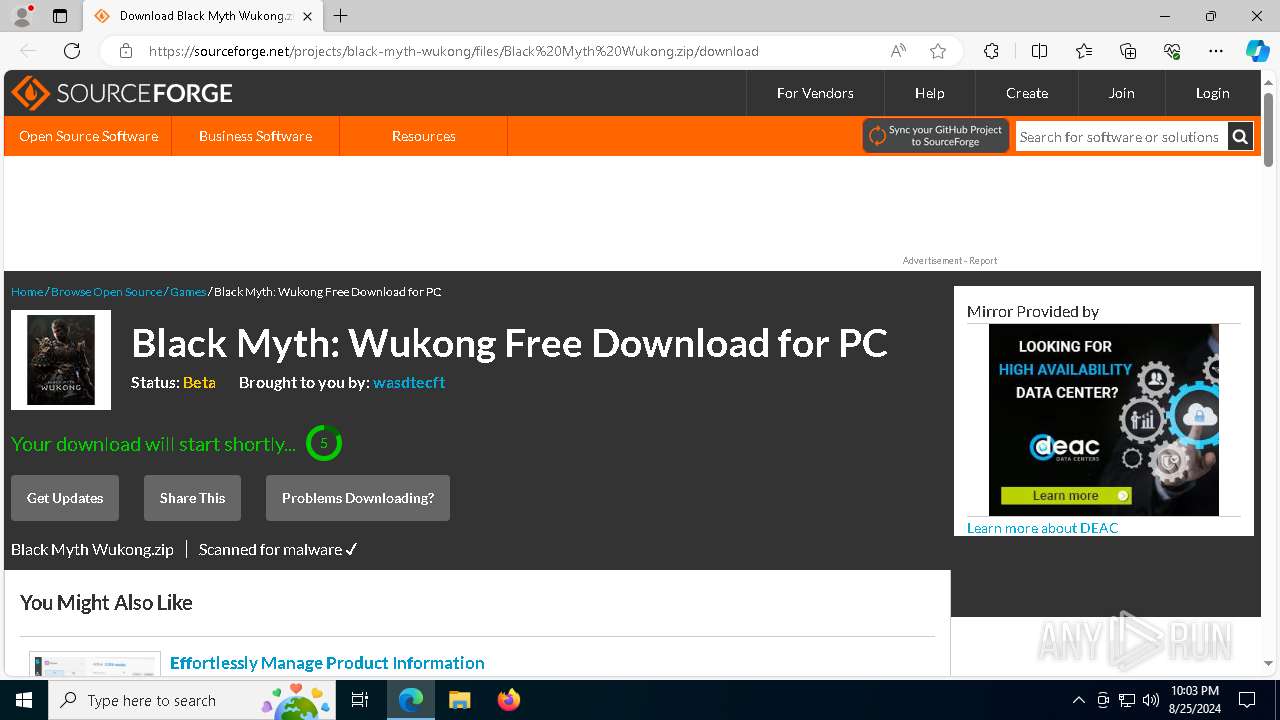
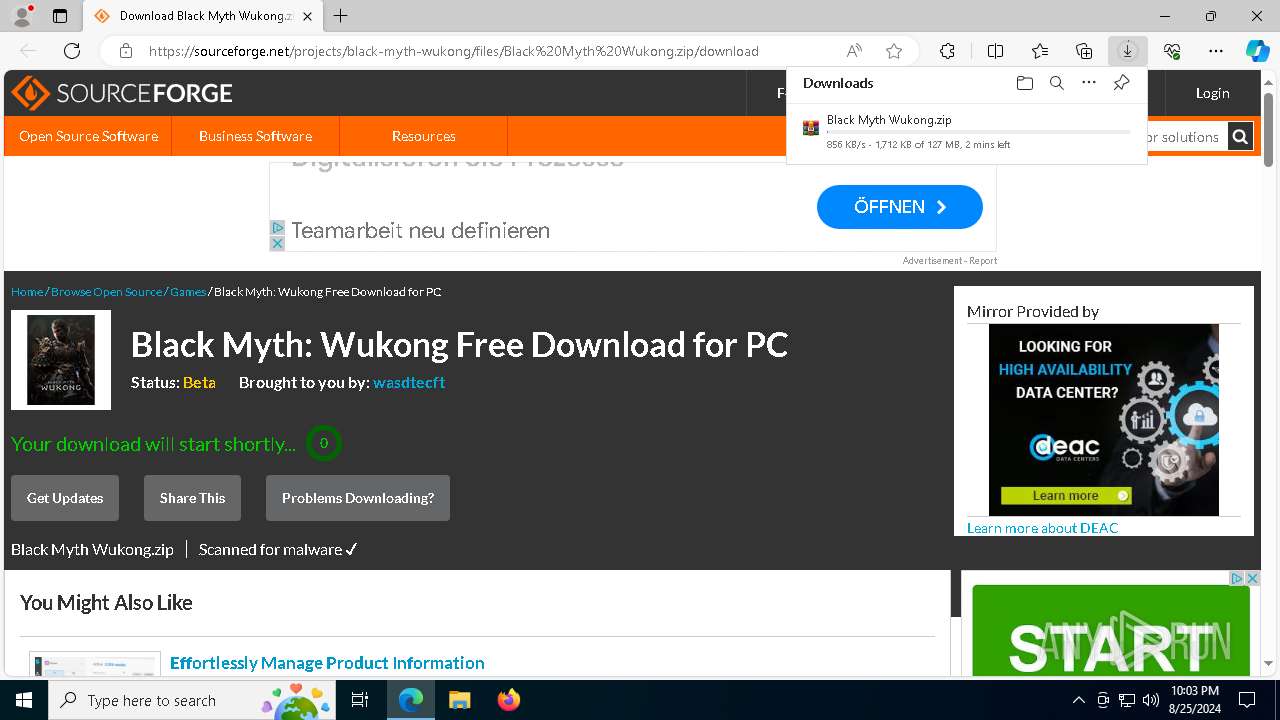
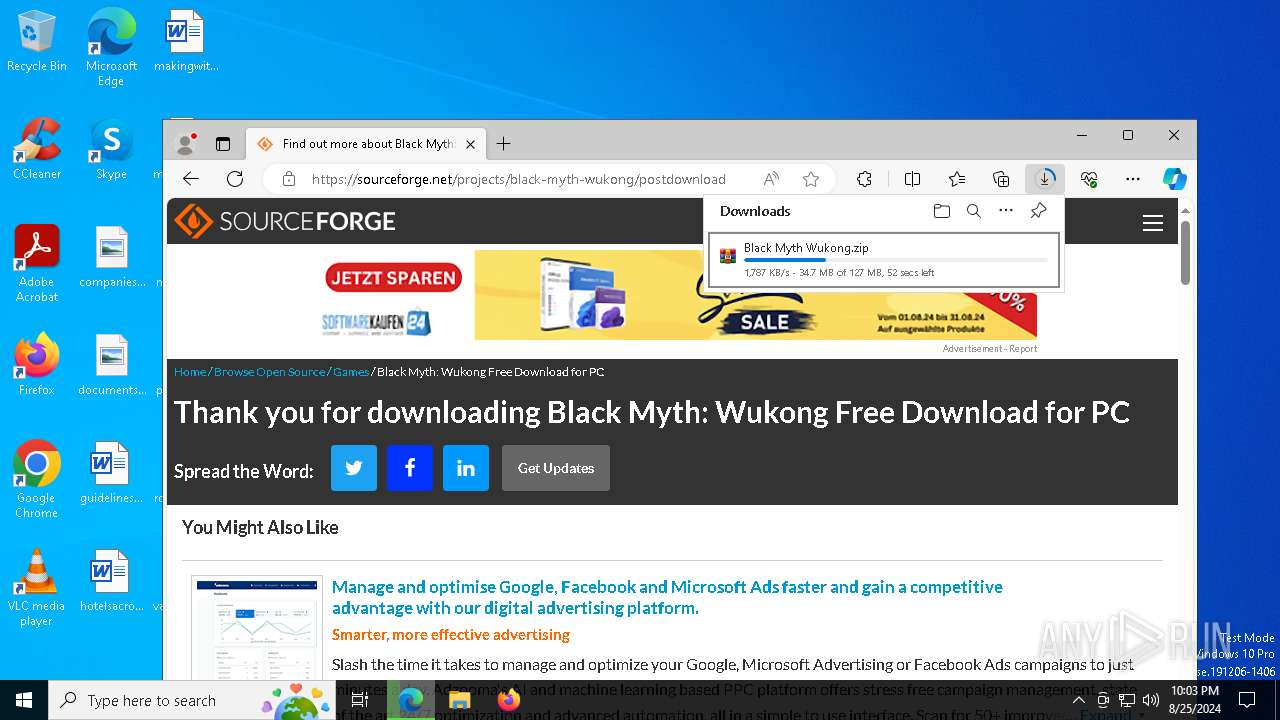
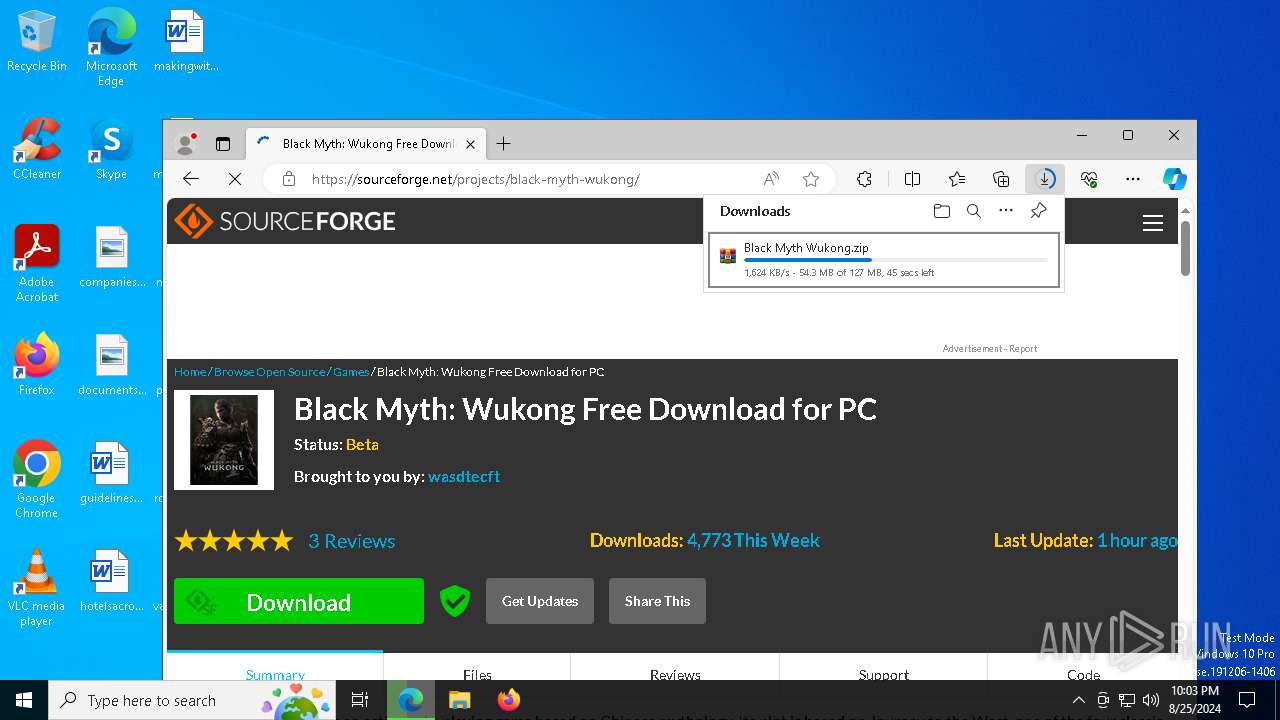
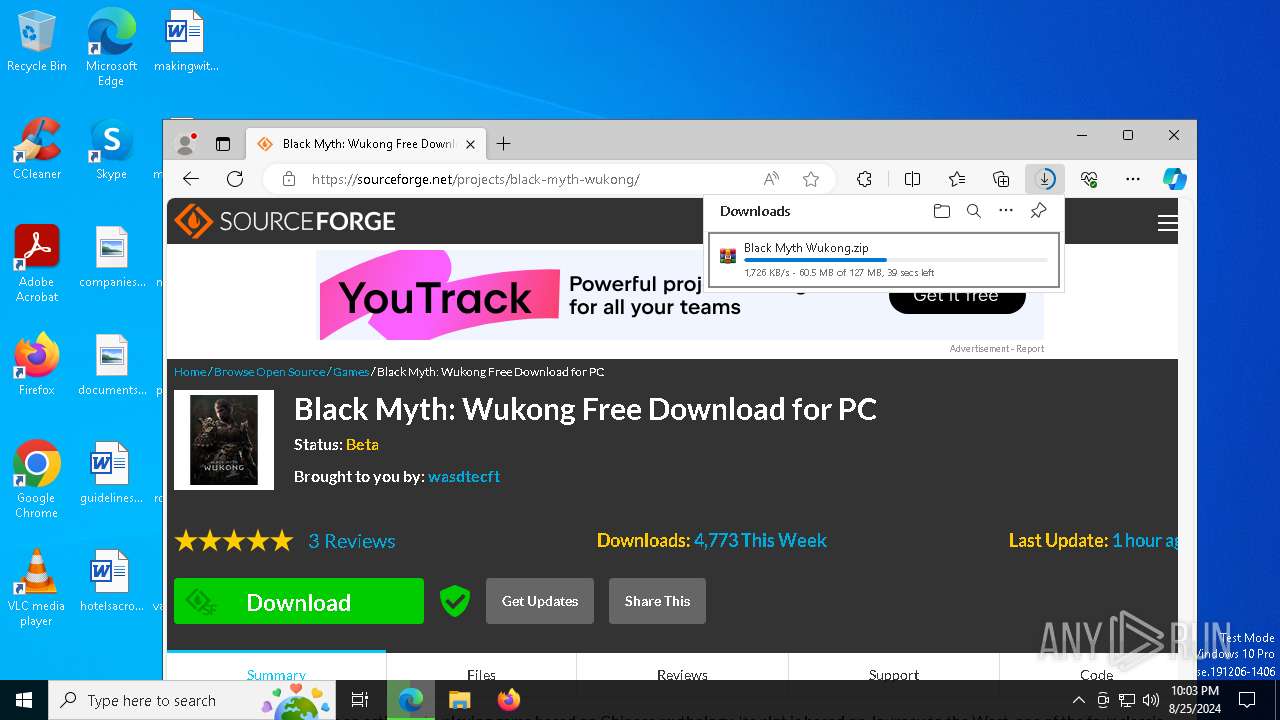
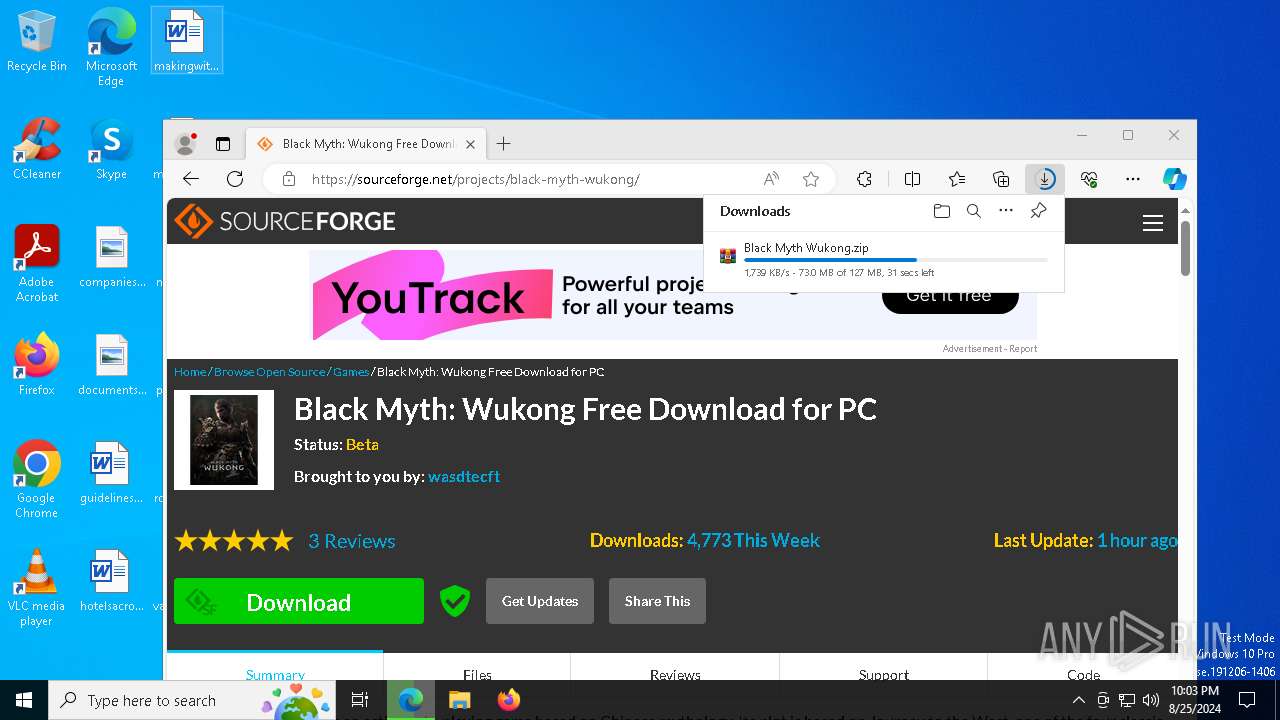
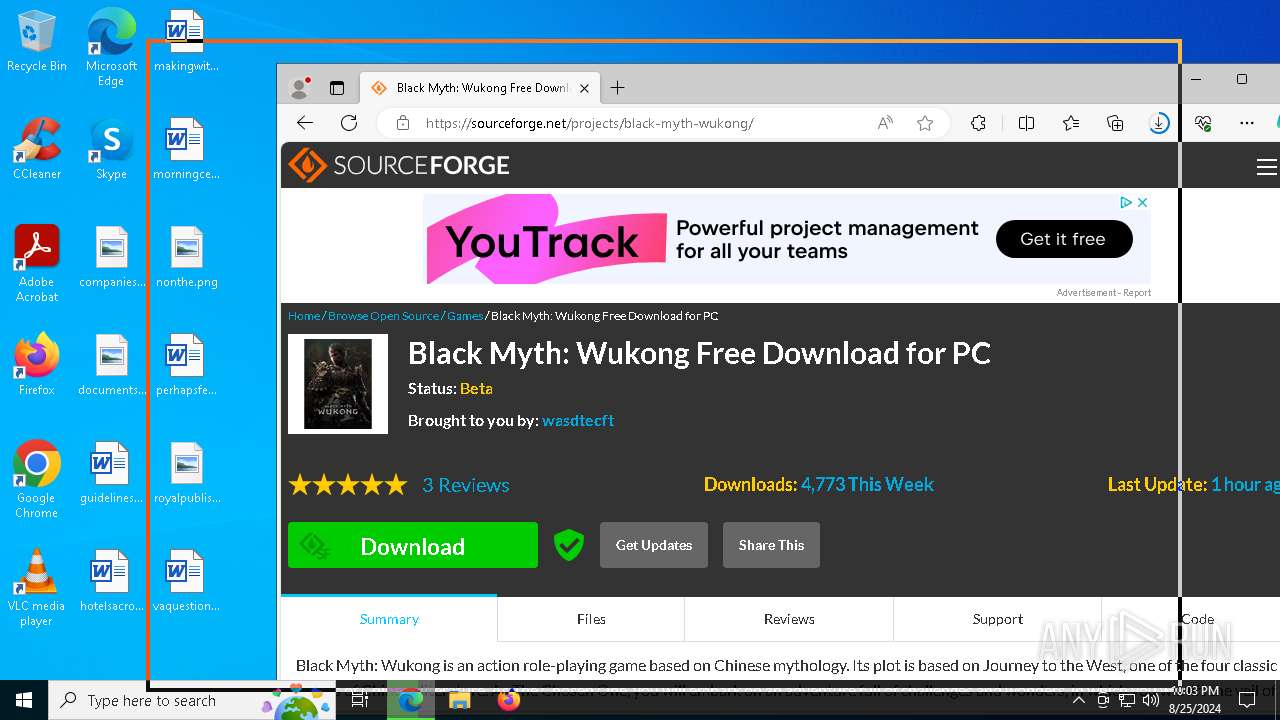
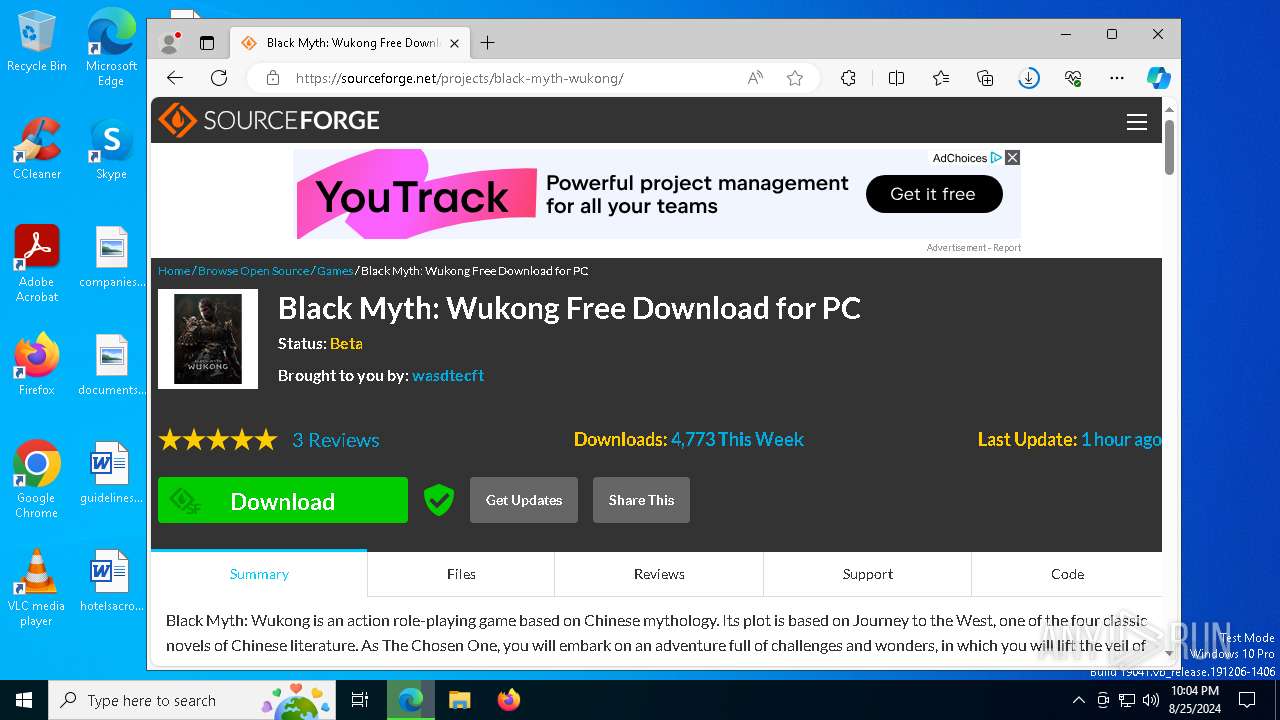
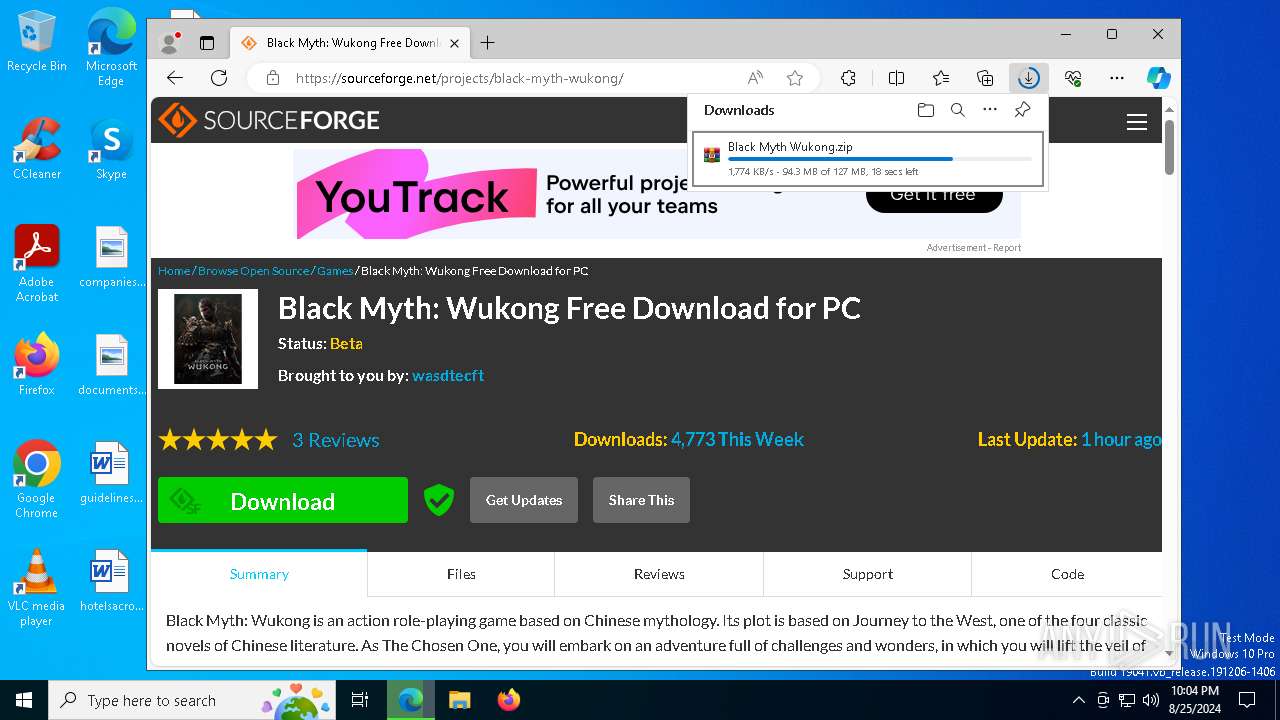
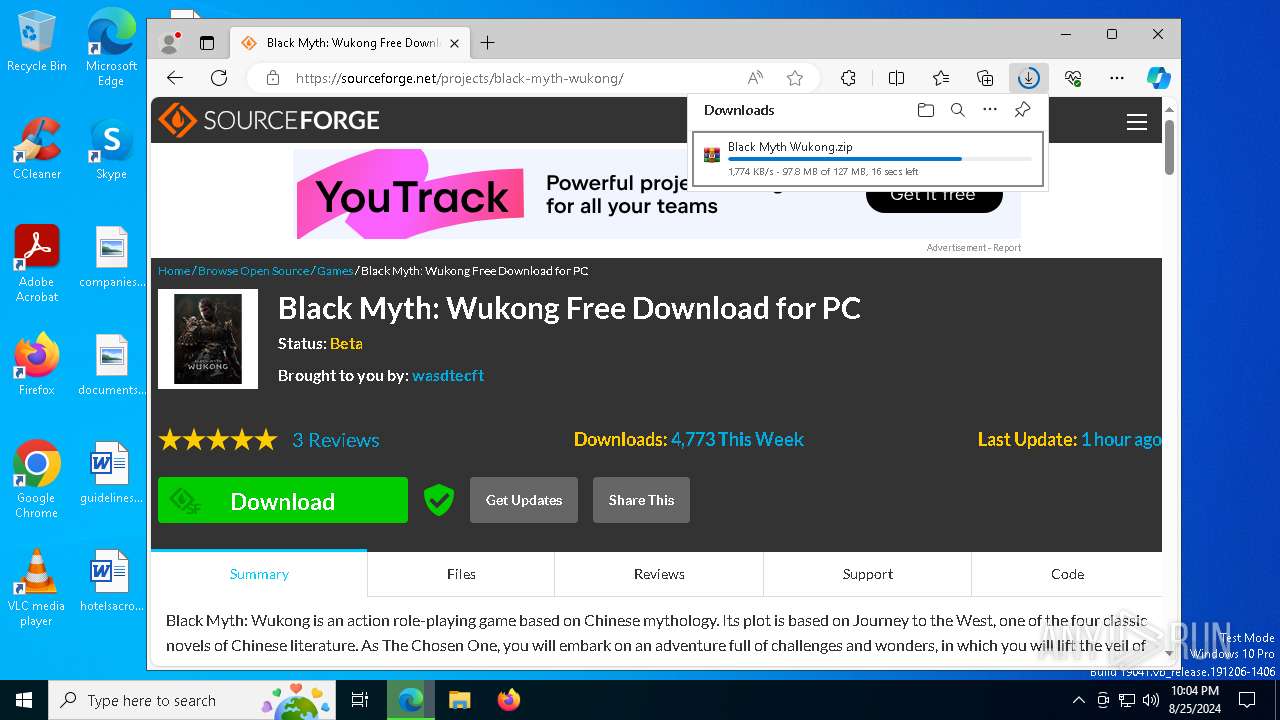
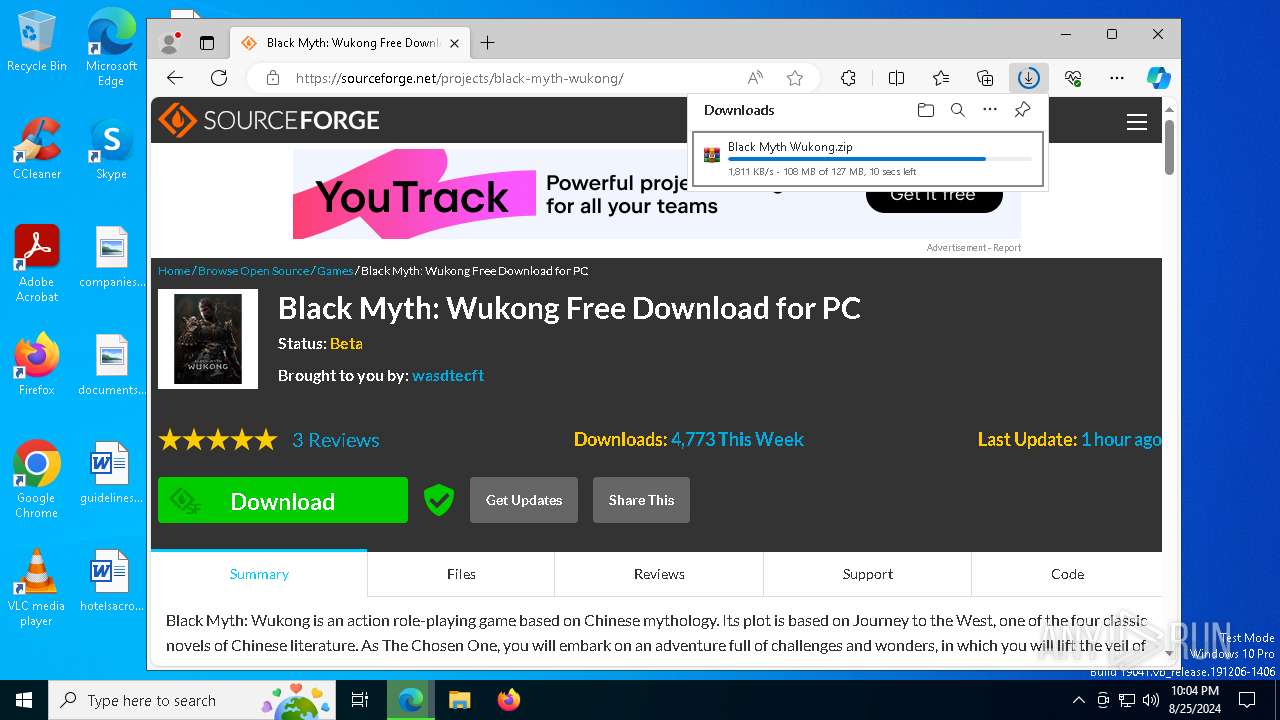
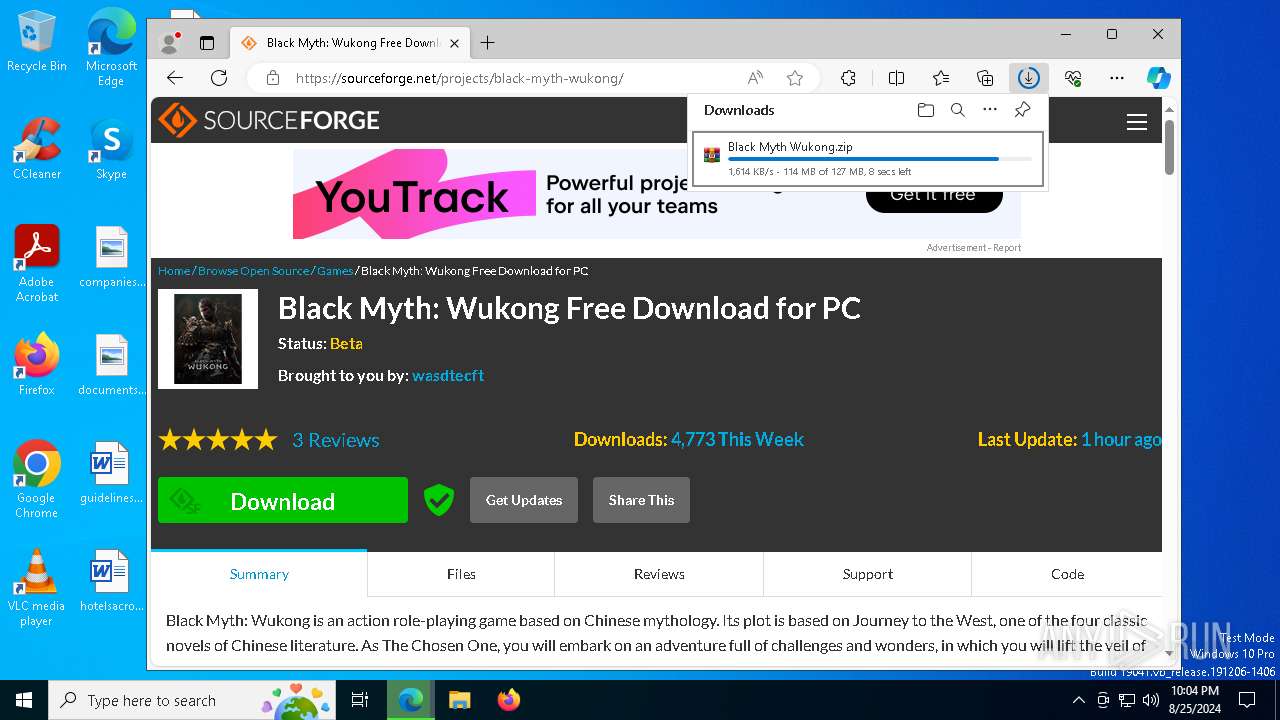
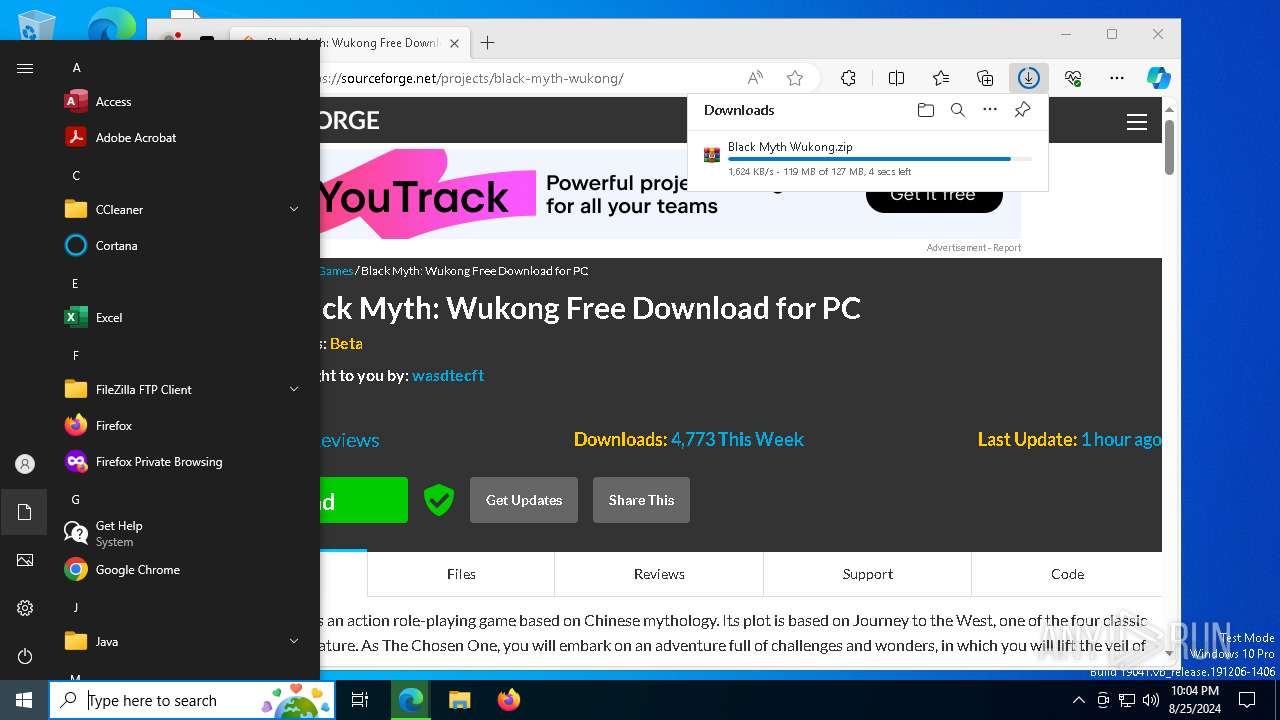
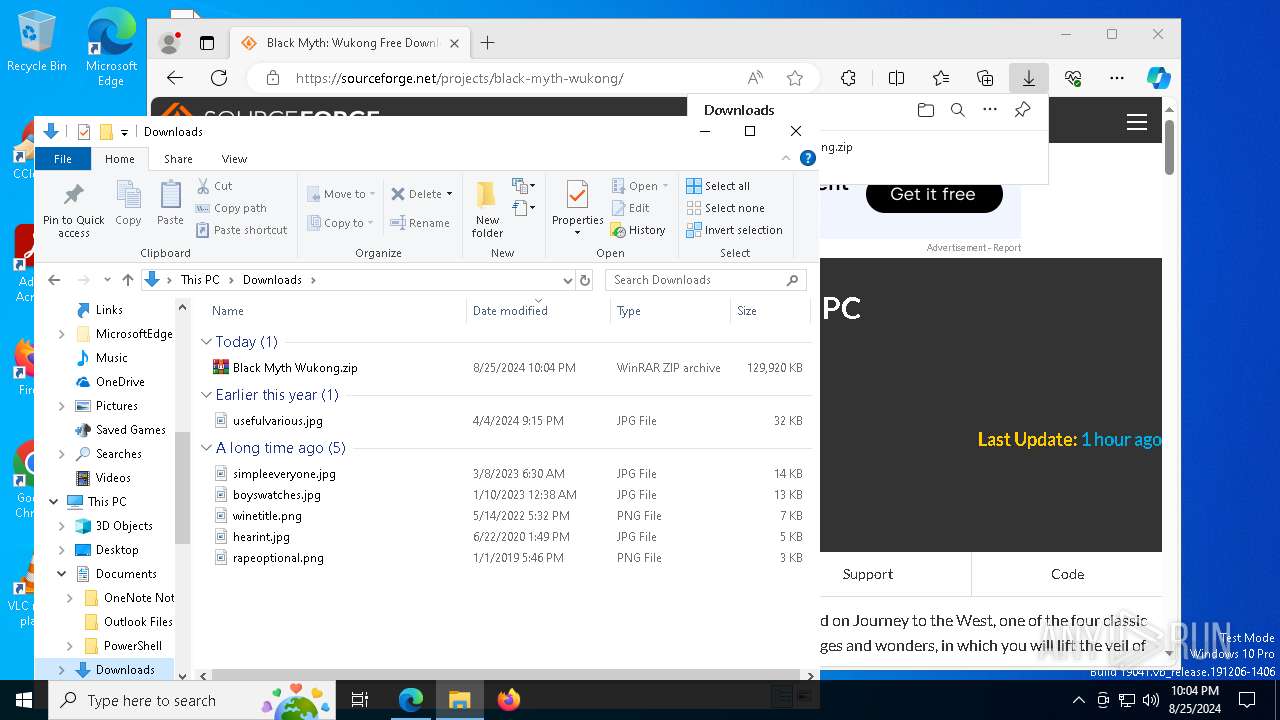
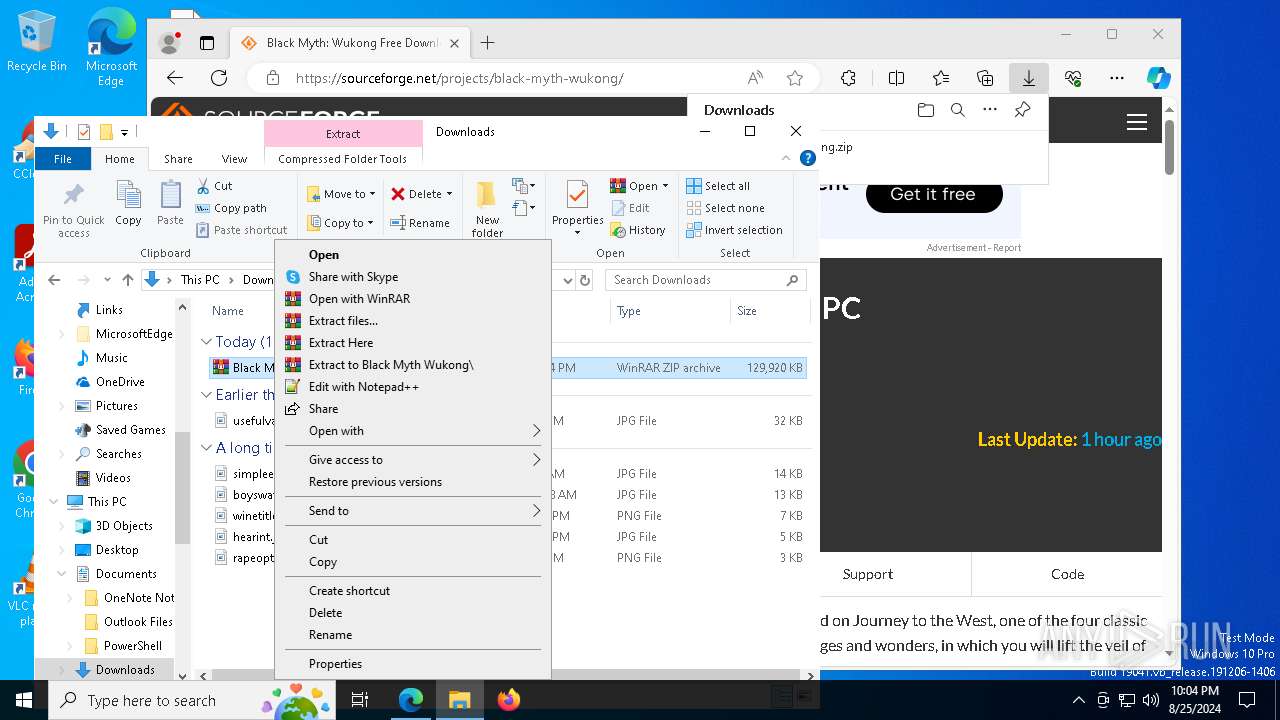
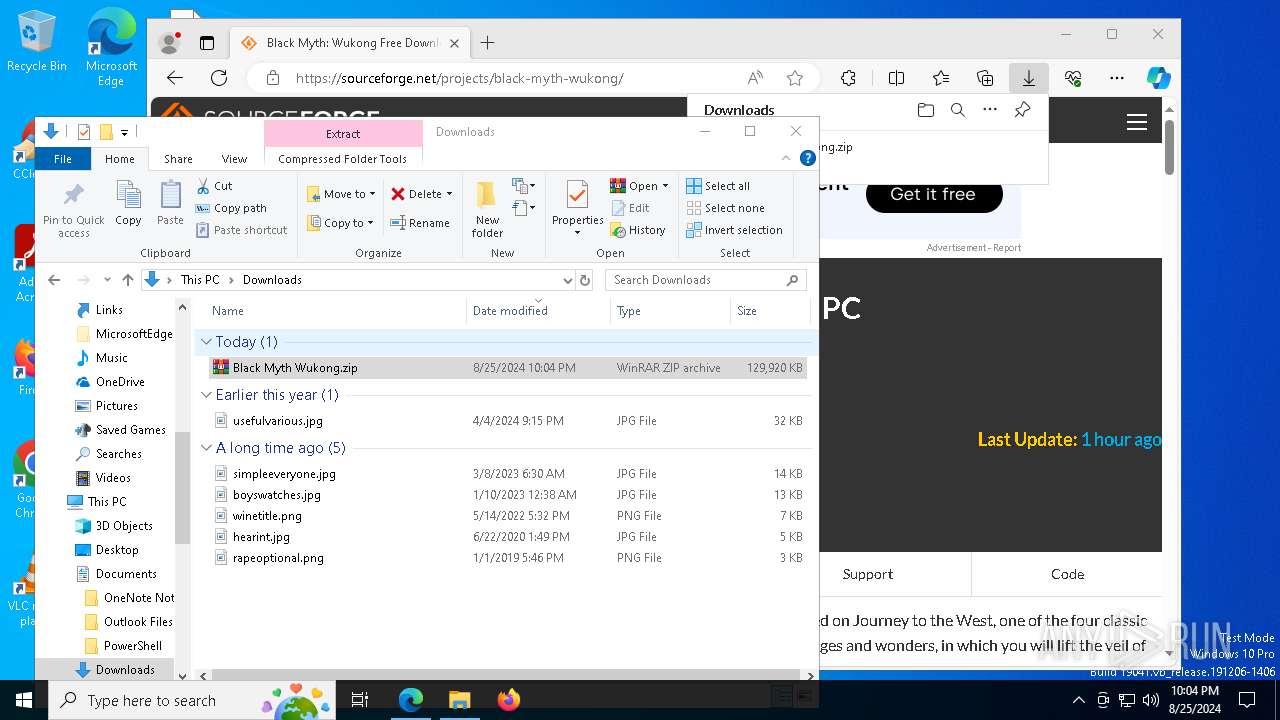
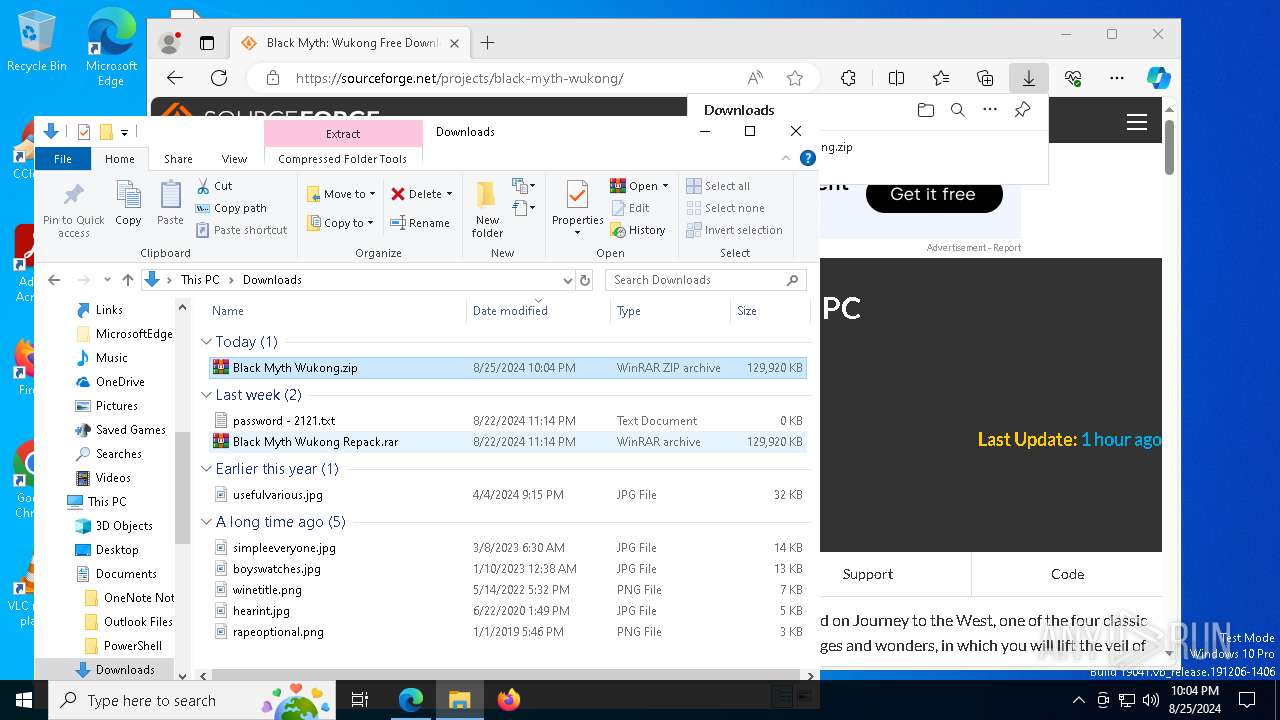
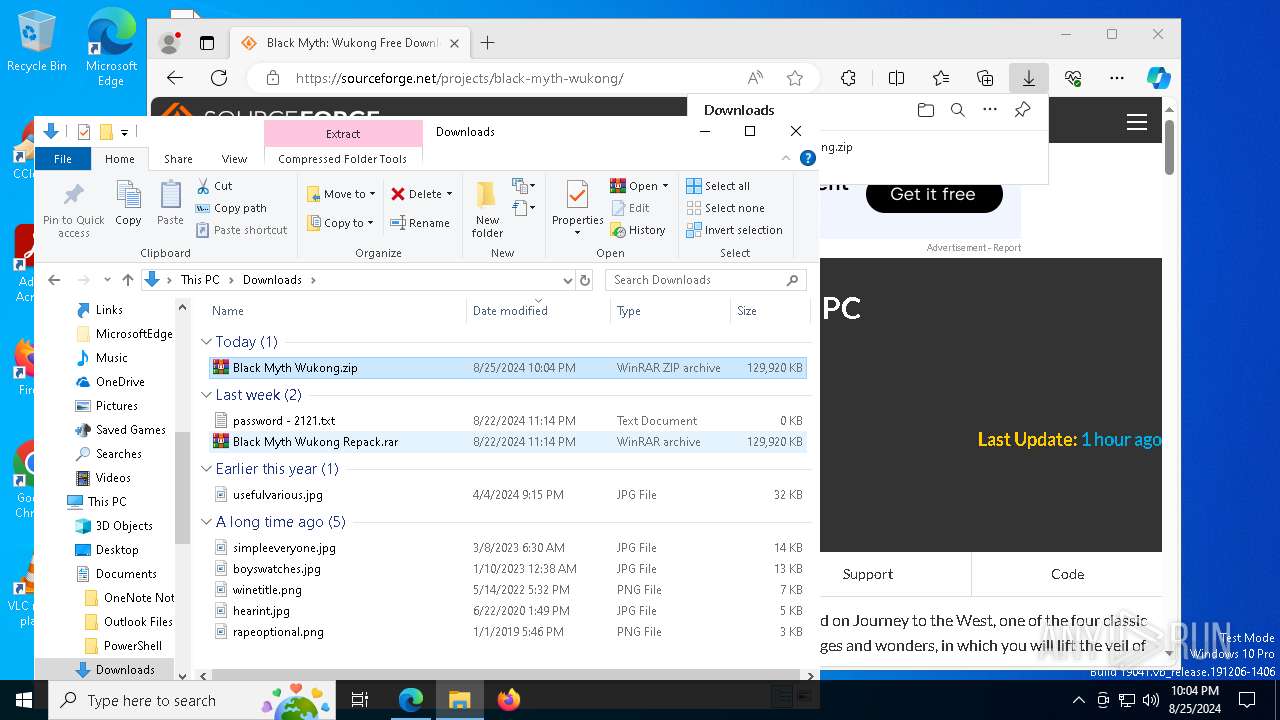
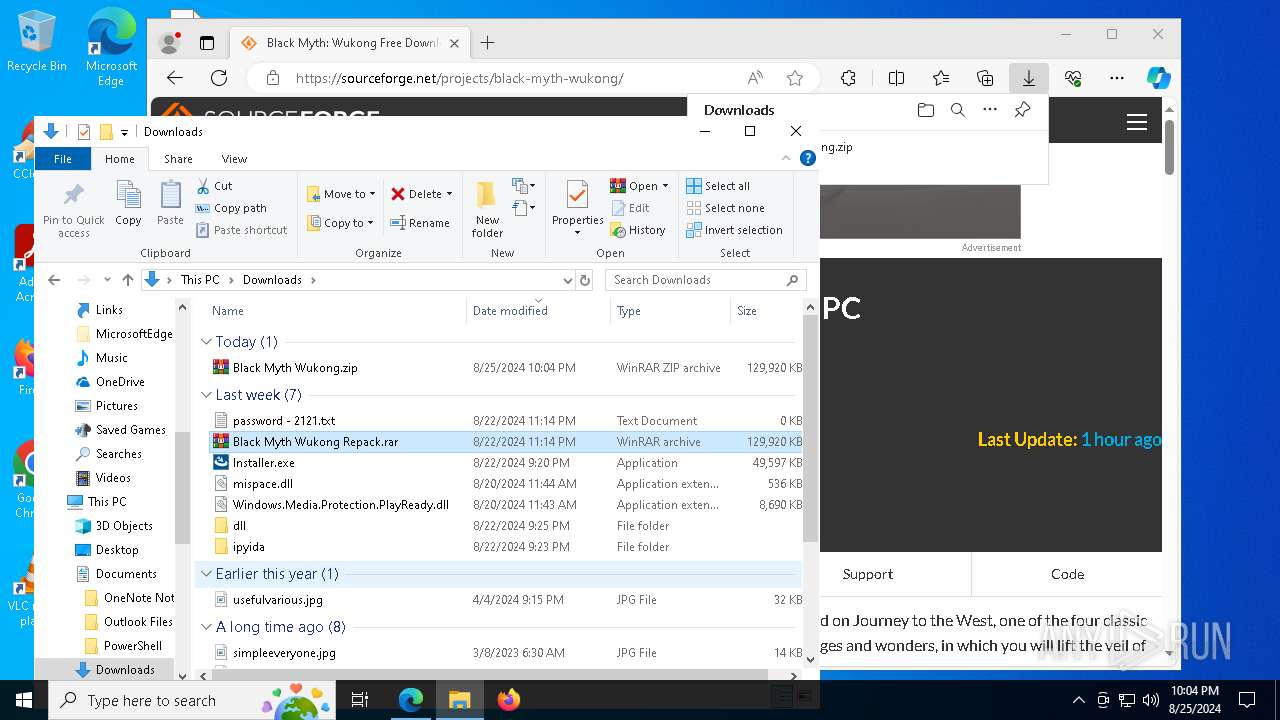
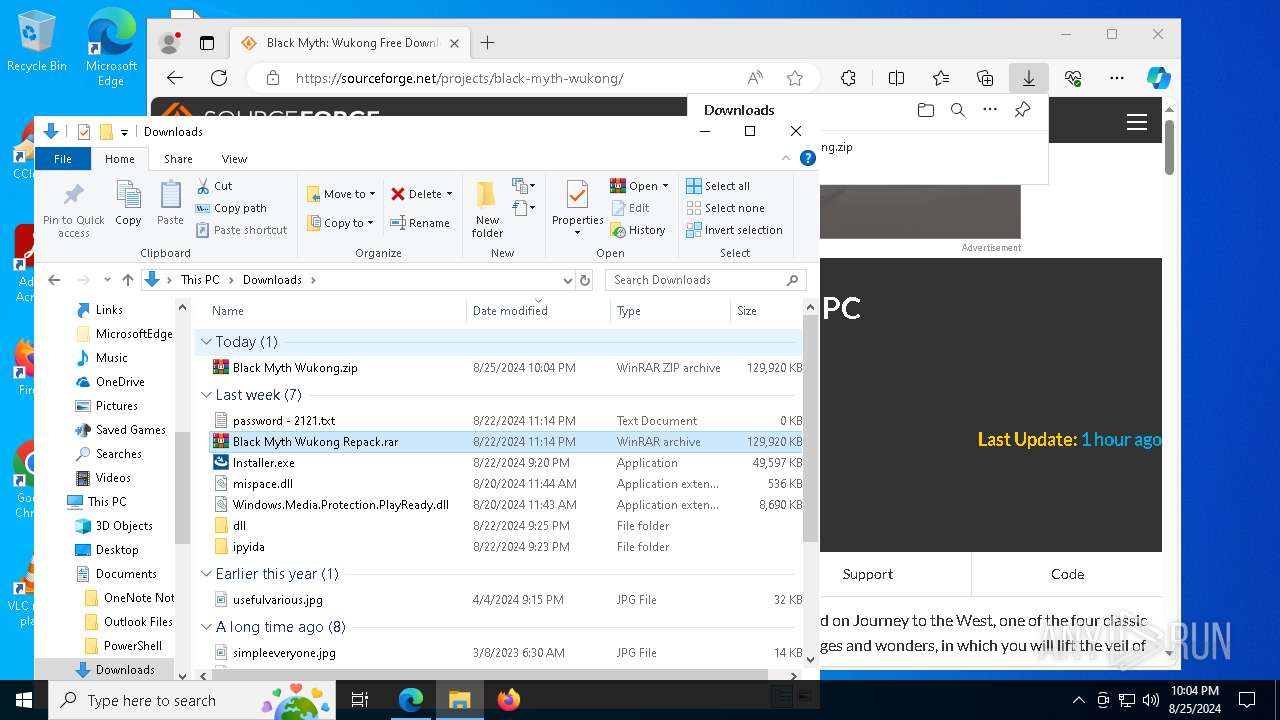
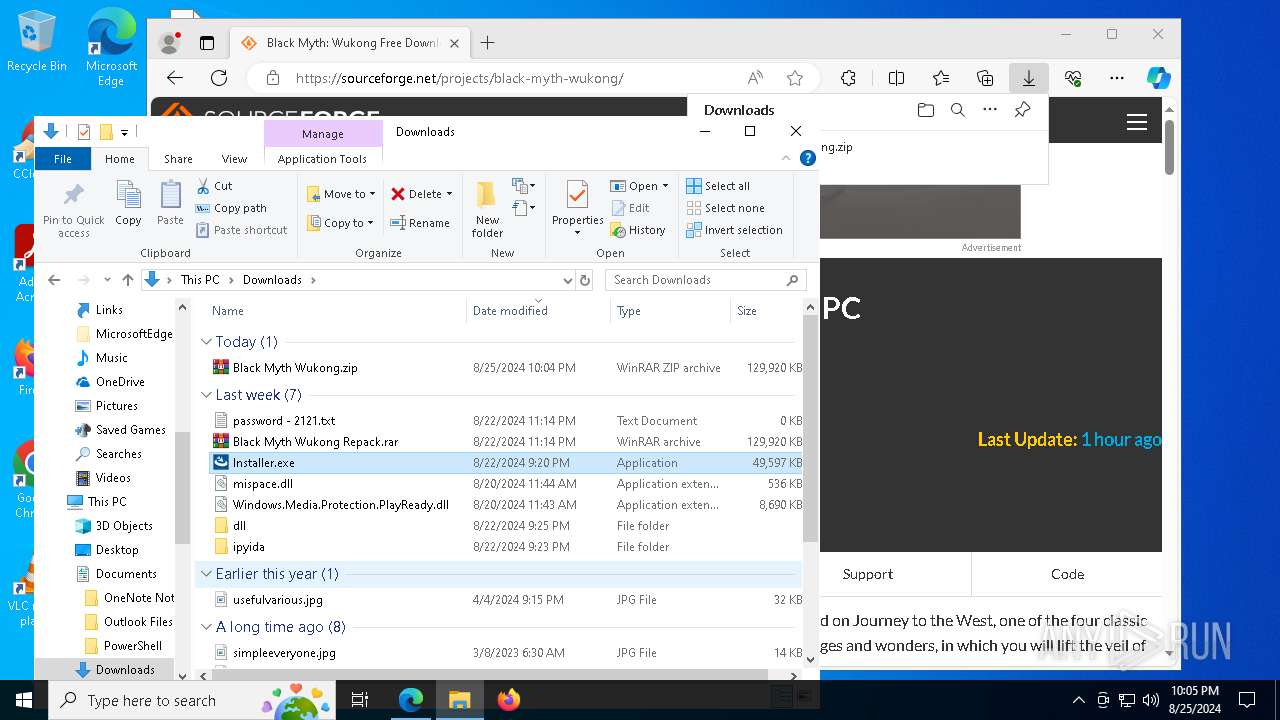
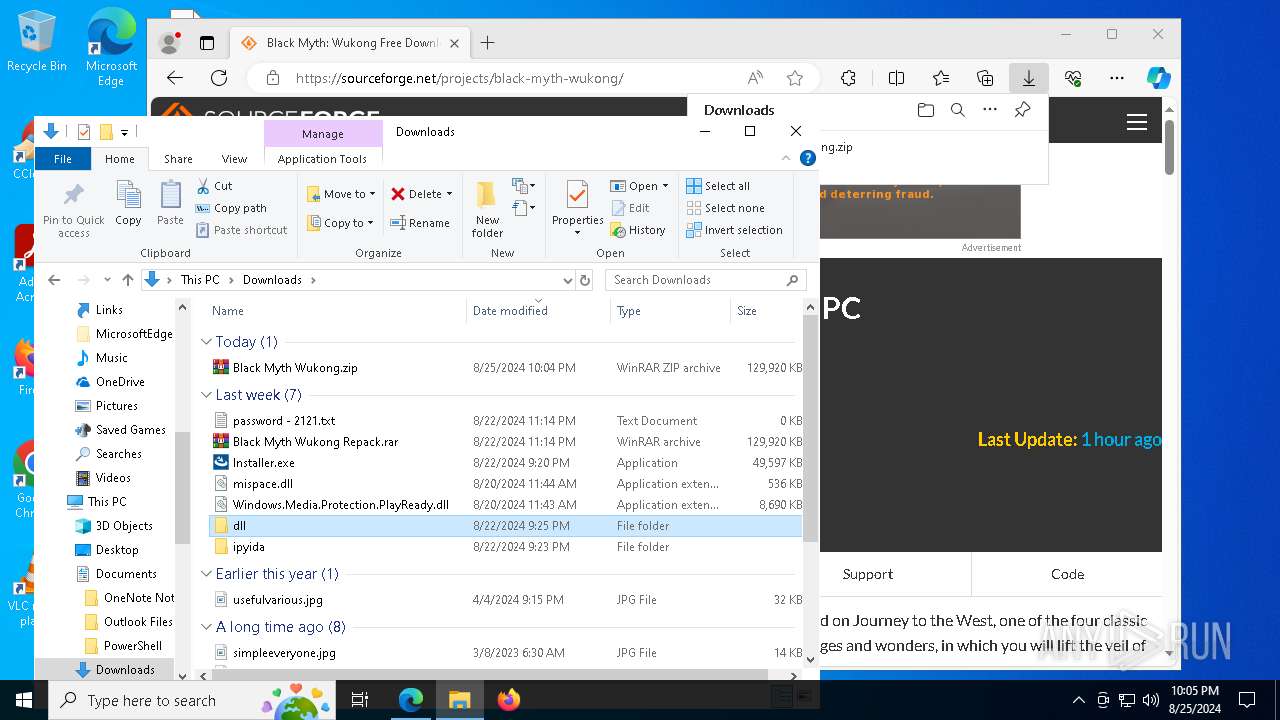
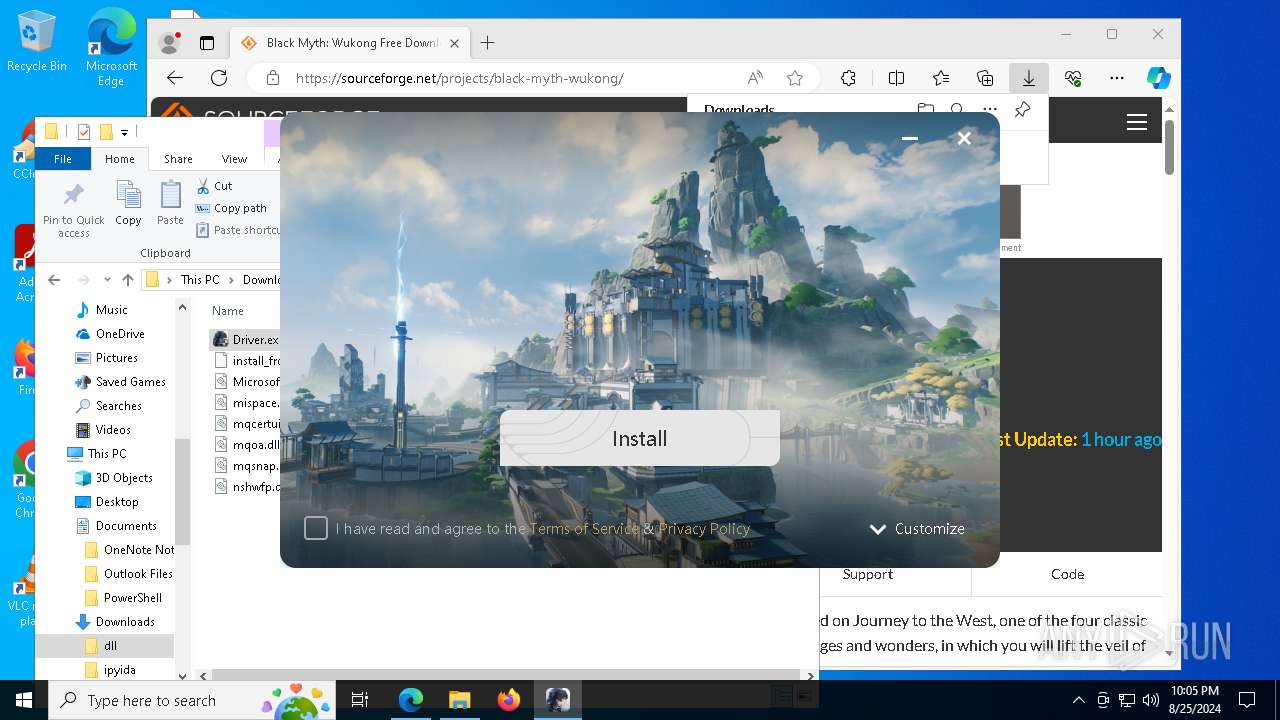
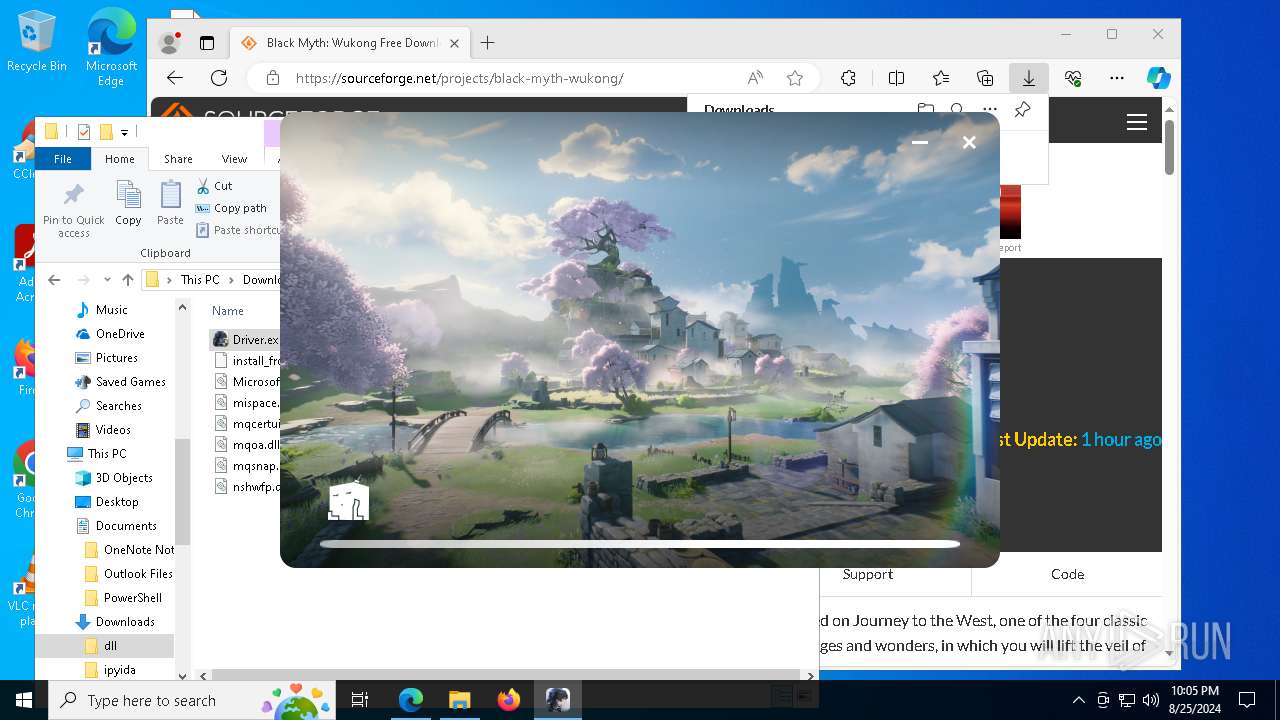
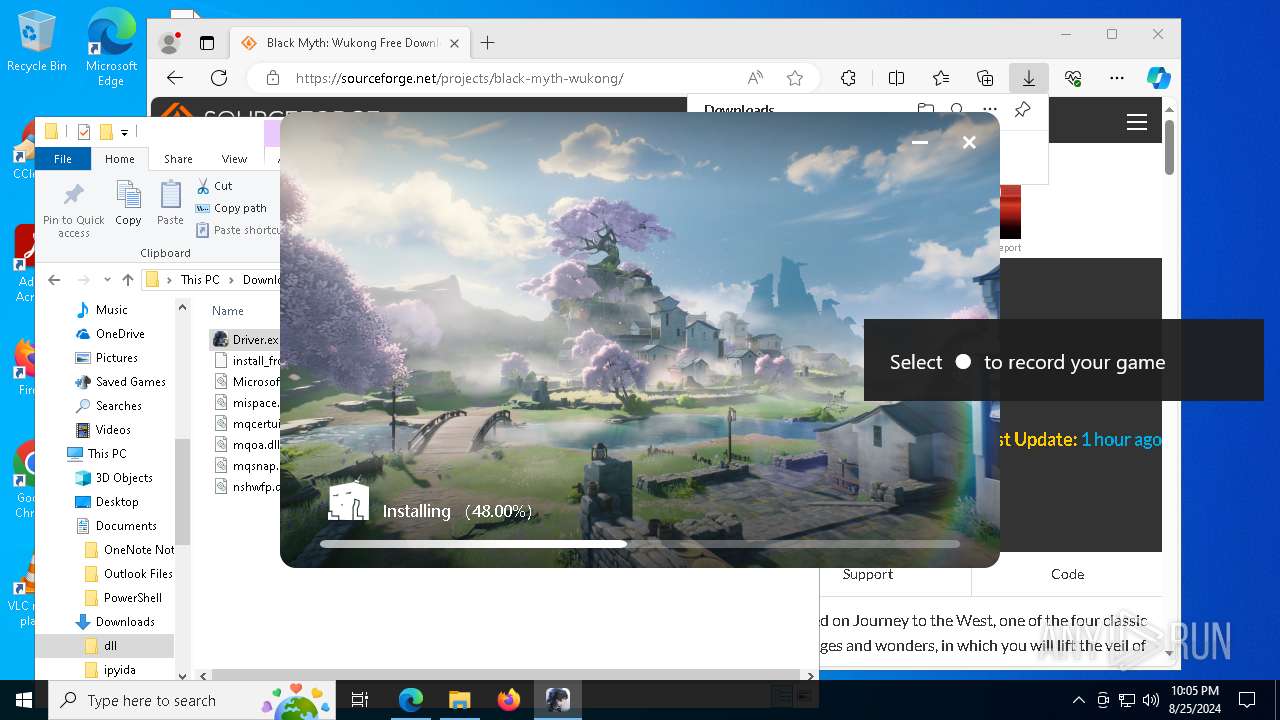
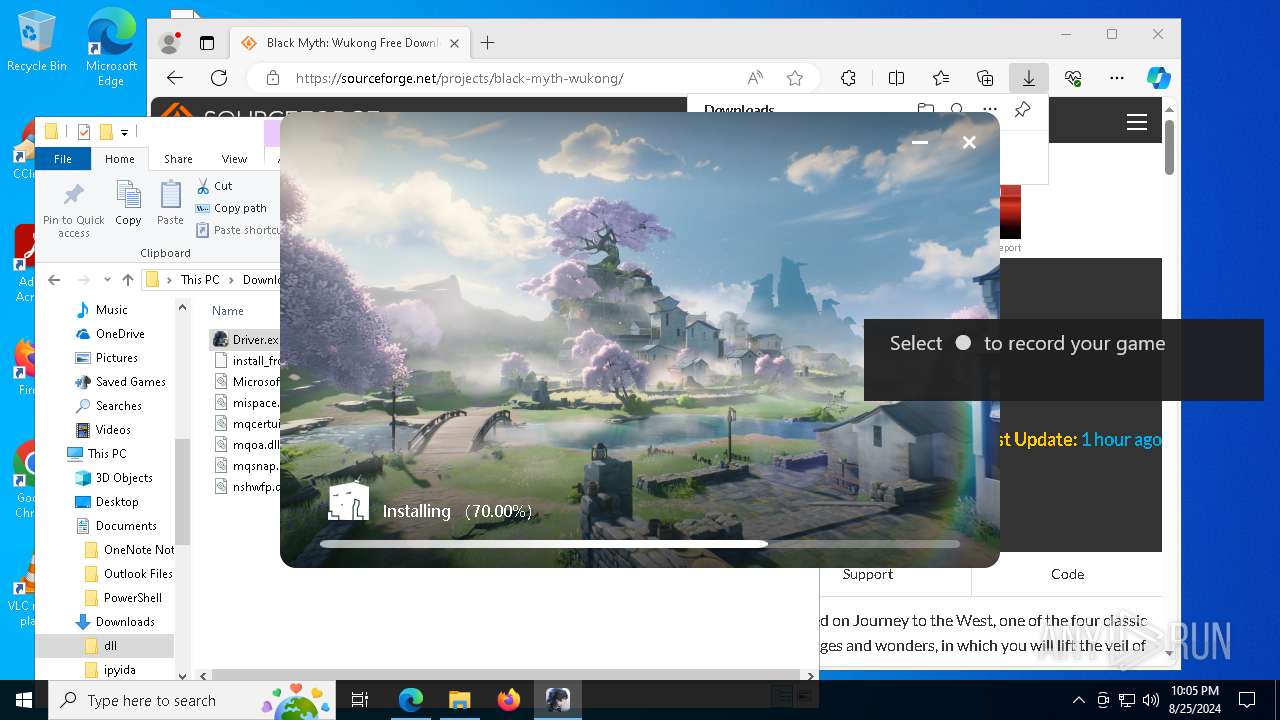
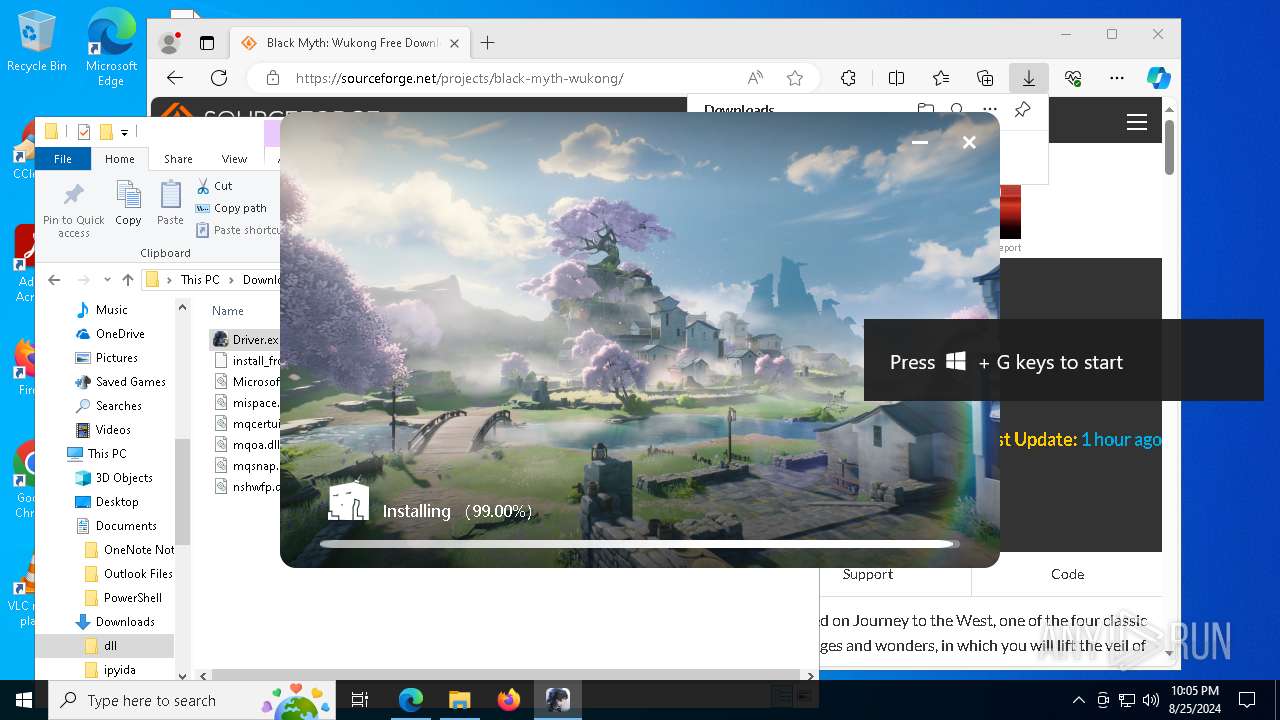
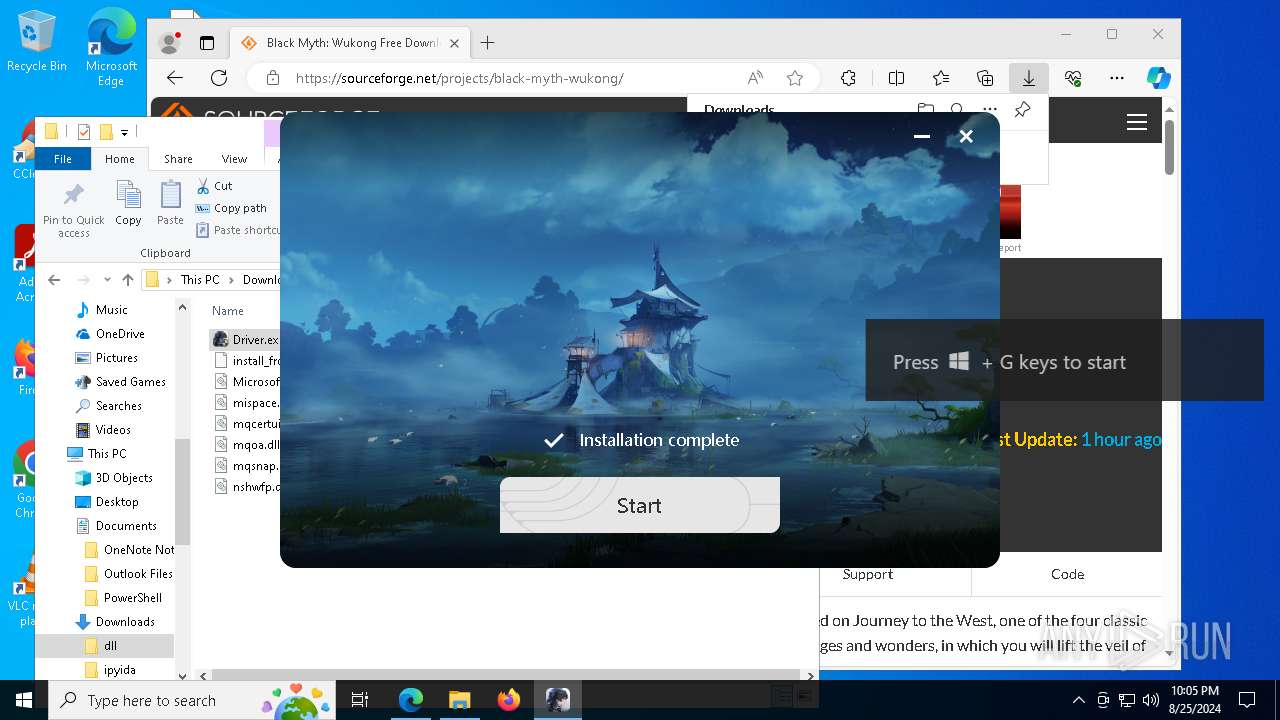
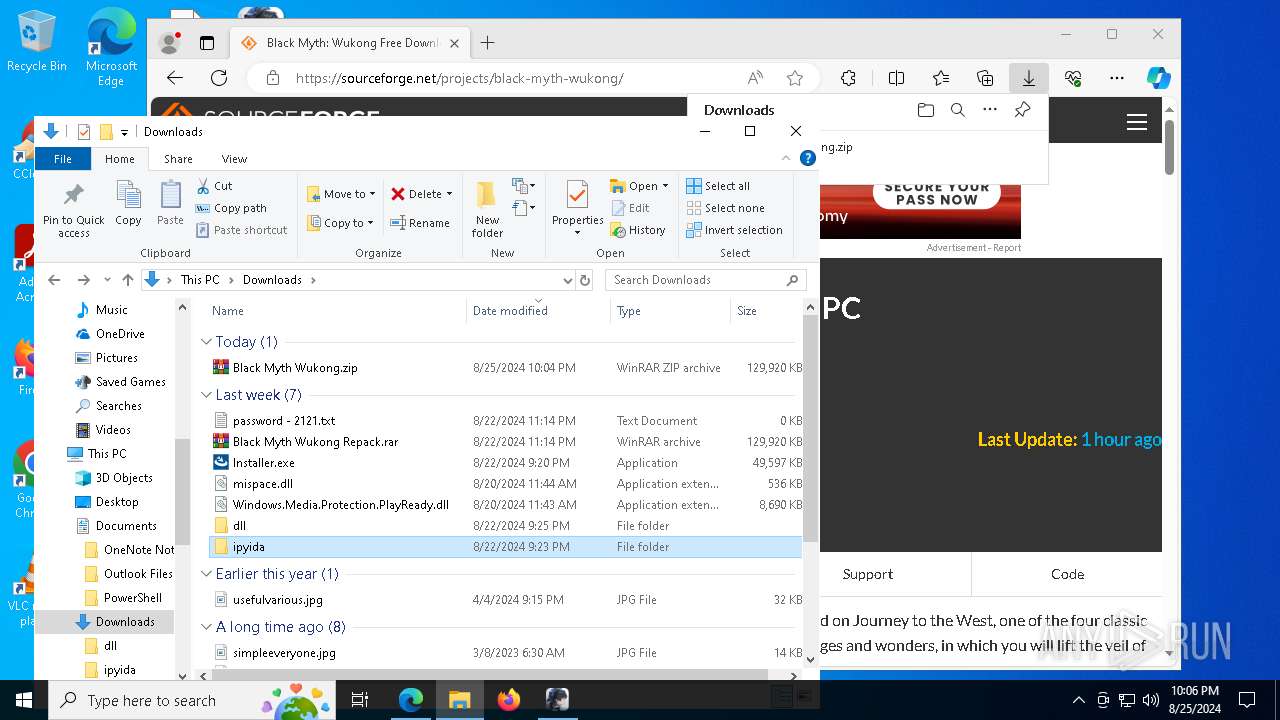
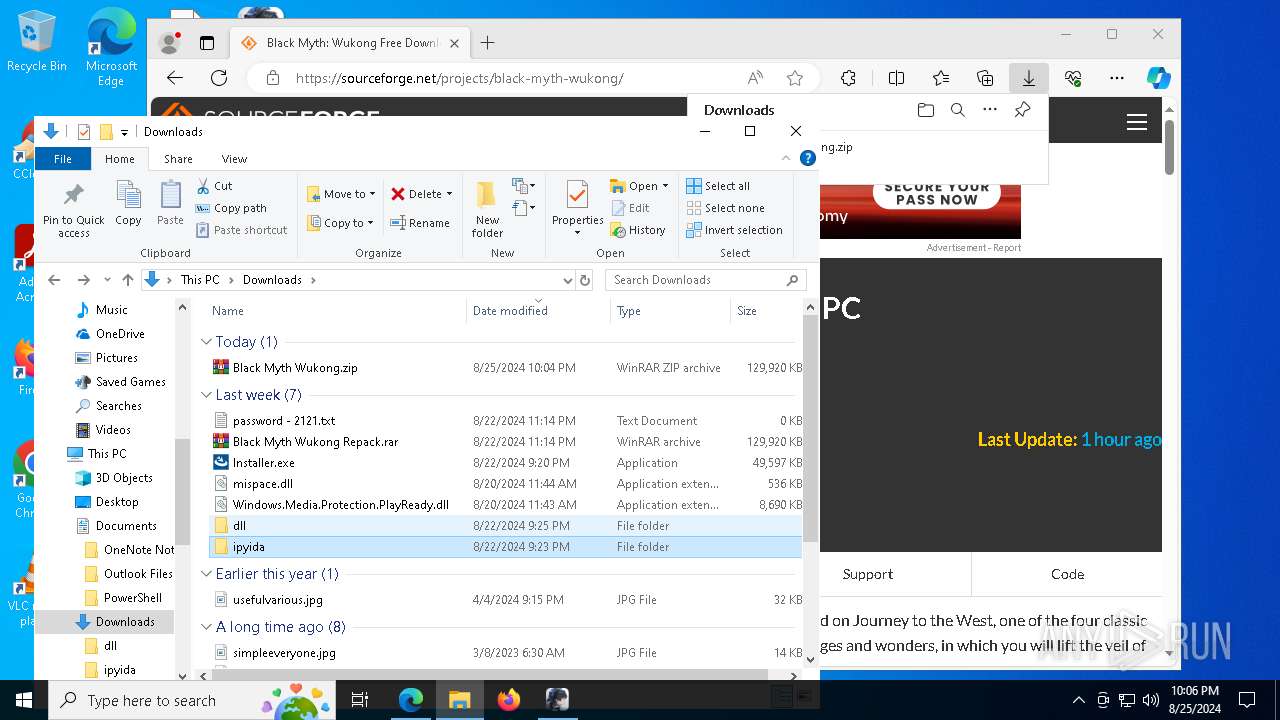
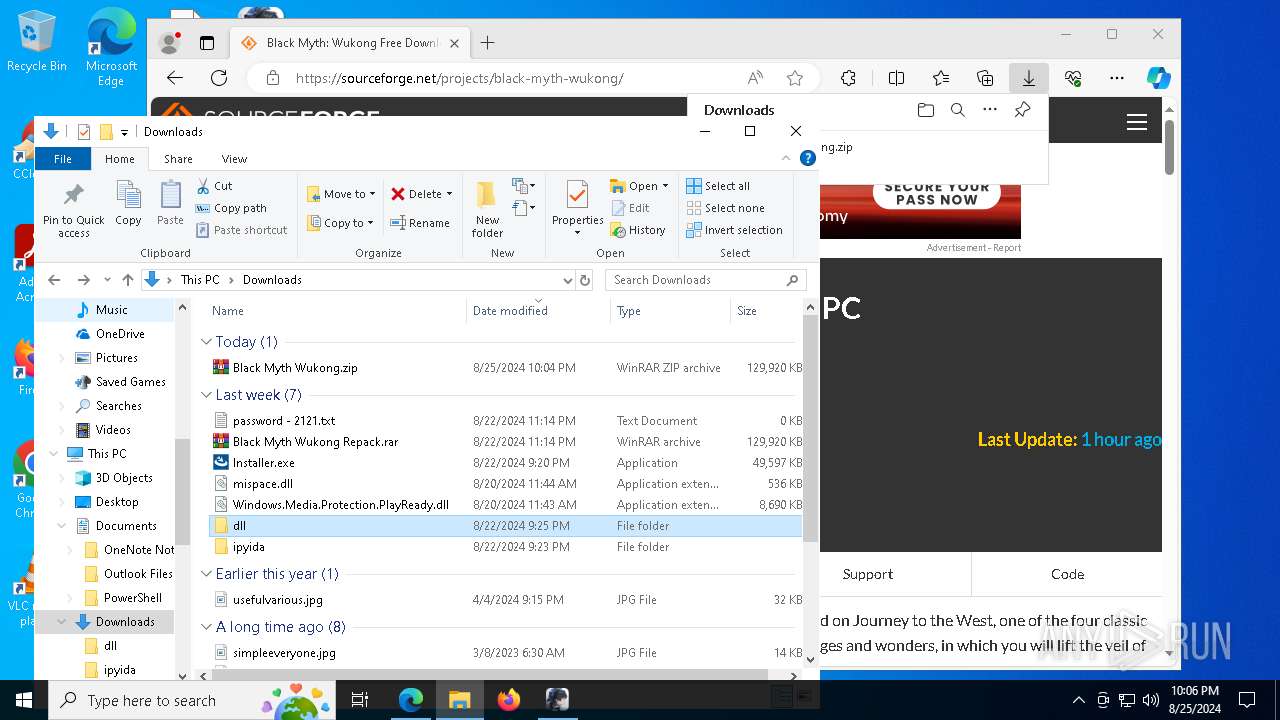
| URL: | https://sourceforge.net/projects/black-myth-wukong/files/Black%20Myth%20Wukong.zip/download |
| Full analysis: | https://app.any.run/tasks/63d02f1c-0dcc-479a-86ad-6c7389296bb2 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
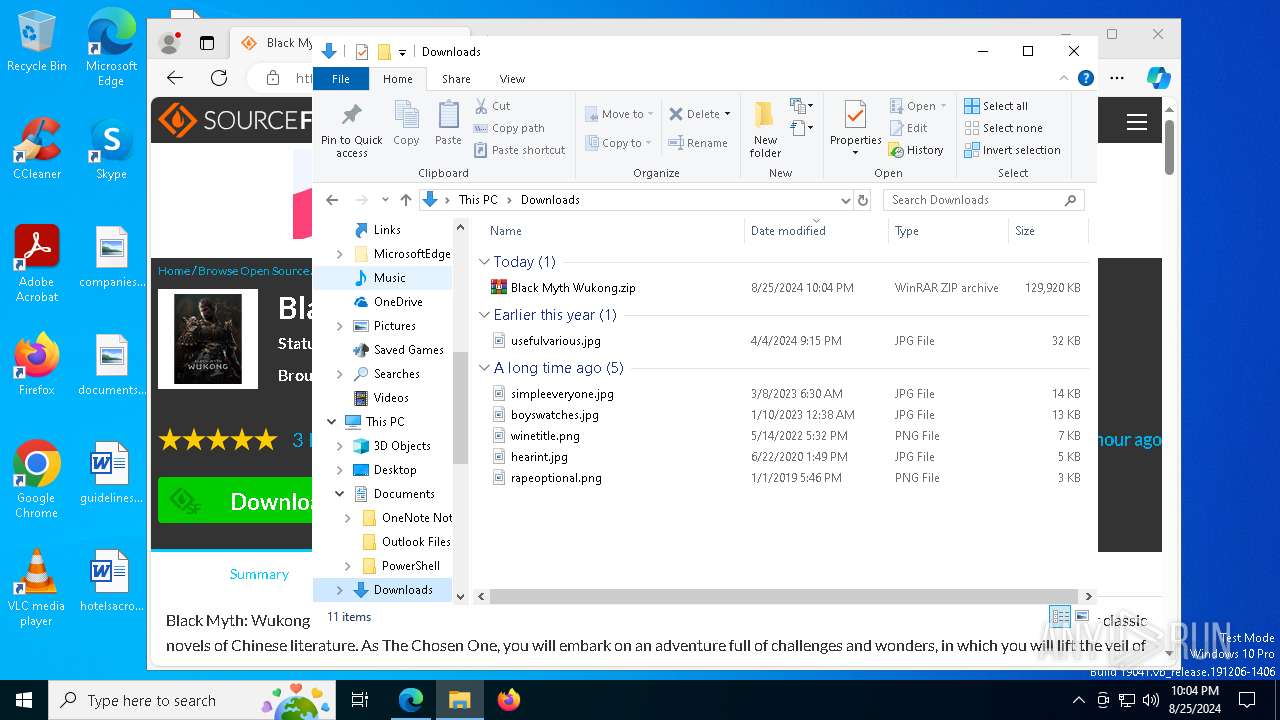
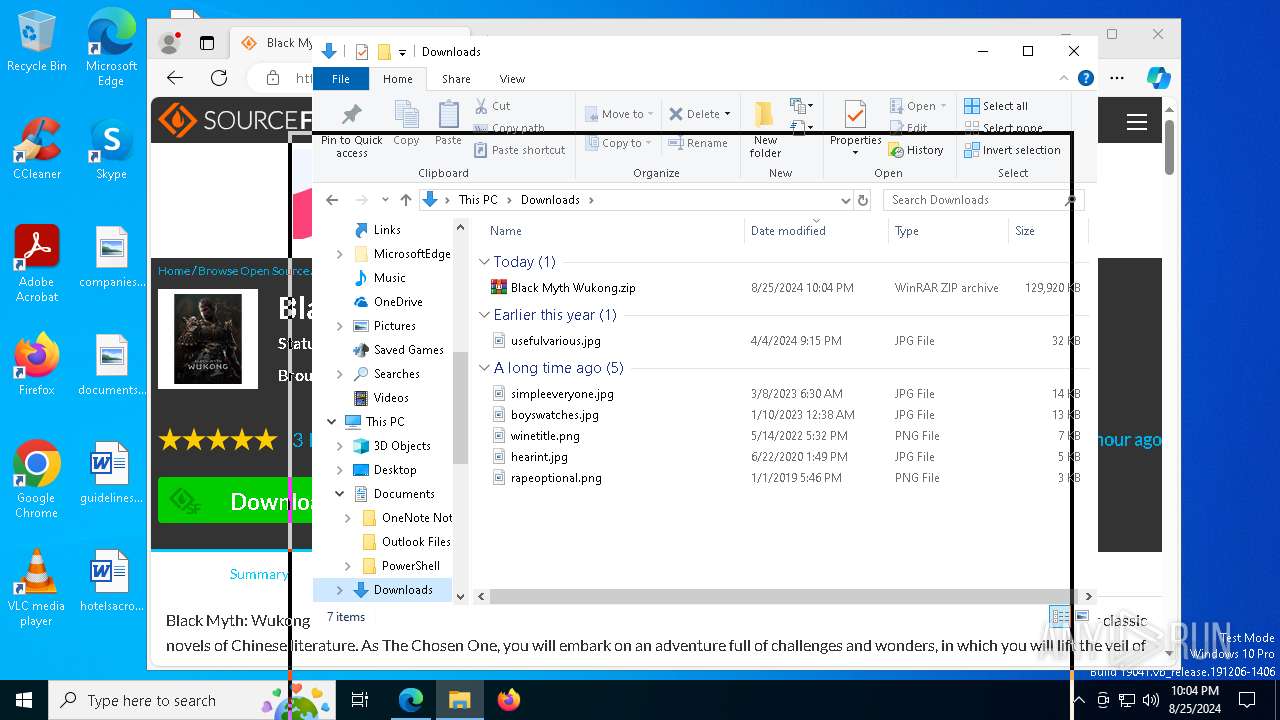
| Analysis date: | August 25, 2024, 22:02:54 |
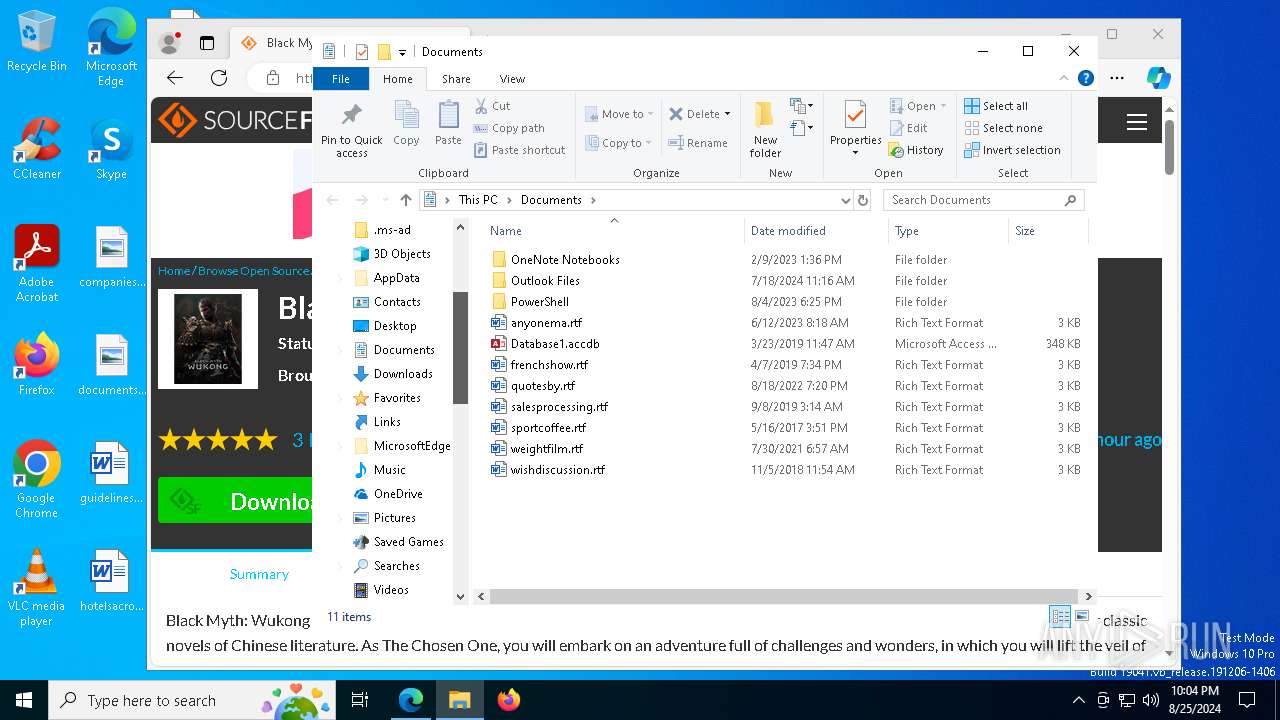
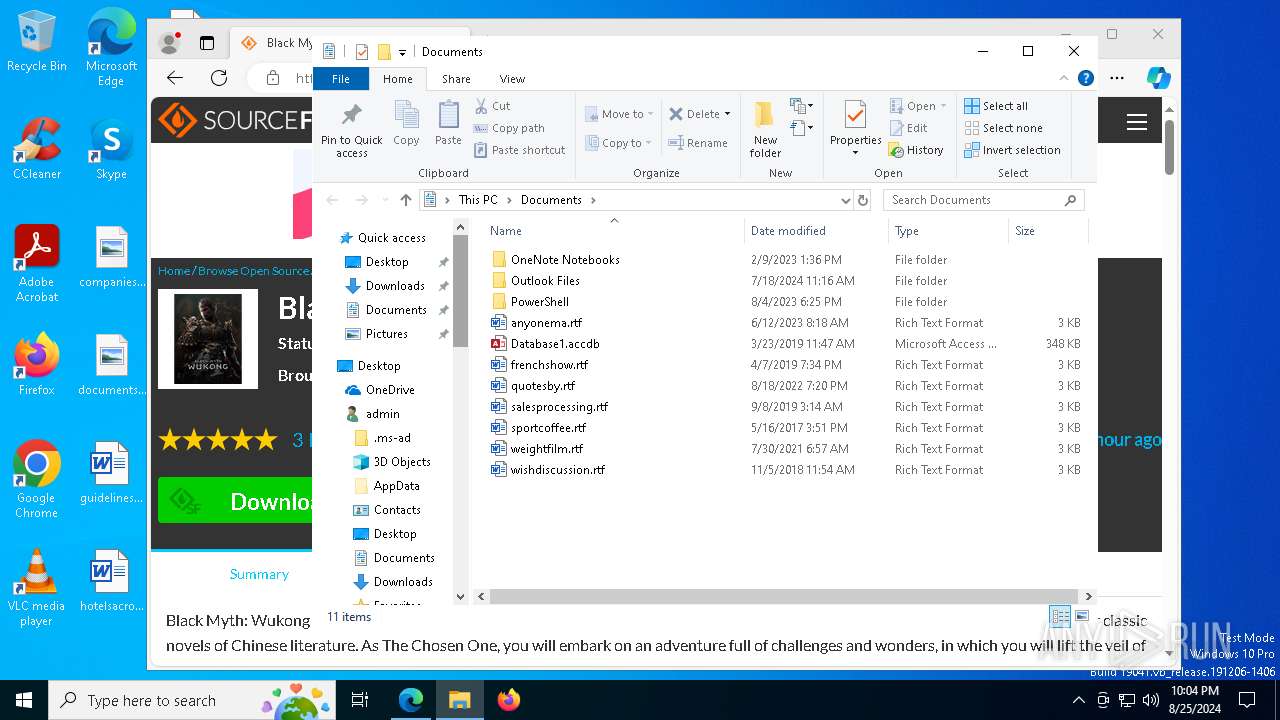
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E13537AFC395D7D2264B453462387BAC |
| SHA1: | 0A9D292D4CE8D021FC1885C9DD9CE894A9DA838E |
| SHA256: | C5DF165A68C8C1179C252782F4F8F7EF2A09ADA45C3602DF59B4B6B8911AADC7 |
| SSDEEP: | 3:N8HCGSuLAuUtLnh4NImKVIlbIgZp:2iGnCtLn64VIVIQ |
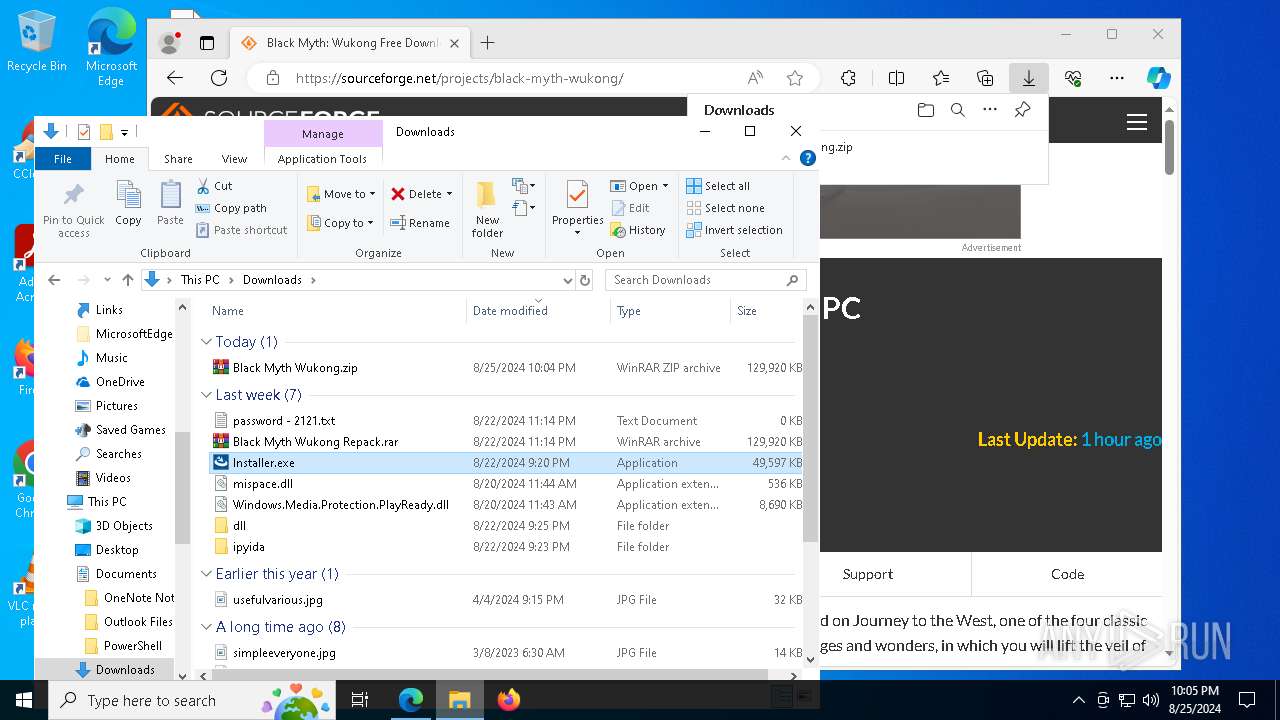
MALICIOUS
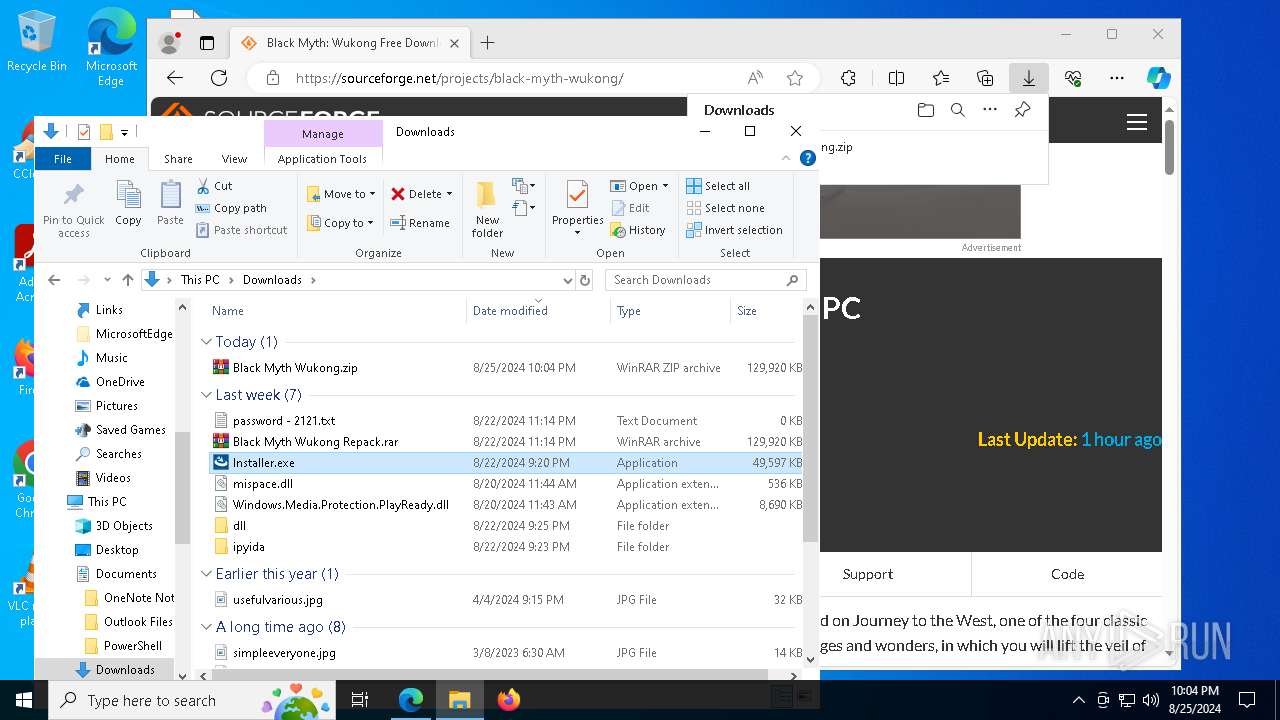
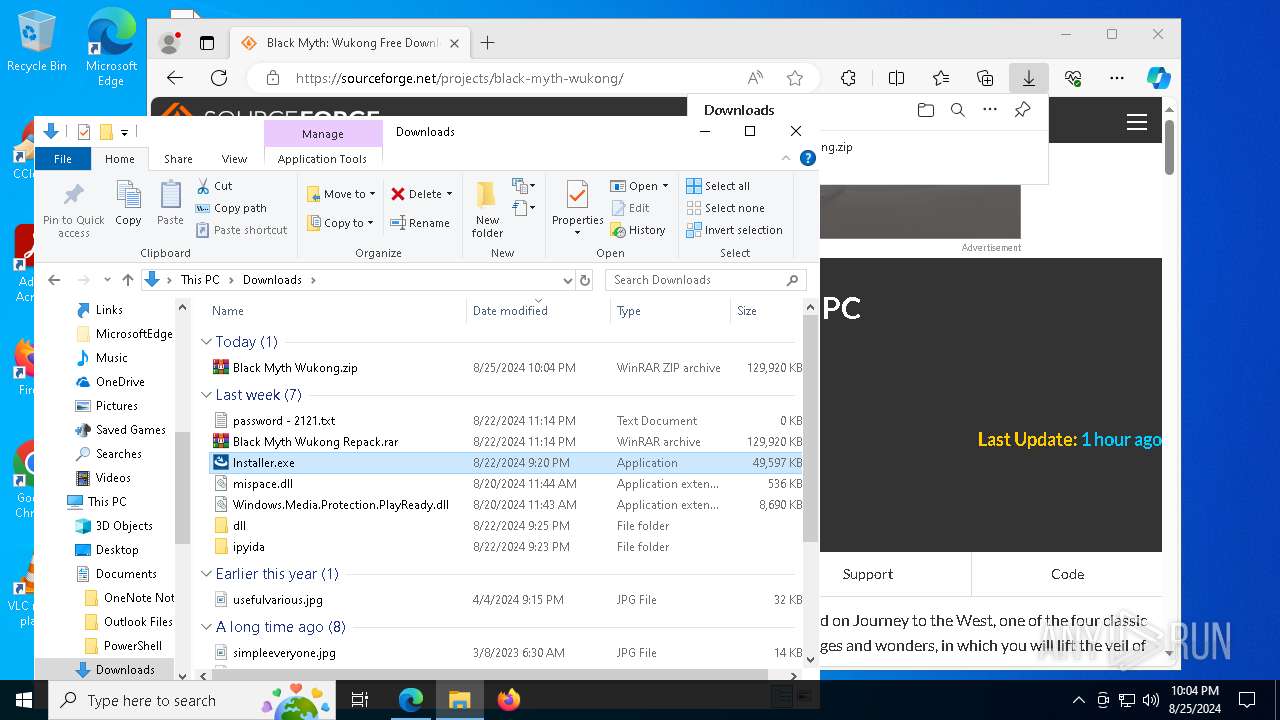
LUMMA has been detected (SURICATA)
- Installer.exe (PID: 7740)
LUMMA has been detected (YARA)
- Installer.exe (PID: 7740)
Stealers network behavior
- Installer.exe (PID: 7740)
Actions looks like stealing of personal data
- Installer.exe (PID: 7740)
XORed URL has been found (YARA)
- launcher.exe (PID: 6408)
SUSPICIOUS
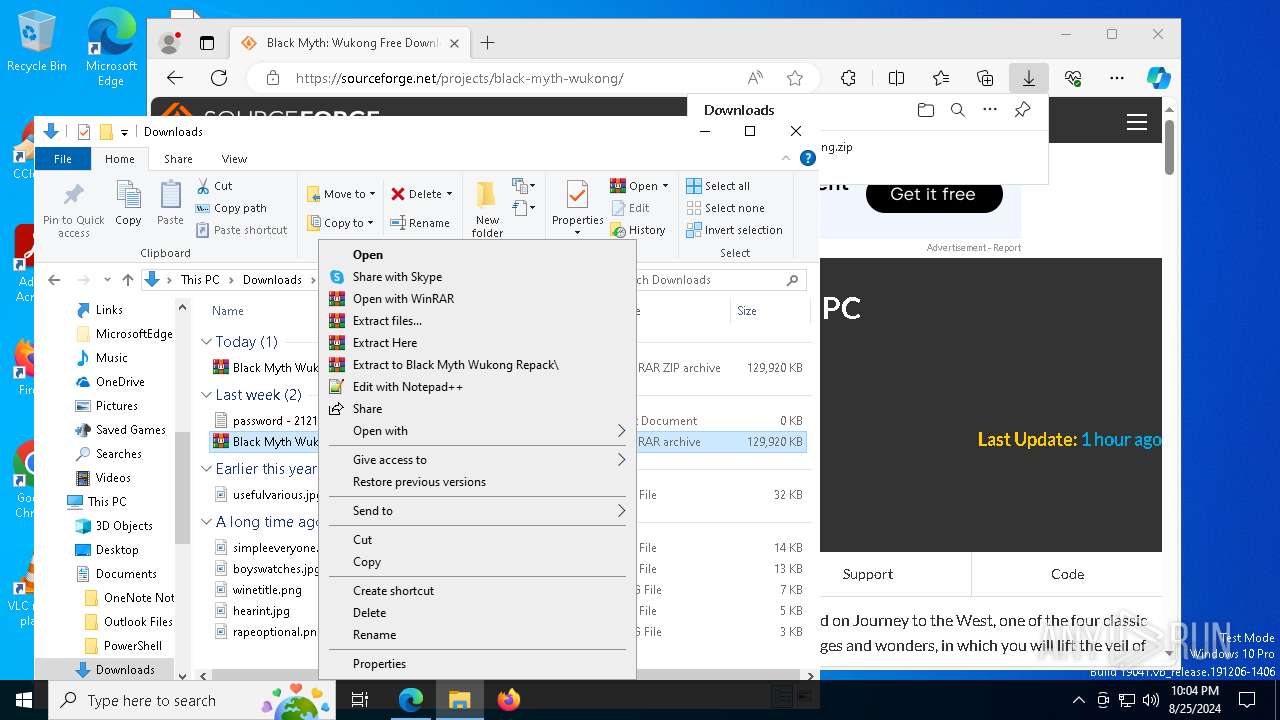
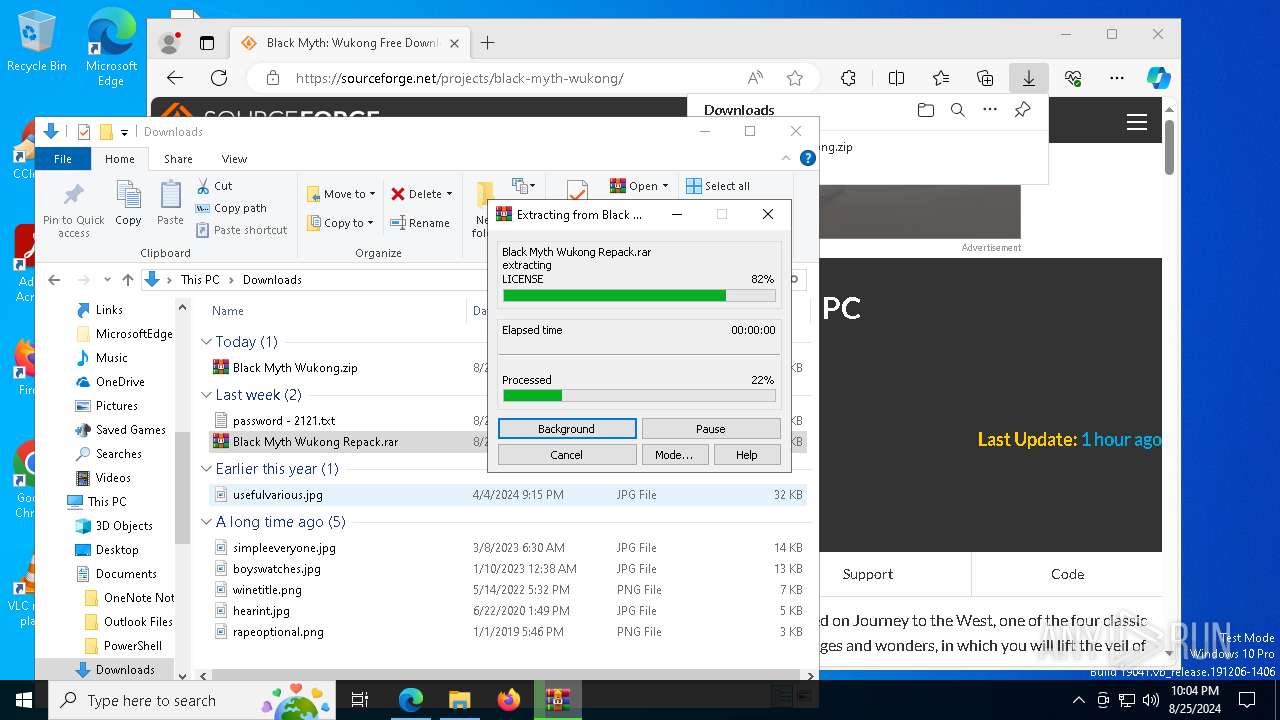
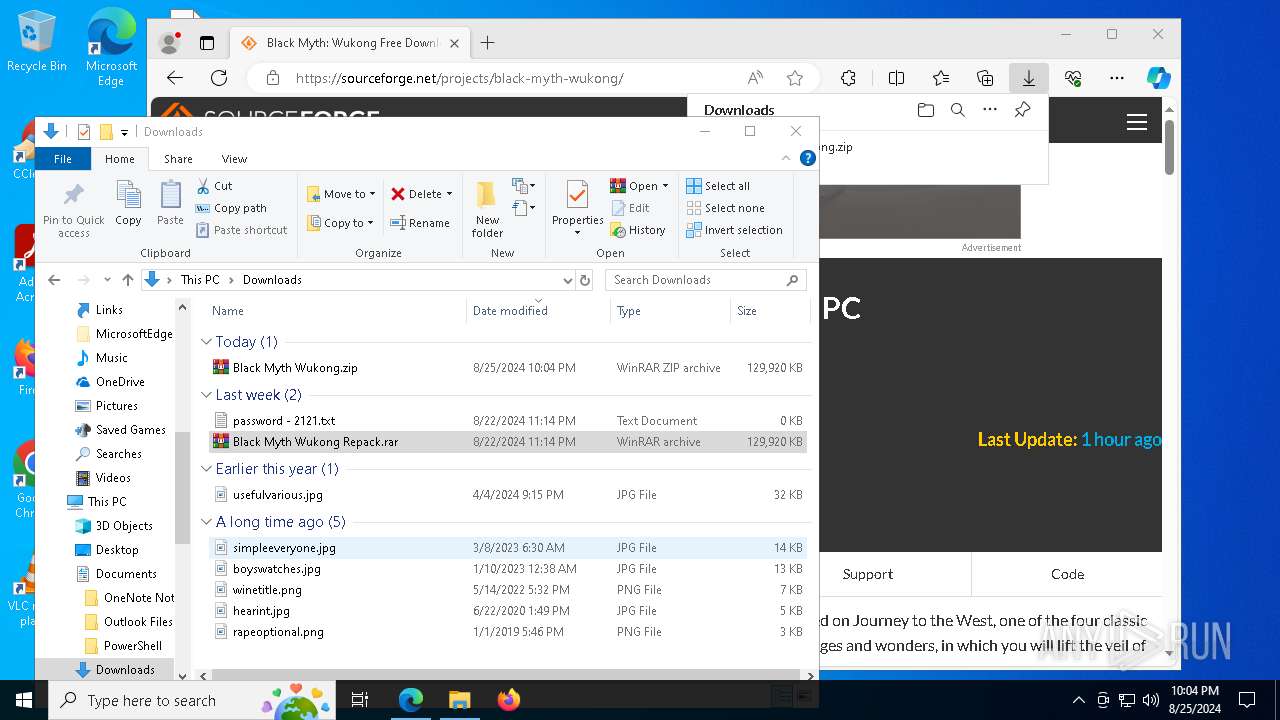
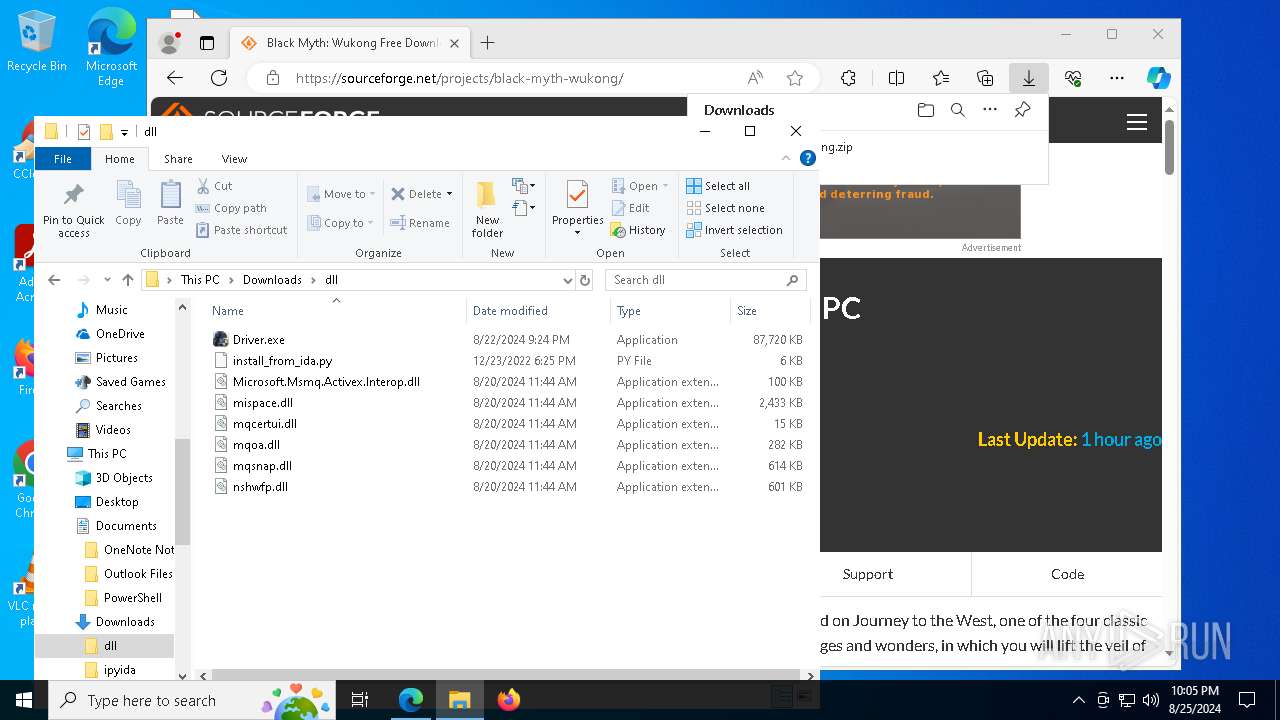
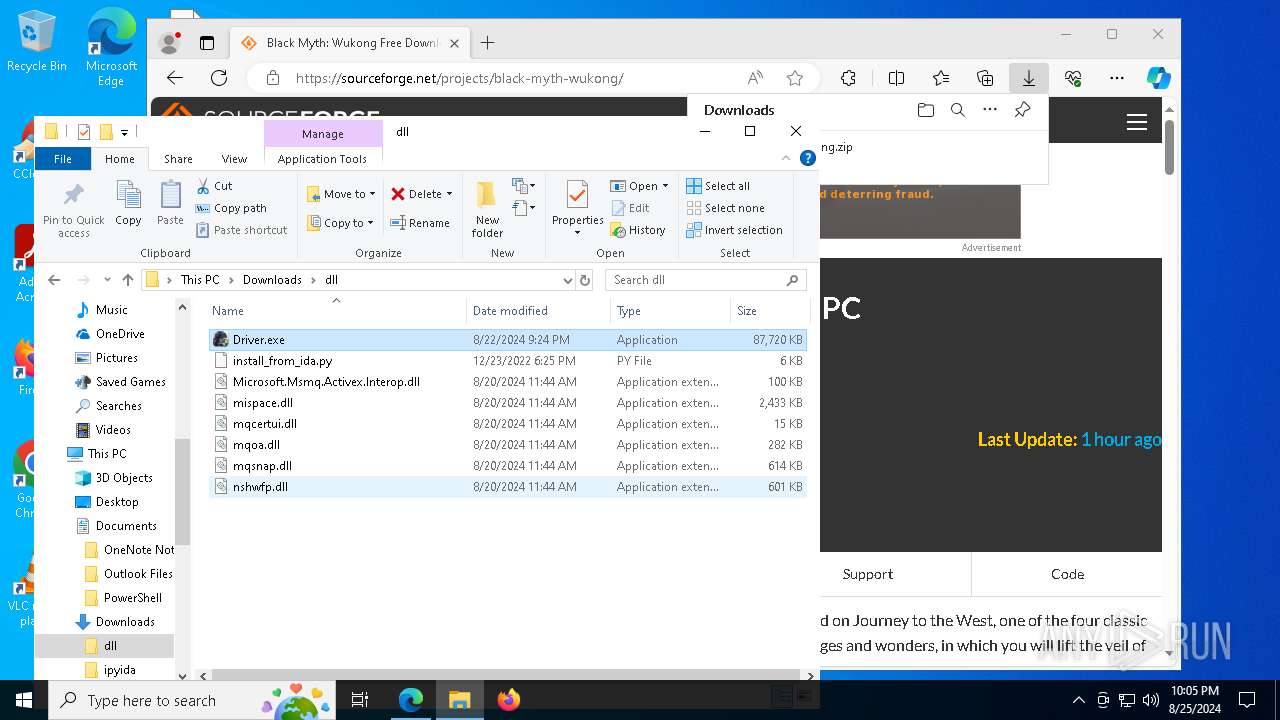
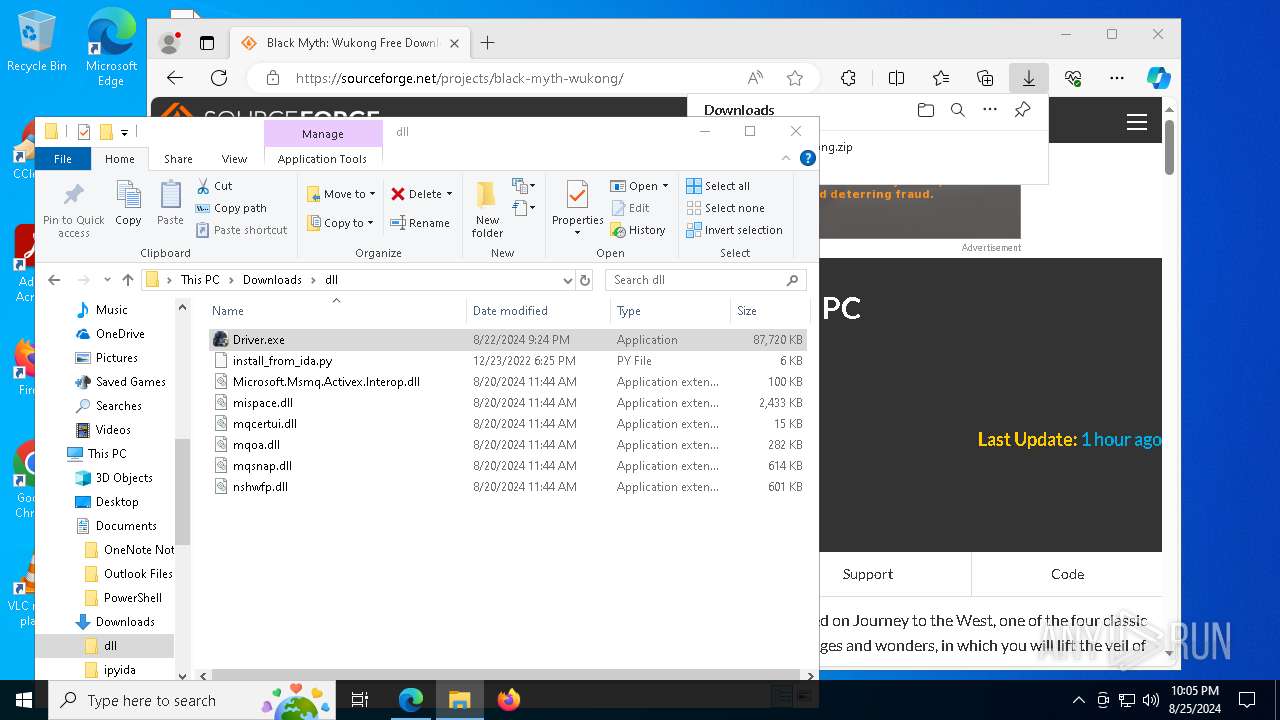
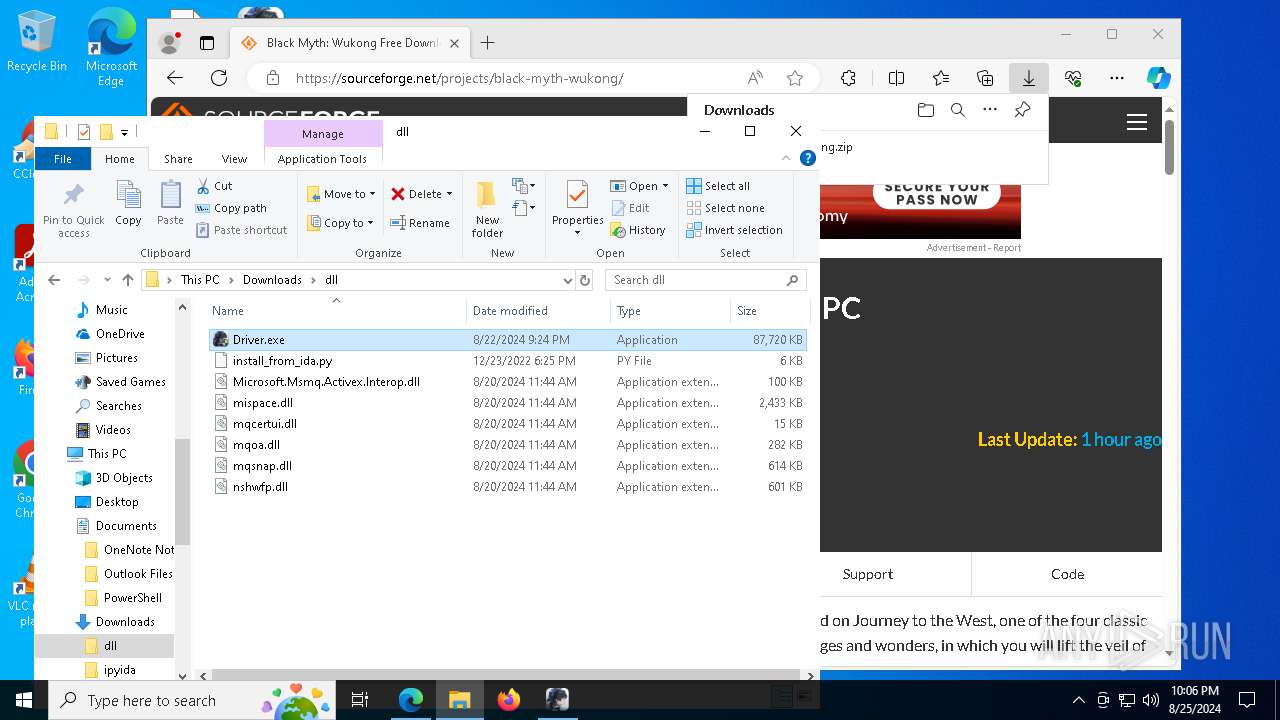
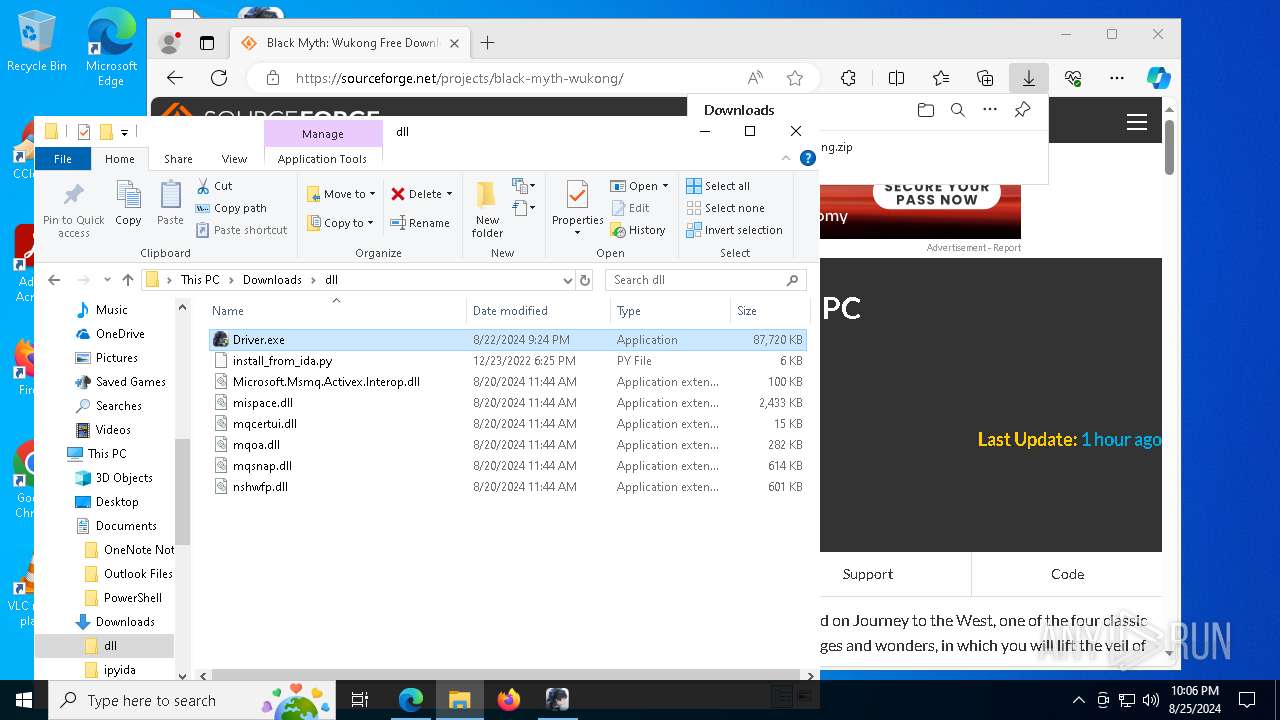
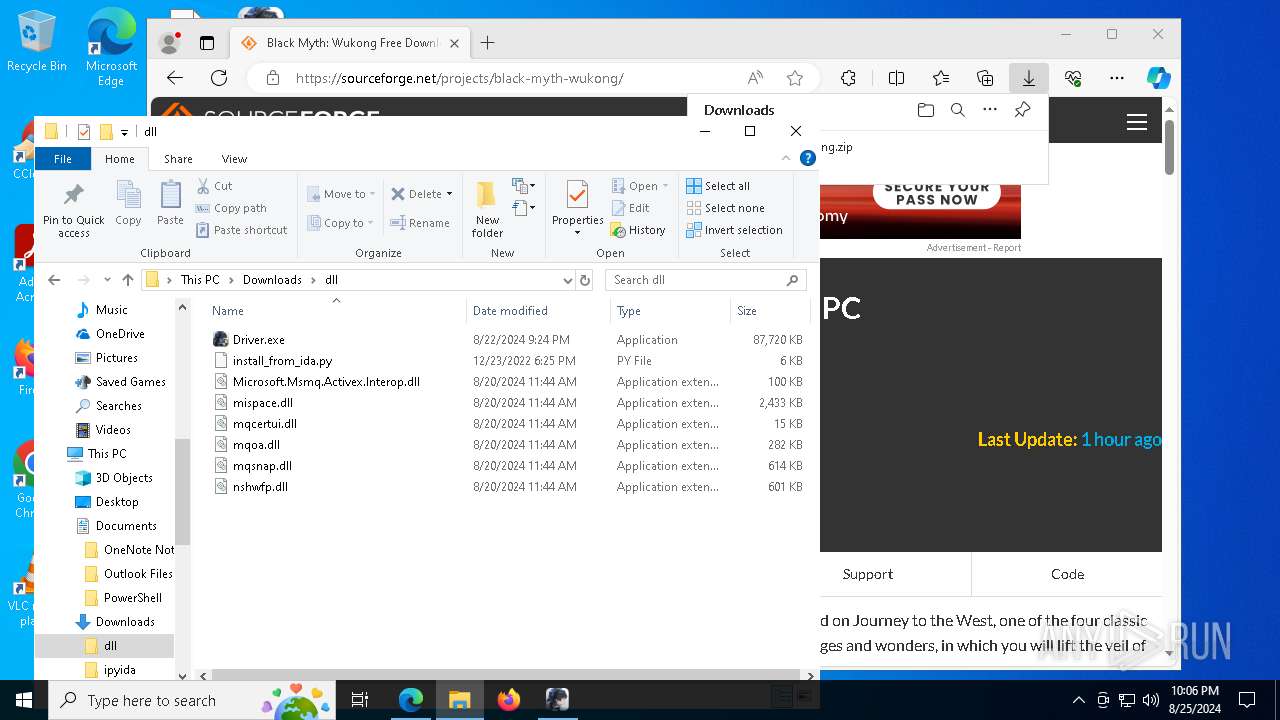
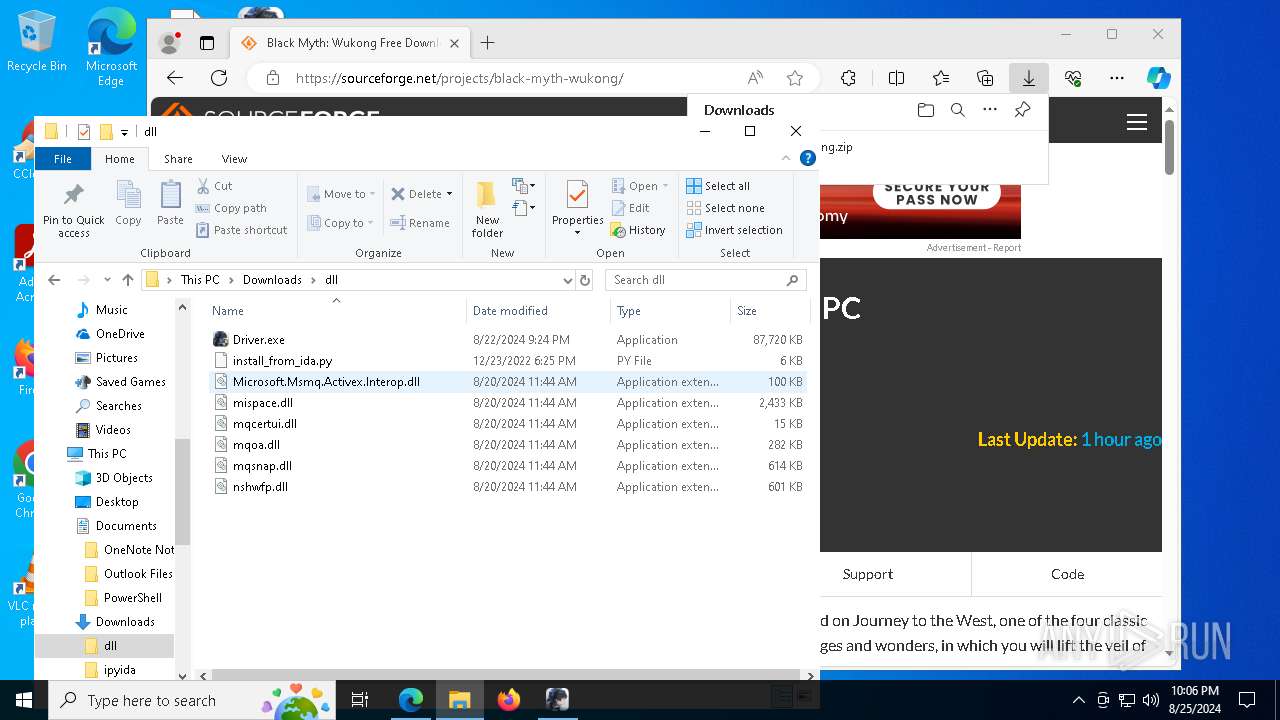
Process drops legitimate windows executable
- WinRAR.exe (PID: 5708)
- Driver.exe (PID: 6028)
Searches for installed software
- Installer.exe (PID: 7740)
- Driver.exe (PID: 6028)
Drops the executable file immediately after the start
- Driver.exe (PID: 6028)
