| File name: | saver.scr |
| Full analysis: | https://app.any.run/tasks/f3f0fcab-79db-40ce-9447-8a034d1018e2 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | November 14, 2018, 08:27:52 |
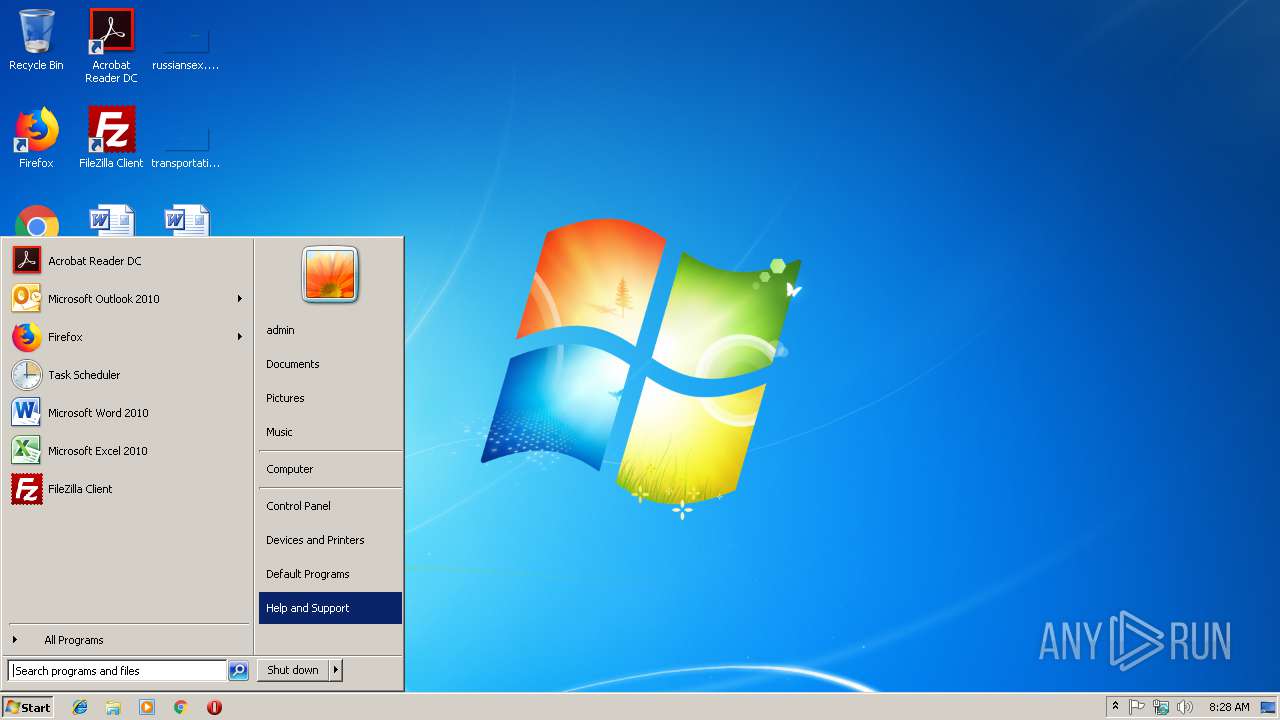
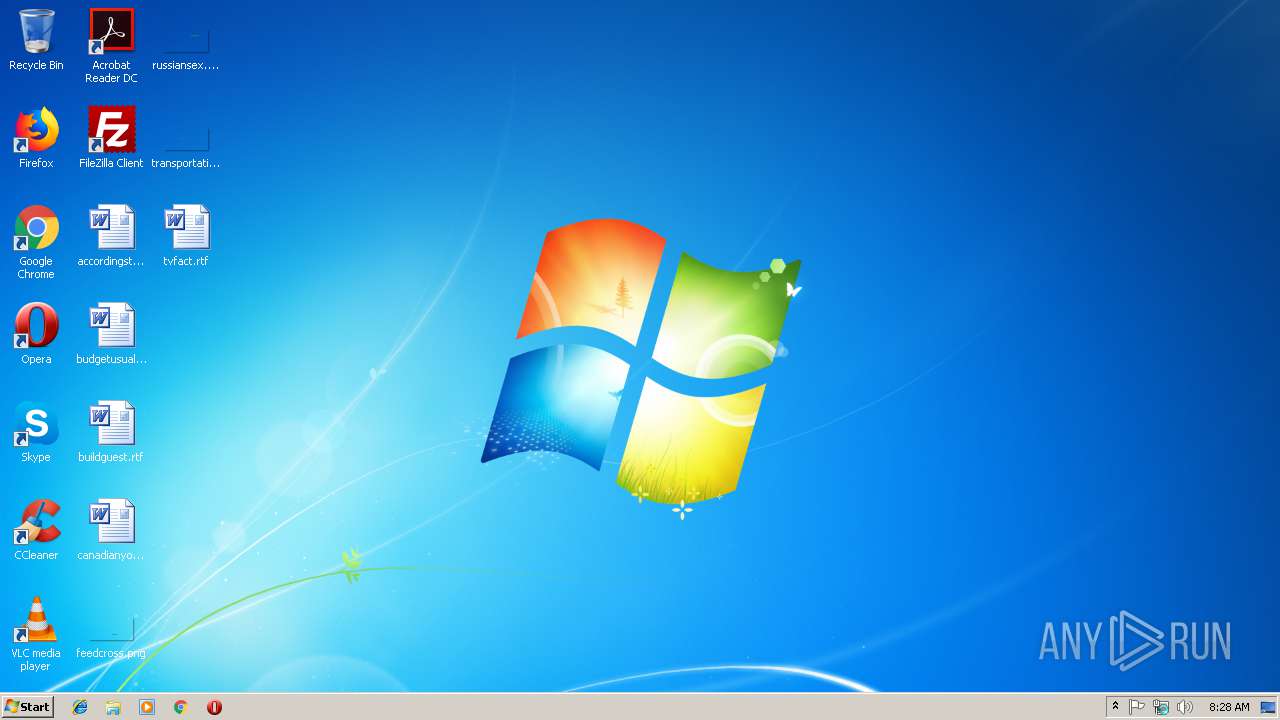
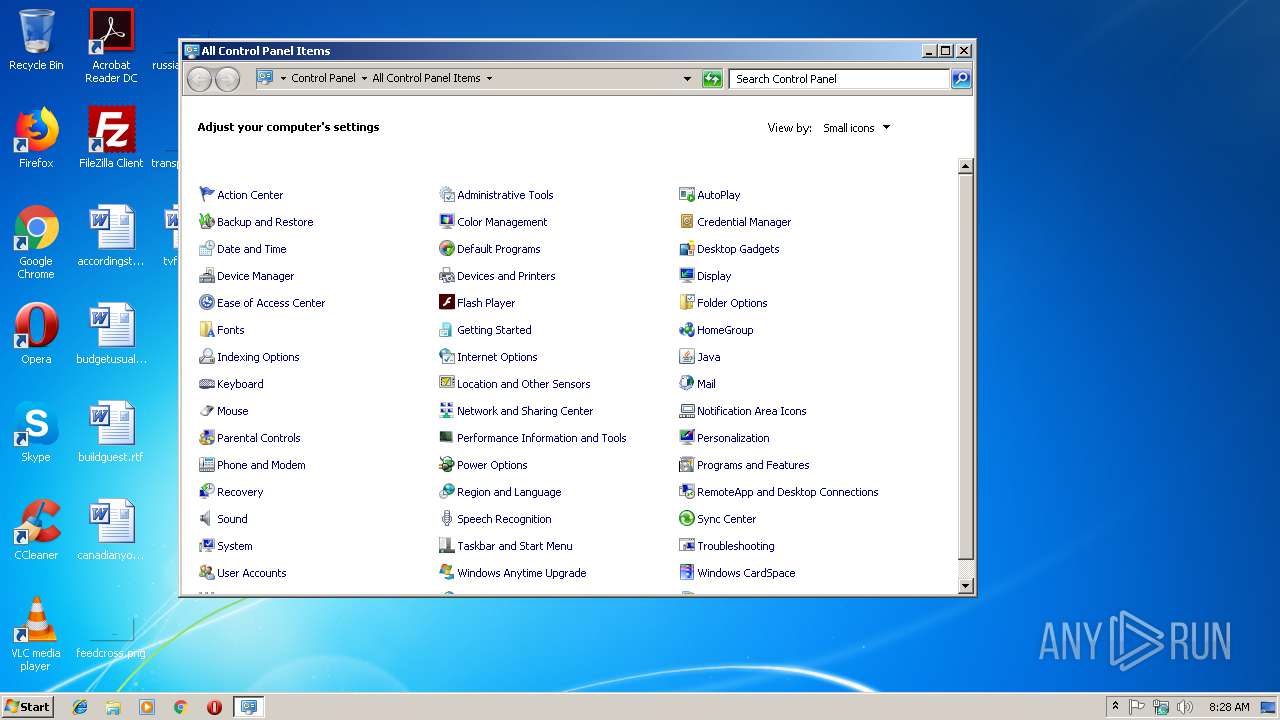
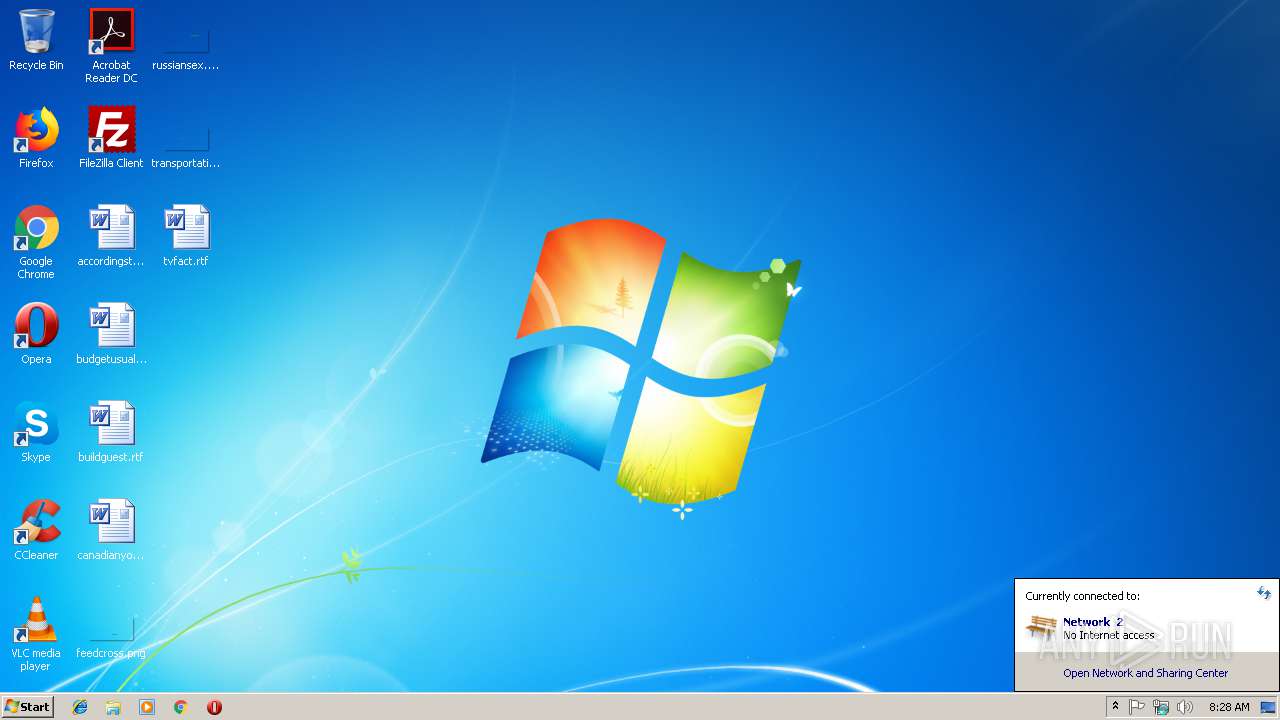
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 824A14D5534E3CB546A836CC8374CC59 |
| SHA1: | 0C96E4F34564707D49948E9C35DA9788006CF854 |
| SHA256: | C768D5DE6C9A9C7F0DB0B3714EC29A6DBB5B21D84BD47D752F1B00A017599EEB |
| SSDEEP: | 3072:1jeemVRCAQNb4Dg8quuK45h/cUSLNnalUN2EjxkU8dQoexMVfzlHcgMyH3gI:RURCpt8qGg/cRJahtd66VfzlHQgQI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- saver.scr (PID: 3744)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 22:21:03+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27648 |
| InitializedDataSize: | 197120 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x36fc |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Apr-2016 20:21:03 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Apr-2016 20:21:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006AB1 | 0x00006C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47221 |
.rdata | 0x00008000 | 0x000014FC | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.085 |
.data | 0x0000A000 | 0x0002D878 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.43179 |
.ndata | 0x00038000 | 0x0001F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00057000 | 0x000041D8 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.0345 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29548 | 1061 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
31
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3744 | "C:\Users\admin\AppData\Local\Temp\saver.scr" /S | C:\Users\admin\AppData\Local\Temp\saver.scr | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
329
Read events
329
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | saver.scr | C:\Users\admin\AppData\Local\Temp\bunny.dll | executable | |
MD5:— | SHA256:— | |||
| 3744 | saver.scr | C:\Users\admin\AppData\Local\Temp\Marabou | binary | |
MD5:— | SHA256:— | |||
| 3744 | saver.scr | C:\Users\admin\AppData\Local\Temp\nsg4293.tmp\System.dll | executable | |
MD5:75ED96254FBF894E42058062B4B4F0D1 | SHA256:A632D74332B3F08F834C732A103DAFEB09A540823A2217CA7F49159755E8F1D7 | |||
| 3744 | saver.scr | C:\Users\admin\AppData\Local\Temp\made.rtf | text | |
MD5:8274425DE767B30B2FFF1124AB54ABB5 | SHA256:0D6AFB7E939F0936F40AFDC759B5A354EA5427EC250A47E7B904AB1EA800A01D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 404 | 185.224.251.1:80 | http://mamujeeproduct.com/sfran/encode.php | unknown | text | 15 b | malicious |
— | — | POST | 404 | 185.224.251.1:80 | http://mamujeeproduct.com/sfran/encode.php | unknown | binary | 23 b | malicious |
— | — | POST | 404 | 185.224.251.1:80 | http://mamujeeproduct.com/sfran/encode.php | unknown | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.224.251.1:80 | mamujeeproduct.com | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mamujeeproduct.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
— | — | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
— | — | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |