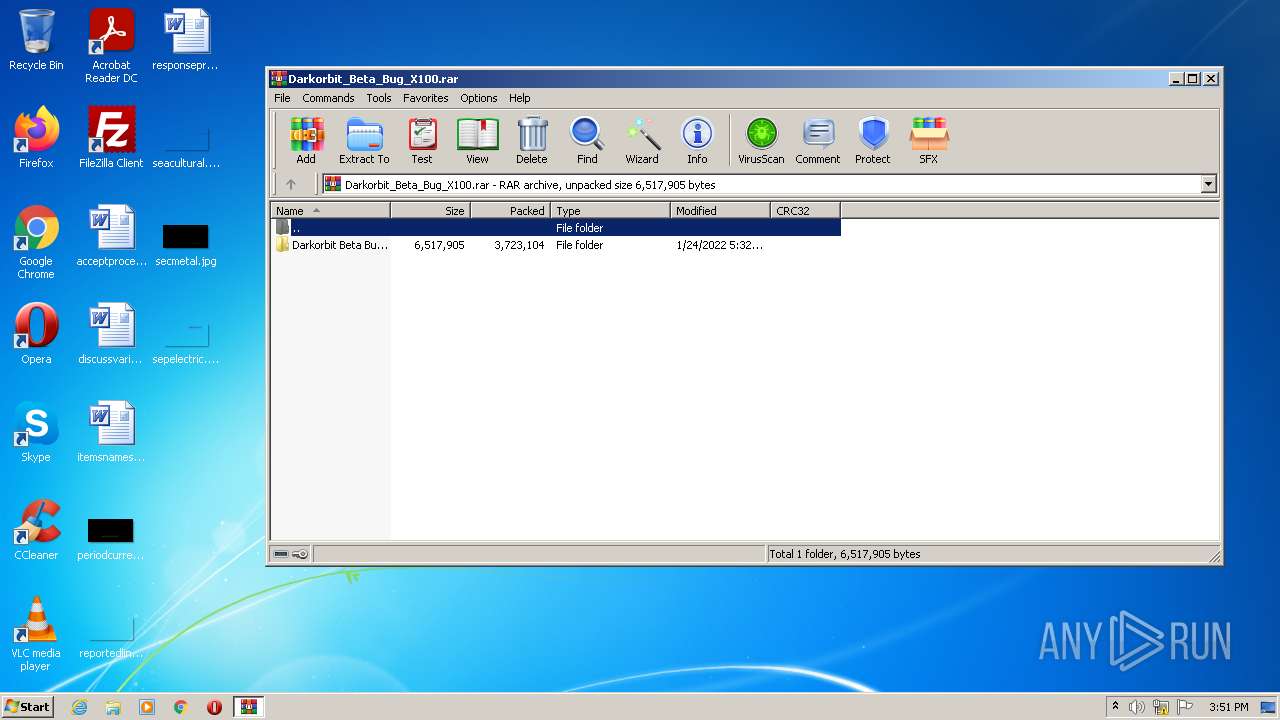
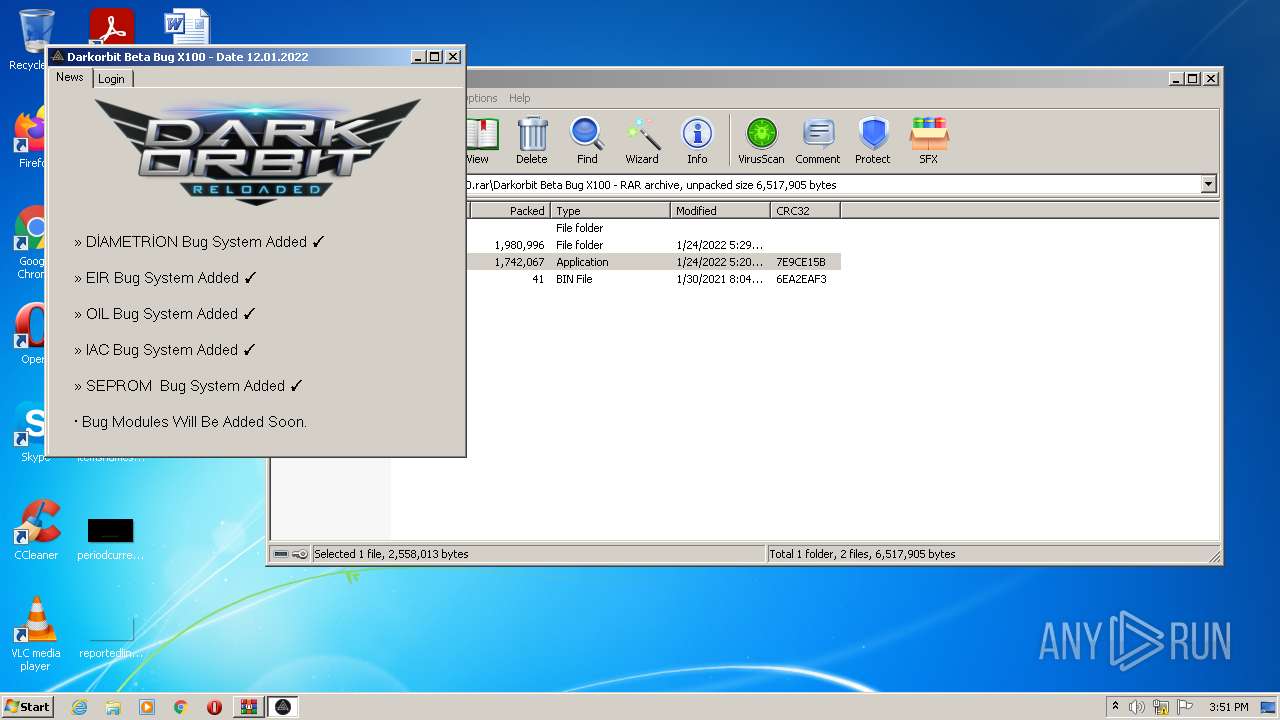
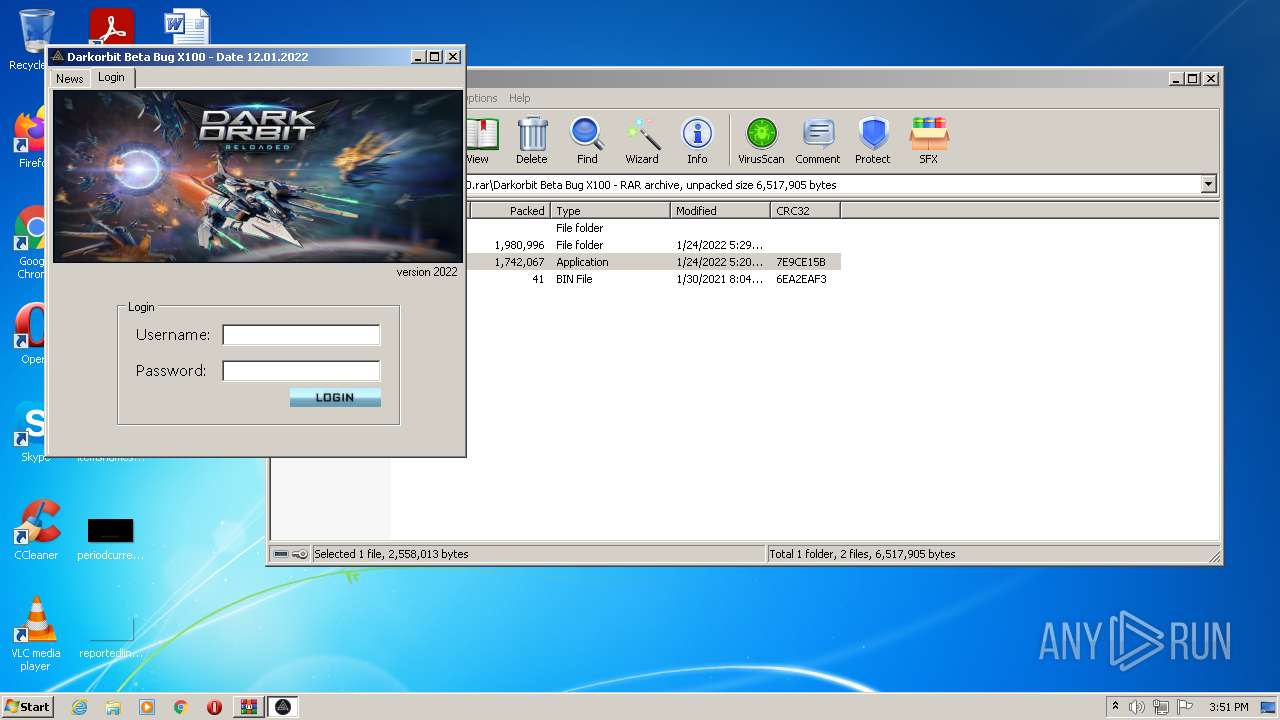
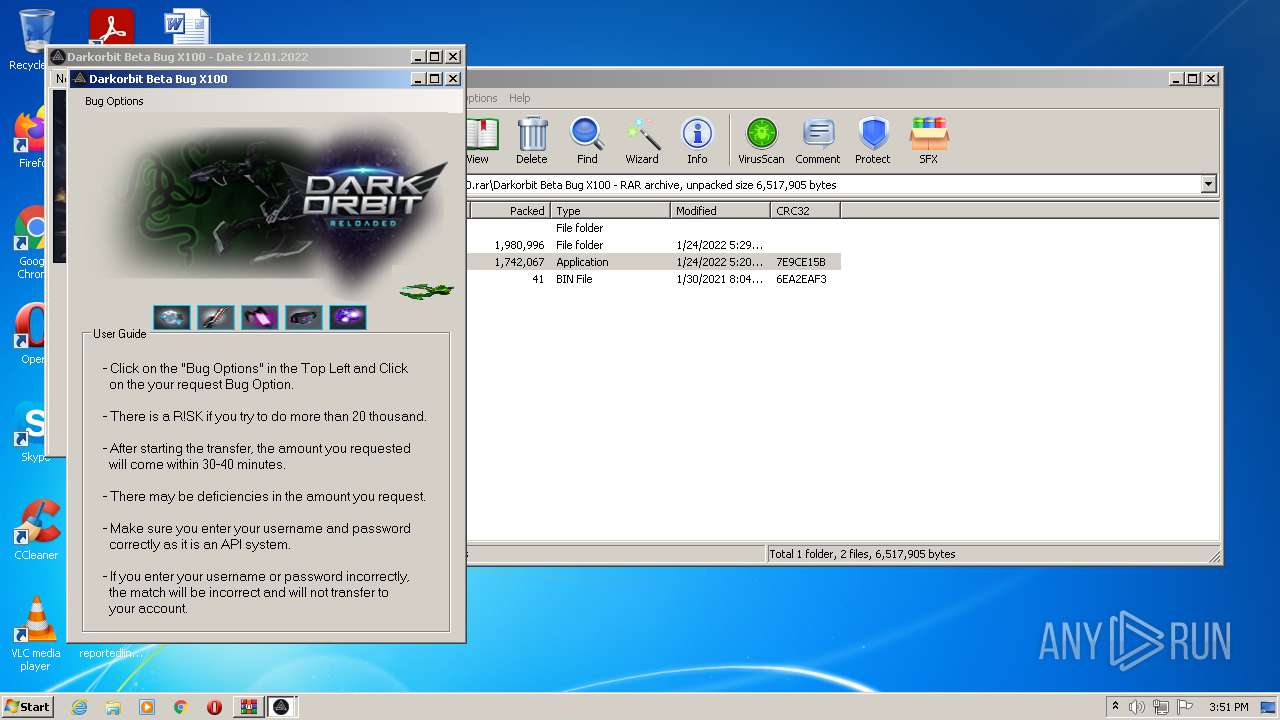
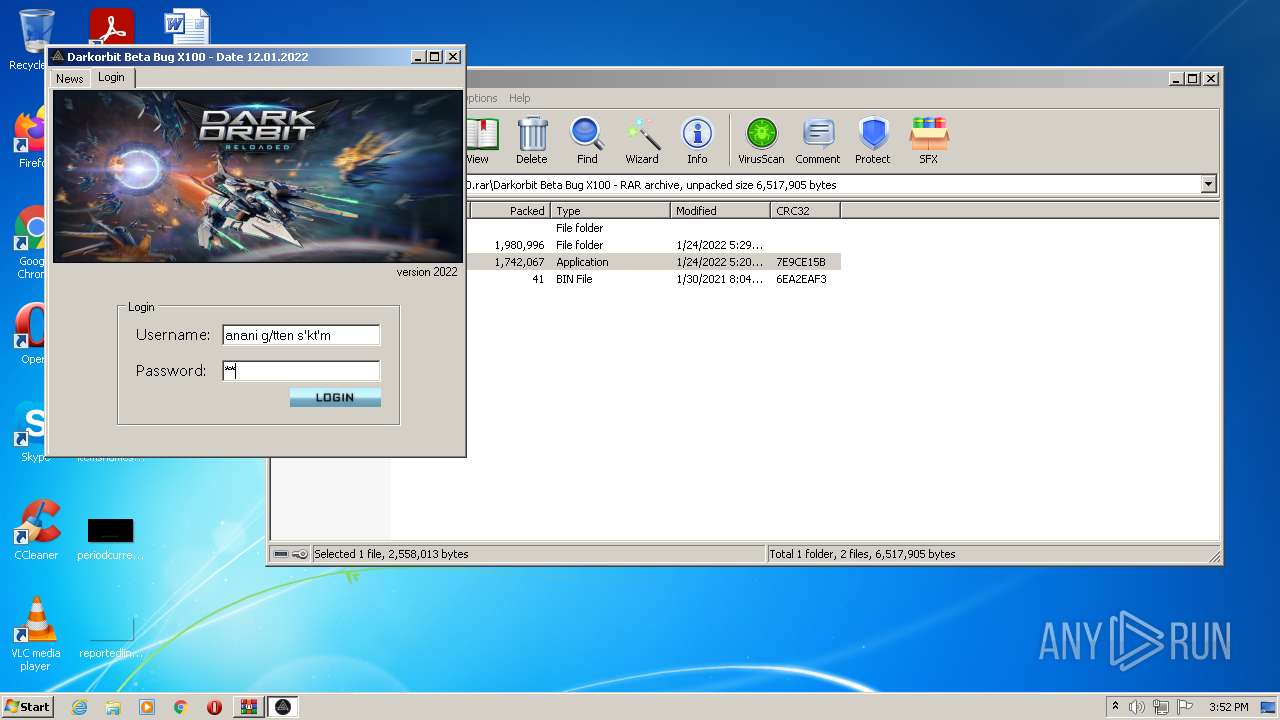
| File name: | Darkorbit_Beta_Bug_X100.rar |
| Full analysis: | https://app.any.run/tasks/98dafe4a-c9dc-4df9-97c6-7de06ccdcff7 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | January 25, 2022, 15:51:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C36741D1E4A393A2386D465043781856 |
| SHA1: | D8E7631EF4C6F508F9842036B224067C44614351 |
| SHA256: | C5E0F48DCD331EF03BA0BCF90462E191DD2A163497CF065C62AE5D47B8CB1AD2 |
| SSDEEP: | 98304:F4iUdLS4iUdLg4iUdLn4iUdL+4iUdL+4iUdLlenU06hb/Djoxqp:F4jS4jg4jn4j+4j+4jlerQTDWG |
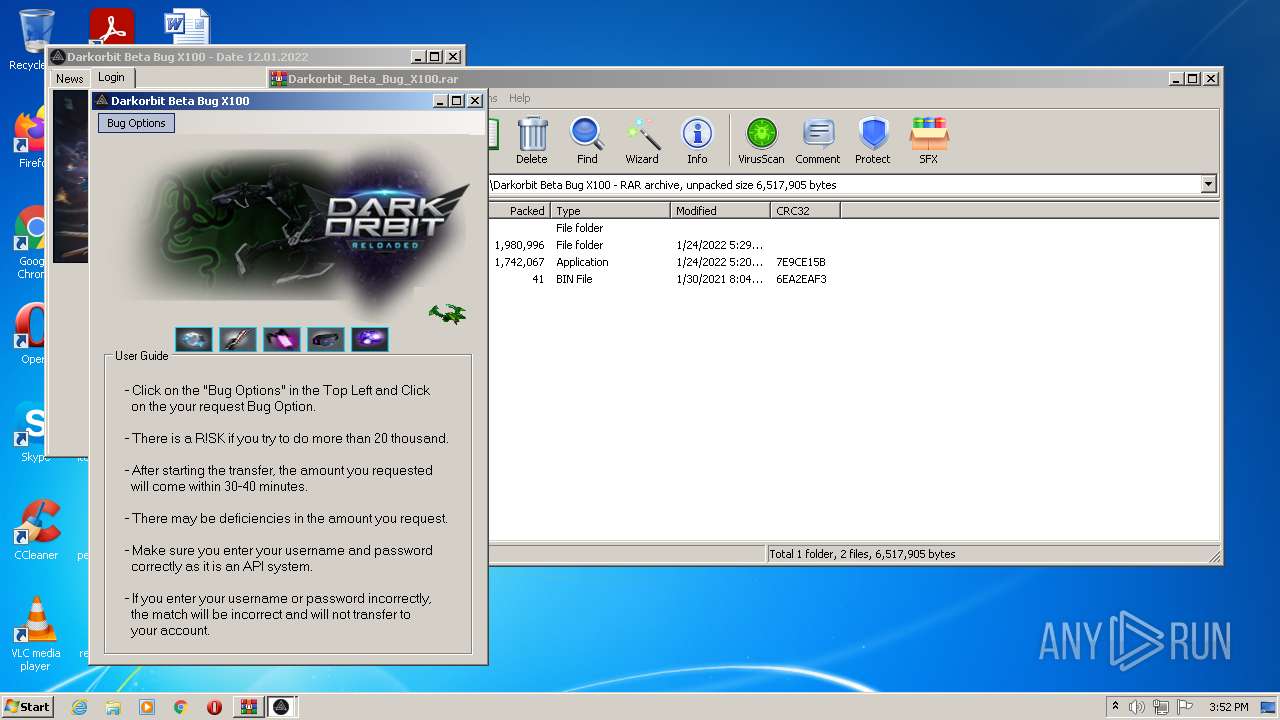
MALICIOUS
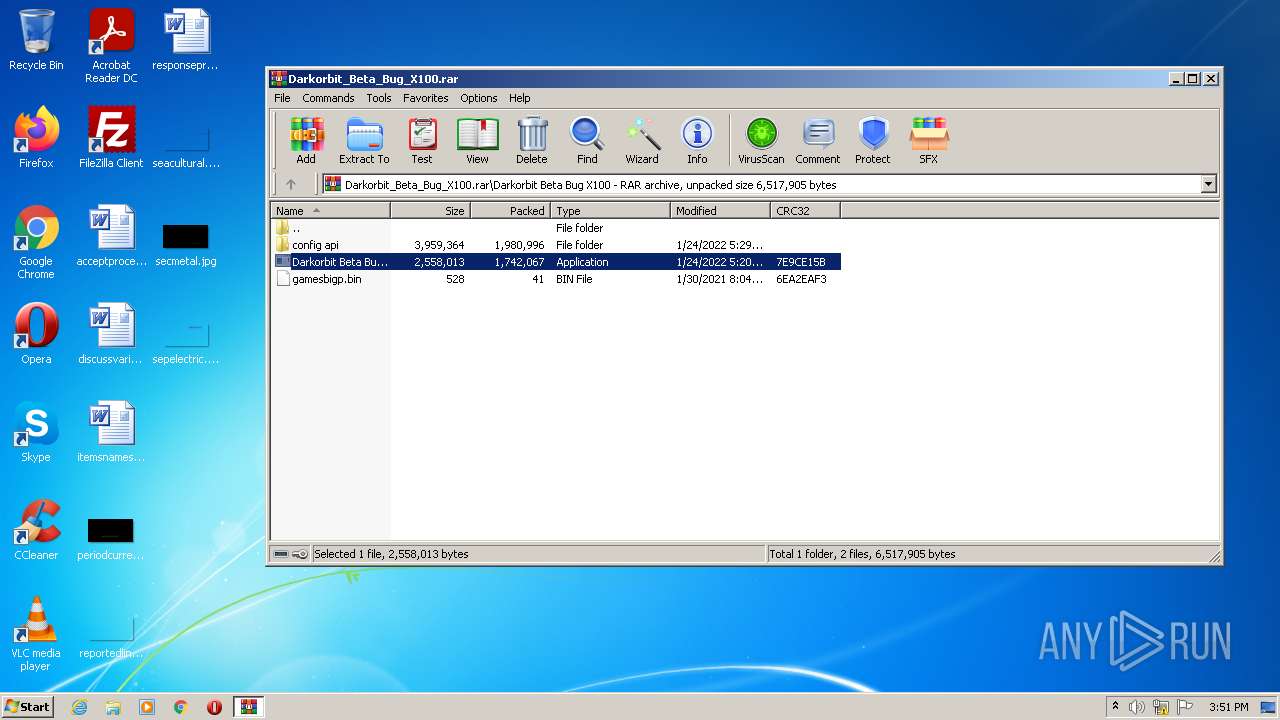
Application was dropped or rewritten from another process
- svchosts.exe (PID: 128)
- Darkorbit Beta Bug X100.exe (PID: 4028)
- Darkorbit Beta Bug X100.exe (PID: 3824)
- svchosts.exe (PID: 2212)
Drops/Copies Quasar RAT executable
- svchosts.exe (PID: 128)
- Darkorbit Beta Bug X100.exe (PID: 4028)
Drops executable file immediately after starts
- Darkorbit Beta Bug X100.exe (PID: 4028)
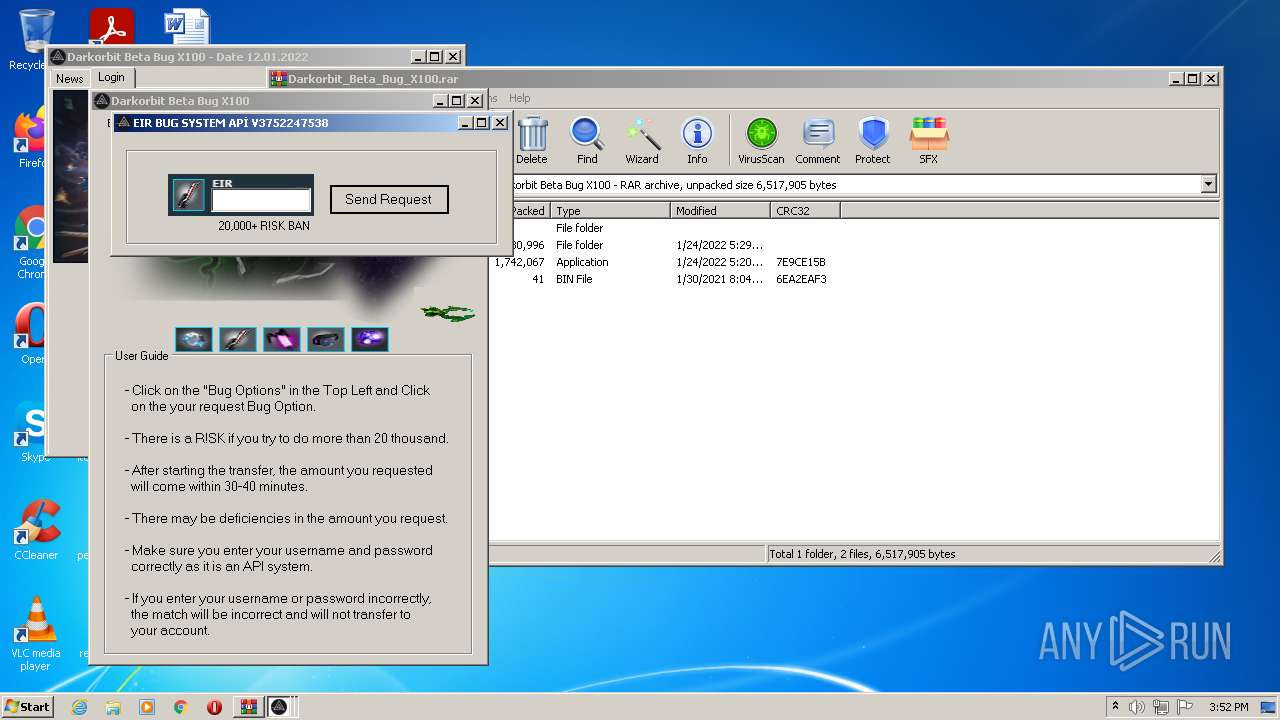
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3752)
- cmd.exe (PID: 3140)
- svchosts.exe (PID: 128)
- Darkorbit Beta Bug X100.exe (PID: 3824)
- svchosts.exe (PID: 2212)
- Darkorbit Beta Bug X100.exe (PID: 4028)
Reads the computer name
- WinRAR.exe (PID: 3752)
- svchosts.exe (PID: 128)
- Darkorbit Beta Bug X100.exe (PID: 3824)
- svchosts.exe (PID: 2212)
- Darkorbit Beta Bug X100.exe (PID: 4028)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3752)
- Darkorbit Beta Bug X100.exe (PID: 4028)
- svchosts.exe (PID: 128)
Drops a file that was compiled in debug mode
- Darkorbit Beta Bug X100.exe (PID: 4028)
- WinRAR.exe (PID: 3752)
Reads Environment values
- svchosts.exe (PID: 128)
- svchosts.exe (PID: 2212)
Creates files in the user directory
- svchosts.exe (PID: 128)
- svchosts.exe (PID: 2212)
Starts itself from another location
- svchosts.exe (PID: 128)
Checks for external IP
- svchosts.exe (PID: 128)
- svchosts.exe (PID: 2212)
Drops a file with a compile date too recent
- svchosts.exe (PID: 2212)
- svchosts.exe (PID: 128)
- Darkorbit Beta Bug X100.exe (PID: 4028)
INFO
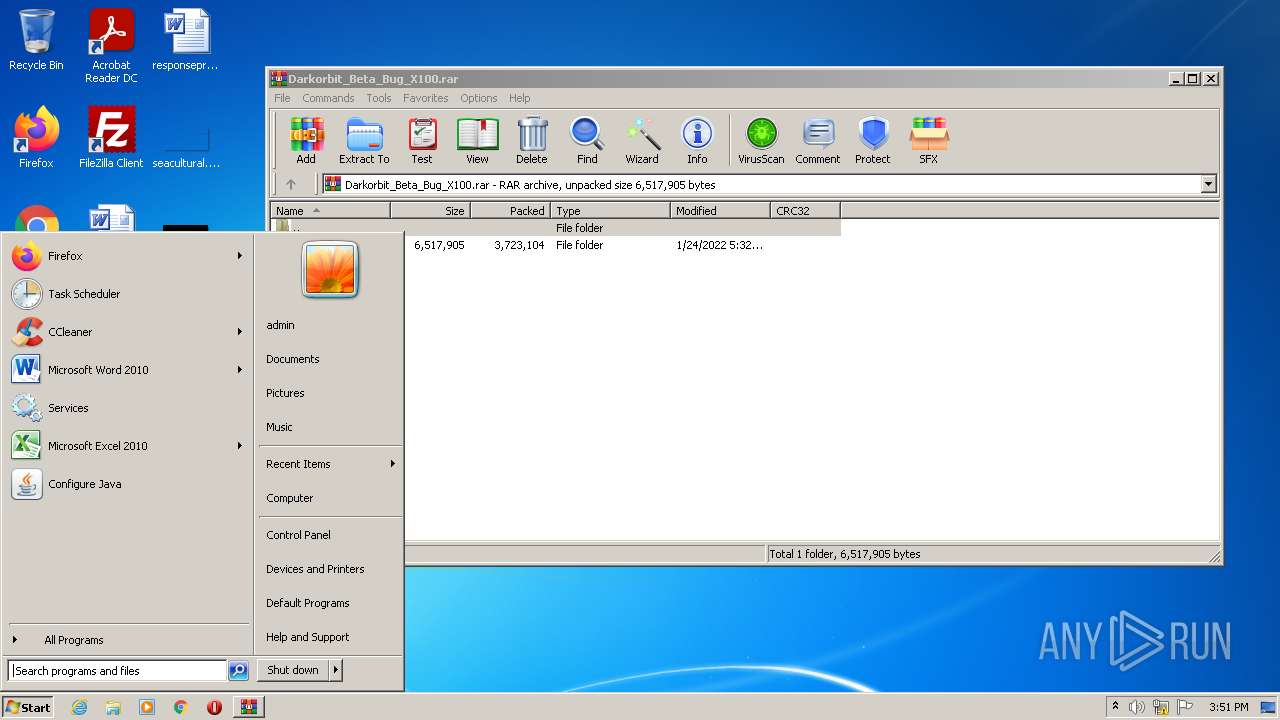
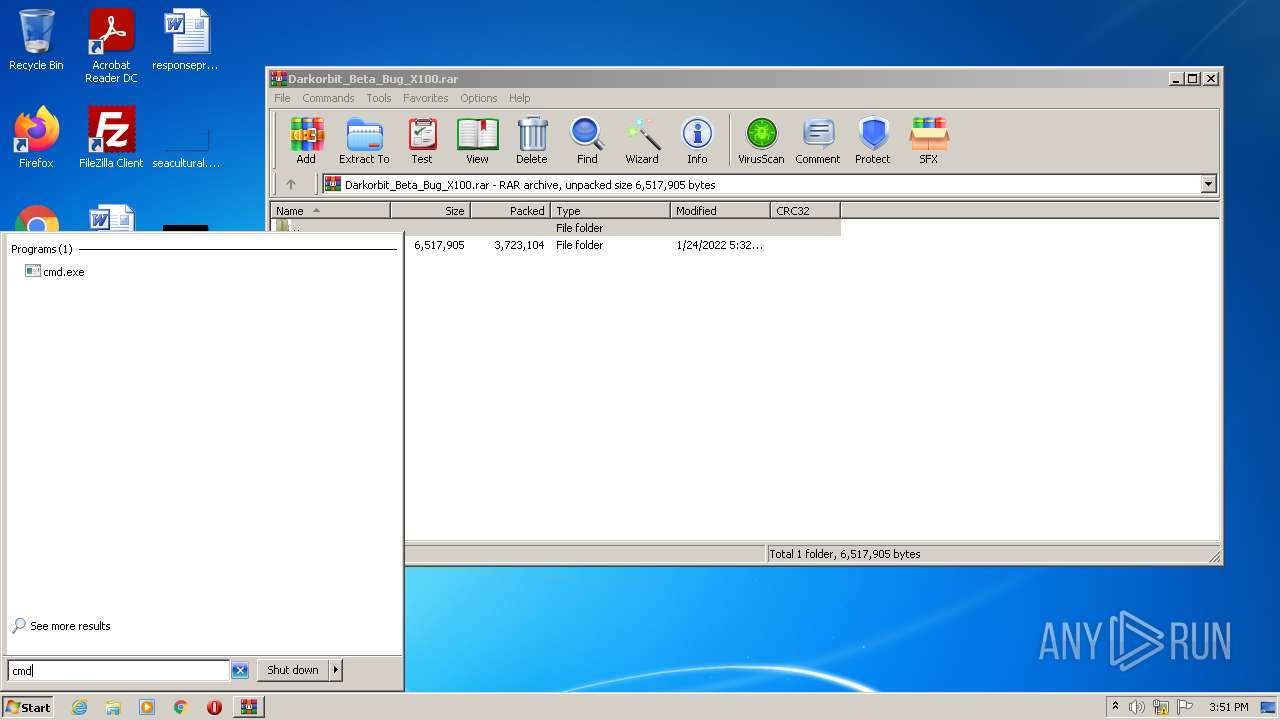
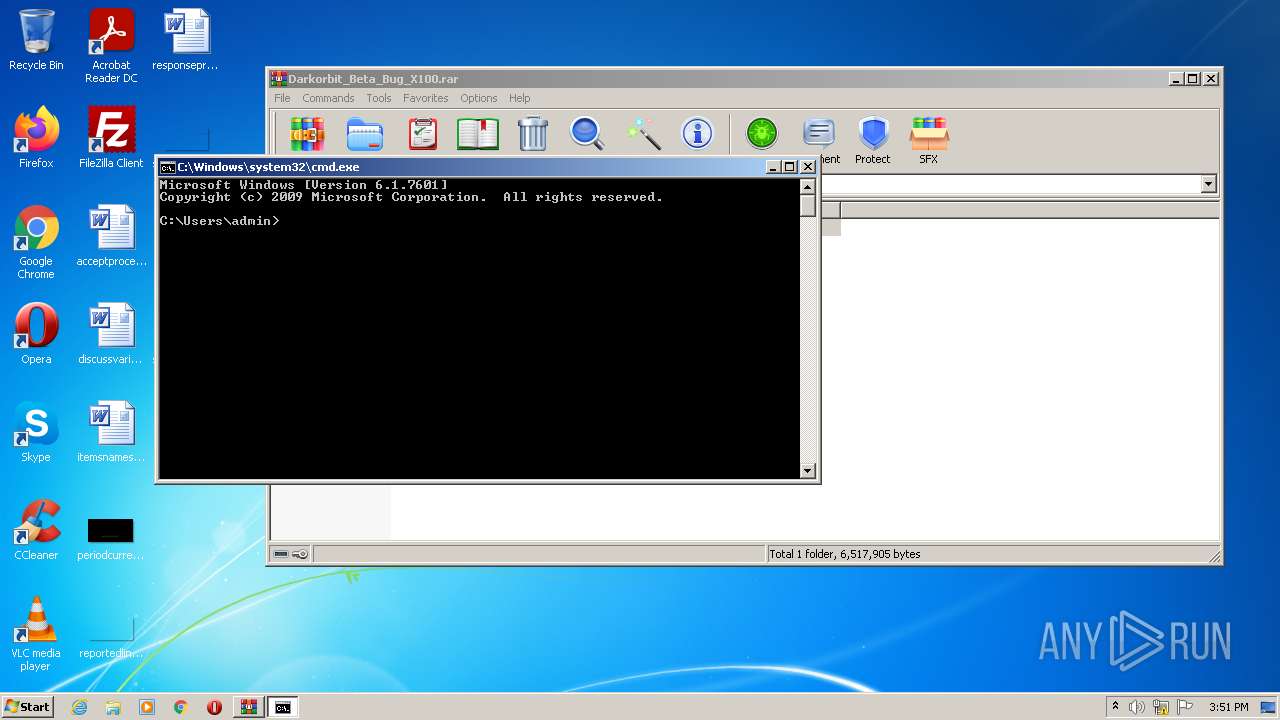
Manual execution by user
- cmd.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\svchosts.exe" | C:\Users\admin\AppData\Local\Temp\svchosts.exe | Darkorbit Beta Bug X100.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Roaming\svchosts\svchosts.exe" | C:\Users\admin\AppData\Roaming\svchosts\svchosts.exe | svchosts.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
| 3140 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
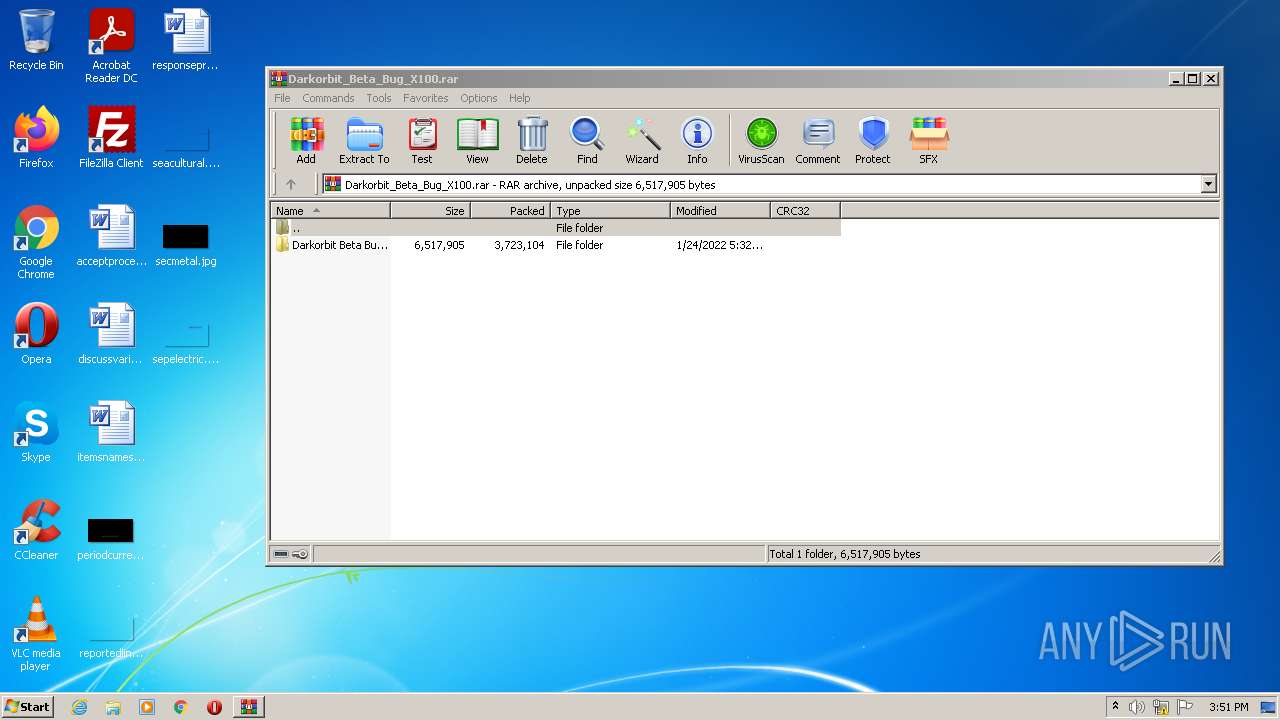
| 3752 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Darkorbit_Beta_Bug_X100.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3824 | "C:\Users\admin\AppData\Local\Temp\Darkorbit Beta Bug X100.exe" | C:\Users\admin\AppData\Local\Temp\Darkorbit Beta Bug X100.exe | — | Darkorbit Beta Bug X100.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Darkorbit Beta Bug X100 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4028 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\Darkorbit Beta Bug X100.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\Darkorbit Beta Bug X100.exe | WinRAR.exe | ||||||||||||
User: admin Company: Byte Technologies Integrity Level: MEDIUM Description: File Exit code: 0 Version: 3.6.1.1 Modules
| |||||||||||||||
Total events
3 048
Read events
3 010
Write events
38
Delete events
0
Modification events
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Darkorbit_Beta_Bug_X100.rar | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
2
Text files
0
Unknown types
0
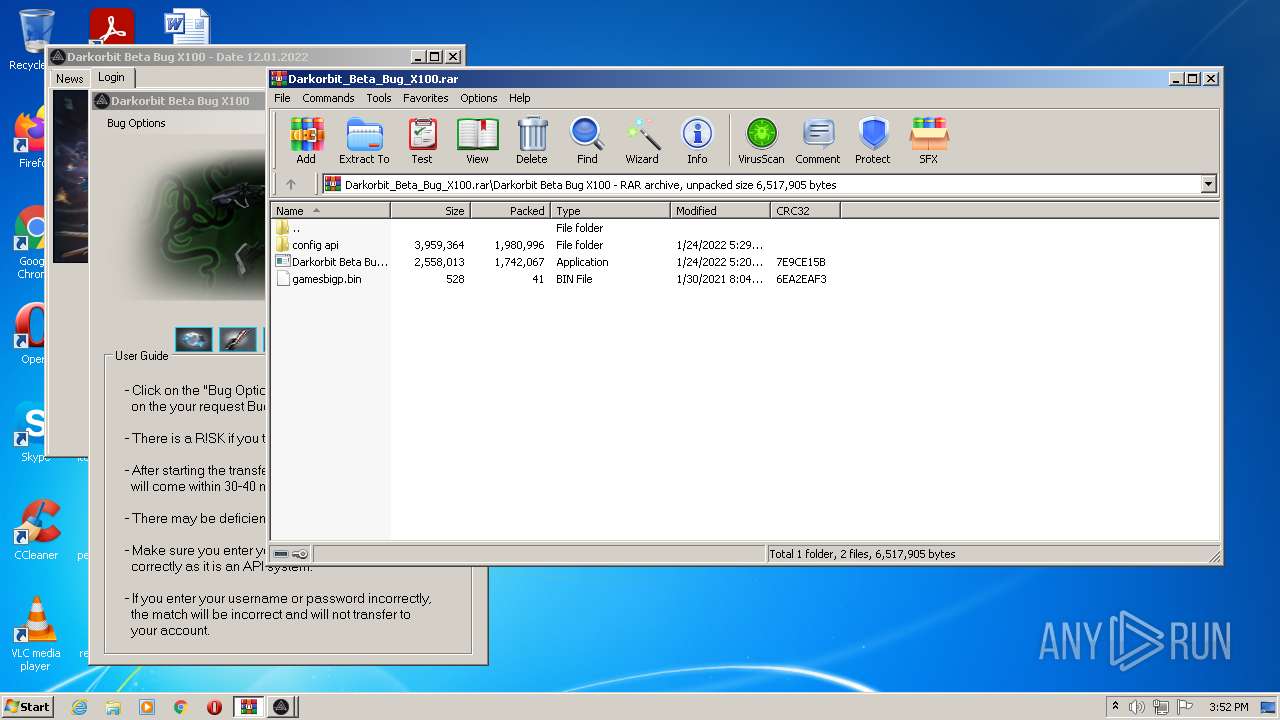
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | svchosts.exe | C:\Users\admin\AppData\Roaming\Logs\01-25-2022 | binary | |
MD5:— | SHA256:— | |||
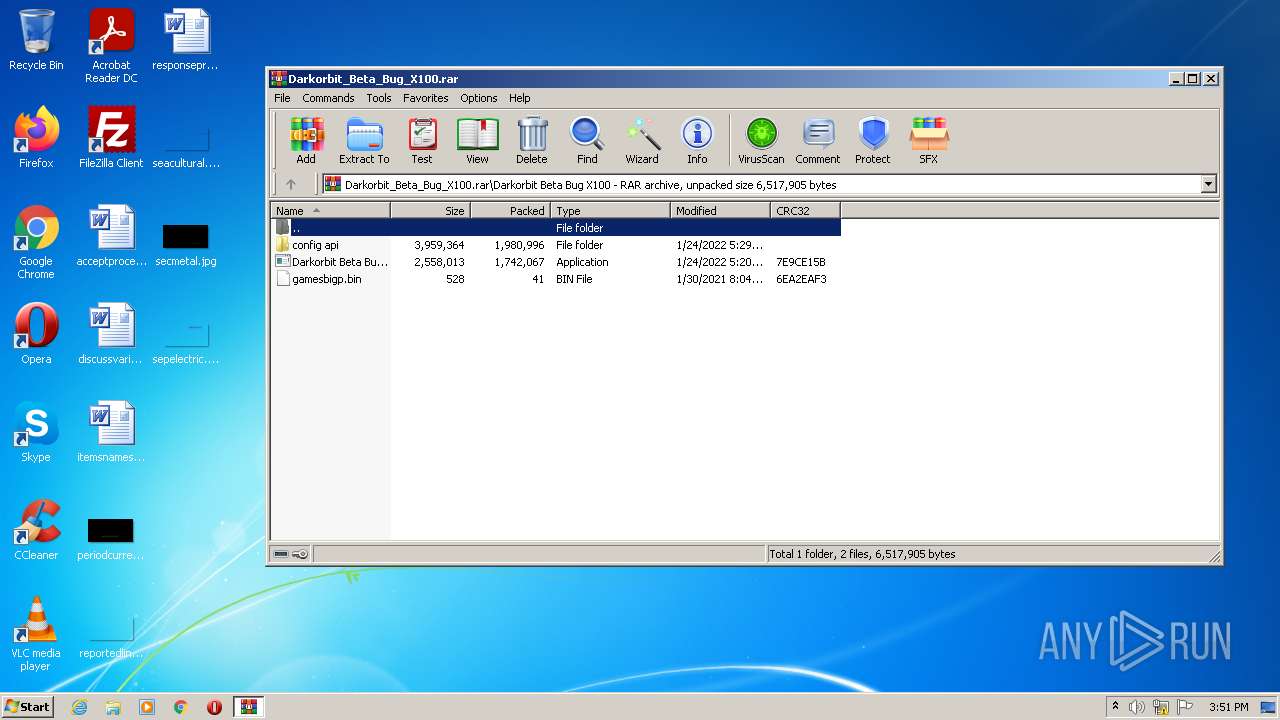
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\Darkorbit Beta Bug X100.exe | executable | |
MD5:D721C42C7CD5DEBFAA8BF57AD8134E1E | SHA256:41F49DFACDDEE78AF4334594F3BC18EFF66EF780306A3F24DFAEAD489A874CFC | |||
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\gamesbigp.bin | binary | |
MD5:B1B8BE1914280C0043B1C95F07927219 | SHA256:D7A9EACEA62AAACD9BEAB1EC1E5EA3729B03B4E7A41C1A8D62830C3AF0A70982 | |||
| 128 | svchosts.exe | C:\Users\admin\AppData\Roaming\svchosts\svchosts.exe | executable | |
MD5:0EA7B250AFA0A67ED55485A0E12CC1CE | SHA256:FB6593CA3E345C14B2FAED44D1DC084456C67354CBAC32EFA73908C6AA8ABE04 | |||
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\config api\darkorbit game | executable | |
MD5:D6208861D684A14B9EDB8679D3AAD046 | SHA256:2C786EA04265B43DDC01309C9BFADFE2E62825D8466941D311A6E574342EBF32 | |||
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\config api\eir | executable | |
MD5:D6208861D684A14B9EDB8679D3AAD046 | SHA256:2C786EA04265B43DDC01309C9BFADFE2E62825D8466941D311A6E574342EBF32 | |||
| 4028 | Darkorbit Beta Bug X100.exe | C:\Users\admin\AppData\Local\Temp\svchosts.exe | executable | |
MD5:0EA7B250AFA0A67ED55485A0E12CC1CE | SHA256:FB6593CA3E345C14B2FAED44D1DC084456C67354CBAC32EFA73908C6AA8ABE04 | |||
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\config api\iac | executable | |
MD5:D6208861D684A14B9EDB8679D3AAD046 | SHA256:2C786EA04265B43DDC01309C9BFADFE2E62825D8466941D311A6E574342EBF32 | |||
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\config api\oil | executable | |
MD5:D6208861D684A14B9EDB8679D3AAD046 | SHA256:2C786EA04265B43DDC01309C9BFADFE2E62825D8466941D311A6E574342EBF32 | |||
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3752.5595\Darkorbit Beta Bug X100\config api\seprom | executable | |
MD5:D6208861D684A14B9EDB8679D3AAD046 | SHA256:2C786EA04265B43DDC01309C9BFADFE2E62825D8466941D311A6E574342EBF32 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2212 | svchosts.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | binary | 301 b | malicious |
128 | svchosts.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | binary | 301 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
128 | svchosts.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
2212 | svchosts.exe | 78.183.228.154:1604 | yedekscan.duckdns.org | Turk Telekom | TR | unknown |
2212 | svchosts.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
yedekscan.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
128 | svchosts.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
128 | svchosts.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2212 | svchosts.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2212 | svchosts.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2 ETPRO signatures available at the full report