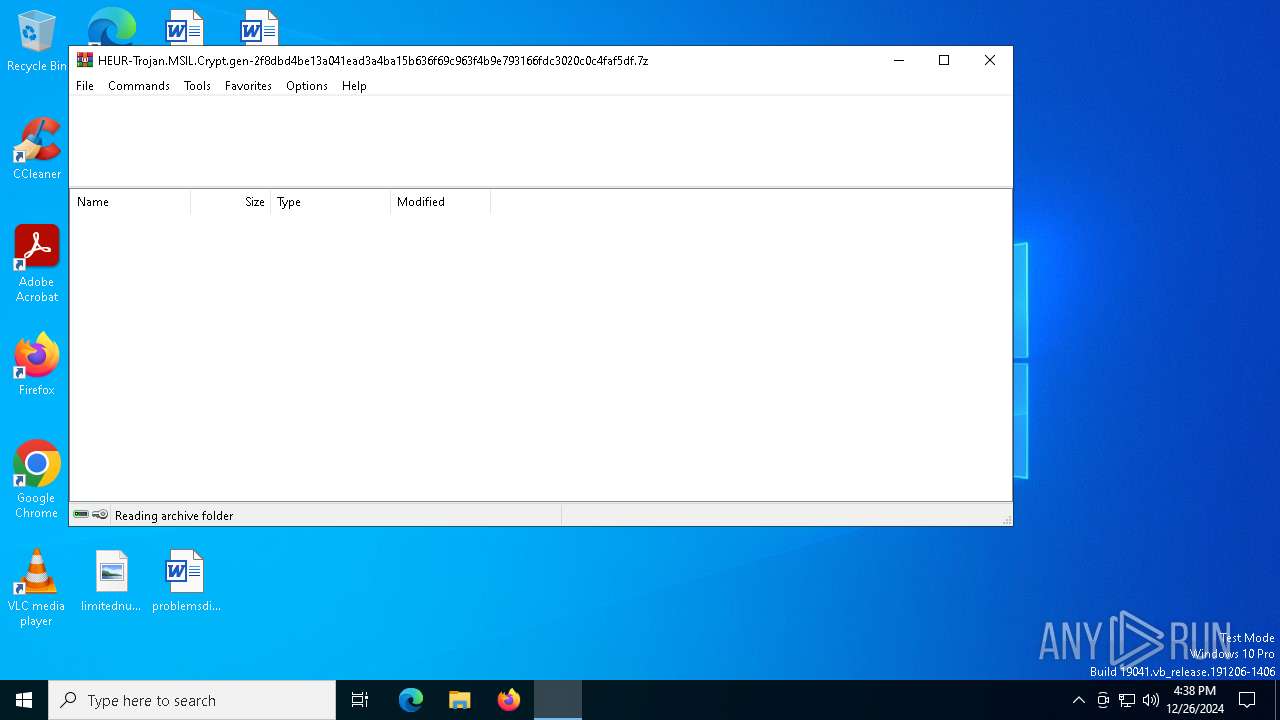
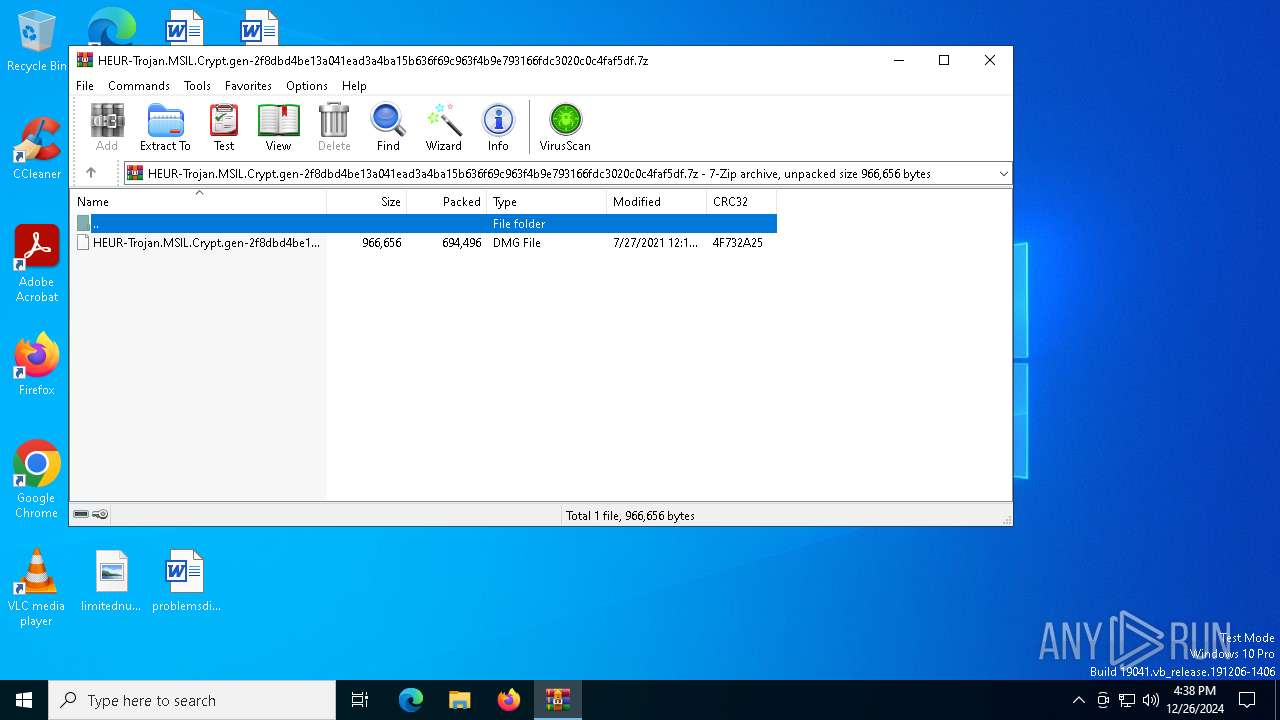
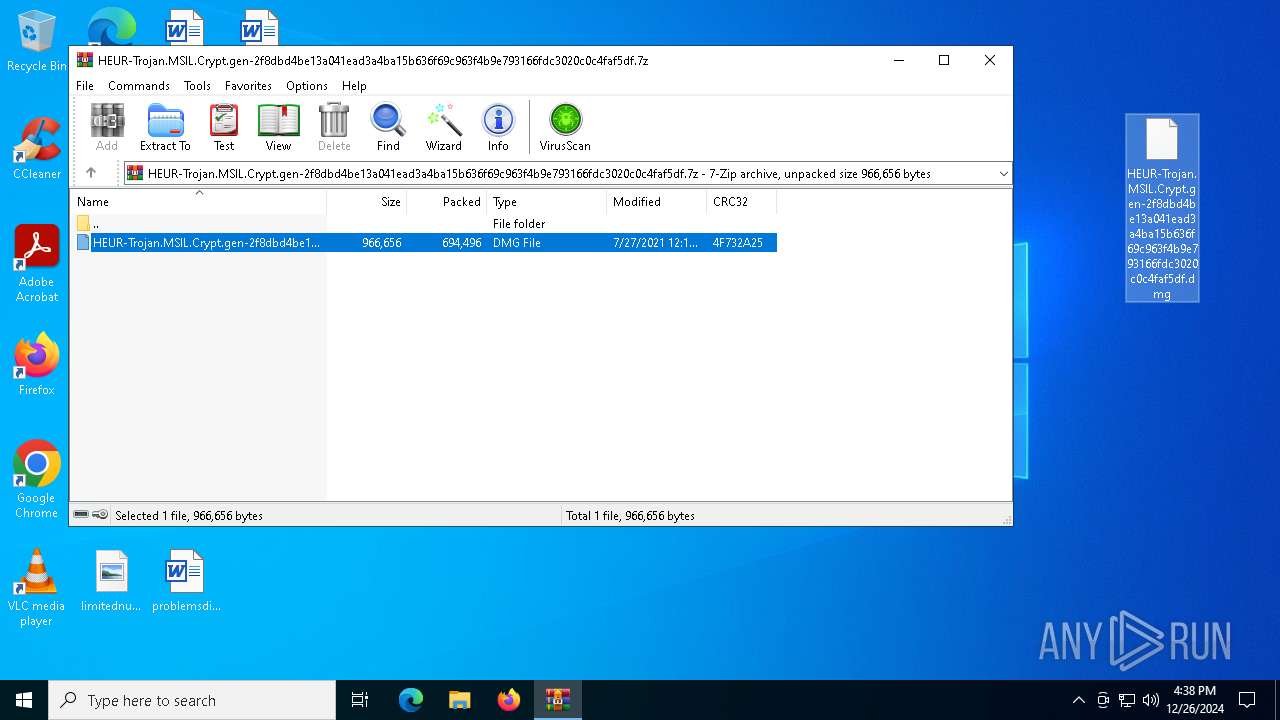
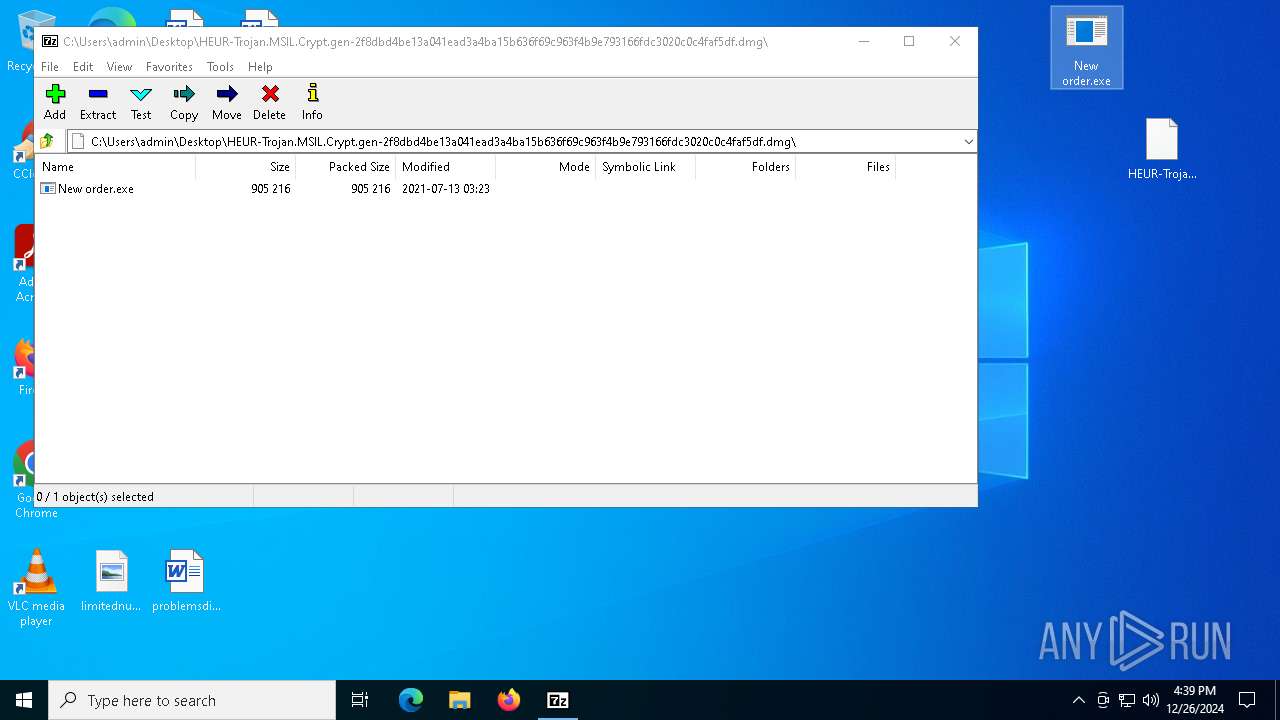
| File name: | HEUR-Trojan.MSIL.Crypt.gen-2f8dbd4be13a041ead3a4ba15b636f69c963f4b9e793166fdc3020c0c4faf5df.7z |
| Full analysis: | https://app.any.run/tasks/42a6fd96-b49d-4384-94ad-f951c9846da7 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 26, 2024, 16:38:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | EBEF4EFA162C3C9187C981602518280D |
| SHA1: | 9FA8B7C2386DA55ACBB3EBFC873771A5FA1B558D |
| SHA256: | C6D435345C9D66855AF04C046C24842FBD650523A9AD877519A5CCD5A49CFE88 |
| SSDEEP: | 24576:B+sP2bqAf3/50i22JisBJH0zS9dRpjVNU24ZYG5K6pUaHJr+Qq47DE6:B+sP2bqAf3/50i22JisBJH0zS9dRpjVa |
MALICIOUS
AGENTTESLA has been detected (YARA)
- New order.exe (PID: 7512)
Steals credentials from Web Browsers
- New order.exe (PID: 7512)
Actions looks like stealing of personal data
- New order.exe (PID: 7512)
SUSPICIOUS
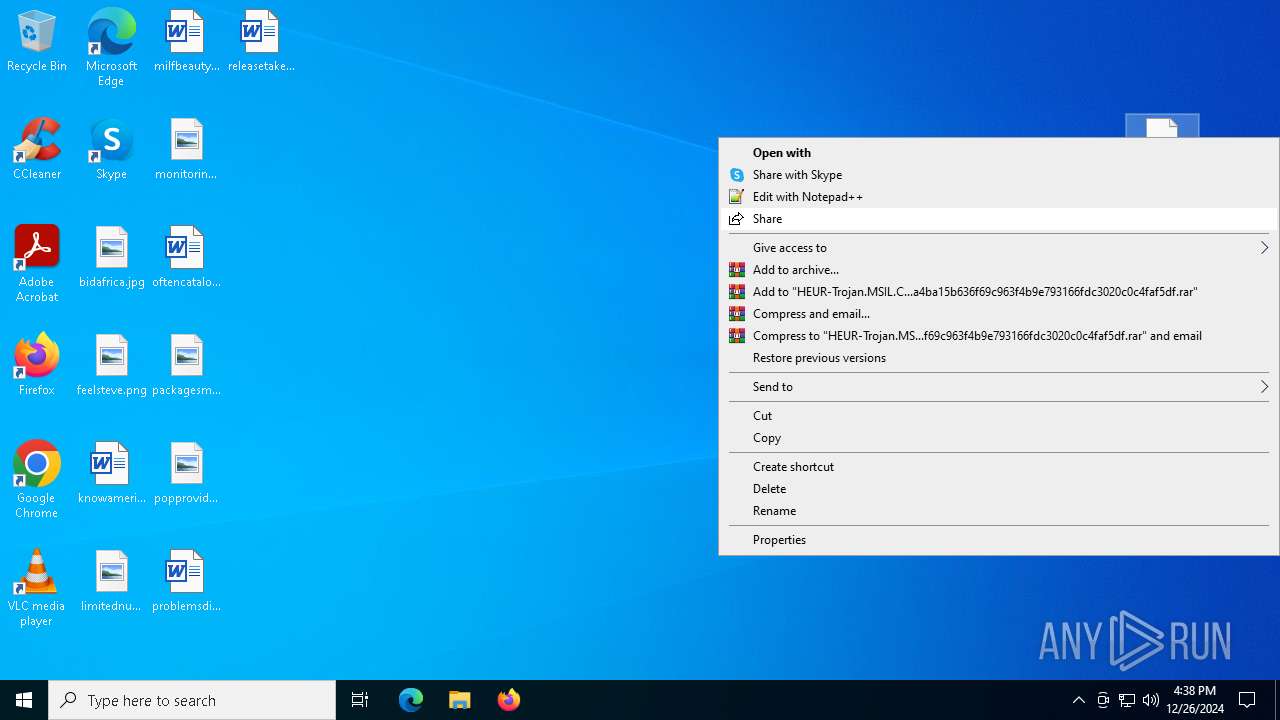
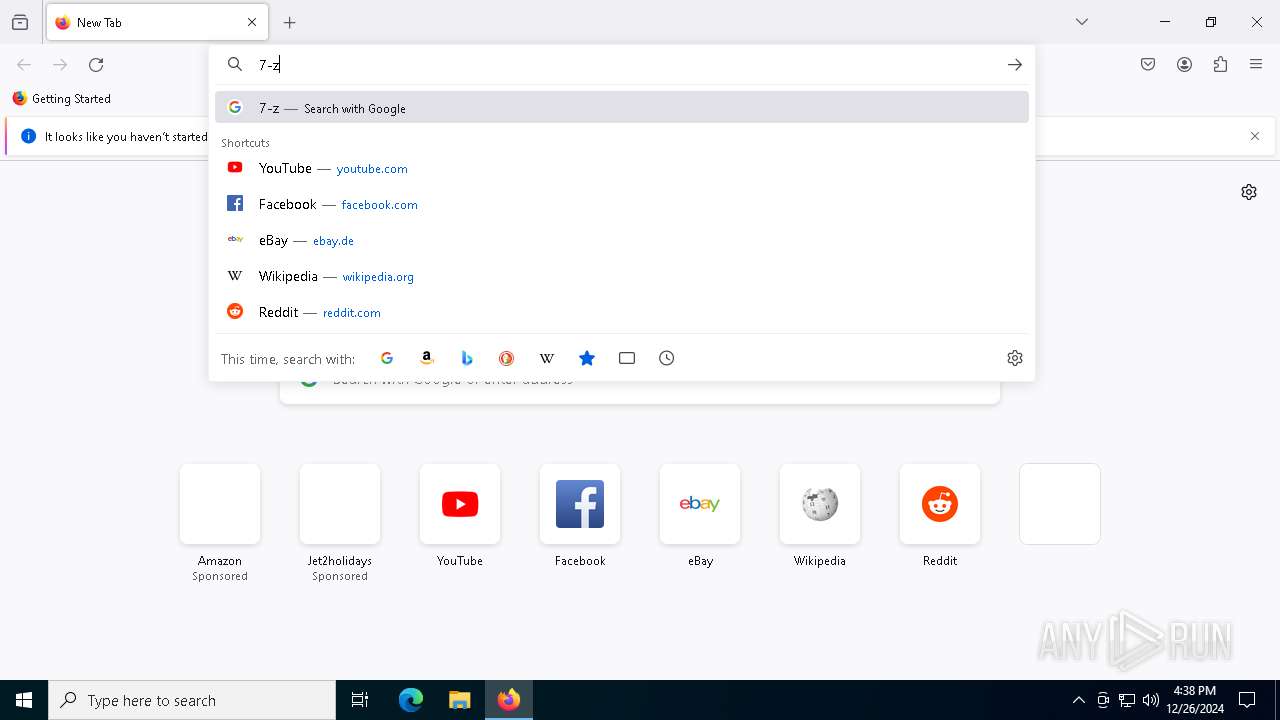
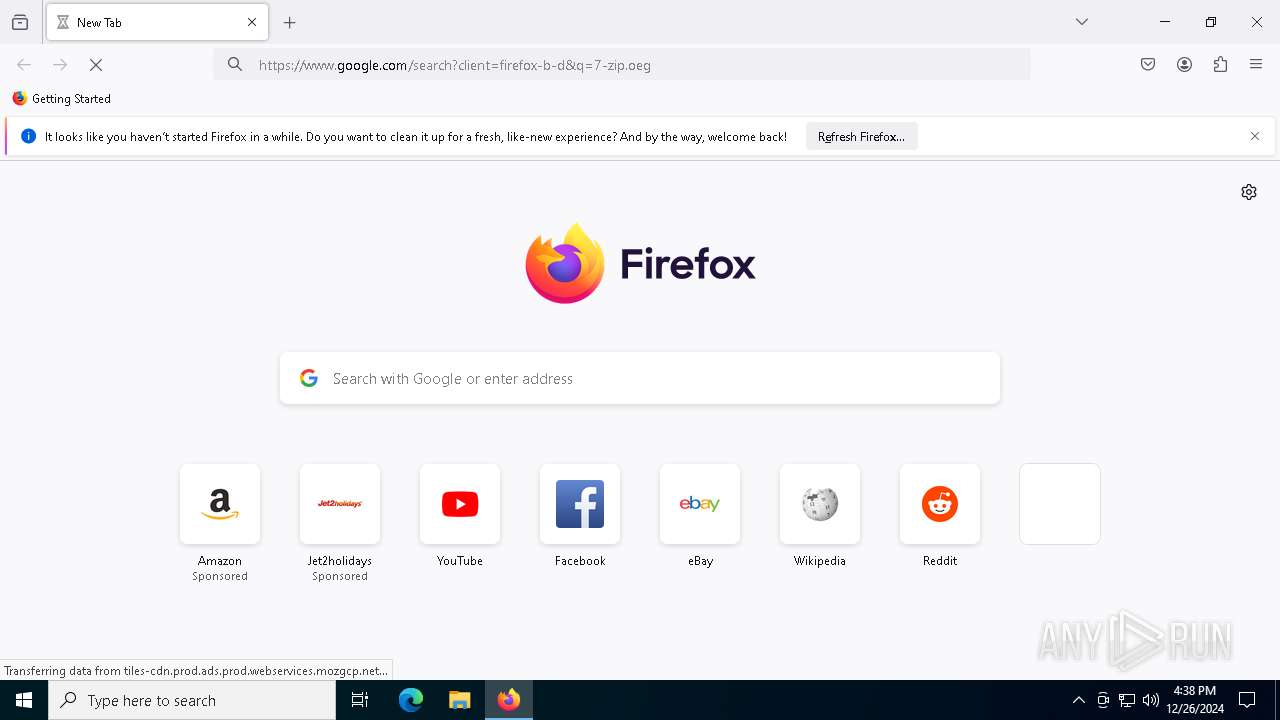
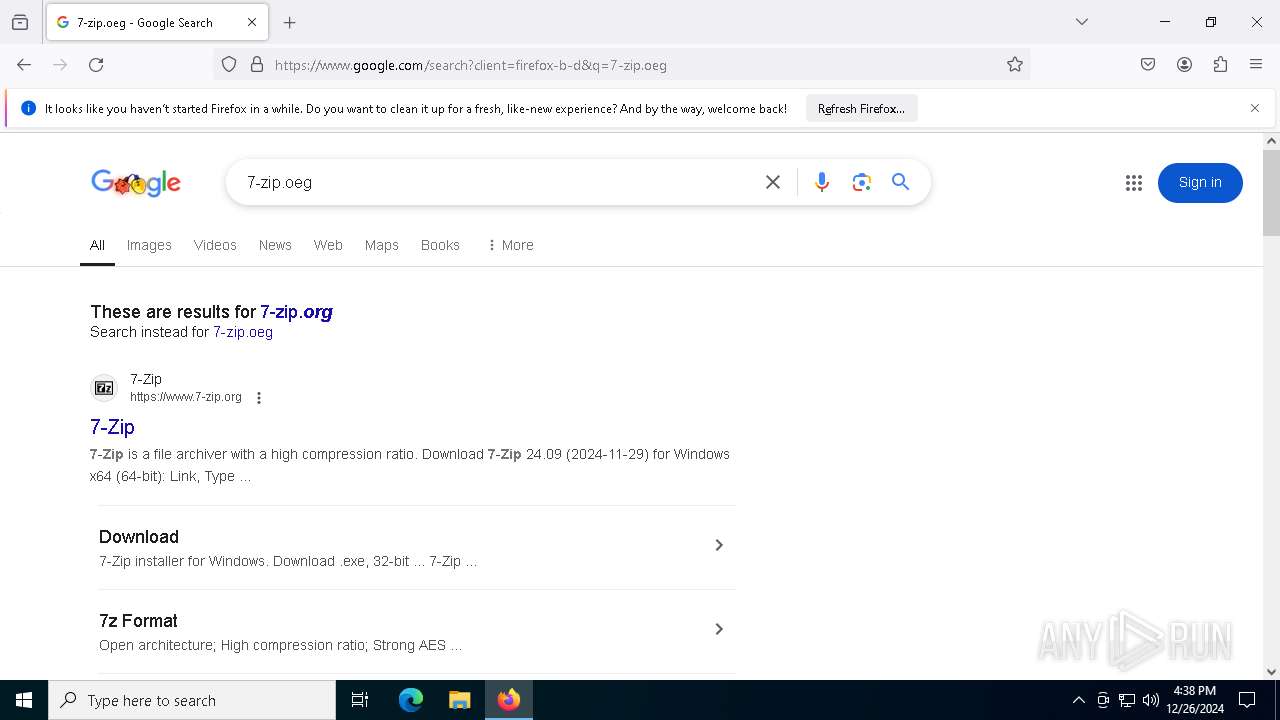
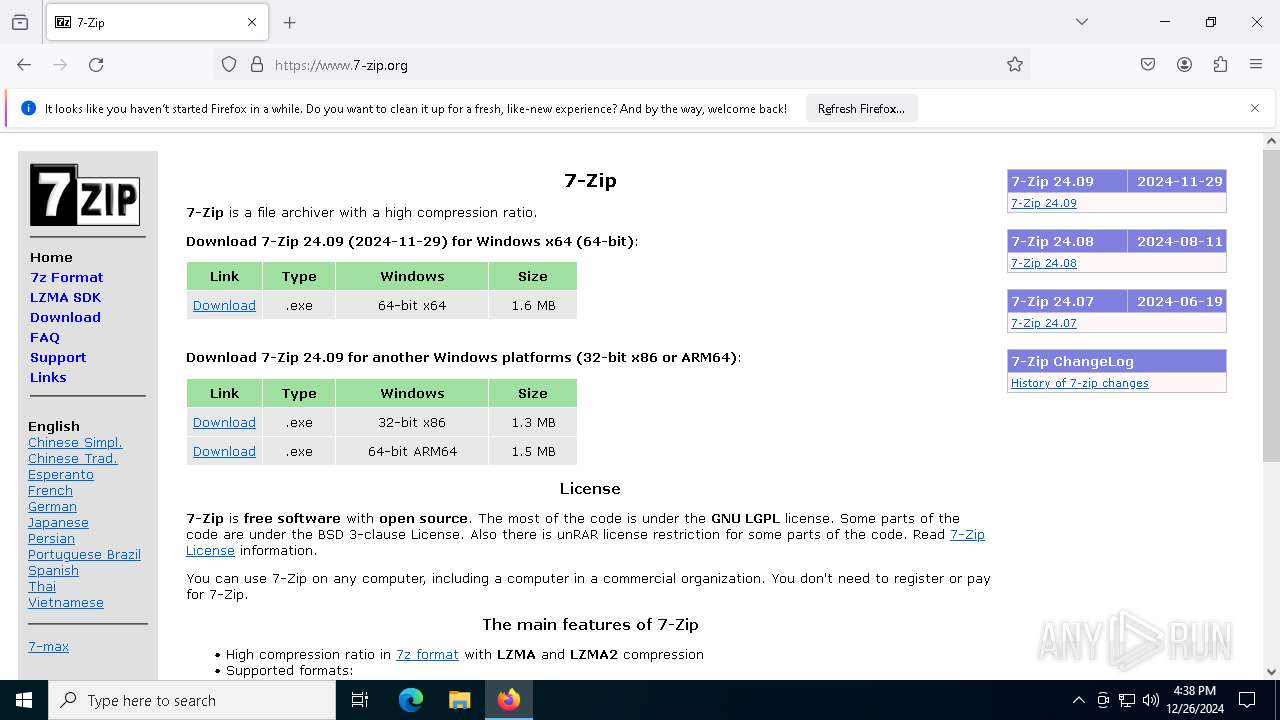
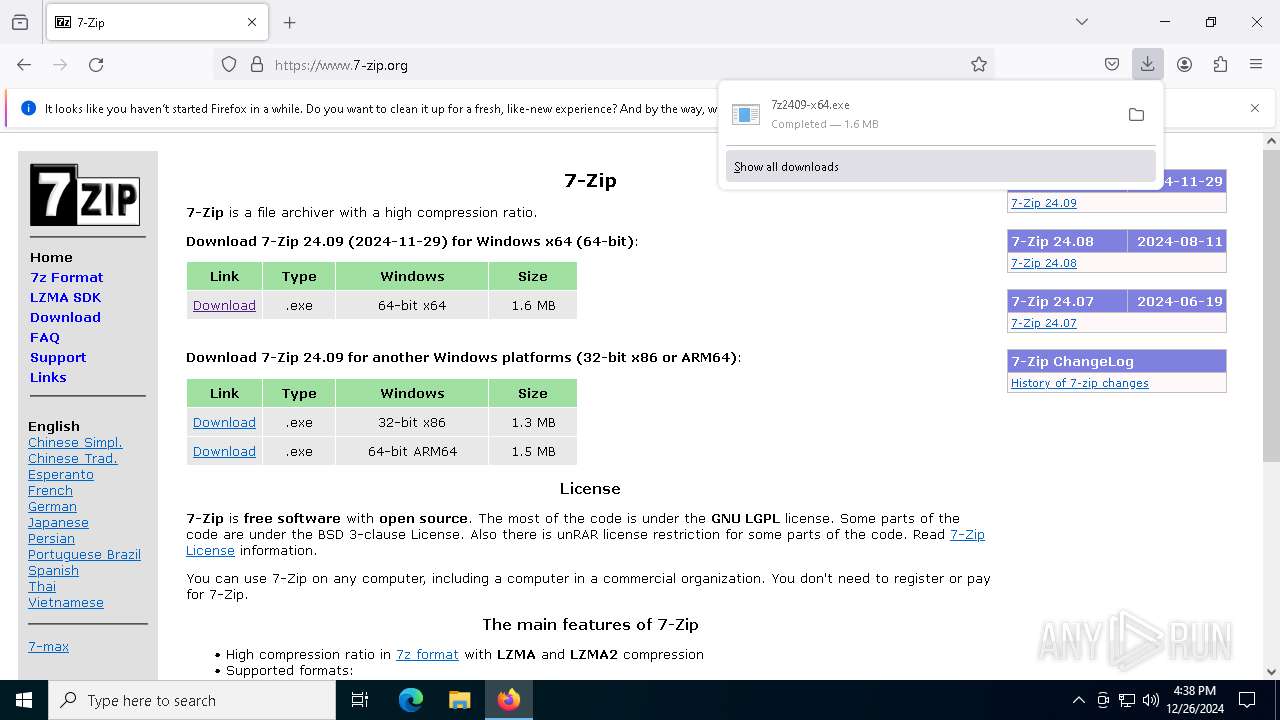
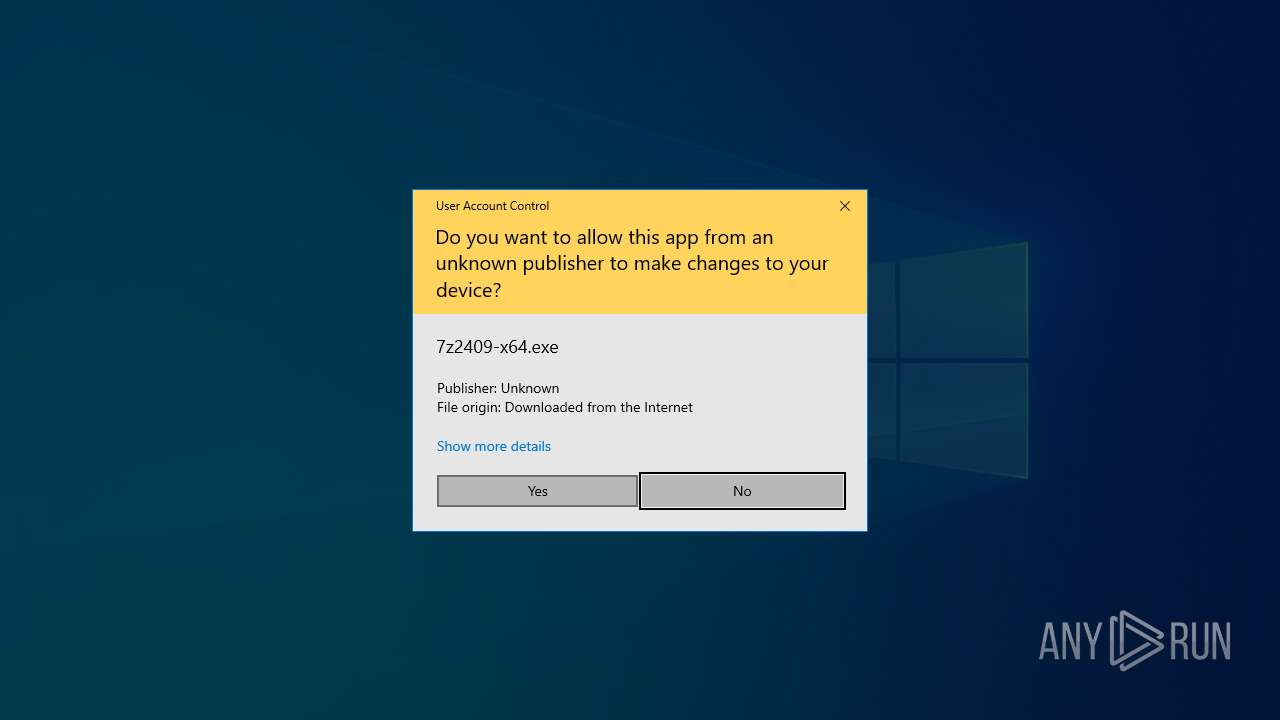
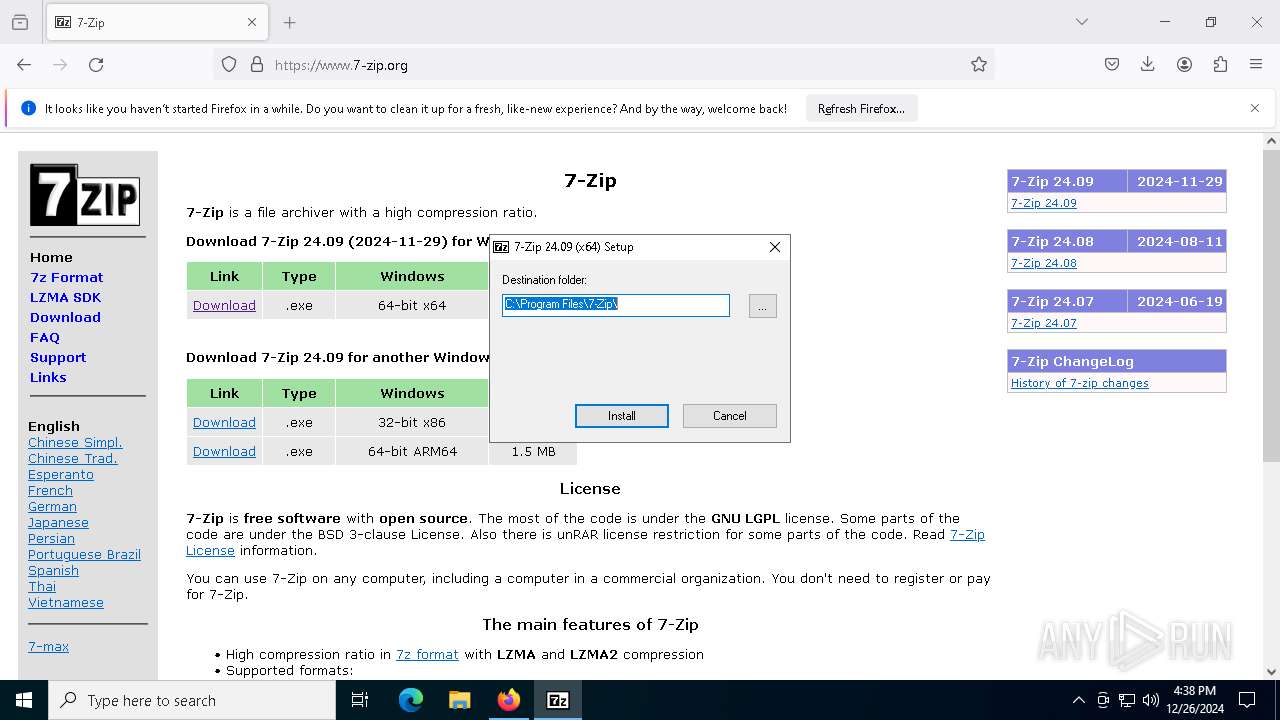
Drops 7-zip archiver for unpacking
- 7z2409-x64.exe (PID: 7704)
- firefox.exe (PID: 6172)
Creates/Modifies COM task schedule object
- 7z2409-x64.exe (PID: 7704)
Executable content was dropped or overwritten
- 7z2409-x64.exe (PID: 7704)
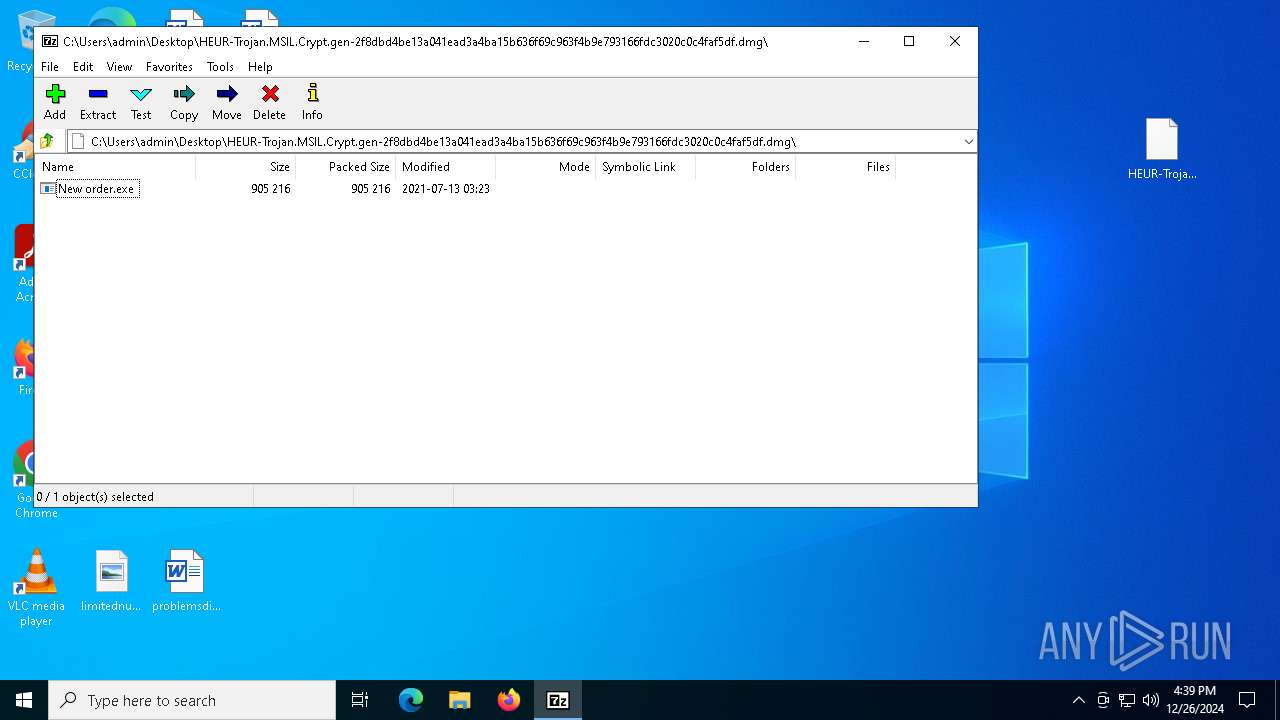
- 7zFM.exe (PID: 8144)
Creates a software uninstall entry
- 7z2409-x64.exe (PID: 7704)
Possible usage of Discord/Telegram API has been detected (YARA)
- New order.exe (PID: 7512)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- New order.exe (PID: 7512)
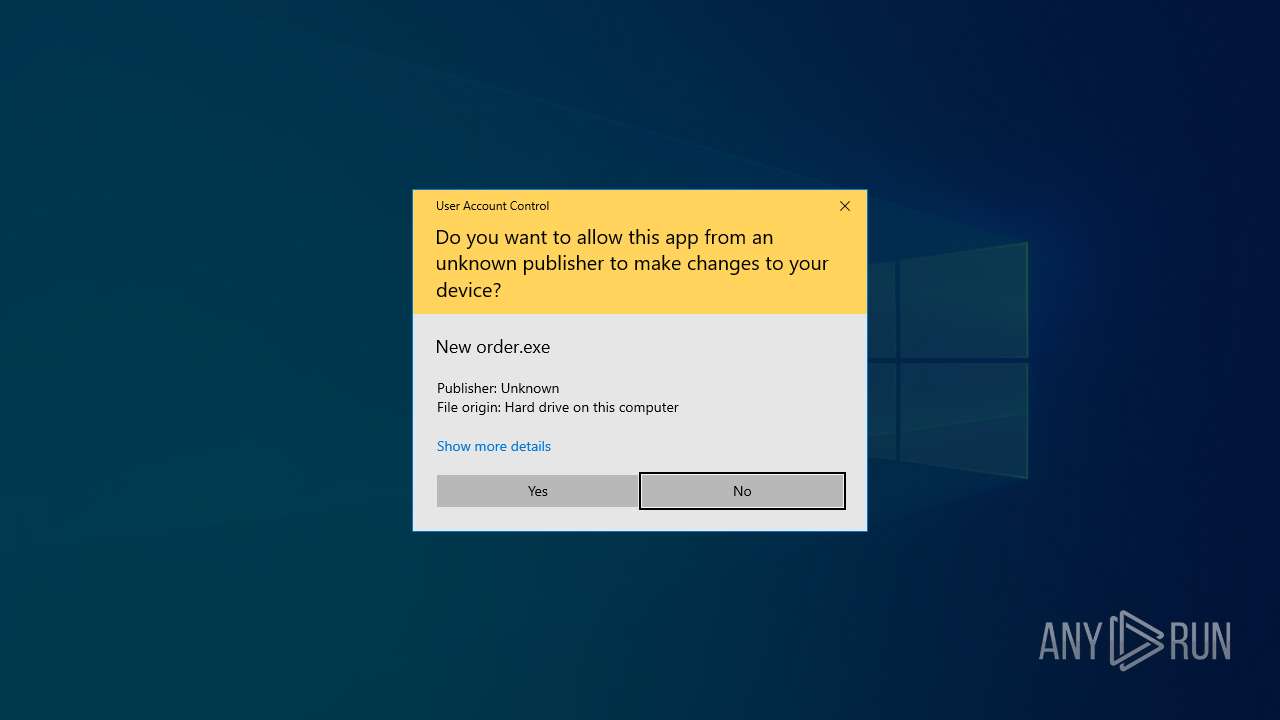
Application launched itself
- New order.exe (PID: 5920)
The process connected to a server suspected of theft
- New order.exe (PID: 7512)
INFO
Application launched itself
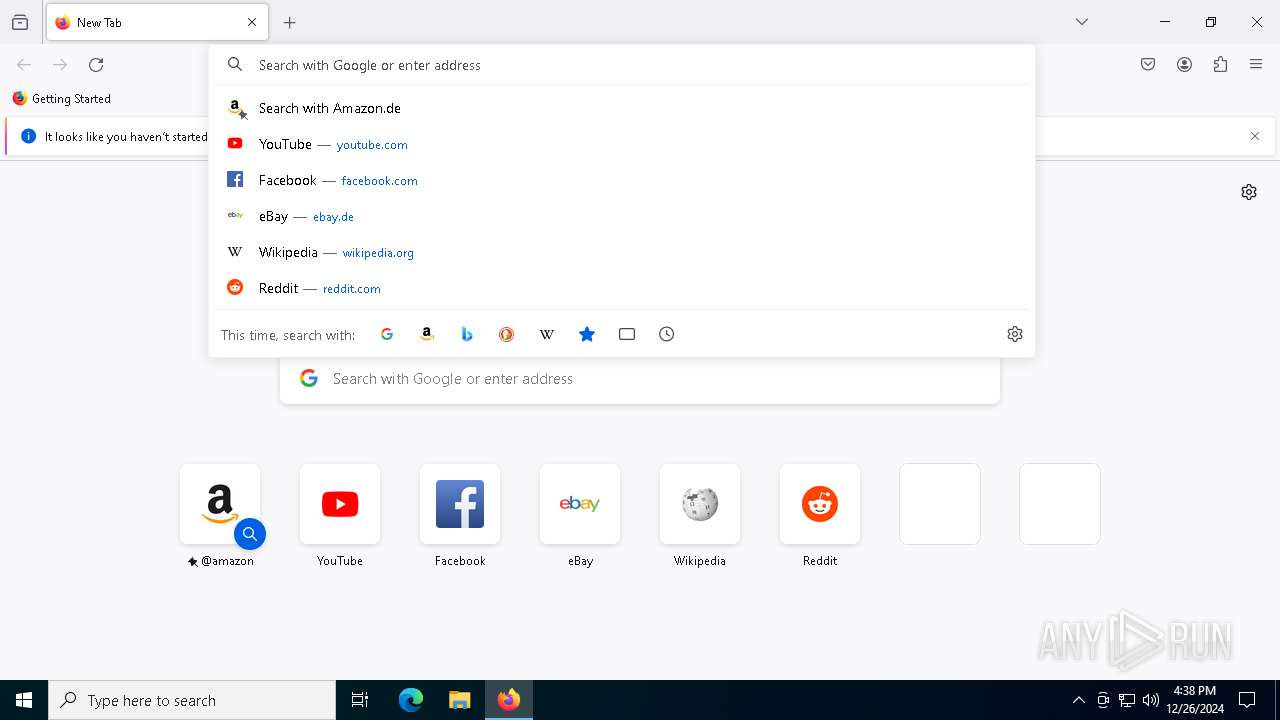
- firefox.exe (PID: 6172)
- firefox.exe (PID: 5340)
The process uses the downloaded file
- WinRAR.exe (PID: 6484)
- firefox.exe (PID: 6172)
Executable content was dropped or overwritten
- firefox.exe (PID: 6172)
The sample compiled with english language support
- firefox.exe (PID: 6172)
- 7z2409-x64.exe (PID: 7704)
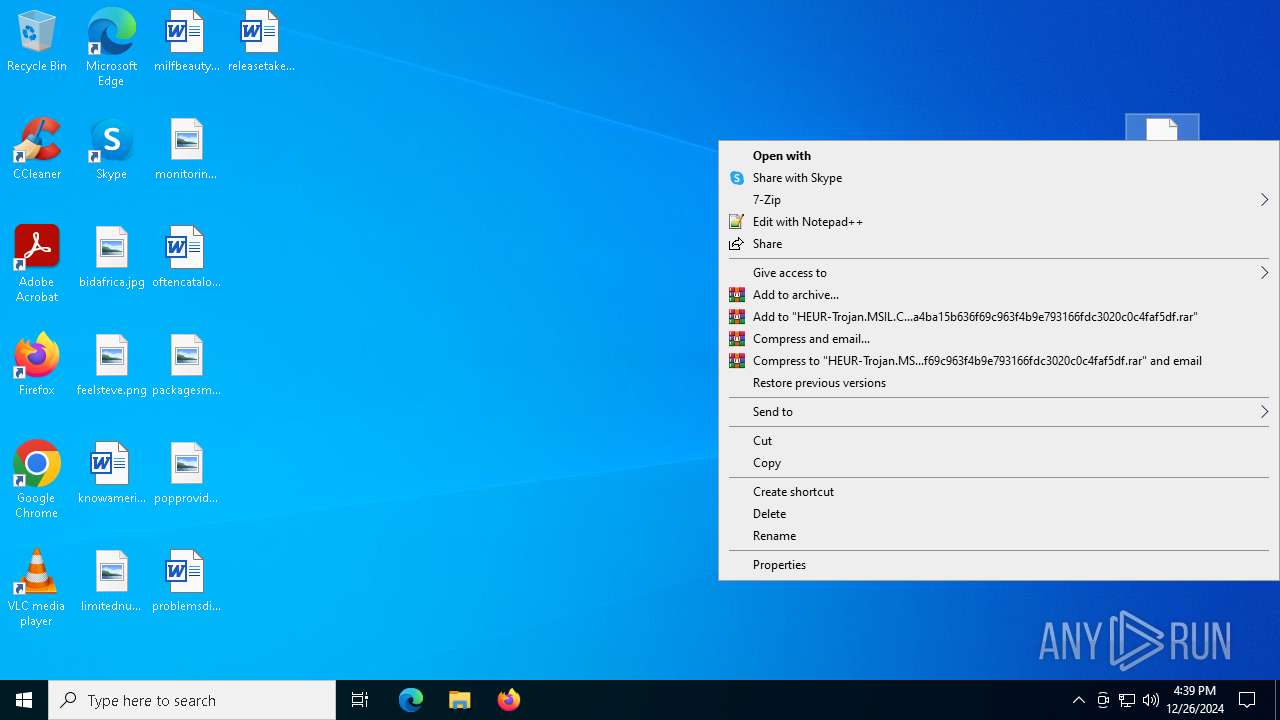
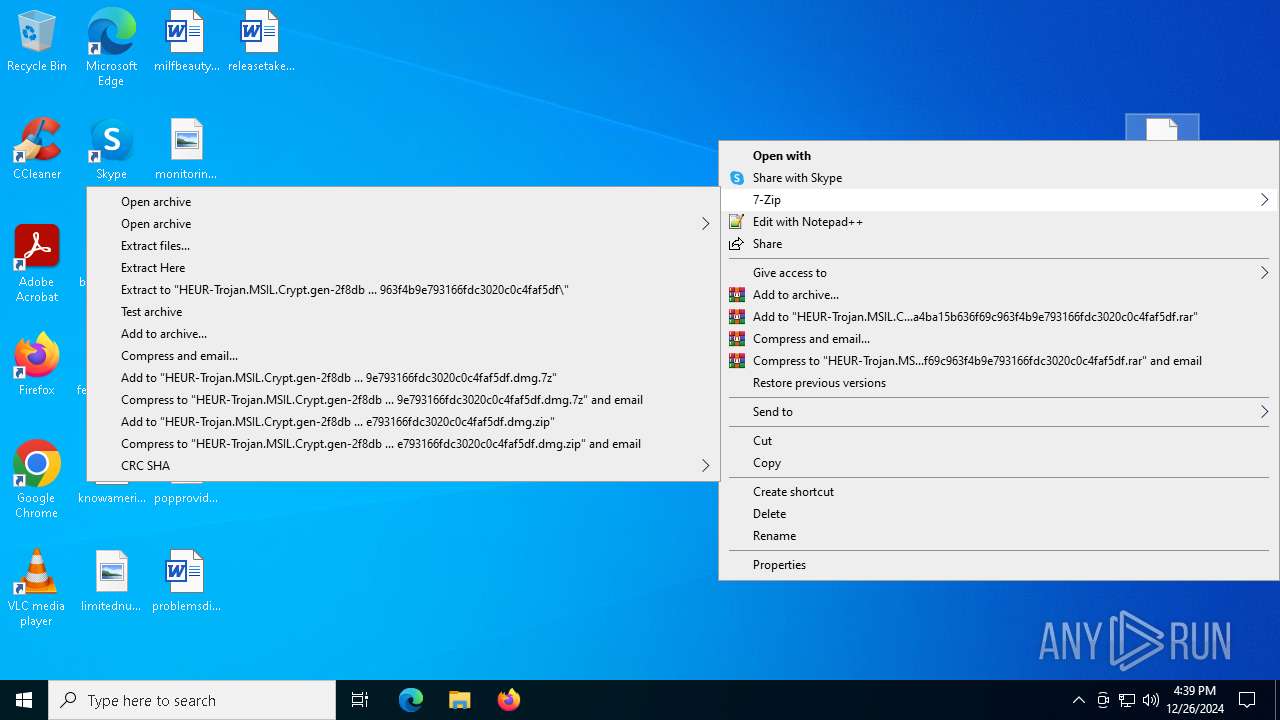
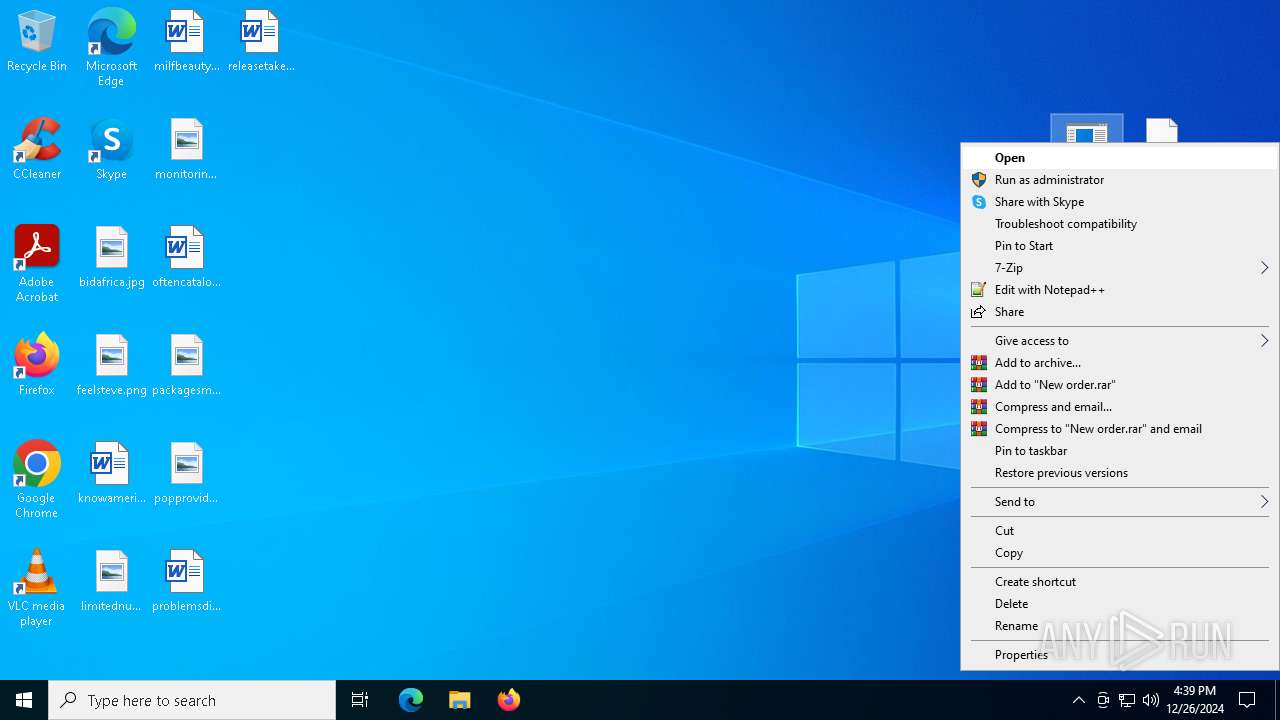
Manual execution by a user
- firefox.exe (PID: 5340)
- New order.exe (PID: 5920)
- 7zFM.exe (PID: 8144)
Creates files in the program directory
- 7z2409-x64.exe (PID: 7704)
Reads the computer name
- 7z2409-x64.exe (PID: 7704)
- 7zFM.exe (PID: 8144)
- New order.exe (PID: 5920)
- New order.exe (PID: 7512)
Checks supported languages
- 7zFM.exe (PID: 8144)
- 7z2409-x64.exe (PID: 7704)
- New order.exe (PID: 5920)
Create files in a temporary directory
- 7zFM.exe (PID: 8144)
Reads the machine GUID from the registry
- New order.exe (PID: 5920)
- New order.exe (PID: 7512)
Reads the software policy settings
- New order.exe (PID: 7512)
Disables trace logs
- New order.exe (PID: 7512)
Checks proxy server information
- New order.exe (PID: 7512)
Attempting to use instant messaging service
- New order.exe (PID: 7512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:07:27 12:12:22+00:00 |
| ArchivedFileName: | HEUR-Trojan.MSIL.Crypt.gen-2f8dbd4be13a041ead3a4ba15b636f69c963f4b9e793166fdc3020c0c4faf5df.dmg |
Total processes
148
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2804 -childID 1 -isForBrowser -prefsHandle 2816 -prefMapHandle 2812 -prefsLen 31447 -prefMapSize 244583 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {230a33a4-e276-4e69-a1b6-e578e6824a1c} 6172 "\\.\pipe\gecko-crash-server-pipe.6172" 19bd299ff50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2080 -prefMapHandle 2060 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {6b512b97-e114-4575-92cc-43b44c7e1ef7} 6172 "\\.\pipe\gecko-crash-server-pipe.6172" 19bc0c7f910 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5280 -childID 5 -isForBrowser -prefsHandle 5288 -prefMapHandle 5292 -prefsLen 31251 -prefMapSize 244583 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {baffc595-08db-41ef-a77c-b3880f83d881} 6172 "\\.\pipe\gecko-crash-server-pipe.6172" 19bd8cea4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3696 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4300 -childID 2 -isForBrowser -prefsHandle 4324 -prefMapHandle 4320 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {dee18fe2-c628-436d-96ae-9f7e20d3e888} 6172 "\\.\pipe\gecko-crash-server-pipe.6172" 19bd5087a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5340 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5732 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5264 -childID 4 -isForBrowser -prefsHandle 5256 -prefMapHandle 5252 -prefsLen 31251 -prefMapSize 244583 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7019db82-5a1d-4c45-a44d-536d9dac1350} 6172 "\\.\pipe\gecko-crash-server-pipe.6172" 19bd8cea310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5920 | "C:\Users\admin\Desktop\New order.exe" | C:\Users\admin\Desktop\New order.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6172 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6432 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1912 -parentBuildID 20240213221259 -prefsHandle 1828 -prefMapHandle 1816 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {3920fdc7-5278-4b47-b70f-cc101d748119} 6172 "\\.\pipe\gecko-crash-server-pipe.6172" 19bcdbeee10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 6484 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\HEUR-Trojan.MSIL.Crypt.gen-2f8dbd4be13a041ead3a4ba15b636f69c963f4b9e793166fdc3020c0c4faf5df.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
16 965
Read events
16 899
Write events
66
Delete events
0
Modification events
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HEUR-Trojan.MSIL.Crypt.gen-2f8dbd4be13a041ead3a4ba15b636f69c963f4b9e793166fdc3020c0c4faf5df.7z | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
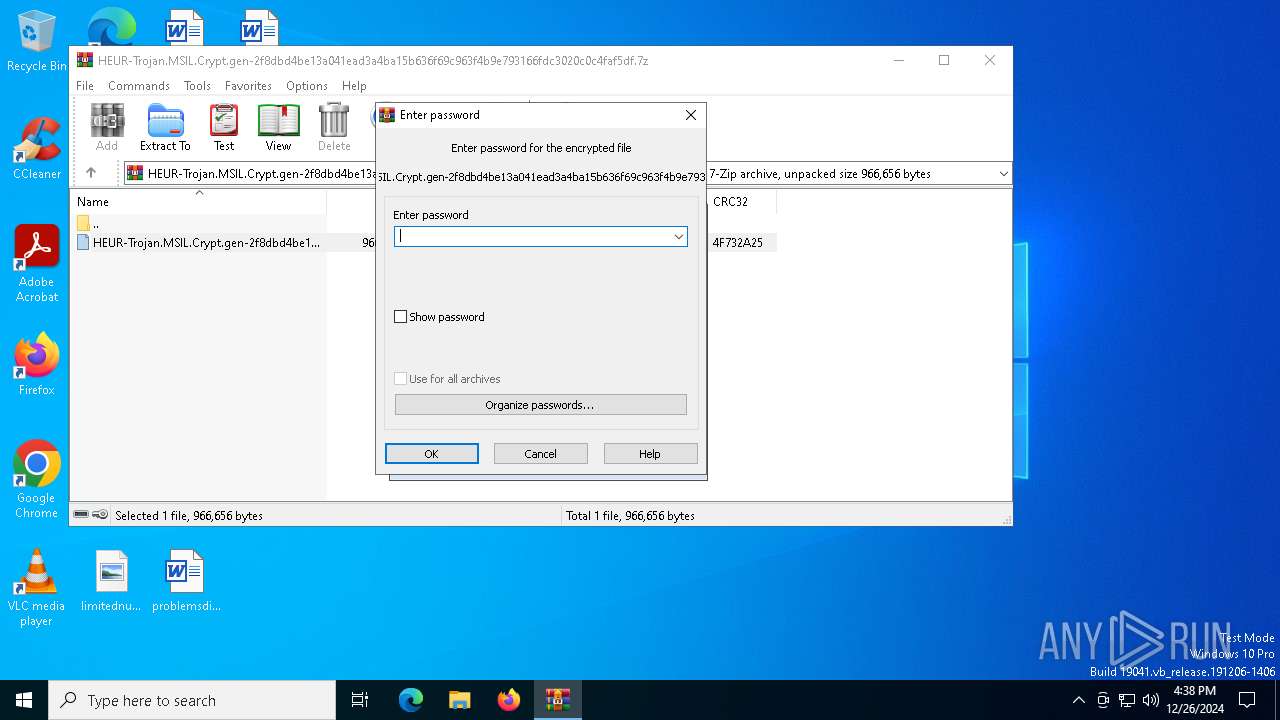
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
12
Suspicious files
168
Text files
114
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6172 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:BBB1C2E0F08321831DF9A6D91E7072BA | SHA256:12CE62FF481C8D88B4923DD53B962196E4FEFF80B36128D21D9FE2D1767760CF | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:BB9FC6B9025BDAD1CDD03608BF265F1B | SHA256:46B05675CAAD3B0164D13CB7140BBFE80EEB4B2715404A9DE76914E45723583D | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:AC3AD69258F2B969D9B5BCD4EA8FBA7B | SHA256:6CFBAD29C1C2668A9B9202C584F38D267090BD985DD3F5E86BFE9CF388FDE070 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
107
DNS requests
130
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6172 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6172 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6172 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6172 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6172 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6172 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.167:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.21.110.139:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
640 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7512 | New order.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
7512 | New order.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7512 | New order.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |