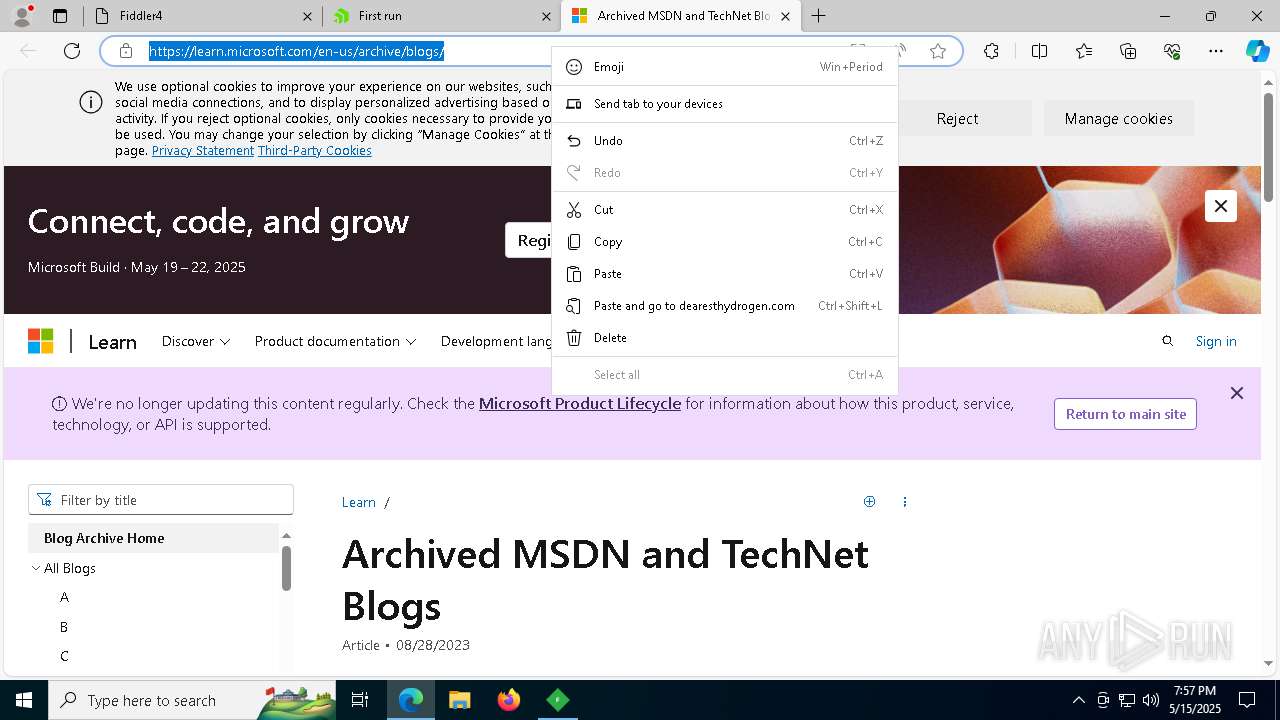
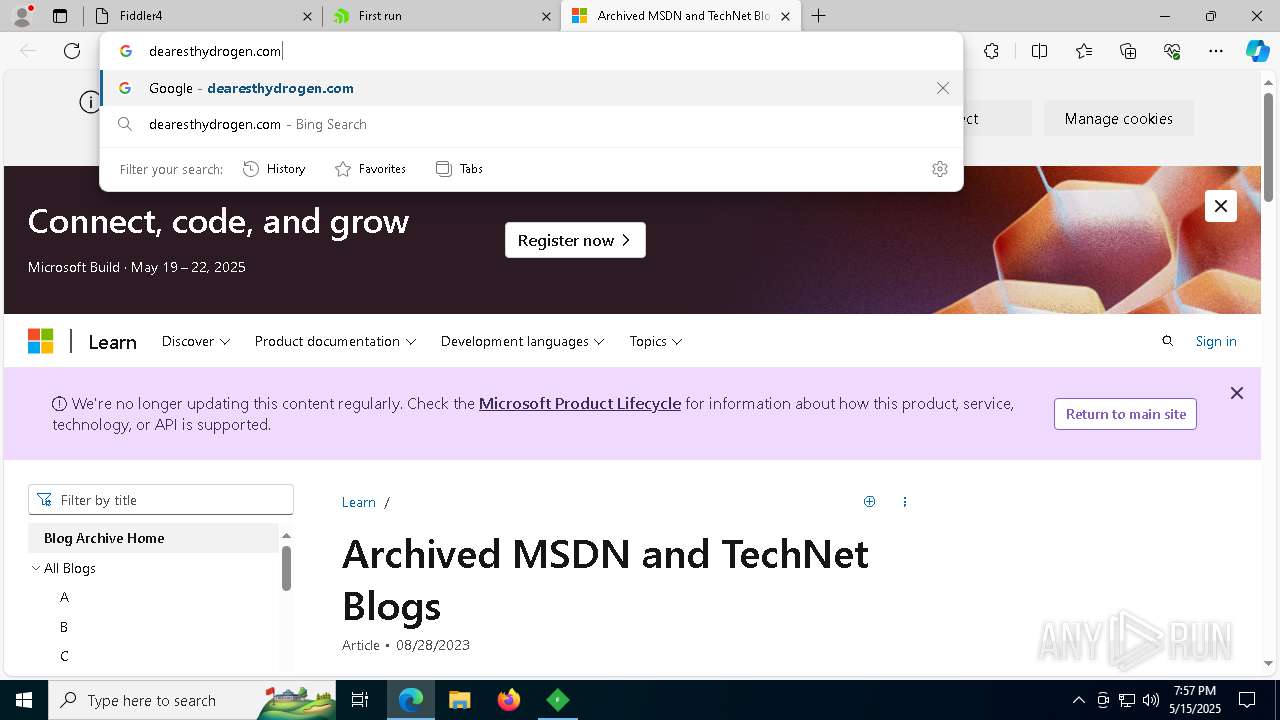
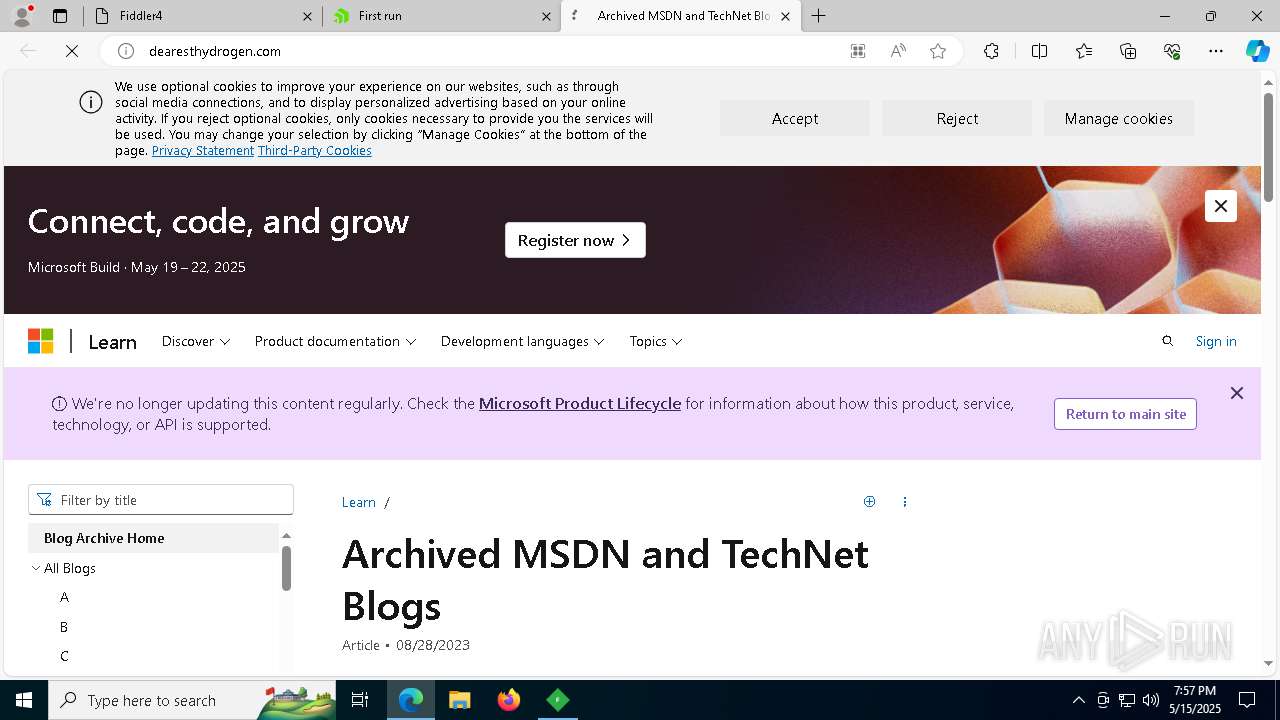
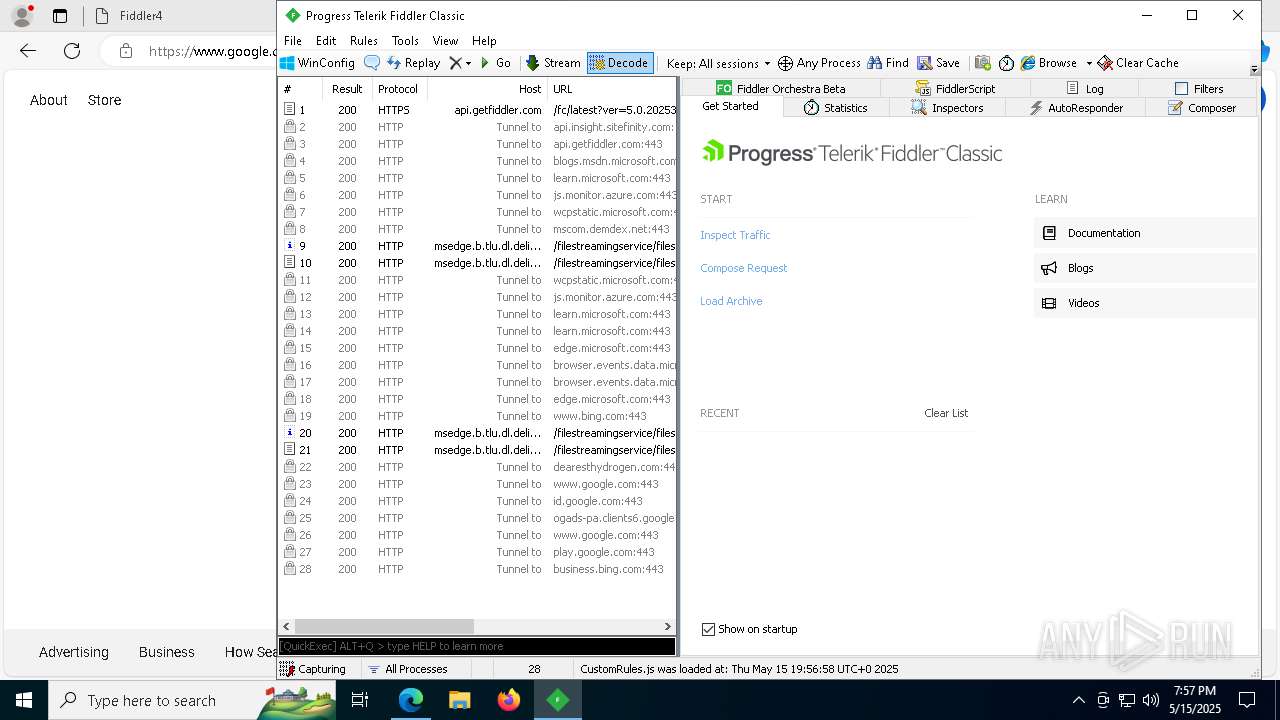
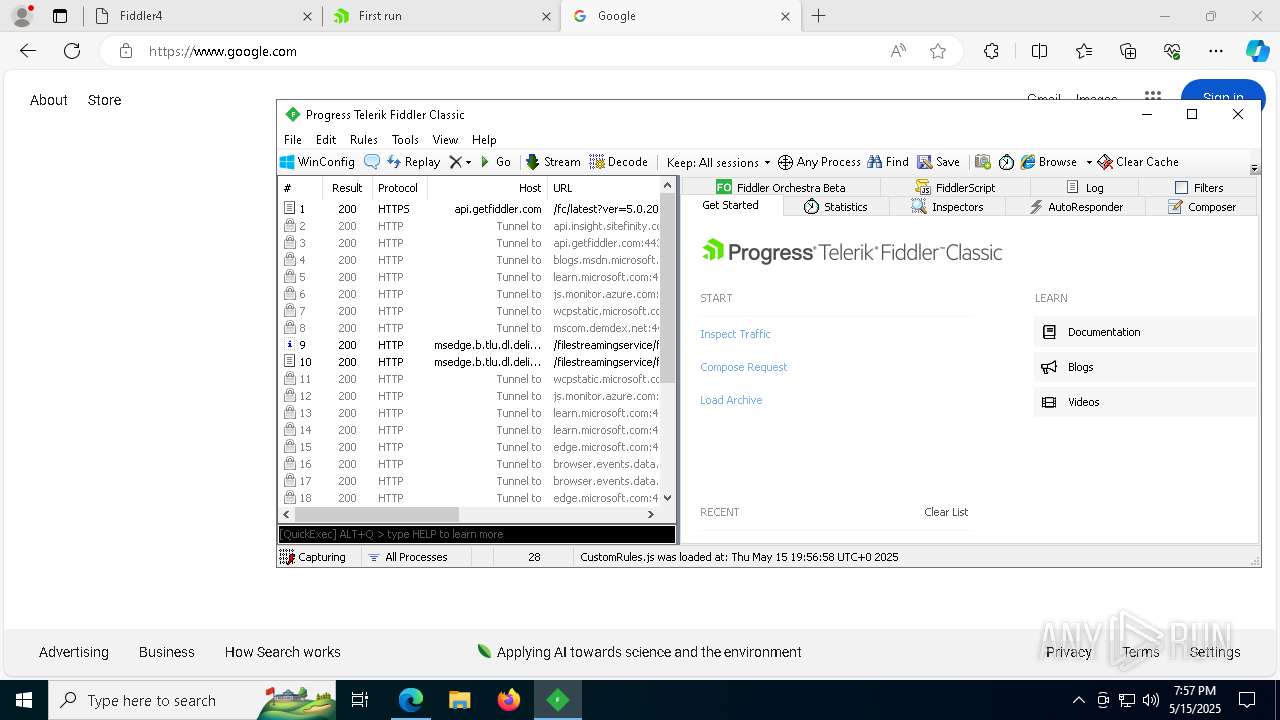
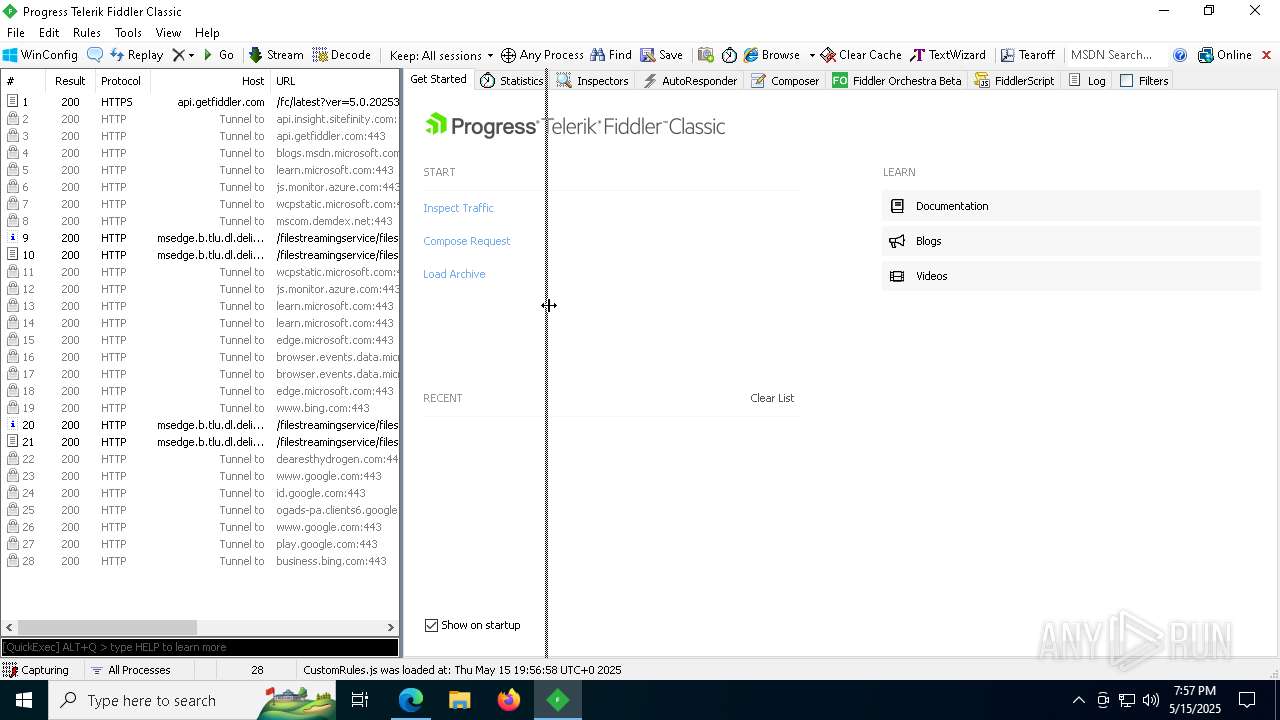
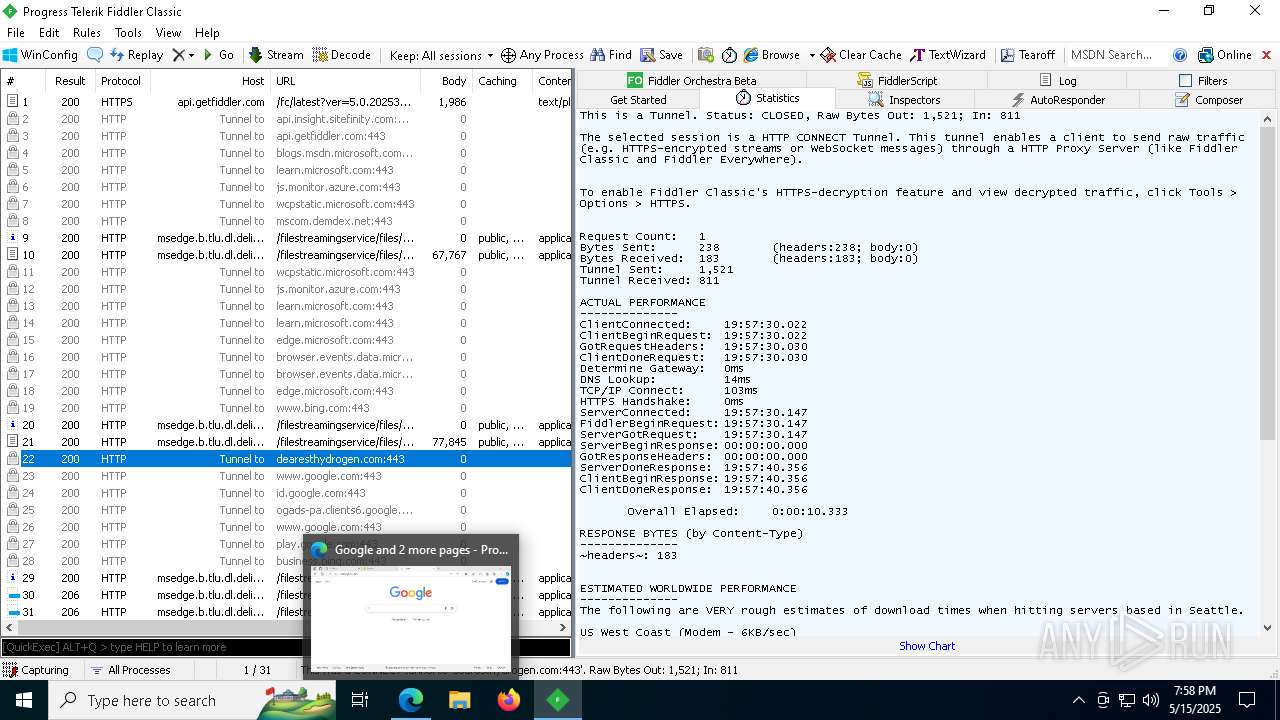
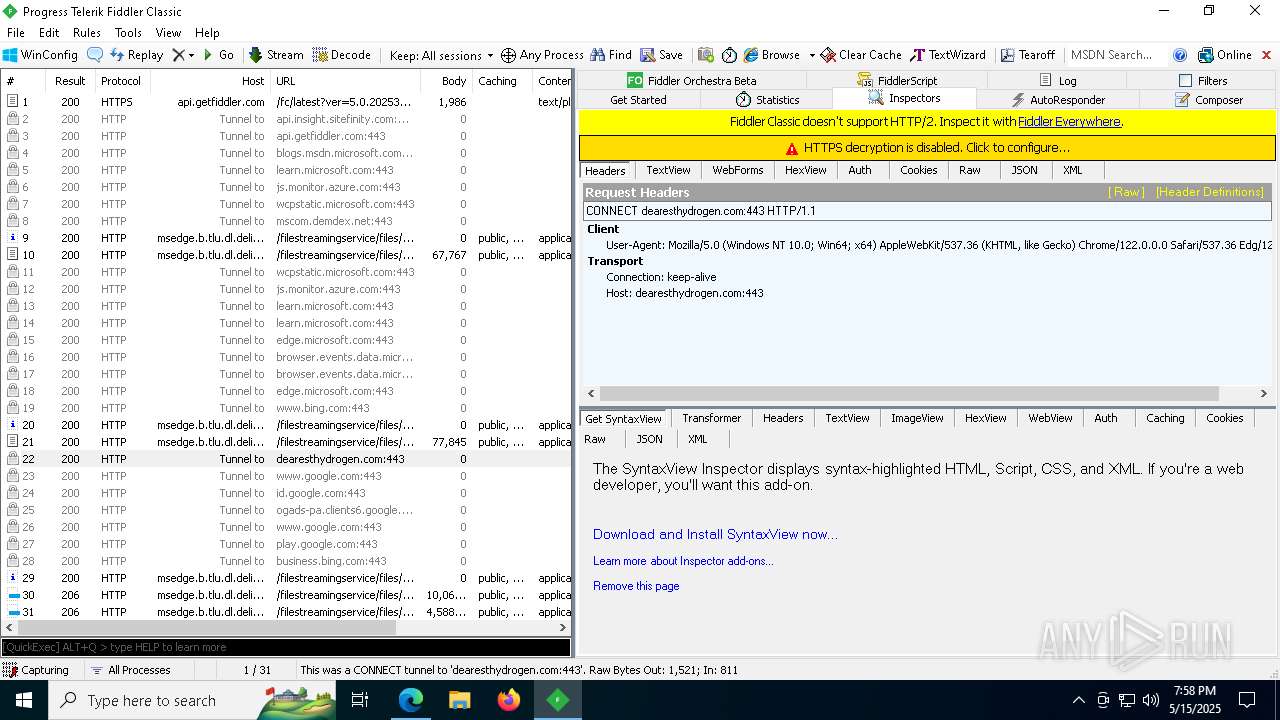
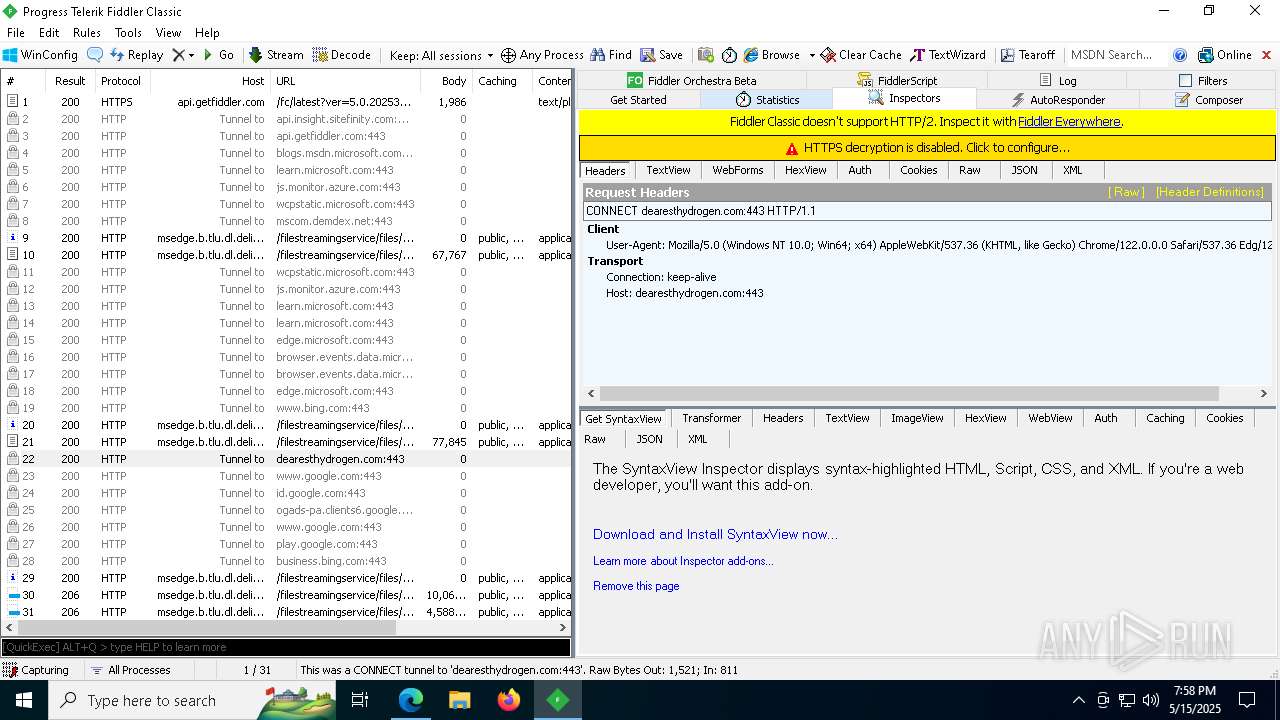
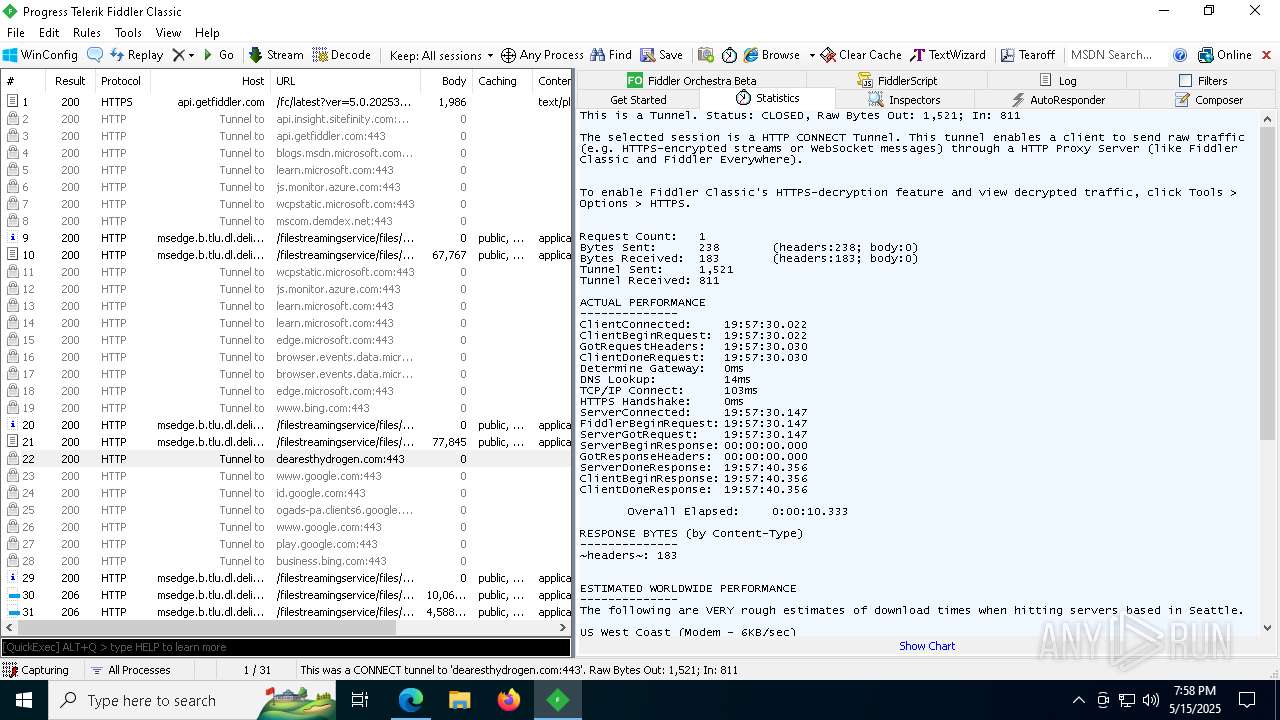
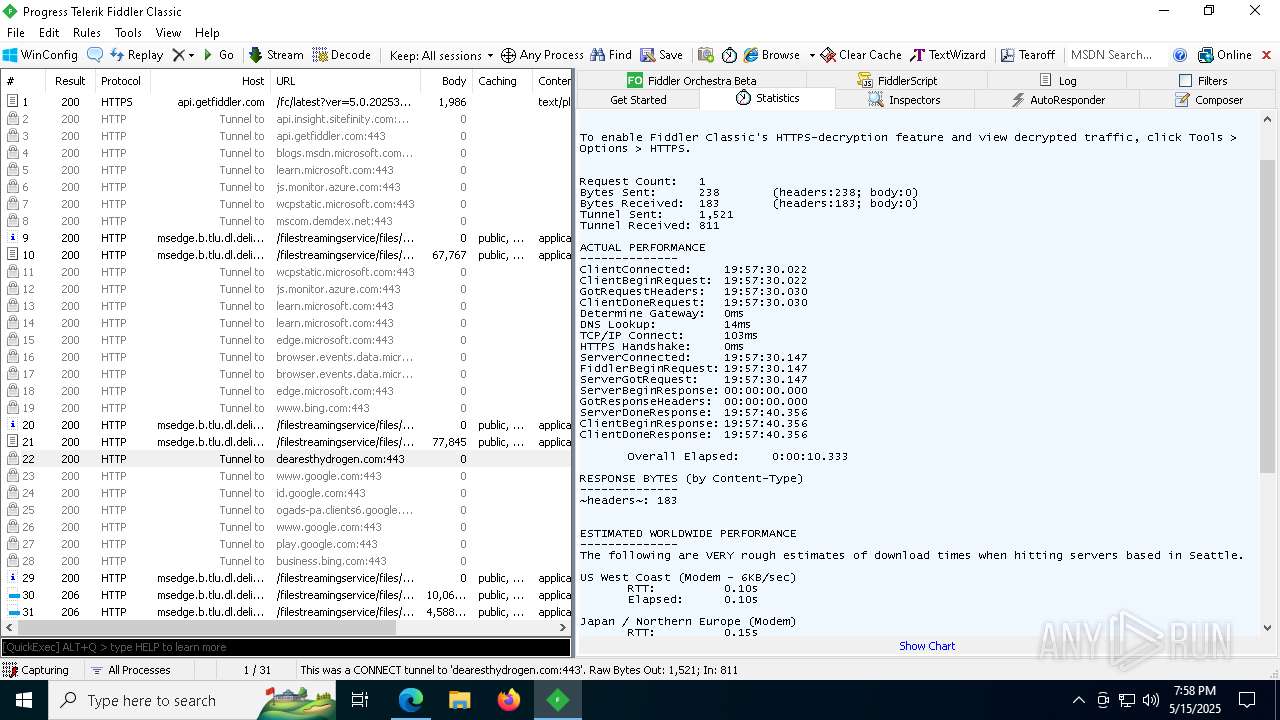
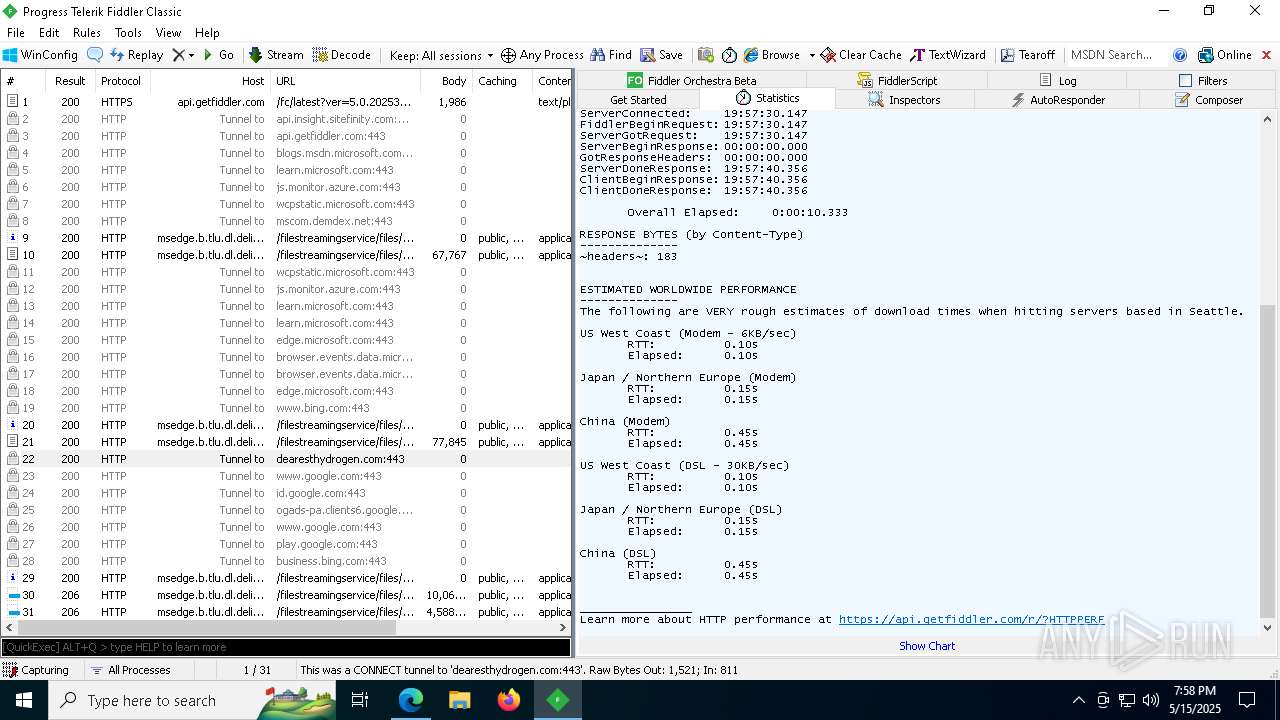
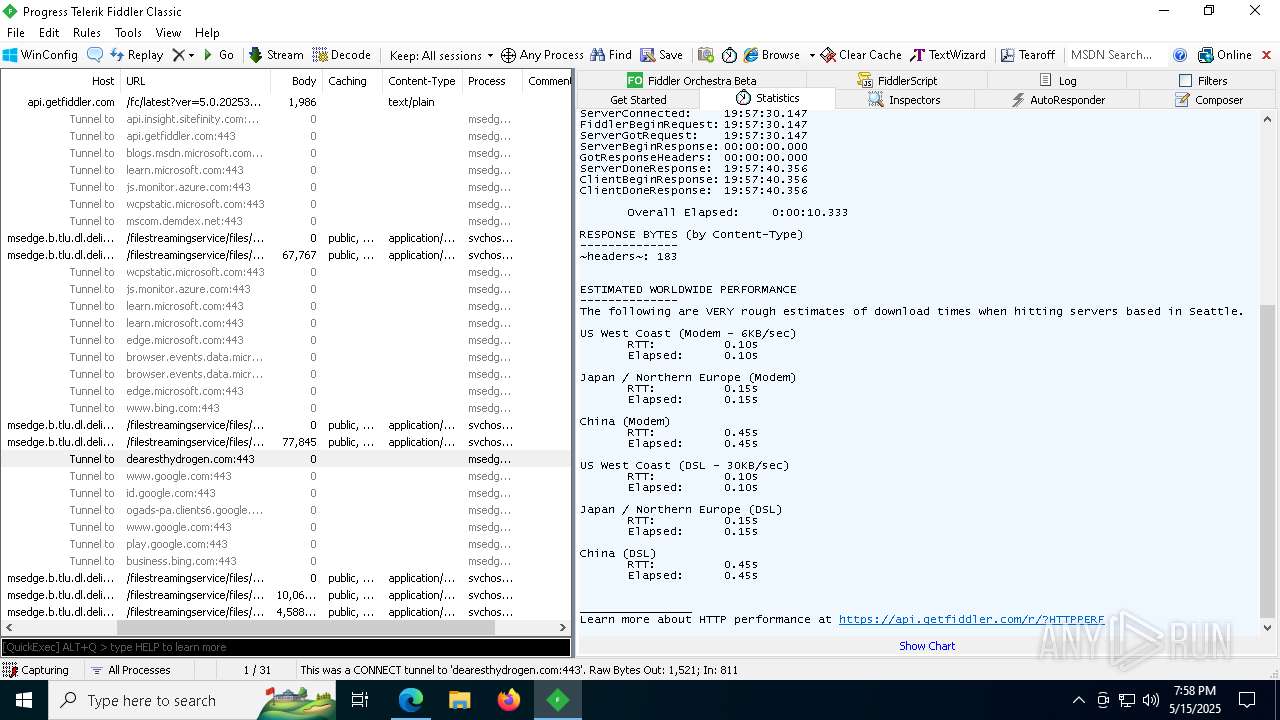
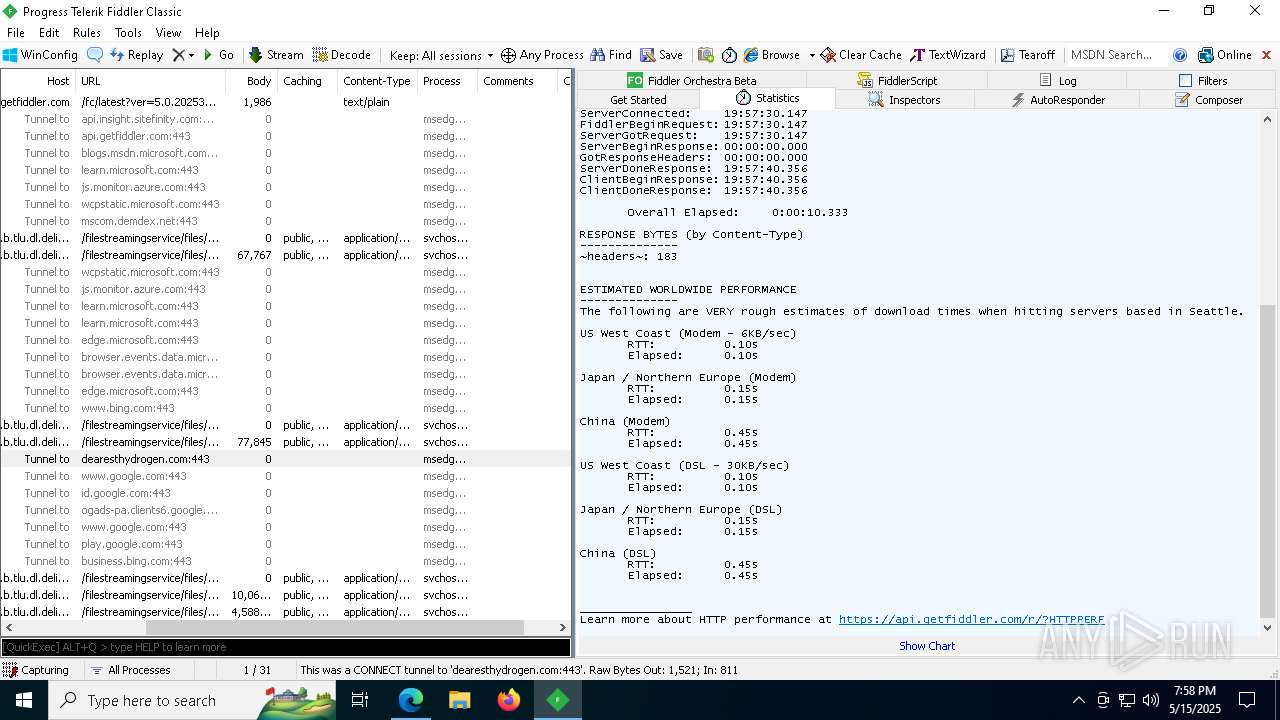
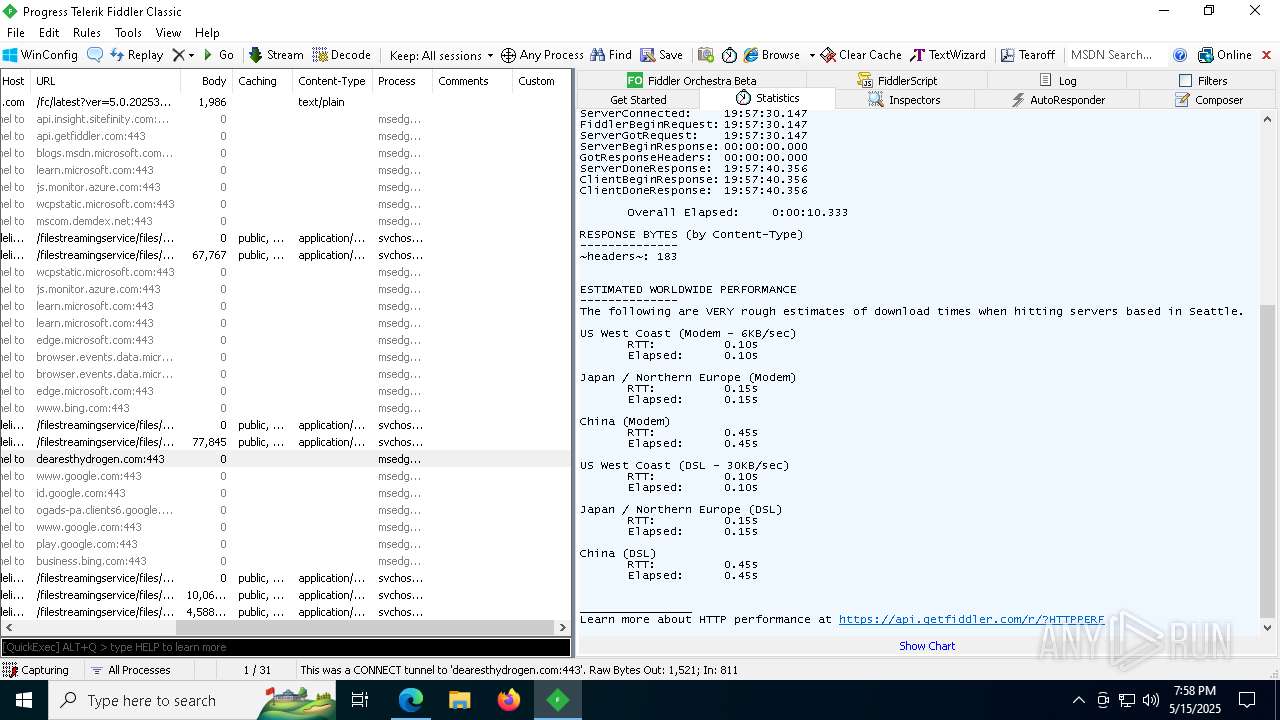
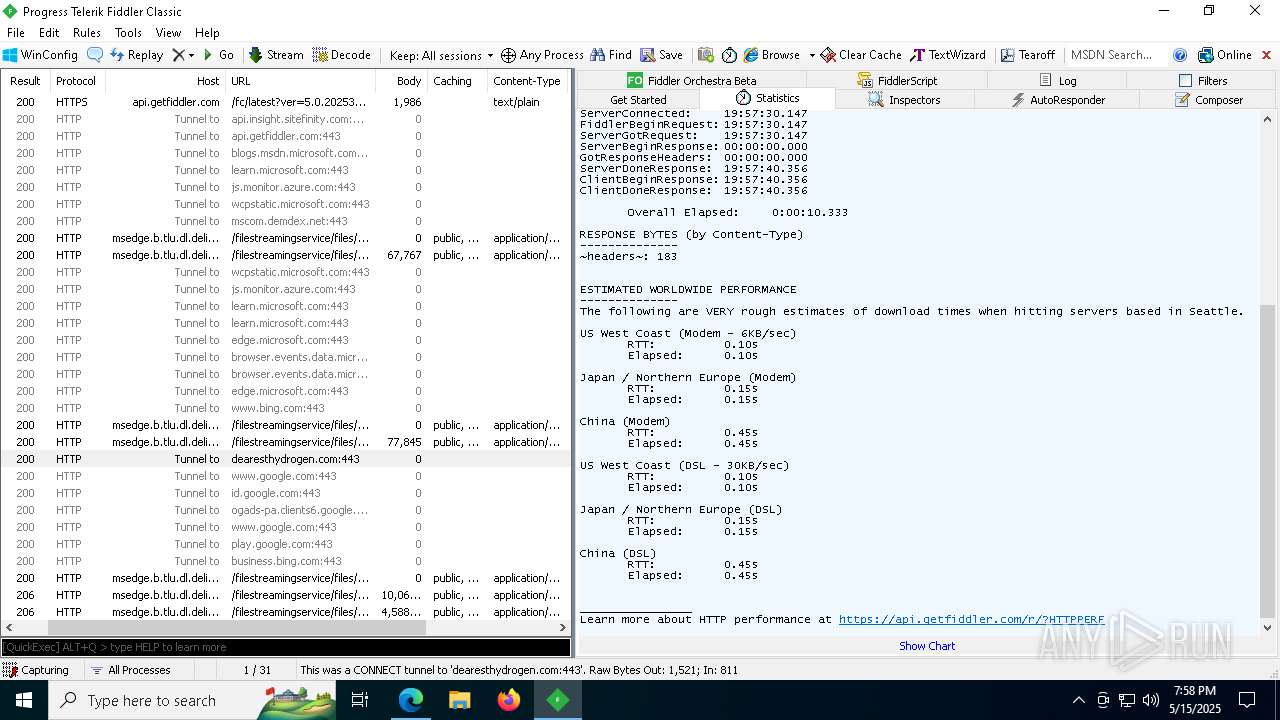
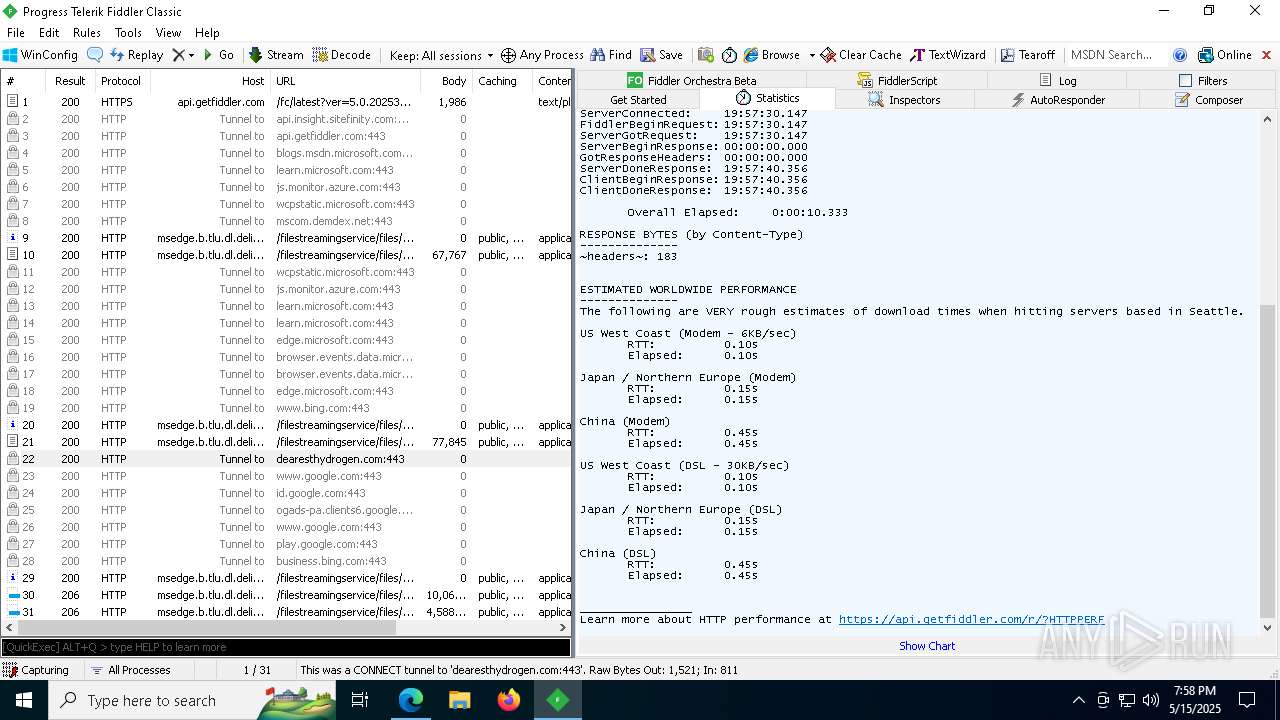
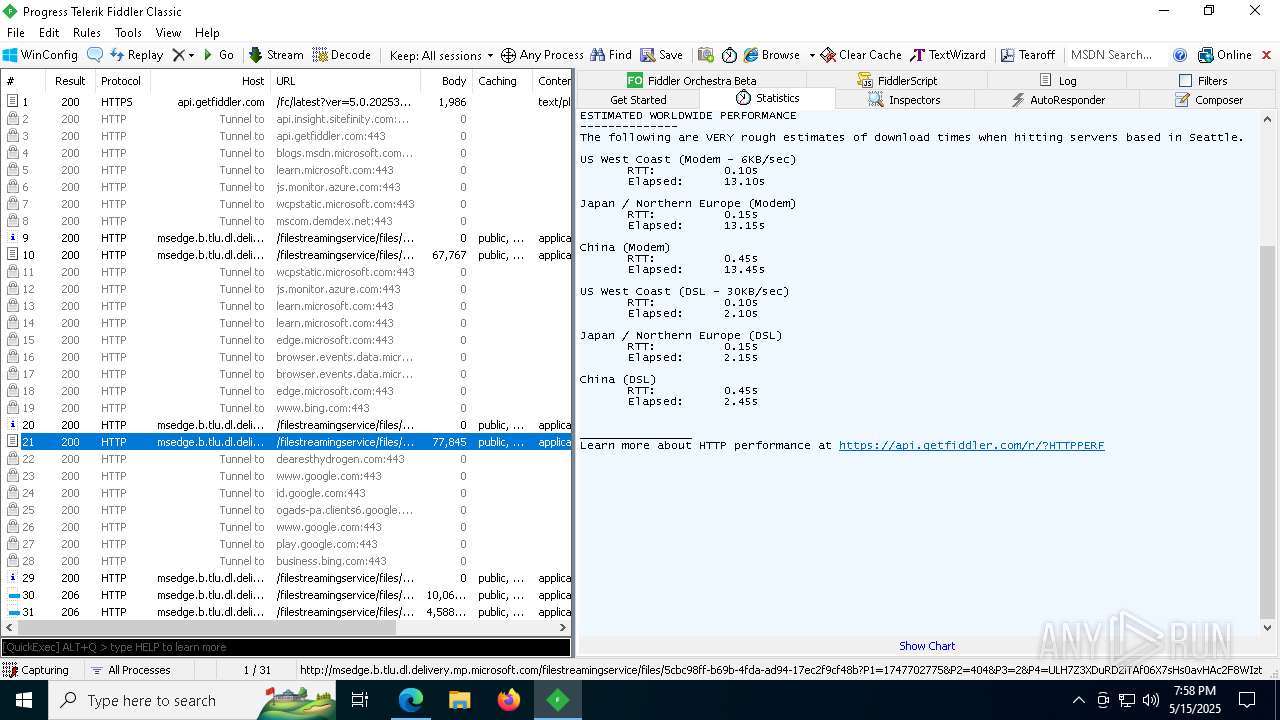
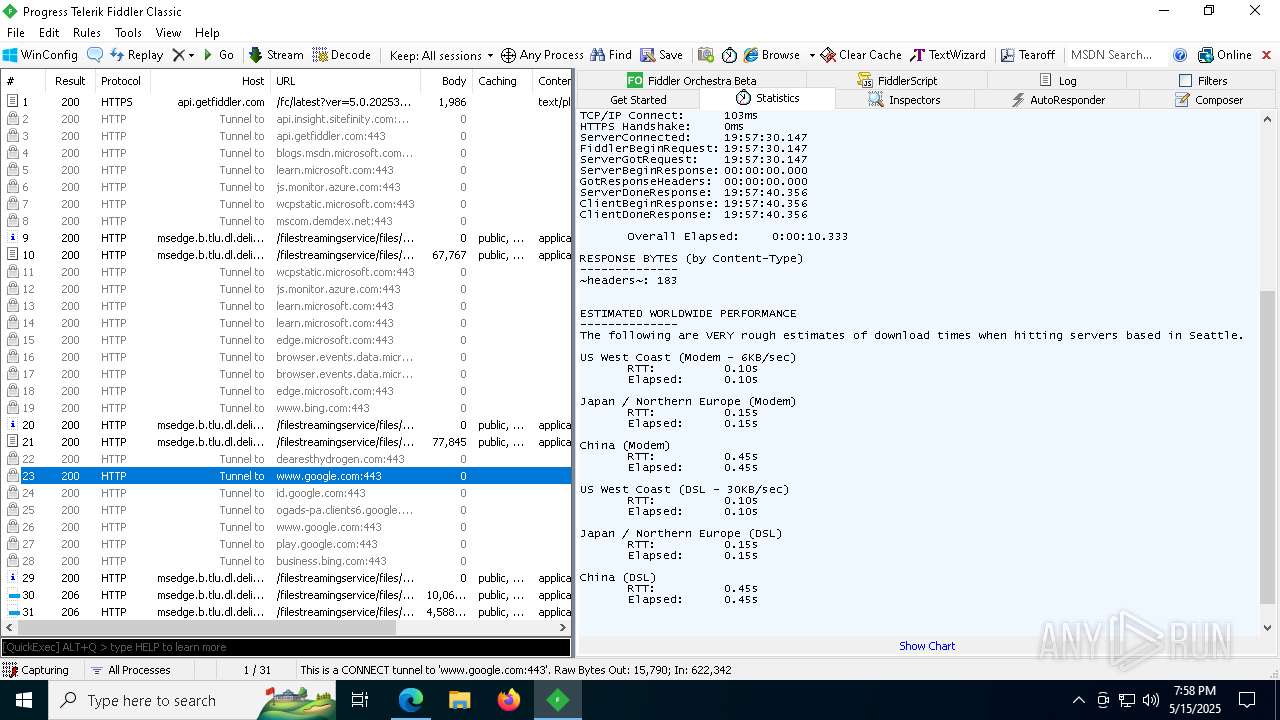
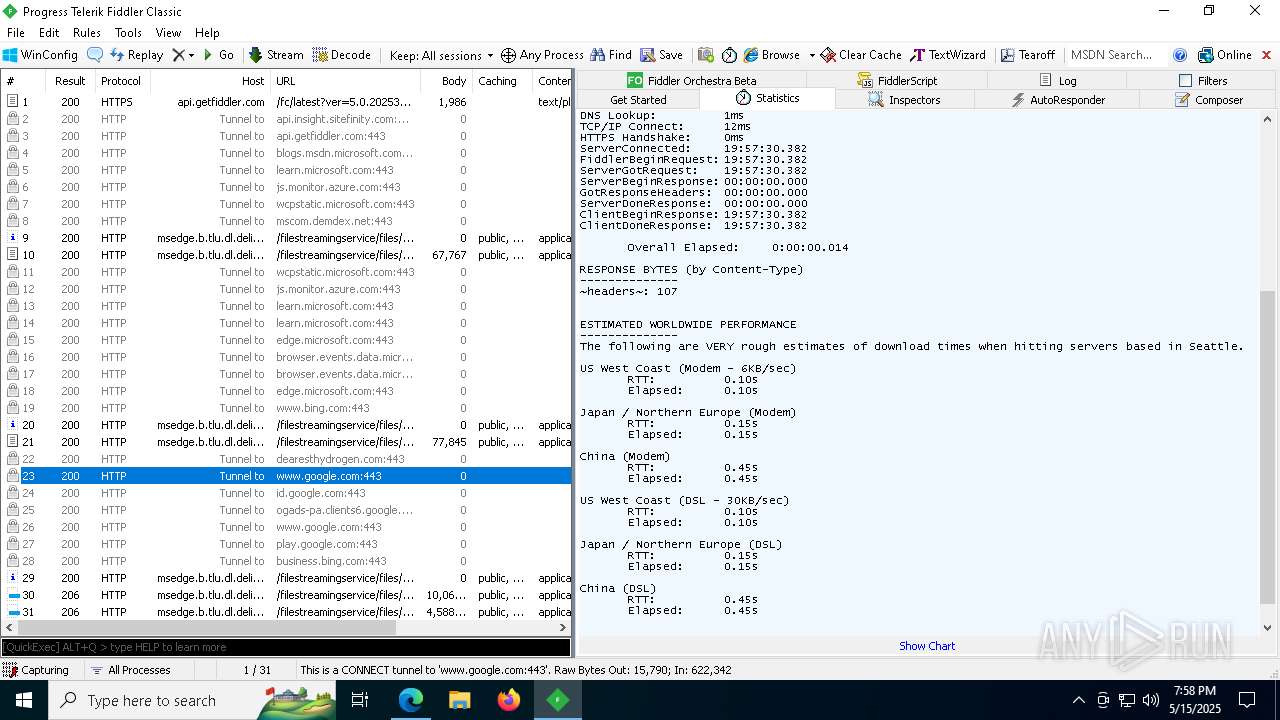
| URL: | dearesthydrogen.com |
| Full analysis: | https://app.any.run/tasks/34203119-9b7d-4205-a1c1-2a9164be1575 |
| Verdict: | Malicious activity |
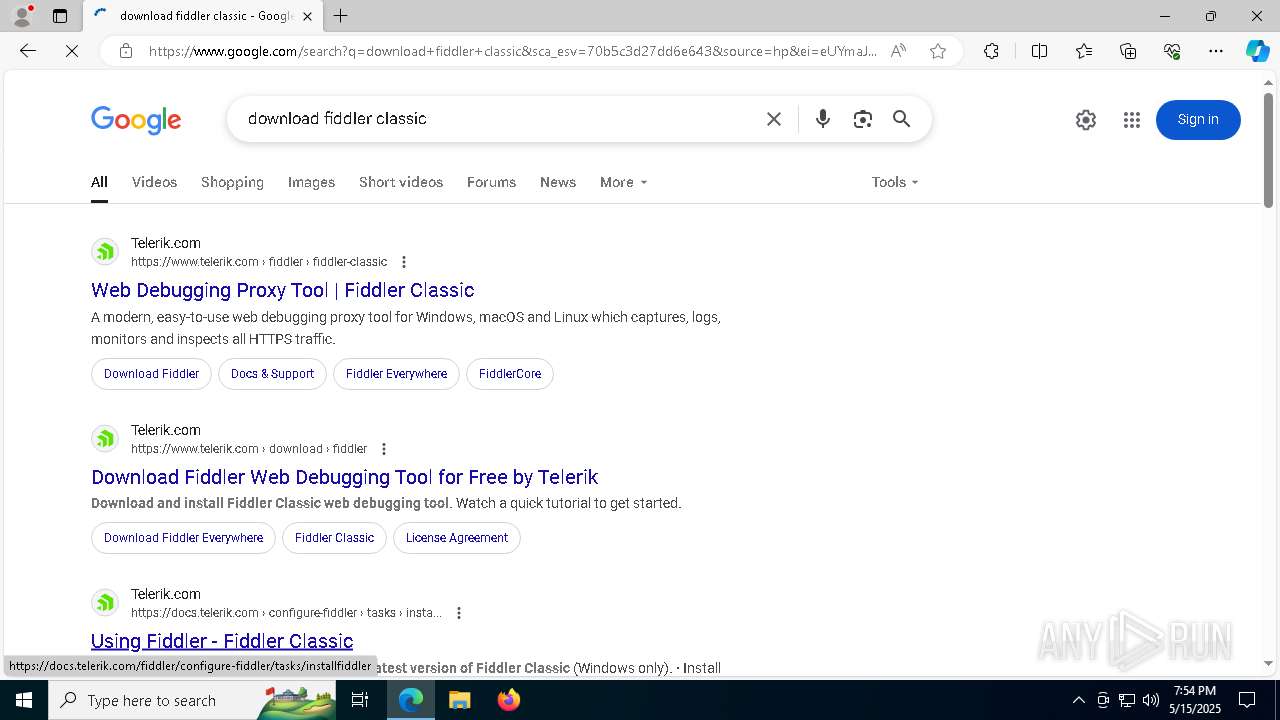
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | May 15, 2025, 19:54:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 89022031417A631821DA08ADF430C67E |
| SHA1: | BE94CA96F6BB197AE2C692679A65EBB5F799EC8B |
| SHA256: | C53E3715F750D161006FE49316F2F80C3585FA1BA1B372D036CB3EFFD32D83B7 |
| SSDEEP: | 3:PrsAL2n:PlSn |
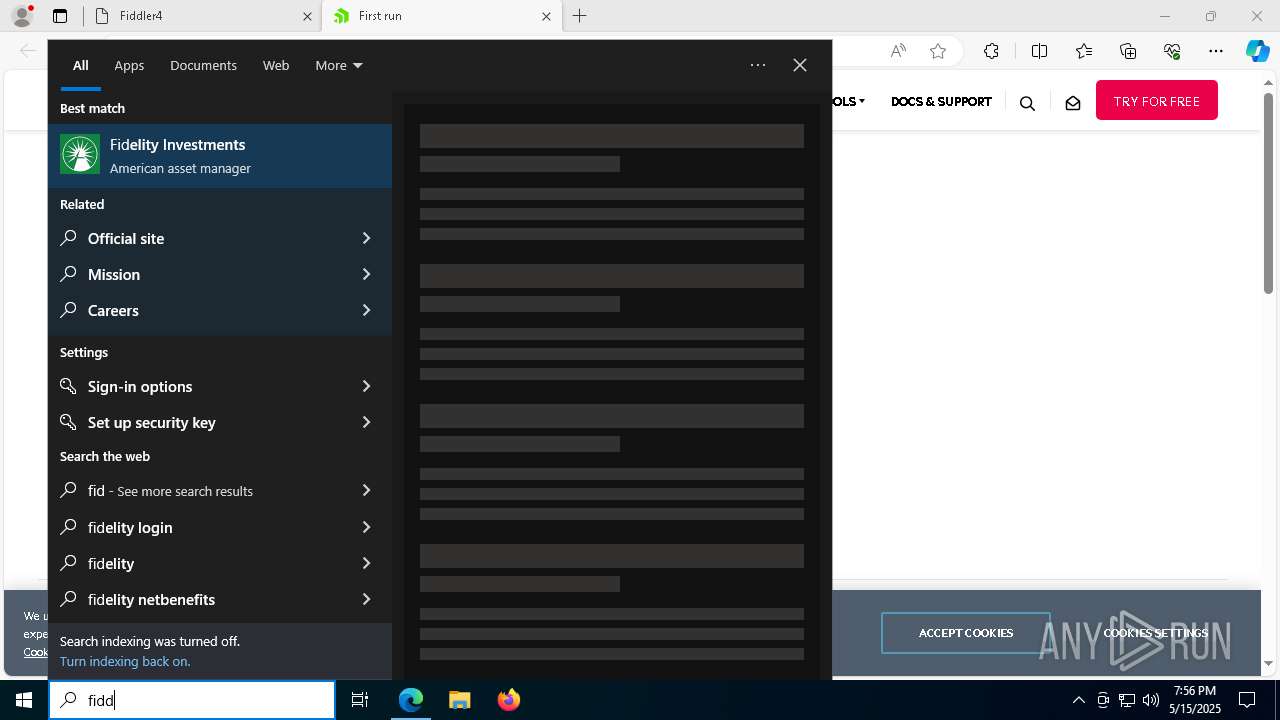
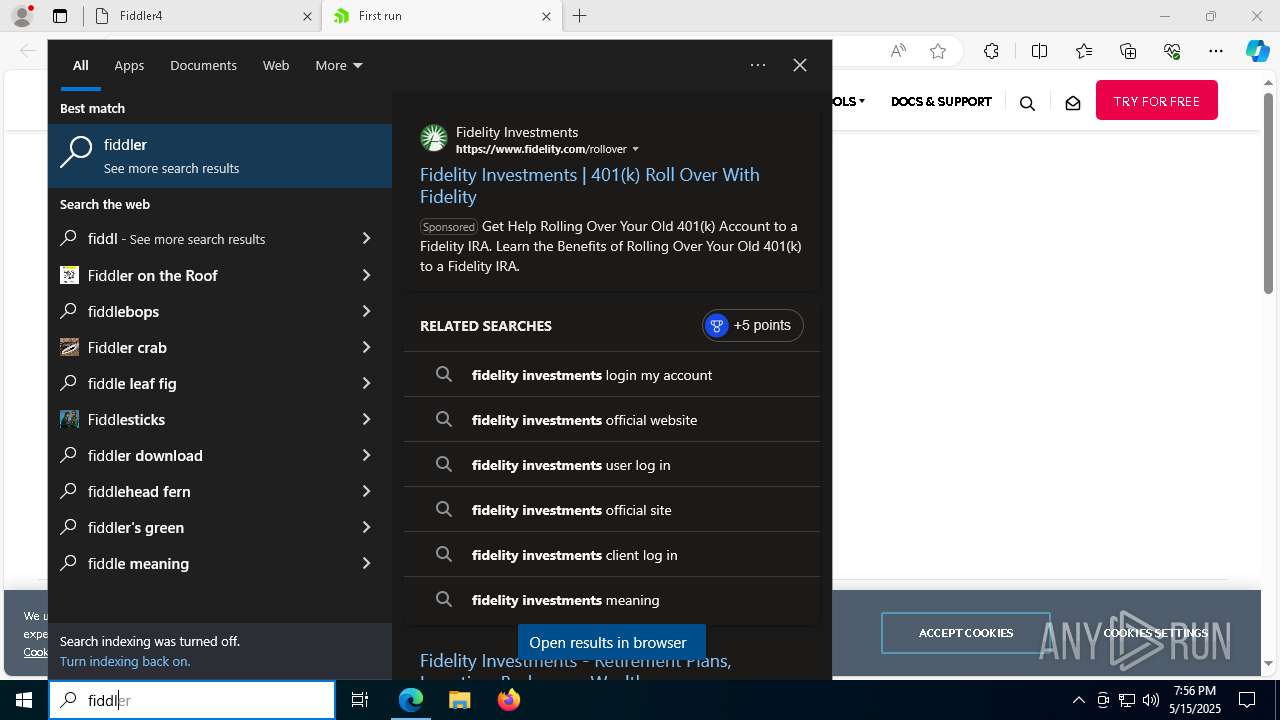
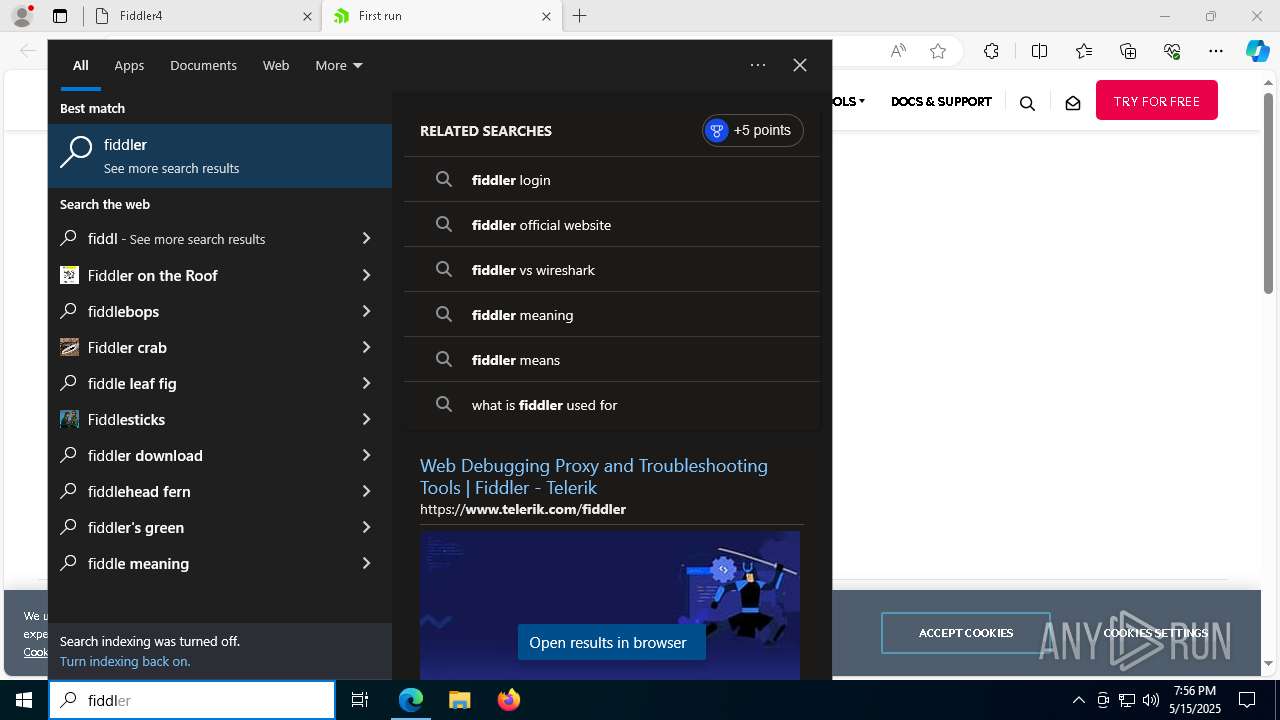
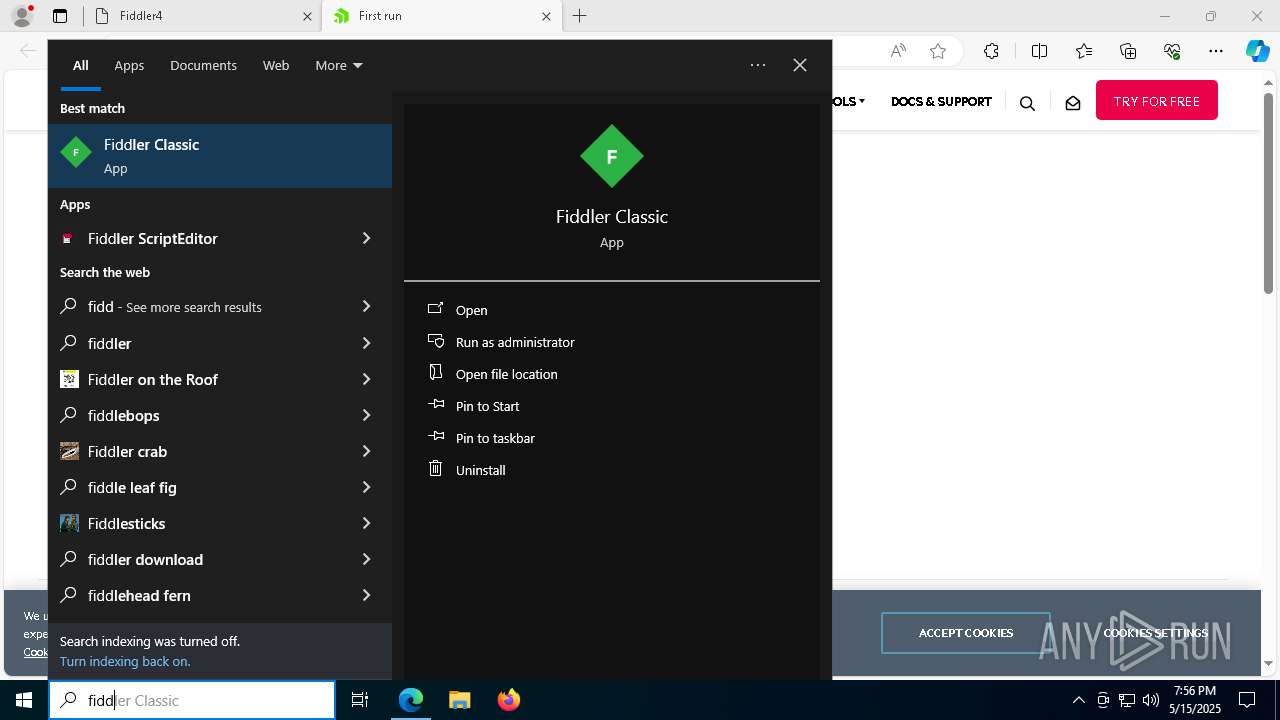
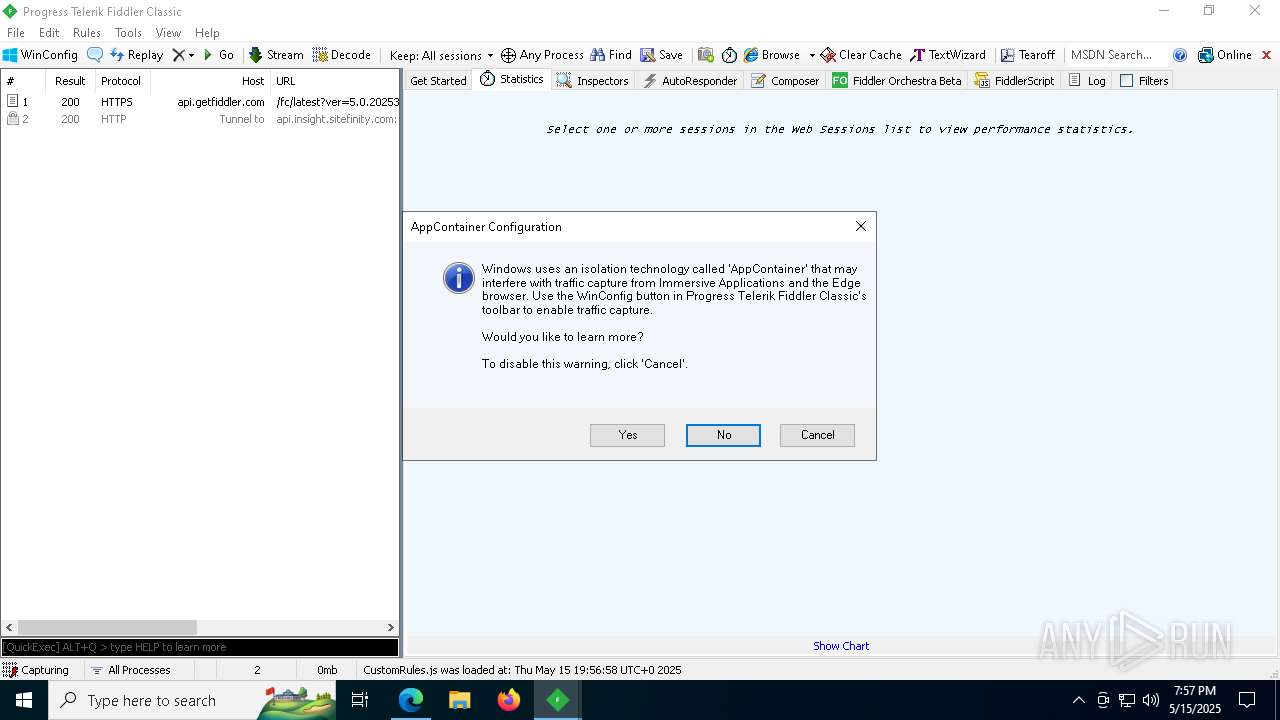
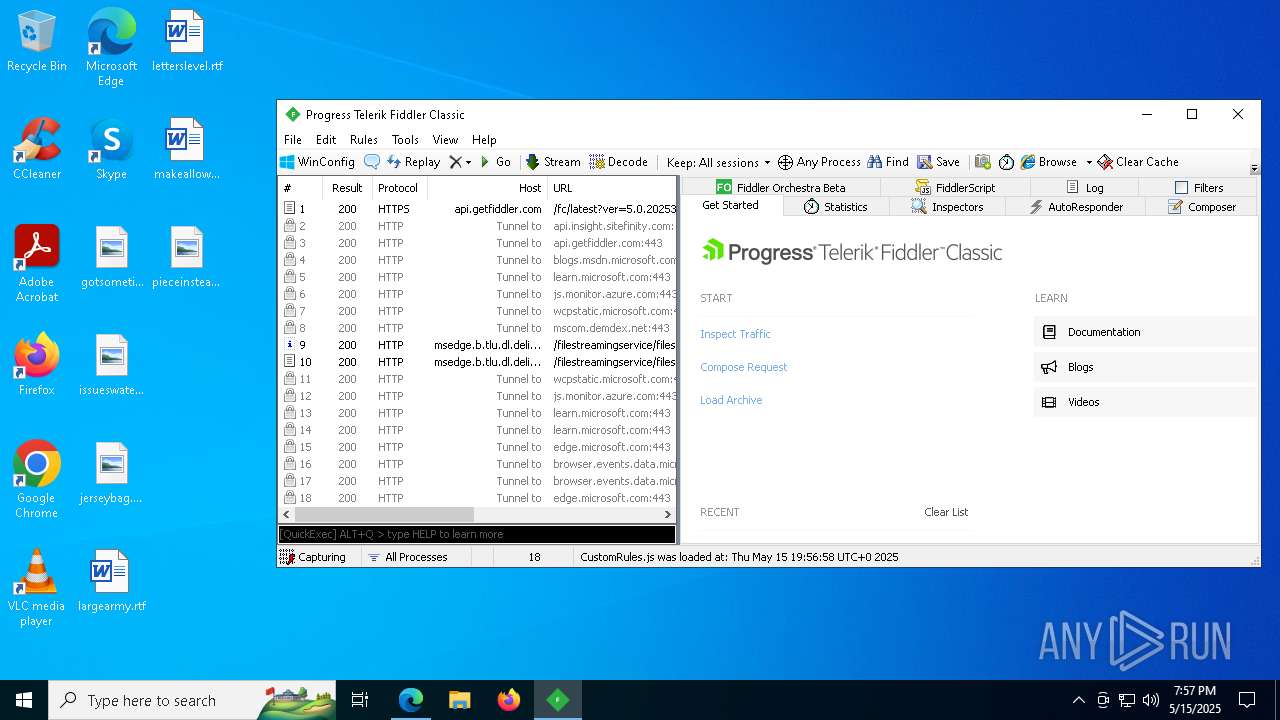
MALICIOUS
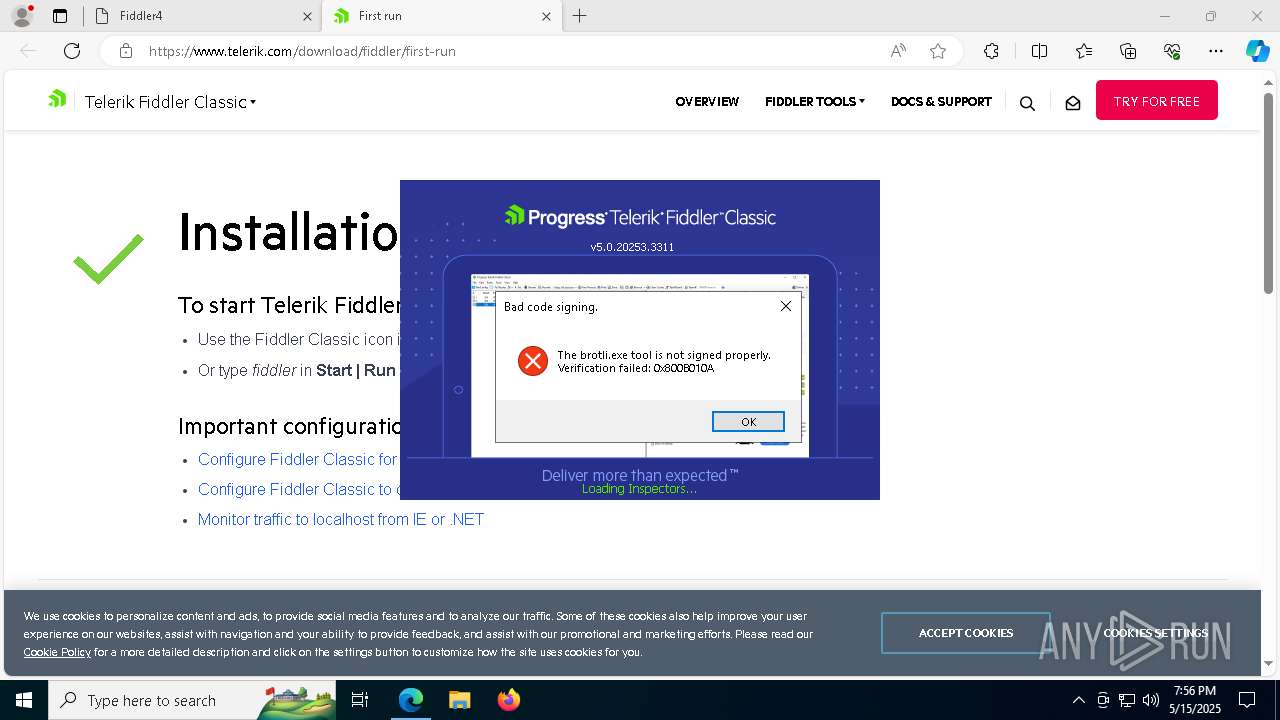
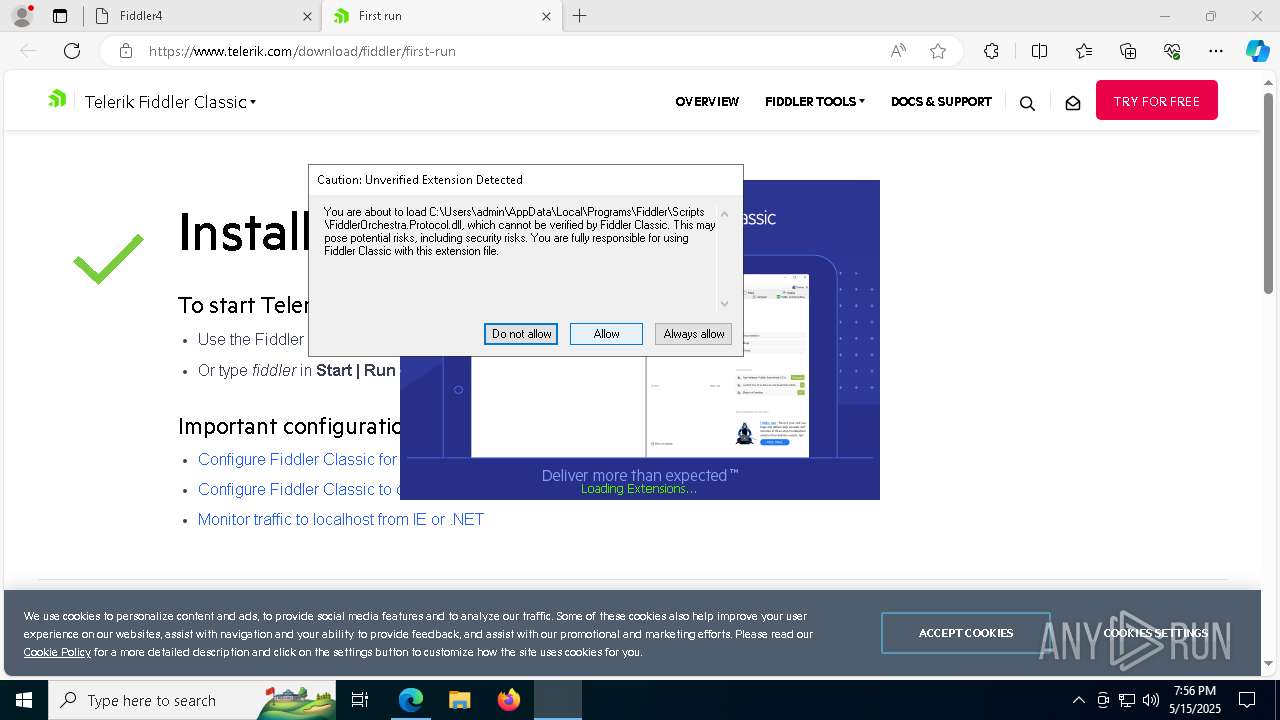
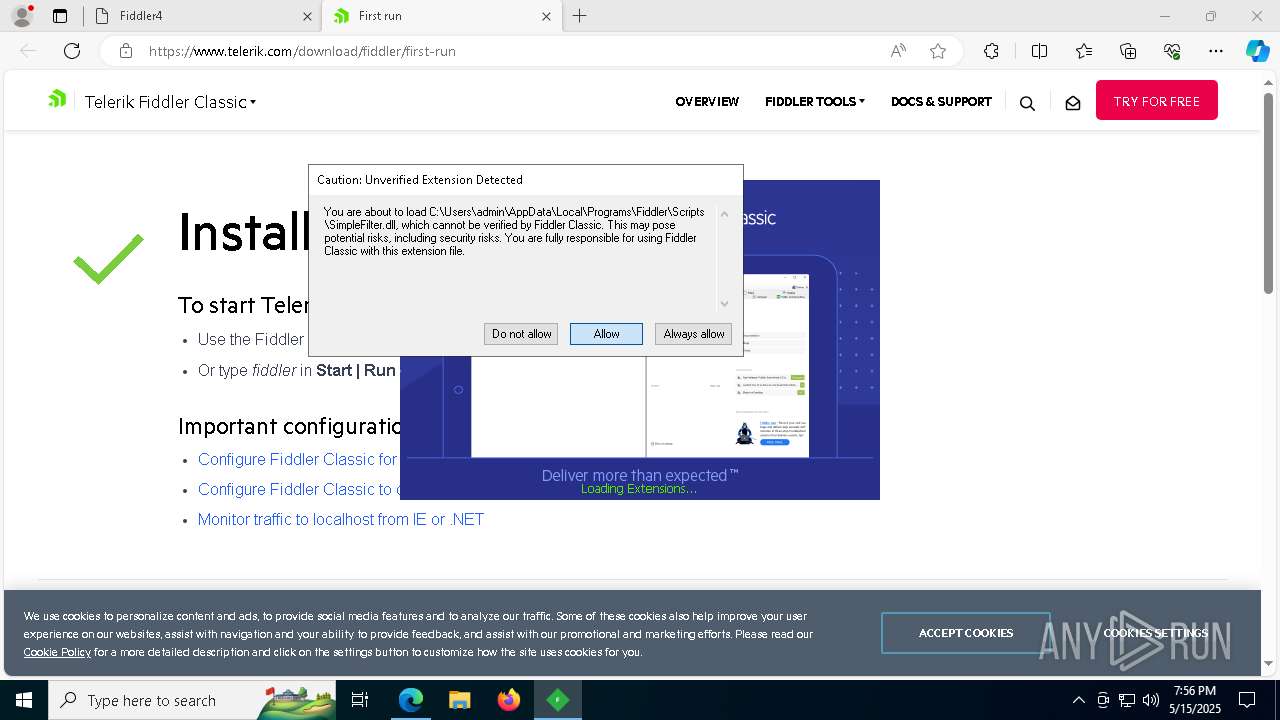
METASTEALER has been detected (YARA)
- Fiddler.exe (PID: 6572)
SUSPICIOUS
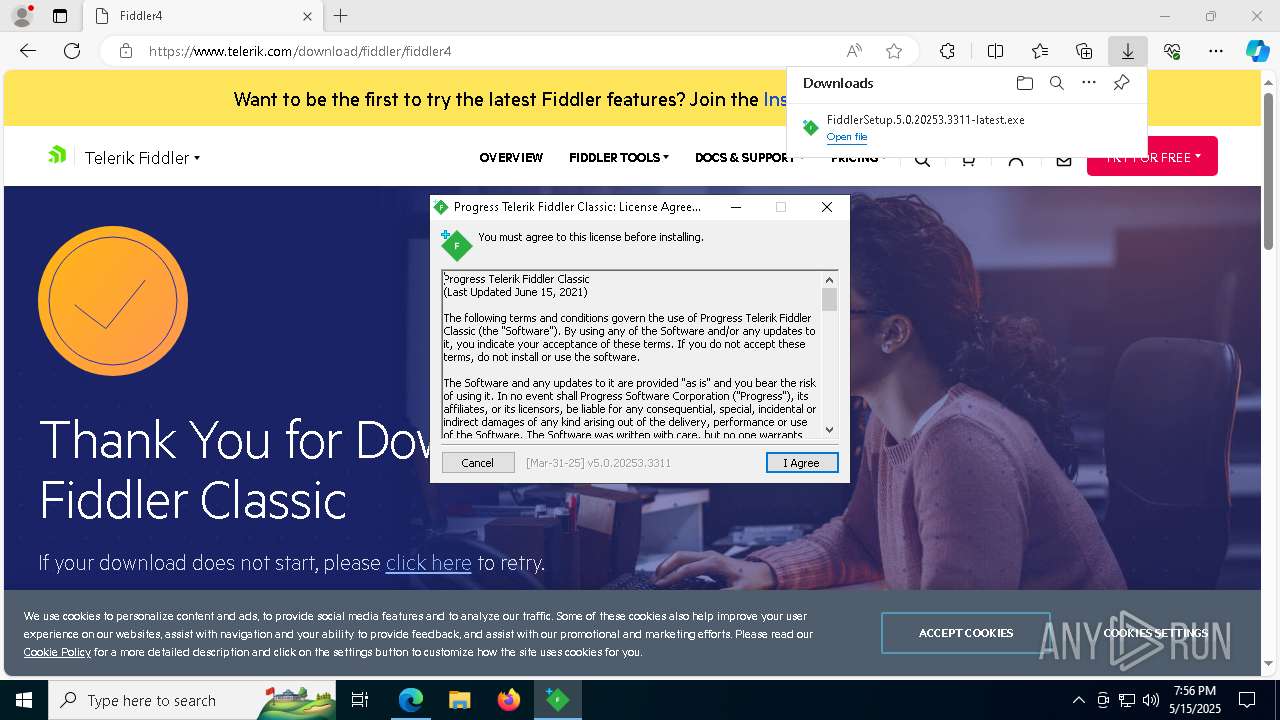
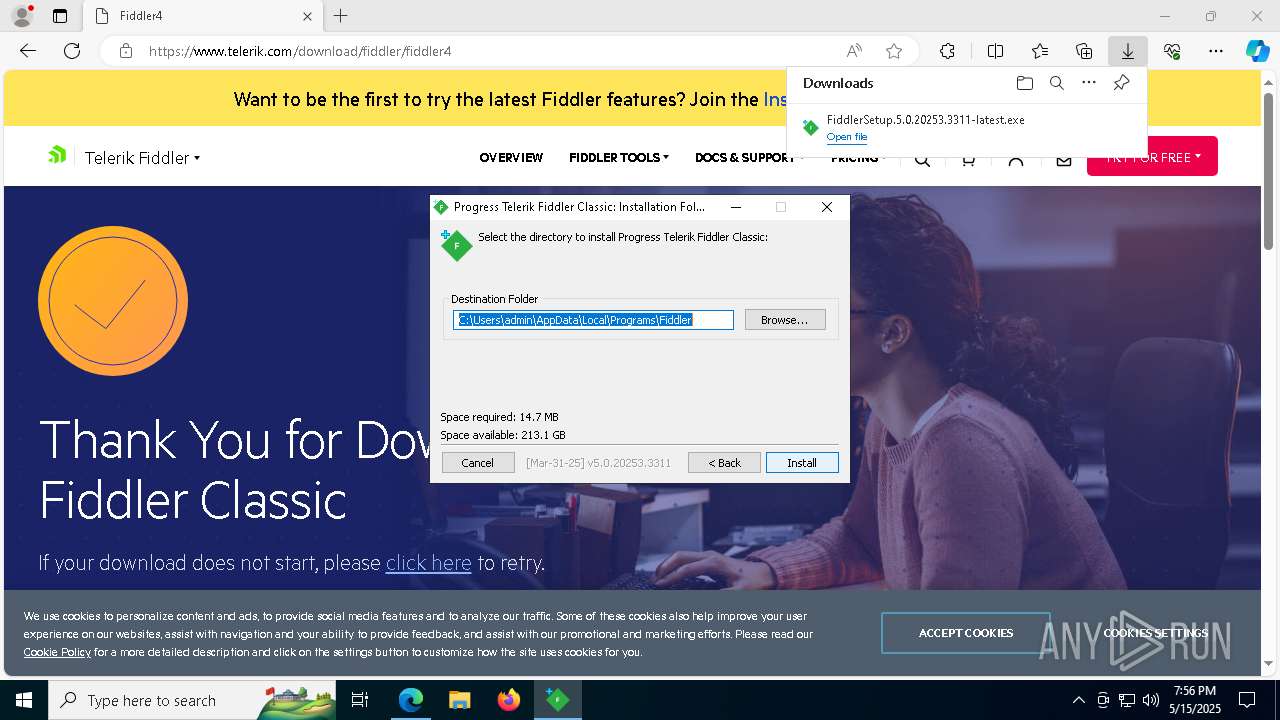
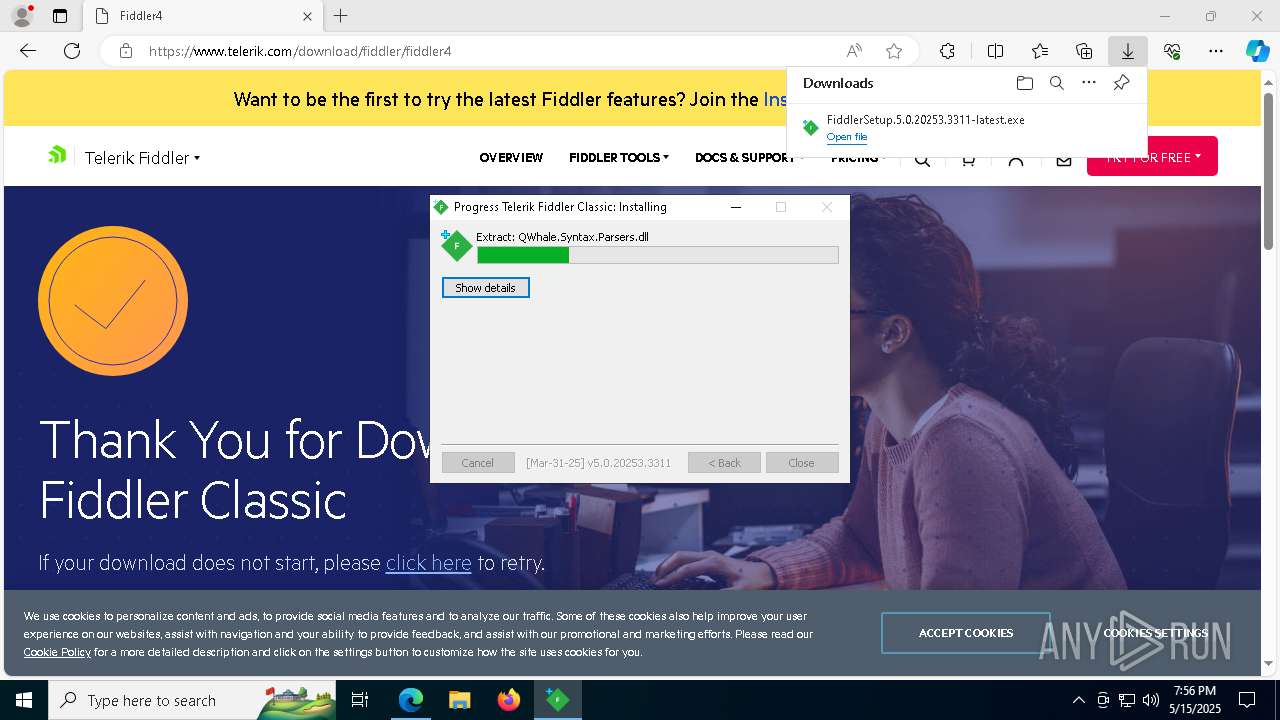
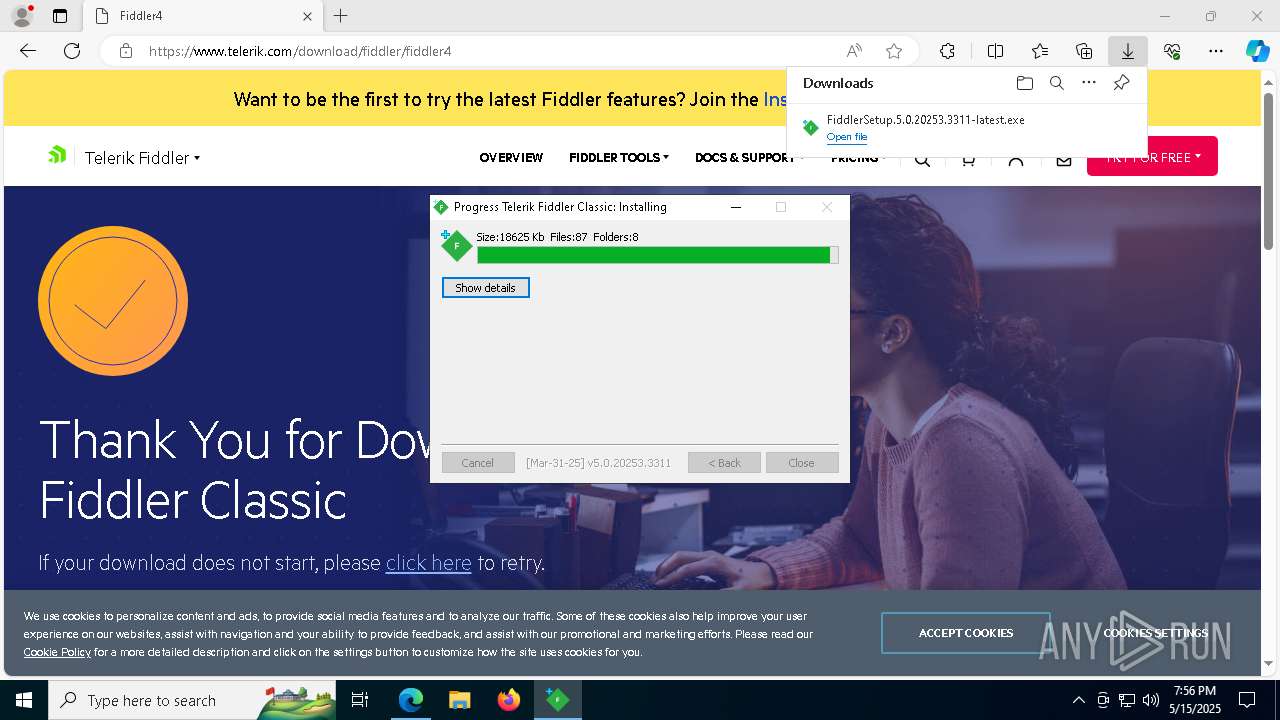
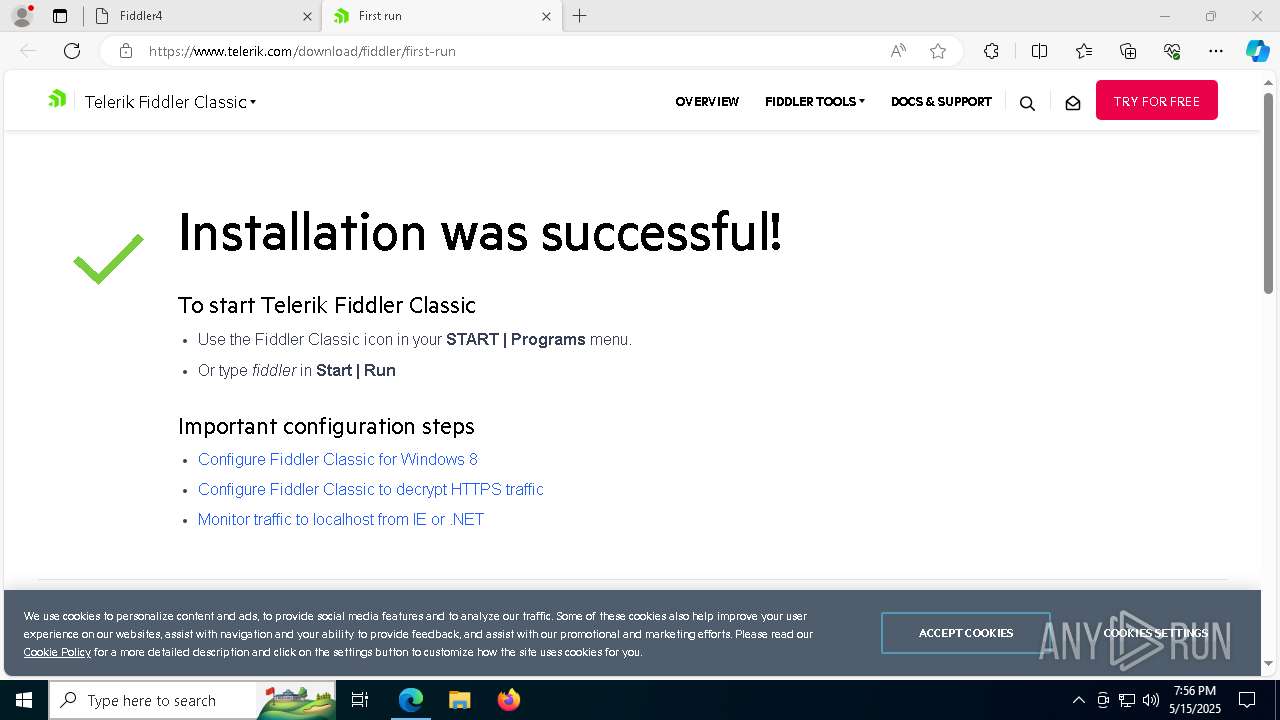
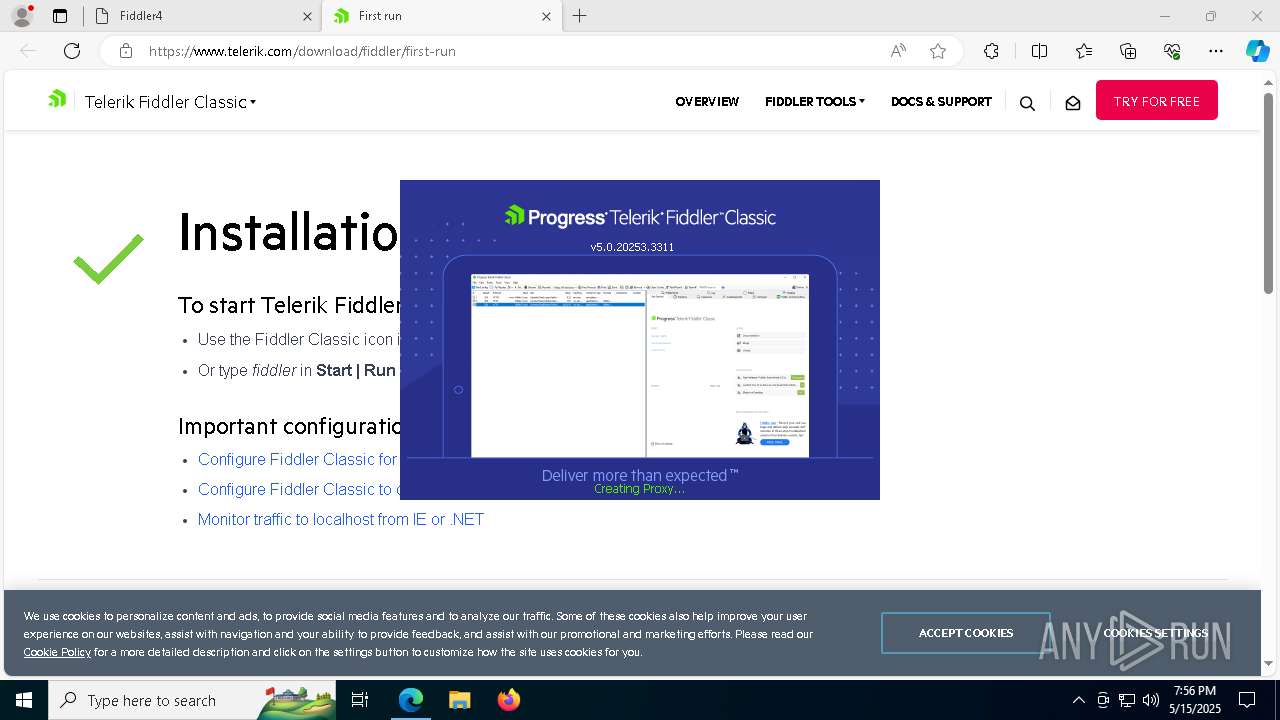
Executable content was dropped or overwritten
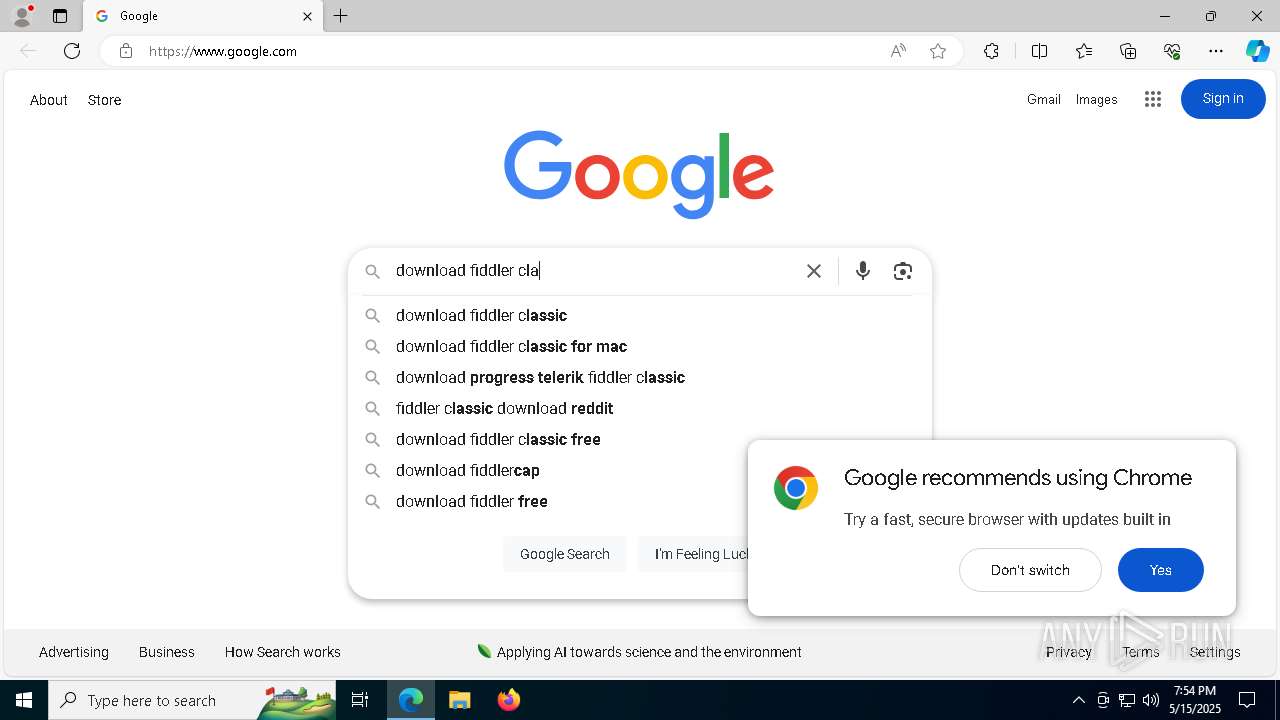
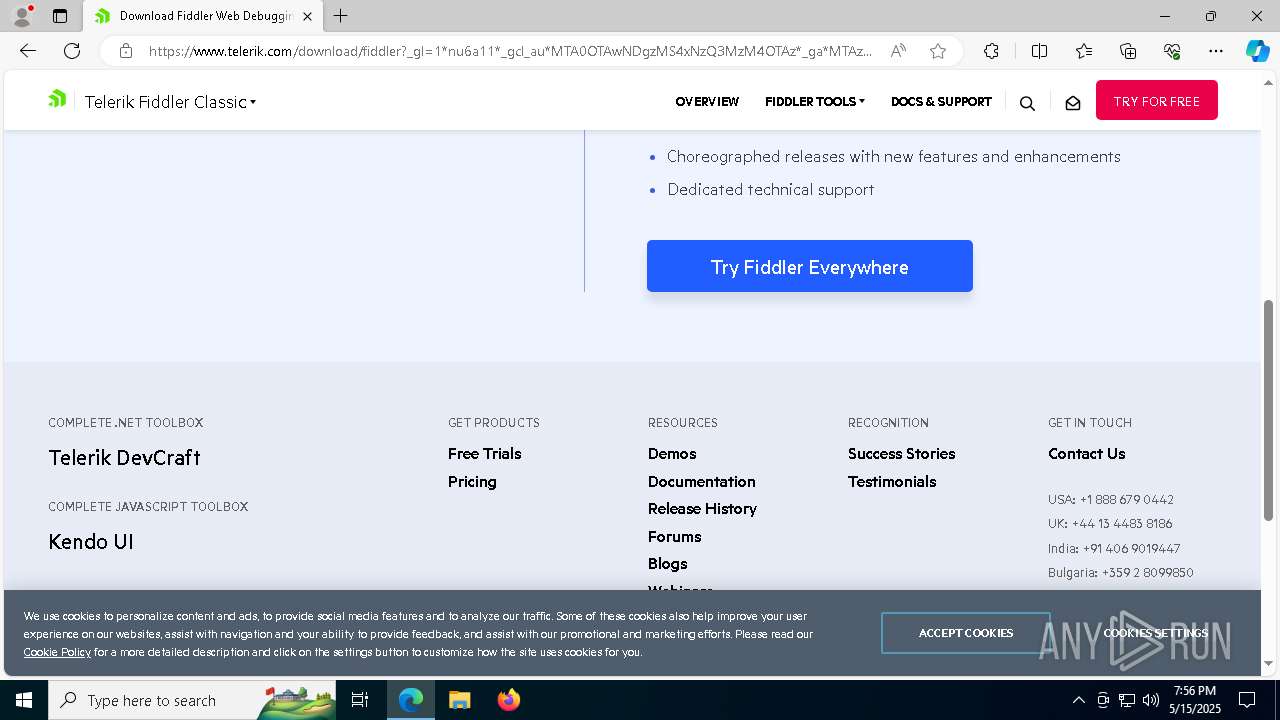
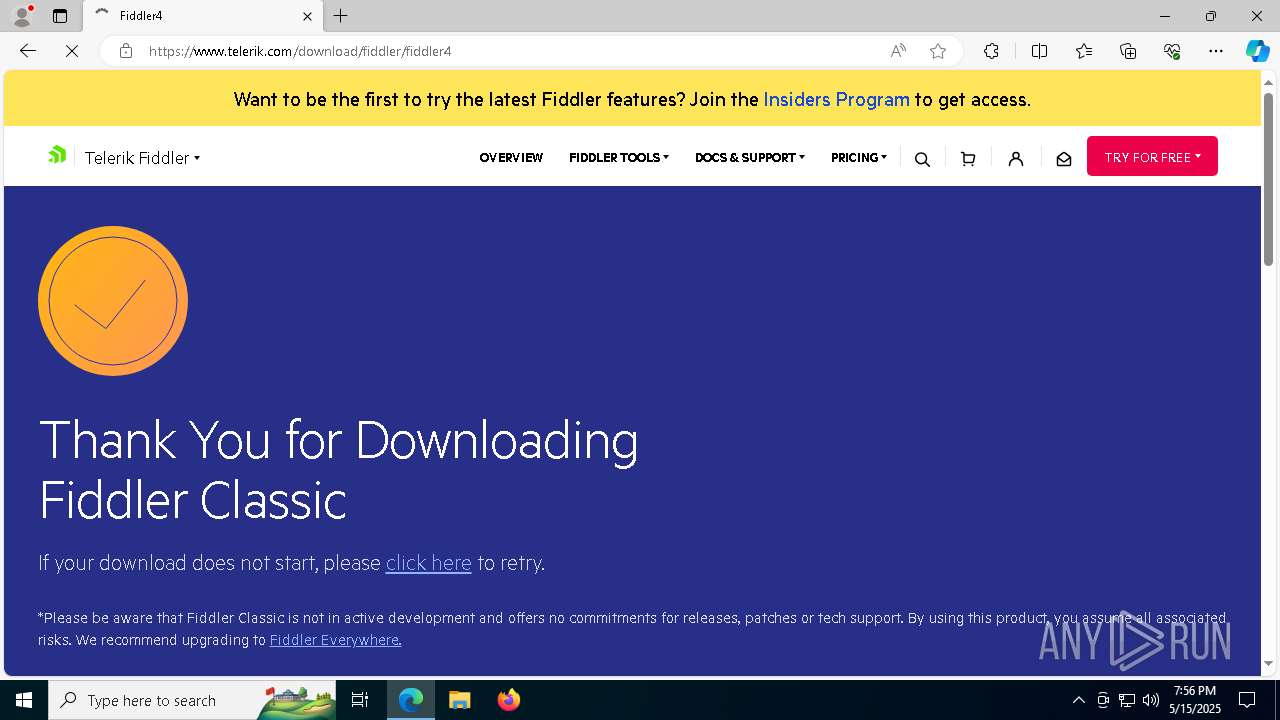
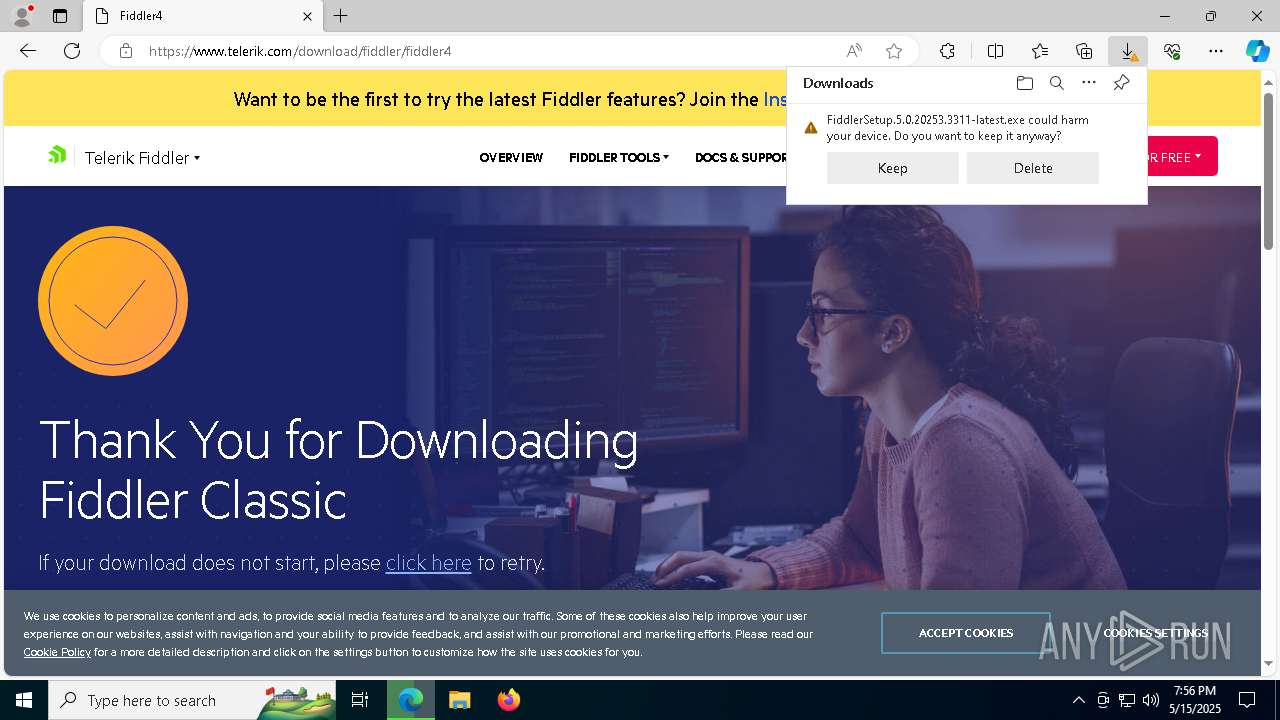
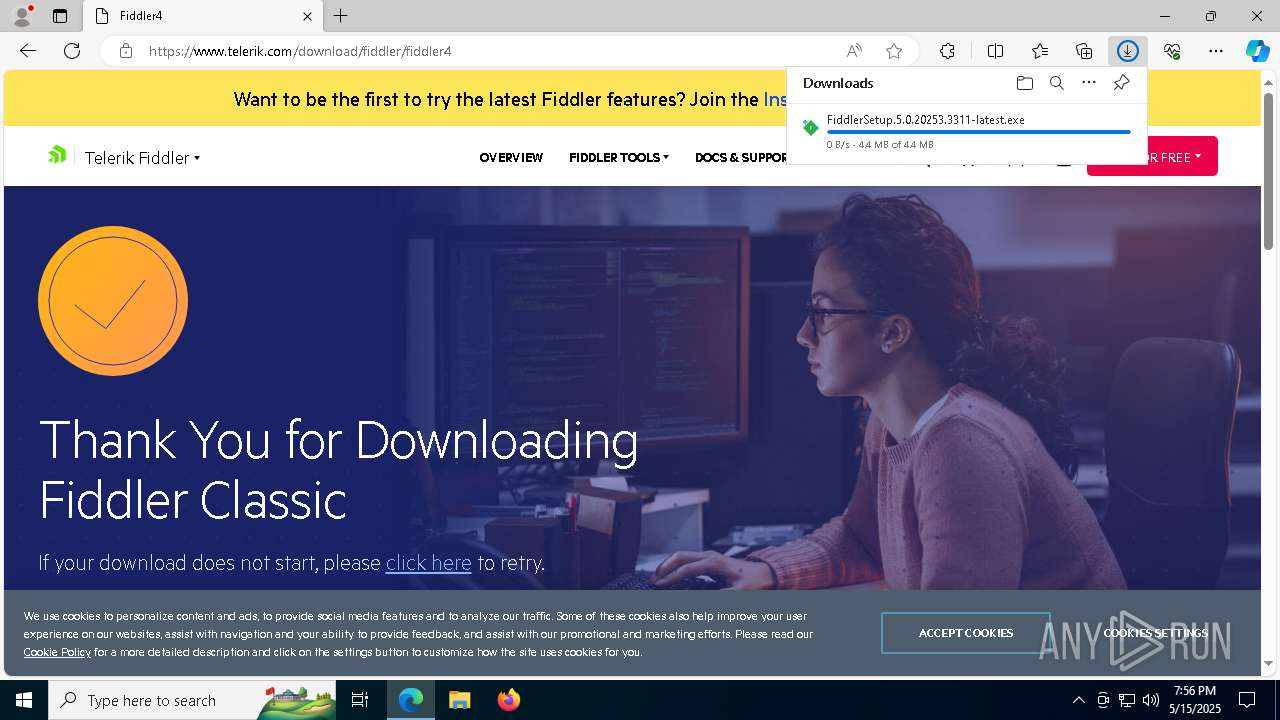
- FiddlerSetup.5.0.20253.3311-latest.exe (PID: 6004)
- FiddlerSetup.exe (PID: 3620)
- mscorsvw.exe (PID: 7764)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 3156)
- mscorsvw.exe (PID: 8308)
- mscorsvw.exe (PID: 8240)
- mscorsvw.exe (PID: 240)
- mscorsvw.exe (PID: 8760)
- mscorsvw.exe (PID: 8744)
- mscorsvw.exe (PID: 8976)
- mscorsvw.exe (PID: 8752)
- mscorsvw.exe (PID: 9080)
- mscorsvw.exe (PID: 9188)
- mscorsvw.exe (PID: 6612)
- mscorsvw.exe (PID: 5980)
- mscorsvw.exe (PID: 4028)
- mscorsvw.exe (PID: 8240)
- mscorsvw.exe (PID: 5796)
- mscorsvw.exe (PID: 6852)
- mscorsvw.exe (PID: 8308)
- mscorsvw.exe (PID: 4000)
- mscorsvw.exe (PID: 9136)
- mscorsvw.exe (PID: 8552)
- mscorsvw.exe (PID: 9028)
- mscorsvw.exe (PID: 3192)
Process drops legitimate windows executable
- FiddlerSetup.exe (PID: 3620)
- mscorsvw.exe (PID: 7764)
- mscorsvw.exe (PID: 3156)
- mscorsvw.exe (PID: 8308)
- mscorsvw.exe (PID: 8240)
- mscorsvw.exe (PID: 240)
- mscorsvw.exe (PID: 8760)
- mscorsvw.exe (PID: 8976)
- mscorsvw.exe (PID: 8752)
- mscorsvw.exe (PID: 9080)
- mscorsvw.exe (PID: 9188)
- mscorsvw.exe (PID: 6852)
- mscorsvw.exe (PID: 6612)
- mscorsvw.exe (PID: 5980)
- mscorsvw.exe (PID: 4028)
- mscorsvw.exe (PID: 8308)
- mscorsvw.exe (PID: 8240)
- mscorsvw.exe (PID: 5796)
- mscorsvw.exe (PID: 4000)
- mscorsvw.exe (PID: 9136)
- mscorsvw.exe (PID: 8552)
- mscorsvw.exe (PID: 9028)
- mscorsvw.exe (PID: 3192)
Reads security settings of Internet Explorer
- FiddlerSetup.exe (PID: 3620)
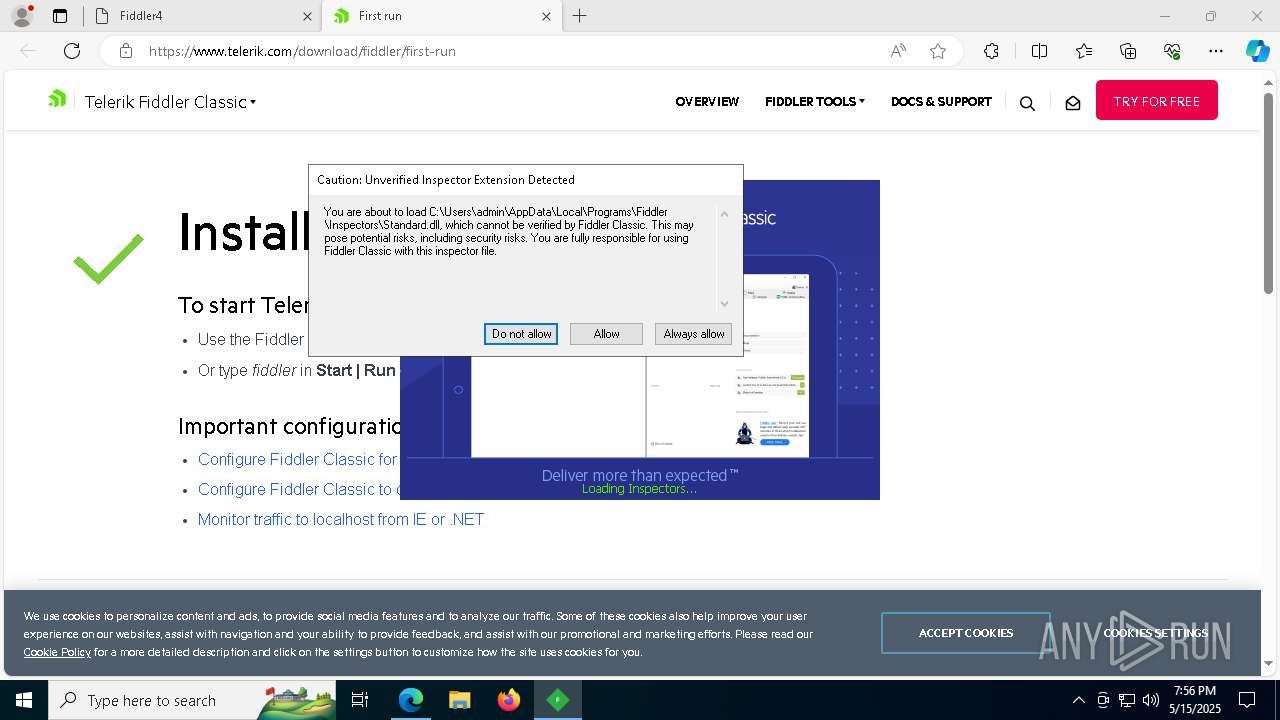
Malware-specific behavior (creating "System.dll" in Temp)
- FiddlerSetup.exe (PID: 3620)
The process creates files with name similar to system file names
- FiddlerSetup.exe (PID: 3620)
Starts application with an unusual extension
- FiddlerSetup.exe (PID: 3620)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- FiddlerSetup.exe (PID: 3620)
Uses NETSH.EXE to add a firewall rule or allowed programs
- FiddlerSetup.exe (PID: 3620)
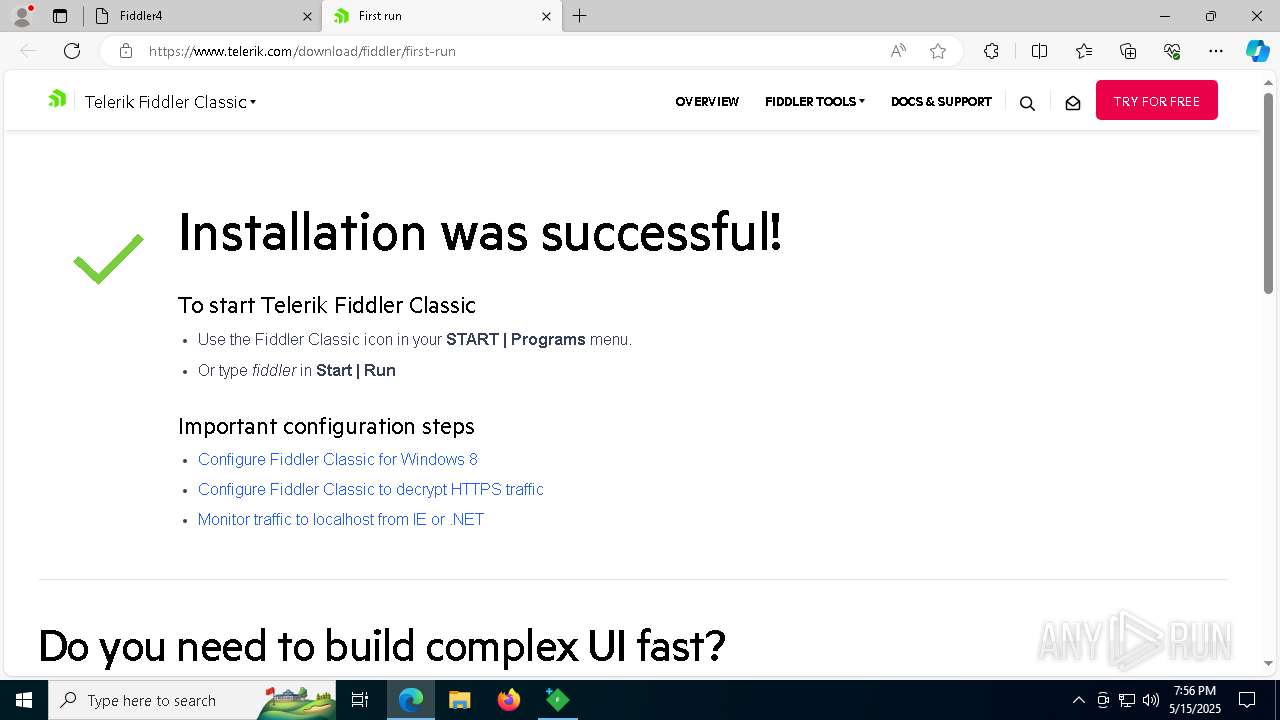
Creates a software uninstall entry
- FiddlerSetup.exe (PID: 3620)
INFO
Checks supported languages
- identity_helper.exe (PID: 5956)
- FiddlerSetup.5.0.20253.3311-latest.exe (PID: 6004)
- FiddlerSetup.exe (PID: 3620)
- ngen.exe (PID: 6744)
- ngen.exe (PID: 5232)
- mscorsvw.exe (PID: 2152)
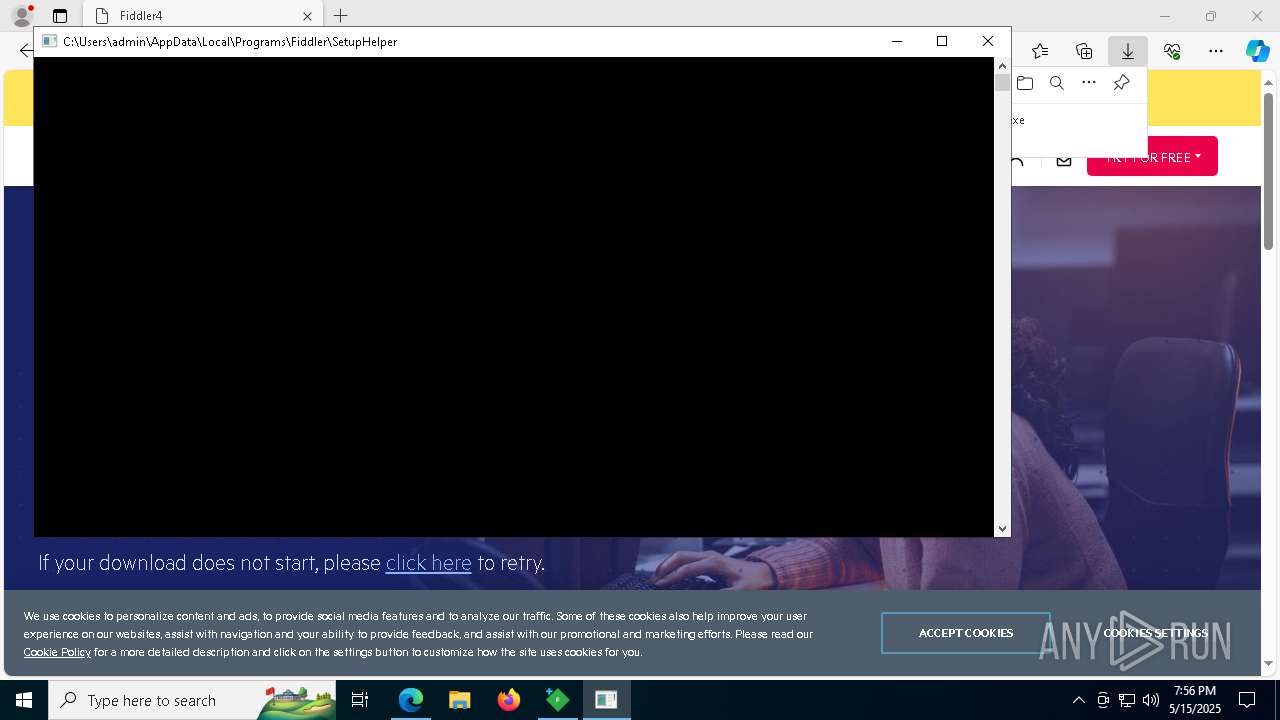
- SetupHelper (PID: 8108)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 7764)
- mscorsvw.exe (PID: 3156)
- mscorsvw.exe (PID: 240)
Executable content was dropped or overwritten
- msedge.exe (PID: 6620)
- msedge.exe (PID: 7380)
- msedge.exe (PID: 8568)
Reads the computer name
- identity_helper.exe (PID: 5956)
- FiddlerSetup.exe (PID: 3620)
- ngen.exe (PID: 5232)
- ngen.exe (PID: 6744)
- SetupHelper (PID: 8108)
- mscorsvw.exe (PID: 2152)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 3156)
- mscorsvw.exe (PID: 7764)
- mscorsvw.exe (PID: 240)
Application launched itself
- msedge.exe (PID: 6620)
Create files in a temporary directory
- FiddlerSetup.5.0.20253.3311-latest.exe (PID: 6004)
- FiddlerSetup.exe (PID: 3620)
Reads Environment values
- identity_helper.exe (PID: 5956)
Reads the software policy settings
- slui.exe (PID: 5868)
Creates files or folders in the user directory
- FiddlerSetup.exe (PID: 3620)
The sample compiled with english language support
- msedge.exe (PID: 7380)
- FiddlerSetup.exe (PID: 3620)
- FiddlerSetup.5.0.20253.3311-latest.exe (PID: 6004)
- msedge.exe (PID: 6620)
- mscorsvw.exe (PID: 7764)
- mscorsvw.exe (PID: 3156)
- mscorsvw.exe (PID: 8308)
- mscorsvw.exe (PID: 8240)
- mscorsvw.exe (PID: 240)
- mscorsvw.exe (PID: 8976)
- mscorsvw.exe (PID: 9080)
- mscorsvw.exe (PID: 8752)
- mscorsvw.exe (PID: 6852)
- mscorsvw.exe (PID: 4028)
- mscorsvw.exe (PID: 8308)
- mscorsvw.exe (PID: 9188)
- mscorsvw.exe (PID: 5796)
- mscorsvw.exe (PID: 8240)
- mscorsvw.exe (PID: 4000)
- mscorsvw.exe (PID: 9136)
- mscorsvw.exe (PID: 9028)
- mscorsvw.exe (PID: 3192)
- msedge.exe (PID: 8568)
Process checks computer location settings
- FiddlerSetup.exe (PID: 3620)
NGen native .NET image generation
- ngen.exe (PID: 6744)
- ngen.exe (PID: 5232)
Reads the machine GUID from the registry
- mscorsvw.exe (PID: 240)
- mscorsvw.exe (PID: 7764)
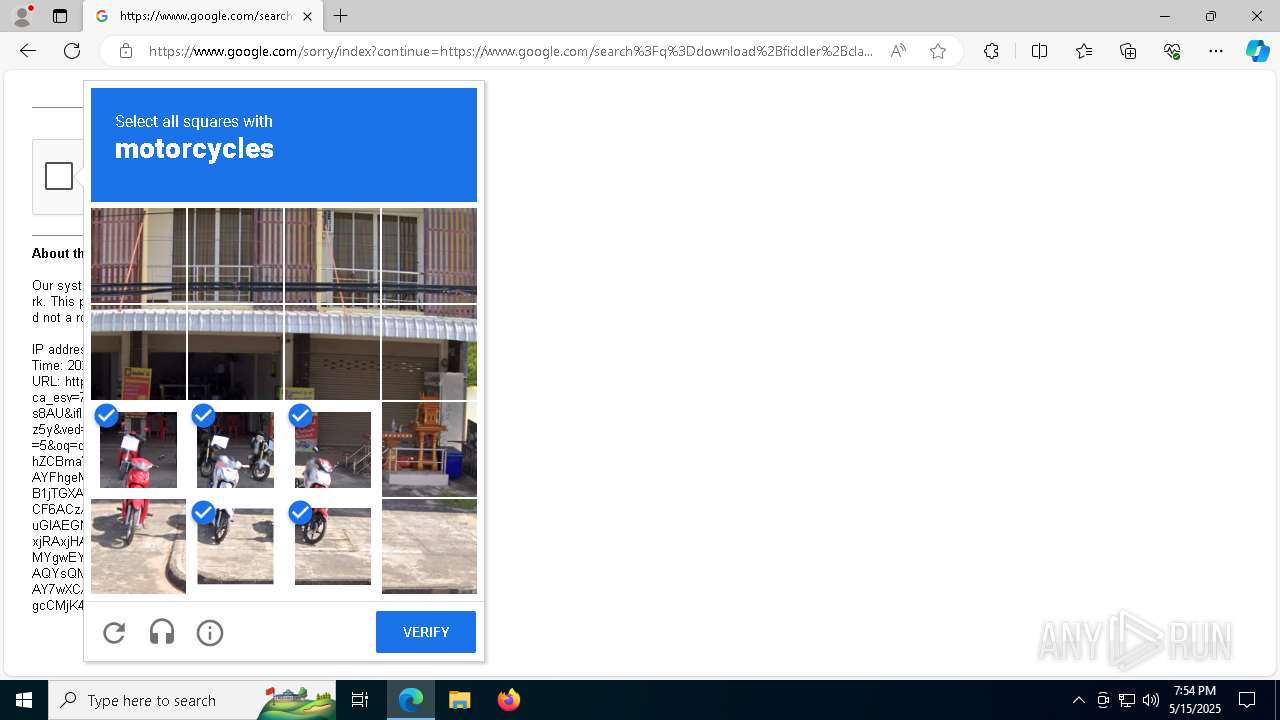
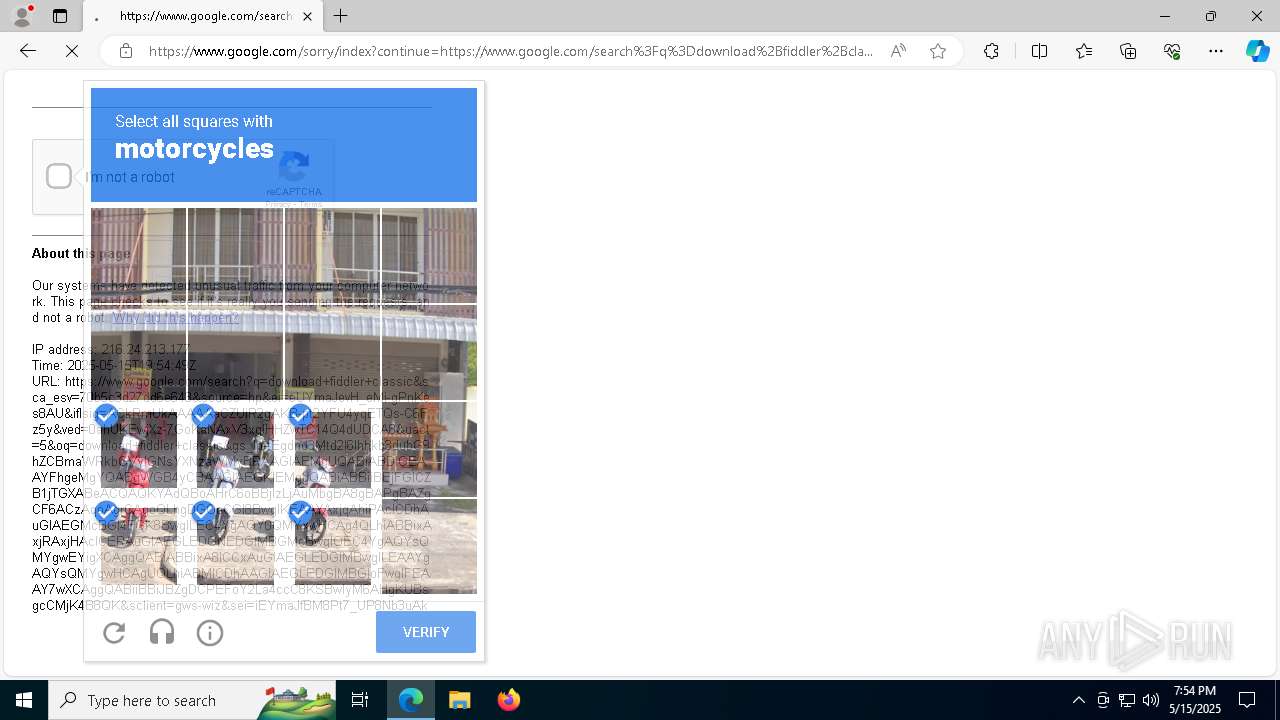
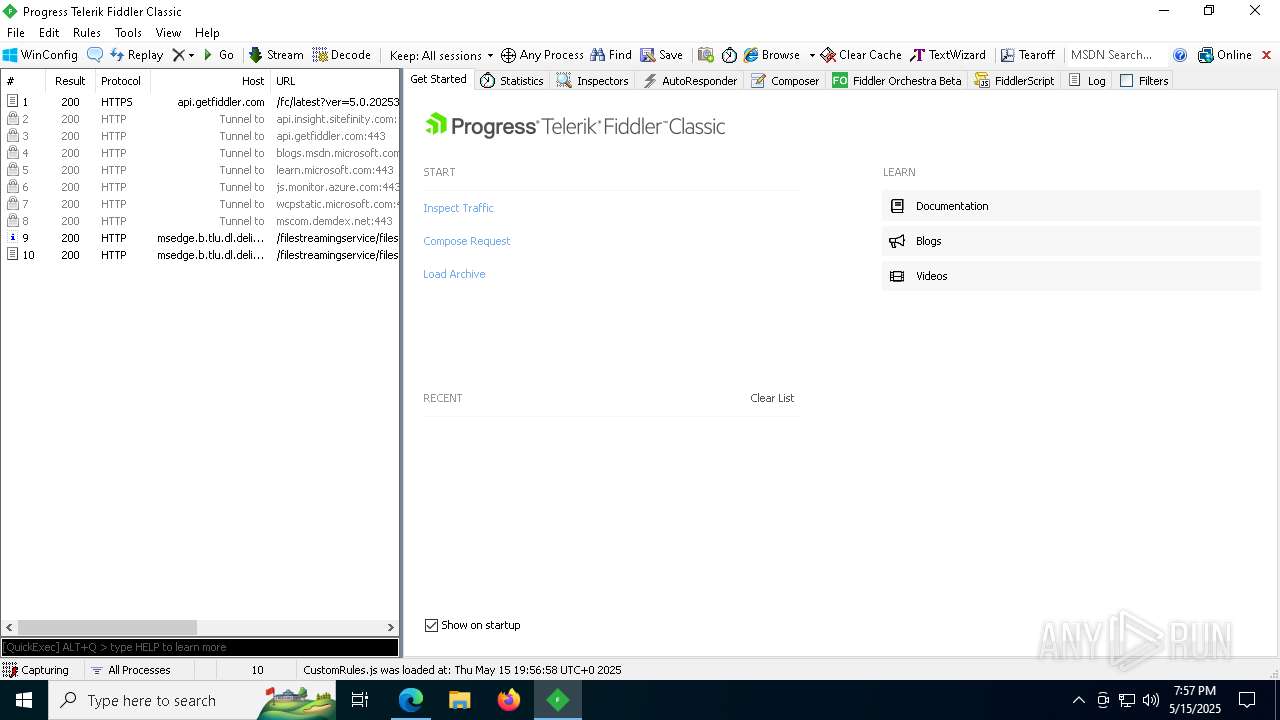
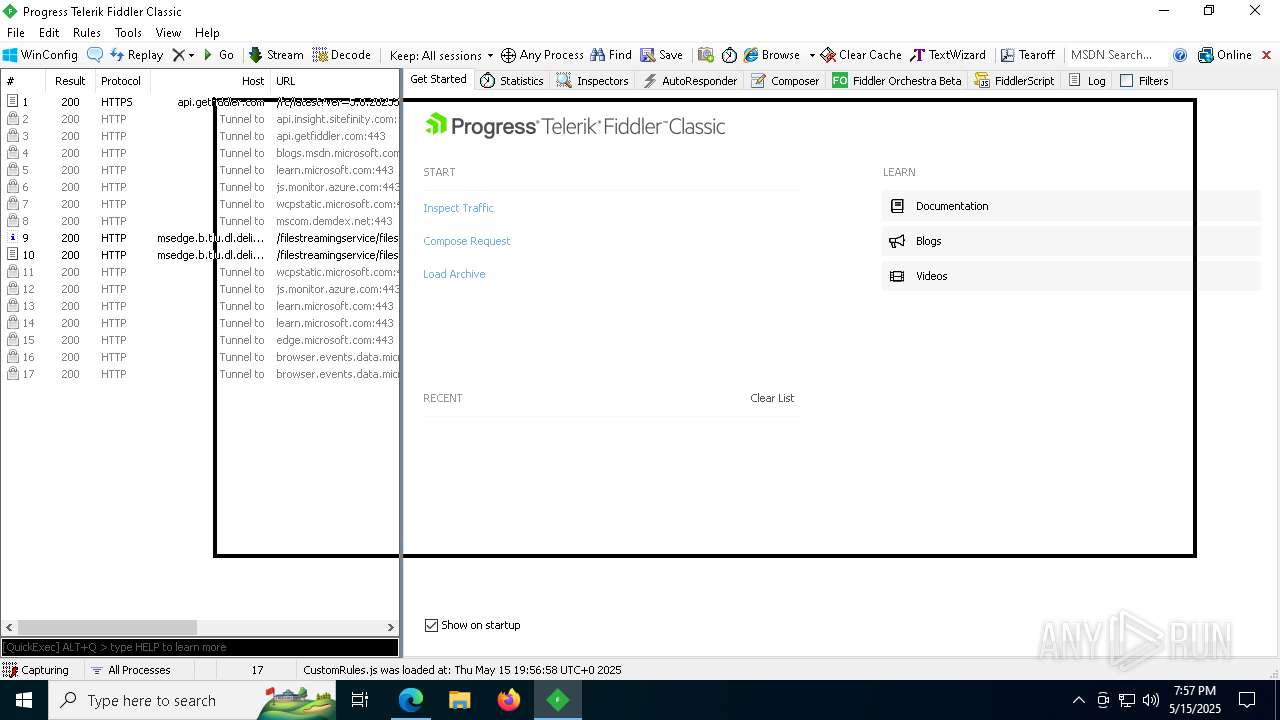
Manual execution by a user
- Fiddler.exe (PID: 6572)
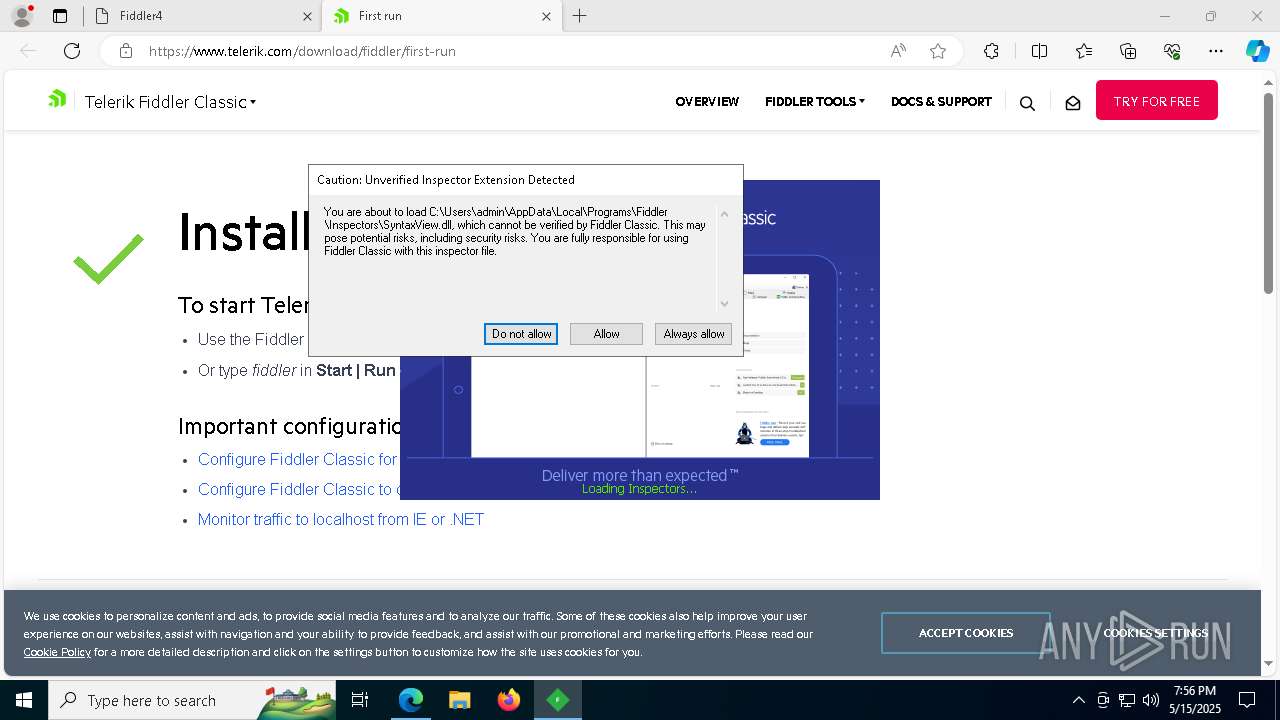
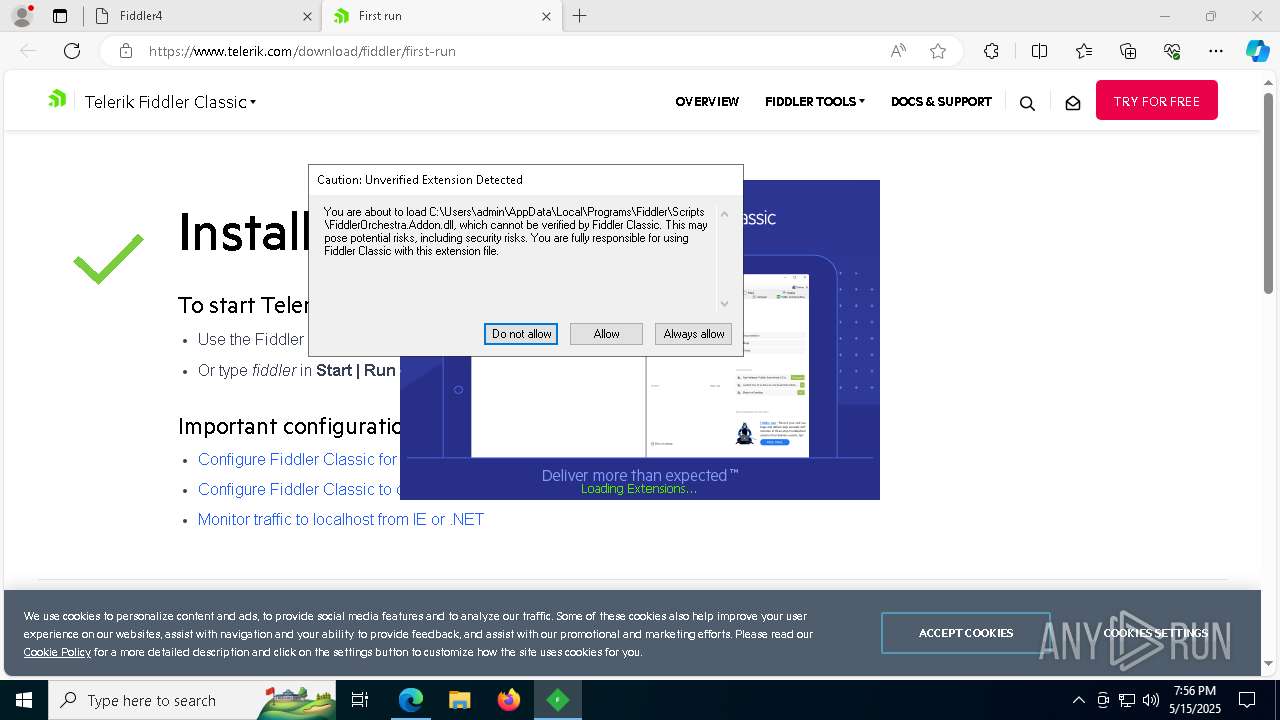
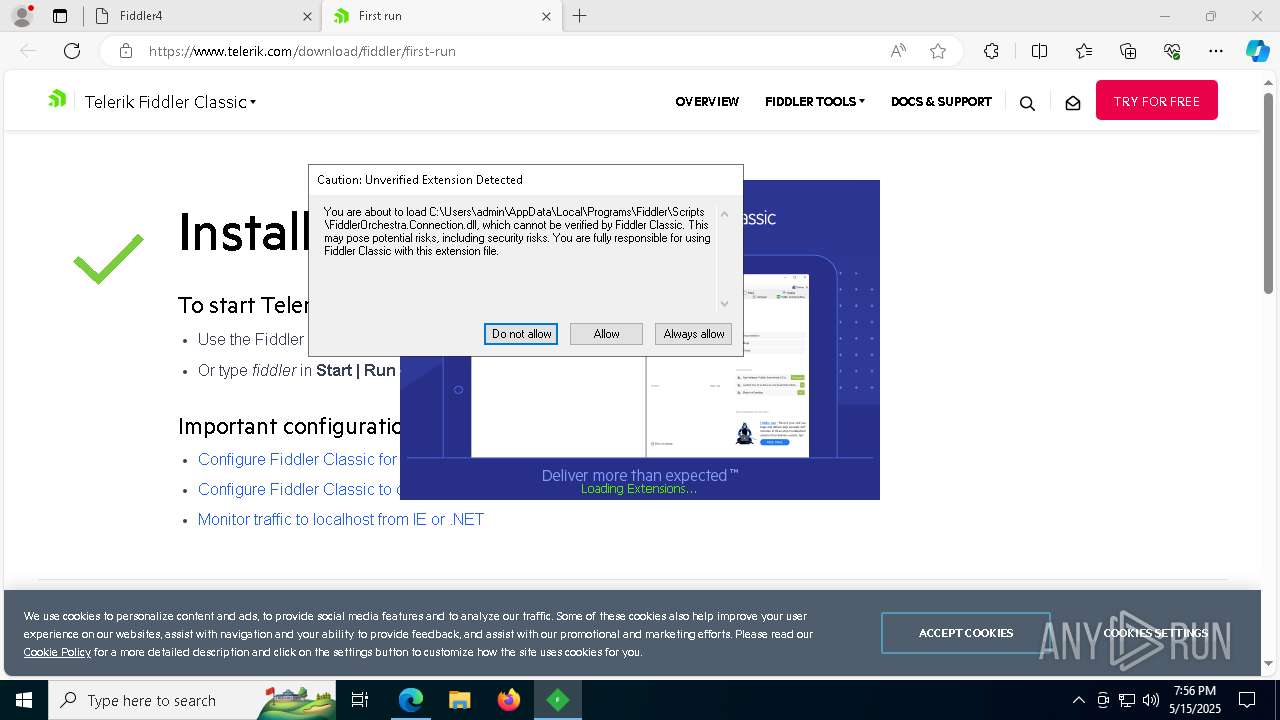
.NET Reactor protector has been detected
- Fiddler.exe (PID: 6572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
274
Monitored processes
129
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7712 --field-trial-handle=2284,i,80398175456058854,10339555253459892123,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 240 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 2c0 -InterruptEvent 0 -NGENProcess 2b0 -Pipe 2bc -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 300 | "C:\WINDOWS\system32\netsh.exe" advfirewall firewall add rule name="FiddlerProxy" program="C:\Users\admin\AppData\Local\Programs\Fiddler\Fiddler.exe" action=allow profile=any dir=in edge=deferuser protocol=tcp description="Permit inbound connections to Fiddler" | C:\Windows\SysWOW64\netsh.exe | — | FiddlerSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=6120 --field-trial-handle=2284,i,80398175456058854,10339555253459892123,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 2a4 -InterruptEvent 0 -NGENProcess 294 -Pipe 35c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5560 --field-trial-handle=2284,i,80398175456058854,10339555253459892123,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6856 --field-trial-handle=2284,i,80398175456058854,10339555253459892123,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=3736 --field-trial-handle=2284,i,80398175456058854,10339555253459892123,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --mojo-platform-channel-handle=4188 --field-trial-handle=2284,i,80398175456058854,10339555253459892123,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
30 789
Read events
30 583
Write events
185
Delete events
21
Modification events
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CBE24B51C8932F00 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C7E85551C8932F00 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E9164BD9-D739-498E-A8D3-233C109EFB85} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4EECE55C-AF34-406C-81C5-1FC16E1F0B63} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1B4F6025-FEAC-4161-B181-370710E85760} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5ACA96CD-0CAD-408B-BFC3-8A36A8C2B89C} | |||
Executable files
121
Suspicious files
599
Text files
102
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b46d.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b47d.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b48c.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b48c.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b48c.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
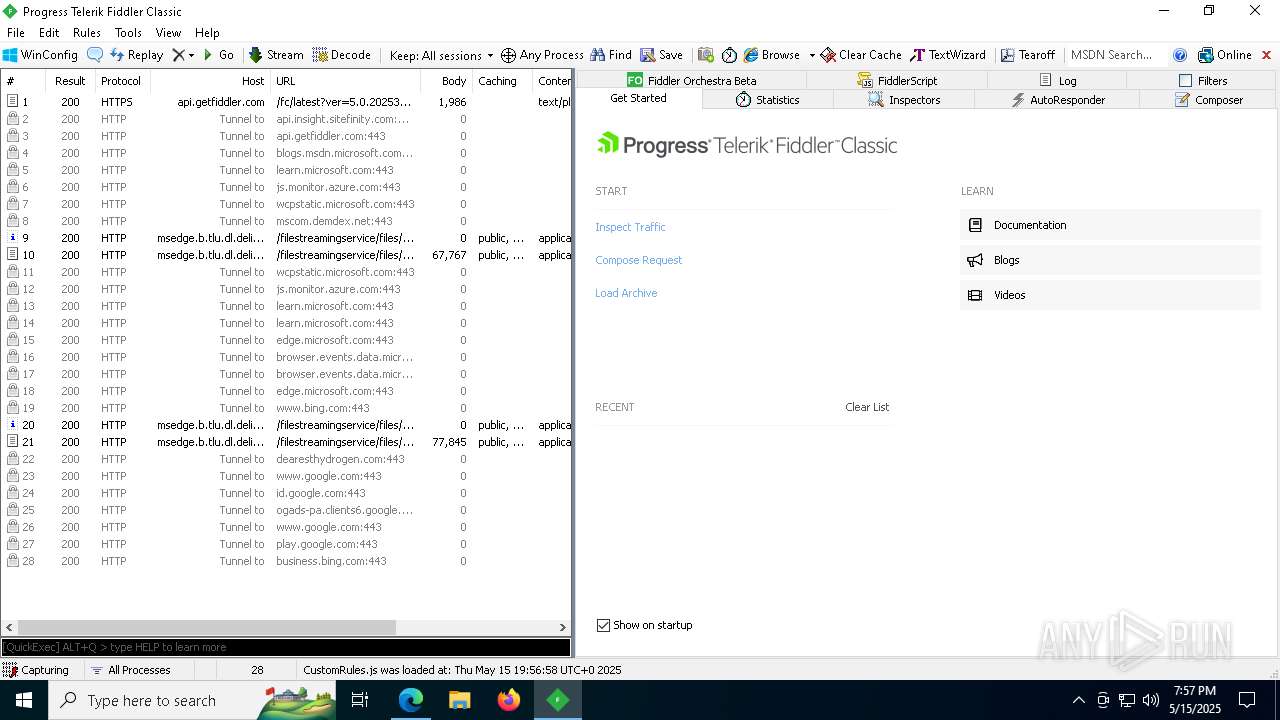
HTTP(S) requests
56
TCP/UDP connections
371
DNS requests
357
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6592 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6592 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
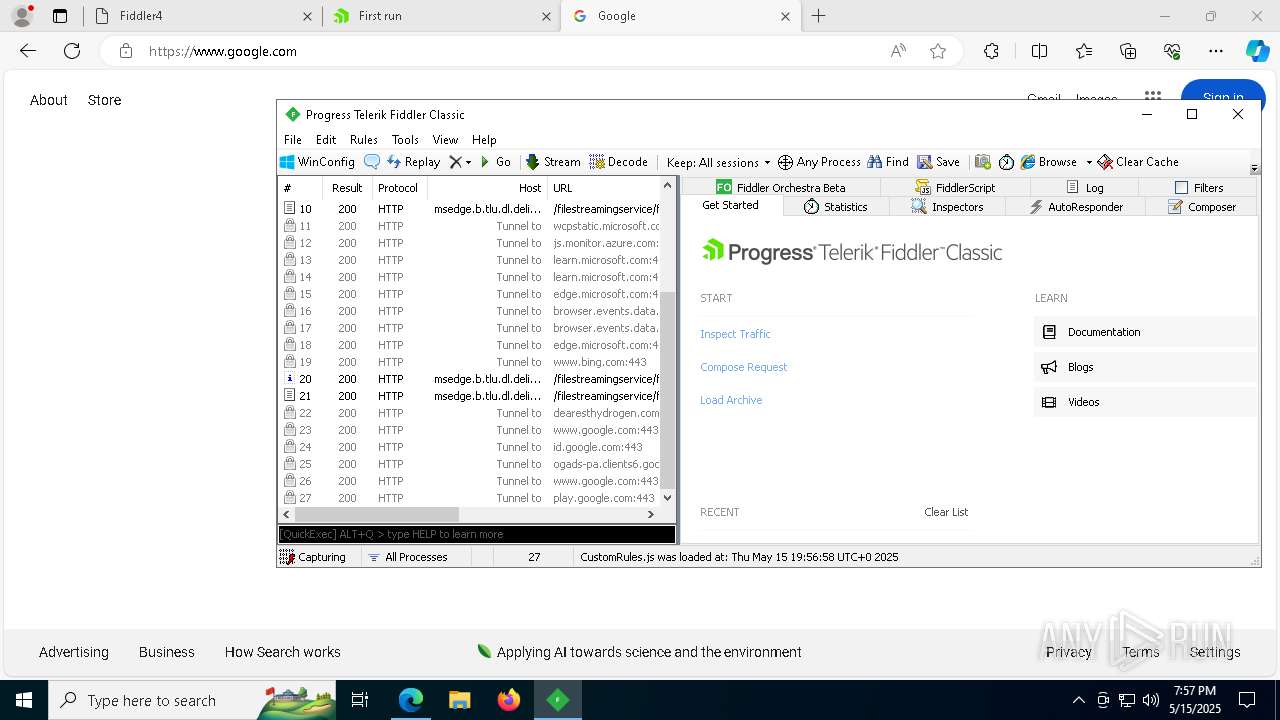
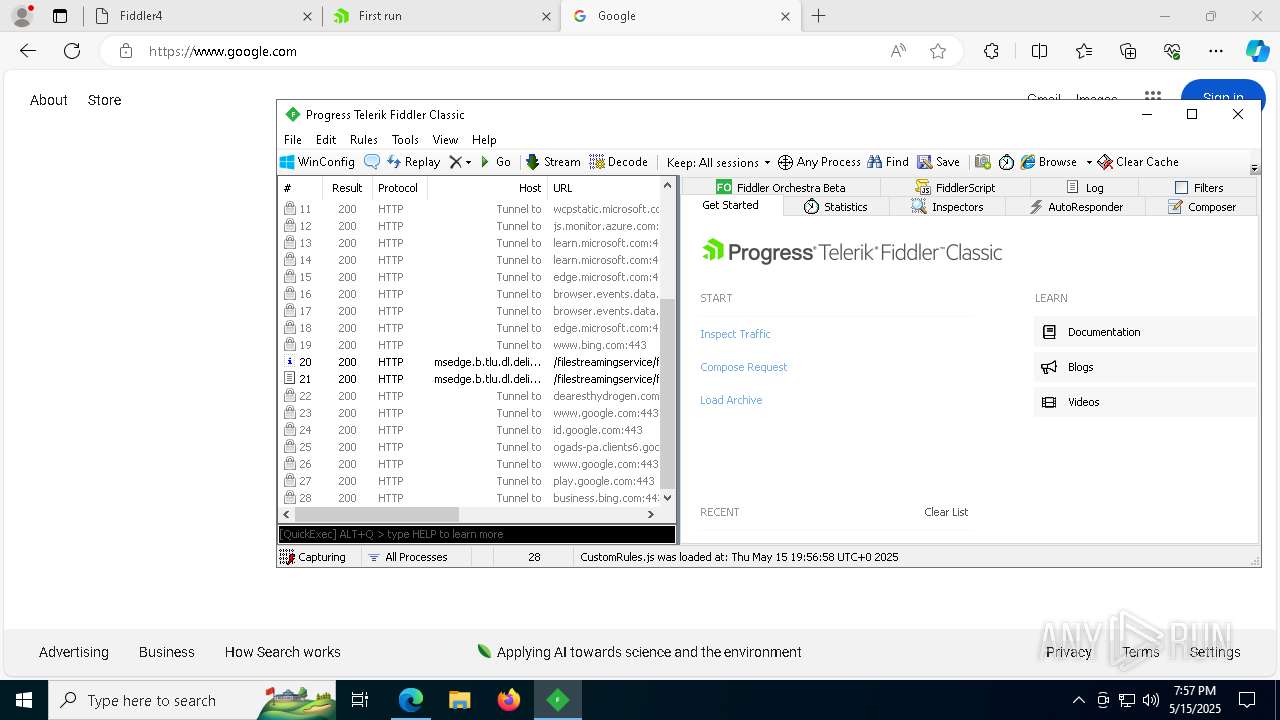
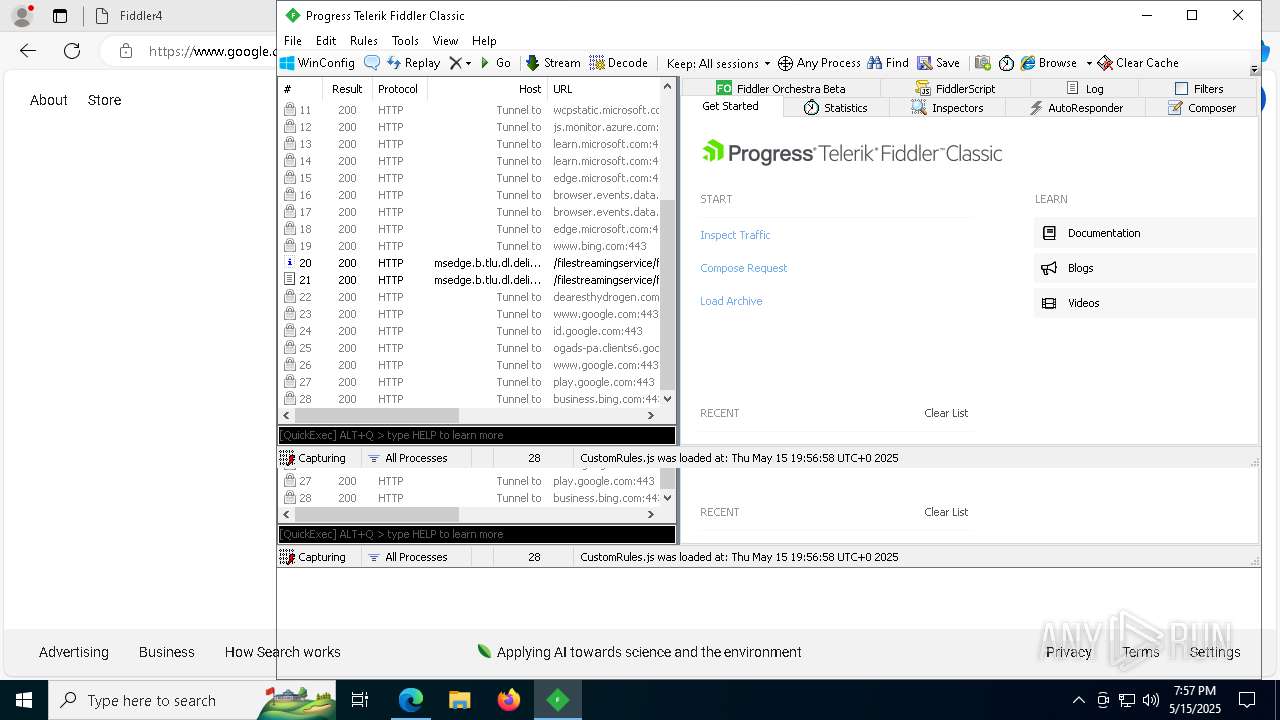
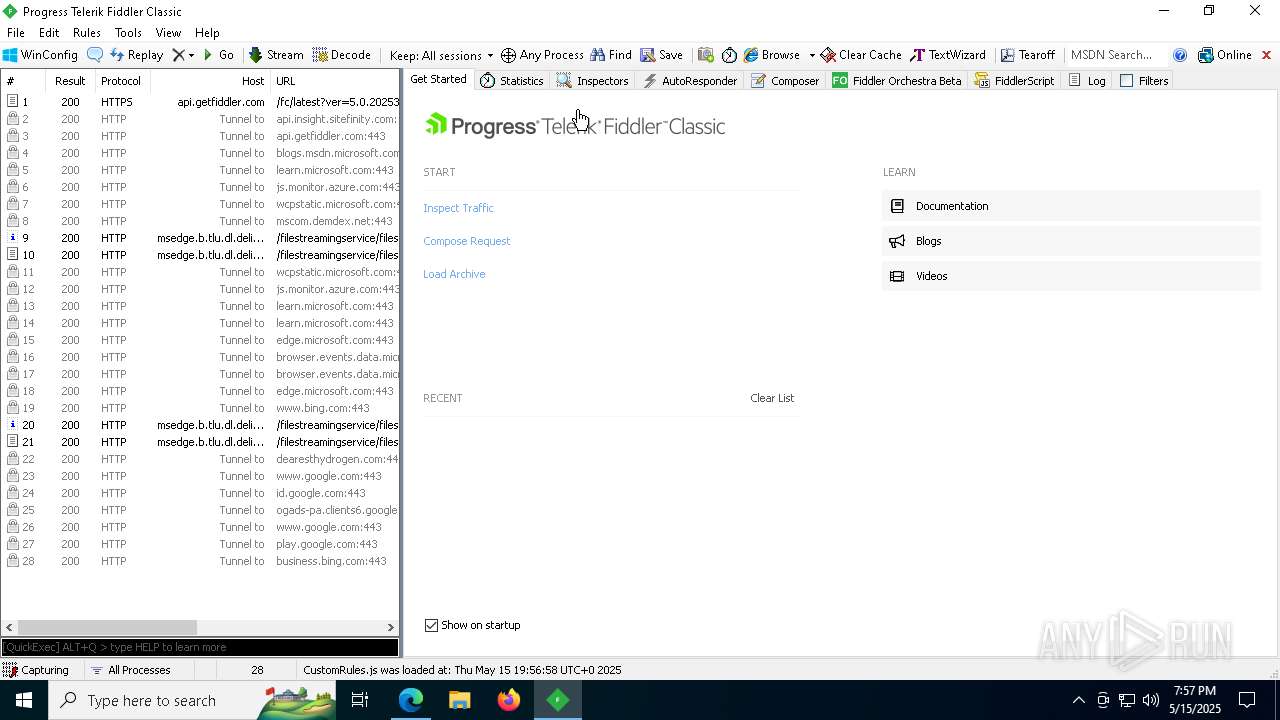
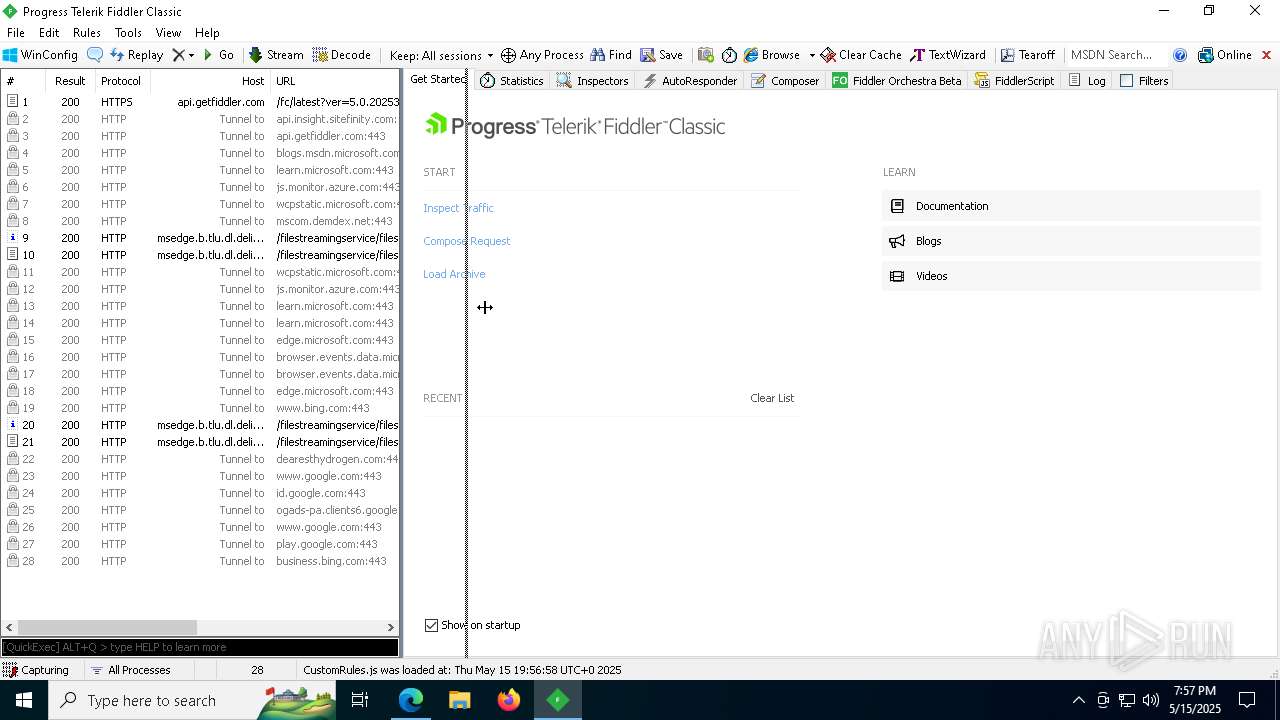
5528 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747702776&P2=404&P3=2&P4=JiK0KX4KyvyqUL%2fw2NxTiDwneuP6RYlTIWxDz1w51zkZ%2buIcUWJPwjRrfcpggzFpAbPZrW5MXxRZTHMY9FXXqA%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747702776&P2=404&P3=2&P4=JiK0KX4KyvyqUL%2fw2NxTiDwneuP6RYlTIWxDz1w51zkZ%2buIcUWJPwjRrfcpggzFpAbPZrW5MXxRZTHMY9FXXqA%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747702776&P2=404&P3=2&P4=JiK0KX4KyvyqUL%2fw2NxTiDwneuP6RYlTIWxDz1w51zkZ%2buIcUWJPwjRrfcpggzFpAbPZrW5MXxRZTHMY9FXXqA%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747702776&P2=404&P3=2&P4=JiK0KX4KyvyqUL%2fw2NxTiDwneuP6RYlTIWxDz1w51zkZ%2buIcUWJPwjRrfcpggzFpAbPZrW5MXxRZTHMY9FXXqA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
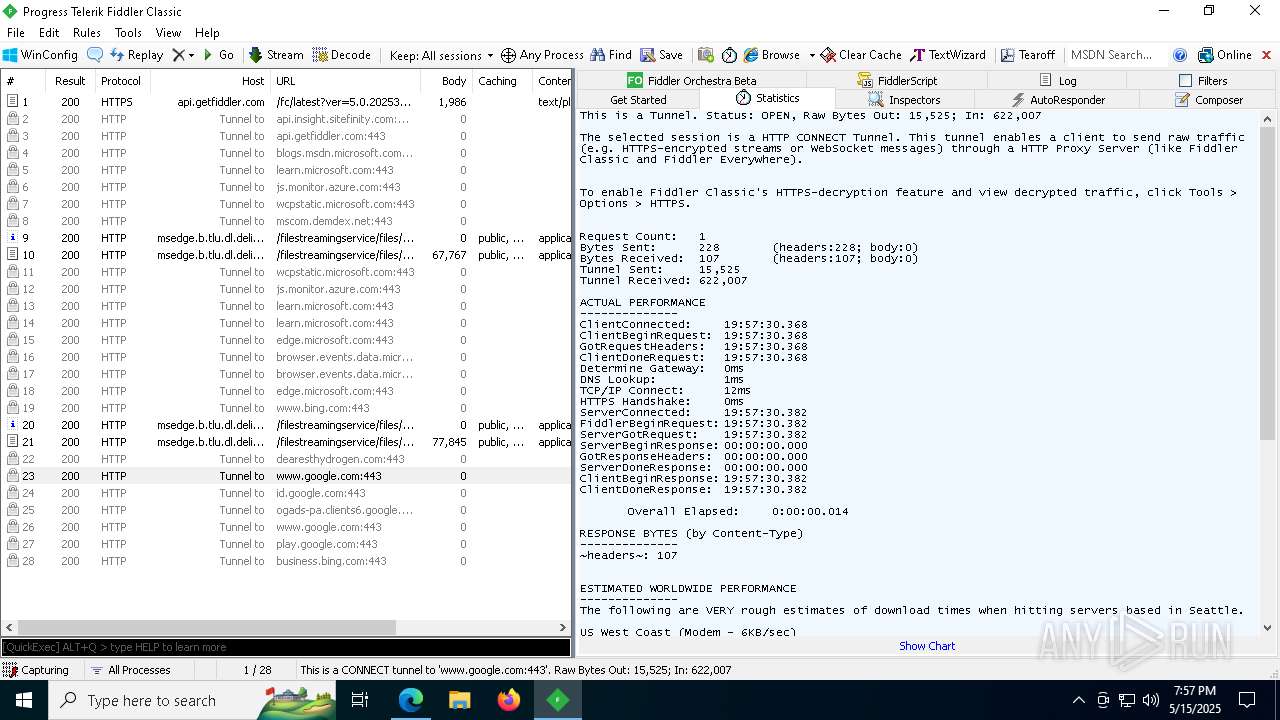
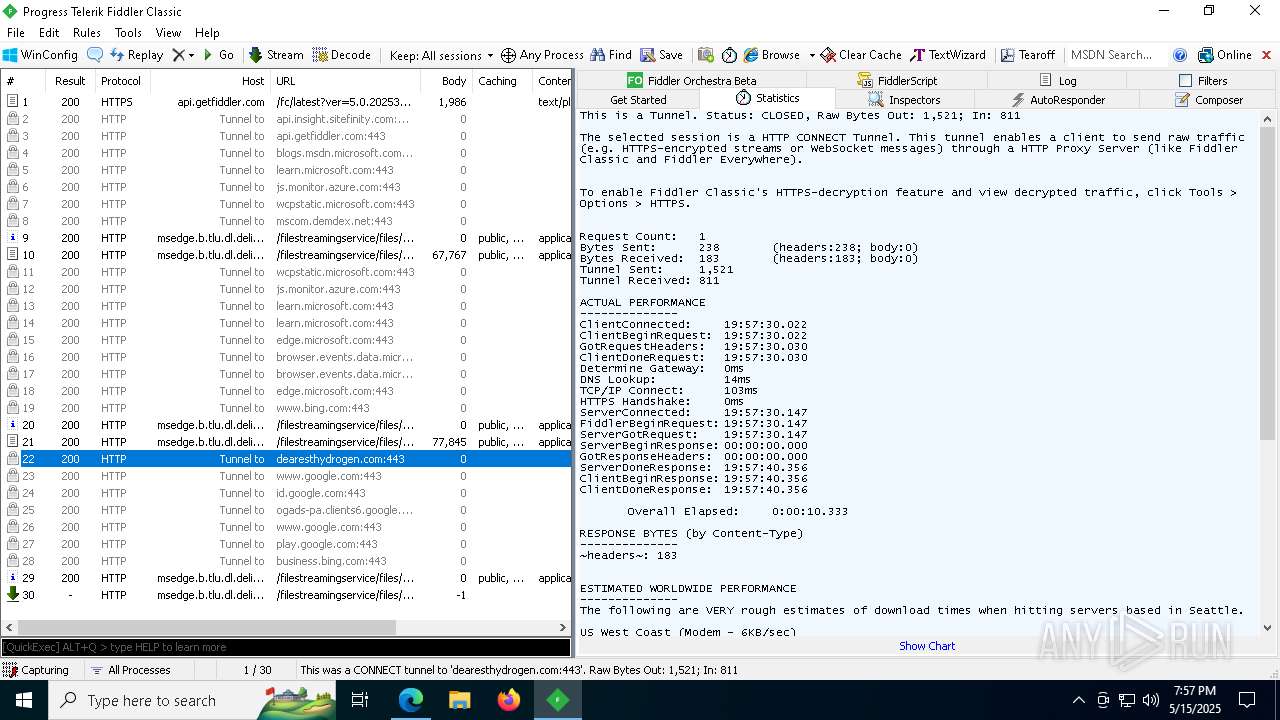
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6620 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
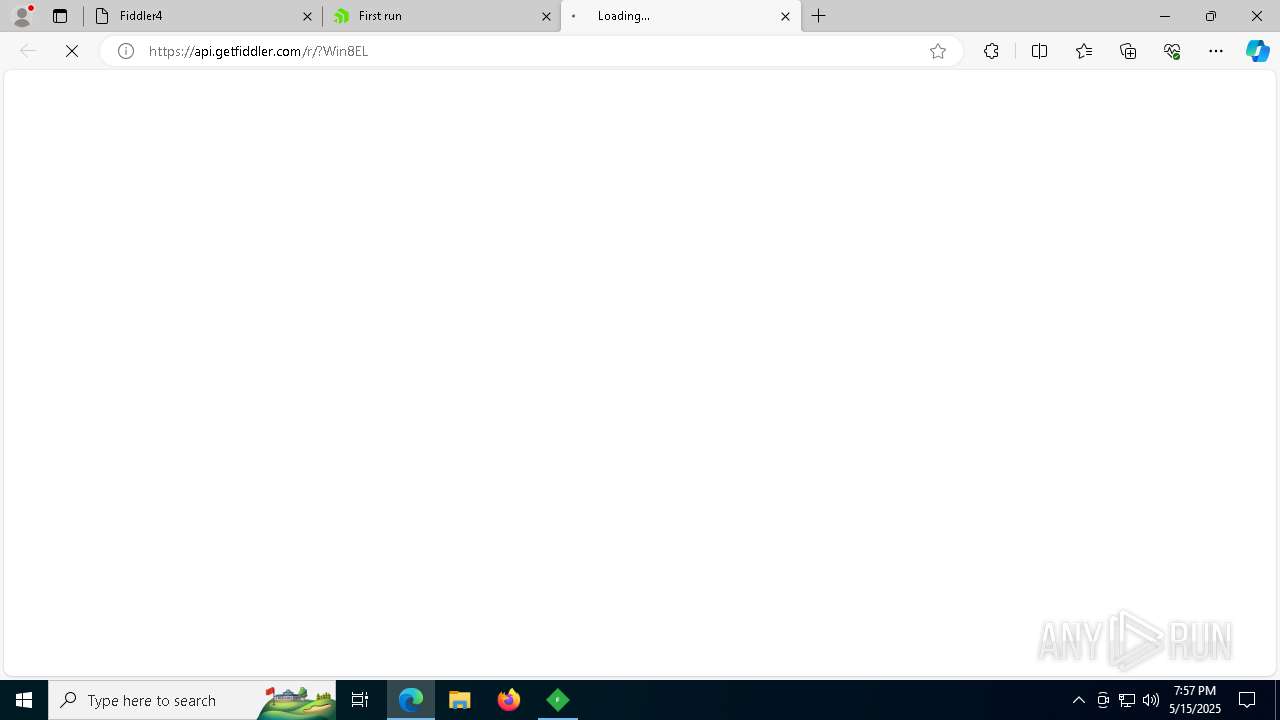
7380 | msedge.exe | 172.240.108.68:80 | dearesthydrogen.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
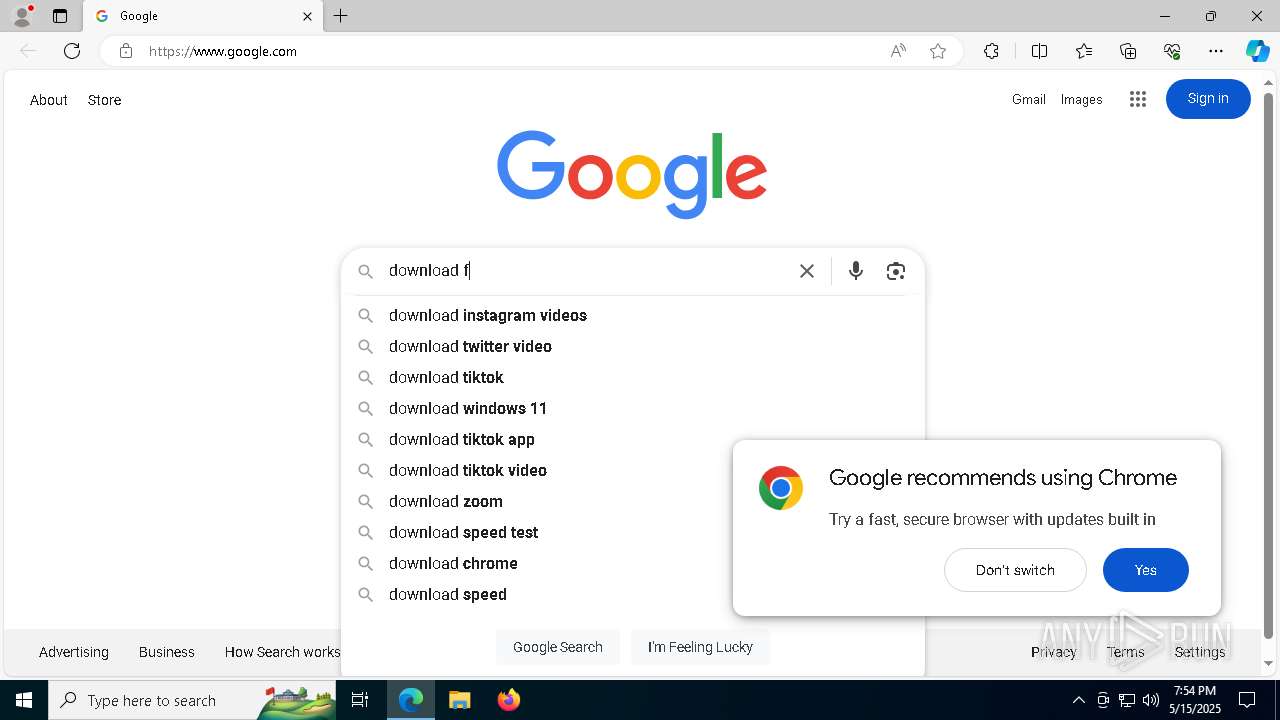
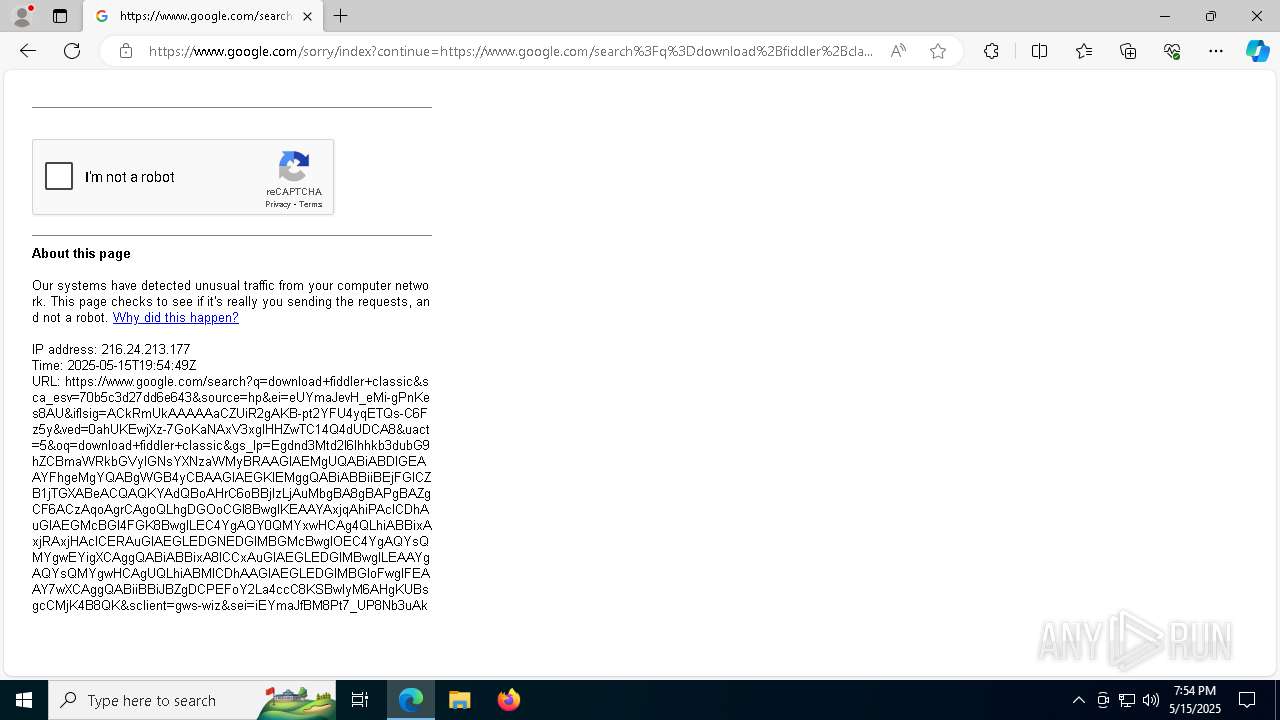
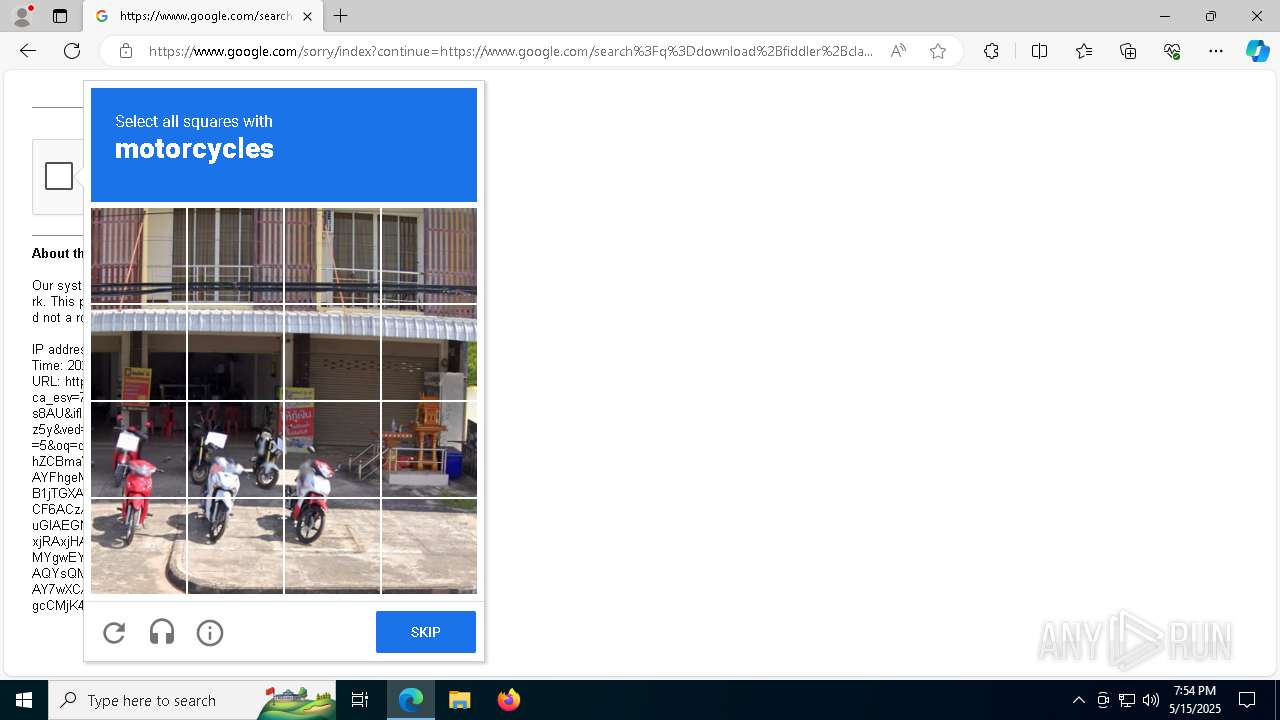
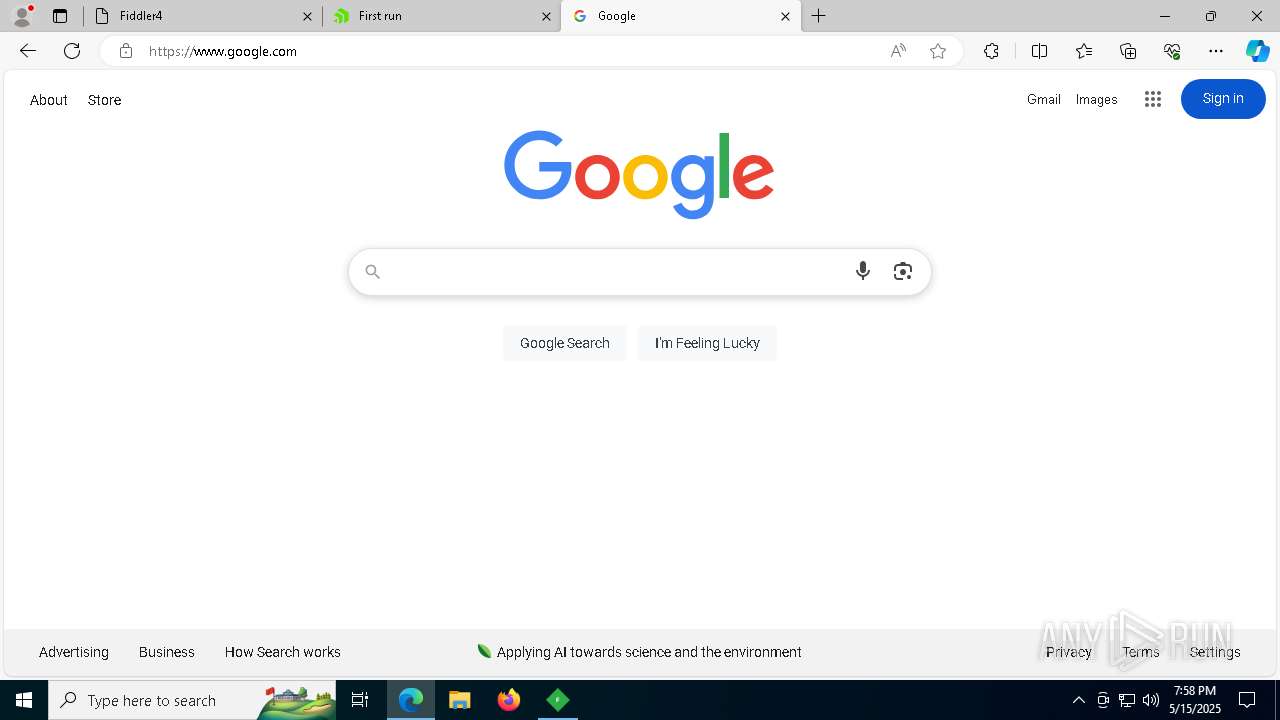
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
dearesthydrogen.com |
| unknown |
business.bing.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |