| File name: | c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe |
| Full analysis: | https://app.any.run/tasks/e7de9fec-c3f7-4a29-908d-c41f4d9dbed1 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | February 21, 2020, 18:00:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B282CB24537F0B729C786E56CDE3ECEC |
| SHA1: | 8638EDE0273E3E36F1B2176B582A6013C867390A |
| SHA256: | C5D0B5D2CFD6E96004A37B465851B4435A5A82F2E588557952EE45010FA90B08 |
| SSDEEP: | 24576:UOn6uMvoNksN0AQgrG5abK1HoOiod+Mn7AHGtQUwMeVihTn8rVz/IQRhgzE:UQQoNkUQwG5abK5B2MnEH9VihT8rB/IJ |
MALICIOUS
Changes the autorun value in the registry
- c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe (PID: 3580)
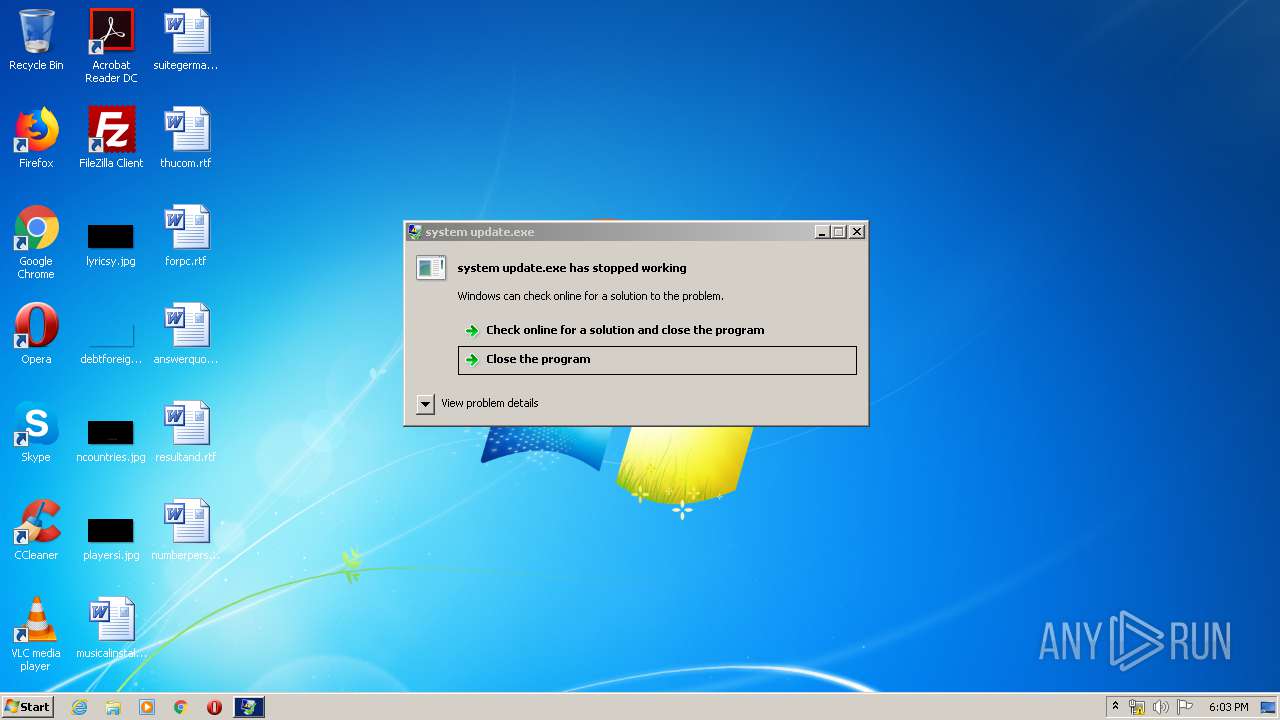
Runs injected code in another process
- system update.exe (PID: 3968)
Application was injected by another process
- explorer.exe (PID: 372)
Connects to CnC server
- system update.exe (PID: 3968)
AVEMARIA was detected
- system update.exe (PID: 3968)
SUSPICIOUS
Executable content was dropped or overwritten
- c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe (PID: 3580)
Creates files in the user directory
- c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe (PID: 3580)
Starts itself from another location
- c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe (PID: 3580)
Reads the machine GUID from the registry
- system update.exe (PID: 3968)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:19 20:10:39+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 820736 |
| InitializedDataSize: | 413184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e9f6 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.15.2.9590 |
| ProductVersionNumber: | 5.15.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | windows update |
| FileDescription: | WinSCP: SFTP, FTP, WebDAV, S3 and SCP client |
| CompanyName: | microsoft |
| LegalCopyright: | (c) 2000-2019 Martin Prikryl |
| ProductVersion: | 5.15.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Feb-2020 19:10:39 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| ProductName: | windows update |
| FileDescription: | WinSCP: SFTP, FTP, WebDAV, S3 and SCP client |
| CompanyName: | microsoft |
| LegalCopyright: | (c) 2000-2019 Martin Prikryl |
| ProductVersion: | 5.15.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Feb-2020 19:10:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000C854C | 0x000C8600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54433 |
.rdata | 0x000CA000 | 0x00025CF4 | 0x00025E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.87268 |
.data | 0x000F0000 | 0x00034FCC | 0x00033800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.67713 |
.rsrc | 0x00125000 | 0x0000048C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70308 |
.reloc | 0x00126000 | 0x0000B138 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.5948 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3580 | "C:\Users\admin\AppData\Local\Temp\c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe" | C:\Users\admin\AppData\Local\Temp\c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Roaming\system update.exe" | C:\Users\admin\AppData\Roaming\system update.exe | c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
41
Read events
28
Write events
13
Delete events
0
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @explorer.exe,-7001 |
Value: Find Help topics, tutorials, troubleshooting, and other support services. | |||
| (PID) Process: | (3580) c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3580) c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (3580) c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\TTA34P140N |
| Operation: | write | Name: | inst |
Value: 6934C6811D622A38772C95A4AB8E2EF86EA2CF682B6439FDBF15385A534A59ECEDA637867F4A399D49DCBAE0C24BFA59BEDB825BEA2B880B44DD0241B5A0FB78EF48CAFF63111CE9030193E0367CF4C79A7F04C6CA3DFD3CA68F90D0BB3AB724A1E1 | |||
| (PID) Process: | (3580) c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | boot |
Value: C:\Users\admin\AppData\Roaming\system update.exe | |||
| (PID) Process: | (3968) system update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3968) system update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | c5d0b5d2cfd6e96004a37b465851b4435a5a82f2e588557952ee45010fa90b08.exe | C:\Users\admin\AppData\Roaming\system update.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | system update.exe | 91.192.100.52:10356 | — | SOFTplus Entwicklungen GmbH | CH | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3968 | system update.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
3968 | system update.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3968 | system update.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
1 ETPRO signatures available at the full report