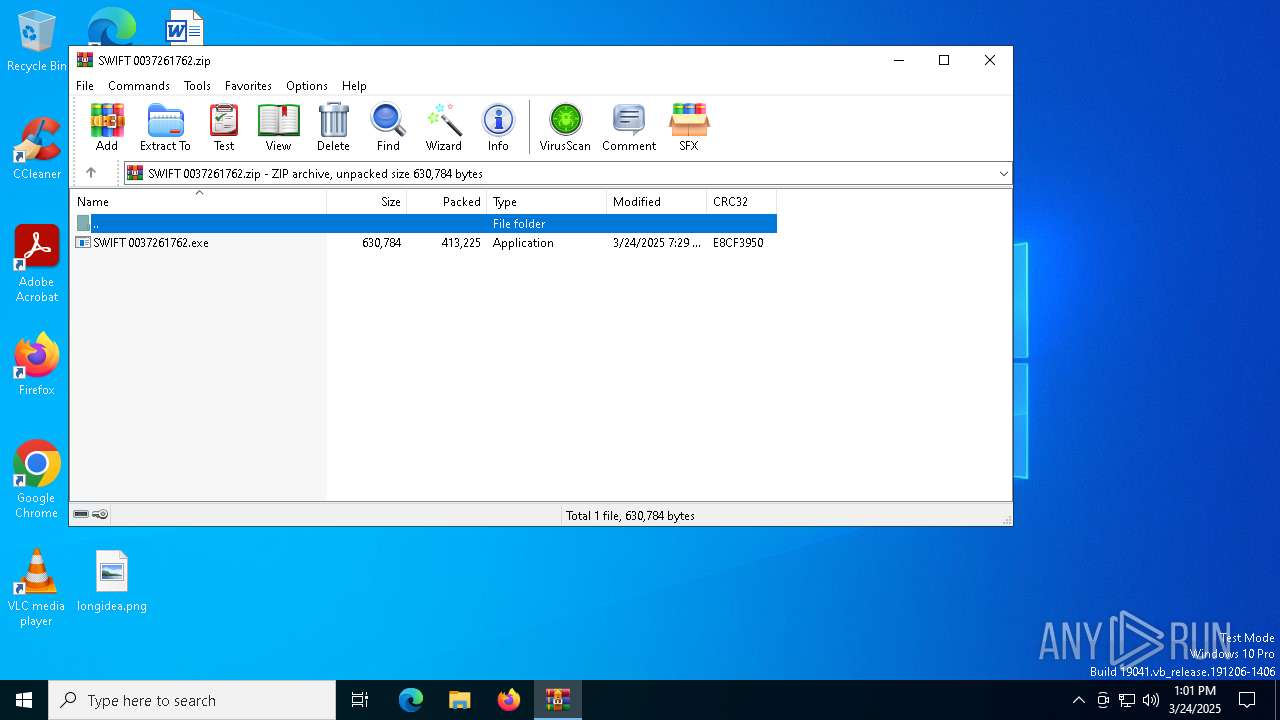
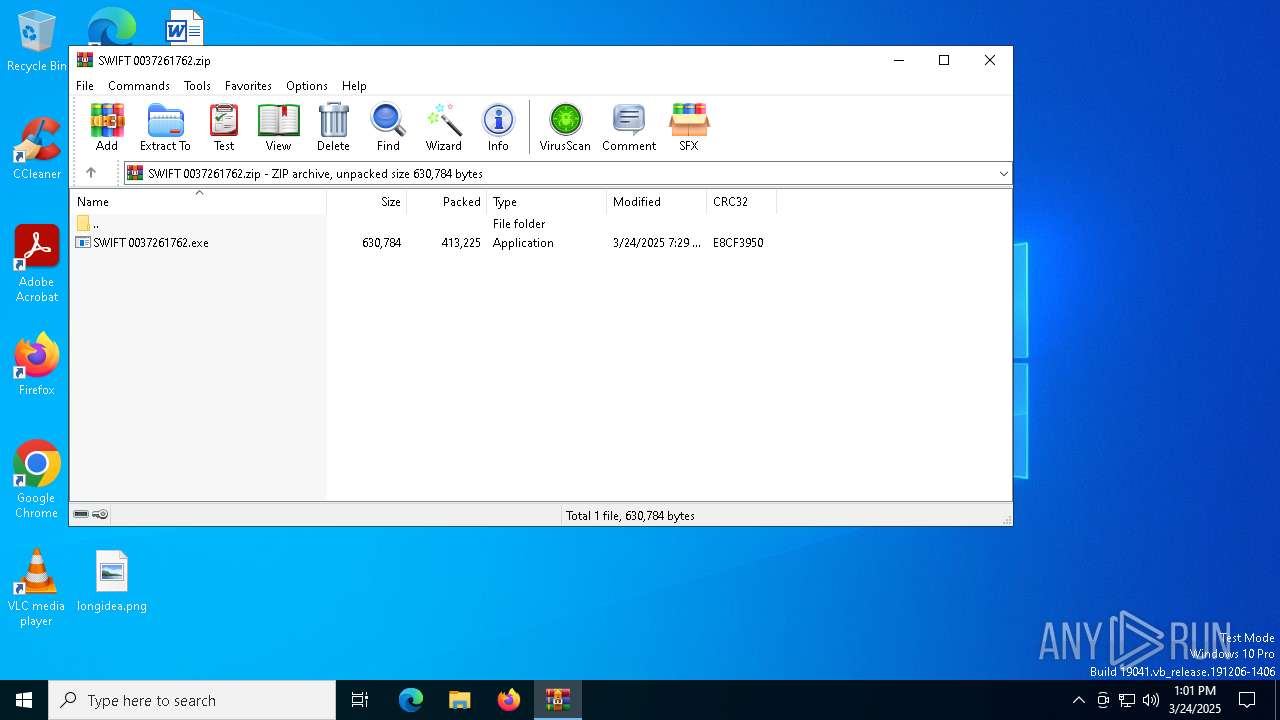
| File name: | SWIFT 0037261762.zip |
| Full analysis: | https://app.any.run/tasks/9ea1c489-9fdd-4477-9023-b9219f850ea0 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 24, 2025, 13:00:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 26B84009B2C54D331DB6479BE68091BC |
| SHA1: | 38303B67EEA26A22CD9EBA557D22096EAF577170 |
| SHA256: | C3B5E071B93BF026DF68AA9C77B1009A8C4C009CE2C54512A0ECE837AF8DCFA0 |
| SSDEEP: | 12288:9KPc3GsD/nQVdKCYsu6/E3F7pZdjFbi2BD9o/osOrOK3sZCYFhxpKqpZ:9KPc3pD/nEdKCYsu683F7pZdZbi2BD9i |
MALICIOUS
Actions looks like stealing of personal data
- skype.exe (PID: 7620)
- cmd.exe (PID: 8032)
- csrss.exe (PID: 5824)
- skype.exe (PID: 7396)
Create files in the Startup directory
- cmd.exe (PID: 8032)
FORMBOOK has been detected
- cmd.exe (PID: 7776)
- explorer.exe (PID: 5492)
Changes the login/logoff helper path in the registry
- reg.exe (PID: 2140)
FORMBOOK has been detected (SURICATA)
- explorer.exe (PID: 5492)
Connects to the CnC server
- explorer.exe (PID: 5492)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 8032)
Starts CMD.EXE for commands execution
- SWIFT 0037261762.exe (PID: 960)
- skype.exe (PID: 7620)
- explorer.exe (PID: 5492)
- cmd.exe (PID: 7776)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 8032)
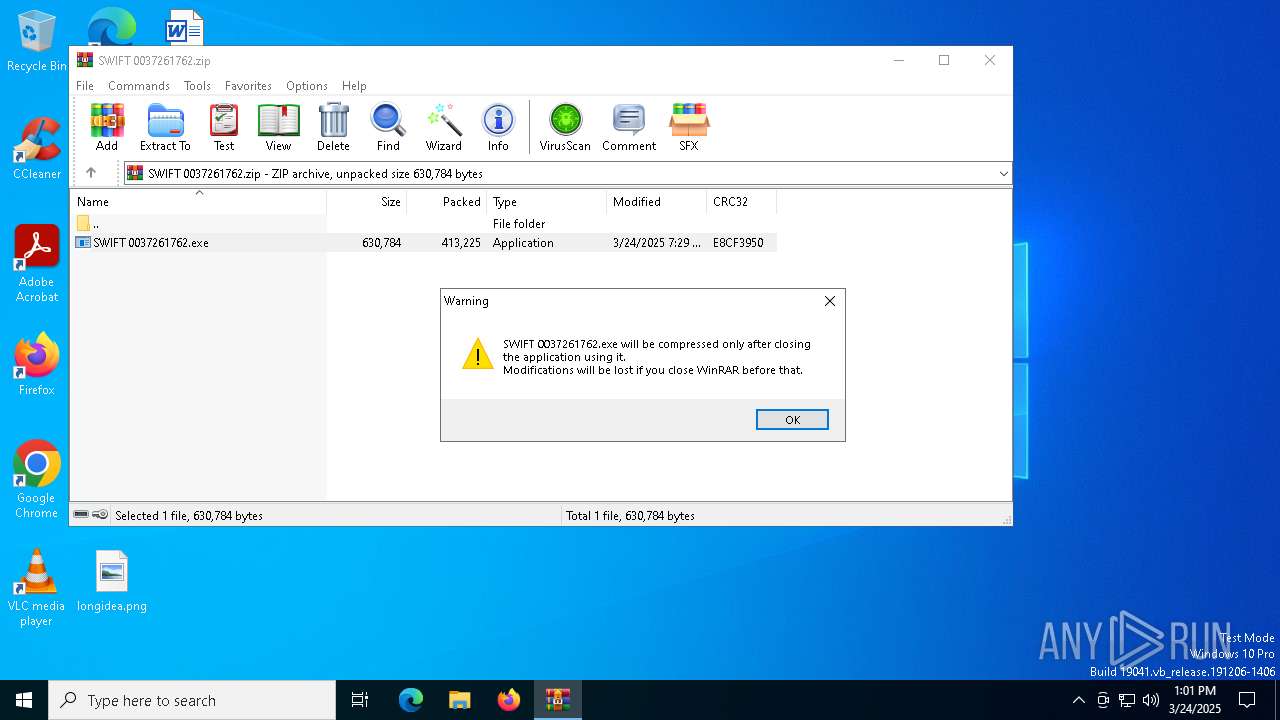
Executable content was dropped or overwritten
- SWIFT 0037261762.exe (PID: 960)
- cmd.exe (PID: 8032)
Reads security settings of Internet Explorer
- SWIFT 0037261762.exe (PID: 960)
Starts itself from another location
- SWIFT 0037261762.exe (PID: 960)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7384)
The executable file from the user directory is run by the CMD process
- skype.exe (PID: 7396)
Application launched itself
- cmd.exe (PID: 7776)
Deletes system .NET executable
- cmd.exe (PID: 7352)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 5492)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6272)
Reads the machine GUID from the registry
- SWIFT 0037261762.exe (PID: 960)
- skype.exe (PID: 7620)
- skype.exe (PID: 7396)
Process checks computer location settings
- SWIFT 0037261762.exe (PID: 960)
Checks supported languages
- SWIFT 0037261762.exe (PID: 960)
- skype.exe (PID: 7620)
- skype.exe (PID: 7396)
Manual execution by a user
- cmd.exe (PID: 7776)
Autorun file from Startup directory
- cmd.exe (PID: 8032)
Reads the software policy settings
- slui.exe (PID: 7184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 07:29:46 |
| ZipCRC: | 0xe8cf3950 |
| ZipCompressedSize: | 413225 |
| ZipUncompressedSize: | 630784 |
| ZipFileName: | SWIFT 0037261762.exe |
Total processes
159
Monitored processes
26
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | ping 127.0.0.1 -n 13 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6272.8144\SWIFT 0037261762.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6272.8144\SWIFT 0037261762.exe | WinRAR.exe | ||||||||||||
User: admin Company: 9EJJDD=74A3@G=C:FG?CJH23 Integrity Level: MEDIUM Description: A<9?>CDD2?=BGIBF:=549 Exit code: 0 Version: 9.14.19.24 Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | REG ADD "HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /f /v "Shell" /t REG_SZ /d "explorer.exe,C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\skype\skype.exe," | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5824 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
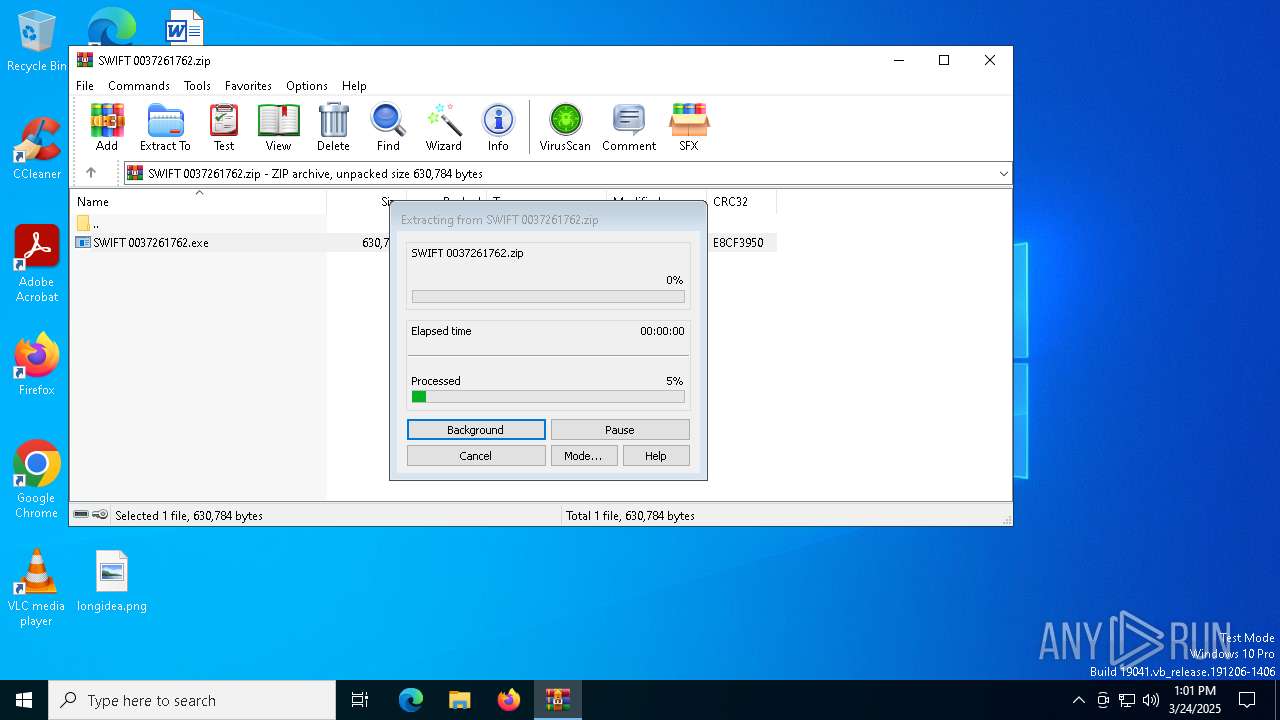
| 6272 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SWIFT 0037261762.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7184 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7292 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 570
Read events
5 568
Write events
2
Delete events
0
Modification events
| (PID) Process: | (8168) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe,C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\skype\skype.exe, | |||
| (PID) Process: | (2140) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe,C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\skype\skype.exe, | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6272 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6272.8144\SWIFT 0037261762.exe | executable | |
MD5:33597EEA937DE9FC85C91FC86D4081DA | SHA256:EA4FE51E13F6AB1785535B32345F69EF110E21981BF7DBB09CE02C0BDEC1E43C | |||
| 8032 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\skype\skype.exe | executable | |
MD5:33597EEA937DE9FC85C91FC86D4081DA | SHA256:EA4FE51E13F6AB1785535B32345F69EF110E21981BF7DBB09CE02C0BDEC1E43C | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 960 | SWIFT 0037261762.exe | C:\Users\admin\AppData\Local\Temp\skype.exe | executable | |
MD5:33597EEA937DE9FC85C91FC86D4081DA | SHA256:EA4FE51E13F6AB1785535B32345F69EF110E21981BF7DBB09CE02C0BDEC1E43C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.48.23.189:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5212 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 403 | 64.190.62.22:80 | http://www.seo-companies22.online/3nop/?Tpst_=Mp2LiTVHolrXMjl&GPTp60=+o10su/0Zm9klbwwq28MsoxESSfq7AjMcojnTuIB5njs5atToi3KoOFqATZ+tR6Glq0r | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.48.23.189:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2656 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5492 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |