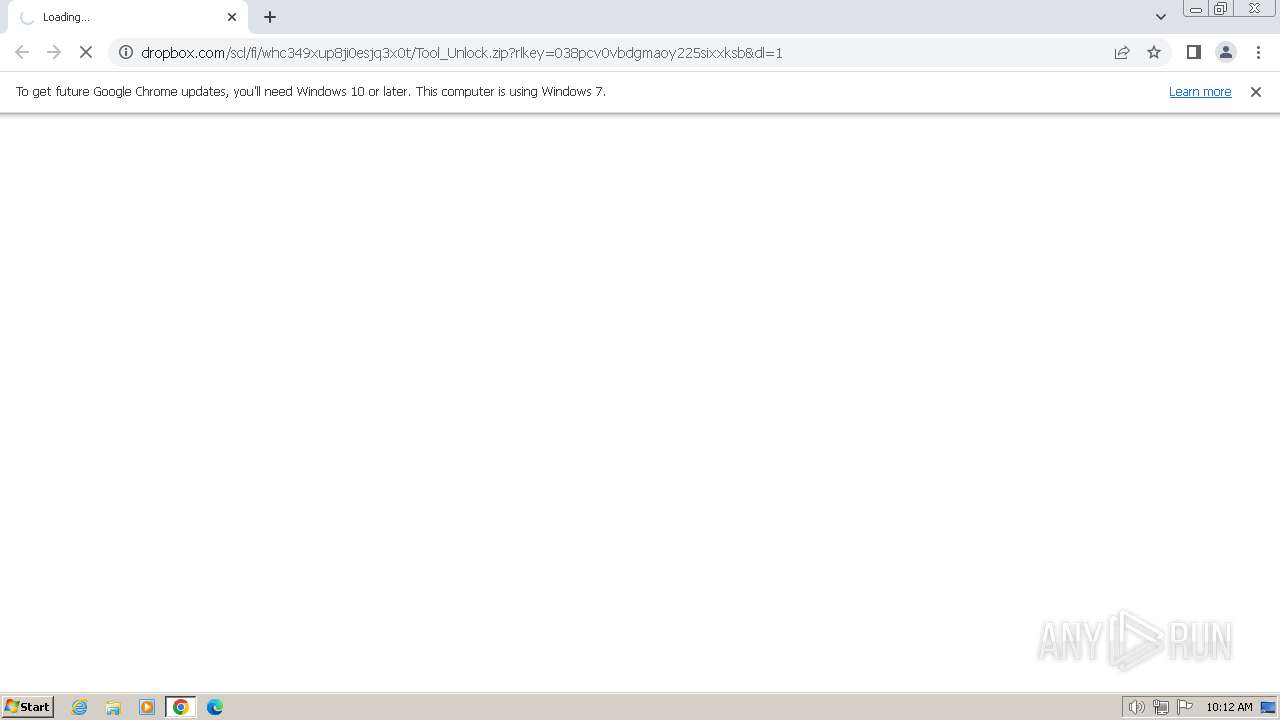
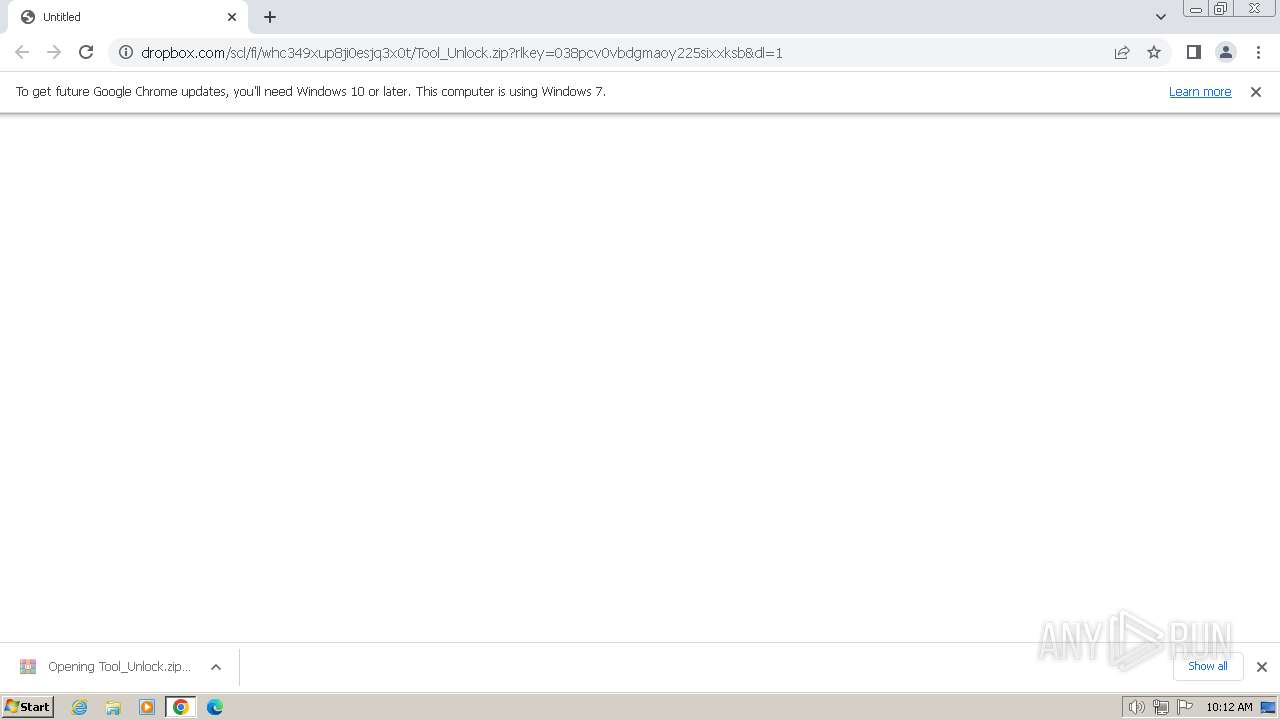
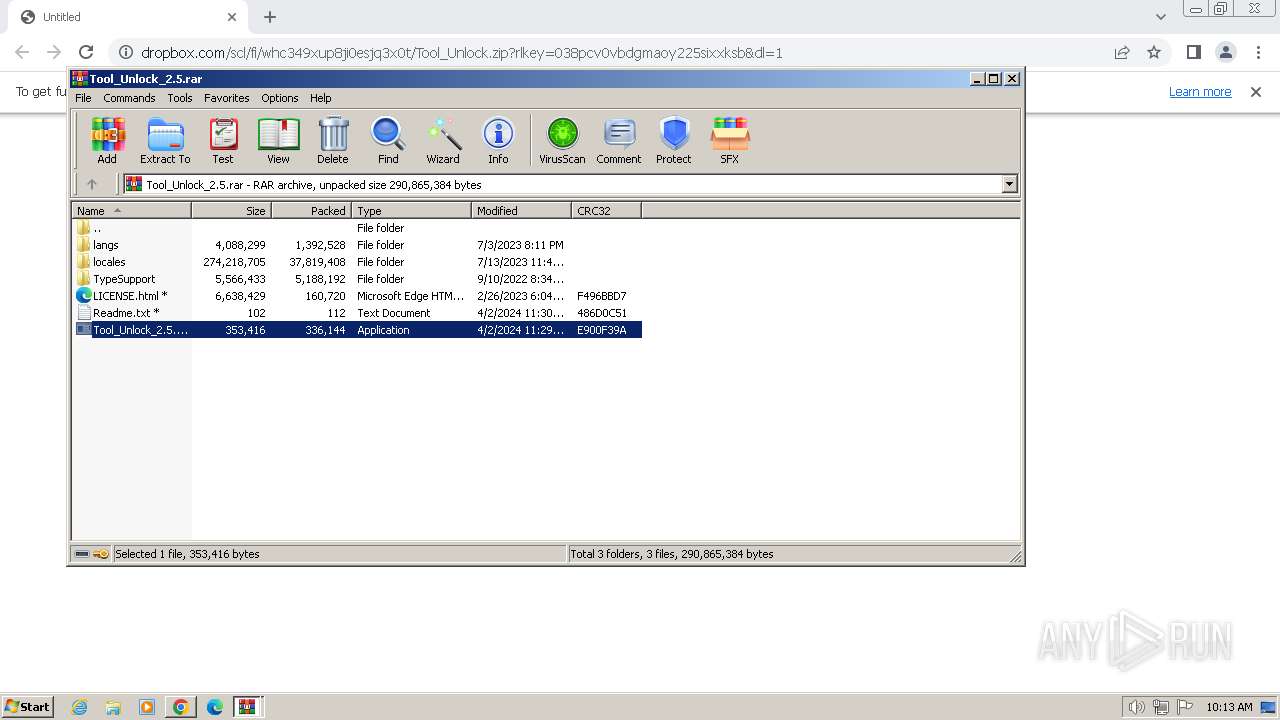
| URL: | https://www.dropbox.com/scl/fi/whc349xup8ji0esjq3x0t/Tool_Unlock.zip?rlkey=038pcv0vbdgmaoy225sixxksb&dl=1 |
| Full analysis: | https://app.any.run/tasks/db0a006b-aa47-4e85-ba8e-faef7ac39d31 |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | April 03, 2024, 09:11:48 |
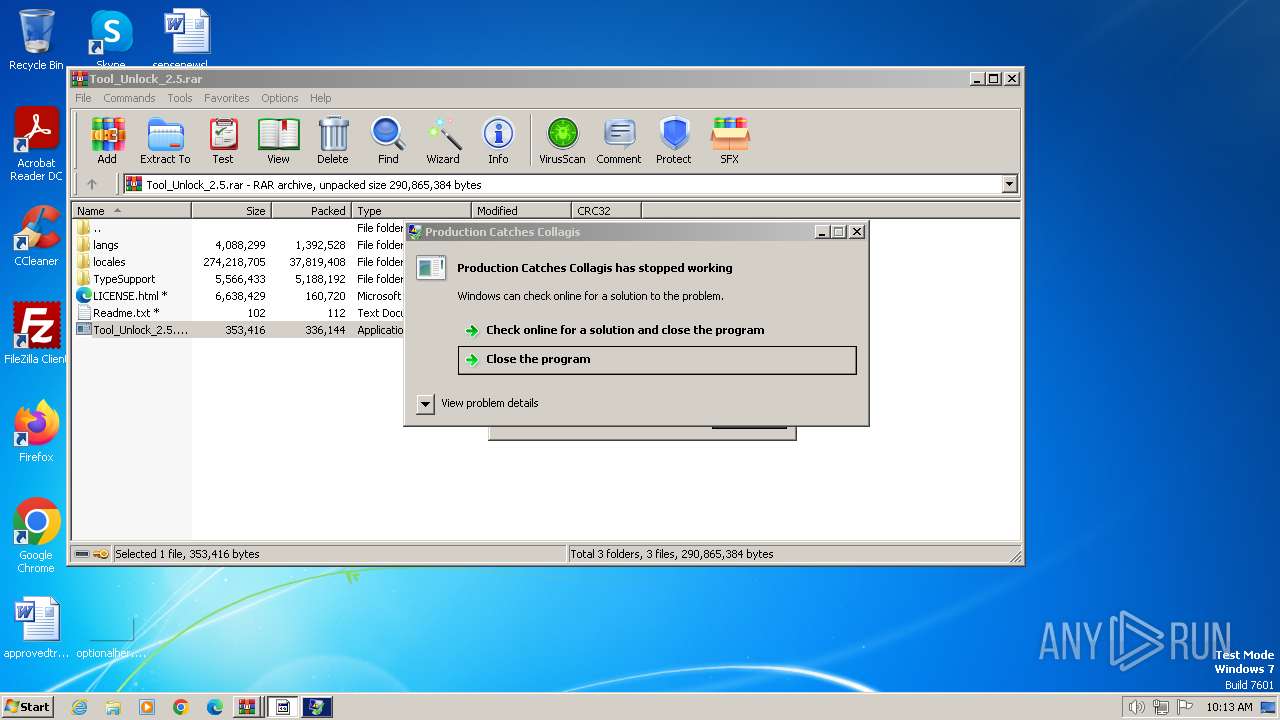
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AF86D1C896ECA53F2DFA588578976368 |
| SHA1: | F7DFDB2400AB52D5FE20EC83748EC93361D62ADF |
| SHA256: | C5775BDC61B5BB9EE0E8B7ED30F6B09FD2652CAE22C6633EB7FB219AFACC8ADD |
| SSDEEP: | 3:N8DSLcVHGkG6/4sAWPUbkkwXJOAcY8XE5HBCFHg9BWU:2OLHkcWPUbL15Y8XE5hCFA9BT |
MALICIOUS
REDLINE has been detected (YARA)
- RegAsm.exe (PID: 884)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 884)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 884)
SUSPICIOUS
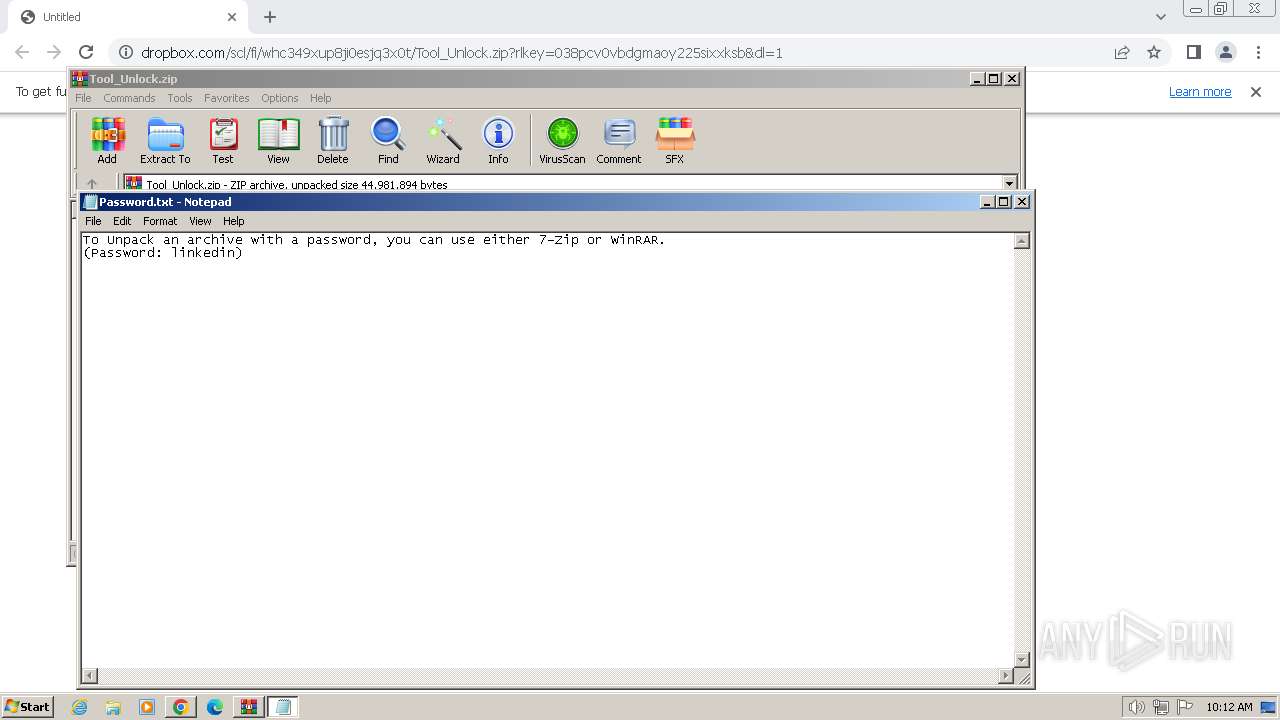
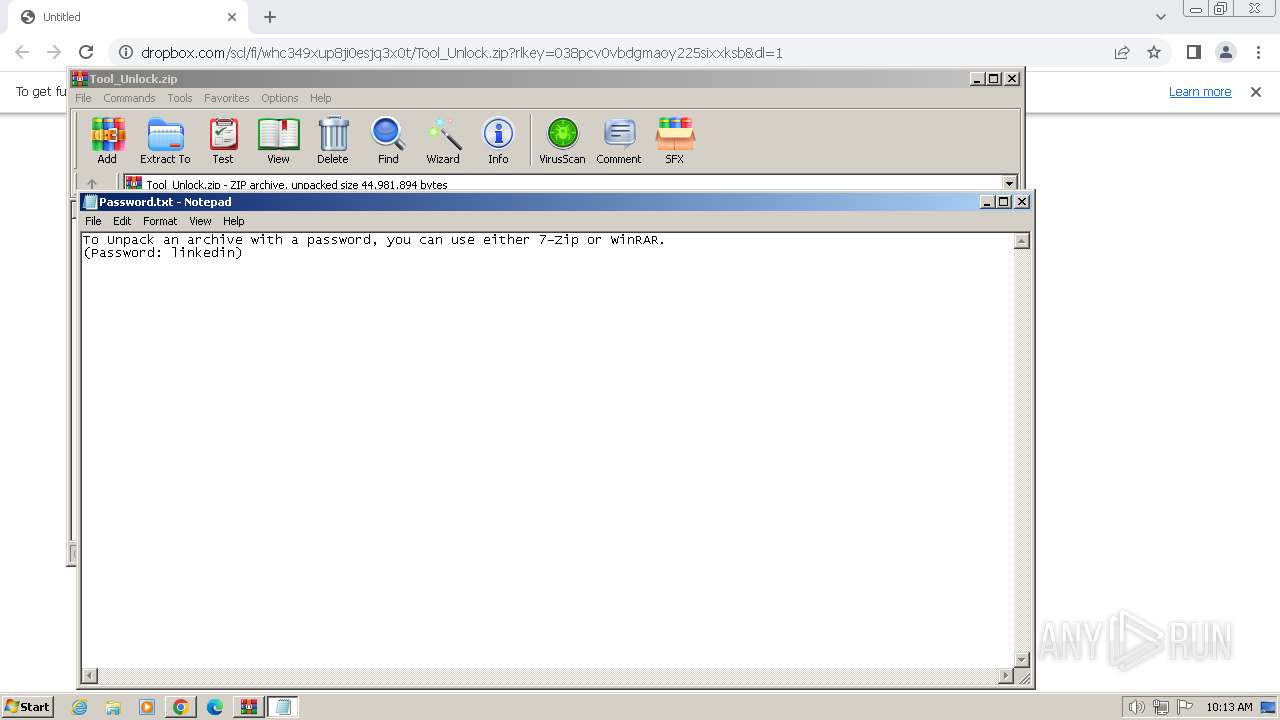
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 924)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 924)
- WinRAR.exe (PID: 1172)
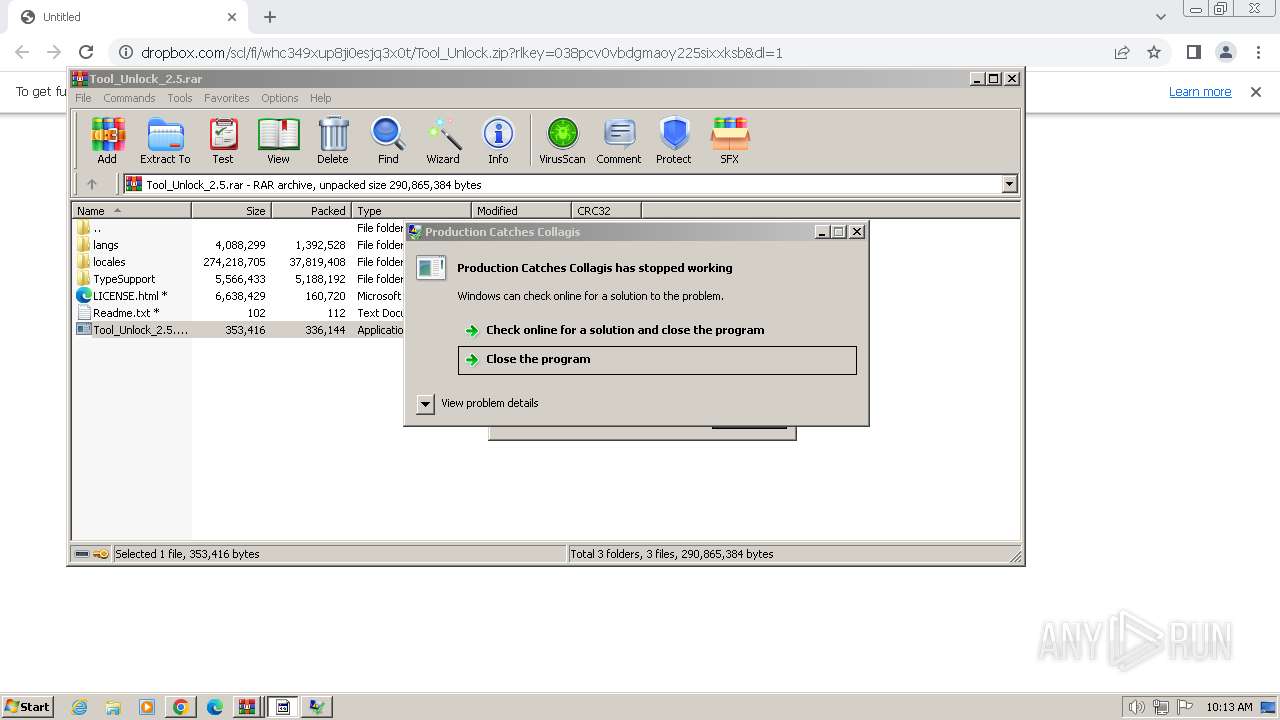
Application launched itself
- WinRAR.exe (PID: 924)
Connects to unusual port
- RegAsm.exe (PID: 884)
Non-standard symbols in registry
- RegAsm.exe (PID: 884)
Reads browser cookies
- RegAsm.exe (PID: 884)
Searches for installed software
- RegAsm.exe (PID: 884)
INFO
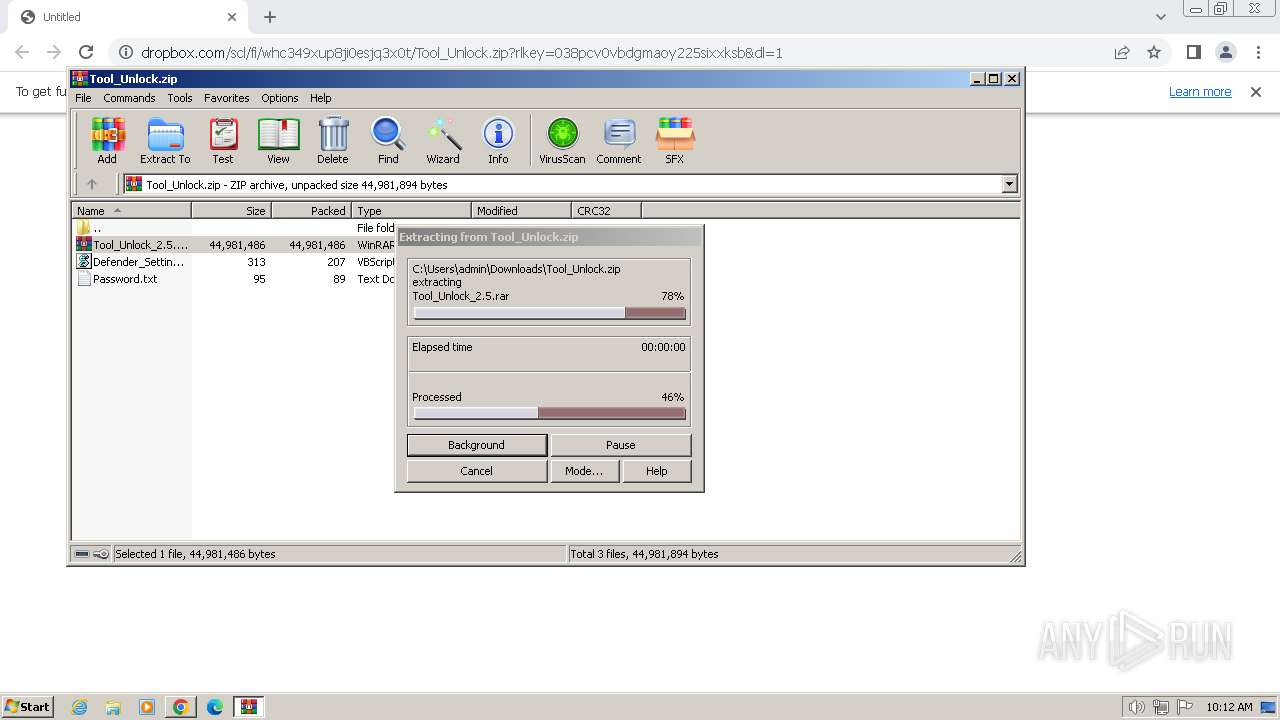
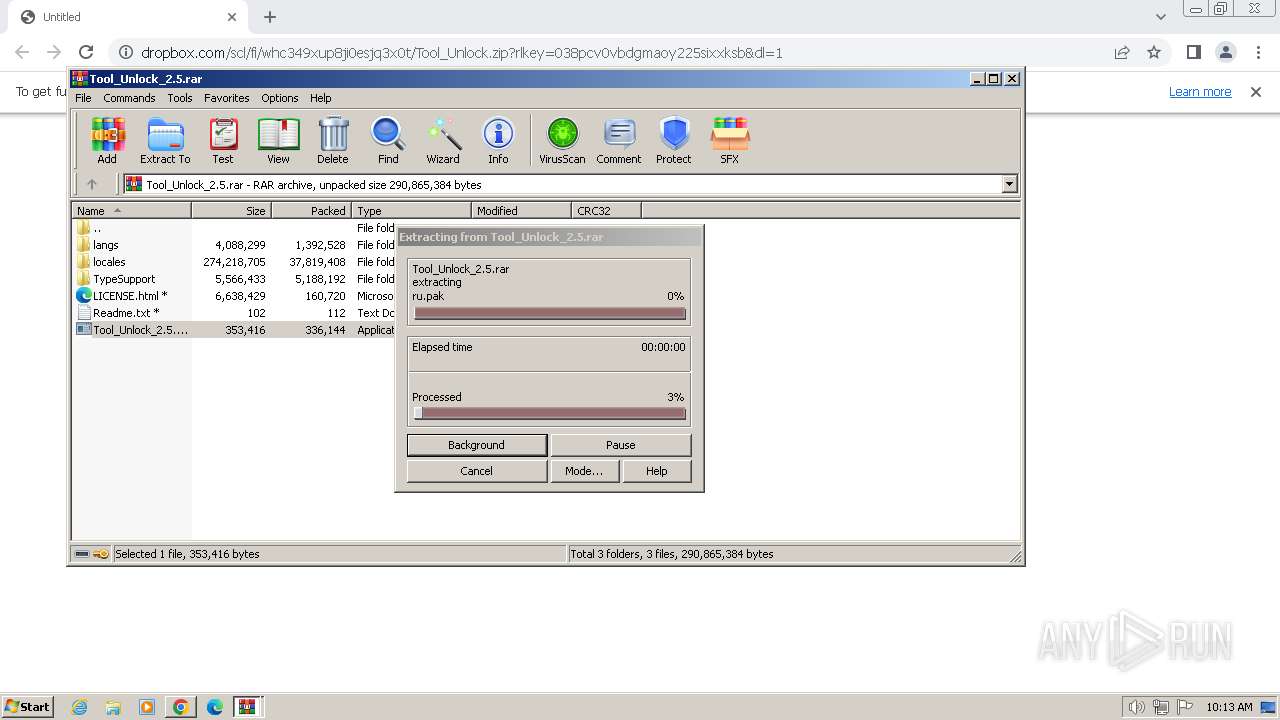
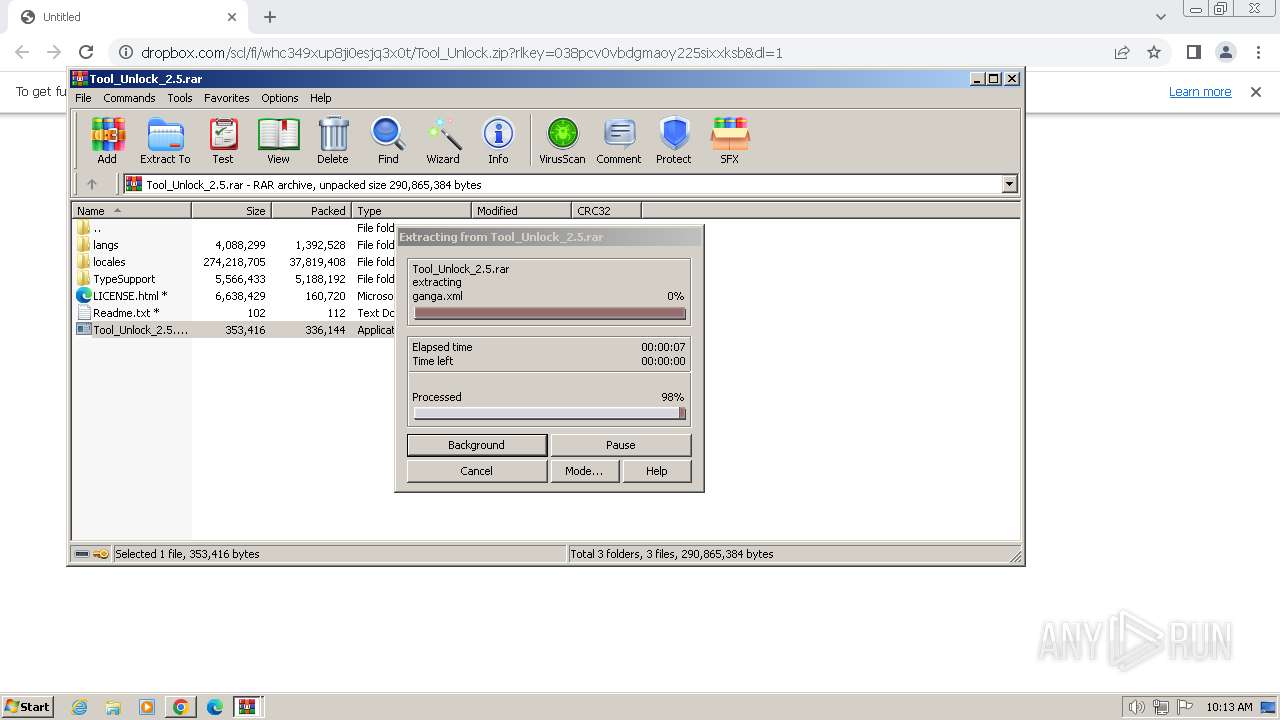
The process uses the downloaded file
- chrome.exe (PID: 1540)
- WinRAR.exe (PID: 924)
Reads the computer name
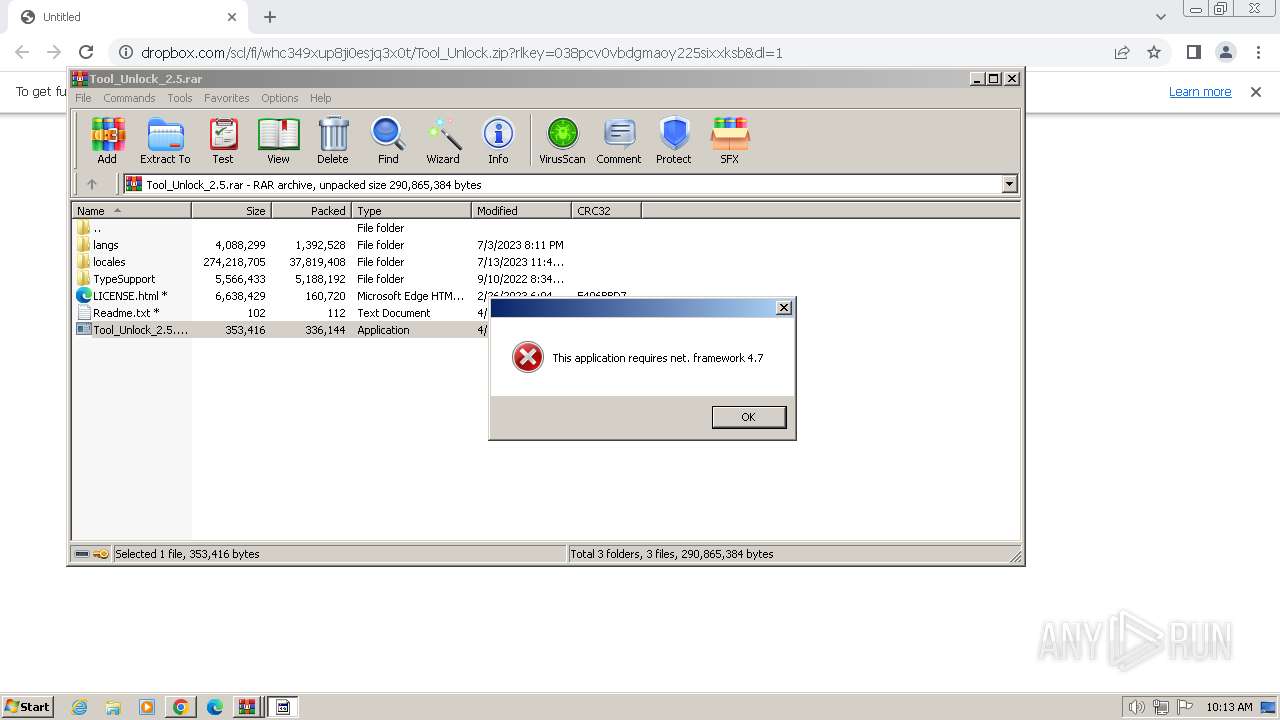
- Tool_Unlock_2.5.exe (PID: 3332)
- RegAsm.exe (PID: 884)
Checks supported languages
- RegAsm.exe (PID: 884)
- Tool_Unlock_2.5.exe (PID: 3332)
Creates files or folders in the user directory
- RegAsm.exe (PID: 884)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 884)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1172)
- chrome.exe (PID: 2104)
Application launched itself
- chrome.exe (PID: 3936)
Reads product name
- RegAsm.exe (PID: 884)
Reads Environment values
- RegAsm.exe (PID: 884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(884) RegAsm.exe
C2 (1)34.31.226.230:37558
Botnetdermantin
Version1
Total processes
63
Monitored processes
22
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1332 --field-trial-handle=1156,i,15448876778692707990,5015845601911243075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 4294967295 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 884 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | Tool_Unlock_2.5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
RedLine(PID) Process(884) RegAsm.exe C2 (1)34.31.226.230:37558 Botnetdermantin Version1 | |||||||||||||||
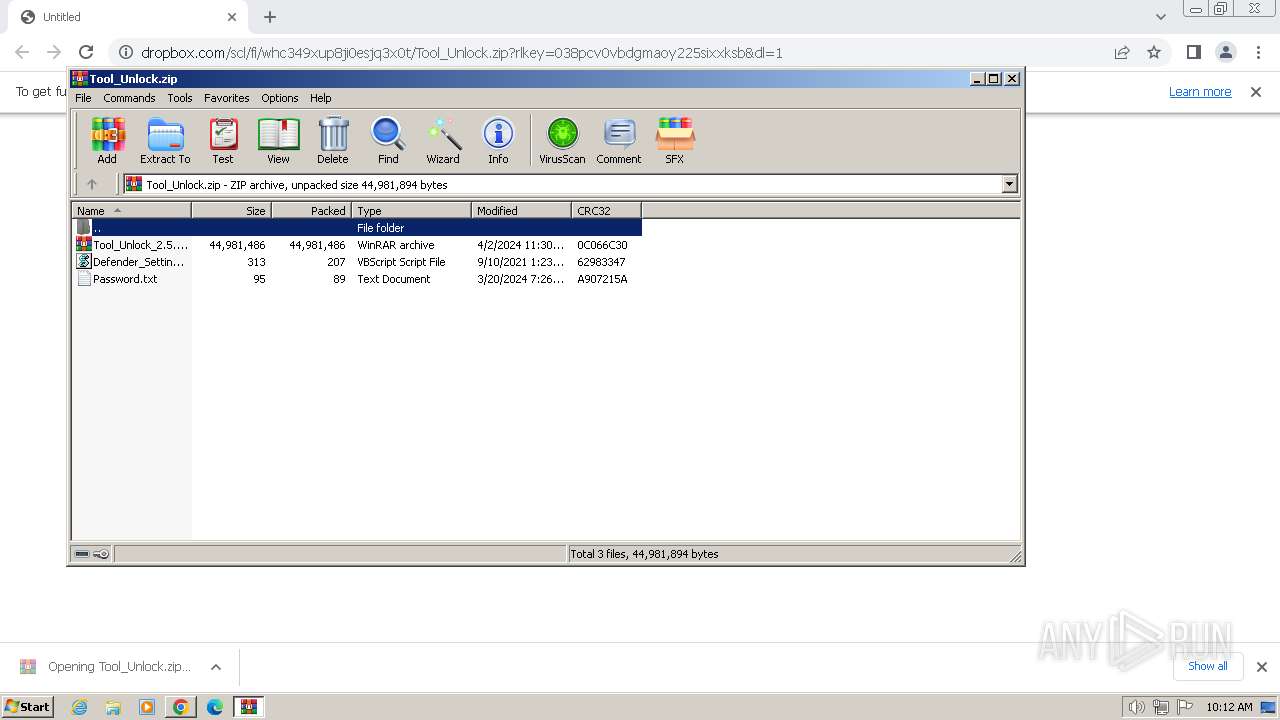
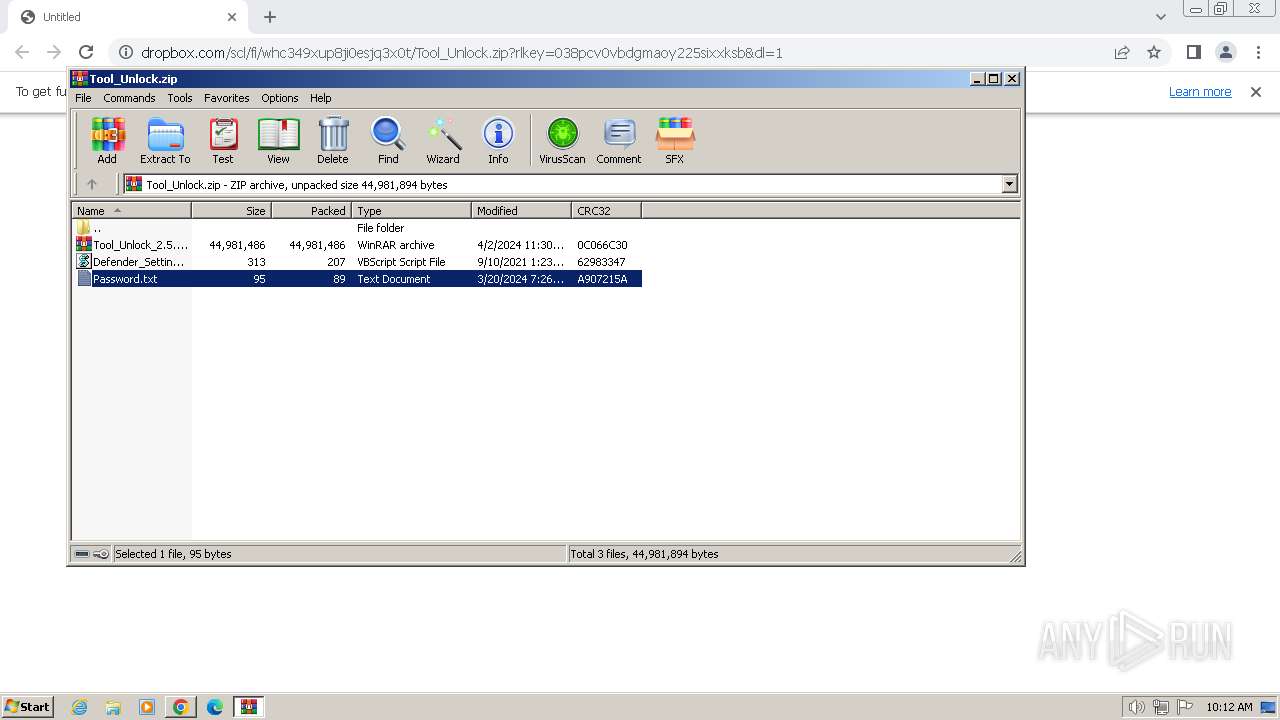
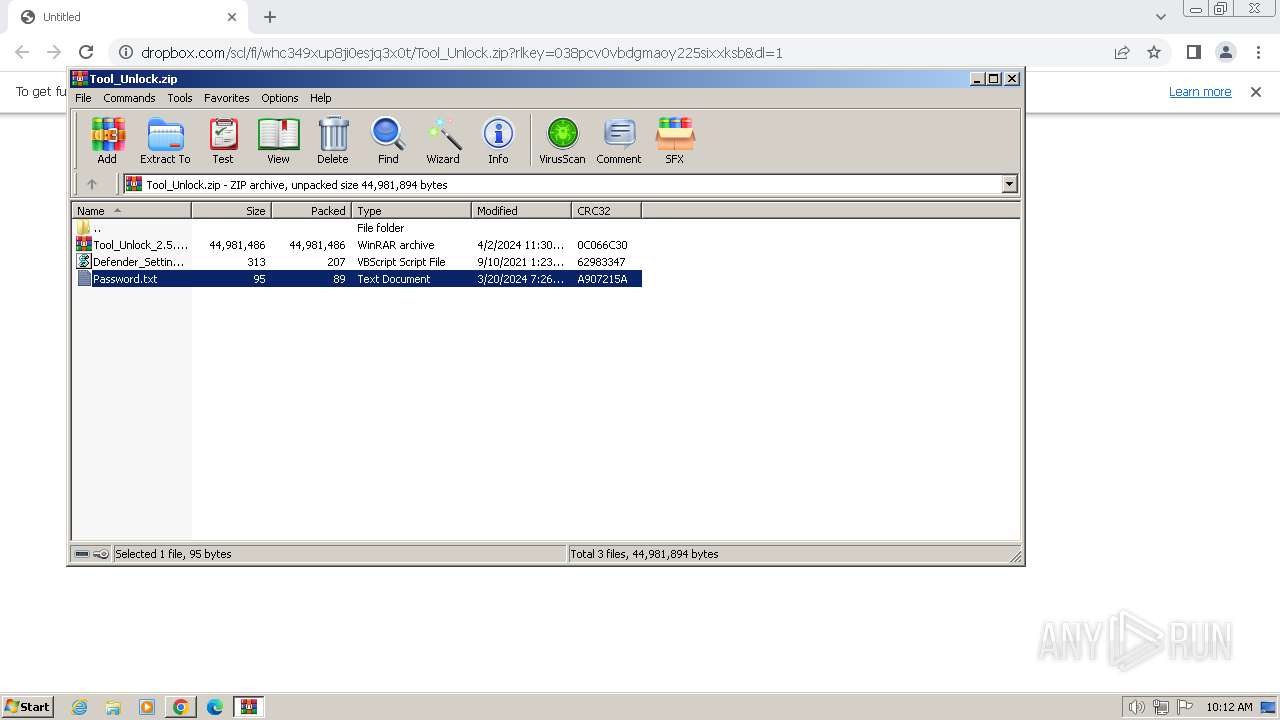
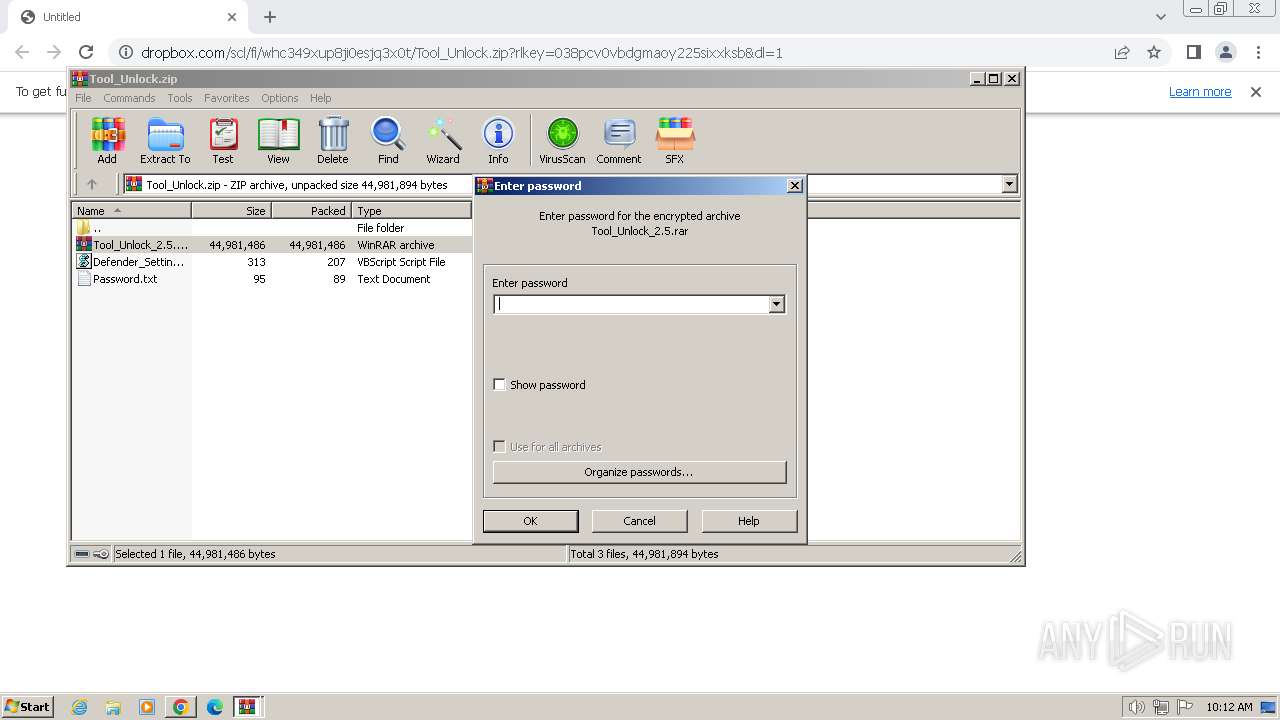
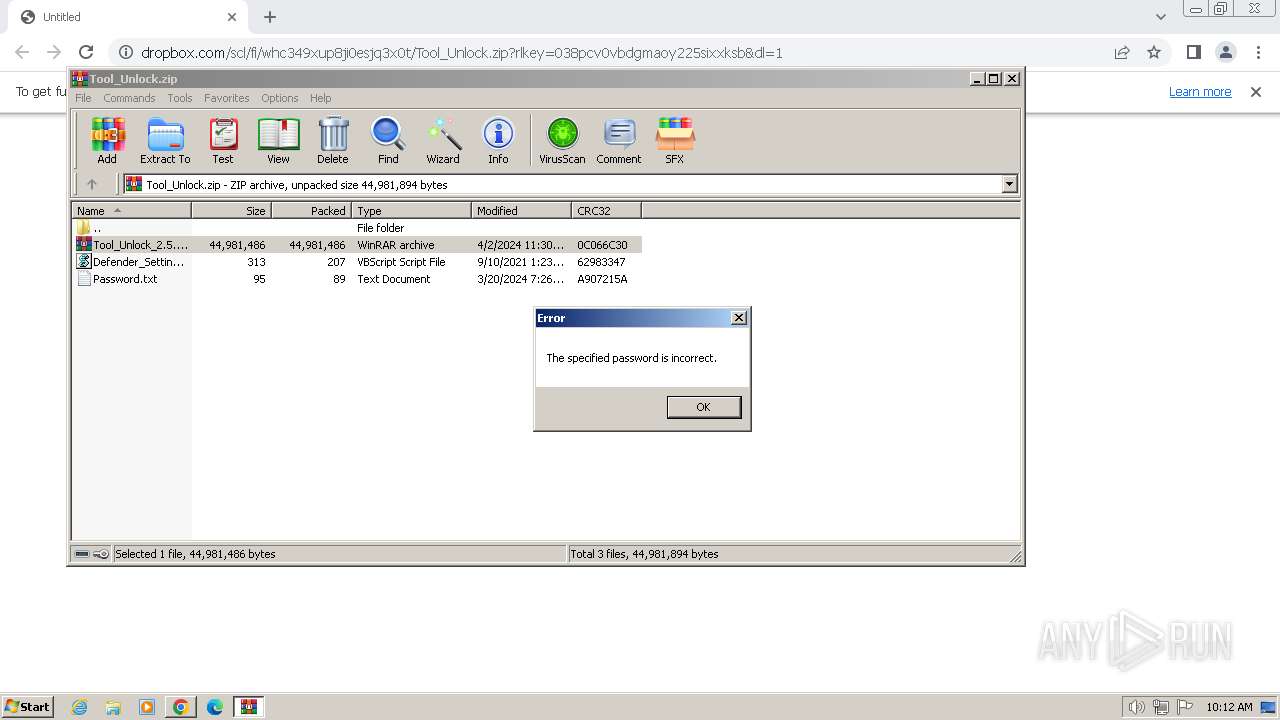
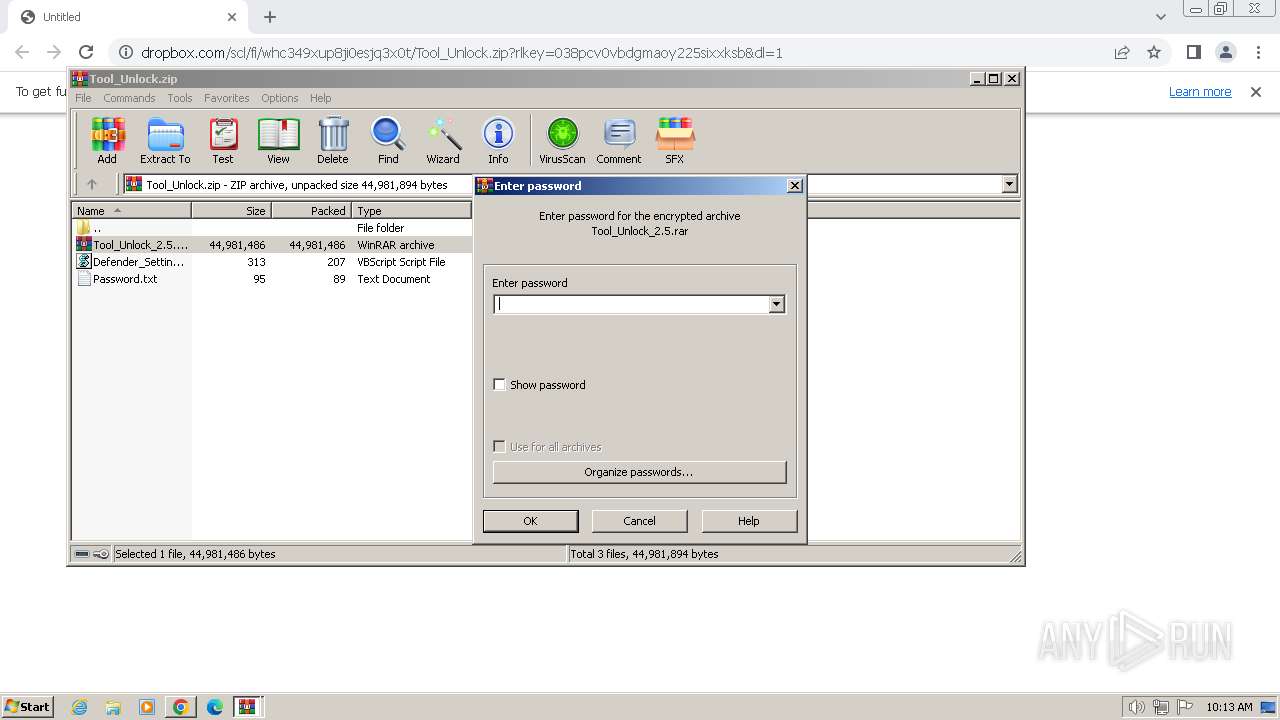
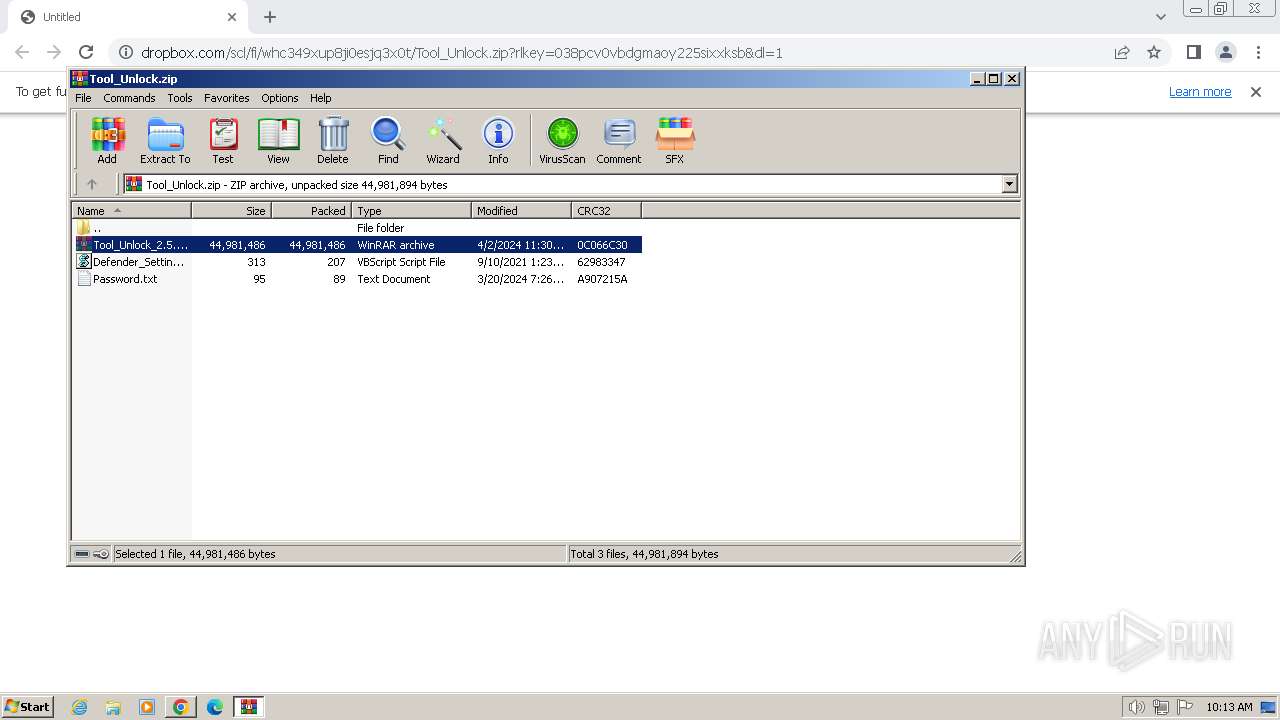
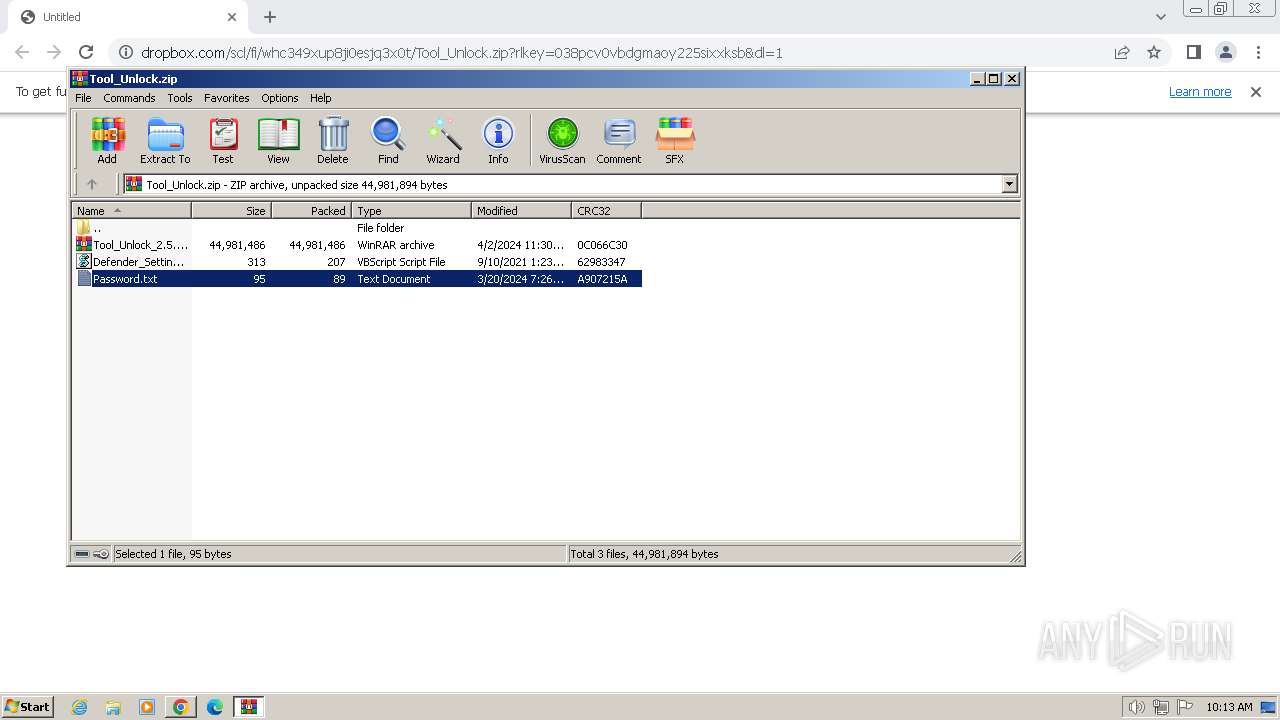
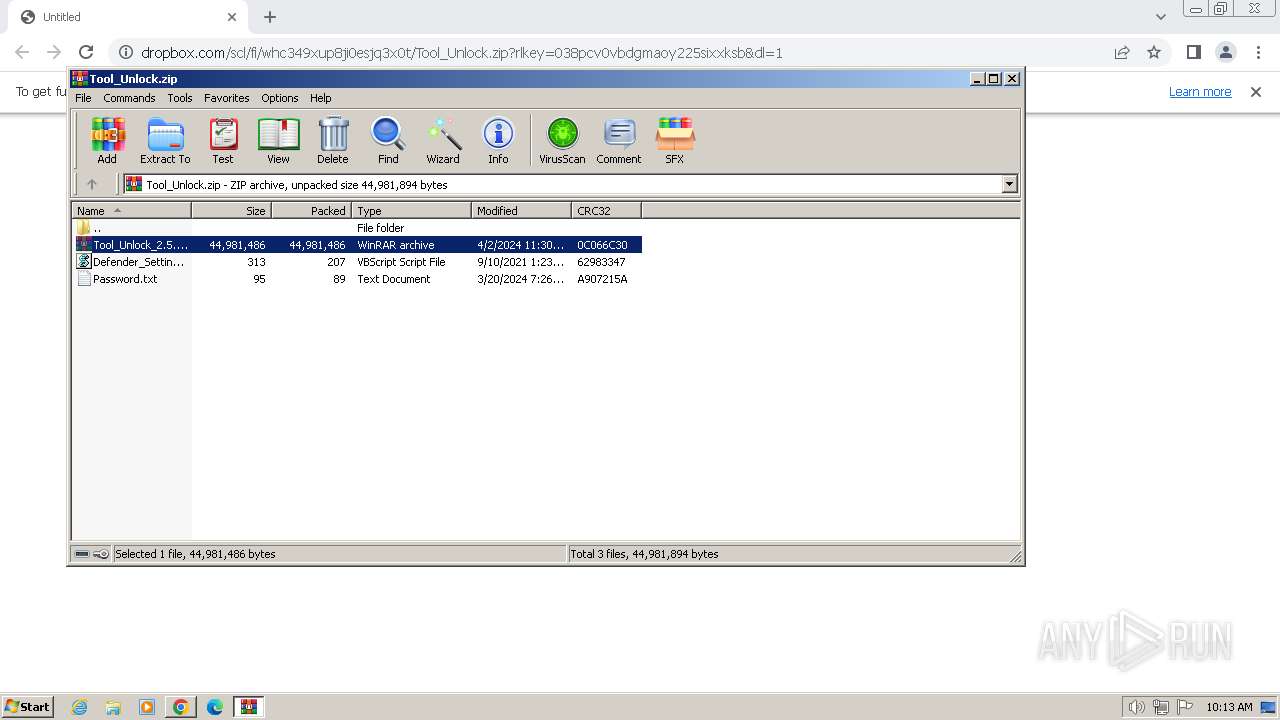
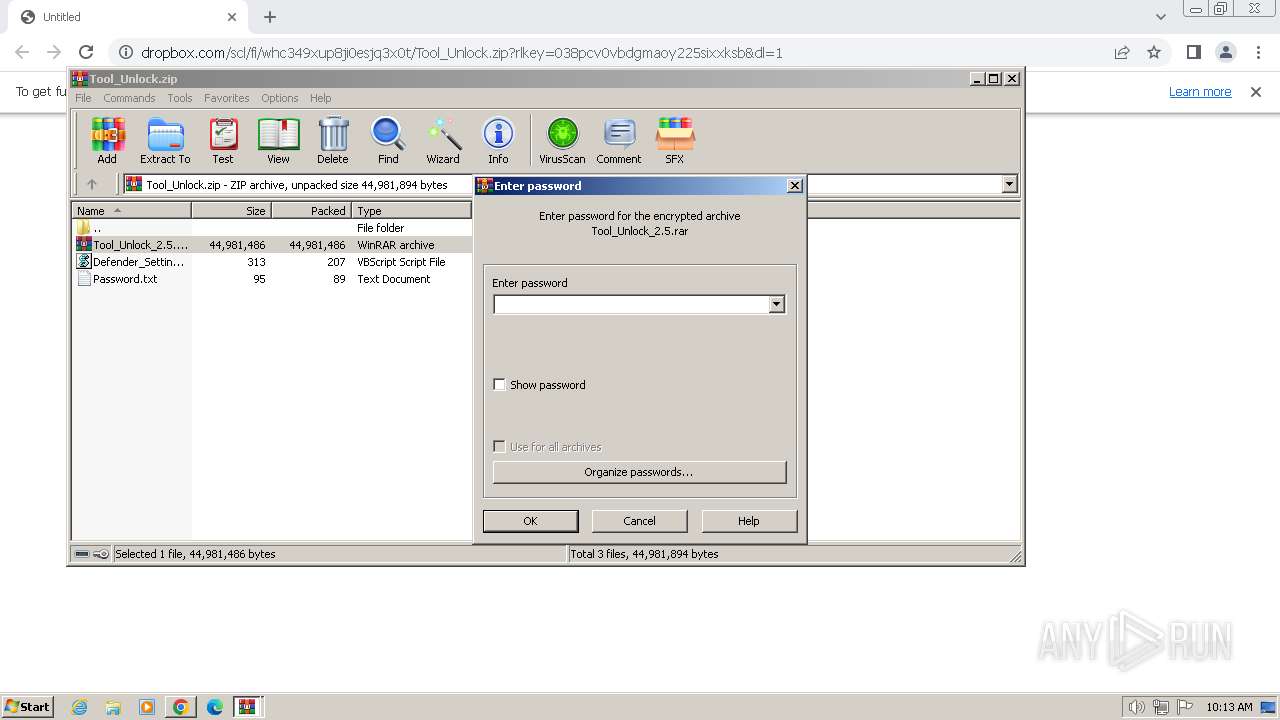
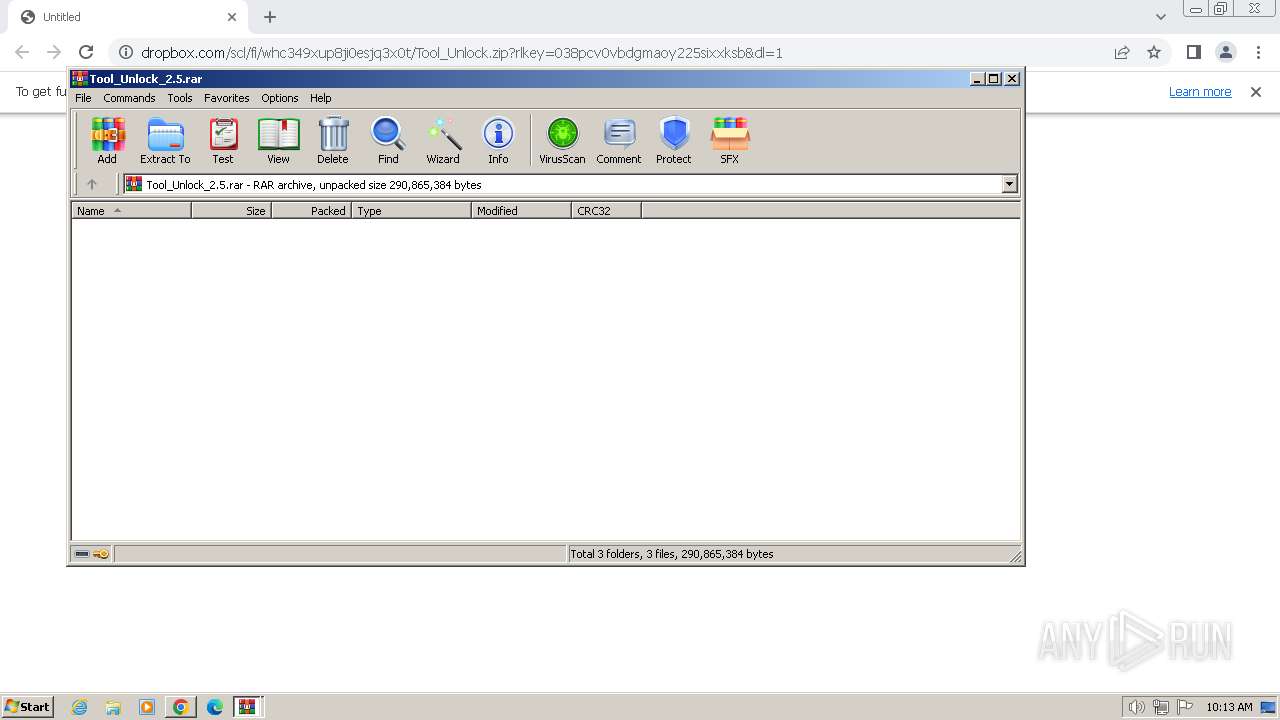
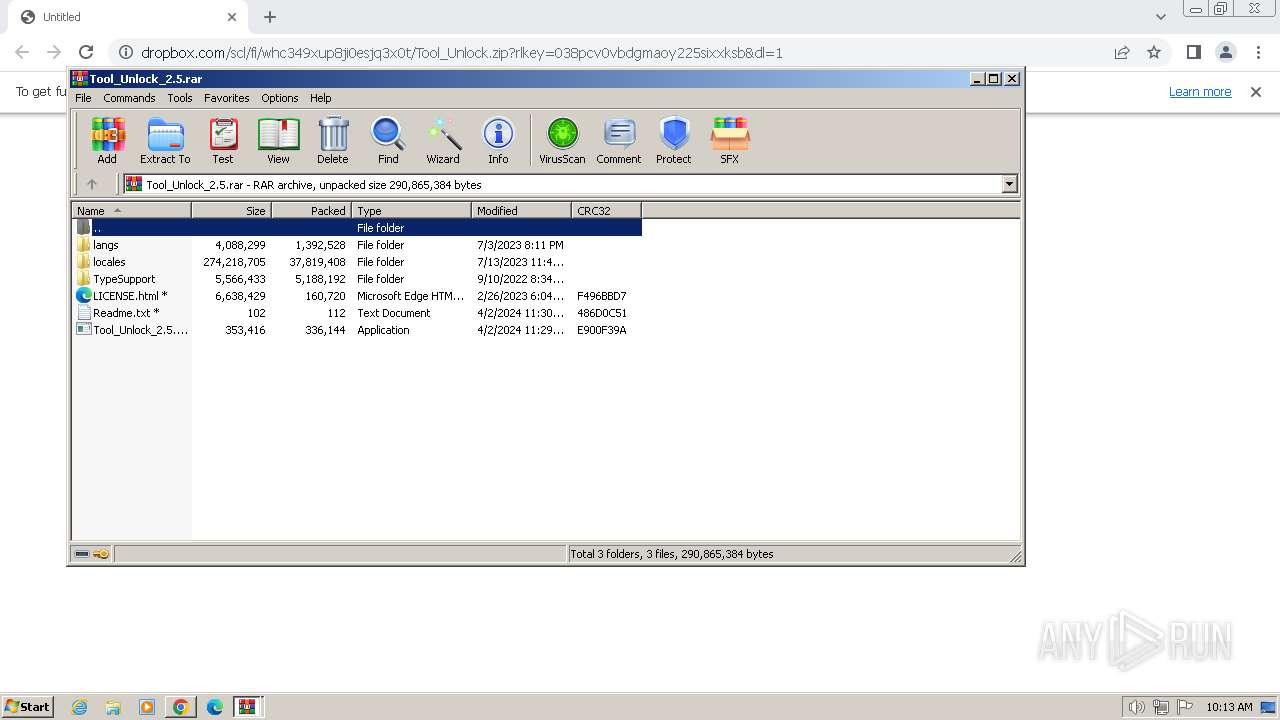
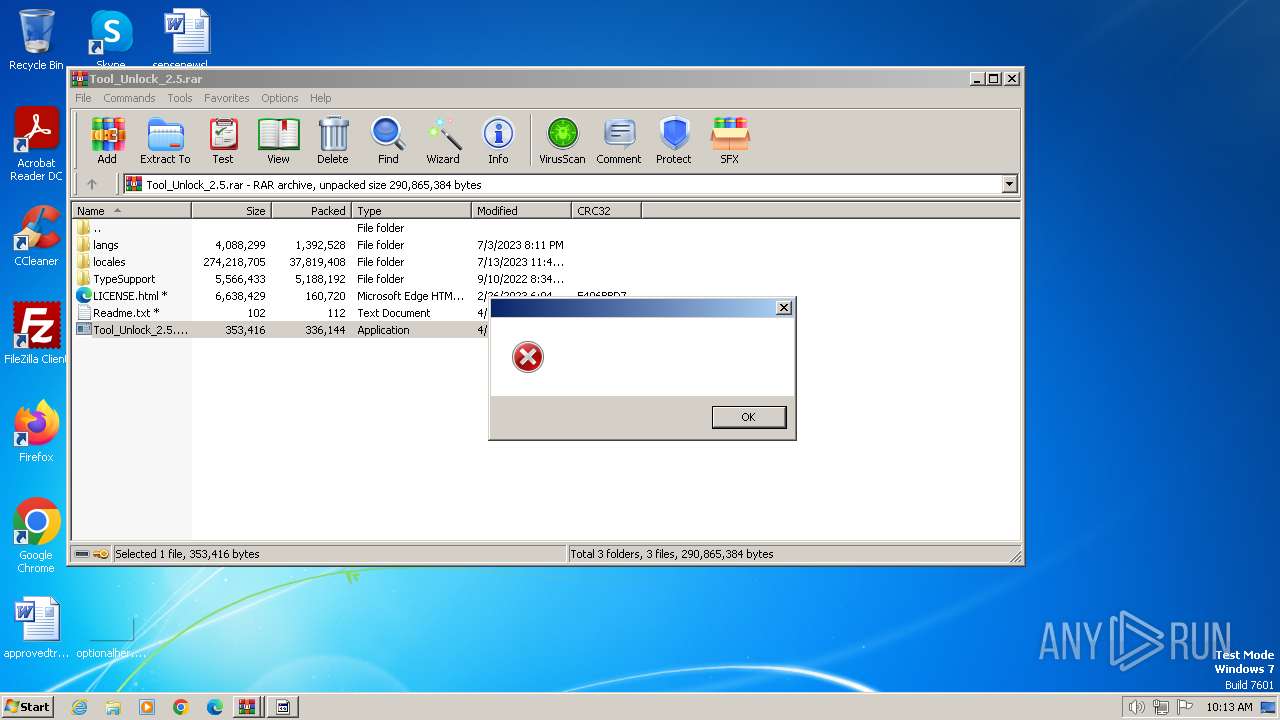
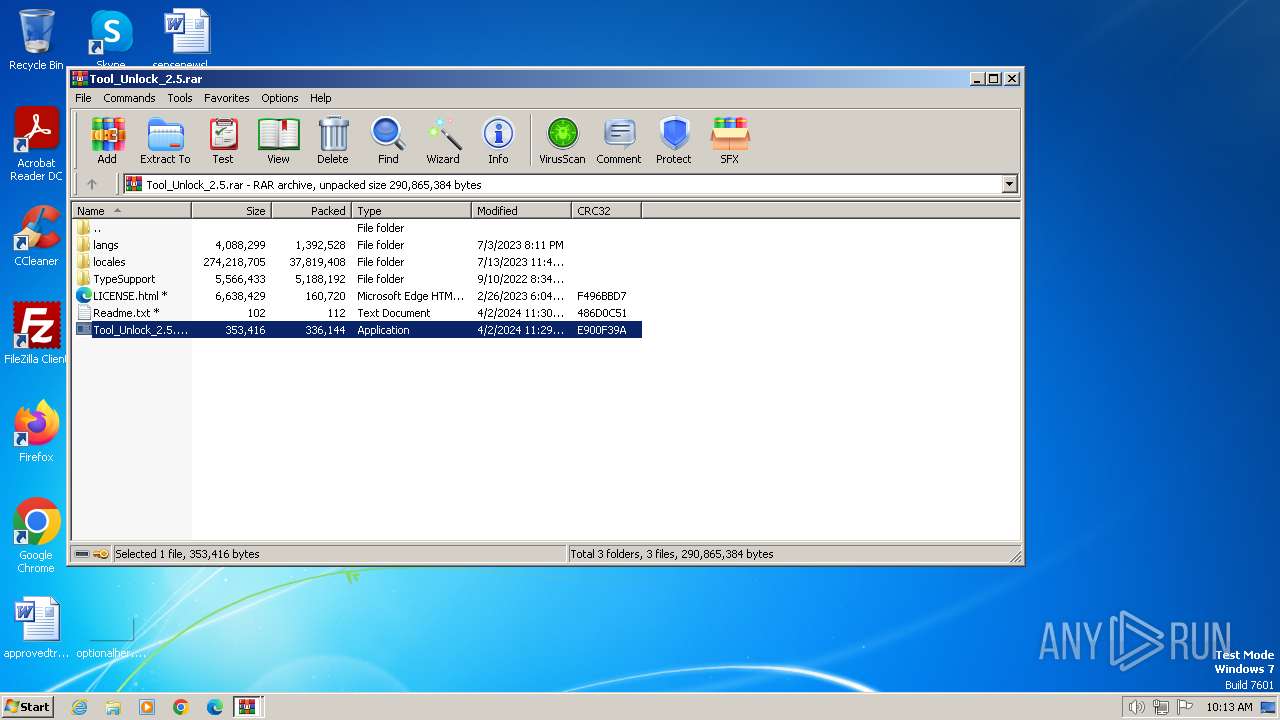
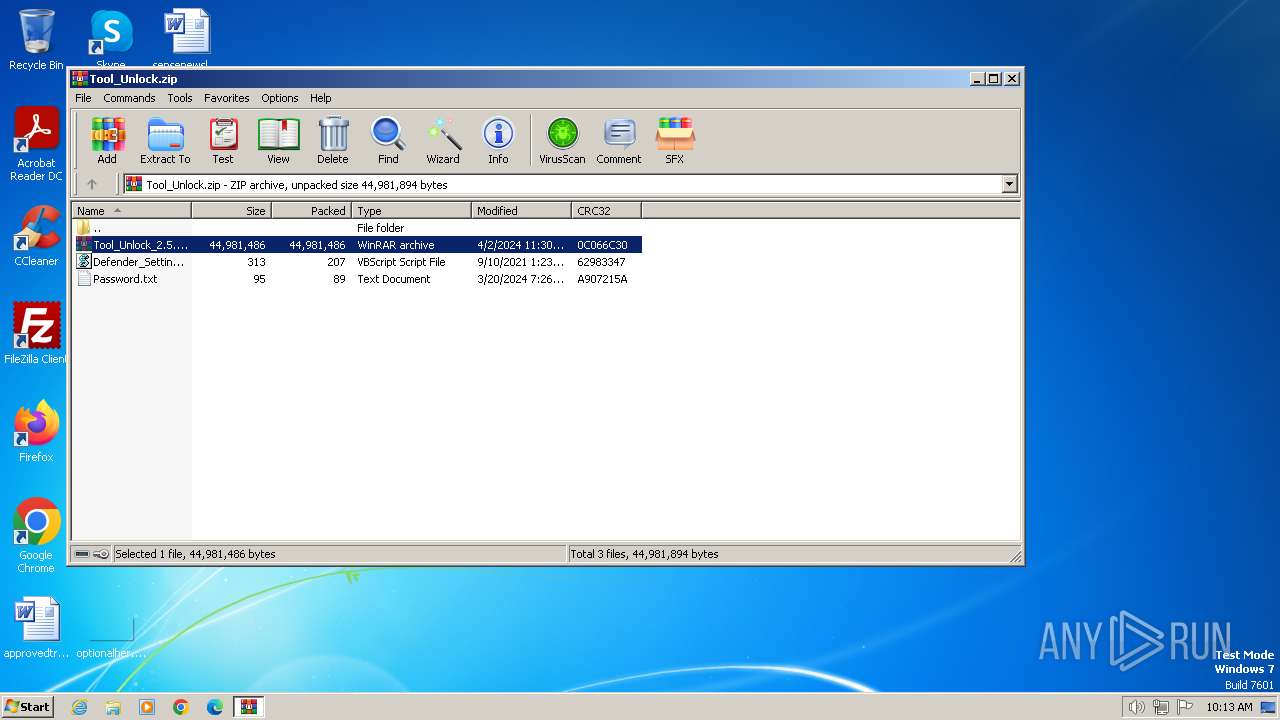
| 924 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Tool_Unlock.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3464 --field-trial-handle=1156,i,15448876778692707990,5015845601911243075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa924.4010\Password.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa924.7426\Tool_Unlock_2.5.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1292 --field-trial-handle=1156,i,15448876778692707990,5015845601911243075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=2128 --field-trial-handle=1156,i,15448876778692707990,5015845601911243075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa924.5658\Tool_Unlock_2.5.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 820
Read events
19 643
Write events
164
Delete events
13
Modification events
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
89
Suspicious files
58
Text files
185
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18397a.TMP | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1839a9.TMP | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c5c418ed-0fa8-461c-8c0d-94ed147ef864.tmp | binary | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1839c8.TMP | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
17
DNS requests
17
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad2qlmqj6ndvttv75s3yxlx3rrfq_8637/hfnkpimlhhgieaddgfemjhofmfblmnib_8637_all_ad7poul3jyodgptyz52jfcizkw4a.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad2qlmqj6ndvttv75s3yxlx3rrfq_8637/hfnkpimlhhgieaddgfemjhofmfblmnib_8637_all_ad7poul3jyodgptyz52jfcizkw4a.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad2qlmqj6ndvttv75s3yxlx3rrfq_8637/hfnkpimlhhgieaddgfemjhofmfblmnib_8637_all_ad7poul3jyodgptyz52jfcizkw4a.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad2qlmqj6ndvttv75s3yxlx3rrfq_8637/hfnkpimlhhgieaddgfemjhofmfblmnib_8637_all_ad7poul3jyodgptyz52jfcizkw4a.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1496 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
3936 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1496 | chrome.exe | 162.125.65.18:443 | www.dropbox.com | DROPBOX | NL | unknown |
1496 | chrome.exe | 162.125.66.15:443 | uc659afd7a53200a4b17d08a94f5.dl.dropboxusercontent.com | DROPBOX | DE | malicious |
3936 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1496 | chrome.exe | 172.217.16.132:443 | www.google.com | GOOGLE | US | whitelisted |
1496 | chrome.exe | 142.250.181.238:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.dropbox.com |
| shared |
uc659afd7a53200a4b17d08a94f5.dl.dropboxusercontent.com |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1496 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
884 | RegAsm.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
— | — | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer/MetaStealer Family Related (MC-NMF Authorization) |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer/MetaStealer Family Activity (Response) |
— | — | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |