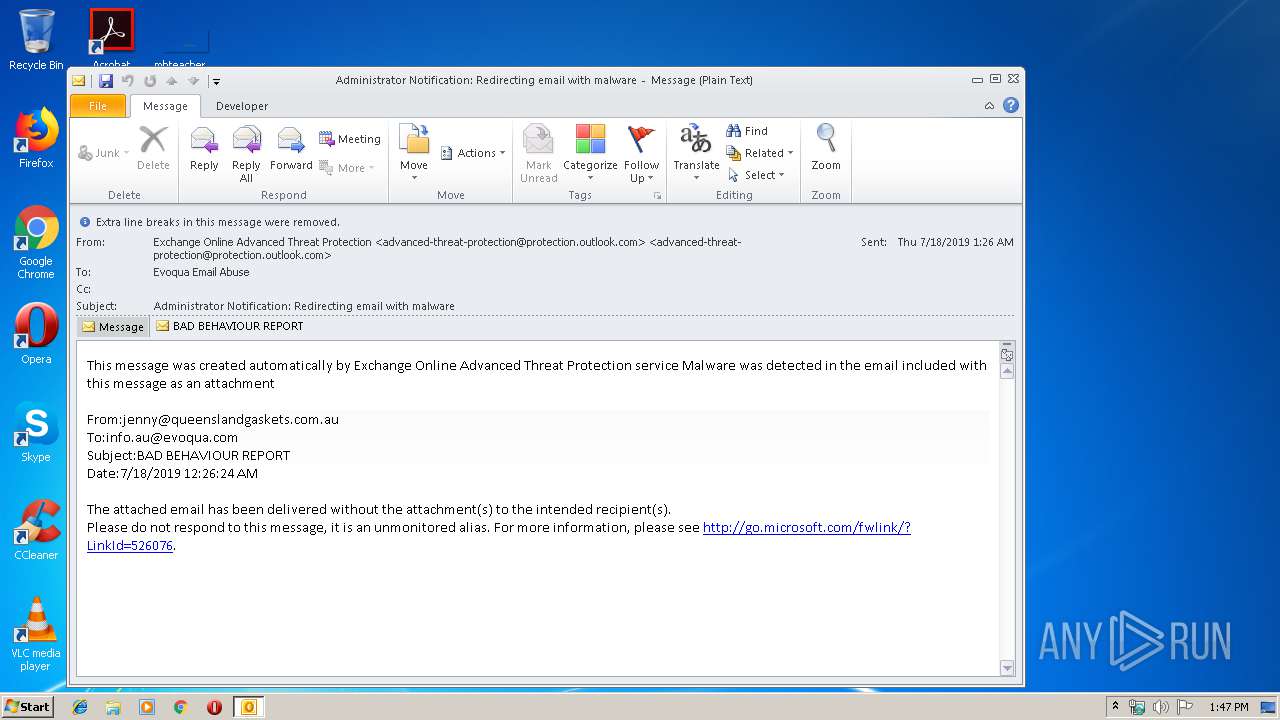
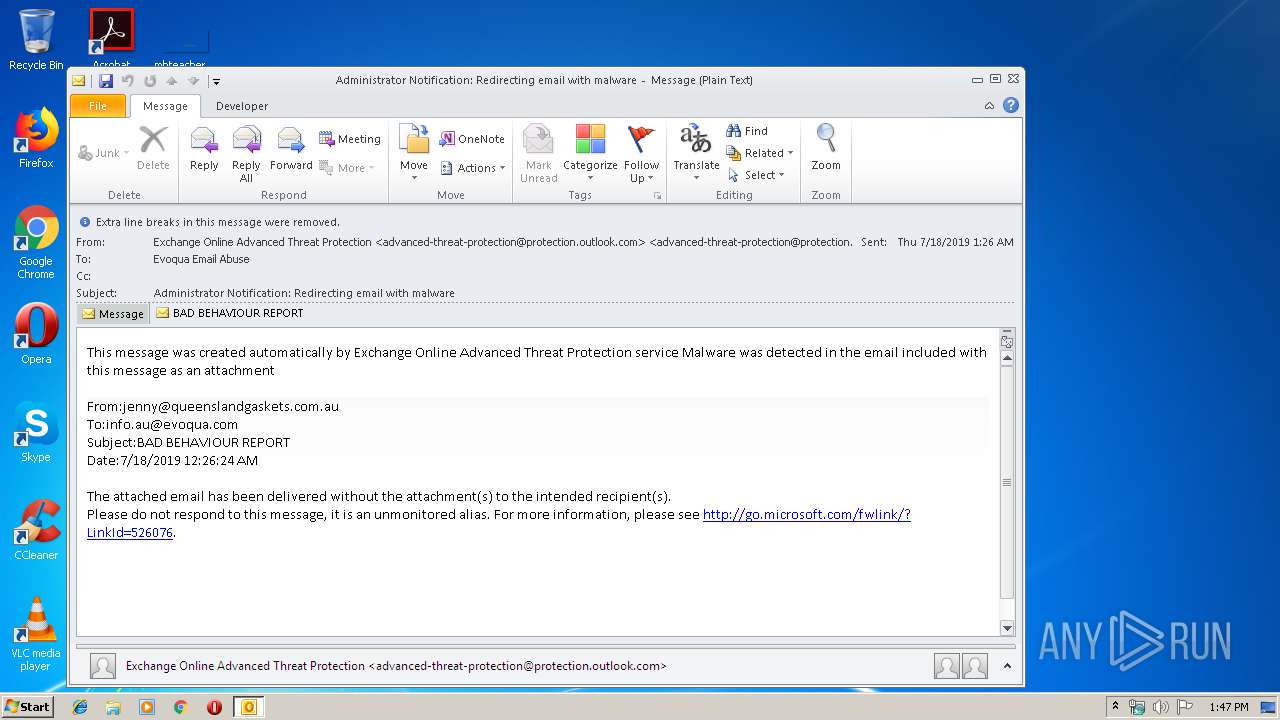
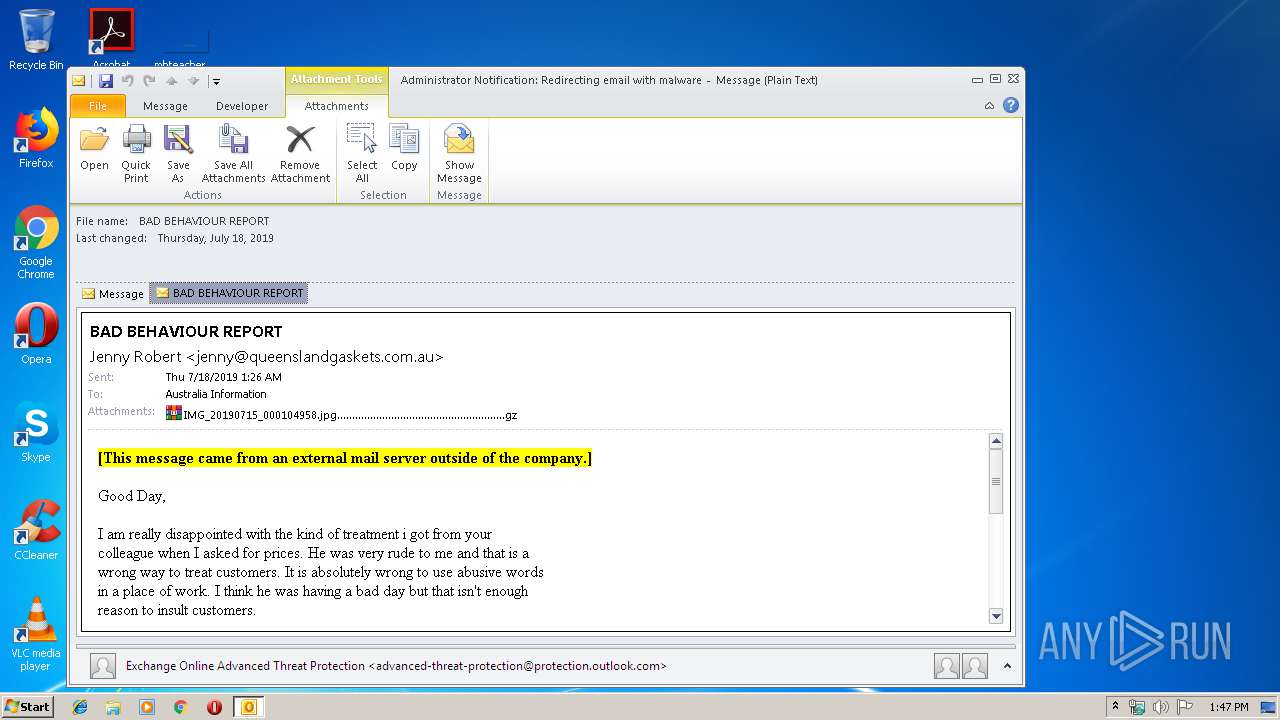
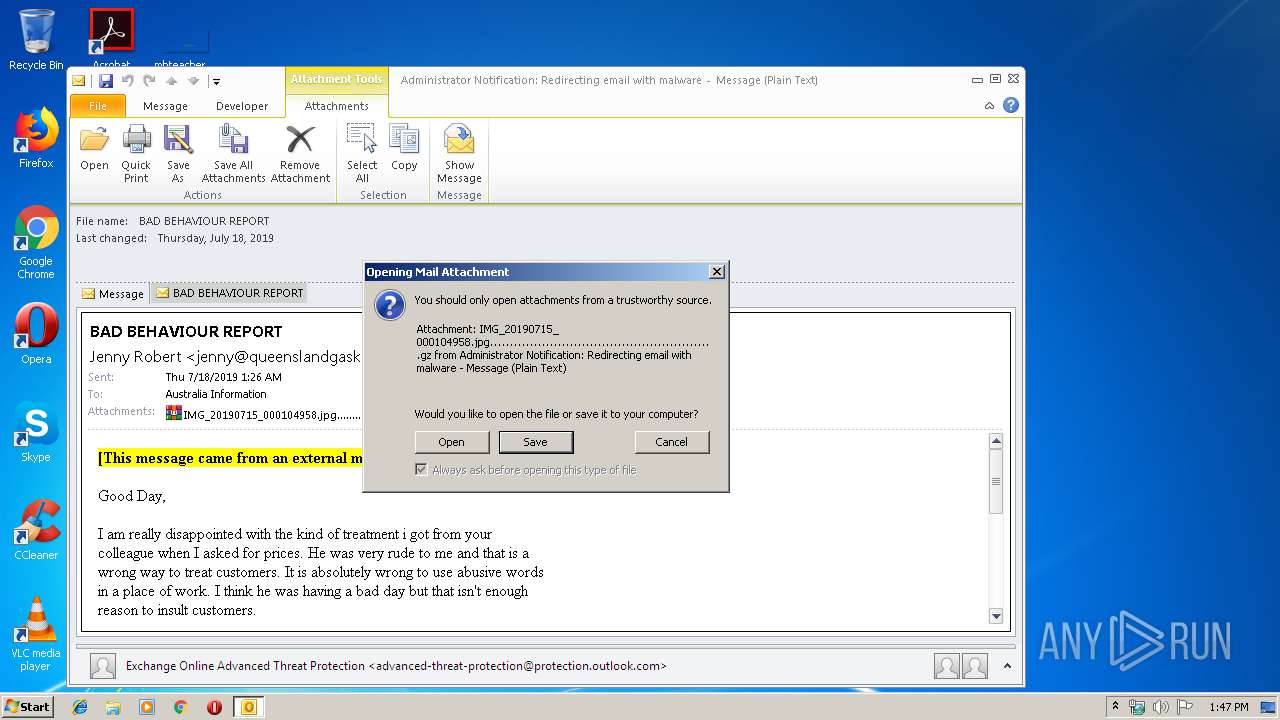
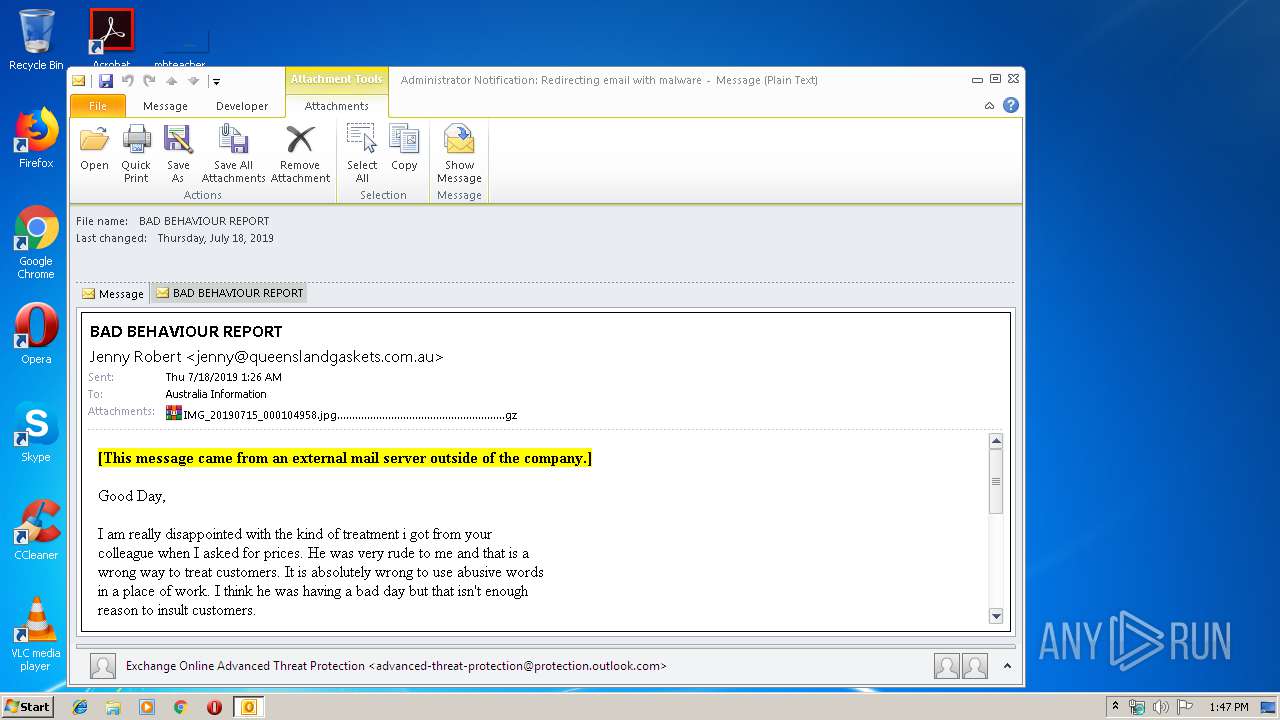
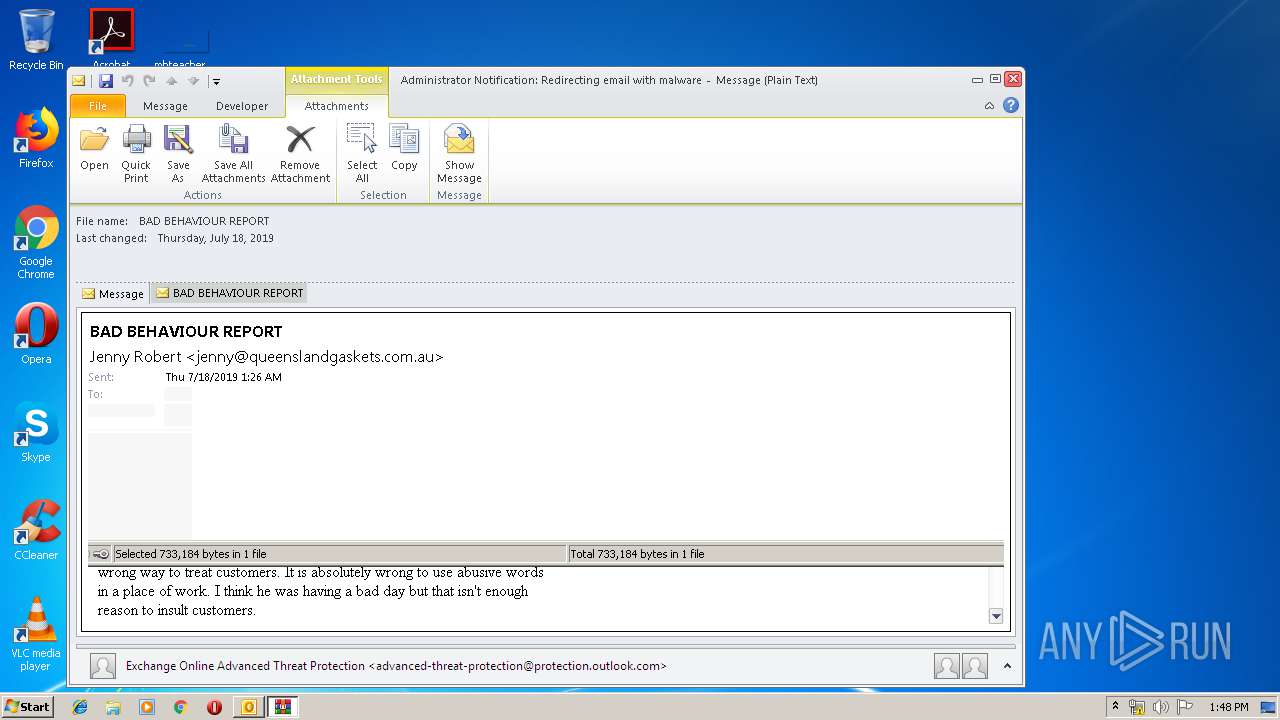
| File name: | Administrator Notification_ Redirecting email with malware.msg |
| Full analysis: | https://app.any.run/tasks/34d2453b-7230-4bbd-b7d2-0d239fa16303 |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | July 18, 2019, 12:47:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 46A34BF20D05CC28F1E89383904F67E1 |
| SHA1: | EC072EA282CB299F4738676858BD7D3D581DC8A9 |
| SHA256: | C4164257C3F415FF93A94E8E2E97E546E47A376EA2415BBC9EA94851F54CF064 |
| SSDEEP: | 6144:RTEW55uXBPxhG8NhMSovbPskPCHqUoY1iqcrrqJJ7ts3cT0FeJk40zC3weJygtxj:FOMdvbU+FKJ7tmka4B3wYy8I+7L |
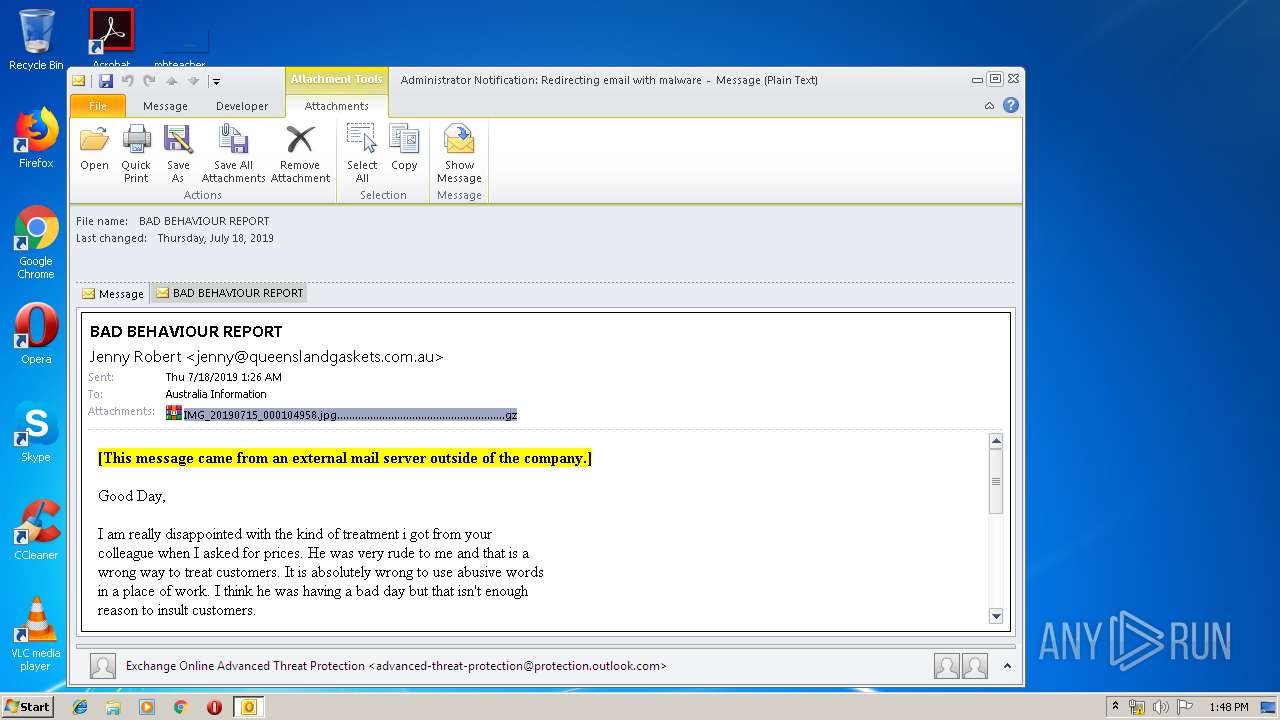
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3004)
PONY was detected
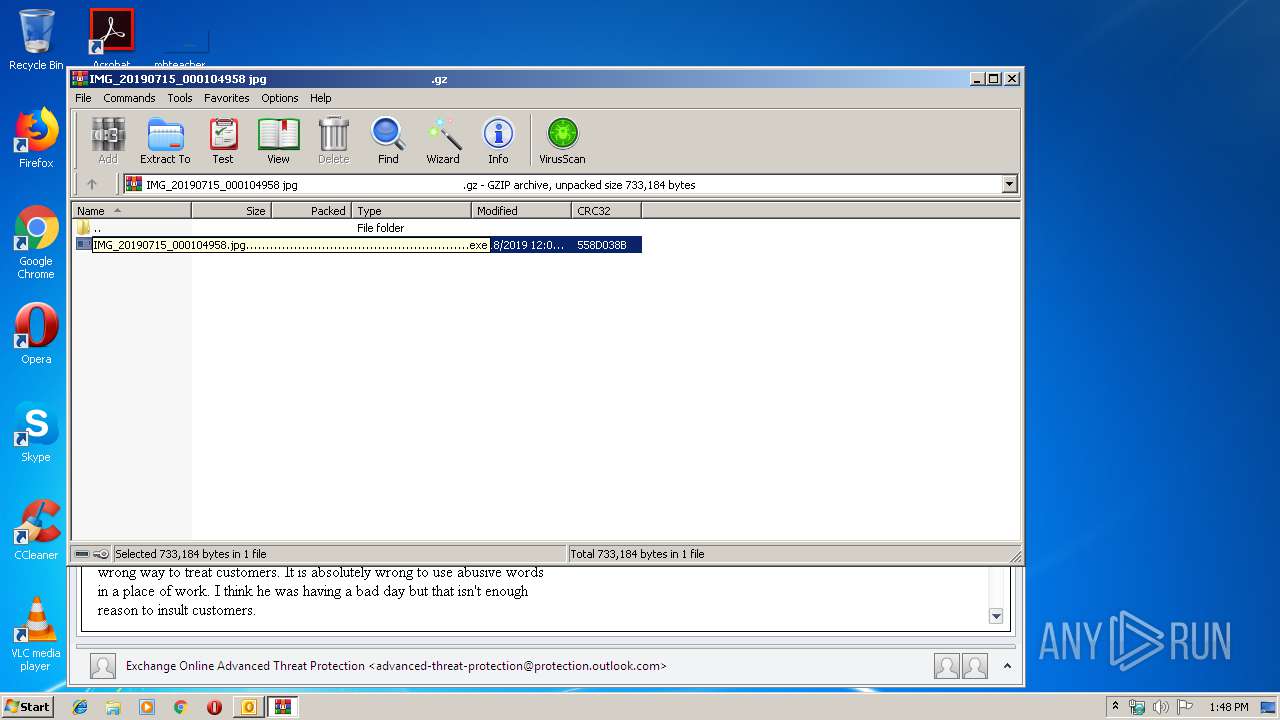
- IMG_20190715_000104958.jpg........................................................exe (PID: 2544)
Connects to CnC server
- IMG_20190715_000104958.jpg........................................................exe (PID: 3704)
- IMG_20190715_000104958.jpg........................................................exe (PID: 2544)
Application was dropped or rewritten from another process
- IMG_20190715_000104958.jpg........................................................exe (PID: 2128)
- IMG_20190715_000104958.jpg........................................................exe (PID: 3704)
- IMG_20190715_000104958.jpg........................................................exe (PID: 2544)
- IMG_20190715_000104958.jpg........................................................exe (PID: 2304)
Actions looks like stealing of personal data
- IMG_20190715_000104958.jpg........................................................exe (PID: 2544)
- IMG_20190715_000104958.jpg........................................................exe (PID: 3704)
Detected Pony/Fareit Trojan
- IMG_20190715_000104958.jpg........................................................exe (PID: 3704)
SUSPICIOUS
Starts CMD.EXE for commands execution
- IMG_20190715_000104958.jpg........................................................exe (PID: 2544)
- IMG_20190715_000104958.jpg........................................................exe (PID: 3704)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3004)
Executable content was dropped or overwritten
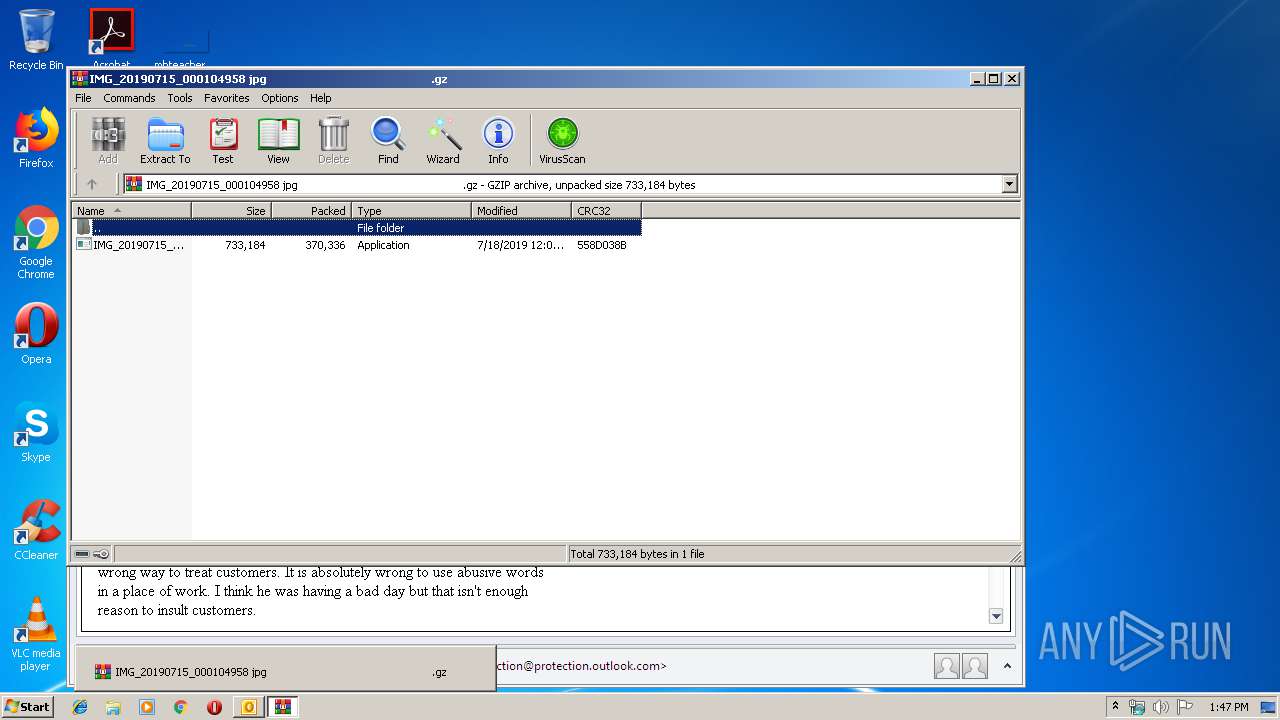
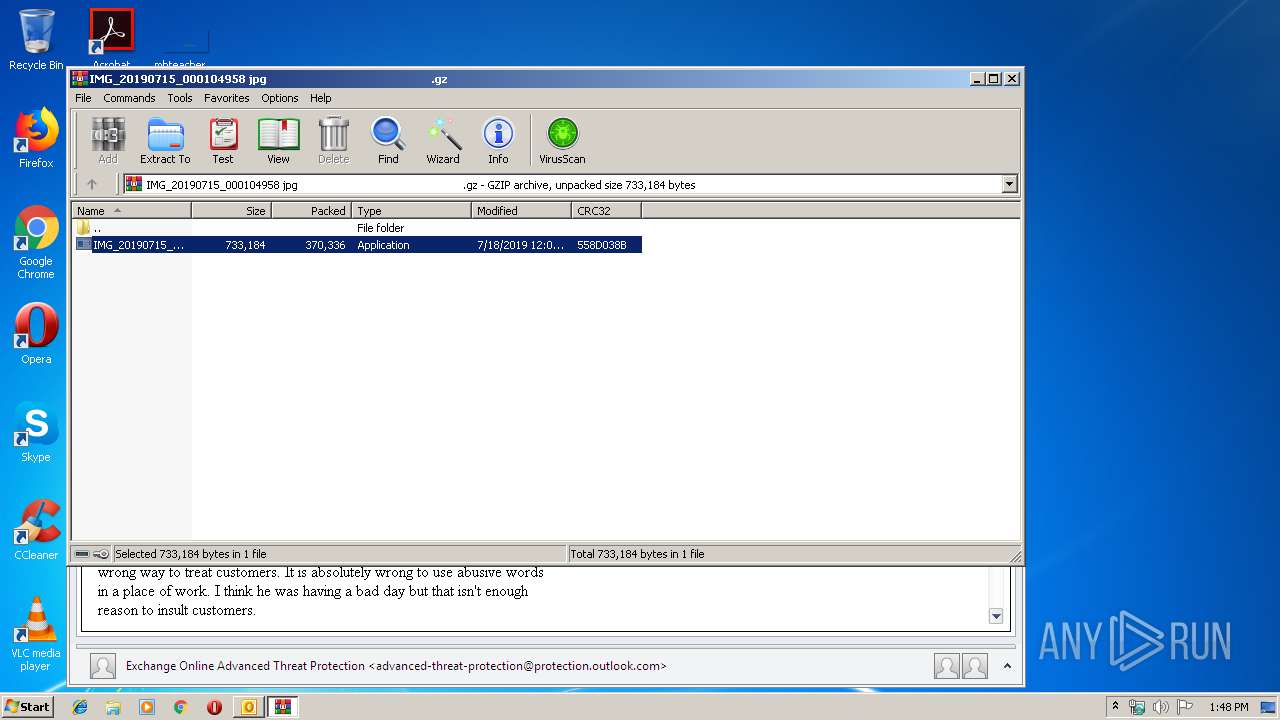
- WinRAR.exe (PID: 3952)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3004)
Application launched itself
- IMG_20190715_000104958.jpg........................................................exe (PID: 2304)
- IMG_20190715_000104958.jpg........................................................exe (PID: 2128)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
45
Monitored processes
8
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.9100\IMG_20190715_000104958.jpg........................................................exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.9100\IMG_20190715_000104958.jpg........................................................exe | — | WinRAR.exe | |||||||||||
User: admin Company: Saab Integrity Level: MEDIUM Description: Platformer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2296 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1650875.bat" "C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.7438\IMG_20190715_000104958.jpg........................................................exe" " | C:\Windows\system32\cmd.exe | — | IMG_20190715_000104958.jpg........................................................exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2304 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.7438\IMG_20190715_000104958.jpg........................................................exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.7438\IMG_20190715_000104958.jpg........................................................exe | — | WinRAR.exe | |||||||||||
User: admin Company: Saab Integrity Level: MEDIUM Description: Platformer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.9100\IMG_20190715_000104958.jpg........................................................exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.9100\IMG_20190715_000104958.jpg........................................................exe | IMG_20190715_000104958.jpg........................................................exe | ||||||||||||
User: admin Company: Saab Integrity Level: MEDIUM Description: Platformer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3416 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1655640.bat" "C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.9100\IMG_20190715_000104958.jpg........................................................exe" " | C:\Windows\system32\cmd.exe | — | IMG_20190715_000104958.jpg........................................................exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.7438\IMG_20190715_000104958.jpg........................................................exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.7438\IMG_20190715_000104958.jpg........................................................exe | IMG_20190715_000104958.jpg........................................................exe | ||||||||||||
User: admin Company: Saab Integrity Level: MEDIUM Description: Platformer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\803OZQHK\IMG_20190715_000104958 jpg .gz" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 757
Read events
2 305
Write events
431
Delete events
21
Modification events
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 'u# |
Value: 27752300BC0B0000010000000000000000000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: BC0B000006236CF4663DD50100000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220131360 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1324482581 | |||
Executable files
2
Suspicious files
2
Text files
26
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRB517.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF748B35072A3DDB38.TMP | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\803OZQHK\IMG_20190715_000104958 jpg (2).gz\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\803OZQHK\IMG_20190715_000104958 jpg .gz | compressed | |
MD5:— | SHA256:— | |||
| 3952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.7438\IMG_20190715_000104958.jpg........................................................exe | executable | |
MD5:— | SHA256:— | |||
| 3952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3952.9100\IMG_20190715_000104958.jpg........................................................exe | executable | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\803OZQHK\IMG_20190715_000104958 jpg (2).gz | compressed | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_89CBD978722BC9499E46F671949E4AB9.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_D810E424E7095649A157EA3735BDFE42.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
2
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3704 | IMG_20190715_000104958.jpg........................................................exe | GET | 404 | 111.90.142.106:80 | http://readadrsswe.ga/edupentest/edu.exe | MY | html | 1.12 Kb | malicious |
2544 | IMG_20190715_000104958.jpg........................................................exe | GET | 404 | 111.90.142.106:80 | http://readadrsswe.ga/edupentest/edu.exe | MY | html | 1.12 Kb | malicious |
3704 | IMG_20190715_000104958.jpg........................................................exe | POST | 200 | 111.90.142.106:80 | http://readadrsswe.ga/edupentest/gate.php | MY | binary | 20 b | malicious |
2544 | IMG_20190715_000104958.jpg........................................................exe | POST | 200 | 111.90.142.106:80 | http://readadrsswe.ga/edupentest/gate.php | MY | binary | 20 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | IMG_20190715_000104958.jpg........................................................exe | 111.90.142.106:80 | readadrsswe.ga | — | MY | suspicious |
2544 | IMG_20190715_000104958.jpg........................................................exe | 111.90.142.106:80 | readadrsswe.ga | — | MY | suspicious |
3004 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
readadrsswe.ga |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
3704 | IMG_20190715_000104958.jpg........................................................exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3704 | IMG_20190715_000104958.jpg........................................................exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3704 | IMG_20190715_000104958.jpg........................................................exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
3704 | IMG_20190715_000104958.jpg........................................................exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
3704 | IMG_20190715_000104958.jpg........................................................exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |
3704 | IMG_20190715_000104958.jpg........................................................exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
3704 | IMG_20190715_000104958.jpg........................................................exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader Checkin |
3704 | IMG_20190715_000104958.jpg........................................................exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony CnC Server stdResponse |
3704 | IMG_20190715_000104958.jpg........................................................exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 3 |
2 ETPRO signatures available at the full report