Executable content was dropped or overwritten
- Driver.exe (PID: 6028)
The process creates files with name similar to system file names
- Driver.exe (PID: 6028)
Malware-specific behavior (creating "System.dll" in Temp)
- Driver.exe (PID: 6028)
The process drops C-runtime libraries
- Driver.exe (PID: 6028)
Uses WMIC.EXE to obtain physical disk drive information
- Driver.exe (PID: 6028)
- launcher.exe (PID: 6408)
Reads security settings of Internet Explorer
- GameBar.exe (PID: 752)
- TQMCenter_64.exe (PID: 7740)
Uses WMIC.EXE to obtain CPU information
- Driver.exe (PID: 6028)
- launcher.exe (PID: 6408)
Creates a software uninstall entry
- Driver.exe (PID: 6028)
Process drops SQLite DLL files
- Driver.exe (PID: 6028)
Reads the date of Windows installation
- TQMCenter_64.exe (PID: 7740)
The process deletes folder without confirmation
- TQMCenter_64.exe (PID: 7740)
Starts CMD.EXE for commands execution
- TQMCenter_64.exe (PID: 7740)
INFO
Reads the computer name
- identity_helper.exe (PID: 7276)
- Installer.exe (PID: 7740)
- GameBar.exe (PID: 752)
- Driver.exe (PID: 6028)
- launcher.exe (PID: 6408)
- KRInstallExternal.exe (PID: 2324)
- TQMCenter_64.exe (PID: 7740)
Checks supported languages
- identity_helper.exe (PID: 7276)
- Installer.exe (PID: 7740)
- Driver.exe (PID: 6028)
- GameBar.exe (PID: 752)
- launcher.exe (PID: 6408)
- KRInstallExternal.exe (PID: 2324)
- TQMCenter_64.exe (PID: 7740)
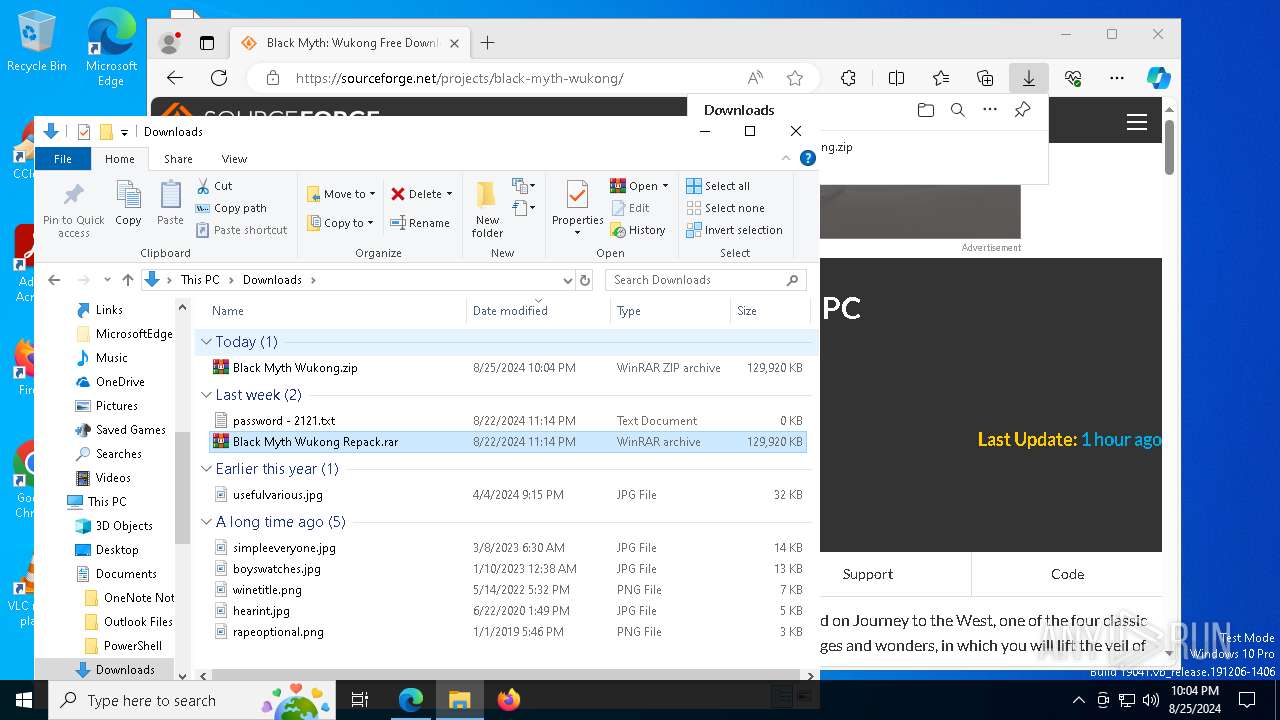
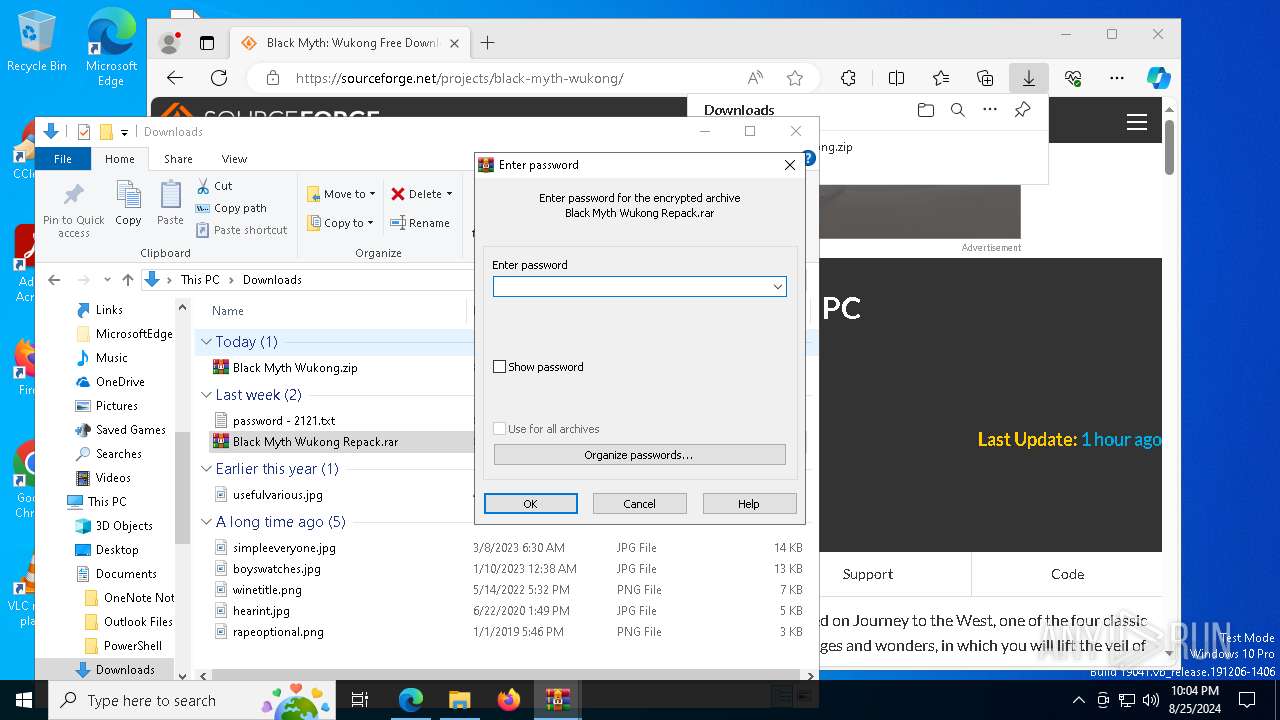
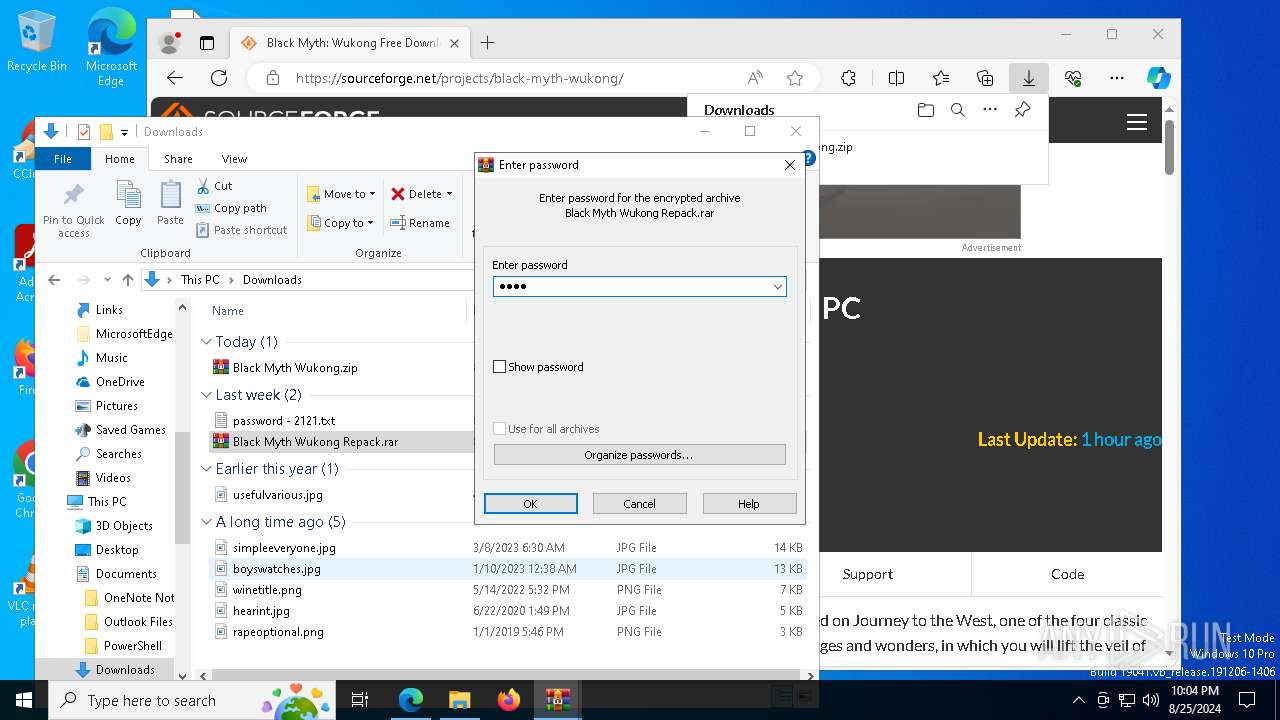
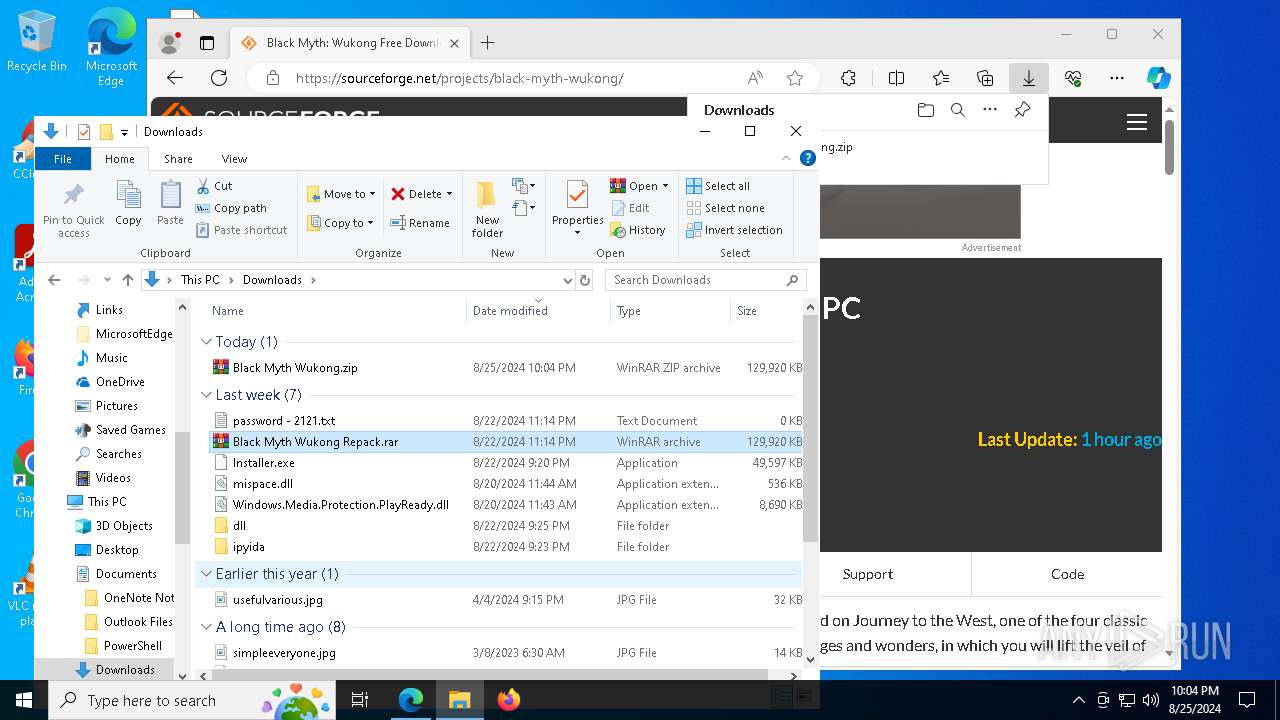
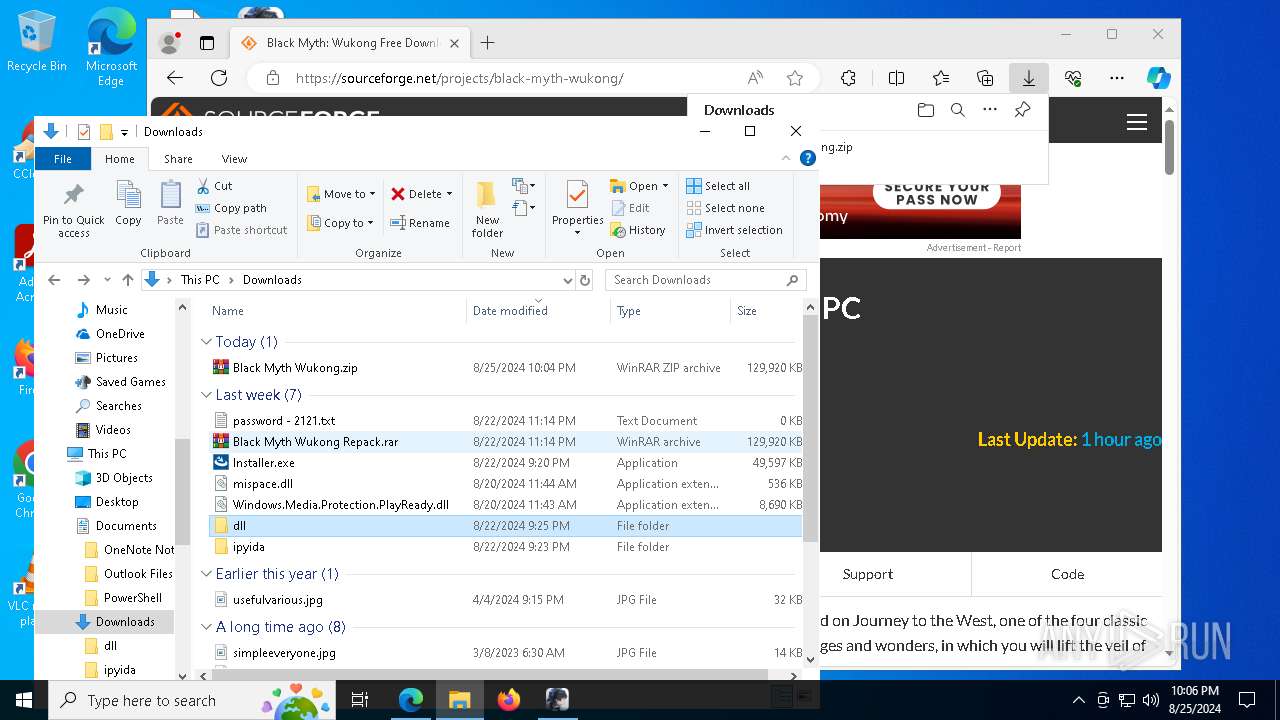
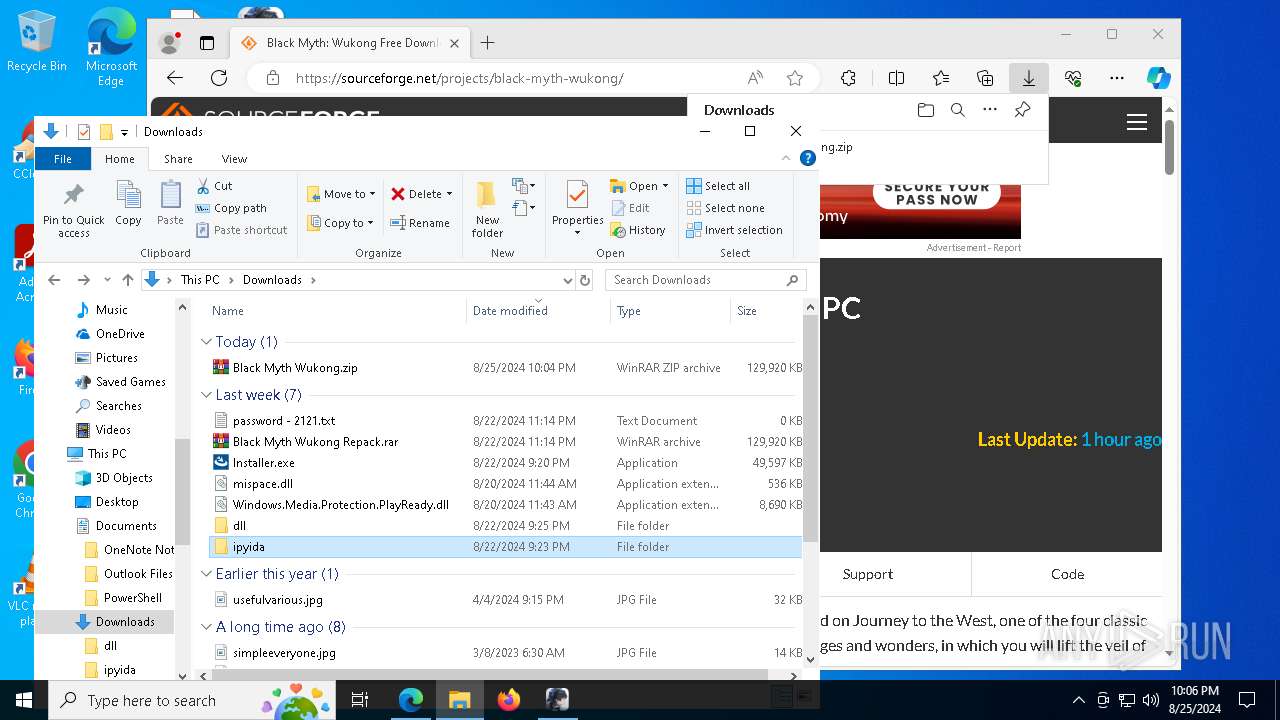
Manual execution by a user
- WinRAR.exe (PID: 5708)
- Installer.exe (PID: 7740)
- WinRAR.exe (PID: 7764)
- Driver.exe (PID: 3996)
- Driver.exe (PID: 6028)
Application launched itself
- msedge.exe (PID: 6576)
Reads Environment values
- identity_helper.exe (PID: 7276)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6576)
Reads the software policy settings
- Installer.exe (PID: 7740)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5708)
Create files in a temporary directory
- Driver.exe (PID: 6028)
Dropped object may contain TOR URL's
- Driver.exe (PID: 6028)
Reads the machine GUID from the registry
- Driver.exe (PID: 6028)
- launcher.exe (PID: 6408)
- KRInstallExternal.exe (PID: 2324)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3784)
- WMIC.exe (PID: 3964)
- WMIC.exe (PID: 7980)
- WMIC.exe (PID: 7644)
- WMIC.exe (PID: 6880)
- WMIC.exe (PID: 2992)
Creates files or folders in the user directory
- Driver.exe (PID: 6028)
- launcher.exe (PID: 6408)
- KRInstallExternal.exe (PID: 2324)
Checks proxy server information
- Driver.exe (PID: 6028)
- launcher.exe (PID: 6408)
Creates files in the program directory
- Driver.exe (PID: 6028)
Process checks computer location settings
- TQMCenter_64.exe (PID: 7740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
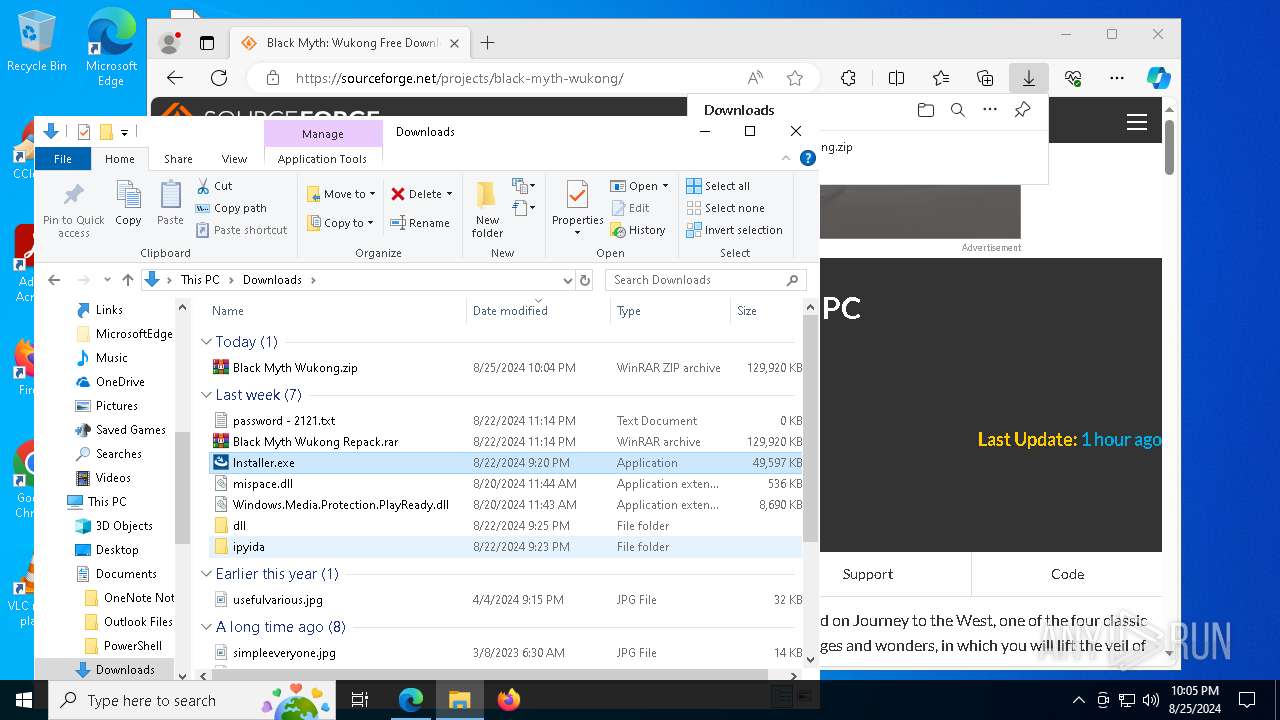
Lumma
(PID) Process(7740) Installer.exe
C2 (9)deicedosmzj.shop
southedhiscuso.shop
cagedwifedsozm.shop
consciousourwi.shop
interactiedovspm.shop
charecteristicdxp.shop
potentioallykeos.shop
reagoofydwqioo.shop
weiggheticulop.shop
xor-url
(PID) Process(6408) launcher.exe
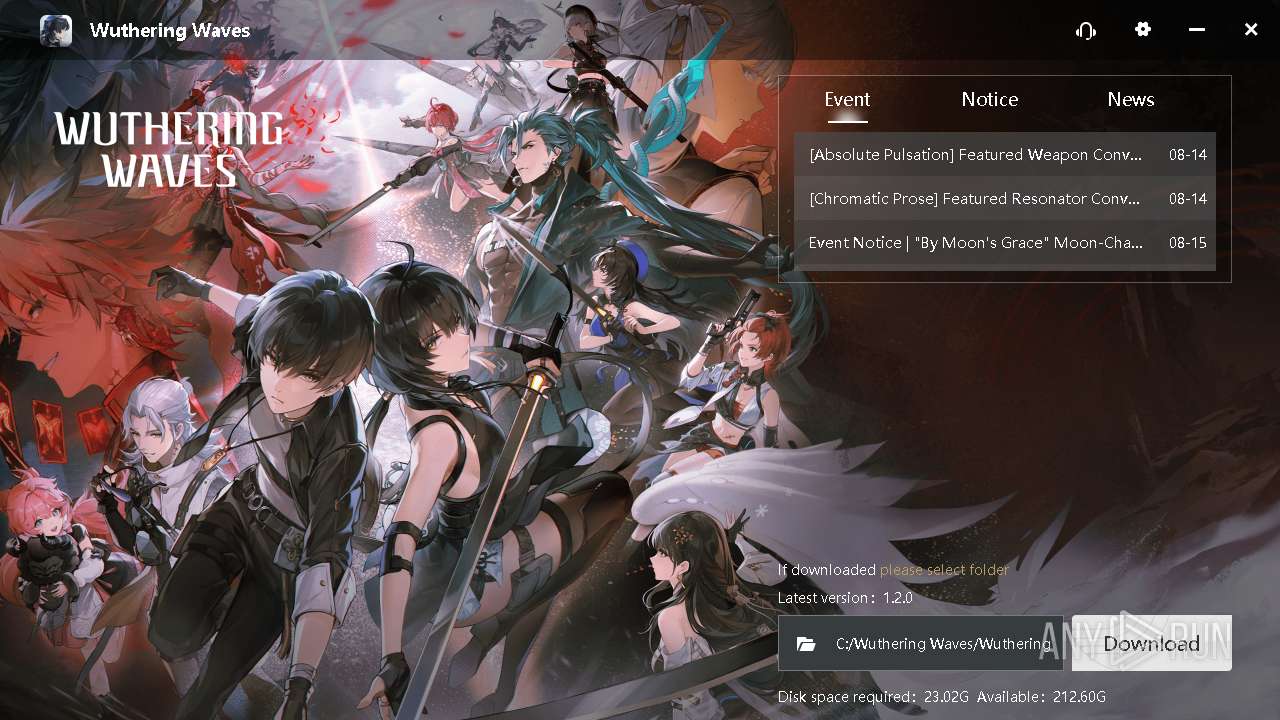
Decrypted-URLs (3)https://hw-pcdownload-qcloud.aki-game.net/pcstarter/prod/starter/background/nyXBPdijYH.zip,localAnimateZipFilePath:C:/Wuthering
https://prod-alicdn-gamestarter.kurogame.com/pcstarter/prod/game/G153/50004_obOHXFrFanqsaIEOmuKroCcbZkQRBC7c/social/en.json,
https://prod-alicdn-gamestarter.kurogame.com/pcstarter/prod/starter/50004_obOHXFrFanqsaIEOmuK
Decrypted-URLs (1)https://hw-pcdownload-qcloud.aki-game.net/pcstarter/prod/starter/background/nyXBPdijYH.zip,localAnimateZipFilePath:C:/Wuthering
Decrypted-URLs (5)https://hw-pcdownload-qcloud.aki-game.net/pcstarter/prod/starter/background/nyXBPdijYH.zip,localAnimateZipFilePath:C:/Wuthering
https://media-cdn-mingchao.kurogame.com/social-media/mini-icon/btn_reddit_28.png,succeed
https://prod-alicdn-gamestarter.kurogame.com/pcstarter/prod/game/G153/50004_obOHXFrFanqsaIEOmuKroCcbZkQRBC7c/social/en.json,
https://starter-server-api.kurogame.net/launcher/gray,strLanguage:en
https://starter-server-api.kurogame.net/launcher/gray?deviceId=1D1FB0BB-21B9-4FC0-B017-A4DADA231E17&gameId=G153&appId=50004_obOHXFrFanqsaIEOmuKroCcbZkQRBC7c&identify=installer
Decrypted-URLs (1)https://media-cdn-mingchao.kurogame.com/social-media/mini-icon/btn_reddit_28.png,succeed
Total processes
219
Monitored processes
80
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe" -ServerName:App.AppXbdkk0yrkwpcgeaem8zk81k8py1eaahny.mca | C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1060 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8036 --field-trial-handle=2424,i,6695159631684603315,11568911476225948883,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1124 | "C:\Windows\System32\cmd.exe" /c rmdir /s /q "C:\Wuthering Waves\tqm64\stm\" | C:\Windows\System32\cmd.exe | — | TQMCenter_64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5628 --field-trial-handle=2424,i,6695159631684603315,11568911476225948883,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2324 | "C:\Wuthering Waves\KRInstallExternal.exe" ewogICAgImRiX3BhdGgiOiAiQzpcXFVzZXJzXFxhZG1pblxcQXBwRGF0YVxcUm9hbWluZ1xcS1JMYXVuY2hlclxcRzE1M1xcQzUwMDA0XFwiLAogICAgImRpZCI6ICIxRDFGQjBCQi0yMUI5LTRGQzAtQjAxNy1BNERBREEyMzFFMTciLAogICAgInJlcG9ydF9pZCI6ICI1ZDQ4MTNkZTBlODk0MDJmYTI2ZWE2MmU0YjkzZDNjYSIsCiAgICAicmVwb3J0X2tleSI6ICJNSUdmTUEwR0NTcUdTSWIzRFFFQkFRVUFBNEdOQURDQmlRS0JnUURDSy9MMStnc2YvWXFJcXNLbElLSDhLOGRmRitPSlVmdzRJdkNuNU9sbytyRUszYlowclMrMncvKzl4TS90c3d2ZDU1Y1BWVUhzWkQ3a1RzbUl2K0dnNTdKanFQZmJYMW5Ub2FXZkNHdEVuWE11TWNtU3JkblBDOUZwNGs1WXlCY2ROV3lSb2Q3bGp5M1g1TGRudkVpWEQ0Qjk4WjRpVzg1YjFVODVseURjUFFJREFRQUIiLAogICAgInJlcG9ydF91cmwiOiAiaHR0cHM6Ly9xY2xvdWQtc2ctZGF0YXJlY2VpdmVyLmt1cm9nYW1lLnh5ei8iLAogICAgInV1aWQiOiAiezE0NmI0YzYzLTE2M2EtNDdjNC1hNzhhLTUyNDE0MTcxYWY1M30iCn0K | C:\Wuthering Waves\KRInstallExternal.exe | launcher.exe | ||||||||||||
User: admin Company: KURO TECHNOLOGY (HONG KONG) Integrity Level: HIGH Description: KRInstallExternal Version: 1.0.0.0 Modules
| |||||||||||||||
| 2992 | wmic cpu get Name | C:\Windows\System32\wbem\WMIC.exe | — | launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3648 --field-trial-handle=2424,i,6695159631684603315,11568911476225948883,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=8032 --field-trial-handle=2424,i,6695159631684603315,11568911476225948883,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
22 775
Read events
22 603
Write events
168
Delete events
4
Modification events
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6576) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
131
Suspicious files
439
Text files
607
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11dafb.TMP | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11dafb.TMP | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11db0b.TMP | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11db0b.TMP | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11db1b.TMP | — | |
MD5:— | SHA256:— | |||
| 6576 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
252
DNS requests
203
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 1.09 Kb | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 28 b | whitelisted |
2132 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 40.3 Kb | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 9.71 Kb | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 76.1 Kb | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 2.68 Kb | whitelisted |
8164 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725197896&P2=404&P3=2&P4=TJK5oEUEY53rHmREjoxPZtNMUJbze9ZfNlf1Pp%2fQyV9jnbollYH5lYD0YHdRbQ77DiZrR5qKYil4InTVyDzGjA%3d%3d | US | binary | 215 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4876 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4296 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6576 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6876 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6876 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6876 | msedge.exe | 104.18.37.111:443 | sourceforge.net | CLOUDFLARENET | — | unknown |
6876 | msedge.exe | 13.107.246.67:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6876 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
sourceforge.net |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
a.fsdn.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
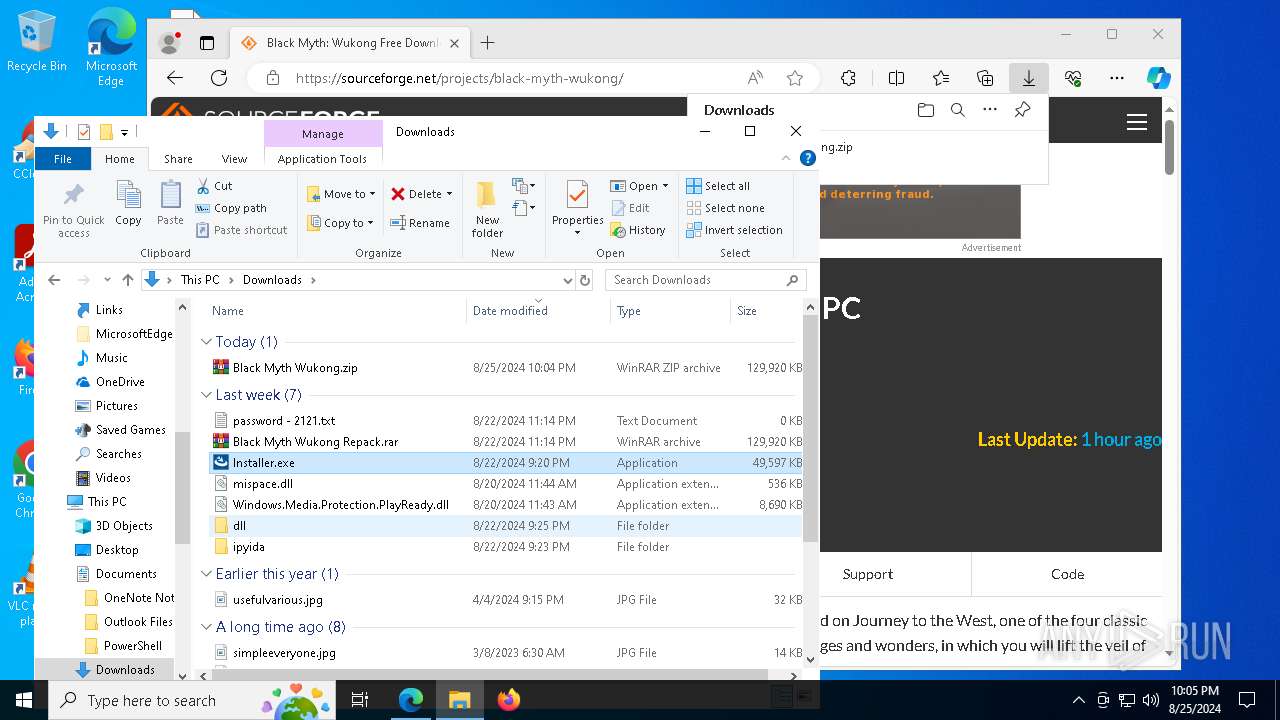
Threats
PID | Process | Class | Message |
|---|---|---|---|
7740 | Installer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
Process | Message |
|---|---|
Driver.exe | [KRInstall] NSIS Plugin Dir: C:\Users\admin\AppData\Local\Temp\nsf4882.tmp
|
Driver.exe | "dir:C:,size:228410793984"
|
Driver.exe | "dir:C:,size:228410662912"
|
Driver.exe | setup init com error , Cannot change thread mode after it is set.
|
Driver.exe | get getComputerNumber success
|
Driver.exe | setup shushu login
|
Driver.exe | [KRInstall] OnStartExtractFiles
|
Driver.exe | [KRInstall] Install Dir: C:\Wuthering Waves
|
Driver.exe | qt.network.ssl: QSslSocket::connectToHostEncrypted: TLS initialization failed
|
Driver.exe | qt.network.ssl: QSslSocket::connectToHostEncrypted: TLS initialization failed
|