144.225.57/WW/sfx_123_310.exe | unknown | — | — | malicious |
2064 | bumperWW.exe | HEAD | 200 | 45.144.225.57:80 | http://45.144.225.57/download/NiceProcessX32.bmp | unknown | — | — | malicious |
2064 | bumperWW.exe | HEAD | 200 | 45.144.225.57:80 | http://45.144.225.57/EU/searchEUunlim.exe | unknown | — | — | malicious |
2064 | bumperWW.exe | HEAD | 404 | 212.193.30.45:80 | http://212.193.30.45/WW/file8.exe | RU | — | — | malicious |
2064 | bumperWW.exe | HEAD | 200 | 85.209.157.230:80 | http://stylesheet.faseaegasdfase.com/hp8/g1/rtst1053.exe | unknown | — | — | malicious |
2064 | bumperWW.exe | HEAD | 404 | 212.193.30.29:80 | http://212.193.30.29/WW/file2.exe | RU | — | — | malicious |
2064 | bumperWW.exe | HEAD | 200 | 212.193.30.29:80 | http://212.193.30.29/download/Service.bmp | RU | — | — | malicious |
2064 | bumperWW.exe | HEAD | 200 | 193.56.146.76:80 | http://193.56.146.76/Proxypub.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | bumperWW.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2064 | bumperWW.exe | 45.133.1.107:80 | — | — | — | malicious |
2064 | bumperWW.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
2064 | bumperWW.exe | 2.56.59.42:80 | — | — | — | malicious |
2064 | bumperWW.exe | 185.215.113.208:80 | — | Ebonyhorizon Telecomunicacoes S.A. | PT | malicious |
2064 | bumperWW.exe | 34.117.59.81:443 | ipinfo.io | — | US | whitelisted |
2064 | bumperWW.exe | 193.56.146.76:80 | — | — | — | malicious |
2064 | bumperWW.exe | 212.193.30.45:80 | — | — | RU | malicious |
2064 | bumperWW.exe | 212.193.30.29:80 | — | — | RU | malicious |
2064 | bumperWW.exe | 188.165.5.107:80 | innovicservice.net | OVH SAS | IE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
cdn.discordapp.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ipinfo.io |
| shared |
db-ip.com |
| whitelisted |
api.db-ip.com |
| shared |
xmtbsj.com |
| suspicious |
tg8.cllgxx.com |
| malicious |
stylesheet.faseaegasdfase.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2064 | bumperWW.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2064 | bumperWW.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
2064 | bumperWW.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
2064 | bumperWW.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2064 | bumperWW.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2064 | bumperWW.exe | A Network Trojan was detected | ET TROJAN Win32/Unk.HRESQ! MultiDownloader Checkin |
2064 | bumperWW.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2064 | bumperWW.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2064 | bumperWW.exe | A Network Trojan was detected | AV POLICY EXE or DLL in HTTP Image Content Inbound - Likely Malicious |
2064 | bumperWW.exe | A Network Trojan was detected | ET TROJAN Win32/Unk.HRESQ! MultiDownloader Checkin |
326 ETPRO signatures available at the full report
Process | Message |
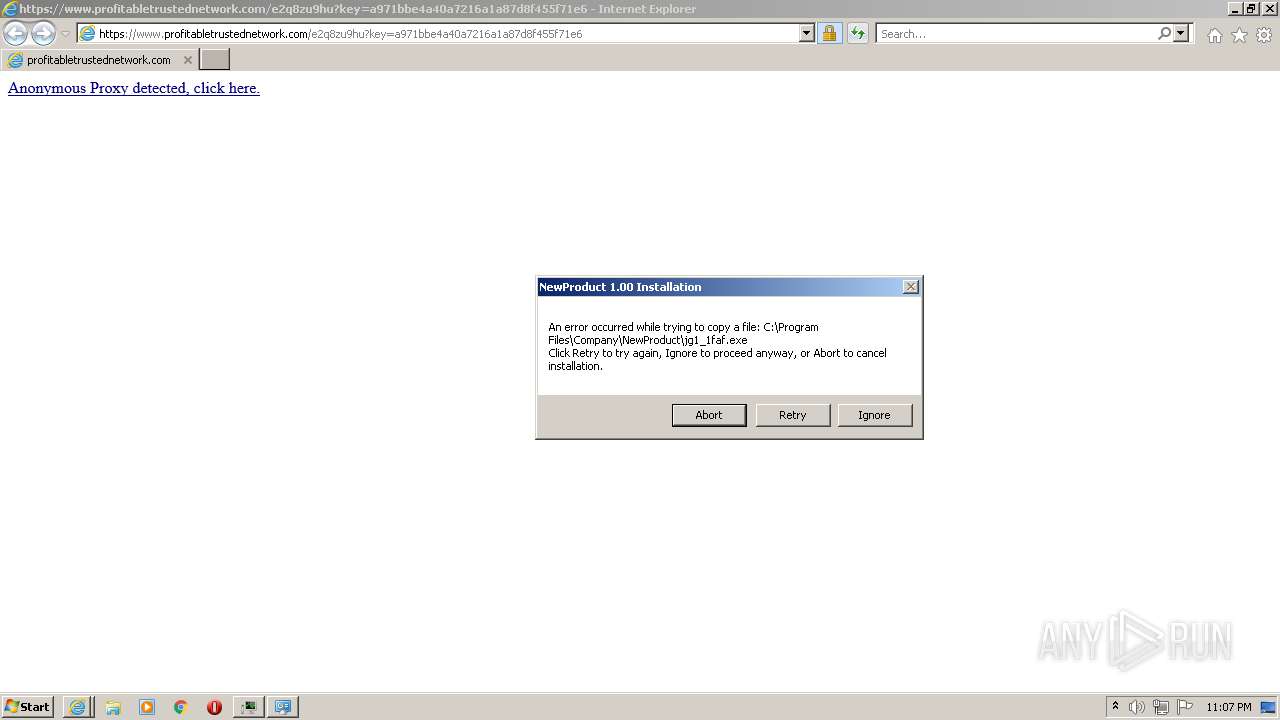
|---|---|
jg1_1faf.exe | http://186.2.171.17/seemorebty/poe.php?e=jg1_1faf |
jg1_1faf.exe | |
jg1_1faf.exe | |
jg1_1faf.exe | Download failed
|
jg1_1faf.exe | <<< Exit with same app>>> |