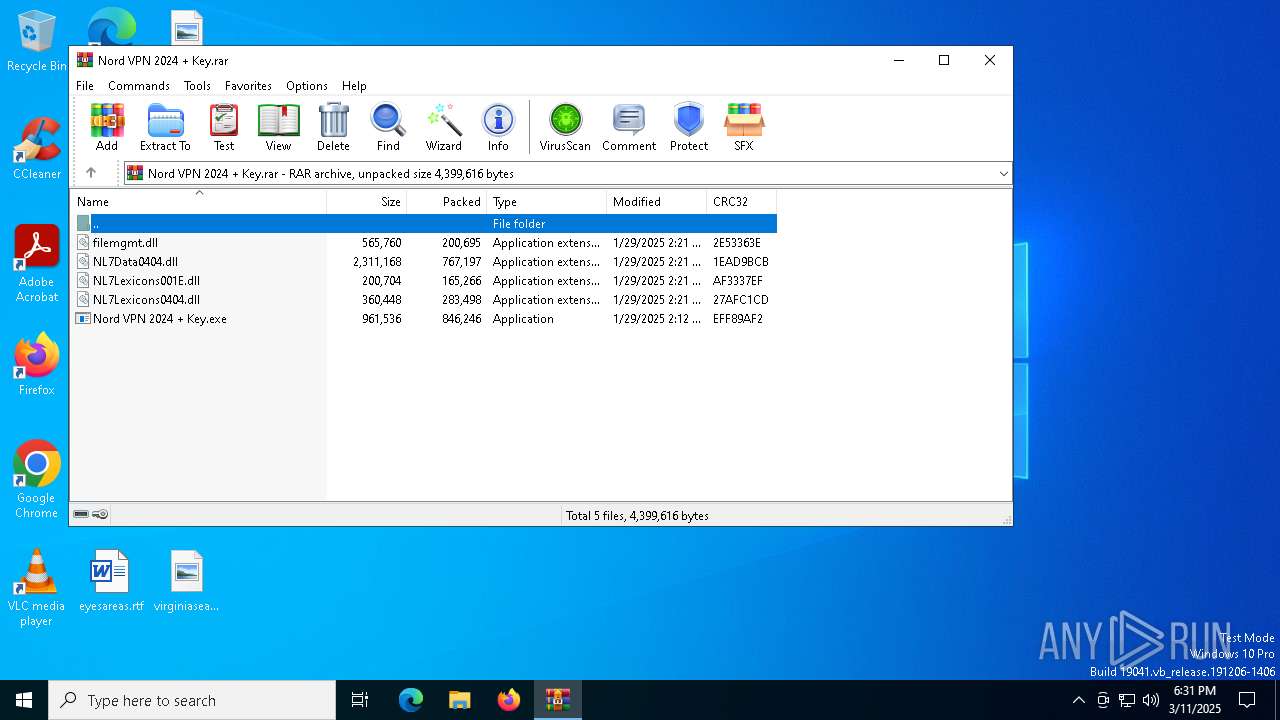
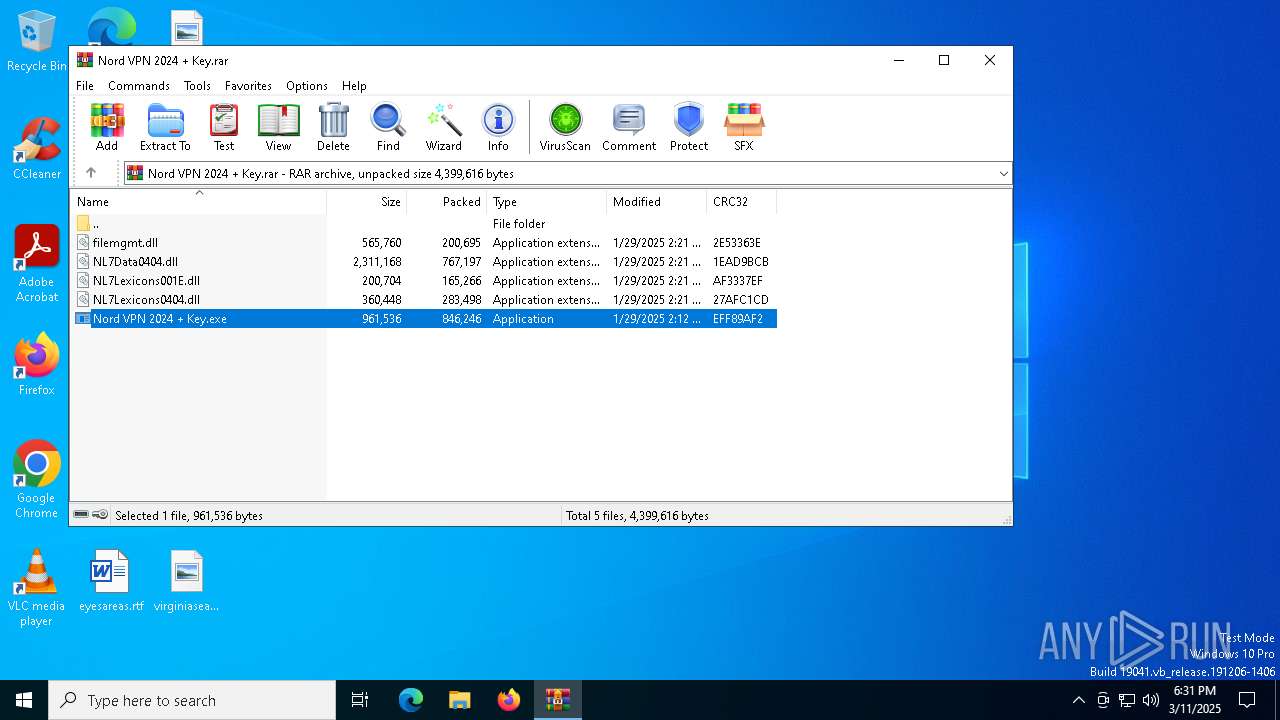
| File name: | Nord VPN 2024 + Key.rar |
| Full analysis: | https://app.any.run/tasks/93878e3e-2cc4-4bbc-a5c0-5fa9ad45fdde |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 11, 2025, 18:31:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3AB1D385CA12EE5DDC33DE08FC08E5BD |
| SHA1: | AFE4EA193268168576CE477352D6E9D9FB82ABD4 |
| SHA256: | C759E0B95BA72127C2A46EDA3A5517337BE3E1E00A72B7CF922B219CF28B7C2D |
| SSDEEP: | 98304:F1z7TBqK5s8tPu8R6zIuIRHSUYENNEQYKHCGyXctsVA1LEuFYIqWUzs+7DVPRLW/:c0GZQ |
MALICIOUS
LUMMA mutex has been found
- w6dJNZEmzi.exe (PID: 3888)
Create files in the Startup directory
- w6dJNZEmzi.exe (PID: 3888)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Executable content was dropped or overwritten
- w6dJNZEmzi.exe (PID: 3888)
- Nord VPN 2024 + Key.exe (PID: 2096)
Process drops legitimate windows executable
- WinRAR.exe (PID: 720)
Executes application which crashes
- Nord VPN 2024 + Key.exe (PID: 904)
- jMor3ZoAfo.exe (PID: 1164)
Application launched itself
- Nord VPN 2024 + Key.exe (PID: 904)
- jMor3ZoAfo.exe (PID: 1164)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 720)
The process creates files with name similar to system file names
- w6dJNZEmzi.exe (PID: 3888)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 720)
Creates files or folders in the user directory
- Nord VPN 2024 + Key.exe (PID: 2096)
- w6dJNZEmzi.exe (PID: 3888)
- WerFault.exe (PID: 1568)
- BackgroundTransferHost.exe (PID: 5392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 720)
Checks supported languages
- Nord VPN 2024 + Key.exe (PID: 904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 846246 |
| UncompressedSize: | 961536 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Nord VPN 2024 + Key.exe |
Total processes
153
Monitored processes
17
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Nord VPN 2024 + Key.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 904 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\Nord VPN 2024 + Key.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\Nord VPN 2024 + Key.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chicken Exit code: 3221226505 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\AppData\Roaming\jMor3ZoAfo.exe" | C:\Users\admin\AppData\Roaming\jMor3ZoAfo.exe | Nord VPN 2024 + Key.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chicken Exit code: 3221226505 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\AppData\Roaming\jMor3ZoAfo.exe" | C:\Users\admin\AppData\Roaming\jMor3ZoAfo.exe | jMor3ZoAfo.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chicken Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 904 -s 836 | C:\Windows\SysWOW64\WerFault.exe | — | Nord VPN 2024 + Key.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\Nord VPN 2024 + Key.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\Nord VPN 2024 + Key.exe | Nord VPN 2024 + Key.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chicken Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1164 -s 836 | C:\Windows\SysWOW64\WerFault.exe | — | jMor3ZoAfo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "C:\Users\admin\AppData\Roaming\w6dJNZEmzi.exe" | C:\Users\admin\AppData\Roaming\w6dJNZEmzi.exe | Nord VPN 2024 + Key.exe | ||||||||||||
User: admin Company: Microsoft Windows Integrity Level: MEDIUM Description: system32 Version: 15.6.13.6 Modules
| |||||||||||||||
| 5392 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 905
Read events
8 880
Write events
25
Delete events
0
Modification events
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Nord VPN 2024 + Key.rar | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (720) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6964) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6964) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
8
Suspicious files
9
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1568 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Nord VPN 2024 + _8520b4f1bfe7f21b4b5ad32175710687886683_8ffc409c_0a93a1b3-9616-4d78-ba56-844bb1c06660\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2420 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_jMor3ZoAfo.exe_7eb1488dc86d5aed26e7c2ab9746930aa9ad8bb_1b02a2e0_c47ad7c5-9a11-4bfd-b840-1286f3992349\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1568 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Nord VPN 2024 + Key.exe.904.dmp | — | |
MD5:— | SHA256:— | |||
| 5392 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7b78c9b1-9418-4d1e-bfeb-9fe2f7df9874.down_data | — | |
MD5:— | SHA256:— | |||
| 2420 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\jMor3ZoAfo.exe.1164.dmp | — | |
MD5:— | SHA256:— | |||
| 720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\Nord VPN 2024 + Key.exe | executable | |
MD5:025FF5672AC6FC9D1F68017B5CD177A1 | SHA256:D3559848CCA07DADB0C9F4AAAEE81BBC51753B8E9278E0BA020683A6569B9732 | |||
| 720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\filemgmt.dll | executable | |
MD5:D7C3007DCA0312785BF75FE212506431 | SHA256:BCEC0ECD295639E81044611F32E28A2B3129CCE499B0CD44BA46514C01B0D84E | |||
| 720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\NL7Data0404.dll | executable | |
MD5:81B14FD1C9D2B830E55C93C4C38AFA2F | SHA256:878E2DBAC4B6A6BCCE54742F3C7BFD87AA93A6637CCCC1E5D18AB65215D81BEE | |||
| 720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa720.20134\NL7Lexicons001E.dll | executable | |
MD5:2215175AA6BB8F42F16B9F9BB5A034F7 | SHA256:FBF5CB7BFD332E926E28CA20271820E7124DD8DFC92628F1B1C8375E9B2BEBBF | |||
| 2096 | Nord VPN 2024 + Key.exe | C:\Users\admin\AppData\Roaming\jMor3ZoAfo.exe | executable | |
MD5:8BE86E1ECED7FEA7D67B300DAC2C73F3 | SHA256:294285A5E5104850961D4DFEA51FC7F13E025B4893A32A219206CFC7C5AA738C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
27
DNS requests
25
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6388 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
8080 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
8080 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5392 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6388 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6388 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
paleboreei.biz |
| malicious |
guardeduppe.com |
| malicious |
toppyneedus.biz |
| malicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (paleboreei .biz) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (guardeduppe .com) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (toppyneedus .biz) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (flockefaccek .org) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (toppyneedus .biz) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (babberstalek .org) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (babberstalek .org) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (climepunneddus .com) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (carrystuppeder .net) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (rebuildhurrte .com) |