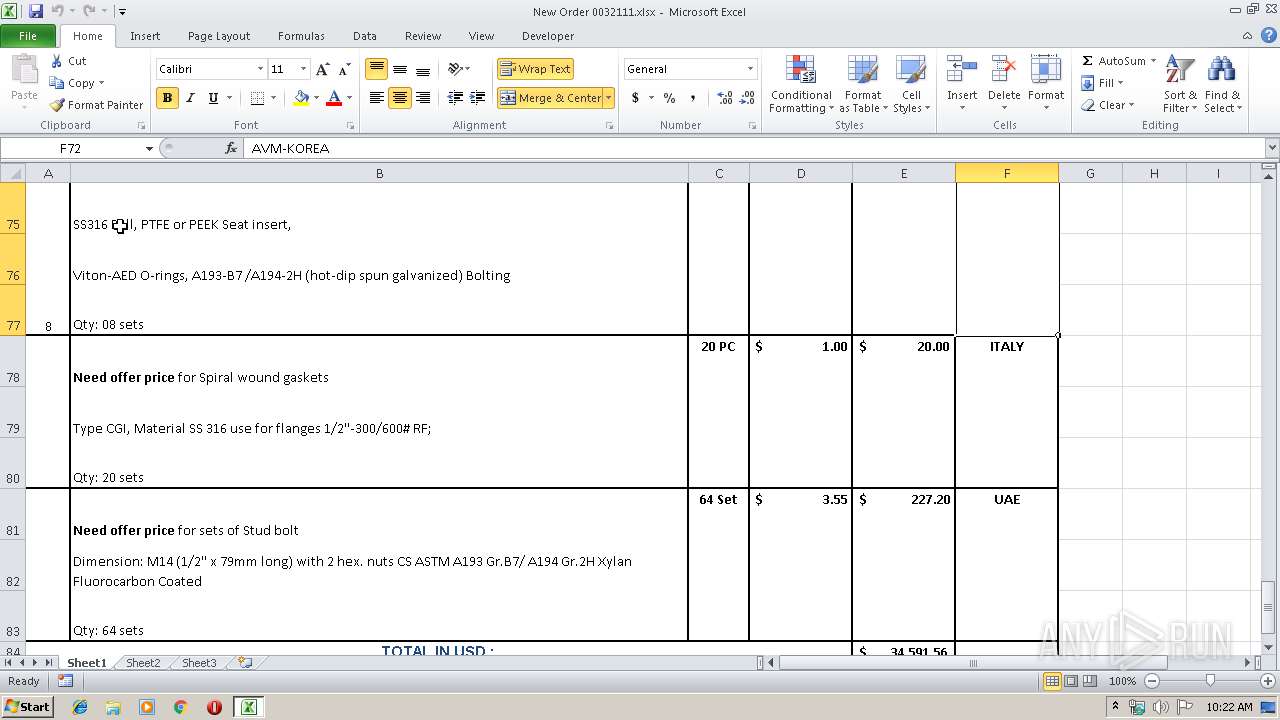
| File name: | New Order 0032111.xlsx |
| Full analysis: | https://app.any.run/tasks/0f31e1f5-a007-4ef8-89f6-5acf63e94808 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | June 12, 2019, 09:22:18 |
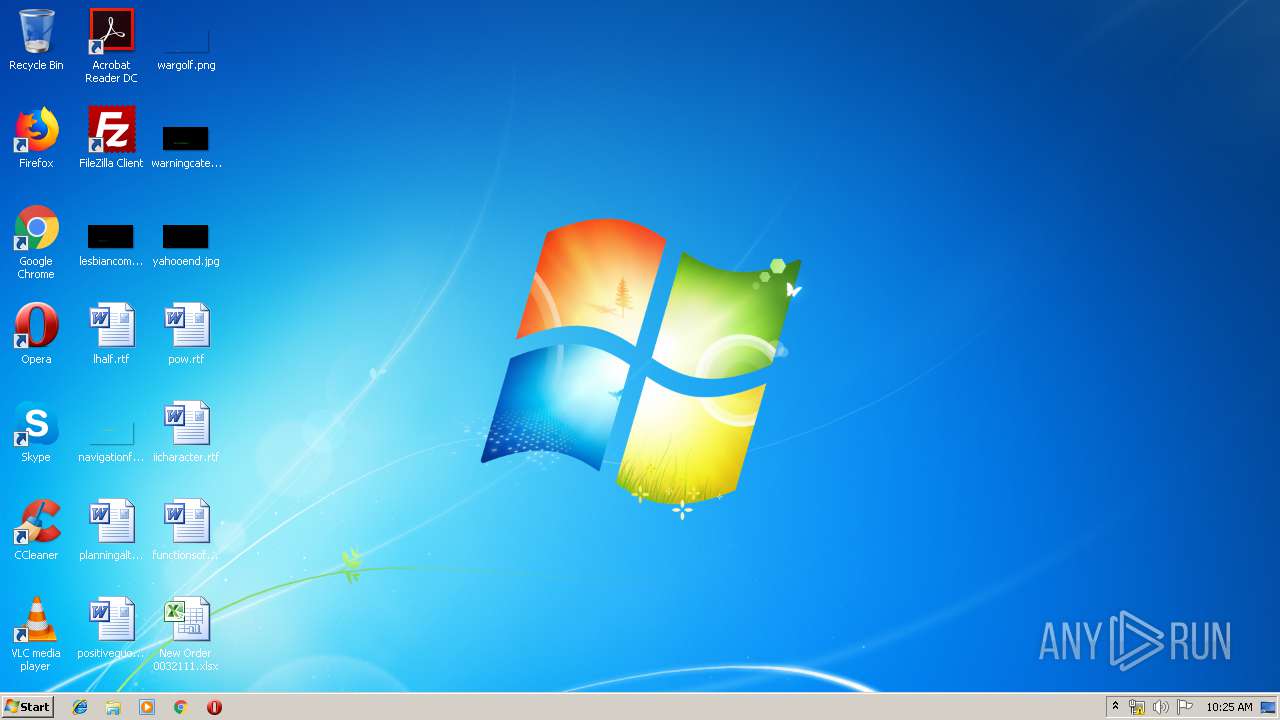
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | D5B68AB5ED5E2FFABEEC23ACBCE758CF |
| SHA1: | FE6F56DECAEC81C42078F97784D72A0B9E4D7927 |
| SHA256: | C556E0475AEB9419B1504E58DC7CE656AE6375BF70BC0A3228DC8949FA07E532 |
| SSDEEP: | 384:azsAgGwlalqJdSe9RQfT9XrPrjhXhPHBNs8MEwfHlKlMb:ssp/lalqJMn9XvjrPHBNylKlMb |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3504)
Application was dropped or rewritten from another process
- 6453gtdysuxhctd.exe (PID: 3300)
- 6453gtdysuxhctd.exe (PID: 1908)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3504)
Detected Hawkeye Keylogger
- 6453gtdysuxhctd.exe (PID: 1908)
Stealing of credential data
- vbc.exe (PID: 2904)
- vbc.exe (PID: 3872)
Actions looks like stealing of personal data
- vbc.exe (PID: 2904)
- vbc.exe (PID: 3872)
Changes settings of System certificates
- 6453gtdysuxhctd.exe (PID: 1908)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3504)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3504)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3504)
Application launched itself
- 6453gtdysuxhctd.exe (PID: 3300)
Executes scripts
- 6453gtdysuxhctd.exe (PID: 1908)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2904)
Adds / modifies Windows certificates
- 6453gtdysuxhctd.exe (PID: 1908)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2956)
Creates files in the user directory
- EXCEL.EXE (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:10 19:11:16 |
| ZipCRC: | 0x29e00db9 |
| ZipCompressedSize: | 411 |
| ZipUncompressedSize: | 1905 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | Shaikh |
|---|
XML
| LastModifiedBy: | USER |
|---|---|
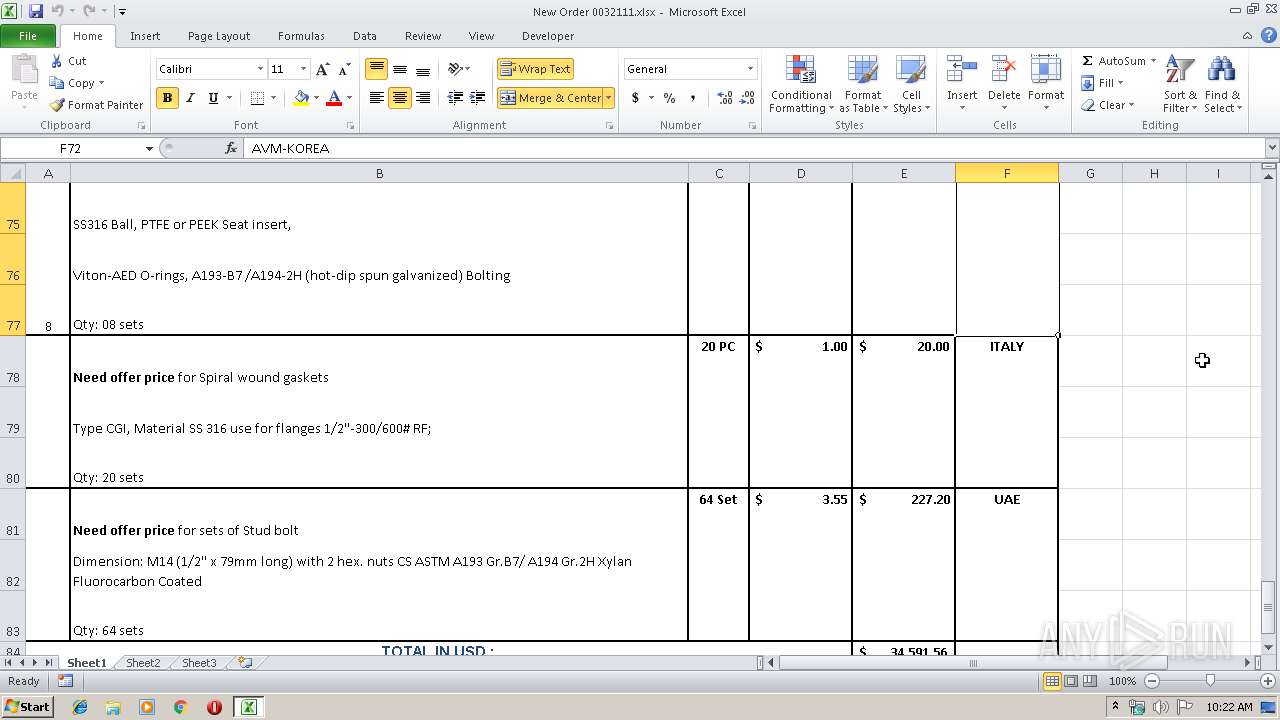
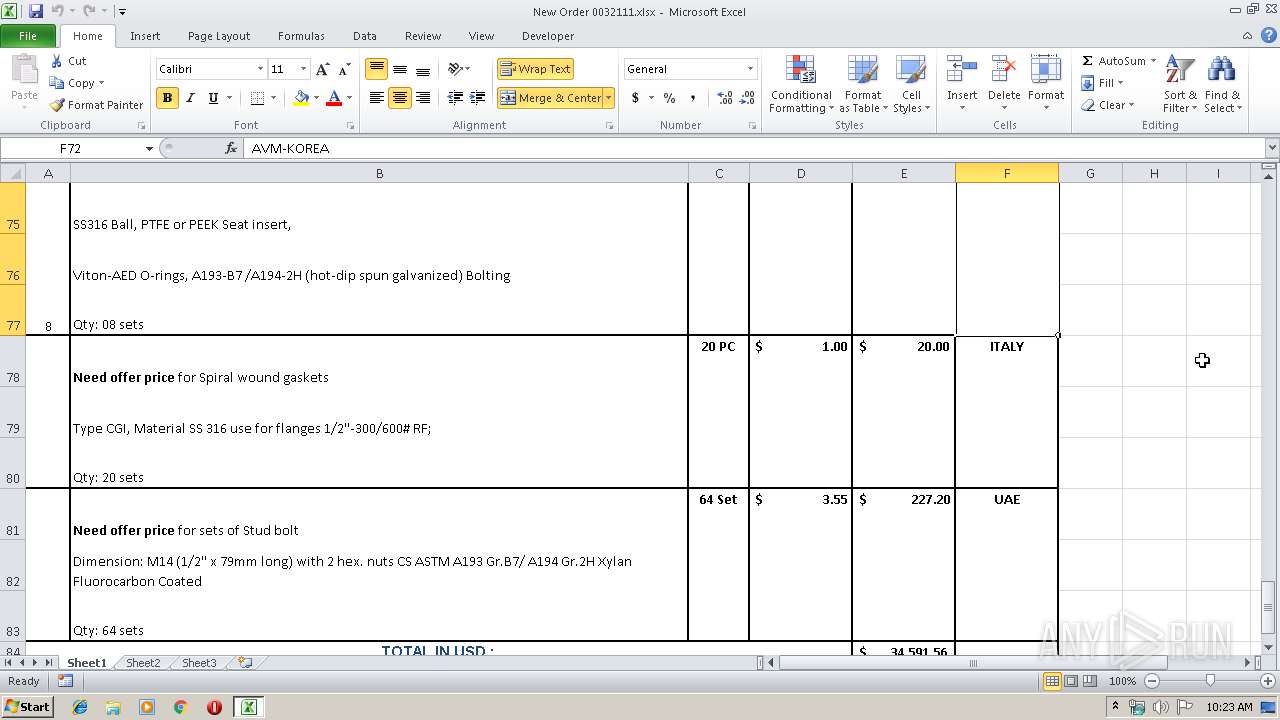
| CreateDate: | 2019:03:07 11:34:48Z |
| ModifyDate: | 2019:03:11 09:57:12Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15.03 |
Total processes
43
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1908 | "C:\Users\admin\AppData\Roaming\6453gtdysuxhctd.exe" | C:\Users\admin\AppData\Roaming\6453gtdysuxhctd.exe | 6453gtdysuxhctd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2904 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp7FCE.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | 6453gtdysuxhctd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3300 | "C:\Users\admin\AppData\Roaming\6453gtdysuxhctd.exe" | C:\Users\admin\AppData\Roaming\6453gtdysuxhctd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3504 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3872 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpAC9C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | 6453gtdysuxhctd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
Total events
605
Read events
531
Write events
59
Delete events
15
Modification events
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | dy |
Value: 647920008C0B0000010000000000000000000000 | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 8C0B0000169B985E0021D50100000000 | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | dy |
Value: 647920008C0B0000010000000000000000000000 | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3504) EQNEDT32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109E60090400000000000F01FEC\Usage |
| Operation: | write | Name: | EquationEditorFilesIntl_1033 |
Value: 1321992195 | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
5
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE964.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2956 | EXCEL.EXE | C:\Users\admin\Desktop\~$New Order 0032111.xlsx | — | |
MD5:— | SHA256:— | |||
| 2956 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3504 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\777[1].exe | executable | |
MD5:— | SHA256:— | |||
| 1908 | 6453gtdysuxhctd.exe | C:\Users\admin\AppData\Local\Temp\25291068-43af-3e16-50f6-5889d9ce7904 | text | |
MD5:— | SHA256:— | |||
| 3504 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\6453gtdysuxhctd.exe | executable | |
MD5:— | SHA256:— | |||
| 2956 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\New Order 0032111.xlsx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2904 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp7FCE.tmp | text | |
MD5:3E1E093DCCE32C716267A28292E0EE27 | SHA256:56285445424AD06DC043154819B5BDABAA7C26F5779CA3E37E08424ED9926CB8 | |||
| 3872 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpAC9C.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3504 | EQNEDT32.EXE | GET | 200 | 208.43.64.151:80 | http://masertalaamar.com/777.exe | US | executable | 1006 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | EQNEDT32.EXE | 208.43.64.151:80 | masertalaamar.com | SoftLayer Technologies Inc. | US | suspicious |
1908 | 6453gtdysuxhctd.exe | 77.88.21.38:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
masertalaamar.com |
| malicious |
smtp.yandex.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3504 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Possible Malicious Macro DL EXE Feb 2016 |
3504 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1908 | 6453gtdysuxhctd.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |